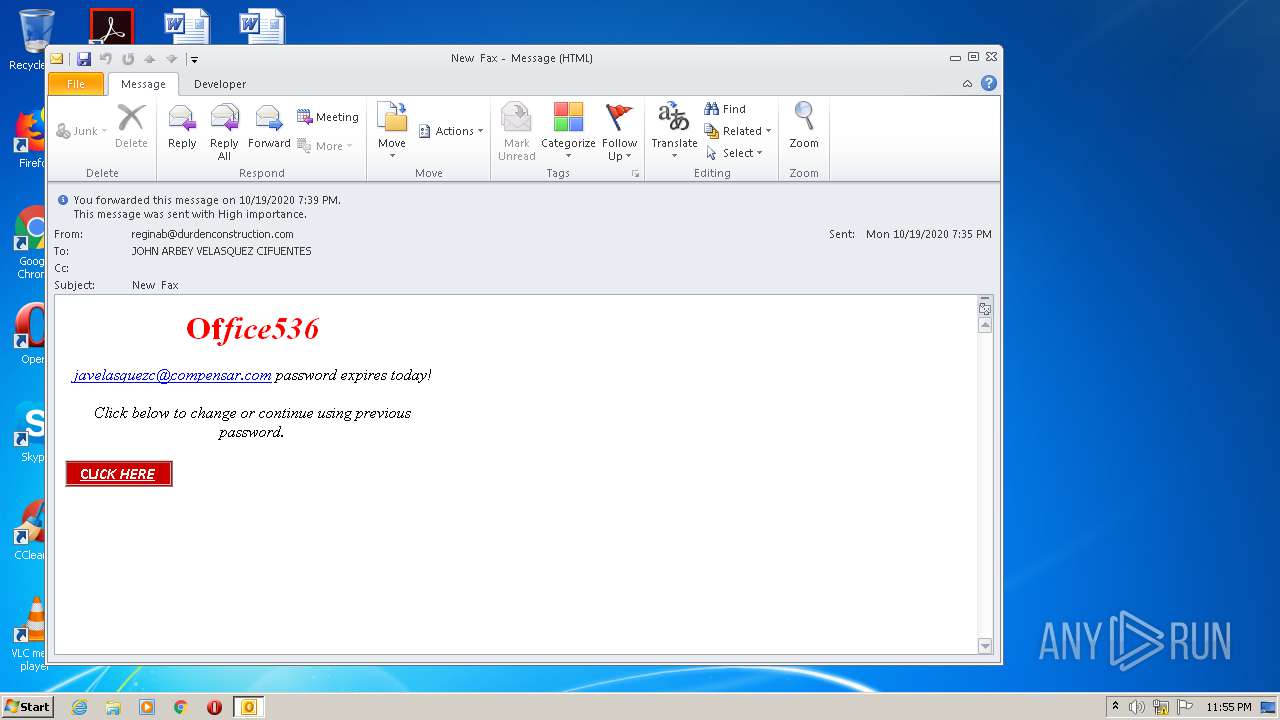
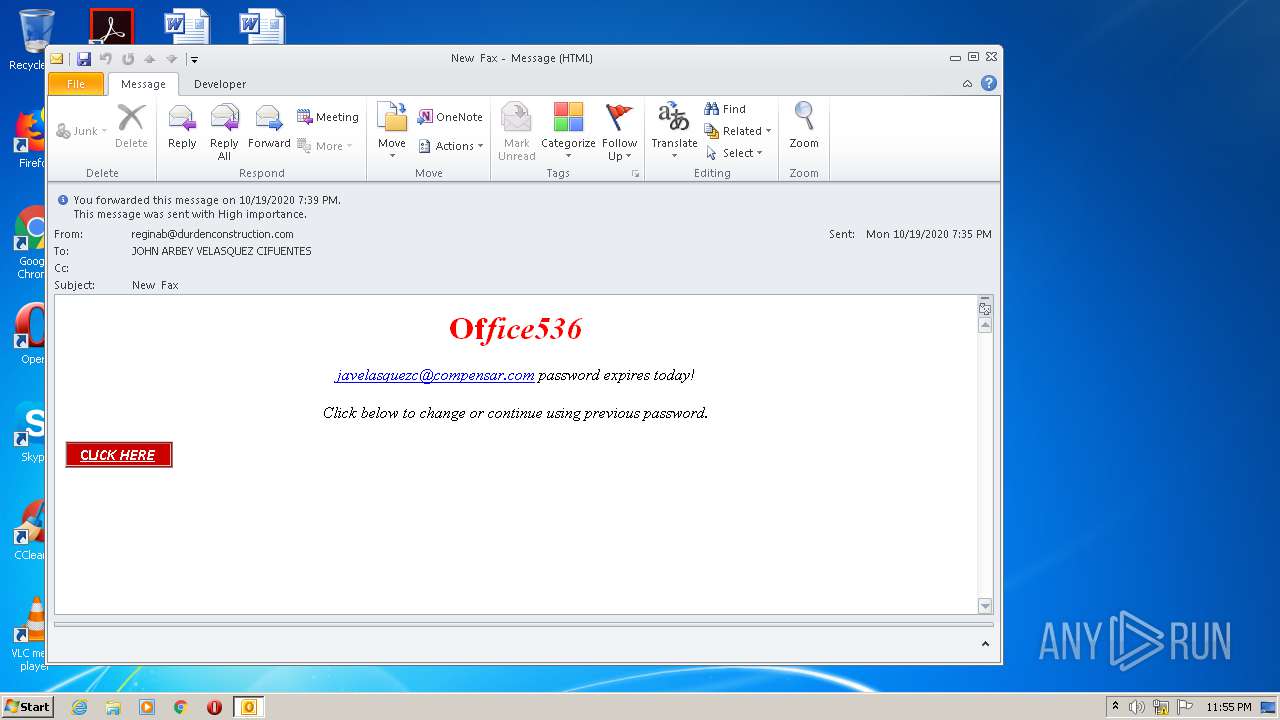
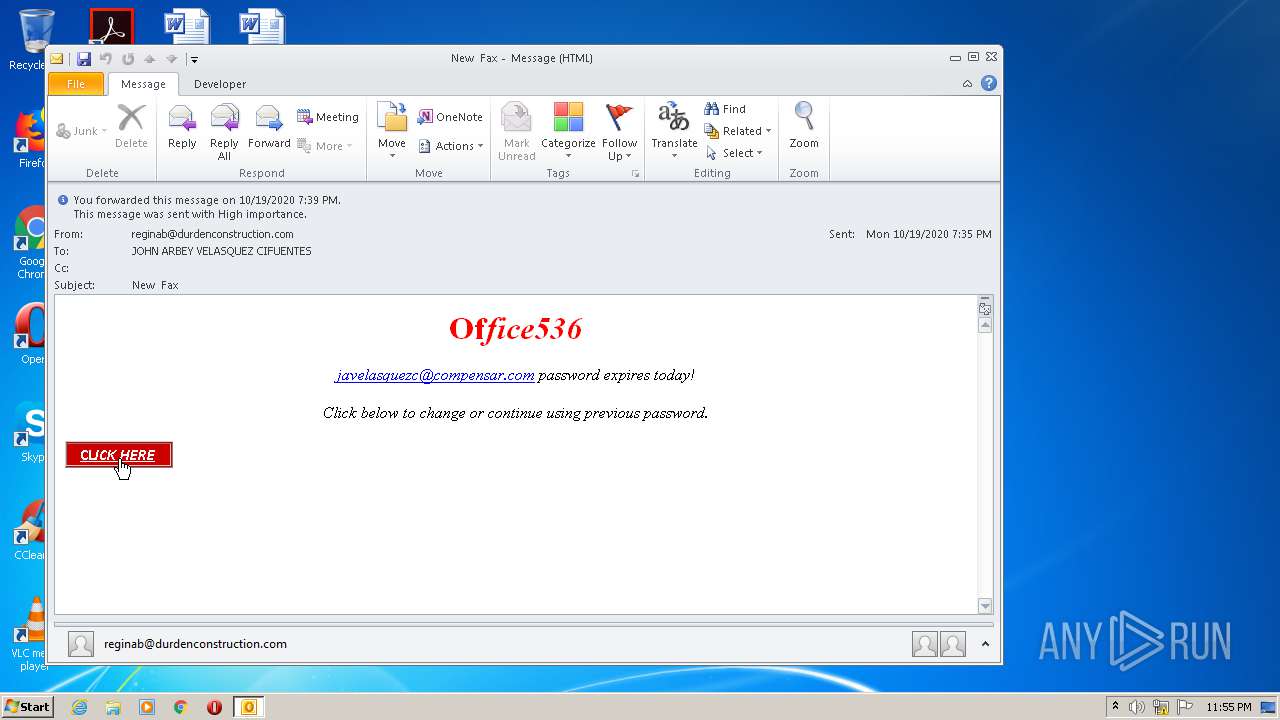
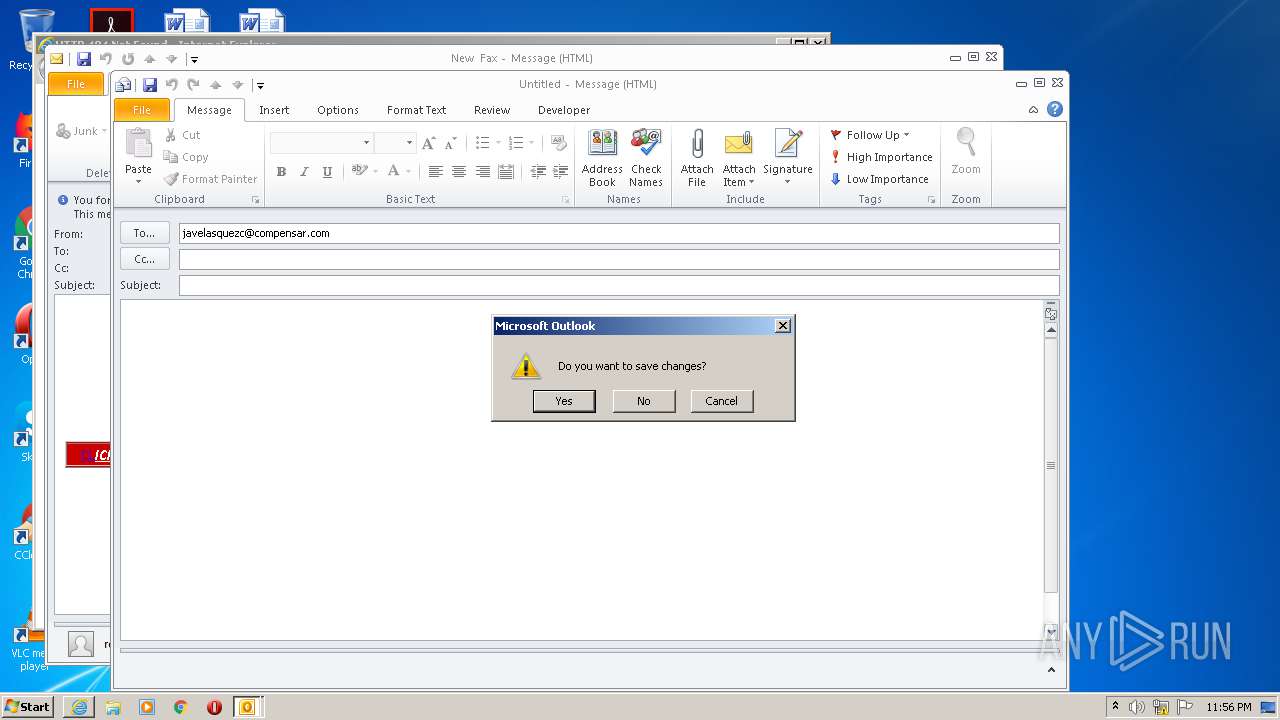
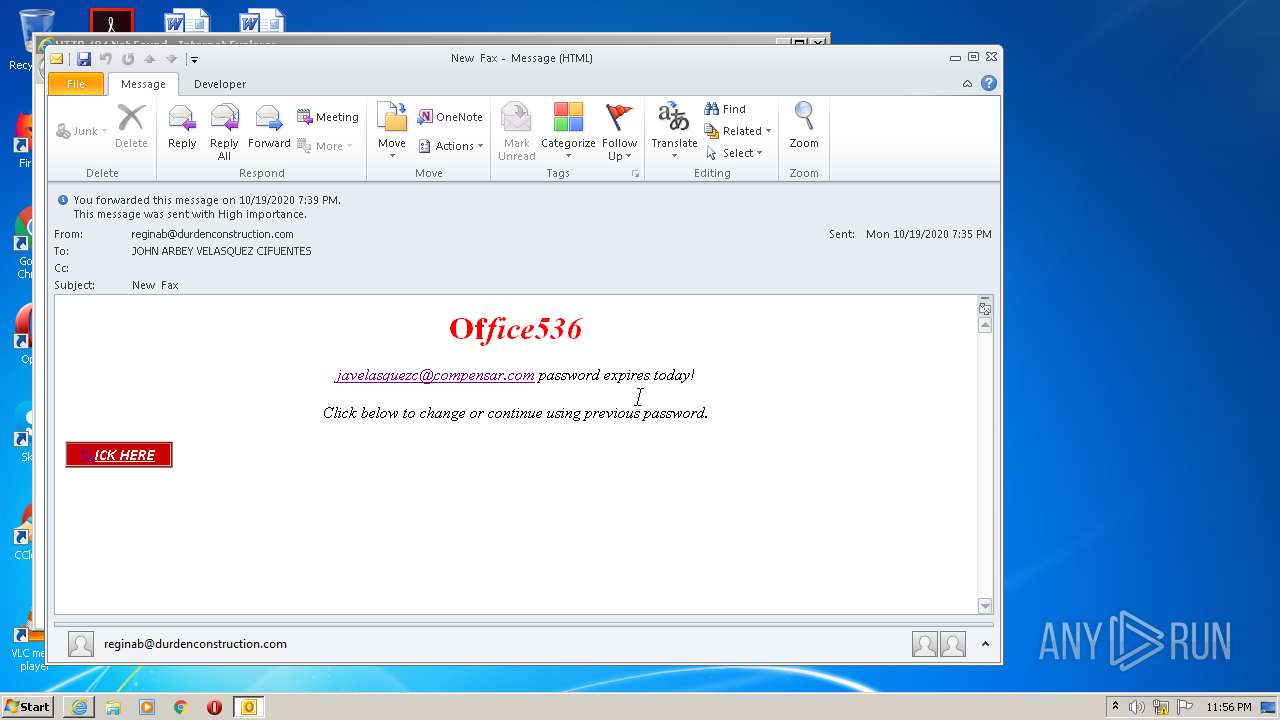
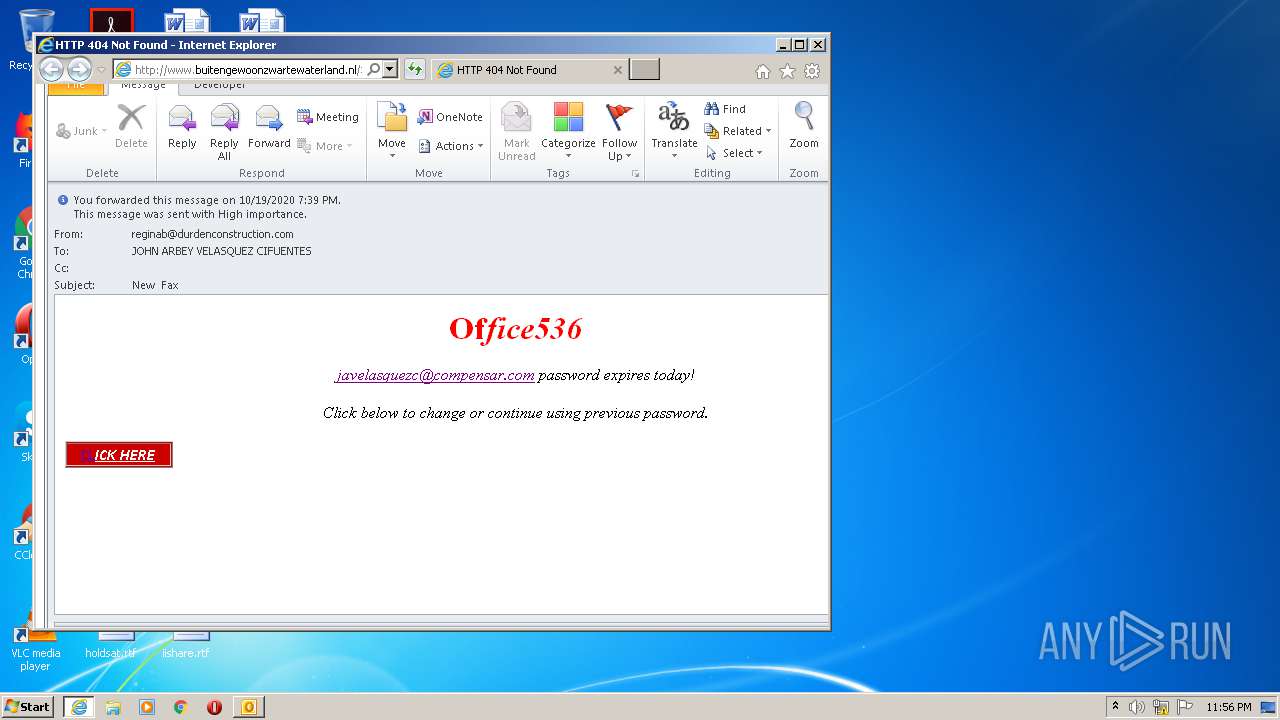
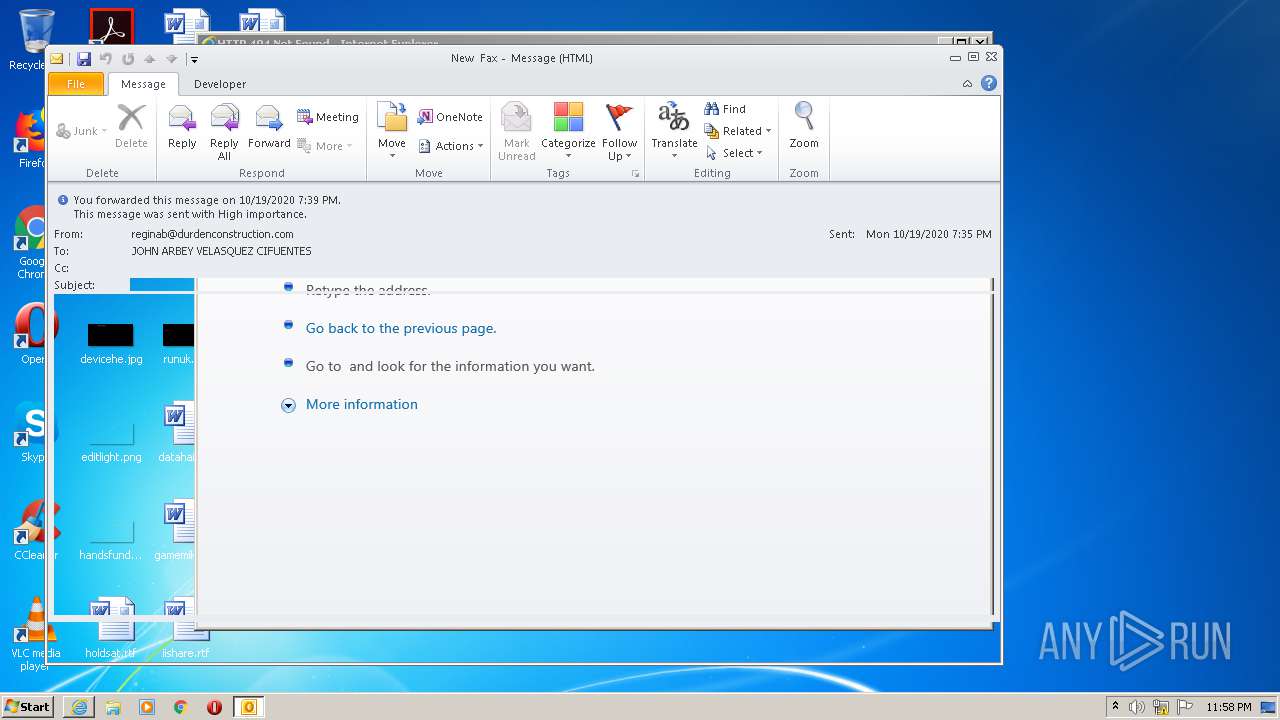
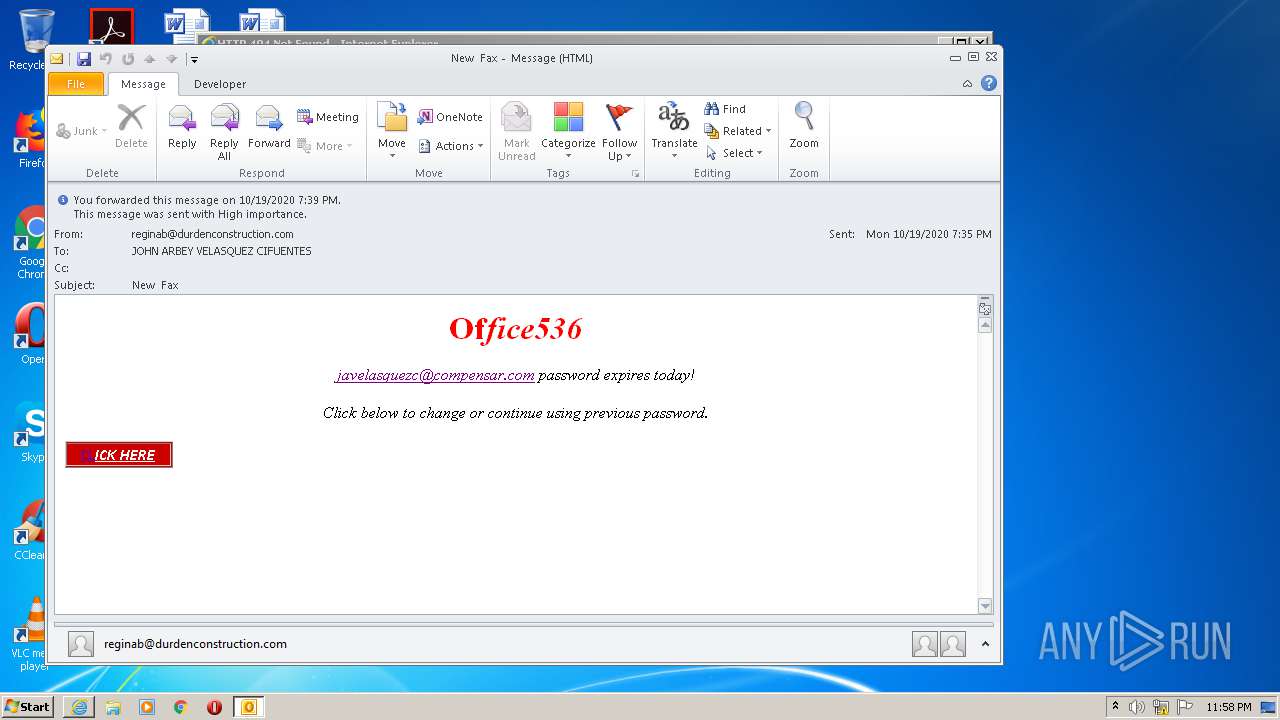
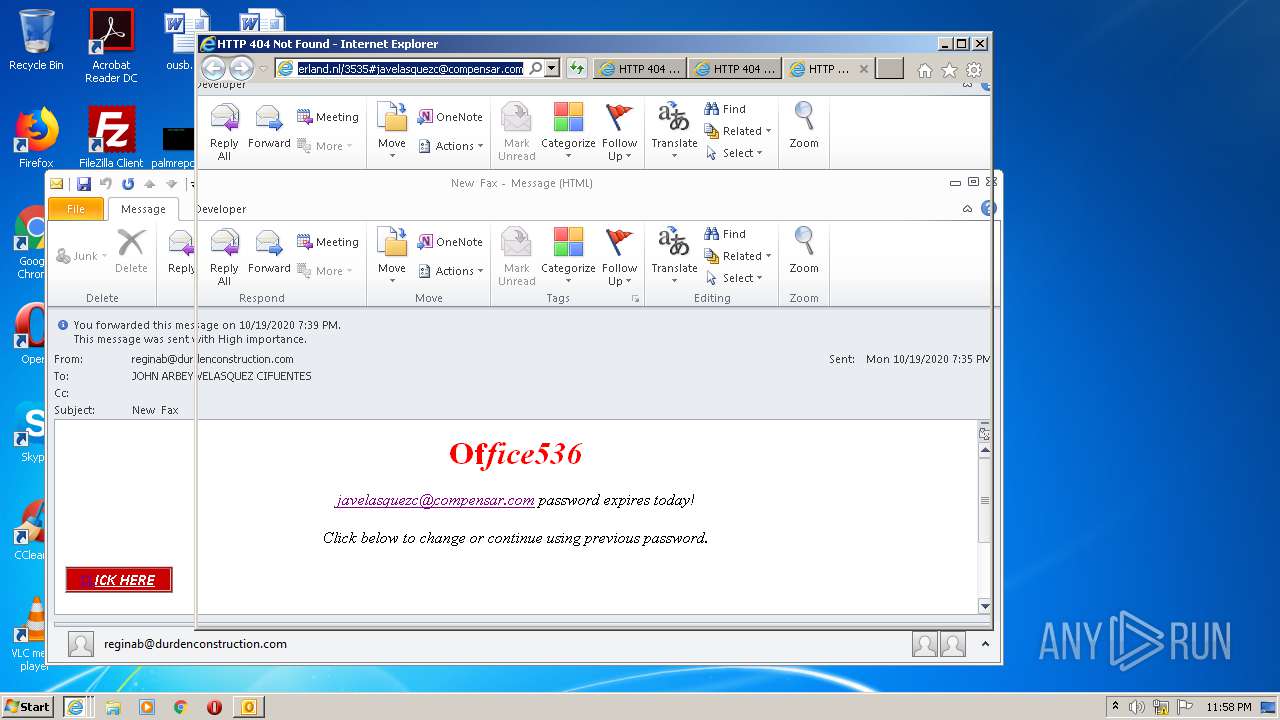
| File name: | New Fax.msg |
| Full analysis: | https://app.any.run/tasks/69d518f5-d190-457f-92bf-a0e2adf8fc57 |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 22:55:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | D48BF1FE2CF5AD1EB3FAB040933D2229 |
| SHA1: | 87FA9F485687CB36107A521E51816CC4D3E3CB1B |
| SHA256: | 716A903F485A34F69F884A0A3CA57852796AED3344DDD7D87AE872828DE693F1 |
| SSDEEP: | 1536:L1XUMWDWfe5HeWKuLmbnWOWmC1Xz2bkZ0hxUZpLGGC:L1Xw5HiuLrXWkZtIGC |
MALICIOUS
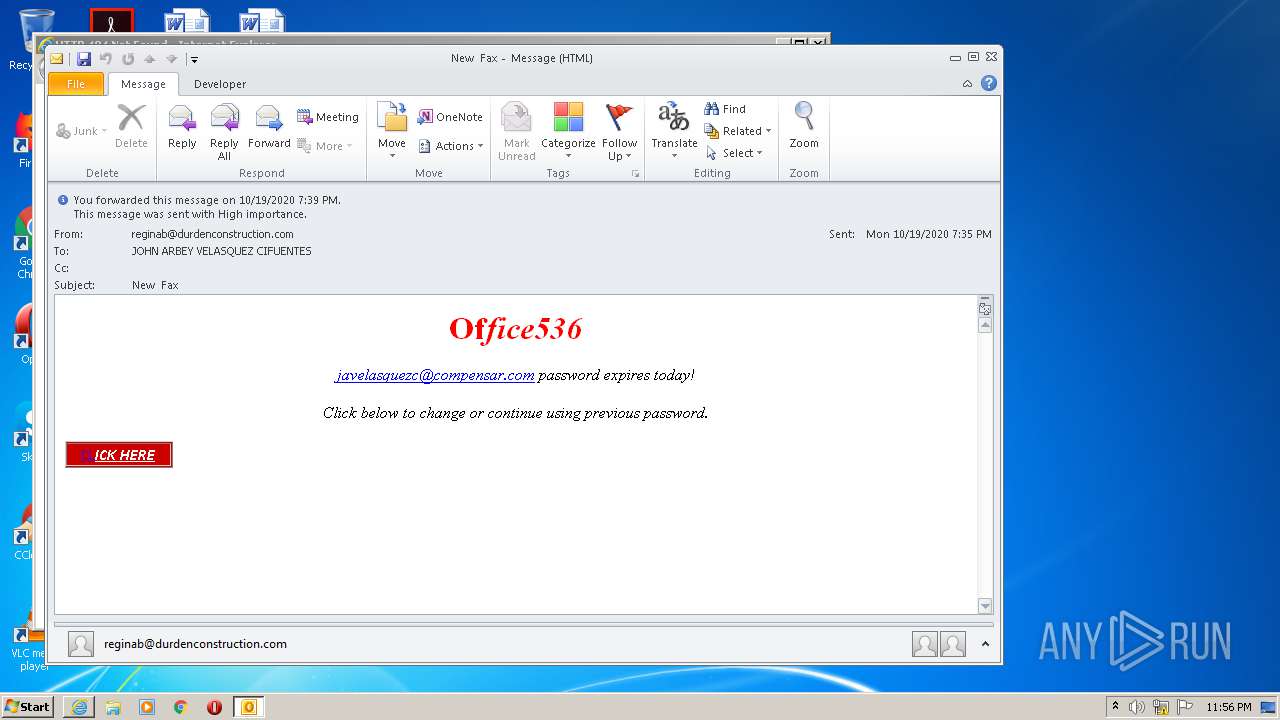
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 1772)
SUSPICIOUS
Starts Internet Explorer
- OUTLOOK.EXE (PID: 1772)
Starts itself from another location
- OUTLOOK.EXE (PID: 1772)
INFO
Application launched itself
- iexplore.exe (PID: 3876)
Reads Internet Cache Settings
- iexplore.exe (PID: 3716)
- iexplore.exe (PID: 3876)
- iexplore.exe (PID: 1788)
- OUTLOOK.EXE (PID: 1772)
- iexplore.exe (PID: 3860)
Creates files in the user directory
- iexplore.exe (PID: 3716)
- OUTLOOK.EXE (PID: 1772)
- iexplore.exe (PID: 3876)
Reads internet explorer settings
- iexplore.exe (PID: 3716)
- iexplore.exe (PID: 1788)
- iexplore.exe (PID: 3876)
- iexplore.exe (PID: 3860)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3876)
Reads settings of System Certificates
- iexplore.exe (PID: 3876)
Changes settings of System certificates
- iexplore.exe (PID: 3876)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1772)
- OUTLOOK.EXE (PID: 1724)
Changes internet zones settings
- iexplore.exe (PID: 3876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
44
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
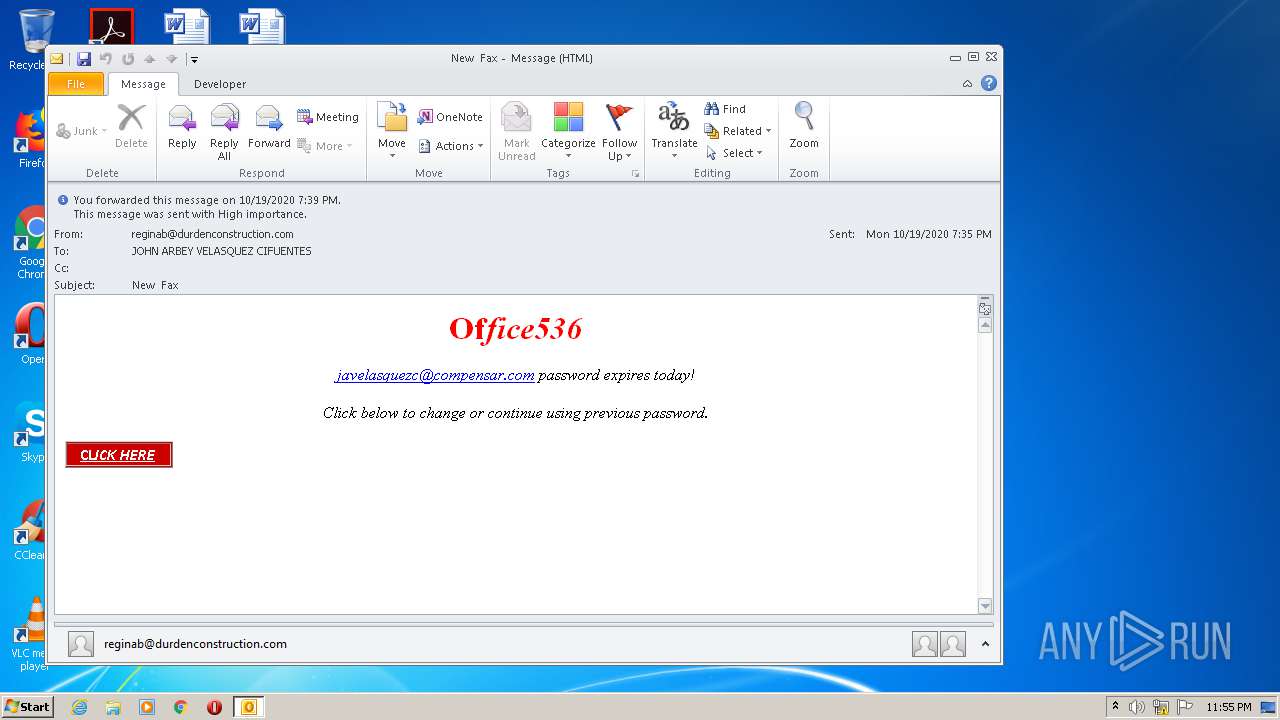
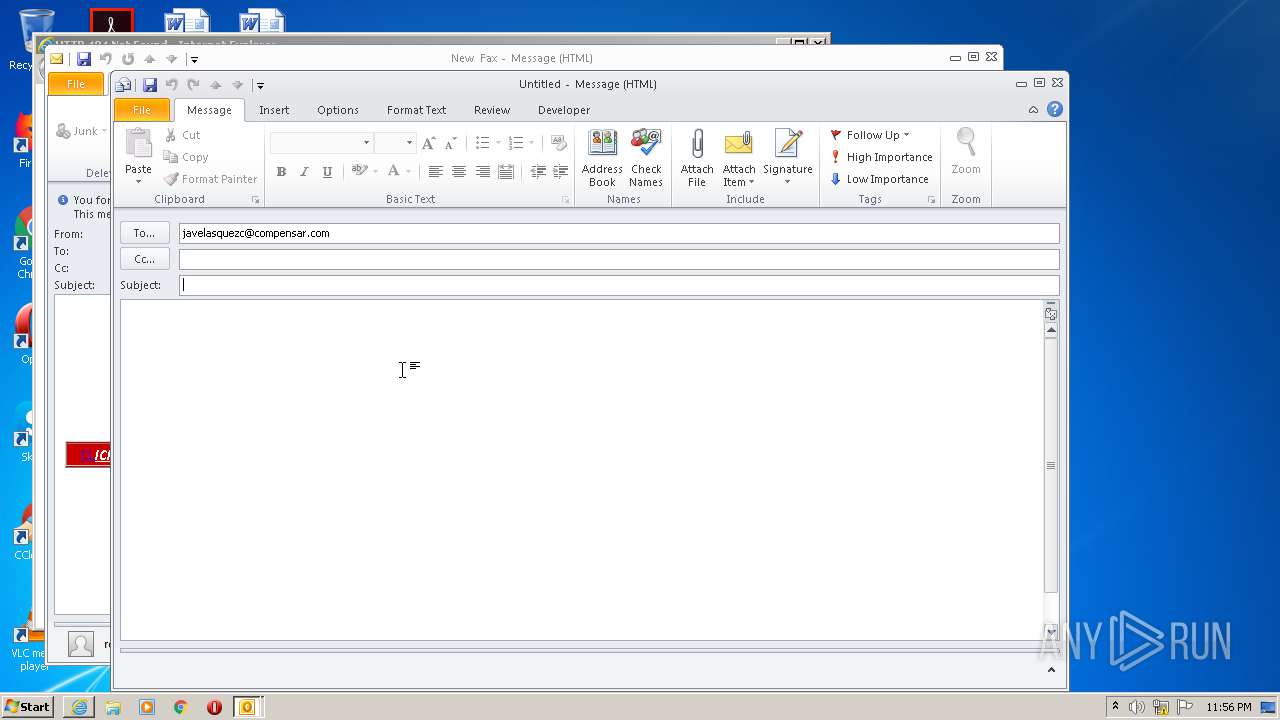
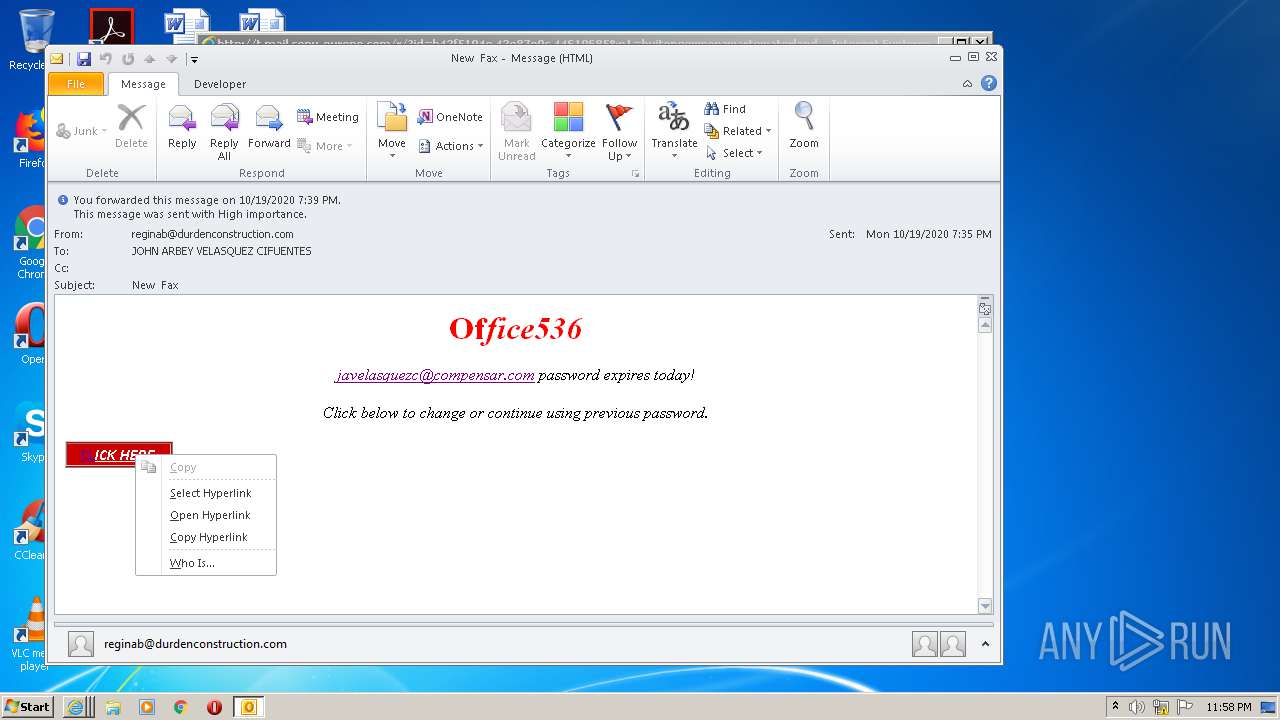
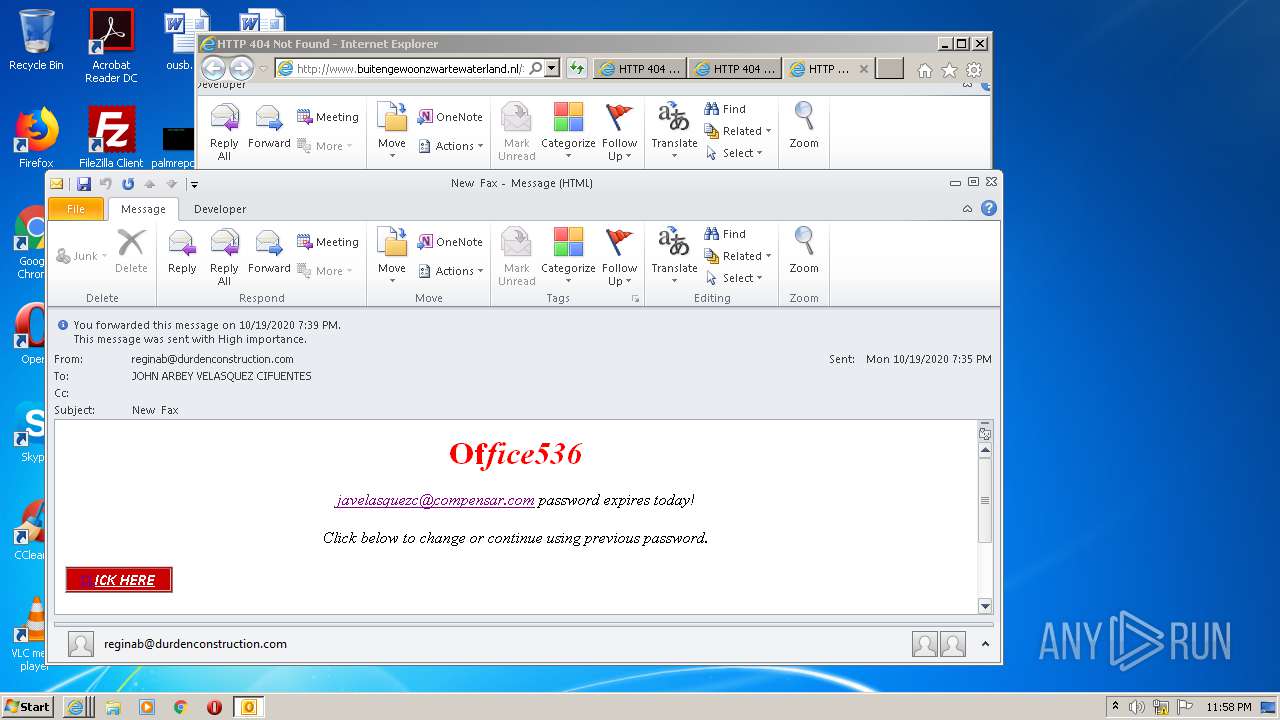
| 1724 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:javelasquezc@compensar.com" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\New Fax.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3876 CREDAT:1185040 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3716 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3876 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3860 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3876 CREDAT:2954513 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
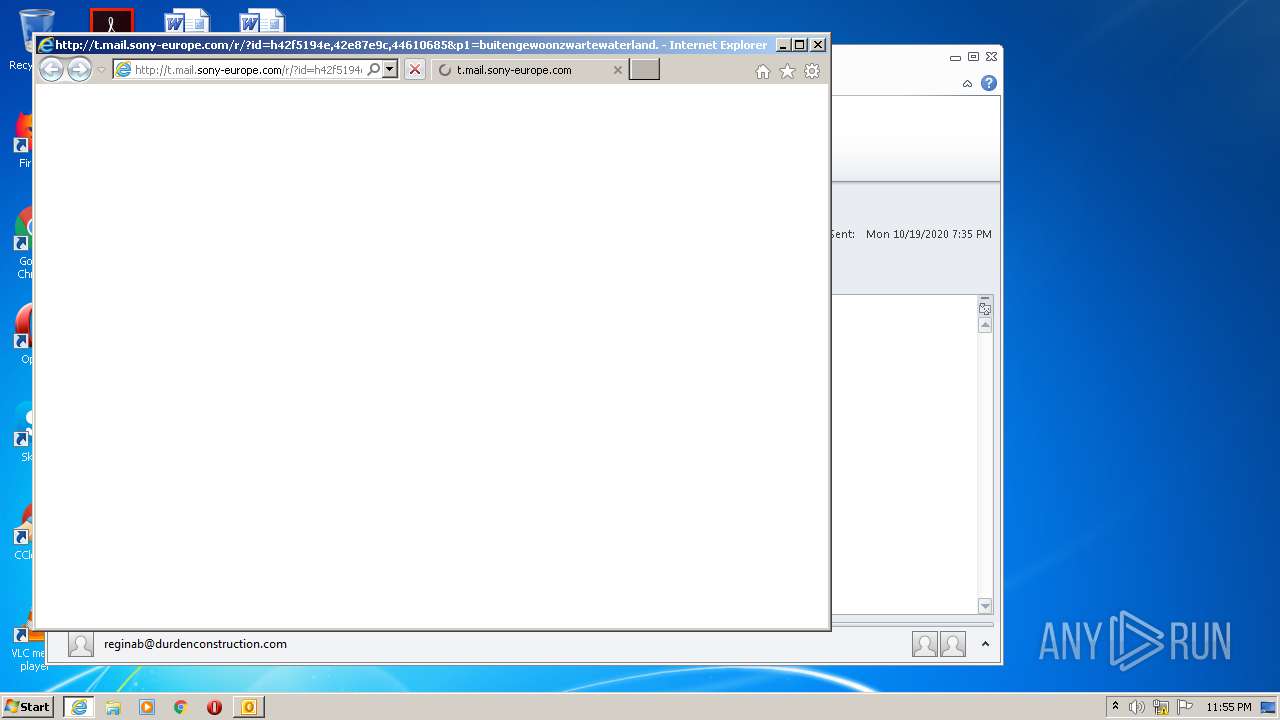
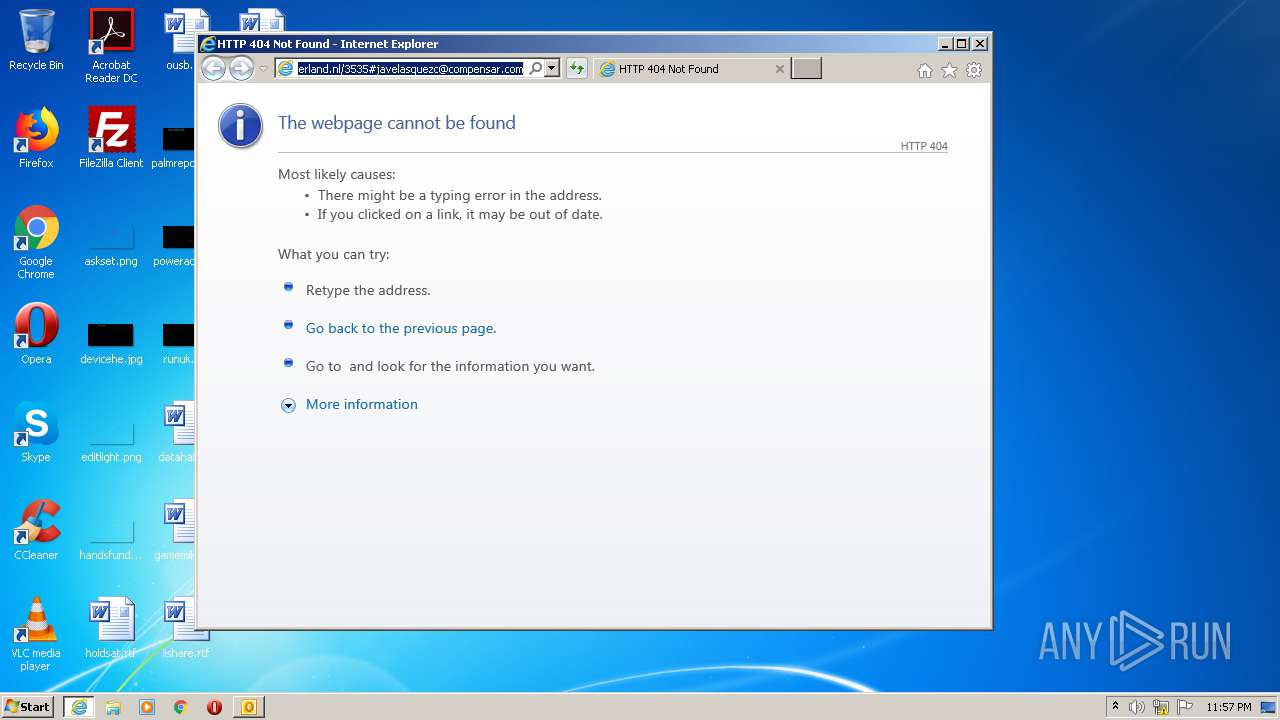
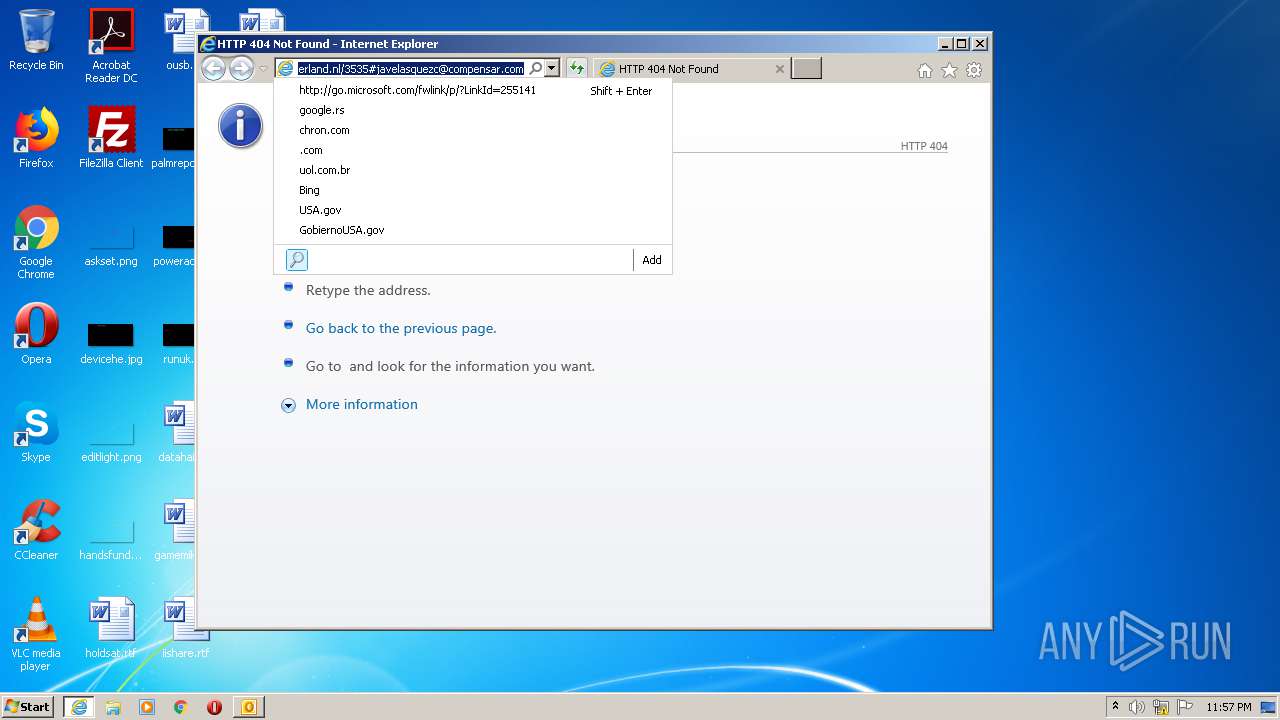
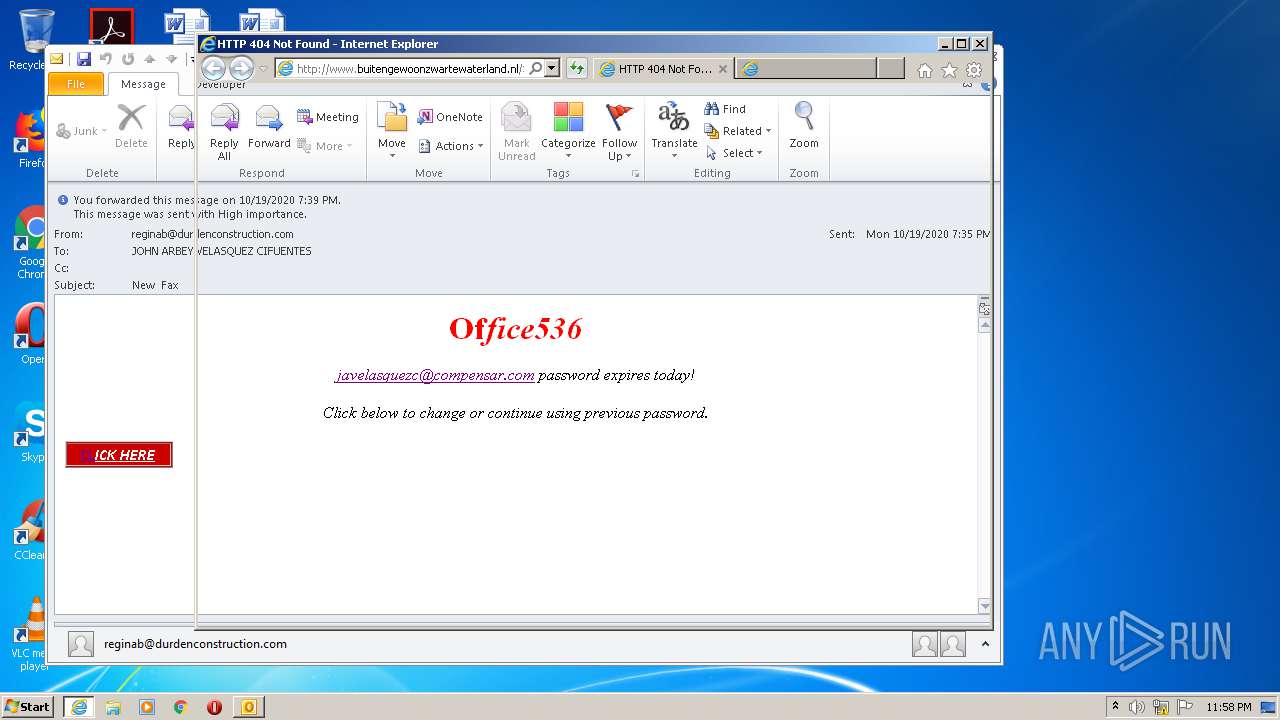
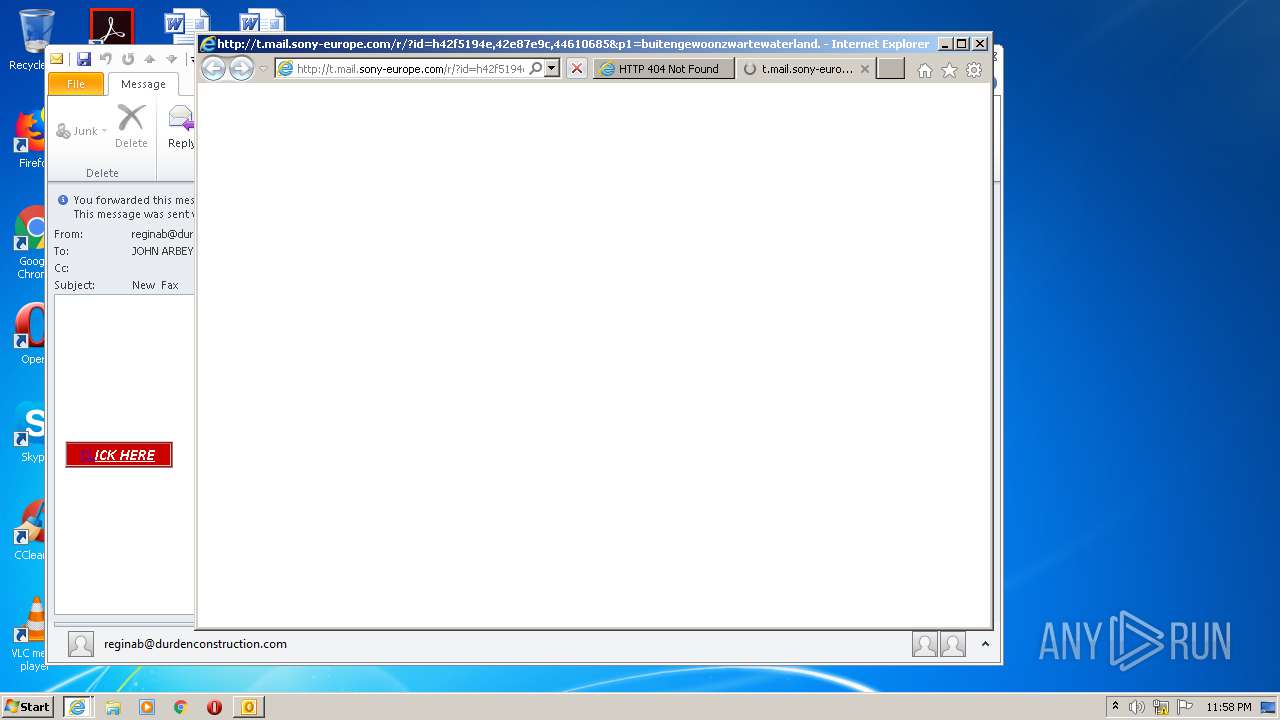
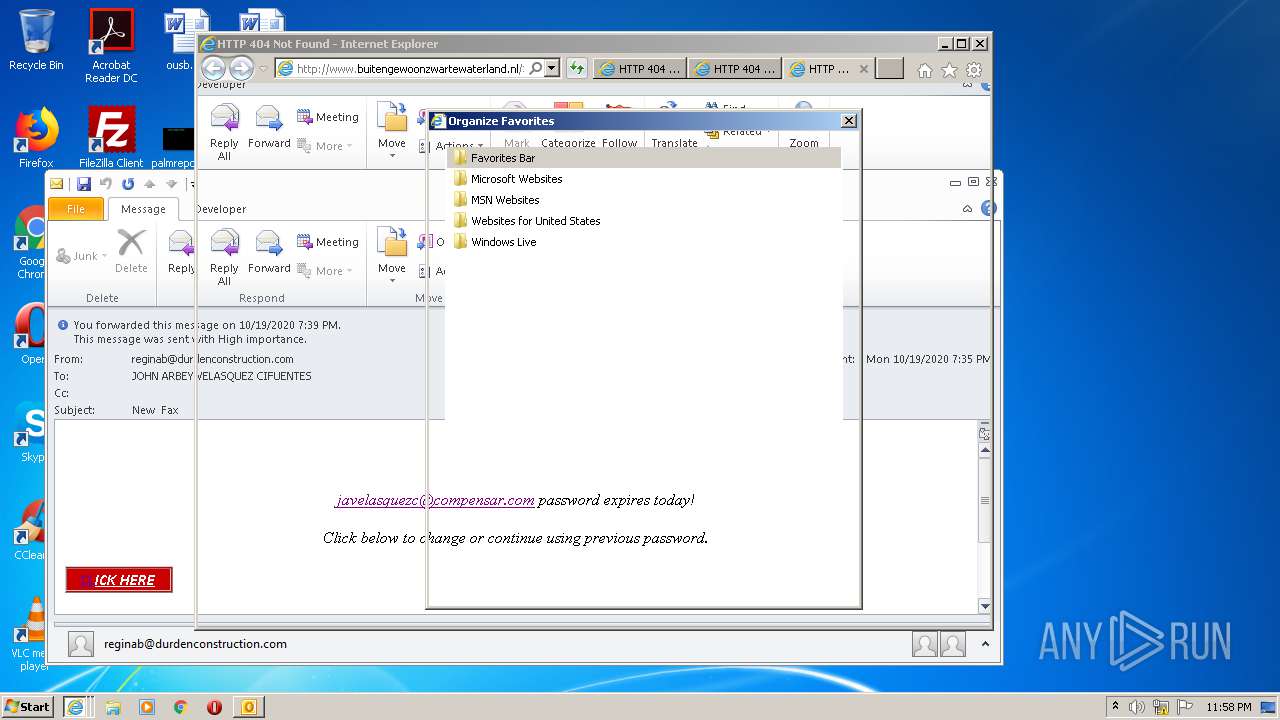
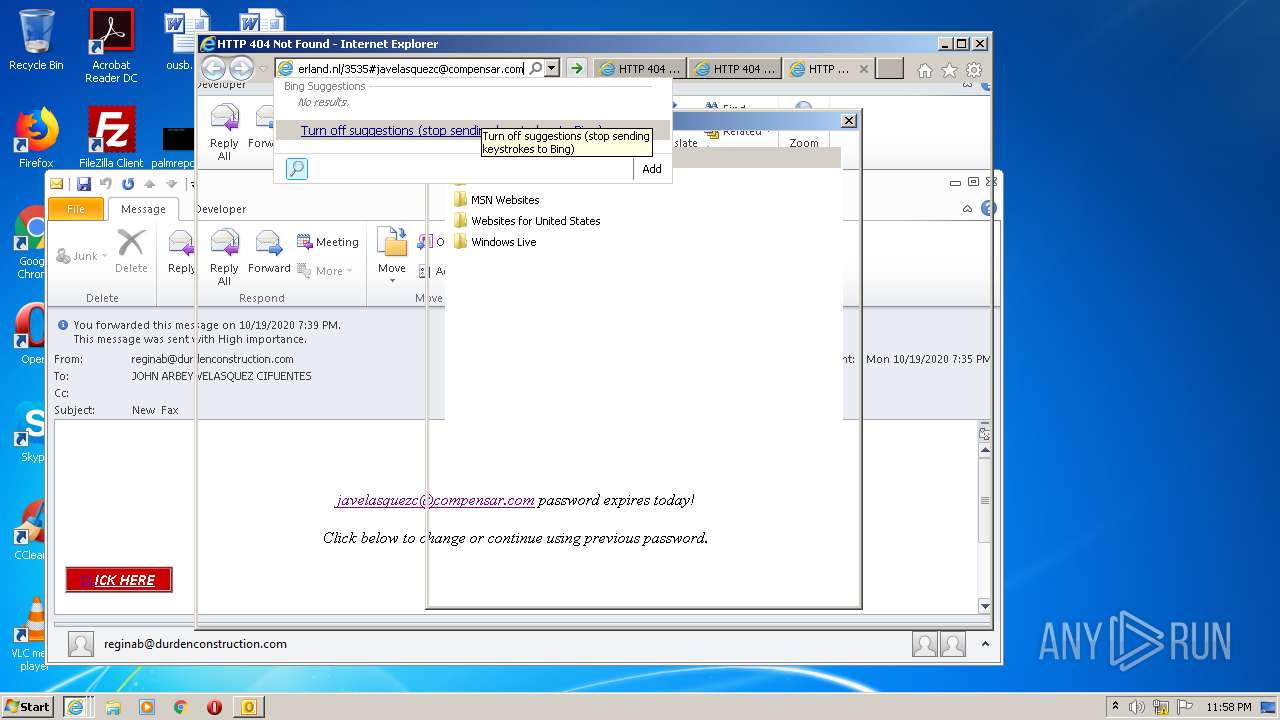
| 3876 | "C:\Program Files\Internet Explorer\iexplore.exe" http://t.mail.sony-europe.com/r/?id=h42f5194e,42e87e9c,44610685&p1=buitengewoonzwartewaterland.nl/3535#javelasquezc@compensar.com | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
3 145
Read events
2 376
Write events
738
Delete events
31
Modification events
| (PID) Process: | (1772) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1772) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1772) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1772) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1772) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1772) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1772) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1772) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1772) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1772) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
10
Text files
67
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1772 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR40D6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1772 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3716 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\errorPageStrings[2] | text | |
MD5:— | SHA256:— | |||
| 3716 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 3876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1724 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRE12D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1772 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1772 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{C7E6EE8B-AEA4-4DCB-AD16-6D45369BD4BD}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 3876 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab6B7.tmp | — | |
MD5:— | SHA256:— | |||
| 3876 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar6B8.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
25
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1772 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
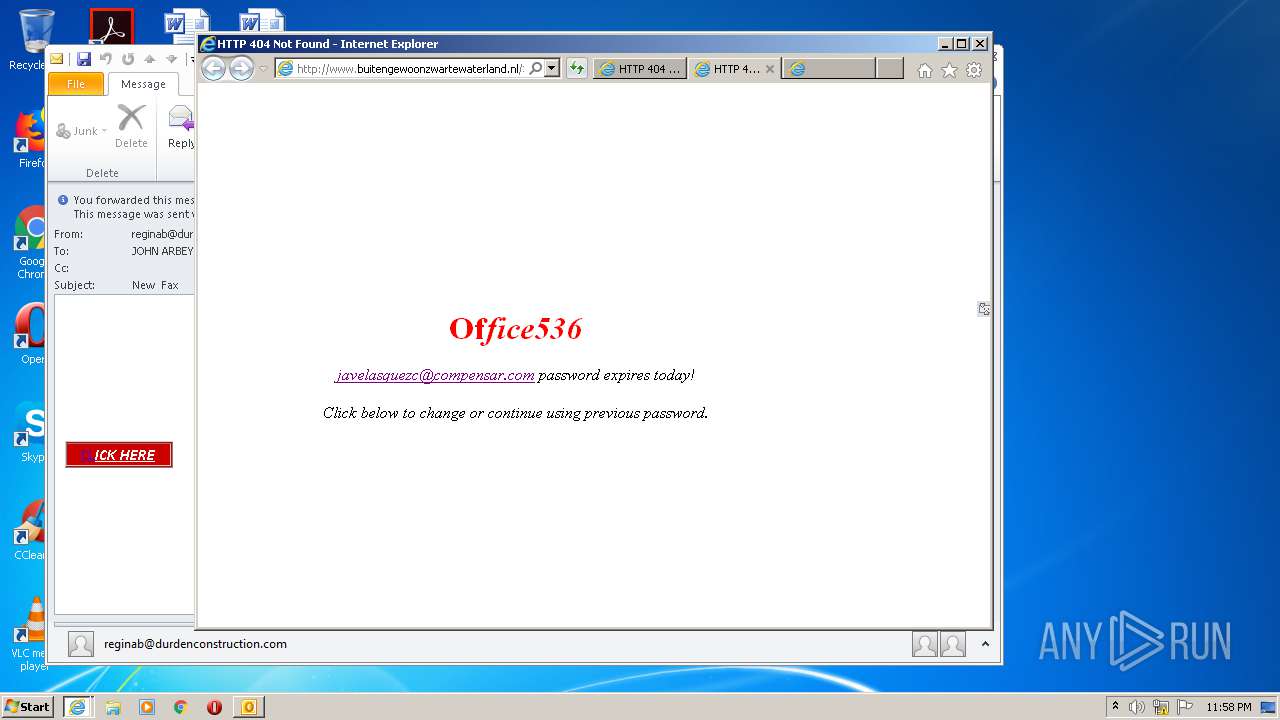
3716 | iexplore.exe | GET | 301 | 185.104.29.4:80 | http://buitengewoonzwartewaterland.nl/3535 | NL | — | — | suspicious |
3860 | iexplore.exe | GET | 301 | 185.104.29.4:80 | http://buitengewoonzwartewaterland.nl/3535 | NL | — | — | suspicious |
1788 | iexplore.exe | GET | 301 | 185.104.29.4:80 | http://buitengewoonzwartewaterland.nl/3535 | NL | — | — | suspicious |
3716 | iexplore.exe | GET | 404 | 185.104.29.4:80 | http://www.buitengewoonzwartewaterland.nl/3535 | NL | compressed | 363 b | malicious |
1788 | iexplore.exe | GET | 404 | 185.104.29.4:80 | http://www.buitengewoonzwartewaterland.nl/3535 | NL | compressed | 363 b | malicious |
3876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3860 | iexplore.exe | GET | 404 | 185.104.29.4:80 | http://www.buitengewoonzwartewaterland.nl/3535 | NL | compressed | 363 b | malicious |
3716 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=%2Fr%2F%3Fid%3Dh42f5194e,42e87e9c,44610685%26p1%3Dbuitengewoonzwartewaterland.nl%2F3535%23javelasquezc%40compensar.com&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 246 b | whitelisted |
3876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1772 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3716 | iexplore.exe | 99.86.7.90:80 | t.mail.sony-europe.com | AT&T Services, Inc. | US | unknown |
3716 | iexplore.exe | 185.104.29.4:80 | buitengewoonzwartewaterland.nl | Stichting DIGI NL | NL | malicious |
3876 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3876 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3716 | iexplore.exe | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
3860 | iexplore.exe | 99.86.7.125:80 | t.mail.sony-europe.com | AT&T Services, Inc. | US | malicious |
3860 | iexplore.exe | 185.104.29.4:80 | buitengewoonzwartewaterland.nl | Stichting DIGI NL | NL | malicious |
3876 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1788 | iexplore.exe | 99.86.7.125:80 | t.mail.sony-europe.com | AT&T Services, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
t.mail.sony-europe.com |
| suspicious |
buitengewoonzwartewaterland.nl |
| suspicious |
www.buitengewoonzwartewaterland.nl |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |