| File name: | FA-43-03-2025 (10).jar |
| Full analysis: | https://app.any.run/tasks/8b62f530-0855-4892-8033-229c1250ce0d |
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2025, 10:21:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | D56A1D826E18852E27E516716E7EFDEE |
| SHA1: | B78EB8A3E7A5BF9AF425322FBFA69DC6D85DC7B4 |
| SHA256: | 716020E639D7316797F3C34402F7A3E64AF7533C0CC299D161C86CF973E56FB9 |
| SSDEEP: | 98304:qbHcEsO1w72ayRQvAiqCPCo2KRlO+jDpgwQ3VR1MMQbcB0lUvHQCR5VFn2jrgFox:VDvN2/xTuu34 |
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 5608)
- reg.exe (PID: 6468)
SUSPICIOUS
Starts CMD.EXE for commands execution
- javaw.exe (PID: 4844)
- javaw.exe (PID: 5216)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5024)
- cmd.exe (PID: 6156)
There is functionality for taking screenshot (YARA)
- javaw.exe (PID: 4844)
Connects to unusual port
- javaw.exe (PID: 4844)
- javaw.exe (PID: 5216)
INFO
Creates files in the program directory
- javaw.exe (PID: 4844)
Application based on Java
- javaw.exe (PID: 4844)
- javaw.exe (PID: 5216)
Create files in a temporary directory
- javaw.exe (PID: 4844)
- javaw.exe (PID: 5216)
Reads the computer name
- javaw.exe (PID: 4844)
- javaw.exe (PID: 5216)
Creates files or folders in the user directory
- javaw.exe (PID: 4844)
Auto-launch of the file from Registry key
- reg.exe (PID: 5608)
- reg.exe (PID: 6468)
Checks supported languages
- javaw.exe (PID: 4844)
- javaw.exe (PID: 5216)
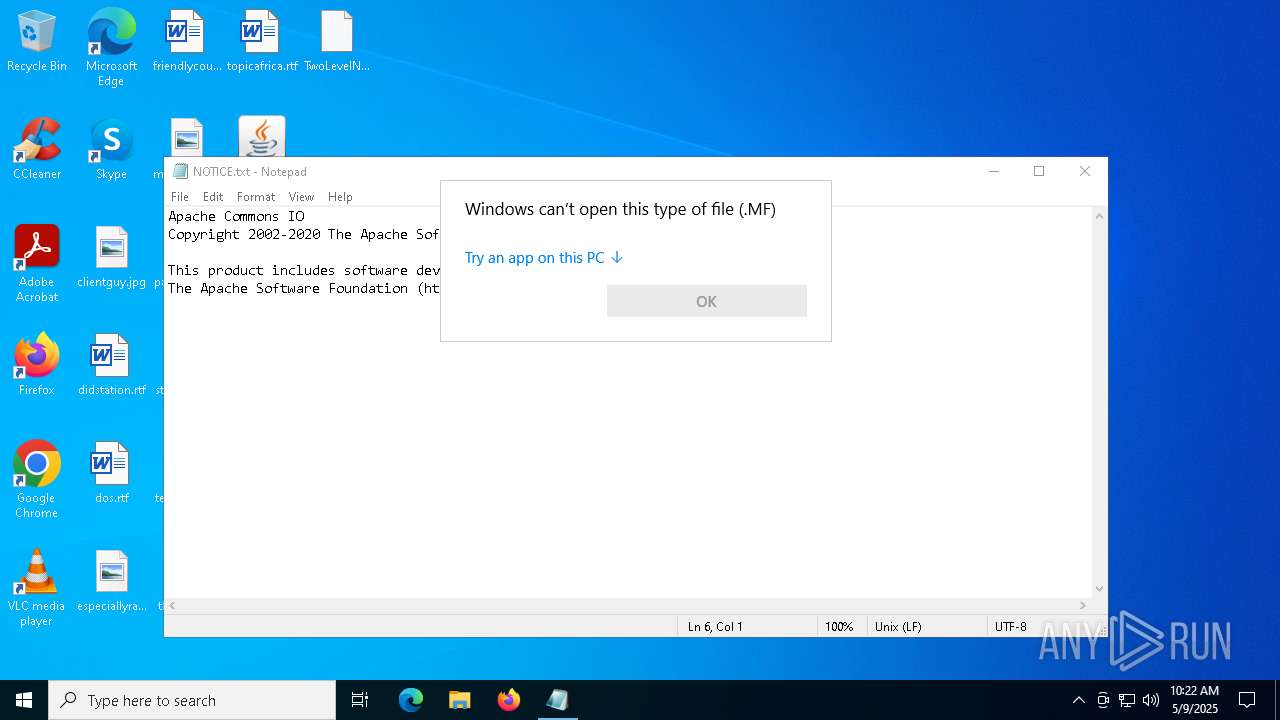
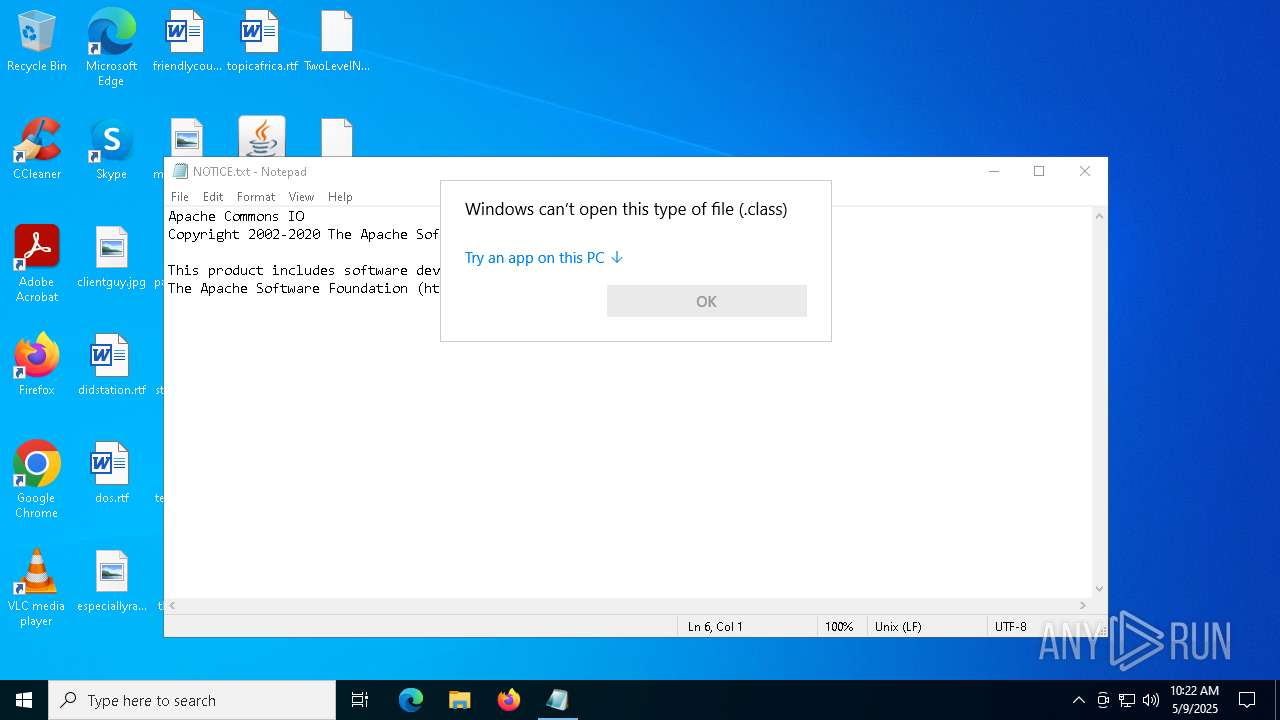
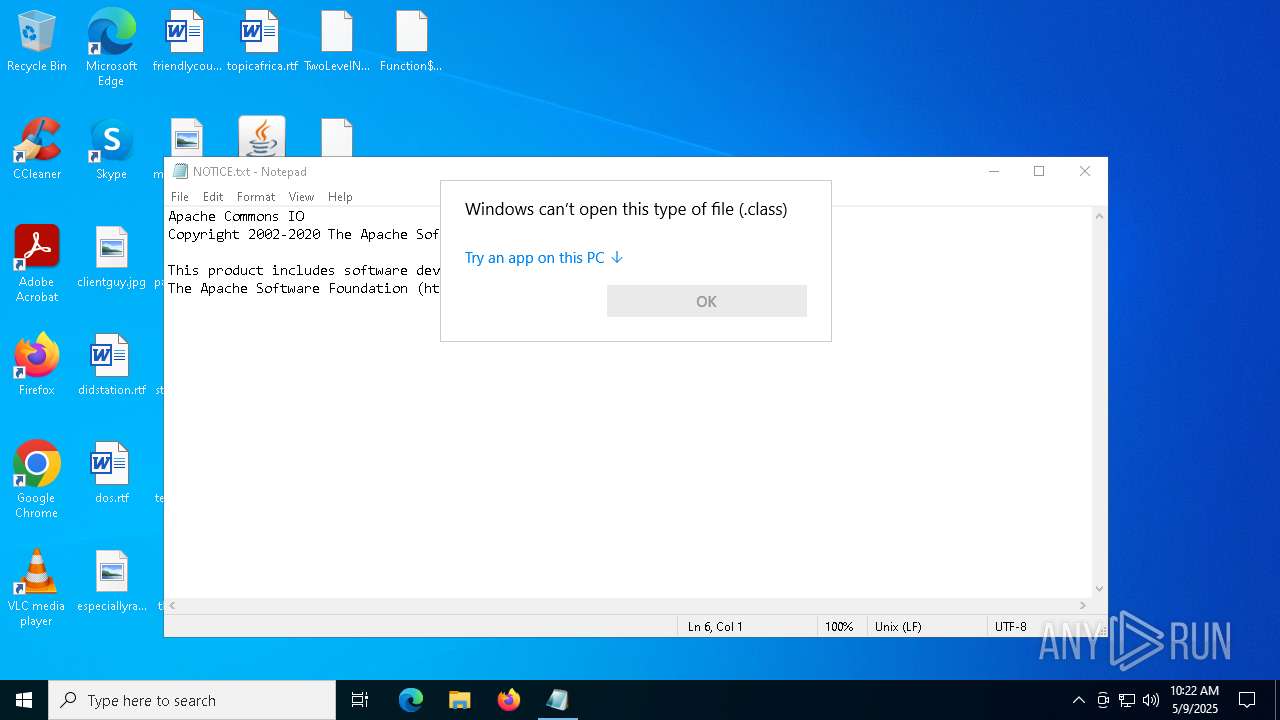
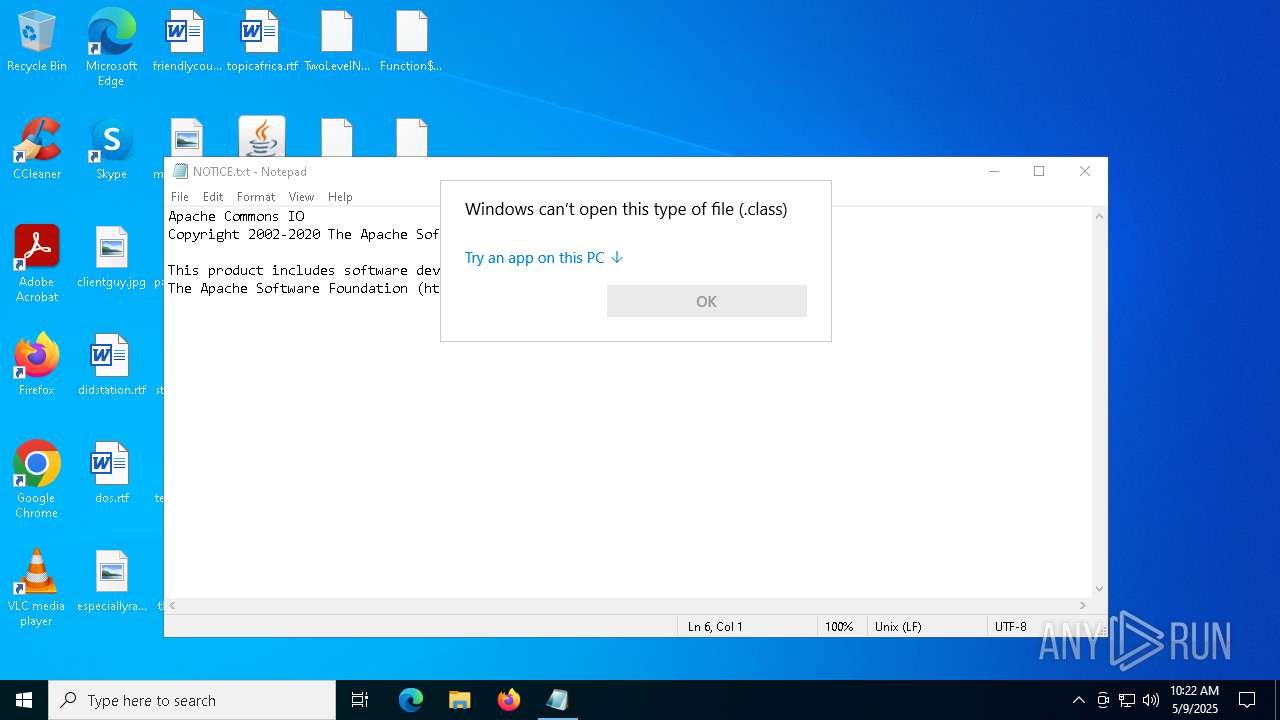
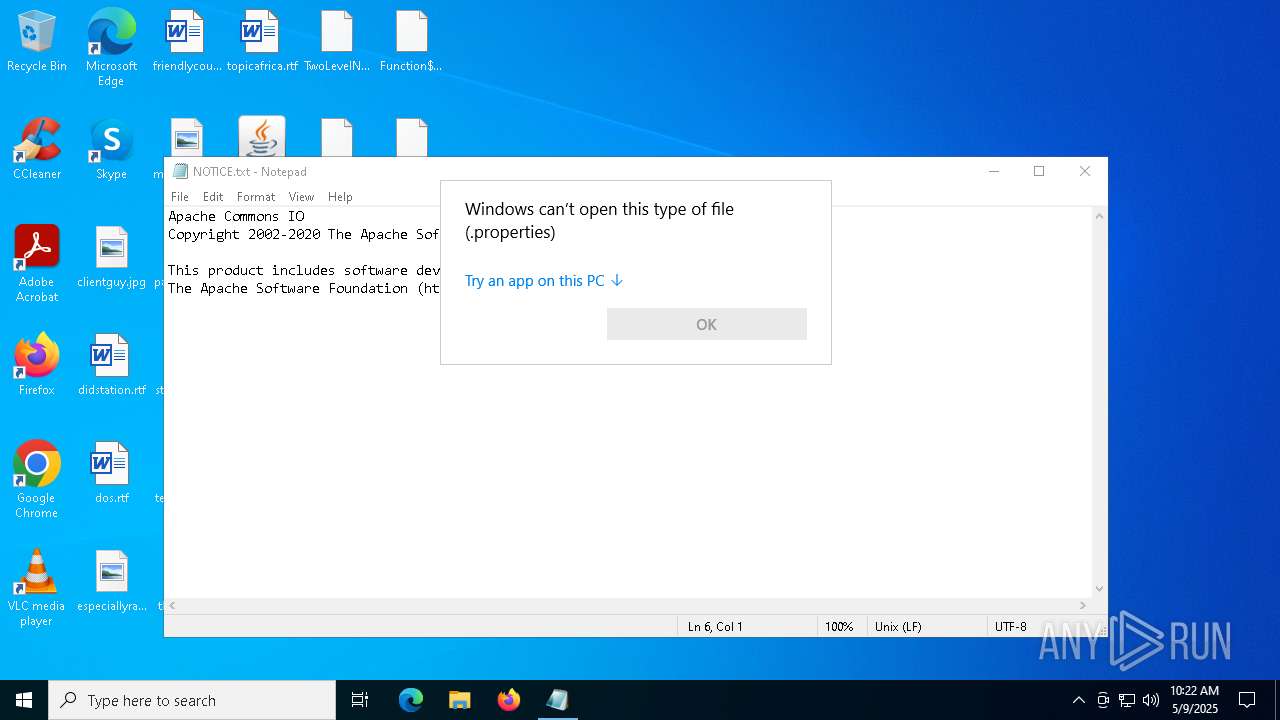
Manual execution by a user
- javaw.exe (PID: 5216)
- notepad.exe (PID: 728)
- OpenWith.exe (PID: 2552)
- OpenWith.exe (PID: 1628)
- OpenWith.exe (PID: 744)
- OpenWith.exe (PID: 5436)
- OpenWith.exe (PID: 4428)
- OpenWith.exe (PID: 3180)
- OpenWith.exe (PID: 3884)
- OpenWith.exe (PID: 4068)
- OpenWith.exe (PID: 3896)
- OpenWith.exe (PID: 6248)
- OpenWith.exe (PID: 6800)
- OpenWith.exe (PID: 2516)
- OpenWith.exe (PID: 684)
- OpenWith.exe (PID: 5116)
- OpenWith.exe (PID: 5964)
Reads security settings of Internet Explorer
- notepad.exe (PID: 728)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 3884)
- OpenWith.exe (PID: 4068)
- OpenWith.exe (PID: 2552)
- OpenWith.exe (PID: 1628)
- OpenWith.exe (PID: 744)
- OpenWith.exe (PID: 5436)
- OpenWith.exe (PID: 3180)
- OpenWith.exe (PID: 4428)
- OpenWith.exe (PID: 5964)
- OpenWith.exe (PID: 6248)
- OpenWith.exe (PID: 3896)
- OpenWith.exe (PID: 2516)
- OpenWith.exe (PID: 684)
- OpenWith.exe (PID: 5116)
- OpenWith.exe (PID: 6800)
Reads the software policy settings
- slui.exe (PID: 1188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jar | | | Java Archive (43.2) |
|---|---|---|
| .xpi | | | Mozilla Firefox browser extension (23.8) |
| .zip | | | ZIP compressed archive (11.9) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:03:19 13:17:04 |
| ZipCRC: | 0xcdab109e |
| ZipCompressedSize: | 1001 |
| ZipUncompressedSize: | 2869 |
| ZipFileName: | org/reactfx/EventStreams$8.class |
Total processes
157
Monitored processes
29
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Desktop\pom.properties | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
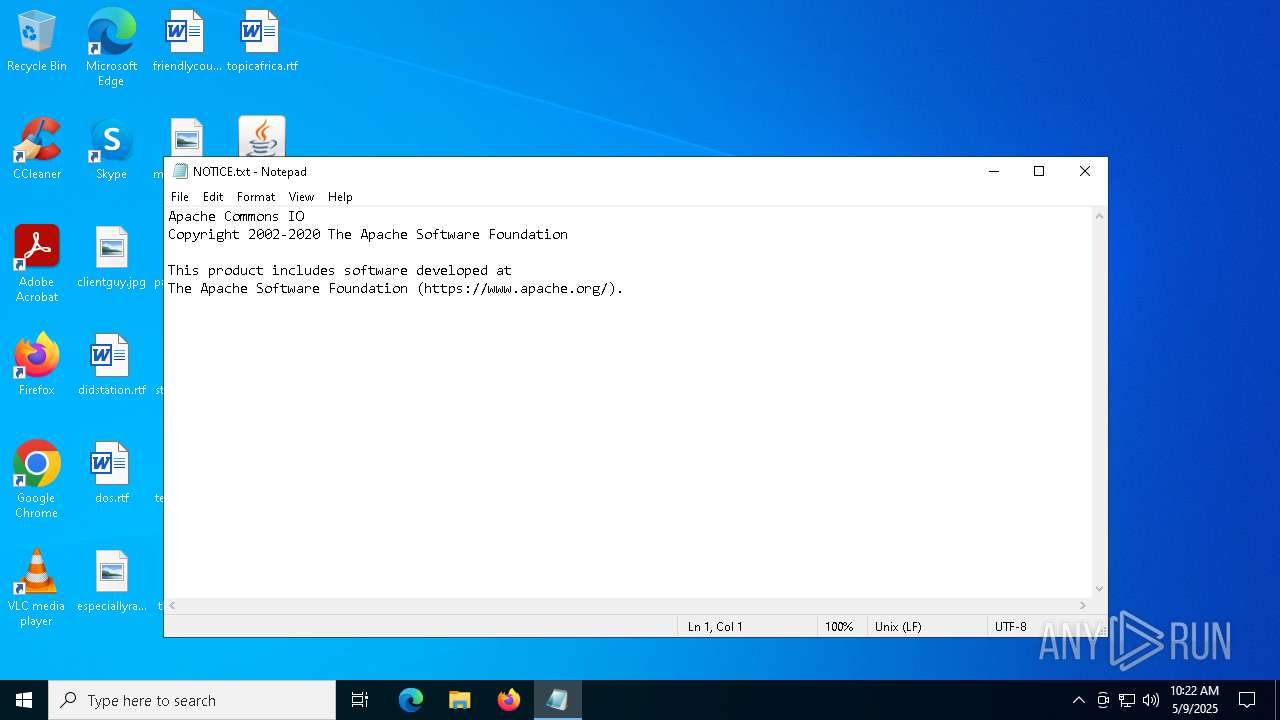
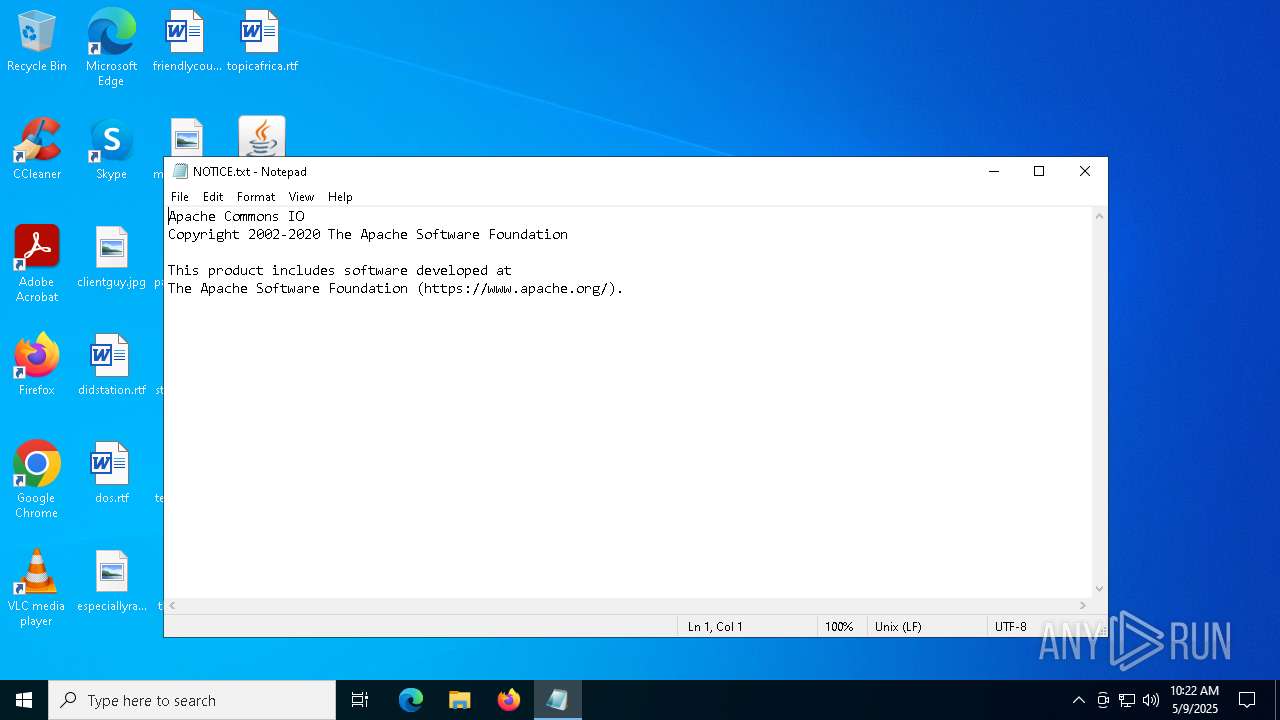
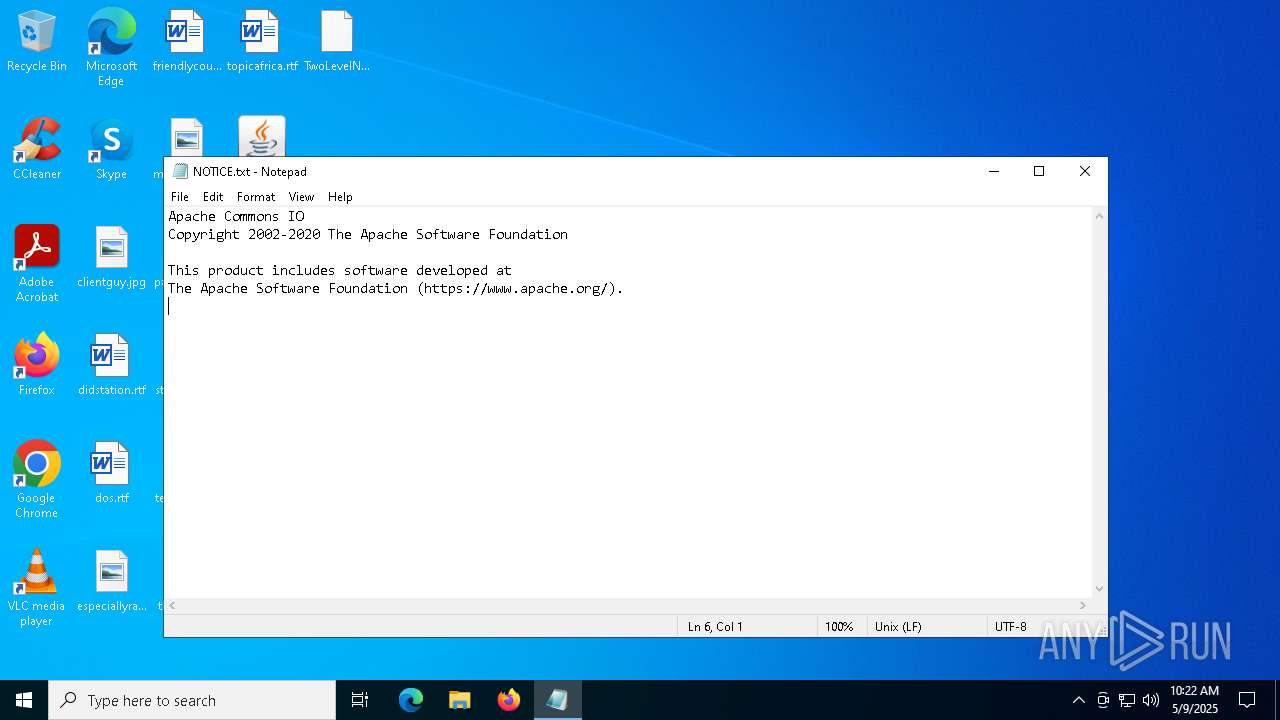
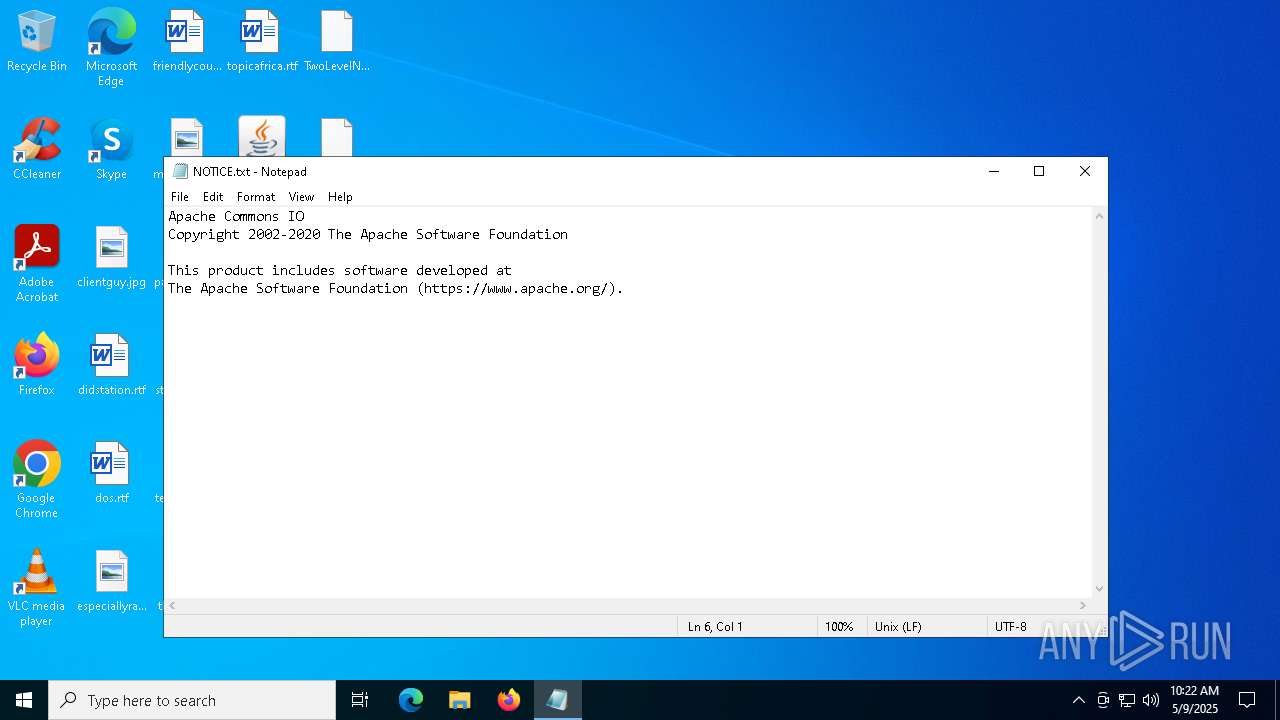
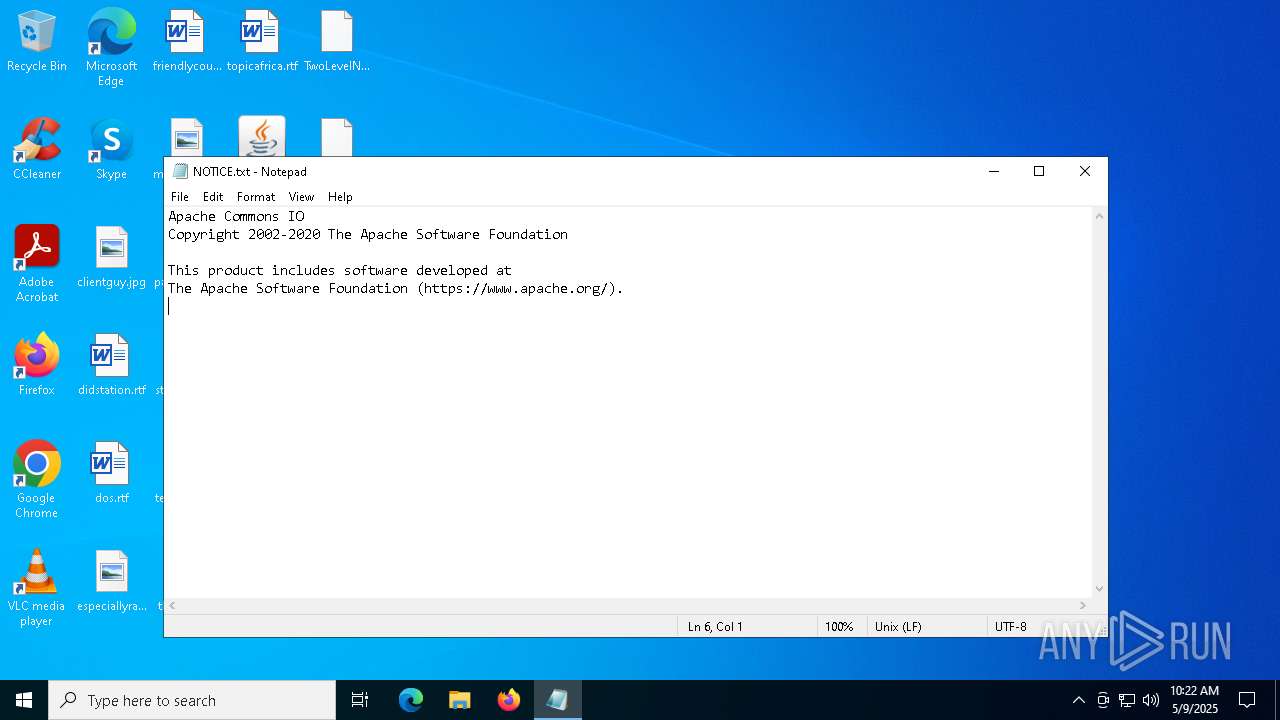
| 728 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\NOTICE.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Desktop\MANIFEST.MF | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
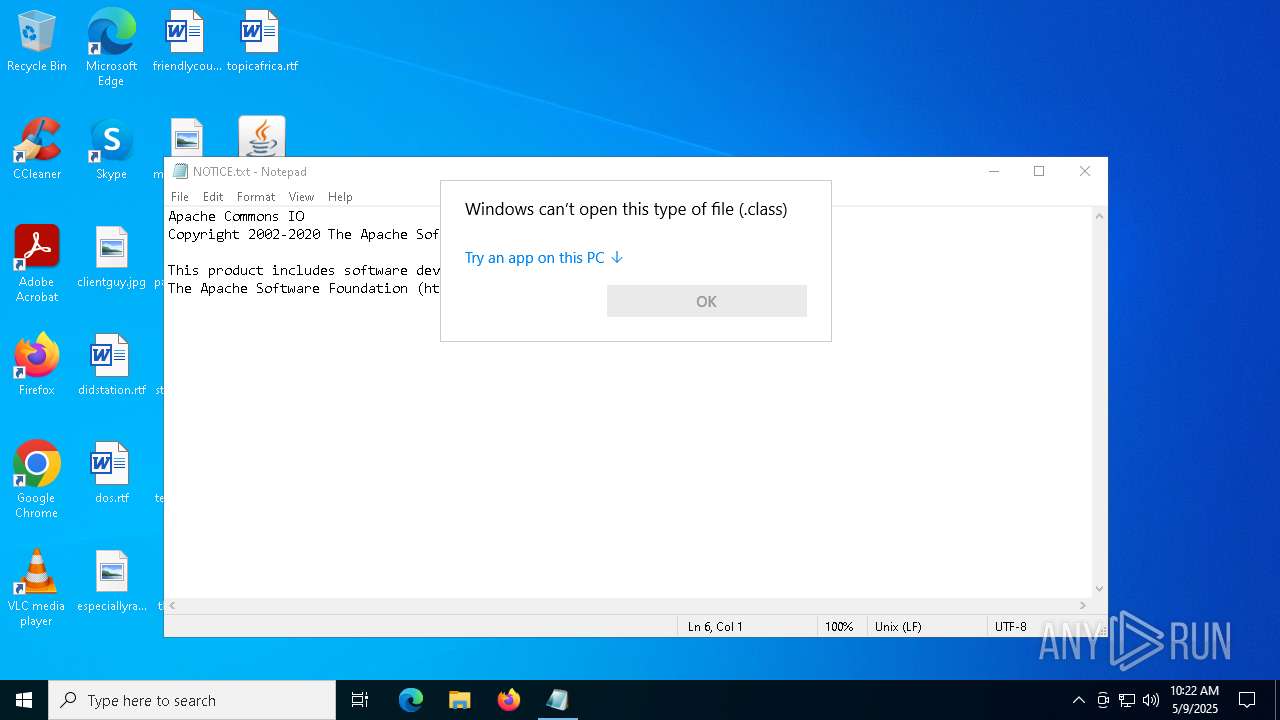
| 1628 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Desktop\TwoLevelNavigator$1.class | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2516 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Desktop\ClassNameMatcher.class | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Desktop\Pointer$1.class | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3180 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Desktop\StdCall.class | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
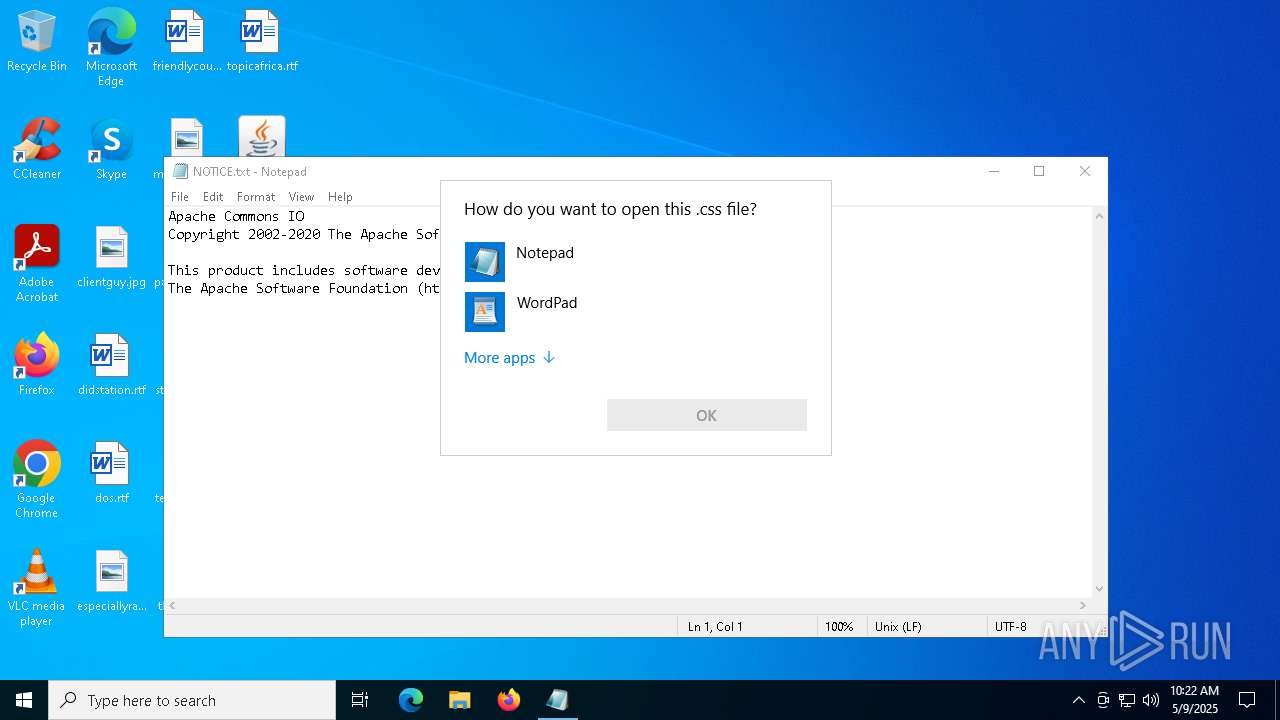
| 3884 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Desktop\styled-text-area.css | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3896 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 140
Read events
9 137
Write events
3
Delete events
0
Modification events
| (PID) Process: | (5608) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | AutoRunKey |
Value: C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe -jar C:\Users\admin\AppData\Roaming\DATA\1746786112956.png | |||
| (PID) Process: | (6468) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | AutoRunKey |
Value: C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe -jar C:\Users\admin\AppData\Roaming\DATA\1746786112956.png | |||
| (PID) Process: | (3884) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.css\OpenWithProgids |
| Operation: | write | Name: | CSSfile |
Value: | |||
Executable files
0
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4844 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:08DEE29D897EBF468A1661BFE3EBB847 | SHA256:0EDE3BFC1A27EDBCFD4EBEAE0FA0F3117C2FF1AB68FF7ED8E1BB1A6BAD5CAB67 | |||
| 4844 | javaw.exe | C:\Users\admin\AppData\Roaming\DATA\1746786112956.png | compressed | |
MD5:D56A1D826E18852E27E516716E7EFDEE | SHA256:716020E639D7316797F3C34402F7A3E64AF7533C0CC299D161C86CF973E56FB9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
241
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.129:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5056 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5056 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.129:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4844 | javaw.exe | 158.178.201.63:8911 | dc8vcreun.localto.net | — | GB | malicious |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
dc8vcreun.localto.net |
| malicious |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |