| URL: | http://web.archive.org/web/20180620152813/http://archiecentral.coffeecup.com/Google.html |
| Full analysis: | https://app.any.run/tasks/fdeb688b-a92b-474f-98e7-0a14664eaf21 |
| Verdict: | No threats detected |
| Analysis date: | April 27, 2020, 11:23:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 91E3DC58C22000C1A944861158F4AB12 |
| SHA1: | 6C27421D27E70E91D66B4F3797BDCE2DB8ECE6C4 |
| SHA256: | 71736B6A5BC2AB85AE914C0D7B3F4190A454EAE6CA5C5B785F43D312C95823F1 |
| SSDEEP: | 3:N1KJAQXxXJeuDXVJXsDzqWfbCbdGESRbwJ:COQhX8uDFZsDzIGESlwJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 660)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3168)
Reads Internet Cache Settings
- iexplore.exe (PID: 3168)
- iexplore.exe (PID: 3480)
Reads settings of System Certificates
- iexplore.exe (PID: 3480)
Reads internet explorer settings
- iexplore.exe (PID: 3480)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3168 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://web.archive.org/web/20180620152813/http://archiecentral.coffeecup.com/Google.html" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3480 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3168 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
530
Read events
474
Write events
56
Delete events
0
Modification events
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1867295038 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30809222 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
4
Text files
26
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 660 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 660 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\playback.bundle[1].js | text | |
MD5:E1E4B1C1744D03667EC2363D78DB6049 | SHA256:DCD138F73C3411791096D07118A5074BFE6A4E6BBC794C7C3CA380C28932AB0C | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabEFF6.tmp | — | |
MD5:— | SHA256:— | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarEFF7.tmp | — | |
MD5:— | SHA256:— | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:6432630646D7BA087677C8D72FECF836 | SHA256:114A9BCD1EEB00A5641998CC6FF4F912D00AD2867829F05344EE35149B7B79A6 | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\ait-client-rewrite[1].js | text | |
MD5:47EE8D10E1C07CC5298764676D174D9A | SHA256:06B95A192858FDD37BEEFF40C0032FF1327C67922BA19CBC22427ACDAA37AD0D | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\analytics[1].js | text | |
MD5:408039DA8111BBD670BA53E5DF9F2231 | SHA256:6996C520E991E08E97F0C8CABE42ADC9A81D98AB43EA823F094C05A9FC70BCAC | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\banner-styles[1].css | text | |
MD5:887A901DE10F7A6BF14717EACFDDF000 | SHA256:11FB63F2AFC4AF3BDDCA7AD06BDE4C0AD80CCC557FF5EB5CA6F5CC2CB63DF9CF | |||
| 3480 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\wbhack[1].js | text | |
MD5:DD77DADCCB8BC218F635BBDAB7949BBD | SHA256:AF2ACF0FDEE1A96BC2B061E7992ABEDDBAA2E9B25E63D3C0A88D35863A6EA0A0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
21
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3480 | iexplore.exe | GET | 200 | 207.241.233.214:80 | http://web.archive.org/_static/images/web-screenshot.svg | US | image | 740 b | whitelisted |
3480 | iexplore.exe | GET | 200 | 207.241.225.95:80 | http://analytics.archive.org/0.gif?service=wb&server_name=wwwb-app57.us.archive.org&server_ms=1158&kind=pageview&timediff=1&locale=en-US&referrer=-&loadtime=1543&nav_to_done_ms=1543&ga_cd1=25.6px&ga_cd2=1&version=2&count=13 | US | image | 35 b | whitelisted |
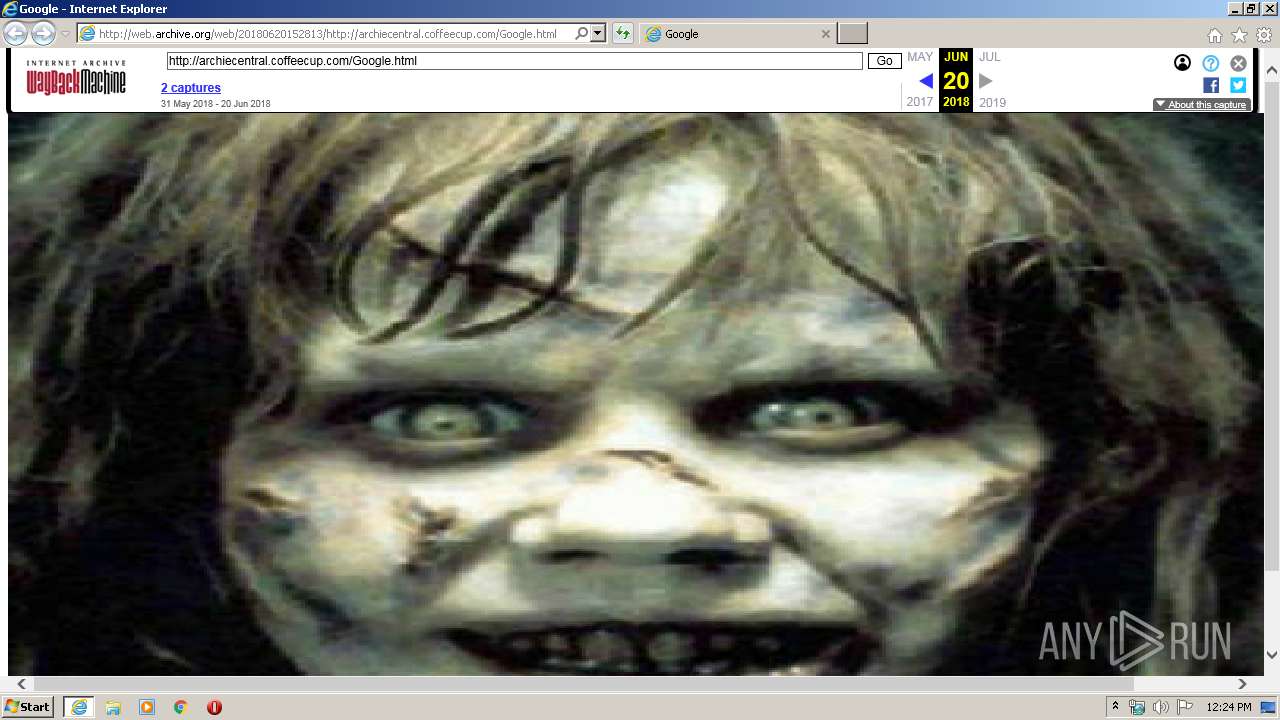
3480 | iexplore.exe | GET | 200 | 207.241.233.214:80 | http://web.archive.org/web/20180620153326oe_/http://archiecentral.coffeecup.com/Google.swf | US | swf | 383 Kb | whitelisted |
3480 | iexplore.exe | GET | 200 | 207.241.233.214:80 | http://web.archive.org/web/20180620152813/http://archiecentral.coffeecup.com/Google.html | US | html | 4.54 Kb | whitelisted |
3480 | iexplore.exe | GET | 200 | 207.241.233.214:80 | http://web.archive.org/_static/js/playback.bundle.js | US | text | 7.78 Kb | whitelisted |
3480 | iexplore.exe | GET | 200 | 207.241.233.214:80 | http://web.archive.org/_static/js/ait-client-rewrite.js | US | text | 5.99 Kb | whitelisted |
3480 | iexplore.exe | GET | 200 | 207.241.233.214:80 | http://web.archive.org/_static/js/wbhack.js | US | text | 734 b | whitelisted |
3480 | iexplore.exe | GET | 200 | 207.241.233.214:80 | http://web.archive.org/_static/css/banner-styles.css | US | text | 2.48 Kb | whitelisted |
3480 | iexplore.exe | GET | 200 | 207.241.233.214:80 | http://web.archive.org/_static/images/toolbar/wayback-toolbar-logo.png | US | image | 7.39 Kb | whitelisted |
3480 | iexplore.exe | GET | 200 | 207.241.224.2:80 | http://archive.org/includes/analytics.js?v=cf34f82 | US | text | 4.45 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3480 | iexplore.exe | 207.241.233.214:80 | web.archive.org | Internet Archive | US | suspicious |
3480 | iexplore.exe | 207.241.224.2:80 | archive.org | Internet Archive | US | malicious |
3480 | iexplore.exe | 207.241.224.2:443 | archive.org | Internet Archive | US | malicious |
3480 | iexplore.exe | 192.124.249.22:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
3480 | iexplore.exe | 207.241.225.95:80 | analytics.archive.org | Internet Archive | US | unknown |
3168 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3168 | iexplore.exe | 207.241.233.214:80 | web.archive.org | Internet Archive | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
web.archive.org |
| whitelisted |
archive.org |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
analytics.archive.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3480 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |