| File name: | dll1.dll |
| Full analysis: | https://app.any.run/tasks/e839021a-3431-4705-811b-7c615e91b228 |
| Verdict: | Malicious activity |
| Analysis date: | November 02, 2021, 08:19:20 |
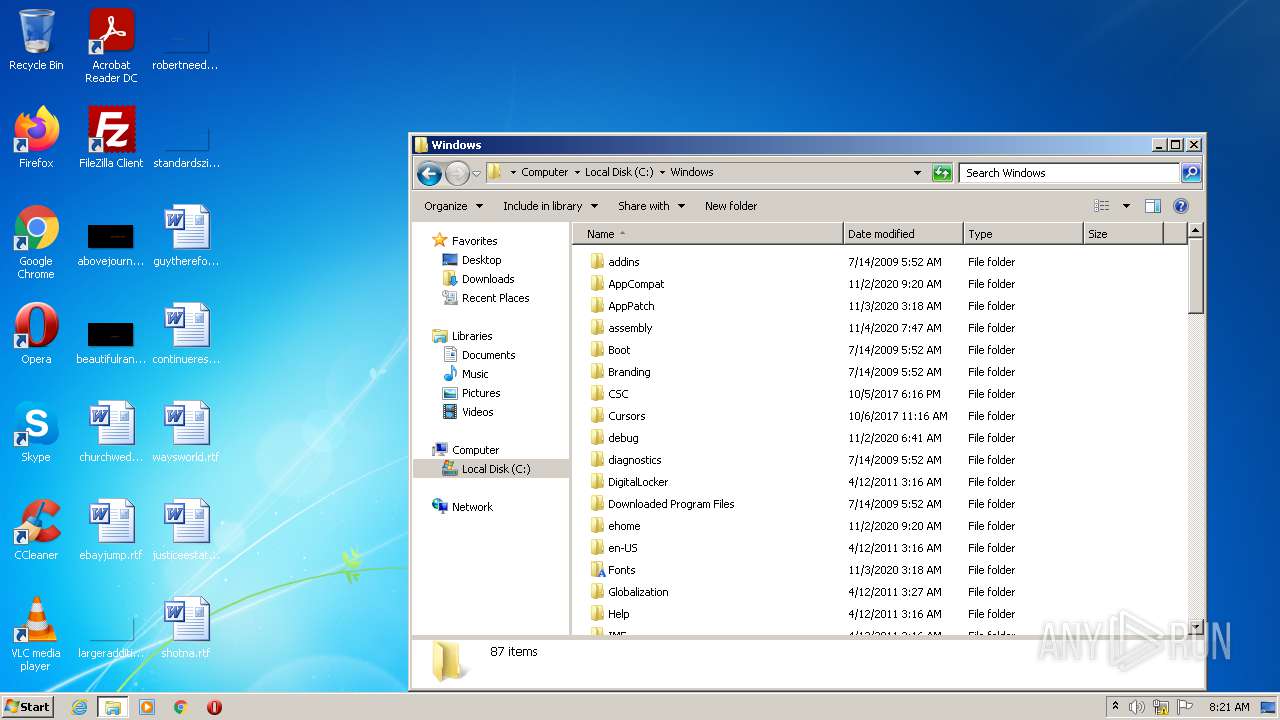
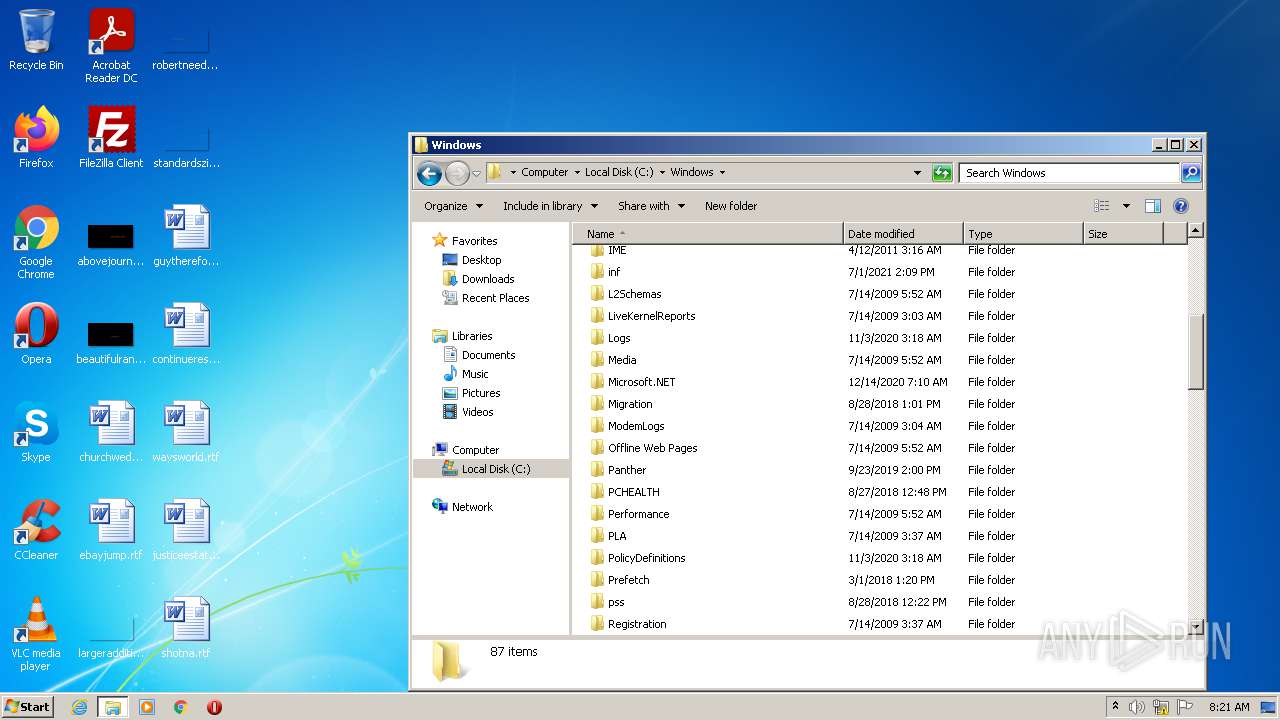
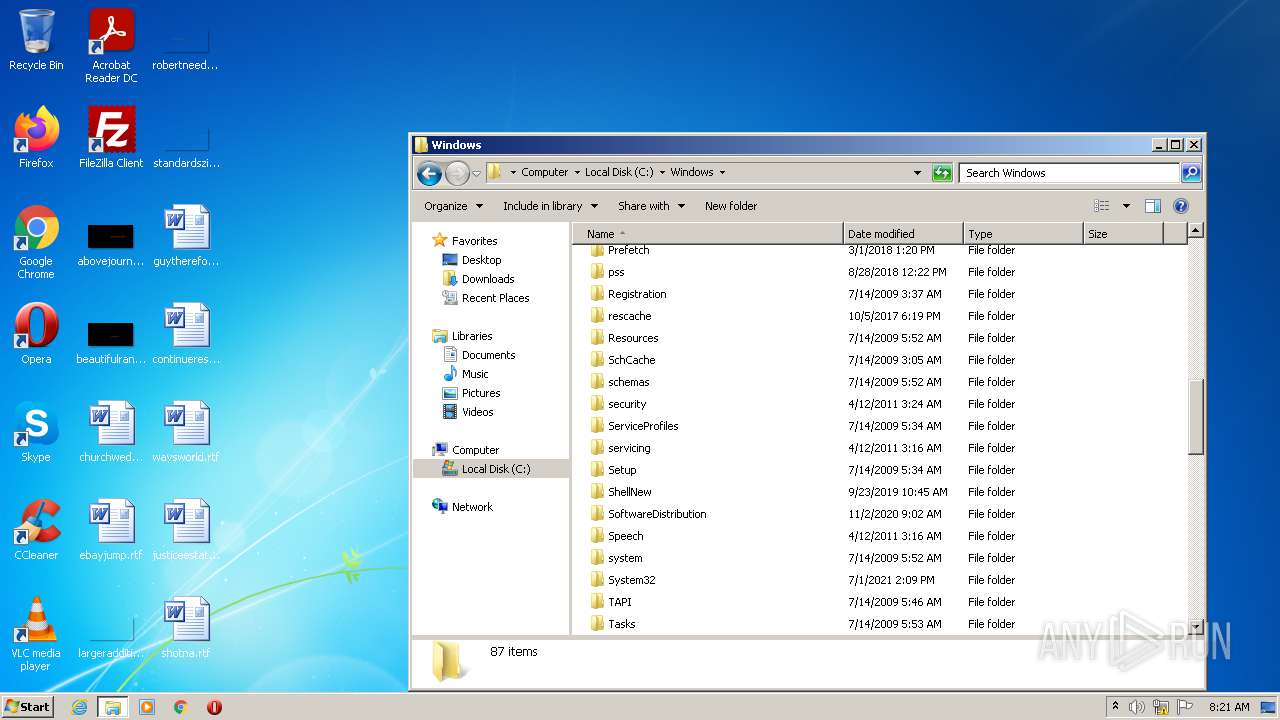
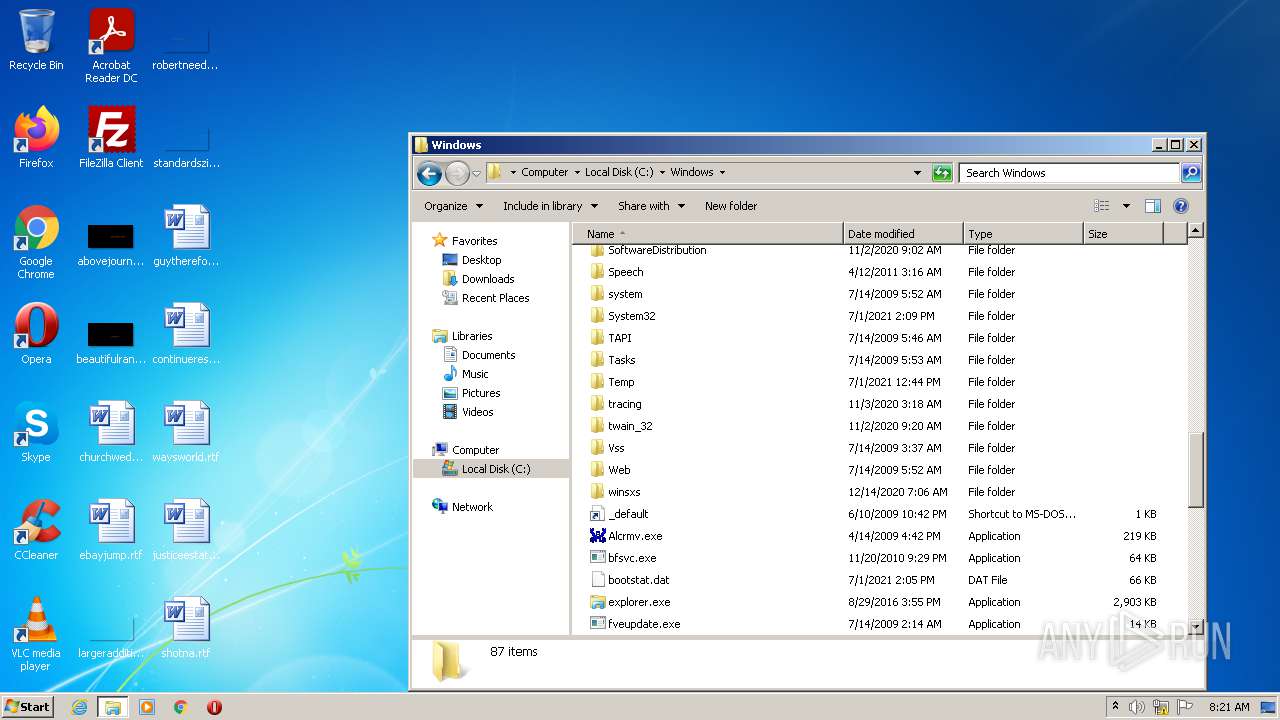
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 73CD683E449B11B9792AEA03997F0229 |
| SHA1: | 9F34B81F618FBC2476FF5510681F0D6FB0E3F1C3 |
| SHA256: | 71A78EFCF1922385E42405B5A62B4CD81EEFCA688A3472065E01F022D78B67B1 |
| SSDEEP: | 12288:P3Cf6O5kY3xYN2Pj13d7aTKcU3RTiLazdD:PyirYKcLT3clazd |
MALICIOUS
Drops executable file immediately after starts
- explorer.exe (PID: 3300)
SUSPICIOUS
Drops a file with too old compile date
- explorer.exe (PID: 3300)
Executable content was dropped or overwritten
- explorer.exe (PID: 3300)
Executed via COM
- DllHost.exe (PID: 2372)
- DllHost.exe (PID: 1032)
Checks supported languages
- notepad++.exe (PID: 2172)
INFO
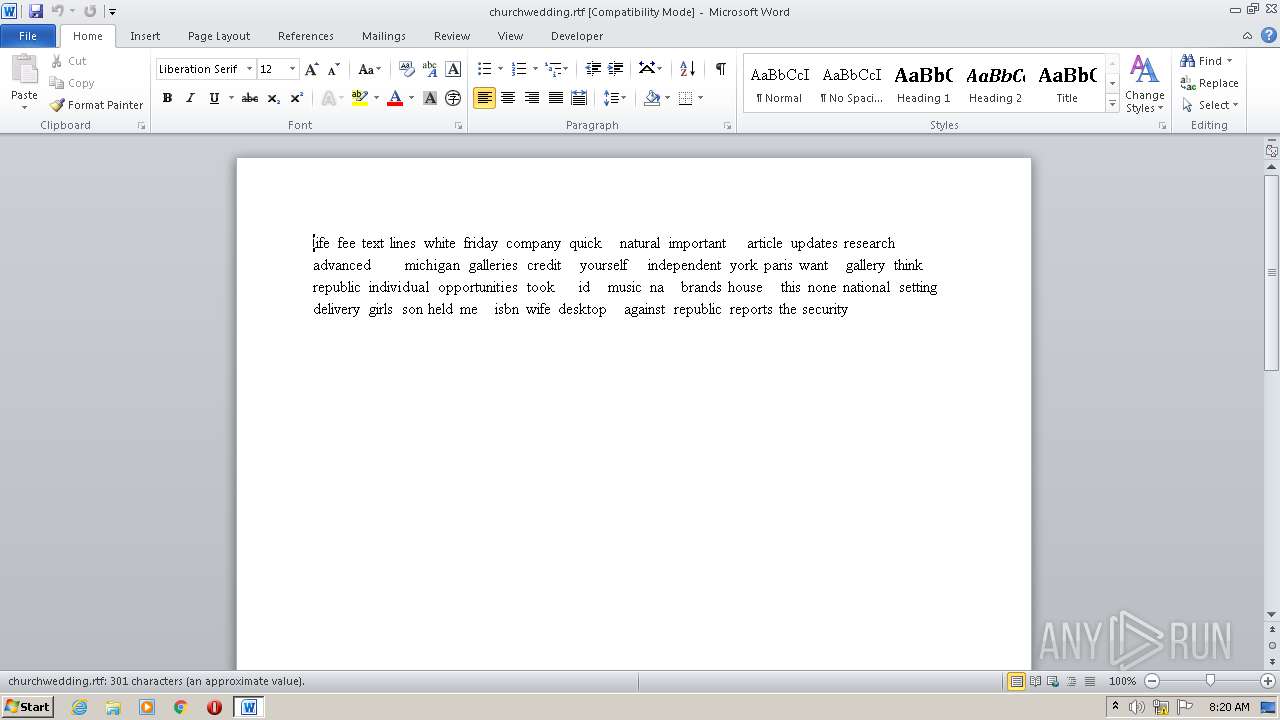
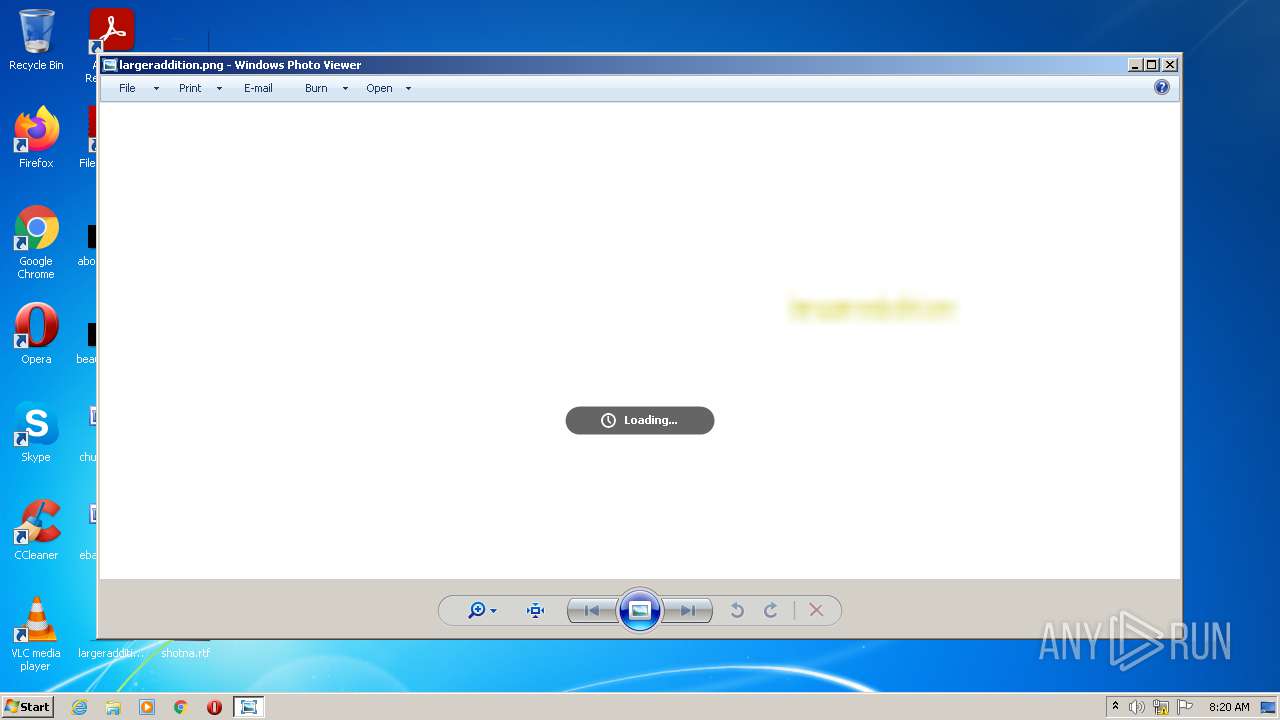
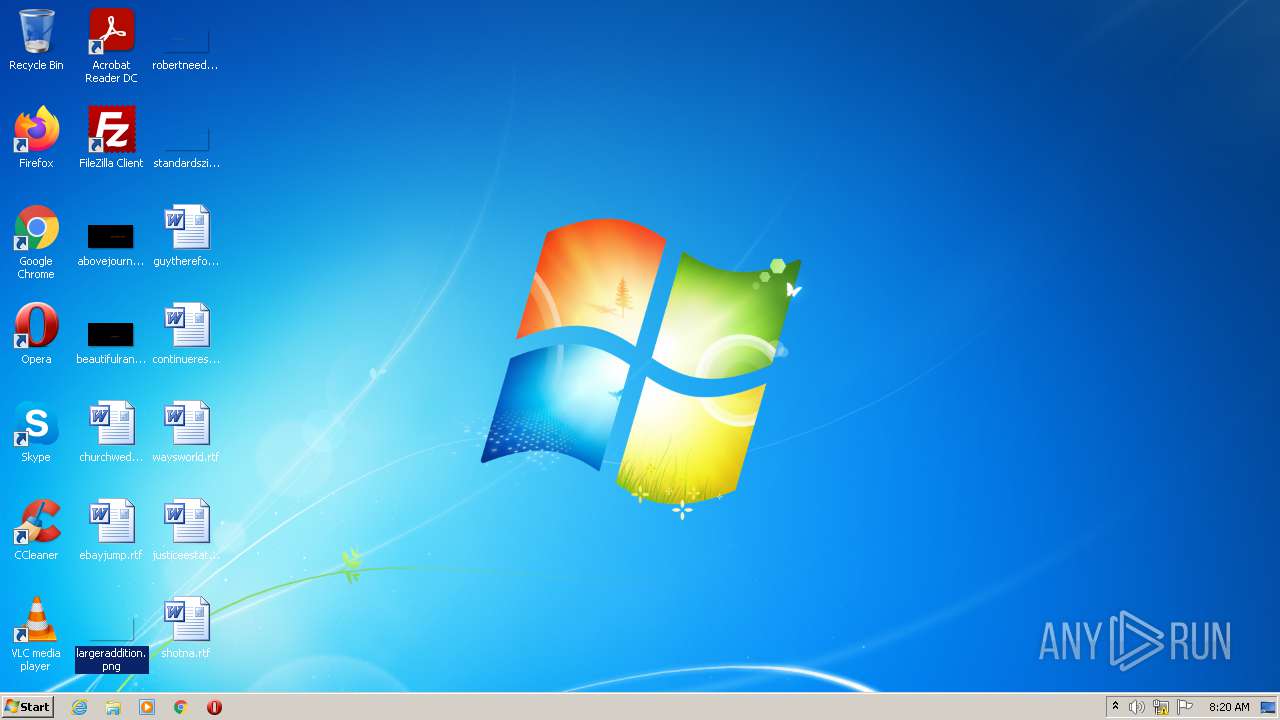
Manual execution by user
- WINWORD.EXE (PID: 2772)
- explorer.exe (PID: 1448)
- notepad++.exe (PID: 2172)
Checks supported languages
- explorer.exe (PID: 3300)
- regsvr32.exe (PID: 3928)
- WINWORD.EXE (PID: 2772)
- DllHost.exe (PID: 2372)
- explorer.exe (PID: 1448)
- DllHost.exe (PID: 1032)
Reads the computer name
- regsvr32.exe (PID: 3928)
- WINWORD.EXE (PID: 2772)
- explorer.exe (PID: 3300)
- DllHost.exe (PID: 2372)
- DllHost.exe (PID: 1032)
- explorer.exe (PID: 1448)
Creates files in the user directory
- WINWORD.EXE (PID: 2772)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 379392 |
| InitializedDataSize: | 206336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5d6a4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0005C814 | 0x0005CA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54396 |
DATA | 0x0005E000 | 0x000012AC | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.07538 |
BSS | 0x00060000 | 0x00000C9D | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00061000 | 0x000020B4 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.91395 |
.reloc | 0x00064000 | 0x00006BAC | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.68239 |
.rsrc | 0x0006B000 | 0x00028400 | 0x00028400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.17707 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.85232 | 744 | UNKNOWN | English - United States | RT_ICON |
2 | 2.80231 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4081 | 3.33647 | 896 | UNKNOWN | UNKNOWN | RT_STRING |
4082 | 3.2068 | 492 | UNKNOWN | UNKNOWN | RT_STRING |
4083 | 3.25256 | 328 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Total processes
49
Monitored processes
7
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1032 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
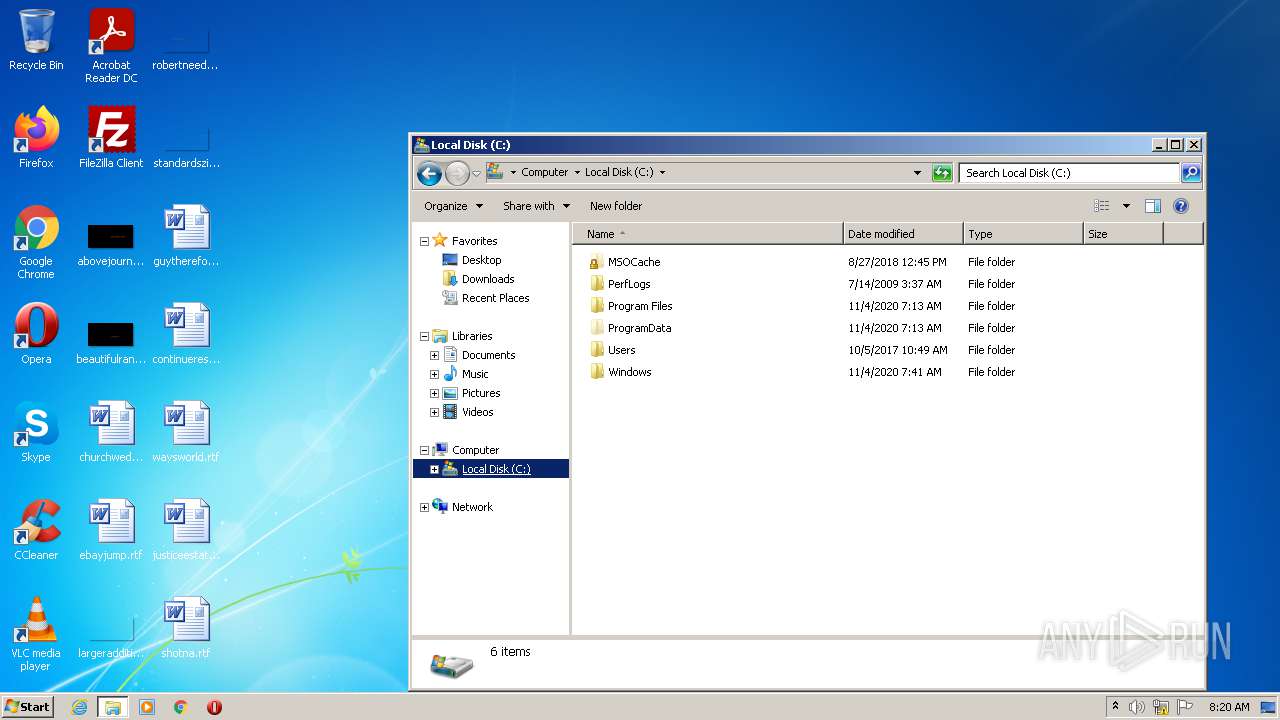
| 1448 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
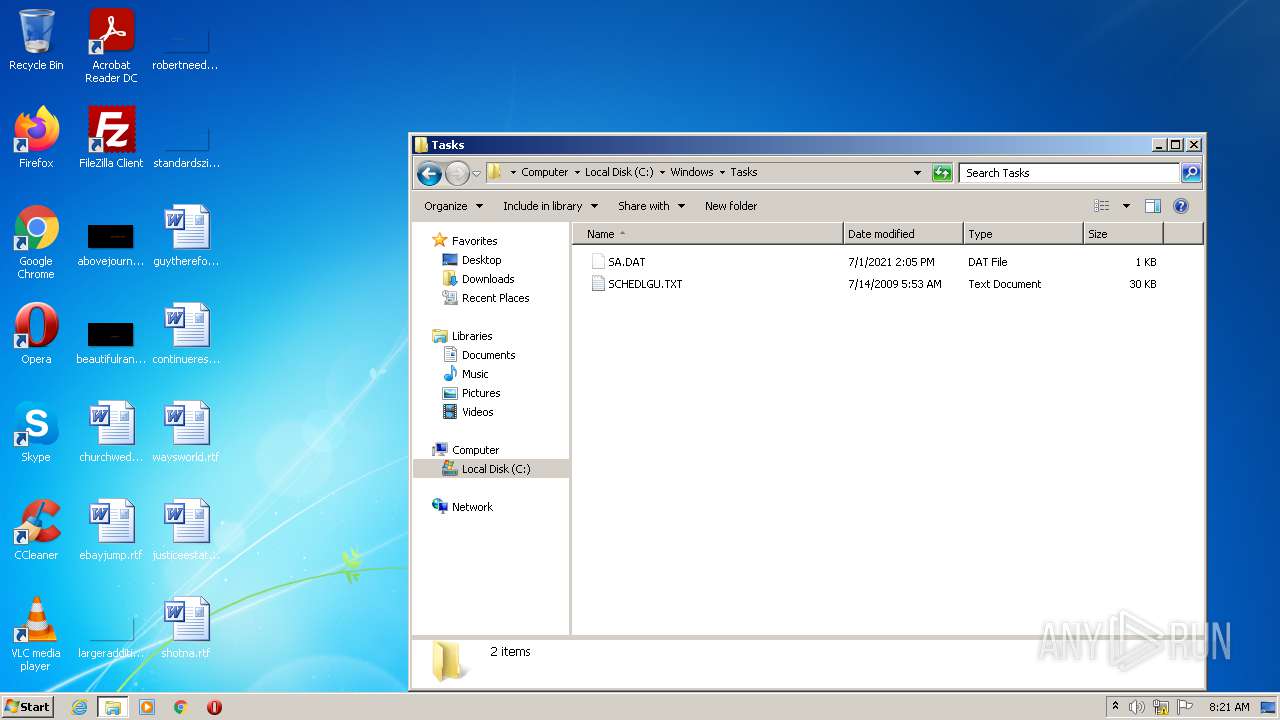
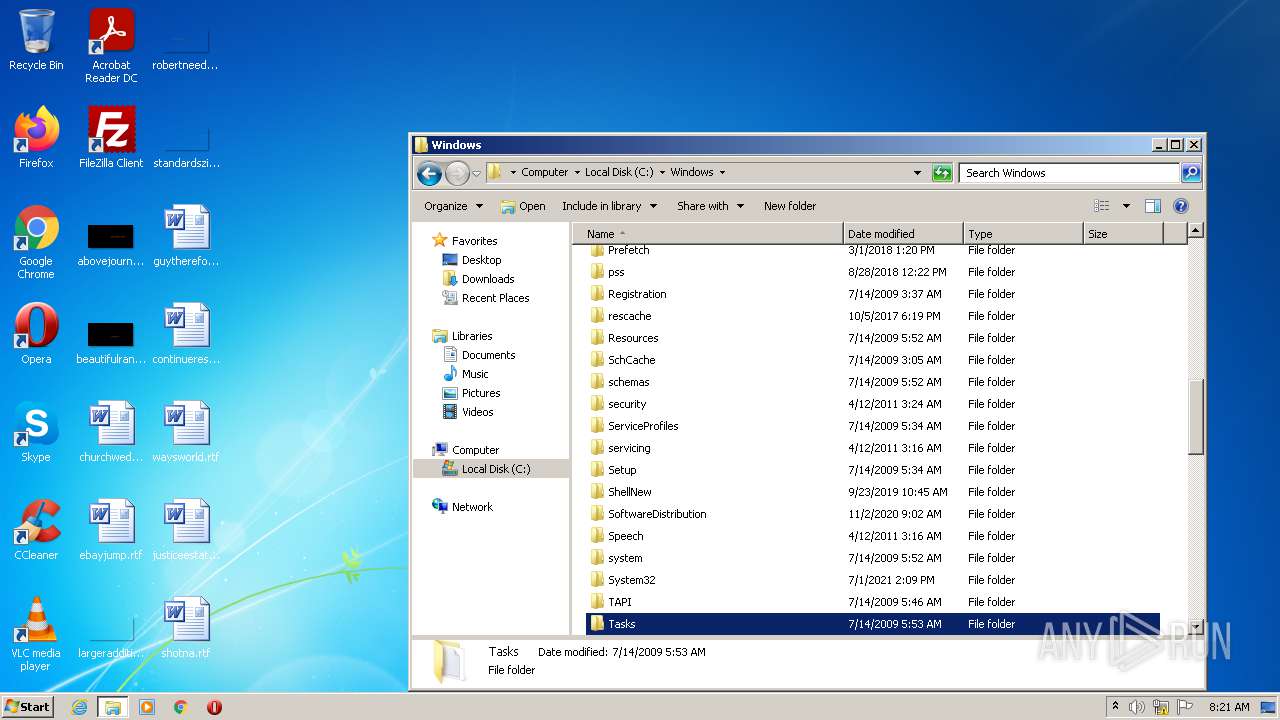
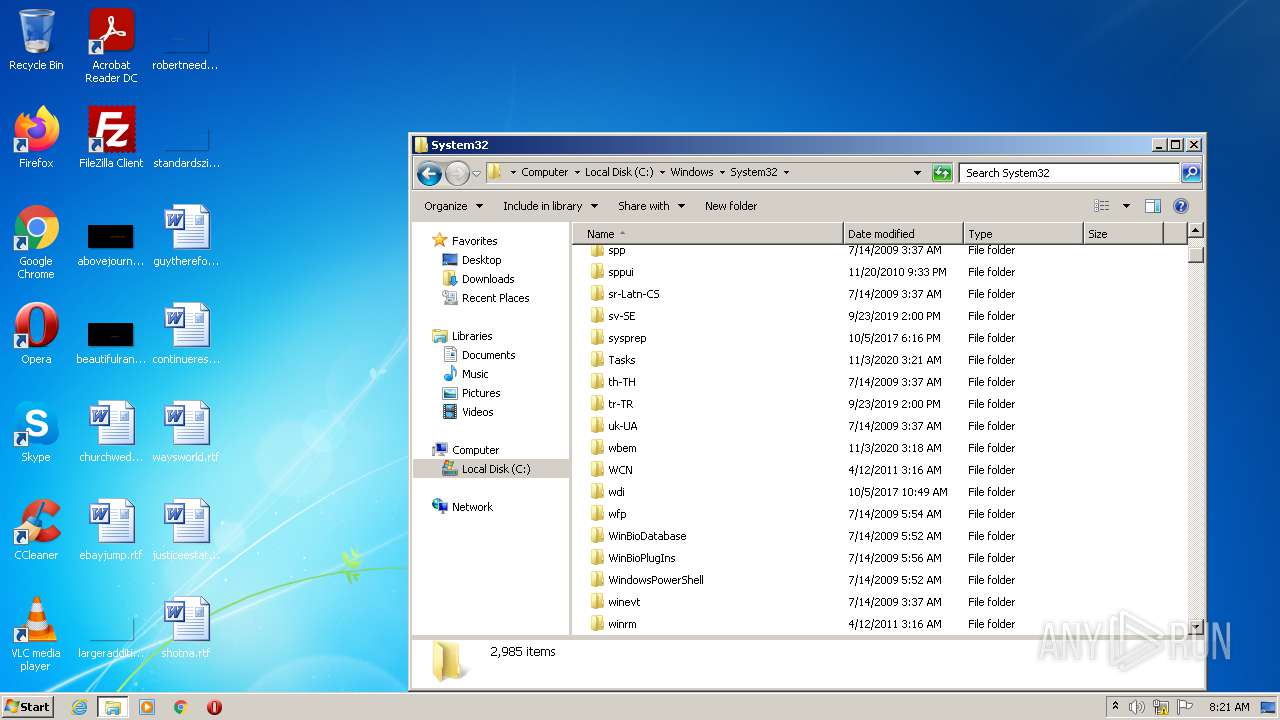
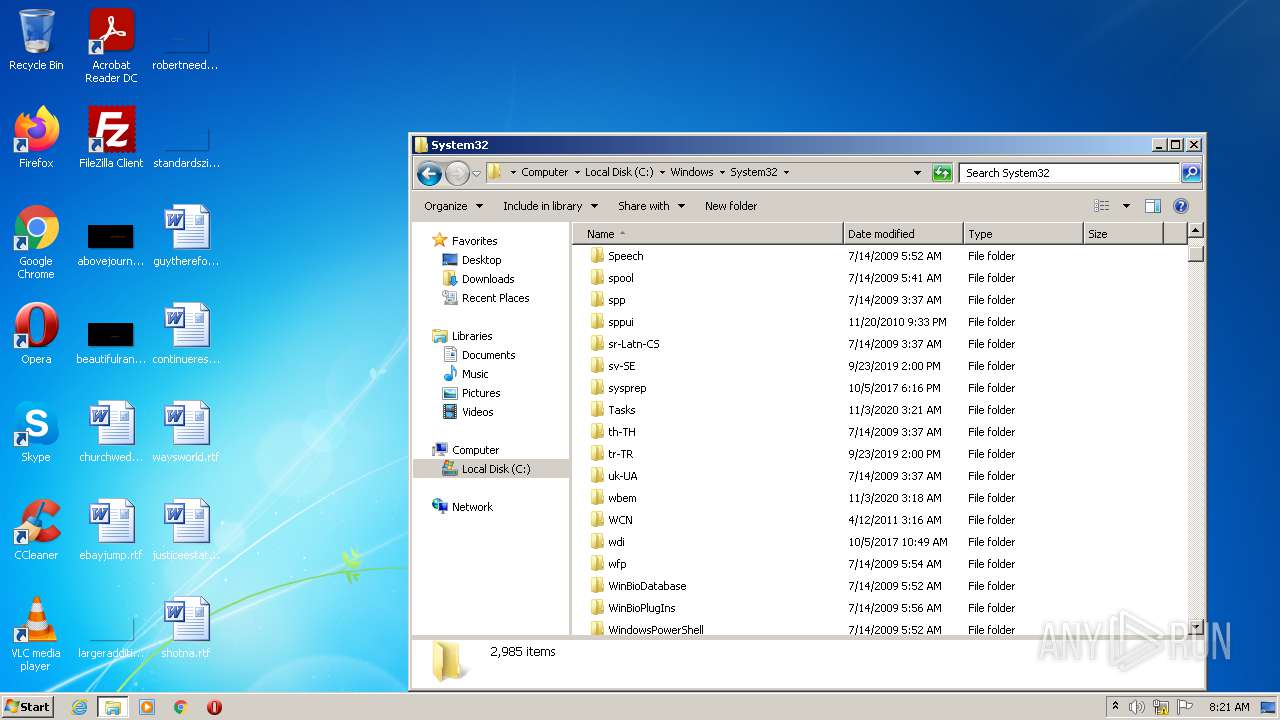
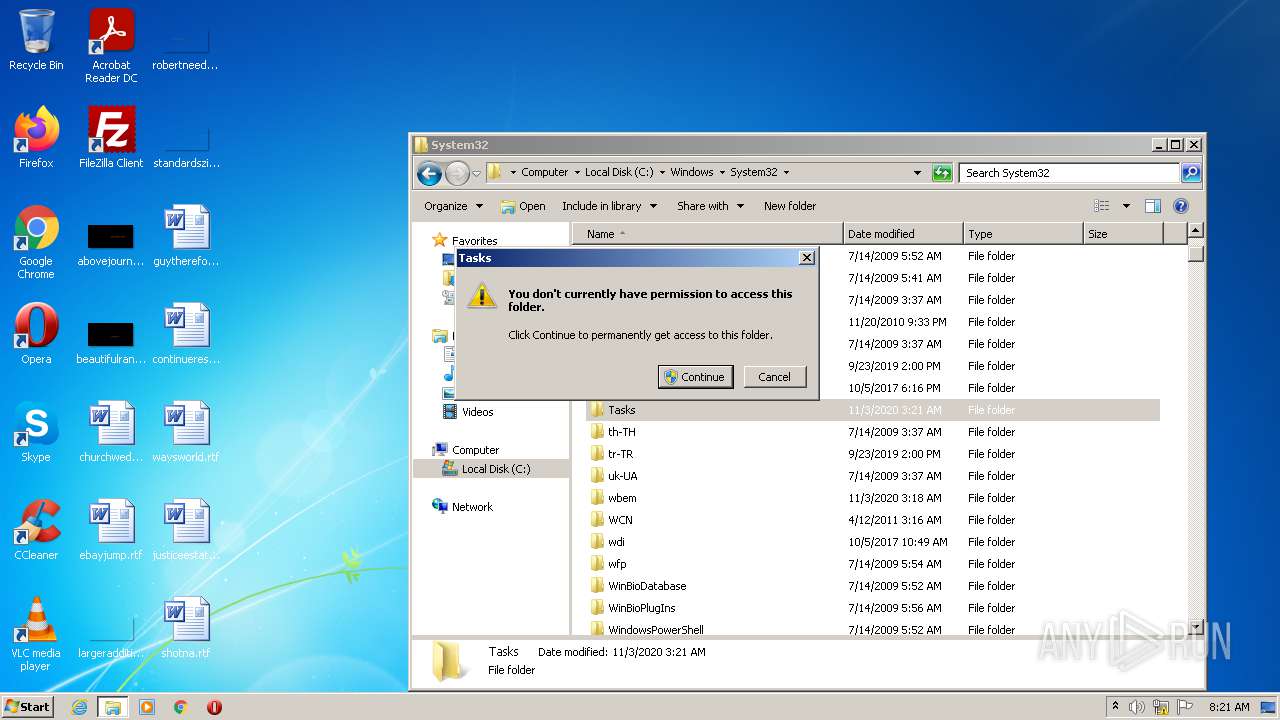
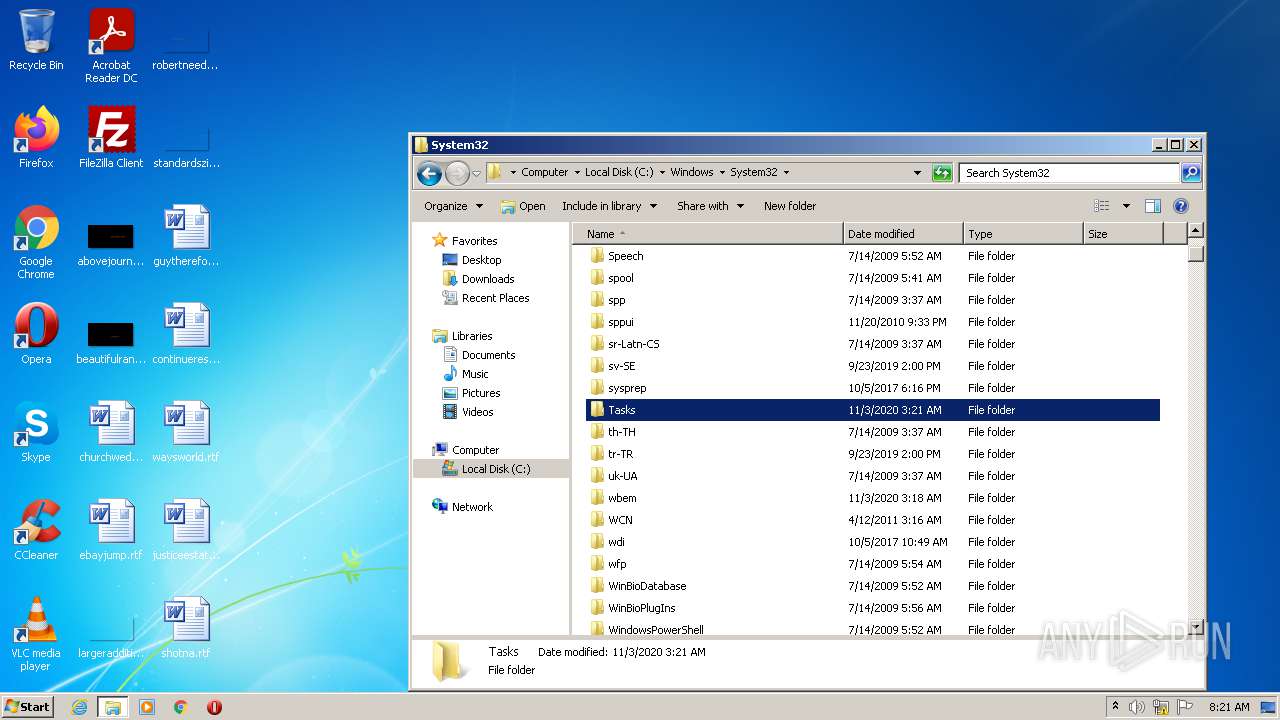
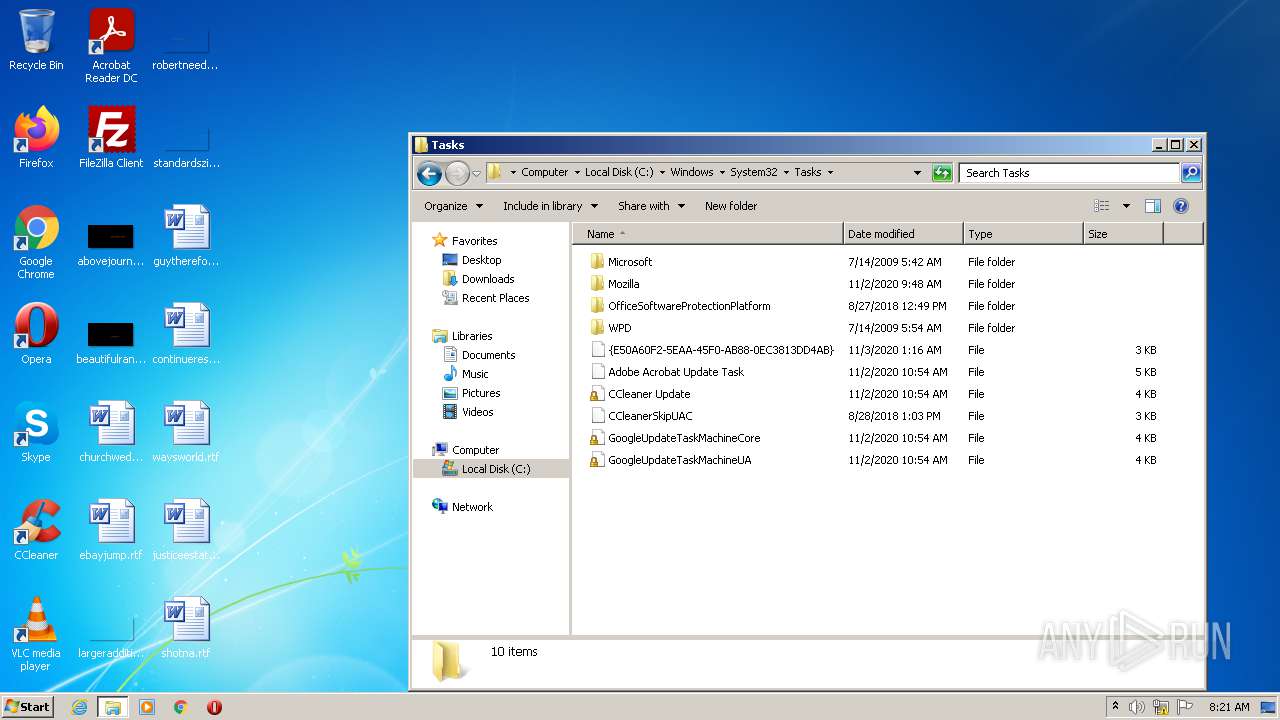
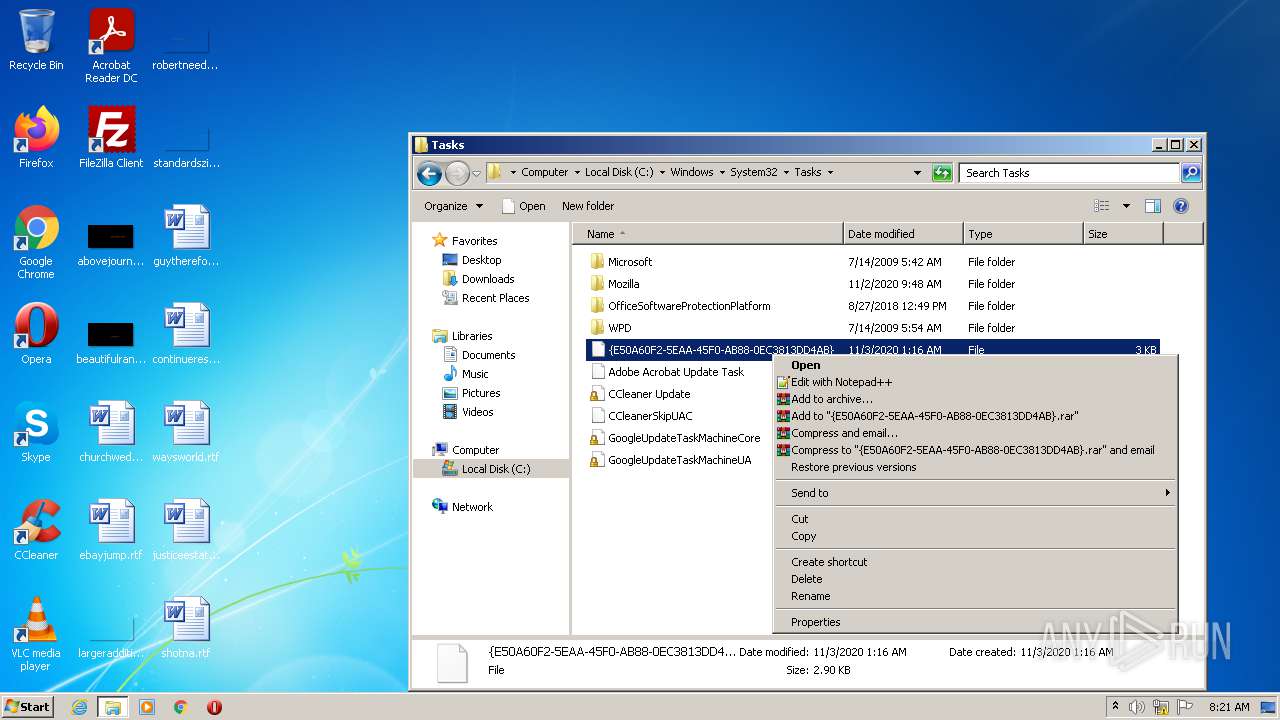
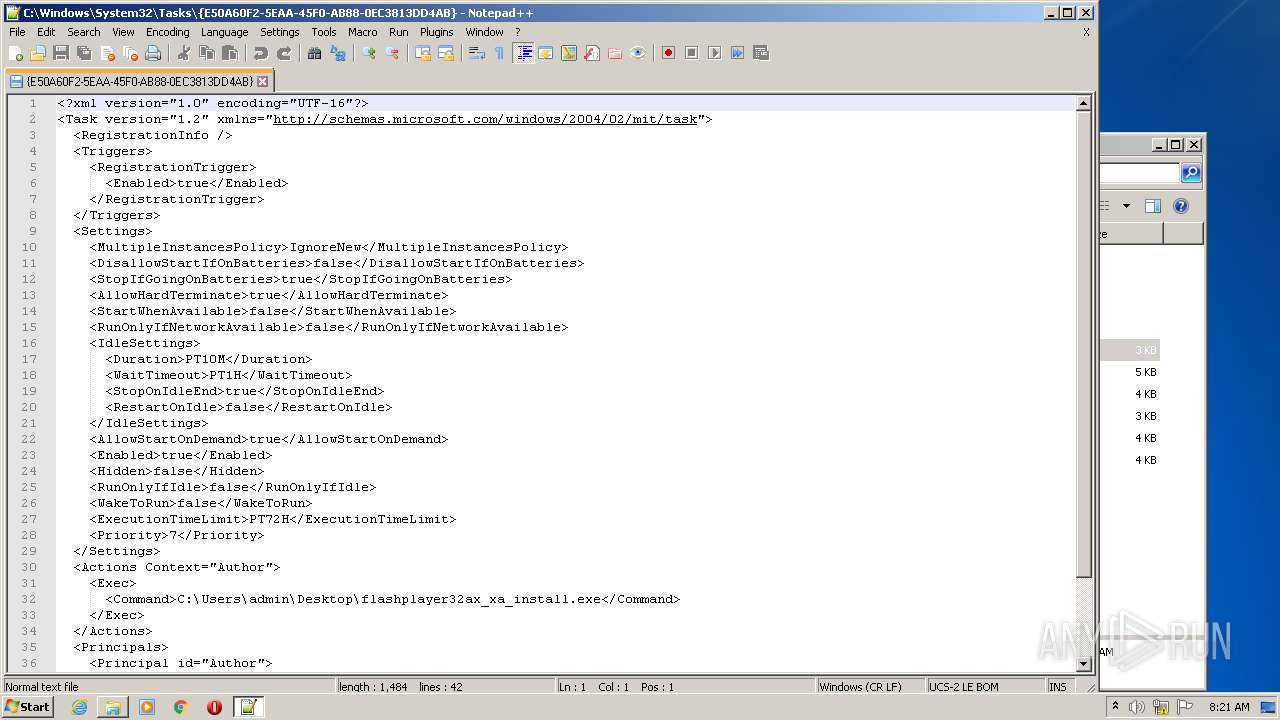
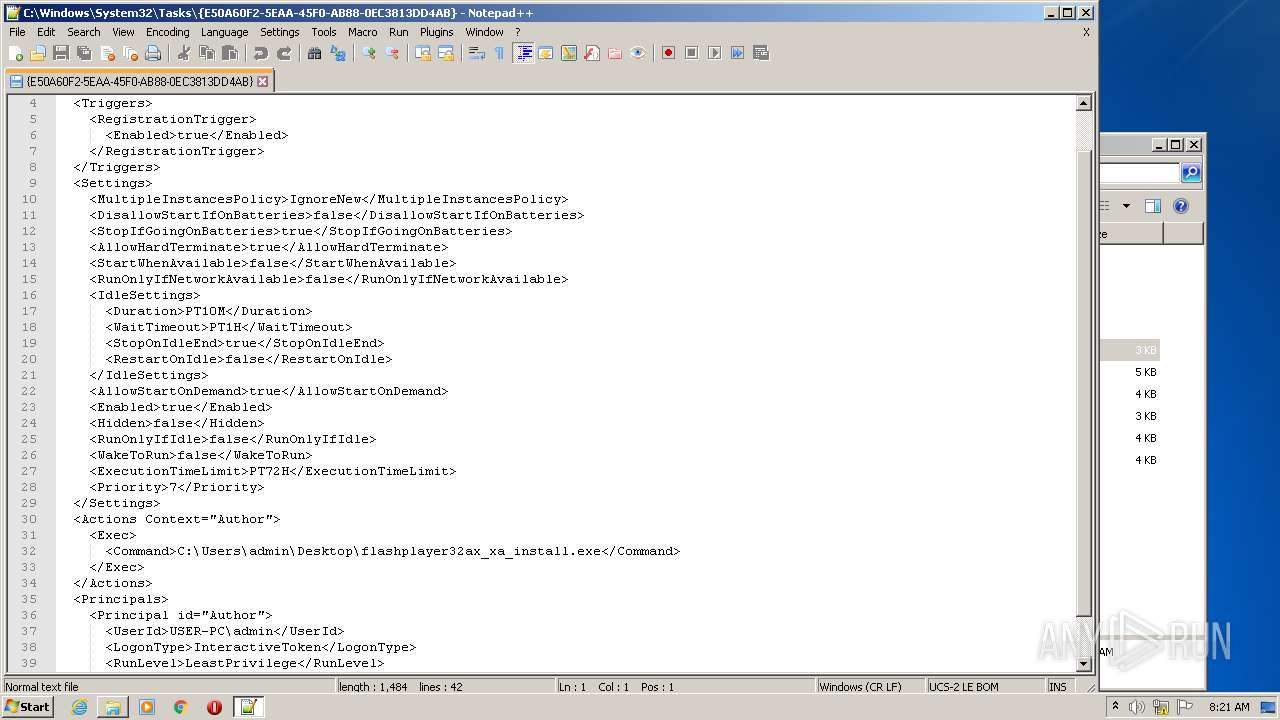
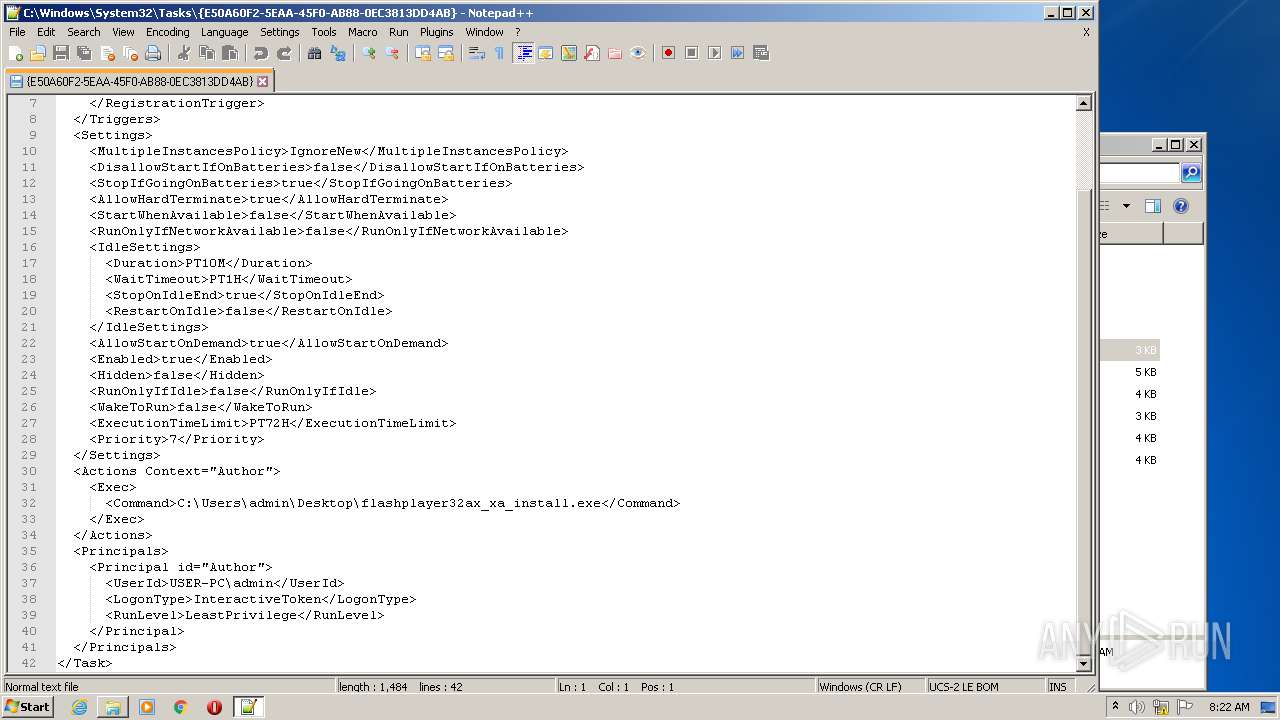
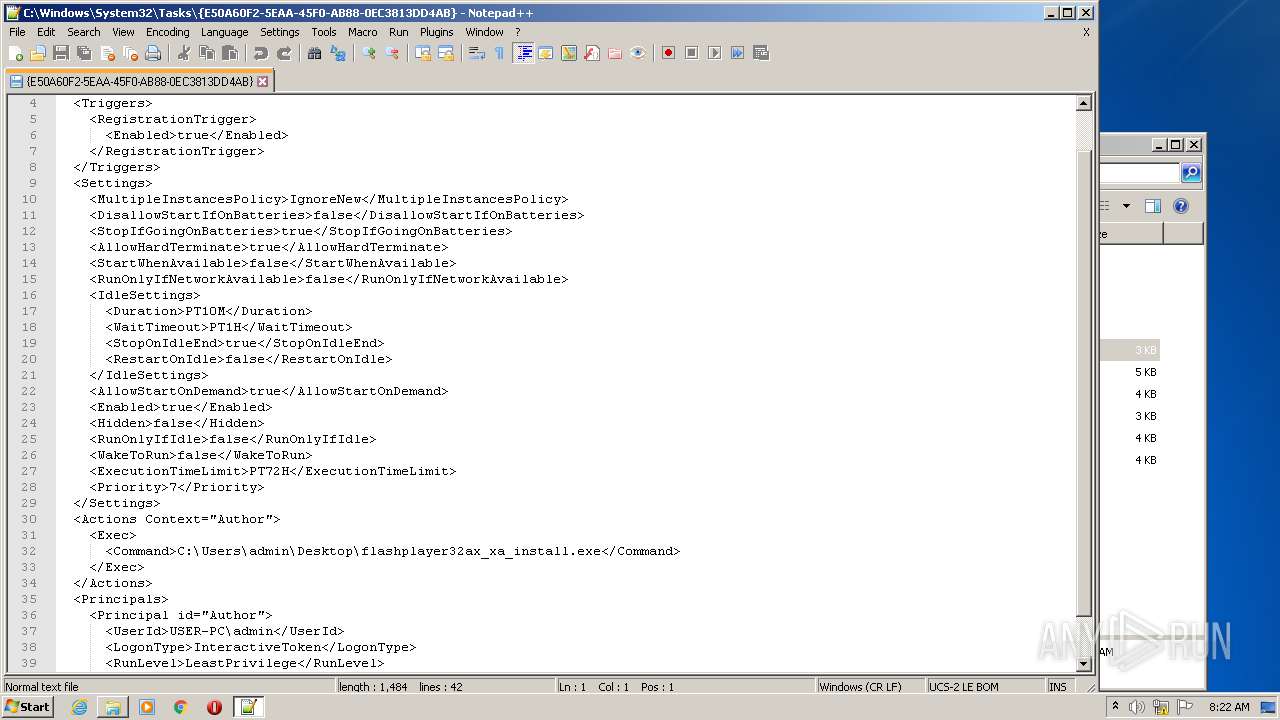
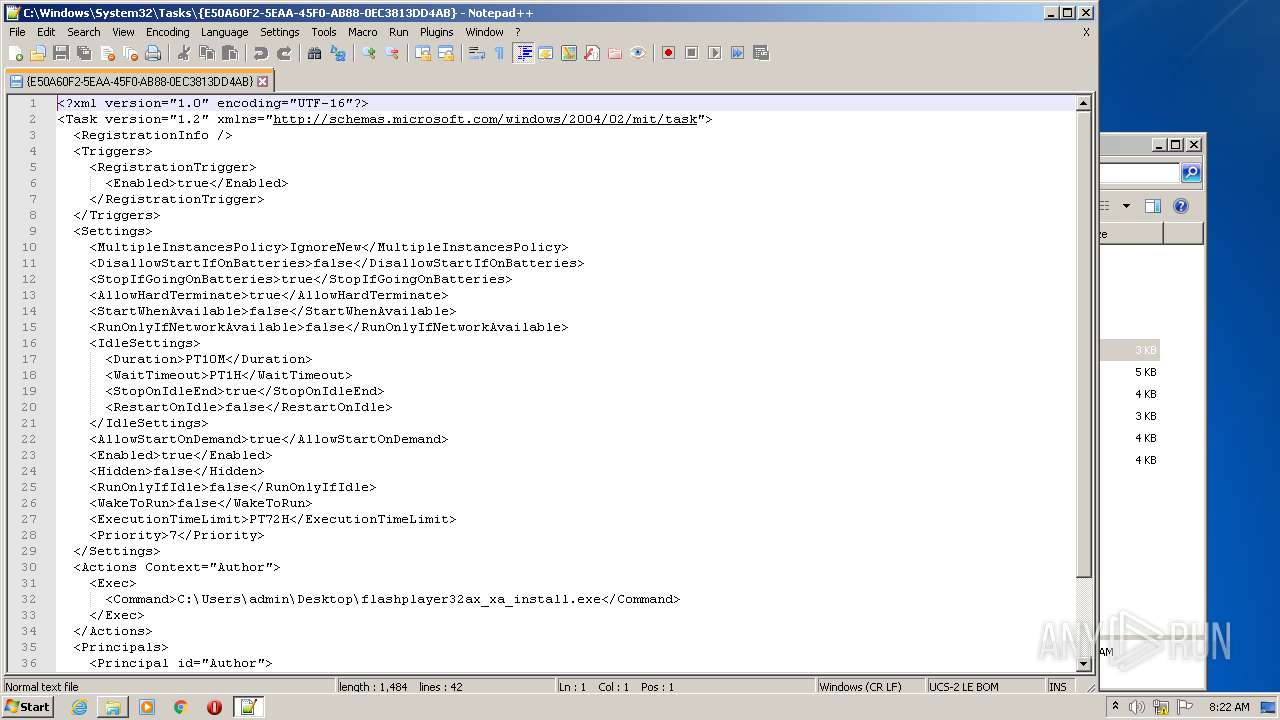
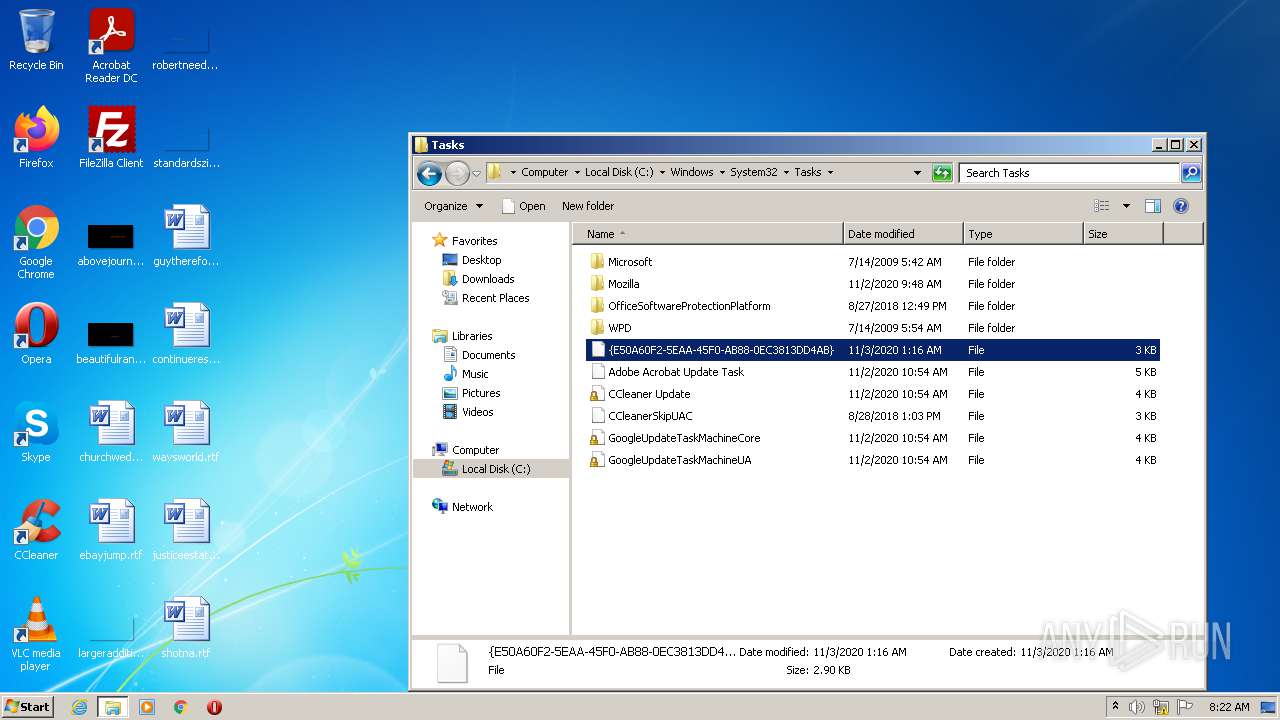
| 2172 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Windows\System32\Tasks\{E50A60F2-5EAA-45F0-AB88-0EC3813DD4AB}" | C:\Program Files\Notepad++\notepad++.exe | Explorer.EXE | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 2372 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\churchwedding.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3300 | C:\Windows\explorer.exe | C:\Windows\explorer.exe | regsvr32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
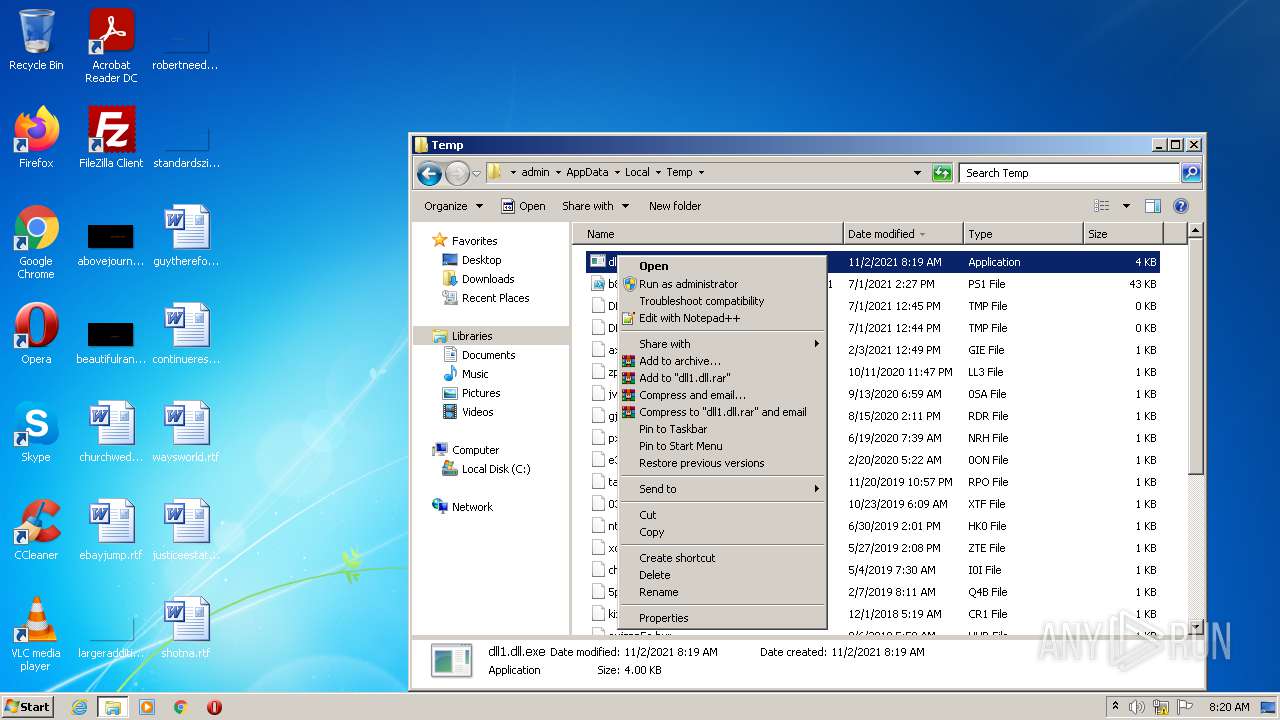
| 3928 | "C:\Windows\System32\regsvr32.exe" C:\Users\admin\AppData\Local\Temp\dll1.dll.exe | C:\Windows\System32\regsvr32.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 190
Read events
2 852
Write events
193
Delete events
145
Modification events
| (PID) Process: | (3300) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Ytfovlymmxqrt |
| Operation: | write | Name: | 9abda0b5 |
Value: 78FD41573BD99A1F72AB7870315B0E3453028C2CB868FED0AF9ED99462BC4217A1D271A8EA0356DF43535841214A5F0FFC6490664BB2D686 | |||
| (PID) Process: | (3300) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Ytfovlymmxqrt |
| Operation: | write | Name: | af2270fb |
Value: 1671B1CB492C5556C055EBE1070186F4539120B65789D71DB758F7249231D7EFE81C8ECAE56FBF12EB97D74FCE28A7C64420349CAD704EF46C08C28785325DA04EC55E6E8CDFA42531F0946B3321C8CB01D1E8F360D47B846A3463E7919A5EE78CEB4A7EF37FE781B04F1E724F76D4D471D962C1AF767DCD901BB854F670DB2AAFDA7EC62D66B8100666C6C42D912507FAFC5C6C86059C6523A7917E99DBC84F0152E8C16D170DA625DEE8DB4EFDD0BAFE8AC174238FCFCE5B284F9E110924B2CA4C60EE9A086EC4EA53370598DCA4606D | |||
| (PID) Process: | (3300) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Ytfovlymmxqrt |
| Operation: | write | Name: | ad635087 |
Value: 3F5FCA242F6BC310CEAAC572F217631E80818206CC63DD11A011436B60540631896528F881B58F8D7524A62F733EFFF1B65DEC863701EF377DB32346C7CAEBF22254622CA4CA2148A5E14D101F2C82D3E373B8F7A28CCE6187EAD42B23EA18A1DBE81CA2 | |||
| (PID) Process: | (3300) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Ytfovlymmxqrt |
| Operation: | write | Name: | 15df37e2 |
Value: B713E4E0E8A1DB4C504871DFD6CD30AAEE4A2773BD02E7476A0A12CD3C8FC1D0D460B2BEF1C202D2A957D3AC2FD06D | |||
| (PID) Process: | (3300) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Ytfovlymmxqrt |
| Operation: | write | Name: | 68d77868 |
Value: FDAA9851894CBEB40AE666C238A829AC7D067B43784036B67ED14F73523A690DA110E0822121380F4474A045F950DFA5F4E571D81A3BCB4FC46D8D17CE5B0104C618671B46604225C4157F1D8E2C771823C93812AC68E744F8CD1B185F4C90181B | |||
| (PID) Process: | (3300) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Ytfovlymmxqrt |
| Operation: | write | Name: | d06b1f0d |
Value: AD659A1C351545021CF96C5D5B9329BE52522392BC1E5EA22C4E1317AC8AAFA82D2B77C6901735FBCC06F5399FAF61D3F005B0319A198178E5B939362F98C9D3FD8BFE4DE91FFF0E3F3018A7FAC315D2389211532683CF1C7B58608894E81C4B | |||
| (PID) Process: | (3300) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Ytfovlymmxqrt |
| Operation: | write | Name: | 179e179e |
Value: 18D68B559E5481419B811576418B7B92AAA117E47E6BE147A40EF6C8A0FA223B37FB4E249371D2480F29E54823A6A221329EF6424F46D87A19FE0794B298D319B418155A4366B3FE | |||
| (PID) Process: | (3300) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Ytfovlymmxqrt |
| Operation: | write | Name: | e5f4cf43 |
Value: 2BF73CCC9ED93F03D708F5D28211873DDE7DD93558AF6796436756F202AE4D70E074748CB258856424 | |||
| (PID) Process: | (3300) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Ytfovlymmxqrt |
| Operation: | write | Name: | 9abda0b5 |
Value: 78FD56573BD9AF68E2E8B224399AEC08954AA6972D0881DB5D1EEB0CC8377942D4EC0D3FEECDEC230CD8B164A163762742B72E187D4E6D08D27D035F5E8C4C61A83C0095B69099EBCE0C386560 | |||
| (PID) Process: | (2772) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 9$? |
Value: 39243F00D40A0000010000000000000000000000 | |||
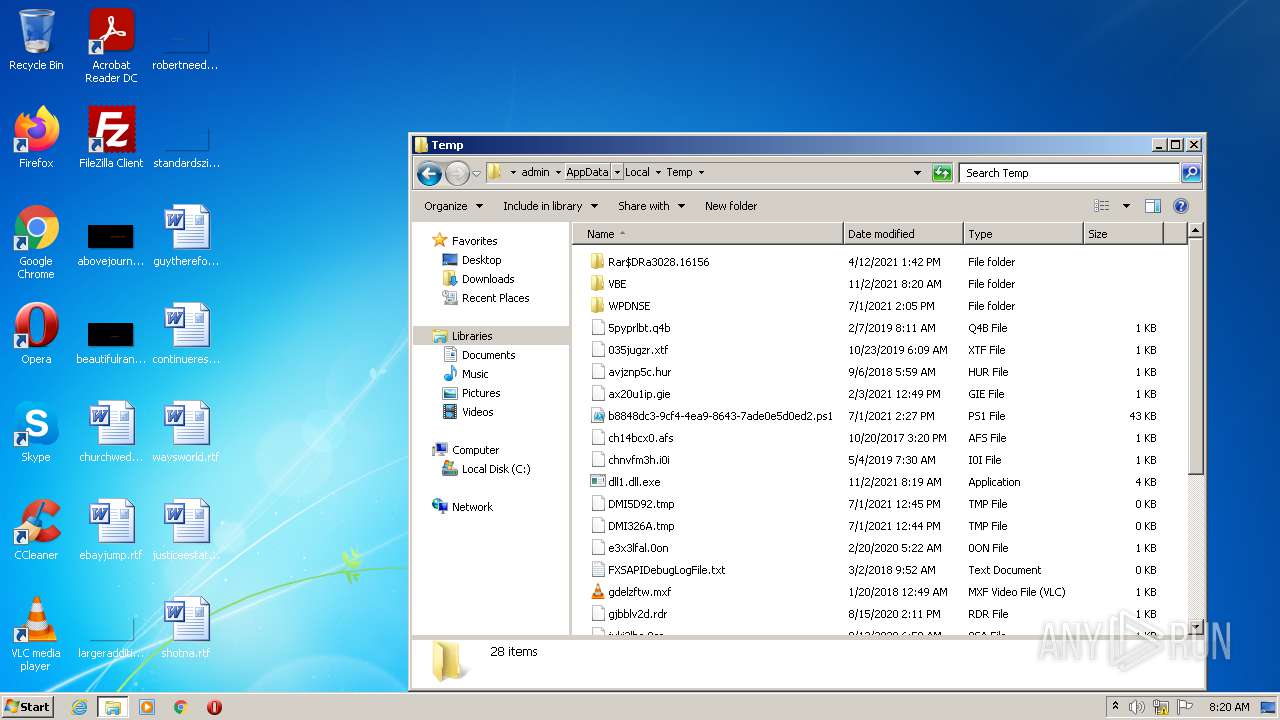
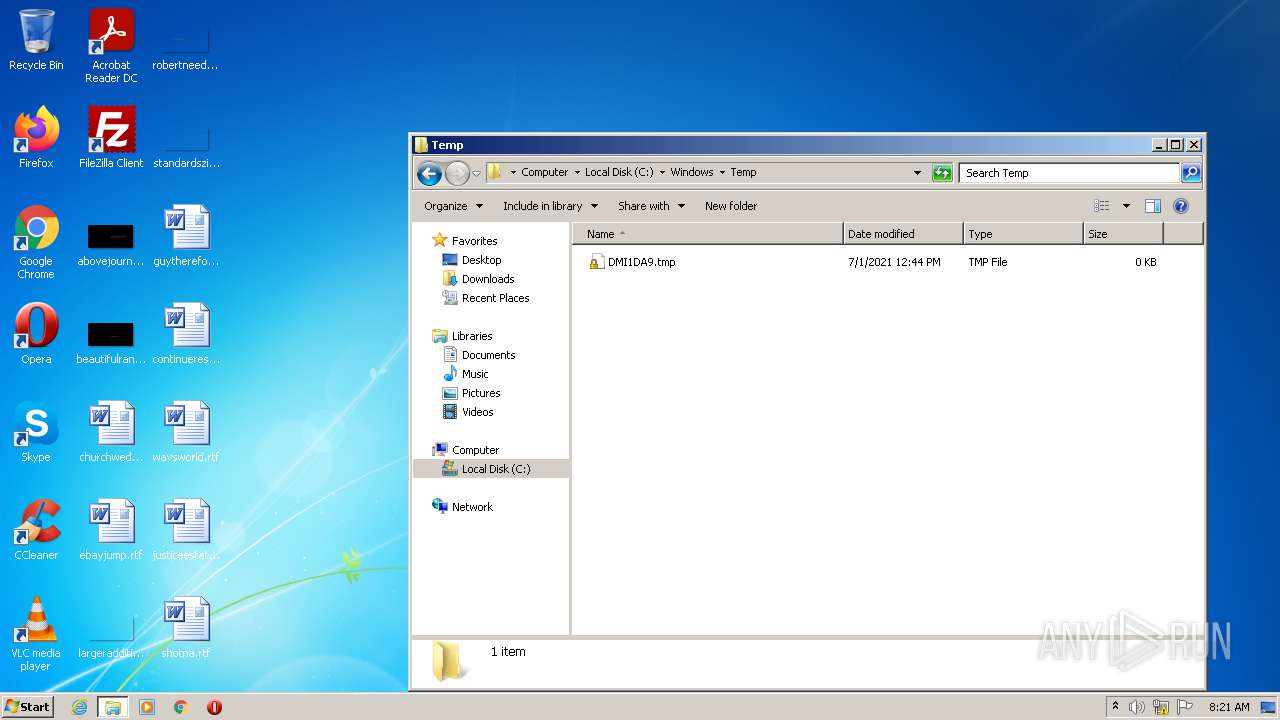
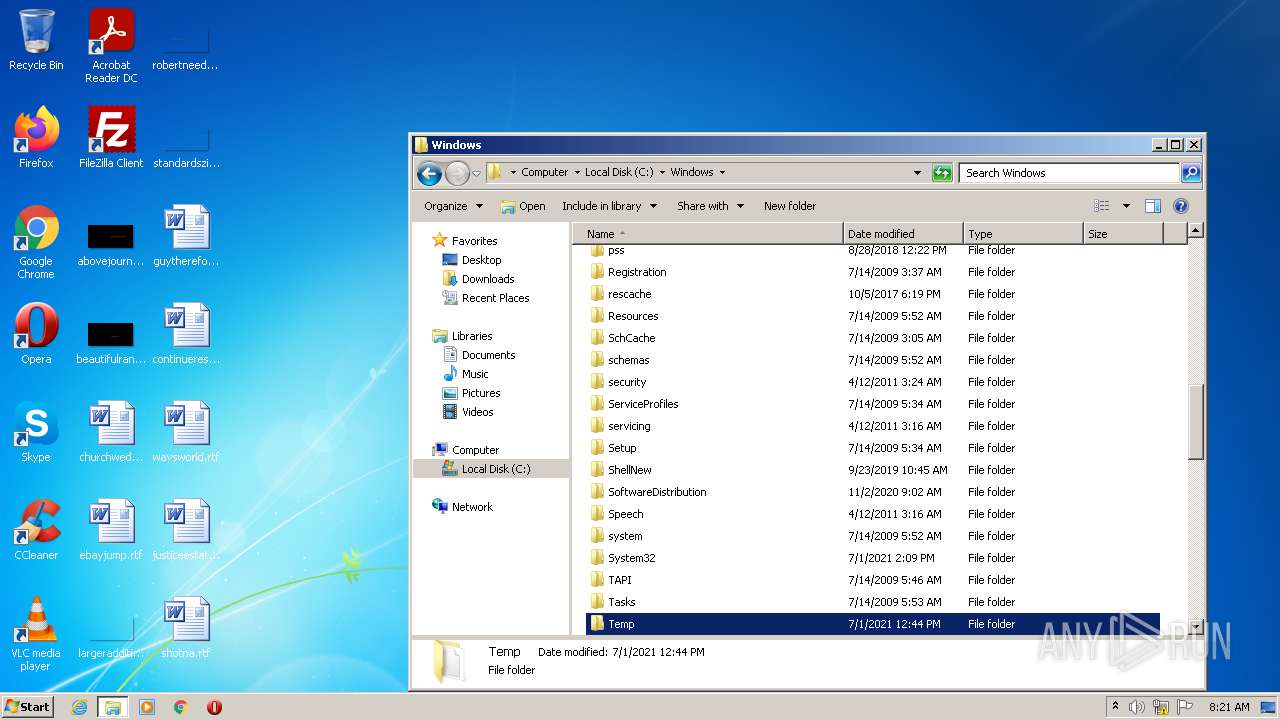
Executable files
1
Suspicious files
1
Text files
3
Unknown types
5
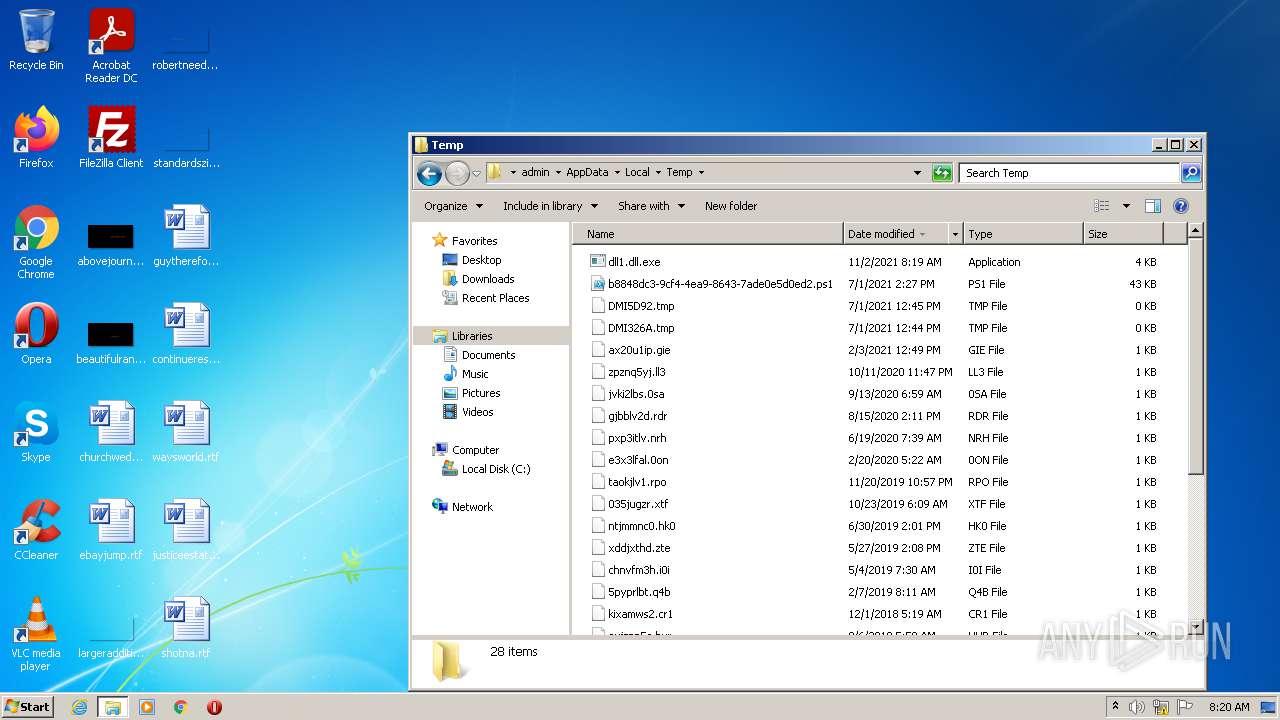
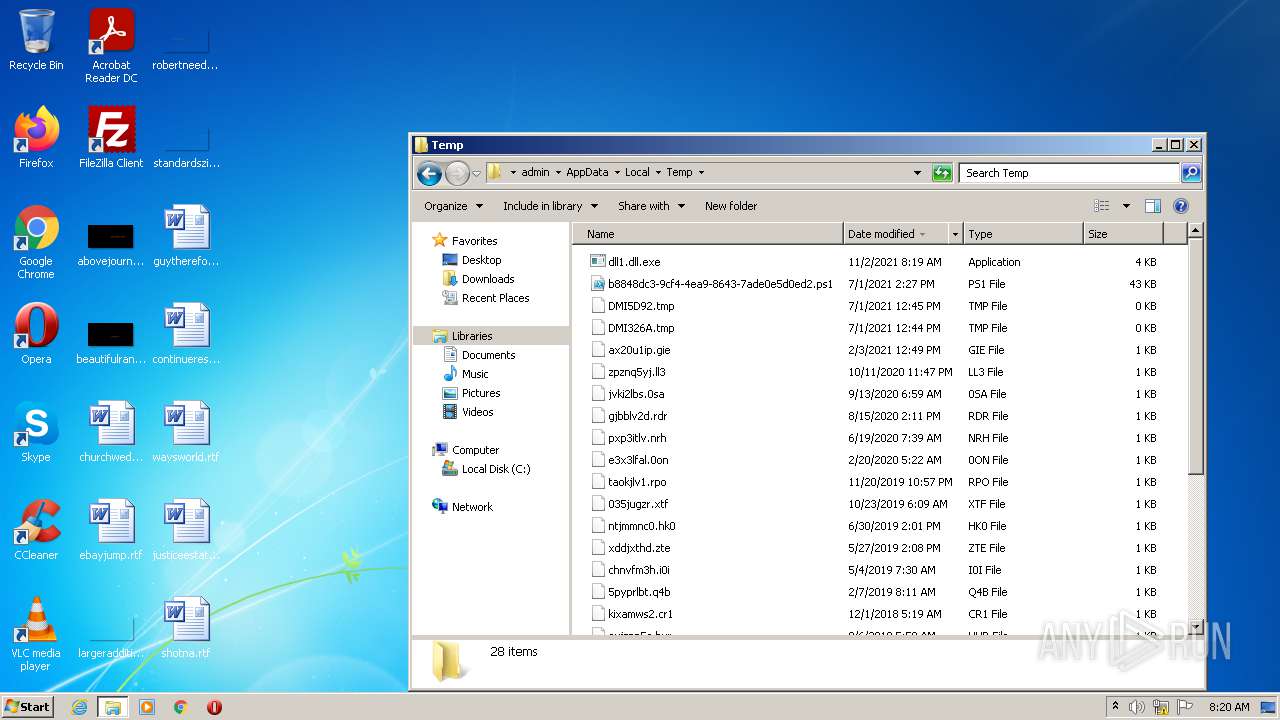
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2772 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRACB9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2772 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2772 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{592C3D10-ECA2-4835-B21D-947B1C427538}.tmp | dbf | |
MD5:— | SHA256:— | |||
| 2772 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{2955D710-1418-4BD0-8496-9EF1A931812C}.tmp | binary | |
MD5:— | SHA256:— | |||
| 2172 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:— | SHA256:— | |||
| 2772 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\churchwedding.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2772 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2772 | WINWORD.EXE | C:\Users\admin\Desktop\~$urchwedding.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2772 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{BB5C9E09-E7C8-461E-8F48-1836F54721F5}.tmp | smt | |
MD5:5D4D94EE7E06BBB0AF9584119797B23A | SHA256:4826C0D860AF884D3343CA6460B0006A7A2CE7DBCCC4D743208585D997CC5FD1 | |||
| 3300 | explorer.exe | C:\Users\admin\AppData\Local\Temp\dll1.dll.exe | executable | |
MD5:EAC8B09862160F6A0F35C4EF072FC330 | SHA256:EEEC187ABF1F05FE192198B6ACEE9ABDC3EF4CA4DCF3A09148566D46F33E085B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
regsvr32.exe | Hello qqq |
regsvr32.exe | Hello qqq |
regsvr32.exe | Hello qqq |
regsvr32.exe | Hello qqq |
regsvr32.exe | Hello qqq |
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|