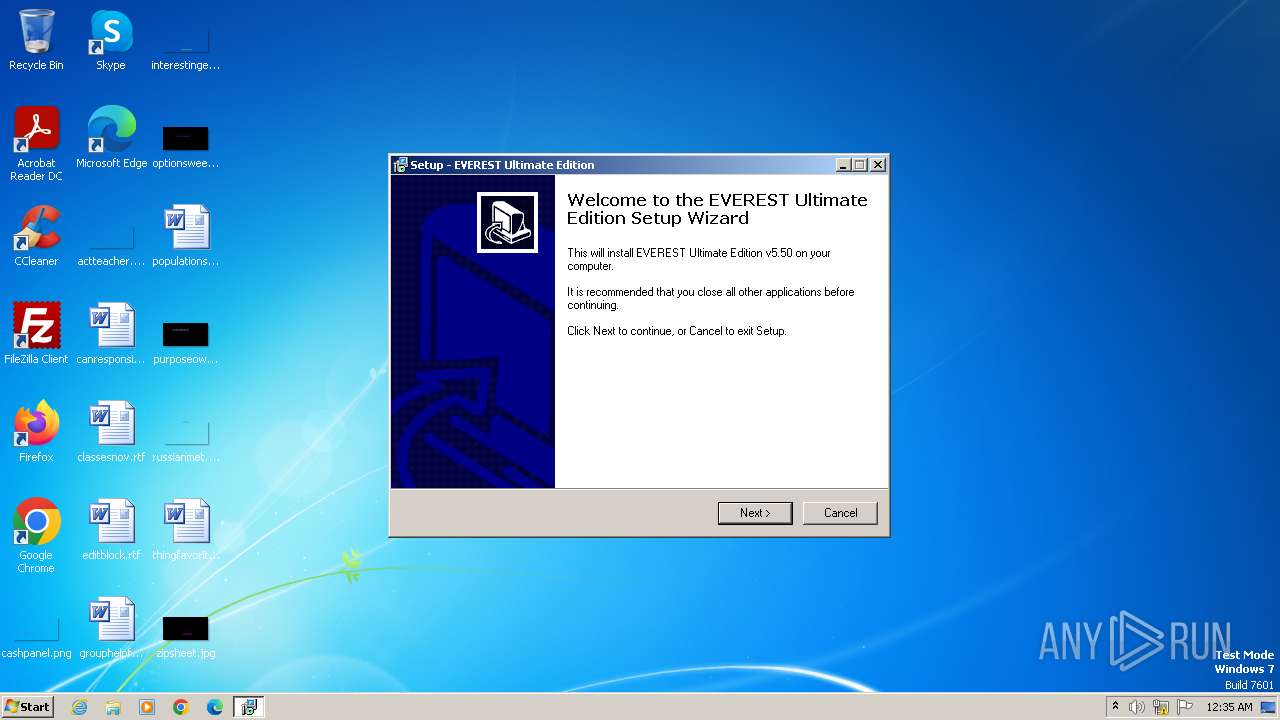
| File name: | everest-ultimate-edition-5-50-2100.exe |
| Full analysis: | https://app.any.run/tasks/9d6fd551-4a1f-40dd-8142-fbf497e3c9ea |
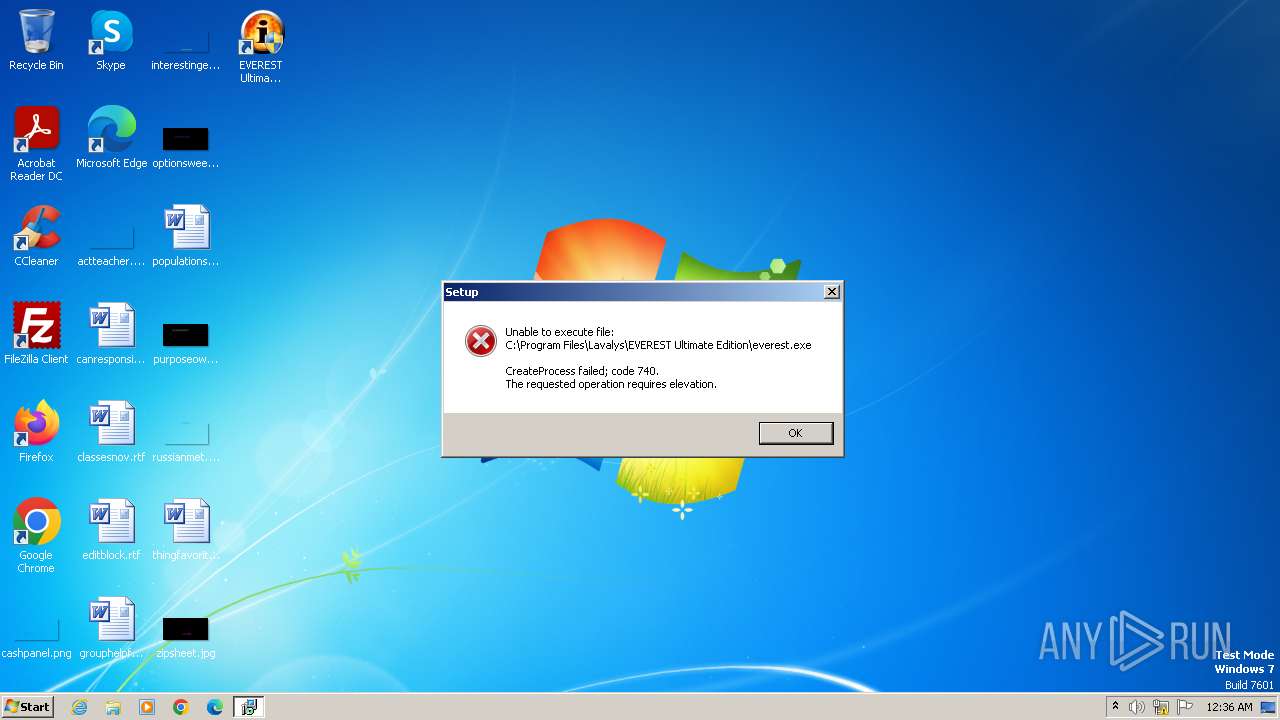
| Verdict: | Malicious activity |
| Analysis date: | June 11, 2024, 23:35:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4774480869AFD209CE8D6F8A69C847D1 |
| SHA1: | CED88468EDEF5748B909A359FC080252750D6957 |
| SHA256: | 71674B870FCBD2CC289DD1F736BAD3DF659A18E91BEF8EB812C2E7DC1EB02692 |
| SSDEEP: | 98304:ERS4+6yaS6pBOb2wkB4JO3eNAl8lxki+yATVa0XBA+/Zcf42bUe6AUaDc4QGQ0qk:5JMbHv9fgGrP8 |
MALICIOUS
Drops the executable file immediately after the start
- everest-ultimate-edition-5-50-2100.exe (PID: 3984)
- everest-ultimate-edition-5-50-2100.tmp (PID: 1036)
- everest-ultimate-edition-5-50-2100.exe (PID: 820)
SUSPICIOUS
Executable content was dropped or overwritten
- everest-ultimate-edition-5-50-2100.exe (PID: 3984)
- everest-ultimate-edition-5-50-2100.tmp (PID: 1036)
- everest-ultimate-edition-5-50-2100.exe (PID: 820)
Reads the Windows owner or organization settings
- everest-ultimate-edition-5-50-2100.tmp (PID: 1036)
Process drops legitimate windows executable
- everest-ultimate-edition-5-50-2100.tmp (PID: 1036)
Reads the Internet Settings
- everest-ultimate-edition-5-50-2100.tmp (PID: 4000)
- hh.exe (PID: 1432)
Reads security settings of Internet Explorer
- everest-ultimate-edition-5-50-2100.tmp (PID: 4000)
Reads Internet Explorer settings
- hh.exe (PID: 1432)
Reads Microsoft Outlook installation path
- hh.exe (PID: 1432)
INFO
Checks supported languages
- everest-ultimate-edition-5-50-2100.exe (PID: 3984)
- everest-ultimate-edition-5-50-2100.tmp (PID: 1036)
- everest-ultimate-edition-5-50-2100.exe (PID: 820)
- everest-ultimate-edition-5-50-2100.tmp (PID: 4000)
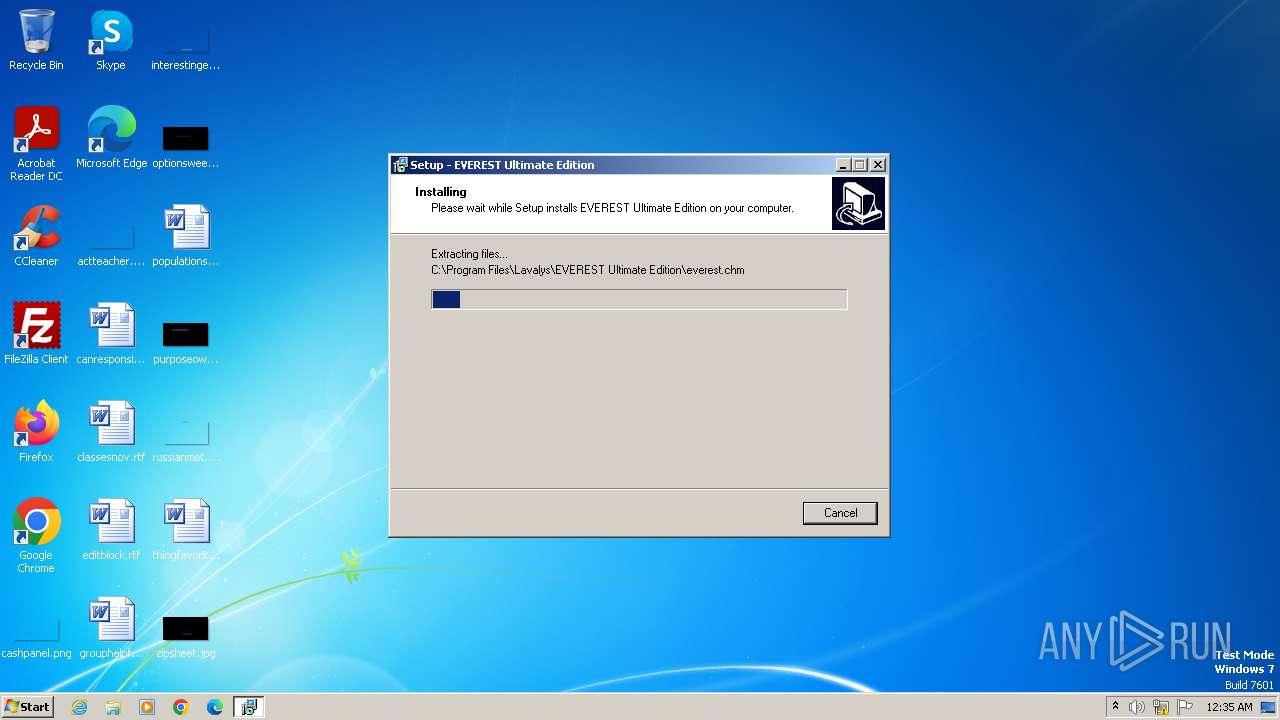
Create files in a temporary directory
- everest-ultimate-edition-5-50-2100.exe (PID: 3984)
- hh.exe (PID: 1432)
- everest-ultimate-edition-5-50-2100.tmp (PID: 1036)
- everest-ultimate-edition-5-50-2100.exe (PID: 820)
Creates files in the program directory
- everest-ultimate-edition-5-50-2100.tmp (PID: 1036)
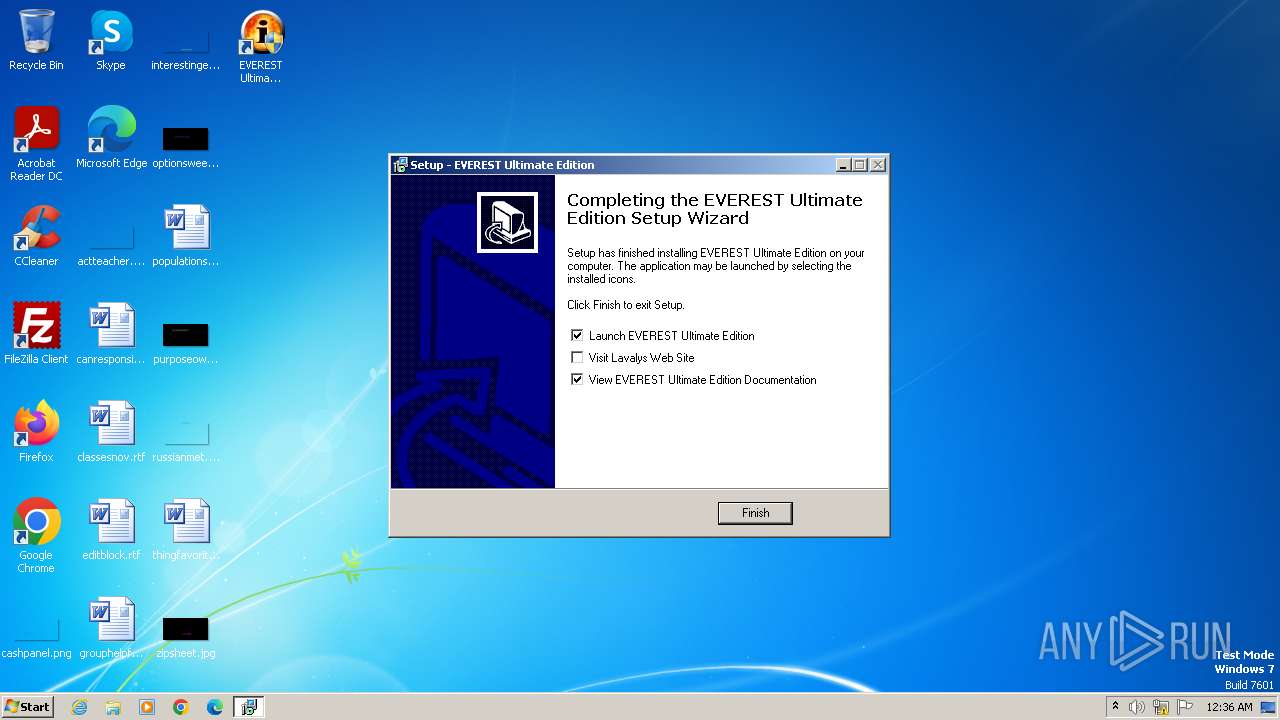
Creates a software uninstall entry
- everest-ultimate-edition-5-50-2100.tmp (PID: 1036)
Reads the computer name
- everest-ultimate-edition-5-50-2100.tmp (PID: 1036)
- everest-ultimate-edition-5-50-2100.tmp (PID: 4000)
Reads the machine GUID from the registry
- hh.exe (PID: 1432)
Reads security settings of Internet Explorer
- hh.exe (PID: 1432)
Checks proxy server information
- hh.exe (PID: 1432)
Creates files or folders in the user directory
- hh.exe (PID: 1432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9b24 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.50.2100.0 |
| ProductVersionNumber: | 5.50.2100.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
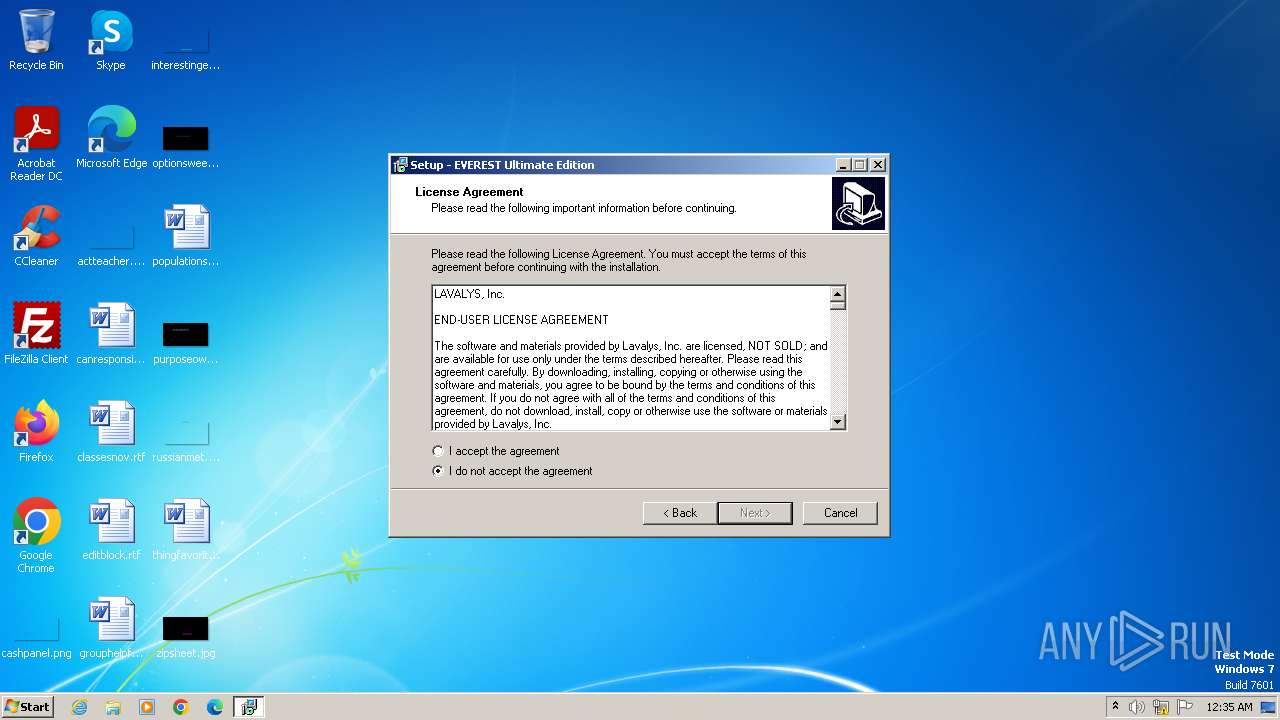
| CompanyName: | Lavalys, Inc. |
| FileDescription: | EVEREST Ultimate Edition |
| FileVersion: | 5.50.2100.0 |
| LegalCopyright: | Copyright (c) 2003-2010 Lavalys, Inc. |
| ProductName: | EVEREST Ultimate Edition |
| ProductVersion: | 5.50.2100.0 |
Total processes
42
Monitored processes
6
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files\Lavalys\EVEREST Ultimate Edition\everest.exe" | C:\Program Files\Lavalys\EVEREST Ultimate Edition\everest.exe | — | everest-ultimate-edition-5-50-2100.tmp | |||||||||||
User: admin Company: Lavalys, Inc. Integrity Level: MEDIUM Description: EVEREST Ultimate Edition Exit code: 3221226540 Version: 5.50.2100 Modules
| |||||||||||||||
| 820 | "C:\Users\admin\AppData\Local\Temp\everest-ultimate-edition-5-50-2100.exe" /SPAWNWND=$20134 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\everest-ultimate-edition-5-50-2100.exe | everest-ultimate-edition-5-50-2100.tmp | ||||||||||||
User: admin Company: Lavalys, Inc. Integrity Level: HIGH Description: EVEREST Ultimate Edition Exit code: 0 Version: 5.50.2100.0 Modules
| |||||||||||||||
| 1036 | "C:\Users\admin\AppData\Local\Temp\is-DPJGV.tmp\everest-ultimate-edition-5-50-2100.tmp" /SL5="$40130,9897390,54272,C:\Users\admin\AppData\Local\Temp\everest-ultimate-edition-5-50-2100.exe" /SPAWNWND=$20134 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\is-DPJGV.tmp\everest-ultimate-edition-5-50-2100.tmp | everest-ultimate-edition-5-50-2100.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.50.0.0 Modules
| |||||||||||||||
| 1432 | "C:\Windows\hh.exe" C:\Program Files\Lavalys\EVEREST Ultimate Edition\everest.chm | C:\Windows\hh.exe | — | everest-ultimate-edition-5-50-2100.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3984 | "C:\Users\admin\AppData\Local\Temp\everest-ultimate-edition-5-50-2100.exe" | C:\Users\admin\AppData\Local\Temp\everest-ultimate-edition-5-50-2100.exe | explorer.exe | ||||||||||||
User: admin Company: Lavalys, Inc. Integrity Level: MEDIUM Description: EVEREST Ultimate Edition Exit code: 0 Version: 5.50.2100.0 Modules
| |||||||||||||||
| 4000 | "C:\Users\admin\AppData\Local\Temp\is-K61IC.tmp\everest-ultimate-edition-5-50-2100.tmp" /SL5="$20138,9897390,54272,C:\Users\admin\AppData\Local\Temp\everest-ultimate-edition-5-50-2100.exe" | C:\Users\admin\AppData\Local\Temp\is-K61IC.tmp\everest-ultimate-edition-5-50-2100.tmp | — | everest-ultimate-edition-5-50-2100.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.50.0.0 Modules
| |||||||||||||||
Total events
6 776
Read events
6 737
Write events
39
Delete events
0
Modification events
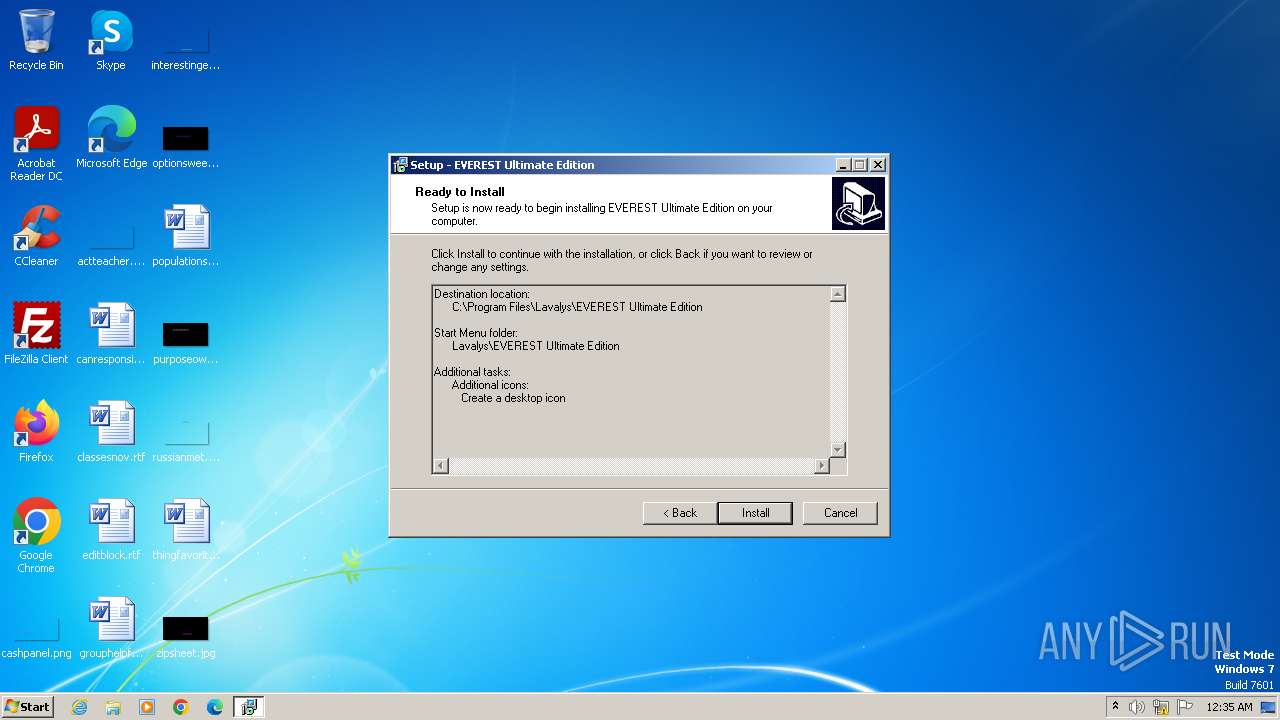
| (PID) Process: | (1036) everest-ultimate-edition-5-50-2100.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EVEREST Ultimate Edition_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.3.5 (a) | |||
| (PID) Process: | (1036) everest-ultimate-edition-5-50-2100.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EVEREST Ultimate Edition_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
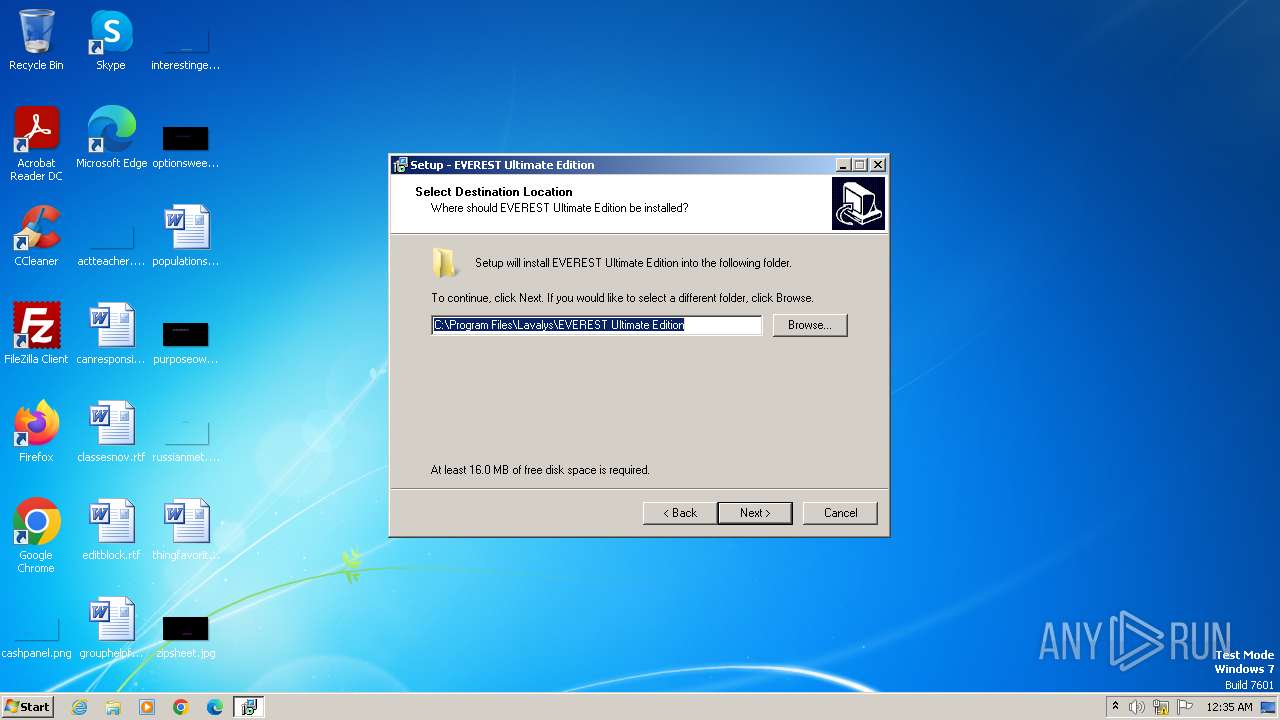
Value: C:\Program Files\Lavalys\EVEREST Ultimate Edition | |||
| (PID) Process: | (1036) everest-ultimate-edition-5-50-2100.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EVEREST Ultimate Edition_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Lavalys\EVEREST Ultimate Edition\ | |||
| (PID) Process: | (1036) everest-ultimate-edition-5-50-2100.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EVEREST Ultimate Edition_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Lavalys\EVEREST Ultimate Edition | |||
| (PID) Process: | (1036) everest-ultimate-edition-5-50-2100.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EVEREST Ultimate Edition_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (1036) everest-ultimate-edition-5-50-2100.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EVEREST Ultimate Edition_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon | |||
| (PID) Process: | (1036) everest-ultimate-edition-5-50-2100.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EVEREST Ultimate Edition_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: quicklaunchicon | |||
| (PID) Process: | (1036) everest-ultimate-edition-5-50-2100.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EVEREST Ultimate Edition_is1 |
| Operation: | write | Name: | DisplayName |
Value: EVEREST Ultimate Edition v5.50 | |||
| (PID) Process: | (1036) everest-ultimate-edition-5-50-2100.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EVEREST Ultimate Edition_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Lavalys\EVEREST Ultimate Edition\unins000.exe" | |||
| (PID) Process: | (1036) everest-ultimate-edition-5-50-2100.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EVEREST Ultimate Edition_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\Lavalys\EVEREST Ultimate Edition\unins000.exe" /SILENT | |||
Executable files
38
Suspicious files
12
Text files
82
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3984 | everest-ultimate-edition-5-50-2100.exe | C:\Users\admin\AppData\Local\Temp\is-K61IC.tmp\everest-ultimate-edition-5-50-2100.tmp | executable | |
MD5:ED69E64731547EBA52476A2D2A2F7882 | SHA256:427FA988A8A8C63393693FFEB61DDEC195F000220EE55FD5112EC91682E933B0 | |||
| 1036 | everest-ultimate-edition-5-50-2100.tmp | C:\Program Files\Lavalys\EVEREST Ultimate Edition\is-PROPC.tmp | binary | |
MD5:658501A07C9D4F4F5DAC5B5112E96D72 | SHA256:6A94EEE0F05BA3D6F4ECCD4425F33F45C84A5CA33F8FE4C9FC9E531B92BBA6A7 | |||
| 1036 | everest-ultimate-edition-5-50-2100.tmp | C:\Program Files\Lavalys\EVEREST Ultimate Edition\unins000.exe | executable | |
MD5:5CE65EF37592FE8B39B2B9928093C48F | SHA256:F183AFA75050481B3A9DC87DBF68343A9386778E558528D97F0601013EED6534 | |||
| 1036 | everest-ultimate-edition-5-50-2100.tmp | C:\Users\admin\AppData\Local\Temp\is-S3VKI.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:0EE914C6F0BB93996C75941E1AD629C6 | SHA256:4DC09BAC0613590F1FAC8771D18AF5BE25A1E1CB8FDBF4031AA364F3057E74A2 | |||
| 1036 | everest-ultimate-edition-5-50-2100.tmp | C:\Program Files\Lavalys\EVEREST Ultimate Edition\everest.chm | binary | |
MD5:658501A07C9D4F4F5DAC5B5112E96D72 | SHA256:6A94EEE0F05BA3D6F4ECCD4425F33F45C84A5CA33F8FE4C9FC9E531B92BBA6A7 | |||
| 1036 | everest-ultimate-edition-5-50-2100.tmp | C:\Program Files\Lavalys\EVEREST Ultimate Edition\is-PJGKC.tmp | executable | |
MD5:5A272D47FBE16EA49C68916380FD3C62 | SHA256:86354F408627580C5EC8B6CCB5F8DD6802C7DB76DA5D3223B108B90AF816A1C0 | |||
| 1036 | everest-ultimate-edition-5-50-2100.tmp | C:\Program Files\Lavalys\EVEREST Ultimate Edition\is-SG8BG.tmp | executable | |
MD5:5CE65EF37592FE8B39B2B9928093C48F | SHA256:F183AFA75050481B3A9DC87DBF68343A9386778E558528D97F0601013EED6534 | |||
| 1036 | everest-ultimate-edition-5-50-2100.tmp | C:\Users\admin\AppData\Local\Temp\is-S3VKI.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 820 | everest-ultimate-edition-5-50-2100.exe | C:\Users\admin\AppData\Local\Temp\is-DPJGV.tmp\everest-ultimate-edition-5-50-2100.tmp | executable | |
MD5:ED69E64731547EBA52476A2D2A2F7882 | SHA256:427FA988A8A8C63393693FFEB61DDEC195F000220EE55FD5112EC91682E933B0 | |||
| 1036 | everest-ultimate-edition-5-50-2100.tmp | C:\Program Files\Lavalys\EVEREST Ultimate Edition\is-9VB70.tmp | binary | |
MD5:8A324FFA99EA1C31F56A436903048E27 | SHA256:3D7AF9FEE64AD7D363E2209A4E4E3F14035929CF0DA7E9B8526E7B59BFEA1668 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |