| File name: | fugawi.4.5.14.1696-patch.exe |
| Full analysis: | https://app.any.run/tasks/0ecaeb0c-aec7-4267-9d3e-4c4626cdff44 |
| Verdict: | Malicious activity |
| Analysis date: | April 02, 2024, 12:07:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 2685A34E1989D822508456F723B50A1E |
| SHA1: | FA73CA4812AC35C74D2E990AC62057F3C1788FA6 |
| SHA256: | 716DA60D7BA11C853DE2C11287C85E388D35F64391207109B76DB0F7FDFE8DD0 |
| SSDEEP: | 6144:pSM/ec+mwPKbDGJngPJdtabTO4LGmeQW1o/x:pYc+9PgDcgxdtav7Nmi/ |
MALICIOUS
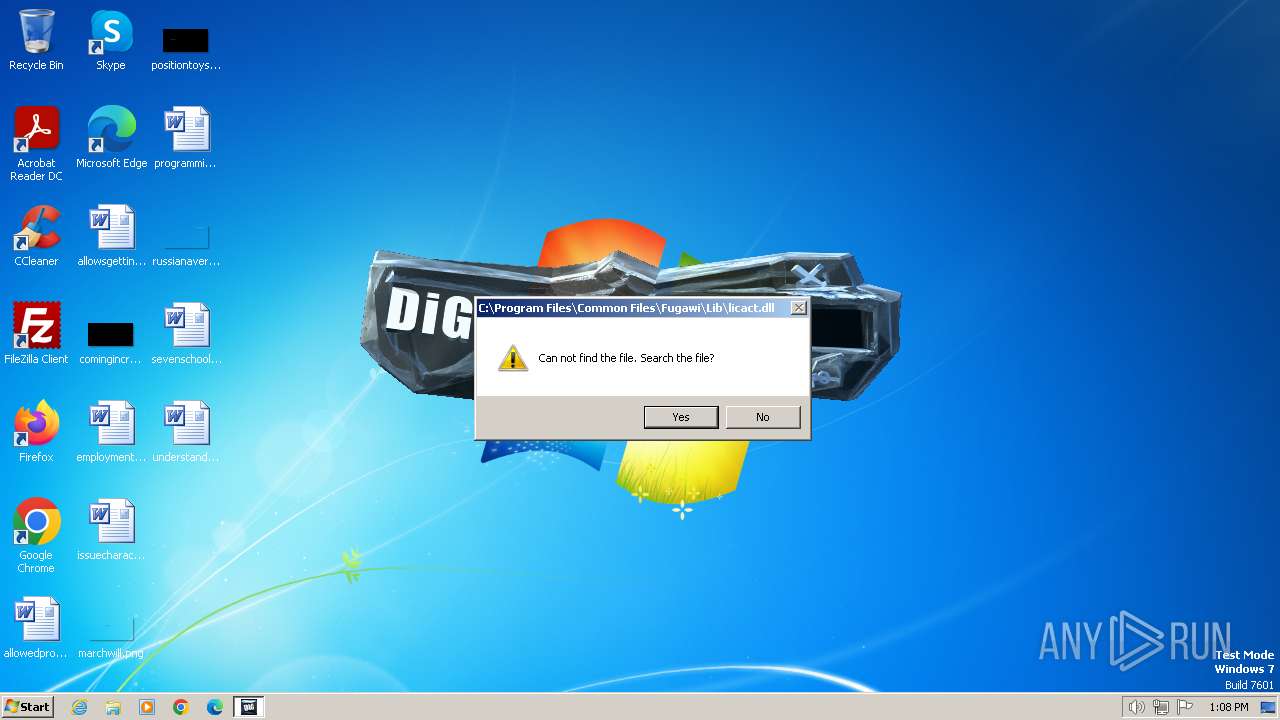
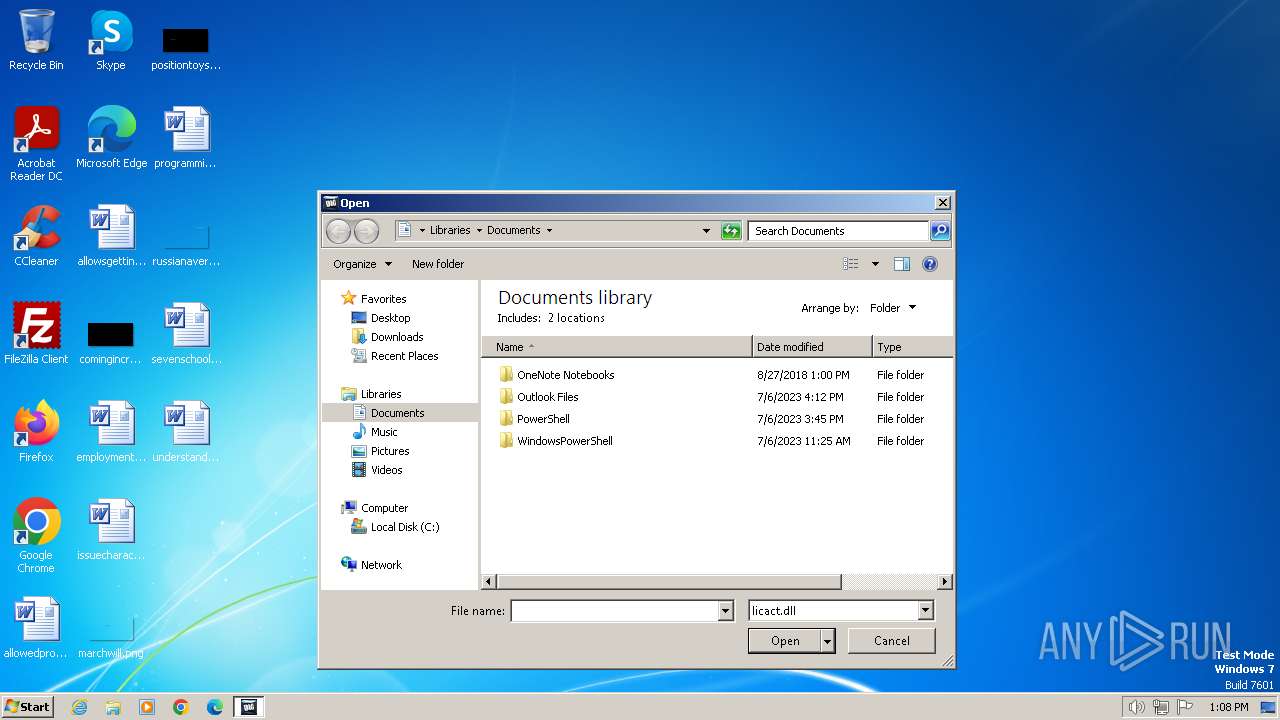
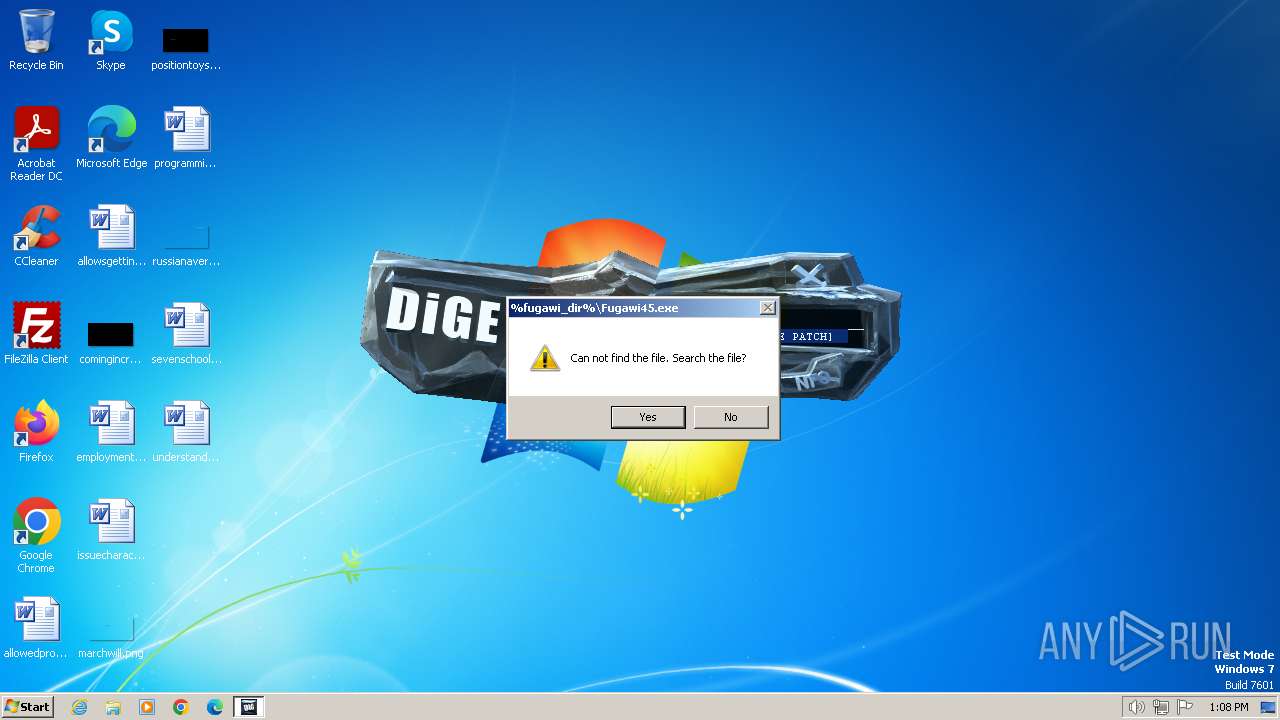
Drops the executable file immediately after the start
- fugawi.4.5.14.1696-patch.exe (PID: 2292)
Creates a writable file in the system directory
- fugawi.4.5.14.1696-patch.exe (PID: 2292)
SUSPICIOUS
Creates file in the systems drive root
- fugawi.4.5.14.1696-patch.exe (PID: 2292)
- regedit.exe (PID: 2596)
INFO
Checks supported languages
- fugawi.4.5.14.1696-patch.exe (PID: 2292)
Reads the computer name
- fugawi.4.5.14.1696-patch.exe (PID: 2292)
Reads the machine GUID from the registry
- fugawi.4.5.14.1696-patch.exe (PID: 2292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:08:20 15:16:23+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 5.12 |
| CodeSize: | 172032 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 294912 |
| EntryPoint: | 0x72370 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2120 | "C:\Users\admin\AppData\Local\Temp\fugawi.4.5.14.1696-patch.exe" | C:\Users\admin\AppData\Local\Temp\fugawi.4.5.14.1696-patch.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2292 | "C:\Users\admin\AppData\Local\Temp\fugawi.4.5.14.1696-patch.exe" | C:\Users\admin\AppData\Local\Temp\fugawi.4.5.14.1696-patch.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2596 | regedit.exe -s c:\regpatch.reg | C:\Windows\regedit.exe | — | fugawi.4.5.14.1696-patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
11 096
Read events
7 764
Write events
3 331
Delete events
1
Modification events
| (PID) Process: | (2292) fugawi.4.5.14.1696-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2292) fugawi.4.5.14.1696-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000070000000100000006000000000000000B0000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2292) fugawi.4.5.14.1696-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (2292) fugawi.4.5.14.1696-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (2292) fugawi.4.5.14.1696-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (2292) fugawi.4.5.14.1696-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2292) fugawi.4.5.14.1696-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 4 |
Value: 6600750067006100770069002E0034002E0035002E00310034002E0031003600390036002D00700061007400630068002E00650078006500000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000003D010000BE000000BD0300009E020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2292) fugawi.4.5.14.1696-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | 4 |
Value: fugawi.4.5.14.1696-patch.exe | |||
| (PID) Process: | (2292) fugawi.4.5.14.1696-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 4 |
Value: 6600750067006100770069002E0034002E0035002E00310034002E0031003600390036002D00700061007400630068002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000003D010000ED000000C2030000C7010000000000000000000000000000000000003D010000BE000000BD0300009E020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2292) fugawi.4.5.14.1696-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0400000000000000020000000300000001000000FFFFFFFF | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2292 | fugawi.4.5.14.1696-patch.exe | C:\Windows\system32\BASSMOD.dll | executable | |
MD5:— | SHA256:— | |||
| 2292 | fugawi.4.5.14.1696-patch.exe | C:\regpatch.reg | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |