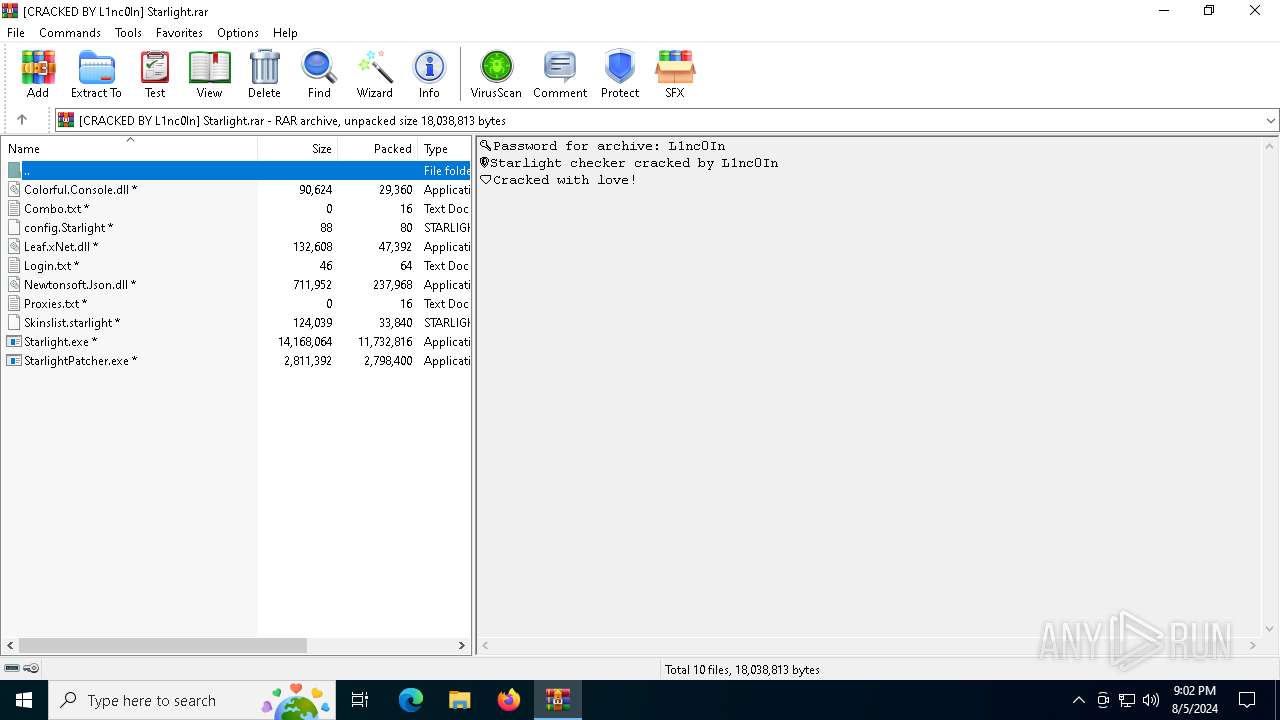
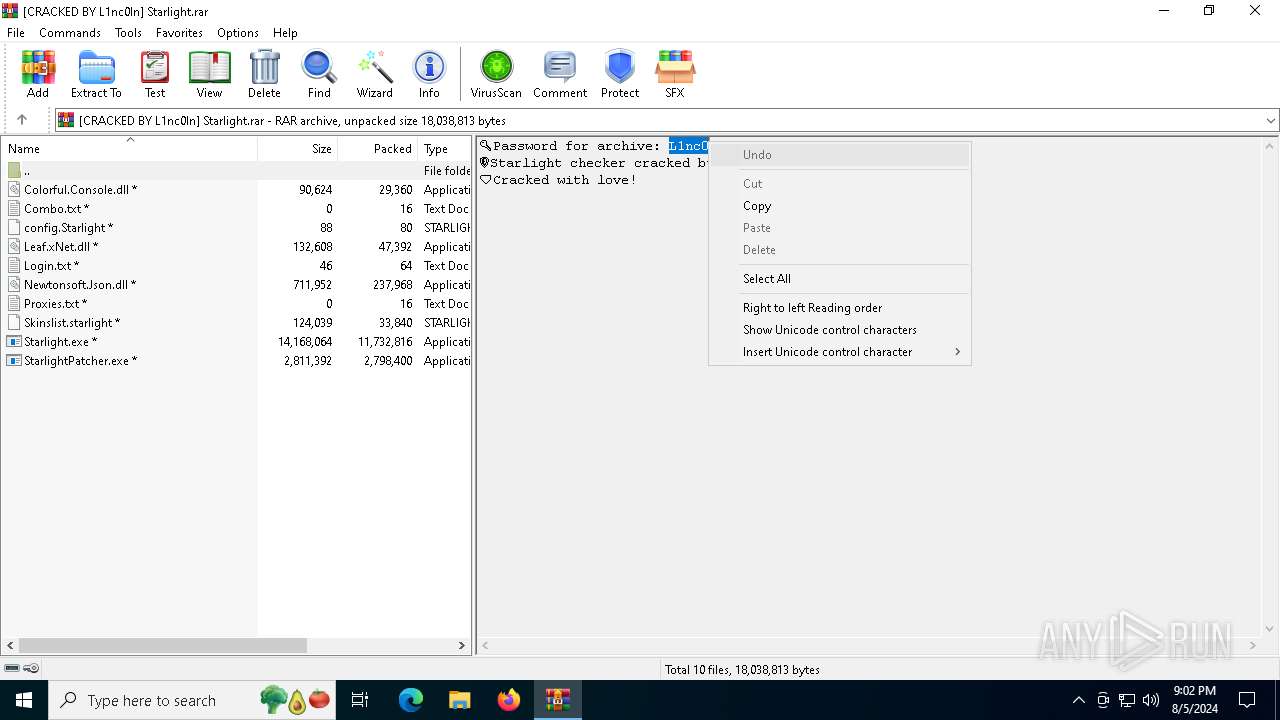
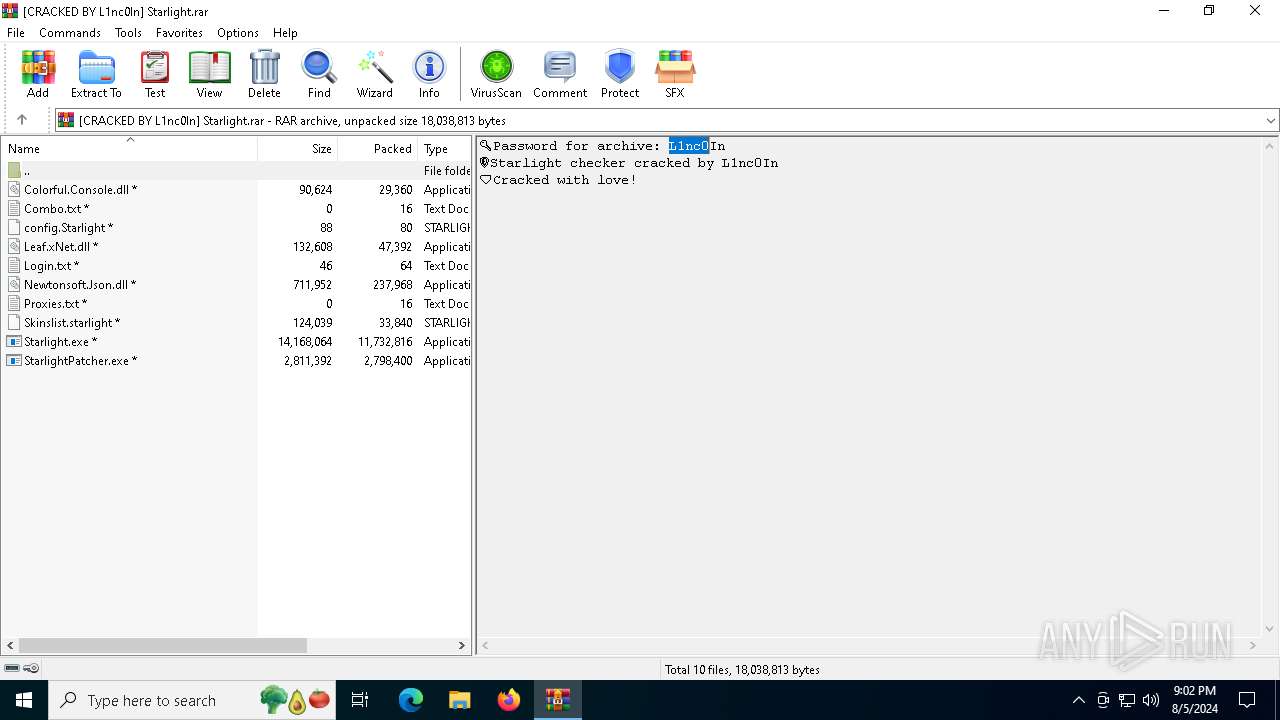
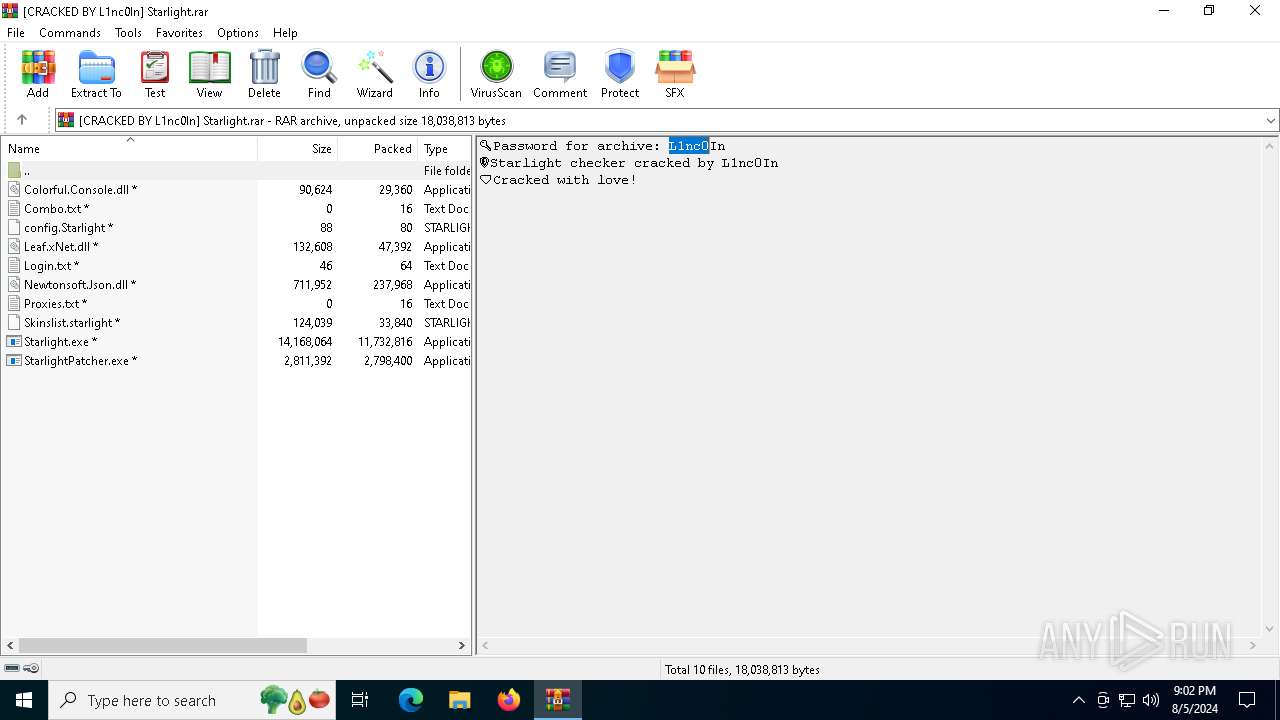
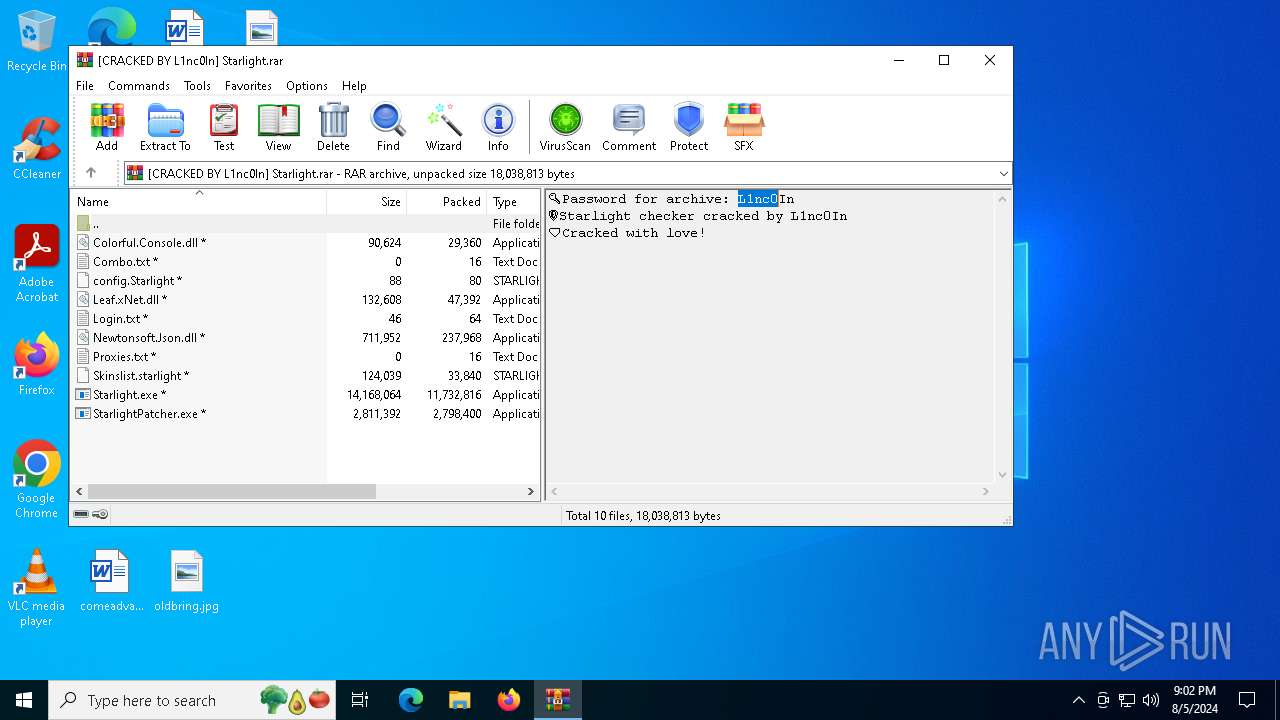
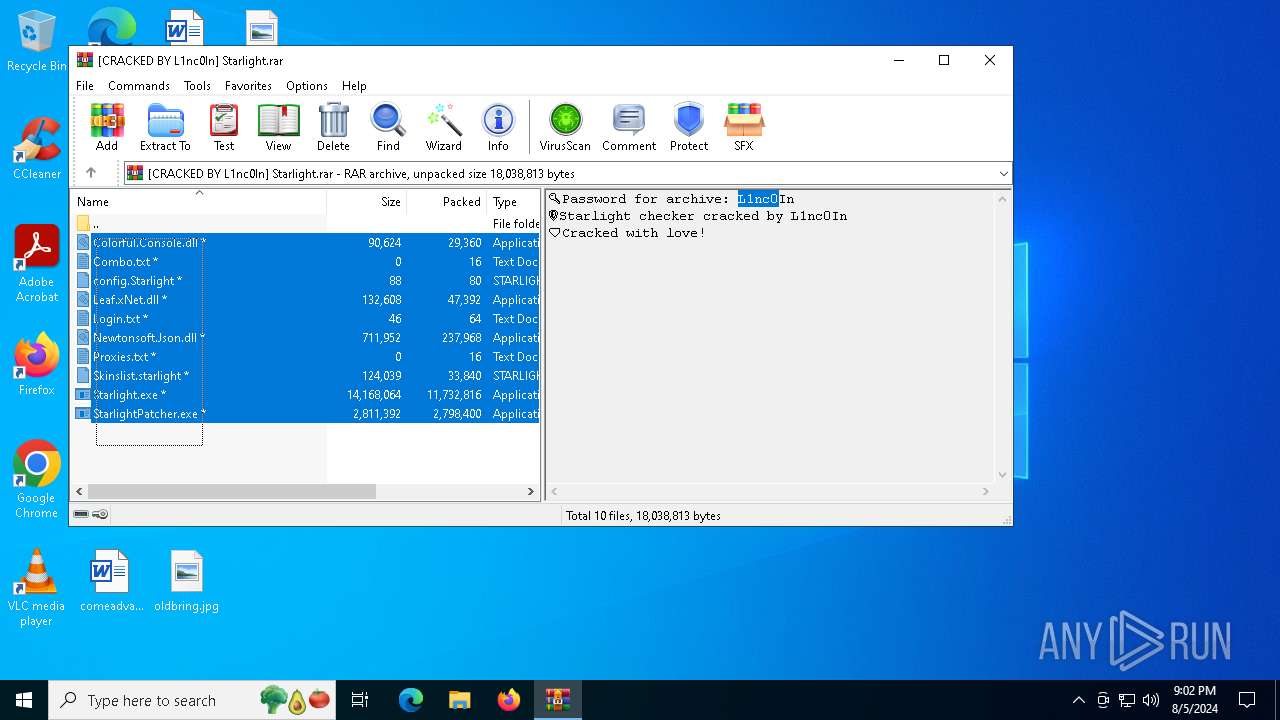
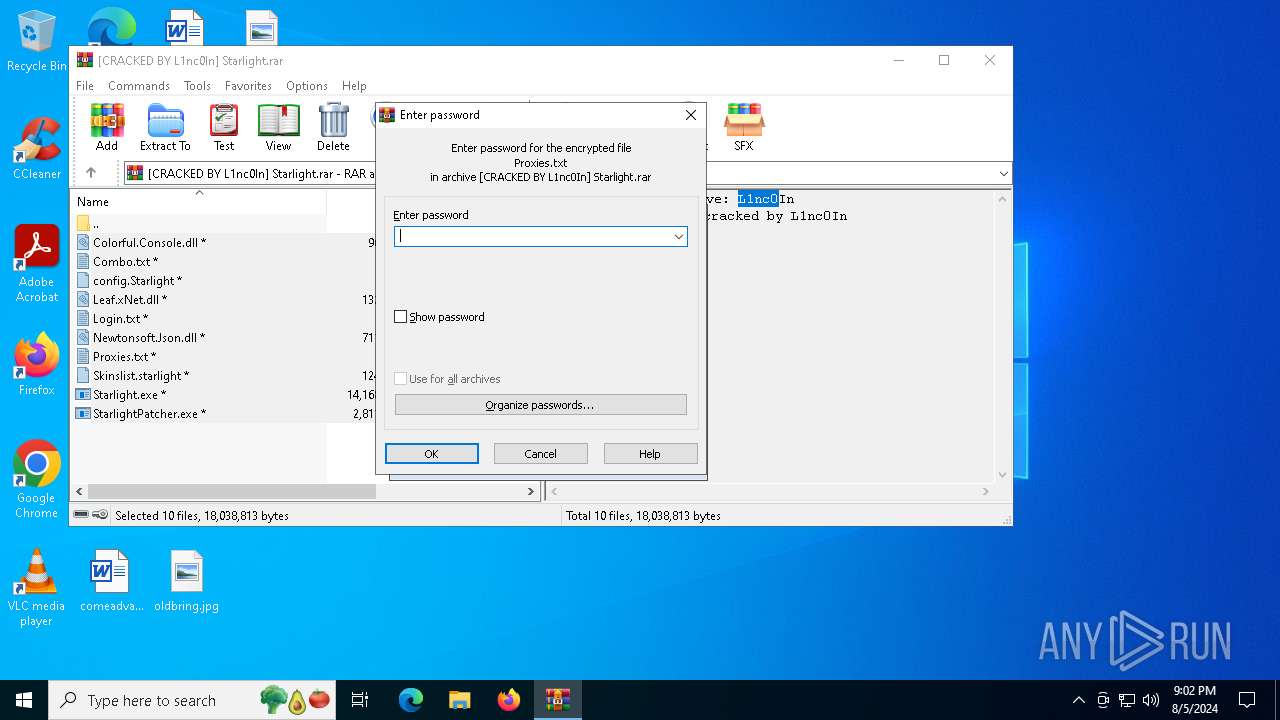
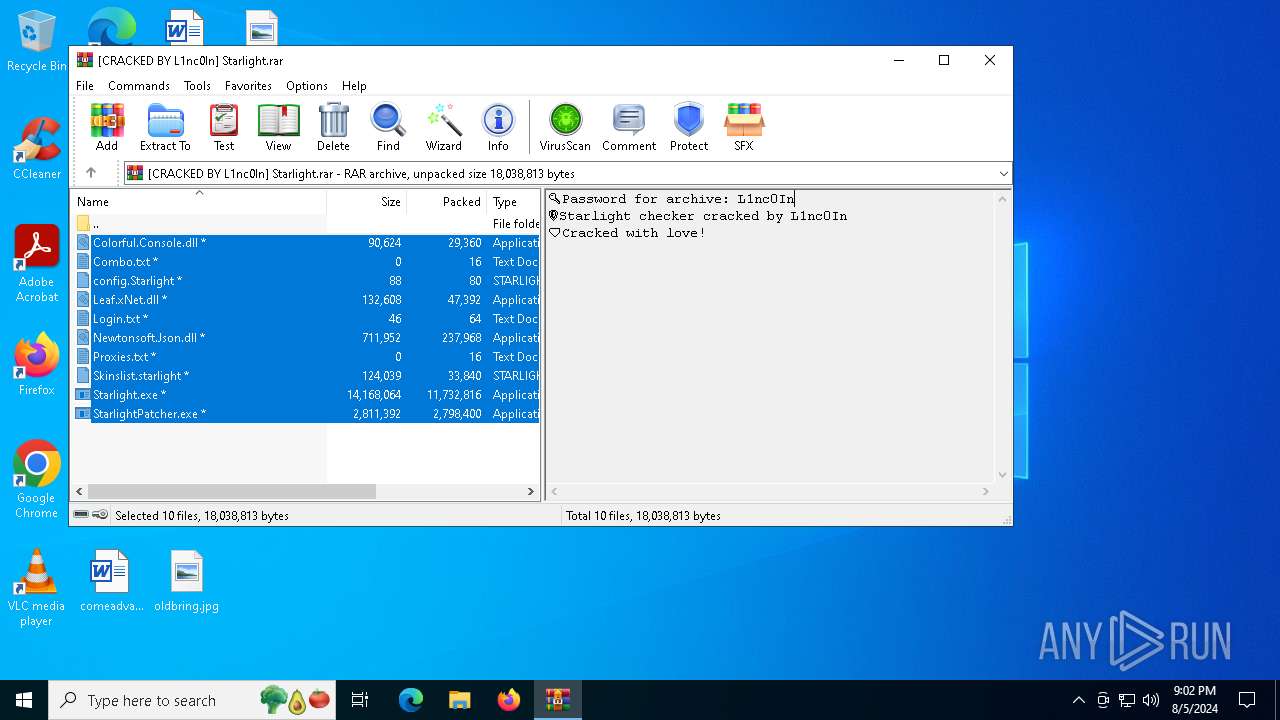
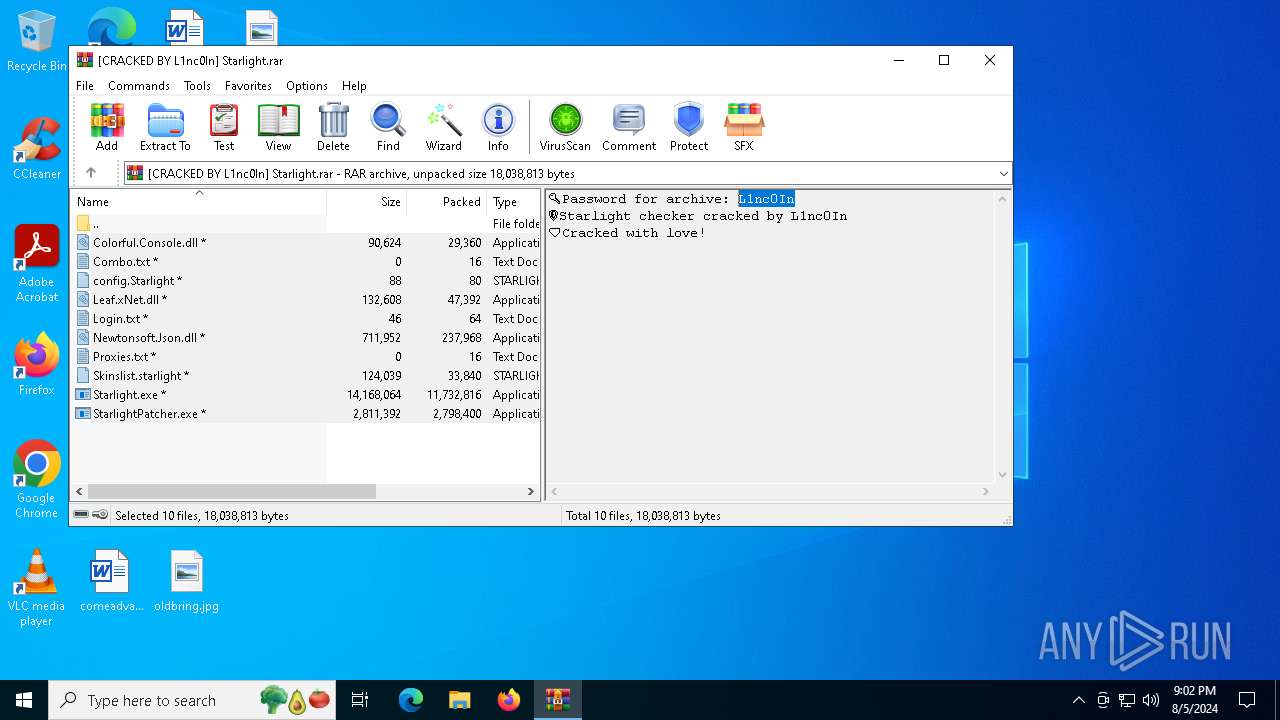
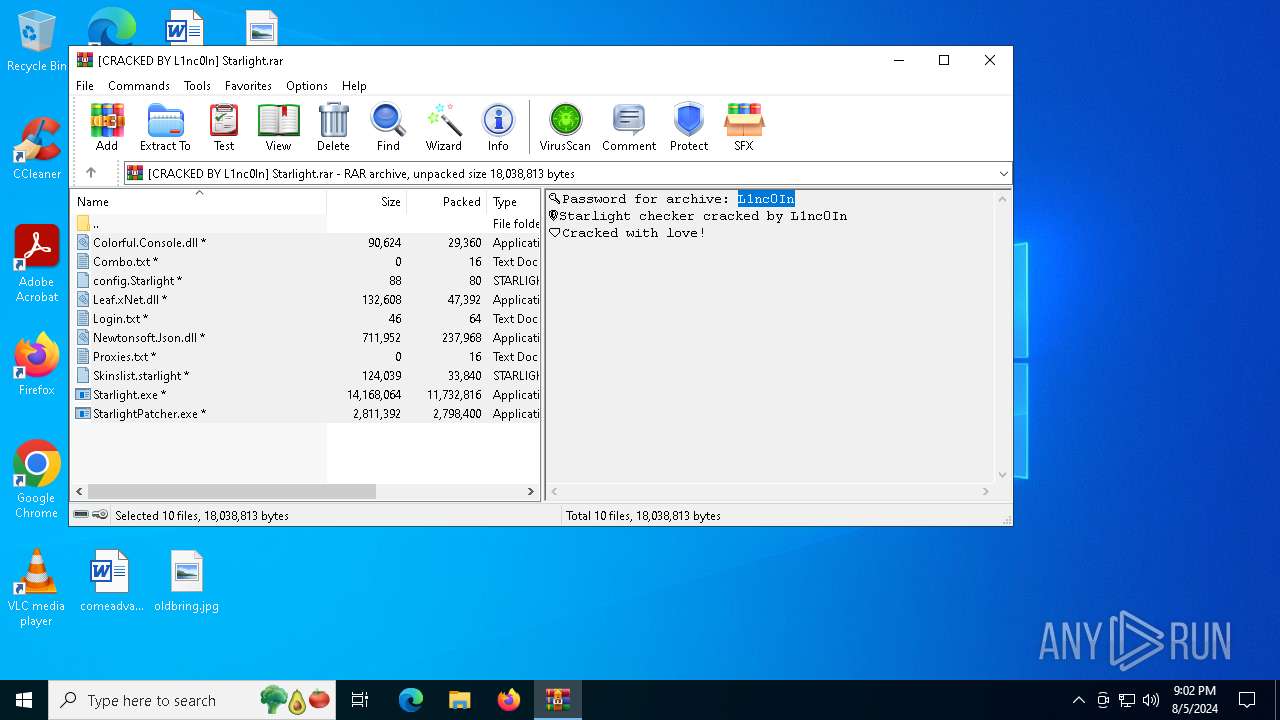
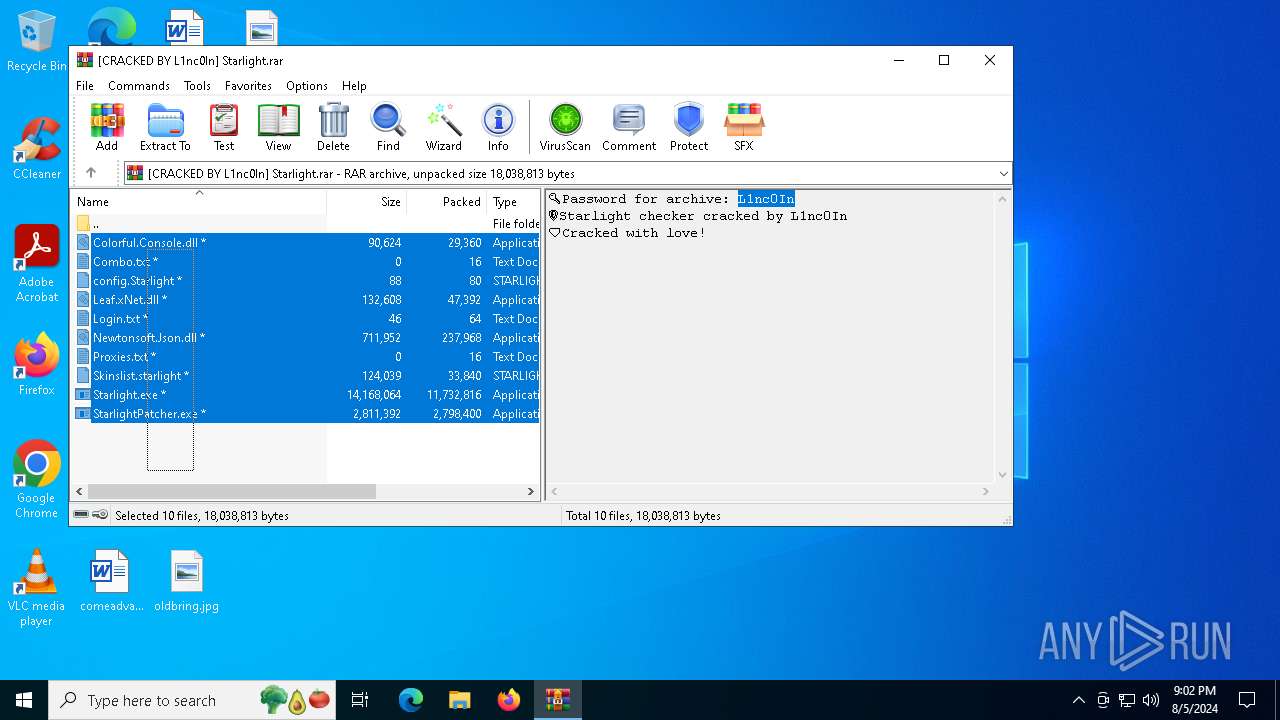
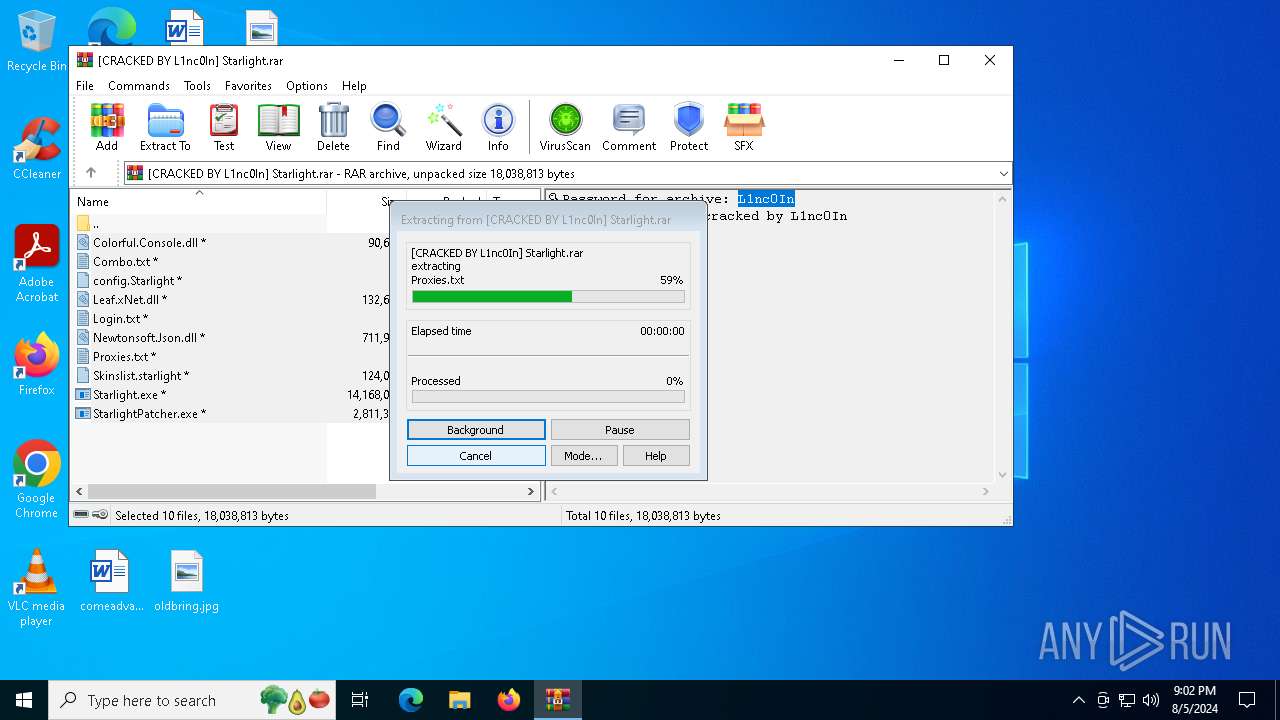
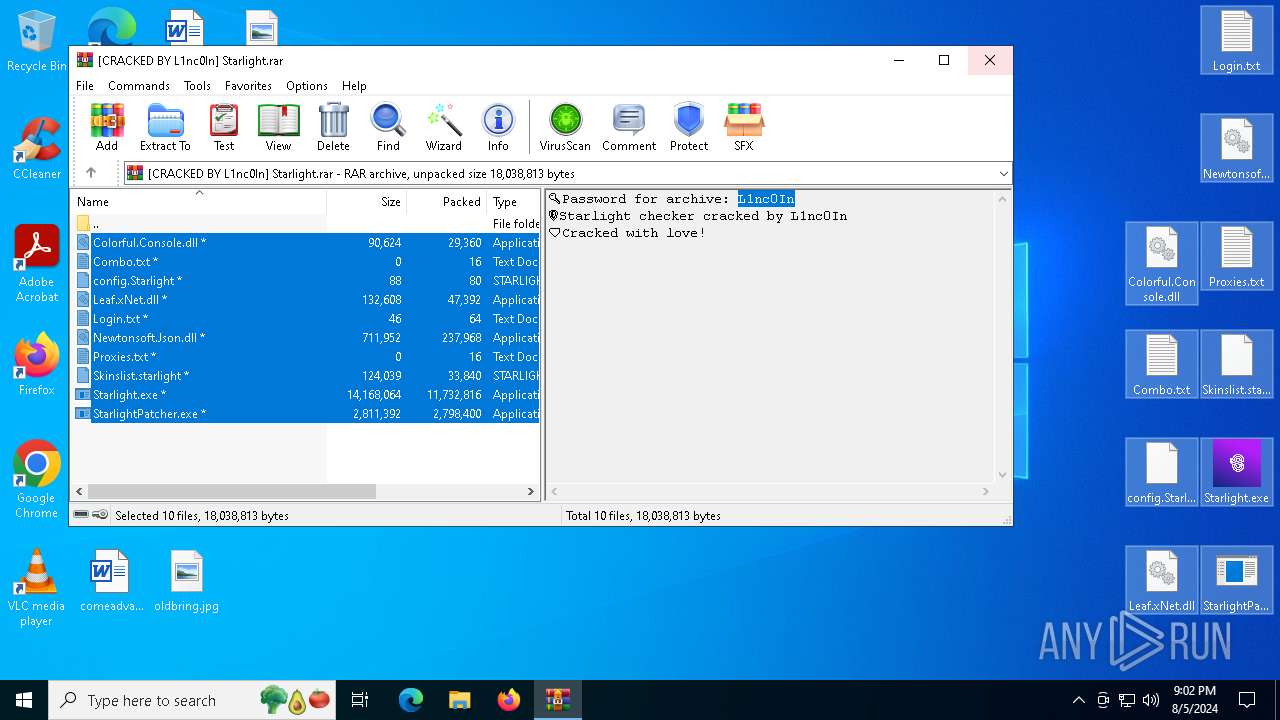
| File name: | [CRACKED BY L1nc0In] Starlight.rar |
| Full analysis: | https://app.any.run/tasks/7b1adb20-e669-4e13-bf5b-53e00cf3b705 |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2024, 21:02:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 243024505A3A48089DED0BA60E8524AE |
| SHA1: | 34FA2F296C0EB2C3F70E4C9E2709D7F592B3A0D4 |
| SHA256: | 719F0600D92E06801D31922E685389A8A70F86B2739FE9C417DB7FFCC4AA72E9 |
| SSDEEP: | 196608:MuI86XYJhl79sC1HXu2fFymxveiB7nLJd:esJhl7N1HXpyeeiB7L |
MALICIOUS
Drops the executable file immediately after the start
- Starlight.exe (PID: 6288)
SUSPICIOUS
Executable content was dropped or overwritten
- Starlight.exe (PID: 6288)
Reads the BIOS version
- StarlightPatcher.exe (PID: 3476)
- Starlight.exe (PID: 6288)
INFO
Checks supported languages
- Starlight.exe (PID: 6288)
- StarlightPatcher.exe (PID: 3476)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6468)
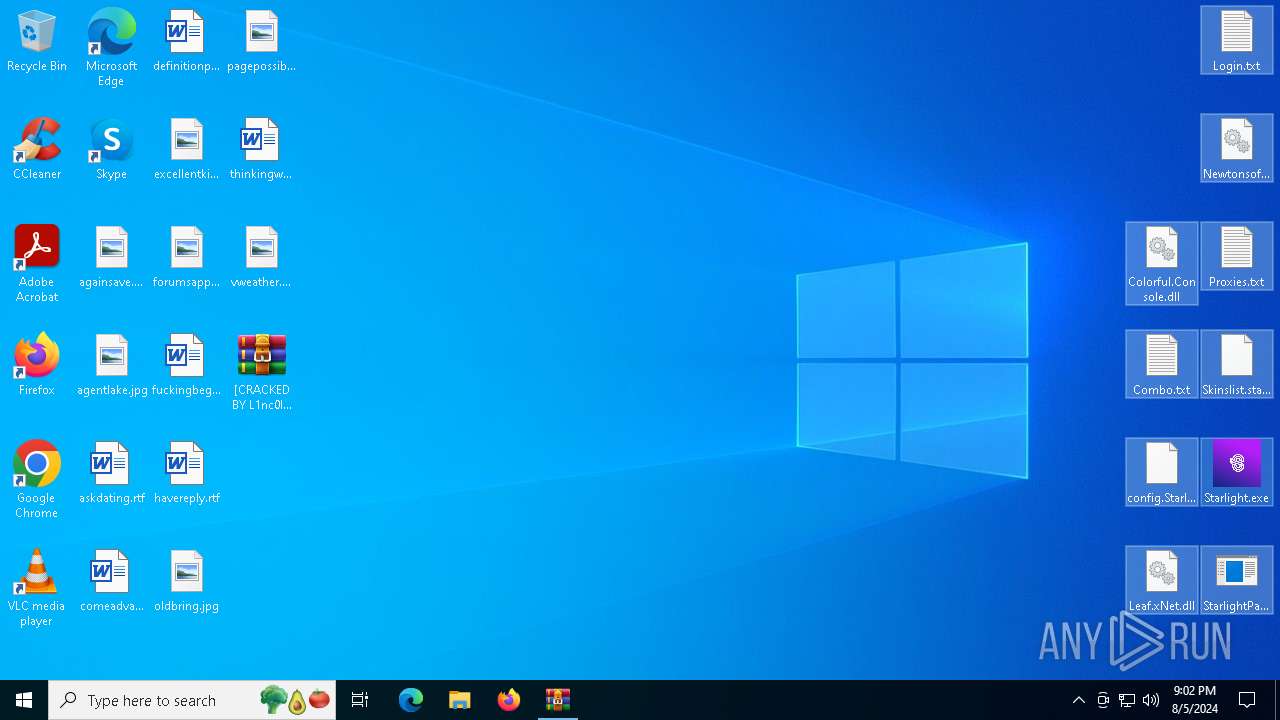
Manual execution by a user
- Starlight.exe (PID: 6288)
- StarlightPatcher.exe (PID: 3476)
- notepad.exe (PID: 3372)
Reads security settings of Internet Explorer
- notepad.exe (PID: 3372)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6468)
Reads the machine GUID from the registry
- Starlight.exe (PID: 6288)
Create files in a temporary directory
- Starlight.exe (PID: 6288)
Reads Environment values
- Starlight.exe (PID: 6288)
Reads the computer name
- Starlight.exe (PID: 6288)
Themida protector has been detected
- StarlightPatcher.exe (PID: 3476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
137
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3372 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Proxies.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
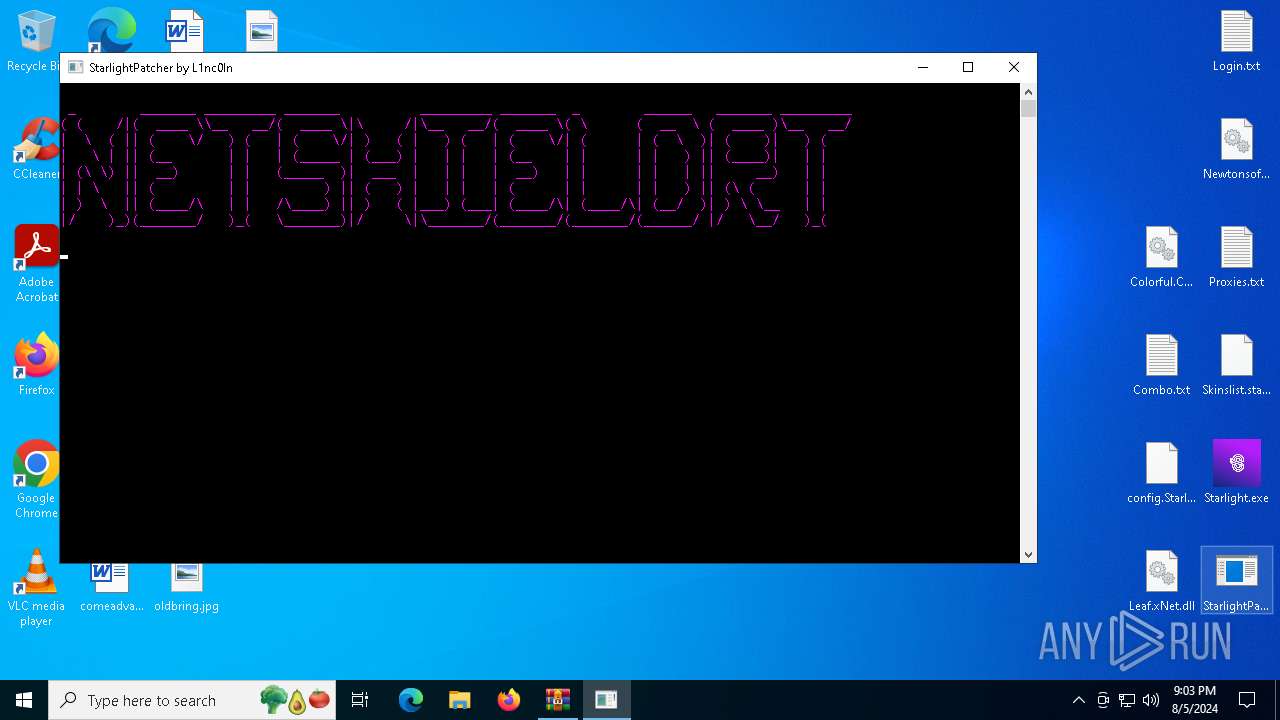
| 3476 | "C:\Users\admin\Desktop\StarlightPatcher.exe" | C:\Users\admin\Desktop\StarlightPatcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | StarlightPatcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6288 | "C:\Users\admin\Desktop\Starlight.exe" | C:\Users\admin\Desktop\Starlight.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: StarlightFNCLR Exit code: 3221225786 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6468 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\[CRACKED BY L1nc0In] Starlight.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7112 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Starlight.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 603
Read events
4 592
Write events
11
Delete events
0
Modification events
| (PID) Process: | (6468) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6468) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6468) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6468) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\[CRACKED BY L1nc0In] Starlight.rar | |||
| (PID) Process: | (6468) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6468) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6468) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6468) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
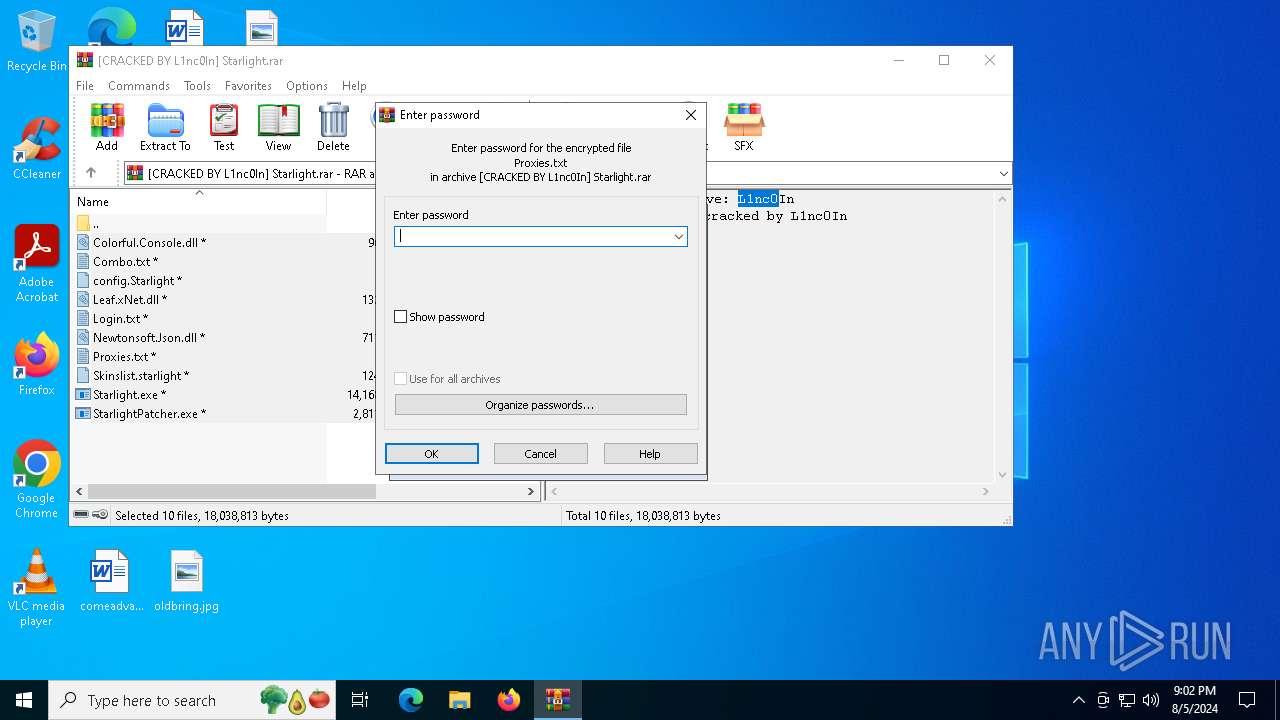
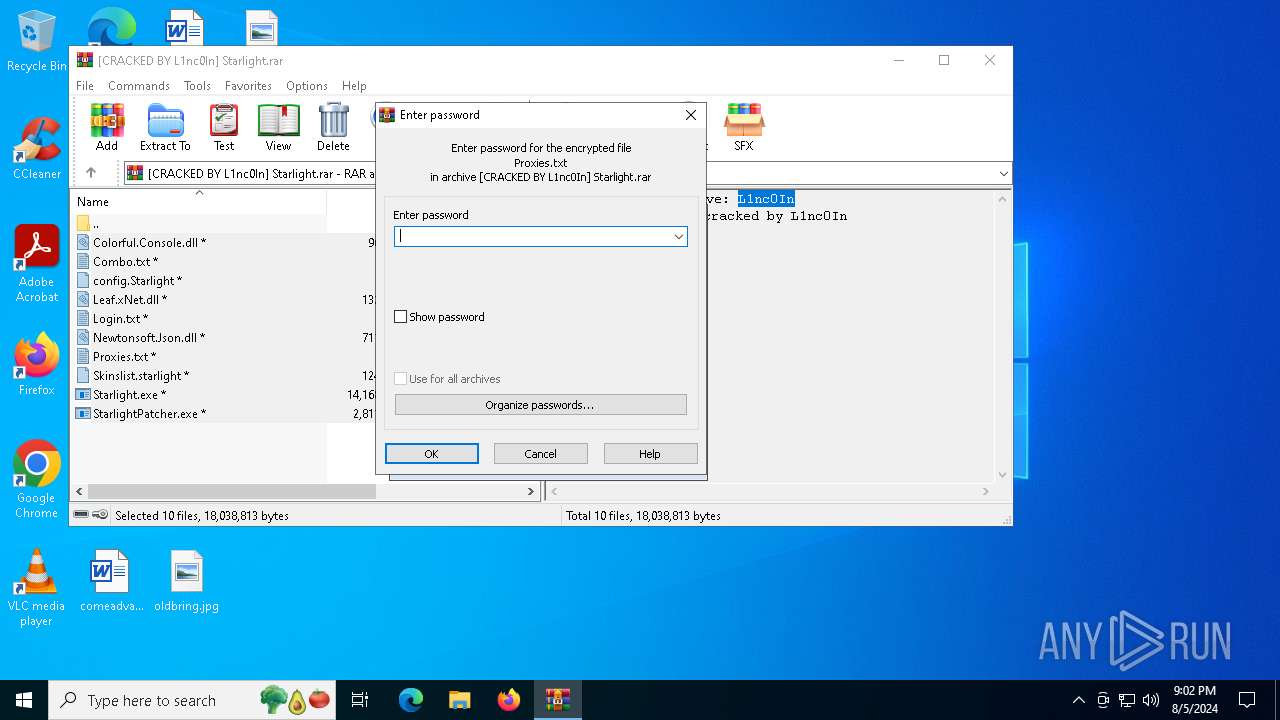
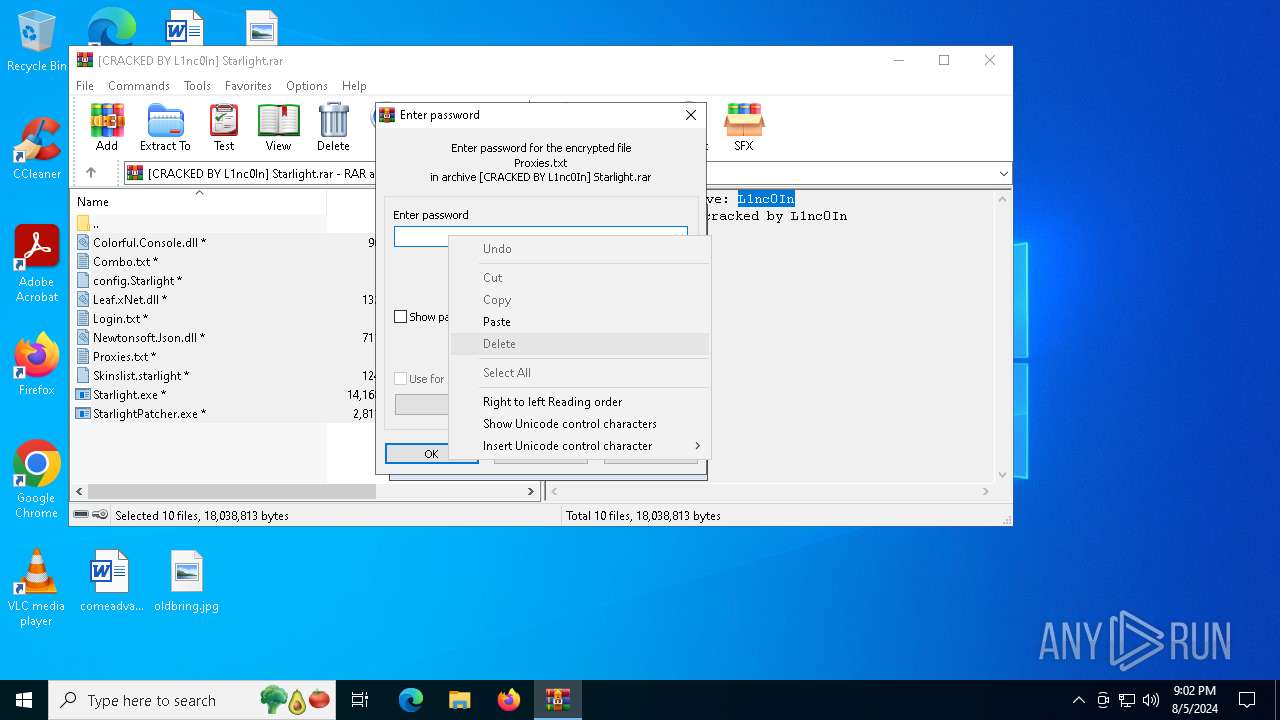
| (PID) Process: | (6468) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
10
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6468.8370\Skinslist.starlight | text | |
MD5:4386679D6567D45BCE383B72EF29D5E7 | SHA256:BCF7F541B2D67147C3578002DEF6EC38E146D204C5F3F0A5FD0AA5D7372FC34E | |||
| 6468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6468.8370\Starlight.exe | executable | |
MD5:AF03BC61B9AF79803D90E927E01047A8 | SHA256:59FC924B6B8BD373E06137EF7446CE049D6329311D71ECA08D23DFE4C9E5205F | |||
| 6468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6468.8370\config.Starlight | text | |
MD5:4BFA15E9422440C67B1D9E1F0069A7BC | SHA256:5AC3C029C8B7E29C42C63139A525298AA2AE076020C2FA455F4DD6FDD50C9C10 | |||
| 6468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6468.8370\StarlightPatcher.exe | executable | |
MD5:4930131FAC6FCD61F5194ADD476C4952 | SHA256:0C860B47B748394CAC11E33D575B57A939DCCD41C096F8DDBCF6C291E671DEF1 | |||
| 6468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6468.8370\Leaf.xNet.dll | executable | |
MD5:EA87F37E78FB9AF4BF805F6E958F68F4 | SHA256:DE9AEA105F31F3541CBC5C460B0160D0689A2872D80748CA1456E6E223F0A4AA | |||
| 6468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6468.8370\Colorful.Console.dll | executable | |
MD5:9F6CE7FF934FB2E786CED3516705EFAD | SHA256:59A3696950AC3525E31CDD26727DABD9FECD2E1BDC1C47C370D4B04420592436 | |||
| 6288 | Starlight.exe | C:\Users\admin\AppData\Local\Temp\evbFEA3.tmp | executable | |
MD5:E19F1AB63874138C99D0047C27D478D8 | SHA256:4DD8C4AC0E9B213FA9D160F893B170054934E43C9F9D58F5DA5193355422BD6A | |||
| 6288 | Starlight.exe | C:\Users\admin\AppData\Local\Temp\evbFE35.tmp | executable | |
MD5:26FC5802D3DA1539A5B4A4E9D1C0BE94 | SHA256:D1781882A8F4ED09D0F0237271A72522B7679ACA3112755C75F9B60E5DB18840 | |||
| 6288 | Starlight.exe | C:\Users\admin\AppData\Local\Temp\evbFE24.tmp | executable | |
MD5:26FC5802D3DA1539A5B4A4E9D1C0BE94 | SHA256:D1781882A8F4ED09D0F0237271A72522B7679ACA3112755C75F9B60E5DB18840 | |||
| 6468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6468.8370\Newtonsoft.Json.dll | executable | |
MD5:195FFB7167DB3219B217C4FD439EEDD6 | SHA256:E1E27AF7B07EEEDF5CE71A9255F0422816A6FC5849A483C6714E1B472044FA9D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
43
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4540 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4540 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6796 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6856 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3360 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1120 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3360 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5336 | SearchApp.exe | 2.23.209.133:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4540 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |