| URL: | http://clickemailmkt.seedsofdreams.org/ls/click?upn=S4hrHcLLwGToZPkhsV2WJeMO4BF6-2FU2TxNlIOtYxSMUfmMq4vefoKSVxZqRKgTvtSyT47ibnx-2F-2B2YQENzfUz-2FlUbVA-2F5W4G32TAe6KYApDbtaY9ive3tYs-2BuTFUB1qtQdo0KNn1JPudQQ12q83EAmLojMCL3DKfV0PFU9vmk-2Ba9EgBrDl4-2FslzViL7xPPVxhfadW7tZ-2Fric6MVrQCb2rttDzuvHsGYwMl3p6HDg2JEc-3DyUsT_GwiqylxLZXUGVCtyvgjn8tWVt6rr7u-2BBxdqFO7CaZayMX4tBphXJ8XsgajvQMFEkamHHWDmUnIHNP-2Fn83GXiXR91EI-2BXxaTgZXnBDfZ2-2BLPk9BuVYddPekQn3w89Ei63jcrE7fD1t2c4mXAIbHq4bSQqYBLxngugO92JF4PVkOWRMH0fMLAvZZIZrmXGus9GfP-2FowxCi6avvkkWOioFGTO05VjPGPn-2BO3V77g-2F-2Bvy9zLVQS59LdNB79g0JpGBY20jIz2-2FcJdbhaplanzOyVeMHSR7jUkNoMpv6XOdQRwBHLdiDilGz-2FoYUapuyoaZhLB7VAj5oI-2Fm7ZT2ft4X1vgCVmwtEszn2BTwbI41RxFRPuBV9pOfBwjItONT35XsgVJS9GirgxNE7rNkK-2Bo6cdC824fYYeR9wzdh5fcGQ-2FNGDxlr5klvOTKlKCCTrwqG3xhBDRh0Vs8C-2B6GnycCvwljevfv1W-2B-2FiO8QoUg-2FUwV9W9NwqsJQ1p-2BuM1i8AgcYUoNUgFKVNKxoVsb-2B9i9fmjskriie4JUEwHt8sQI6vP2Y6zQcV1T335OM9eidq9Rq05zH4OrwXvh62qvsRJ4xvr-2FIN12T0bp1qNP2TwugsW3biYo9Ml6rmM0Zpcq9v-2BZZbZE67QnoqbIyXXeqjcgI8Xymh87T9-2BLqFBfo1x8OTlhIH9A-3D |
| Full analysis: | https://app.any.run/tasks/7a921e32-cc8d-4c99-a0a3-5902a3cdb3cd |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2023, 18:36:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DCFB622A0B73C99FEB9E712DEBE506C9 |
| SHA1: | 288F03A0F3CEFA2FA147000D3AE1366755AF6CC1 |
| SHA256: | 71E5D999BA2AB79E1E752C6594FC0BCB068ABC2A4306E071BE78D50360EB6149 |
| SSDEEP: | 24:F9GifkL55jYY9ZebJkewihf6ucHVC0zABhNShHu6sdt:XVfQ3MY9akewi3cI0z+QhHlsD |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- wmpnscfg.exe (PID: 2600)
Application launched itself
- iexplore.exe (PID: 844)
Reads the computer name
- wmpnscfg.exe (PID: 2600)
Manual execution by a user
- wmpnscfg.exe (PID: 2600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 844 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://clickemailmkt.seedsofdreams.org/ls/click?upn=S4hrHcLLwGToZPkhsV2WJeMO4BF6-2FU2TxNlIOtYxSMUfmMq4vefoKSVxZqRKgTvtSyT47ibnx-2F-2B2YQENzfUz-2FlUbVA-2F5W4G32TAe6KYApDbtaY9ive3tYs-2BuTFUB1qtQdo0KNn1JPudQQ12q83EAmLojMCL3DKfV0PFU9vmk-2Ba9EgBrDl4-2FslzViL7xPPVxhfadW7tZ-2Fric6MVrQCb2rttDzuvHsGYwMl3p6HDg2JEc-3DyUsT_GwiqylxLZXUGVCtyvgjn8tWVt6rr7u-2BBxdqFO7CaZayMX4tBphXJ8XsgajvQMFEkamHHWDmUnIHNP-2Fn83GXiXR91EI-2BXxaTgZXnBDfZ2-2BLPk9BuVYddPekQn3w89Ei63jcrE7fD1t2c4mXAIbHq4bSQqYBLxngugO92JF4PVkOWRMH0fMLAvZZIZrmXGus9GfP-2FowxCi6avvkkWOioFGTO05VjPGPn-2BO3V77g-2F-2Bvy9zLVQS59LdNB79g0JpGBY20jIz2-2FcJdbhaplanzOyVeMHSR7jUkNoMpv6XOdQRwBHLdiDilGz-2FoYUapuyoaZhLB7VAj5oI-2Fm7ZT2ft4X1vgCVmwtEszn2BTwbI41RxFRPuBV9pOfBwjItONT35XsgVJS9GirgxNE7rNkK-2Bo6cdC824fYYeR9wzdh5fcGQ-2FNGDxlr5klvOTKlKCCTrwqG3xhBDRh0Vs8C-2B6GnycCvwljevfv1W-2B-2FiO8QoUg-2FUwV9W9NwqsJQ1p-2BuM1i8AgcYUoNUgFKVNKxoVsb-2B9i9fmjskriie4JUEwHt8sQI6vP2Y6zQcV1T335OM9eidq9Rq05zH4OrwXvh62qvsRJ4xvr-2FIN12T0bp1qNP2TwugsW3biYo9Ml6rmM0Zpcq9v-2BZZbZE67QnoqbIyXXeqjcgI8Xymh87T9-2BLqFBfo1x8OTlhIH9A-3D" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3816 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:844 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
9 808
Read events
9 727
Write events
79
Delete events
2
Modification events
| (PID) Process: | (844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
11
Text files
15
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 844 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:3EA958BC0C7495A87C738736E7C818E5 | SHA256:00EDB456A84C17E956413EBDF6338C127B738930FBEAD2CC03739A2D884A04DC | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:2E8CB5B72B131F80C9ABECCEE2E4FDB3 | SHA256:74447BC6D840609750B438E00039747C8D1E5D39FB14B42B93FA85B5D97FA79A | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\GQST6JQ0.txt | text | |
MD5:54DDEC9C33FEDB979E5683F5E1F7E262 | SHA256:F43292F3BD7107BCF0BB552DAD57169DBD05C5DDB14B6F20A7B391F62A77BE4E | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_C5130A0BDC8C859A2757D77746C10868 | der | |
MD5:D56F8BE95F822E5E132F4363389D6116 | SHA256:3F05D033BD176AF61310A6180854595A2A46EF72967DBDA0F205B28F9FB8D7F5 | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_C5130A0BDC8C859A2757D77746C10868 | binary | |
MD5:AF4A5B456EA8F6D29AF7E6ABF3513DB9 | SHA256:CC748E1BA0EC79A837871D9F0110331409450808BC6E34BB9CDA8ADF293362B6 | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\8X2DUFIQ.txt | text | |
MD5:E87A393006E46A12A579553D1C600946 | SHA256:F6E294A3B718BF6CE9EE3126E2973A77DFF0274005D8FD0BED77BEA3D7CEFBE6 | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verE3EC.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:E218DC50D979746B5C632CC457E23151 | SHA256:F1237055FF8A3089EACF2E72FFF24D2D339E963BBB9FF58B03C42015E4FD3406 | |||
| 844 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:82CA6852654F09AD49480D5A7B7C4C45 | SHA256:28214A356E5B5CD6B07E7E5B5A38A4621640D4E430EF67F5FD4B1E2D335578E9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
37
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3816 | iexplore.exe | GET | 302 | 167.89.115.150:80 | http://clickemailmkt.seedsofdreams.org/ls/click?upn=S4hrHcLLwGToZPkhsV2WJeMO4BF6-2FU2TxNlIOtYxSMUfmMq4vefoKSVxZqRKgTvtSyT47ibnx-2F-2B2YQENzfUz-2FlUbVA-2F5W4G32TAe6KYApDbtaY9ive3tYs-2BuTFUB1qtQdo0KNn1JPudQQ12q83EAmLojMCL3DKfV0PFU9vmk-2Ba9EgBrDl4-2FslzViL7xPPVxhfadW7tZ-2Fric6MVrQCb2rttDzuvHsGYwMl3p6HDg2JEc-3DyUsT_GwiqylxLZXUGVCtyvgjn8tWVt6rr7u-2BBxdqFO7CaZayMX4tBphXJ8XsgajvQMFEkamHHWDmUnIHNP-2Fn83GXiXR91EI-2BXxaTgZXnBDfZ2-2BLPk9BuVYddPekQn3w89Ei63jcrE7fD1t2c4mXAIbHq4bSQqYBLxngugO92JF4PVkOWRMH0fMLAvZZIZrmXGus9GfP-2FowxCi6avvkkWOioFGTO05VjPGPn-2BO3V77g-2F-2Bvy9zLVQS59LdNB79g0JpGBY20jIz2-2FcJdbhaplanzOyVeMHSR7jUkNoMpv6XOdQRwBHLdiDilGz-2FoYUapuyoaZhLB7VAj5oI-2Fm7ZT2ft4X1vgCVmwtEszn2BTwbI41RxFRPuBV9pOfBwjItONT35XsgVJS9GirgxNE7rNkK-2Bo6cdC824fYYeR9wzdh5fcGQ-2FNGDxlr5klvOTKlKCCTrwqG3xhBDRh0Vs8C-2B6GnycCvwljevfv1W-2B-2FiO8QoUg-2FUwV9W9NwqsJQ1p-2BuM1i8AgcYUoNUgFKVNKxoVsb-2B9i9fmjskriie4JUEwHt8sQI6vP2Y6zQcV1T335OM9eidq9Rq05zH4OrwXvh62qvsRJ4xvr-2FIN12T0bp1qNP2TwugsW3biYo9Ml6rmM0Zpcq9v-2BZZbZE67QnoqbIyXXeqjcgI8Xymh87T9-2BLqFBfo1x8OTlhIH9A-3D | unknown | html | 184 b | unknown |
844 | iexplore.exe | GET | — | 23.32.238.163:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e535a2b726b1acf4 | unknown | — | — | unknown |
3816 | iexplore.exe | GET | 302 | 167.89.115.150:80 | http://clickemailmkt.seedsofdreams.org/ls/click?upn=S4hrHcLLwGToZPkhsV2WJeMO4BF6-2FU2TxNlIOtYxSMUfmMq4vefoKSVxZqRKgTvtSyT47ibnx-2F-2B2YQENzfUz-2FlUbVA-2F5W4G32TAe6KYApDbtaY9ive3tYs-2BuTFUB1qtQdo0KNn1JPudQQ12q83EAmLojMCL3DKfV0PFU9vmk-2Ba9EgBrDl4-2FslzViL7xPPVxhfadW7tZ-2Fric6MVrQCb2rttDzuvHsGYwMl3p6HDg2JEc-3DyUsT_GwiqylxLZXUGVCtyvgjn8tWVt6rr7u-2BBxdqFO7CaZayMX4tBphXJ8XsgajvQMFEkamHHWDmUnIHNP-2Fn83GXiXR91EI-2BXxaTgZXnBDfZ2-2BLPk9BuVYddPekQn3w89Ei63jcrE7fD1t2c4mXAIbHq4bSQqYBLxngugO92JF4PVkOWRMH0fMLAvZZIZrmXGus9GfP-2FowxCi6avvkkWOioFGTO05VjPGPn-2BO3V77g-2F-2Bvy9zLVQS59LdNB79g0JpGBY20jIz2-2FcJdbhaplanzOyVeMHSR7jUkNoMpv6XOdQRwBHLdiDilGz-2FoYUapuyoaZhLB7VAj5oI-2Fm7ZT2ft4X1vgCVmwtEszn2BTwbI41RxFRPuBV9pOfBwjItONT35XsgVJS9GirgxNE7rNkK-2Bo6cdC824fYYeR9wzdh5fcGQ-2FNGDxlr5klvOTKlKCCTrwqG3xhBDRh0Vs8C-2B6GnycCvwljevfv1W-2B-2FiO8QoUg-2FUwV9W9NwqsJQ1p-2BuM1i8AgcYUoNUgFKVNKxoVsb-2B9i9fmjskriie4JUEwHt8sQI6vP2Y6zQcV1T335OM9eidq9Rq05zH4OrwXvh62qvsRJ4xvr-2FIN12T0bp1qNP2TwugsW3biYo9Ml6rmM0Zpcq9v-2BZZbZE67QnoqbIyXXeqjcgI8Xymh87T9-2BLqFBfo1x8OTlhIH9A-3D | unknown | html | 184 b | unknown |
844 | iexplore.exe | GET | — | 23.32.238.163:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?947160355facb38e | unknown | — | — | unknown |
844 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
844 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 23.216.77.146:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?abdc0569852e700a | unknown | compressed | 65.2 Kb | unknown |
1080 | svchost.exe | GET | 200 | 23.216.77.146:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c21afaf42e4512af | unknown | compressed | 4.66 Kb | unknown |
844 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
844 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3816 | iexplore.exe | 167.89.115.150:80 | clickemailmkt.seedsofdreams.org | SENDGRID | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
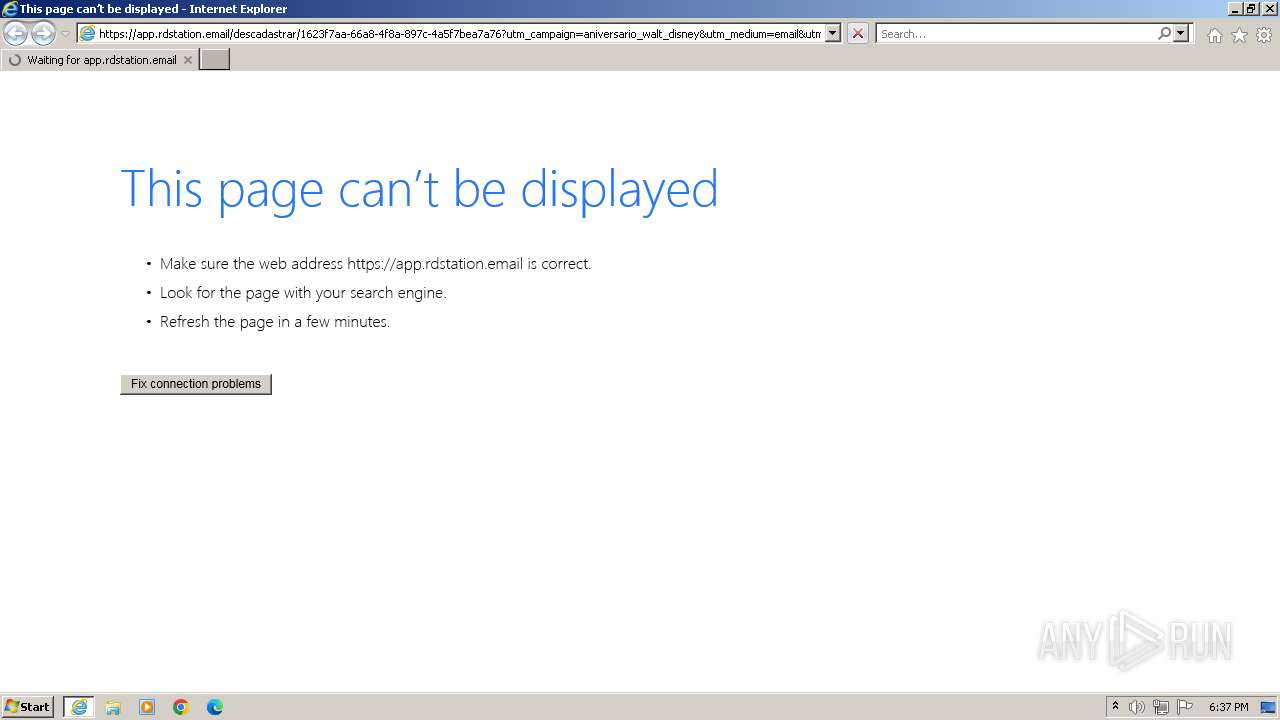
3816 | iexplore.exe | 35.223.116.65:443 | app.rdstation.email | GOOGLE-CLOUD-PLATFORM | US | unknown |
844 | iexplore.exe | 104.126.37.154:443 | www.bing.com | Akamai International B.V. | DE | unknown |
844 | iexplore.exe | 23.32.238.163:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
844 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
844 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clickemailmkt.seedsofdreams.org |
| unknown |
app.rdstation.email |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |