| File name: | Annabelle.exe |
| Full analysis: | https://app.any.run/tasks/d8d110cd-30ed-4b11-a43b-d5501a24cfa6 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 16:16:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | 0F743287C9911B4B1C726C7C7EDCAF7D |
| SHA1: | 9760579E73095455FCBADDFE1E7E98A2BB28BFE0 |
| SHA256: | 716335BA5CD1E7186C40295B199190E2B6655E48F1C1CBE12139BA67FAA5E1AC |
| SSDEEP: | 393216:UMwm0qBknxdEX+LbMUgoSZmWSmh4aaRN22ChHCMNku1y4:UMcKX+Lbjgd7W1RNVC9ku1x |
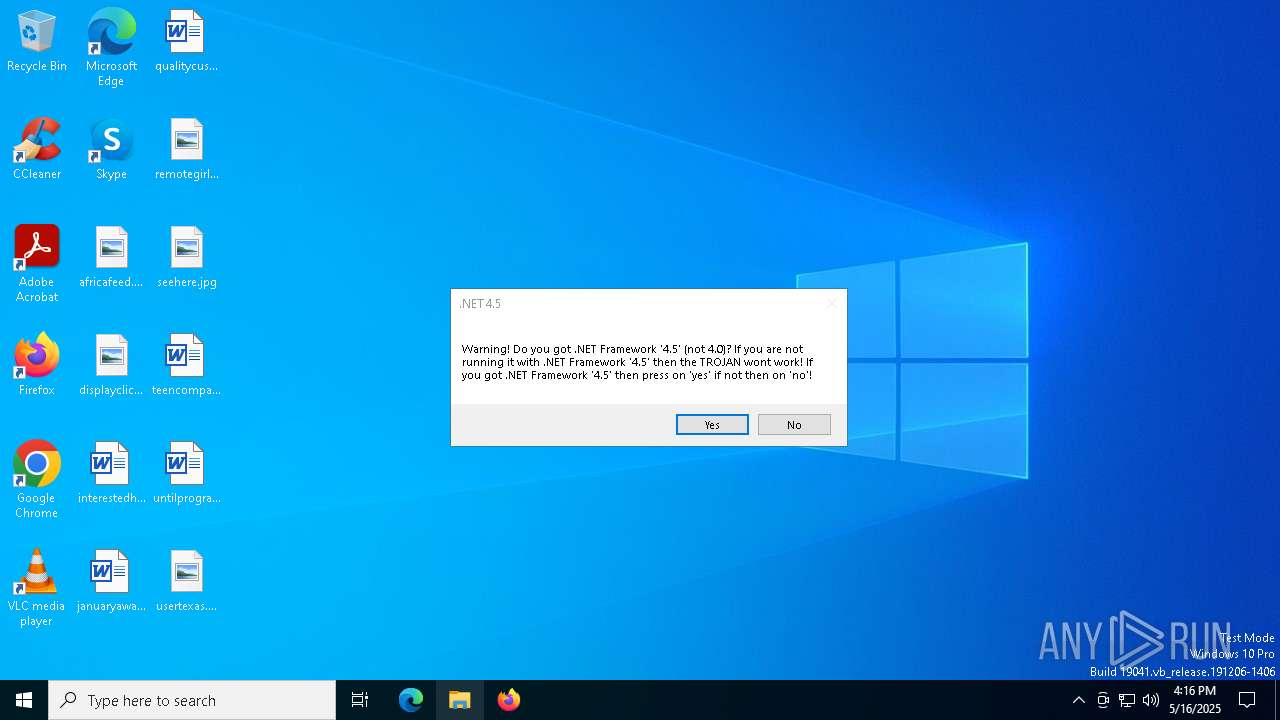
MALICIOUS
Deletes shadow copies
- Annabelle.exe (PID: 7384)
Changes the autorun value in the registry
- Annabelle.exe (PID: 7384)
Disables Windows Defender
- Annabelle.exe (PID: 7384)
UAC/LUA settings modification
- Annabelle.exe (PID: 7384)
Disables task manager
- Annabelle.exe (PID: 7384)
Changes the login/logoff helper path in the registry
- Annabelle.exe (PID: 7384)
Disables the Run the Start menu
- Annabelle.exe (PID: 7384)
Changes image file execution options
- Annabelle.exe (PID: 7384)
SUSPICIOUS
Uses NETSH.EXE to change the status of the firewall
- Annabelle.exe (PID: 7384)
Reads security settings of Internet Explorer
- Annabelle.exe (PID: 7384)
- ShellExperienceHost.exe (PID: 2384)
Creates file in the systems drive root
- Annabelle.exe (PID: 7384)
Reads the date of Windows installation
- Annabelle.exe (PID: 7384)
The system shut down or reboot
- Annabelle.exe (PID: 7384)
Executes as Windows Service
- VSSVC.exe (PID: 7920)
INFO
Reads the machine GUID from the registry
- Annabelle.exe (PID: 7384)
Checks supported languages
- Annabelle.exe (PID: 7384)
- ShellExperienceHost.exe (PID: 2384)
Reads the computer name
- Annabelle.exe (PID: 7384)
- ShellExperienceHost.exe (PID: 2384)
Process checks computer location settings
- Annabelle.exe (PID: 7384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2018:02:18 17:54:24+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 80 |
| CodeSize: | 16437248 |
| InitializedDataSize: | 274432 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.0.0 |
| ProductVersionNumber: | 2.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Annabelle |
| FileVersion: | 2.1.0.0 |
| InternalName: | Annabelle.exe |
| LegalCopyright: | Copyright © 2018 |
| LegalTrademarks: | - |
| OriginalFileName: | Annabelle.exe |
| ProductName: | UpdateBackup |
| ProductVersion: | 2.1.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
148
Monitored processes
14
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2384 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3900 | "C:\Windows\System32\shutdown.exe" -r -t 00 -f | C:\Windows\System32\shutdown.exe | — | Annabelle.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4488 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | shutdown.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7280 | "C:\Users\admin\AppData\Local\Temp\Annabelle.exe" | C:\Users\admin\AppData\Local\Temp\Annabelle.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Annabelle Exit code: 3221226540 Version: 2.1.0.0 Modules
| |||||||||||||||
| 7384 | "C:\Users\admin\AppData\Local\Temp\Annabelle.exe" | C:\Users\admin\AppData\Local\Temp\Annabelle.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Annabelle Version: 2.1.0.0 Modules
| |||||||||||||||
| 7700 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | Annabelle.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7708 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | Annabelle.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7716 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | vssadmin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7724 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | Annabelle.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | vssadmin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 604
Read events
2 515
Write events
89
Delete events
0
Modification events
| (PID) Process: | (7384) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\cmd.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7384) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\chrome.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7384) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\firefox.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7384) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\opera.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7384) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\microsoftedge.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7384) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\microsoftedgecp.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7384) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\notepad++.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7384) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\notepad.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7384) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\iexplore.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7384) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MSASCuiL.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
Executable files
0
Suspicious files
27
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7384 | Annabelle.exe | C:\Users\admin\Documents\Database1.accdb.ANNABELLE | binary | |
MD5:6923415A237011EFB8D48C0981D40E42 | SHA256:66C65F8208725E985A2DE2E56200173FC3F91FBDB64EFDE9DF799945BF0E9E1C | |||
| 7384 | Annabelle.exe | C:\Users\admin\Documents\ownaccessories.rtf.ANNABELLE | binary | |
MD5:10C2AEE012510492B321E920051998B2 | SHA256:173D203672060895813BF24FF71D5AAC16D06B8AF8DBF69A9B8E242D65A85D22 | |||
| 7384 | Annabelle.exe | C:\Users\admin\Documents\sees.rtf.ANNABELLE | binary | |
MD5:49F5A5FB3C16261A08434BBE1E2EB405 | SHA256:0AE296E96E320114400DDD72CFD0A94B872D40AFB8A8ABFDE22106E1A1F66BCA | |||
| 7384 | Annabelle.exe | C:\Users\admin\Documents\alongassociated.rtf.ANNABELLE | binary | |
MD5:7CE653BFD0EE00DA298F60FE4E81B7C8 | SHA256:95F52849AAFFD68CD87BA80816C09F2031BF365786CA931DD56D89E152E72C4D | |||
| 7384 | Annabelle.exe | C:\Users\admin\Pictures\educationalsend.png.ANNABELLE | binary | |
MD5:D1A9B622AB5AFC541EE0BBC8128D7A2C | SHA256:3200B59E3D1A26F6B2D939FB1A13ADEBF1D1DA5BE74C7EB1F82101F772784AE8 | |||
| 7384 | Annabelle.exe | C:\Users\admin\Pictures\likelysame.png.ANNABELLE | binary | |
MD5:EF3023383E6BDB00F42B7E9F576D79E5 | SHA256:A37391FCE9D39419BC85AAFDC42DF8CE77FDF742DC29D884FE85338140218EBD | |||
| 7384 | Annabelle.exe | C:\Users\admin\Downloads\wantspecific.jpg.ANNABELLE | binary | |
MD5:4FB5CFD208A6F68F0BDD6168F3E00212 | SHA256:BAB71C26D370CC7C8BB673202BD9F22E6255BA515FECE57CDCC6AA70D646CBE1 | |||
| 7384 | Annabelle.exe | C:\Users\admin\Downloads\effectivemajor.png.ANNABELLE | binary | |
MD5:1268EBB99405D5ADD7459827D6704799 | SHA256:EC31B6A3BF22FBF6DE9DA7927F8D146D28D02342890A2013E112A0FBBF17AFB2 | |||
| 7384 | Annabelle.exe | C:\Users\admin\Downloads\restaurantsoct.jpg.ANNABELLE | binary | |
MD5:88032ACC61EFD0D7487397A1D322445F | SHA256:D725BD37E5938F7C4489FFFCF8992397A126879AFDB651415775F1FD2ABE0578 | |||
| 7384 | Annabelle.exe | C:\Users\admin\Desktop\africafeed.jpg.ANNABELLE | binary | |
MD5:493A8314FAE4775B078C30E28DDFCA43 | SHA256:75A1B4440BE55C6C6AB4F5B2EE3AFD7849BE17CCAC26D8521A01189213C2A368 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
34
DNS requests
16
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2292 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
3812 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
go.microsoft.com |
| whitelisted |