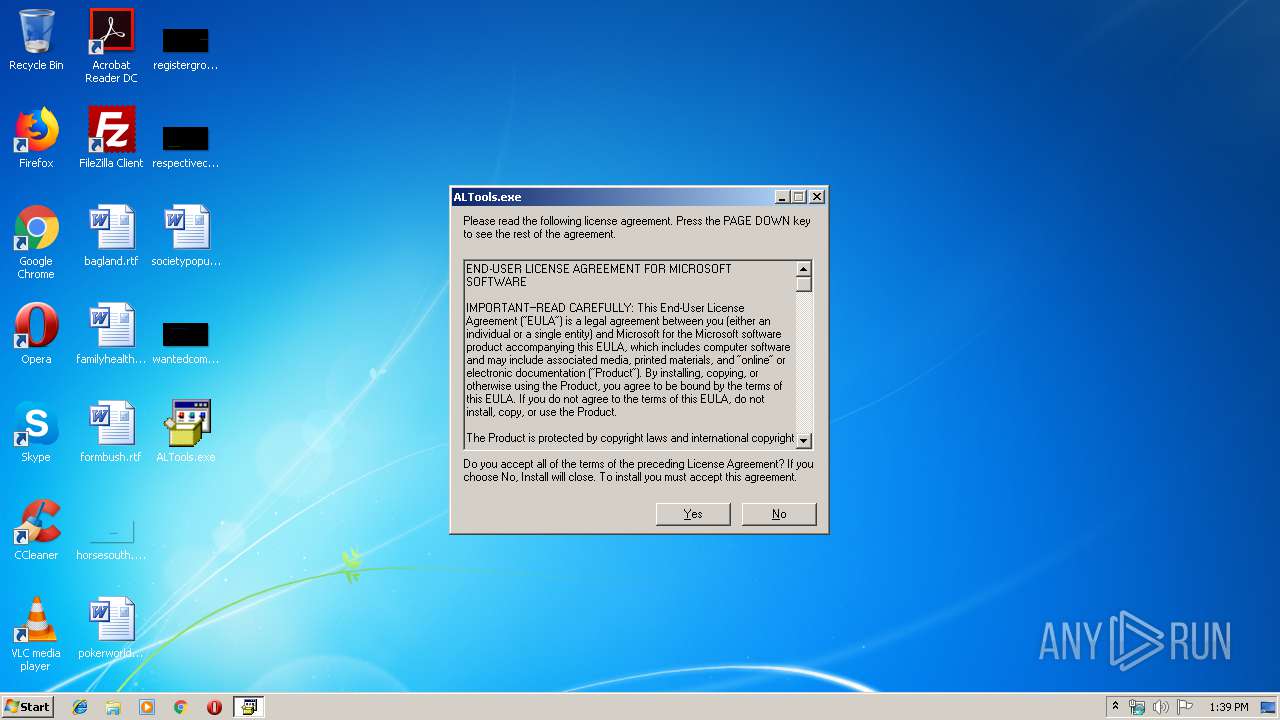
| File name: | ALTools.exe |
| Full analysis: | https://app.any.run/tasks/4f179555-6815-480c-ae5b-265ffd410dc3 |
| Verdict: | Malicious activity |
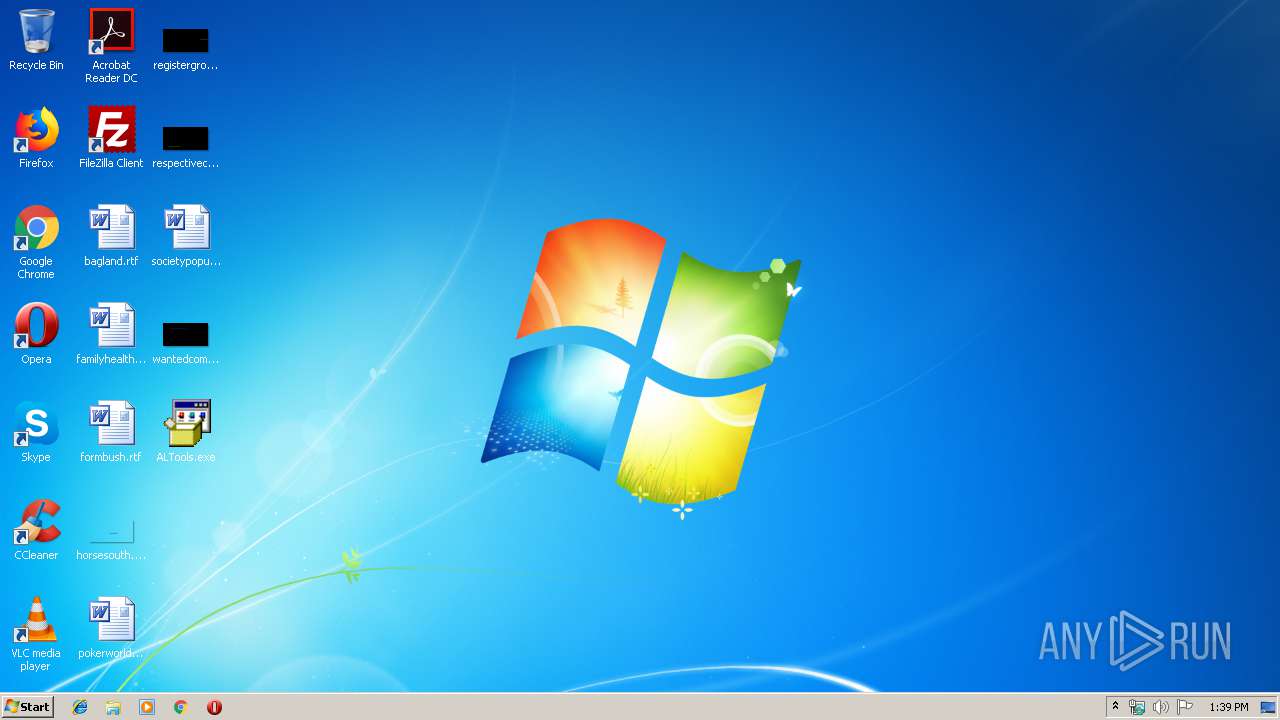
| Analysis date: | May 17, 2019, 12:39:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, MS CAB-Installer self-extracting archive |
| MD5: | 906279704A47DC539A24BE7CD0B91D6B |
| SHA1: | B628039DBDF4A9051D3112CBB632FFD13D5762BA |
| SHA256: | 716718C095EF5AD5724BC8344CBCCC176E14FD773DE89C517F6C8514CD3AE260 |
| SSDEEP: | 24576:nLpbSucGILJ4PVTxFMY9FYFKm5nhd5sG1SvQZ53bm:nLpOucGILJ4PLbiFHsGkQZ53q |
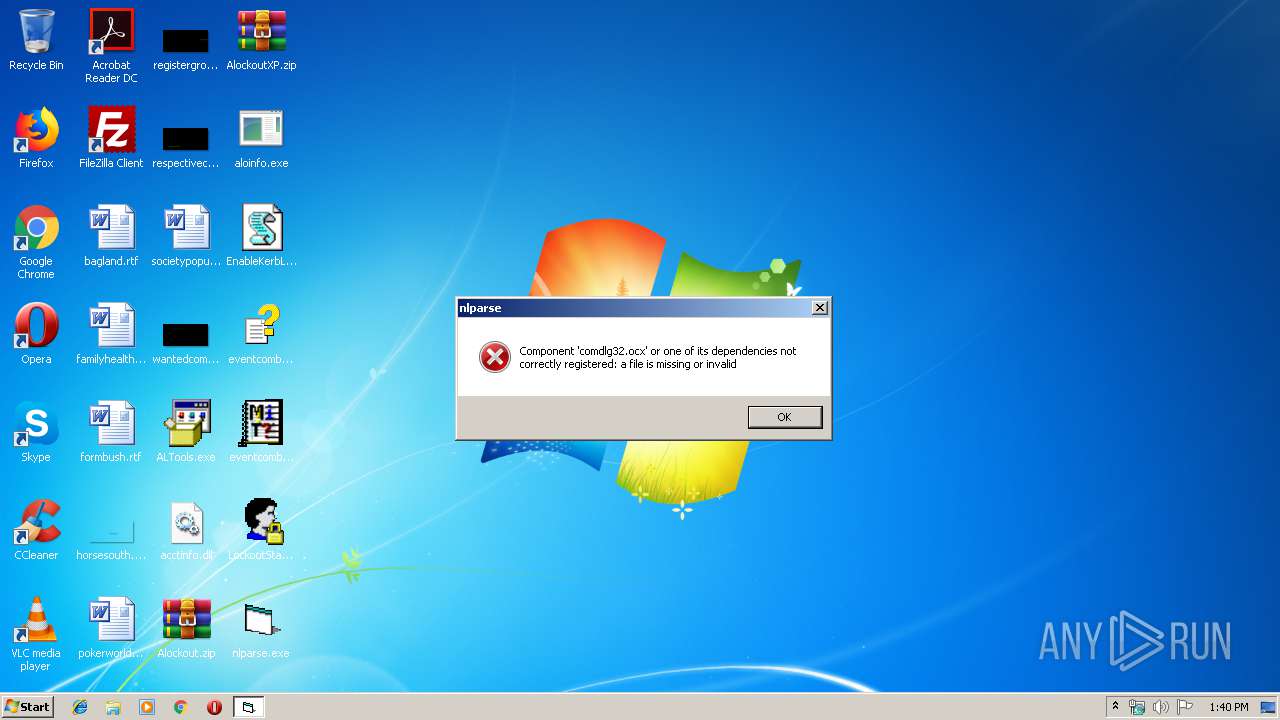
MALICIOUS
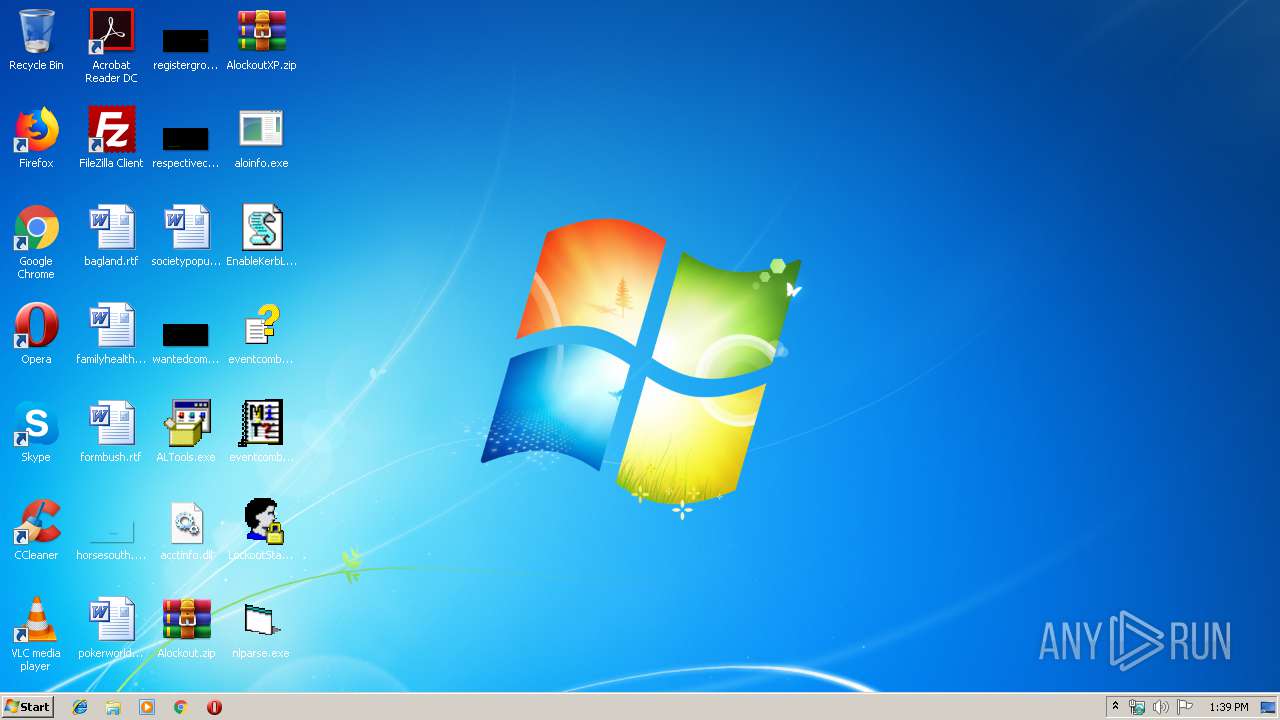
Application was dropped or rewritten from another process
- nlparse.exe (PID: 3432)
- LockoutStatus.exe (PID: 2440)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1256)
SUSPICIOUS
Executable content was dropped or overwritten
- ALTools.exe (PID: 3112)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Microsoft Update - Self Extracting Cabinet (47.3) |
|---|---|---|
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (42.3) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (4.3) |
| .exe | | | Win64 Executable (generic) (3.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2002:08:29 10:25:42+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7 |
| CodeSize: | 34816 |
| InitializedDataSize: | 826880 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5ae4 |
| OSVersion: | 5.1 |
| ImageVersion: | 5.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.2800.1106 |
| ProductVersionNumber: | 6.0.2800.1106 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 6.00.2800.1106 (xpsp1.020828-1920) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.00.2800.1106 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Aug-2002 08:25:42 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 6.00.2800.1106 (xpsp1.020828-1920) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | WEXTRACT.EXE |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.00.2800.1106 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 29-Aug-2002 08:25:42 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000086E6 | 0x00008800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61846 |
.data | 0x0000A000 | 0x00001BE4 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.18428 |
.rsrc | 0x0000C000 | 0x000CA000 | 0x000C9A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.97604 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.437 | 1064 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 3.53793 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
63 | 2.48958 | 140 | Latin 1 / Western European | English - United States | RT_STRING |
76 | 3.2674 | 1312 | Latin 1 / Western European | English - United States | RT_STRING |
77 | 3.29977 | 1484 | Latin 1 / Western European | English - United States | RT_STRING |
80 | 3.27174 | 1200 | Latin 1 / Western European | English - United States | RT_STRING |
83 | 3.2912 | 1098 | Latin 1 / Western European | English - United States | RT_STRING |
85 | 3.13591 | 974 | Latin 1 / Western European | English - United States | RT_STRING |
2001 | 3.35785 | 716 | Latin 1 / Western European | English - United States | RT_DIALOG |
2002 | 3.34986 | 394 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
Total processes
38
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1256 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
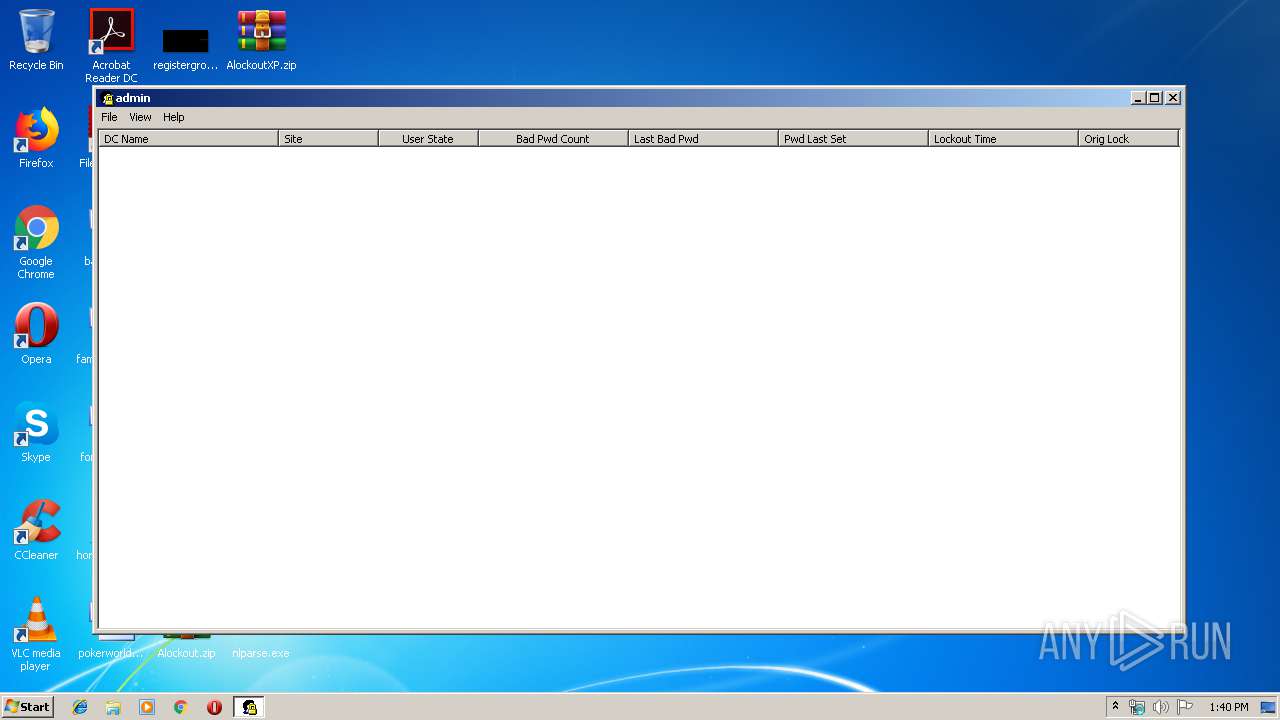
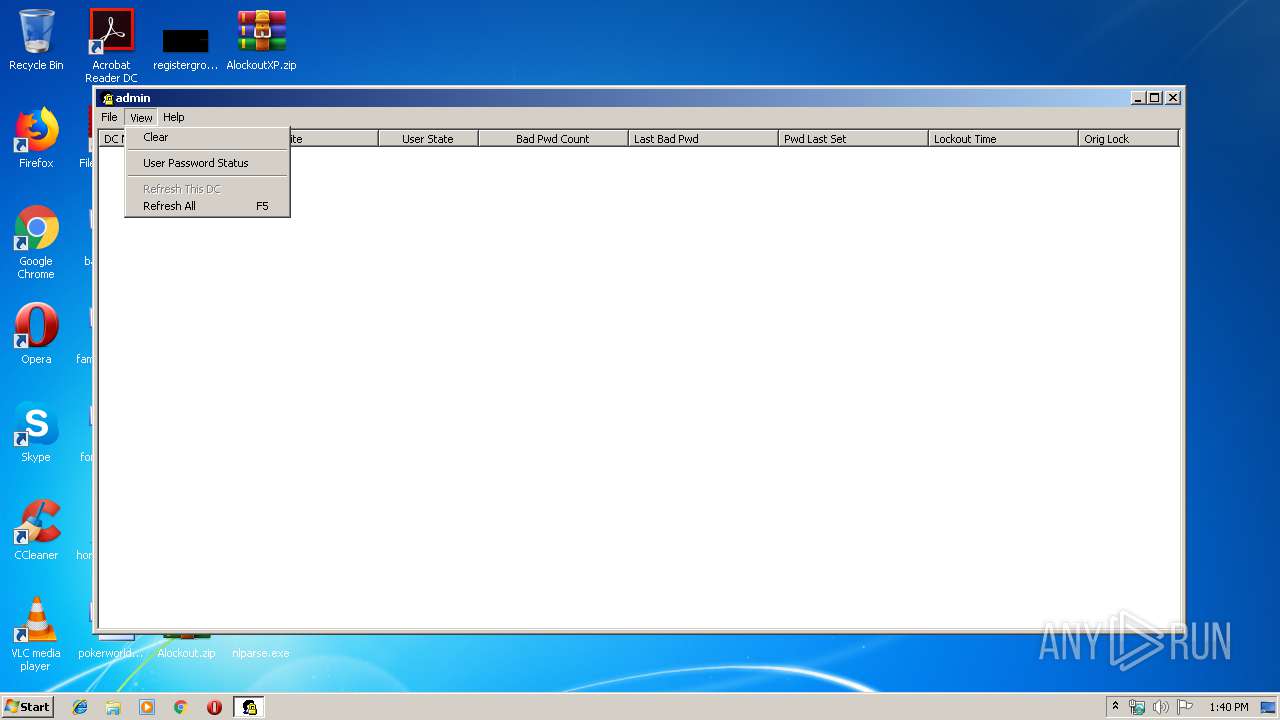
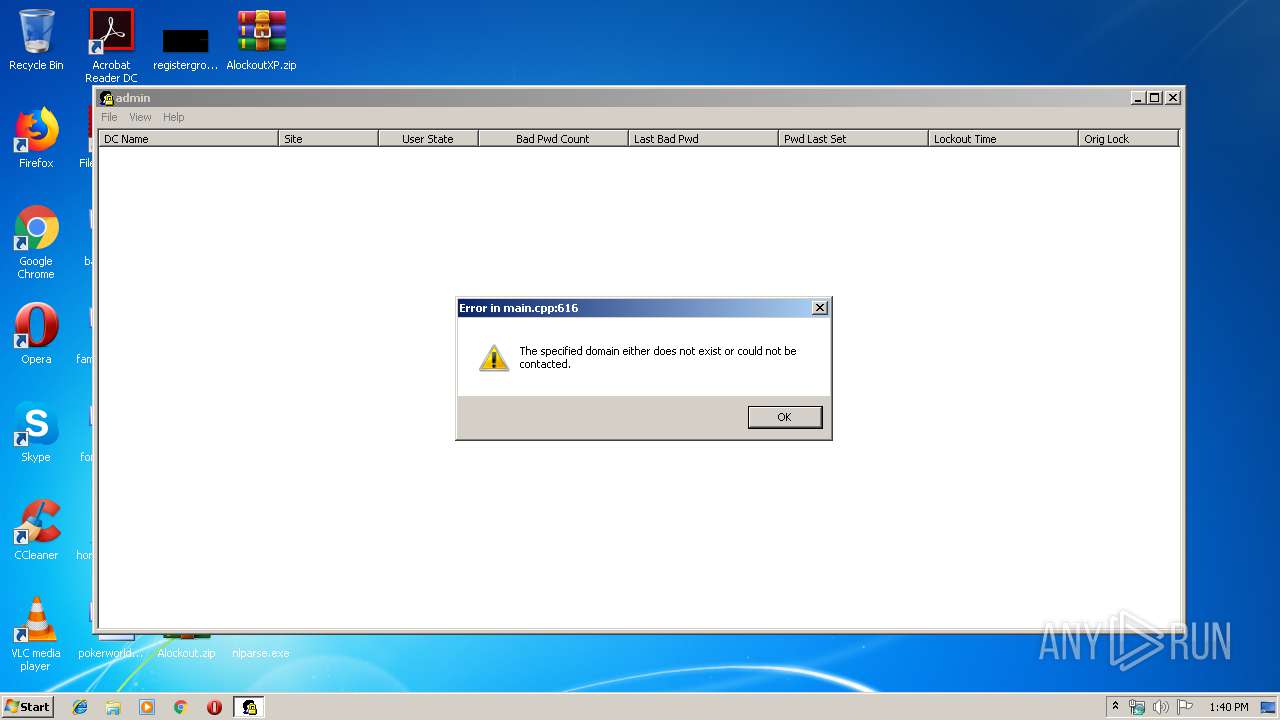
| 2440 | "C:\Users\admin\Desktop\LockoutStatus.exe" | C:\Users\admin\Desktop\LockoutStatus.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Account Lockout Status Exit code: 0 Version: 1, 0, 0, 50 Modules
| |||||||||||||||
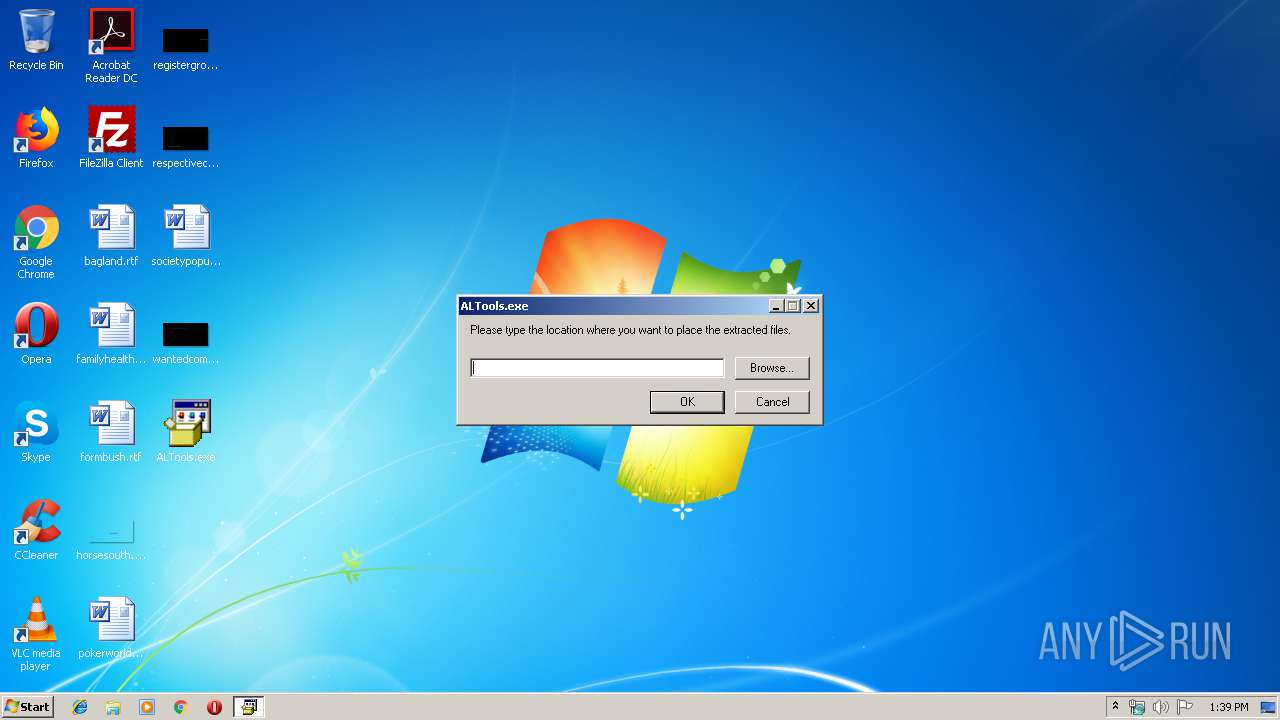
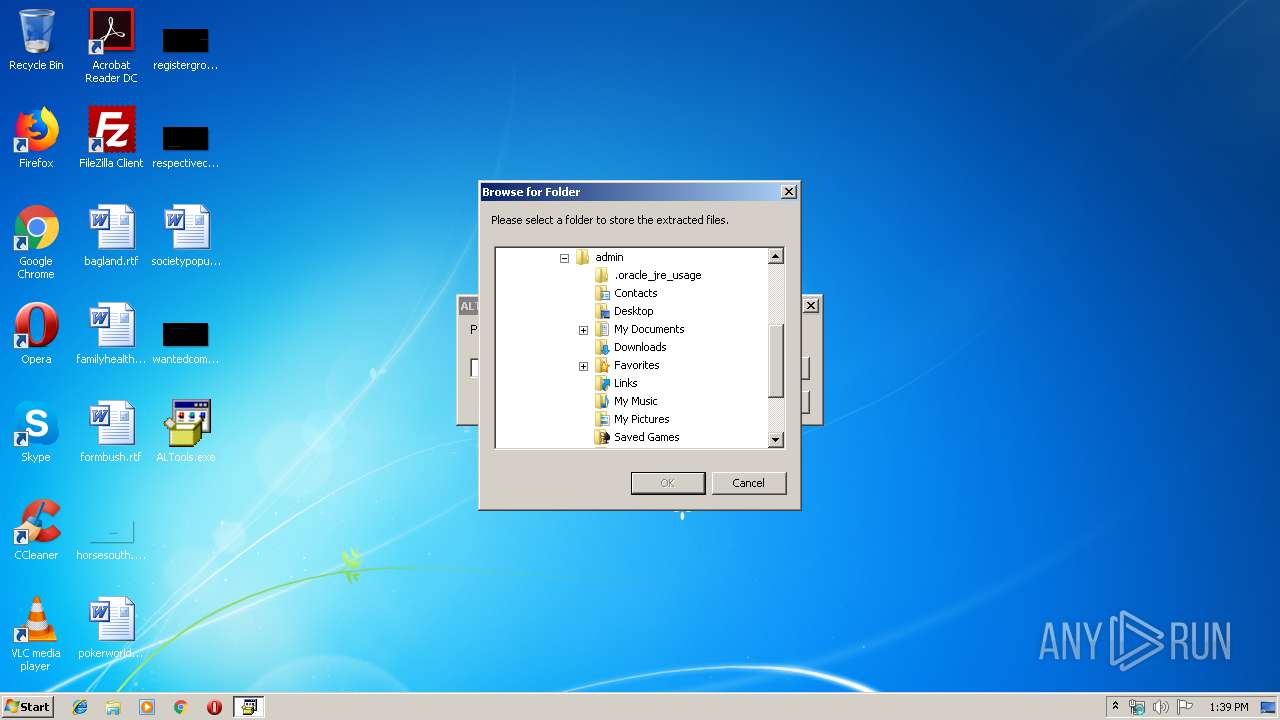
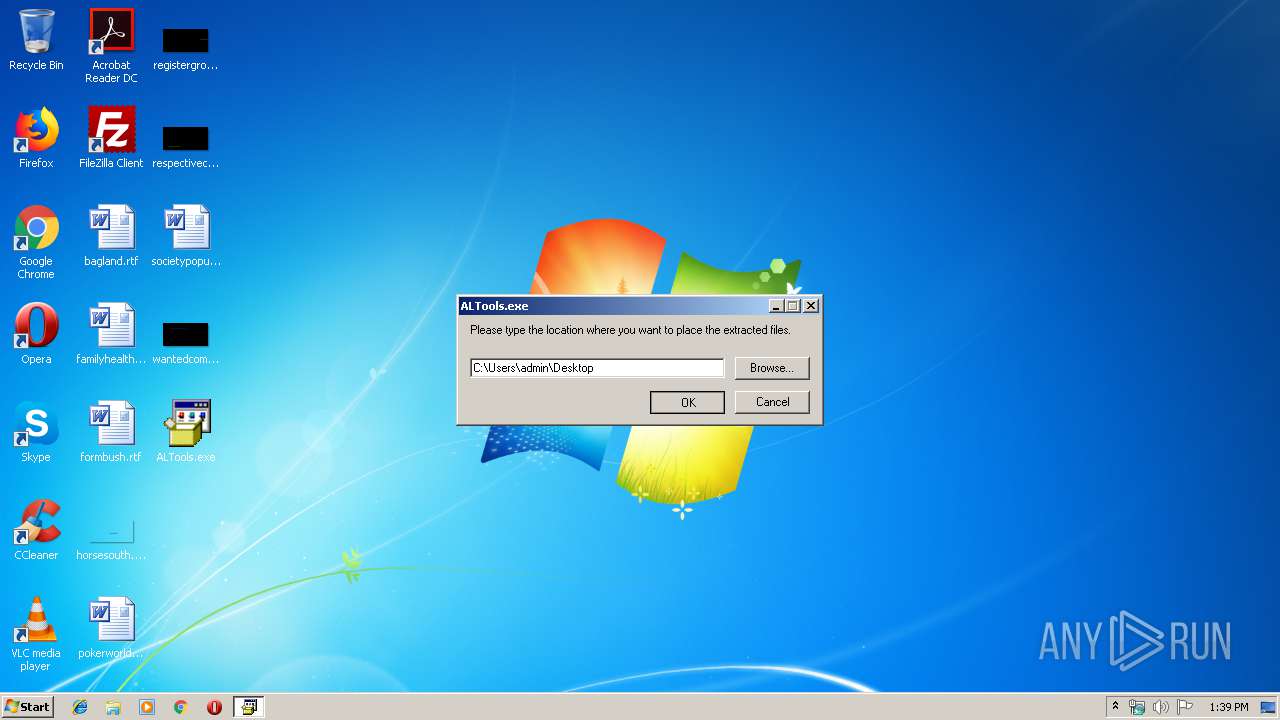
| 3112 | "C:\Users\admin\Desktop\ALTools.exe" | C:\Users\admin\Desktop\ALTools.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 6.00.2800.1106 (xpsp1.020828-1920) Modules
| |||||||||||||||
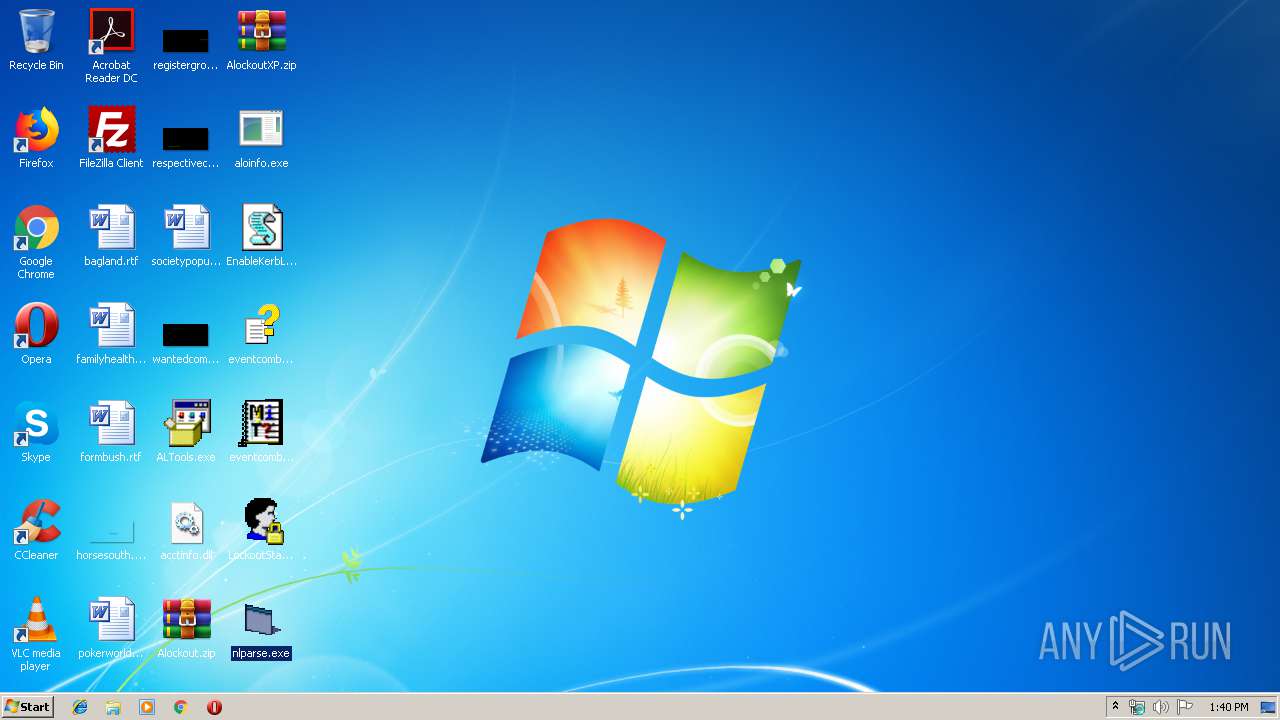
| 3432 | "C:\Users\admin\Desktop\nlparse.exe" | C:\Users\admin\Desktop\nlparse.exe | — | explorer.exe | |||||||||||
User: admin Company: MS Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
116
Read events
104
Write events
12
Delete events
0
Modification events
| (PID) Process: | (3112) ALTools.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1256) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1256) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (1256) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\hhctrl.ocx,-452 |
Value: Compiled HTML Help file | |||
Executable files
5
Suspicious files
2
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3112 | ALTools.exe | C:\Users\admin\Desktop\aloinfo.exe | executable | |
MD5:BAE3B4DE715013DF2C739EFF3FE6010A | SHA256:47ED995E3239B8E11A0FAF6205559368CBA851CCC7F738266F7EAF5E5DF5AB20 | |||
| 3112 | ALTools.exe | C:\Users\admin\Desktop\EnableKerbLog.vbs | text | |
MD5:20ACAAA72F7ECEC8551A93E053870B61 | SHA256:4C2267E10D542A2880954BA816D4DB839C32512698FE28C1B31E89C332A0F504 | |||
| 3112 | ALTools.exe | C:\Users\admin\Desktop\AlockoutXP.zip | compressed | |
MD5:BAC01C1CCA45DBDACD79FBB8DE73C5F7 | SHA256:46F891945AC7B6775499910DDD4B36121B590579D527E0ABF4064BAC84E613AE | |||
| 3112 | ALTools.exe | C:\Users\admin\Desktop\LockoutStatus.exe | executable | |
MD5:449E3183E893EEDCBB72F5C935C31DD0 | SHA256:8A7C3CEE167CFBBF5452A1091F13CDAD3BC412017FCE77C94B7CE1CA309EBA3A | |||
| 3112 | ALTools.exe | C:\Users\admin\Desktop\eventcombmt.chm | chm | |
MD5:869A7E37406A6B6AC1E690900D608074 | SHA256:F362668304F2B48861E1A5A455092D2A27BCF430F44065A97C80DAAE948C22F3 | |||
| 3112 | ALTools.exe | C:\Users\admin\Desktop\Alockout.zip | compressed | |
MD5:BAD044EC32EDC76D13C2B39B959031D9 | SHA256:3A0F1373725F70DFC10418A6521399DA30AB41E902F1BA5A8581B7FEBE5C0BB6 | |||
| 3112 | ALTools.exe | C:\Users\admin\Desktop\acctinfo.dll | executable | |
MD5:204AA9B5259A3BE495A1A0545EBC3CDF | SHA256:7C9C9E525B5156DAC288F7228584F190A3D1A3ADE58F382A2598012894156F7A | |||
| 3112 | ALTools.exe | C:\Users\admin\Desktop\nlparse.exe | executable | |
MD5:FC8F026039FC95BFA2F8D02371C7D537 | SHA256:7C347D64FD583BB71B95CC3E2CC61B488C097A28327EED98597107BEC396E802 | |||
| 3112 | ALTools.exe | C:\Users\admin\Desktop\eventcombMT.exe | executable | |
MD5:B8532EBC109723C7DD0D9857FAD9E9B5 | SHA256:4ABE75B1A2DCE146EDBD3685259F91DD441C041D7277DEC541352751A1D75B90 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
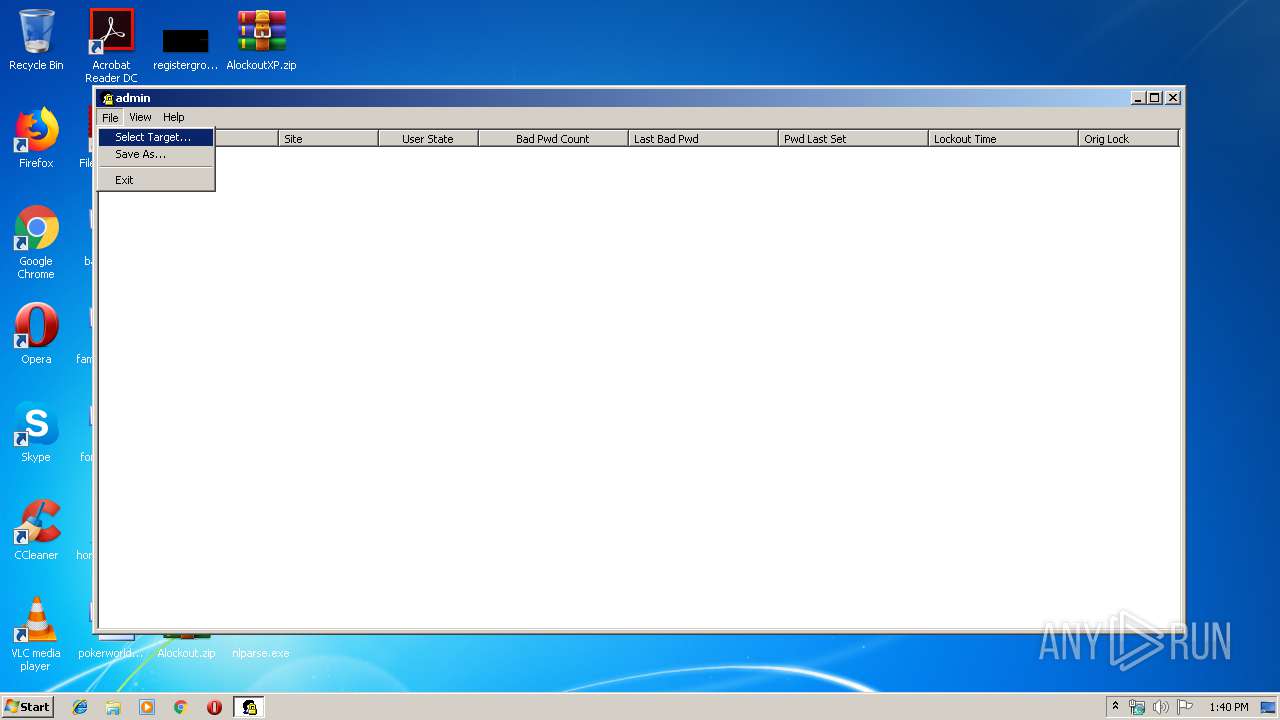
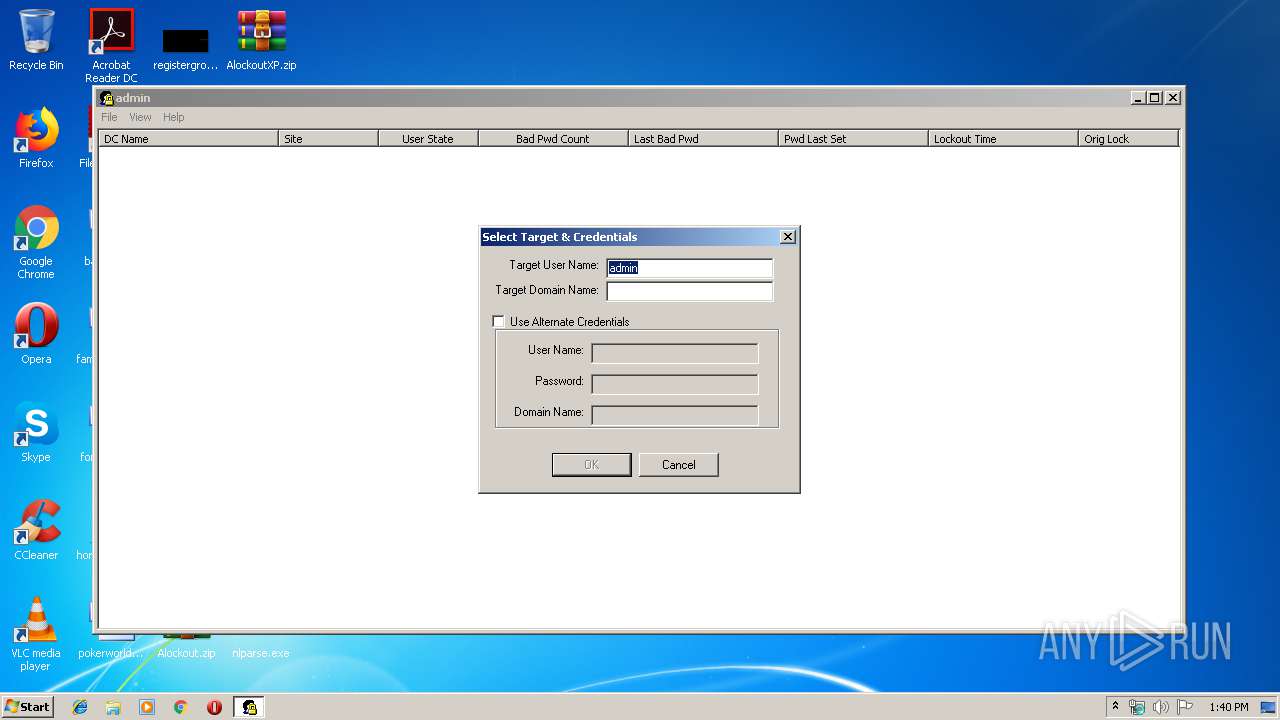
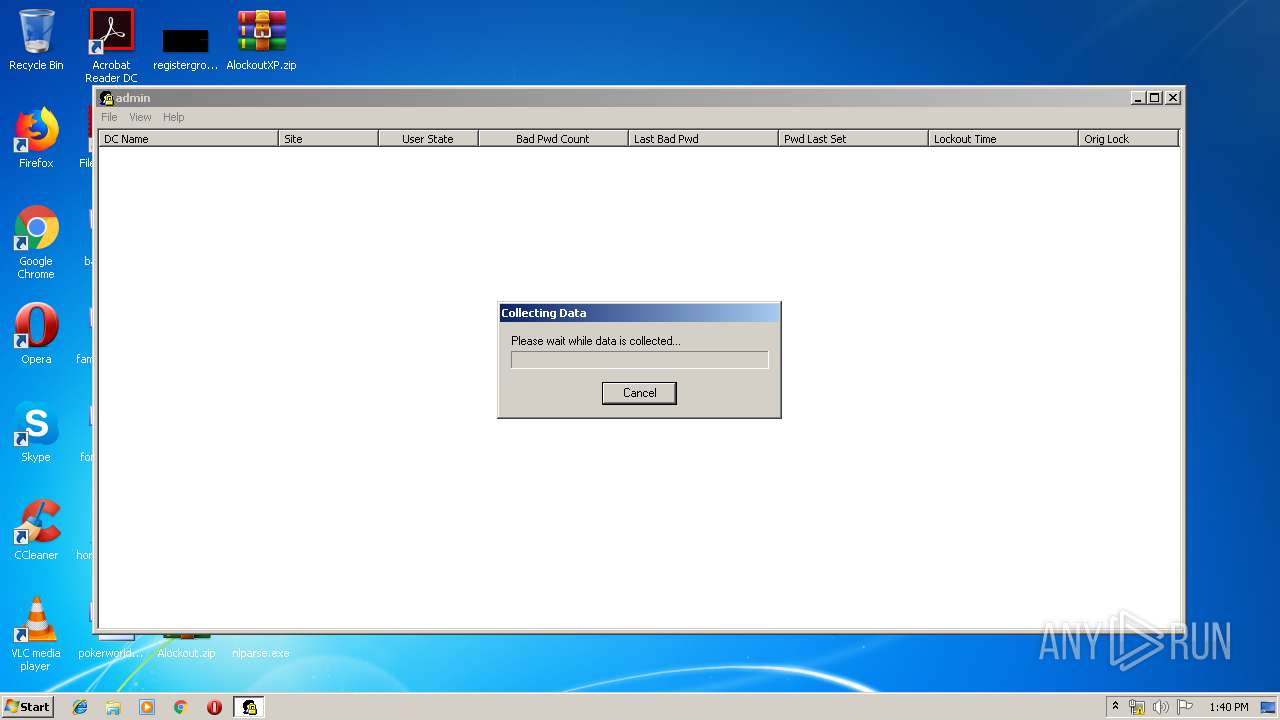
LockoutStatus.exe | [2440:2468] InitInstance() cmdLine: "C:\Users\admin\Desktop\LockoutStatus.exe" |
LockoutStatus.exe | [2440:2468] InitRegistryValues: On Enter |
LockoutStatus.exe | [2440:2468] InitRegistryValues: Found Current User: admin |
LockoutStatus.exe | [2440:2468] GetDefaultDomainName: On Enter |
LockoutStatus.exe | [2440:2468] GetDefaultDomainName: Leaving with 0x54b |
LockoutStatus.exe | [2440:2468] InitRegistryValues: Could not retrive domain name from system. |
LockoutStatus.exe | [2440:2468] InitRegistryValues: Leaving with 0x0 |
LockoutStatus.exe | [2440:2468] GetUserPasswordMetrics: Target: ax |
LockoutStatus.exe | [2440:2468] GetUserPasswordMetrics: Target: admin |
LockoutStatus.exe | [2440:2468] GetUserPasswordMetrics: Domain: |