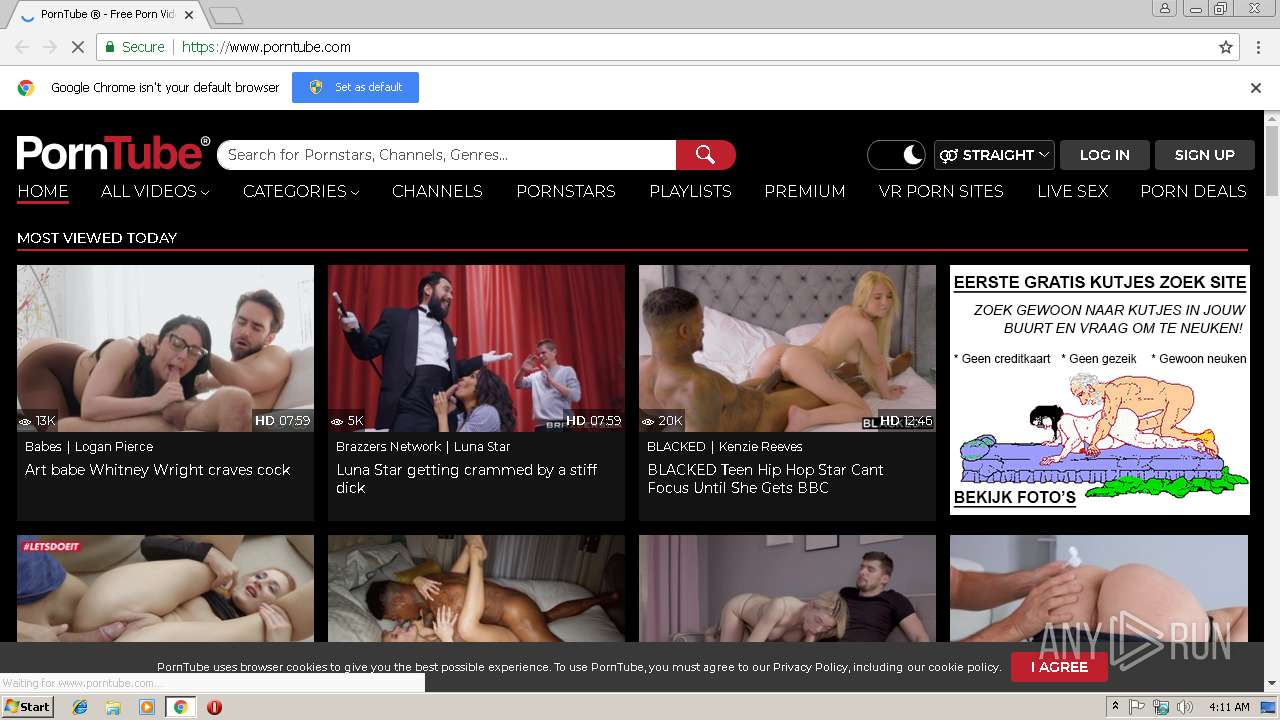
| URL: | https://www.porntube.com |
| Full analysis: | https://app.any.run/tasks/a98d260e-7c65-44a2-8021-8b282b213513 |
| Verdict: | Malicious activity |
| Analysis date: | March 05, 2019, 04:11:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CC5EB2C29A3C64B7F38AA6B704A0F3D0 |
| SHA1: | A6D7DDBE3466AEF5F2643AFDEFAD14C4DA221547 |
| SHA256: | 71656185ABBFAFCF66693C3B7118F9026A48E1A3890FAF50E1338E939B5A5130 |
| SSDEEP: | 3:N8DSLRAyTn:2OLmyT |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3556)
Reads settings of System Certificates
- chrome.exe (PID: 3556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
11
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6fe300b0,0x6fe300c0,0x6fe300cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=876,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=1DF6CE24415C0D47DBDC682FF8E09CC1 --mojo-platform-channel-handle=908 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=876,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=A6142528A66AF5EBA5A3D68E68CCD718 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A6142528A66AF5EBA5A3D68E68CCD718 --renderer-client-id=8 --mojo-platform-channel-handle=3908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=ppapi --field-trial-handle=876,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --ppapi-flash-args --lang=en-US --device-scale-factor=1 --ppapi-antialiased-text-enabled=0 --ppapi-subpixel-rendering-setting=0 --service-request-channel-token=495D6526CC1B0D57DE0E0D1C1D391E7F --mojo-platform-channel-handle=4124 --ignored=" --type=renderer " /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=876,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=D99BF07744311F229660B0BA050E1CC1 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D99BF07744311F229660B0BA050E1CC1 --renderer-client-id=6 --mojo-platform-channel-handle=3360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=876,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --service-pipe-token=2A22F96F3CC9AF46DDE14AD0B9EFBE25 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2A22F96F3CC9AF46DDE14AD0B9EFBE25 --renderer-client-id=4 --mojo-platform-channel-handle=1916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=876,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=0B562E5D74C14C8C00ED20DAC0FA1298 --mojo-platform-channel-handle=4340 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3560 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://www.porntube.com | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=876,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --service-pipe-token=53B909491FA10089FC2AA71D5F3A3012 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=53B909491FA10089FC2AA71D5F3A3012 --renderer-client-id=3 --mojo-platform-channel-handle=2052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
599
Read events
550
Write events
46
Delete events
3
Modification events
| (PID) Process: | (3496) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3556-13196232693245250 |
Value: 259 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3556-13196232693245250 |
Value: 259 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
48
Text files
78
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dcfd86b2-7e45-4f66-a515-ff00ad73e7e1.tmp | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4c2cb092-742f-4045-9278-1b9a4439f329.tmp | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1ae272.TMP | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1ae2a1.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
111
DNS requests
65
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3556 | chrome.exe | GET | 302 | 104.24.120.31:80 | http://srv.sexmotors.com/r.php?back=tsr&i=726819971&p=p2326325&s=s3&t=1551759115&c=NXJOMDBVWmxESk00QUVRY1lOKzhLdz09 | US | — | — | shared |
3556 | chrome.exe | GET | 301 | 66.254.114.41:80 | http://www.pornhub.com/categories?utm_source=barbarian&utm_medium=PT&utm_campaign=barbarian-cats | US | — | — | whitelisted |
3556 | chrome.exe | GET | 302 | 104.16.67.60:80 | http://rotator.trafficstars.com/api/v1/direct/3358959ed991474991846a1a0e93ec59?subid=dt | US | — | — | shared |
3556 | chrome.exe | GET | 200 | 18.153.1.86:80 | http://v3.qrlsx.com/redirect?target=BASE64aHR0cDovL3JvdGF0b3IudHJhZmZpY3N0YXJzLmNvbS9hcGkvdjEvZGlyZWN0LzMzNTg5NTllZDk5MTQ3NDk5MTg0NmExYTBlOTNlYzU5P3N1YmlkPWR0&ts=1551759115346&hash=_l3ZFp9CSF694eBff3kxWhGXO9xnrgWba_sbVZRxVb0&rm=D | US | html | 299 b | suspicious |
3556 | chrome.exe | GET | 200 | 104.24.121.31:80 | http://sexmotors.com/r.php?i=726819971&p=p2326325&s=s3&t=1551759115&c=NXJOMDBVWmxESk00QUVRY1lOKzhLdz09 | US | html | 519 b | whitelisted |
3556 | chrome.exe | GET | 200 | 18.153.1.78:80 | http://vo2.qrlsx.com/0196da96-1996-4dec-9769-74a34923ad34 | US | html | 444 b | shared |
3556 | chrome.exe | GET | 200 | 69.55.63.49:80 | http://www.hornycrocodile.com/ | US | html | 137 b | unknown |
3556 | chrome.exe | GET | 404 | 69.55.63.49:80 | http://www.hornycrocodile.com/favicon.ico | US | html | 209 b | unknown |
3556 | chrome.exe | GET | 302 | 69.55.63.23:80 | http://www.trafficserving.com/videos1.php | US | binary | 1 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3556 | chrome.exe | 66.254.122.102:443 | cdn1-thumbnails.porntube.com | Reflected Networks, Inc. | US | suspicious |
3556 | chrome.exe | 74.125.206.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3556 | chrome.exe | 172.64.131.32:443 | hinhasimi.com | Cloudflare Inc | US | shared |
3556 | chrome.exe | 95.211.229.245:443 | origin-ads.exosrv.com | LeaseWeb Netherlands B.V. | NL | suspicious |
3556 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3556 | chrome.exe | 205.185.216.42:443 | ads.exosrv.com | Highwinds Network Group, Inc. | US | whitelisted |
3556 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3556 | chrome.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3556 | chrome.exe | 104.18.148.225:443 | www.porntube.com | Cloudflare Inc | US | shared |
3556 | chrome.exe | 172.217.22.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.porntube.com |
| unknown |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
ads.exoclick.com |
| suspicious |
syndication.exoclick.com |
| suspicious |
cdn1-ht-assets.porntube.com |
| unknown |
syndication.exosrv.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |