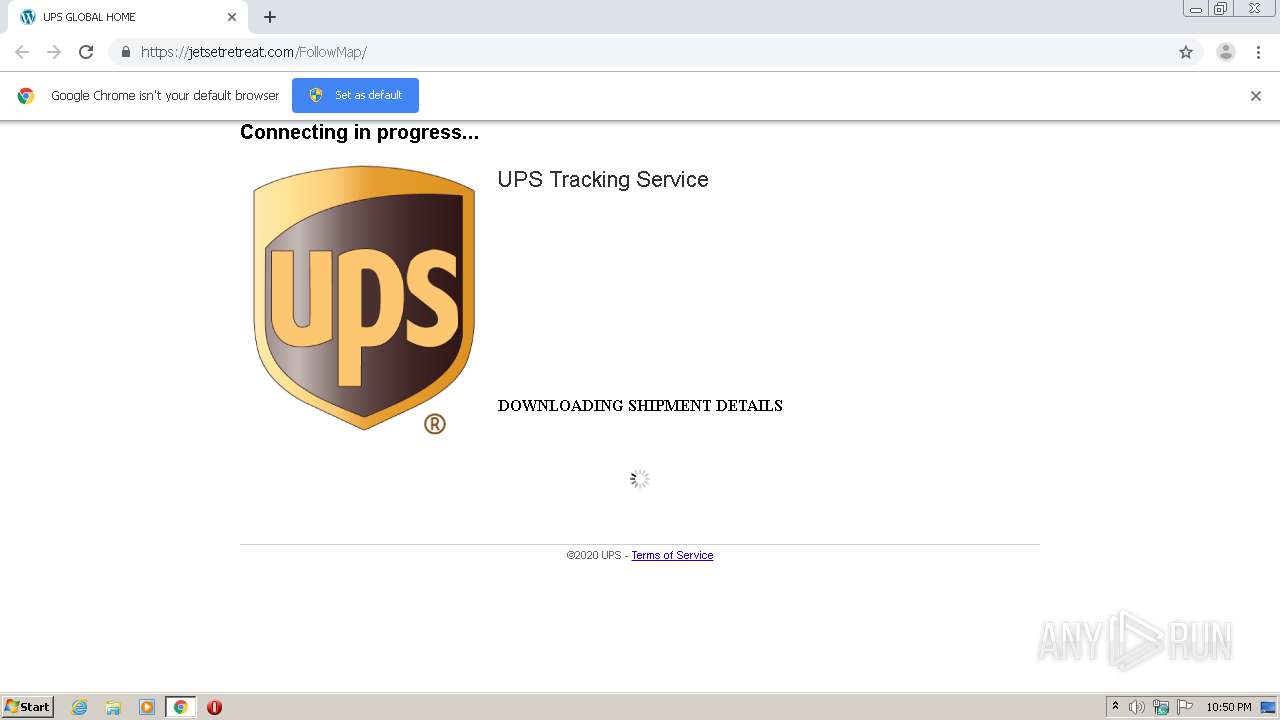
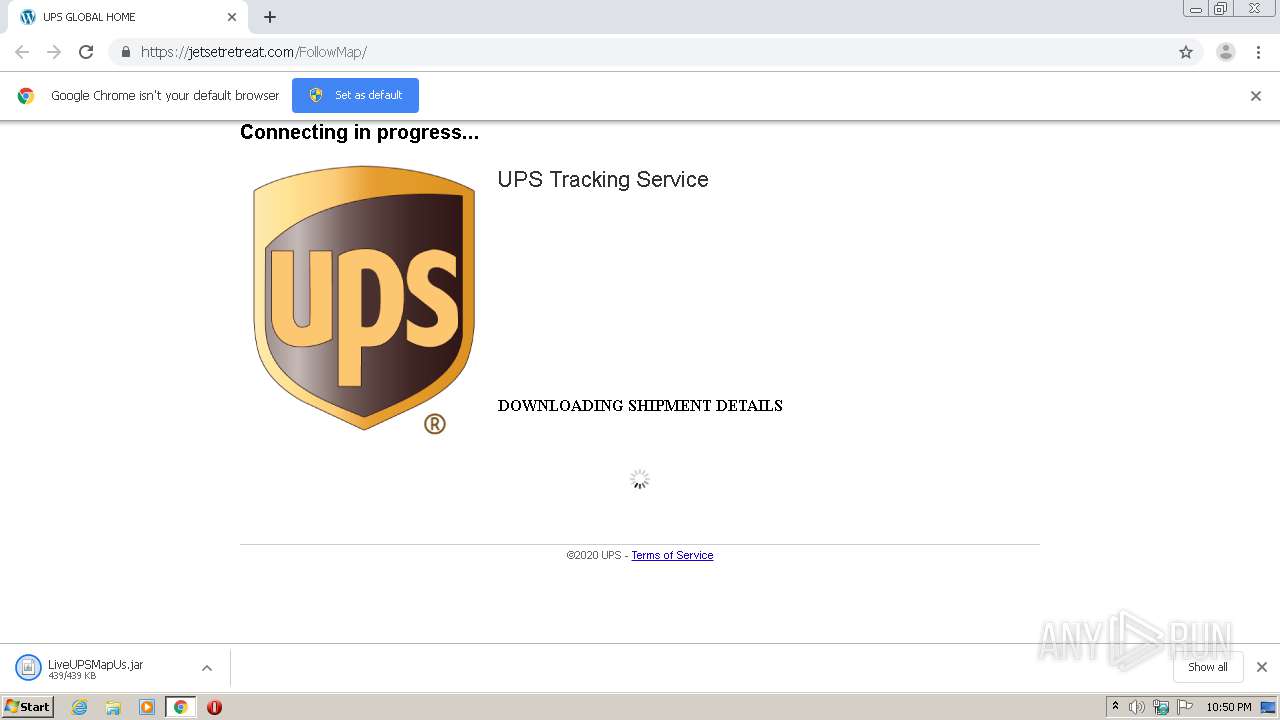
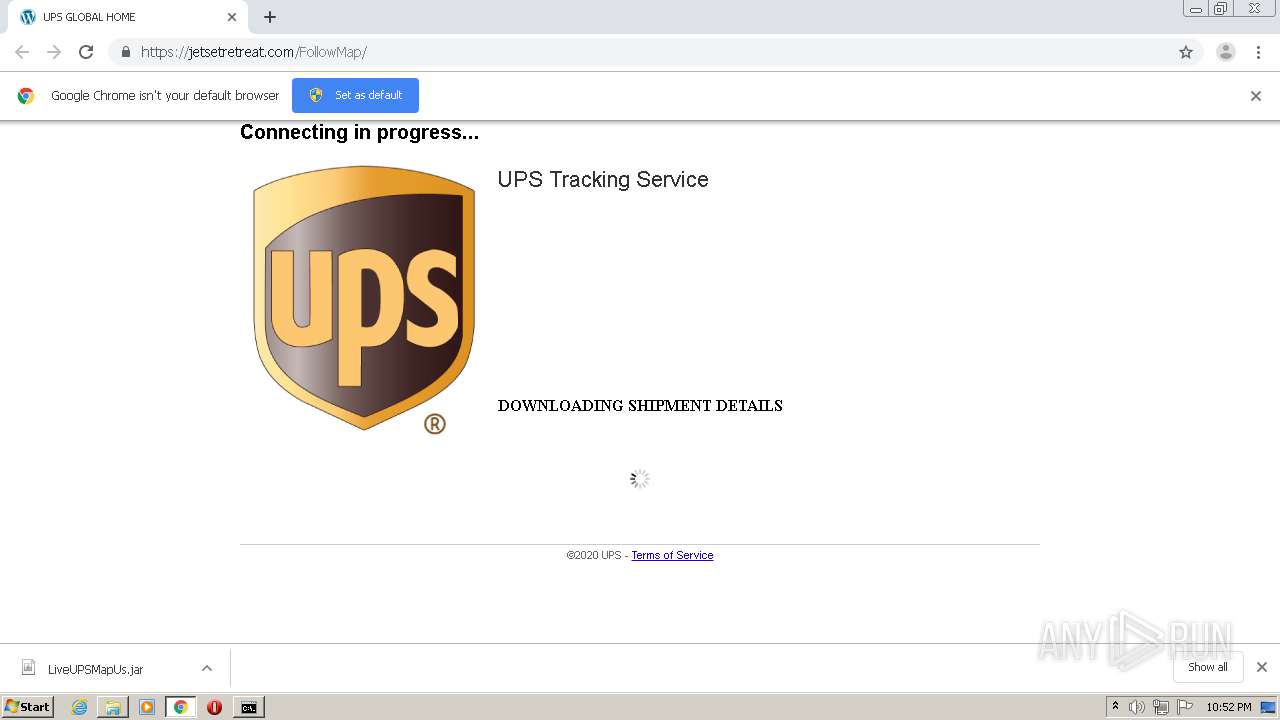
| URL: | http://track.smtpsendemail.com/9016770/c?p=zpeYx3MRyym6YKmlkKysCm3tFjsAfYvHF27yvetHCYzlXZojXwFLixqBLqE_4gEYvVO8ummFH5mhJ2YH-BG1UOwOQYZpIm7j5FRY26Ax2HKwxFrnwlbDE1c9FcVt9514mrTuHh3WMYokD2MojnbEog== |
| Full analysis: | https://app.any.run/tasks/d0a189b6-b052-4146-88e6-102163e60051 |
| Verdict: | Malicious activity |
| Analysis date: | July 21, 2020, 21:49:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 13139991A4F1DF239157E7385D6F8A64 |
| SHA1: | 59A4095C39582F380B7F6115BE928ACD4F0F1993 |
| SHA256: | 715F5F5EDF955BAE7BC5709F53BA155E4E2D4894A3F99040A45C55C2F0A4DFEC |
| SSDEEP: | 6:CKXvQI5KkUV4TAJkPdUug6hf938DUXtjLFhRTW/i8KlKI:/vQI51qJkPy0l9MDU9jBSa8Klp |
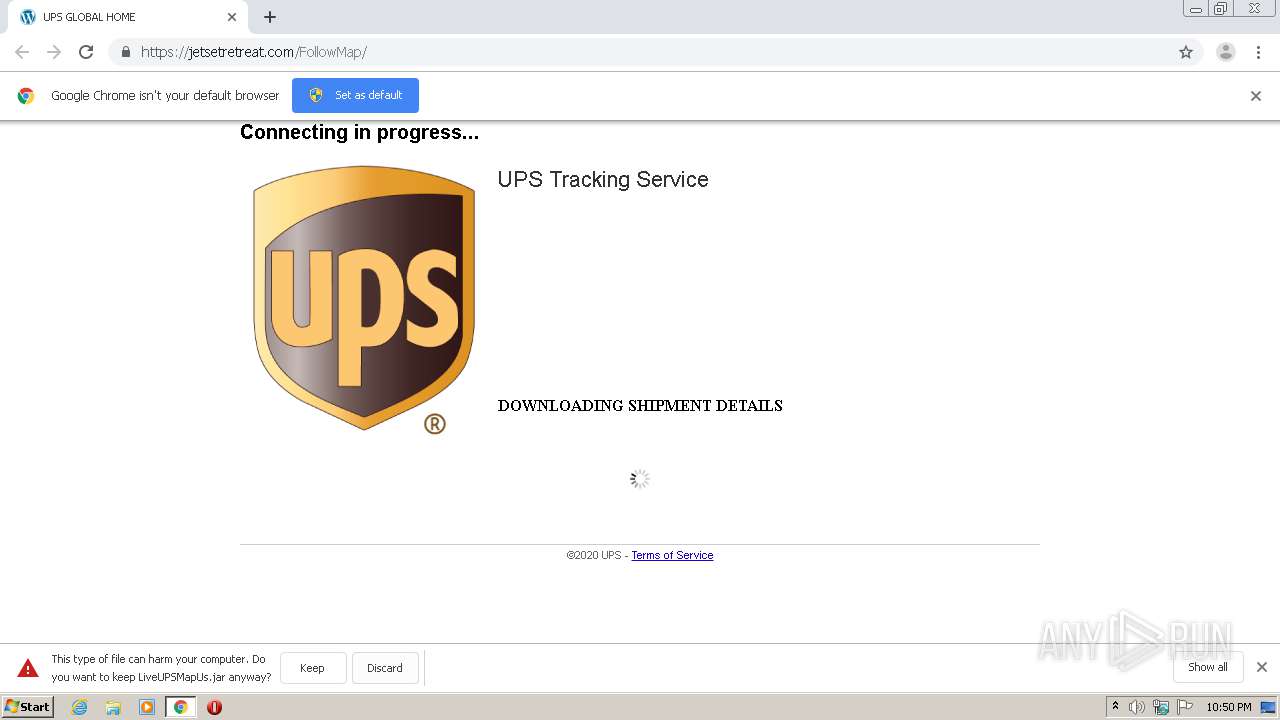
MALICIOUS
Runs app for hidden code execution
- javaw.exe (PID: 2920)
Loads dropped or rewritten executable
- javaw.exe (PID: 2920)
- explorer.exe (PID: 292)
- SearchProtocolHost.exe (PID: 2628)
- svchost.exe (PID: 804)
Changes the autorun value in the registry
- javaw.exe (PID: 2920)
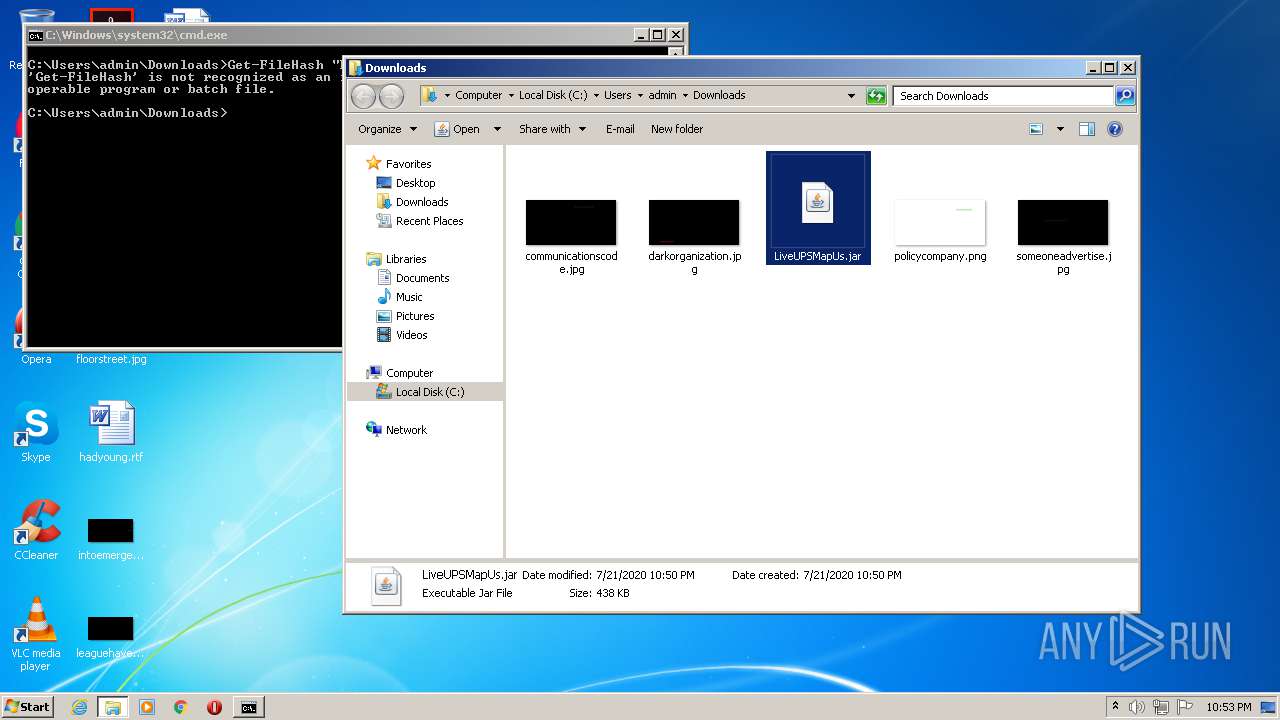
Application was dropped or rewritten from another process
- javaw.exe (PID: 2920)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2592)
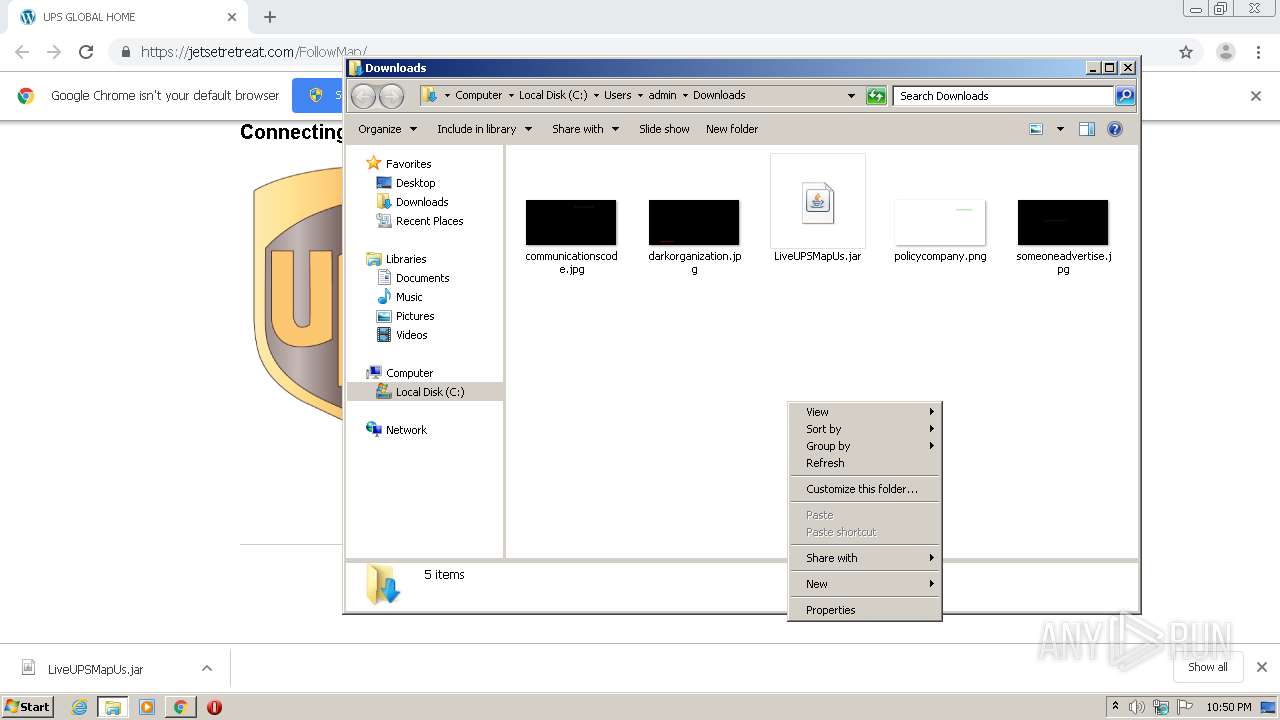
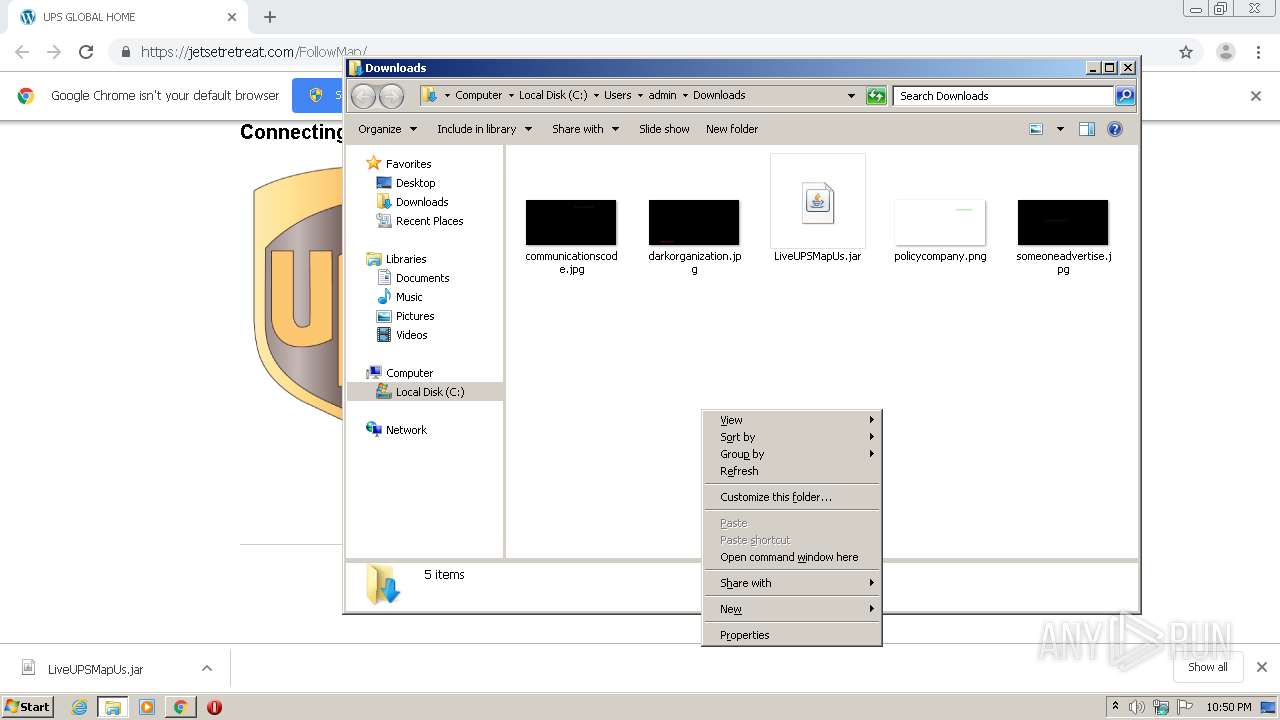
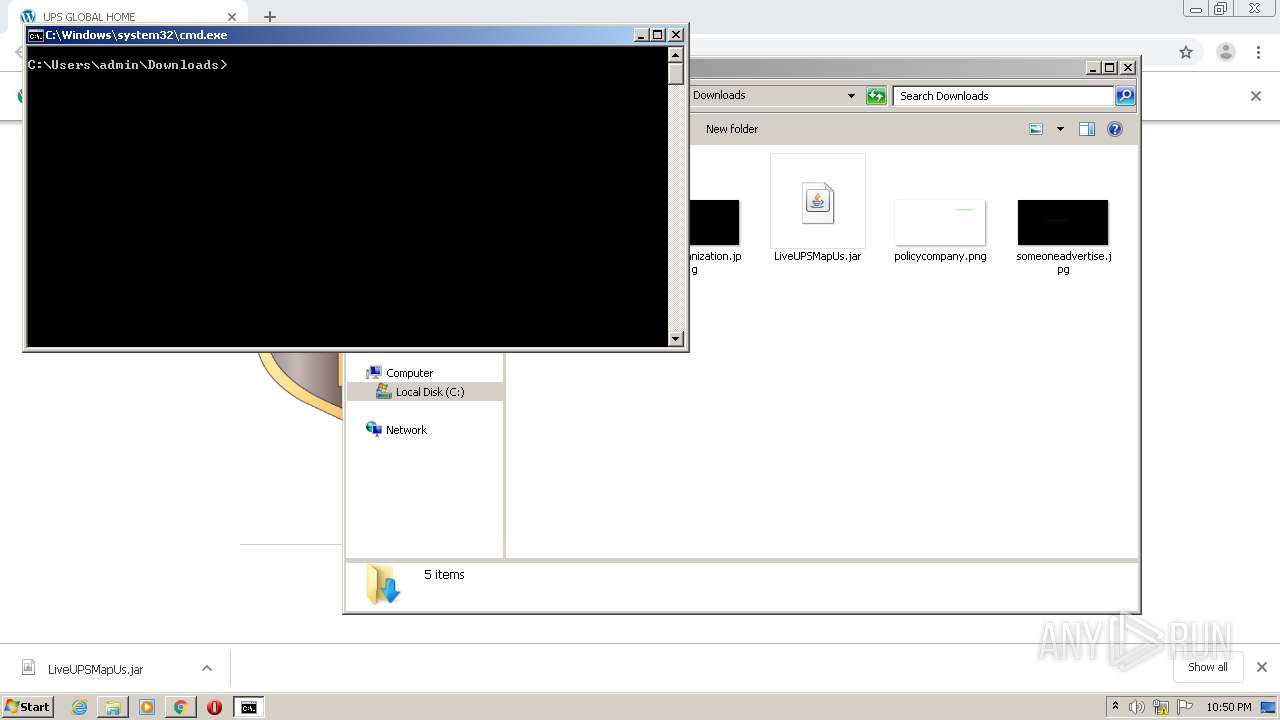
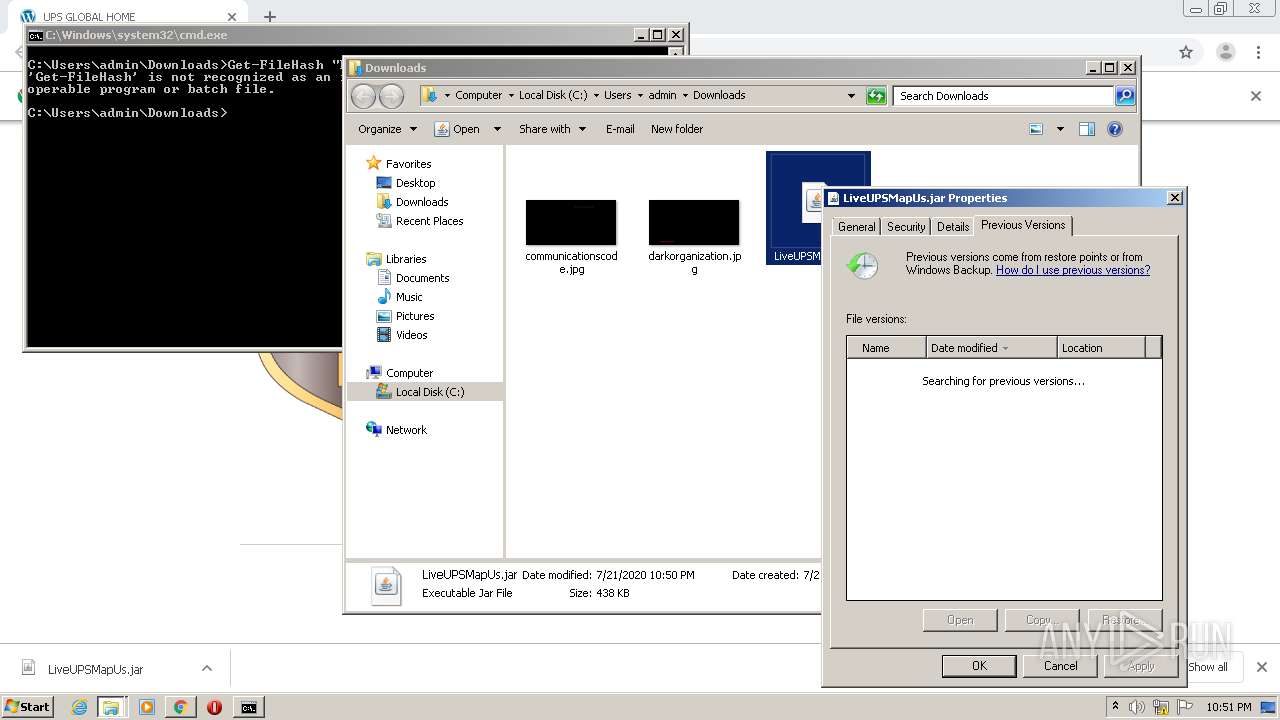
Starts CMD.EXE for commands execution
- javaw.exe (PID: 2920)
- explorer.exe (PID: 292)
Executes JAVA applets
- explorer.exe (PID: 292)
Uses WMIC.EXE to obtain a list of Firewalls
- cmd.exe (PID: 1640)
Uses WMIC.EXE to obtain a list of AntiViruses
- cmd.exe (PID: 1960)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 1640)
- cmd.exe (PID: 1960)
- cmd.exe (PID: 3632)
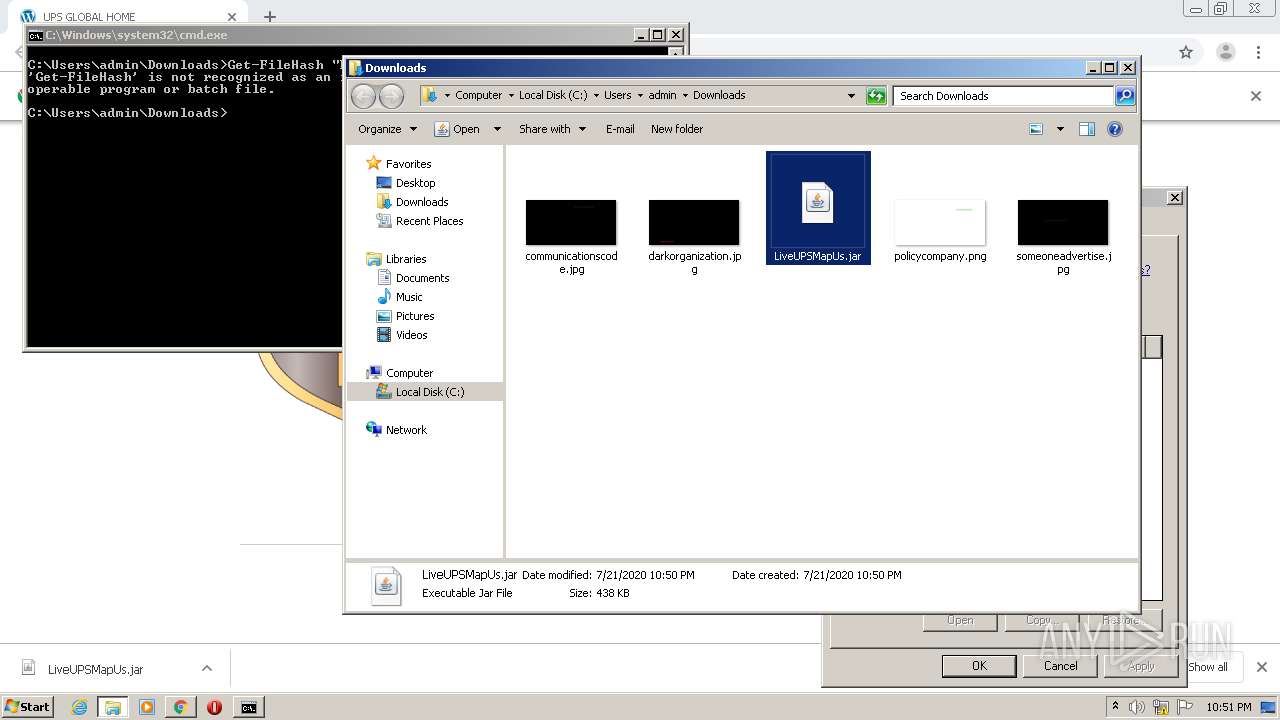
Creates files in the user directory
- javaw.exe (PID: 2920)
Executable content was dropped or overwritten
- javaw.exe (PID: 2920)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 2920)
Writes to a desktop.ini file (may be used to cloak folders)
- javaw.exe (PID: 2920)
Executes scripts
- javaw.exe (PID: 2920)
INFO
Application launched itself
- chrome.exe (PID: 2592)
Reads the hosts file
- chrome.exe (PID: 1828)
- chrome.exe (PID: 2592)
Reads Internet Cache Settings
- chrome.exe (PID: 2592)
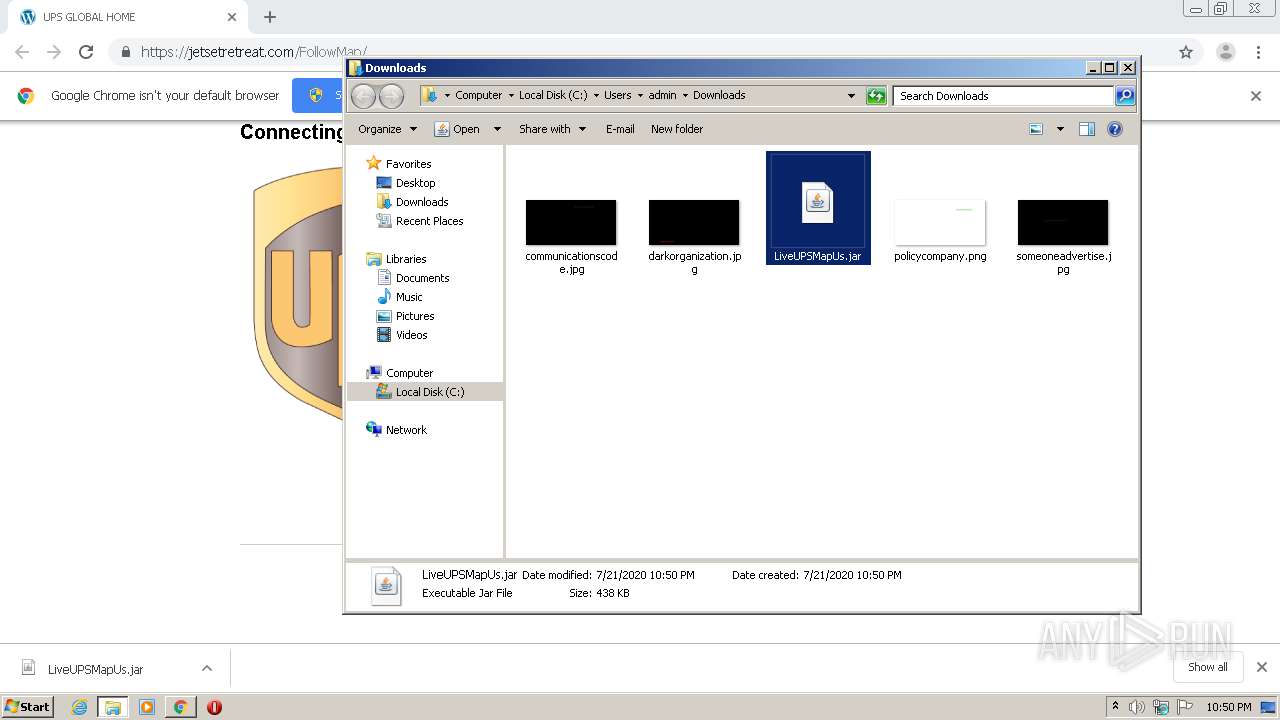
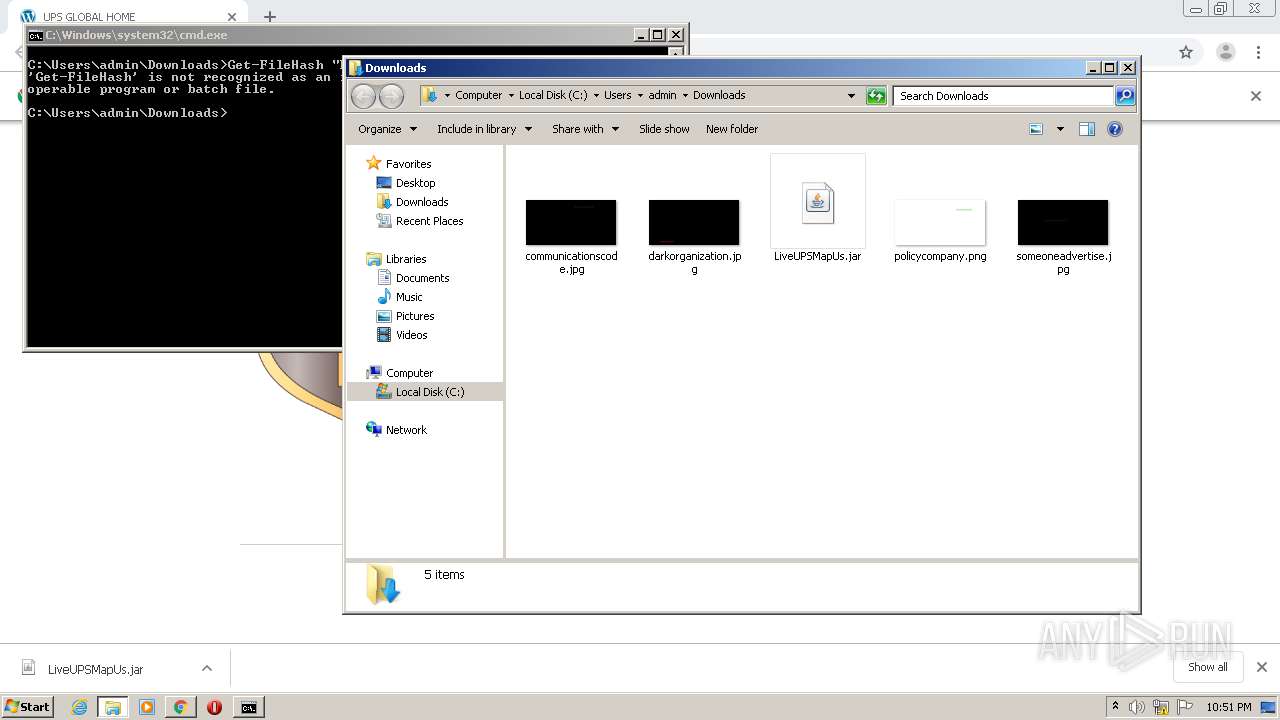
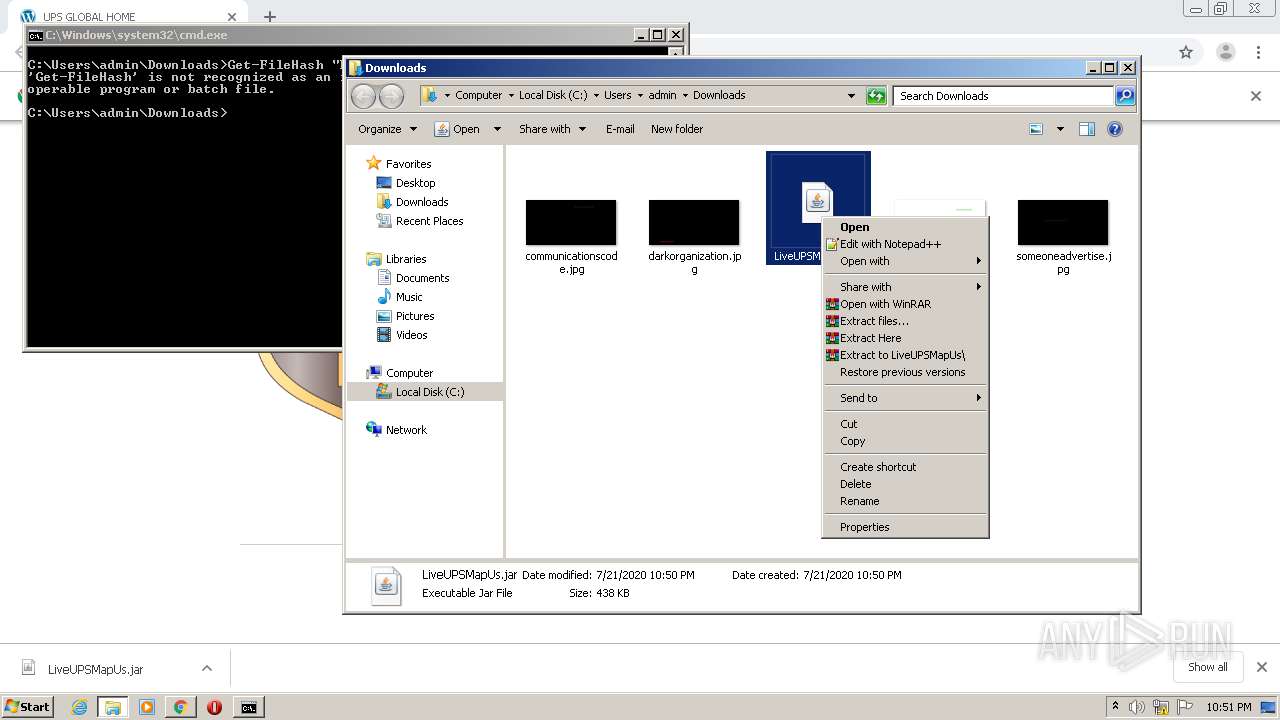
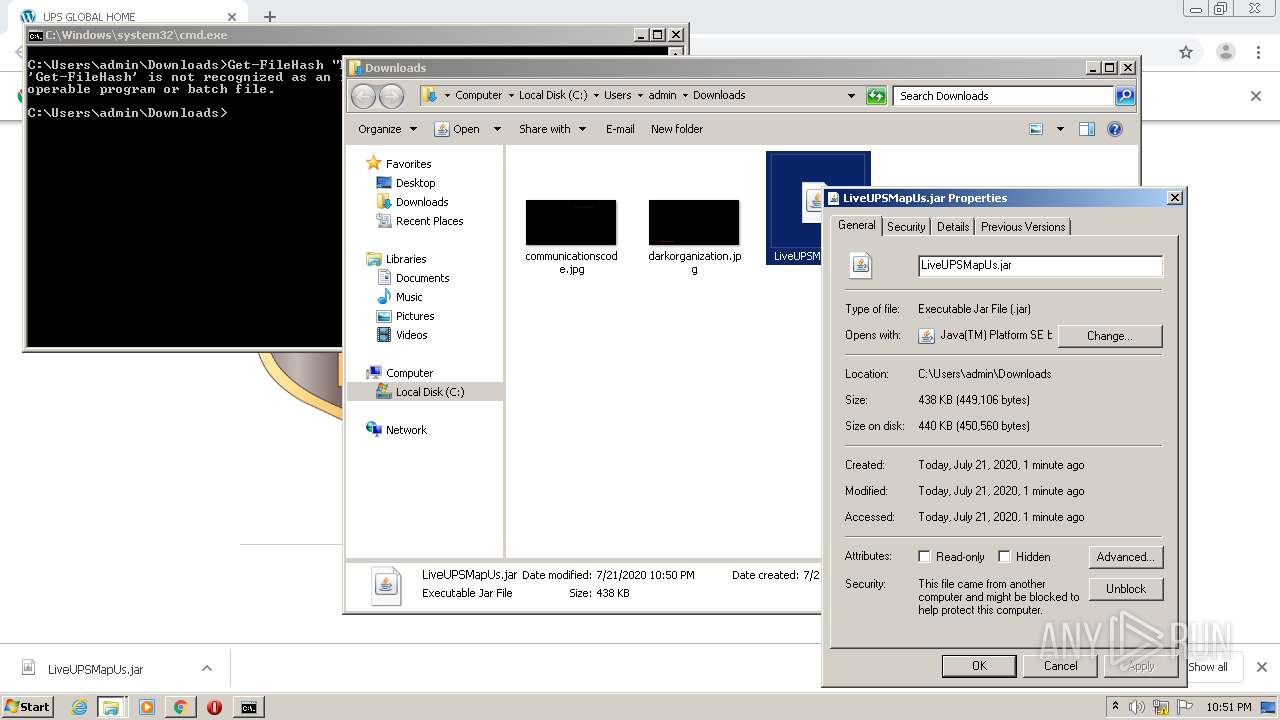
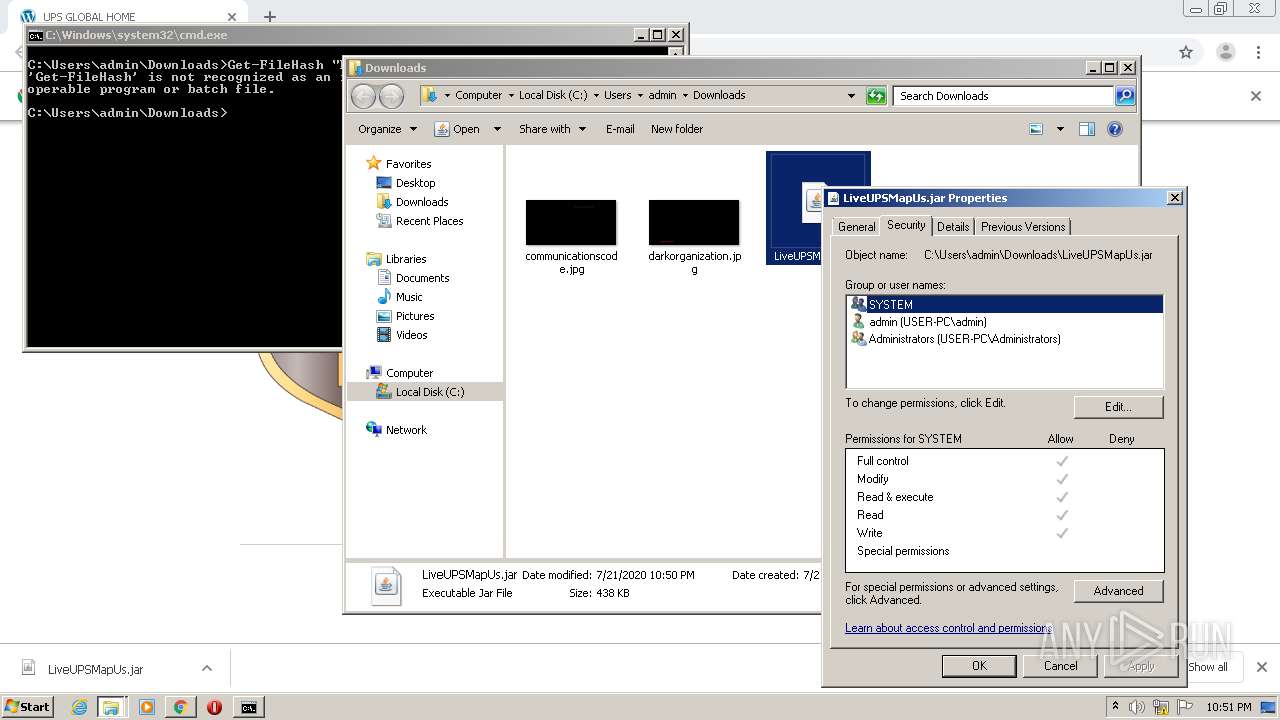
Manual execution by user
- javaw.exe (PID: 2920)
- cmd.exe (PID: 4064)
Reads settings of System Certificates
- chrome.exe (PID: 1828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
100
Monitored processes
49
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | C:\Windows\System32\wscript.exe //E:vbs C:\Users\admin\AppData\Local\Temp\ESBfexPNSzA7274844851927211522.vbs | C:\Windows\System32\wscript.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 704 | WMIC /Node:localhost /Namespace:\\root\SecurityCenter2 Path FirewallProduct Get displayName /Format:List | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,14339148993326063126,13442253081672001389,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5840428720684963421 --mojo-platform-channel-handle=3556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,14339148993326063126,13442253081672001389,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11333961645724324148 --mojo-platform-channel-handle=4252 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 804 | C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,14339148993326063126,13442253081672001389,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15244936932442883508 --mojo-platform-channel-handle=4328 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 968 | wmic /Node:localhost /Namespace:\\root\cimv2 Path Win32_PnpSignedDriver Get /Format:List | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1640 | cmd.exe | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,14339148993326063126,13442253081672001389,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12684144041896809694 --mojo-platform-channel-handle=976 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 097
Read events
1 878
Write events
212
Delete events
7
Modification events
| (PID) Process: | (2592) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2592) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2592) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2592) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2592) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2592-13239841792723625 |
Value: 259 | |||
| (PID) Process: | (2592) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2592) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2592) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2592) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
113
Suspicious files
28
Text files
324
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F176301-A20.pma | — | |
MD5:— | SHA256:— | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\48aaf753-fa80-4775-a032-22689ed0ee5f.tmp | — | |
MD5:— | SHA256:— | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF110a7c.TMP | text | |
MD5:— | SHA256:— | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF110a3e.TMP | text | |
MD5:— | SHA256:— | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1109c1.TMP | text | |
MD5:— | SHA256:— | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2592 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF110bb5.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
25
DNS requests
16
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1828 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
1828 | chrome.exe | GET | 302 | 192.40.165.109:80 | http://track.smtpsendemail.com/9016770/c?p=zpeYx3MRyym6YKmlkKysCm3tFjsAfYvHF27yvetHCYzlXZojXwFLixqBLqE_4gEYvVO8ummFH5mhJ2YH-BG1UOwOQYZpIm7j5FRY26Ax2HKwxFrnwlbDE1c9FcVt9514mrTuHh3WMYokD2MojnbEog== | US | — | — | whitelisted |
1828 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNmRlQUFXU0o1UkNFTWx3aGRUUHBsWUJUZw/7819.902.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
1828 | chrome.exe | GET | 200 | 74.125.168.7:80 | http://r2---sn-q0cedn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=78.153.204.5&mm=28&mn=sn-q0cedn7s&ms=nvh&mt=1595367731&mv=u&mvi=2&pl=19&shardbypass=yes | US | crx | 293 Kb | whitelisted |
1828 | chrome.exe | GET | 200 | 74.125.168.10:80 | http://r5---sn-q0cedn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNmRlQUFXU0o1UkNFTWx3aGRUUHBsWUJUZw/7819.902.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=8p&mip=78.153.204.5&mm=28&mn=sn-q0cedn7s&ms=nvh&mt=1595367731&mv=u&mvi=5&pl=19&shardbypass=yes | US | crx | 824 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
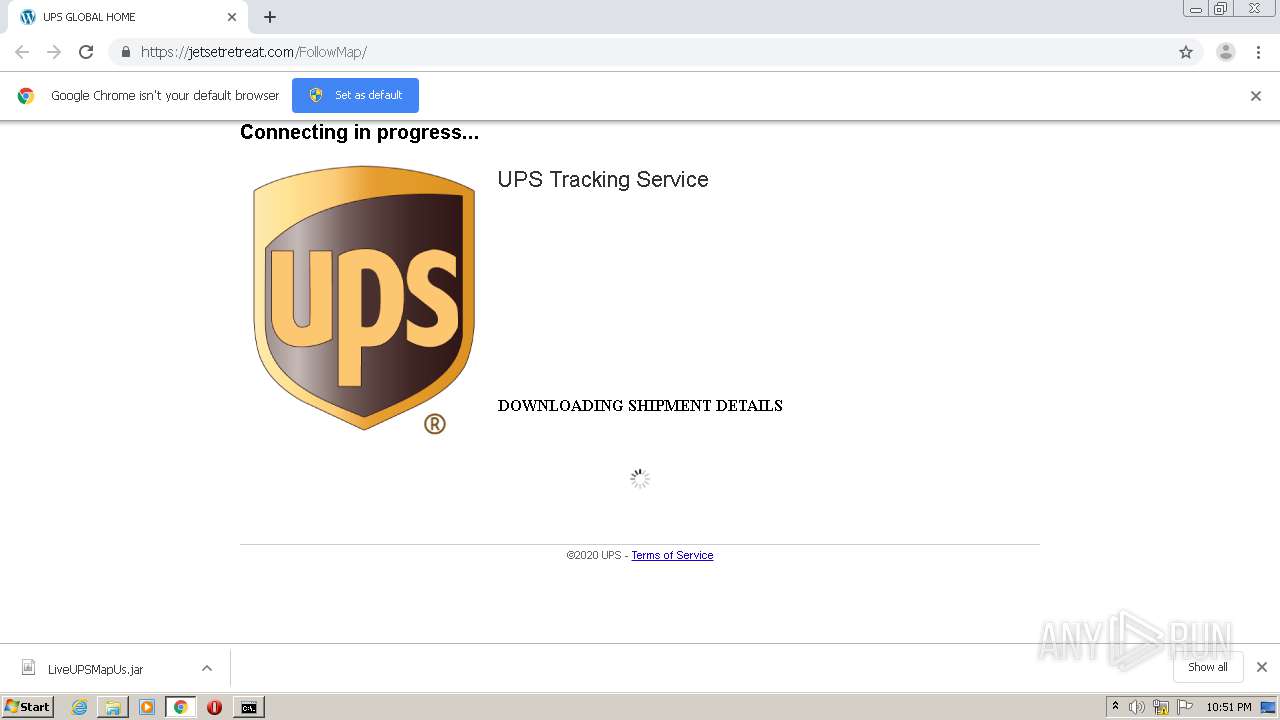
1828 | chrome.exe | 192.40.165.109:80 | track.smtpsendemail.com | SMTP, Inc. | US | suspicious |
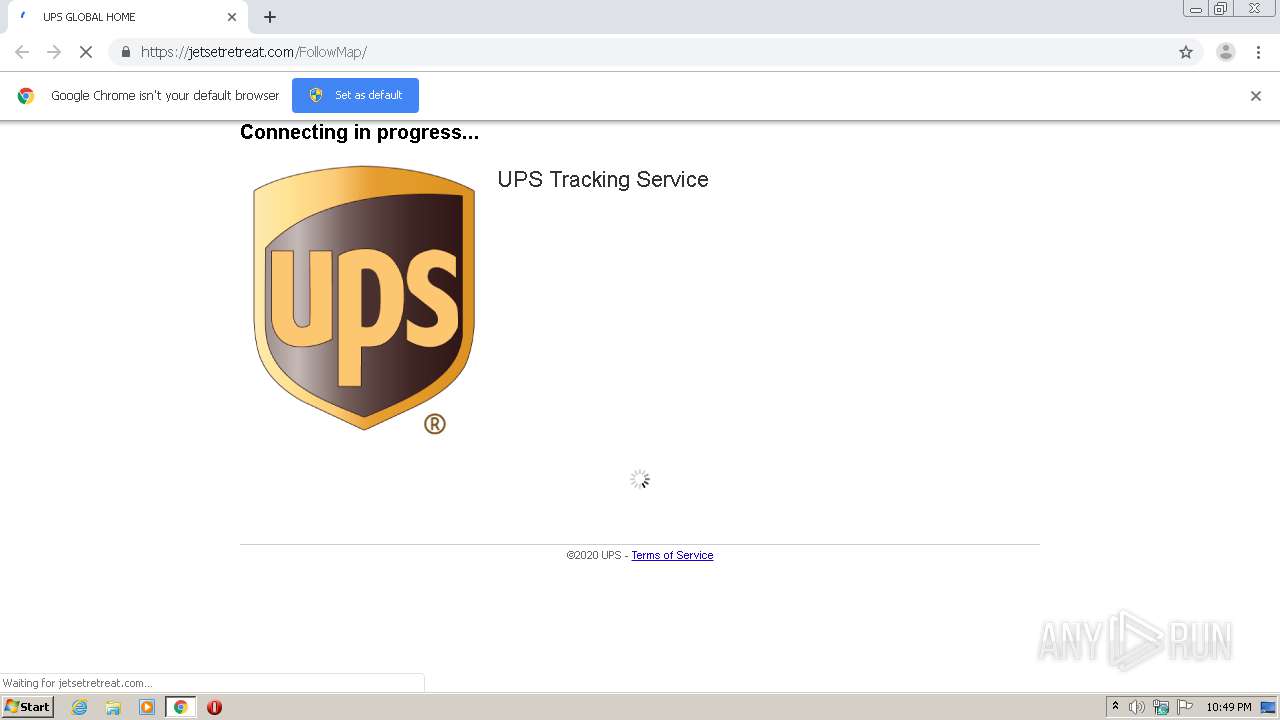
1828 | chrome.exe | 96.125.173.132:443 | jetsetretreat.com | CyrusOne LLC | US | unknown |
1828 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
1828 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
1828 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
1828 | chrome.exe | 172.217.22.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1828 | chrome.exe | 216.58.206.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1828 | chrome.exe | 74.125.168.10:80 | r5---sn-q0cedn7s.gvt1.com | Google Inc. | US | whitelisted |
1828 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1828 | chrome.exe | 74.125.168.7:80 | r2---sn-q0cedn7s.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
track.smtpsendemail.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
jetsetretreat.com |
| unknown |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r2---sn-q0cedn7s.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
r5---sn-q0cedn7s.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1040 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |