| File name: | 460e6a63-122c-433e-b20a-723c010bfde6.exe |
| Full analysis: | https://app.any.run/tasks/61d58d29-887e-4028-b73a-1c4484464b30 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 19:07:26 |
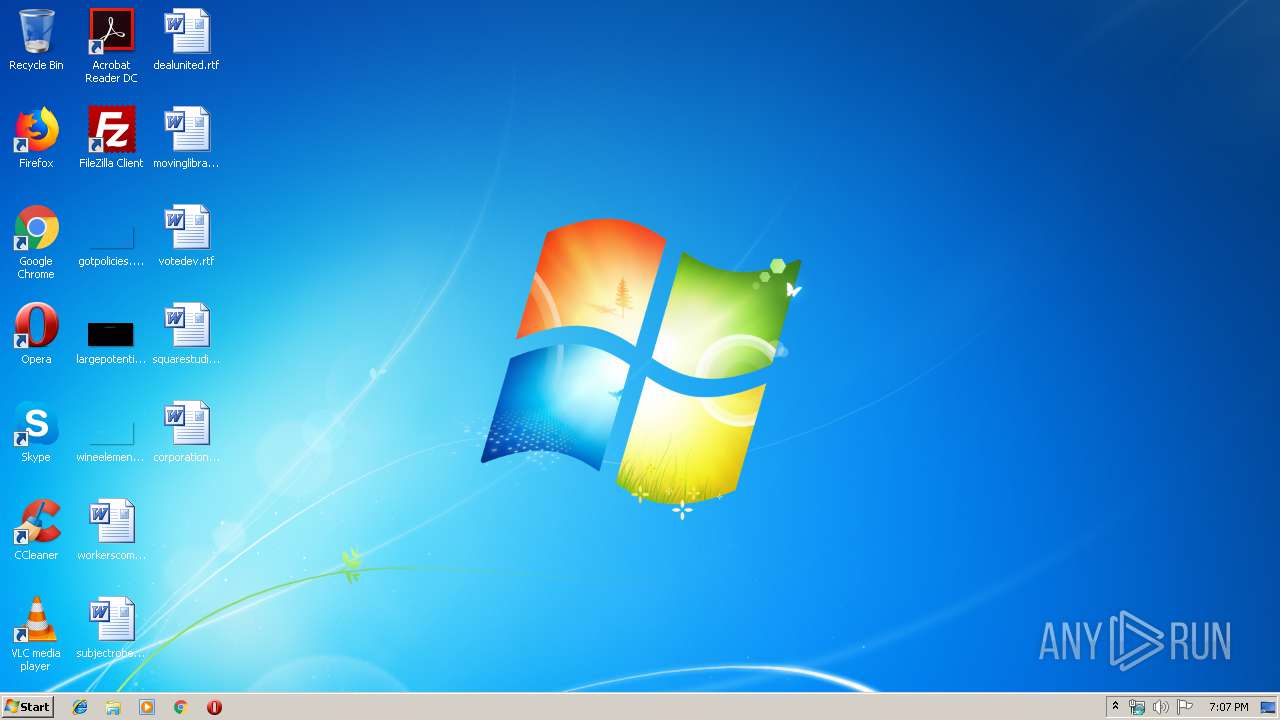
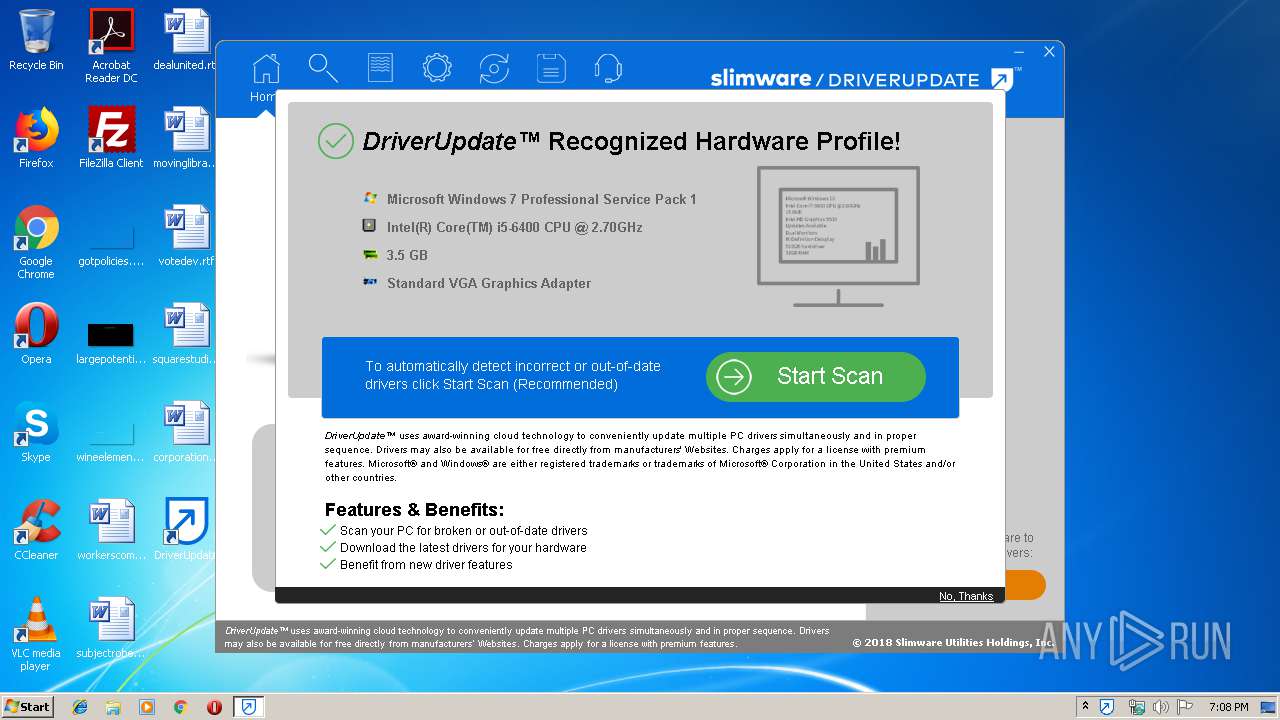
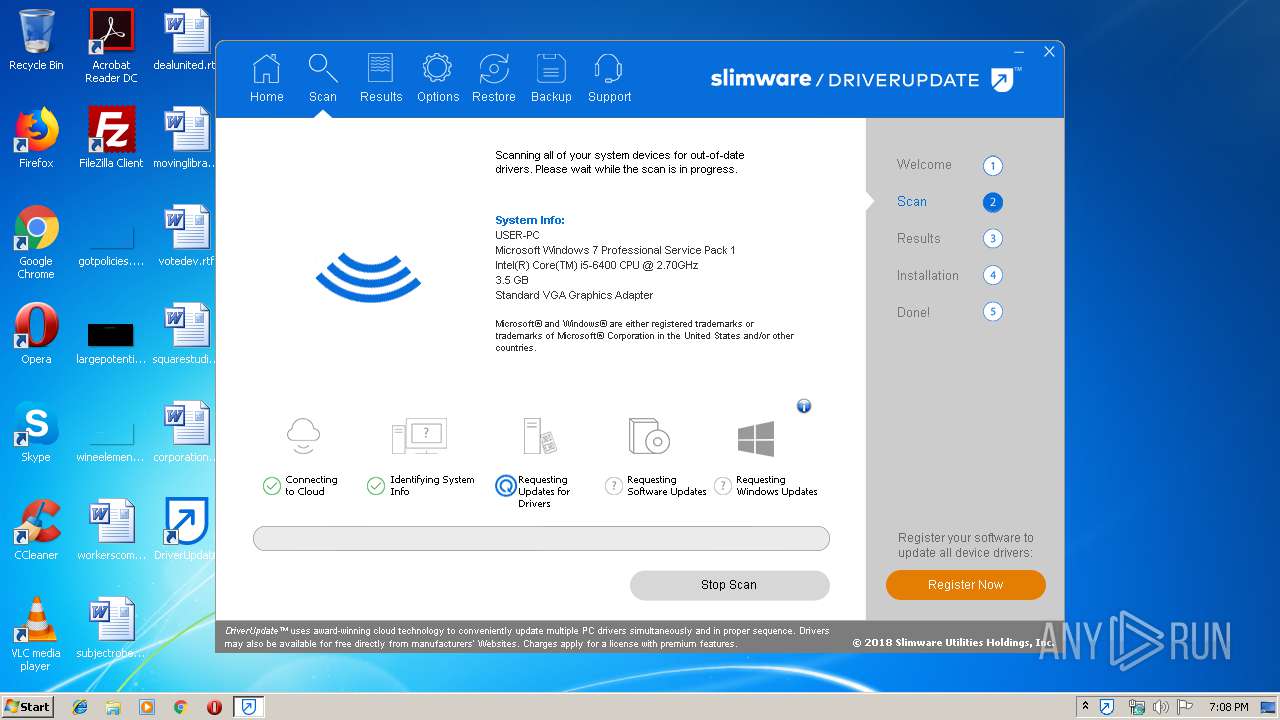
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 69484C39E6AA358B57617B6E6E300D5A |
| SHA1: | F9665FAE82D5F02250B25825E36DE974593623F3 |
| SHA256: | 7177C05A6F7A7759098D5F94B67A8A5C168A4718F5AC04BD4743BF34D1AF8945 |
| SSDEEP: | 3072:D06uN3fztYXIUlQI1p0hDKt3b+zd7uBD/vQiwmJjs7UurJJhK6bJtld82:3e3fzZYWorJYMj2UgXhK6bxS2 |
MALICIOUS
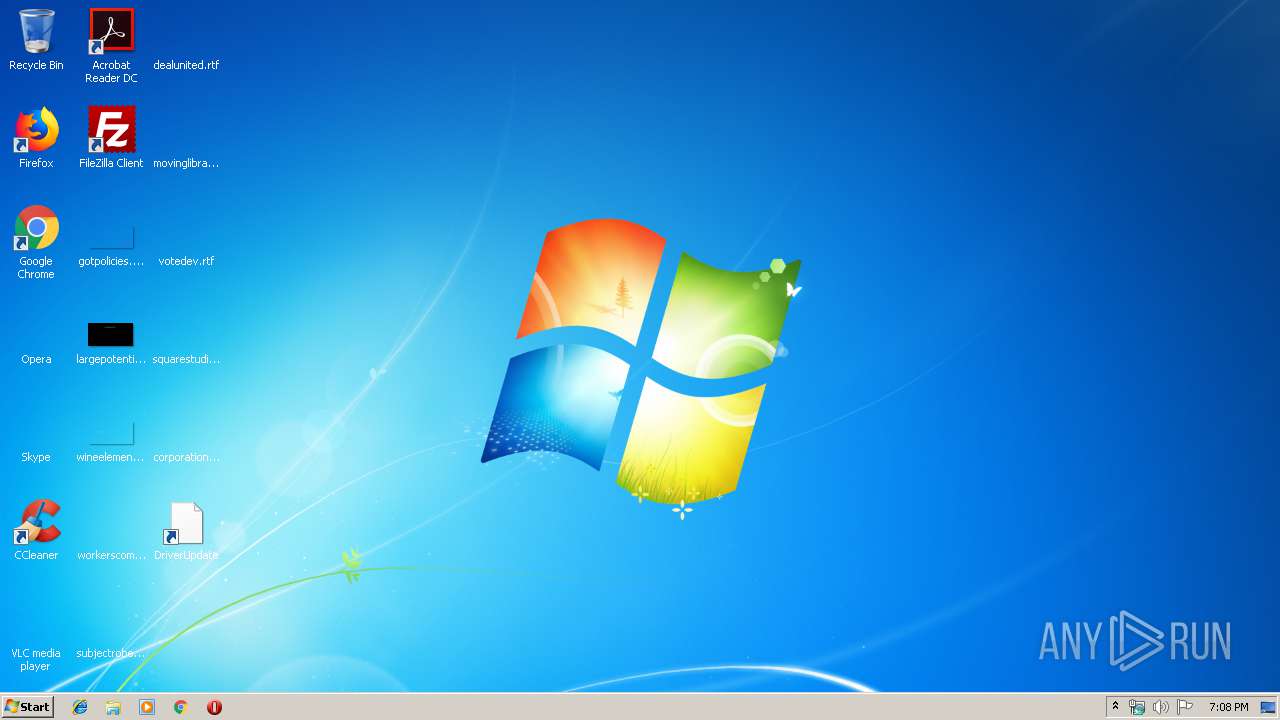
Application was dropped or rewritten from another process
- SlimWare.Session.exe (PID: 1484)
- DriverUpdate-setup.exe (PID: 3960)
- SlimWare.Services.exe (PID: 3856)
Loads dropped or rewritten executable
- csrss.exe (PID: 348)
- svchost.exe (PID: 864)
- DriverUpdate.exe (PID: 3048)
- SlimWare.Services.exe (PID: 3856)
- SlimWare.Session.exe (PID: 1484)
- explorer.exe (PID: 352)
Loads the Task Scheduler DLL interface
- DriverUpdate.exe (PID: 3048)
Loads the Task Scheduler COM API
- DriverUpdate.exe (PID: 3048)
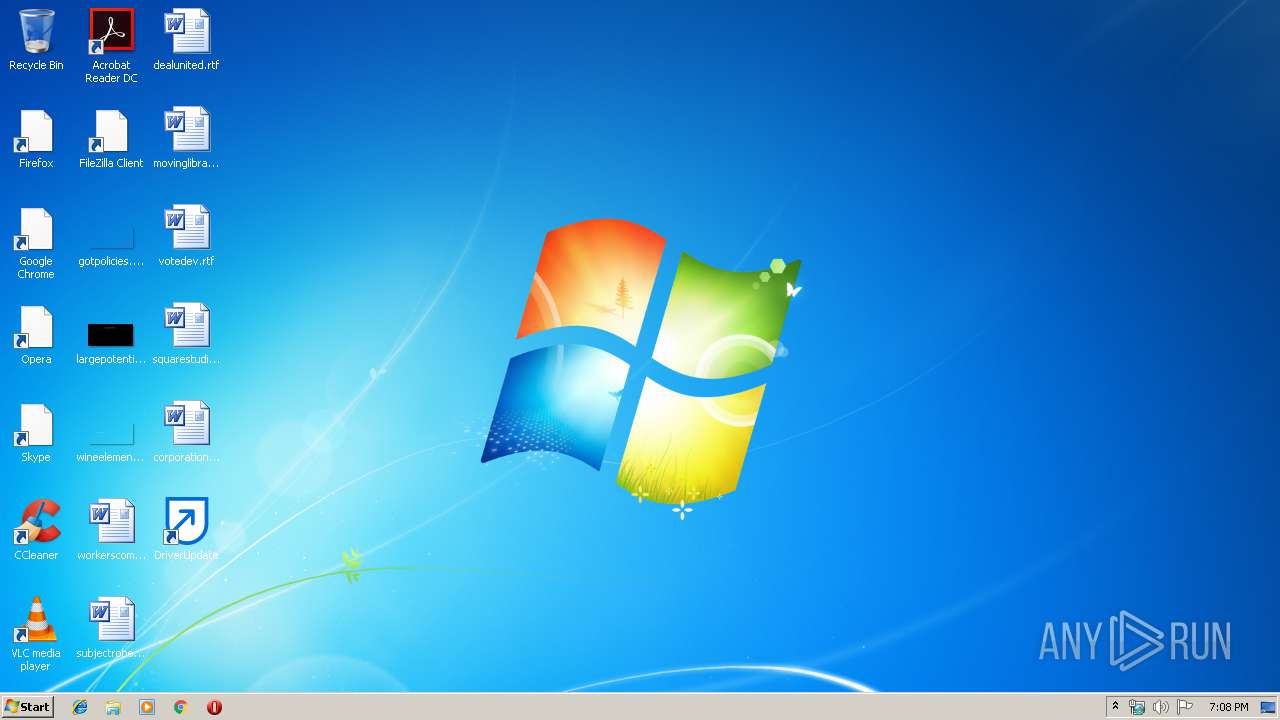
Changes the autorun value in the registry
- DriverUpdate.exe (PID: 3048)
Changes settings of System certificates
- SlimWare.Session.exe (PID: 1484)
SUSPICIOUS
Executable content was dropped or overwritten
- msiexec.exe (PID: 2248)
- DriverUpdate.exe (PID: 3048)
- 460e6a63-122c-433e-b20a-723c010bfde6.exe (PID: 3680)
Changes IE settings (feature browser emulation)
- MsiExec.exe (PID: 3944)
Creates COM task schedule object
- msiexec.exe (PID: 2248)
Executed as Windows Service
- SlimWare.Services.exe (PID: 3856)
Executed via COM
- unsecapp.exe (PID: 1648)
- SlimWare.Session.exe (PID: 1484)
Removes files from Windows directory
- SlimWare.Session.exe (PID: 1484)
- svchost.exe (PID: 864)
Creates files in the Windows directory
- SlimWare.Session.exe (PID: 1484)
- svchost.exe (PID: 864)
Adds / modifies Windows certificates
- SlimWare.Session.exe (PID: 1484)
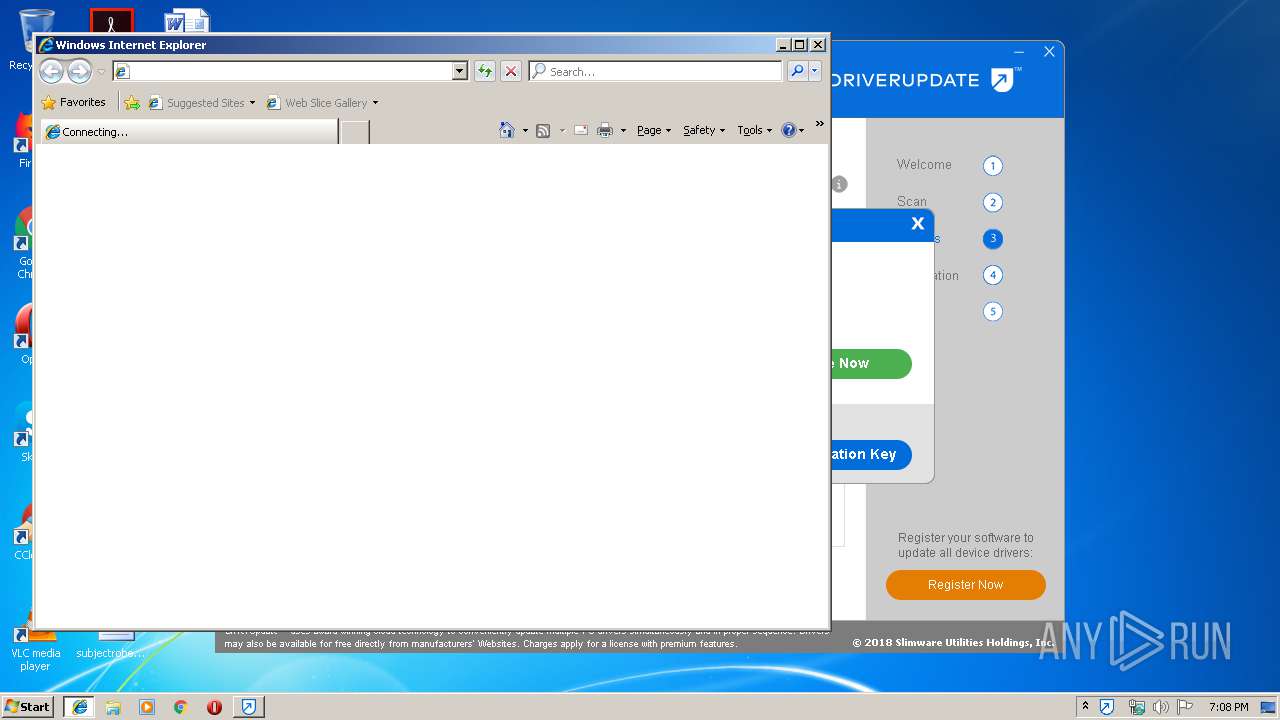
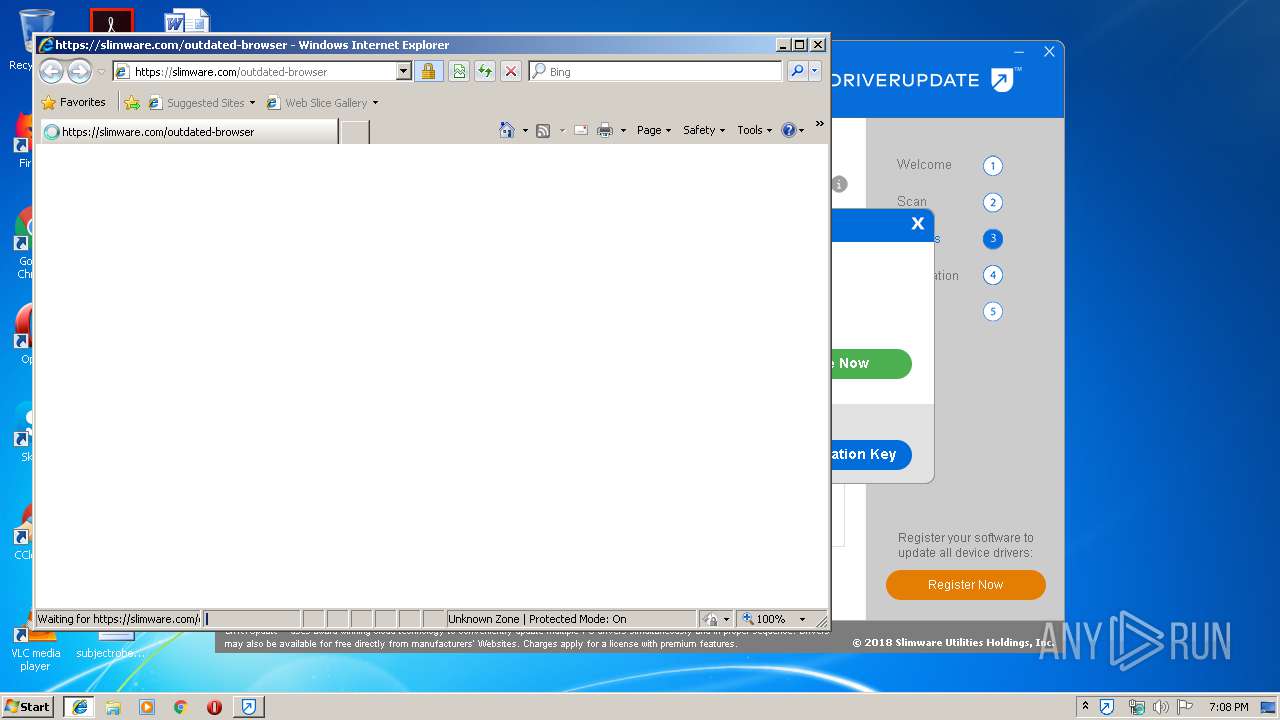
Starts Internet Explorer
- DriverUpdate.exe (PID: 3048)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3944)
Creates files in the program directory
- msiexec.exe (PID: 2248)
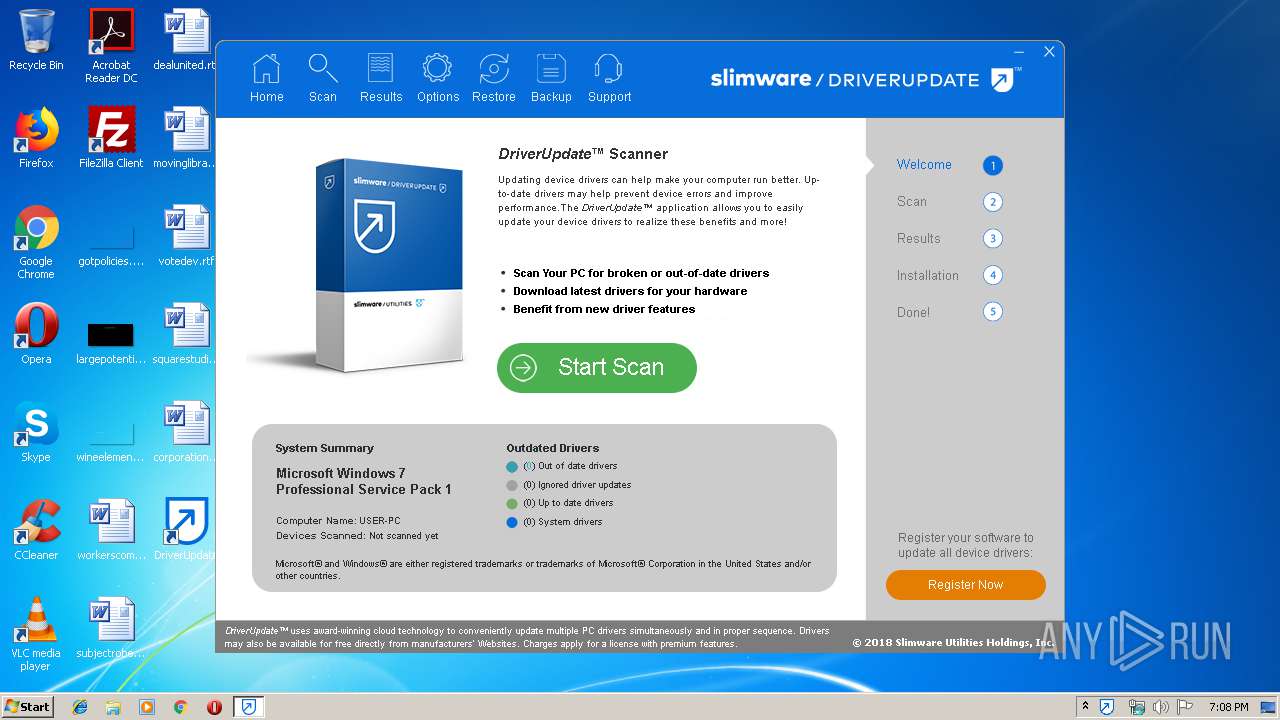
Manual execution by user
- DriverUpdate.exe (PID: 3048)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2248)
Application launched itself
- msiexec.exe (PID: 2248)
Creates a software uninstall entry
- msiexec.exe (PID: 2248)
Reads settings of System Certificates
- SlimWare.Session.exe (PID: 1484)
Changes internet zones settings
- iexplore.exe (PID: 2520)
Reads Internet Cache Settings
- iexplore.exe (PID: 3456)
Creates files in the user directory
- iexplore.exe (PID: 3456)
Reads internet explorer settings
- iexplore.exe (PID: 3456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:01 19:37:13+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 144896 |
| InitializedDataSize: | 107520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14b8b |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.4.1.0 |
| ProductVersionNumber: | 2.4.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | SlimWare Utilities Holdings, Inc. |
| FileDescription: | DriverUpdate SlimWare Downloader |
| FileVersion: | 2.4.1 |
| InternalName: | SlimWare Downloader |
| LegalCopyright: | Copyright 2014-2017 SlimWare Utilities Holdings, Inc. |
| OriginalFileName: | SlimWareDownloader.exe |
| ProductName: | DriverUpdate |
| ProductVersion: | 2.4.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Feb-2019 18:37:13 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | SlimWare Utilities Holdings, Inc. |
| FileDescription: | DriverUpdate SlimWare Downloader |
| FileVersion: | 2.4.1 |
| InternalName: | SlimWare Downloader |
| LegalCopyright: | Copyright 2014-2017 SlimWare Utilities Holdings, Inc. |
| OriginalFilename: | SlimWareDownloader.exe |
| ProductName: | DriverUpdate |
| ProductVersion: | 2.4.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Feb-2019 18:37:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000235AD | 0x00023600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59193 |
.rdata | 0x00025000 | 0x0000C806 | 0x0000CA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.45068 |
.data | 0x00032000 | 0x000052E8 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.19659 |
.rsrc | 0x00038000 | 0x00005950 | 0x00005A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.65242 |
.reloc | 0x0003E000 | 0x00002A6C | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56255 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.31786 | 833 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.04799 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 1.9793 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.94605 | 12740 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
CRYPT32.dll |
KERNEL32.dll |
SHELL32.dll (delay-loaded) |
USER32.dll |
WINTRUST.dll |
ole32.dll |
Total processes
48
Monitored processes
14
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | — | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | "C:\Program Files\SlimWare Utilities\Services\SlimWare.Session.exe" -Embedding | C:\Program Files\SlimWare Utilities\Services\SlimWare.Session.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: SlimWare Utilities Holdings, Inc. Integrity Level: SYSTEM Description: SlimWare.Session Server Exit code: 0 Version: 1.0.5 Modules
| |||||||||||||||
| 1648 | C:\Windows\system32\wbem\unsecapp.exe -Embedding | C:\Windows\system32\wbem\unsecapp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sink to receive asynchronous callbacks for WMI client application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1876 | "C:\Users\admin\AppData\Local\Temp\460e6a63-122c-433e-b20a-723c010bfde6.exe" | C:\Users\admin\AppData\Local\Temp\460e6a63-122c-433e-b20a-723c010bfde6.exe | — | explorer.exe | |||||||||||
User: admin Company: SlimWare Utilities Holdings, Inc. Integrity Level: MEDIUM Description: DriverUpdate SlimWare Downloader Exit code: 3221226540 Version: 2.4.1 Modules
| |||||||||||||||
| 2248 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://slimware.com/register/driverupdate?newgui=1&installer_data=ewogICAidWxfc3R1YmlkIiA6ICIyRkM0NTc0NS04MkQzLTQwNDctOUM2Mi1CNDVBOUM0MjJCOUMi%0D%0ACn0K&config=YTo1OntzOjY6Im1lbW9yeSI7czo2OiIzLjUgR0IiO3M6NToibW9kZWwiO3M6NDoiREVMTCI7czo4%0D%0AOiJncmFwaGljcyI7czoyOToiU3RhbmRhcmQgVkdBIEdyYXBoaWNzIEFkYXB0ZXIiO3M6OToicHJv%0D%0AY2Vzc29yIjtzOjM5OiJJbnRlbChSKSBDb3JlKFRNKSBpNS02NDAwIENQVSBAIDIuNzBHSHoiO3M6%0D%0AMTI6Im1hbnVmYWN0dXJlciI7czo0OiJERUxMIjt9&machineId=1FC6F66F-7870-45D5-9C76-D0BEC5A68D21&installId=7C9514C1-1BFA-4186-8D46-FD85008FF370&count=4&productVersion=5.8.10.33" | C:\Program Files\Internet Explorer\iexplore.exe | DriverUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3048 | "C:\Program Files\DriverUpdate\DriverUpdate.exe" /byUser | C:\Program Files\DriverUpdate\DriverUpdate.exe | explorer.exe | ||||||||||||
User: admin Company: SlimWare Utilities, Inc. Integrity Level: MEDIUM Description: DriverUpdate Exit code: 0 Version: 5.8.10 Modules
| |||||||||||||||
| 3456 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2520 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 239
Read events
1 813
Write events
401
Delete events
25
Modification events
| (PID) Process: | (3680) 460e6a63-122c-433e-b20a-723c010bfde6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\SlimWare Utilities Inc |
| Operation: | write | Name: | MachineID |
Value: 6FF6C61F7078D5459C76D0BEC5A68D21 | |||
| (PID) Process: | (3680) 460e6a63-122c-433e-b20a-723c010bfde6.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3680) 460e6a63-122c-433e-b20a-723c010bfde6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\SlimWare Utilities Inc\DriverUpdate\InstallerData |
| Operation: | write | Name: | ul_stubid |
Value: 2FC45745-82D3-4047-9C62-B45A9C422B9C | |||
| (PID) Process: | (2248) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000_CLASSES\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2248) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: C808000096CCE97B68ACD501 | |||
| (PID) Process: | (2248) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: DE35B83E394240278C6F7AA476B3ADD27DCF75877149D409E3B64AE7BD517A30 | |||
| (PID) Process: | (2248) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2248) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\InProgress |
| Operation: | write | Name: | |
Value: C:\Windows\Installer\39f1af.ipi | |||
| (PID) Process: | (3944) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Owner |
Value: 680F000040D8977C68ACD501 | |||
| (PID) Process: | (3944) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | SessionHash |
Value: AD8471A607E29824BD3ABF726C47E4F9CD86247B7B9400D067B4F92387E0BA72 | |||
Executable files
30
Suspicious files
6
Text files
19
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3680 | 460e6a63-122c-433e-b20a-723c010bfde6.exe | C:\Users\admin\AppData\Local\Temp\SWICDE9.tmp | — | |
MD5:— | SHA256:— | |||
| 3960 | DriverUpdate-setup.exe | C:\Users\admin\AppData\Local\Temp\SIOUT3795765\DriverUpdate-setup.msi | — | |
MD5:— | SHA256:— | |||
| 3960 | DriverUpdate-setup.exe | C:\Users\admin\AppData\Local\Downloaded Installers\{6C8E0198-FF1D-40FB-A26C-9AFE8AF84D3C}\setup.msi | — | |
MD5:— | SHA256:— | |||
| 2248 | msiexec.exe | C:\Windows\Installer\39f1ad.msi | — | |
MD5:— | SHA256:— | |||
| 2248 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF1706F36674AFCC57.TMP | — | |
MD5:— | SHA256:— | |||
| 2248 | msiexec.exe | C:\Windows\Installer\MSIF5D6.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | msiexec.exe | C:\Program Files\DriverUpdate\DriverUpdate.exe | — | |
MD5:— | SHA256:— | |||
| 2248 | msiexec.exe | C:\Windows\Installer\39f1af.ipi | binary | |
MD5:— | SHA256:— | |||
| 3680 | 460e6a63-122c-433e-b20a-723c010bfde6.exe | C:\Users\admin\AppData\Local\Temp\DriverUpdate-setup.exe | executable | |
MD5:— | SHA256:— | |||
| 864 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
16
DNS requests
13
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3680 | 460e6a63-122c-433e-b20a-723c010bfde6.exe | GET | 301 | 54.86.231.162:80 | http://apps-api.slimwareutilities.com/install/du/6.1/x86/DriverUpdate-setup.exe?machineId=1FC6F66F-7870-45D5-9C76-D0BEC5A68D21 | US | — | — | malicious |
3680 | 460e6a63-122c-433e-b20a-723c010bfde6.exe | GET | 200 | 52.4.3.53:80 | http://stc.slimwareutilities.com/gettrack?product=SW2 | US | — | — | shared |
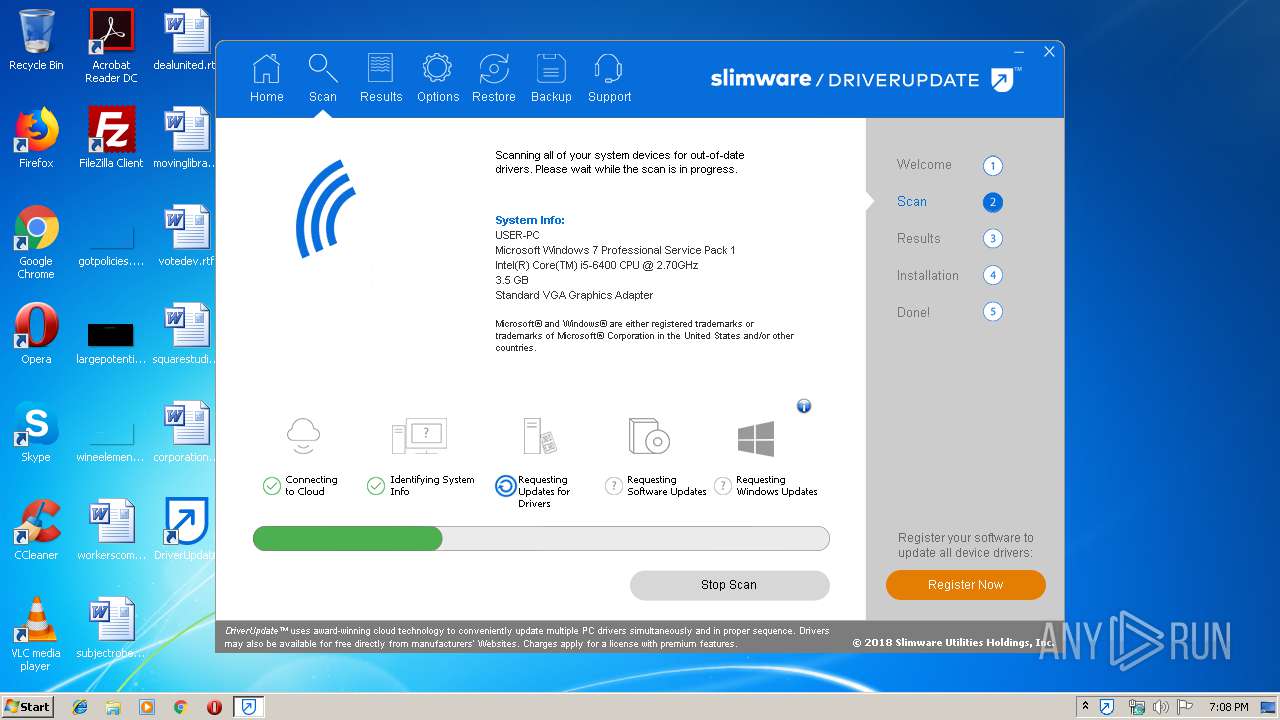
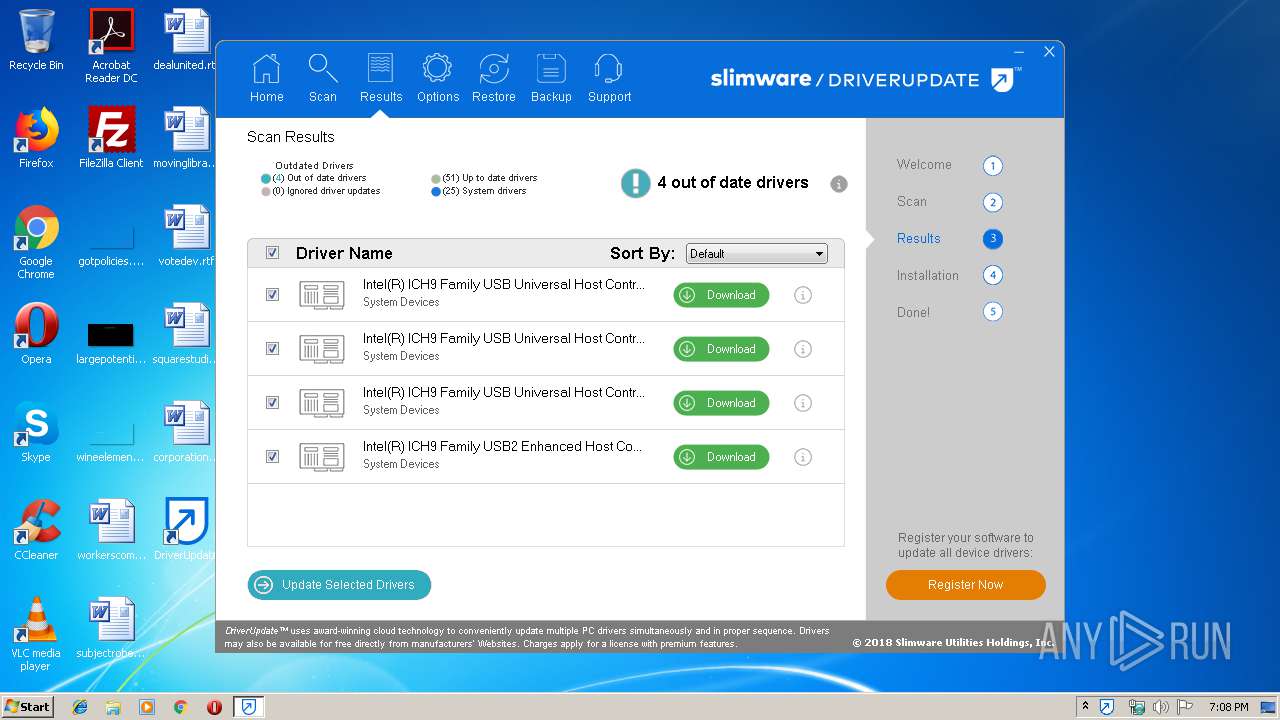
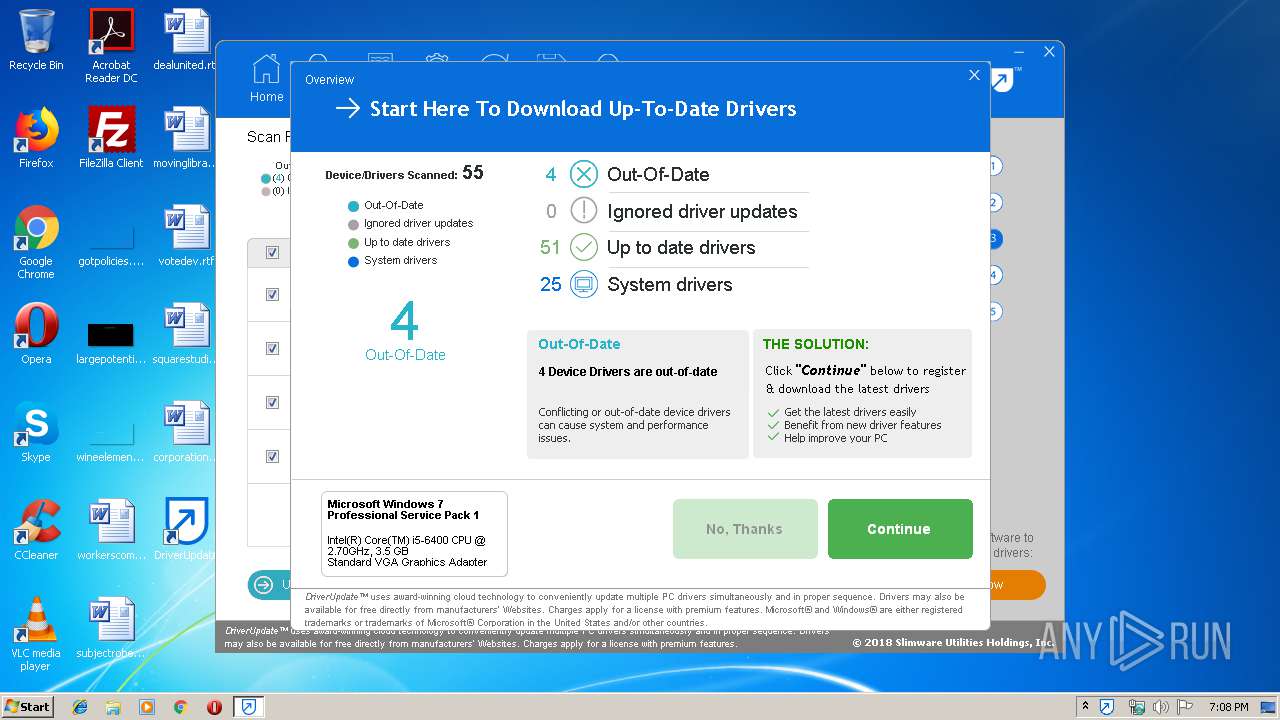
1484 | SlimWare.Session.exe | GET | 200 | 34.236.116.104:80 | http://trk.slimwareutilities.com/ulc.php?ev=UIView&platformOSVersion=6.1&installId=7C9514C1-1BFA-4186-8D46-FD85008FF370&view=%2FIntro&ul_stubid=2FC45745-82D3-4047-9C62-B45A9C422B9C&productVersion=5.8.10&product=SW2&sessionid=47D90C13-F436-4909-B4FD-EC727B5ED3D0&machineId=1FC6F66F-7870-45D5-9C76-D0BEC5A68D21&platformOS=Windows | US | text | 2 b | malicious |
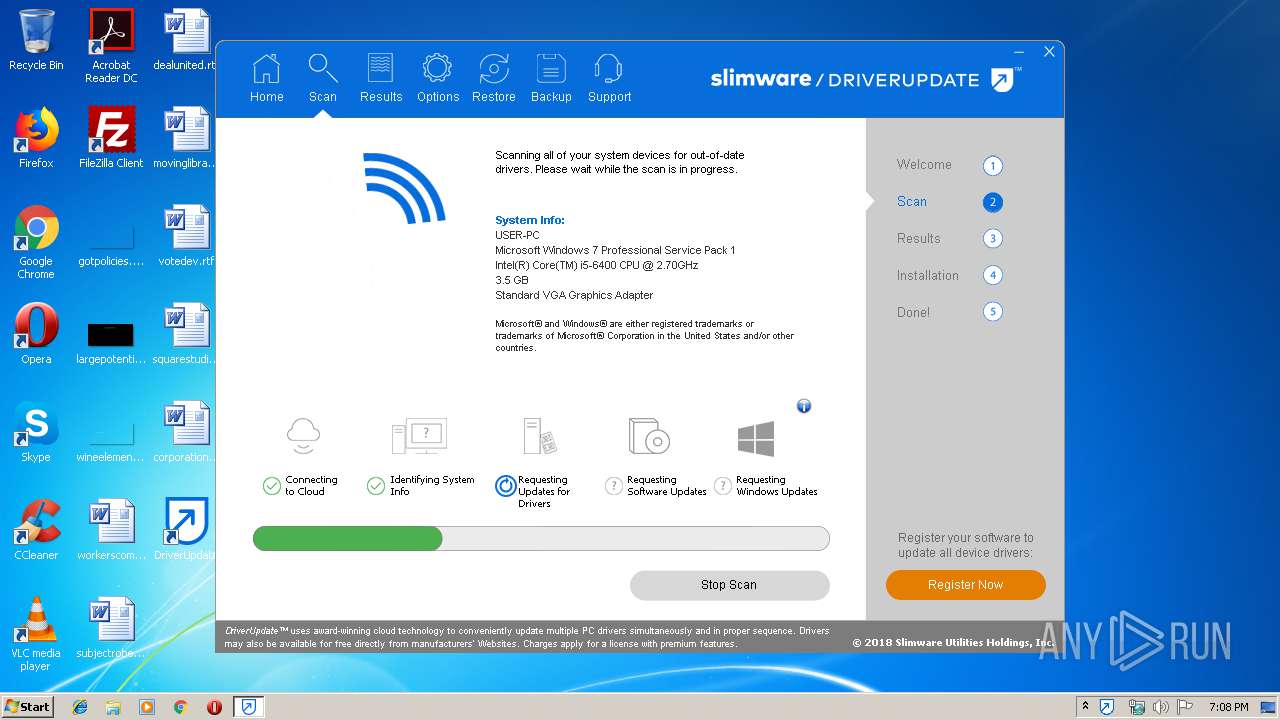
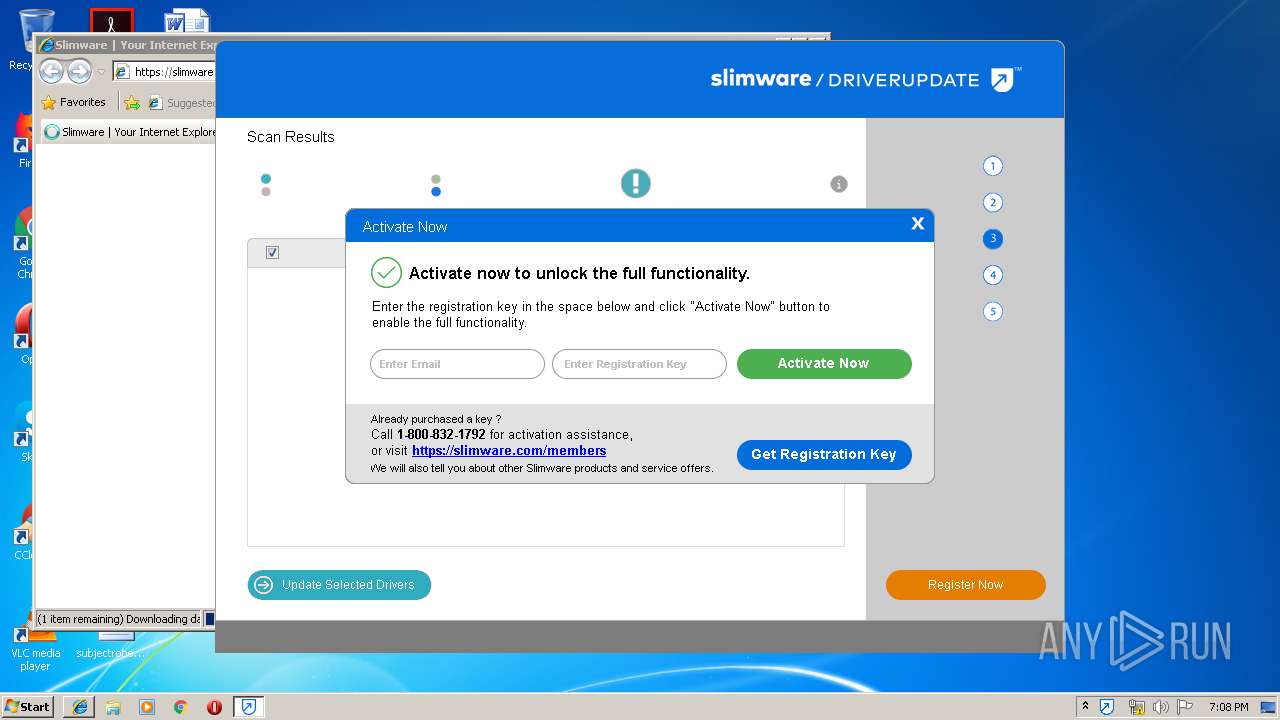
1484 | SlimWare.Session.exe | GET | 200 | 34.236.116.104:80 | http://trk.slimwareutilities.com/ulc.php?ev=ScanResults&timeSpent=5&platformOSVersion=6.1&systemDriverCount=29&engine=DriverUpdater&installId=7C9514C1-1BFA-4186-8D46-FD85008FF370&upToDateDriverCount=22&resultTotalCount=4&ul_stubid=2FC45745-82D3-4047-9C62-B45A9C422B9C&productVersion=5.8.10&product=SW2&machineId=1FC6F66F-7870-45D5-9C76-D0BEC5A68D21&platformOS=Windows&ignoredDriverCount=0 | US | text | 2 b | malicious |
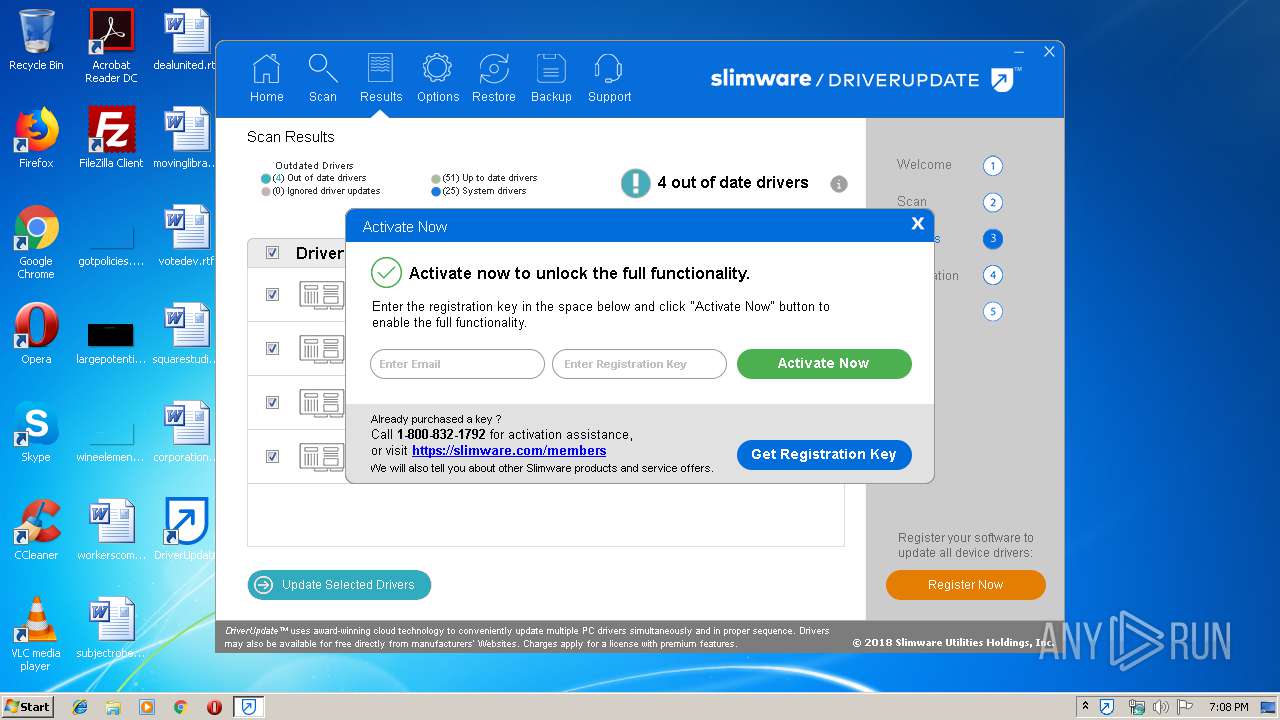
1484 | SlimWare.Session.exe | GET | 200 | 34.236.116.104:80 | http://trk.slimwareutilities.com/ulc.php?ev=UIView&platformOSVersion=6.1&installId=7C9514C1-1BFA-4186-8D46-FD85008FF370&view=%2FActivation&ul_stubid=2FC45745-82D3-4047-9C62-B45A9C422B9C&productVersion=5.8.10&product=SW2&sessionid=47D90C13-F436-4909-B4FD-EC727B5ED3D0&machineId=1FC6F66F-7870-45D5-9C76-D0BEC5A68D21&platformOS=Windows | US | text | 2 b | malicious |
1484 | SlimWare.Session.exe | GET | 200 | 34.236.116.104:80 | http://trk.slimwareutilities.com/ulc.php?ev=UIView&platformOSVersion=6.1&installId=7C9514C1-1BFA-4186-8D46-FD85008FF370&view=%2FMain%2FResults&ul_stubid=2FC45745-82D3-4047-9C62-B45A9C422B9C&productVersion=5.8.10&product=SW2&sessionid=47D90C13-F436-4909-B4FD-EC727B5ED3D0&machineId=1FC6F66F-7870-45D5-9C76-D0BEC5A68D21&platformOS=Windows | US | text | 2 b | malicious |
3048 | DriverUpdate.exe | POST | 200 | 54.86.231.162:80 | http://apps-api.slimwareutilities.com/rpc/version-info | US | text | 478 b | malicious |
1484 | SlimWare.Session.exe | GET | 200 | 34.236.116.104:80 | http://trk.slimwareutilities.com/ulc.php?ev=UIControl&platformOSVersion=6.1&installId=7C9514C1-1BFA-4186-8D46-FD85008FF370&ul_stubid=2FC45745-82D3-4047-9C62-B45A9C422B9C&productVersion=5.8.10&product=SW2&sessionid=47D90C13-F436-4909-B4FD-EC727B5ED3D0&machineId=1FC6F66F-7870-45D5-9C76-D0BEC5A68D21&owner=%2FBuyNow&platformOS=Windows&label=Continue | US | text | 2 b | malicious |
1484 | SlimWare.Session.exe | GET | 200 | 34.236.116.104:80 | http://trk.slimwareutilities.com/ulc.php?ev=UIView&platformOSVersion=6.1&installId=7C9514C1-1BFA-4186-8D46-FD85008FF370&view=%2FBuyNow&ul_stubid=2FC45745-82D3-4047-9C62-B45A9C422B9C&productVersion=5.8.10&product=SW2&sessionid=47D90C13-F436-4909-B4FD-EC727B5ED3D0&machineId=1FC6F66F-7870-45D5-9C76-D0BEC5A68D21&platformOS=Windows | US | text | 2 b | malicious |
1484 | SlimWare.Session.exe | GET | 200 | 34.236.116.104:80 | http://trk.slimwareutilities.com/ulc.php?ev=UIControl&platformOSVersion=6.1&installId=7C9514C1-1BFA-4186-8D46-FD85008FF370&ul_stubid=2FC45745-82D3-4047-9C62-B45A9C422B9C&productVersion=5.8.10&product=SW2&sessionid=47D90C13-F436-4909-B4FD-EC727B5ED3D0&machineId=1FC6F66F-7870-45D5-9C76-D0BEC5A68D21&owner=%2FIntro&platformOS=Windows&label=Start%20Scan | US | text | 2 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3680 | 460e6a63-122c-433e-b20a-723c010bfde6.exe | 52.4.3.53:80 | stc.slimwareutilities.com | Amazon.com, Inc. | US | malicious |
3680 | 460e6a63-122c-433e-b20a-723c010bfde6.exe | 52.7.3.6:80 | trk.slimwareutilities.com | Amazon.com, Inc. | US | malicious |
3680 | 460e6a63-122c-433e-b20a-723c010bfde6.exe | 54.86.231.162:80 | apps-api.slimwareutilities.com | Amazon.com, Inc. | US | malicious |
3680 | 460e6a63-122c-433e-b20a-723c010bfde6.exe | 13.35.254.215:80 | download.driverupdate.net | — | US | suspicious |
3048 | DriverUpdate.exe | 54.86.231.162:80 | apps-api.slimwareutilities.com | Amazon.com, Inc. | US | malicious |
1484 | SlimWare.Session.exe | 34.239.217.2:443 | messaging.slimware.com | Amazon.com, Inc. | US | unknown |
1484 | SlimWare.Session.exe | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3456 | iexplore.exe | 3.209.42.54:443 | slimware.com | — | US | unknown |
2520 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3456 | iexplore.exe | 172.217.22.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stc.slimwareutilities.com |
| shared |
trk.slimwareutilities.com |
| unknown |
apps-api.slimwareutilities.com |
| malicious |
download.driverupdate.net |
| shared |
www.download.windowsupdate.com |
| whitelisted |
messaging.slimware.com |
| unknown |
driverrpc.driverupdate.net |
| unknown |
slimware.com |
| unknown |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3680 | 460e6a63-122c-433e-b20a-723c010bfde6.exe | Generic Protocol Command Decode | SURICATA HTTP Request abnormal Content-Encoding header |
3680 | 460e6a63-122c-433e-b20a-723c010bfde6.exe | Potentially Bad Traffic | ET POLICY Executable served from Amazon S3 |
3680 | 460e6a63-122c-433e-b20a-723c010bfde6.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1484 | SlimWare.Session.exe | Generic Protocol Command Decode | SURICATA HTTP Request abnormal Content-Encoding header |
1484 | SlimWare.Session.exe | Generic Protocol Command Decode | SURICATA HTTP Request abnormal Content-Encoding header |
1484 | SlimWare.Session.exe | Generic Protocol Command Decode | SURICATA HTTP Request abnormal Content-Encoding header |
1484 | SlimWare.Session.exe | Generic Protocol Command Decode | SURICATA HTTP Request abnormal Content-Encoding header |
1484 | SlimWare.Session.exe | Generic Protocol Command Decode | SURICATA HTTP Request abnormal Content-Encoding header |
1484 | SlimWare.Session.exe | Generic Protocol Command Decode | SURICATA HTTP Request abnormal Content-Encoding header |
1484 | SlimWare.Session.exe | Generic Protocol Command Decode | SURICATA HTTP Request abnormal Content-Encoding header |
5 ETPRO signatures available at the full report