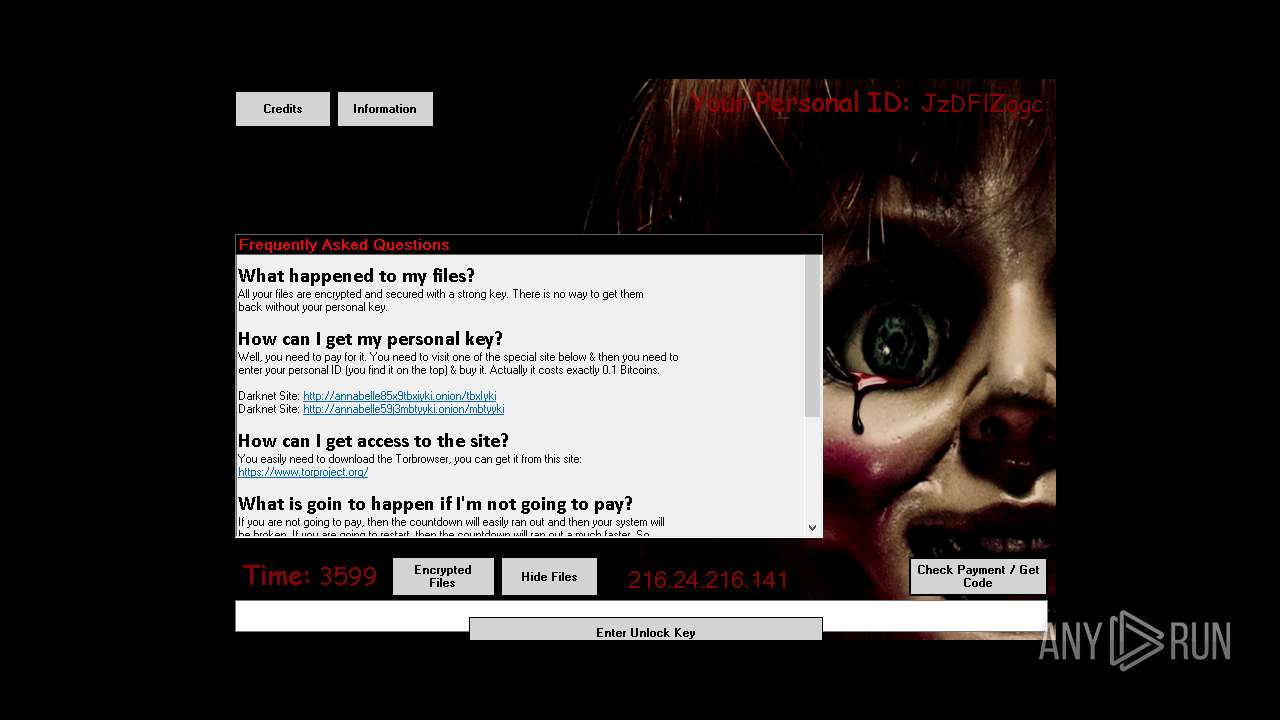
| File name: | Annabelle.exe |
| Full analysis: | https://app.any.run/tasks/b078ba8b-b2ce-48ab-9acd-5cc237fde597 |
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2025, 17:57:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | 0F743287C9911B4B1C726C7C7EDCAF7D |
| SHA1: | 9760579E73095455FCBADDFE1E7E98A2BB28BFE0 |
| SHA256: | 716335BA5CD1E7186C40295B199190E2B6655E48F1C1CBE12139BA67FAA5E1AC |
| SSDEEP: | 393216:UMwm0qBknxdEX+LbMUgoSZmWSmh4aaRN22ChHCMNku1y4:UMcKX+Lbjgd7W1RNVC9ku1x |
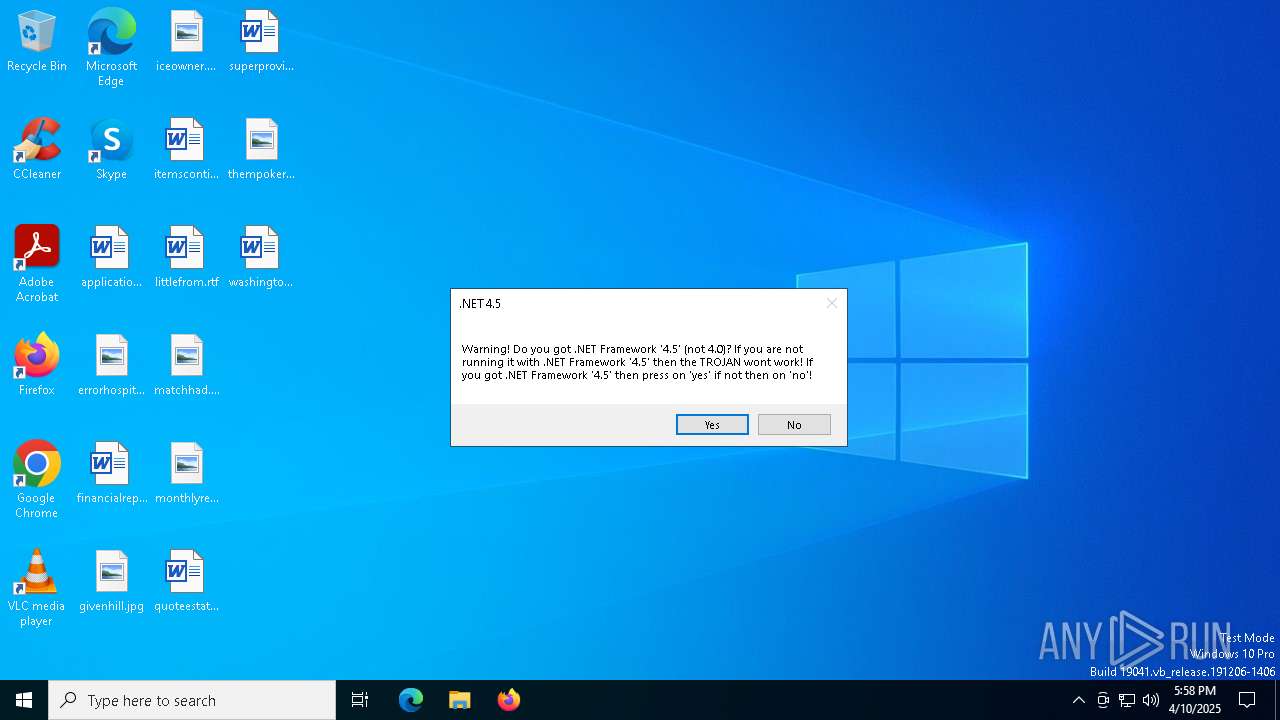
MALICIOUS
Deletes shadow copies
- Annabelle.exe (PID: 7204)
Disables task manager
- Annabelle.exe (PID: 7204)
Disables Windows Defender
- Annabelle.exe (PID: 7204)
Changes the autorun value in the registry
- Annabelle.exe (PID: 7204)
UAC/LUA settings modification
- Annabelle.exe (PID: 7204)
Changes the login/logoff helper path in the registry
- Annabelle.exe (PID: 7204)
Changes image file execution options
- Annabelle.exe (PID: 7204)
Disables the Run the Start menu
- Annabelle.exe (PID: 7204)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 7912)
Creates file in the systems drive root
- Annabelle.exe (PID: 7204)
Reads the date of Windows installation
- Annabelle.exe (PID: 7204)
Reads security settings of Internet Explorer
- Annabelle.exe (PID: 7204)
- ShellExperienceHost.exe (PID: 7180)
The system shut down or reboot
- Annabelle.exe (PID: 7204)
Uses NETSH.EXE to change the status of the firewall
- Annabelle.exe (PID: 7204)
INFO
Checks supported languages
- Annabelle.exe (PID: 7204)
- ShellExperienceHost.exe (PID: 7180)
Process checks computer location settings
- Annabelle.exe (PID: 7204)
Reads the computer name
- ShellExperienceHost.exe (PID: 7180)
- Annabelle.exe (PID: 7204)
Reads the machine GUID from the registry
- Annabelle.exe (PID: 7204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2018:02:18 17:54:24+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 80 |
| CodeSize: | 16437248 |
| InitializedDataSize: | 274432 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.0.0 |
| ProductVersionNumber: | 2.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Annabelle |
| FileVersion: | 2.1.0.0 |
| InternalName: | Annabelle.exe |
| LegalCopyright: | Copyright © 2018 |
| LegalTrademarks: | - |
| OriginalFileName: | Annabelle.exe |
| ProductName: | UpdateBackup |
| ProductVersion: | 2.1.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
140
Monitored processes
14
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | shutdown.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6480 | "C:\Windows\System32\shutdown.exe" -r -t 00 -f | C:\Windows\System32\shutdown.exe | — | Annabelle.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6944 | "C:\Users\admin\AppData\Local\Temp\Annabelle.exe" | C:\Users\admin\AppData\Local\Temp\Annabelle.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Annabelle Exit code: 3221226540 Version: 2.1.0.0 Modules
| |||||||||||||||
| 7180 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7204 | "C:\Users\admin\AppData\Local\Temp\Annabelle.exe" | C:\Users\admin\AppData\Local\Temp\Annabelle.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Annabelle Version: 2.1.0.0 Modules
| |||||||||||||||
| 7644 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | Annabelle.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7652 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | vssadmin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7660 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | Annabelle.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7668 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | Annabelle.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | vssadmin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 043
Read events
1 956
Write events
87
Delete events
0
Modification events
| (PID) Process: | (7204) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | UpdateBackup |
Value: C:\Users\admin\AppData\Local\Temp\Annabelle.exe | |||
| (PID) Process: | (7204) Annabelle.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | UpdateBackup |
Value: C:\Users\admin\AppData\Local\Temp\Annabelle.exe | |||
| (PID) Process: | (7204) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | UpdateBackup |
Value: C:\Users\admin\AppData\Local\Temp\Annabelle.exe | |||
| (PID) Process: | (7204) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msconfig.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7204) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\taskmgr.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7204) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\cmd.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7204) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\chrome.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7204) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\firefox.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7204) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\notepad++.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
| (PID) Process: | (7204) Annabelle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\notepad.exe |
| Operation: | write | Name: | Debugger |
Value: RIP | |||
Executable files
0
Suspicious files
27
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7204 | Annabelle.exe | C:\Users\admin\Pictures\goodalways.png.ANNABELLE | binary | |
MD5:B23EA612F5C6E95C2BBEB6B729CD8394 | SHA256:2149515AE65F27196A6AED09227CD33CE07931DF6FA5BAB7F63F15396789D6E4 | |||
| 7204 | Annabelle.exe | C:\Users\admin\Documents\littleperiod.rtf.ANNABELLE | binary | |
MD5:8183C68A3F2C2E2F8FA27E15963A143A | SHA256:0E74E03E5B1C98DEBA5EFF2D326DE17397860DEBFEFD9BE2B0D57D55ACD44F12 | |||
| 7204 | Annabelle.exe | C:\Users\admin\Documents\iraqpayment.rtf.ANNABELLE | binary | |
MD5:5DCF4F860668AC69B8045ED7D75CF60F | SHA256:DB0FD8E33BB149CB28EBC325CFBE7CD0C65676DEDA13DB5997188EAB405474FF | |||
| 7204 | Annabelle.exe | C:\Users\admin\Documents\sodeal.rtf.ANNABELLE | binary | |
MD5:313994A24DDDB4946FAC1DF6002CAA0C | SHA256:60EBBB31C3FCCE0424A33BCEA2C27643C756ED71CE523E123CE9FA869C2DDFFB | |||
| 7204 | Annabelle.exe | C:\Users\admin\Documents\leadingprivacy.rtf.ANNABELLE | binary | |
MD5:99F5D568AA97DE8A8A3B0CE31F6D0DDC | SHA256:A9EB49BE6CCFDCB428D29FF8CA0D48521013DDAD7AF3F2CAD1801ED517F518BA | |||
| 7204 | Annabelle.exe | C:\Users\admin\Documents\Database1.accdb.ANNABELLE | binary | |
MD5:6923415A237011EFB8D48C0981D40E42 | SHA256:66C65F8208725E985A2DE2E56200173FC3F91FBDB64EFDE9DF799945BF0E9E1C | |||
| 7204 | Annabelle.exe | C:\Users\admin\Documents\emailmb.rtf.ANNABELLE | binary | |
MD5:C60AC02AA94AB446A4CE10561DF89CD8 | SHA256:6E3FDE8E582D655EC1D6BADA3C312867C56B70C4DB8DEF2866FF7D58F11155E5 | |||
| 7204 | Annabelle.exe | C:\Users\admin\Documents\provideforeign.rtf.ANNABELLE | binary | |
MD5:A114703930317608A7CB0CB84D9D90B5 | SHA256:04B9BF069468F5B3D8404BDC9C4191E63BD7E5F3A7A9D0F0412C13E535055A5C | |||
| 7204 | Annabelle.exe | C:\Users\admin\Documents\allowshill.rtf.ANNABELLE | binary | |
MD5:7127DFBD4DEE7005BF8DAA21AC72698A | SHA256:874C1C8B9A38073E02163D8663383C57CF57B6498675731C06573A1F7929E871 | |||
| 7204 | Annabelle.exe | C:\Users\admin\Downloads\wintersummer.png.ANNABELLE | binary | |
MD5:C0824905FC40236E466C8620E9C1F38E | SHA256:FA27310719CAC0CF3C630D86FAAF3C387EE93D049F76895206B7CA7123629FEB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
34
DNS requests
23
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 146.112.255.205:80 | http://myip.dnsomatic.com/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3812 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2292 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Device Retrieving External IP Address Detected | ET INFO Internal Host Retrieving External IP via myip.dnsomatic.com |
— | — | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |