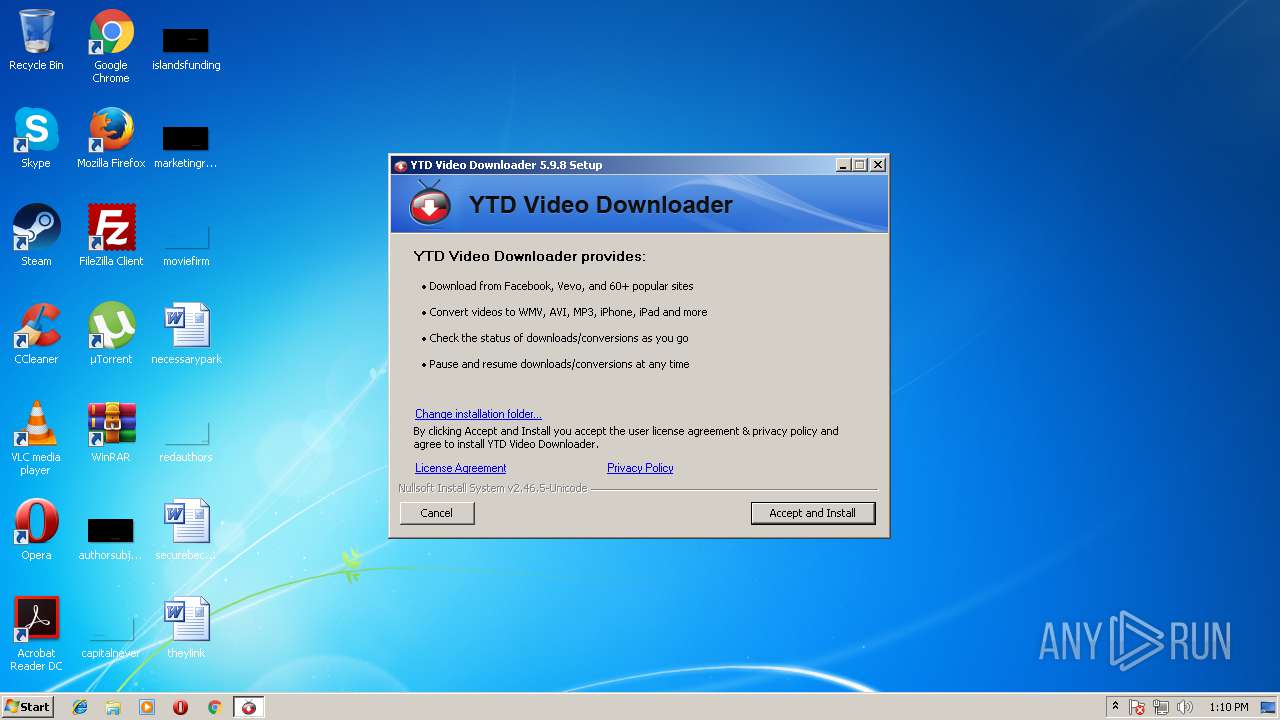
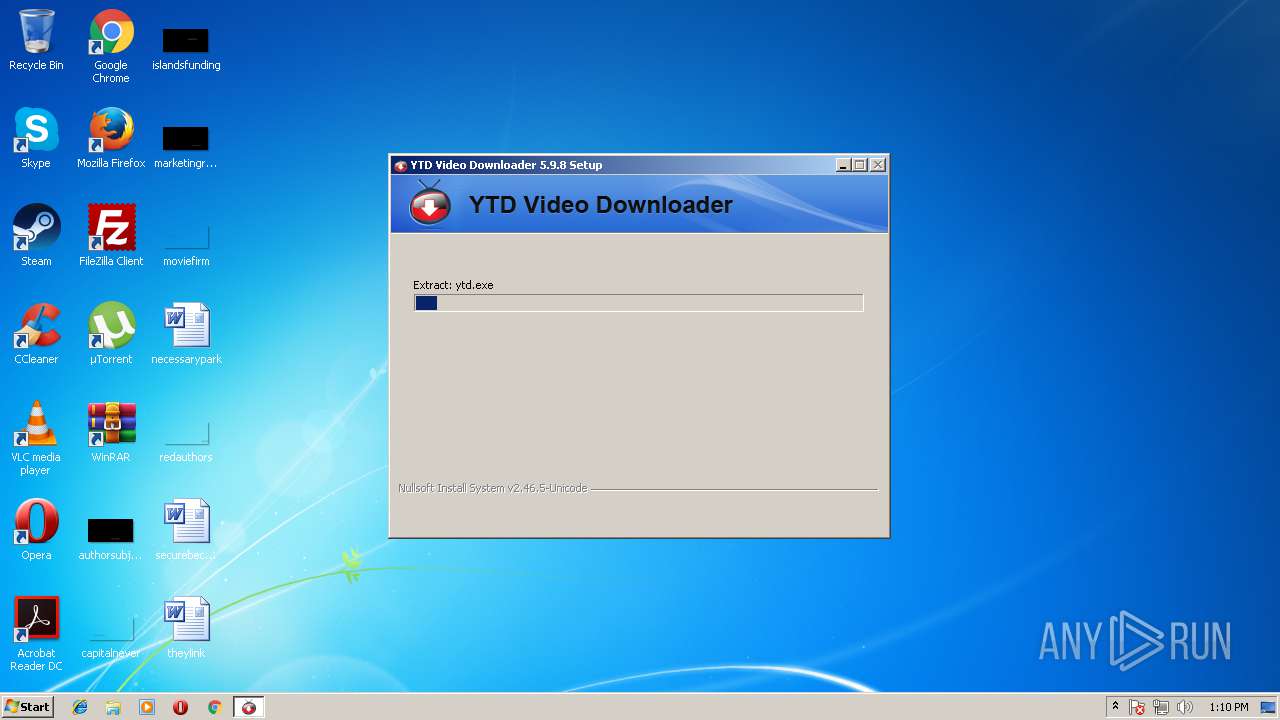
| File name: | YTDSetup.exe |
| Full analysis: | https://app.any.run/tasks/e36e73c4-ebff-4061-8a7b-509ebbb8082c |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2018, 12:10:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B866001FD872C1668A45EFFCB5B9D2AC |
| SHA1: | D8FF094AFF645F98ABCE21279988340B6D1EE8E6 |
| SHA256: | 71EEB7FC8D64FB5D61262071A64AE0C5EE69B75C8FF3A33A27F65756287DDB84 |
| SSDEEP: | 196608:C5sSTEX7Tpc4+jXiC4pPGdROaoW5CdtM+/LW8gcx86R7NbEF6epXNjZKSK003:usHWJjXiC4p+/oW5Cdy+1x8kNbcpXNj+ |
MALICIOUS
Loads dropped or rewritten executable
- YTDSetup.exe (PID: 2592)
- ytd.exe (PID: 3568)
- ytd.exe (PID: 960)
- ytd.exe (PID: 1872)
Application was dropped or rewritten from another process
- ytd.exe (PID: 3568)
- OpenUrl.exe (PID: 2932)
- OpenUrl.exe (PID: 3012)
- ytd.exe (PID: 1872)
- ytd.exe (PID: 960)
SUSPICIOUS
Creates a software uninstall entry
- YTDSetup.exe (PID: 2592)
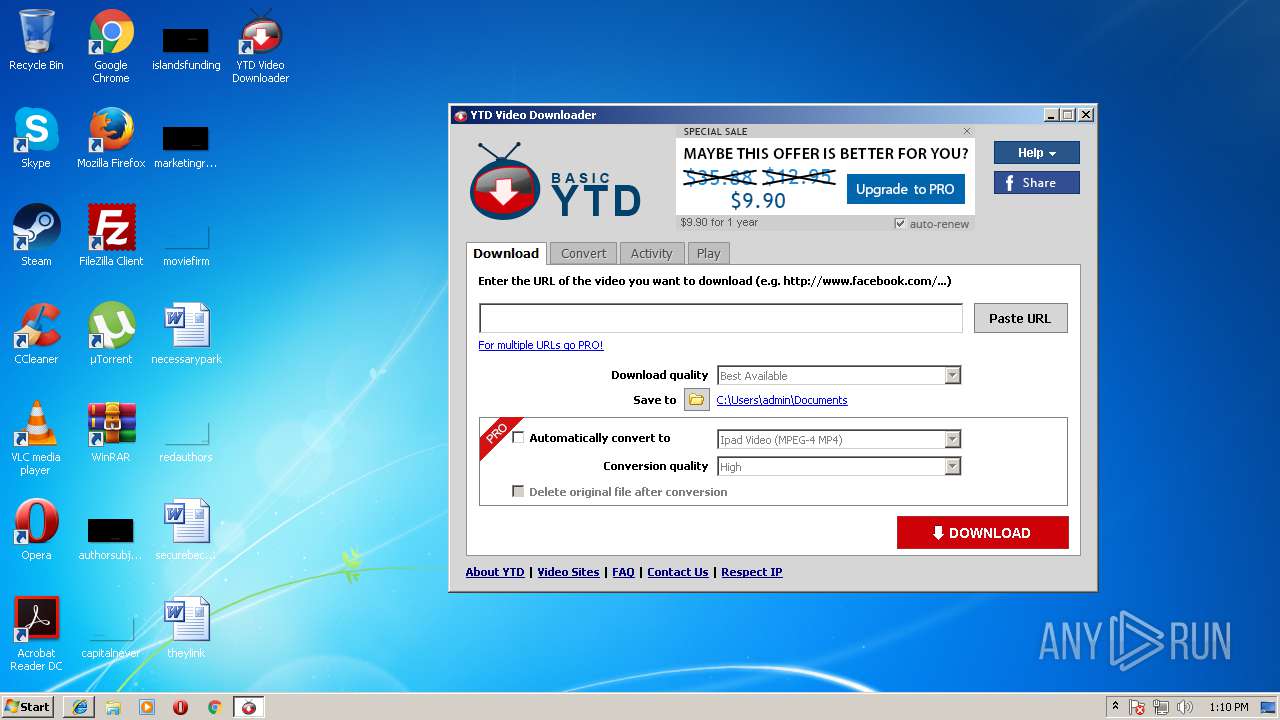
Creates files in the program directory
- ytd.exe (PID: 3568)
- YTDSetup.exe (PID: 2592)
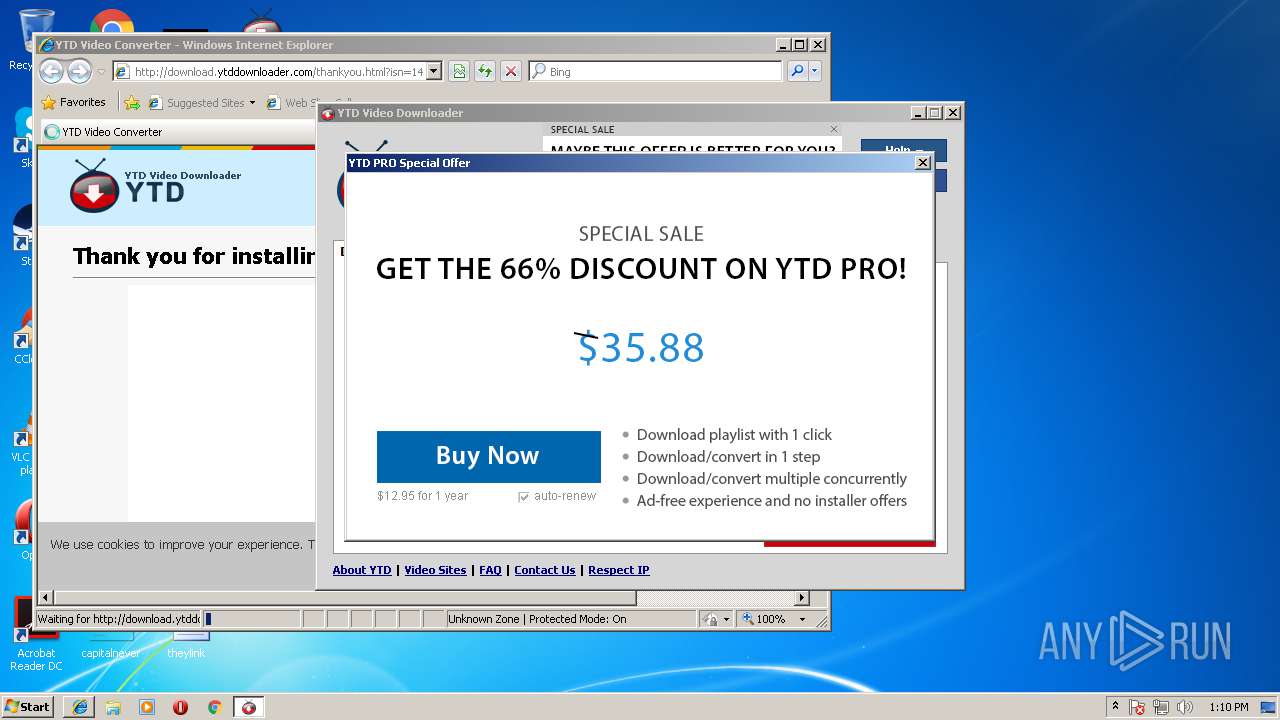
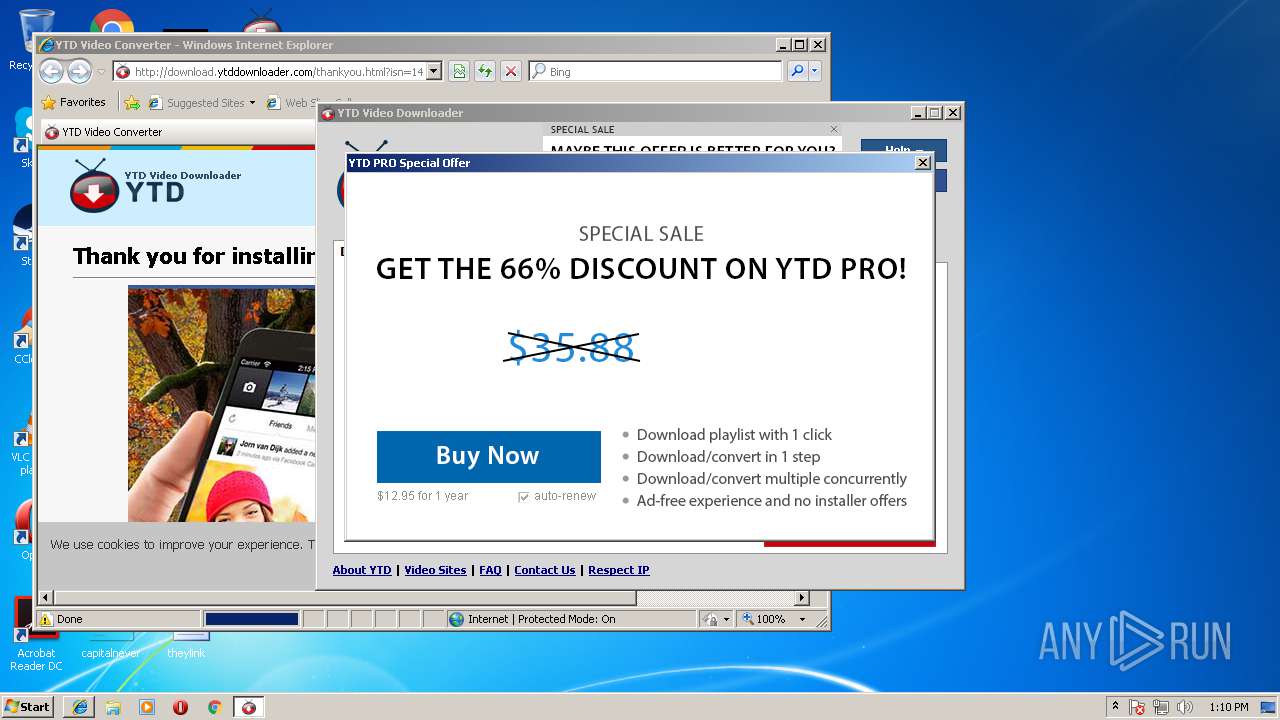
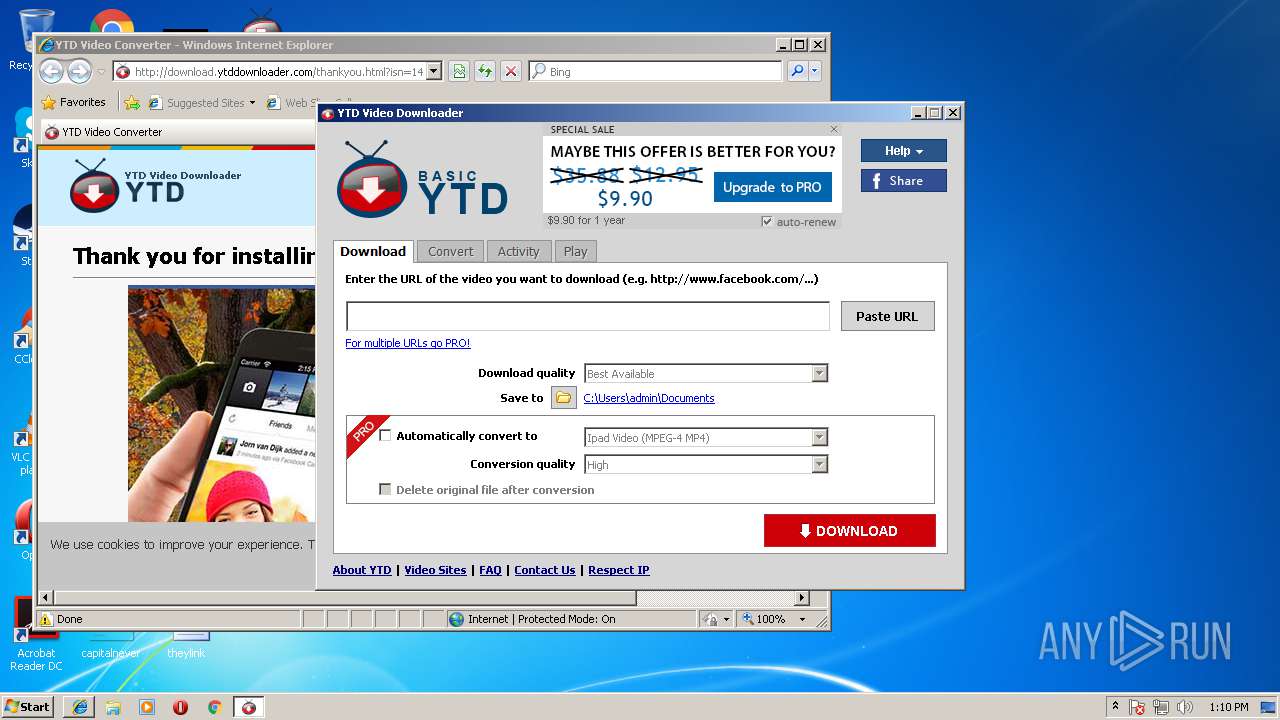
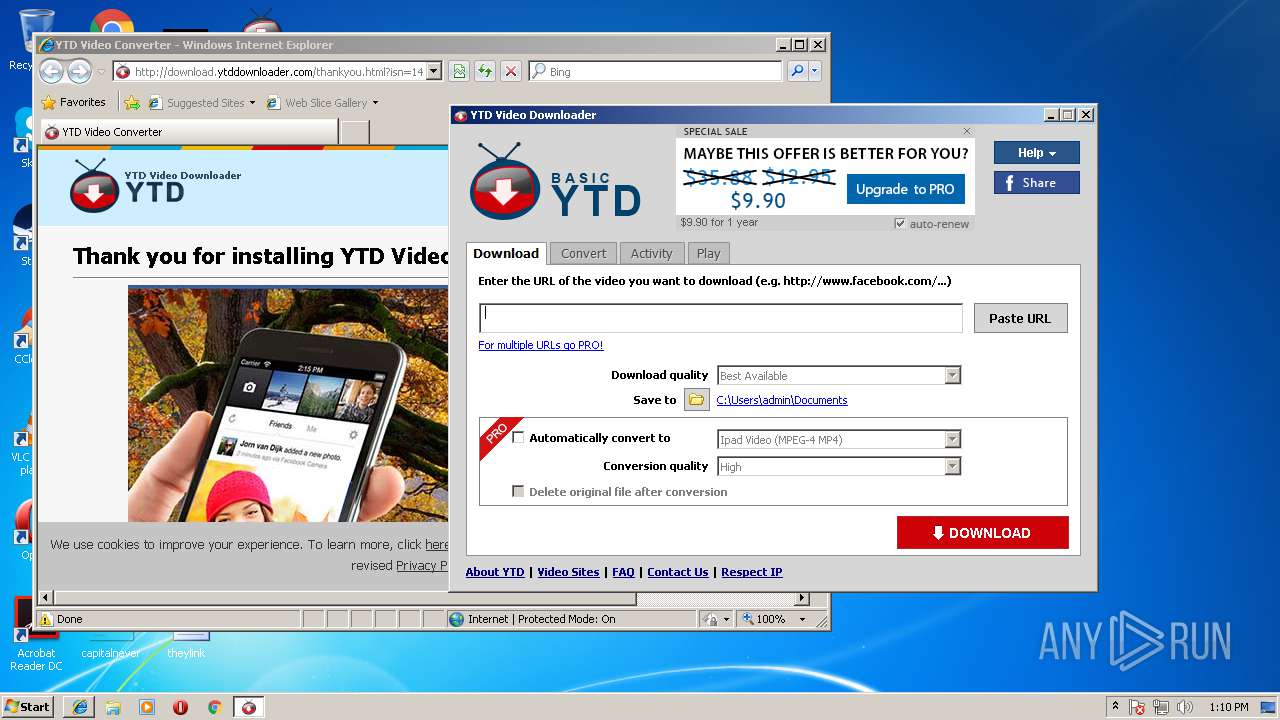
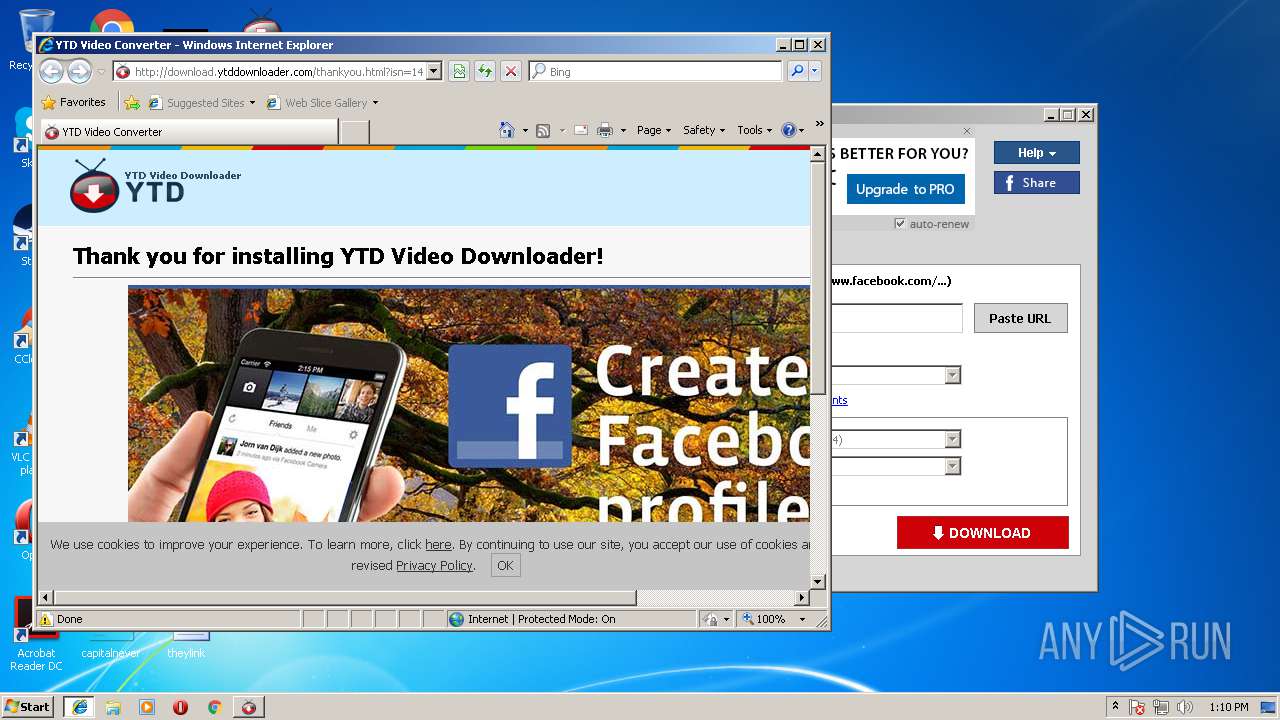
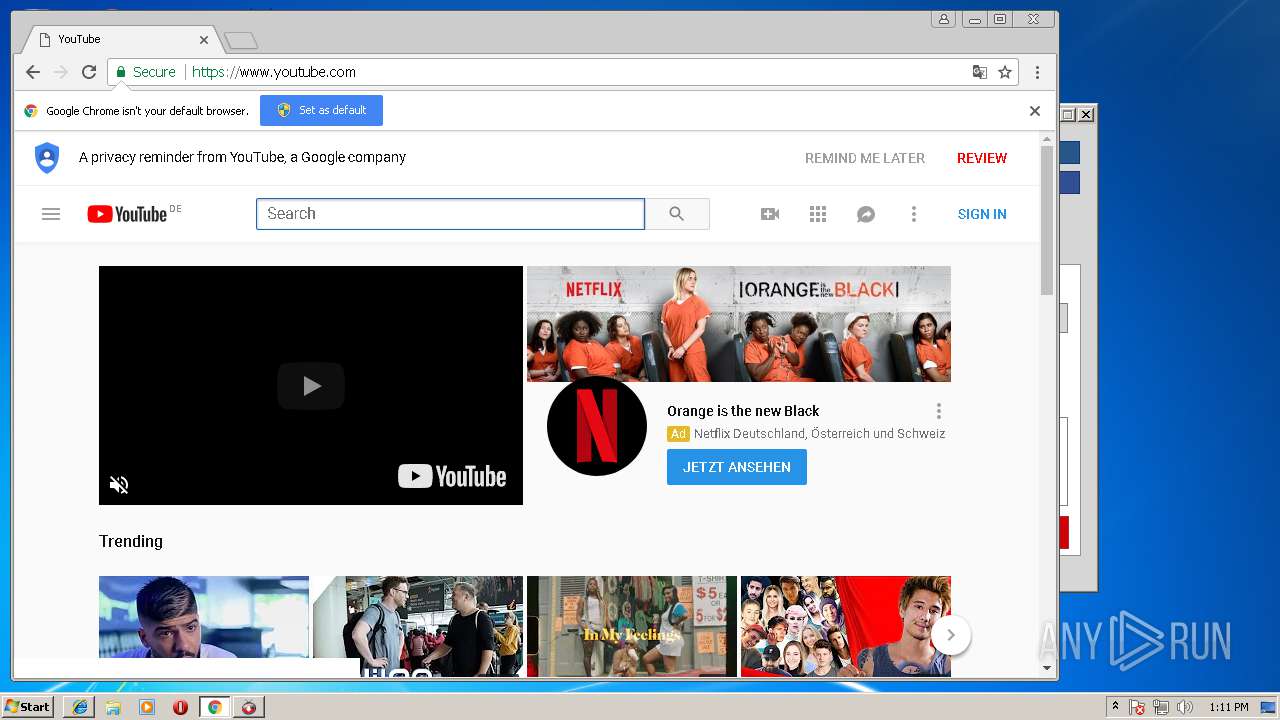
Starts Internet Explorer
- OpenUrl.exe (PID: 2932)
Reads internet explorer settings
- ytd.exe (PID: 3568)
Executable content was dropped or overwritten
- YTDSetup.exe (PID: 2592)
Creates files in the user directory
- ytd.exe (PID: 3568)
Reads Internet Cache Settings
- ytd.exe (PID: 3568)
INFO
Application launched itself
- iexplore.exe (PID: 3324)
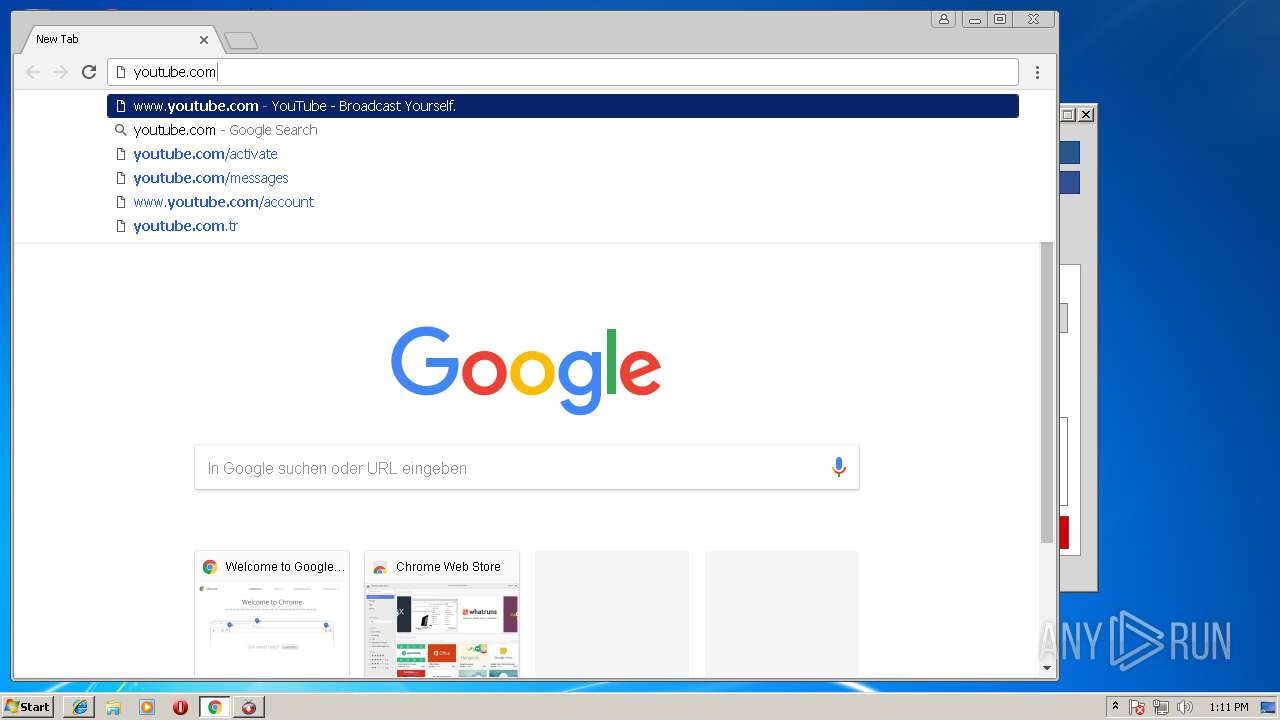
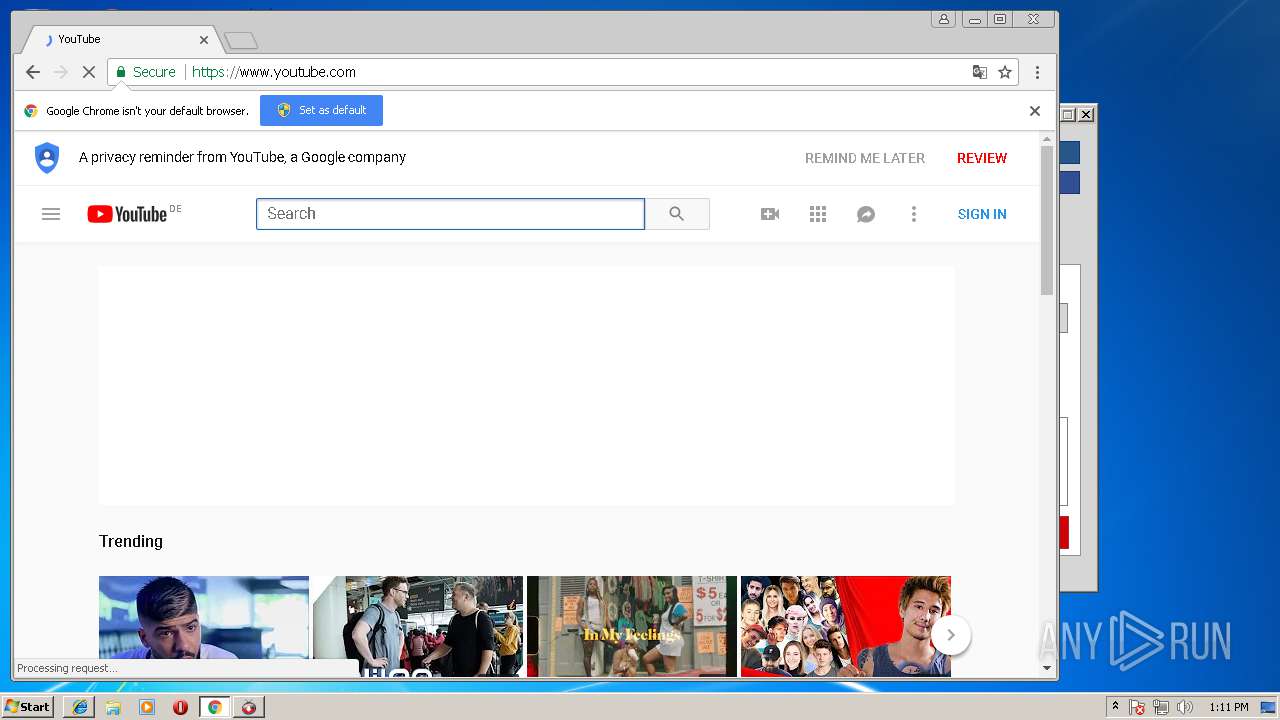
- chrome.exe (PID: 1888)
Changes internet zones settings
- iexplore.exe (PID: 3324)
Reads Internet Cache Settings
- iexplore.exe (PID: 2180)
Dropped object may contain URL's
- iexplore.exe (PID: 2180)
- ytd.exe (PID: 3568)
- YTDSetup.exe (PID: 2592)
- iexplore.exe (PID: 3324)
- chrome.exe (PID: 1888)
Reads internet explorer settings
- iexplore.exe (PID: 2180)
Creates files in the user directory
- iexplore.exe (PID: 2180)
- FlashUtil32_27_0_0_187_ActiveX.exe (PID: 3840)
Reads settings of System Certificates
- chrome.exe (PID: 1888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:19:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28672 |
| InitializedDataSize: | 445952 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x39e3 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.9.8.0 |
| ProductVersionNumber: | 5.9.8.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
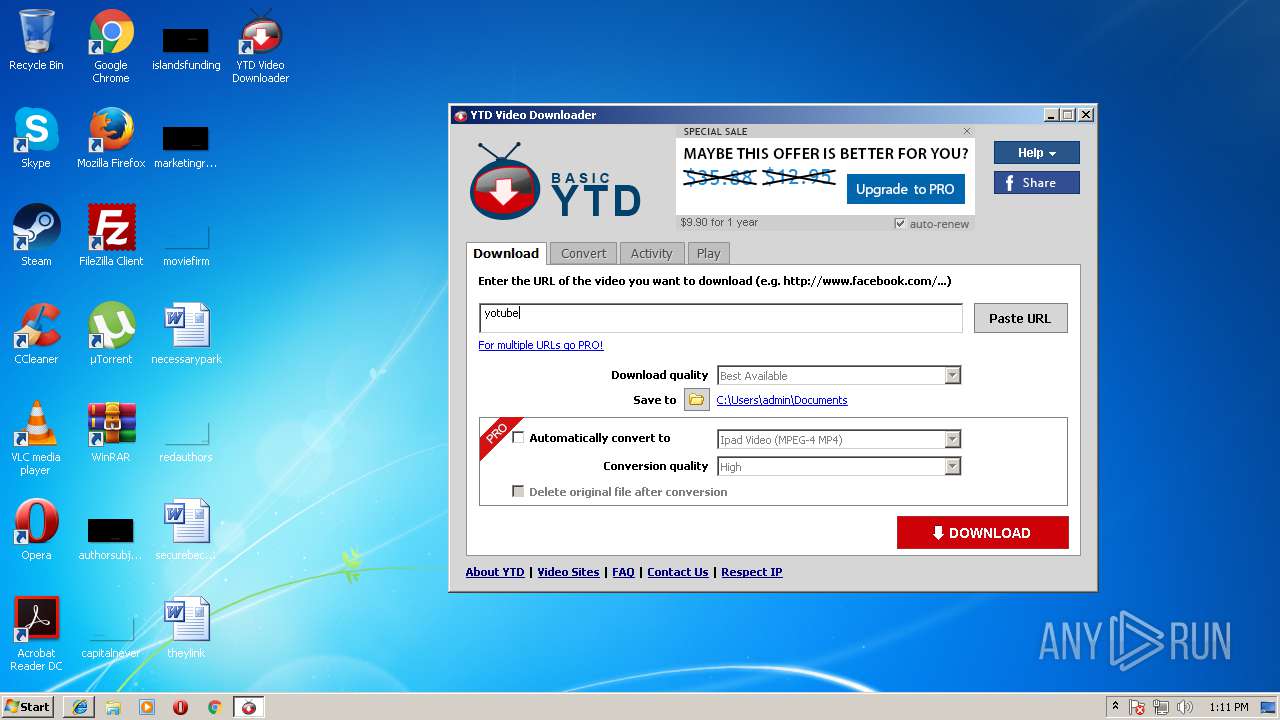
| FileDescription: | YTD Video Downloader |
| FileVersion: | 5.9.8 |
| LegalCopyright: | Copyright © 2007-2018 GreenTree Applications SRL |
| OriginalFileName: | Uninstall.exe |
| ProductName: | YTD Video Downloader |
| ProductVersion: | 5.9.8.0.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:19:59 |
| Detected languages: |
|
| FileDescription: | YTD Video Downloader |
| FileVersion: | 5.9.8 |
| LegalCopyright: | Copyright © 2007-2018 GreenTree Applications SRL |
| OriginalFilename: | Uninstall.exe |
| ProductName: | YTD Video Downloader |
| ProductVersion: | 5.9.8.0.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:19:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006F10 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49788 |
.rdata | 0x00008000 | 0x00002A92 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39389 |
.data | 0x0000B000 | 0x00067EBC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.47278 |
.ndata | 0x00073000 | 0x001B9000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0022C000 | 0x0000C690 | 0x0000C800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.7772 |
.reloc | 0x00239000 | 0x00000F8A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.91193 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21712 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.48451 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 4.63086 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.39833 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 6.01171 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 6.35747 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 5.04145 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.71858 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.67385 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
55
Monitored processes
18
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\Program Files\GreenTree Applications\YTD Video Downloader\ytd.exe" | C:\Program Files\GreenTree Applications\YTD Video Downloader\ytd.exe | — | explorer.exe | |||||||||||
User: admin Company: GreenTree Applications SRL Integrity Level: MEDIUM Description: YTD Video Downloader Exit code: 0 Version: 5, 9, 8, 2 Modules
| |||||||||||||||
| 1872 | "C:\Program Files\GreenTree Applications\YTD Video Downloader\ytd.exe" | C:\Program Files\GreenTree Applications\YTD Video Downloader\ytd.exe | — | explorer.exe | |||||||||||
User: admin Company: GreenTree Applications SRL Integrity Level: MEDIUM Description: YTD Video Downloader Exit code: 0 Version: 5, 9, 8, 2 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3324 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1768,17374287351950559694,2633501881543047873,131072 --service-pipe-token=80B5F2CBB2393FC6D9C38F335A204FBE --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=80B5F2CBB2393FC6D9C38F335A204FBE --renderer-client-id=2 --mojo-platform-channel-handle=1976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2592 | "C:\Users\admin\AppData\Local\Temp\YTDSetup.exe" | C:\Users\admin\AppData\Local\Temp\YTDSetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: YTD Video Downloader Exit code: 0 Version: 5.9.8 Modules
| |||||||||||||||
| 2700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2324 --on-initialized-event-handle=296 --parent-handle=300 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1768,17374287351950559694,2633501881543047873,131072 --service-pipe-token=D575FBC59BE88455156D17523996015D --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=D575FBC59BE88455156D17523996015D --renderer-client-id=6 --mojo-platform-channel-handle=3812 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1768,17374287351950559694,2633501881543047873,131072 --disable-direct-composition --use-gl=swiftshader-webgl --supports-dual-gpus=false --gpu-driver-bug-workarounds=9,12,13,22,23,24,27,49,84 --disable-gl-extensions="GL_KHR_blend_equation_advanced GL_KHR_blend_equation_advanced_coherent" --disable-accelerated-video-decode --gpu-vendor-id=0x1234 --gpu-device-id=0x1111 --gpu-driver-vendor="Google Inc." --gpu-driver-version=3.3.0.2 --gpu-driver-date=2017/04/07 --service-request-channel-token=52273FBFE13C6D1FEAC8AAFD4D8203DA --mojo-platform-channel-handle=4140 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1768,17374287351950559694,2633501881543047873,131072 --service-pipe-token=EA6DDA8DEFD2726863DCAEA5FA86DA9D --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=EA6DDA8DEFD2726863DCAEA5FA86DA9D --renderer-client-id=4 --mojo-platform-channel-handle=1776 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
Total events
1 111
Read events
942
Write events
165
Delete events
4
Modification events
| (PID) Process: | (2592) YTDSetup.exe | Key: | HKEY_CURRENT_USER\Software\GreenTree Applications\YTD |
| Operation: | write | Name: | ISN |
Value: 14FFDD765AA74FDCACAA22A02E150F0E | |||
| (PID) Process: | (2592) YTDSetup.exe | Key: | HKEY_CURRENT_USER\Software\GreenTree Applications\YTD |
| Operation: | write | Name: | |
Value: C:\Program Files\GreenTree Applications\YTD Video Downloader | |||
| (PID) Process: | (2592) YTDSetup.exe | Key: | HKEY_CURRENT_USER\Software\GreenTree Applications\YTD |
| Operation: | write | Name: | Language |
Value: 1033 | |||
| (PID) Process: | (2592) YTDSetup.exe | Key: | HKEY_CURRENT_USER\Software\GreenTree Applications\YTD |
| Operation: | write | Name: | kitType |
Value: ytd | |||
| (PID) Process: | (2592) YTDSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1a413f37-ed88-4fec-9666-5c48dc4b7bb7} |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\GreenTree Applications\YTD Video Downloader\ytd.exe,0 | |||
| (PID) Process: | (2592) YTDSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1a413f37-ed88-4fec-9666-5c48dc4b7bb7} |
| Operation: | write | Name: | DisplayName |
Value: YTD Video Downloader 5.9.8 | |||
| (PID) Process: | (2592) YTDSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1a413f37-ed88-4fec-9666-5c48dc4b7bb7} |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\GreenTree Applications\YTD Video Downloader\uninstall.exe" | |||
| (PID) Process: | (2592) YTDSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1a413f37-ed88-4fec-9666-5c48dc4b7bb7} |
| Operation: | write | Name: | Publisher |
Value: GreenTree Applications SRL | |||
| (PID) Process: | (2592) YTDSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1a413f37-ed88-4fec-9666-5c48dc4b7bb7} |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.ytddownloader.com | |||
| (PID) Process: | (2592) YTDSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1a413f37-ed88-4fec-9666-5c48dc4b7bb7} |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
Executable files
25
Suspicious files
50
Text files
107
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2592 | YTDSetup.exe | C:\Users\admin\AppData\Local\Temp\nss5CEC.tmp\inst_start | — | |
MD5:— | SHA256:— | |||
| 2592 | YTDSetup.exe | C:\Users\admin\AppData\Local\Temp\nss5CEC.tmp\NSISHelper.dll | executable | |
MD5:EBC2D9669925943059BC08F5C78951F2 | SHA256:AA8236FFE0CBA7A7000AE8E574FE8D8946E5356975FFCD2B88E3CDF4A7D529F7 | |||
| 2592 | YTDSetup.exe | C:\Users\admin\AppData\Local\Temp\nss5CEC.tmp\nsDialogs.dll | executable | |
MD5:4CCC4A742D4423F2F0ED744FD9C81F63 | SHA256:416133DD86C0DFF6B0FCAF1F46DFE97FDC85B37F90EFFB2D369164A8F7E13AE6 | |||
| 2592 | YTDSetup.exe | C:\Users\admin\AppData\Local\Temp\nss5CEC.tmp\System.dll | executable | |
MD5:BF712F32249029466FA86756F5546950 | SHA256:7851CB12FA4131F1FEE5DE390D650EF65CAC561279F1CFE70AD16CC9780210AF | |||
| 2592 | YTDSetup.exe | C:\Program Files\GreenTree Applications\YTD Video Downloader\COPYING.Apachev2 | text | |
MD5:D273D63619C9AEAF15CDAF76422C4F87 | SHA256:3DDF9BE5C28FE27DAD143A5DC76EEA25222AD1DD68934A047064E56ED2FA40C5 | |||
| 2592 | YTDSetup.exe | C:\Users\admin\AppData\Local\Temp\nss5CEC.tmp\UserInfo.dll | executable | |
MD5:C7CE0E47C83525983FD2C4C9566B4AAD | SHA256:6293408A5FA6D0F55F0A4D01528EB5B807EE9447A75A28B5986267475EBCD3AE | |||
| 2592 | YTDSetup.exe | C:\Users\admin\AppData\Local\Temp\nss5CEC.tmp\modern-header.bmp | image | |
MD5:3FD933AE9F031241E079AF6BAC356206 | SHA256:3EDA2CF101377503BAE145E54351636DD117A89D9D680A3D49ED7F6026485590 | |||
| 2592 | YTDSetup.exe | C:\Users\admin\AppData\Local\Temp\nss5CEC.tmp\getCountry | text | |
MD5:796834E7A2839412D79DBC5F1327594D | SHA256:4334FFCF78137D9C9D5866146D7F29A62735F232FC7239BD43332145E376BDA3 | |||
| 2592 | YTDSetup.exe | C:\Program Files\GreenTree Applications\YTD Video Downloader\manual.bat | text | |
MD5:AAE0878136D8C1559FAC69F5C5B895E2 | SHA256:FD8839722BA7FFD3FBE48149FD909DB3E66E9A5213FA88E511286214BE109B9D | |||
| 2592 | YTDSetup.exe | C:\Users\admin\AppData\Local\Temp\nss5CEC.tmp\NSISdl.dll | executable | |
MD5:7CAAF58A526DA33C24CBE122E7839693 | SHA256:19DEBDC4C0B6F5DC9582BDA7A2C1146516F683E8D741190E6D4B81AD10B33F61 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
65
DNS requests
33
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2592 | YTDSetup.exe | GET | — | 5.79.67.108:80 | http://www.youtubedownloadersite.com/images/pixel.gif?action=install&point=finish&oldver=&version=5.9.8&lngid=1033&cid=e9558a4c85844e2aef7e395465b3cdb6&isn=14FFDD765AA74FDCACAA22A02E150F0E&kt=ytd&br=1&ai=0<=0 | NL | — | — | malicious |
2592 | YTDSetup.exe | GET | — | 5.79.67.108:80 | http://www.youtubedownloadersite.com/images/pixel.gif?action=install&point=start&version=5.9.8&lngid=1033&cid=e9558a4c85844e2aef7e395465b3cdb6&isn=14FFDD765AA74FDCACAA22A02E150F0E&kt=ytd<=0 | NL | — | — | malicious |
2180 | iexplore.exe | GET | — | 5.79.67.111:80 | http://download.ytddownloader.com/styles.css | NL | — | — | malicious |
3568 | ytd.exe | POST | 200 | 5.79.67.111:80 | http://www.youtubedownloadersite.com/api/rcsvc.php?kt=ytd | NL | binary | 1.01 Kb | malicious |
3568 | ytd.exe | GET | 200 | 5.79.67.111:80 | http://www.youtubedownloadersite.com/ads/default-w/x.gif | NL | image | 1.08 Kb | malicious |
3568 | ytd.exe | GET | 200 | 5.79.67.111:80 | http://www.youtubedownloadersite.com/ads/default-w/win.php?inst=2018-08-05&kt=ytd&isn=14FFDD765AA74FDCACAA22A02E150F0E<=4&ver=5.9.8 | NL | html | 1.37 Kb | malicious |
3568 | ytd.exe | GET | 200 | 5.79.67.111:80 | http://www.youtubedownloadersite.com/ads/default-w/defw-win-bg.gif | NL | image | 9.52 Kb | malicious |
3568 | ytd.exe | GET | 200 | 5.79.67.111:80 | http://www.youtubedownloadersite.com/ads/default-w/renew.png | NL | image | 1.26 Kb | malicious |
3568 | ytd.exe | GET | 200 | 5.79.67.111:80 | http://www.youtubedownloadersite.com/ads/default-w/defw-win-btn-new.png | NL | image | 2.11 Kb | malicious |
3568 | ytd.exe | POST | 200 | 5.79.67.111:80 | http://www.youtubedownloadersite.com/api/rcsvc.php?kt=ytd | NL | binary | 1.12 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2592 | YTDSetup.exe | 5.79.67.108:80 | www.youtubedownloadersite.com | LeaseWeb Netherlands B.V. | NL | malicious |
3568 | ytd.exe | 5.79.67.111:80 | www.youtubedownloadersite.com | LeaseWeb Netherlands B.V. | NL | suspicious |
3568 | ytd.exe | 216.58.215.238:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3324 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2180 | iexplore.exe | 5.79.67.111:80 | www.youtubedownloadersite.com | LeaseWeb Netherlands B.V. | NL | suspicious |
3568 | ytd.exe | 172.217.168.42:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2180 | iexplore.exe | 172.217.168.42:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2180 | iexplore.exe | 212.124.124.178:80 | www.exactbridge.com | True Records Inc. | US | suspicious |
2180 | iexplore.exe | 216.58.215.238:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2180 | iexplore.exe | 104.111.228.202:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtubedownloadersite.com |
| malicious |
www.google-analytics.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.ytddownloader.com |
| suspicious |
download.ytddownloader.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
www.exactbridge.com |
| suspicious |
connect.facebook.net |
| whitelisted |
s7.addthis.com |
| whitelisted |
irncdn.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2180 | iexplore.exe | Web Application Attack | SC Microsoft Edge Uint8Array - Remote Code Execution |
2180 | iexplore.exe | Web Application Attack | SC Microsoft Edge Uint8Array - Remote Code Execution |