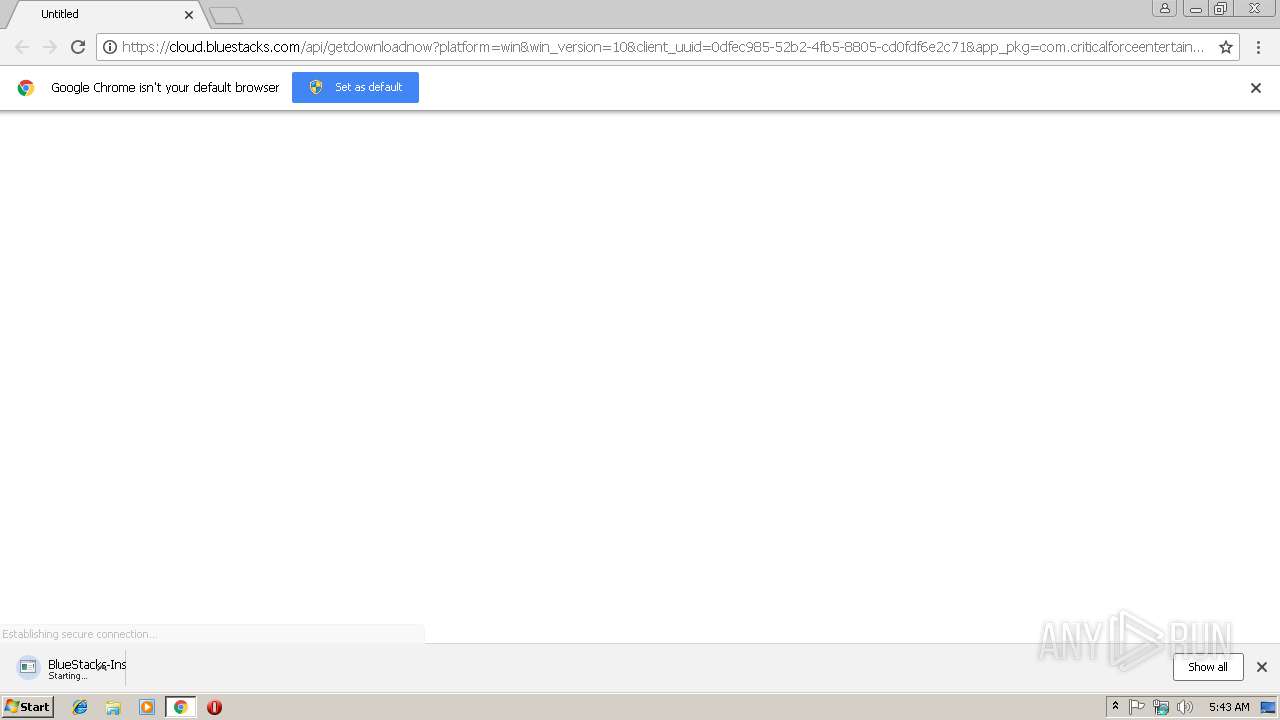
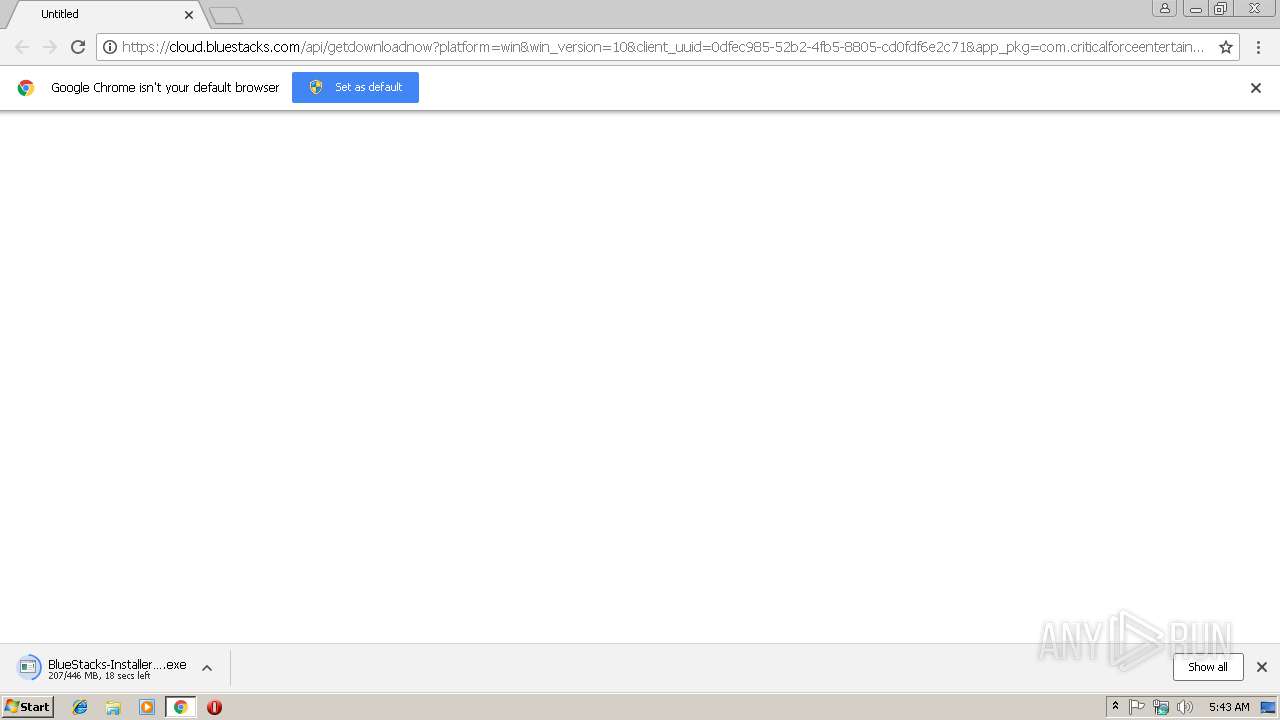
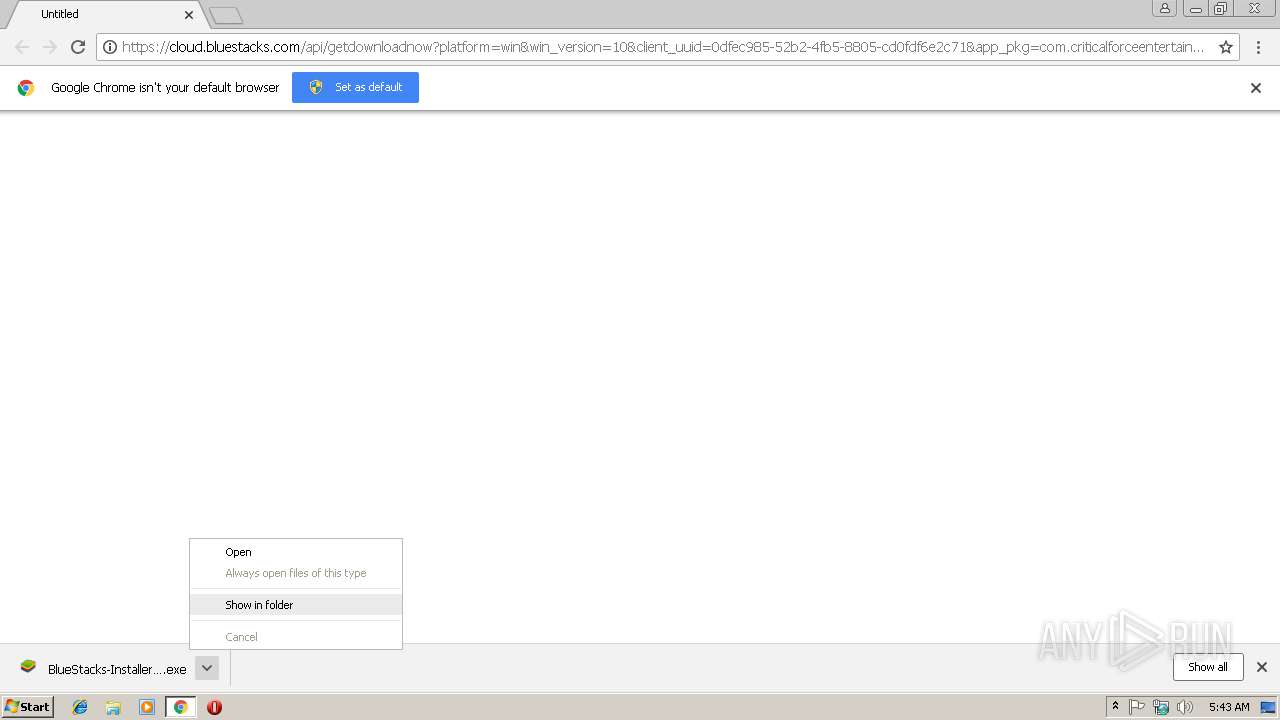
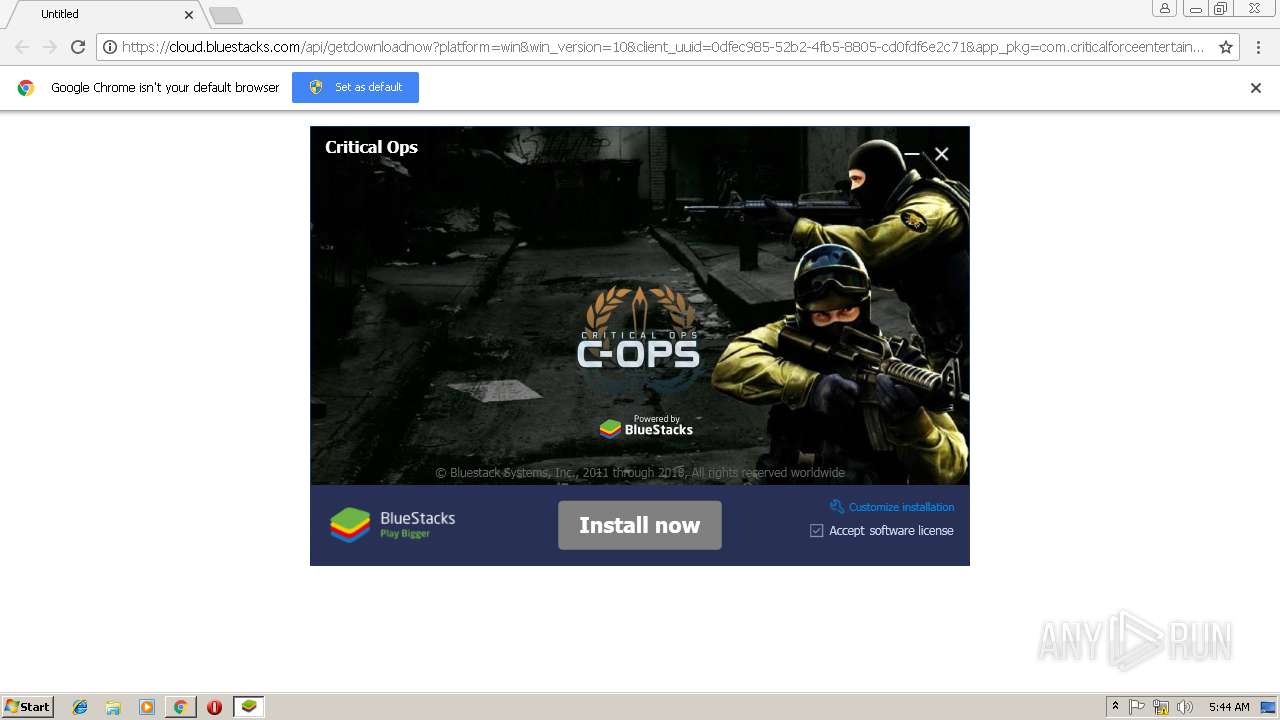
| URL: | https://cloud.bluestacks.com/api/getdownloadnow?platform=win&win_version=10&client_uuid=0dfec985-52b2-4fb5-8805-cd0fdf6e2c71&app_pkg=com.criticalforceentertainment.criticalops&utm_source=&utm_medium=&utm_campaign=homepage-dl-button-en&exit_utm_campaign=ap-critical-ops-us&referrer=&first_landing_page=https%253A%252F%252Fwww.bluestacks.com%252F&download_page_referrer=&gaCookie=&gclid=&clickid=&msclkid=&affiliateId=&offerId=&transaction_id=&aff_sub=&platform_cloud=%257B%2522description%2522%253A%2522Chrome%252072.0.3626.121%2520on%2520Windows%252010%252064-bit%2522%252C%2522layout%2522%253A%2522Blink%2522%252C%2522manufacturer%2522%253Anull%252C%2522name%2522%253A%2522Chrome%2522%252C%2522prerelease%2522%253Anull%252C%2522product%2522%253Anull%252C%2522ua%2522%253A%2522Mozilla%252F5.0%2520(Windows%2520NT%252010.0%253B%2520Win64%253B%2520x64)%2520AppleWebKit%252F537.36%2520(KHTML%252C%2520like%2520Gecko)%2520Chrome%252F72.0.3626.121%2520Safari%252F537.36%2522%252C%2522version%2522%253A%252272.0.3626.121%2522%252C%2522os%2522%253A%257B%2522architecture%2522%253A64%252C%2522family%2522%253A%2522Windows%2522%252C%2522version%2522%253A%252210%2522%257D%257D&preferred_lang=en |
| Full analysis: | https://app.any.run/tasks/7c22949c-bdef-4675-97b0-2227997fa3a7 |
| Verdict: | Malicious activity |
| Analysis date: | March 05, 2019, 05:42:57 |
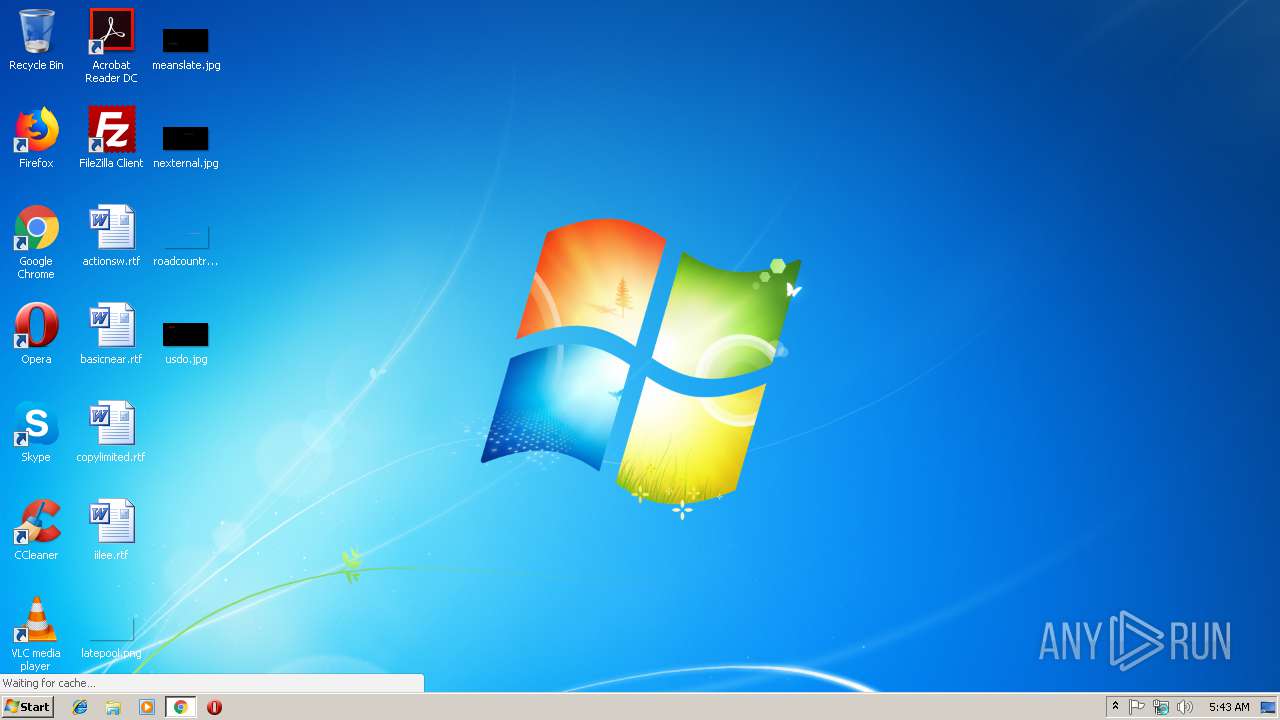
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FFEFAA946CDDB05A68380B4F78F3A35E |
| SHA1: | B8D9ECACE8532CEAABBB6736CD91B160194608AD |
| SHA256: | 71E70D1F9C2AC9DB4C7CDD0619933F13A99885FF0B0D7D83B957640DF0DCBE8A |
| SSDEEP: | 24:2UjzgnuP+fEumViItk6+Yk7x07PPhCw2Ys:EplUiI+6+V7uBk |
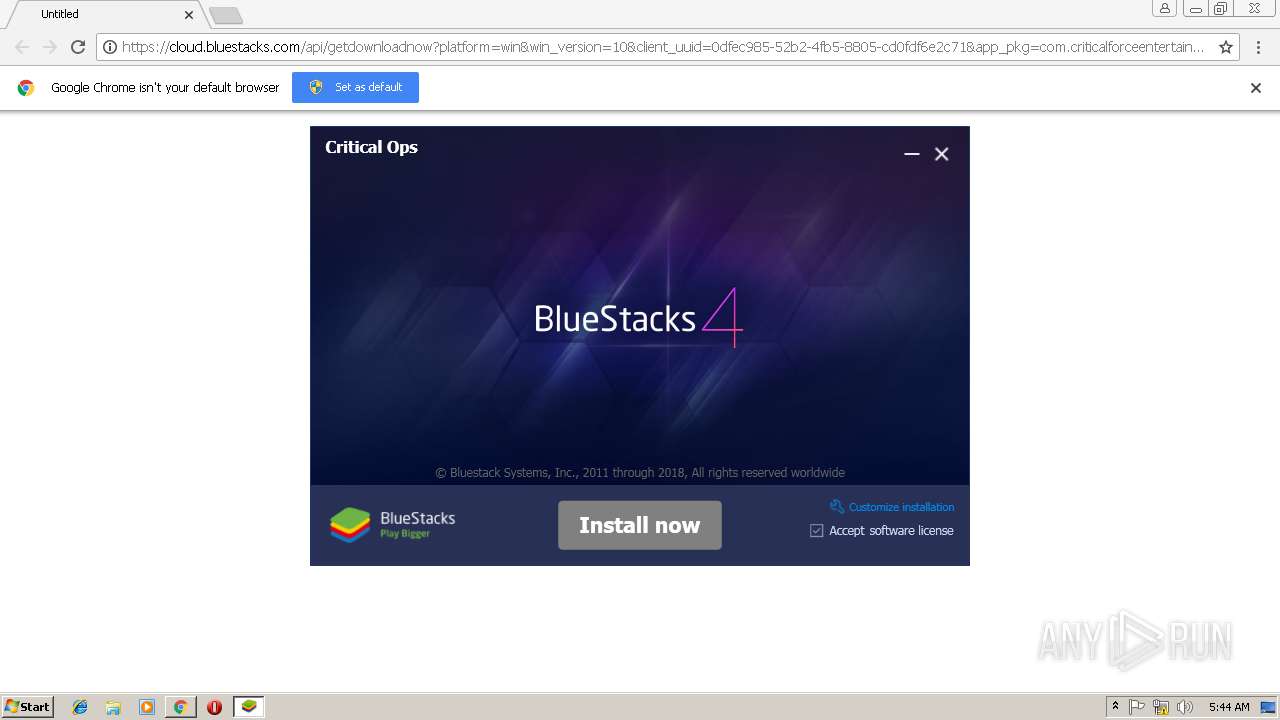
MALICIOUS
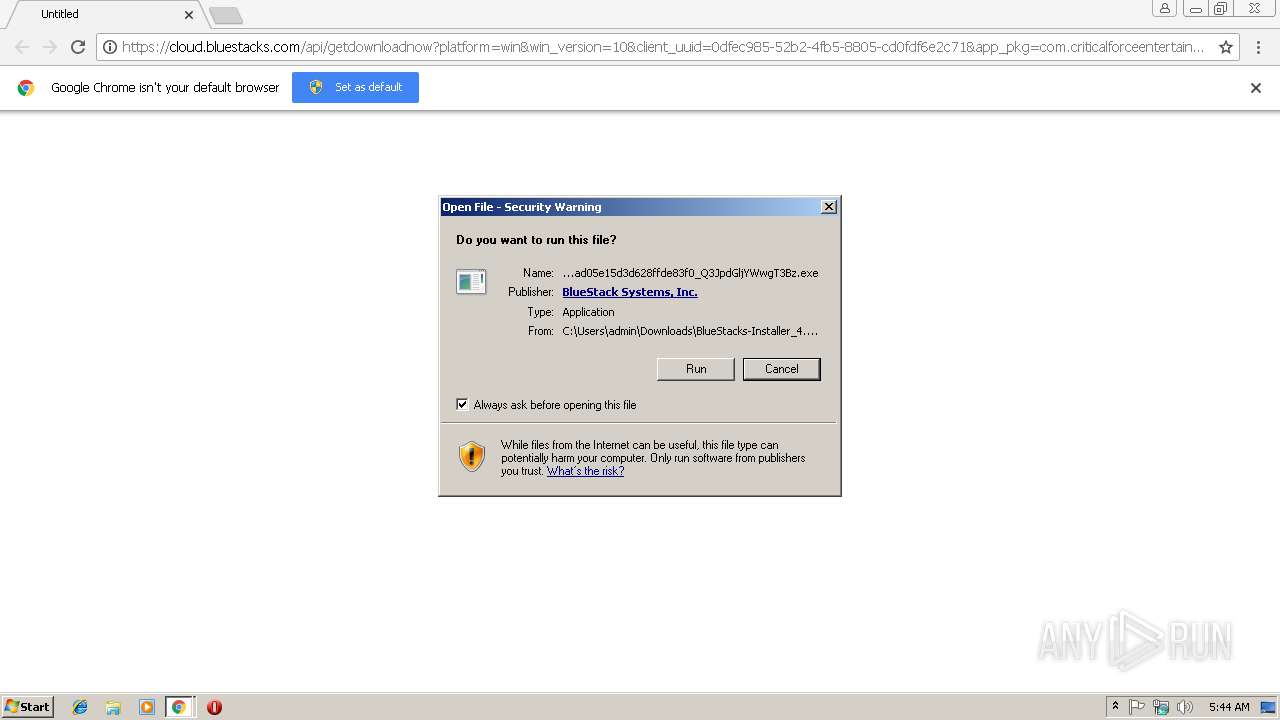
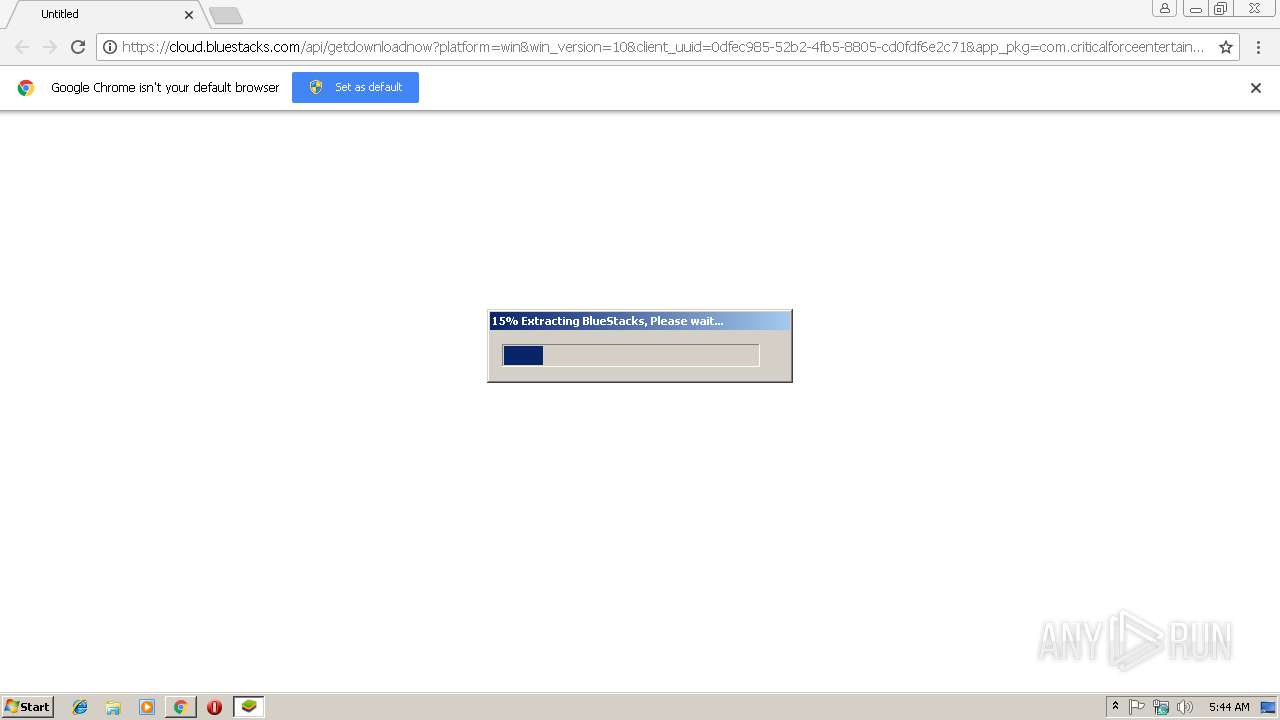
Application was dropped or rewritten from another process
- 7zr.exe (PID: 1424)
- BlueStacks-Installer_4.50.5.1003_x86_native_ddf0d9eebaaad05e15d3d628ffde83f0_Q3JpdGljYWwgT3Bz.exe (PID: 3492)
- Bootstrapper.exe (PID: 3716)
- BlueStacksInstaller.exe (PID: 3432)
- HD-GLCheck.exe (PID: 2892)
- HD-GLCheck.exe (PID: 2720)
Loads dropped or rewritten executable
- BlueStacksInstaller.exe (PID: 3432)
- Bootstrapper.exe (PID: 3716)
Changes settings of System certificates
- BlueStacksInstaller.exe (PID: 3432)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3048)
- BlueStacks-Installer_4.50.5.1003_x86_native_ddf0d9eebaaad05e15d3d628ffde83f0_Q3JpdGljYWwgT3Bz.exe (PID: 3492)
- 7zr.exe (PID: 1424)
Reads Environment values
- BlueStacksInstaller.exe (PID: 3432)
Adds / modifies Windows certificates
- BlueStacksInstaller.exe (PID: 3432)
Starts CMD.EXE for commands execution
- BlueStacksInstaller.exe (PID: 3432)
Reads the machine GUID from the registry
- BlueStacksInstaller.exe (PID: 3432)
INFO
Application launched itself
- chrome.exe (PID: 3048)
Reads settings of System Certificates
- chrome.exe (PID: 3048)
- BlueStacksInstaller.exe (PID: 3432)
Reads Internet Cache Settings
- chrome.exe (PID: 3048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
15
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1424 | "C:\Users\admin\AppData\Local\Temp\7zSA77A.tmp\7zr.exe" x "C:\Users\admin\AppData\Local\Temp\7zSA77A.tmp\CommonInstallUtils.zip" -o"C:\Users\admin\AppData\Local\Temp\7zSA77A.tmp\" -aoa | C:\Users\admin\AppData\Local\Temp\7zSA77A.tmp\7zr.exe | BlueStacksInstaller.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=888,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AA494380577D90A2CDEFA9D0D1E41C19 --mojo-platform-channel-handle=864 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2720 | "C:\Users\admin\AppData\Local\Temp\7zSA77A.tmp\HD-GLCheck.exe" 2 | C:\Users\admin\AppData\Local\Temp\7zSA77A.tmp\HD-GLCheck.exe | — | BlueStacksInstaller.exe | |||||||||||
User: admin Company: BlueStack Systems Integrity Level: HIGH Description: BlueStacks GLCheck Utility Exit code: 0 Version: 4.50.5.1003 | |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --service-pipe-token=7902E1C7612ABD71EF83087B4AAD65DB --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7902E1C7612ABD71EF83087B4AAD65DB --renderer-client-id=4 --mojo-platform-channel-handle=1848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2892 | "C:\Users\admin\AppData\Local\Temp\7zSA77A.tmp\HD-GLCheck.exe" 1 | C:\Users\admin\AppData\Local\Temp\7zSA77A.tmp\HD-GLCheck.exe | — | BlueStacksInstaller.exe | |||||||||||
User: admin Company: BlueStack Systems Integrity Level: HIGH Description: BlueStacks GLCheck Utility Exit code: 1 Version: 4.50.5.1003 Modules
| |||||||||||||||
| 2924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=888,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=4DEDAB7CC9ADC0951A4B09D26DC8FB36 --mojo-platform-channel-handle=3540 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3052 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=888,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8759005EF05A01F8FE8F2126FD8EDD7A --mojo-platform-channel-handle=3728 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3044 | "cmd" /c dir "C:\Users\admin\AppData\Local\Temp\7zSA77A.tmp\" /s | C:\Windows\system32\cmd.exe | — | BlueStacksInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://cloud.bluestacks.com/api/getdownloadnow?platform=win&win_version=10&client_uuid=0dfec985-52b2-4fb5-8805-cd0fdf6e2c71&app_pkg=com.criticalforceentertainment.criticalops&utm_source=&utm_medium=&utm_campaign=homepage-dl-button-en&exit_utm_campaign=ap-critical-ops-us&referrer=&first_landing_page=https%253A%252F%252Fwww.bluestacks.com%252F&download_page_referrer=&gaCookie=&gclid=&clickid=&msclkid=&affiliateId=&offerId=&transaction_id=&aff_sub=&platform_cloud=%257B%2522description%2522%253A%2522Chrome%252072.0.3626.121%2520on%2520Windows%252010%252064-bit%2522%252C%2522layout%2522%253A%2522Blink%2522%252C%2522manufacturer%2522%253Anull%252C%2522name%2522%253A%2522Chrome%2522%252C%2522prerelease%2522%253Anull%252C%2522product%2522%253Anull%252C%2522ua%2522%253A%2522Mozilla%252F5.0%2520(Windows%2520NT%252010.0%253B%2520Win64%253B%2520x64)%2520AppleWebKit%252F537.36%2520(KHTML%252C%2520like%2520Gecko)%2520Chrome%252F72.0.3626.121%2520Safari%252F537.36%2522%252C%2522version%2522%253A%252272.0.3626.121%2522%252C%2522os%2522%253A%257B%2522architecture%2522%253A64%252C%2522family%2522%253A%2522Windows%2522%252C%2522version%2522%253A%252210%2522%257D%257D&preferred_lang=en | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 726
Read events
1 607
Write events
88
Delete events
31
Modification events
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3048-13196238193311625 |
Value: 259 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3048-13196238193311625 |
Value: 259 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
8
Suspicious files
22
Text files
77
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a4c806f6-671a-4ad9-9aa7-97d793cbf183.tmp | — | |
MD5:— | SHA256:— | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5a6e32c3-bec1-40f8-b9e1-579e895df889.tmp | — | |
MD5:— | SHA256:— | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20e89f.TMP | text | |
MD5:— | SHA256:— | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF20e8ce.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
12
DNS requests
11
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3048 | chrome.exe | GET | 200 | 92.122.213.201:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 55.2 Kb | whitelisted |
3048 | chrome.exe | GET | 200 | 143.204.10.192:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3048 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3048 | chrome.exe | 172.217.16.179:443 | cloud.bluestacks.com | Google Inc. | US | whitelisted |
3048 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3048 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3048 | chrome.exe | 143.204.15.23:443 | cdn3.bluestacks.com | — | US | unknown |
3048 | chrome.exe | 172.217.16.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3432 | BlueStacksInstaller.exe | 172.217.16.179:443 | cloud.bluestacks.com | Google Inc. | US | whitelisted |
3432 | BlueStacksInstaller.exe | 143.204.15.118:443 | cdn-bgp.bluestacks.com | — | US | unknown |
3048 | chrome.exe | 92.122.213.201:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3048 | chrome.exe | 143.204.10.192:80 | x.ss2.us | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
cloud.bluestacks.com |
| whitelisted |
accounts.google.com |
| shared |
cdn3.bluestacks.com |
| shared |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
cdn-bgp.bluestacks.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3048 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
Process | Message |
|---|---|
chrome.exe | Error - |
chrome.exe | Too long restart command line passed |
chrome.exe |