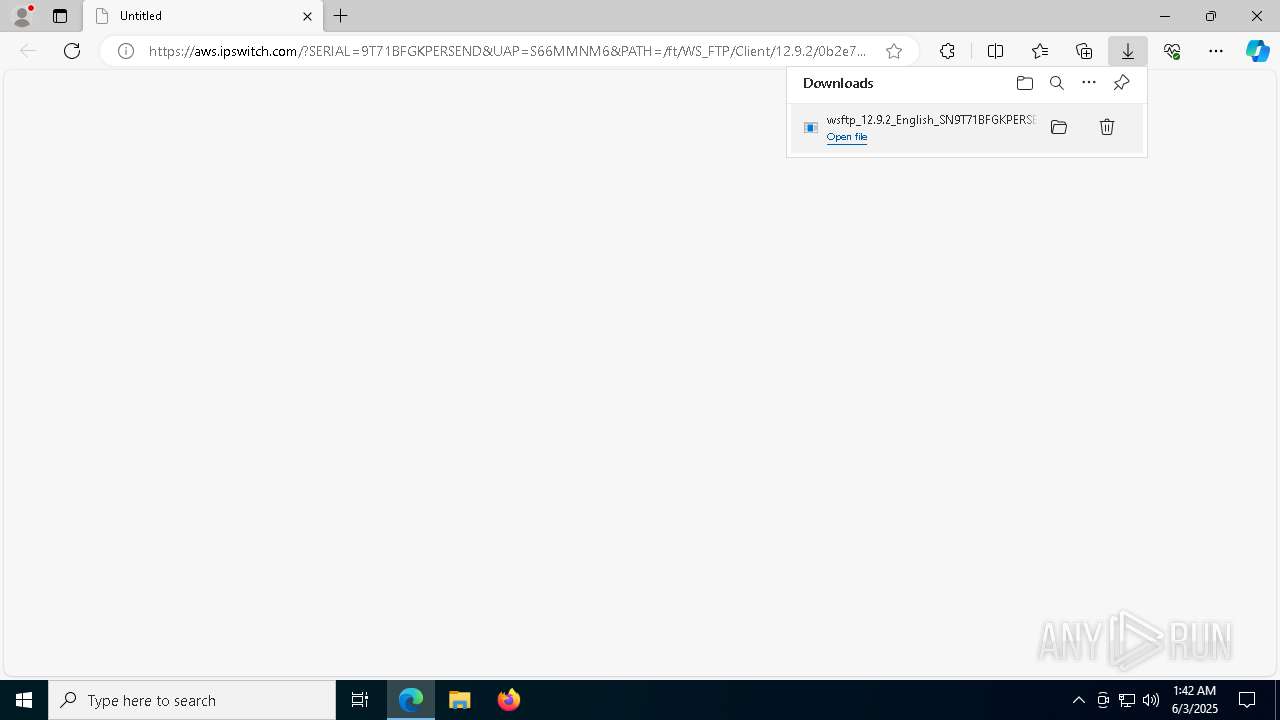
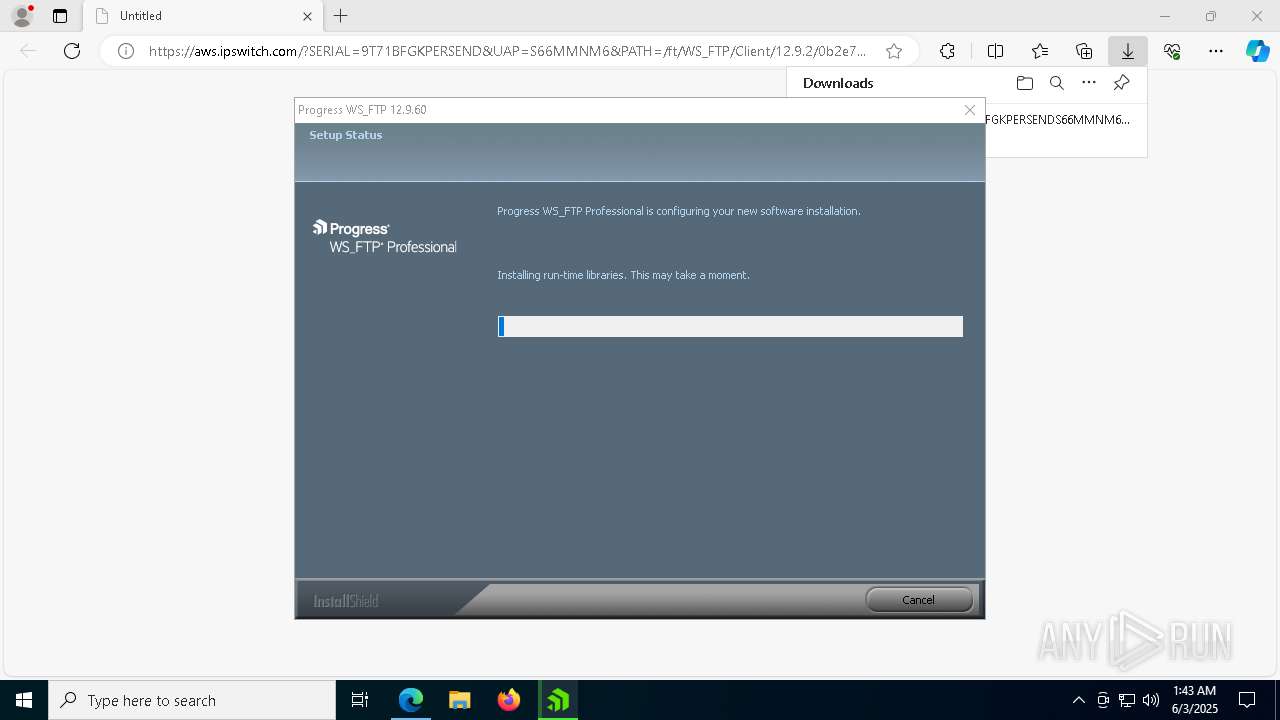
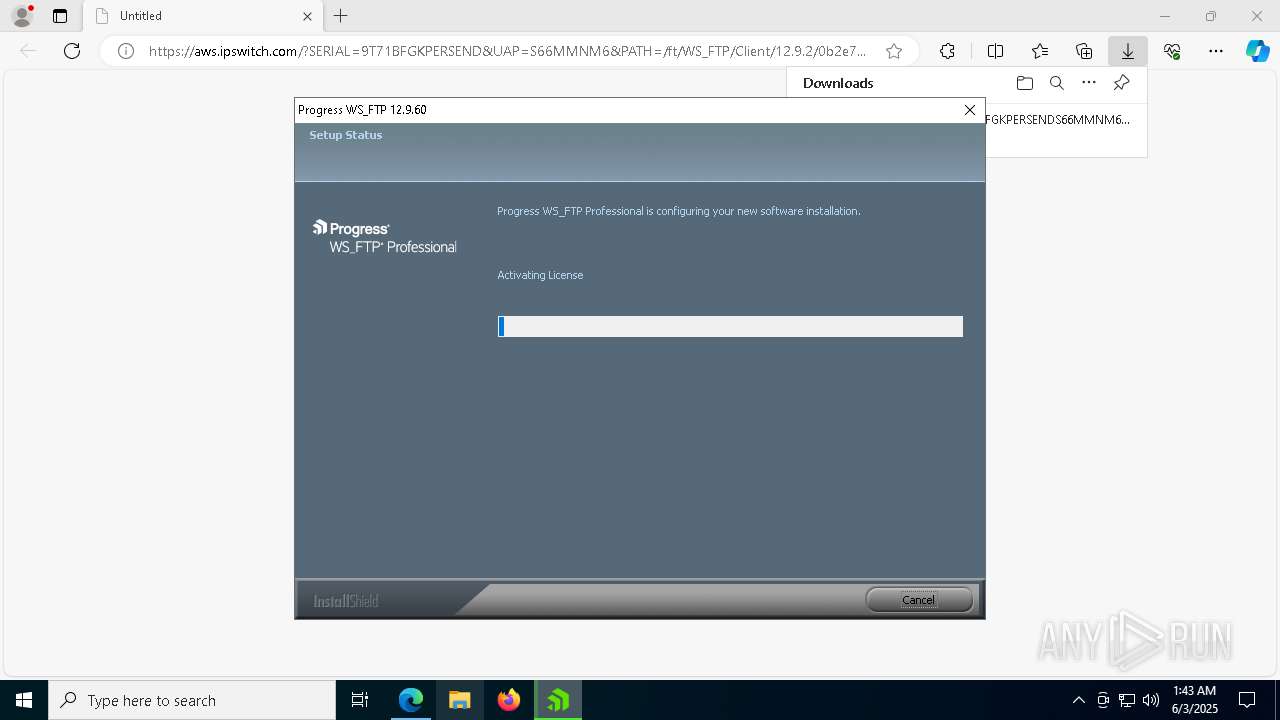
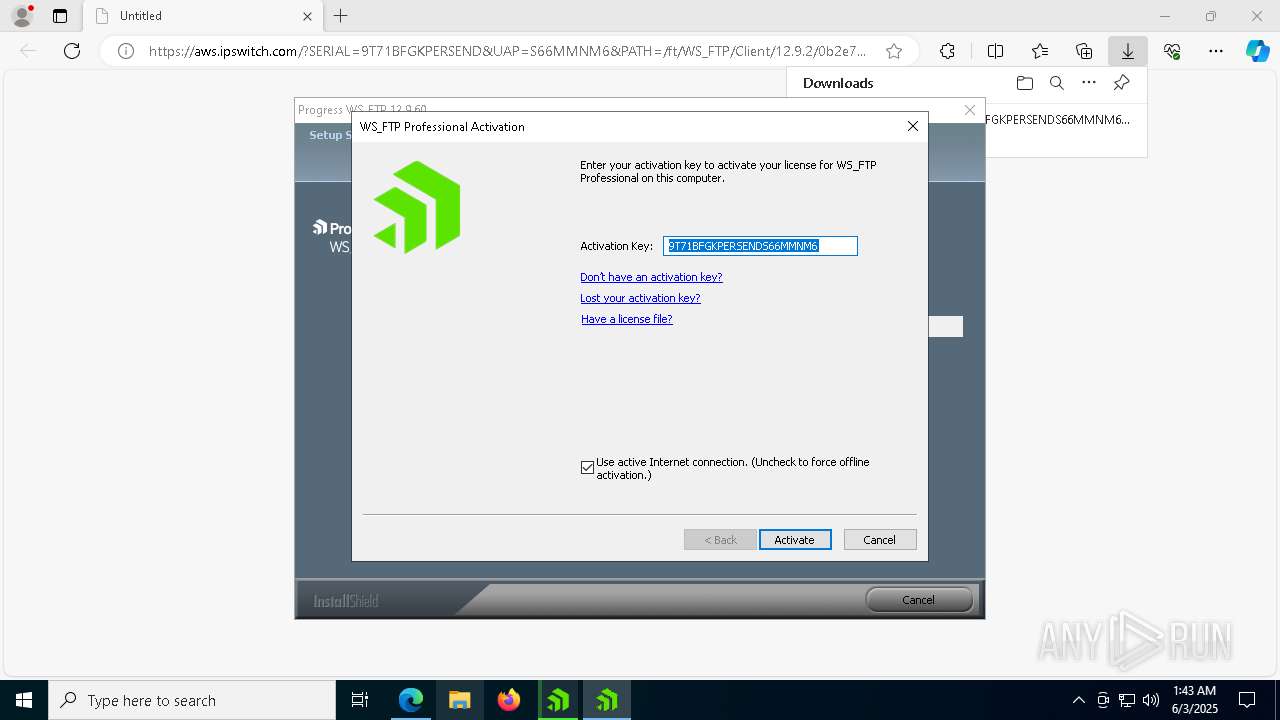
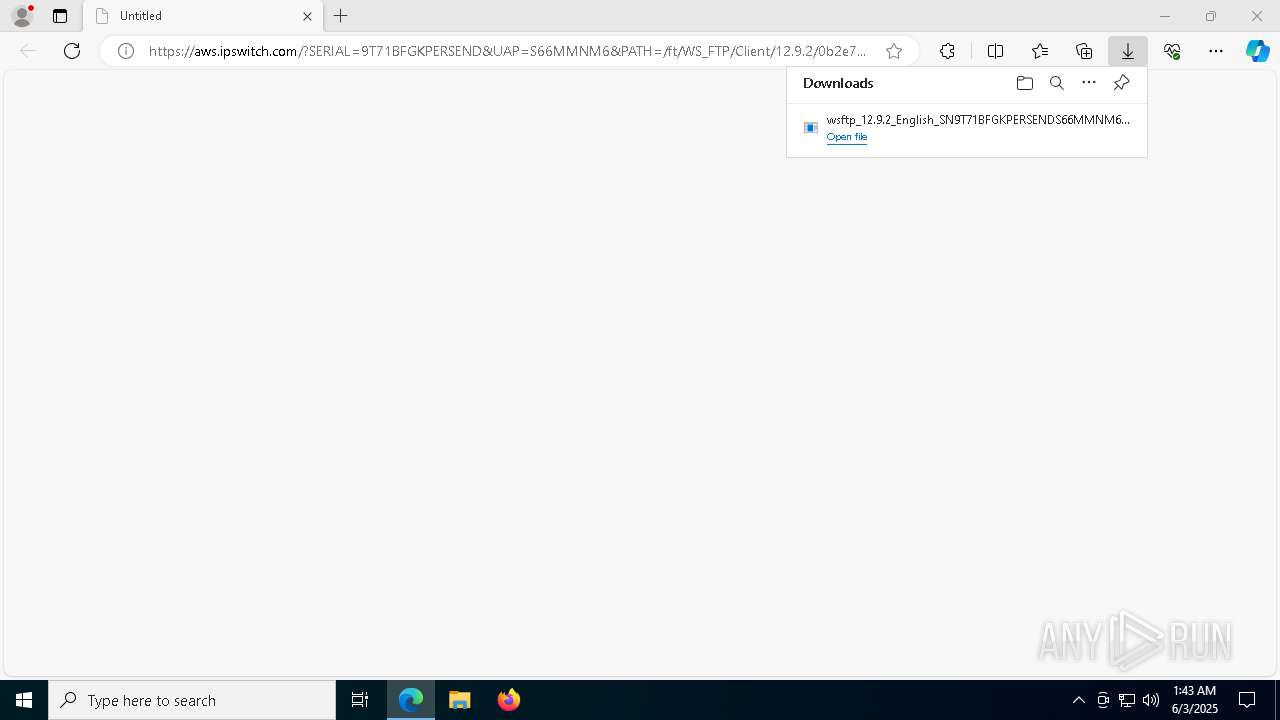
| URL: | https://aws.ipswitch.com/?SERIAL=9T71BFGKPERSEND&UAP=S66MMNM6&PATH=/ft/WS_FTP/Client/12.9.2/0b2e7195ybe9ent6437a6w40bfx82dfn4ce608a5/wsftp_12.9.2_English.exe |
| Full analysis: | https://app.any.run/tasks/7af37889-c64d-4bbb-a33f-ea10f41244f3 |
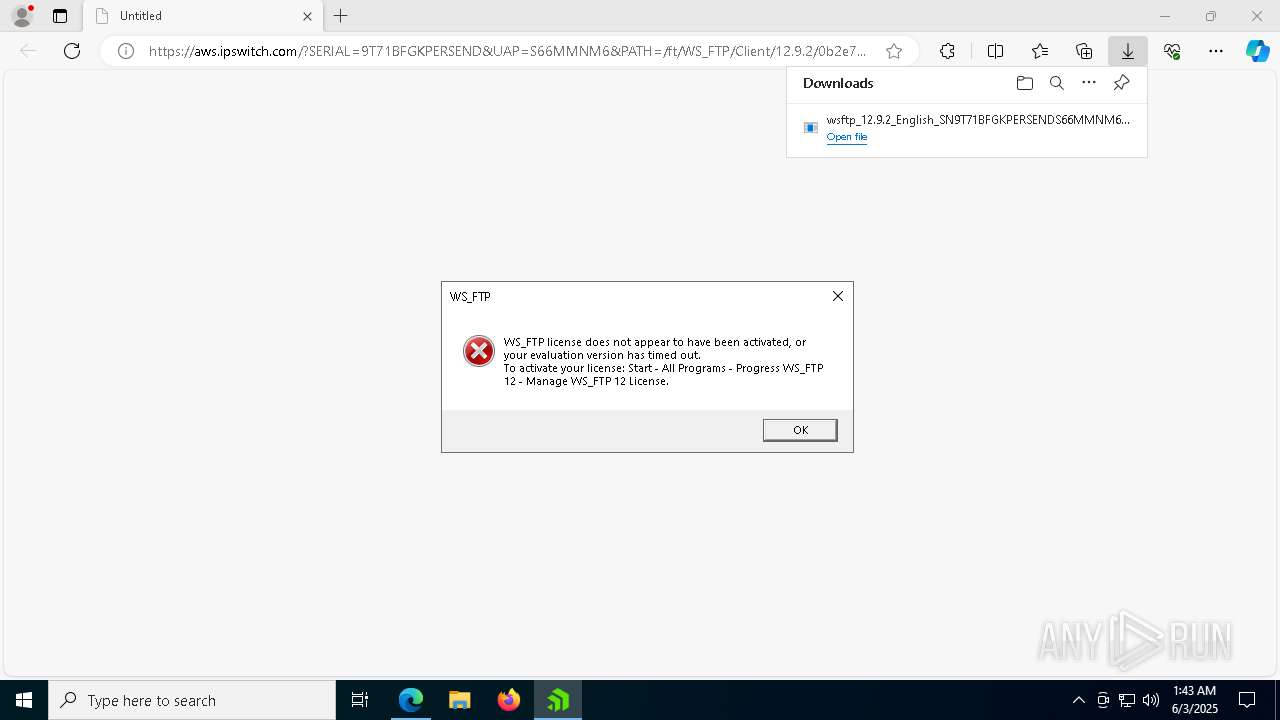
| Verdict: | Malicious activity |
| Analysis date: | June 03, 2025, 01:42:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 0B44D1A09821915CACE8C5D0A9144DFC |
| SHA1: | 9EF7B8EA196BD04C29D88BF6BBEF9859796A19D0 |
| SHA256: | 720B7AC060E3A03A162986EAC3C276A180A6408A7D00B0726819261135B6232C |
| SSDEEP: | 3:N844VWEqXF1eu1QSUYIUuRKUNnUhcH5uRTETKM9z3OGiA:244VEXFvSPYmNnq2URHM9z |
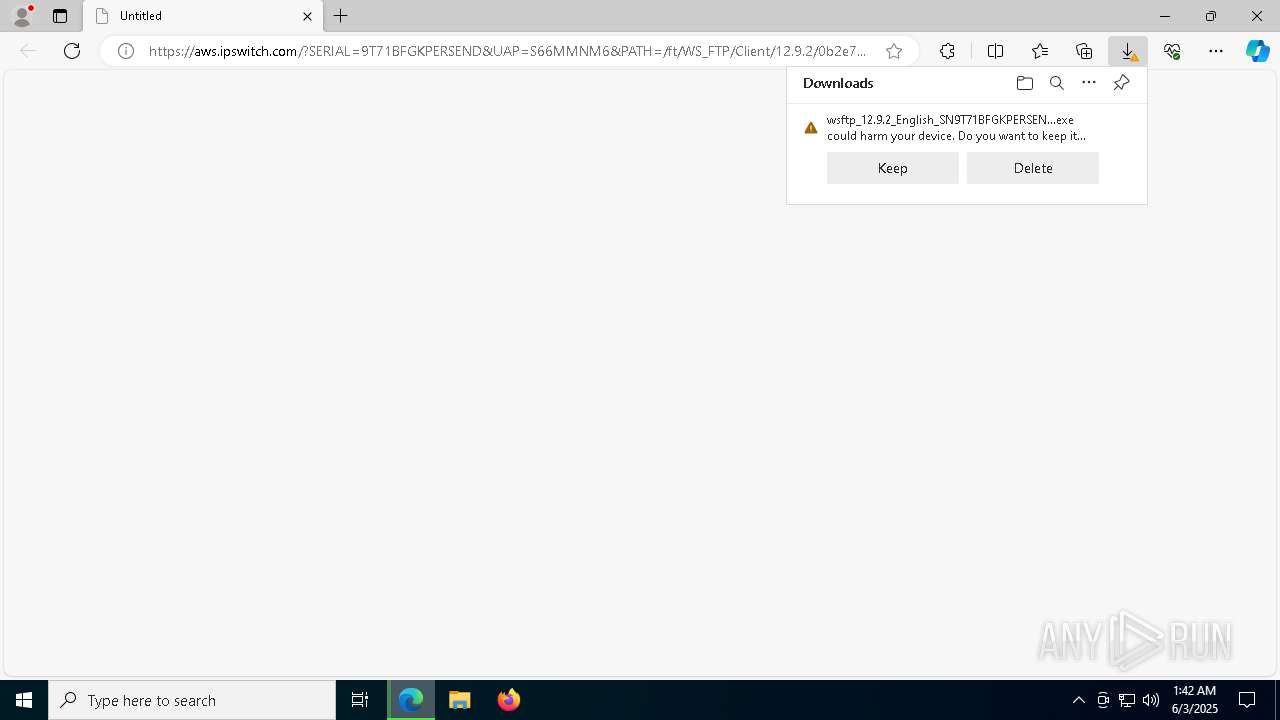
MALICIOUS
Executing a file with an untrusted certificate
- vcredist2012_x86.exe (PID: 1812)
- vcredist2012_x86.exe (PID: 7292)
Registers / Runs the DLL via REGSVR32.EXE
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 924)
SUSPICIOUS
Executable content was dropped or overwritten
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 924)
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 4976)
- vcredist2012_x86.exe (PID: 7292)
- vcredist2012_x86.exe (PID: 1812)
- vc_redist.x86.exe (PID: 1276)
- vc_redist.x86.exe (PID: 7796)
- VC_redist.x86.exe (PID: 8100)
- VC_redist.x86.exe (PID: 5540)
- VC_redist.x86.exe (PID: 7312)
- vc_redist.x64.exe (PID: 8076)
- vc_redist.x64.exe (PID: 5392)
- VC_redist.x64.exe (PID: 2892)
- VC_redist.x64.exe (PID: 2192)
- VC_redist.x64.exe (PID: 4980)
Process drops legitimate windows executable
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 924)
- vcredist2012_x86.exe (PID: 1812)
- vcredist2012_x86.exe (PID: 7292)
- msiexec.exe (PID: 8152)
- vc_redist.x86.exe (PID: 1276)
- vc_redist.x86.exe (PID: 7796)
- VC_redist.x86.exe (PID: 7312)
- VC_redist.x86.exe (PID: 8100)
- vc_redist.x64.exe (PID: 8076)
- VC_redist.x64.exe (PID: 2892)
- vc_redist.x64.exe (PID: 5392)
- VC_redist.x64.exe (PID: 4980)
Searches for installed software
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 924)
- dllhost.exe (PID: 2124)
There is functionality for taking screenshot (YARA)
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 4976)
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 924)
Executes as Windows Service
- VSSVC.exe (PID: 7492)
Starts a Microsoft application from unusual location
- vcredist2012_x86.exe (PID: 1812)
- vcredist2012_x86.exe (PID: 7292)
- vc_redist.x86.exe (PID: 1276)
- vc_redist.x86.exe (PID: 7796)
- VC_redist.x86.exe (PID: 8100)
- vc_redist.x64.exe (PID: 5392)
- VC_redist.x64.exe (PID: 2892)
- vc_redist.x64.exe (PID: 8076)
Application launched itself
- vcredist2012_x86.exe (PID: 1812)
- VC_redist.x86.exe (PID: 7892)
- VC_redist.x86.exe (PID: 5540)
- VC_redist.x64.exe (PID: 5604)
- VC_redist.x64.exe (PID: 2192)
The process drops C-runtime libraries
- msiexec.exe (PID: 8152)
Starts itself from another location
- vc_redist.x86.exe (PID: 7796)
- vc_redist.x64.exe (PID: 5392)
INFO
Reads the computer name
- identity_helper.exe (PID: 6640)
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 924)
- ISBEW64.exe (PID: 4748)
- ISBEW64.exe (PID: 3100)
- ISBEW64.exe (PID: 4648)
- ISBEW64.exe (PID: 7580)
- ISBEW64.exe (PID: 7824)
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 4976)
- ISBEW64.exe (PID: 7548)
Executable content was dropped or overwritten
- msedge.exe (PID: 776)
- msiexec.exe (PID: 8152)
Checks supported languages
- identity_helper.exe (PID: 6640)
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 4976)
- ISBEW64.exe (PID: 3100)
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 924)
- ISBEW64.exe (PID: 4748)
- ISBEW64.exe (PID: 7824)
- ISBEW64.exe (PID: 4648)
- ISBEW64.exe (PID: 7580)
- ISBEW64.exe (PID: 7548)
Reads Environment values
- identity_helper.exe (PID: 6640)
Application launched itself
- msedge.exe (PID: 776)
Create files in a temporary directory
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 924)
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 4976)
The sample compiled with english language support
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 4976)
- wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe (PID: 924)
- vcredist2012_x86.exe (PID: 1812)
- vcredist2012_x86.exe (PID: 7292)
- msiexec.exe (PID: 8152)
- vc_redist.x86.exe (PID: 1276)
- vc_redist.x86.exe (PID: 7796)
- VC_redist.x86.exe (PID: 8100)
- VC_redist.x86.exe (PID: 5540)
- VC_redist.x86.exe (PID: 7312)
- vc_redist.x64.exe (PID: 5392)
- VC_redist.x64.exe (PID: 2892)
- VC_redist.x64.exe (PID: 2192)
- VC_redist.x64.exe (PID: 4980)
- vc_redist.x64.exe (PID: 8076)
Manages system restore points
- SrTasks.exe (PID: 4608)
The sample compiled with chinese language support
- msiexec.exe (PID: 8152)
The sample compiled with Italian language support
- msiexec.exe (PID: 8152)
The sample compiled with spanish language support
- msiexec.exe (PID: 8152)
The sample compiled with russian language support
- msiexec.exe (PID: 8152)
The sample compiled with german language support
- msiexec.exe (PID: 8152)
The sample compiled with japanese language support
- msiexec.exe (PID: 8152)
The sample compiled with french language support
- msiexec.exe (PID: 8152)
The sample compiled with korean language support
- msiexec.exe (PID: 8152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
201
Monitored processes
69
Malicious processes
7
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://aws.ipswitch.com/?SERIAL=9T71BFGKPERSEND&UAP=S66MMNM6&PATH=/ft/WS_FTP/Client/12.9.2/0b2e7195ybe9ent6437a6w40bfx82dfn4ce608a5/wsftp_12.9.2_English.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
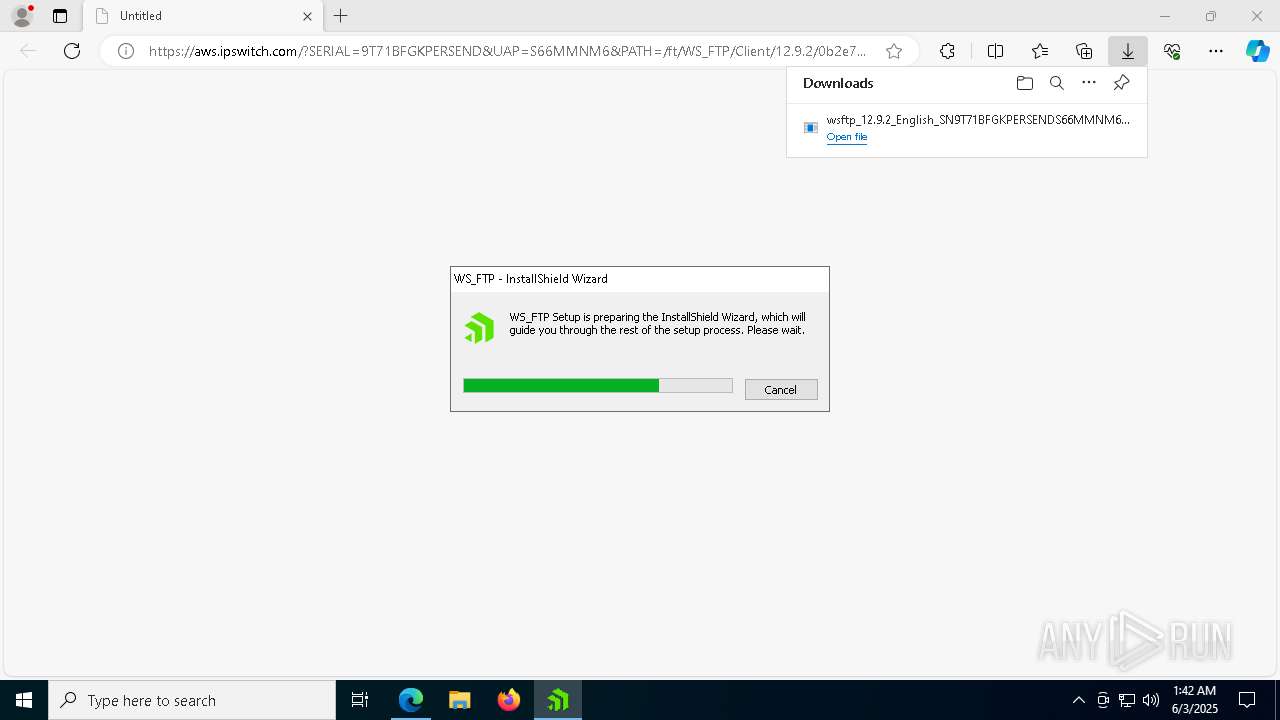
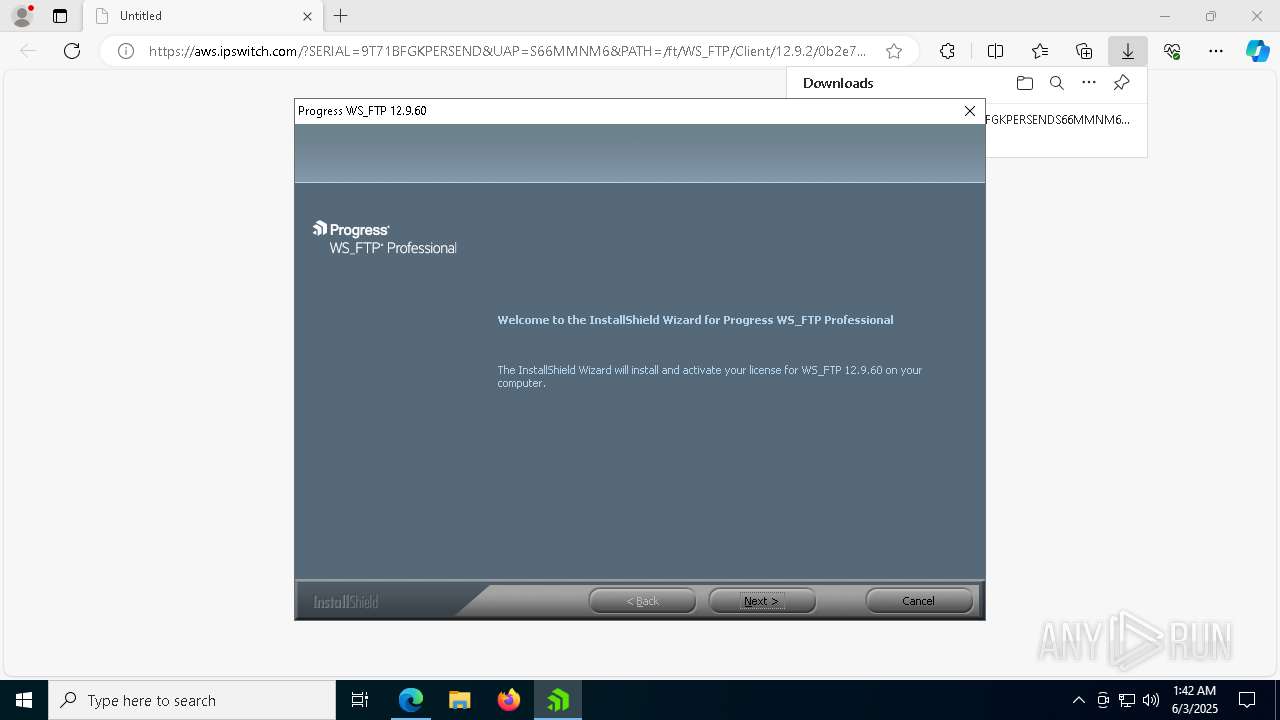
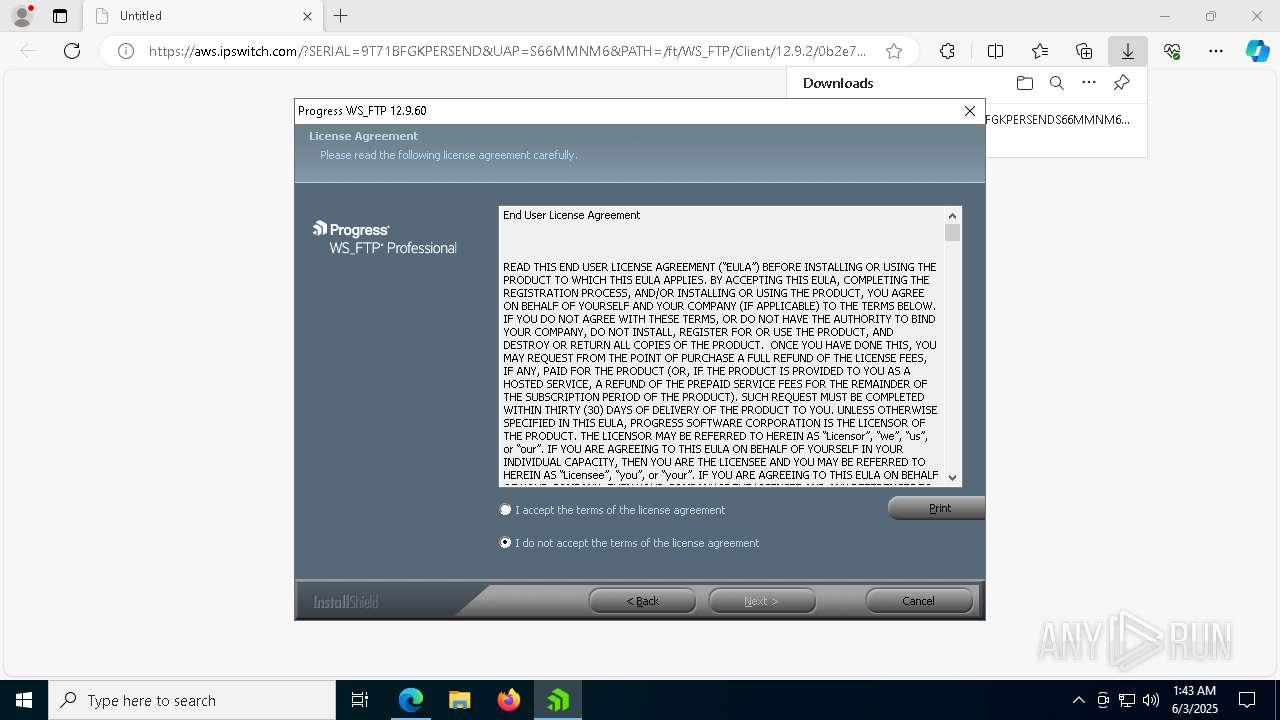
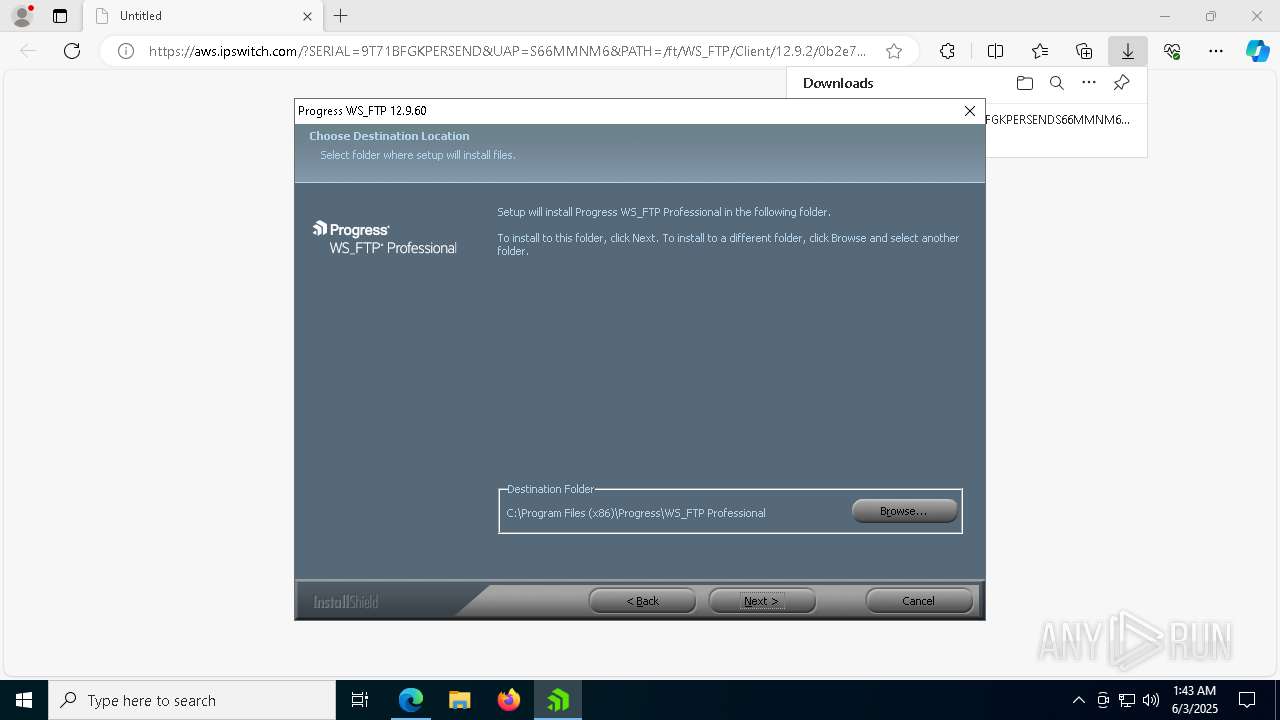
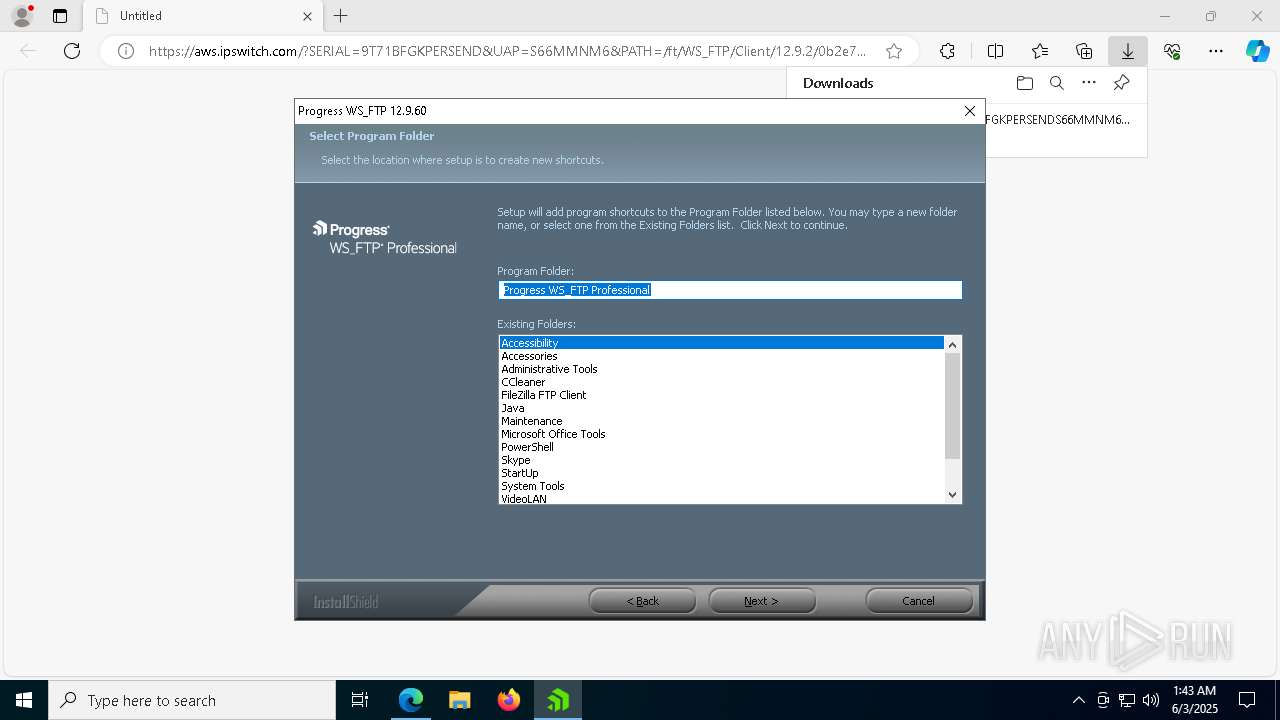
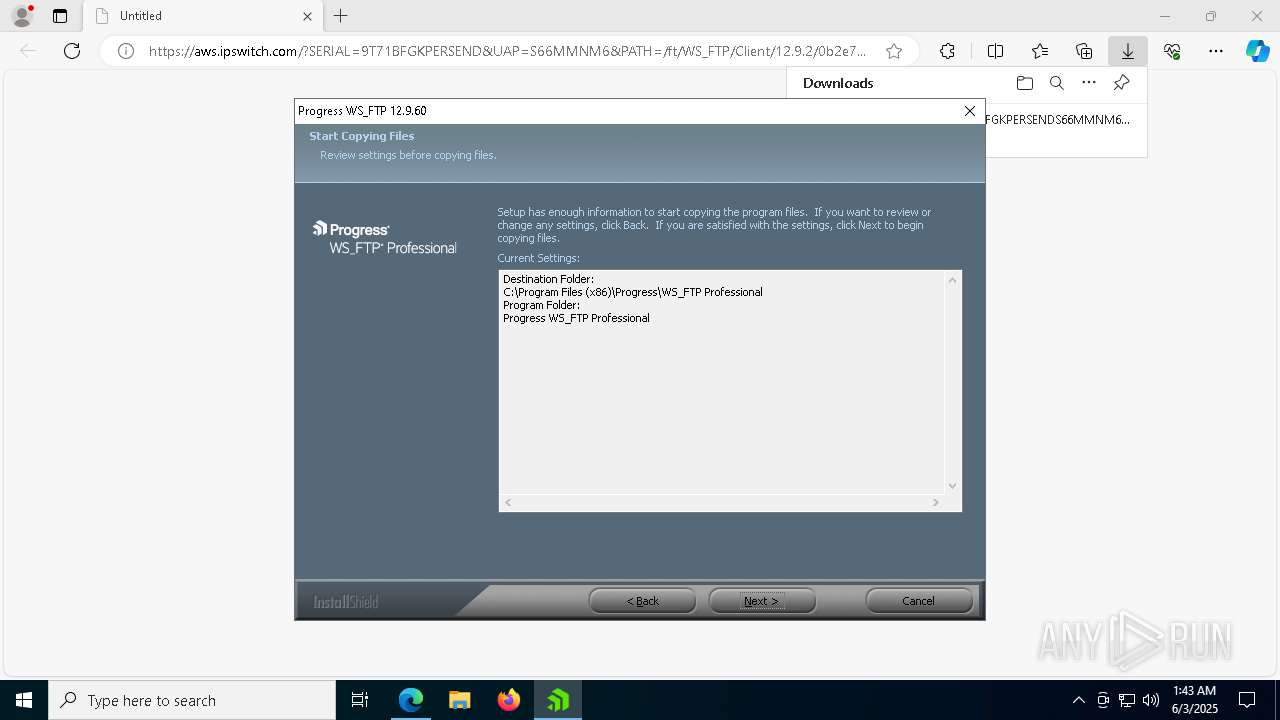
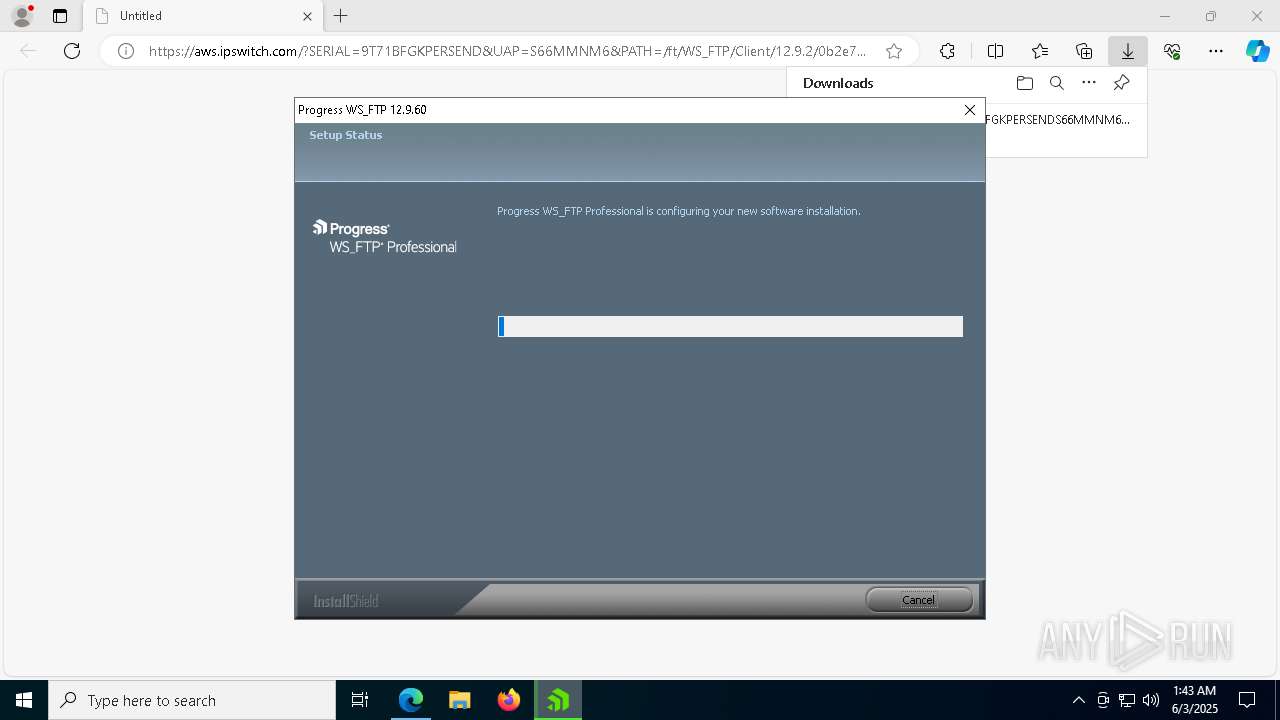
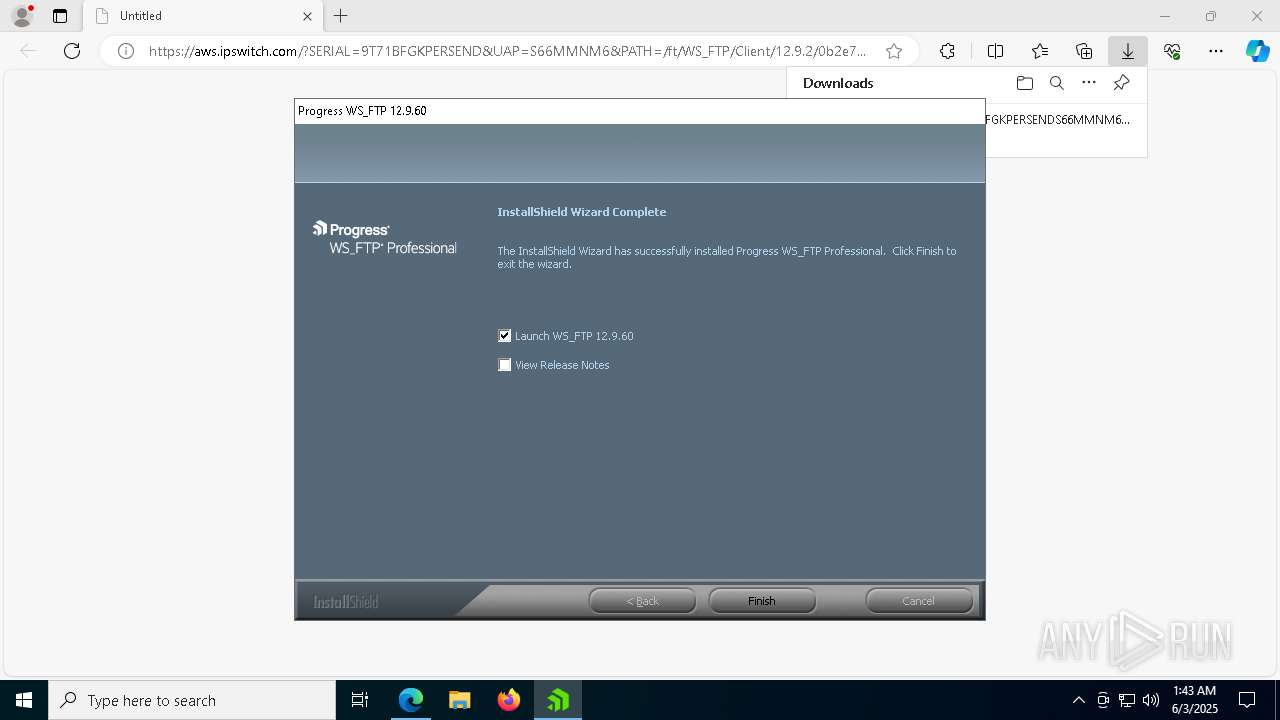
| 924 | C:\Users\admin\AppData\Local\Temp\{0B2985B7-99EE-441D-8987-D944AC574095}\wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe -package:"C:\Users\admin\Downloads\wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe" -no_selfdeleter -IS_temp -media_path:"C:\Users\admin\AppData\Local\Temp\{0B2985B7-99EE-441D-8987-D944AC574095}\Disk1\" -tempdisk1folder:"C:\Users\admin\AppData\Local\Temp\{0B2985B7-99EE-441D-8987-D944AC574095}\" -IS_OriginalLauncher:"C:\Users\admin\AppData\Local\Temp\{0B2985B7-99EE-441D-8987-D944AC574095}\Disk1\wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe" | C:\Users\admin\AppData\Local\Temp\{0B2985B7-99EE-441D-8987-D944AC574095}\wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe | wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe | ||||||||||||
User: admin Company: Progress Integrity Level: HIGH Description: InstallScript Setup Launcher Unicode Version: 12.9.60 Modules
| |||||||||||||||
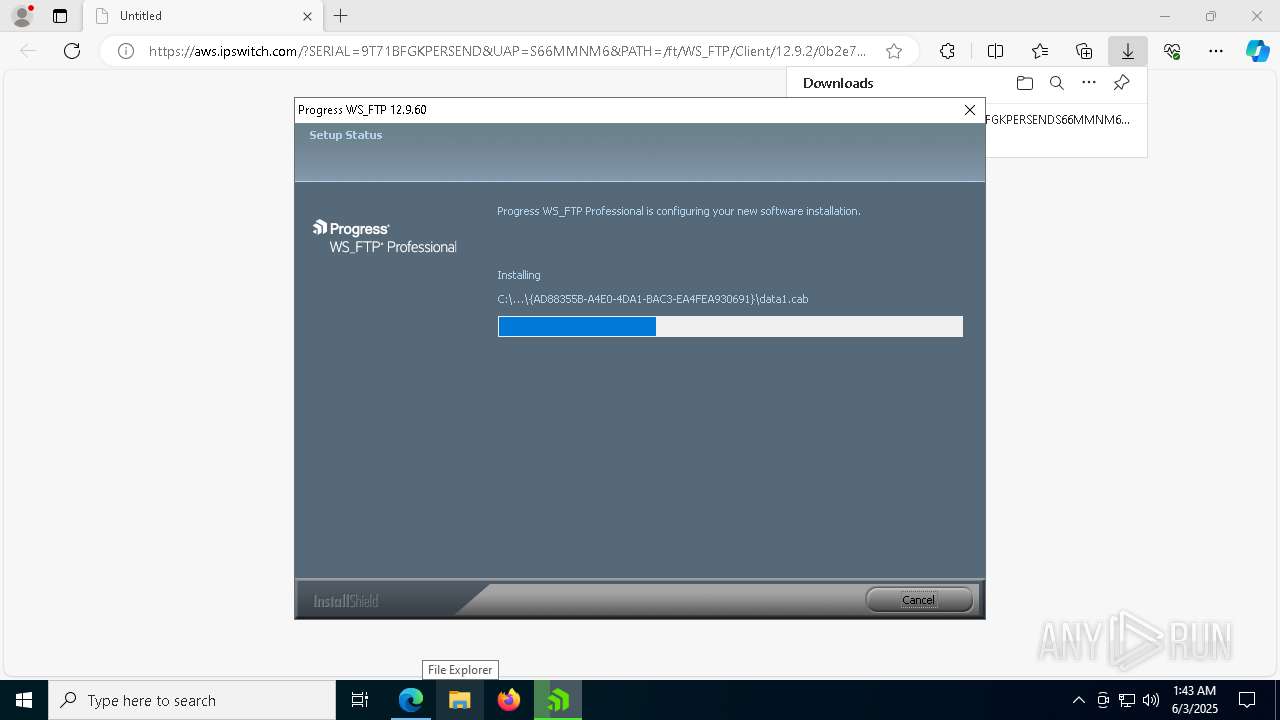
| 1276 | C:\Users\admin\AppData\Local\Temp\{DDD9E43F-2CF2-40F6-8A5A-5AE2738E17B4}\{AD88355B-A4E0-4DA1-BAC3-EA4FEA930691}\vc_redist.x86.exe /Q /norestart | C:\Users\admin\AppData\Local\Temp\{DDD9E43F-2CF2-40F6-8A5A-5AE2738E17B4}\{AD88355B-A4E0-4DA1-BAC3-EA4FEA930691}\vc_redist.x86.exe | wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.40.33810 Exit code: 0 Version: 14.40.33810.0 Modules
| |||||||||||||||
| 1472 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4020 --field-trial-handle=2348,i,8542271280082321903,10522547980962679627,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6908 --field-trial-handle=2348,i,8542271280082321903,10522547980962679627,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1812 | C:\Users\admin\AppData\Local\Temp\{DDD9E43F-2CF2-40F6-8A5A-5AE2738E17B4}\{AD88355B-A4E0-4DA1-BAC3-EA4FEA930691}\vcredist2012_x86.exe /Q /norestart | C:\Users\admin\AppData\Local\Temp\{DDD9E43F-2CF2-40F6-8A5A-5AE2738E17B4}\{AD88355B-A4E0-4DA1-BAC3-EA4FEA930691}\vcredist2012_x86.exe | wsftp_12.9.2_English_SN9T71BFGKPERSENDS66MMNM6.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.50727 Exit code: 0 Version: 11.0.50727.1 Modules
| |||||||||||||||
| 2040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3484 --field-trial-handle=2348,i,8542271280082321903,10522547980962679627,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
| 2124 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6872 --field-trial-handle=2348,i,8542271280082321903,10522547980962679627,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
31 707
Read events
29 561
Write events
1 491
Delete events
655
Modification events
| (PID) Process: | (776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (776) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1994514637952F00 | |||
| (PID) Process: | (776) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1C83594637952F00 | |||
| (PID) Process: | (776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\131970 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3507FD0B-29C9-4945-BE93-F299FA5D3E3E} | |||
| (PID) Process: | (776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\131970 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {608F869C-6EC4-4823-86E1-0F7E1456400E} | |||
| (PID) Process: | (776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
282
Suspicious files
411
Text files
206
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f394.TMP | — | |
MD5:— | SHA256:— | |||
| 776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f3b4.TMP | — | |
MD5:— | SHA256:— | |||
| 776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11f3e2.TMP | — | |
MD5:— | SHA256:— | |||
| 776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF11f3c3.TMP | — | |
MD5:— | SHA256:— | |||
| 776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11f411.TMP | — | |
MD5:— | SHA256:— | |||
| 776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF11f421.TMP | — | |
MD5:— | SHA256:— | |||
| 776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
69
DNS requests
51
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
968 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
968 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1812 | vcredist2012_x86.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1812 | vcredist2012_x86.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2088 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b96d4ca8-86b5-4bcc-9b2f-8200e97368c2?P1=1749216525&P2=404&P3=2&P4=luT1tcr3Wklf7%2bBHooDPrdAr066VpH45F%2fLzuKRxsbrWgchKw8wjjFuPBSpQz90cd7SDKbhGlQVW3RlaUaZNKQ%3d%3d | unknown | — | — | whitelisted |
2088 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b96d4ca8-86b5-4bcc-9b2f-8200e97368c2?P1=1749216525&P2=404&P3=2&P4=luT1tcr3Wklf7%2bBHooDPrdAr066VpH45F%2fLzuKRxsbrWgchKw8wjjFuPBSpQz90cd7SDKbhGlQVW3RlaUaZNKQ%3d%3d | unknown | — | — | whitelisted |
8152 | msiexec.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.31.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
776 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 79.125.112.214:443 | aws.ipswitch.com | AMAZON-02 | IE | unknown |
— | — | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
aws.ipswitch.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|