| File name: | technical prooft.docx |
| Full analysis: | https://app.any.run/tasks/794ccb1f-1400-464b-91db-10eadd83e29d |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2022, 18:53:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 38E96590FDD9BA00EB4B4FB1575E05D4 |
| SHA1: | 0B3E77357004B05502DD5497C251F6085947A110 |
| SHA256: | 7167DF2D3896ADB65EC4E49E8F3868011254ADBBAAB81DDF59ADA59413EB5AC0 |
| SSDEEP: | 1536:YKGcgSbucgSbOcgSb1HYz6rRrKs4cv132DVQ0q:YhcxScxqcxpHYz6rRrWcv13Yrq |
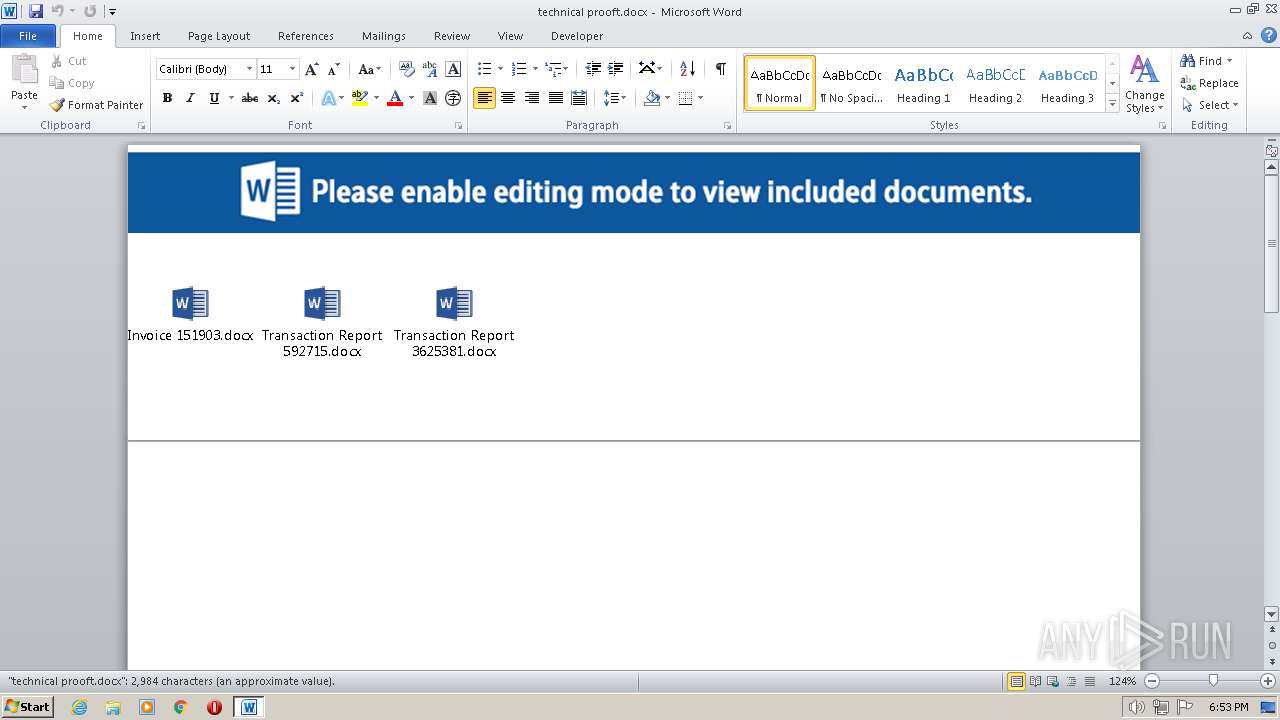
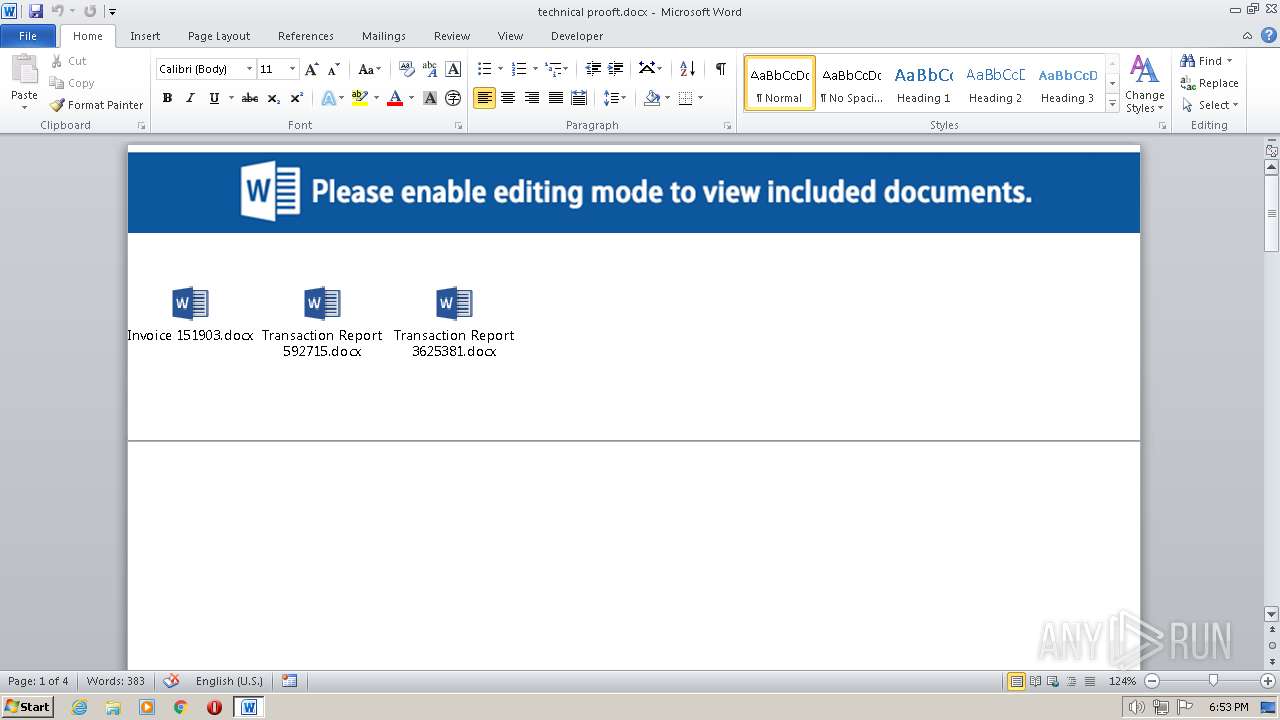
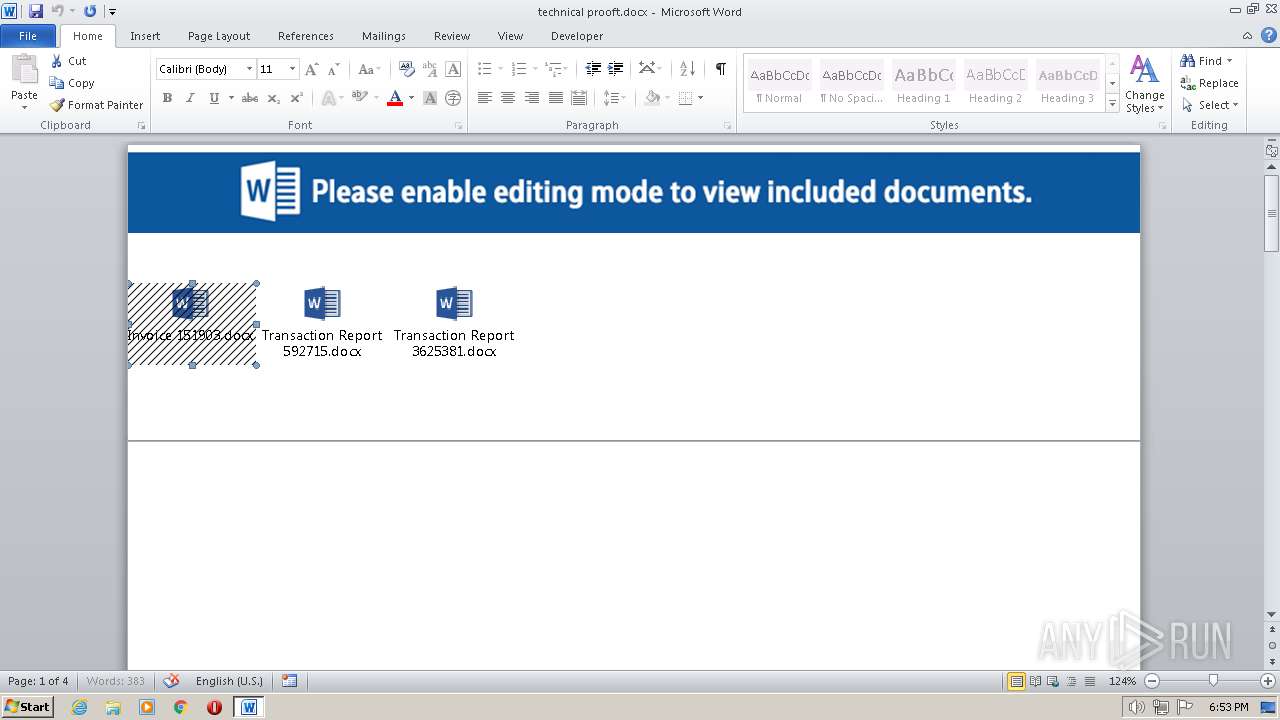
MALICIOUS
Unusual connection from system programs
- WScript.exe (PID: 2560)
SUSPICIOUS
Detected use of alternative data streams (AltDS)
- WINWORD.EXE (PID: 2884)
INFO
Checks proxy server information
- WScript.exe (PID: 2560)
- WScript.exe (PID: 3384)
- WScript.exe (PID: 1752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
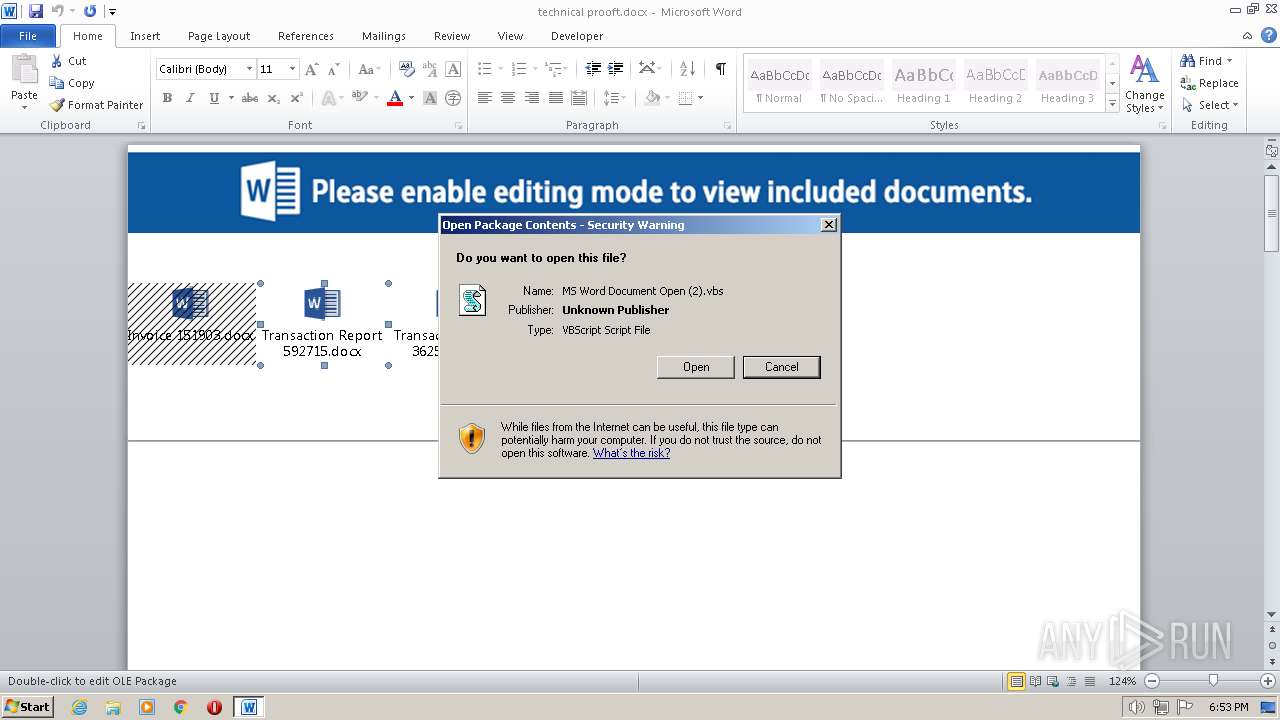
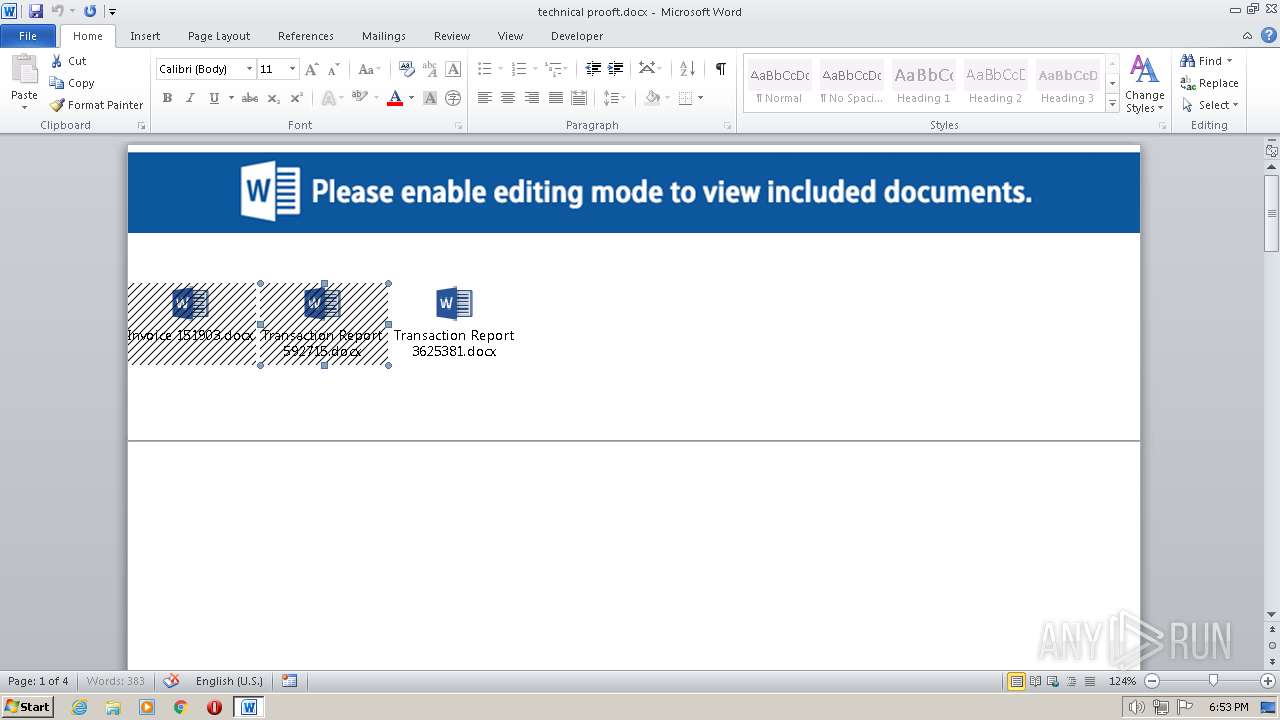
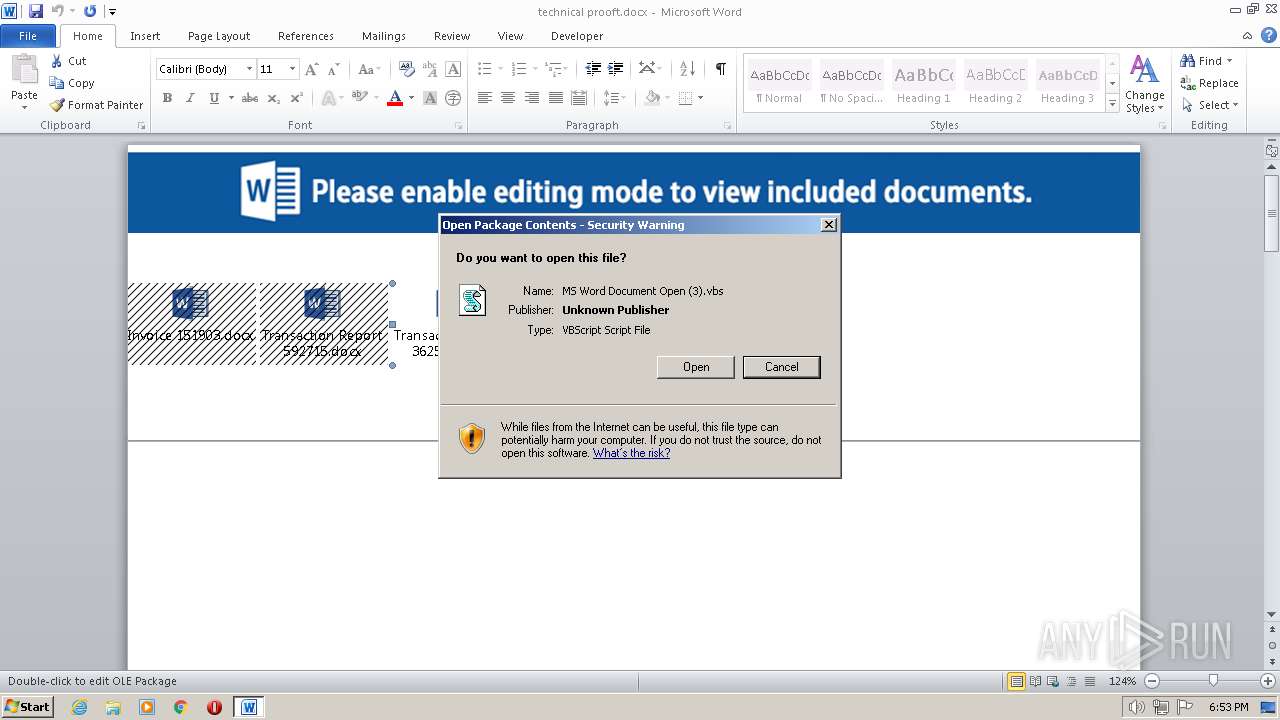
| 1752 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\MS Word Document Open (3).vbs" | C:\Windows\System32\WScript.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2560 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\MS Word Document Open (2).vbs" | C:\Windows\System32\WScript.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2884 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\technical prooft.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
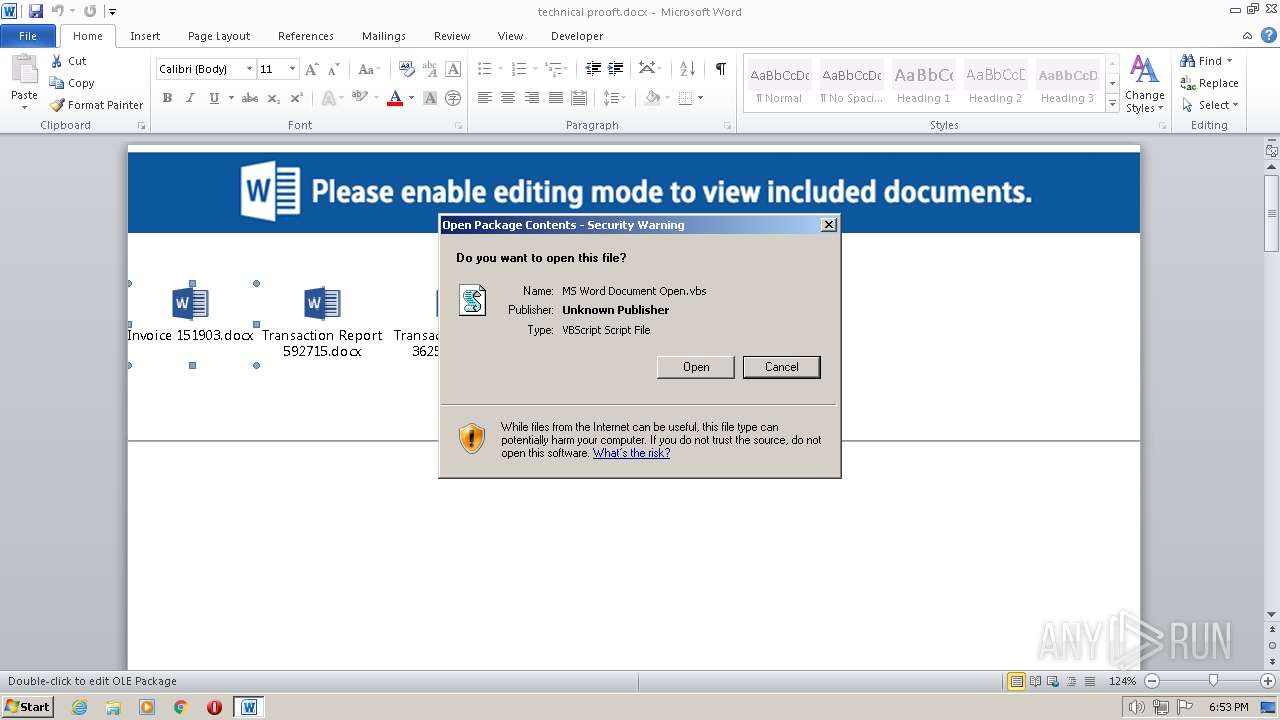
| 3384 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\MS Word Document Open.vbs" | C:\Windows\System32\WScript.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
5 130
Read events
4 271
Write events
699
Delete events
160
Modification events
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 'g. |
Value: 27672E00440B0000010000000000000000000000 | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
7
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF727.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$chnical prooft.docx | pgc | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CB3385EA.emf | emf | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E239CCD6.emf | emf | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FA6CE588.emf | emf | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\MS Word Document Open.vbs | text | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\MS Word Document Open (2).vbs | text | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\MS Word Document Open (3).vbs | text | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryEN0409.lex | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2560 | WScript.exe | GET | — | 185.195.25.79:80 | http://185.195.25.79/5324.csv | RU | — | — | unknown |
3384 | WScript.exe | GET | — | 185.195.25.79:80 | http://185.195.25.79/5324.csv | RU | — | — | unknown |
3384 | WScript.exe | GET | 302 | 213.186.33.5:80 | http://coloctionneur.fr/license.csv | FR | html | 138 b | malicious |
1752 | WScript.exe | GET | — | 185.195.25.79:80 | http://185.195.25.79/5324.csv | RU | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.195.25.79:80 | — | Network Management Ltd | RU | unknown |
2560 | WScript.exe | 185.195.25.79:80 | — | Network Management Ltd | RU | unknown |
3384 | WScript.exe | 185.195.25.79:80 | — | Network Management Ltd | RU | unknown |
3384 | WScript.exe | 213.186.33.5:80 | coloctionneur.fr | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
coloctionneur.fr |
| malicious |
www.coloctionneur.fr |
| malicious |