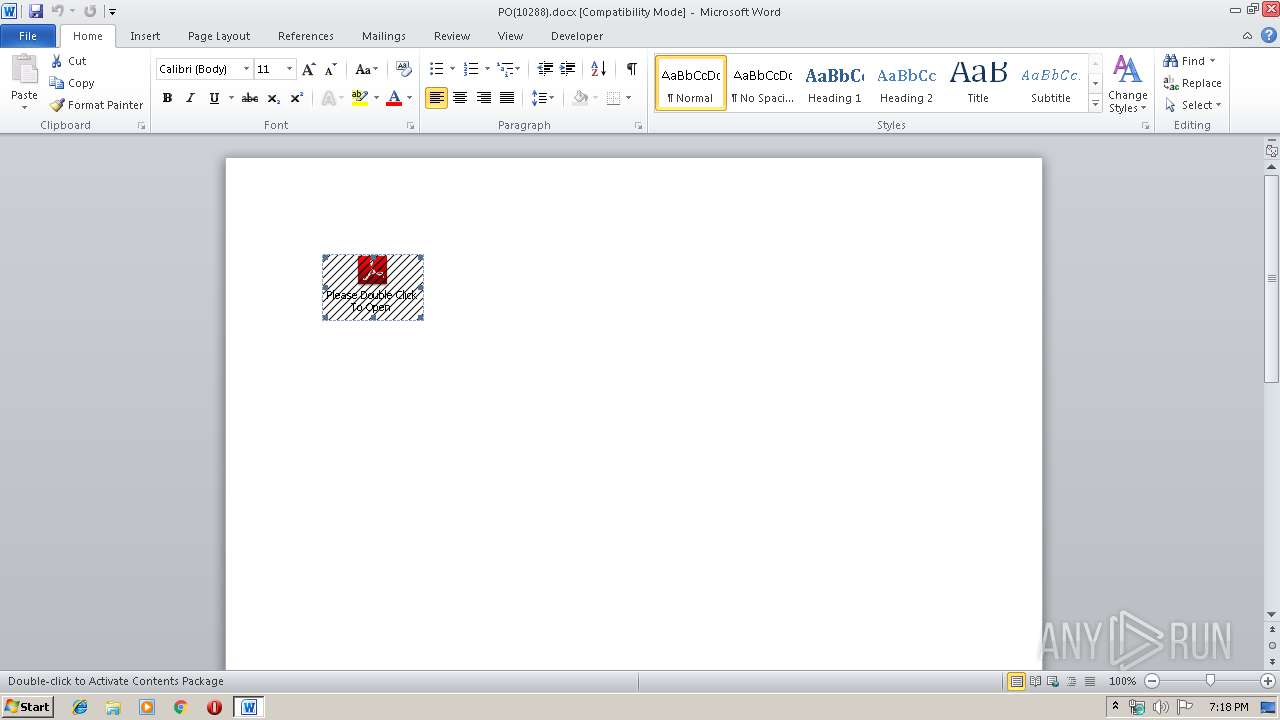
| File name: | PO(10288).docx |
| Full analysis: | https://app.any.run/tasks/0b8b1798-b593-473b-ab66-5a9c6aee78d0 |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2019, 18:17:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 6CD6E209E21AFC068B736CF5E11B2BDD |
| SHA1: | 1C578F46F755521BC2056C68FE053A6463C79F03 |
| SHA256: | 716E08C35F609630319502A5877B72474B1FBCDD0D8A7D53A2CD89BA0E2E0239 |
| SSDEEP: | 6144:RHUTtIuThnAoO/5iuzSYYo11/NkvUe+hjid0ITbtOU5YE7N9T+/fe0/yfCp0LiKt:5EnBPcSYv/NWUbOI8Yoy+0/eCp0LOel |
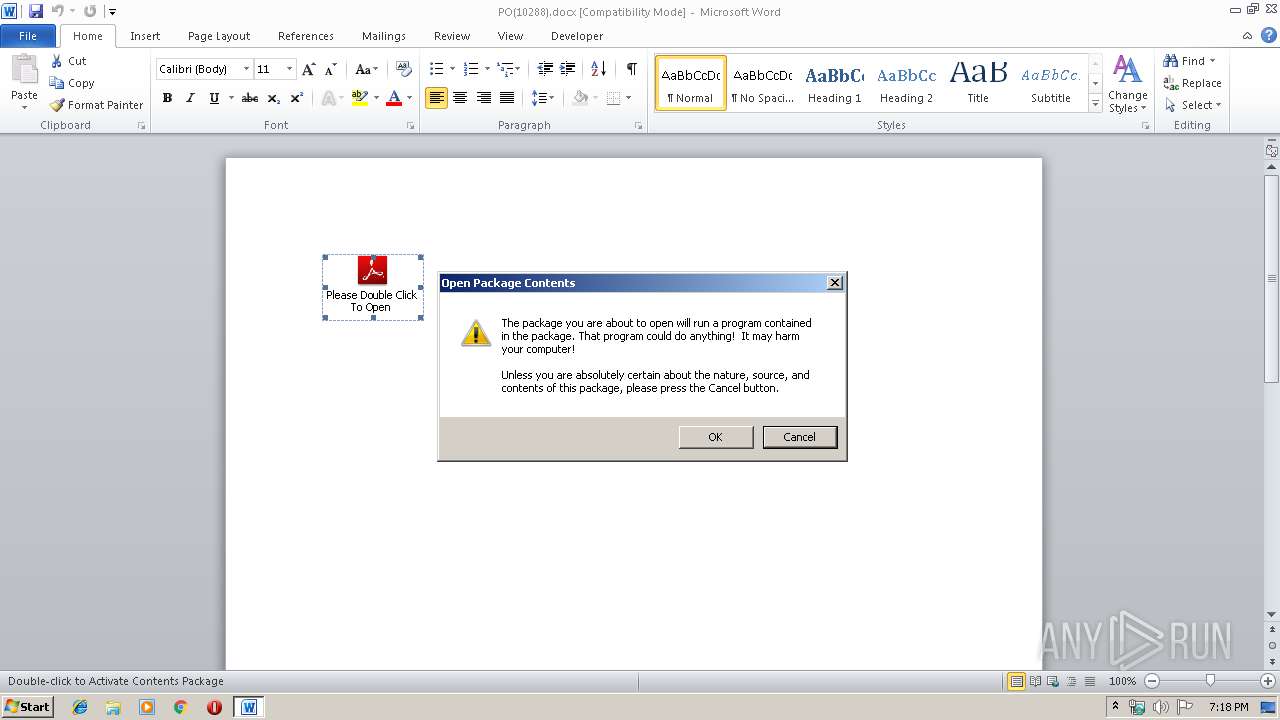
MALICIOUS
Loads the Task Scheduler COM API
- OSPPSVC.EXE (PID: 2736)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2884)
Application was dropped or rewritten from another process
- Order.exe (PID: 2848)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2884)
Loads dropped or rewritten executable
- Order.exe (PID: 2848)
- WINWORD.EXE (PID: 2884)
- DllHost.exe (PID: 2936)
- WINWORD.EXE (PID: 2588)
- OSPPSVC.EXE (PID: 2736)
- AUDIODG.EXE (PID: 2268)
- WINWORD.EXE (PID: 3764)
- DllHost.exe (PID: 3556)
- WINWORD.EXE (PID: 3032)
- SearchFilterHost.exe (PID: 1304)
- DllHost.exe (PID: 2648)
- WINWORD.EXE (PID: 2008)
- DllHost.exe (PID: 3944)
- WINWORD.EXE (PID: 3224)
SUSPICIOUS
Executable content was dropped or overwritten
- Order.exe (PID: 2848)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2884)
- WINWORD.EXE (PID: 3764)
- WINWORD.EXE (PID: 3032)
- WINWORD.EXE (PID: 3224)
- WINWORD.EXE (PID: 2008)
- WINWORD.EXE (PID: 2588)
Creates files in the user directory
- WINWORD.EXE (PID: 2884)
- WINWORD.EXE (PID: 3764)
- WINWORD.EXE (PID: 3032)
- WINWORD.EXE (PID: 3224)
- WINWORD.EXE (PID: 2588)
- WINWORD.EXE (PID: 2008)
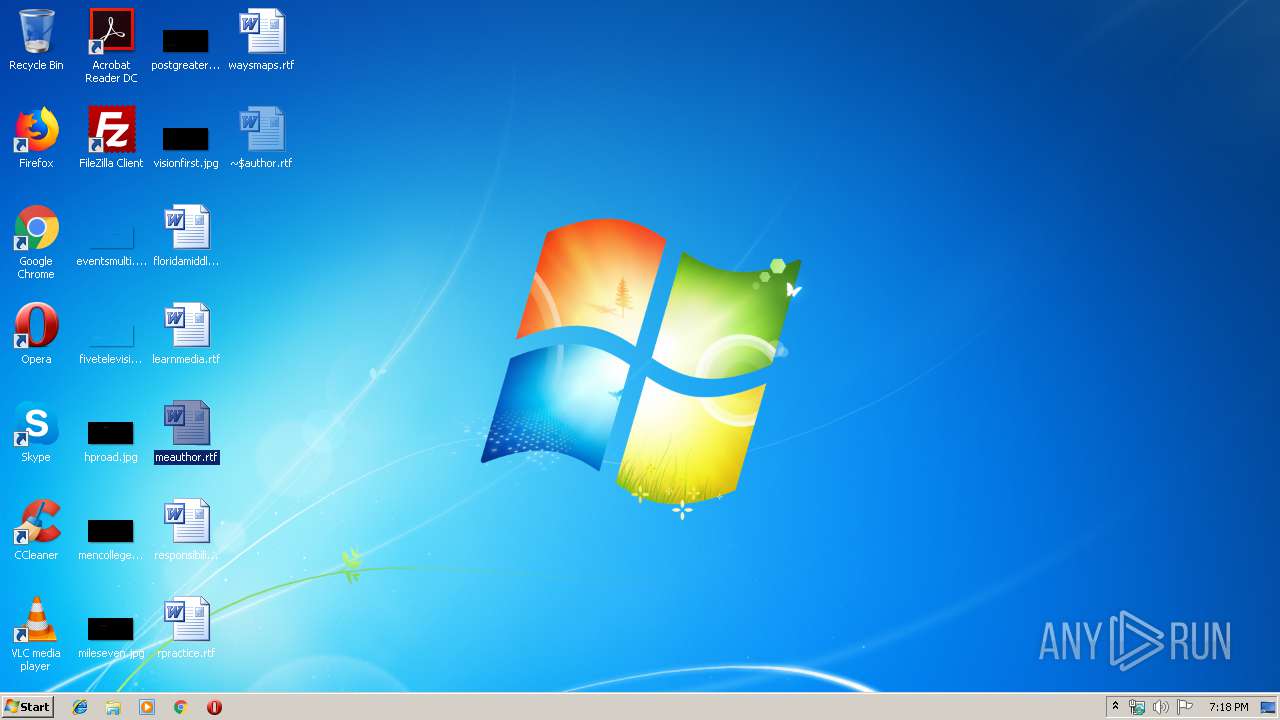
Manual execution by user
- WINWORD.EXE (PID: 2588)
- WINWORD.EXE (PID: 3764)
- WINWORD.EXE (PID: 3032)
- WINWORD.EXE (PID: 2008)
- WINWORD.EXE (PID: 3224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x7fcf3406 |
| ZipCompressedSize: | 386 |
| ZipUncompressedSize: | 1460 |
| ZipFileName: | [Content_Types].xml |
XMP
| Creator: | Windows User |
|---|
XML
| LastModifiedBy: | Windows User |
|---|---|
| RevisionNumber: | 2 |
| CreateDate: | 2019:09:18 00:26:00Z |
| ModifyDate: | 2019:09:18 00:29:00Z |
| Template: | Normal |
| TotalEditTime: | 3 minutes |
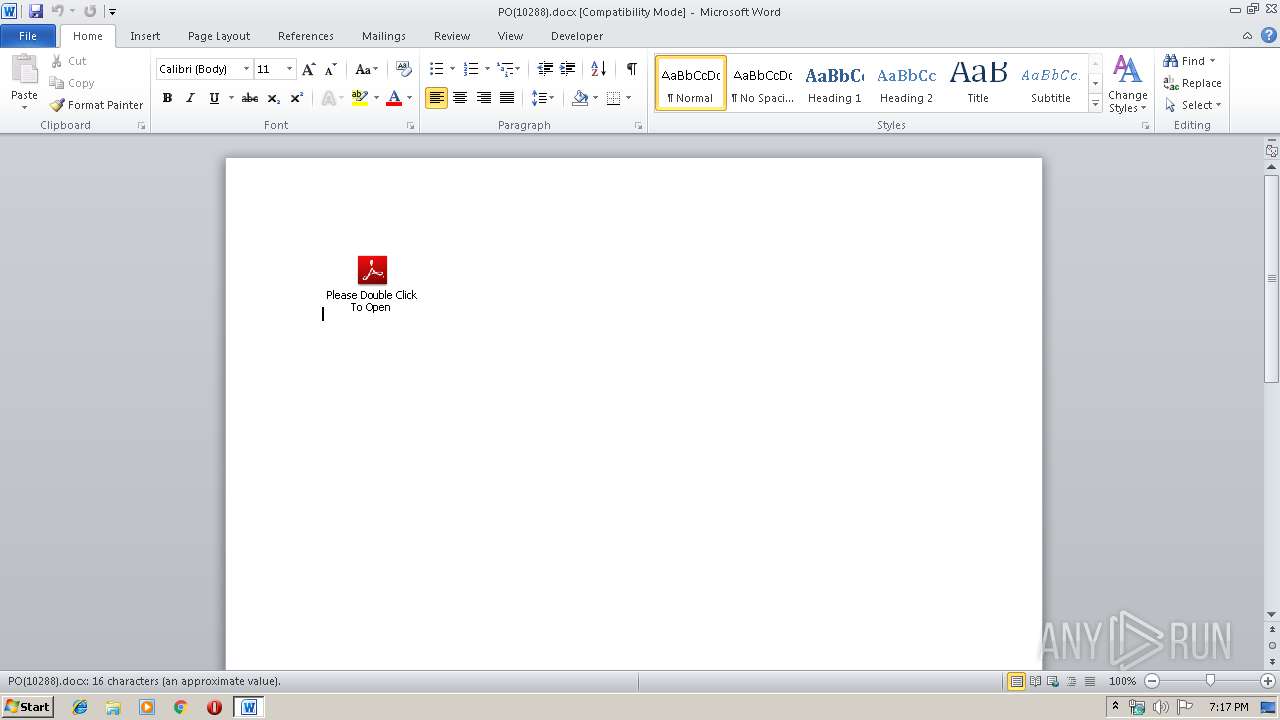
| Pages: | 1 |
| Words: | 3 |
| Characters: | 18 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 20 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 12 |
Total processes
45
Monitored processes
14
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1304 | "C:\Windows\system32\SearchFilterHost.exe" 0 512 516 524 65536 520 | C:\Windows\system32\SearchFilterHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Filter Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\waysmaps.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2268 | C:\Windows\system32\AUDIODG.EXE 0x6b0 | C:\Windows\system32\AUDIODG.EXE | — | svchost.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Audio Device Graph Isolation Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2588 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\waysmaps.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2648 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Common Files\Microsoft Shared\OfficeSoftwareProtectionPlatform\OSPPSVC.EXE" | C:\Program Files\Common Files\Microsoft Shared\OfficeSoftwareProtectionPlatform\OSPPSVC.EXE | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Office Software Protection Platform Service Exit code: 0 Version: 14.0.0370.400 (longhorn(wmbla).090811-1833) Modules
| |||||||||||||||
| 2848 | "C:\Users\admin\AppData\Local\Temp\Order.exe" | C:\Users\admin\AppData\Local\Temp\Order.exe | WINWORD.EXE | ||||||||||||
User: admin Company: AVAST Software Integrity Level: MEDIUM Description: Vxel Tcpip Generators Cryptography Amung Messengers Exit code: 0 Modules
| |||||||||||||||
| 2884 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\PO(10288).docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2936 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3032 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\floridamiddle.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
5 815
Read events
4 619
Write events
1 021
Delete events
175
Modification events
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | )f! |
Value: 29662100440B0000010000000000000000000000 | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1328676894 | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328677008 | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328677009 | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 440B00006EC09D5F4D6ED50100000000 | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | qg! |
Value: 71672100440B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | qg! |
Value: 71672100440B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
4
Text files
33
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9E29.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\Downloads\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\Downloads\~WRD0002.tmp | — | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{63A3F387-1B1B-4B99-8A2B-4EEB81D12786}.tmp | — | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{A2AFDE35-296B-4075-95E9-64EF58055CCE}.tmp | — | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{8D807339-7781-42B4-8FFD-F6A053D2395B}.tmp | — | |
MD5:— | SHA256:— | |||
| 3764 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3F7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3764 | WINWORD.EXE | C:\Users\admin\Desktop\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 3764 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0003.tmp | — | |
MD5:— | SHA256:— | |||
| 3764 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0002.docx | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report