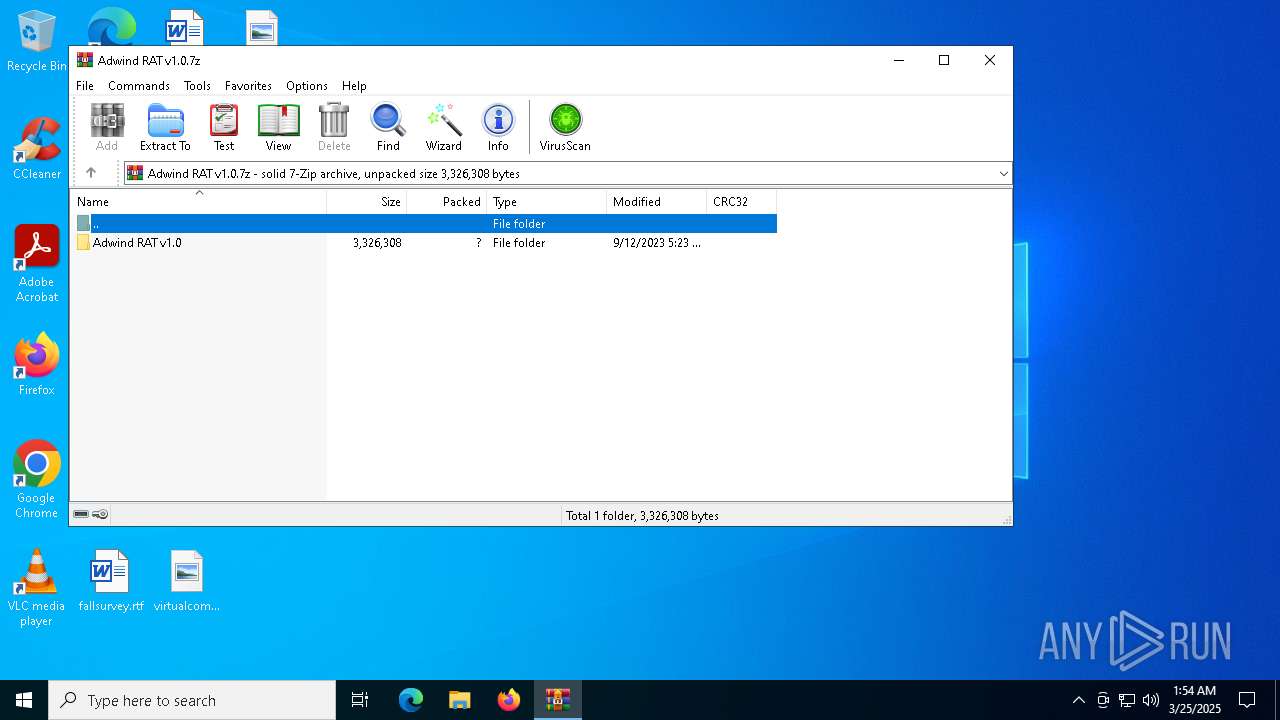
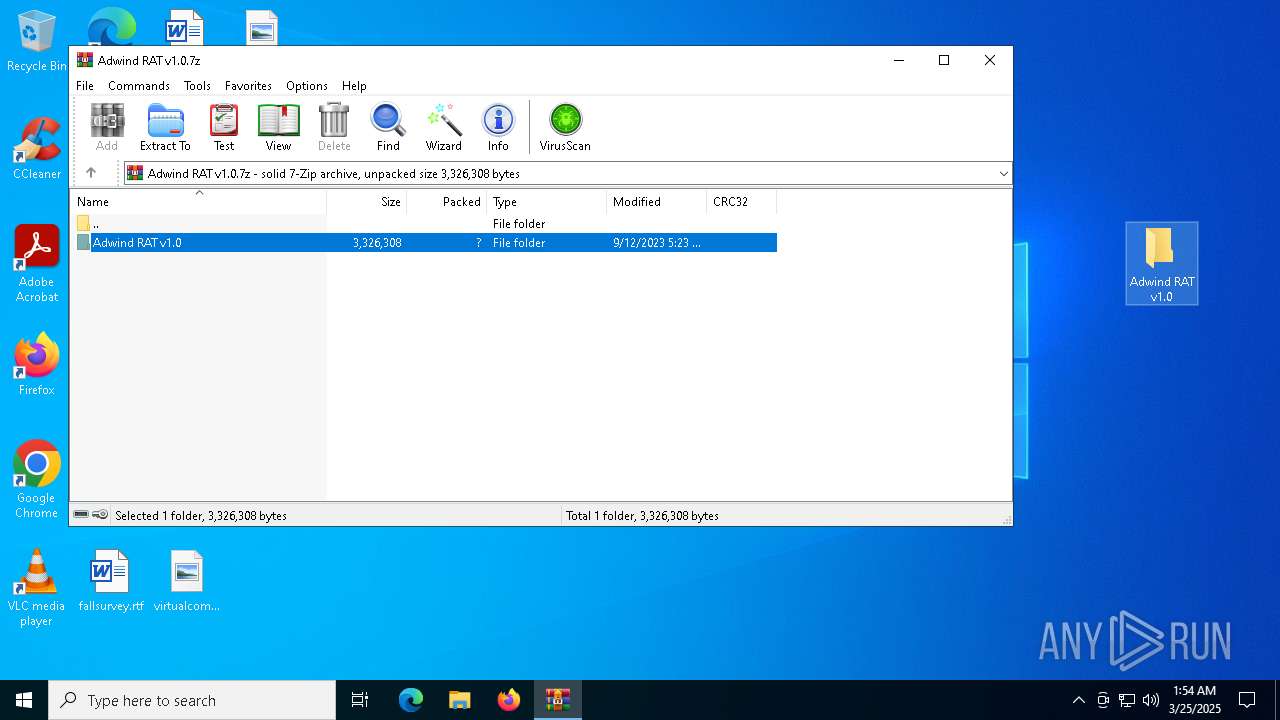
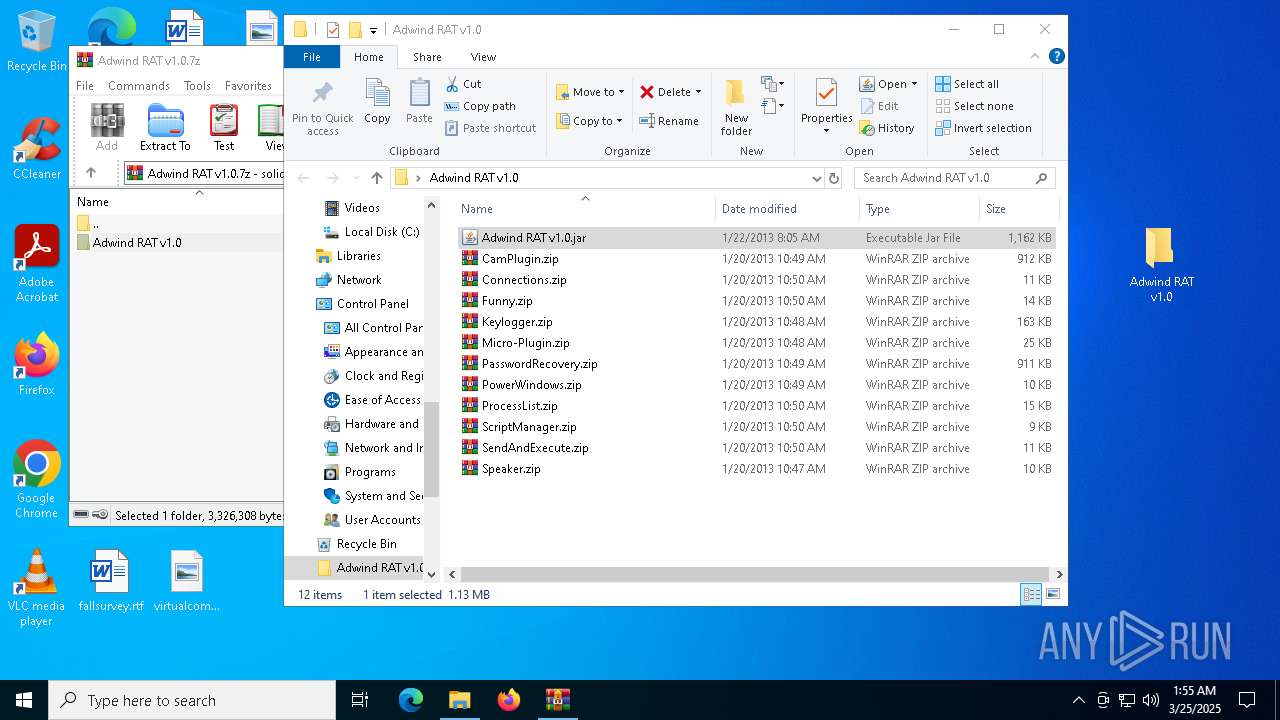
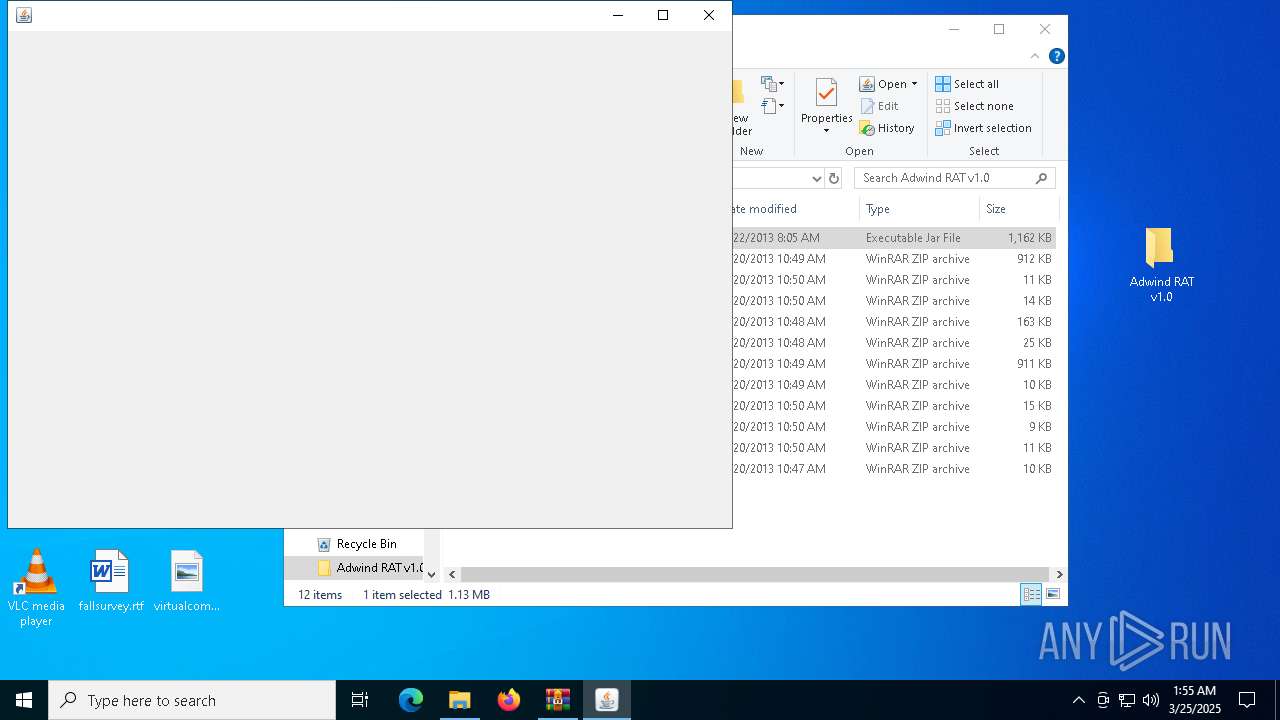
| File name: | Adwind RAT v1.0.7z |
| Full analysis: | https://app.any.run/tasks/308262a8-4ece-4c07-8e09-c6237bbd4104 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 01:54:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 1DDADE852B906DC4DAB30B97E5030B1B |
| SHA1: | 12AEC6FDA4FC4DDC300AD5D6D4D8252FC709F68D |
| SHA256: | 71A4862B661992BAC5689D8AC7E99D401F2396E2002AEE57C011BC501D033FF0 |
| SSDEEP: | 98304:HAEPBAJc0gxBa4ZGmqbAMrzSEu4ayZMs02MpWE/5Oo0J5zXieNA45RPJl9Vfe2GS:KYgh |
MALICIOUS
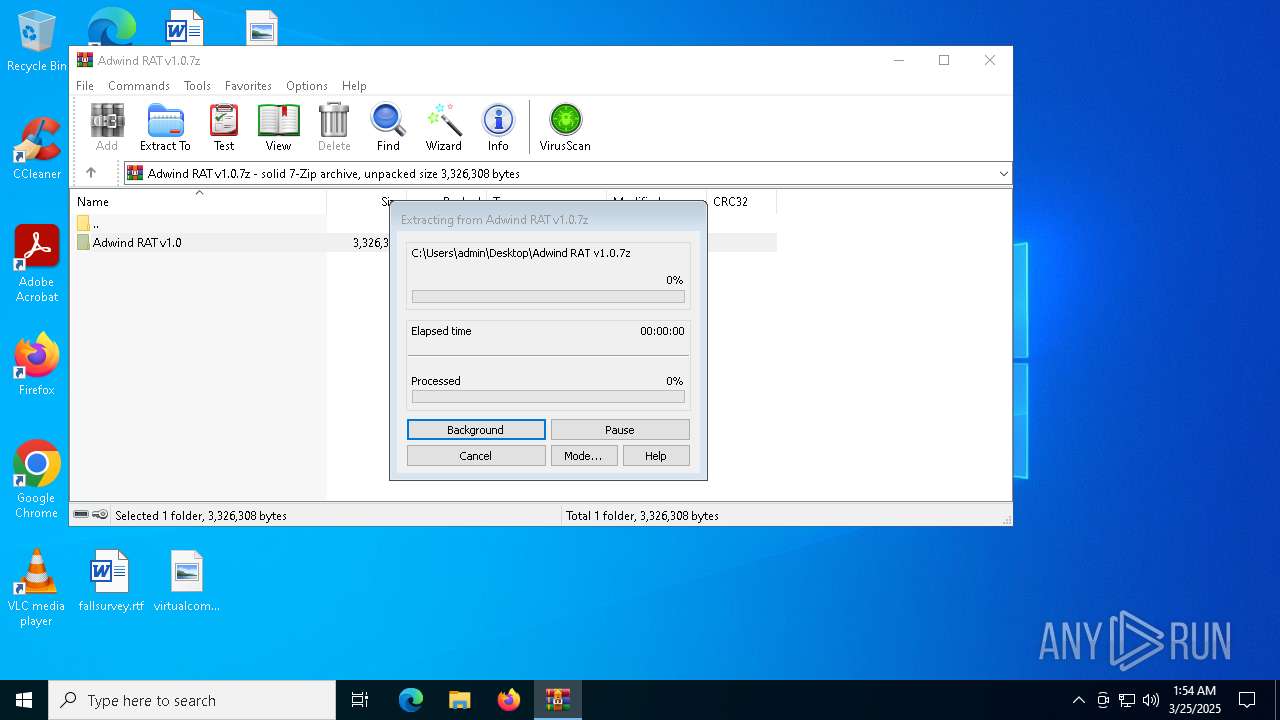
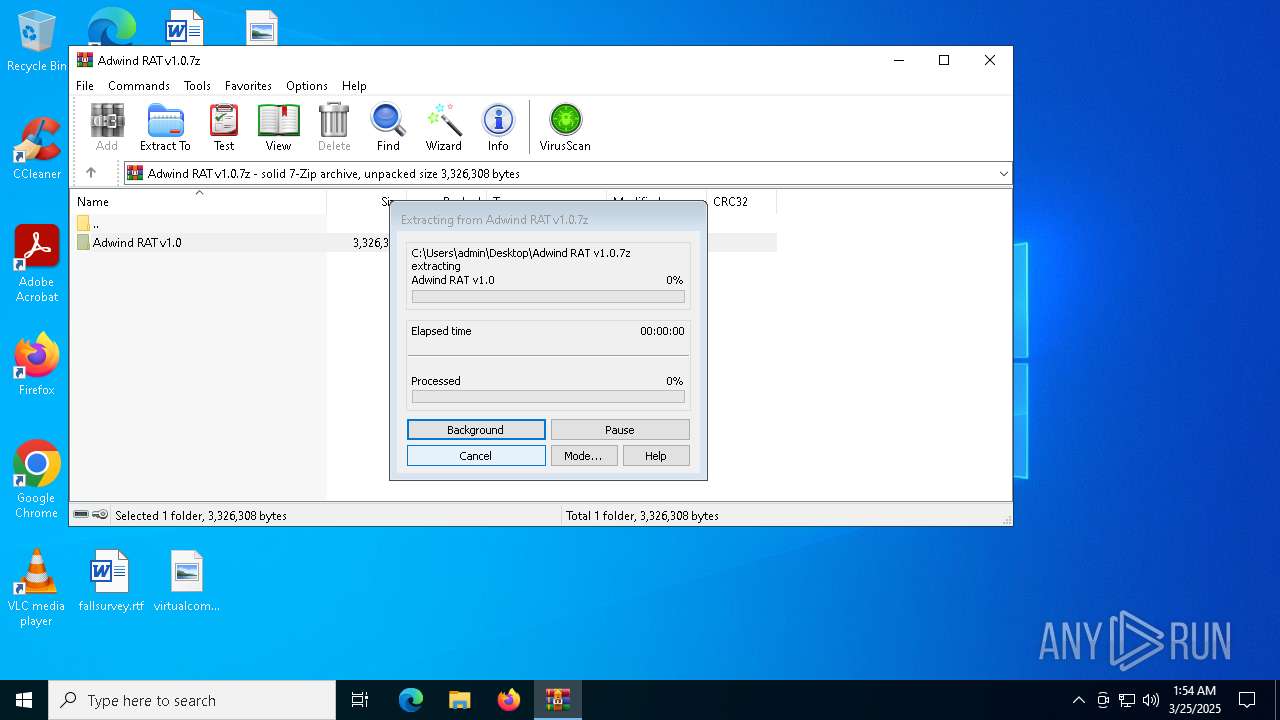
Generic archive extractor
- WinRAR.exe (PID: 7152)
SUSPICIOUS
No suspicious indicators.INFO
Creates files in the program directory
- javaw.exe (PID: 8108)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 8032)
Application based on Java
- javaw.exe (PID: 8108)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 8032)
Checks supported languages
- javaw.exe (PID: 8108)
Create files in a temporary directory
- javaw.exe (PID: 8108)
Reads the computer name
- javaw.exe (PID: 8108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2023:09:12 17:23:49+00:00 |
| ArchivedFileName: | Adwind RAT v1.0 |
Total processes
138
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7152 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Adwind RAT v1.0.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7224 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7244 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7276 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7952 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
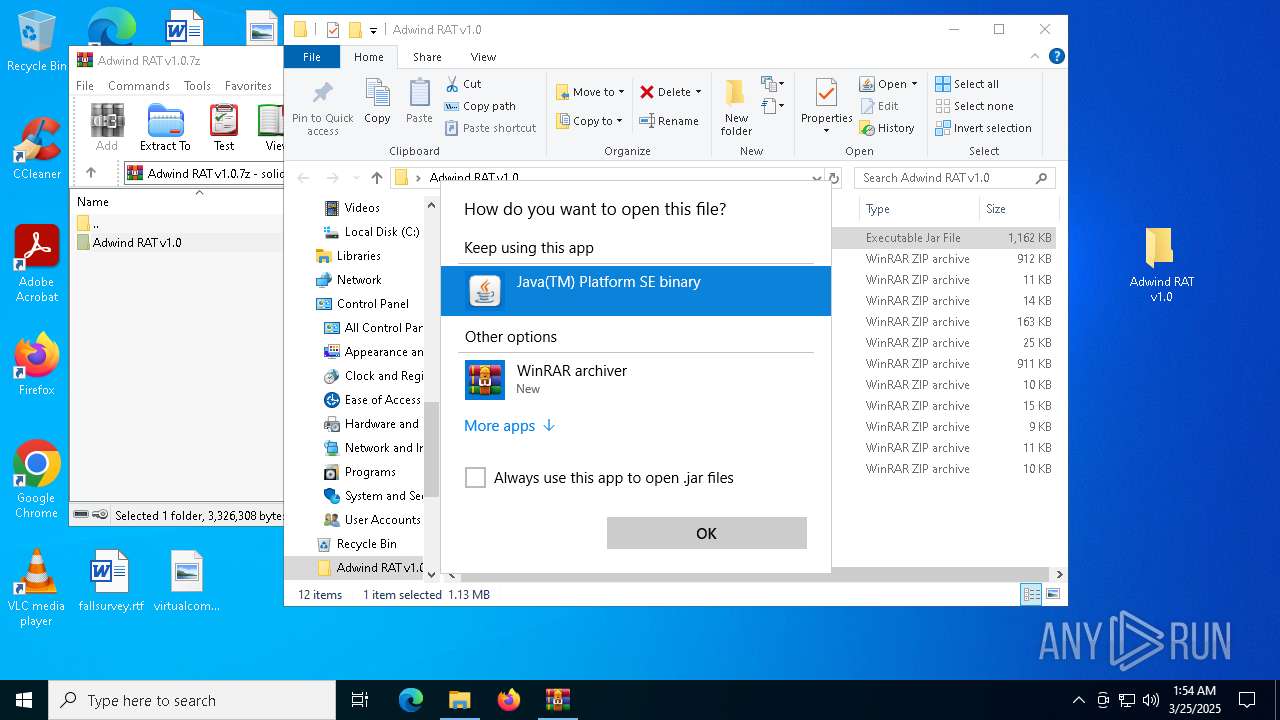
| 8032 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8108 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Users\admin\Desktop\Adwind RAT v1.0\Adwind RAT v1.0.jar" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | OpenWith.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Version: 8.0.2710.9 Modules
| |||||||||||||||
| 8188 | C:\WINDOWS\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 017
Read events
3 005
Write events
12
Delete events
0
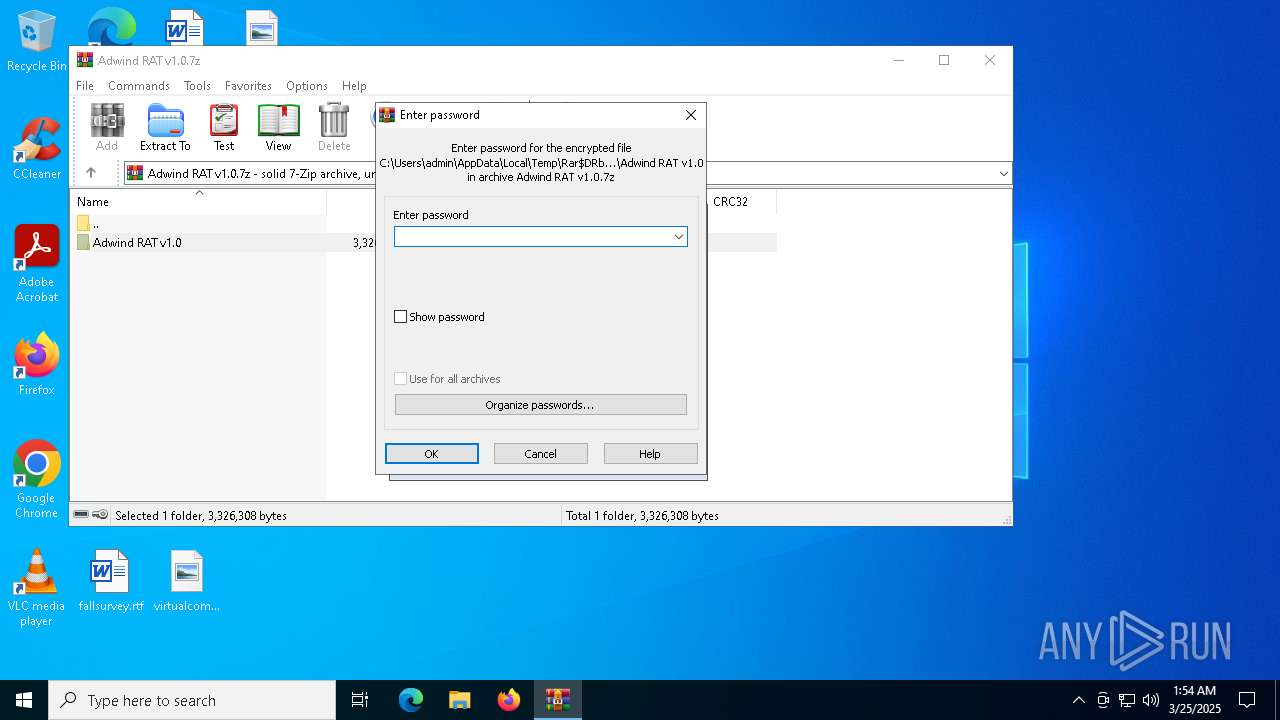
Modification events
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Adwind RAT v1.0.7z | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (8032) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jar\OpenWithProgids |
| Operation: | write | Name: | jarfile |
Value: | |||
Executable files
1
Suspicious files
11
Text files
1
Unknown types
0
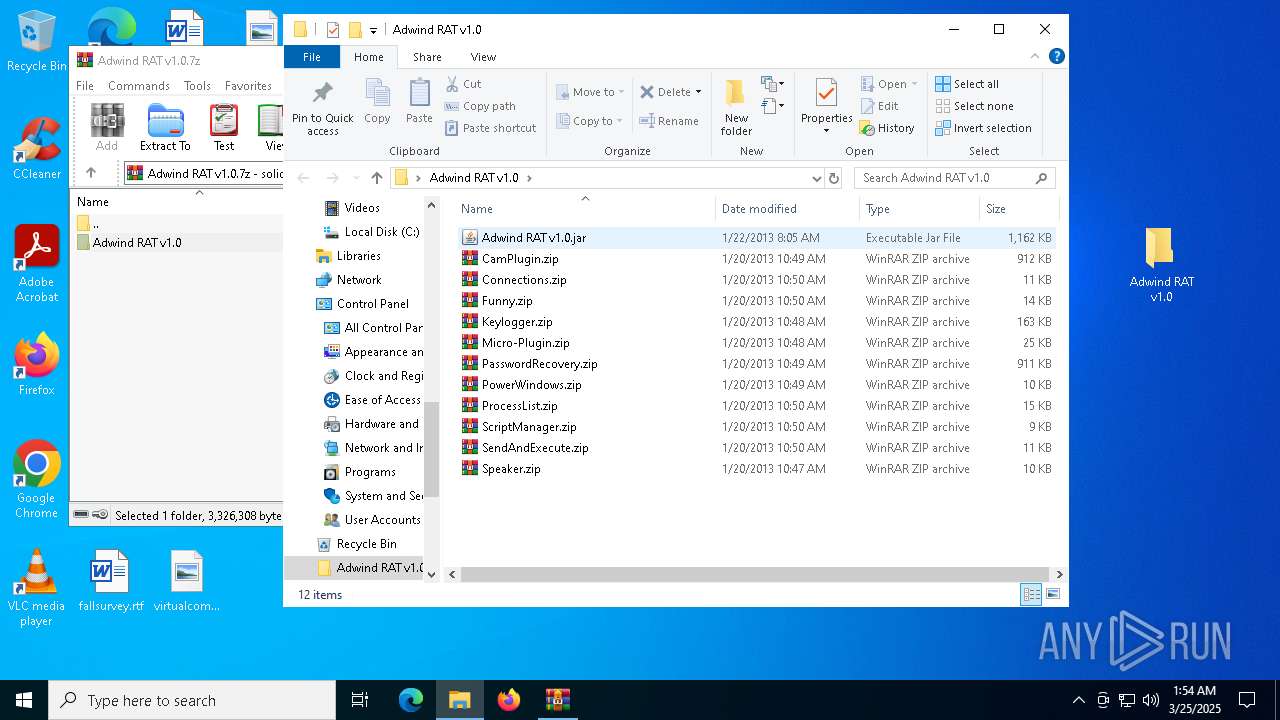
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7152.49987\Adwind RAT v1.0\Adwind RAT v1.0.jar | java | |
MD5:E1A0DC79B342B7CF707266BB6C36E59B | SHA256:42C07911058F30F9973EECFAB43F4FBDDEAC9BAA674464DB95E2D306E6CA6D80 | |||
| 7152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7152.49987\Adwind RAT v1.0\Keylogger.zip | compressed | |
MD5:26E586BDA49F5407E496D8B416269C83 | SHA256:36FB012C529900474CFCCC0D94806FAFAD7DDF97B94131635E1B05E1186A4AF5 | |||
| 7152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7152.49987\Adwind RAT v1.0\Funny.zip | compressed | |
MD5:149AA898D2EE8923A2D6C52325A95C73 | SHA256:AF0199FF7797D54A1D51526C25B97FA77DDE89BA8FE0C5FA3AF8F27626939A1D | |||
| 7152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7152.49987\Adwind RAT v1.0\PowerWindows.zip | compressed | |
MD5:675DE30F816F553893200EC8A8EB945D | SHA256:462F7C2C7C25F8BAA05BBE3EDE97AA6C293D6D9DC9A33896F81D4C1C64B39463 | |||
| 7152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7152.49987\Adwind RAT v1.0\PasswordRecovery.zip | compressed | |
MD5:E157F09FE3BEAC8DCFECBB1B99144854 | SHA256:8A04B410E94F6CC878B27A99D38EF2EE5B80A7B1A41A70D36F9F0EE94DBA2902 | |||
| 7152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7152.49987\Adwind RAT v1.0\ProcessList.zip | compressed | |
MD5:120531A5B810FD542F0F863A1E5B74AA | SHA256:C73DB0AF417EA74337278047A2CC7C22E1878B1BC22A9BE52CD6245A58B4ADED | |||
| 7152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7152.49987\Adwind RAT v1.0\CamPlugin.zip | compressed | |
MD5:1E1CF058144AA7200A225DC964BA3979 | SHA256:8991654787C7E81C7E98C1DFD32154E88303793DC55986BA18695B46B5FE3EE5 | |||
| 7152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7152.49987\Adwind RAT v1.0\Connections.zip | compressed | |
MD5:80B577307D01156660B61981431FE950 | SHA256:A2A2A561CC683CEECE80D8C5815D950C76ABC2188D6CE8D7FE178D945FD6E3F6 | |||
| 7152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7152.49987\Adwind RAT v1.0\ScriptManager.zip | compressed | |
MD5:D12AFEB24D2D6C0C8787D13D221E878F | SHA256:7114B716BC578981FD8D64696F6232FB23C1A2BD58E228AFD2EDC21FC30D3972 | |||
| 7152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7152.49987\Adwind RAT v1.0\SendAndExecute.zip | compressed | |
MD5:8200558866CA60560EAF7C3895191FF0 | SHA256:7DC8391C2FBC755052B64B0C7C044C52309AEB5AD01FA56E5615145785CE727A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.22.242.121:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5404 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5404 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5544 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.22.242.121:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.31.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5544 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |