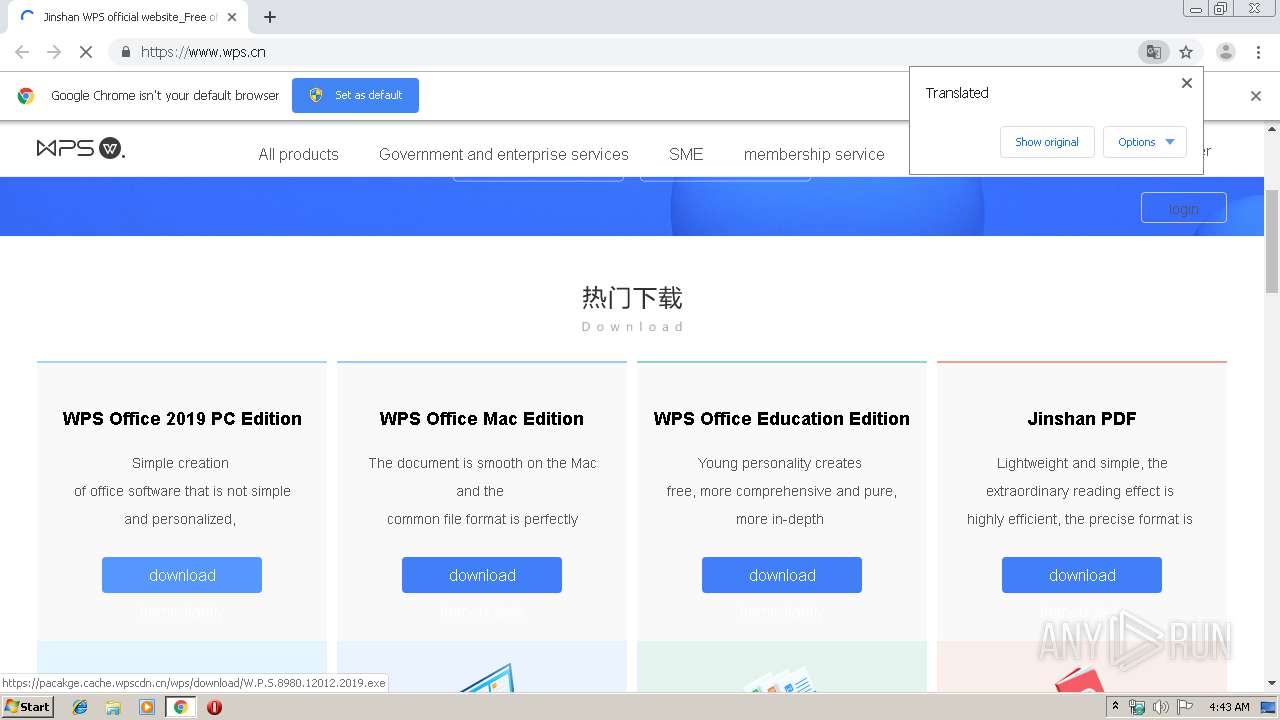
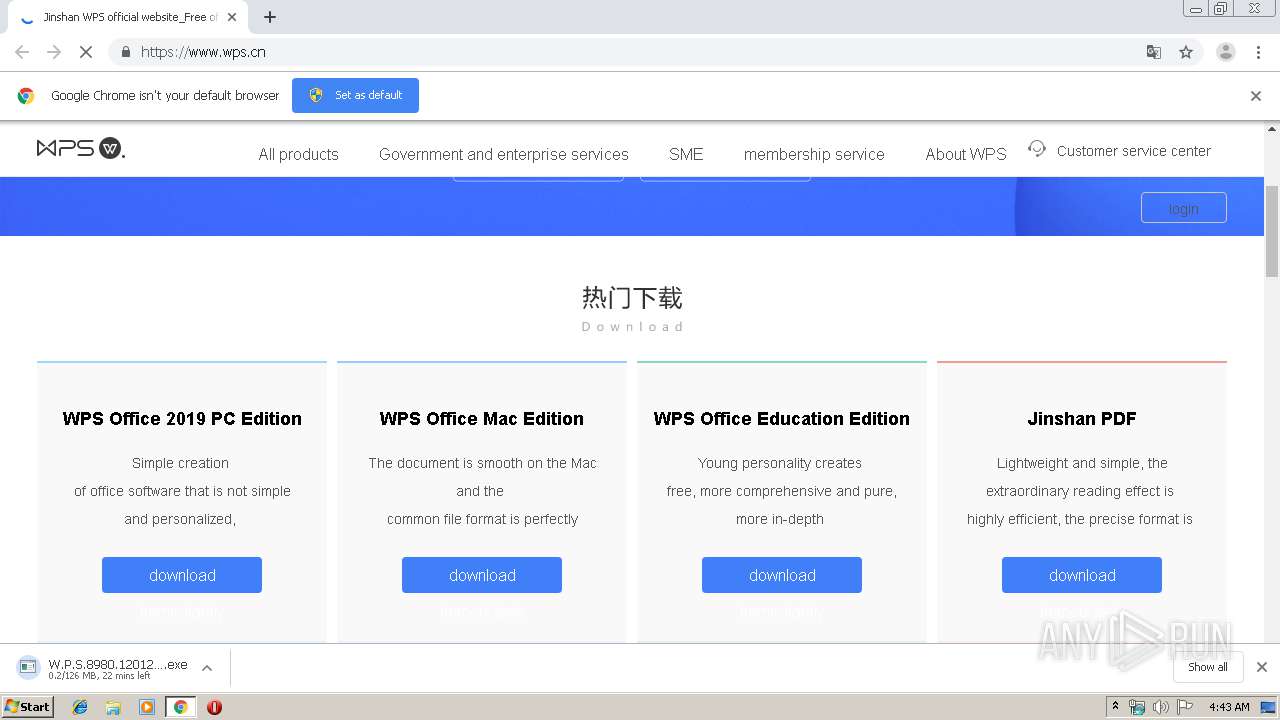
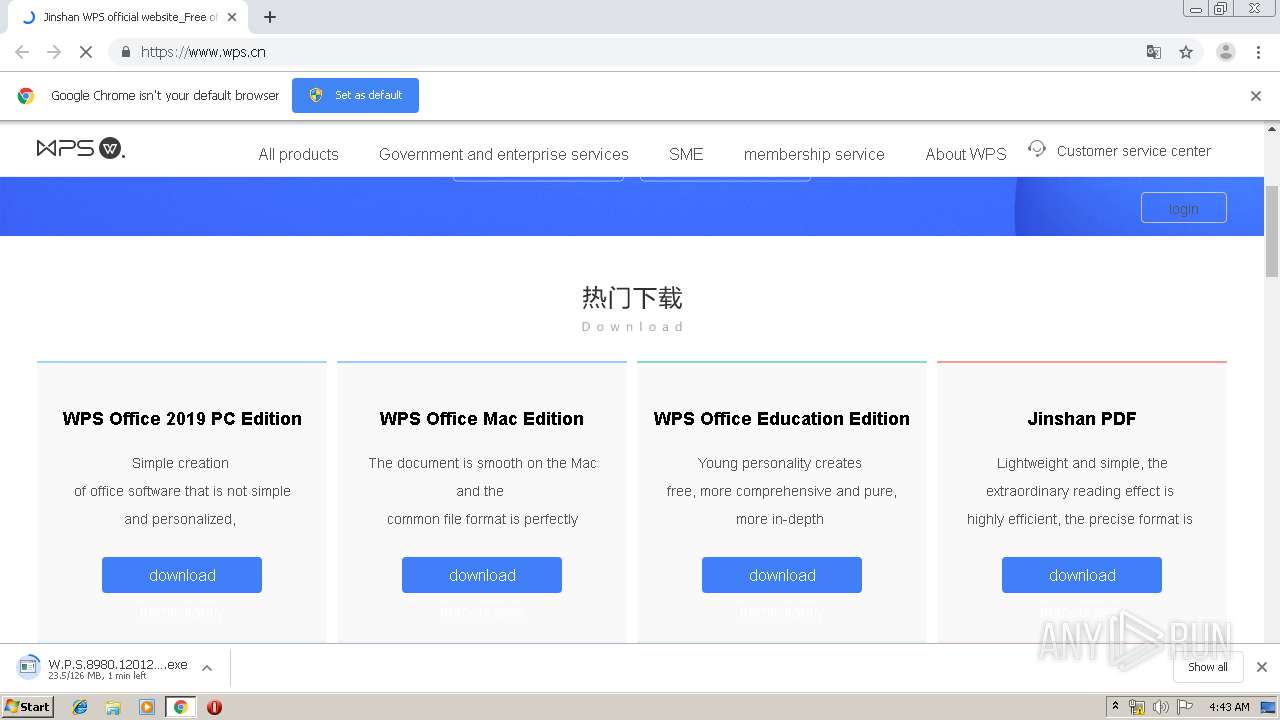
| URL: | http://wps.cn |
| Full analysis: | https://app.any.run/tasks/5ed8f5b9-397e-4210-b60a-126e7e46ba8a |
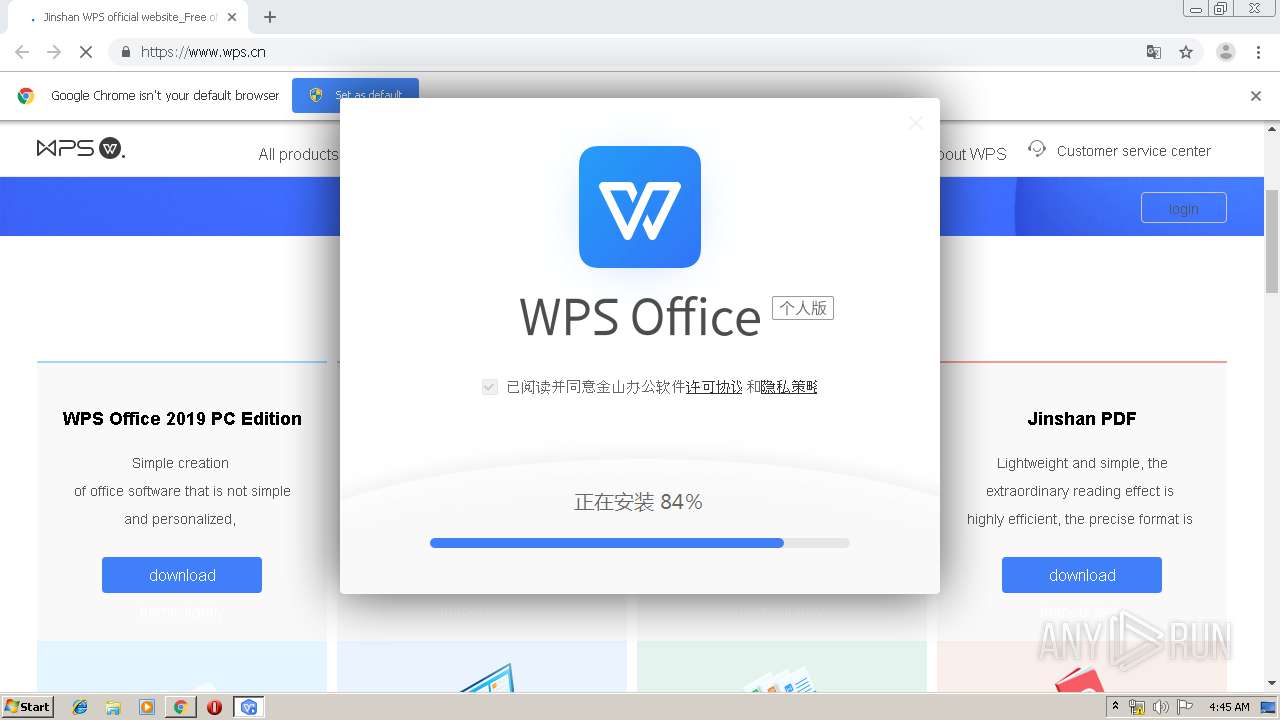
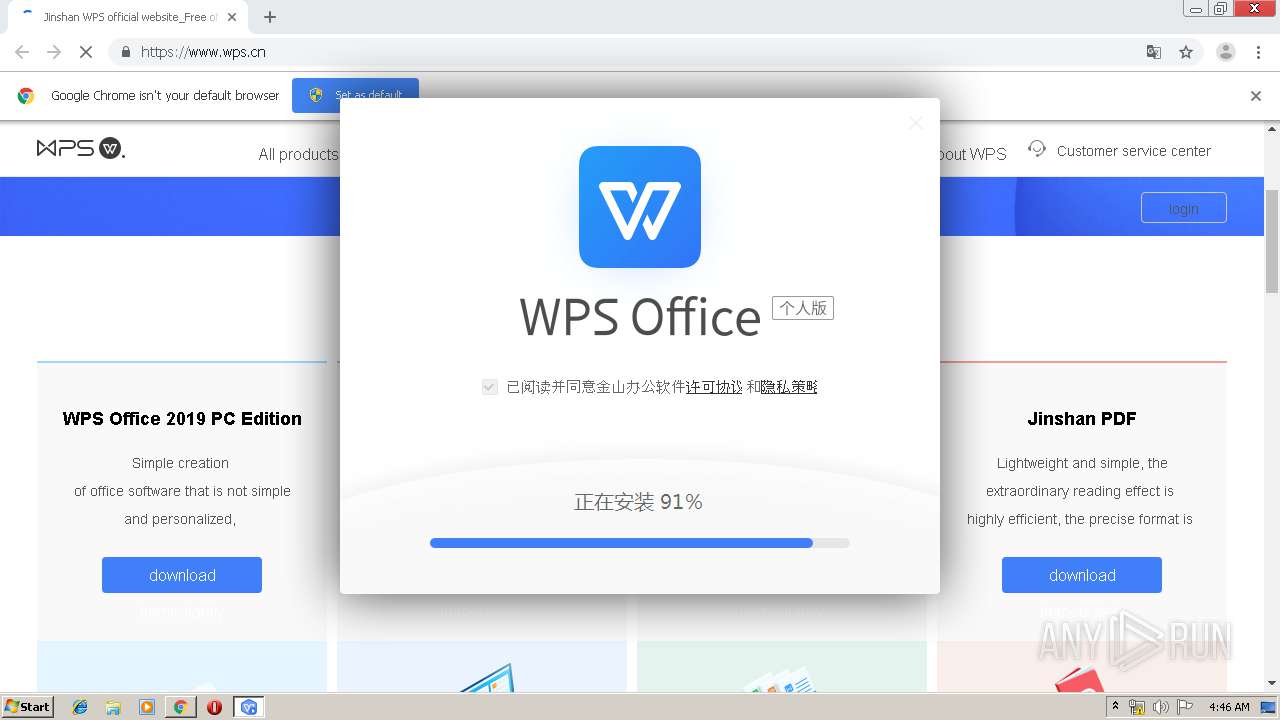
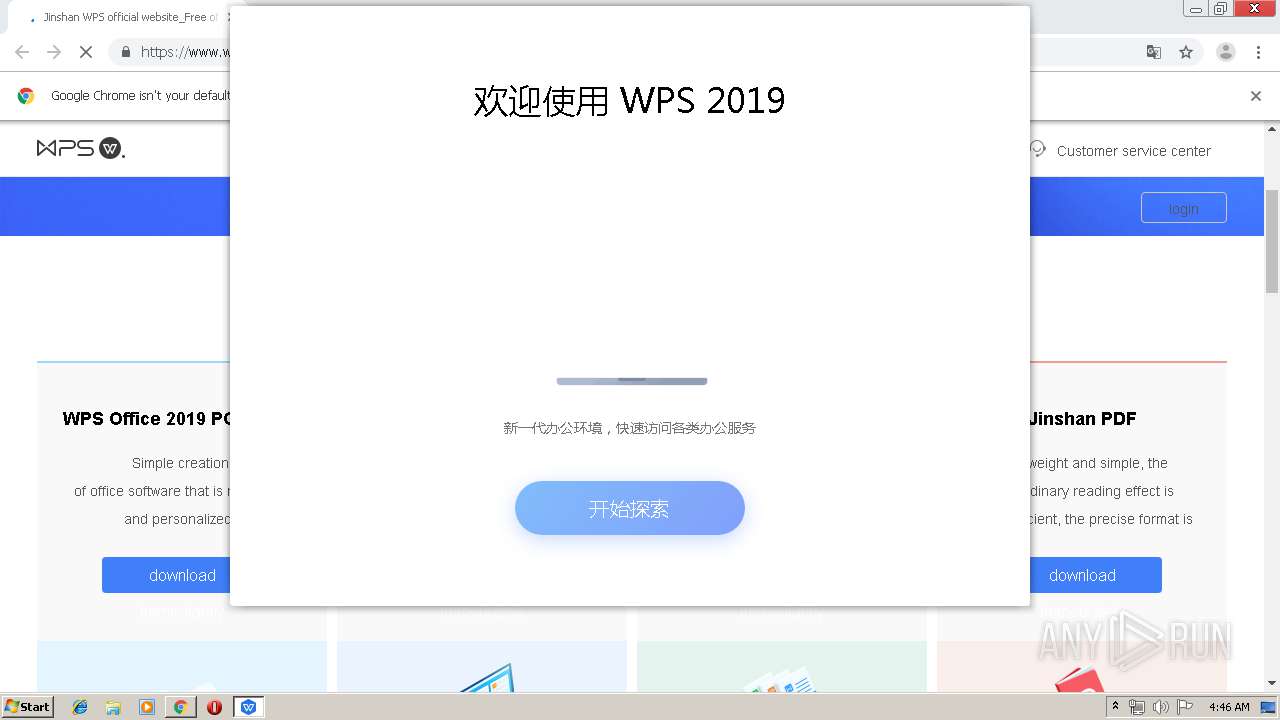
| Verdict: | Malicious activity |
| Analysis date: | August 24, 2019, 03:42:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C4E2B25B54EFF70084B92C82015C5B05 |
| SHA1: | 6B3B4F7395BD8AF68A455B347E1573A79A2B8608 |
| SHA256: | 71DCF41806978A11D088CF63976A3918F4C7EB5ECD982EB41DD82D4AB38538AA |
| SSDEEP: | 3:N1KJVHL:Cf |
MALICIOUS
Application was dropped or rewritten from another process
- W.P.S.8980.12012.2019.exe (PID: 4044)
- W.P.S.8980.12012.2019.exe (PID: 3104)
- wpscloudsvr.exe (PID: 1492)
- wpscloudsvr.exe (PID: 2996)
- wpscloudsvr.exe (PID: 2904)
- wpscloudsvr.exe (PID: 3812)
- ksolaunch.exe (PID: 3412)
- ksolaunch.exe (PID: 320)
- ksolaunch.exe (PID: 2080)
- ksolaunch.exe (PID: 3740)
- ksomisc.exe (PID: 3736)
- ksomisc.exe (PID: 2996)
- ksomisc.exe (PID: 776)
- ksomisc.exe (PID: 3372)
- ksomisc.exe (PID: 3044)
- ksomisc.exe (PID: 3960)
- ksomisc.exe (PID: 308)
- ksomisc.exe (PID: 2336)
- ksomisc.exe (PID: 2256)
- ksomisc.exe (PID: 2452)
- ksomisc.exe (PID: 3328)
- ksomisc.exe (PID: 2008)
- ksomisc.exe (PID: 2972)
- ksomisc.exe (PID: 2428)
- ksomisc.exe (PID: 3076)
- ksomisc.exe (PID: 2436)
- ksomisc.exe (PID: 2960)
- ksomisc.exe (PID: 3784)
- wps.exe (PID: 1444)
- wps.exe (PID: 2832)
- wps.exe (PID: 2076)
- wps.exe (PID: 2508)
- wps.exe (PID: 2328)
- wps.exe (PID: 2012)
- wps.exe (PID: 3408)
- wps.exe (PID: 1536)
- ksomisc.exe (PID: 3288)
- ksomisc.exe (PID: 4004)
- ksomisc.exe (PID: 3588)
- photolaunch.exe (PID: 2440)
- wps.exe (PID: 3928)
- wps.exe (PID: 996)
- ksomisc.exe (PID: 2460)
- wpsupdate.exe (PID: 3428)
- wpsupdate.exe (PID: 3108)
- oem_static.exe (PID: 2476)
- wps.exe (PID: 2244)
Drops known malicious document
- W.P.S.8980.12012.2019.exe (PID: 3908)
Loads dropped or rewritten executable
- ksomisc.exe (PID: 776)
- W.P.S.8980.12012.2019.exe (PID: 4044)
- ksomisc.exe (PID: 3736)
- ksomisc.exe (PID: 2996)
- ksomisc.exe (PID: 3044)
- ksomisc.exe (PID: 3372)
- ksomisc.exe (PID: 3328)
- ksomisc.exe (PID: 308)
- ksomisc.exe (PID: 2008)
- ksomisc.exe (PID: 2428)
- ksomisc.exe (PID: 2256)
- ksomisc.exe (PID: 2336)
- ksomisc.exe (PID: 3960)
- ksomisc.exe (PID: 2452)
- ksomisc.exe (PID: 3076)
- regsvr32.exe (PID: 1008)
- ksomisc.exe (PID: 2972)
- ksomisc.exe (PID: 2436)
- regsvr32.exe (PID: 2364)
- explorer.exe (PID: 276)
- regsvr32.exe (PID: 552)
- svchost.exe (PID: 852)
- wps.exe (PID: 996)
- ksomisc.exe (PID: 2960)
- wps.exe (PID: 2076)
- wps.exe (PID: 1444)
- wps.exe (PID: 3928)
- ksomisc.exe (PID: 3784)
- regsvr32.exe (PID: 2880)
- ksomisc.exe (PID: 3288)
- ksomisc.exe (PID: 2460)
- wps.exe (PID: 2508)
- wps.exe (PID: 2328)
- wps.exe (PID: 2832)
- wps.exe (PID: 3408)
- wps.exe (PID: 1536)
- ksomisc.exe (PID: 3588)
- wpscloudsvr.exe (PID: 2996)
- ksomisc.exe (PID: 4004)
- ksolaunch.exe (PID: 3412)
- wpscloudsvr.exe (PID: 2904)
- regsvr32.exe (PID: 2568)
- ksolaunch.exe (PID: 3740)
- ksolaunch.exe (PID: 320)
- ksolaunch.exe (PID: 2080)
- regsvr32.exe (PID: 3716)
- photolaunch.exe (PID: 2440)
- wps.exe (PID: 2012)
- wpsupdate.exe (PID: 3108)
- wpscloudsvr.exe (PID: 1492)
- wpsupdate.exe (PID: 3428)
- regsvr32.exe (PID: 3296)
- wps.exe (PID: 2244)
Registers / Runs the DLL via REGSVR32.EXE
- ksomisc.exe (PID: 3076)
- W.P.S.8980.12012.2019.exe (PID: 2652)
- ksomisc.exe (PID: 2436)
Loads the Task Scheduler COM API
- wpsupdate.exe (PID: 3428)
- wps.exe (PID: 2076)
- wps.exe (PID: 996)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3436)
- W.P.S.8980.12012.2019.exe (PID: 4044)
- W.P.S.8980.12012.2019.exe (PID: 3908)
- wps.exe (PID: 1536)
- wps.exe (PID: 2508)
Creates files in the program directory
- W.P.S.8980.12012.2019.exe (PID: 4044)
- ksomisc.exe (PID: 3960)
Creates files in the user directory
- W.P.S.8980.12012.2019.exe (PID: 3908)
- ksomisc.exe (PID: 3736)
- ksomisc.exe (PID: 2428)
- wpsupdate.exe (PID: 3108)
- regsvr32.exe (PID: 2364)
- ksomisc.exe (PID: 3288)
- wps.exe (PID: 2508)
- wps.exe (PID: 2012)
Creates a software uninstall entry
- W.P.S.8980.12012.2019.exe (PID: 2652)
Creates COM task schedule object
- ksomisc.exe (PID: 776)
- regsvr32.exe (PID: 1008)
- regsvr32.exe (PID: 3296)
- regsvr32.exe (PID: 2364)
- regsvr32.exe (PID: 552)
- regsvr32.exe (PID: 3716)
- regsvr32.exe (PID: 2880)
- regsvr32.exe (PID: 2568)
Modifies the open verb of a shell class
- ksomisc.exe (PID: 2452)
- ksomisc.exe (PID: 3044)
- ksomisc.exe (PID: 3328)
- ksomisc.exe (PID: 308)
- W.P.S.8980.12012.2019.exe (PID: 2652)
- ksomisc.exe (PID: 776)
- ksomisc.exe (PID: 3588)
Creates files in the Windows directory
- svchost.exe (PID: 852)
- cmd.exe (PID: 2976)
Application launched itself
- wps.exe (PID: 996)
Executed as Windows Service
- wpscloudsvr.exe (PID: 3812)
Reads Internet Cache Settings
- explorer.exe (PID: 276)
- wps.exe (PID: 2508)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3436)
Starts CMD.EXE for commands execution
- wps.exe (PID: 1536)
Starts itself from another location
- wps.exe (PID: 2012)
Connects to server without host name
- wps.exe (PID: 2508)
INFO
Application launched itself
- chrome.exe (PID: 3436)
Reads Internet Cache Settings
- chrome.exe (PID: 3436)
Creates files in the user directory
- chrome.exe (PID: 3436)
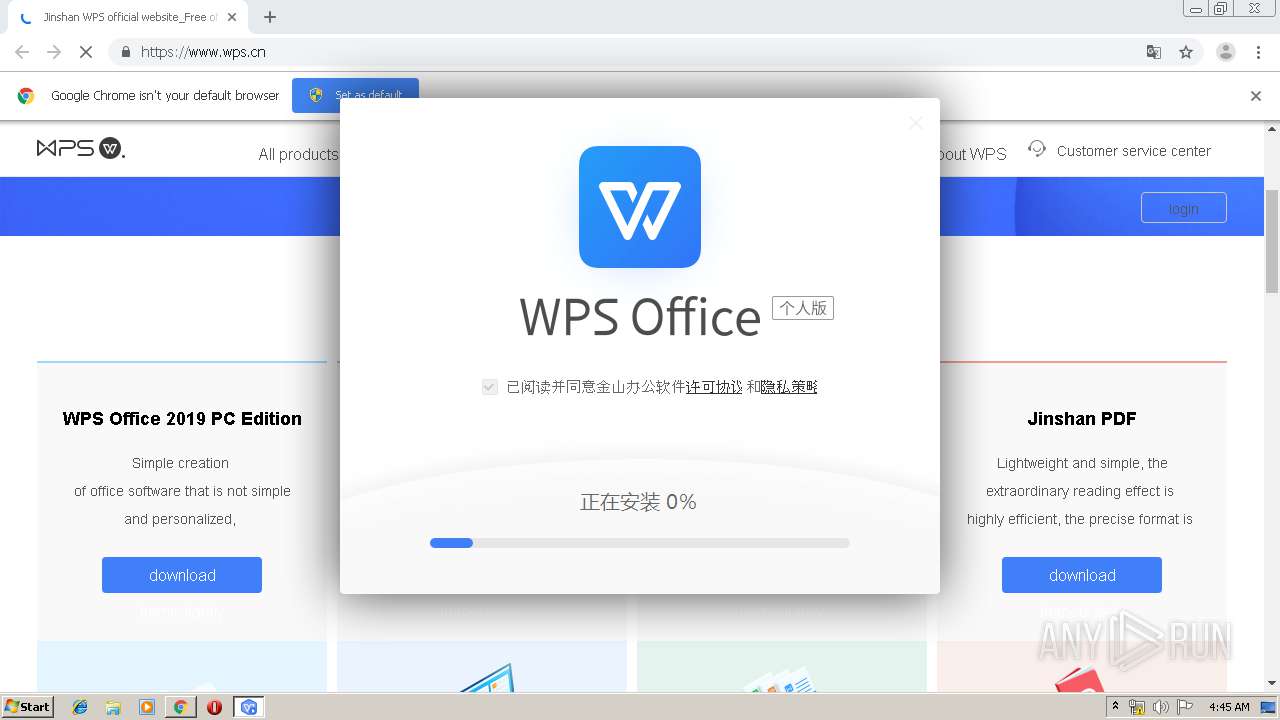
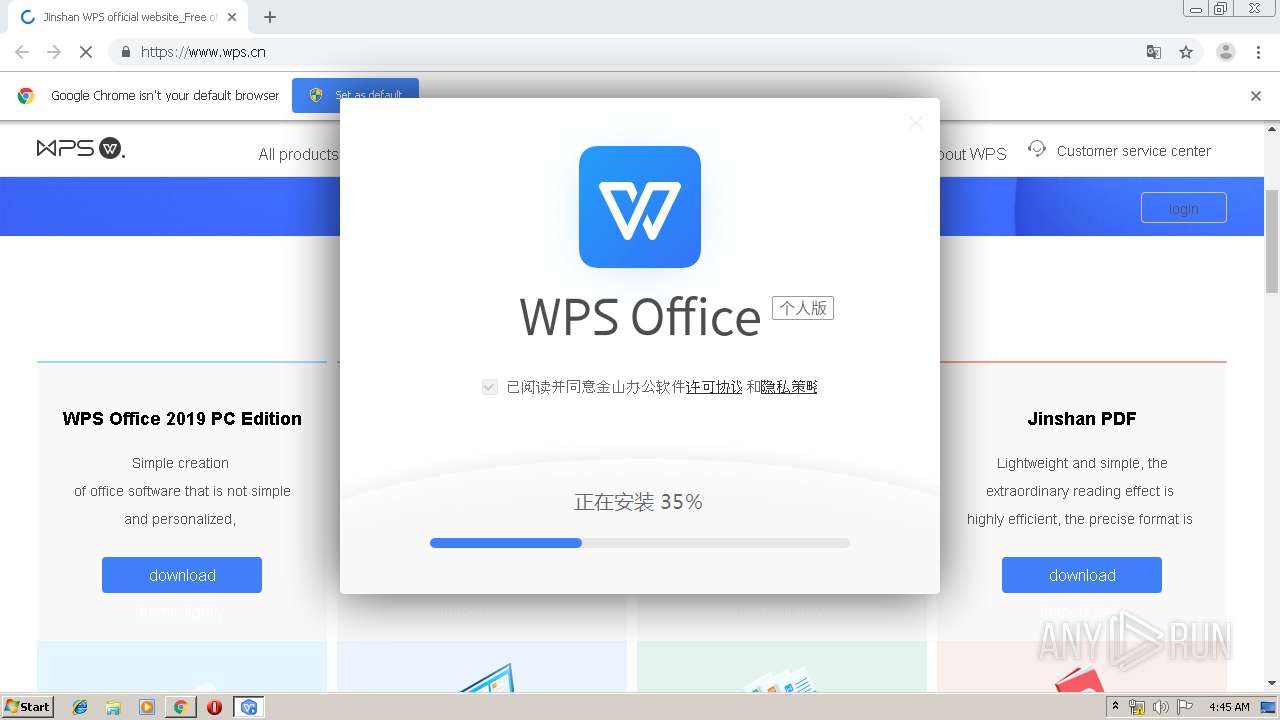
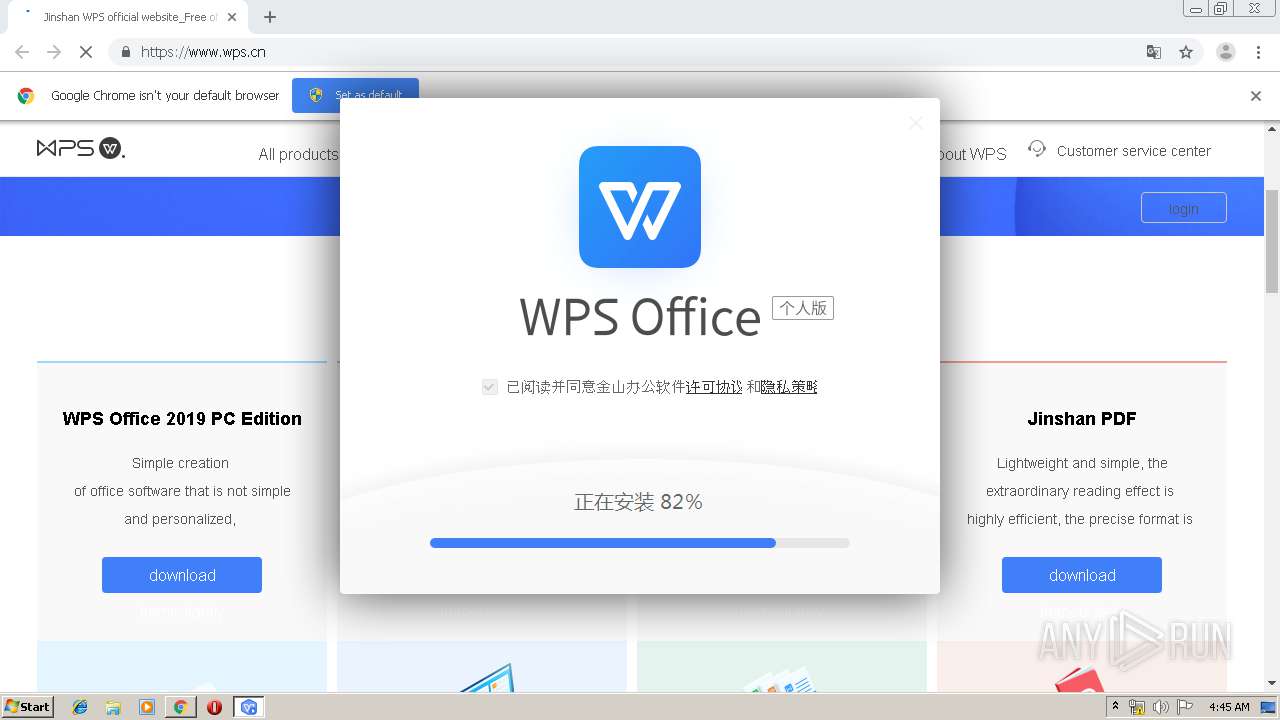
Manual execution by user
- W.P.S.8980.12012.2019.exe (PID: 2652)
Dropped object may contain Bitcoin addresses
- W.P.S.8980.12012.2019.exe (PID: 3908)
- wps.exe (PID: 2508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
122
Monitored processes
82
Malicious processes
49
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,16172058548017808399,7041611739319893982,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6961036308974361384 --mojo-platform-channel-handle=4408 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 276 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 308 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.8980\office6\ksomisc.exe" -Assopowerpnt | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.8980\office6\ksomisc.exe | W.P.S.8980.12012.2019.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Module Exit code: 0 Version: 11,1,0,8980 Modules
| |||||||||||||||
| 320 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\ksolaunch.exe" /krecentfile /init /From=Qing | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\ksolaunch.exe | — | wps.exe | |||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Exit code: 0 Version: 11,1,0,8980 Modules
| |||||||||||||||
| 552 | "C:\Windows\system32\regsvr32.exe" /s /n /i:contextmenu "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.8980\office6\qingnse.dll" | C:\Windows\system32\regsvr32.exe | — | ksomisc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 776 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.8980\office6\ksomisc.exe" -register | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.8980\office6\ksomisc.exe | W.P.S.8980.12012.2019.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Module Exit code: 0 Version: 11,1,0,8980 Modules
| |||||||||||||||
| 852 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,16172058548017808399,7041611739319893982,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2617946441672326904 --mojo-platform-channel-handle=4104 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,16172058548017808399,7041611739319893982,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1914981184956930751 --mojo-platform-channel-handle=4200 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 996 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.8980\office6\wps.exe" Run "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.8980\office6\addons\ktaskschdtool\ktaskschdtool.dll" /task=wpsexternal /createtask | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.8980\office6\wps.exe | — | ksomisc.exe | |||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Exit code: 0 Version: 11,1,0,8980 Modules
| |||||||||||||||
Total events
17 194
Read events
8 419
Write events
8 746
Delete events
29
Modification events
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3436-13211091775714000 |
Value: 259 | |||
| (PID) Process: | (3436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3436) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
Executable files
265
Suspicious files
345
Text files
3 056
Unknown types
338
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\32510823-422e-4ad1-a0b1-656016044daa.tmp | — | |
MD5:— | SHA256:— | |||
| 3436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169c93.TMP | text | |
MD5:DC32343F45B01764B6267AD36548102A | SHA256:A250F5AD57D4BD58AAE92810D50278E3BE2DBF869F126A3A3519691BCDFC2075 | |||
| 3436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169c93.TMP | text | |
MD5:213AE3DA120D7862D60B5763B6C9D466 | SHA256:5736534D6EE654C1BF1A8E79E73330AF58F622E8657285330D2C7189A55604F4 | |||
| 3436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3436 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF169ce1.TMP | text | |
MD5:3D551B6E929CF62F7AA66091E718704B | SHA256:1698A1B1BC3E86676392FB8BD4C712438302A5A2220503C08F290ED4B1790404 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
89
DNS requests
47
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3020 | chrome.exe | GET | 301 | 120.92.124.199:80 | http://wps.cn/ | CN | html | 169 b | whitelisted |
2508 | wps.exe | HEAD | 200 | 123.53.182.246:80 | http://wdl1.cache.wps.cn/per-plugin/dl/addons/list/win-i386/11.1.0.8980/qing/1566293870808.plg | CN | — | — | malicious |
3020 | chrome.exe | GET | — | 173.194.164.121:80 | http://r3---sn-4g5e6nl7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.102.26.200&mm=28&mn=sn-4g5e6nl7&ms=nvh&mt=1566618253&mv=m&mvi=2&pl=25&shardbypass=yes | US | — | — | whitelisted |
2508 | wps.exe | GET | — | 140.210.77.190:80 | http://qing.wps.cn/update?type=switch&wpsver=11.1.0.8980&channel=12012.00002019&qingver=11.1.0.8980&language=zh_CN | CN | — | — | suspicious |
2508 | wps.exe | GET | 200 | 120.92.91.106:80 | http://ic.wps.cn/wpsv6internet/infos.ads?v=D1S1E1&d=ZG09LzIwMTkvd3BzL2NsaWVudC9wbHVnaW4mYWN0aW9uPWRsbGNoZWNrZXJfcnVieSZndWlkPUE0RkMwRDJBRTM5OTQzQTk4RTk5RTg4MjM4NzM5OEMyJmhkaWQ9OEI5RkUwRTUwMUJDOEE5RDY4RDAzNDYxRDE4NUMxMDUmdXVpZD1iZjhhMzc1M2QzZmQxNzZlZTIxYzA5NmQ1YmRhYWY3OCZ2ZXJzaW9uPTExLjEuMC44OTgwJmNoYW5uZWw9MTIwMTIuMDAwMDIwMTkmd29ya2JvYXJkPSZ1c2VyaWQ9JnAwPTAmcG51bT0x | CN | — | — | suspicious |
2012 | wps.exe | GET | — | 120.92.91.106:80 | http://ic.wps.cn/wpsv6internet/infos.ads?v=D1S1E2&d=XD6TfzcRzuMPtzrPrb6PbzrOibMPkHd9arMFl83CnapBt1tSlC6RfLcRqzIOm1d9dLNQarJGqOqGmGaC1LqCva3Dp4KEuKKEvK4Eu8pCuSpCvWpGoO2Qab6PzWZOvOMPmKMDm4ZOZXJOvGcDuG6CpGZDnGMCuKpOn0JDcKNTfHMFYP6EXDpDrC3PpO6PnSZDbLcCnC6CvO3Pr86PX5cPtWZ9sLcSpbsRkrJCnuICk0ZBua3EmOoOe5cRkL6Rz4ZCm4ZCk03Cm0ZCm4JEcStRojcOl5cSarZ9m1JFtL6RZzMRbz5SXTMPVD7QlT7 | CN | — | — | suspicious |
2012 | wps.exe | GET | — | 120.92.91.106:80 | http://ic.wps.cn/wpsv6internet/infos.ads?v=D1S1E2&d=cGMRzyYCm4JElS7SpzoOibMPkHtBX17Sc4sOqbsRkrZRbTtNdLNQaLc9dLNQarJGqOqGmGaC1LqCva3Dp4KEuKKEvK4Eu8pCuSpCvWpGoO2Qab6PzWZOvOMPmKMDm4ZOZXJOvGcDuG6CpGZDnGMCuKpOn0JDcKNTfHMFYP6EXDpDrC3PpO6PnSZDbLcCnC6CvO3Pr86PX5cPtWZ9sLcSpbsRkrJCnuICk0ZBua3EmOoOe5cRkL6Rz4ZCm4ZCk83CnaZ9tzcSh9sRX97PzS7SpzcPcbsObPITpLcSfHMFc07CzSNPiDsRjLsNm5sPbzrSezsTc0dRrrMFnOoNqrJCrOZDs43EpaZCqK3C | CN | — | — | suspicious |
2508 | wps.exe | GET | — | 123.53.182.246:80 | http://wdl1.cache.wps.cn/per-plugin/dl/addons/list/win-i386/11.1.0.8980/qing/index.ini | CN | — | — | malicious |
2508 | wps.exe | GET | — | 10.83.236.159:80 | http://int.dpool.sina.com.cn/iplookup/iplookup.php?format=js | unknown | — | — | malicious |
3020 | chrome.exe | GET | 301 | 120.92.124.198:80 | http://www.wps.cn/ | CN | html | 169 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3020 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3020 | chrome.exe | 120.92.124.199:80 | wps.cn | Beijing Kingsoft Cloud Internet Technology Co., Ltd | CN | unknown |
3020 | chrome.exe | 120.92.124.198:80 | www.wps.cn | Beijing Kingsoft Cloud Internet Technology Co., Ltd | CN | unknown |
3020 | chrome.exe | 120.92.124.198:443 | www.wps.cn | Beijing Kingsoft Cloud Internet Technology Co., Ltd | CN | unknown |
3020 | chrome.exe | 111.48.30.102:443 | qn.cache.wpscdn.cn | Guangdong Mobile Communication Co.Ltd. | CN | unknown |
3020 | chrome.exe | 140.210.77.190:443 | account.wps.cn | China Unicom Beijing Province Network | CN | unknown |
3020 | chrome.exe | 60.221.17.1:443 | js1.epy.wpscdn.cn | CHINA UNICOM China169 Backbone | CN | unknown |
3020 | chrome.exe | 106.122.251.241:443 | js2.epy.wpscdn.cn | Fuzhou | CN | suspicious |
3020 | chrome.exe | 222.85.26.209:443 | c.cnzz.com | No.31,Jin-rong Street | CN | unknown |
3020 | chrome.exe | 203.119.206.95:443 | q17.cnzz.com | — | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wps.cn |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.wps.cn |
| unknown |
qn.cache.wpscdn.cn |
| malicious |
js1.epy.wpscdn.cn |
| suspicious |
js2.epy.wpscdn.cn |
| malicious |
account.wps.cn |
| unknown |
c.cnzz.com |
| whitelisted |
w.cnzz.com |
| unknown |
Threats
Process | Message |
|---|---|
W.P.S.8980.12012.2019.exe | [kscreen] isElide:0 switchRec:0 switchRecElide:1 |
W.P.S.8980.12012.2019.exe | [kscreen] now screensaver is |
W.P.S.8980.12012.2019.exe | unregister dll path:qingshellext.dll
|
W.P.S.8980.12012.2019.exe | unregister dll path:qingshellext.dll
|
W.P.S.8980.12012.2019.exe | unInstall qingshellex success!
|
ksomisc.exe | 2019/08/24 04:45:26 I ksomisc 00000e98:00000e8c [wWinMain][ksomisc begin] cmdline:-setlng zh_CN FL:T:\rc_v11_per_new_20190806\Coding\support\ksomisc\ksomisc.cpp(465)
|
ksomisc.exe | 2019/08/24 04:45:26 I ksomisc 00000bb4:00000b0c [wWinMain][ksomisc begin] cmdline:-setservers FL:T:\rc_v11_per_new_20190806\Coding\support\ksomisc\ksomisc.cpp(465)
|
ksomisc.exe | 2019/08/24 04:45:26 I ksomisc 00000308:000003d0 [wWinMain][ksomisc begin] cmdline:-register FL:T:\rc_v11_per_new_20190806\Coding\support\ksomisc\ksomisc.cpp(465)
|
ksomisc.exe | 2019/08/24 04:45:41 I ksomisc 00000f78:00000888 [wWinMain][ksomisc begin] cmdline:-regmtfont FL:T:\rc_v11_per_new_20190806\Coding\support\ksomisc\ksomisc.cpp(465)
|
ksomisc.exe | 2019/08/24 04:45:41 I ksomisc 00000d2c:00000d68 [wWinMain][ksomisc begin] cmdline:-setappcap FL:T:\rc_v11_per_new_20190806\Coding\support\ksomisc\ksomisc.cpp(465)
|