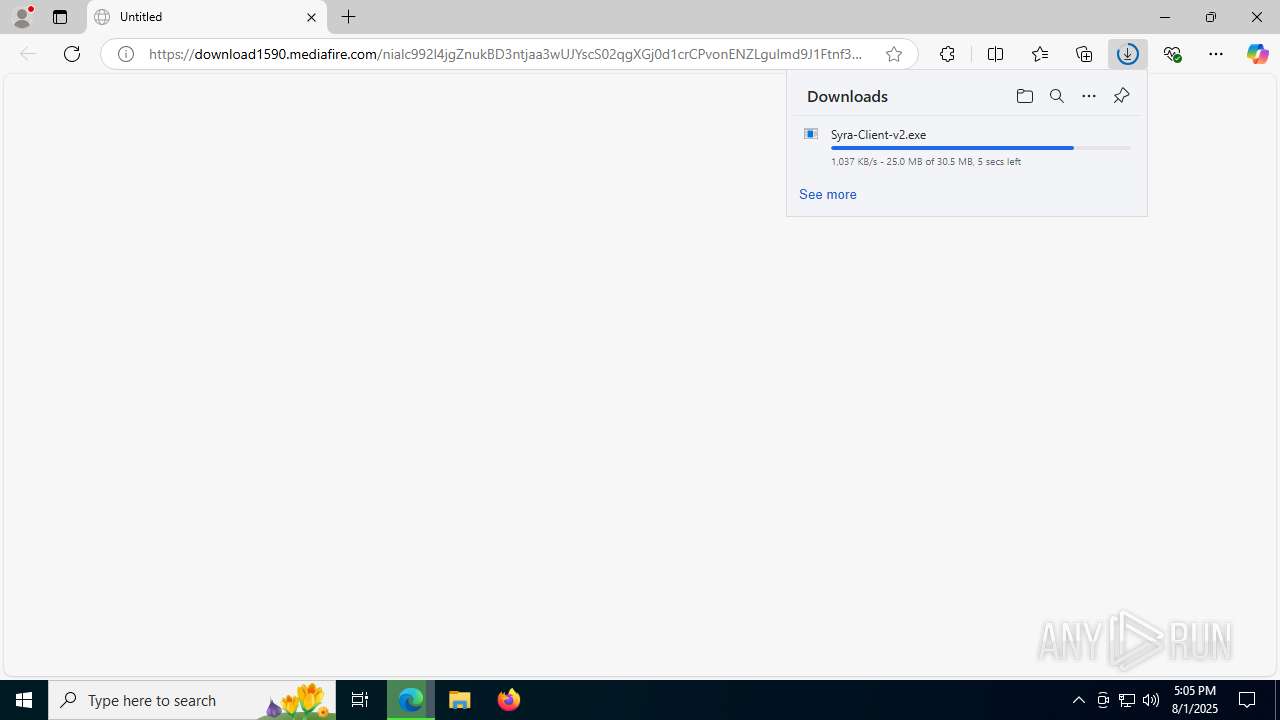
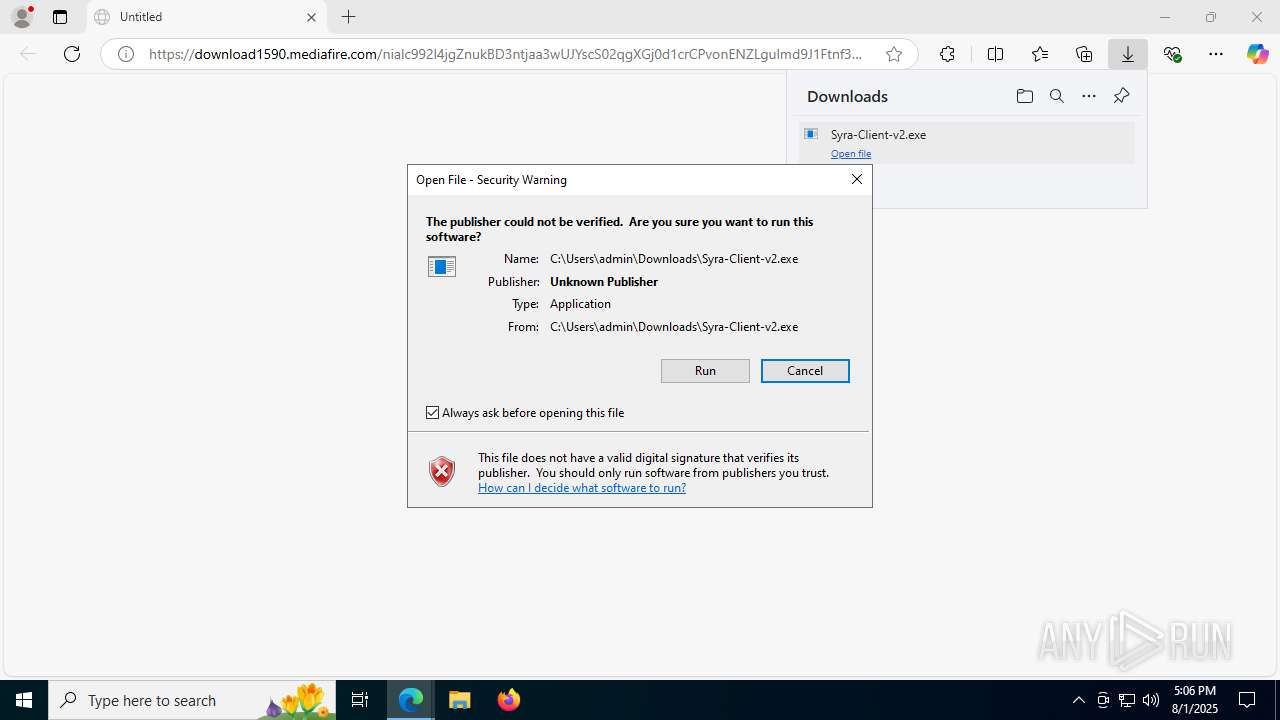
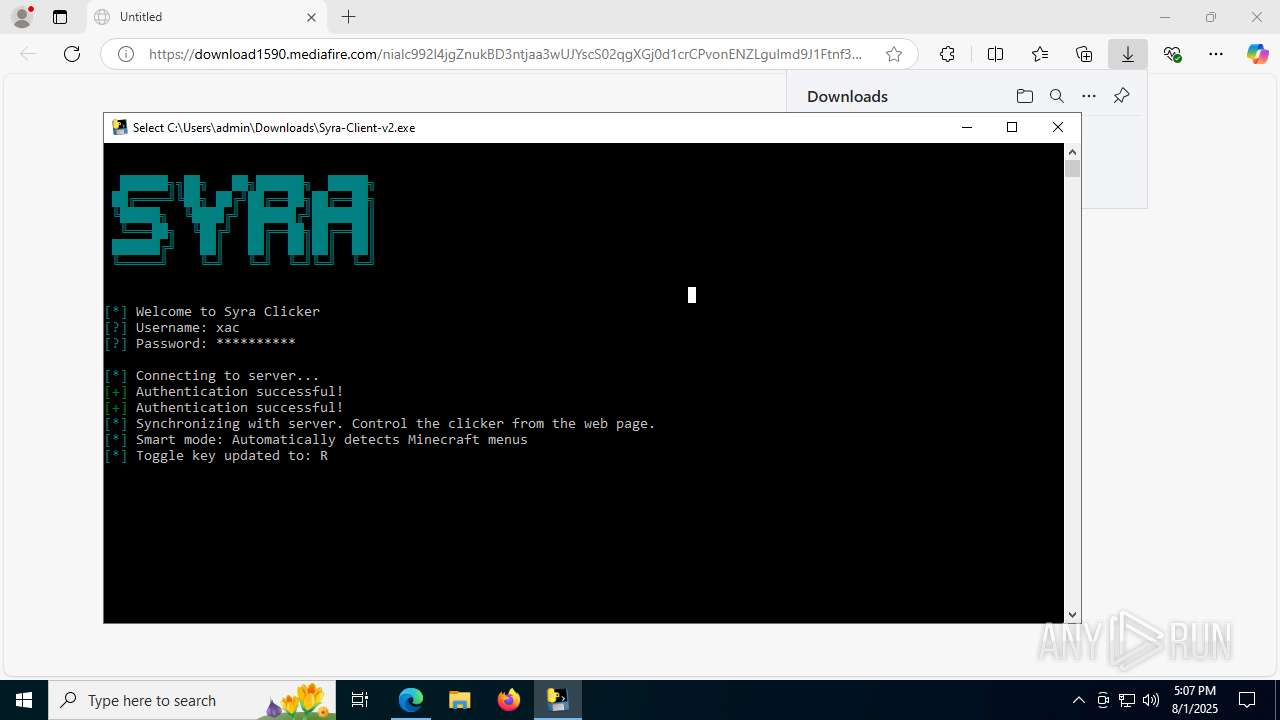
| URL: | https://download1590.mediafire.com/nialc992l4jgZnukBD3ntjaa3wUJYscS02qgXGj0d1crCPvonENZLgulmd9J1Ftnf3u9SC930f6-dEseiZzaa8VB2D8E6hKW0U4-yLnXzWI0Kk6KFPC-rHPSxsxYzKPiTLyhgKg3Vz2FYar3eRnPNFqawPaS-0aAFVwUj3sN1MWi8Ug/64alney959fs1jd/Syra-Client-v2.exe |
| Full analysis: | https://app.any.run/tasks/6fc8f8f6-16f0-4207-87f6-38e0e6291b12 |
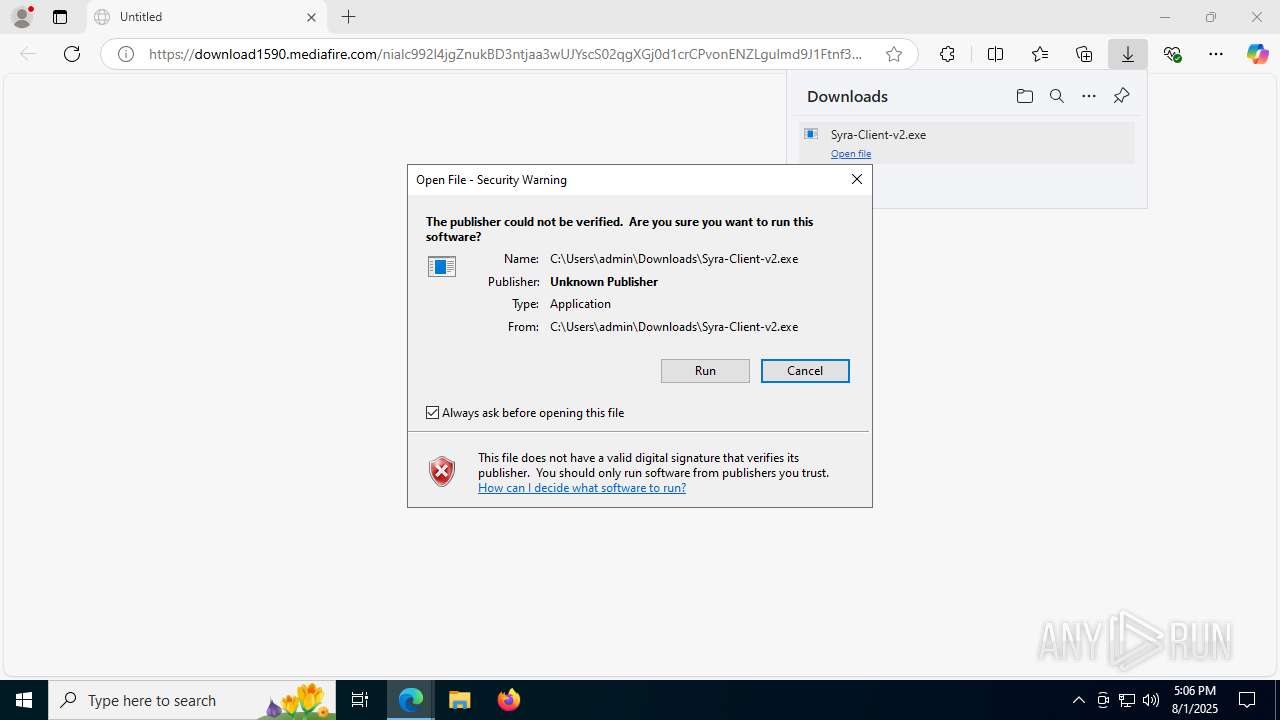
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 17:05:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 63539A0D08CF94C918BA10DAA5FEEB2C |
| SHA1: | A0CA16C1C34F7A13C223BD90E0314DF66A94C851 |
| SHA256: | 716ACDF9307933B93050CDEA970B097D56E6E3ED2AB1461DD4AB41646EF99086 |
| SSDEEP: | 6:2S6cVLIdeG/aEavn7GP/c96QVZWqTEq1m6j1EEX0C:20VLIdegyKPODZdTxj1EYJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
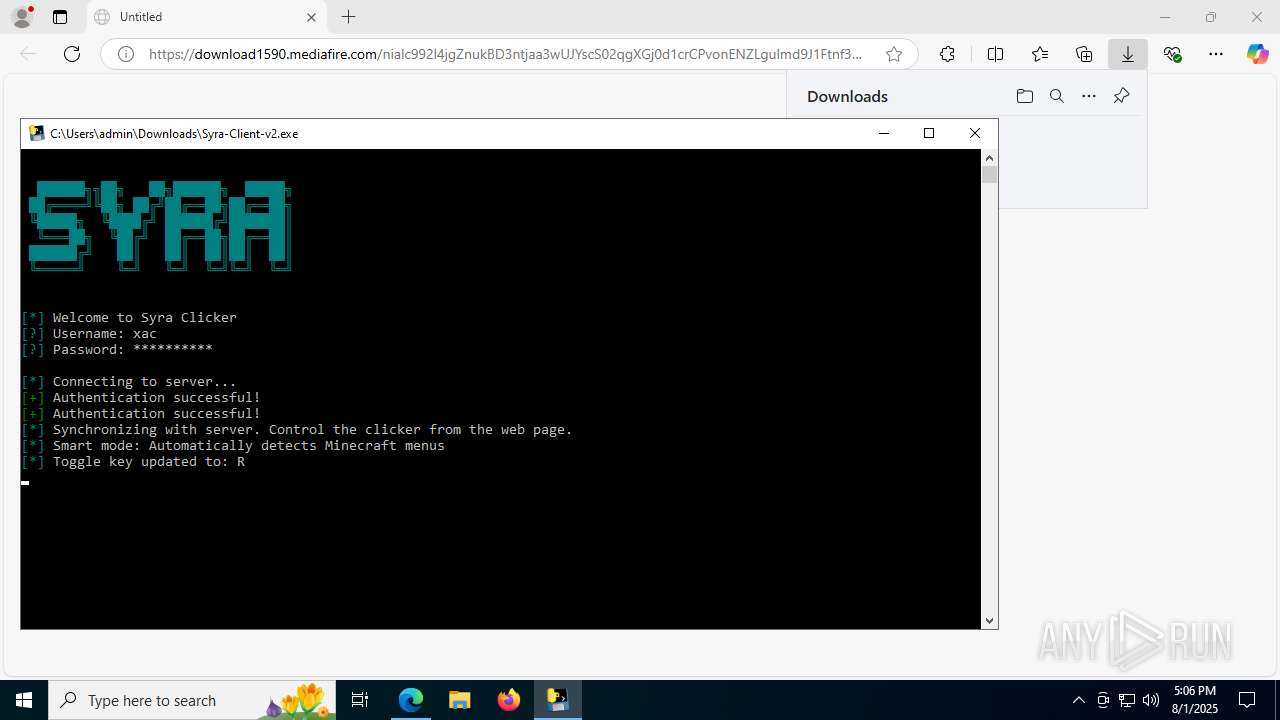
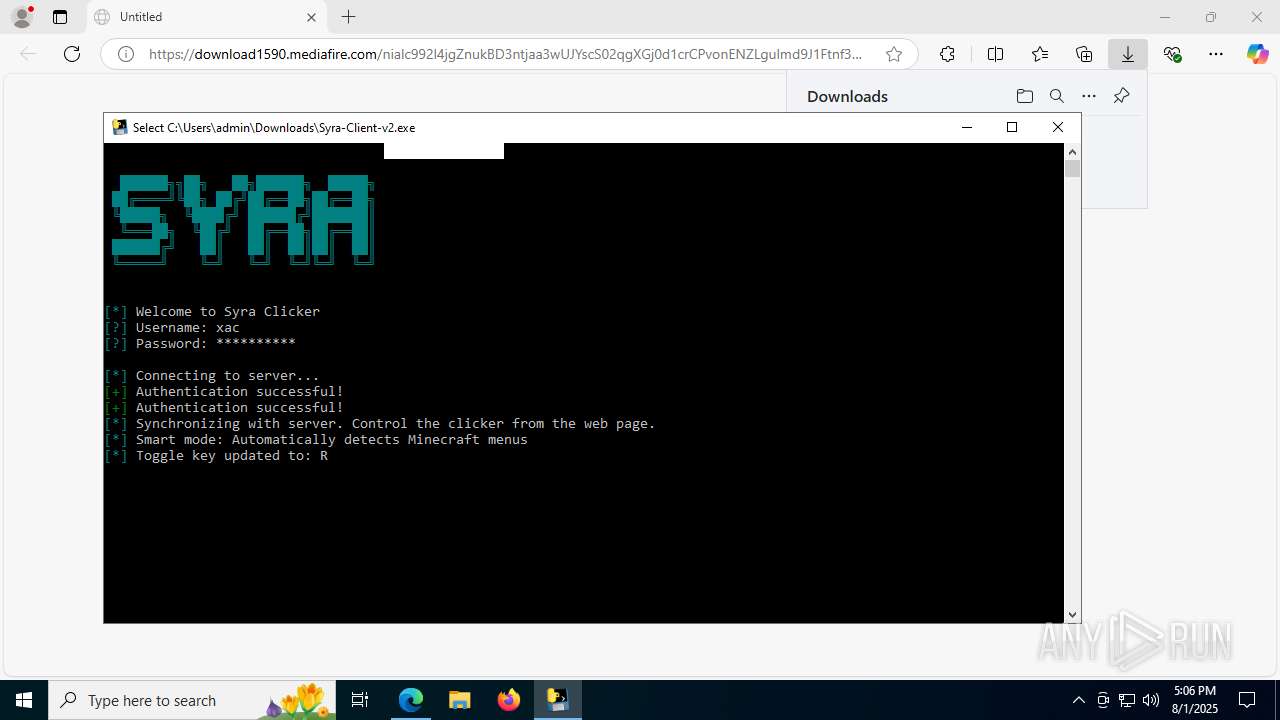
Process drops python dynamic module
- Syra-Client-v2.exe (PID: 5576)
- Syra-Client-v2.exe (PID: 7736)
Executable content was dropped or overwritten
- Syra-Client-v2.exe (PID: 5576)
- Syra-Client-v2.exe (PID: 7736)
Process drops legitimate windows executable
- Syra-Client-v2.exe (PID: 5576)
- Syra-Client-v2.exe (PID: 7736)
Potential Corporate Privacy Violation
- Syra-Client-v2.exe (PID: 2028)
- Syra-Client-v2.exe (PID: 5416)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2632)
- cmd.exe (PID: 5824)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 5556)
- WMIC.exe (PID: 4084)
Application launched itself
- Syra-Client-v2.exe (PID: 5576)
- Syra-Client-v2.exe (PID: 7736)
Loads Python modules
- Syra-Client-v2.exe (PID: 2028)
- Syra-Client-v2.exe (PID: 5416)
The process drops C-runtime libraries
- Syra-Client-v2.exe (PID: 5576)
- Syra-Client-v2.exe (PID: 7736)
Starts CMD.EXE for commands execution
- Syra-Client-v2.exe (PID: 2028)
- Syra-Client-v2.exe (PID: 5416)
Connects to the server without a host name
- Syra-Client-v2.exe (PID: 2028)
There is functionality for taking screenshot (YARA)
- Syra-Client-v2.exe (PID: 5416)
INFO
Checks supported languages
- identity_helper.exe (PID: 7616)
- Syra-Client-v2.exe (PID: 5576)
- Syra-Client-v2.exe (PID: 2028)
- Syra-Client-v2.exe (PID: 7736)
- Syra-Client-v2.exe (PID: 5416)
Reads Environment values
- identity_helper.exe (PID: 7616)
Application launched itself
- msedge.exe (PID: 1828)
Reads the computer name
- identity_helper.exe (PID: 7616)
- Syra-Client-v2.exe (PID: 5576)
- Syra-Client-v2.exe (PID: 7736)
- Syra-Client-v2.exe (PID: 2028)
- Syra-Client-v2.exe (PID: 5416)
Executable content was dropped or overwritten
- msedge.exe (PID: 1828)
Create files in a temporary directory
- Syra-Client-v2.exe (PID: 5576)
- Syra-Client-v2.exe (PID: 7736)
The sample compiled with english language support
- Syra-Client-v2.exe (PID: 5576)
- Syra-Client-v2.exe (PID: 7736)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 5556)
- WMIC.exe (PID: 4084)
PyInstaller has been detected (YARA)
- Syra-Client-v2.exe (PID: 5576)
- Syra-Client-v2.exe (PID: 7736)
- Syra-Client-v2.exe (PID: 5416)
Checks proxy server information
- Syra-Client-v2.exe (PID: 2028)
- Syra-Client-v2.exe (PID: 5416)
- slui.exe (PID: 8044)
Reads the software policy settings
- slui.exe (PID: 8044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
183
Monitored processes
45
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1352 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5380,i,8306729441332569331,15437124281789619947,262144 --variations-seed-version --mojo-platform-channel-handle=4948 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2260,i,8306729441332569331,15437124281789619947,262144 --variations-seed-version --mojo-platform-channel-handle=2352 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1828 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --from-ie-to-edge=8 -- "https://download1590.mediafire.com/nialc992l4jgZnukBD3ntjaa3wUJYscS02qgXGj0d1crCPvonENZLgulmd9J1Ftnf3u9SC930f6-dEseiZzaa8VB2D8E6hKW0U4-yLnXzWI0Kk6KFPC-rHPSxsxYzKPiTLyhgKg3Vz2FYar3eRnPNFqawPaS-0aAFVwUj3sN1MWi8Ug/64alney959fs1jd/Syra-Client-v2.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1964 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6944,i,8306729441332569331,15437124281789619947,262144 --variations-seed-version --mojo-platform-channel-handle=1480 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2028 | "C:\Users\admin\Downloads\Syra-Client-v2.exe" | C:\Users\admin\Downloads\Syra-Client-v2.exe | Syra-Client-v2.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7048,i,8306729441332569331,15437124281789619947,262144 --variations-seed-version --mojo-platform-channel-handle=6424 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3612,i,8306729441332569331,15437124281789619947,262144 --variations-seed-version --mojo-platform-channel-handle=3628 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2632 | C:\WINDOWS\system32\cmd.exe /c "wmic csproduct get uuid" | C:\Windows\System32\cmd.exe | — | Syra-Client-v2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://download1590.mediafire.com/nialc992l4jgZnukBD3ntjaa3wUJYscS02qgXGj0d1crCPvonENZLgulmd9J1Ftnf3u9SC930f6-dEseiZzaa8VB2D8E6hKW0U4-yLnXzWI0Kk6KFPC-rHPSxsxYzKPiTLyhgKg3Vz2FYar3eRnPNFqawPaS-0aAFVwUj3sN1MWi8Ug/64alney959fs1jd/Syra-Client-v2.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 488
Read events
9 470
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (1828) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1828) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1828) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1828) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
200
Suspicious files
222
Text files
98
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d2db.TMP | — | |
MD5:— | SHA256:— | |||
| 1828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d2db.TMP | — | |
MD5:— | SHA256:— | |||
| 1828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18d2eb.TMP | — | |
MD5:— | SHA256:— | |||
| 1828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18d31a.TMP | — | |
MD5:— | SHA256:— | |||
| 1828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d31a.TMP | — | |
MD5:— | SHA256:— | |||
| 1828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1828 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF18d31a.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
188
TCP/UDP connections
62
DNS requests
60
Threats
174
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7772 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1612 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:CKehoHLeC7MQC0mo4PP3quNUP9sbd2Yd0VGbBfs4AWE&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1468 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7772 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2028 | Syra-Client-v2.exe | GET | 200 | 34.23.248.4:80 | http://34.23.248.4/api/version | unknown | — | — | unknown |
3896 | svchost.exe | HEAD | 200 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754359518&P2=404&P3=2&P4=bFe2%2b4BOnu2ObkjMttya9S0ABTBn2ATchOlfV0E3YqQwgnd0vE5XuqmdfqPJxabr3hvg4qrHugHIGsaOWHdSEQ%3d%3d | unknown | — | — | whitelisted |
2028 | Syra-Client-v2.exe | POST | 403 | 34.23.248.4:80 | http://34.23.248.4/api/auth/login | unknown | — | — | unknown |
3896 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754359518&P2=404&P3=2&P4=bFe2%2b4BOnu2ObkjMttya9S0ABTBn2ATchOlfV0E3YqQwgnd0vE5XuqmdfqPJxabr3hvg4qrHugHIGsaOWHdSEQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2216 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1612 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1612 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1612 | msedge.exe | 199.91.152.90:443 | download1590.mediafire.com | MEDIAFIRE | US | whitelisted |
1612 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1612 | msedge.exe | 92.123.104.53:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
download1590.mediafire.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
1612 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
1612 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2028 | Syra-Client-v2.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
2028 | Syra-Client-v2.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
5416 | Syra-Client-v2.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
5416 | Syra-Client-v2.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
5416 | Syra-Client-v2.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
5416 | Syra-Client-v2.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
5416 | Syra-Client-v2.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |