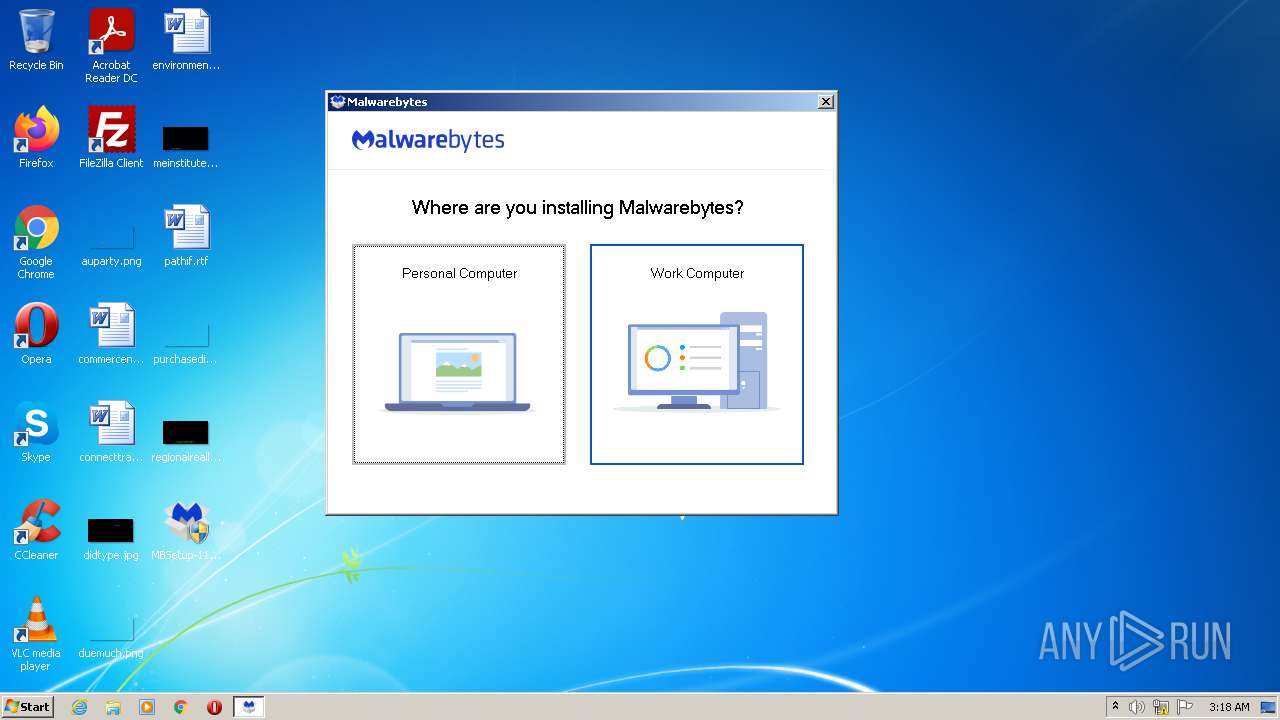
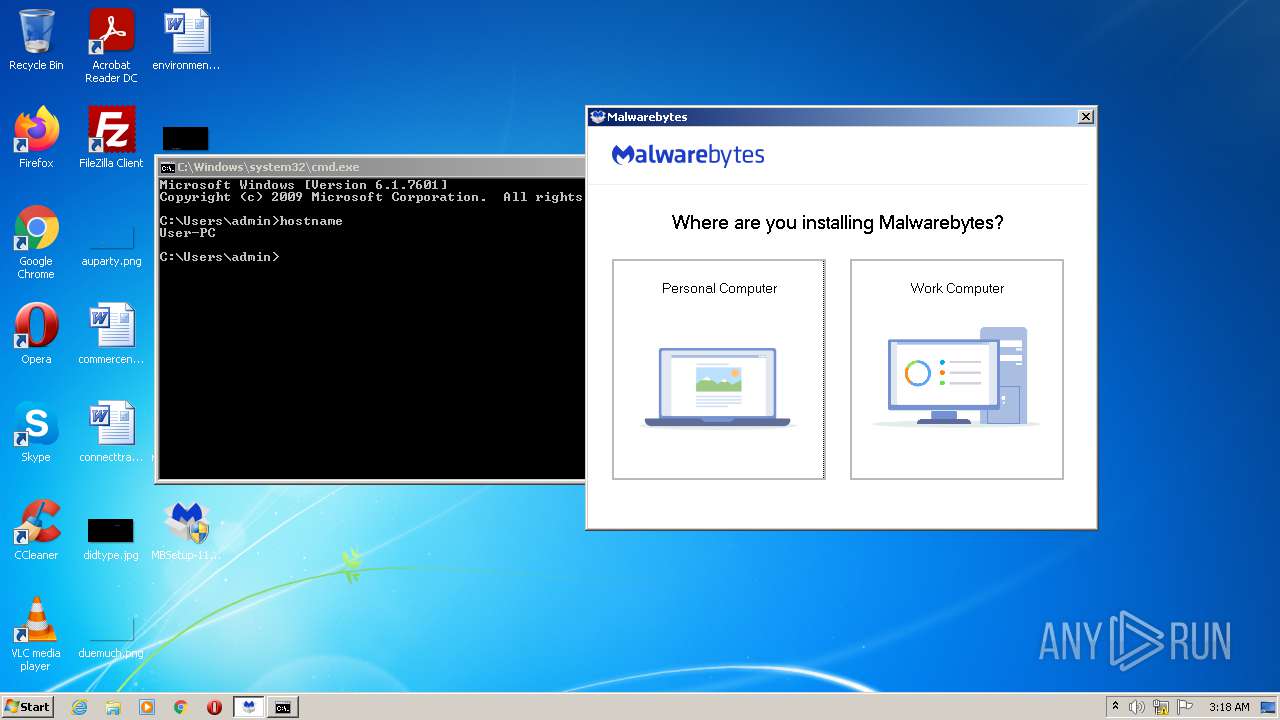
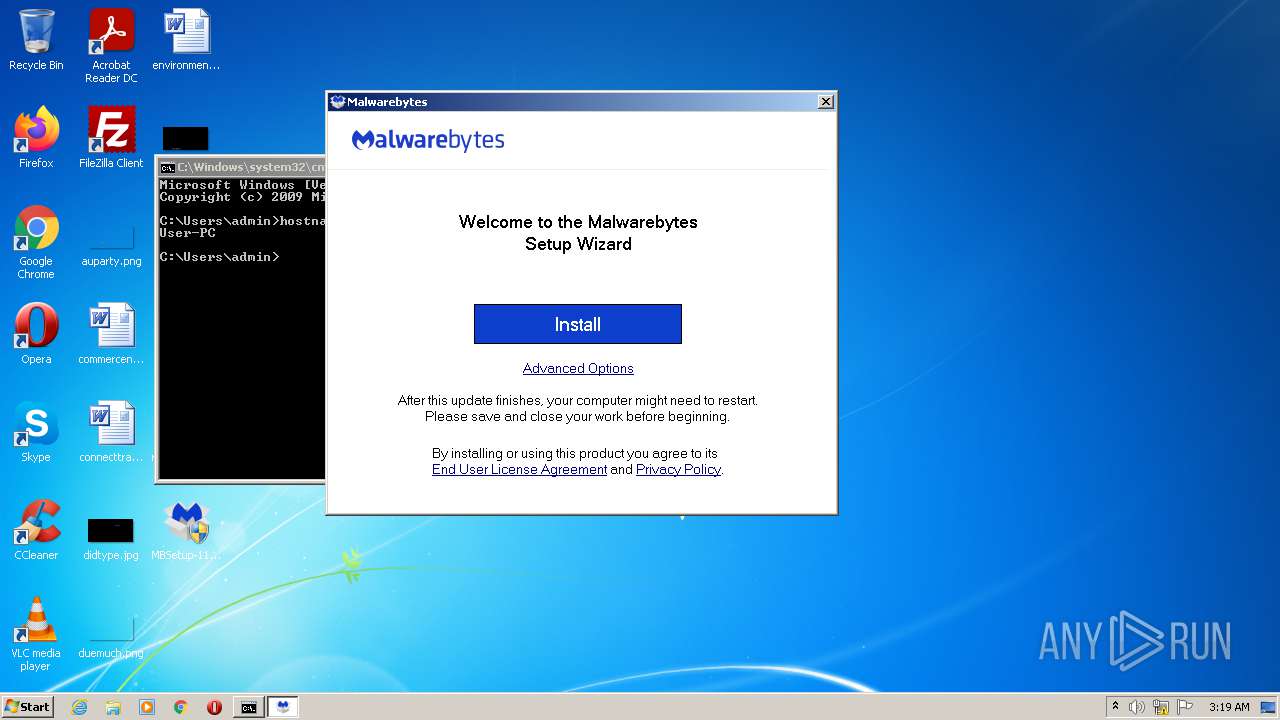
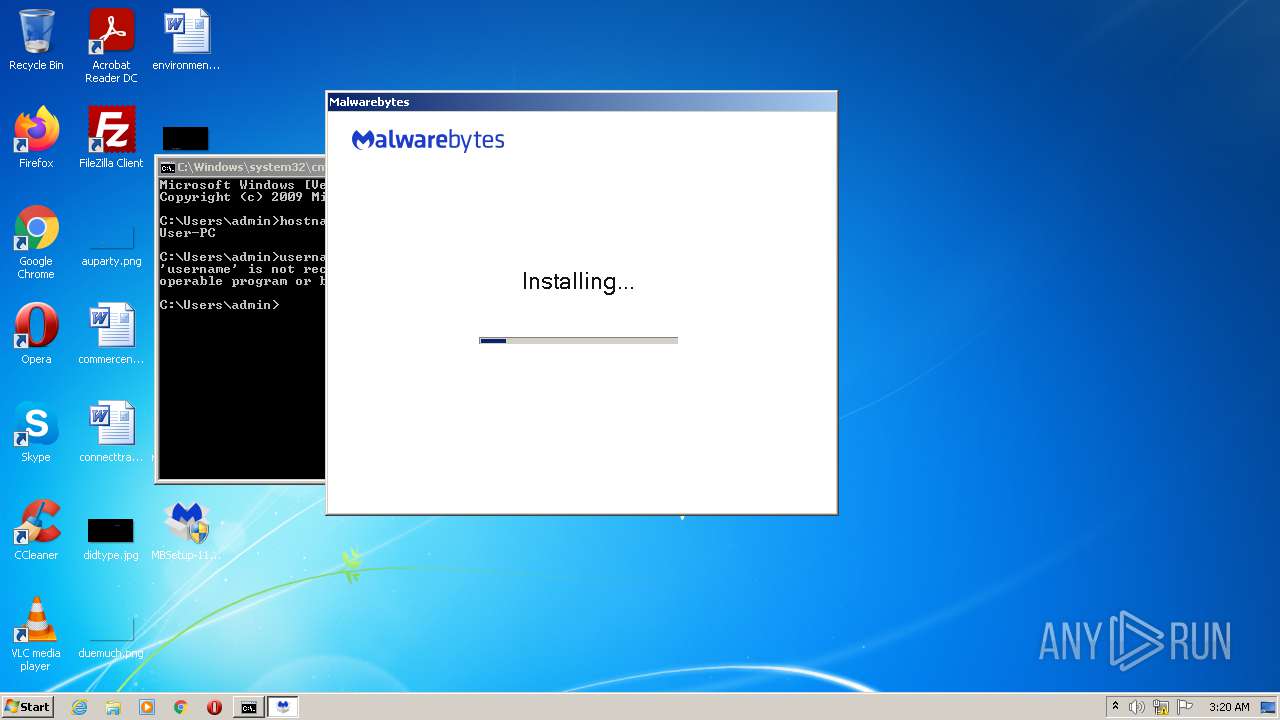
| File name: | MBSetup-119967.119967-consumer.exe |
| Full analysis: | https://app.any.run/tasks/679b99b6-d047-43a4-94ae-d7e5c3e630bb |
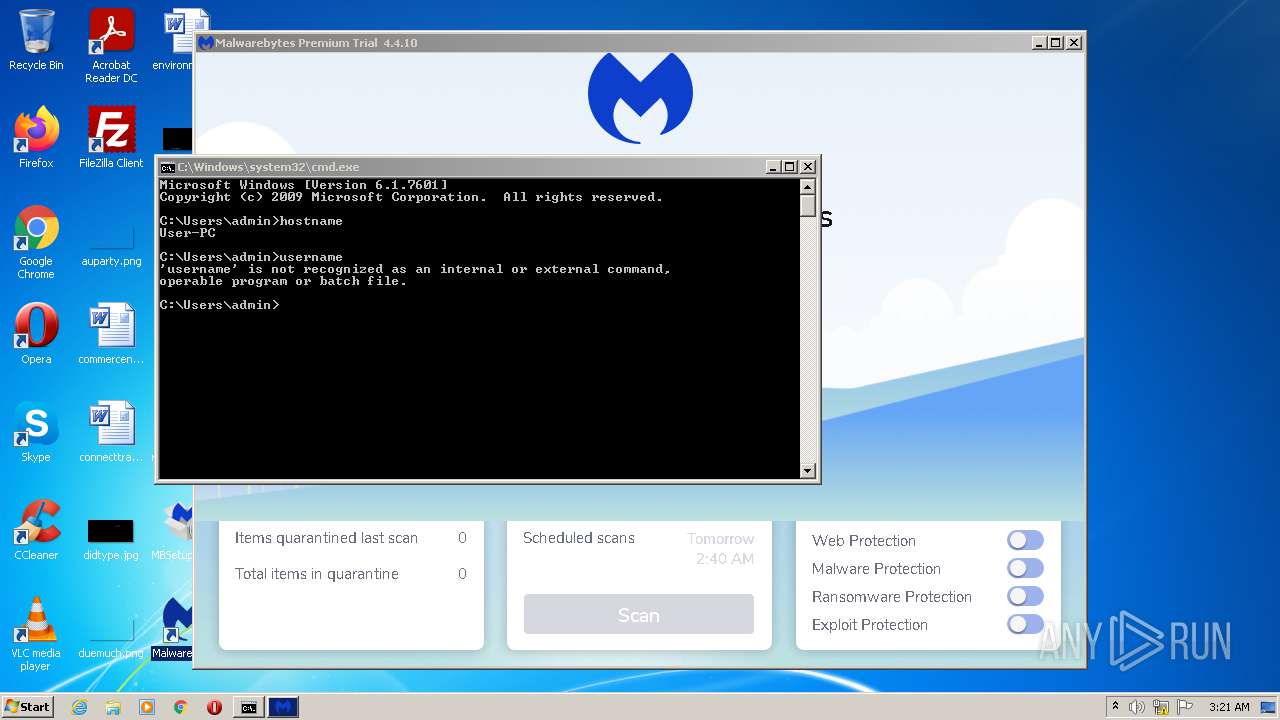
| Verdict: | Malicious activity |
| Analysis date: | November 12, 2021, 03:18:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E310754C3A675EAB7DFC9189DA89B2B7 |
| SHA1: | 9C3DDBDAF79B1ECE068BD56C1DFFCCA92973E7AF |
| SHA256: | 7176CB7FAE5A66D9D823E63A6629E1B6E4ACC8FBCFB78F6150BD32952AA0C8A0 |
| SSDEEP: | 24576:O2yN+CUdUKmuk3i+XzZxX0uY4Z4ekEwixNmf:dFtAP31XzZ+udZ41Ewixwf |
MALICIOUS
Application was dropped or rewritten from another process
- MBAMInstallerService.exe (PID: 3108)
- MBAMService.exe (PID: 2164)
- MBAMService.exe (PID: 2720)
- mbamtray.exe (PID: 3556)
- mbam.exe (PID: 3648)
- mbam.exe (PID: 2932)
- MBAMWsc.exe (PID: 3876)
Loads dropped or rewritten executable
- MBAMInstallerService.exe (PID: 3108)
- SearchProtocolHost.exe (PID: 1588)
- MBAMService.exe (PID: 2720)
- mbamtray.exe (PID: 3556)
- mbam.exe (PID: 3648)
- mbam.exe (PID: 2932)
Changes settings of System certificates
- certutil.exe (PID: 3372)
- certutil.exe (PID: 2428)
- certutil.exe (PID: 2340)
- MBAMService.exe (PID: 2720)
Drops executable file immediately after starts
- MBAMService.exe (PID: 2720)
Steals credentials from Web Browsers
- MBAMService.exe (PID: 2720)
Actions looks like stealing of personal data
- MBAMService.exe (PID: 2720)
SUSPICIOUS
Searches for installed software
- MBSetup-119967.119967-consumer.exe (PID: 3888)
- MBAMInstallerService.exe (PID: 3108)
- MBAMService.exe (PID: 2720)
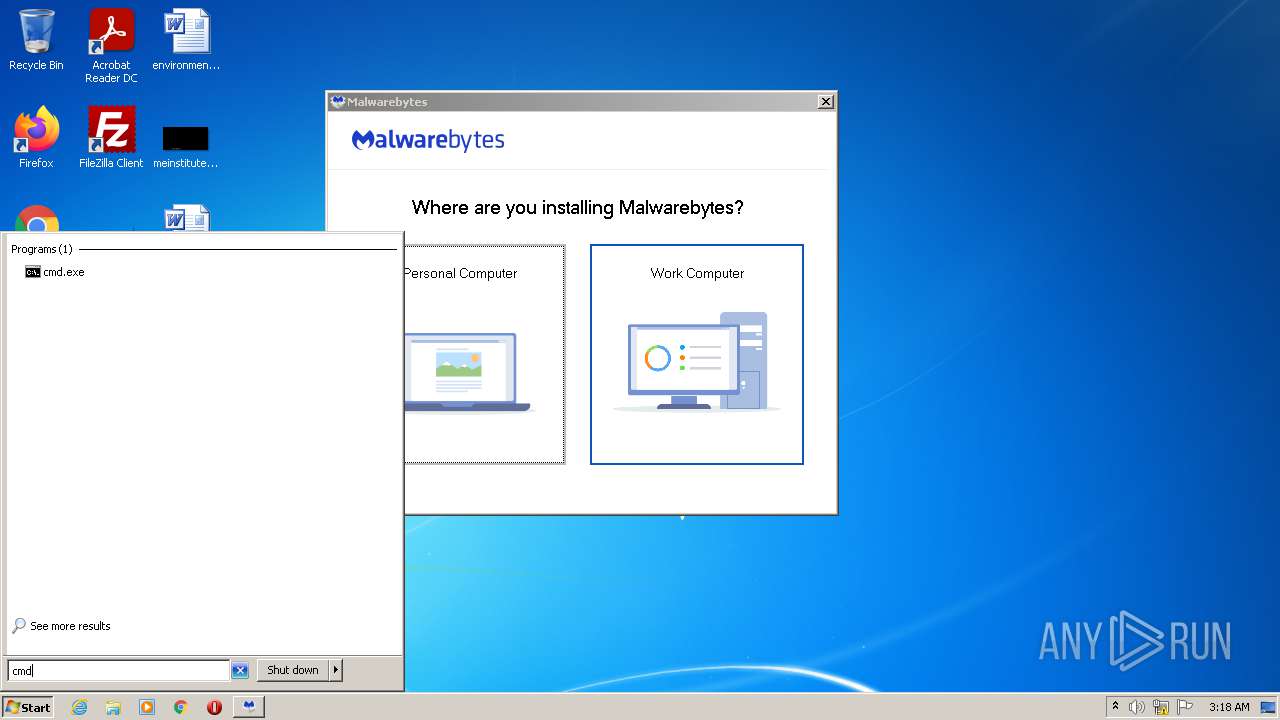
Checks supported languages
- MBSetup-119967.119967-consumer.exe (PID: 3888)
- cmd.exe (PID: 3656)
- MBAMInstallerService.exe (PID: 3108)
- MBAMService.exe (PID: 2164)
- MBAMService.exe (PID: 2720)
- mbamtray.exe (PID: 3556)
- mbam.exe (PID: 3648)
- mbam.exe (PID: 2932)
- MBAMWsc.exe (PID: 3876)
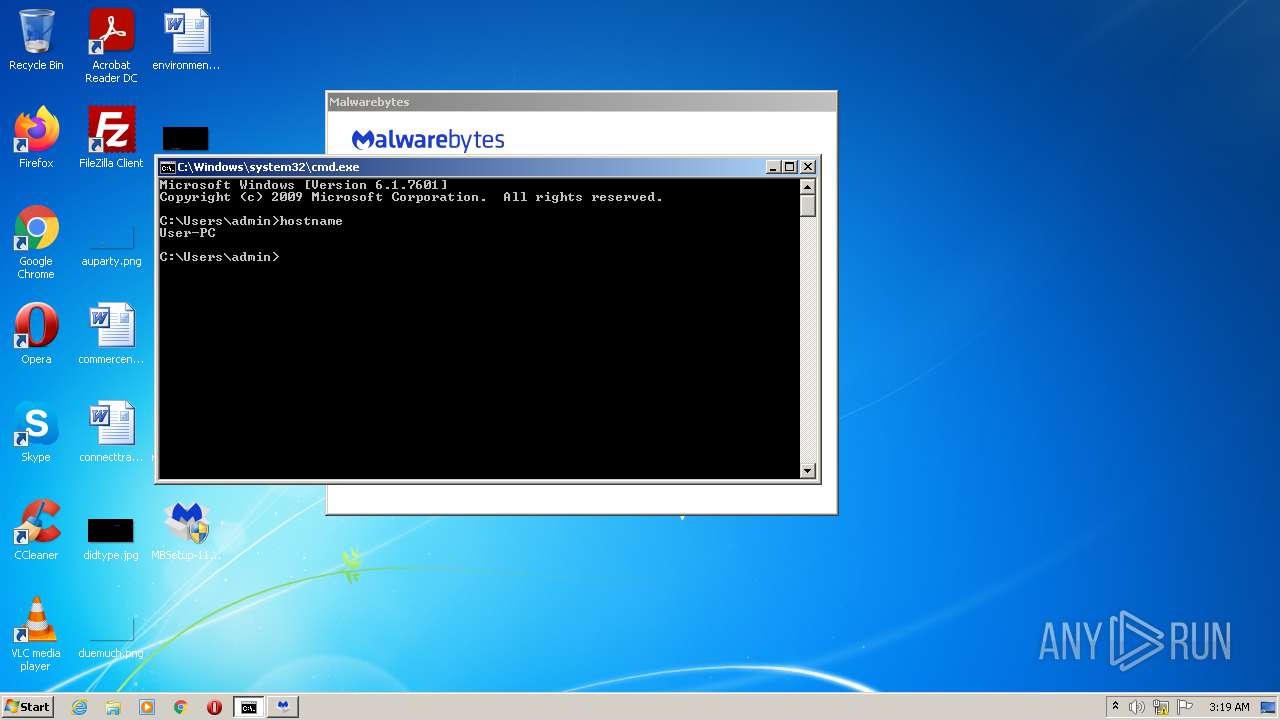
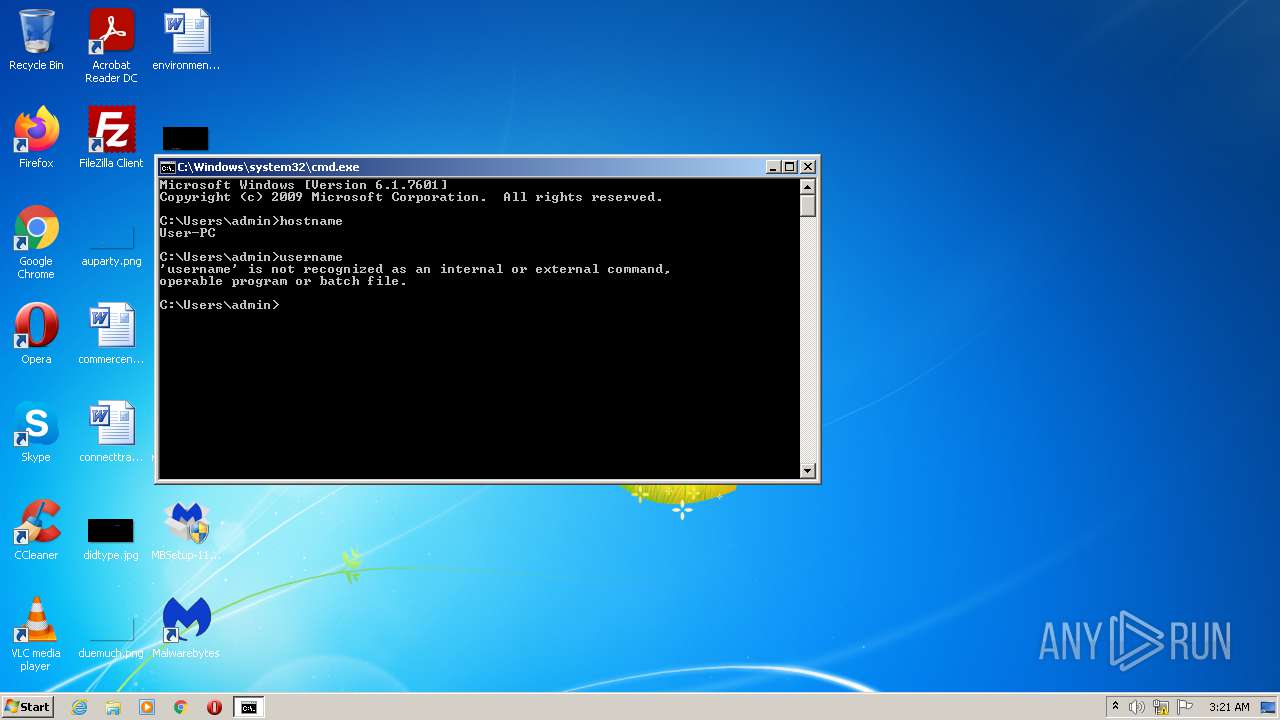
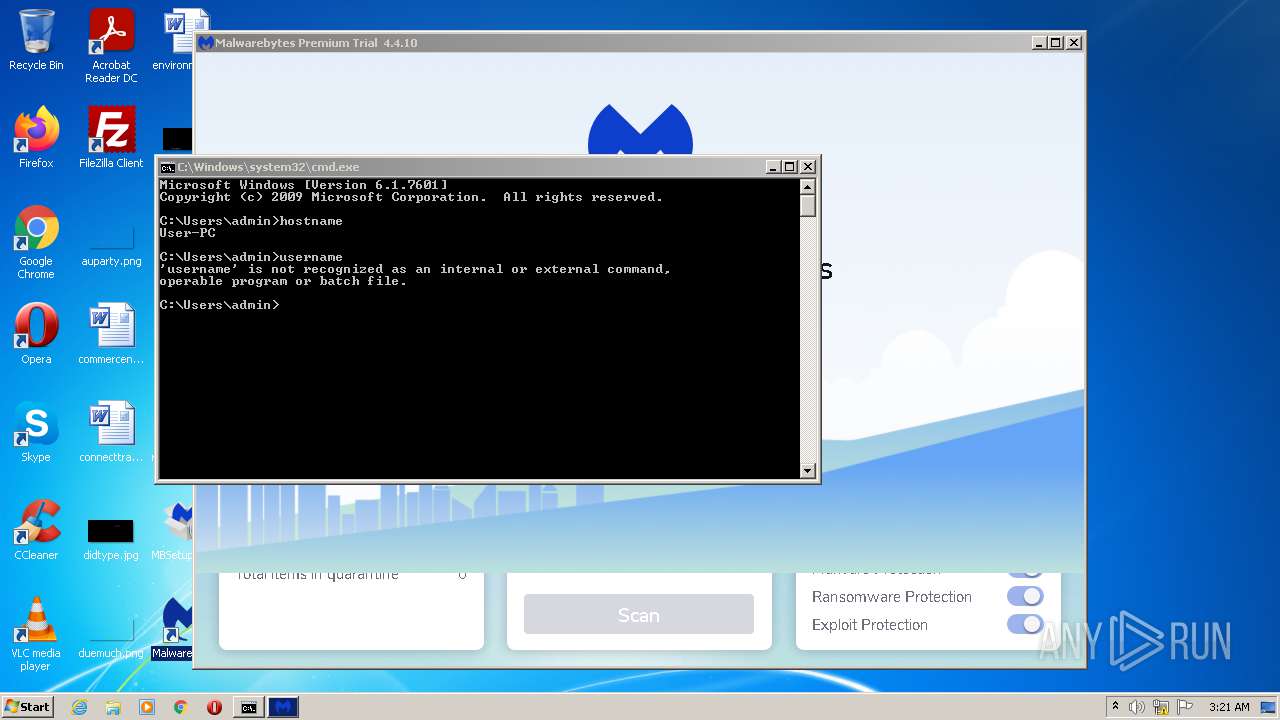
Reads the computer name
- MBSetup-119967.119967-consumer.exe (PID: 3888)
- MBAMInstallerService.exe (PID: 3108)
- MBAMService.exe (PID: 2164)
- MBAMService.exe (PID: 2720)
- mbamtray.exe (PID: 3556)
- mbam.exe (PID: 3648)
- mbam.exe (PID: 2932)
- cmd.exe (PID: 3656)
- MBAMWsc.exe (PID: 3876)
Creates files in the driver directory
- MBSetup-119967.119967-consumer.exe (PID: 3888)
- MBAMInstallerService.exe (PID: 3108)
- MBAMService.exe (PID: 2720)
Creates files in the Windows directory
- MBSetup-119967.119967-consumer.exe (PID: 3888)
- certutil.exe (PID: 3372)
- certutil.exe (PID: 2428)
- certutil.exe (PID: 2340)
- MBAMInstallerService.exe (PID: 3108)
- MBAMService.exe (PID: 2164)
- MBAMService.exe (PID: 2720)
Removes files from Windows directory
- MBSetup-119967.119967-consumer.exe (PID: 3888)
- certutil.exe (PID: 3372)
- certutil.exe (PID: 2340)
- certutil.exe (PID: 2428)
- MBAMService.exe (PID: 2720)
- MBAMInstallerService.exe (PID: 3108)
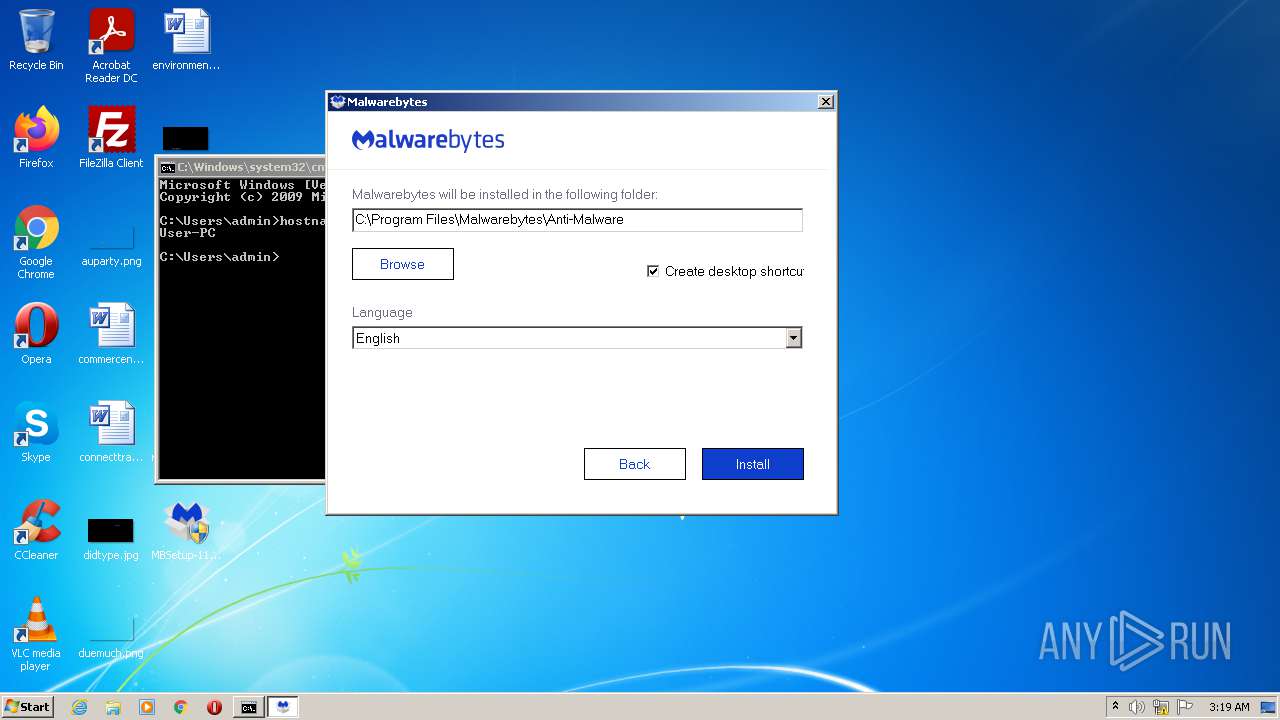
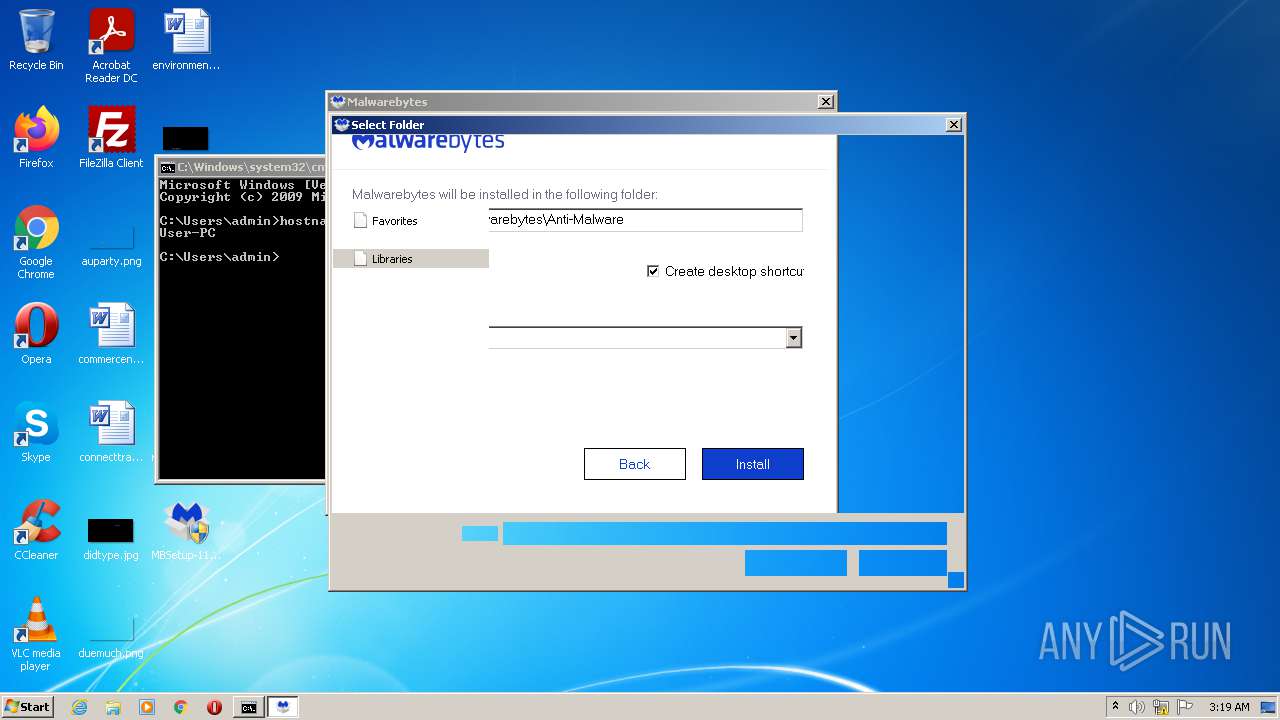
Creates files in the program directory
- MBSetup-119967.119967-consumer.exe (PID: 3888)
- MBAMInstallerService.exe (PID: 3108)
- MBAMService.exe (PID: 2720)
Drops a file that was compiled in debug mode
- MBSetup-119967.119967-consumer.exe (PID: 3888)
- MBAMInstallerService.exe (PID: 3108)
- MBAMService.exe (PID: 2720)
Drops a file with a compile date too recent
- MBSetup-119967.119967-consumer.exe (PID: 3888)
- MBAMInstallerService.exe (PID: 3108)
- MBAMService.exe (PID: 2720)
Executable content was dropped or overwritten
- MBSetup-119967.119967-consumer.exe (PID: 3888)
- MBAMInstallerService.exe (PID: 3108)
- MBAMService.exe (PID: 2720)
Executed as Windows Service
- MBAMInstallerService.exe (PID: 3108)
- MBAMService.exe (PID: 2720)
Reads default file associations for system extensions
- SearchProtocolHost.exe (PID: 1588)
Drops a file with too old compile date
- MBAMInstallerService.exe (PID: 3108)
Changes default file association
- MBAMInstallerService.exe (PID: 3108)
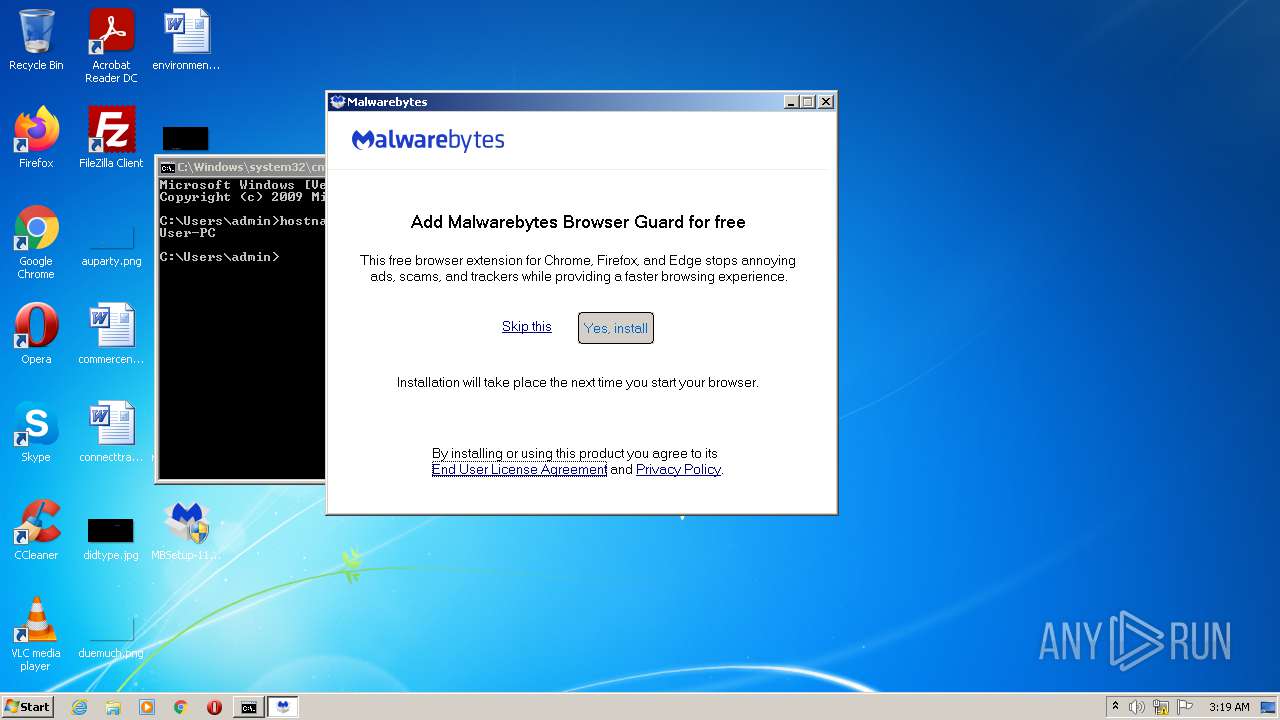
Changes IE settings (feature browser emulation)
- MBAMInstallerService.exe (PID: 3108)
- MBAMService.exe (PID: 2720)
Creates/Modifies COM task schedule object
- MBAMService.exe (PID: 2720)
Creates or modifies windows services
- MBAMService.exe (PID: 2720)
Reads CPU info
- MBAMService.exe (PID: 2720)
Reads the time zone
- MBAMService.exe (PID: 2720)
Creates a software uninstall entry
- MBAMInstallerService.exe (PID: 3108)
Reads Environment values
- MBAMService.exe (PID: 2720)
Reads the date of Windows installation
- mbam.exe (PID: 3648)
Creates files in the user directory
- mbam.exe (PID: 3648)
INFO
Reads the computer name
- HOSTNAME.EXE (PID: 3172)
- SearchProtocolHost.exe (PID: 1588)
- certutil.exe (PID: 3372)
- certutil.exe (PID: 2428)
- certutil.exe (PID: 2340)
Manual execution by user
- cmd.exe (PID: 3656)
- mbam.exe (PID: 2932)
Checks supported languages
- HOSTNAME.EXE (PID: 3172)
- SearchProtocolHost.exe (PID: 1588)
- certutil.exe (PID: 3372)
- certutil.exe (PID: 2428)
- certutil.exe (PID: 2340)
Reads settings of System Certificates
- MBSetup-119967.119967-consumer.exe (PID: 3888)
- MBAMInstallerService.exe (PID: 3108)
- certutil.exe (PID: 3372)
- certutil.exe (PID: 2428)
- certutil.exe (PID: 2340)
- MBAMService.exe (PID: 2720)
- mbamtray.exe (PID: 3556)
- mbam.exe (PID: 3648)
Dropped object may contain Bitcoin addresses
- MBAMInstallerService.exe (PID: 3108)
- MBAMService.exe (PID: 2720)
Checks Windows Trust Settings
- MBAMService.exe (PID: 2720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:10:11 19:56:20+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.15 |
| CodeSize: | 556544 |
| InitializedDataSize: | 1547264 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x46ceb |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.4.8.238 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Malwarebytes |
| FileDescription: | Malwarebytes Setup |
| FileVersion: | 4.4.8.238 |
| LegalCopyright: | Copyright (C) 2017 - 2020 Malwarebytes, Inc. All rights reserved. |
| InternalName: | MBSetup.exe |
| OriginalFileName: | MBSetup.exe |
| ProductName: | Malwarebytes |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Oct-2021 17:56:20 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Malwarebytes |
| FileDescription: | Malwarebytes Setup |
| FileVersion: | 4.4.8.238 |
| LegalCopyright: | Copyright (C) 2017 - 2020 Malwarebytes, Inc. All rights reserved. |
| InternalName: | MBSetup.exe |
| OriginalFilename: | MBSetup.exe |
| ProductName: | Malwarebytes |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Oct-2021 17:56:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00087C37 | 0x00087E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59952 |
.rdata | 0x00089000 | 0x00021390 | 0x00021400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14576 |
.data | 0x000AB000 | 0x00005240 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.38273 |
.rsrc | 0x000B1000 | 0x0014B630 | 0x0014B800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.66999 |
.reloc | 0x001FD000 | 0x00007A40 | 0x00007C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.671 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.16648 | 1842 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.77507 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 4.01467 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 4.15499 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.31512 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 4.69584 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 4.9625 | 266 | UNKNOWN | UNKNOWN | RT_STRING |
8 | 3.52137 | 110 | UNKNOWN | UNKNOWN | RT_STRING |
9 | 2.1346 | 2216 | UNKNOWN | English - United States | RT_ICON |
10 | 5.354 | 618 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
WINHTTP.dll |
ole32.dll |
Total processes
58
Monitored processes
15
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1588 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
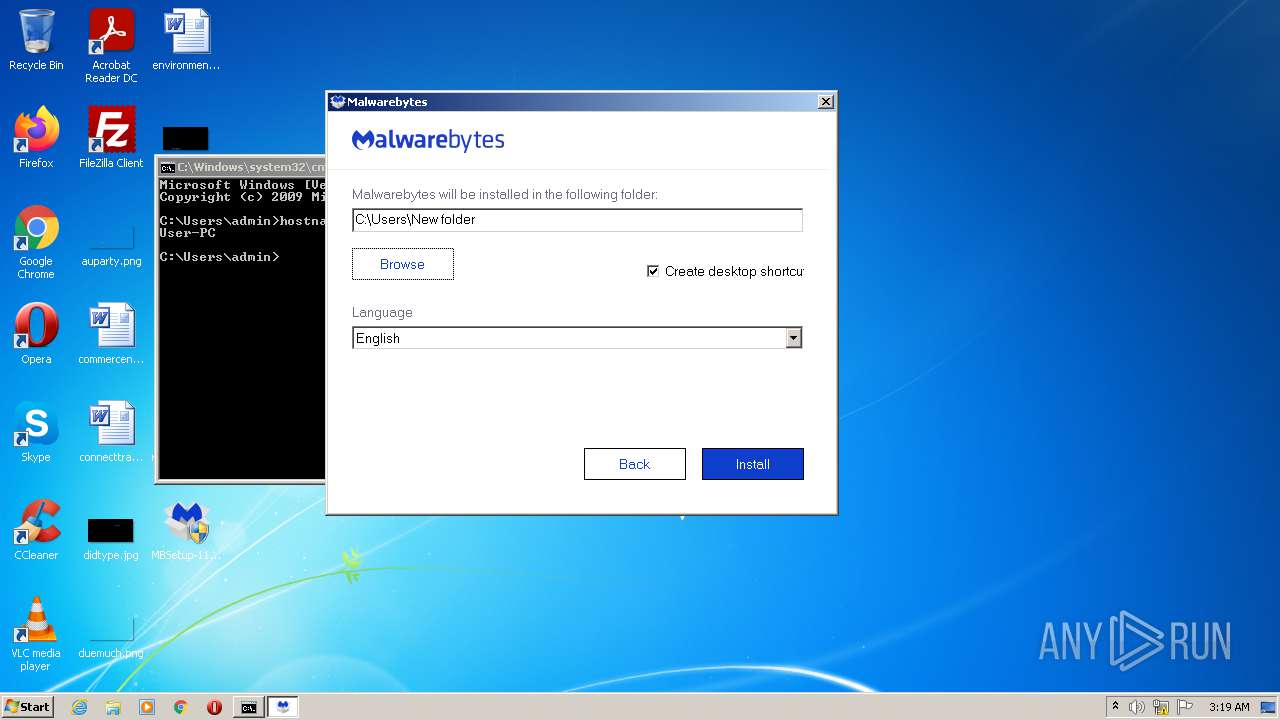
| 2164 | "C:\Users\New folder\MBAMService.exe" /Service | C:\Users\New folder\MBAMService.exe | — | MBAMInstallerService.exe | |||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Description: Malwarebytes Service Exit code: 0 Version: 3.2.0.1005 Modules
| |||||||||||||||
| 2340 | certutil.exe -f -addstore root "C:\Windows\TEMP\MBInstallTemp\servicepkg\starfieldrootcag2_new.crt" | C:\Windows\system32\certutil.exe | — | MBAMInstallerService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: CertUtil.exe Exit code: 0 Version: 6.1.7601.18151 (win7sp1_gdr.130512-1533) Modules
| |||||||||||||||
| 2428 | certutil.exe -f -addstore root "C:\Windows\TEMP\MBInstallTemp\servicepkg\DigiCertEVRoot.crt" | C:\Windows\system32\certutil.exe | — | MBAMInstallerService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: CertUtil.exe Exit code: 0 Version: 6.1.7601.18151 (win7sp1_gdr.130512-1533) Modules
| |||||||||||||||
| 2720 | "C:\Users\New folder\MBAMService.exe" | C:\Users\New folder\MBAMService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Description: Malwarebytes Service Exit code: 0 Version: 3.2.0.1005 Modules
| |||||||||||||||
| 2916 | "C:\Users\admin\Desktop\MBSetup-119967.119967-consumer.exe" | C:\Users\admin\Desktop\MBSetup-119967.119967-consumer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Malwarebytes Integrity Level: MEDIUM Description: Malwarebytes Setup Exit code: 3221226540 Version: 4.4.8.238 Modules
| |||||||||||||||
| 2932 | "C:\Users\New folder\mbam.exe" | C:\Users\New folder\mbam.exe | Explorer.EXE | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: MEDIUM Description: Malwarebytes Exit code: 4294967295 Version: 4.0.0.1162 Modules
| |||||||||||||||
| 3108 | "C:\Users\admin\AppData\Local\Temp\MBAMInstallerService.exe" | C:\Users\admin\AppData\Local\Temp\MBAMInstallerService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Description: Malwarebytes Installer Service Exit code: 0 Version: 4.0.0.424 Modules
| |||||||||||||||
| 3172 | hostname | C:\Windows\system32\HOSTNAME.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Hostname APP Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3372 | certutil.exe -f -addstore root "C:\Windows\TEMP\MBInstallTemp\servicepkg\BaltimoreCyberTrustRoot.crt" | C:\Windows\system32\certutil.exe | — | MBAMInstallerService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: CertUtil.exe Exit code: 0 Version: 6.1.7601.18151 (win7sp1_gdr.130512-1533) Modules
| |||||||||||||||
Total events
64 753
Read events
62 761
Write events
1 981
Delete events
11
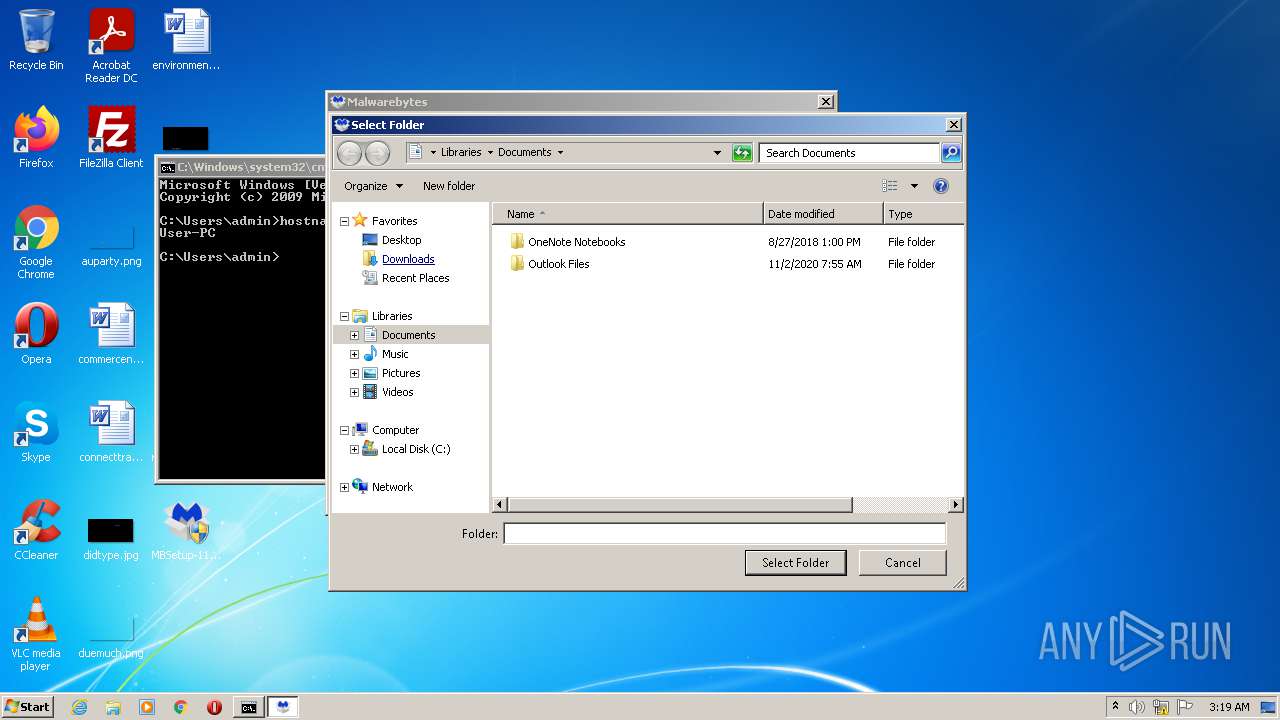
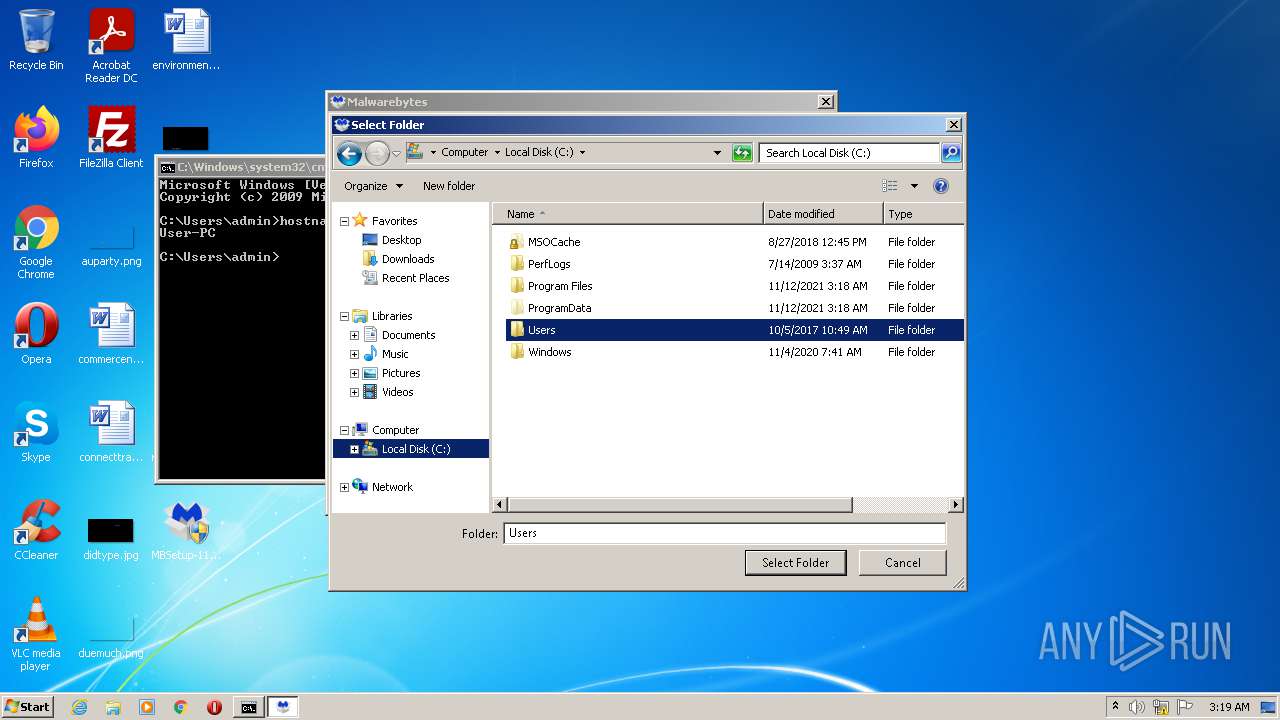
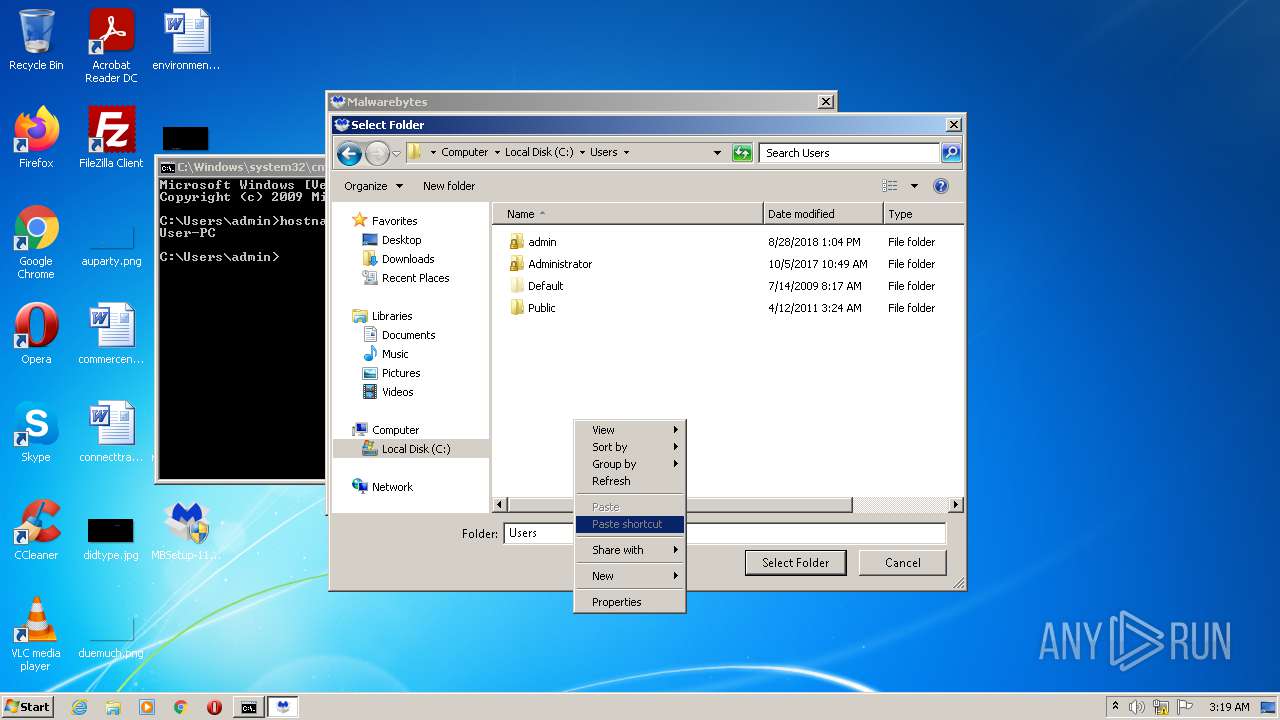
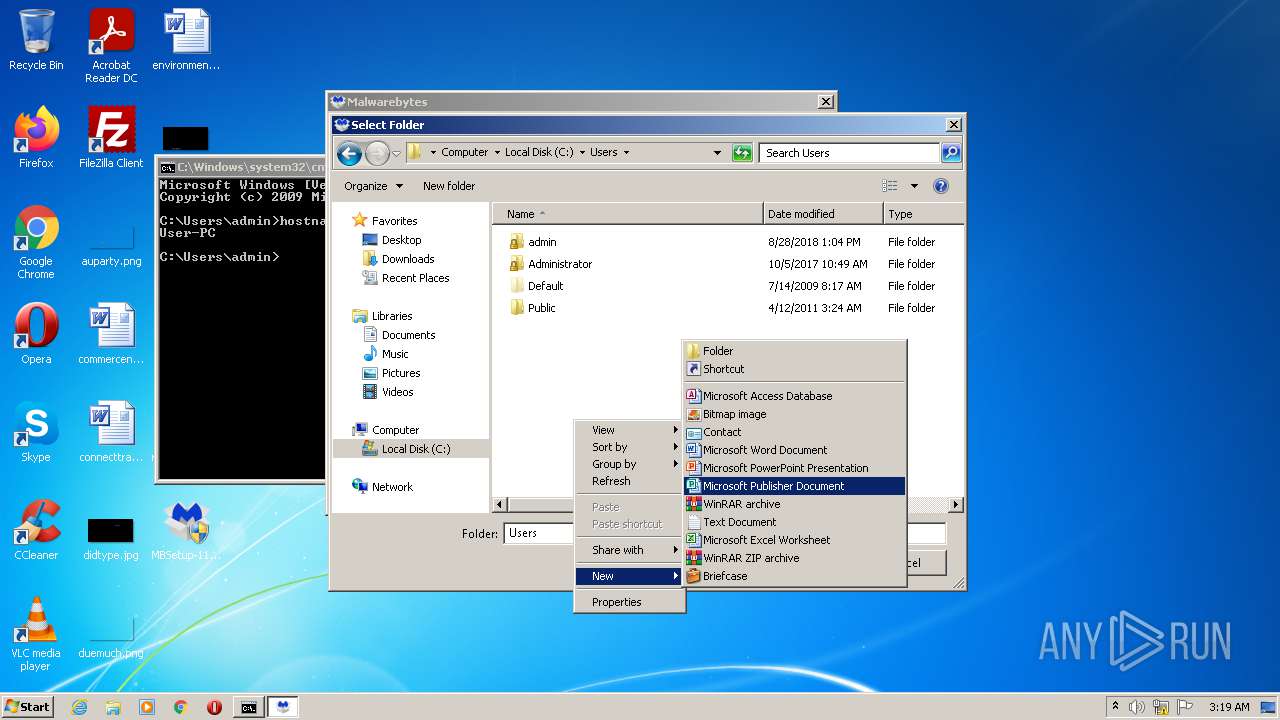
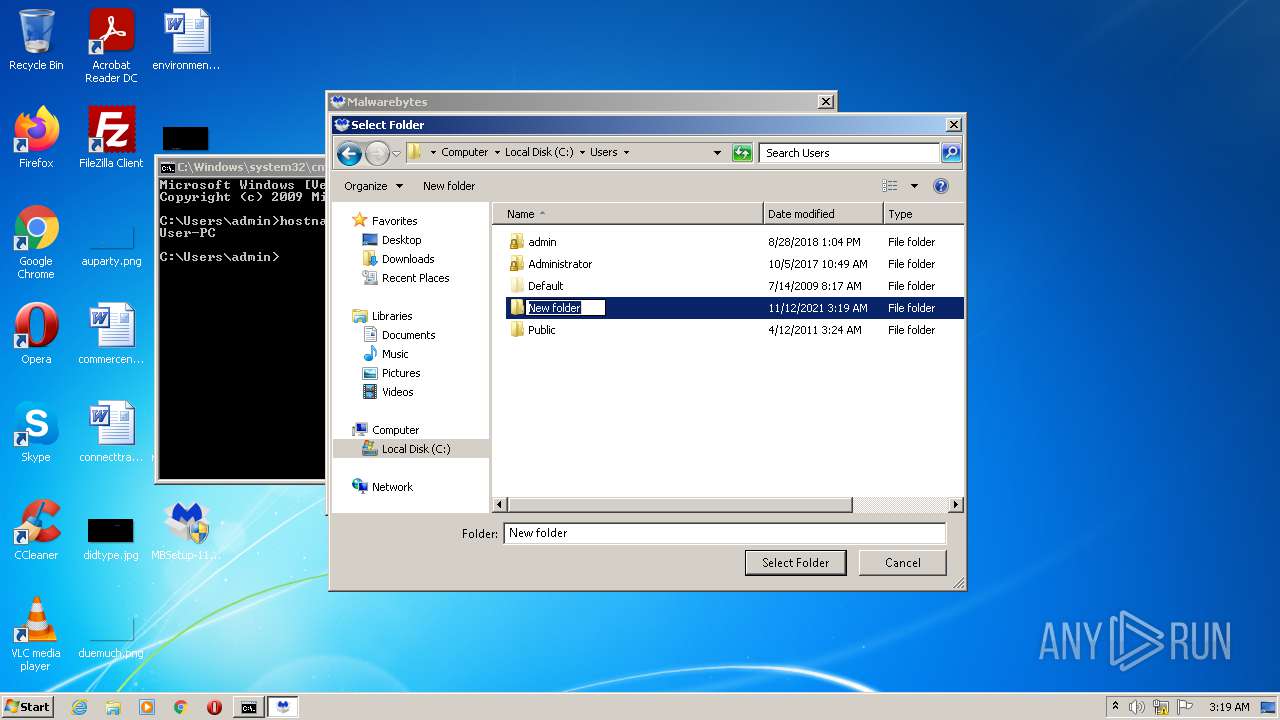
Modification events
| (PID) Process: | (3888) MBSetup-119967.119967-consumer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\mbamtestkey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3888) MBSetup-119967.119967-consumer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3888) MBSetup-119967.119967-consumer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 020000000D000000010000000C000000000000000B00000007000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3888) MBSetup-119967.119967-consumer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (3888) MBSetup-119967.119967-consumer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (3888) MBSetup-119967.119967-consumer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (3888) MBSetup-119967.119967-consumer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3888) MBSetup-119967.119967-consumer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 01000000020000000D0000000C000000000000000B00000007000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3888) MBSetup-119967.119967-consumer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (3888) MBSetup-119967.119967-consumer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
Executable files
308
Suspicious files
342
Text files
1 092
Unknown types
80
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3108 | MBAMInstallerService.exe | C:\Windows\TEMP\MBInstallTemp\ctlrpkg.7z | — | |
MD5:— | SHA256:— | |||
| 3108 | MBAMInstallerService.exe | C:\Windows\TEMP\MBInstallTemp\dbclspkg.7z | — | |
MD5:— | SHA256:— | |||
| 3888 | MBSetup-119967.119967-consumer.exe | C:\Users\admin\AppData\Local\Temp\MBAMInstallerService.exe | executable | |
MD5:— | SHA256:— | |||
| 3108 | MBAMInstallerService.exe | C:\Windows\TEMP\MBInstallTemp\servicepkg.7z | compressed | |
MD5:— | SHA256:— | |||
| 3108 | MBAMInstallerService.exe | C:\Windows\TEMP\MBInstallTemp\servicepkg\srvversion.dat | text | |
MD5:— | SHA256:— | |||
| 3108 | MBAMInstallerService.exe | C:\Windows\TEMP\MBInstallTemp\servicepkg\arwversion.dat | text | |
MD5:— | SHA256:— | |||
| 3108 | MBAMInstallerService.exe | C:\Windows\TEMP\MBInstallTemp\servicepkg\MBAMService.exe | executable | |
MD5:— | SHA256:— | |||
| 3108 | MBAMInstallerService.exe | C:\Windows\TEMP\MBInstallTemp\servicepkg\mbamelam.cat | cat | |
MD5:21BF7F4E5D78A55366DA26A3BE154DE7 | SHA256:2D975971ACA5606C6438D148B3A1FB9FB07509910E7DA4496206B58BC5921194 | |||
| 3888 | MBSetup-119967.119967-consumer.exe | C:\Windows\system32\drivers\mbamtestfile.dat | text | |
MD5:9F06243ABCB89C70E0C331C61D871FA7 | SHA256:837CCB607E312B170FAC7383D7CCFD61FA5072793F19A25E75FBACB56539B86B | |||
| 3108 | MBAMInstallerService.exe | C:\Windows\TEMP\MBInstallTemp\servicepkg\starfieldrootcag2_new.crt | der | |
MD5:D63981C6527E9669FCFCCA66ED05F296 | SHA256:2CE1CB0BF9D2F9E102993FBE215152C3B2DD0CABDE1C68E5319B839154DBB7F5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
19
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2720 | MBAMService.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA%2BoSQYV1wCgviF2%2FcXsbb0%3D | US | der | 471 b | whitelisted |
2720 | MBAMService.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAPxtOFfOoLxFJZ4s9fYR1w%3D | US | der | 471 b | whitelisted |
2720 | MBAMService.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAqhJdbWMht%2BQeQF2jaXwhU%3D | US | der | 471 b | whitelisted |
2720 | MBAMService.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSPwl%2BrBFlJbvzLXU1bGW08VysJ2wQUj%2Bh%2B8G0yagAFI8dwl2o6kP9r6tQCEA02qwgFupRQIg%2BGXFiRj1I%3D | US | der | 471 b | whitelisted |
2720 | MBAMService.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT5hgD4pKvs0jFFLEKNQ1CjblLIPQQU9LbhIB3%2BKa7S5GGlsqIlssgXNW4CEA1CSuC%2BOoj%2FYEAhzhQA8N0%3D | US | der | 471 b | whitelisted |
2720 | MBAMService.exe | GET | 200 | 67.26.81.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?dc612d653d8e4401 | US | compressed | 59.9 Kb | whitelisted |
2720 | MBAMService.exe | GET | 200 | 67.26.81.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5f06403719c772cf | US | compressed | 4.70 Kb | whitelisted |
2720 | MBAMService.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSYagvY3tfizDNoybzVSPFZmSEm0wQUe2jOKarAF75JeuHlP9an90WPNTICEAii7E54oJ4XSxkuVTWYS1k%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | MBSetup-119967.119967-consumer.exe | 52.45.78.72:443 | ark.mwbsys.com | Amazon.com, Inc. | US | suspicious |
3888 | MBSetup-119967.119967-consumer.exe | 13.32.99.49:443 | cdn.mwbsys.com | Amazon.com, Inc. | US | suspicious |
3108 | MBAMInstallerService.exe | 52.45.78.72:443 | ark.mwbsys.com | Amazon.com, Inc. | US | suspicious |
3108 | MBAMInstallerService.exe | 13.32.99.49:443 | cdn.mwbsys.com | Amazon.com, Inc. | US | suspicious |
2720 | MBAMService.exe | 18.209.74.159:443 | iris.mwbsys.com | — | US | unknown |
2720 | MBAMService.exe | 35.160.229.212:443 | telemetry.malwarebytes.com | Amazon.com, Inc. | US | unknown |
2720 | MBAMService.exe | 54.85.205.166:443 | keystone.mwbsys.com | Amazon.com, Inc. | US | unknown |
2720 | MBAMService.exe | 52.10.136.50:443 | telemetry.malwarebytes.com | Amazon.com, Inc. | US | unknown |
2720 | MBAMService.exe | 52.21.116.56:443 | sirius.mwbsys.com | Amazon.com, Inc. | US | unknown |
2720 | MBAMService.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ark.mwbsys.com |
| suspicious |
cdn.mwbsys.com |
| whitelisted |
iris.mwbsys.com |
| unknown |
telemetry.malwarebytes.com |
| whitelisted |
keystone.mwbsys.com |
| unknown |
sirius.mwbsys.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
mbamtray.exe | QAxBase::setControl: requested control {F36AD0D0-B5F0-4C69-AF08-603D177FEF0E} could not be instantiated
|
mbamtray.exe | void __thiscall _MBScanControllerSlots::OnControllerException(int,const class QString &,const class QString &,const class QString &) Controller error, code: -2147467259 source: "" description: "" help: ""
|
mbam.exe | QSingleInstanceApplication and QQmlApplicationEngine created: 0 ms
|
mbam.exe | QAxBase::setControl: requested control {F36AD0D0-B5F0-4C69-AF08-603D177FEF0E} could not be instantiated
|
mbam.exe | void __thiscall _MBScanControllerSlots::OnControllerException(int,const class QString &,const class QString &,const class QString &) Controller error, code: -2147467259 source: "" description: "" help: ""
|
mbam.exe | Connected to primary instance...
|
mbam.exe | Another instance of Mbam is already running.
|