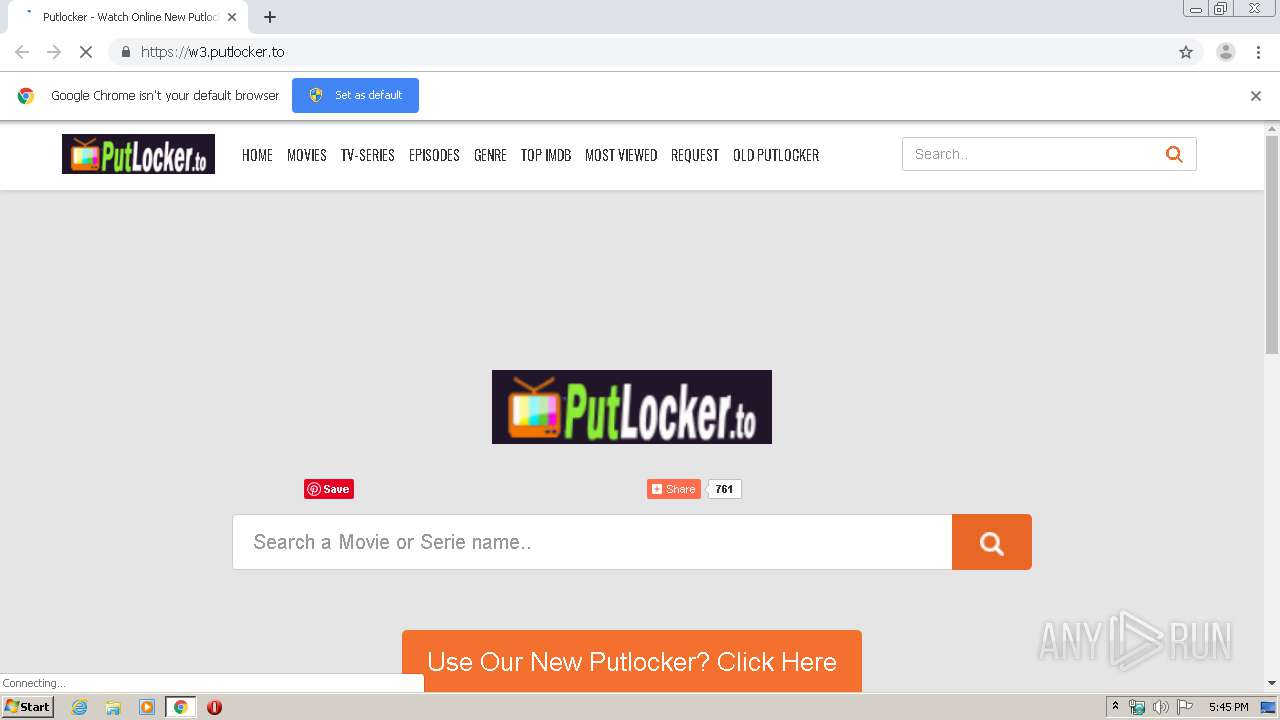
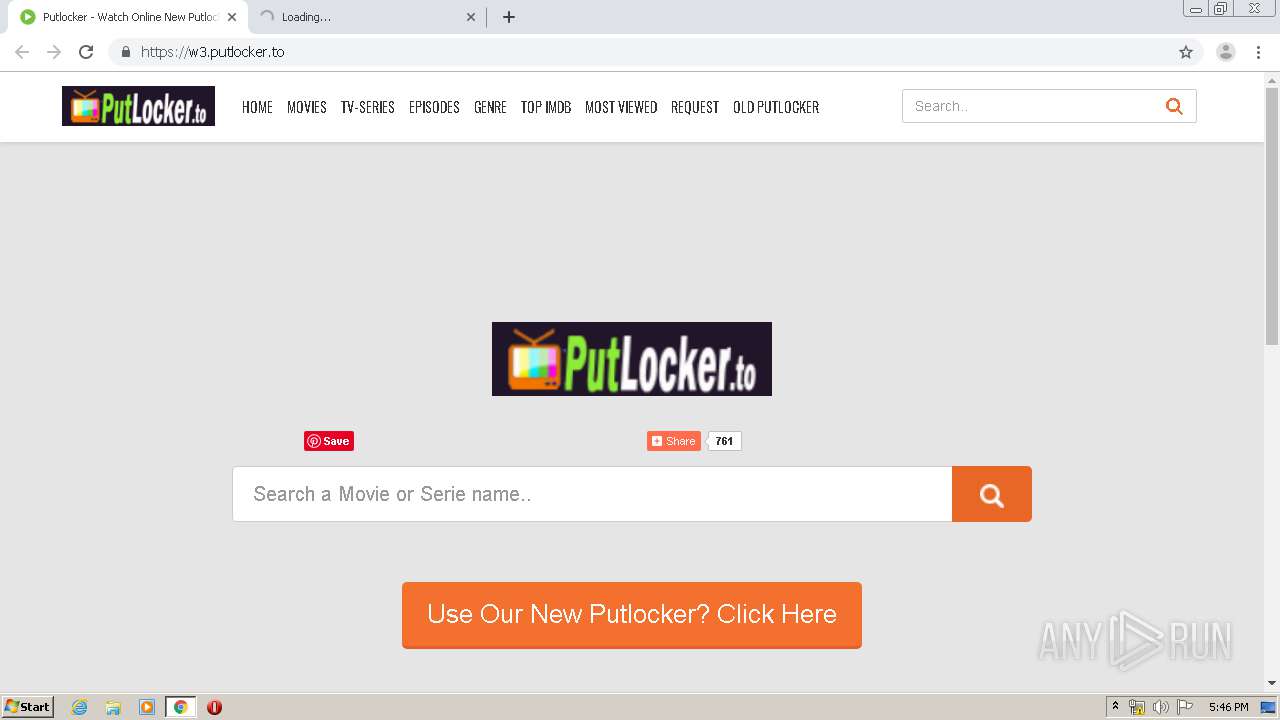
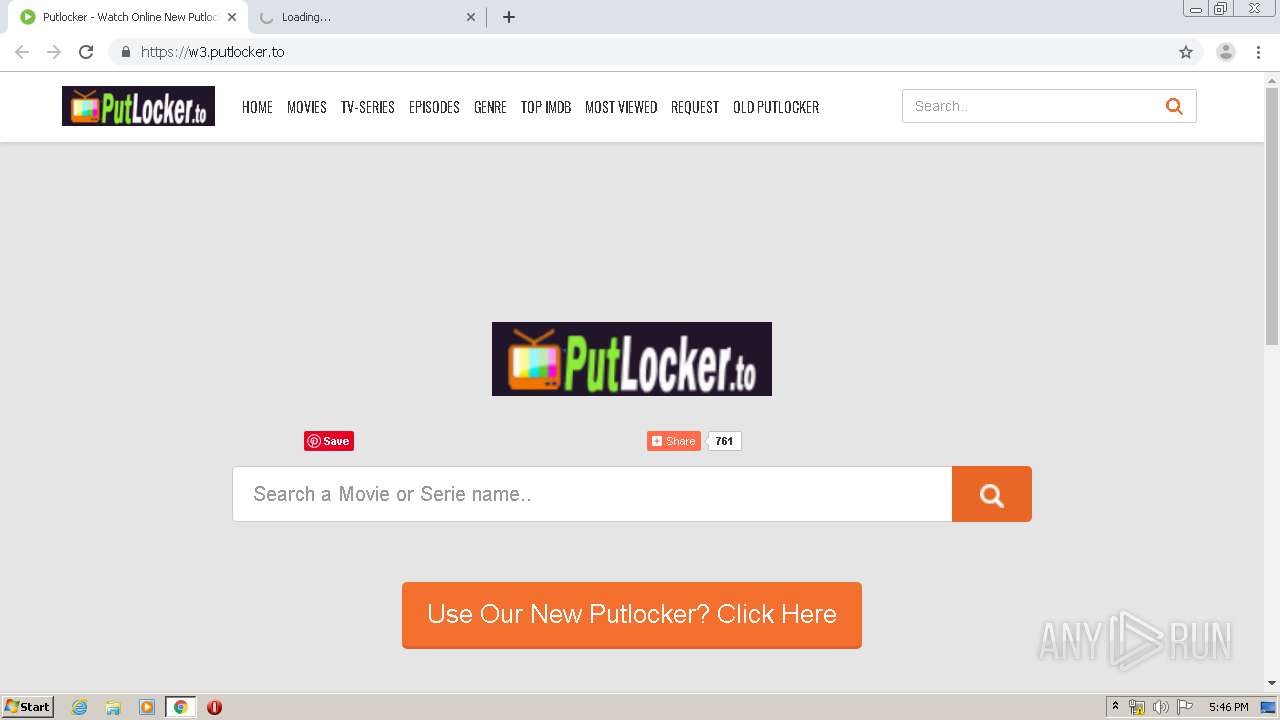
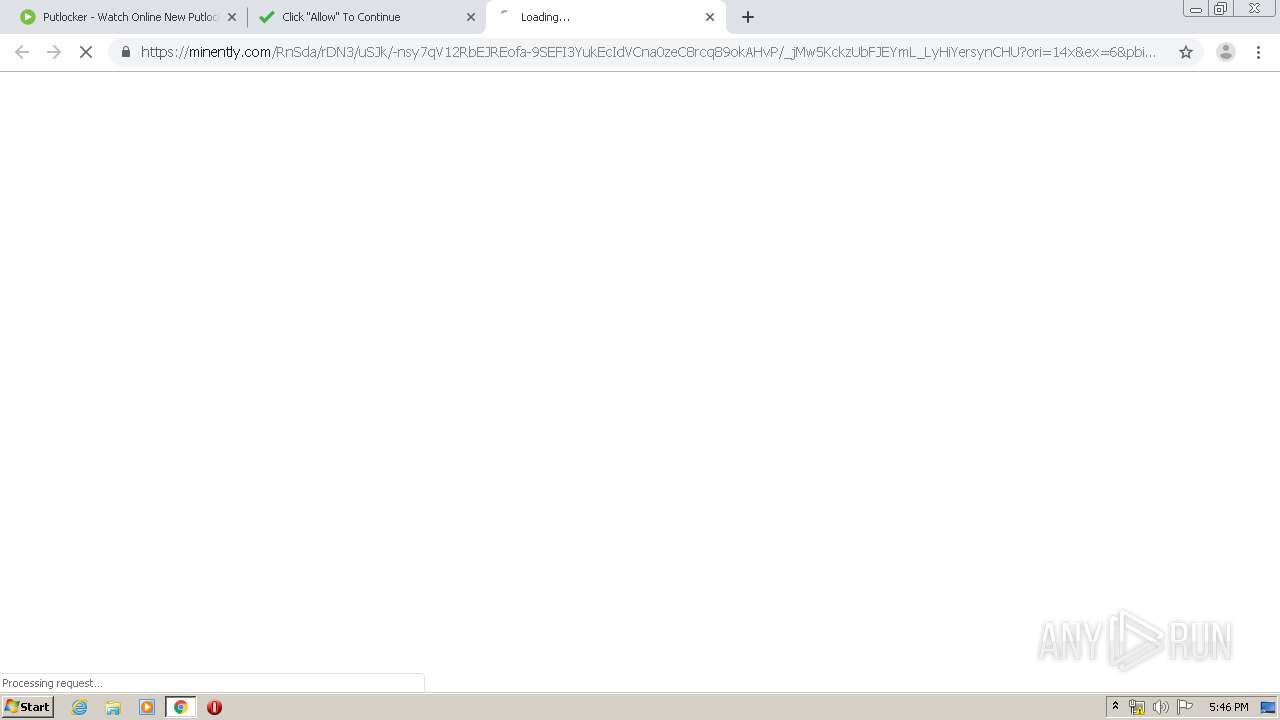
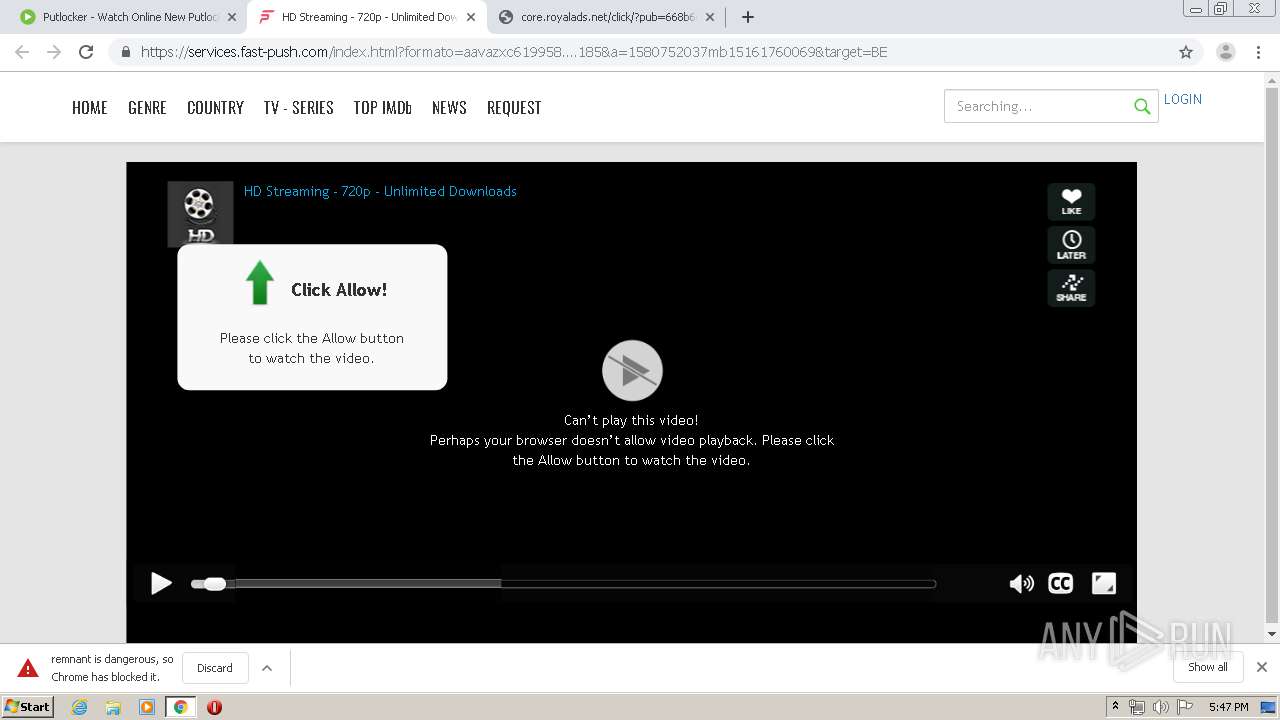
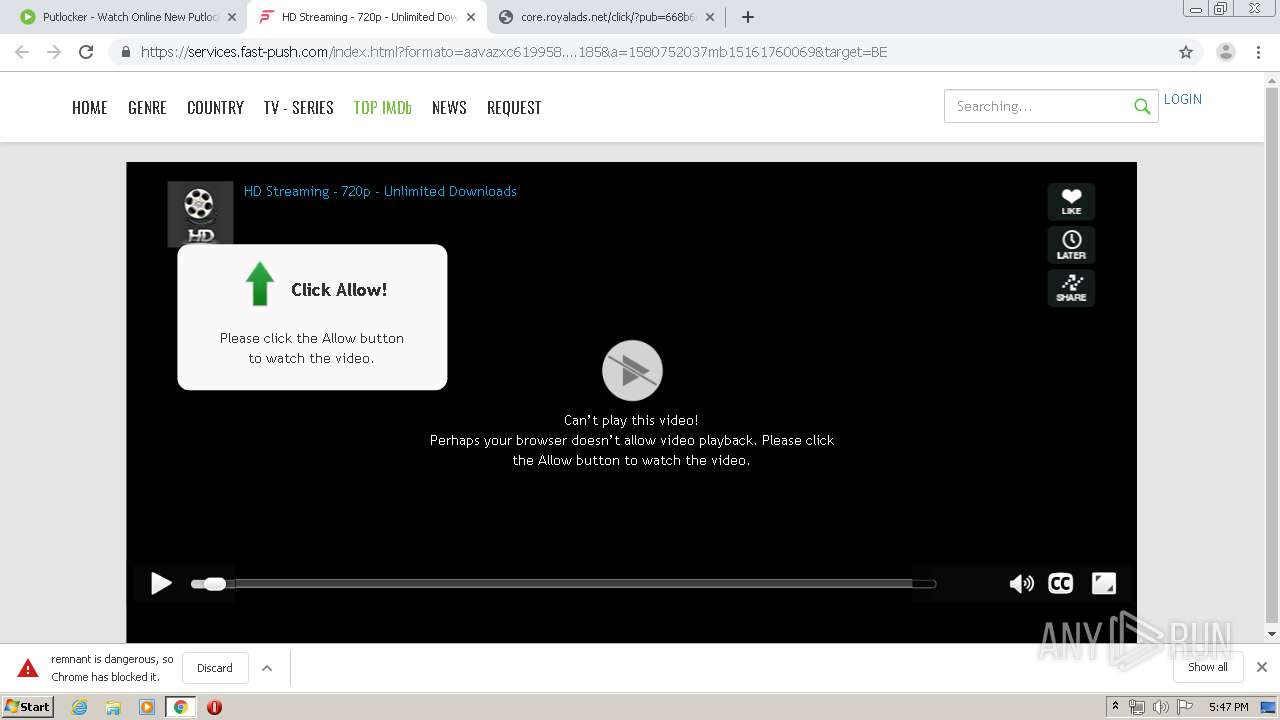
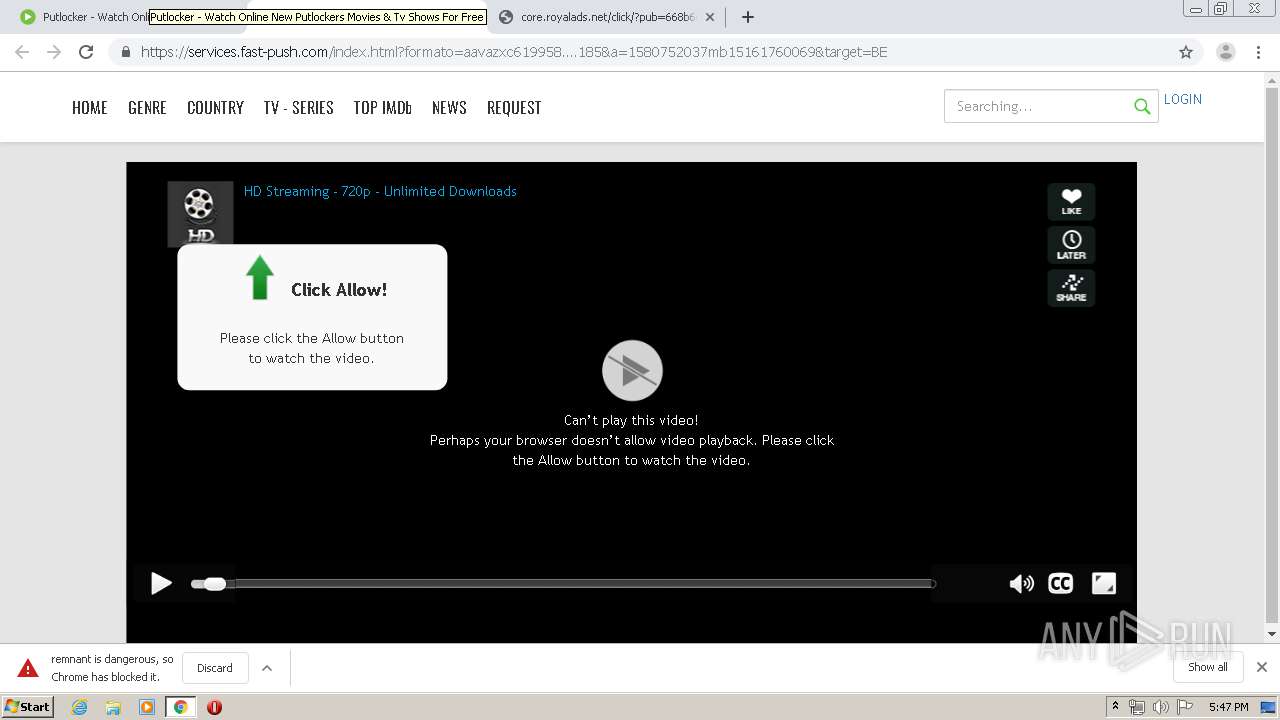
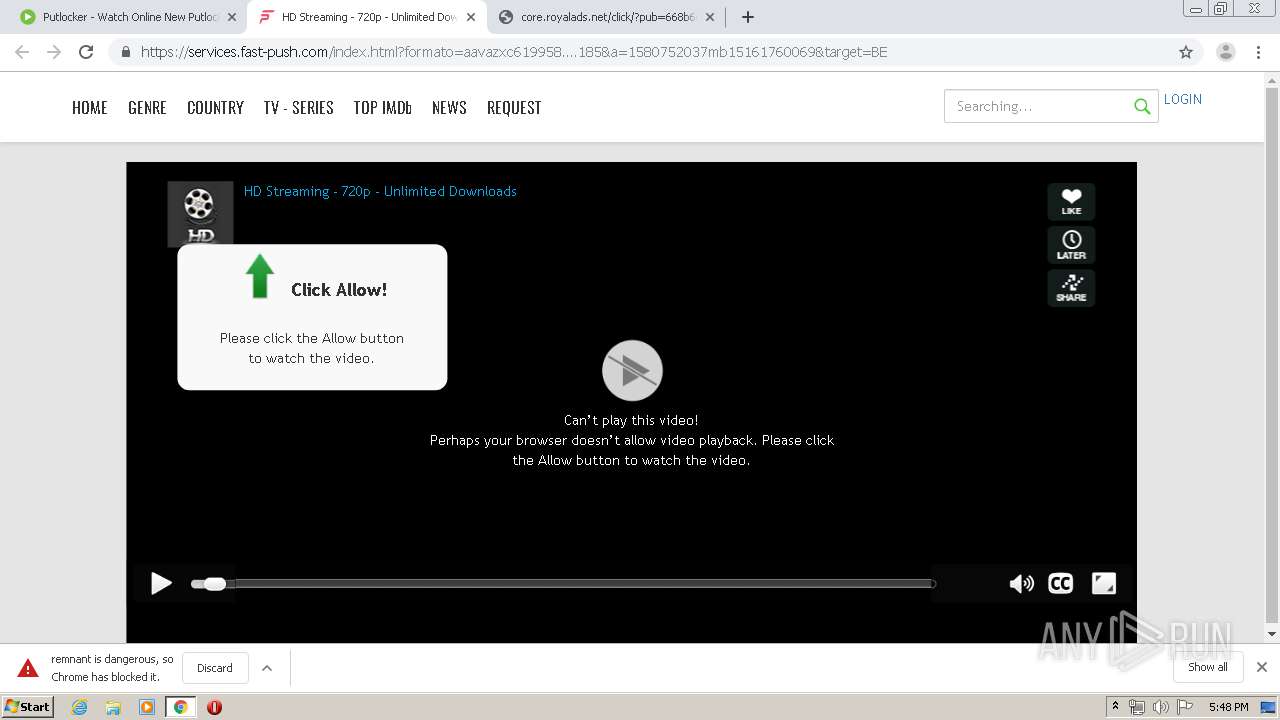
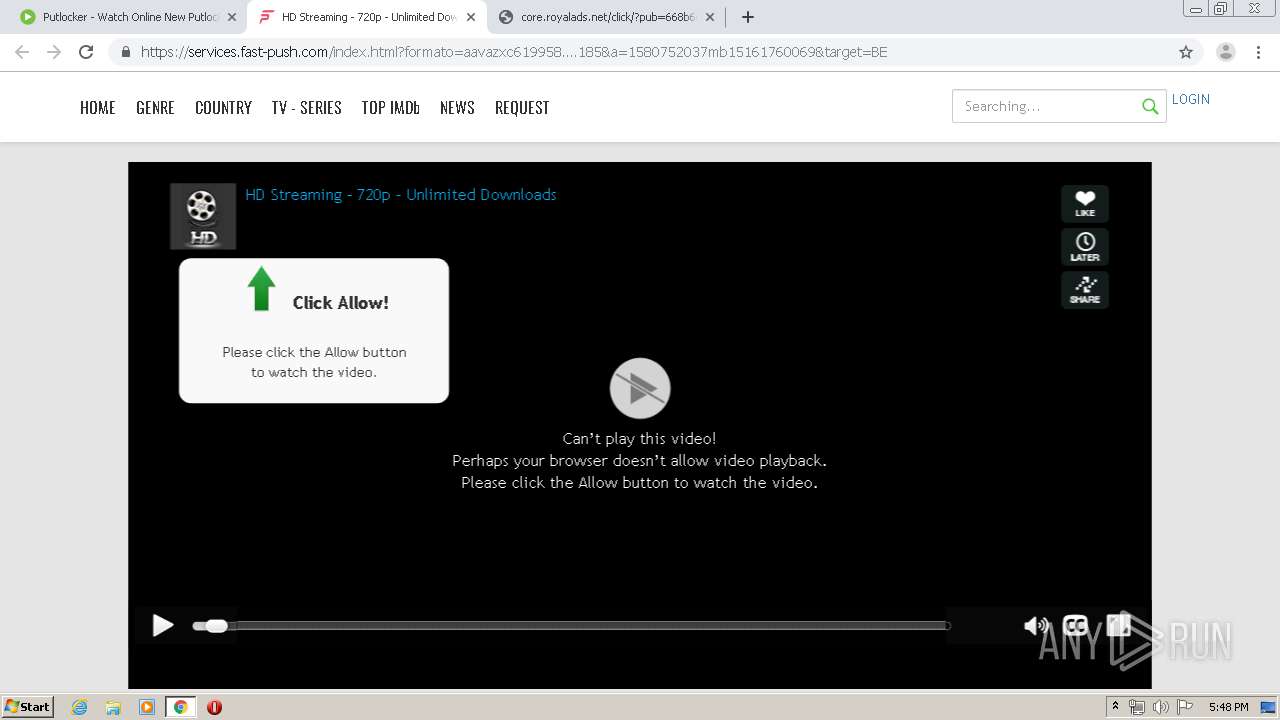
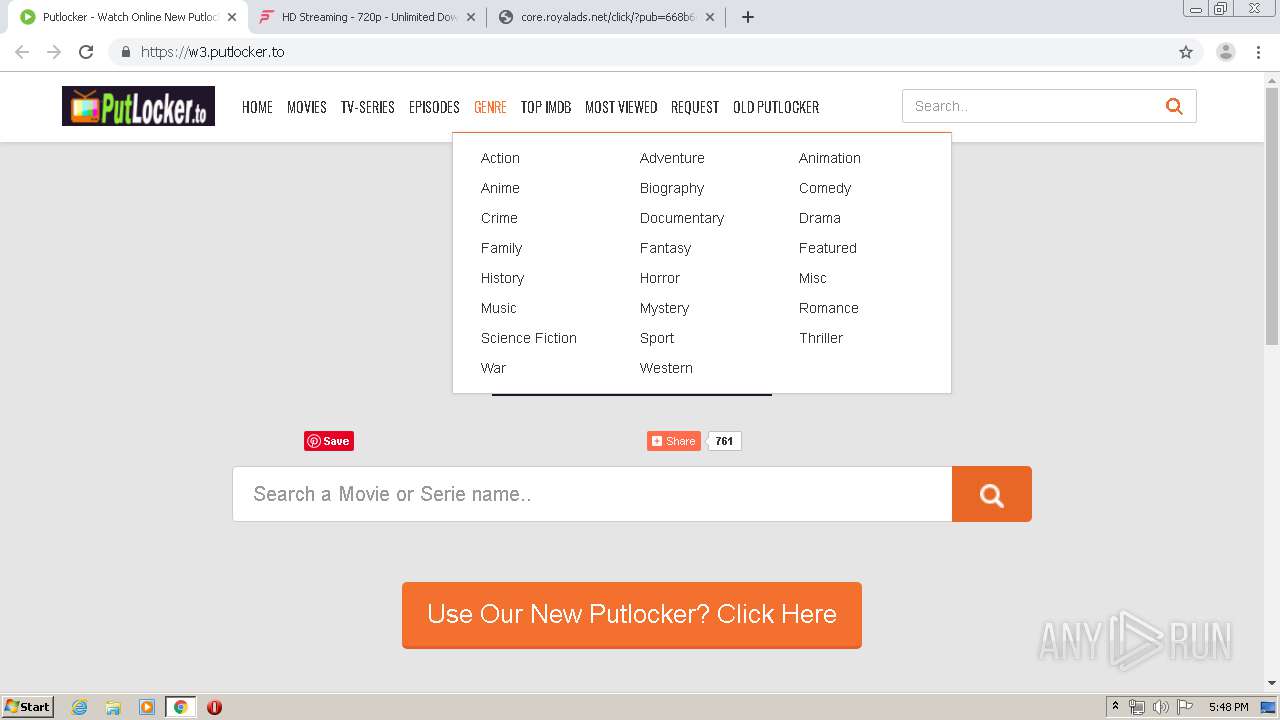
| URL: | https://w3.putlocker.to/ |
| Full analysis: | https://app.any.run/tasks/f2a110cd-fcde-4092-956a-138669383da6 |
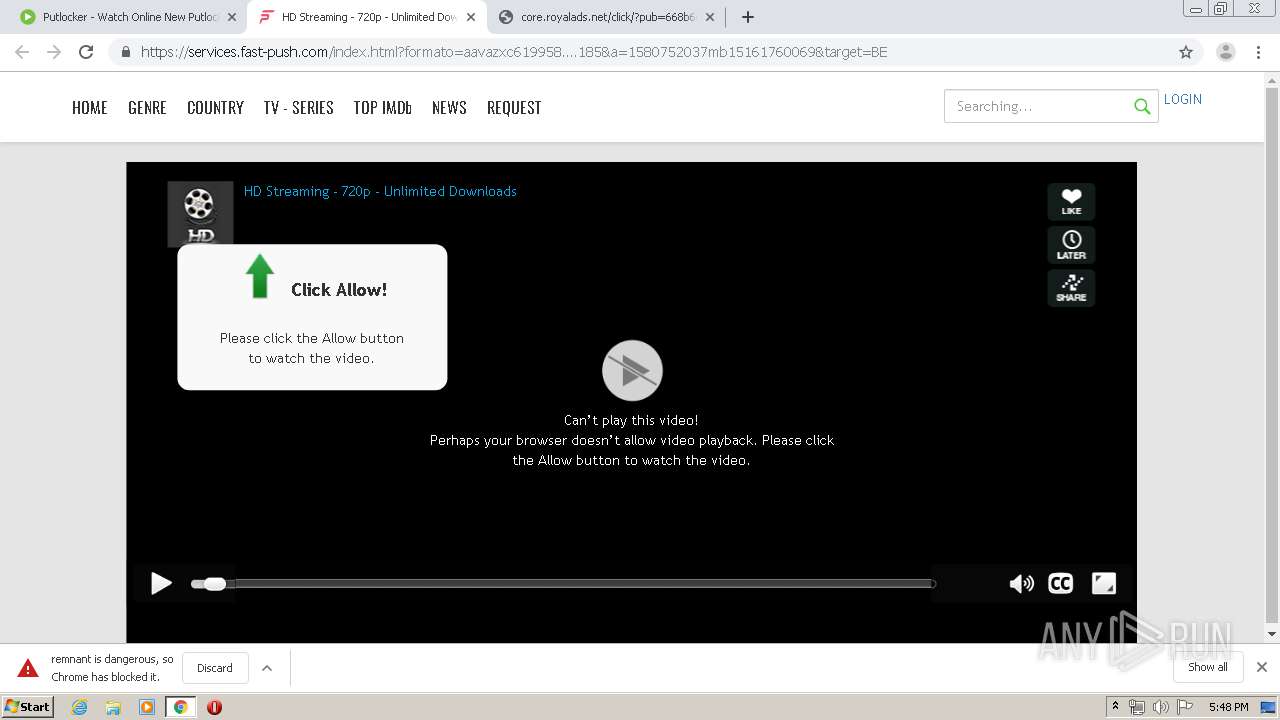
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2020, 17:45:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2ACA4A434ED0BC105EB6848D38BB8A8B |
| SHA1: | 1B49AE2F512026C623835E9A25135895AEC86152 |
| SHA256: | 718215CE5A6B73F2DD76A039033922D55E3366186A4E6D7F0B7C108D7549B264 |
| SSDEEP: | 3:N8rV+OyLr:2Pu |
MALICIOUS
No malicious indicators.SUSPICIOUS
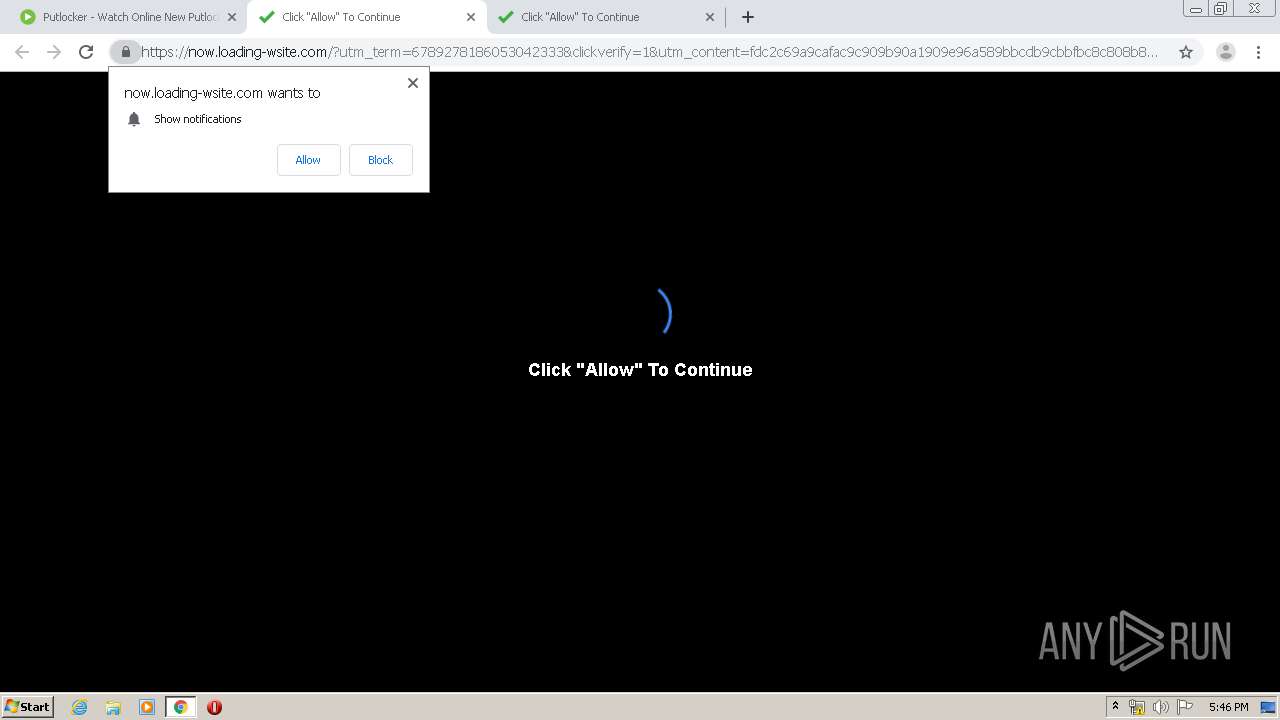
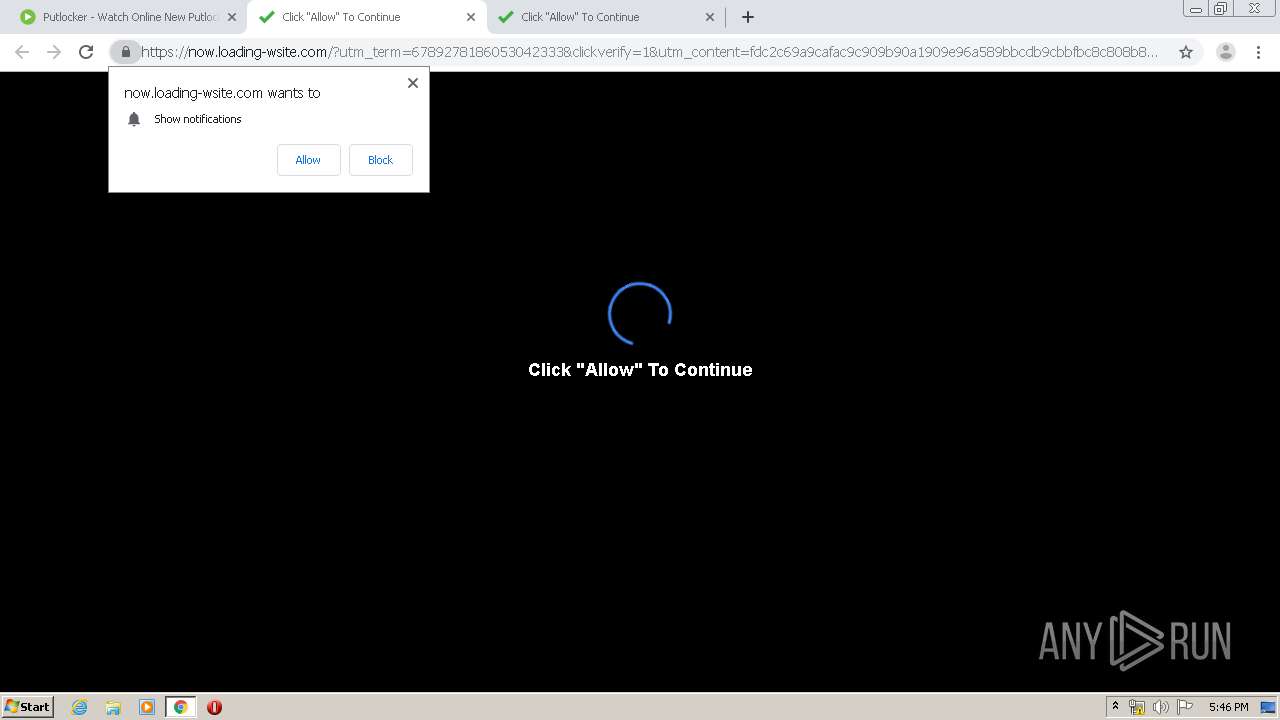
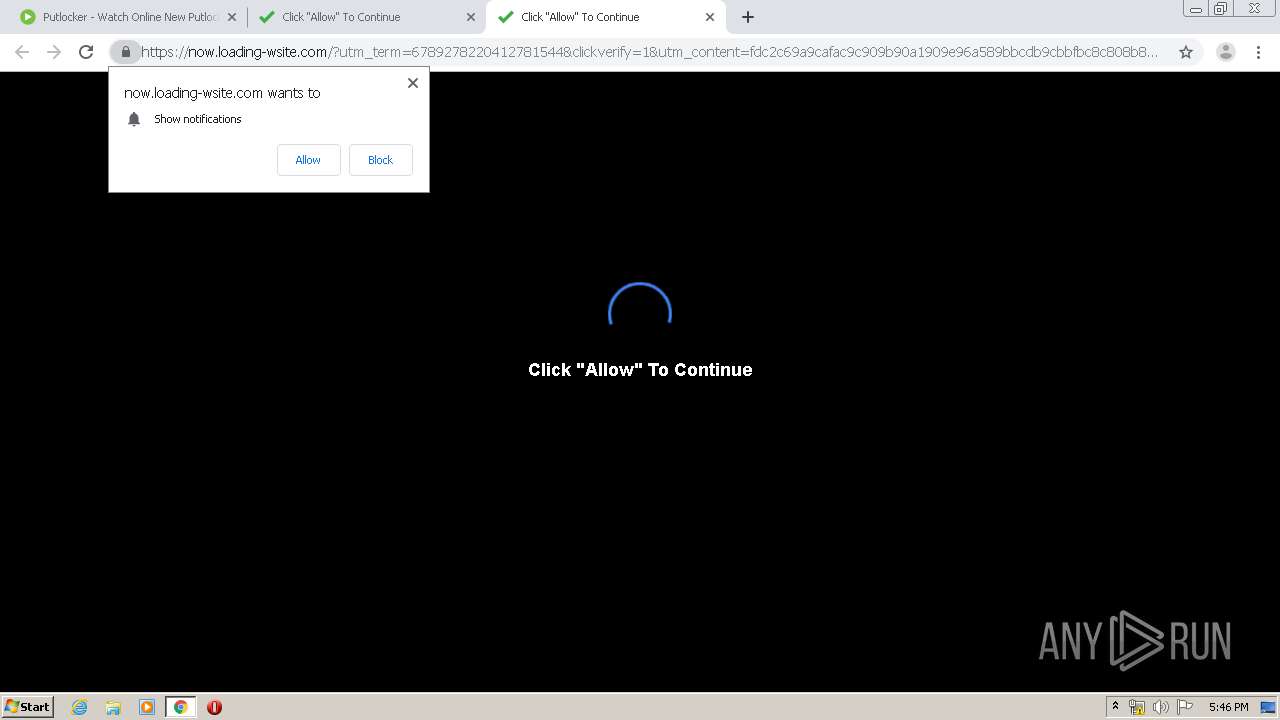
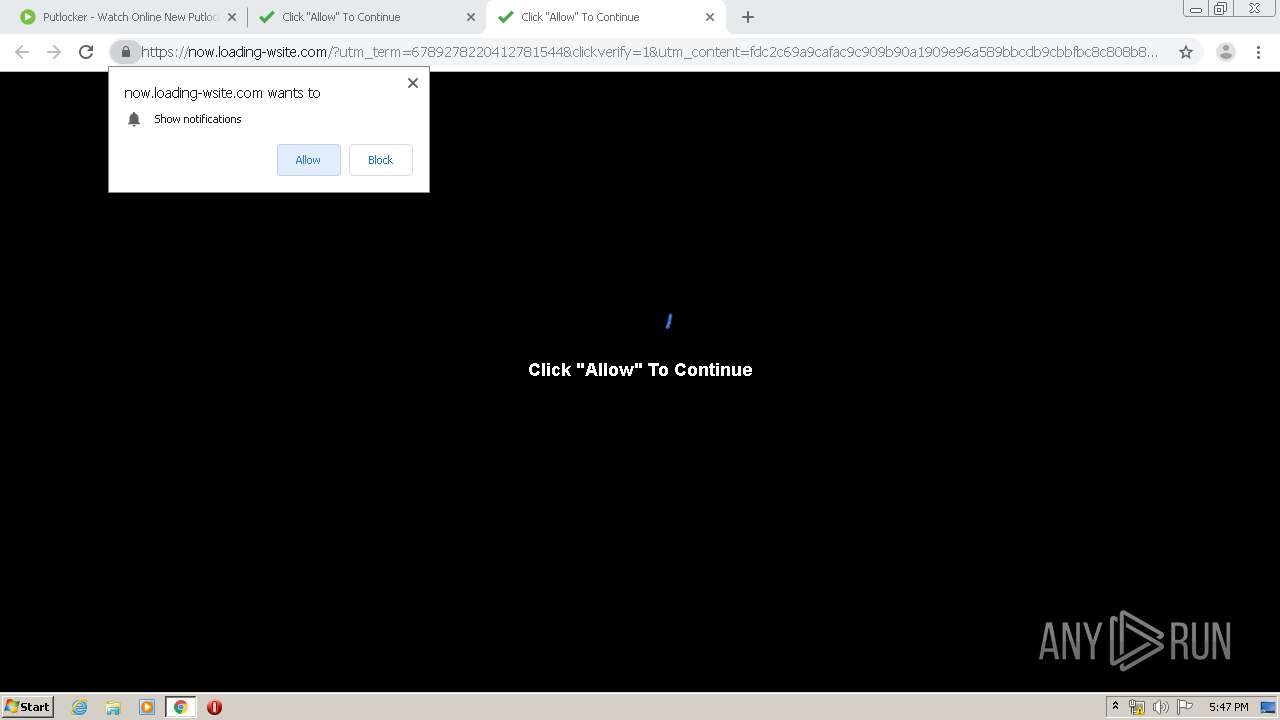
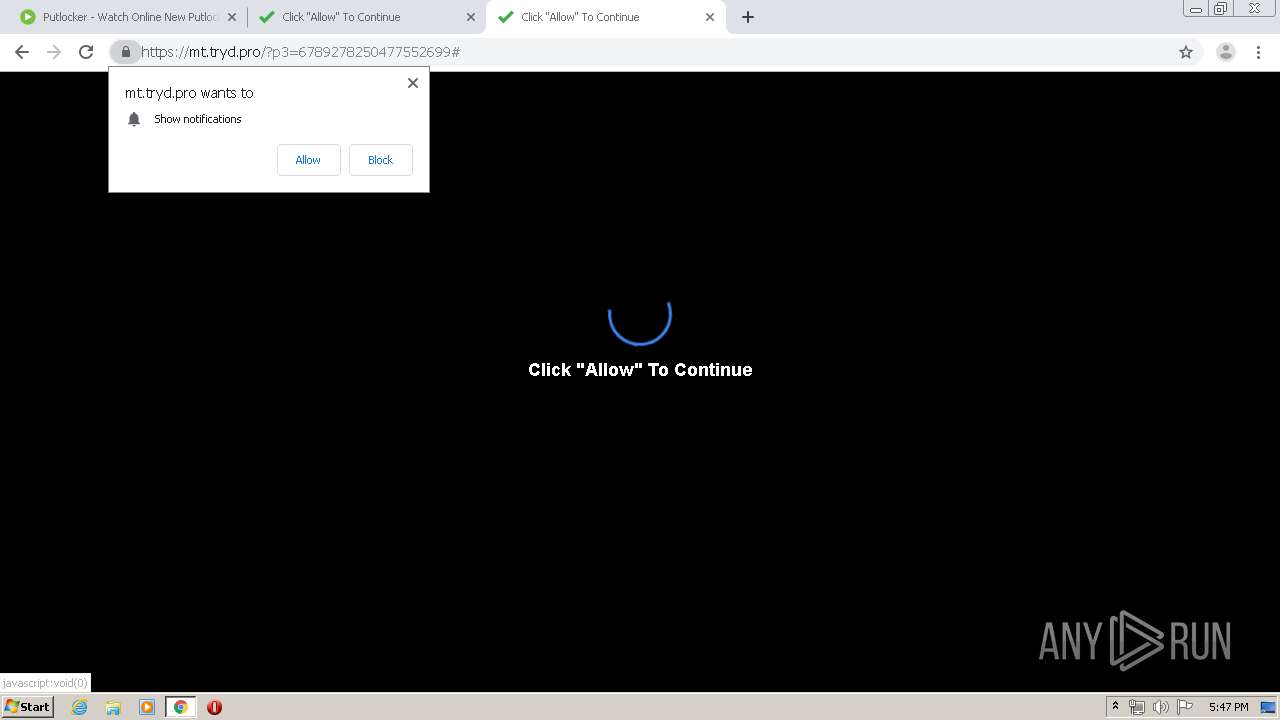
Modifies files in Chrome extension folder
- chrome.exe (PID: 1456)
INFO
Reads the hosts file
- chrome.exe (PID: 3260)
- chrome.exe (PID: 1456)
Connects to unusual port
- chrome.exe (PID: 3260)
Application launched itself
- chrome.exe (PID: 1456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
106
Monitored processes
66
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2419068933030140472 --renderer-client-id=61 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10248939643312184470 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3768 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2839433158284120879 --renderer-client-id=45 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4368 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11139758505845688873 --mojo-platform-channel-handle=4632 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2225599085424212429 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3368 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6663863466639180004 --mojo-platform-channel-handle=2456 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7611785726591577874 --mojo-platform-channel-handle=4412 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1440 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13501475579191628703 --mojo-platform-channel-handle=4128 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://w3.putlocker.to/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
988
Read events
865
Write events
118
Delete events
5
Modification events
| (PID) Process: | (1232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1456-13225225517405625 |
Value: 259 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
103
Text files
319
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E385C2D-5B0.pma | — | |
MD5:— | SHA256:— | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\745dcca4-56f1-407a-a944-d3e24bde9dde.tmp | — | |
MD5:— | SHA256:— | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66c5e.TMP | text | |
MD5:— | SHA256:— | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66c6e.TMP | text | |
MD5:— | SHA256:— | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFa66d39.TMP | text | |
MD5:— | SHA256:— | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66dd5.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
147
DNS requests
76
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
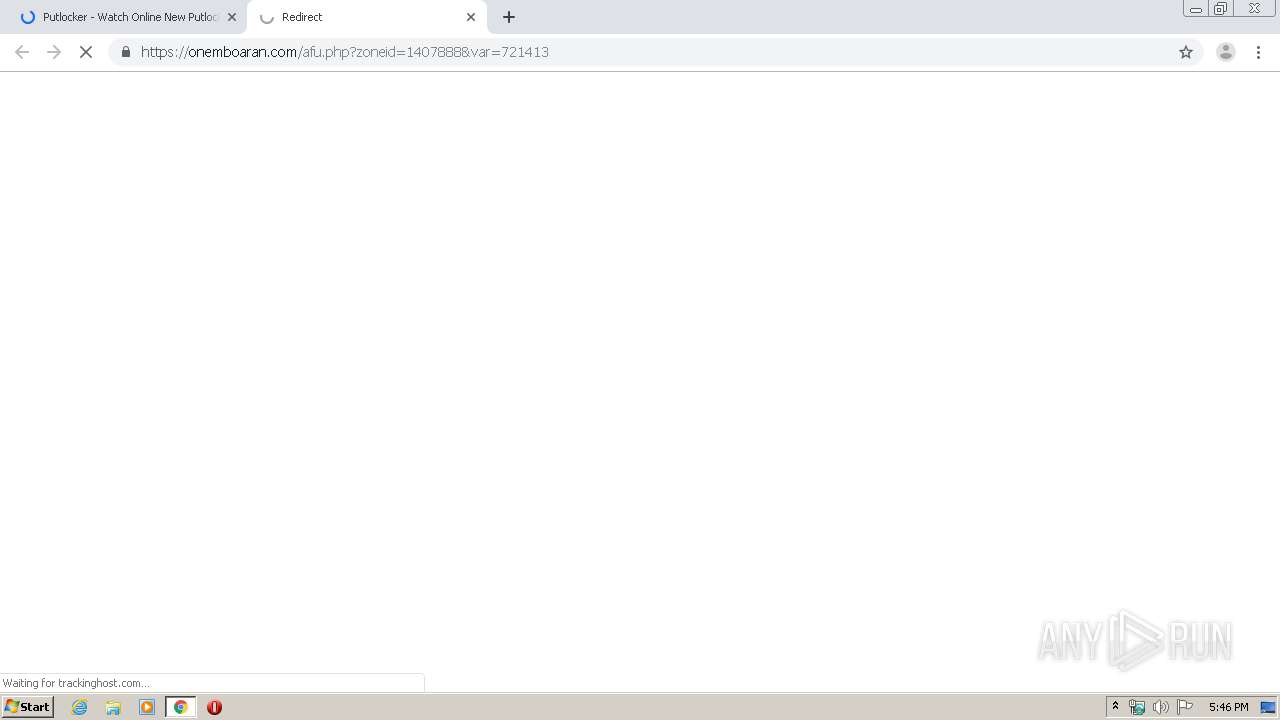
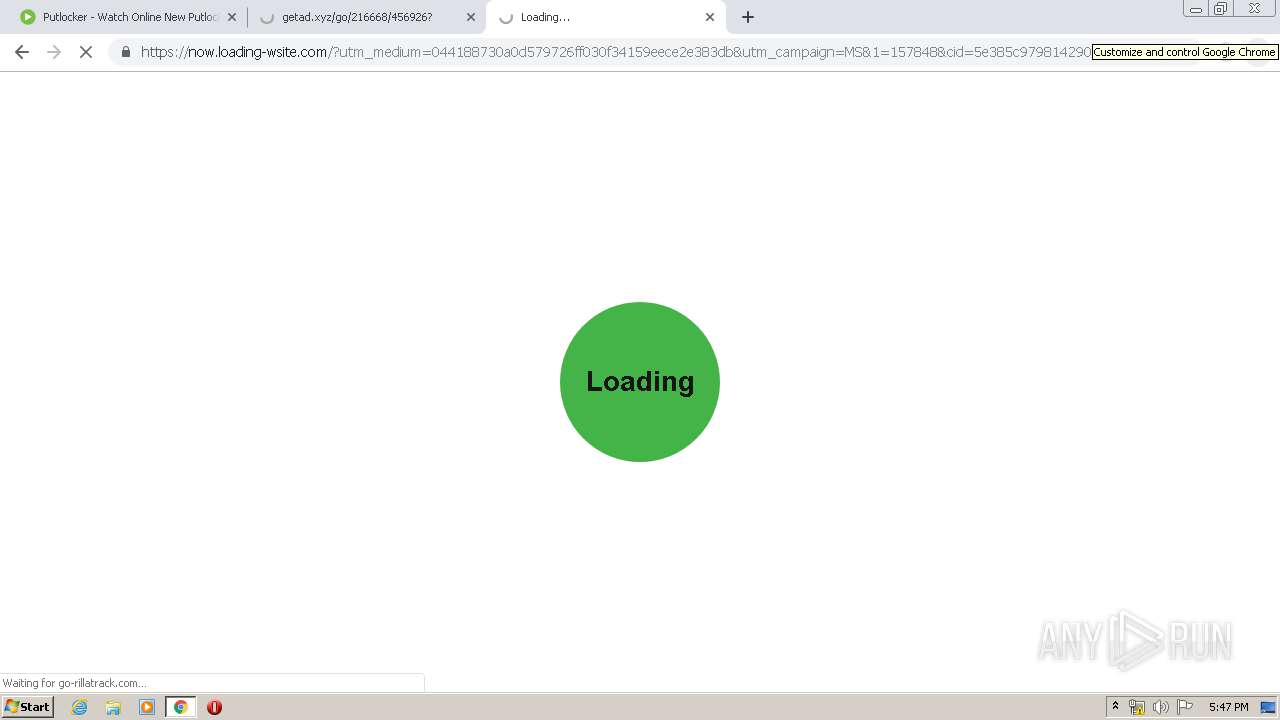
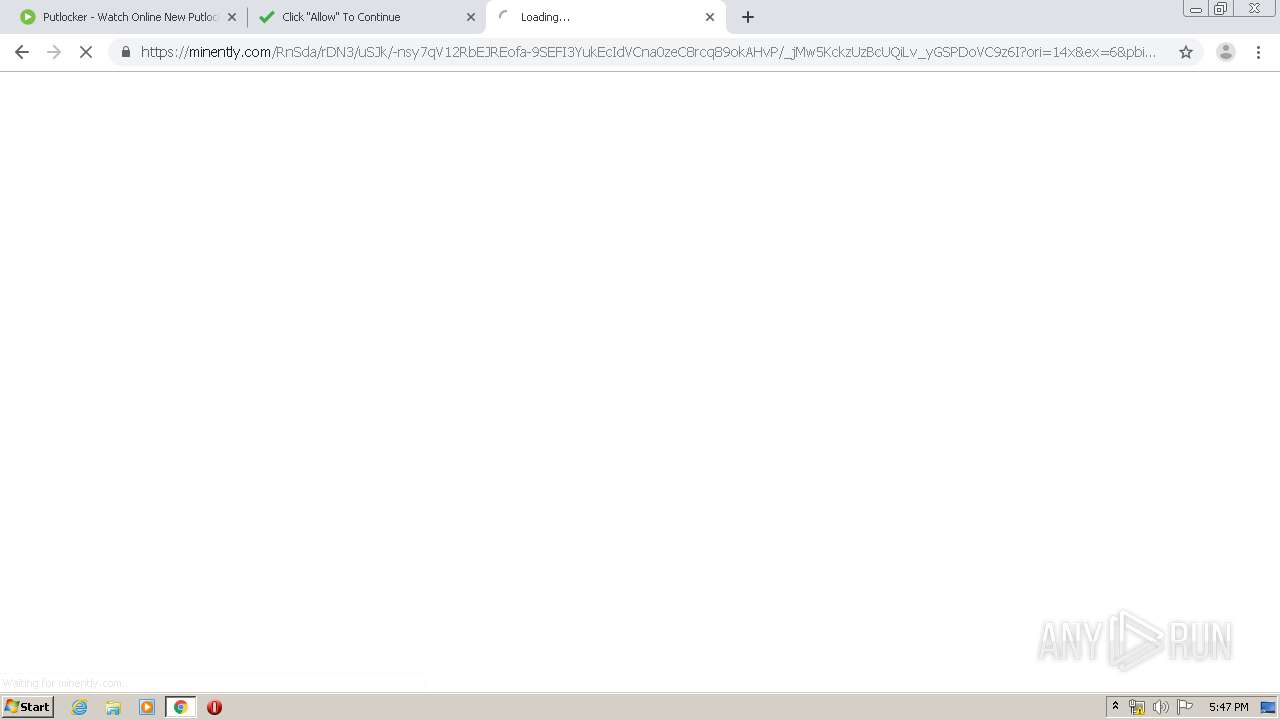
3260 | chrome.exe | GET | 302 | 94.23.206.47:80 | http://go-rillatrack.com/b.php?trf=m&p=custom_105t14y752&d=5cd042df98142940333186ff&pid=lBE20CB3A0909ba0007PS002MZ0XHIX03DSO3G017S03DSO00000000&source=157848&data1=bVfFnTCRr_pzatDj83hx | FR | — | — | unknown |
3260 | chrome.exe | GET | — | 94.23.206.47:80 | http://go-rillatrack.com/b.php?trf=m&p=custom_105t14y752&d=5cd042df98142940333186ff&pid=lBE20CB3A09001d0007PS002MZ0XHIX03DSO3G05S203DSO00000000&source=157848&data1=bVfFnTCRr_pzatDj83hx& | FR | — | — | unknown |
3260 | chrome.exe | GET | 302 | 94.23.206.47:80 | http://go-rillatrack.com/b.php?trf=m&p=custom_105t14y752&d=5cd042df98142940333186ff&pid=lBE20CB3A0904490007PS002MZ0XHIX03DSO3G06UT03DSO00000000&source=157848&data1=fQA8WjCQANeomJo1qwTh& | FR | — | — | unknown |
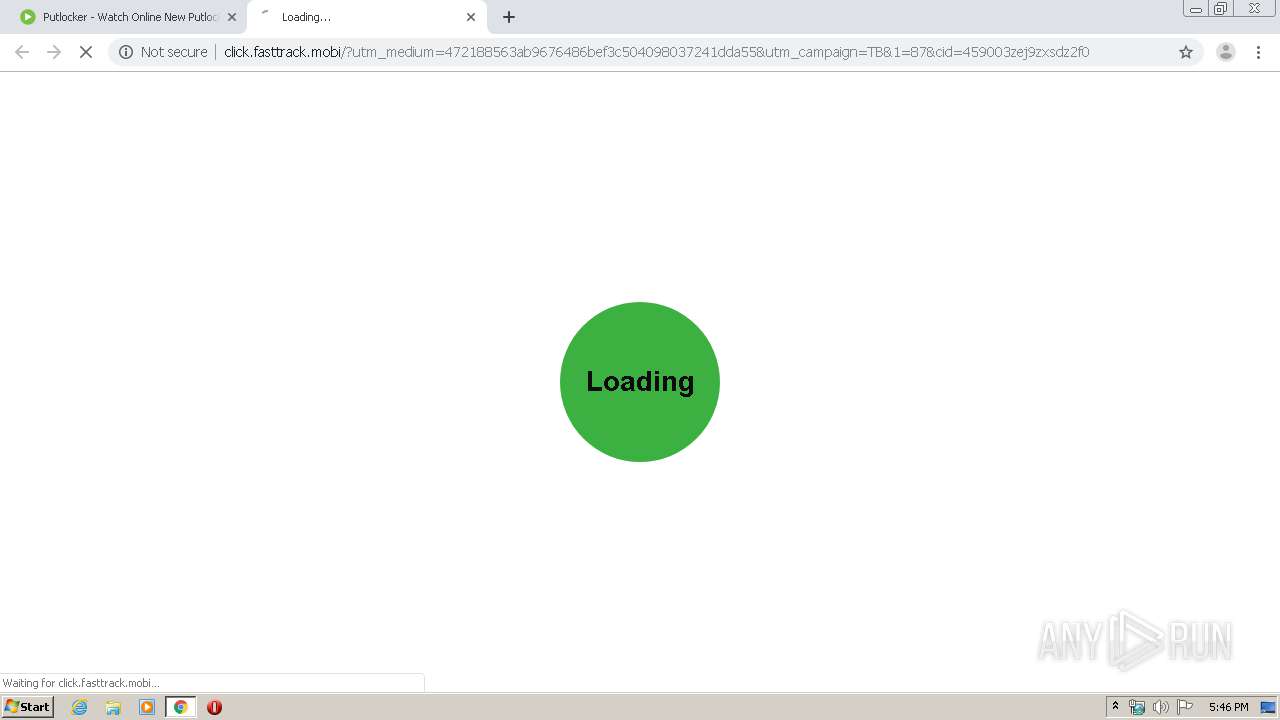
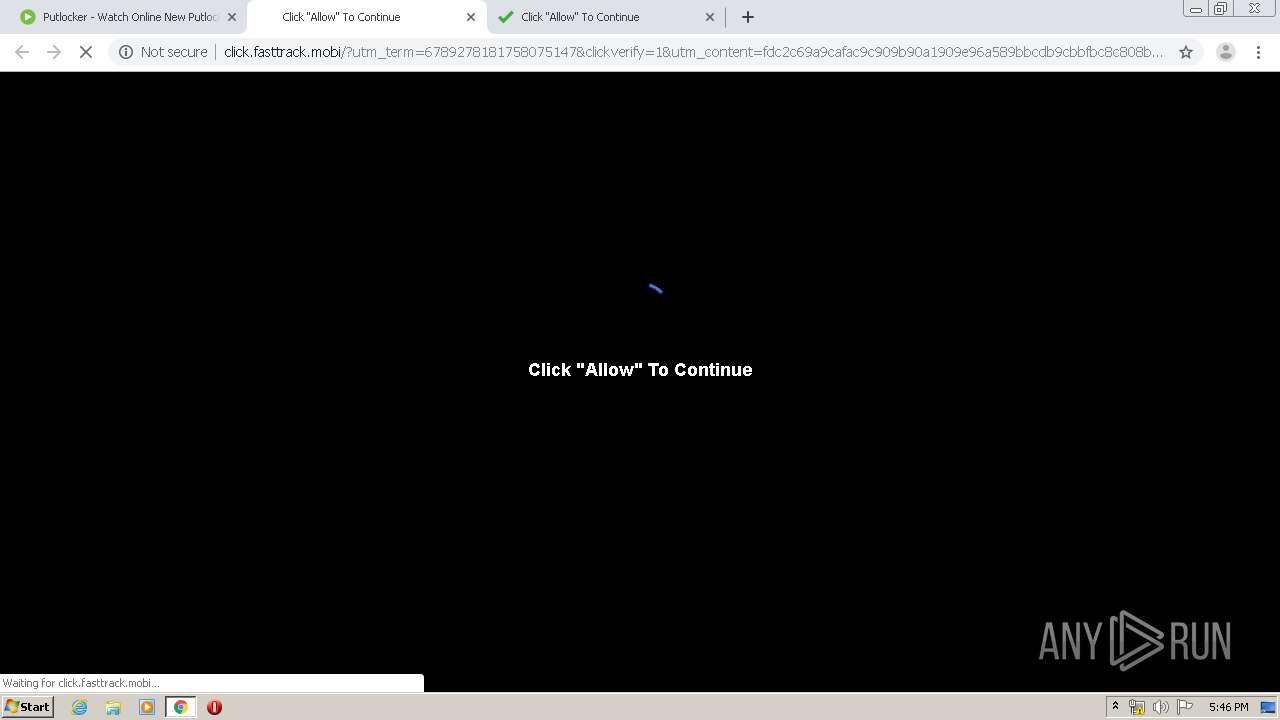
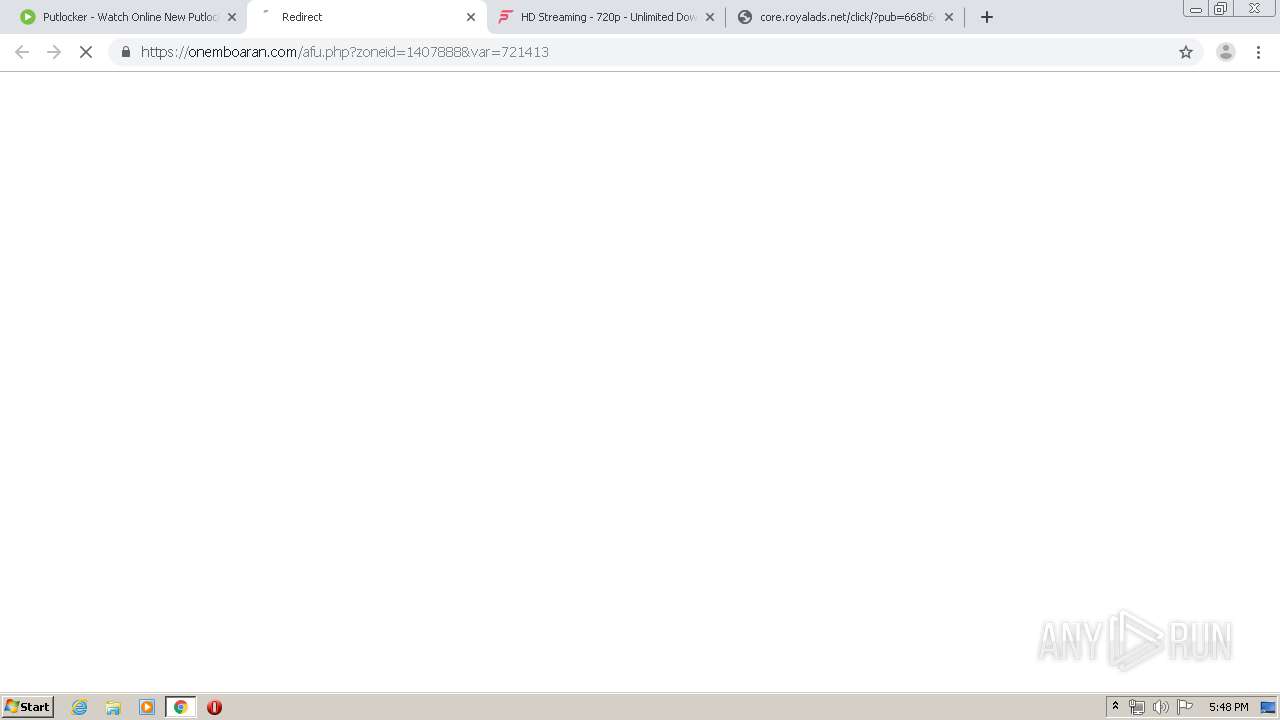
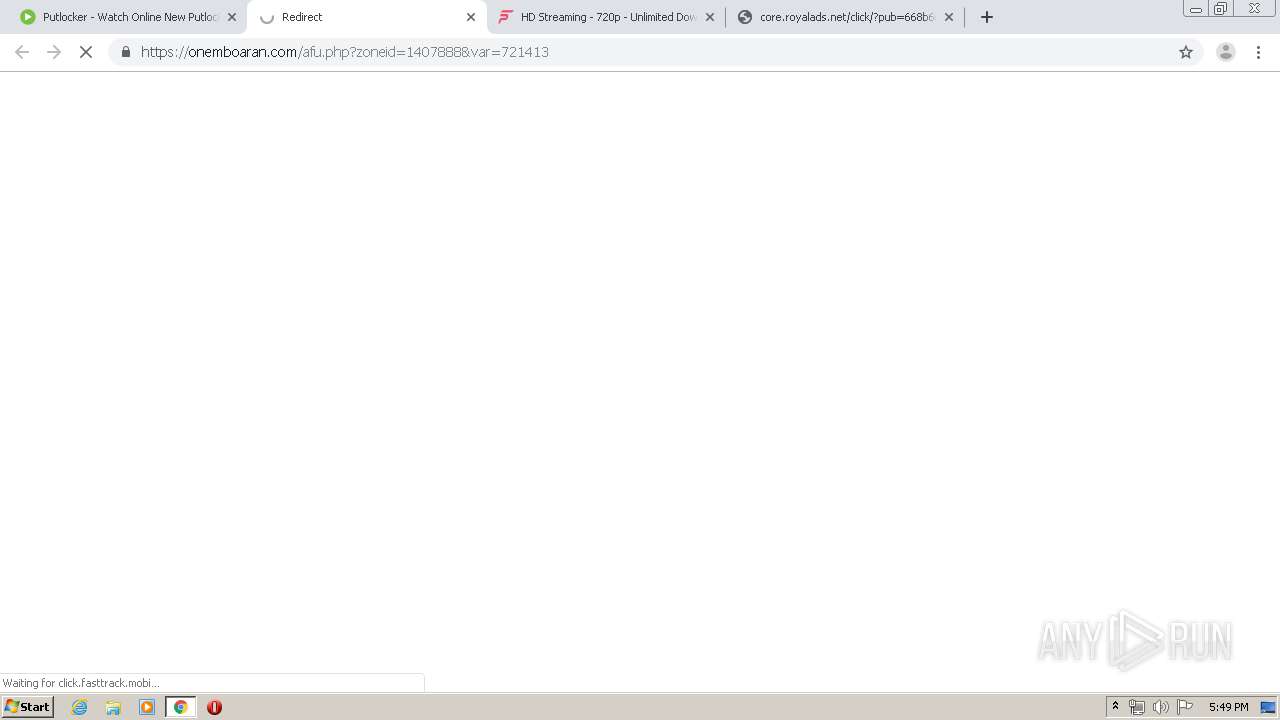
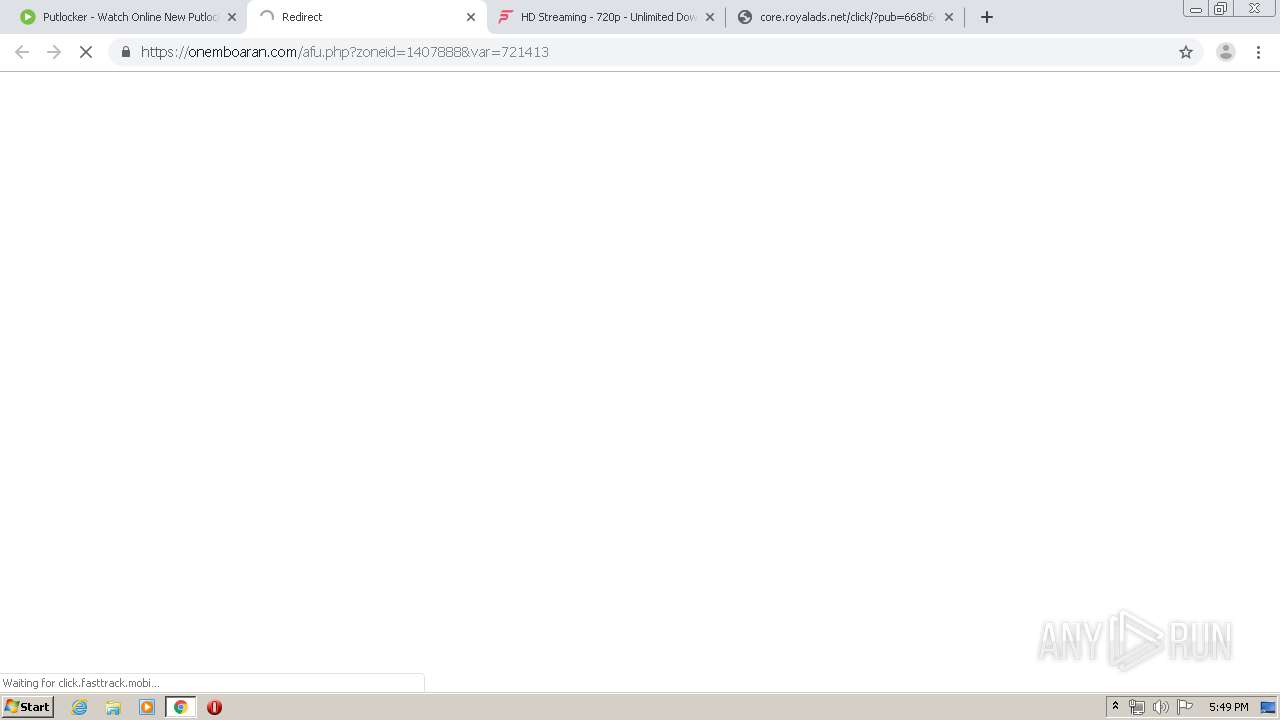
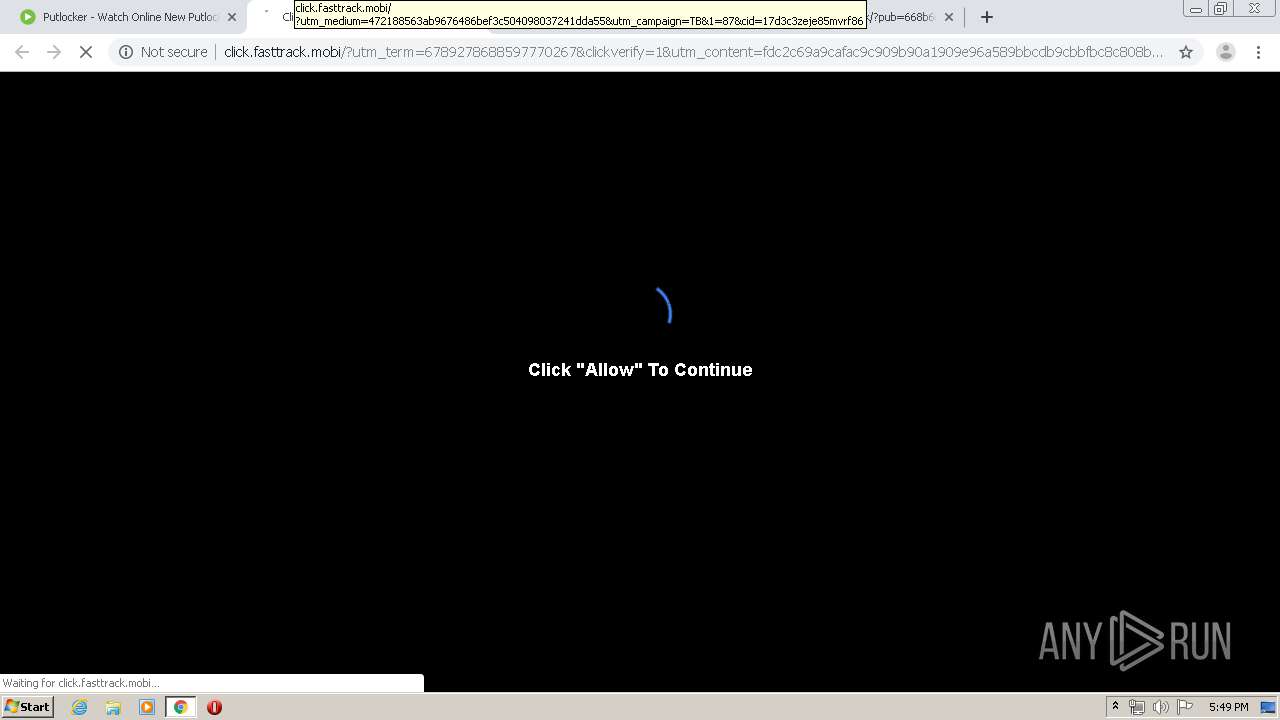
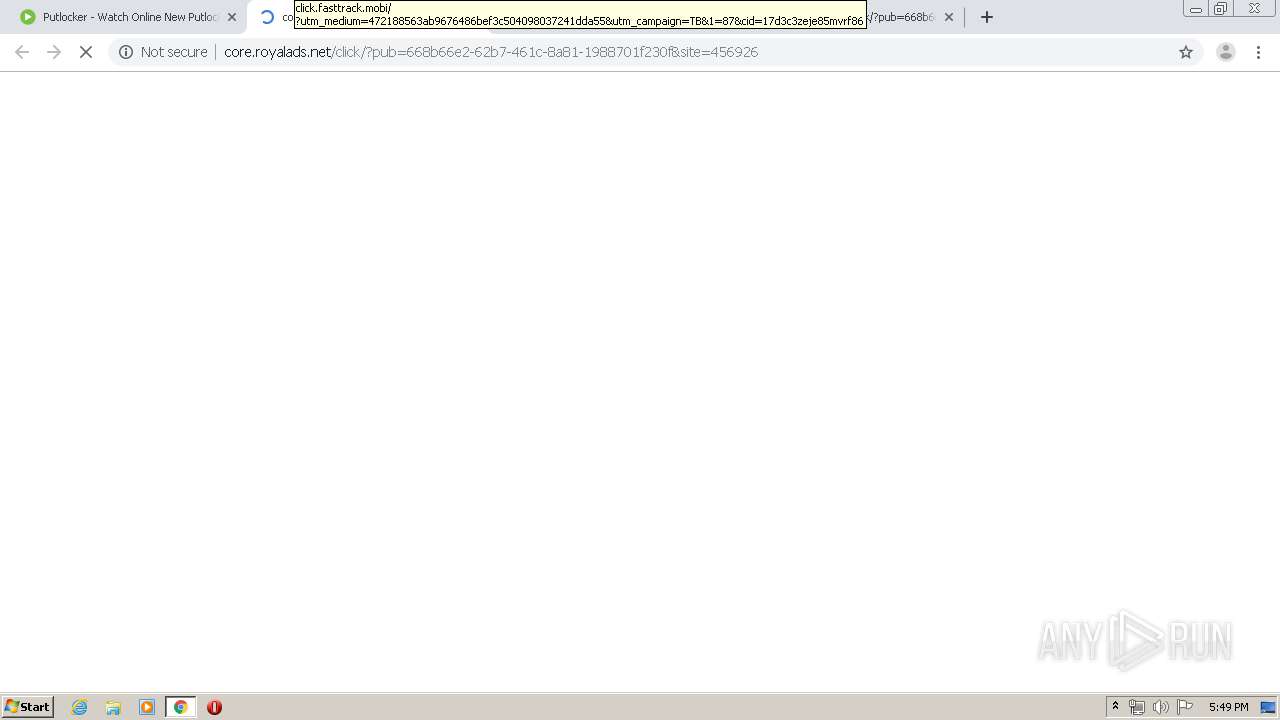
3260 | chrome.exe | GET | — | 198.143.165.222:80 | http://click.fasttrack.mobi/?utm_medium=472188563ab9676486bef3c504098037241dda55&utm_campaign=TB&1=87&cid=fdef63zejslhefe1df | US | — | — | suspicious |
3260 | chrome.exe | GET | 302 | 94.23.206.47:80 | http://go-rillatrack.com/b.php?trf=m&p=custom_105t14y752&d=5cd042df98142940333186ff&pid=lBE20CB3A0909ba0007PS002MZ0XHIX03DSO3G017S03DSO00000000&source=157848&data1=bVfFnTCRr_pzatDj83hx | FR | — | — | unknown |
3260 | chrome.exe | GET | 204 | 172.217.23.131:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
3260 | chrome.exe | GET | 302 | 94.23.206.47:80 | http://go-rillatrack.com/b.php?trf=m&p=custom_105t14y752&d=5cd042df98142940333186ff&pid=lBE20CB3A09001d0007PS002MZ0XHIX03DSO3G05S203DSO00000000&source=157848&data1=bVfFnTCRr_pzatDj83hx | FR | — | — | unknown |
3260 | chrome.exe | GET | 302 | 94.23.206.47:80 | http://go-rillatrack.com/b.php?trf=m&p=custom_105t14y752&d=5cd042df98142940333186ff&pid=lBE20CB3A0904490007PS002MZ0XHIX03DSO3G06UT03DSO00000000&source=157848&data1=fQA8WjCQANeomJo1qwTh | FR | — | — | unknown |
3260 | chrome.exe | GET | 200 | 198.143.165.222:80 | http://click.fasttrack.mobi/?utm_medium=472188563ab9676486bef3c504098037241dda55&utm_campaign=TB&1=87&cid=459003zej9zxsdz2f0 | US | html | 1.25 Kb | suspicious |
3260 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3260 | chrome.exe | 93.184.220.66:443 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3260 | chrome.exe | 104.17.64.4:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
3260 | chrome.exe | 104.23.132.67:443 | hqq.tv | Cloudflare Inc | US | shared |
3260 | chrome.exe | 216.239.34.117:443 | www.google.com | Google Inc. | US | whitelisted |
3260 | chrome.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
3260 | chrome.exe | 46.105.201.240:443 | s10.histats.com | OVH SAS | FR | suspicious |
3260 | chrome.exe | 172.217.16.208:443 | storage.googleapis.com | Google Inc. | US | whitelisted |
3260 | chrome.exe | 104.24.125.211:443 | yandexcdn.com | Cloudflare Inc | US | shared |
3260 | chrome.exe | 198.27.80.143:443 | s4.histats.com | OVH SAS | CA | suspicious |
3260 | chrome.exe | 157.240.20.15:443 | graph.facebook.com | Facebook, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
w3.putlocker.to |
| suspicious |
accounts.google.com |
| shared |
ajax.googleapis.com |
| whitelisted |
s.w.org |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
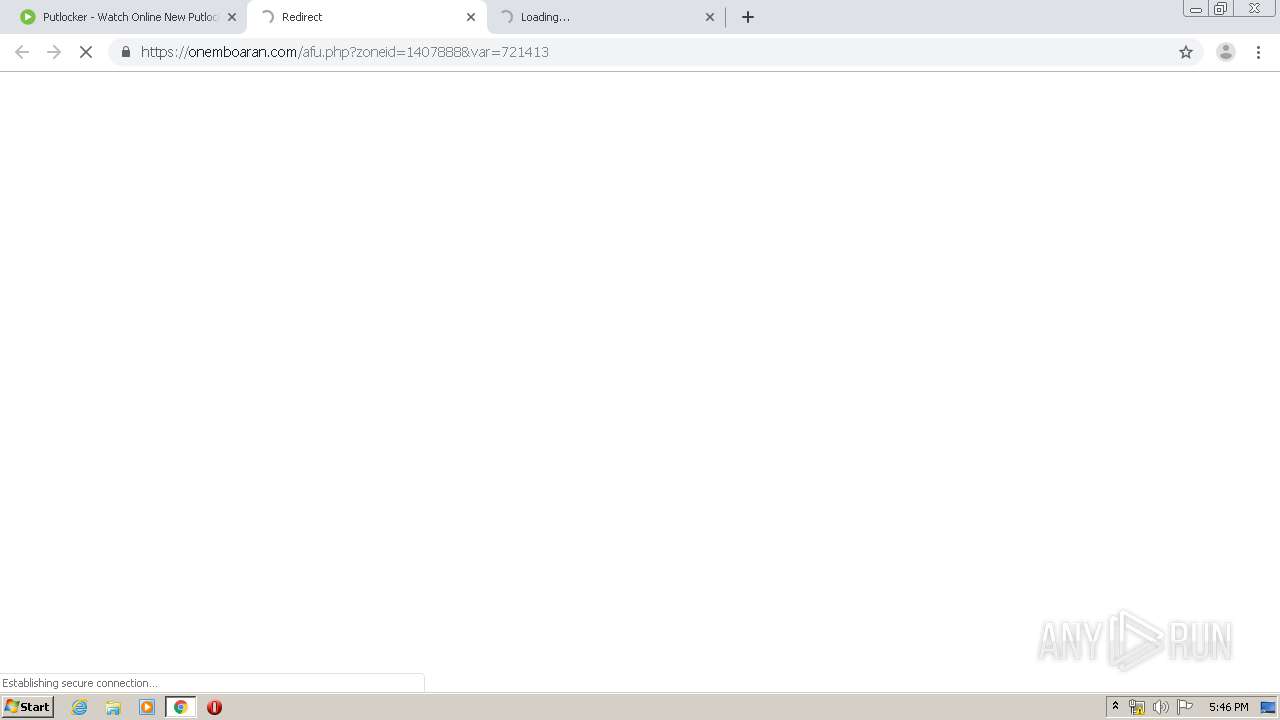
onemboaran.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
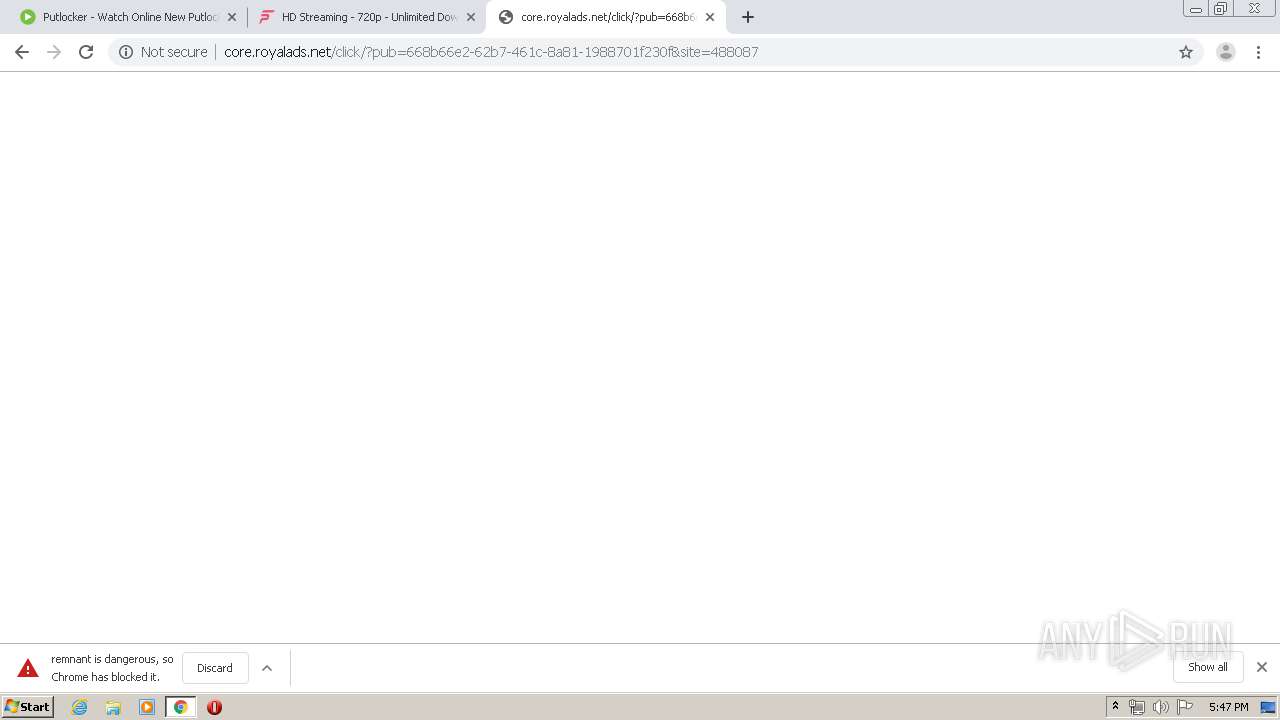
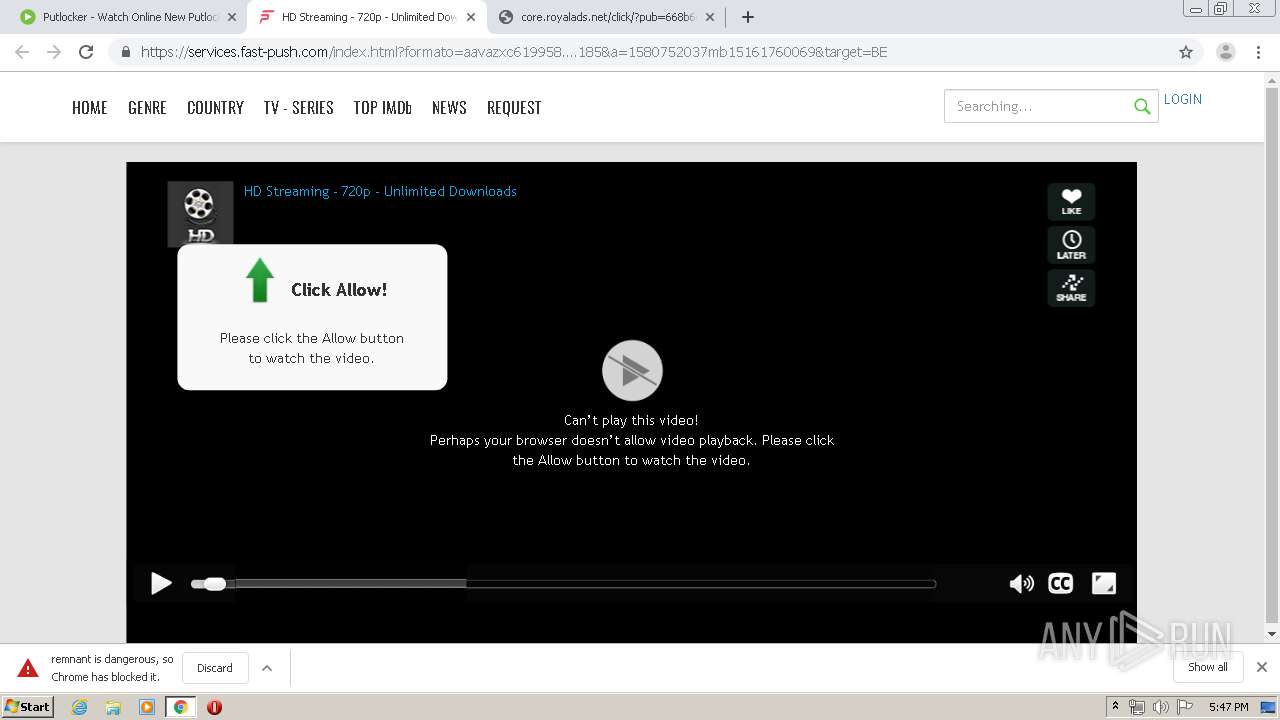
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
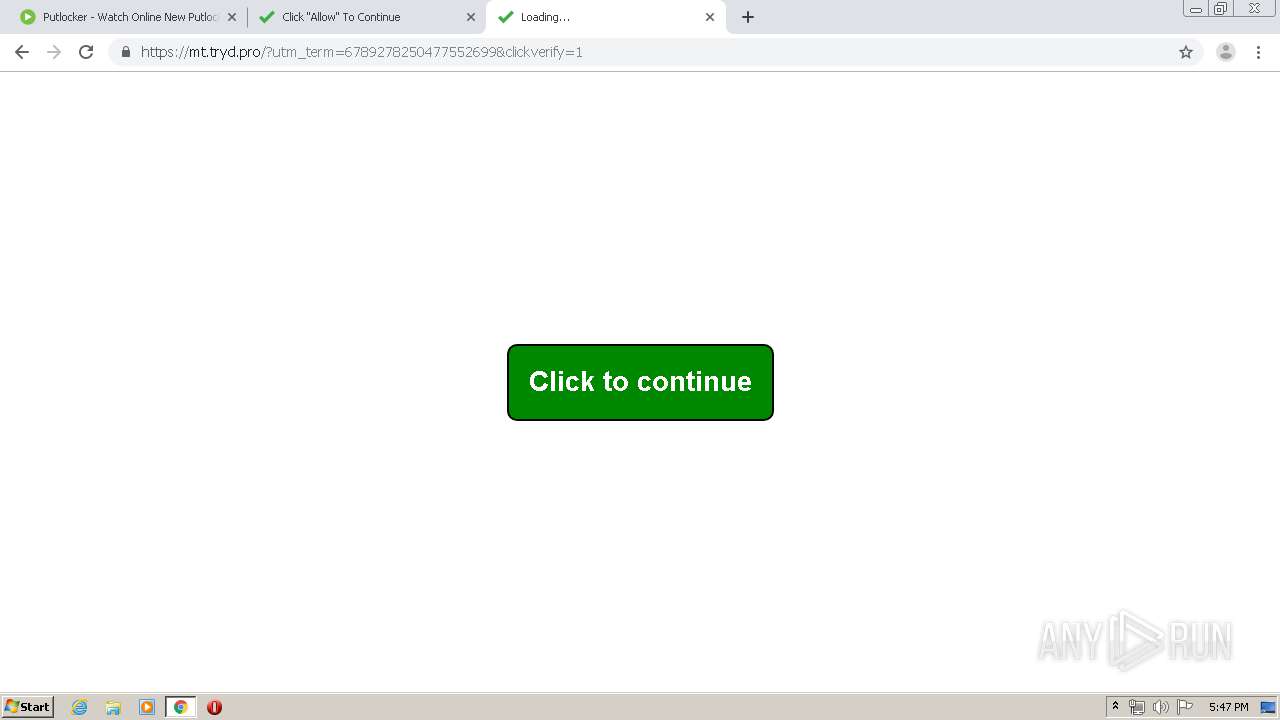
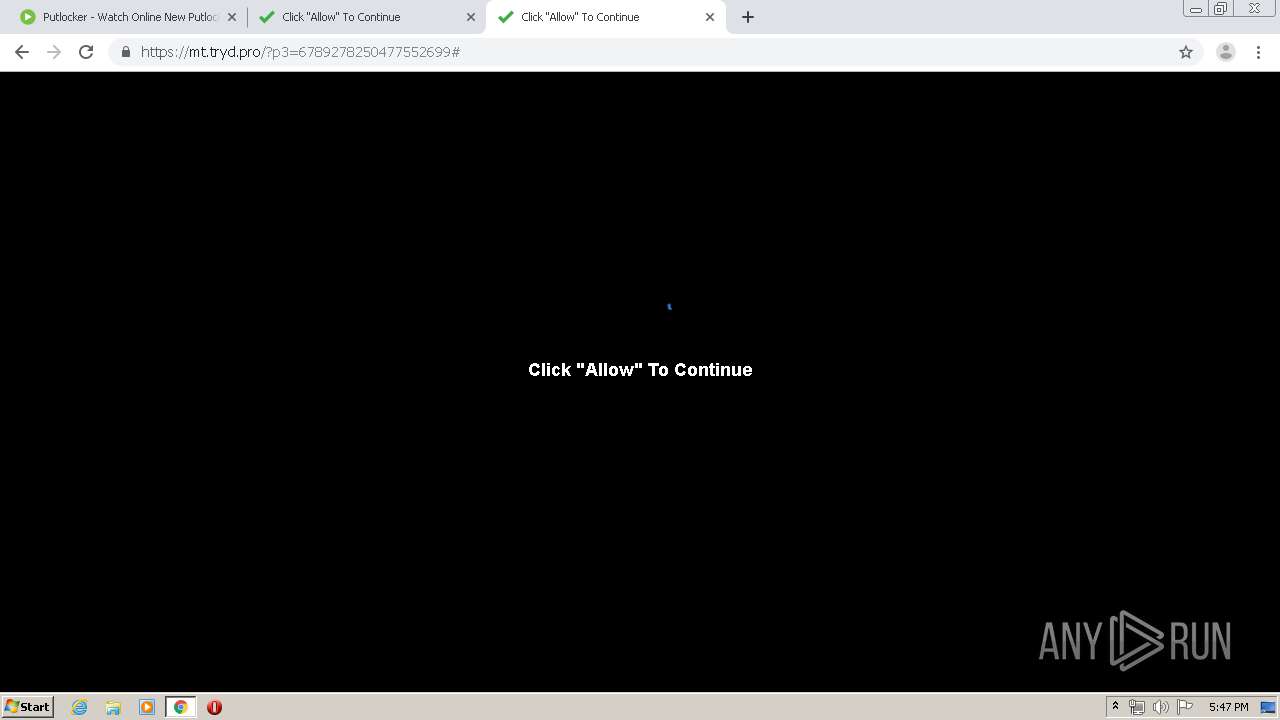
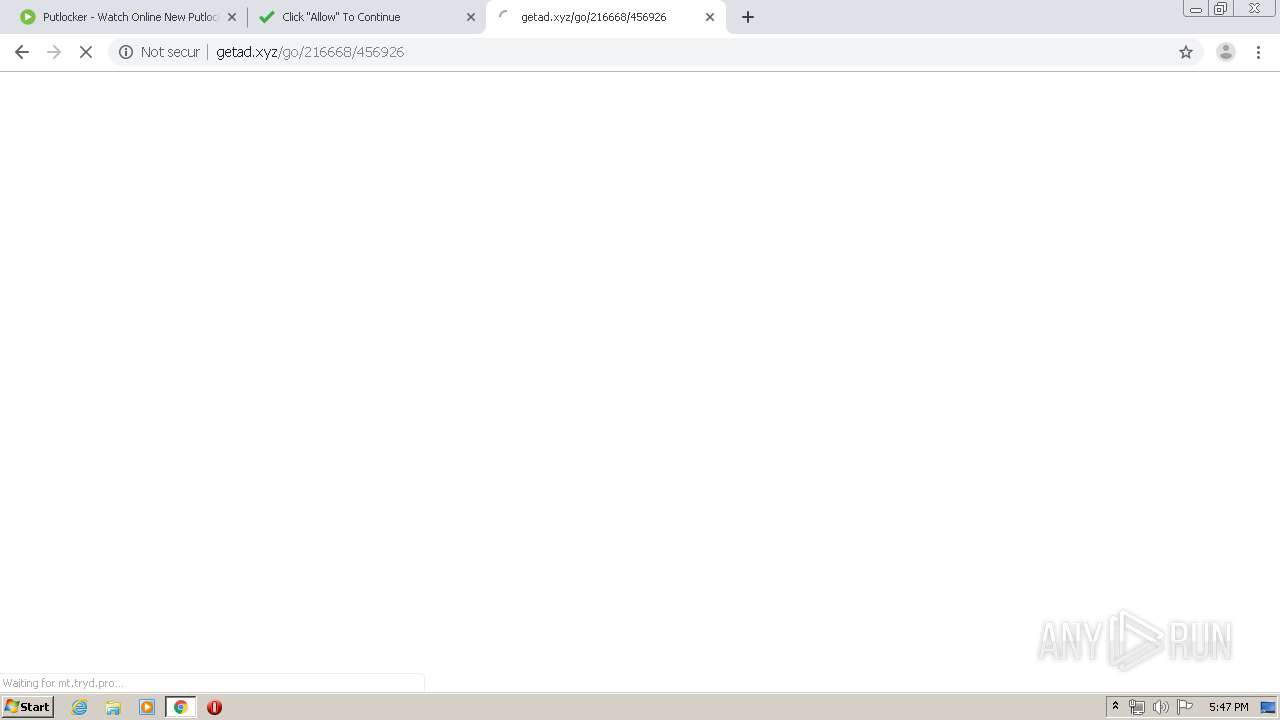
3260 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3260 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3260 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3260 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3260 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3260 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3260 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3260 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |