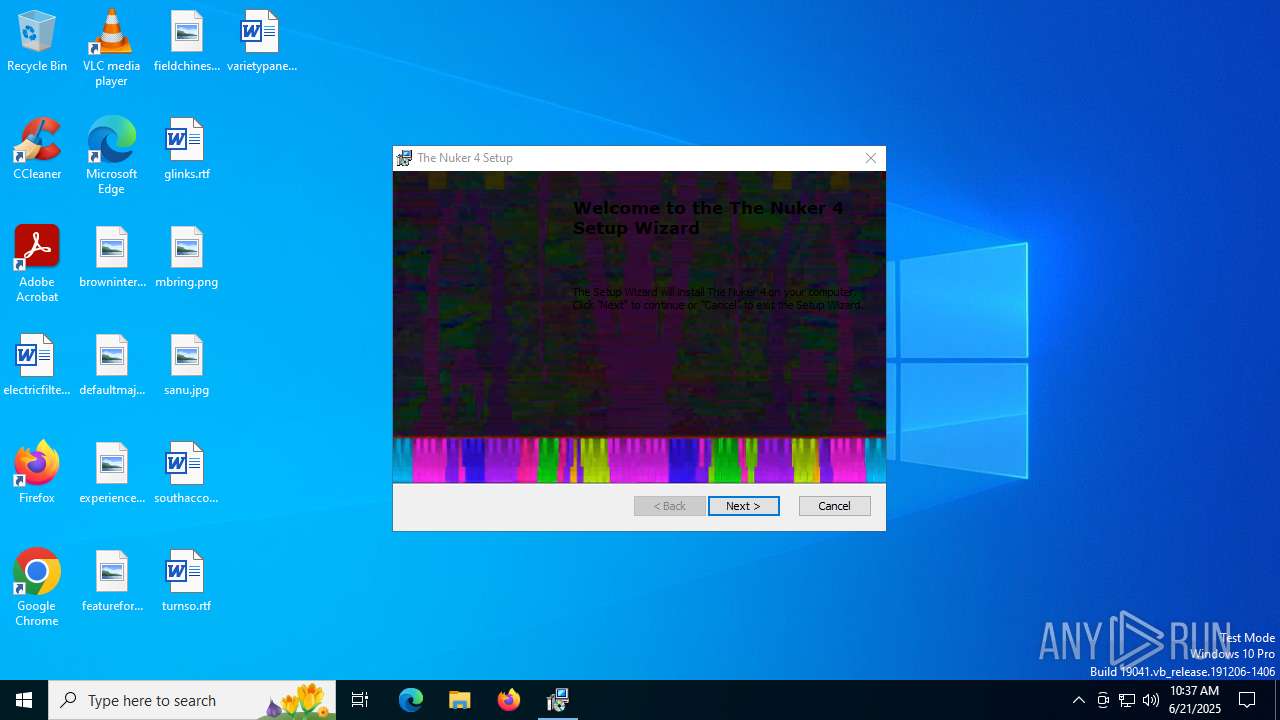
| File name: | The_Nuker_4_Installer.exe |
| Full analysis: | https://app.any.run/tasks/94da3e8c-aac7-498d-8d6d-ff2429102439 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 10:37:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | CCC5C9773432AEA64C2D576FD55EEC35 |
| SHA1: | 678F7869C2F56C632789D5E990EB46E3D5A56BE7 |
| SHA256: | 71D912496B26668FDC7662D07D9D8BC2A4672E771D98B03FDDB1EC4ED92E10B6 |
| SSDEEP: | 98304:XzfyVMcz9E685gGpJaiTpH8qknpAyzMhcn+M5T7bV4lW7hAT7pTtMIUyTCeTs+7q:iiAL9sG |
MALICIOUS
No malicious indicators.SUSPICIOUS
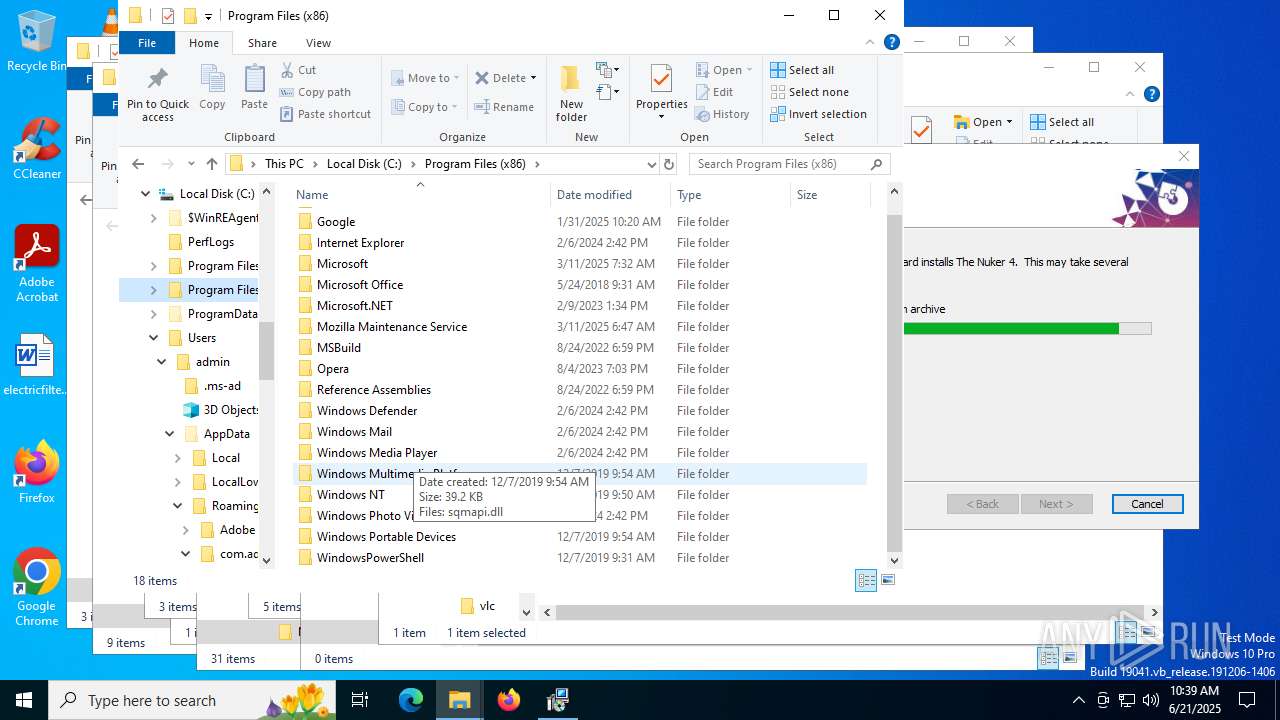
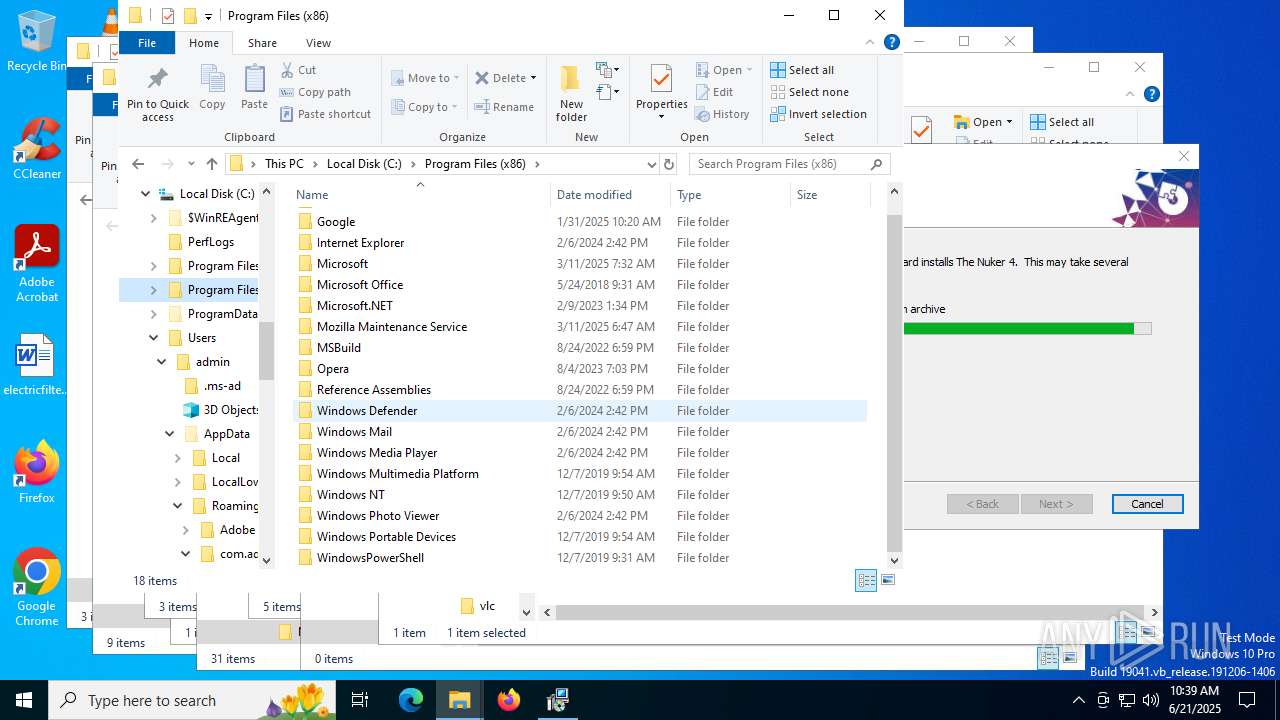
ADVANCEDINSTALLER mutex has been found
- The_Nuker_4_Installer.exe (PID: 2580)
Reads the Windows owner or organization settings
- The_Nuker_4_Installer.exe (PID: 2580)
- msiexec.exe (PID: 6104)
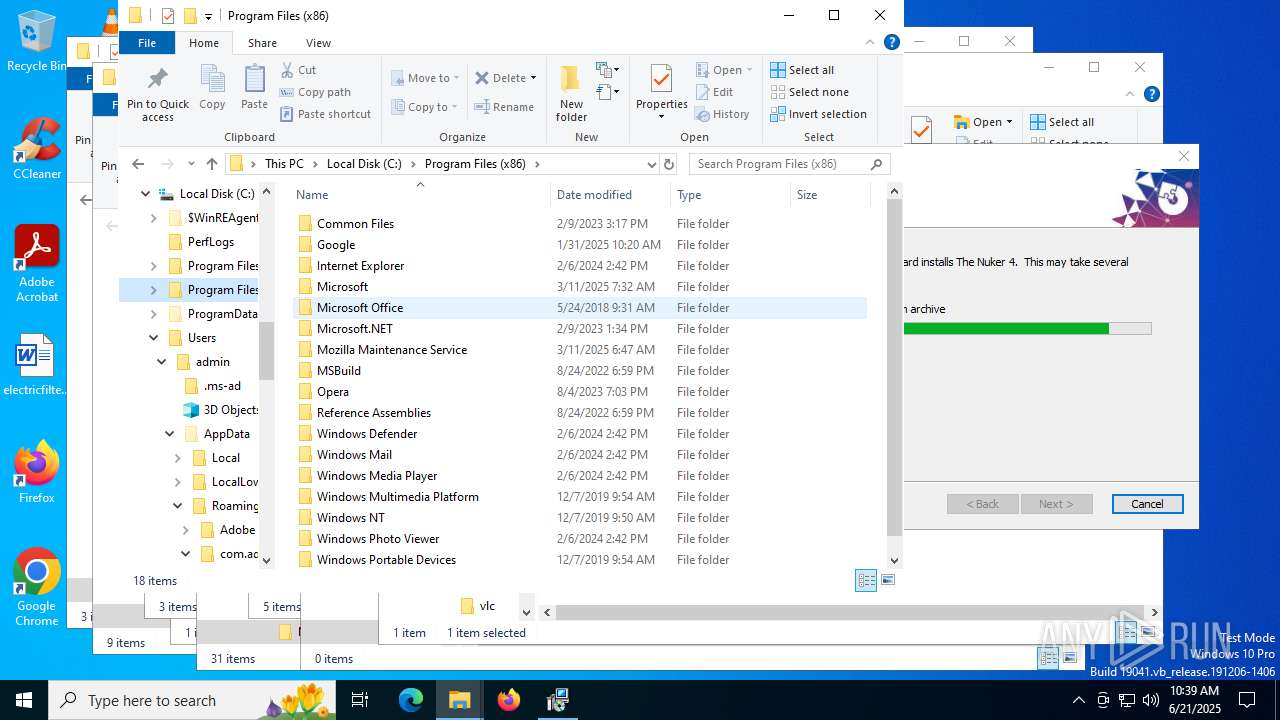
Process drops legitimate windows executable
- The_Nuker_4_Installer.exe (PID: 2580)
Executable content was dropped or overwritten
- The_Nuker_4_Installer.exe (PID: 2580)
Detects AdvancedInstaller (YARA)
- msiexec.exe (PID: 6656)
- The_Nuker_4_Installer.exe (PID: 2580)
Executes as Windows Service
- VSSVC.exe (PID: 7056)
There is functionality for taking screenshot (YARA)
- The_Nuker_4_Installer.exe (PID: 2580)
INFO
Reads the computer name
- msiexec.exe (PID: 6104)
- The_Nuker_4_Installer.exe (PID: 2580)
- msiexec.exe (PID: 2192)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 5244)
- msiexec.exe (PID: 5692)
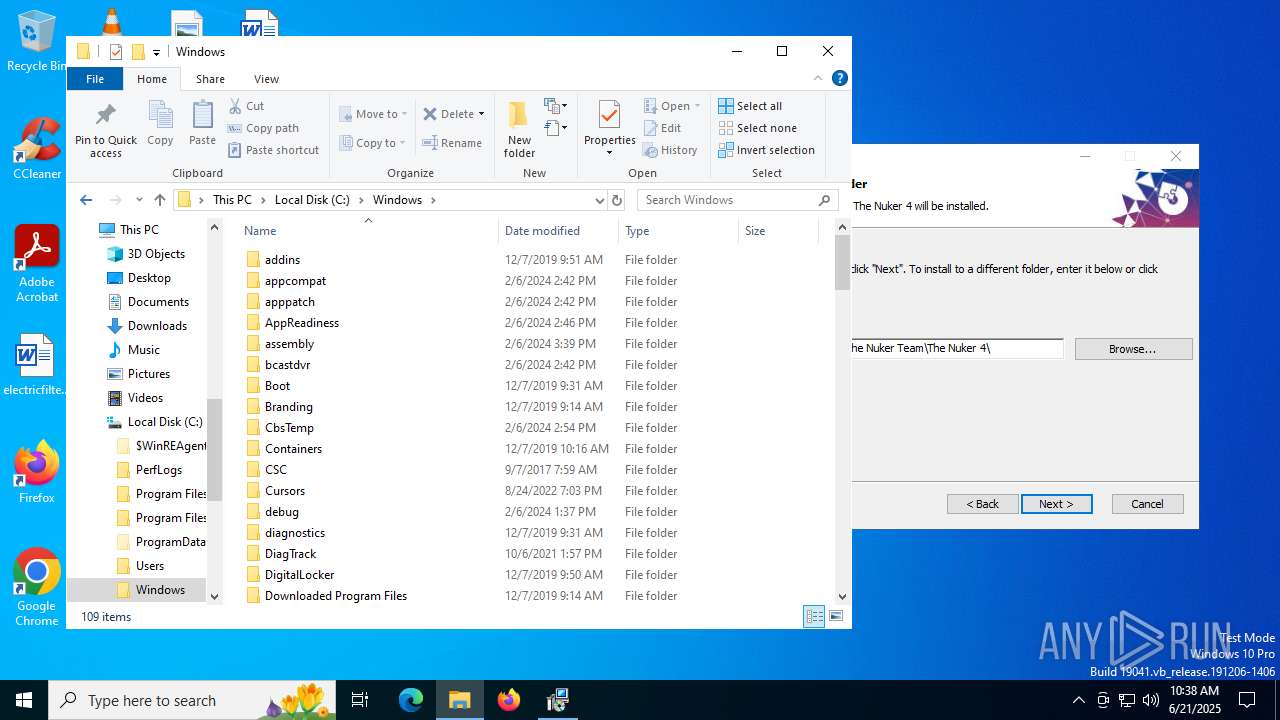
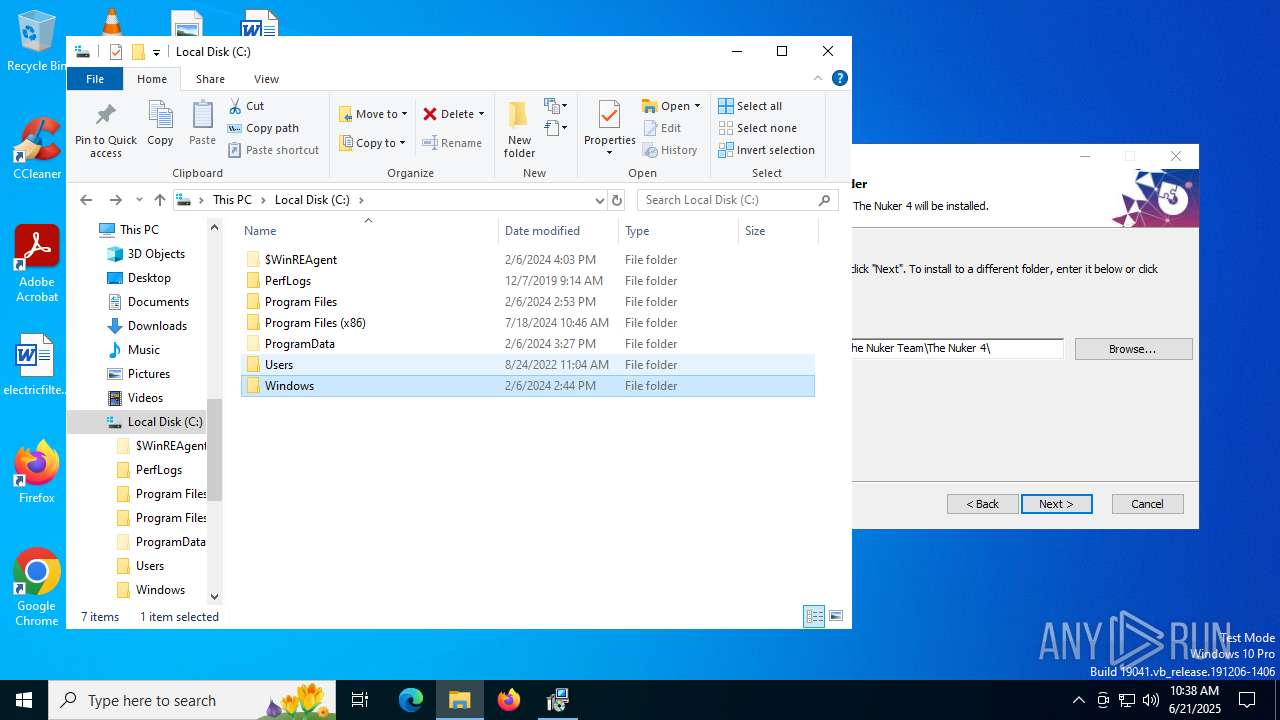
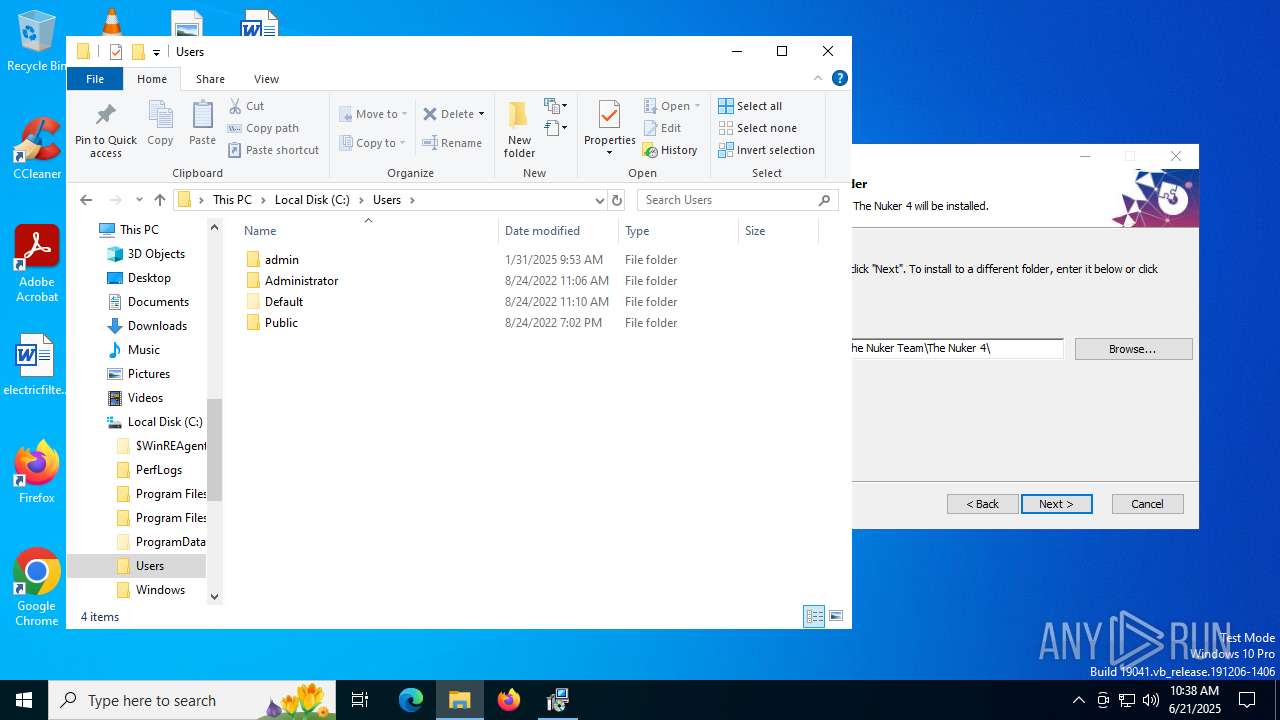
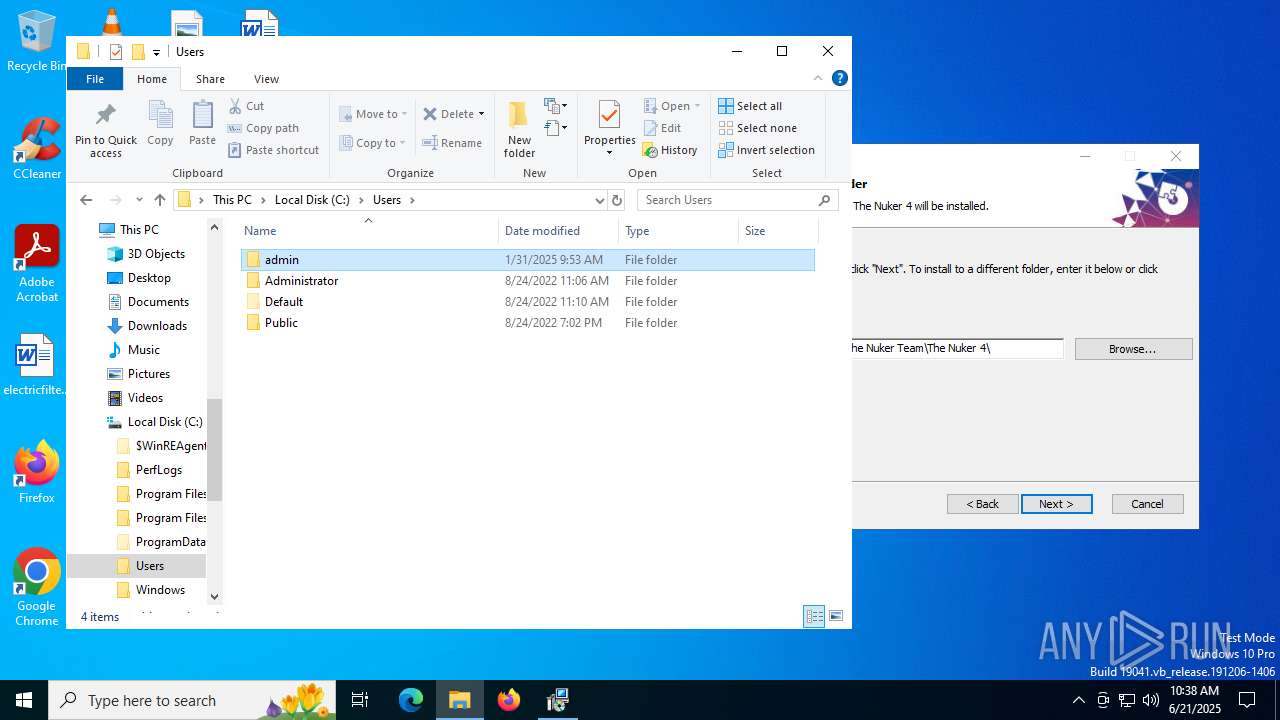
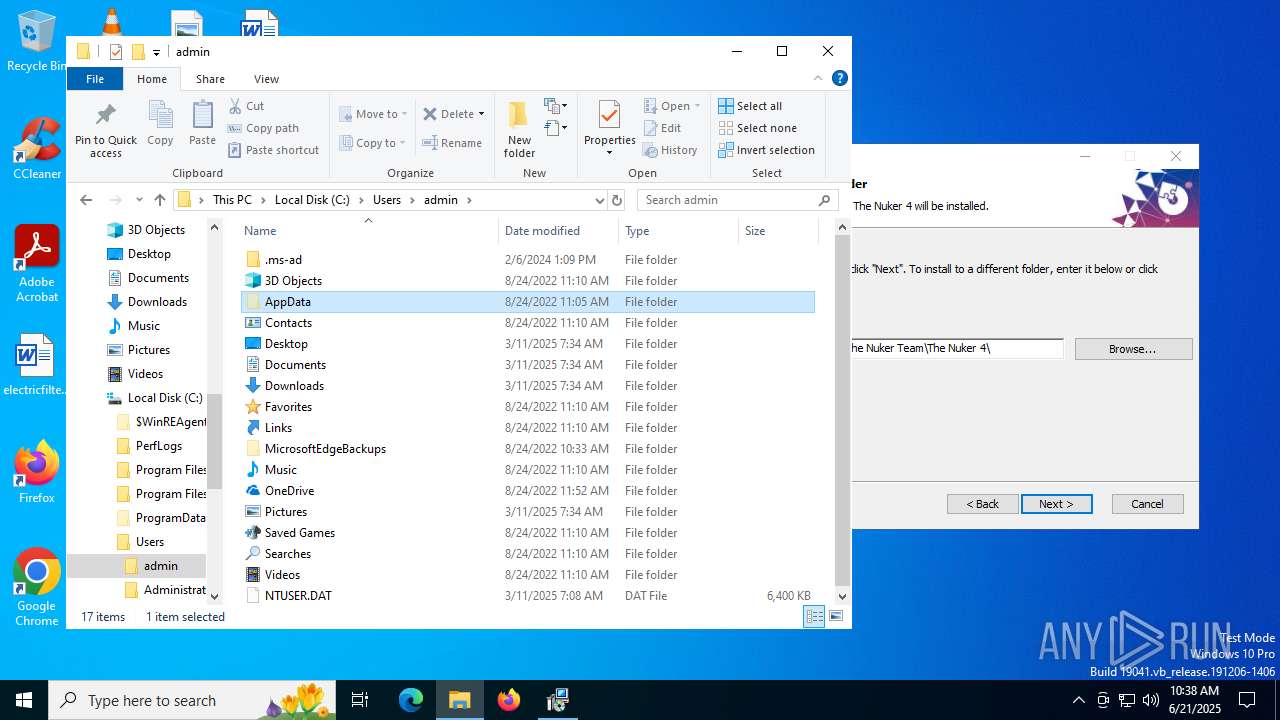
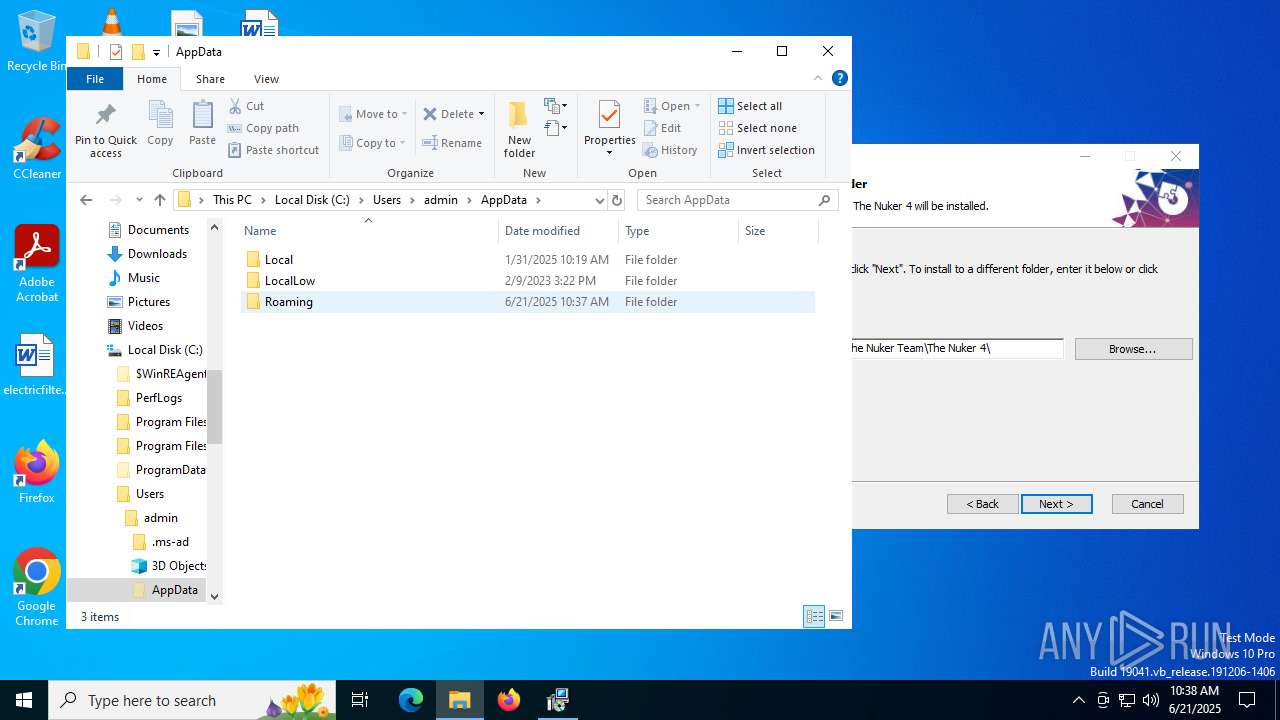
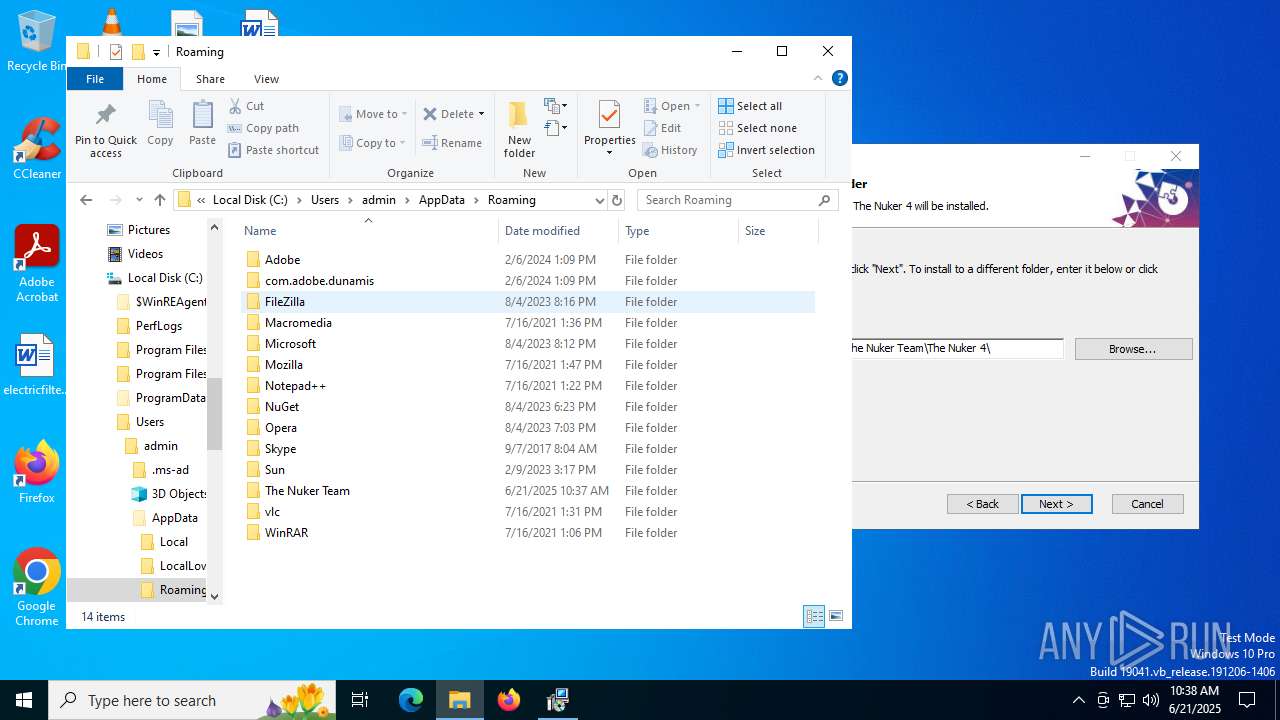
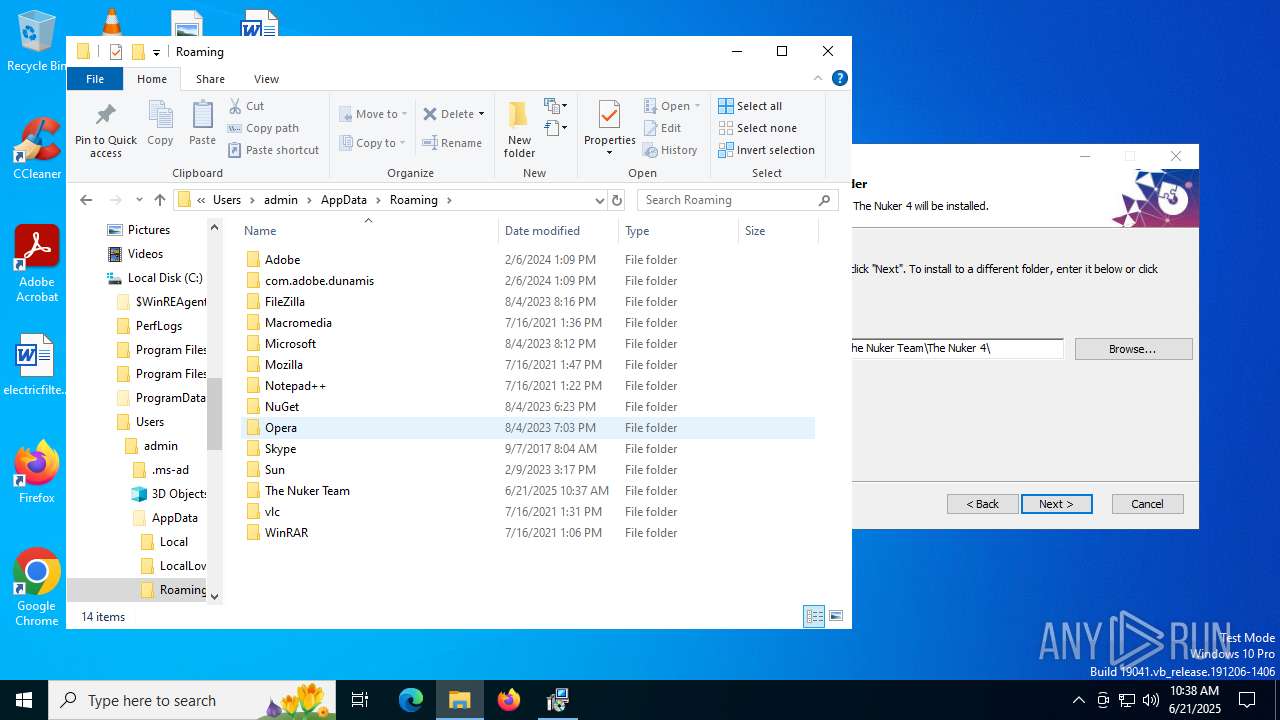
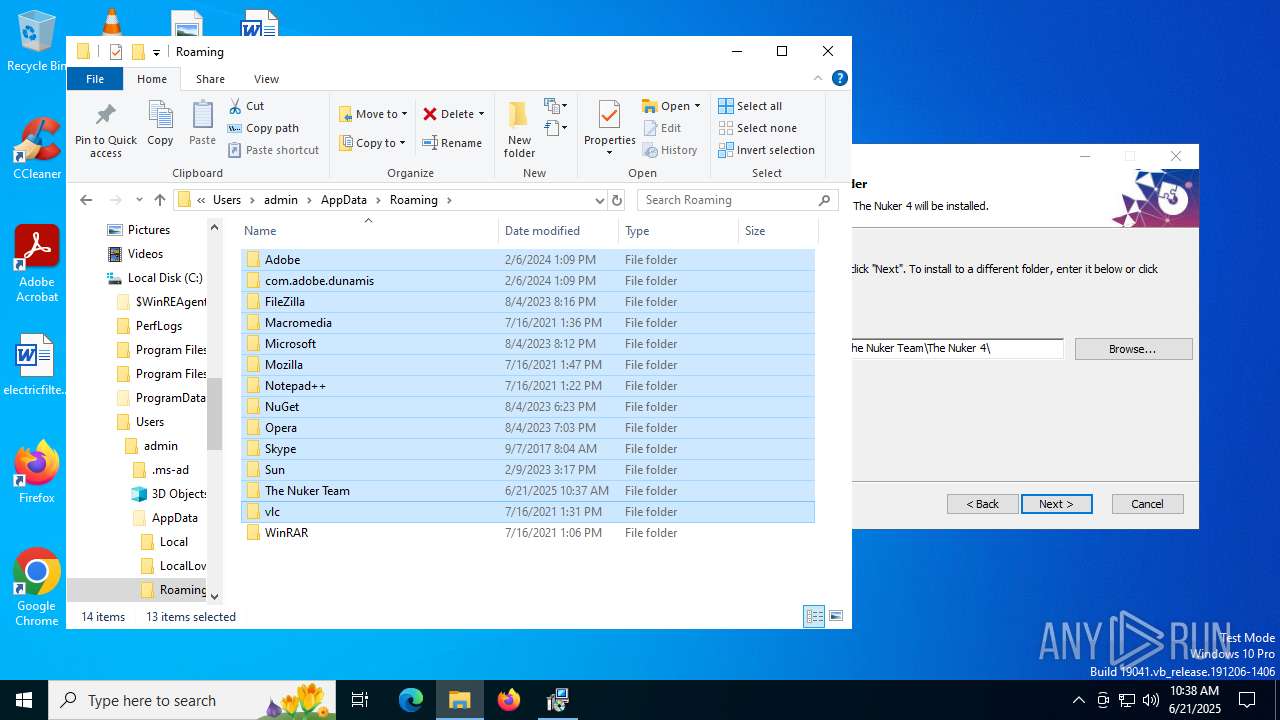
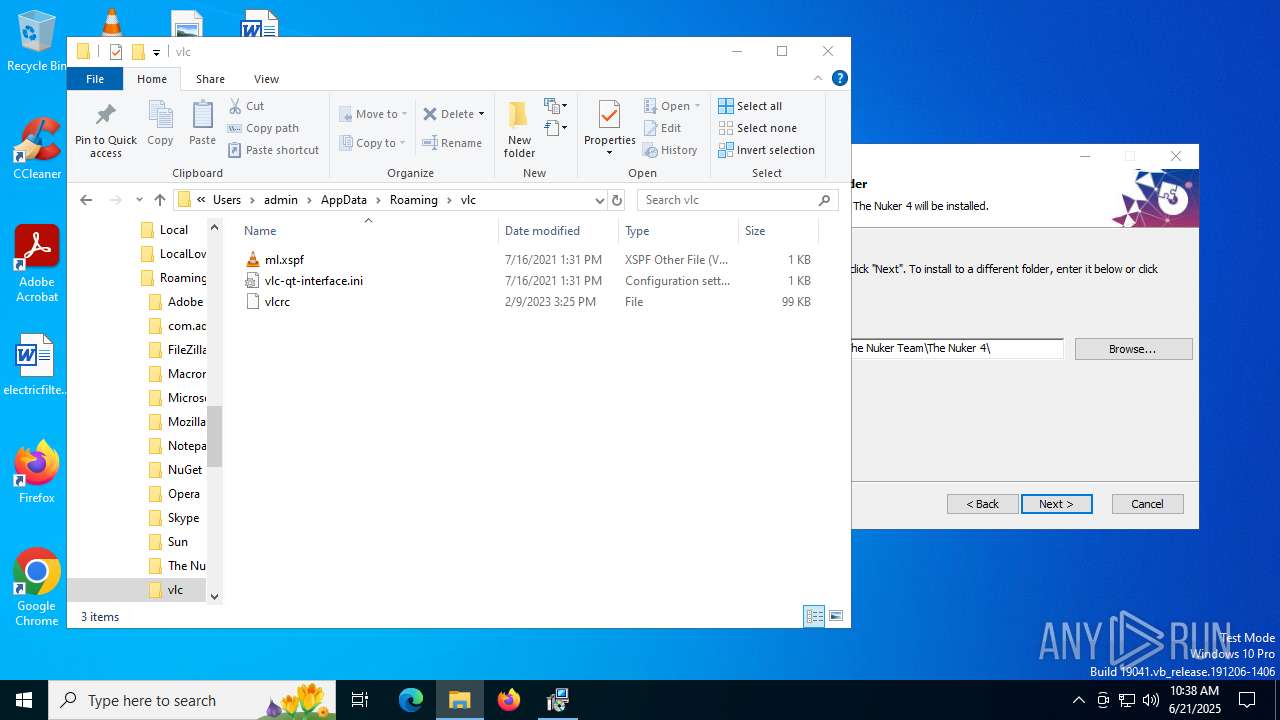
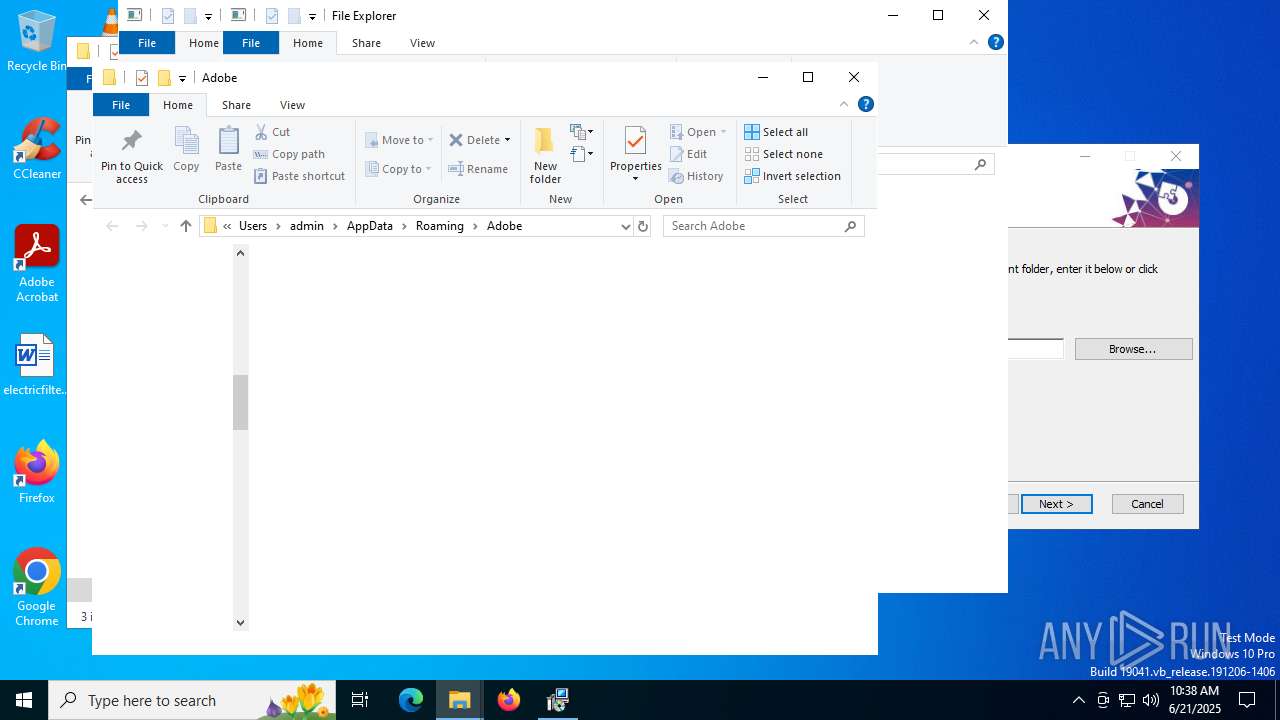
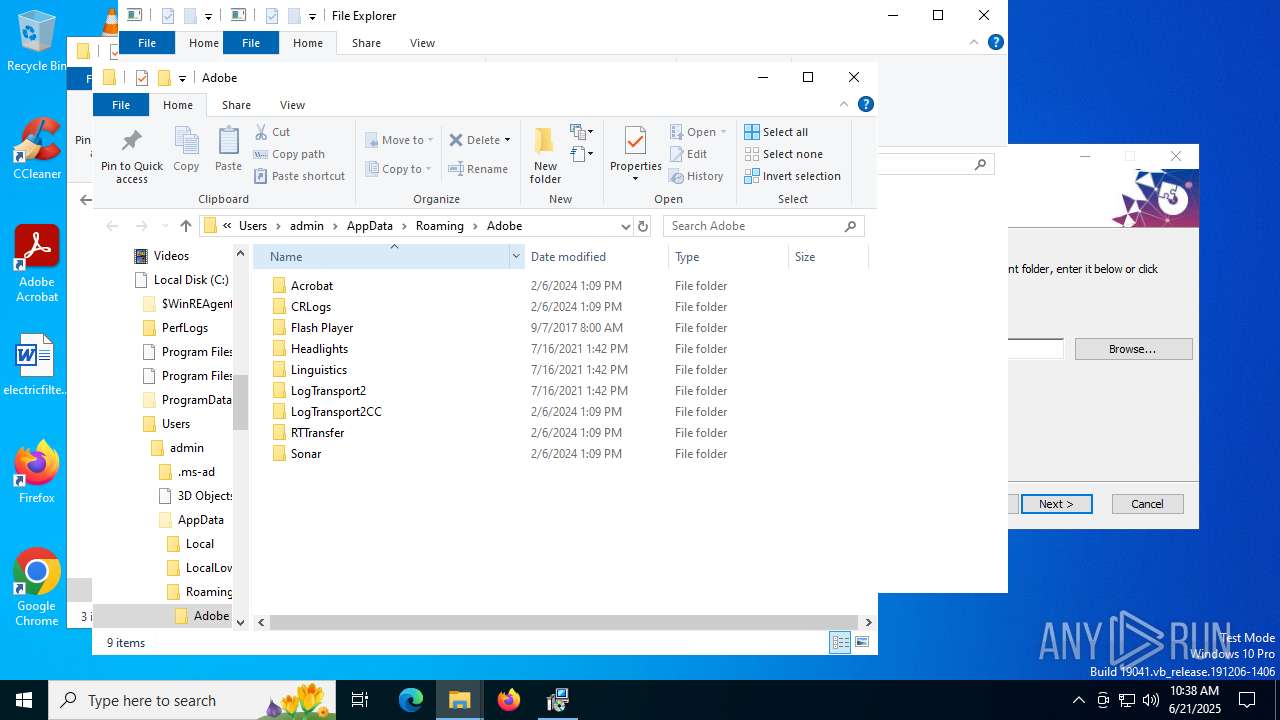
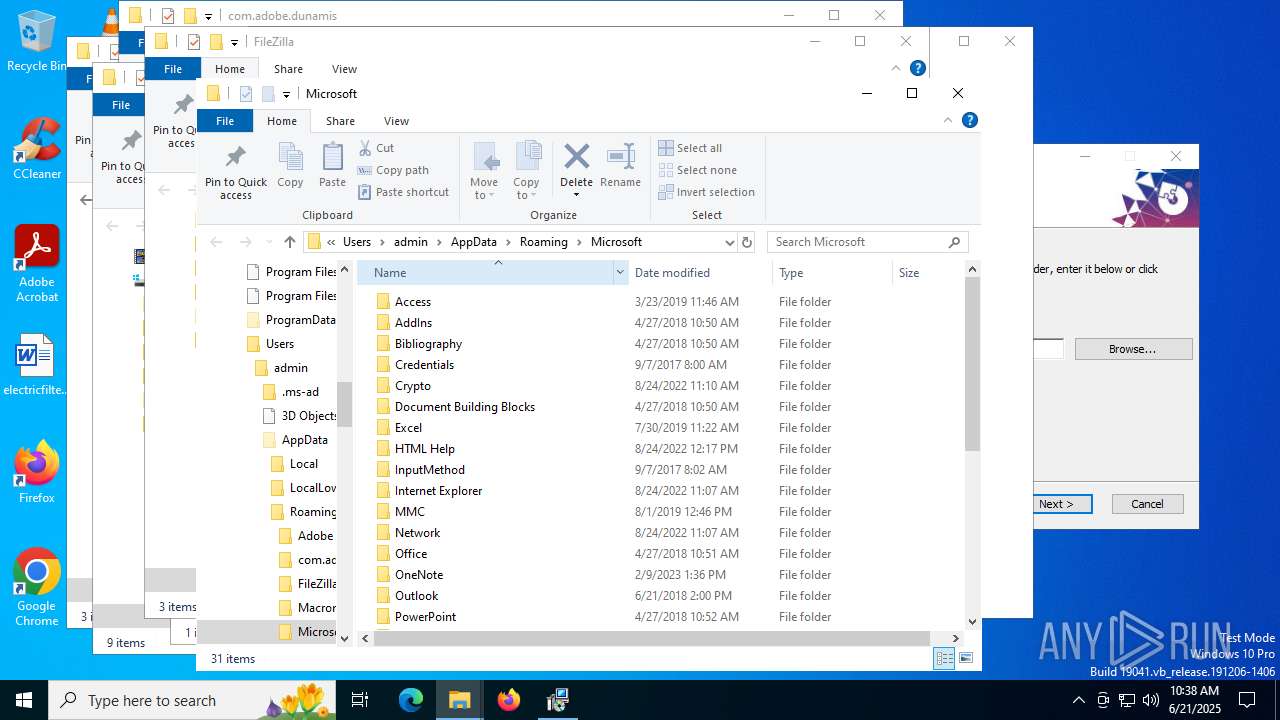
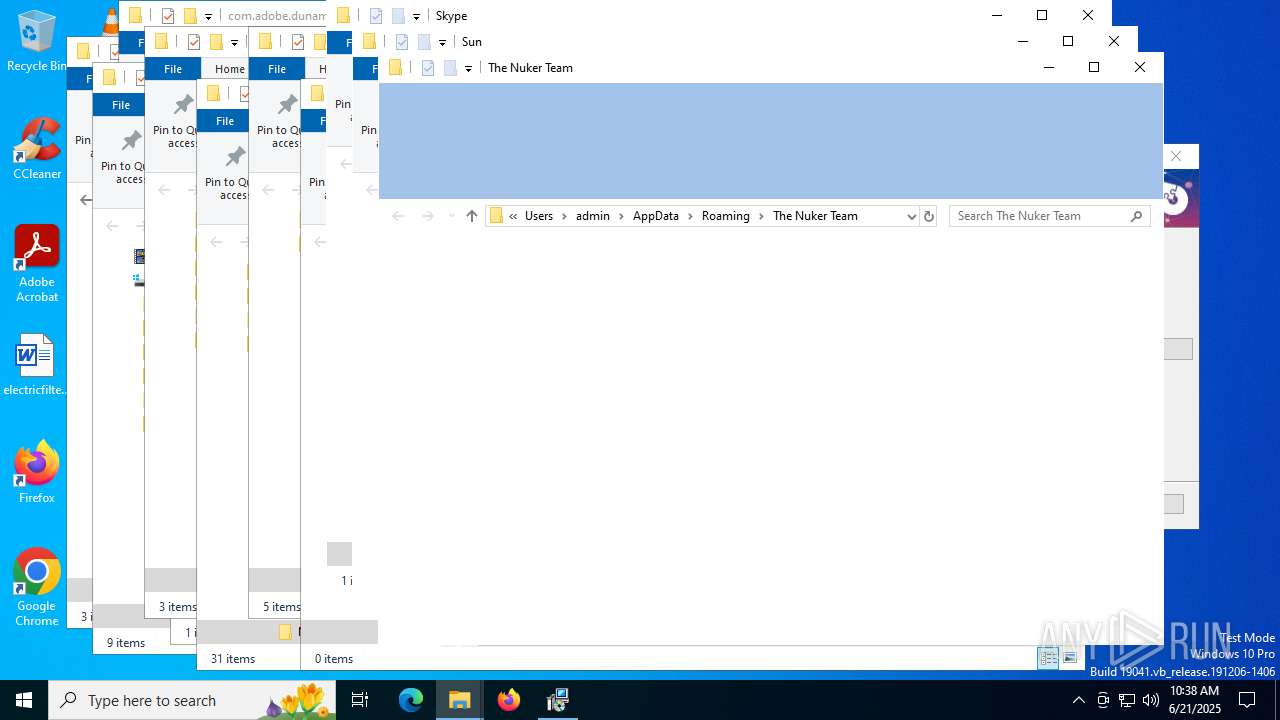
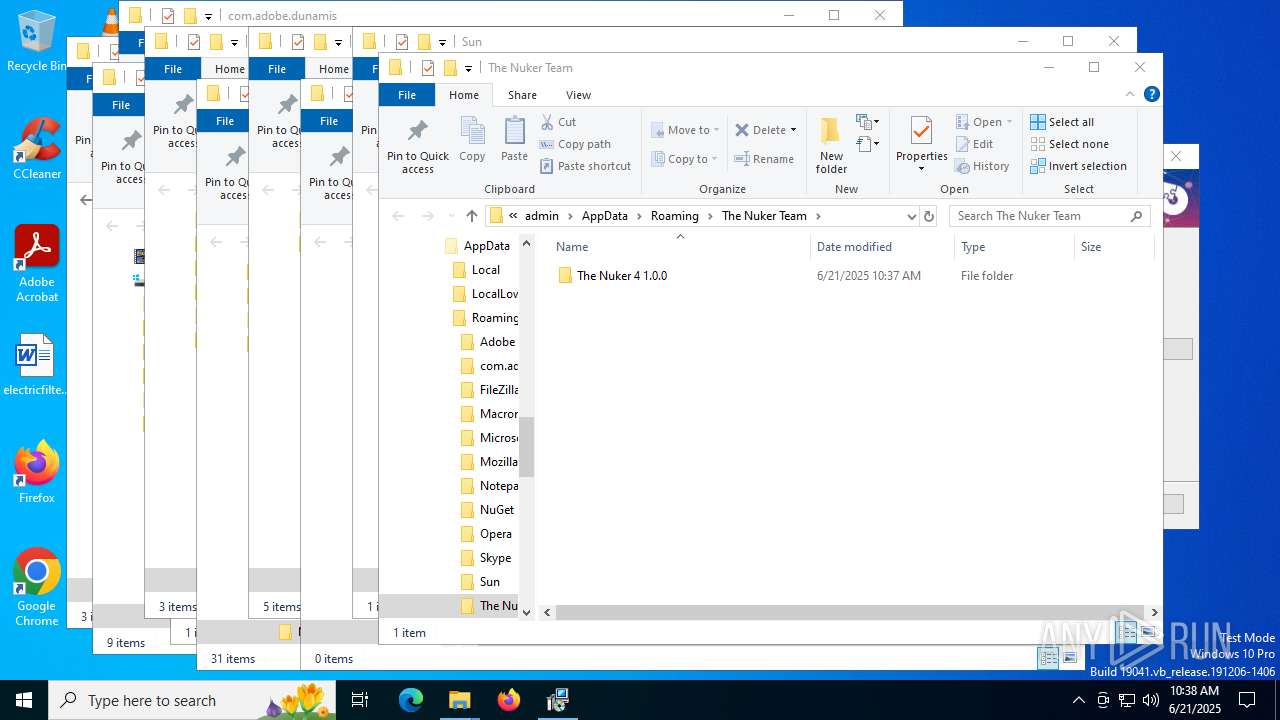
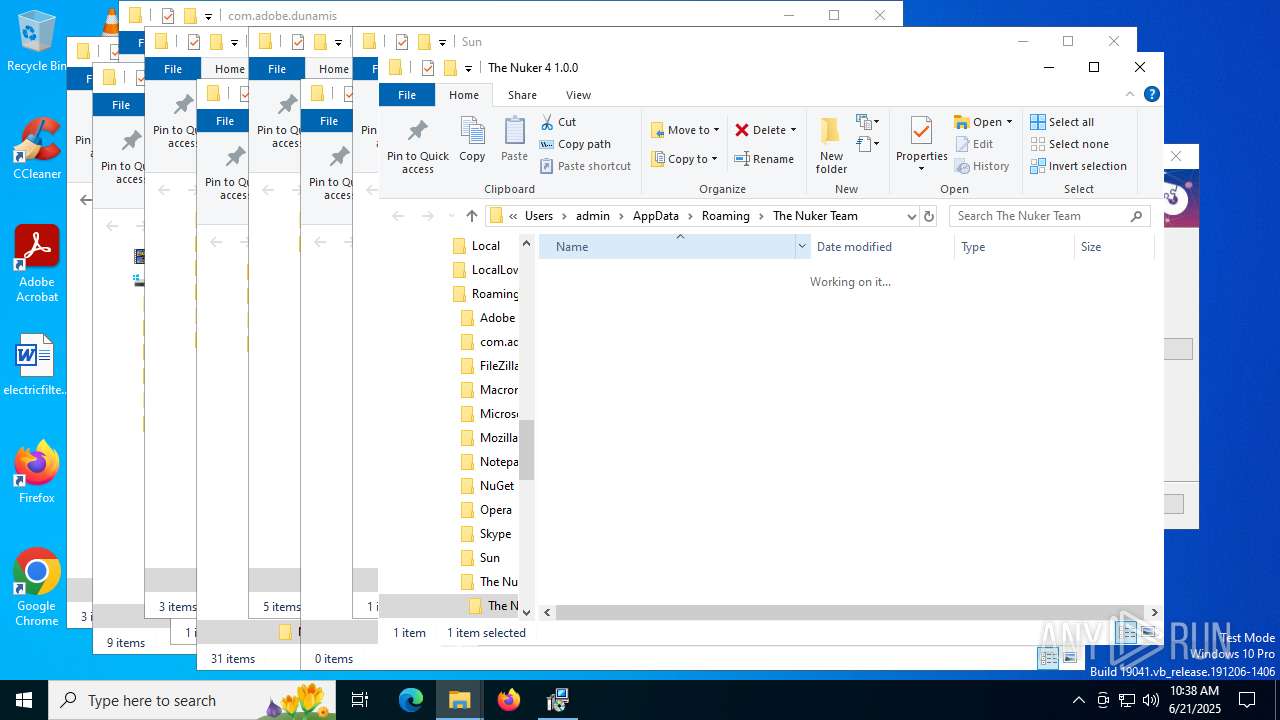
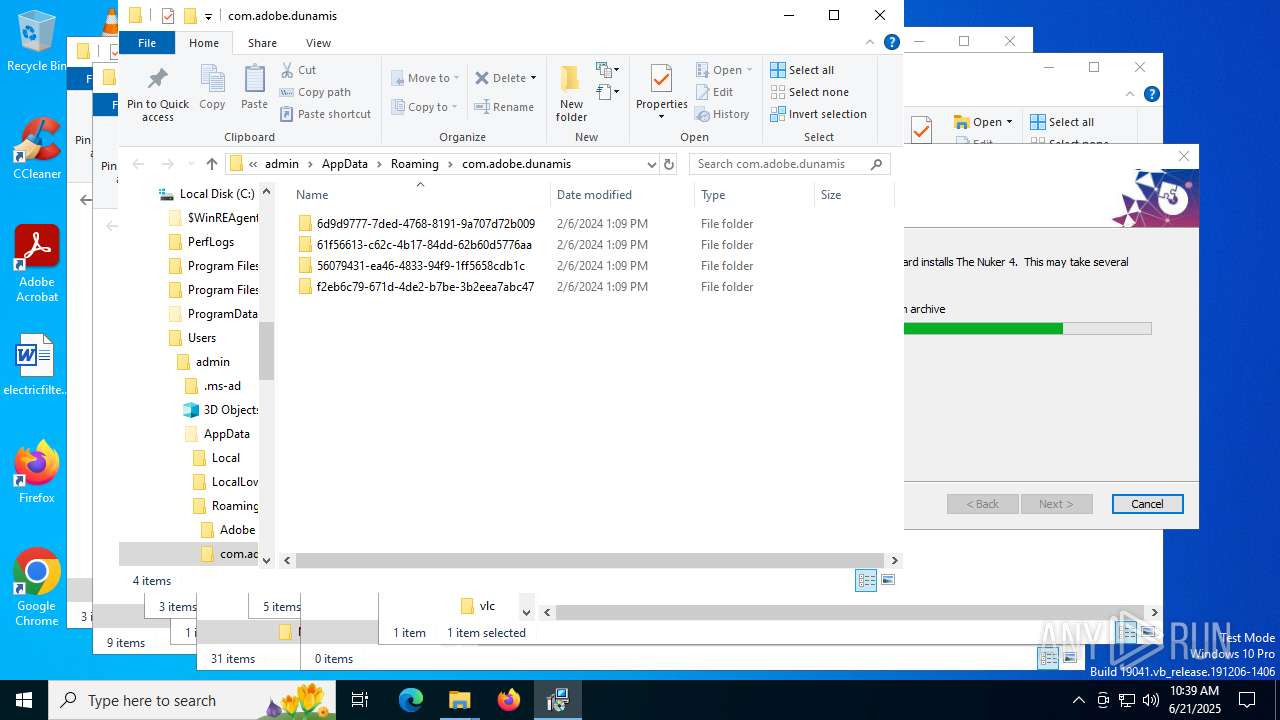
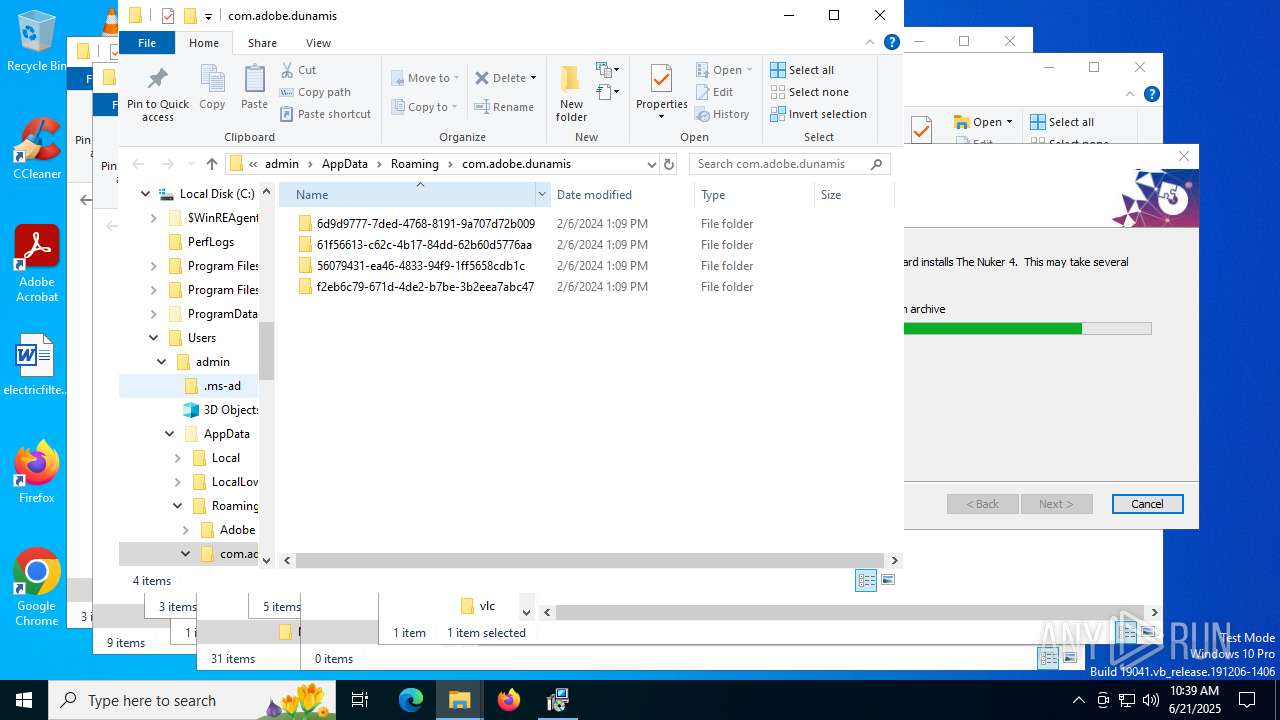
Creates files or folders in the user directory
- The_Nuker_4_Installer.exe (PID: 2580)
Reads Environment values
- The_Nuker_4_Installer.exe (PID: 2580)
- msiexec.exe (PID: 2192)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 5244)
- msiexec.exe (PID: 5692)
Create files in a temporary directory
- The_Nuker_4_Installer.exe (PID: 2580)
- msiexec.exe (PID: 4752)
- msiexec.exe (PID: 6360)
The sample compiled with english language support
- The_Nuker_4_Installer.exe (PID: 2580)
- msiexec.exe (PID: 6656)
- msiexec.exe (PID: 4752)
- msiexec.exe (PID: 6104)
Checks supported languages
- The_Nuker_4_Installer.exe (PID: 2580)
- msiexec.exe (PID: 6104)
- msiexec.exe (PID: 2192)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 5692)
- msiexec.exe (PID: 5244)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6656)
- msiexec.exe (PID: 4752)
- msiexec.exe (PID: 6104)
Manual execution by a user
- msiexec.exe (PID: 4752)
Manages system restore points
- SrTasks.exe (PID: 4324)
Checks proxy server information
- slui.exe (PID: 6748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:04 08:42:22+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.37 |
| CodeSize: | 2600448 |
| InitializedDataSize: | 1385984 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f0006 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
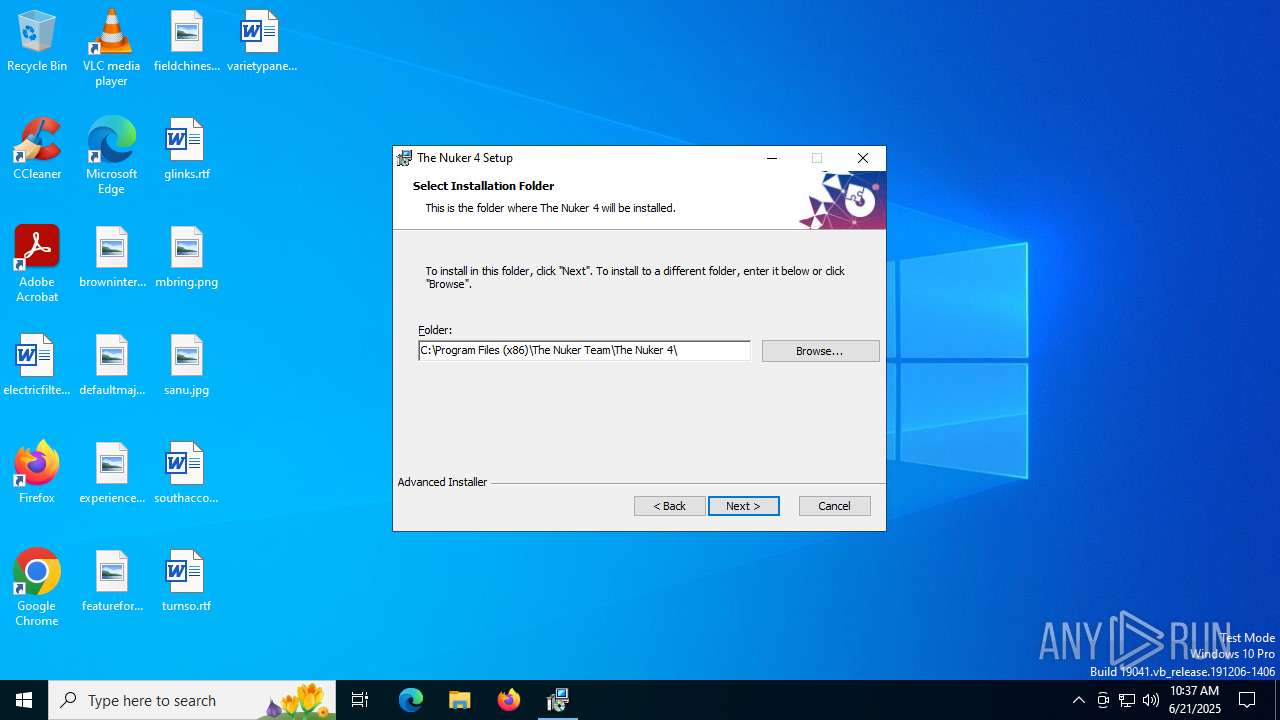
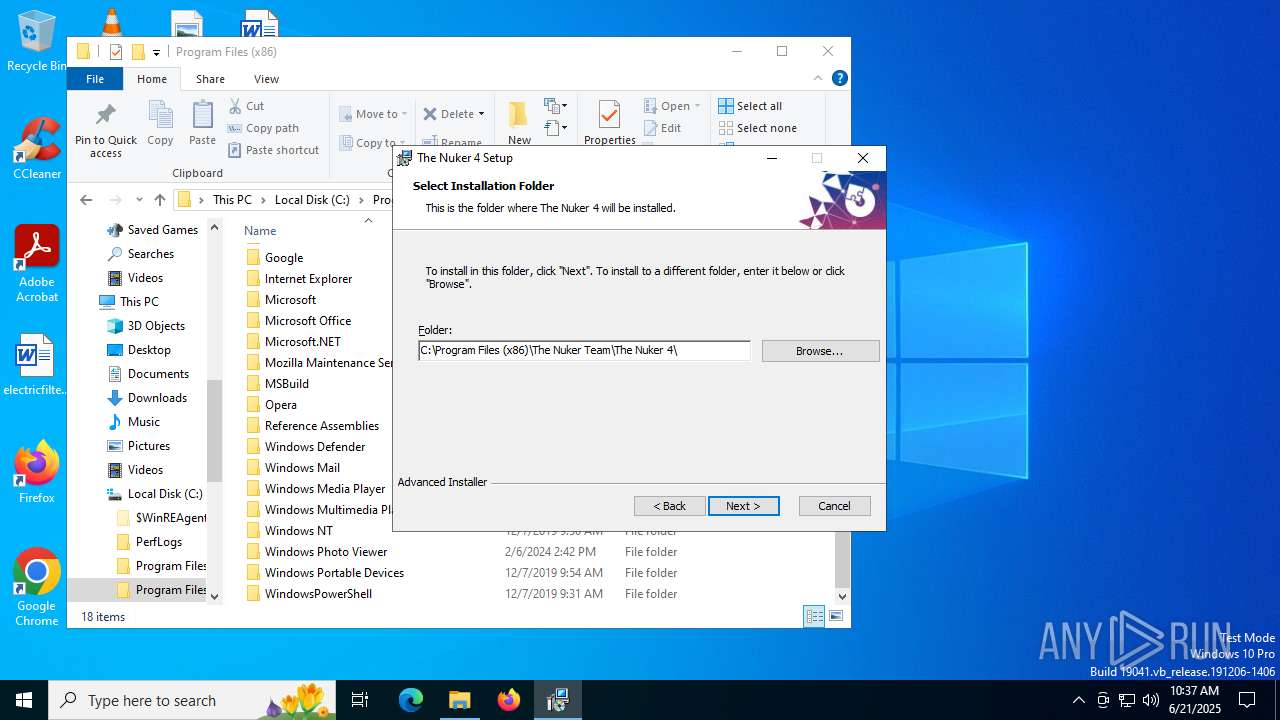
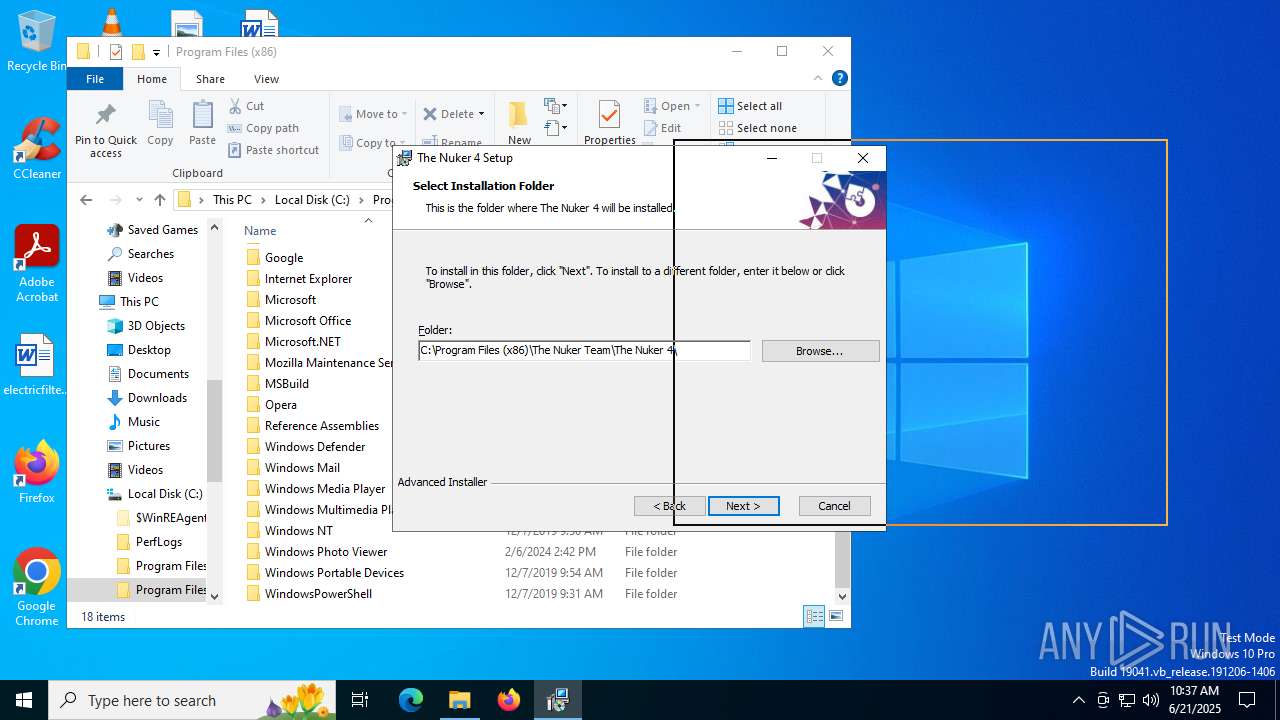
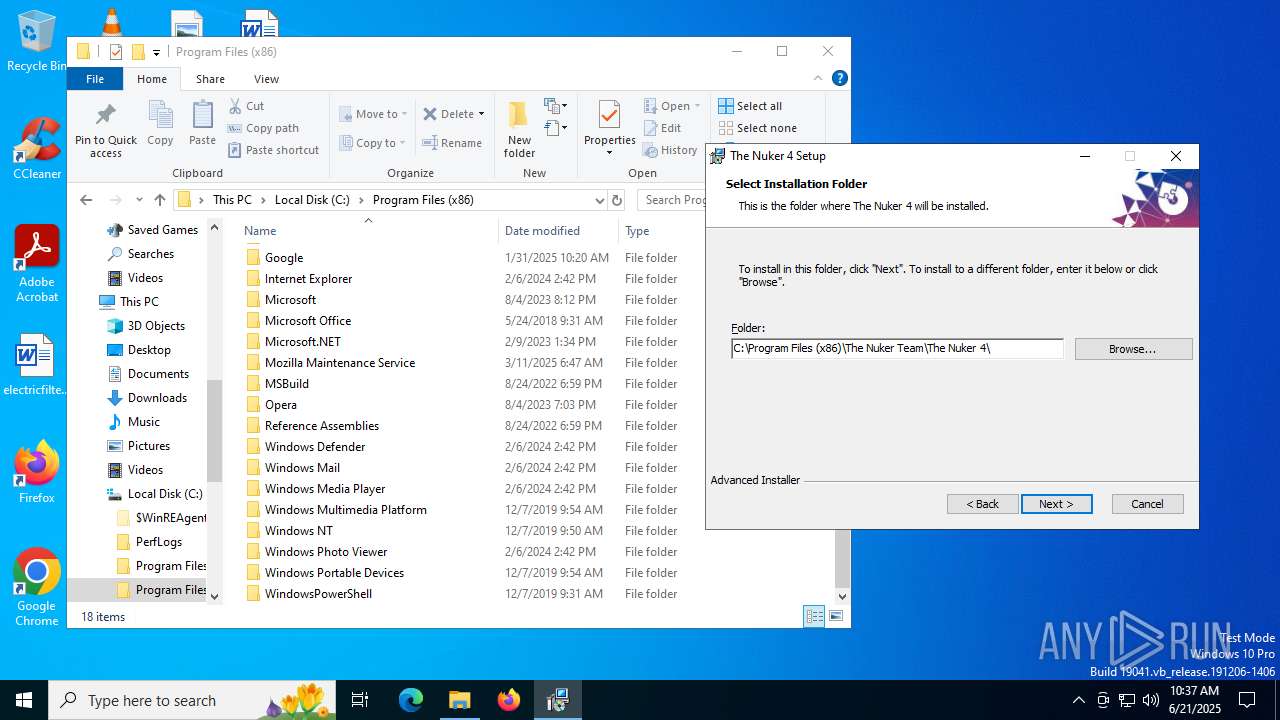
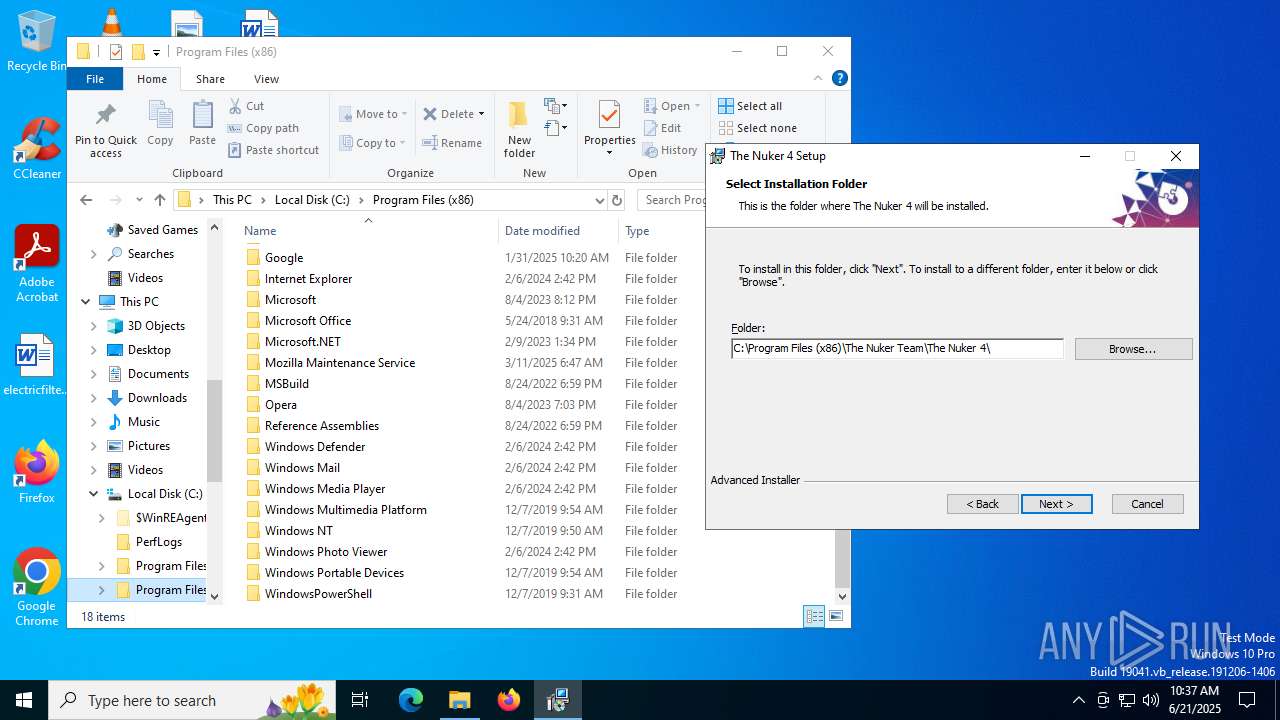
| CompanyName: | The Nuker Team |
| FileDescription: | The Nuker 4 Installer |
| FileVersion: | 1.0.0 |
| InternalName: | The Nuker 4 Installer |
| LegalCopyright: | Copyright (C) 2023 The Nuker Team |
| OriginalFileName: | The Nuker 4 Installer.exe |
| ProductName: | The Nuker 4 |
| ProductVersion: | 1.0.0 |
Total processes
151
Monitored processes
13
Malicious processes
1
Suspicious processes
0
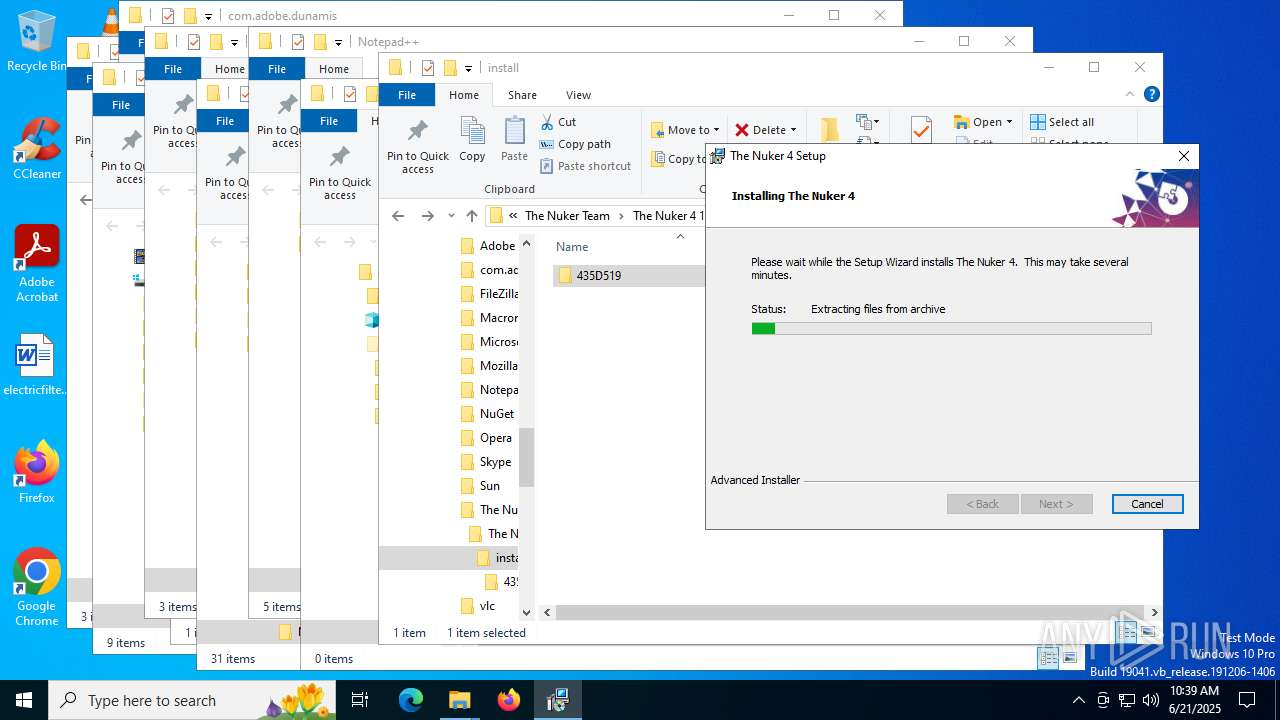
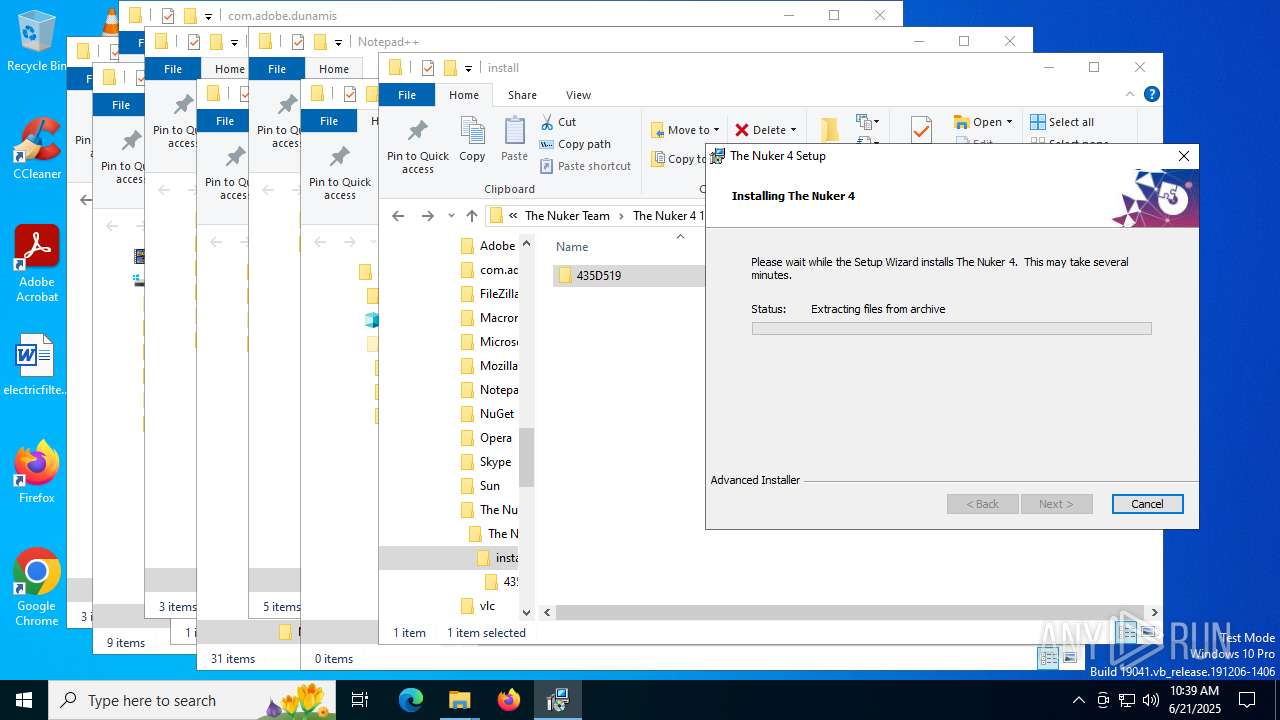
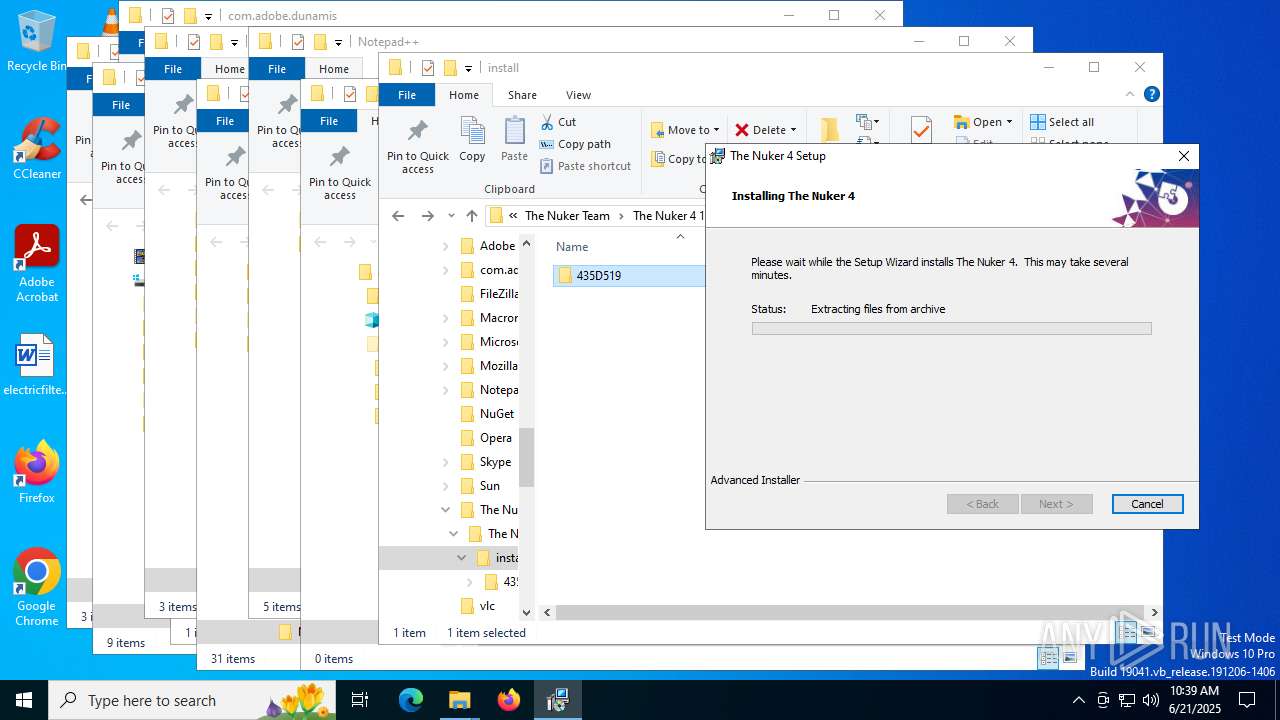
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\Windows\syswow64\MsiExec.exe -Embedding 7B27F5E8981178FD47ECD3E16E5D4C3F C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
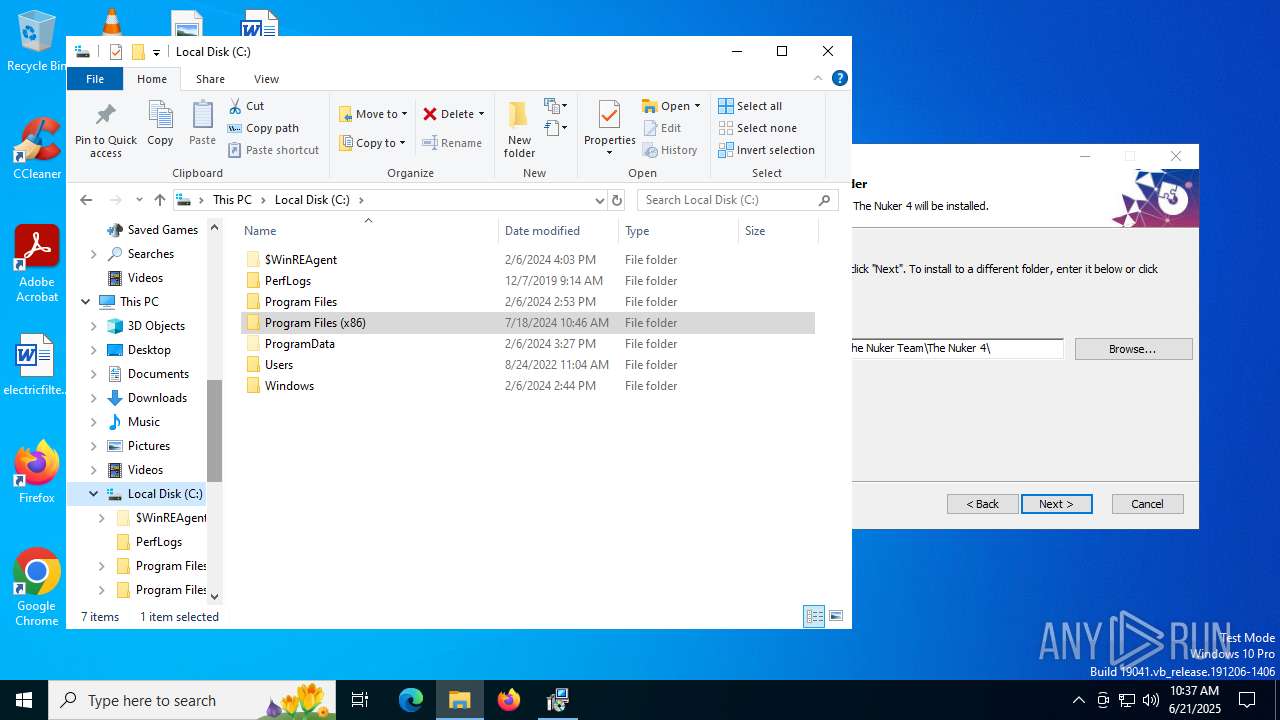
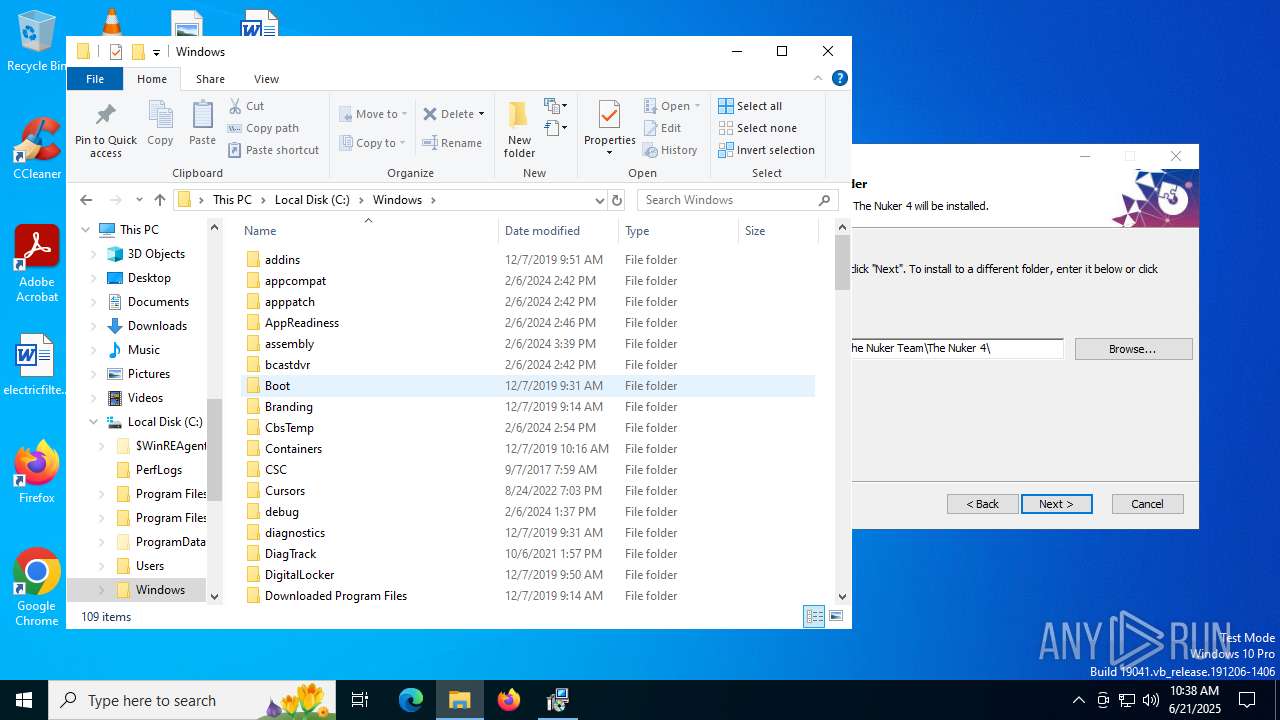
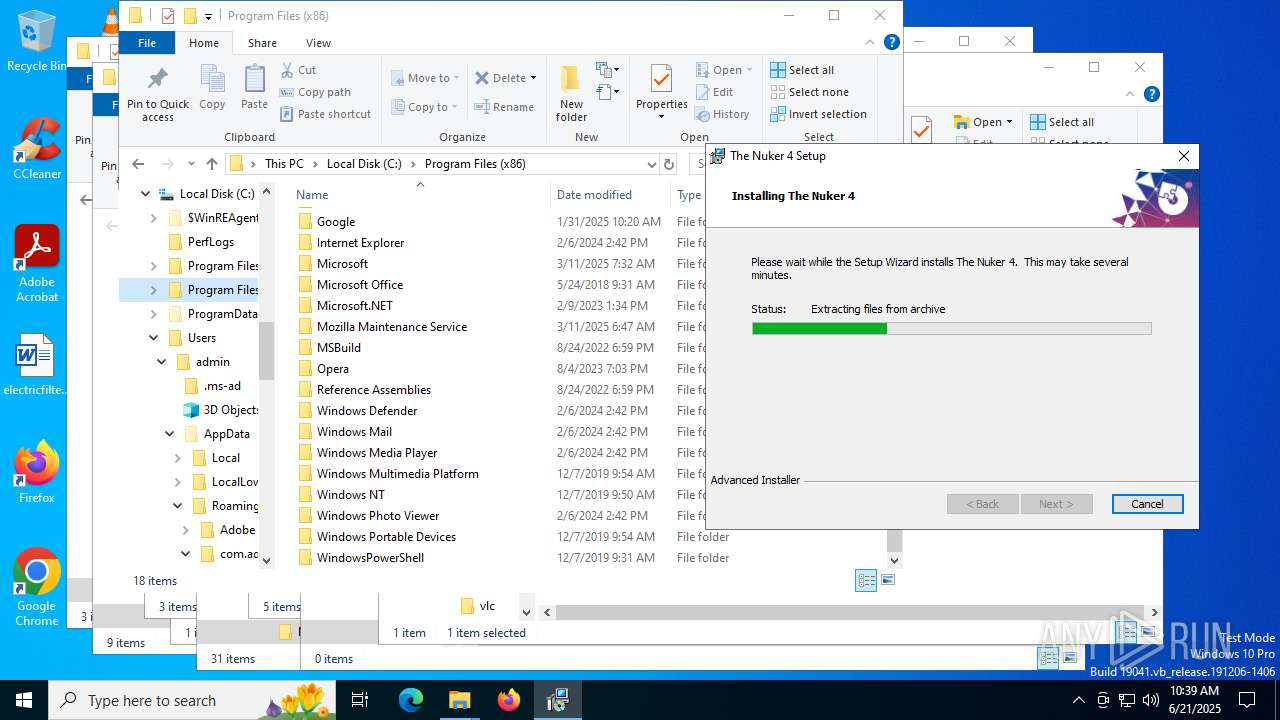
| 2580 | "C:\Users\admin\AppData\Local\Temp\The_Nuker_4_Installer.exe" | C:\Users\admin\AppData\Local\Temp\The_Nuker_4_Installer.exe | explorer.exe | ||||||||||||
User: admin Company: The Nuker Team Integrity Level: MEDIUM Description: The Nuker 4 Installer Version: 1.0.0 Modules
| |||||||||||||||
| 3460 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4324 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
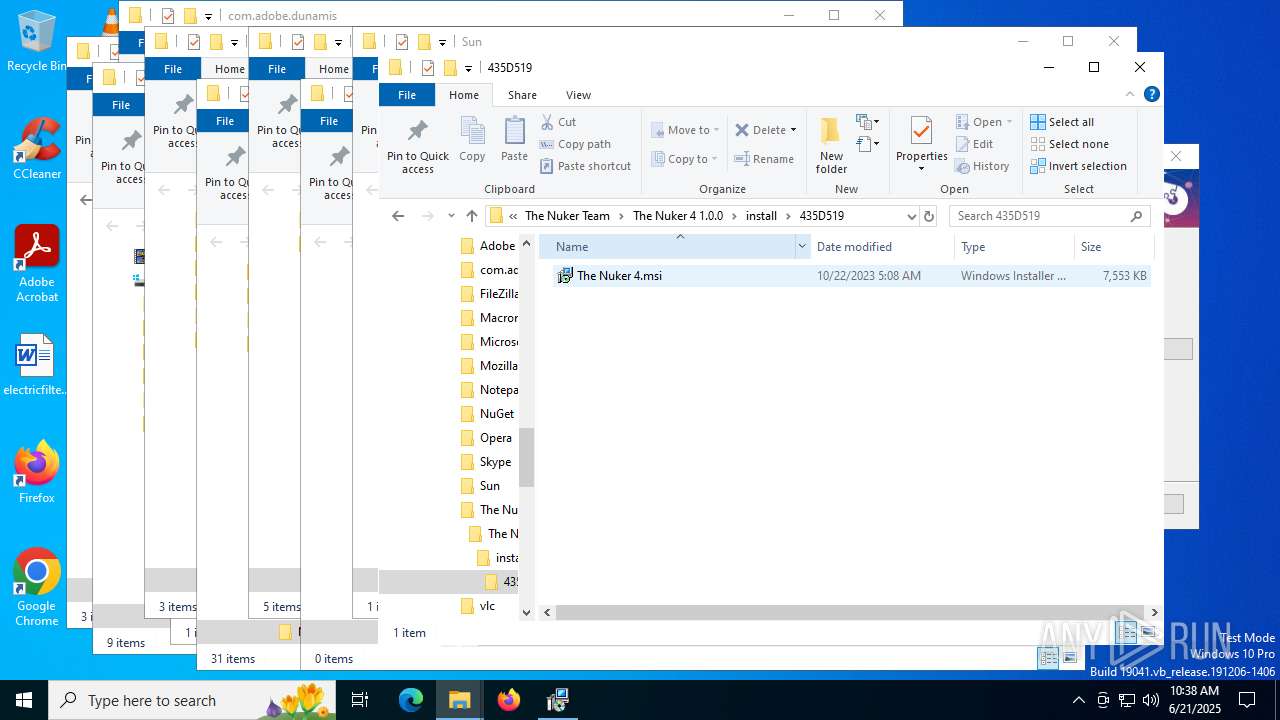
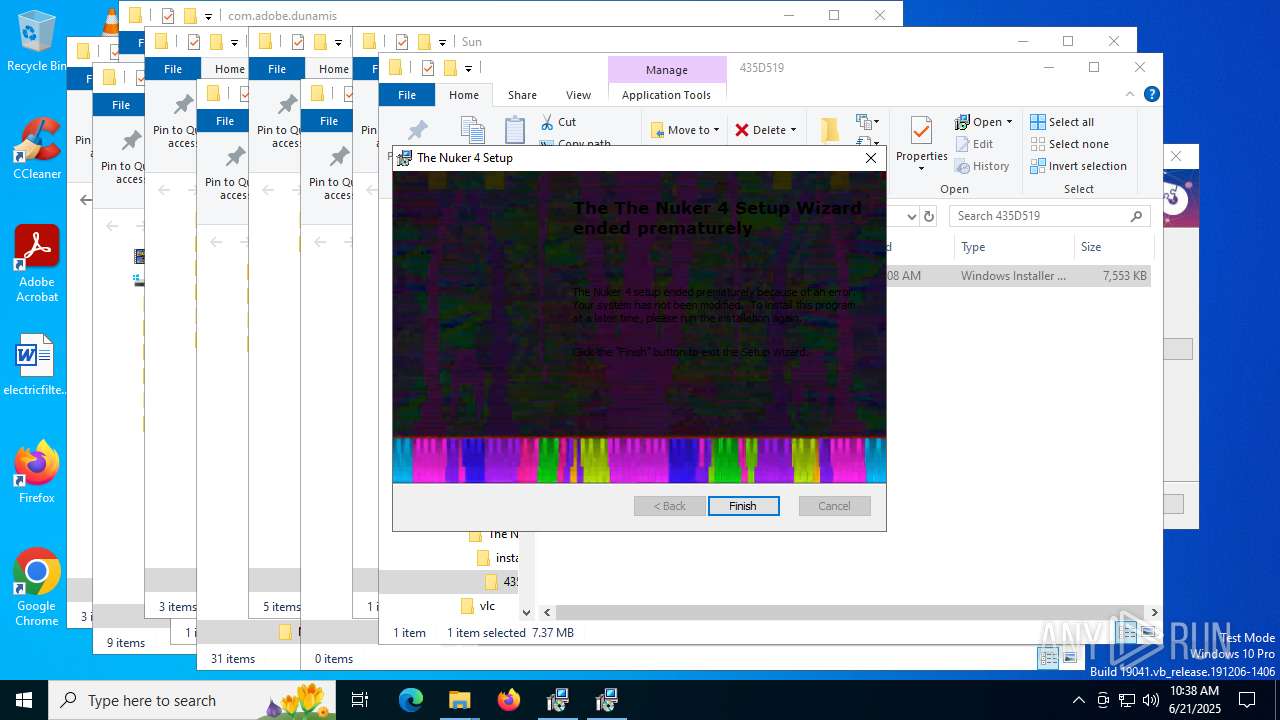
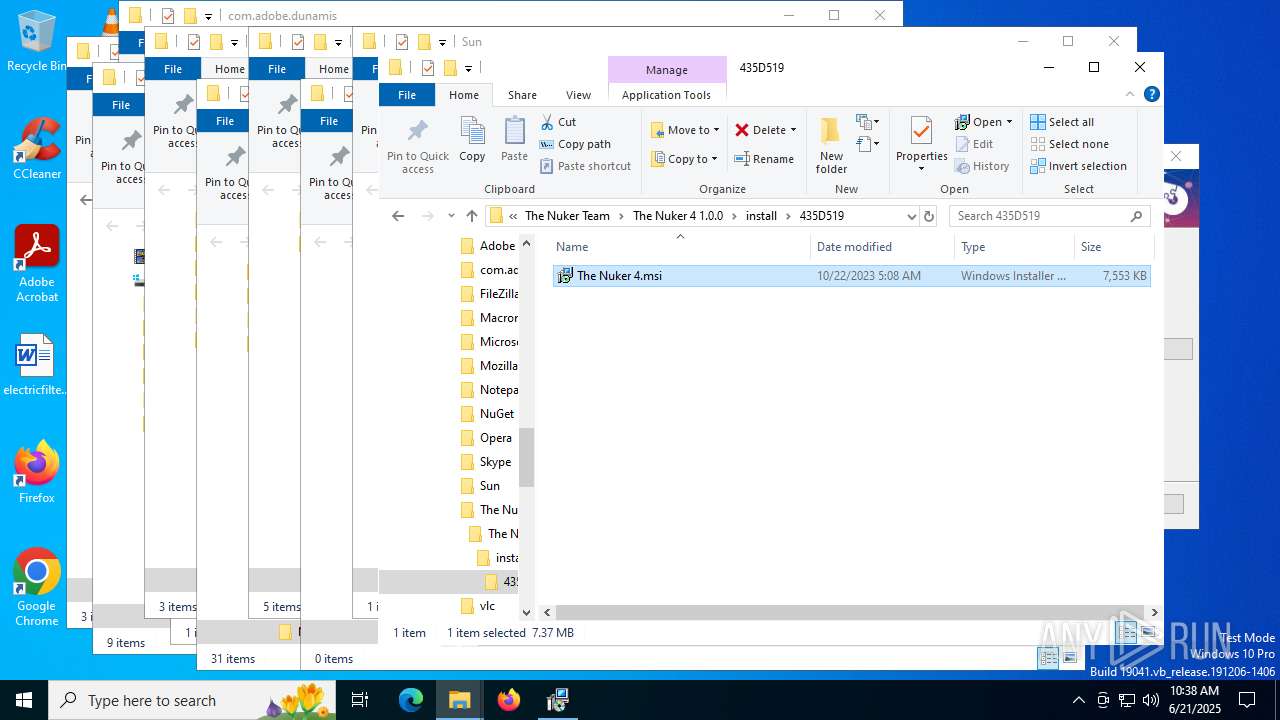
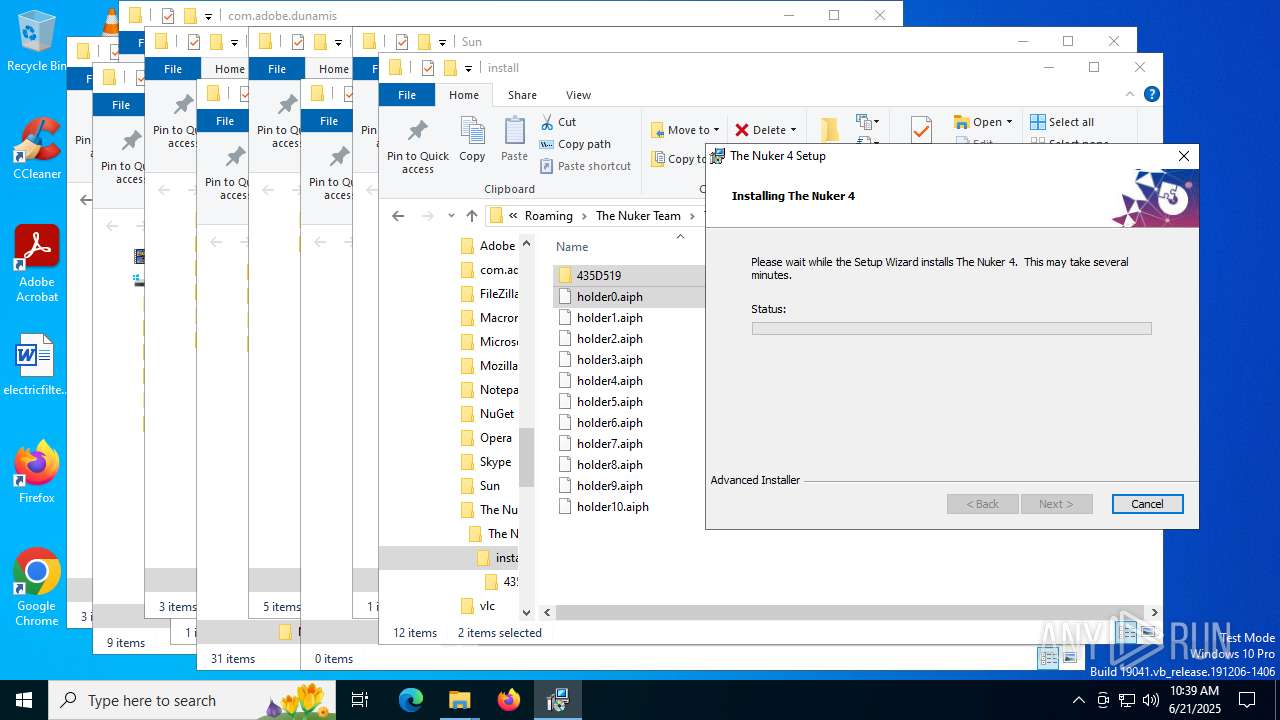
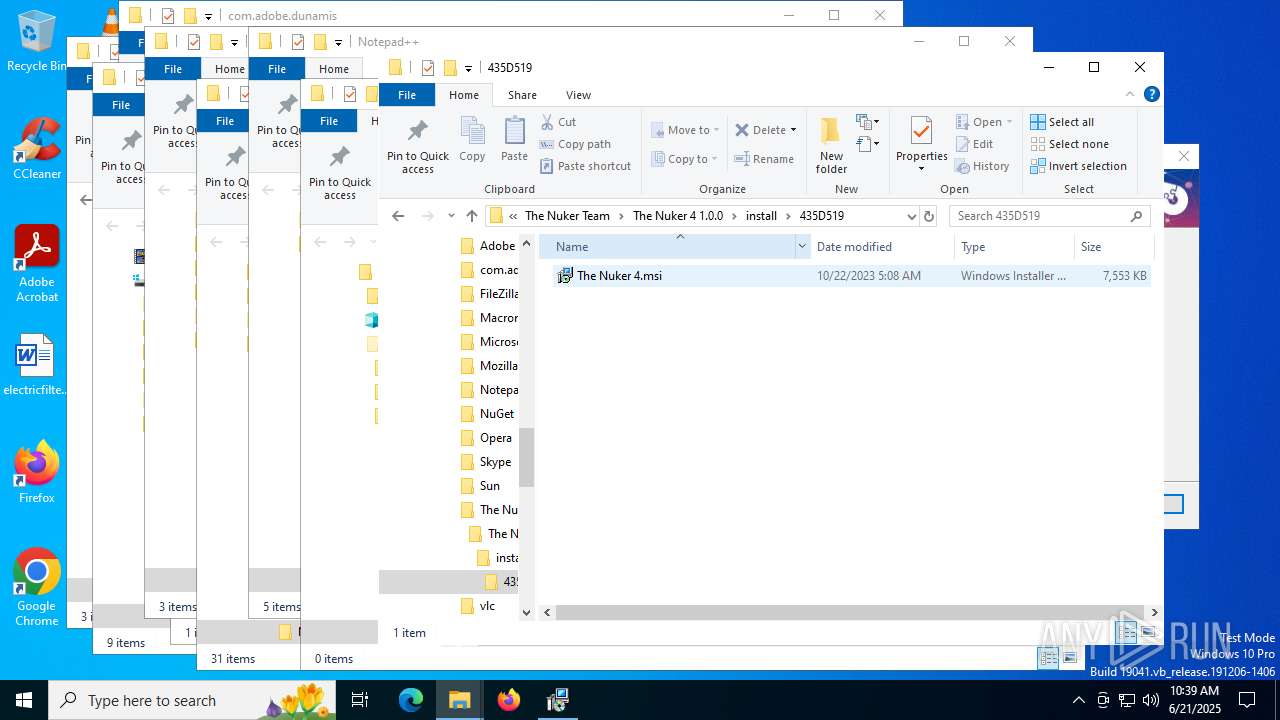
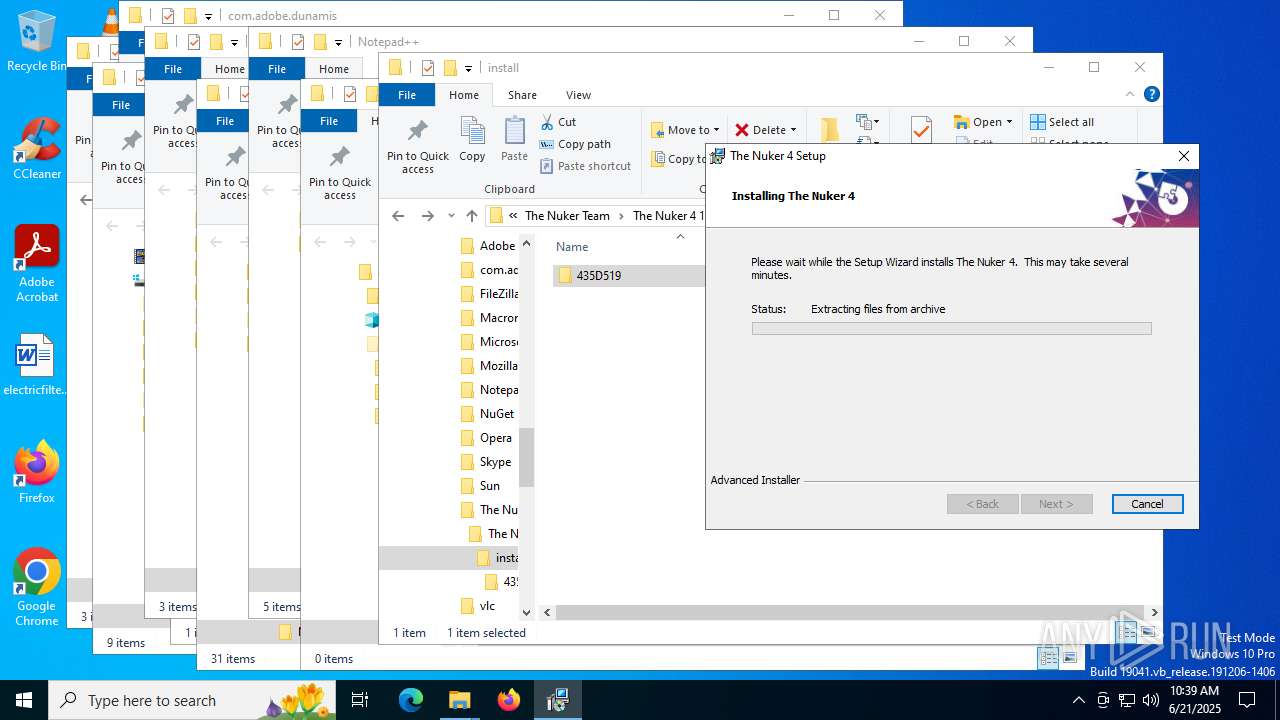
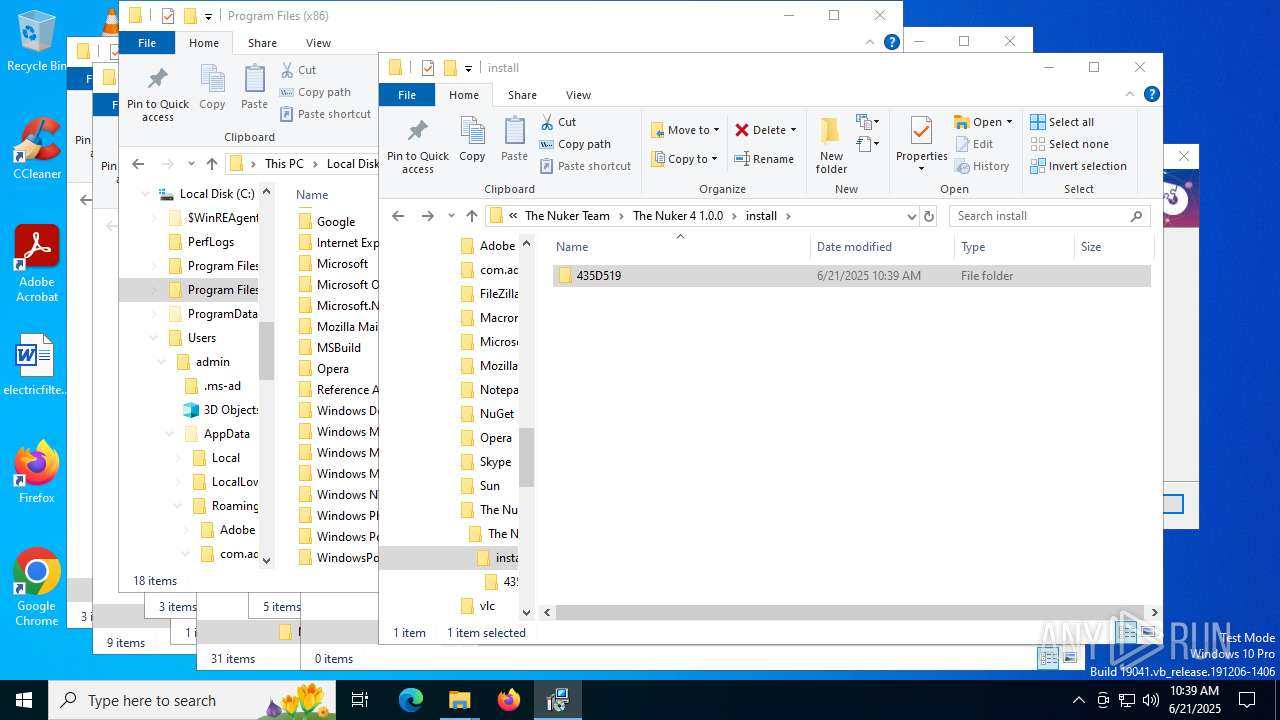
| 4752 | "C:\WINDOWS\System32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\The Nuker Team\The Nuker 4 1.0.0\install\435D519\The Nuker 4.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1603 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5244 | C:\Windows\syswow64\MsiExec.exe -Embedding 07BDB1AB39B5E076F33889460E010182 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5692 | C:\Windows\syswow64\MsiExec.exe -Embedding E656CA8CD6F9E76FEC72E46A1D778173 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5716 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6104 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6360 | C:\Windows\syswow64\MsiExec.exe -Embedding ED68F633DE7134CA02EC6B4B9C1C8A9F C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 964
Read events
3 789
Write events
166
Delete events
9
Modification events
| (PID) Process: | (6104) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000BEE8AFB698E2DB01D817000008190000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6104) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000D3AFB4B698E2DB01D817000008190000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6104) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000F2E490B698E2DB01D817000008190000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6104) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000F2E490B698E2DB01D817000008190000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6104) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000BEE8AFB698E2DB01D817000008190000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6104) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000BEE8AFB698E2DB01D817000008190000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6104) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6104) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000003A2108B798E2DB01D817000008190000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7056) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000C97616B798E2DB01901B0000C4120000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7056) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000C97616B798E2DB01901B0000C0120000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
30
Suspicious files
2
Text files
1
Unknown types
0
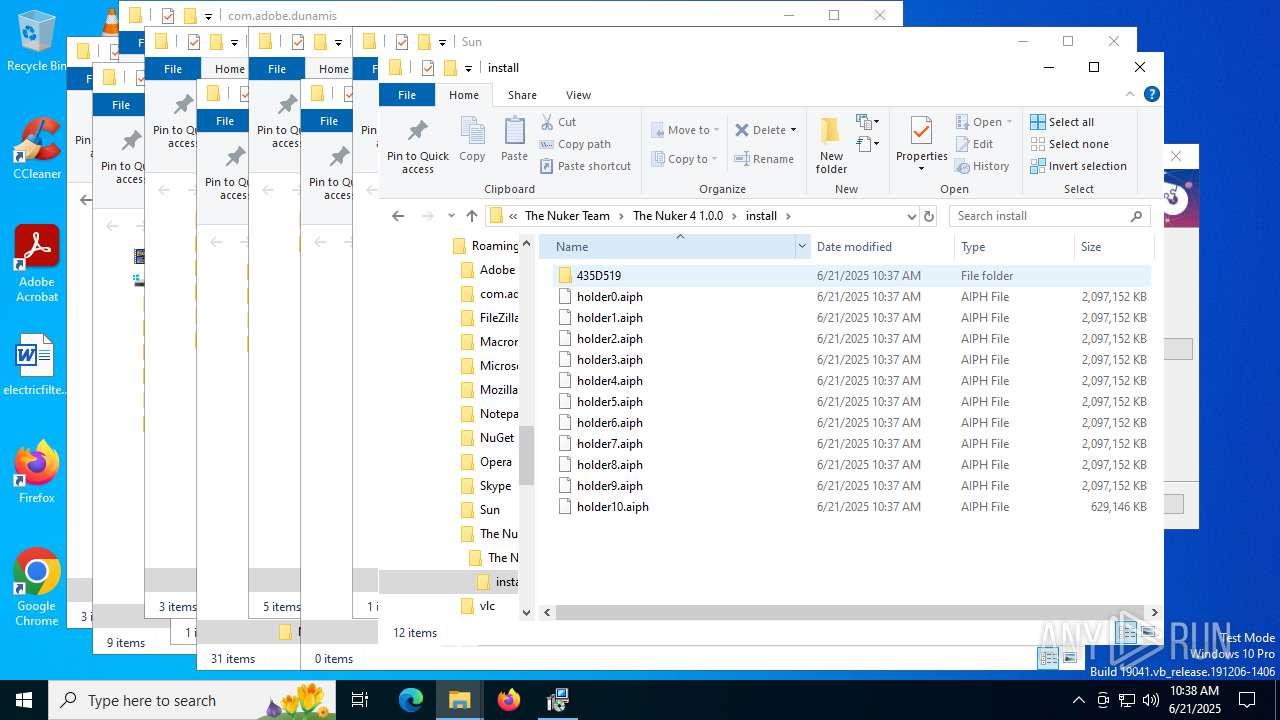
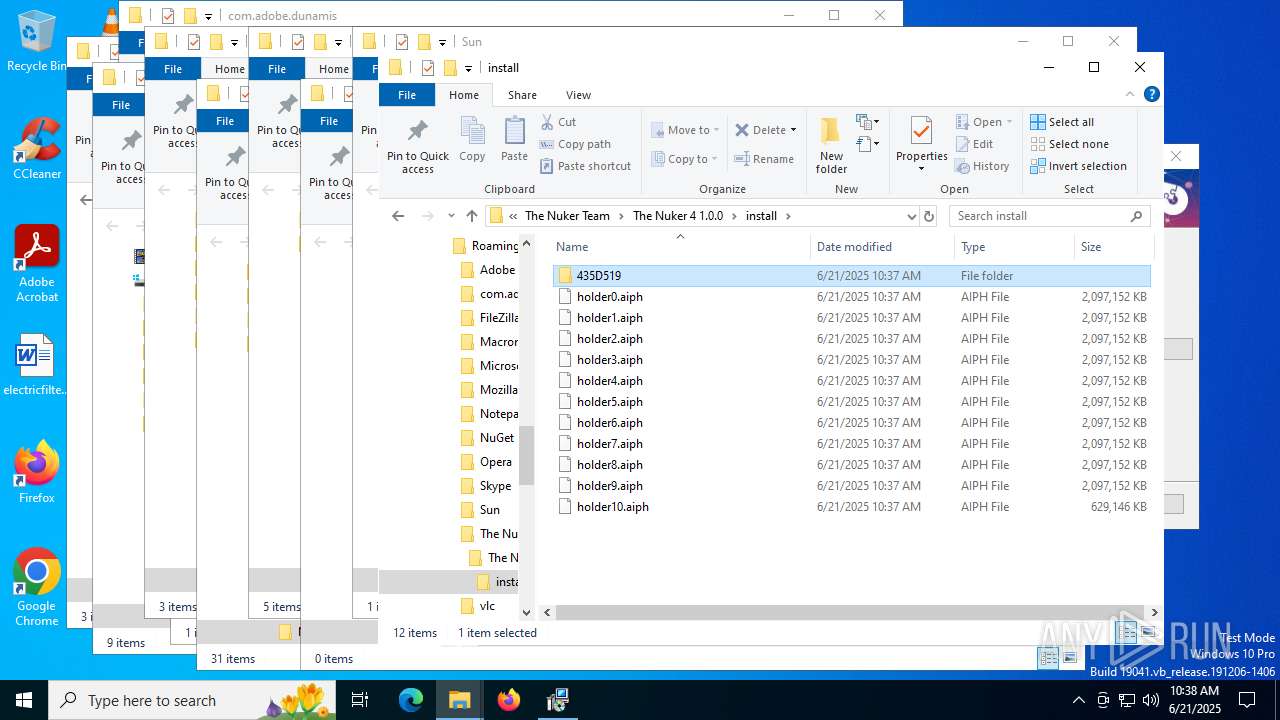
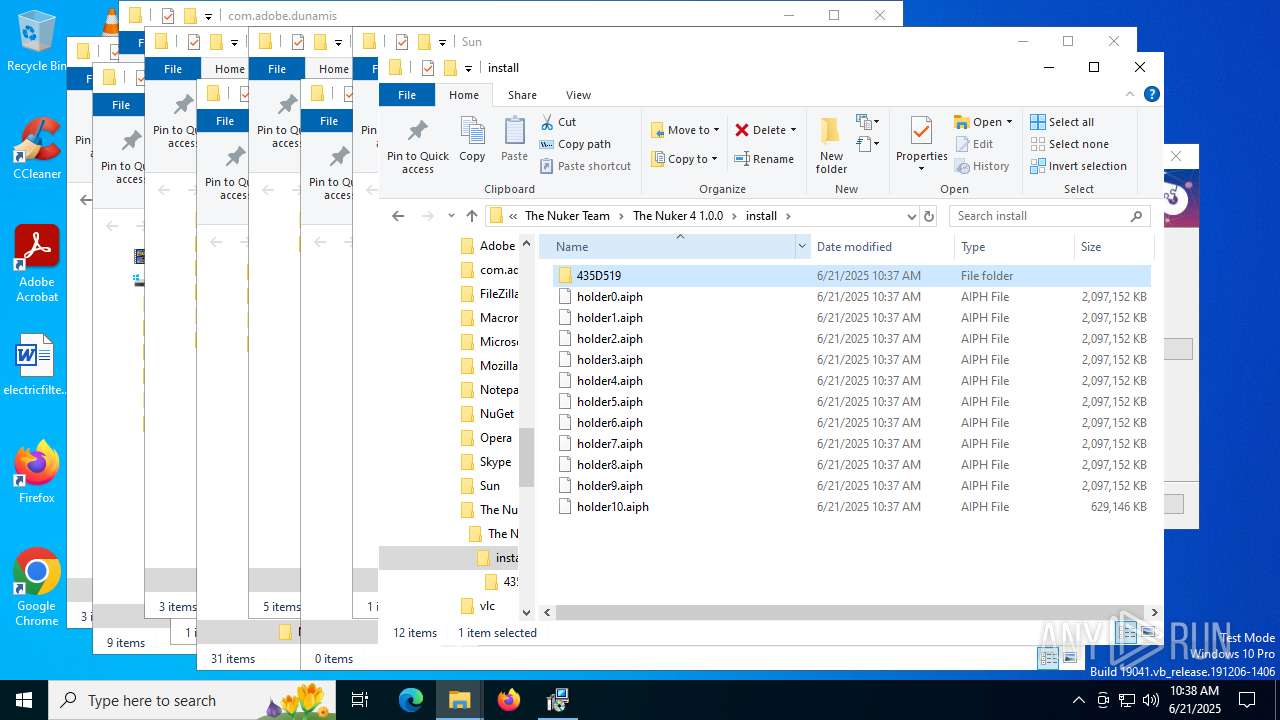
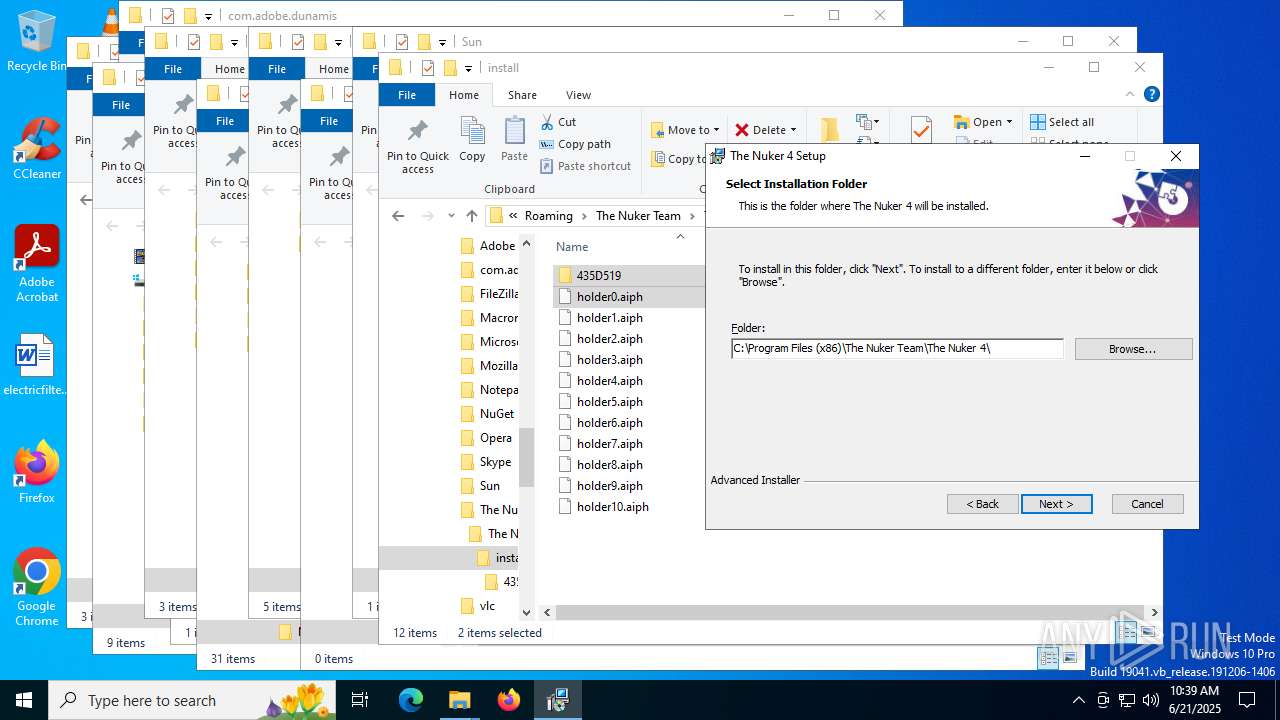
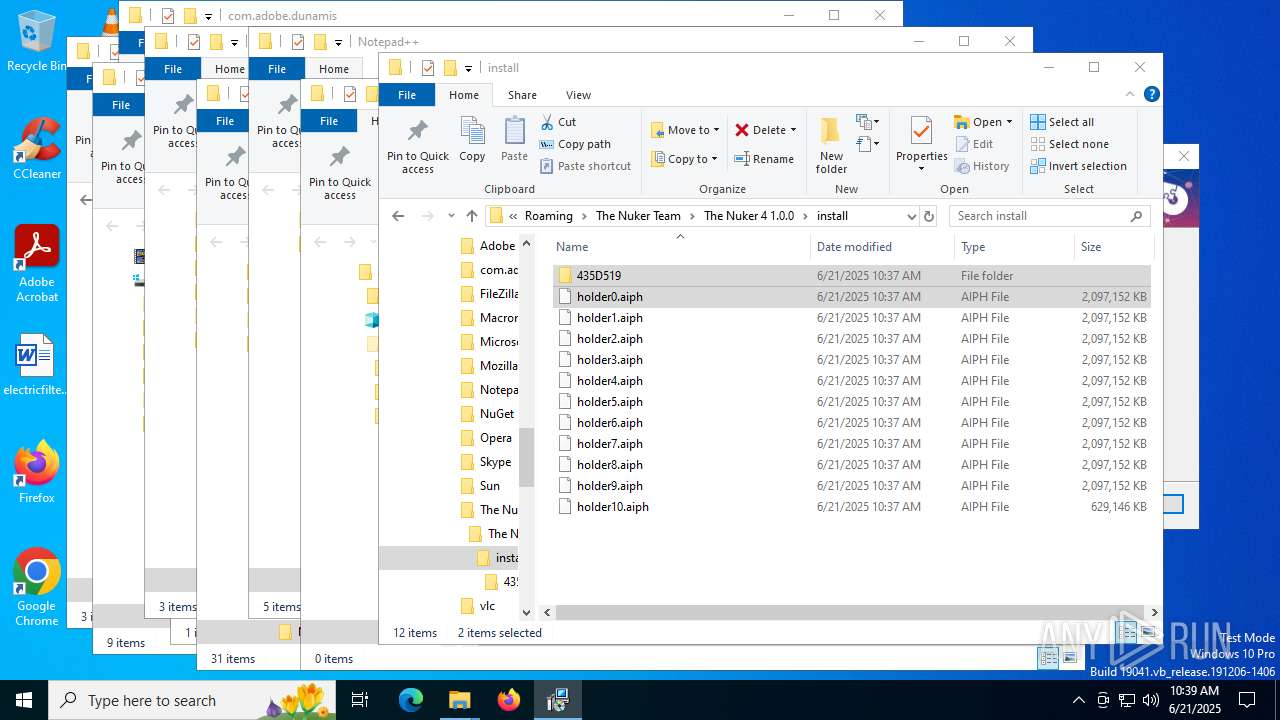
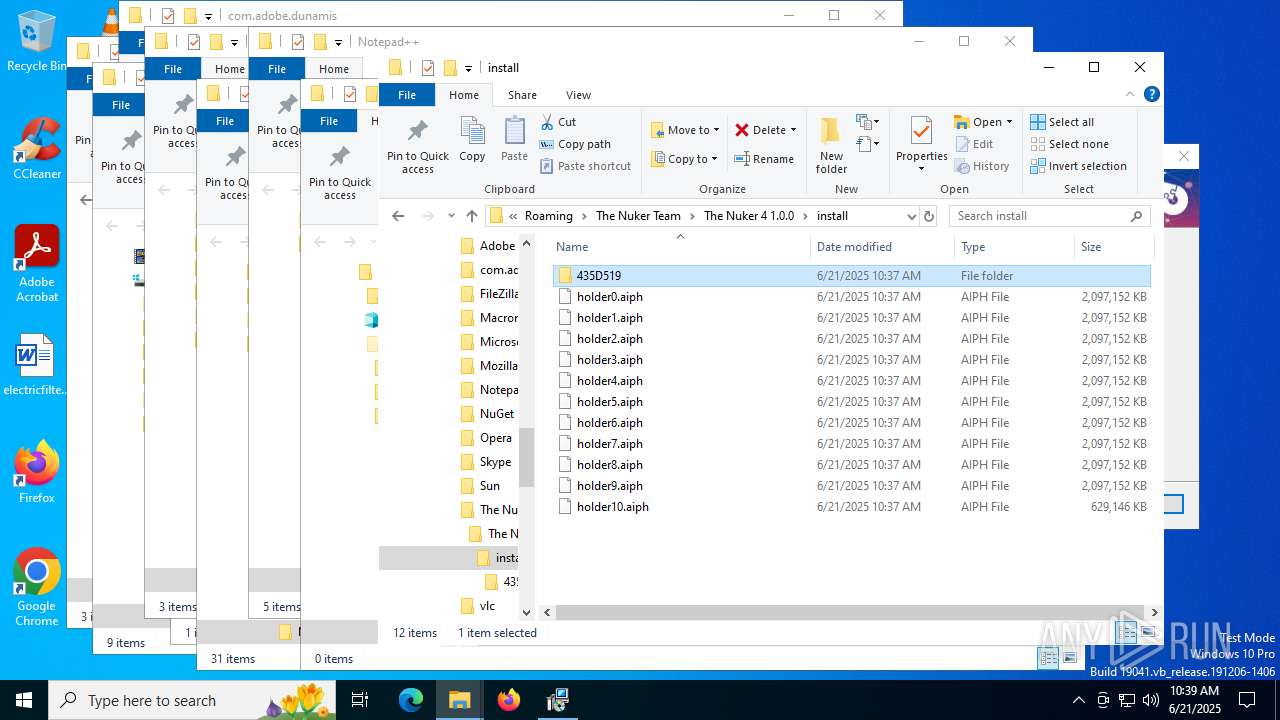
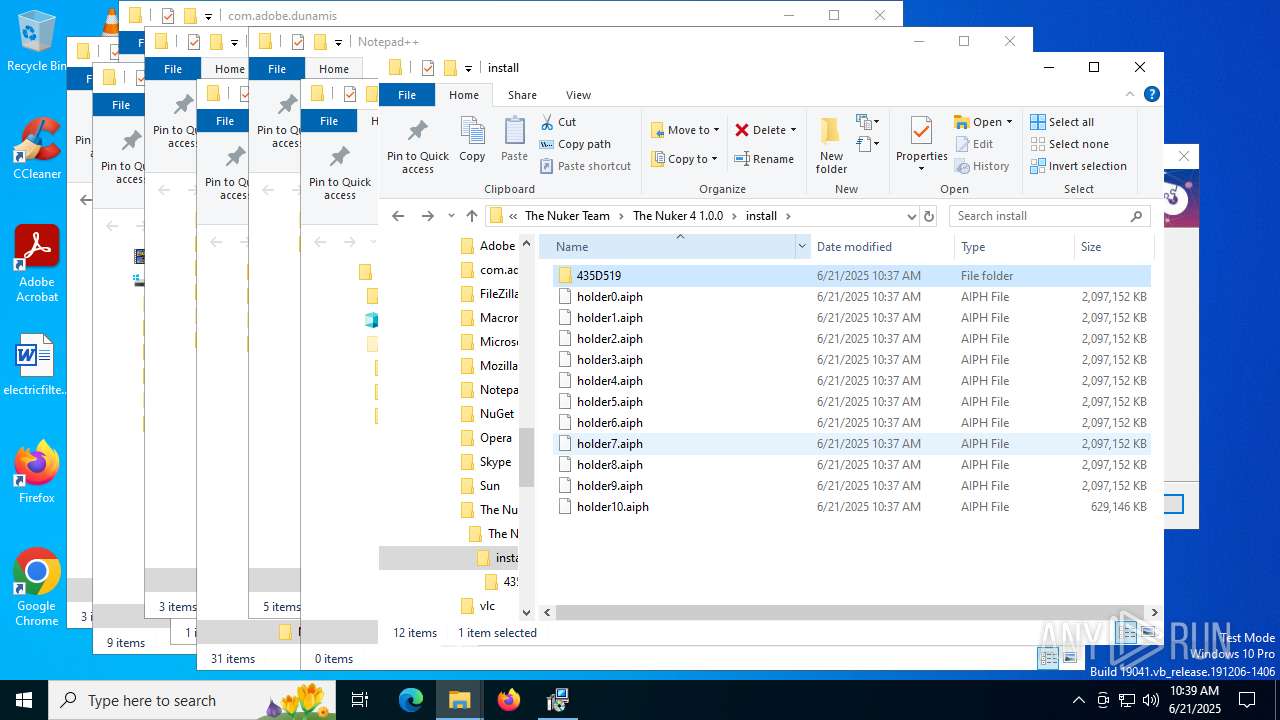
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | The_Nuker_4_Installer.exe | C:\Users\admin\AppData\Roaming\The Nuker Team\The Nuker 4 1.0.0\install\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 2580 | The_Nuker_4_Installer.exe | C:\Users\admin\AppData\Roaming\The Nuker Team\The Nuker 4 1.0.0\install\holder1.aiph | — | |
MD5:— | SHA256:— | |||
| 2580 | The_Nuker_4_Installer.exe | C:\Users\admin\AppData\Roaming\The Nuker Team\The Nuker 4 1.0.0\install\holder2.aiph | — | |
MD5:— | SHA256:— | |||
| 2580 | The_Nuker_4_Installer.exe | C:\Users\admin\AppData\Roaming\The Nuker Team\The Nuker 4 1.0.0\install\holder3.aiph | — | |
MD5:— | SHA256:— | |||
| 2580 | The_Nuker_4_Installer.exe | C:\Users\admin\AppData\Roaming\The Nuker Team\The Nuker 4 1.0.0\install\holder4.aiph | — | |
MD5:— | SHA256:— | |||
| 2580 | The_Nuker_4_Installer.exe | C:\Users\admin\AppData\Roaming\The Nuker Team\The Nuker 4 1.0.0\install\holder5.aiph | — | |
MD5:— | SHA256:— | |||
| 2580 | The_Nuker_4_Installer.exe | C:\Users\admin\AppData\Roaming\The Nuker Team\The Nuker 4 1.0.0\install\holder6.aiph | — | |
MD5:— | SHA256:— | |||
| 2580 | The_Nuker_4_Installer.exe | C:\Users\admin\AppData\Roaming\The Nuker Team\The Nuker 4 1.0.0\install\holder7.aiph | — | |
MD5:— | SHA256:— | |||
| 2580 | The_Nuker_4_Installer.exe | C:\Users\admin\AppData\Roaming\The Nuker Team\The Nuker 4 1.0.0\install\holder8.aiph | — | |
MD5:— | SHA256:— | |||
| 2580 | The_Nuker_4_Installer.exe | C:\Users\admin\AppData\Roaming\The Nuker Team\The Nuker 4 1.0.0\install\holder9.aiph | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report