| URL: | http://www.furnituremediclv.com |
| Full analysis: | https://app.any.run/tasks/b37db2de-789b-4ca2-afd1-976530118704 |
| Verdict: | Malicious activity |
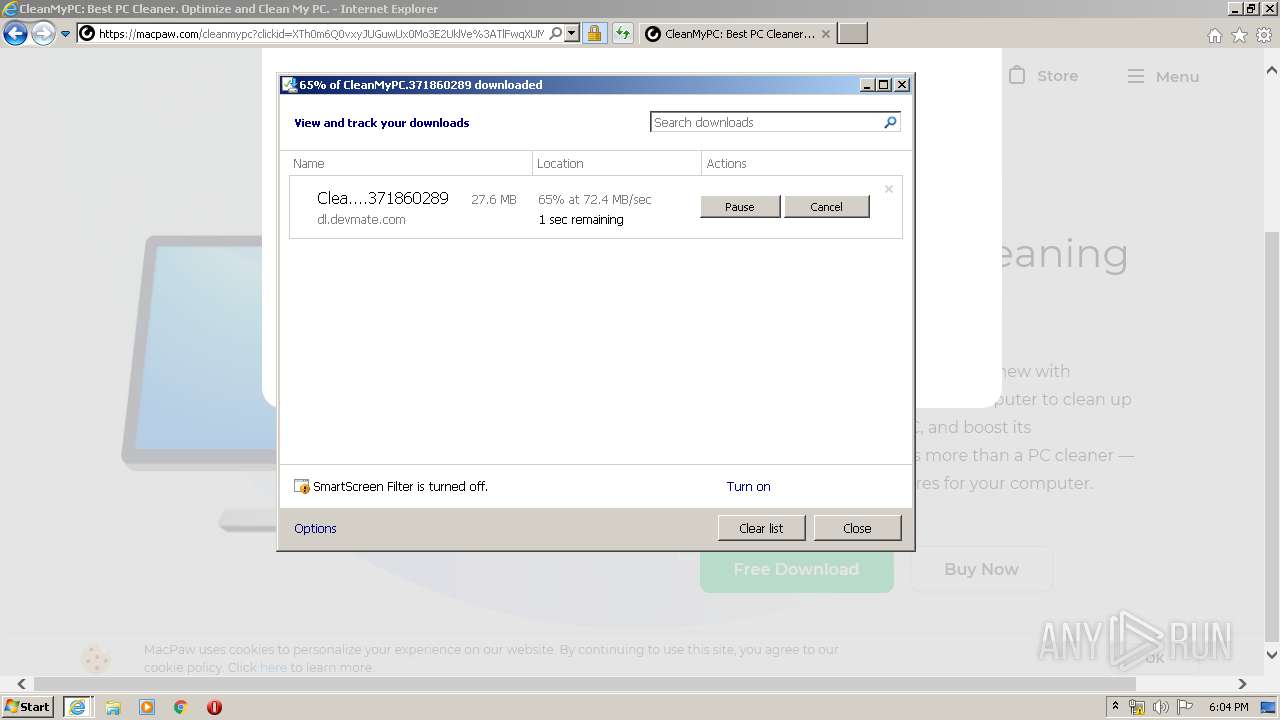
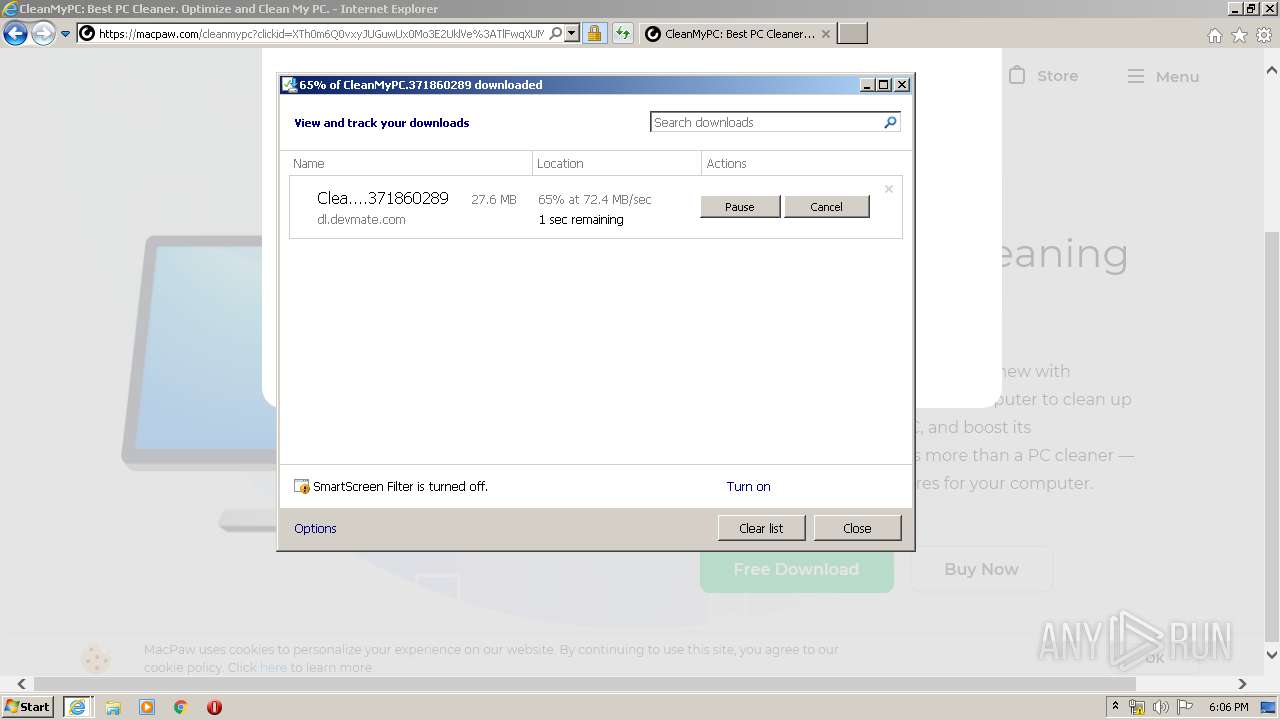
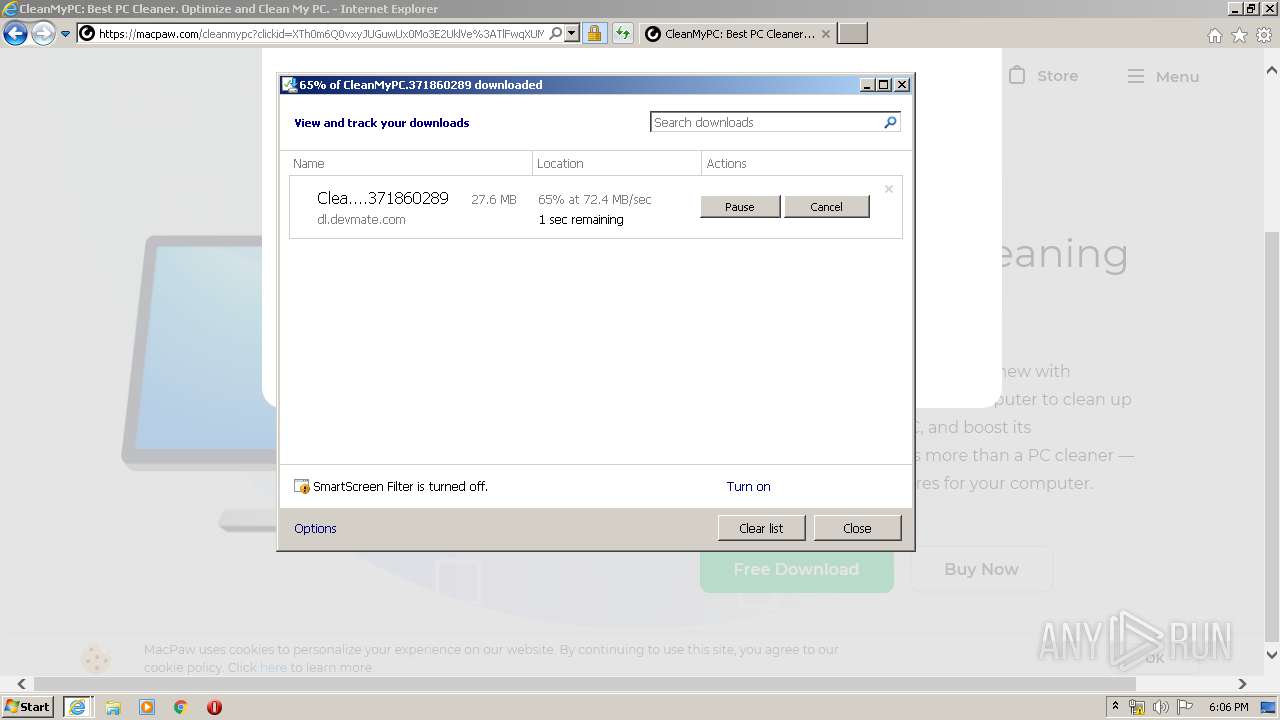
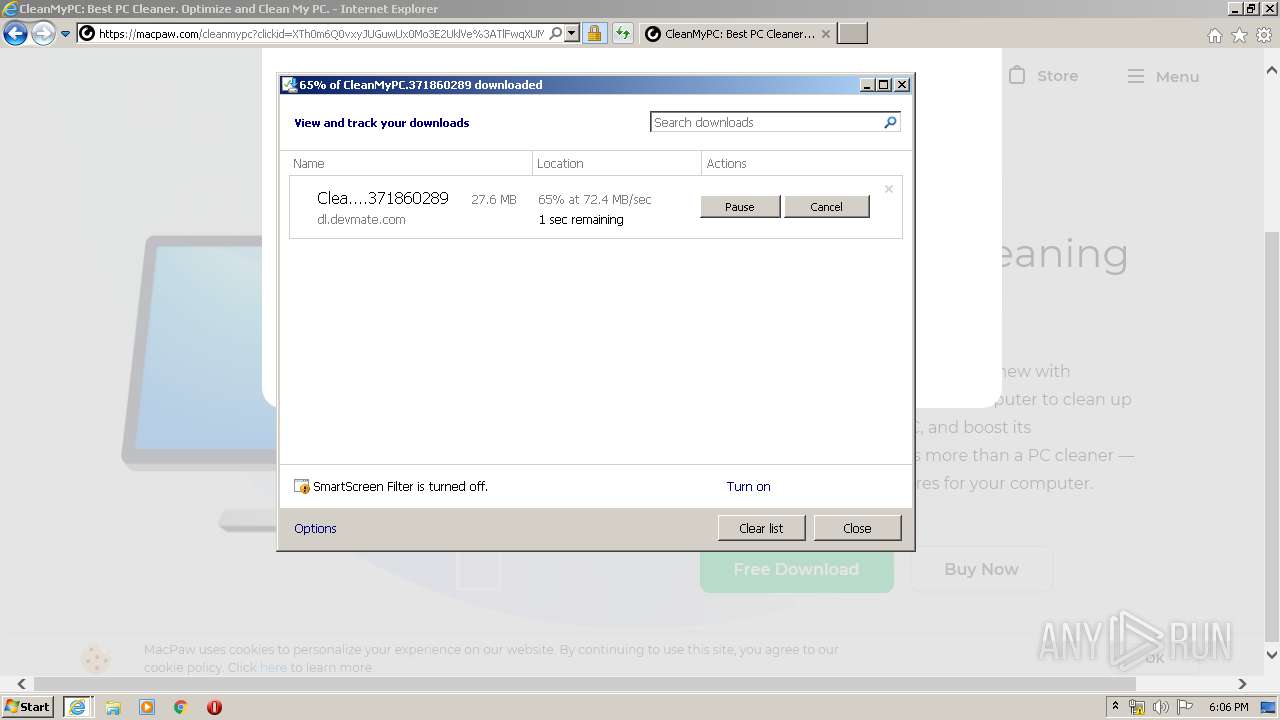
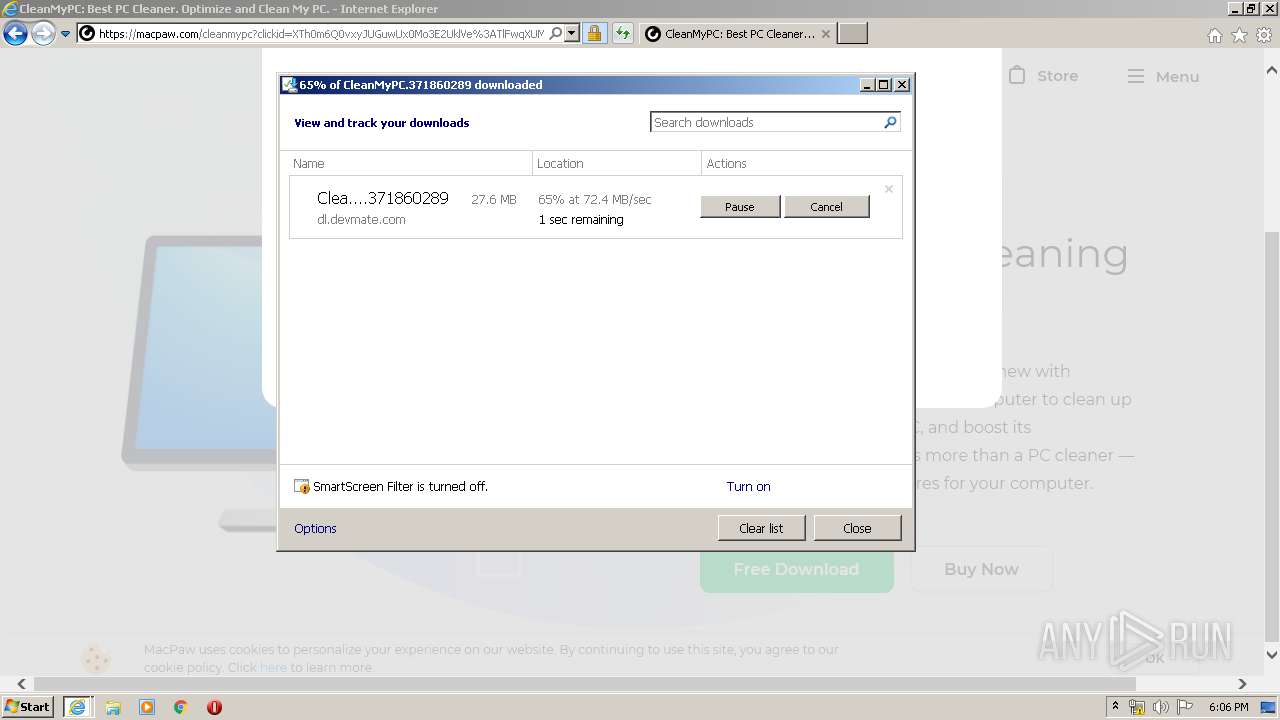
| Analysis date: | February 21, 2020, 18:02:26 |
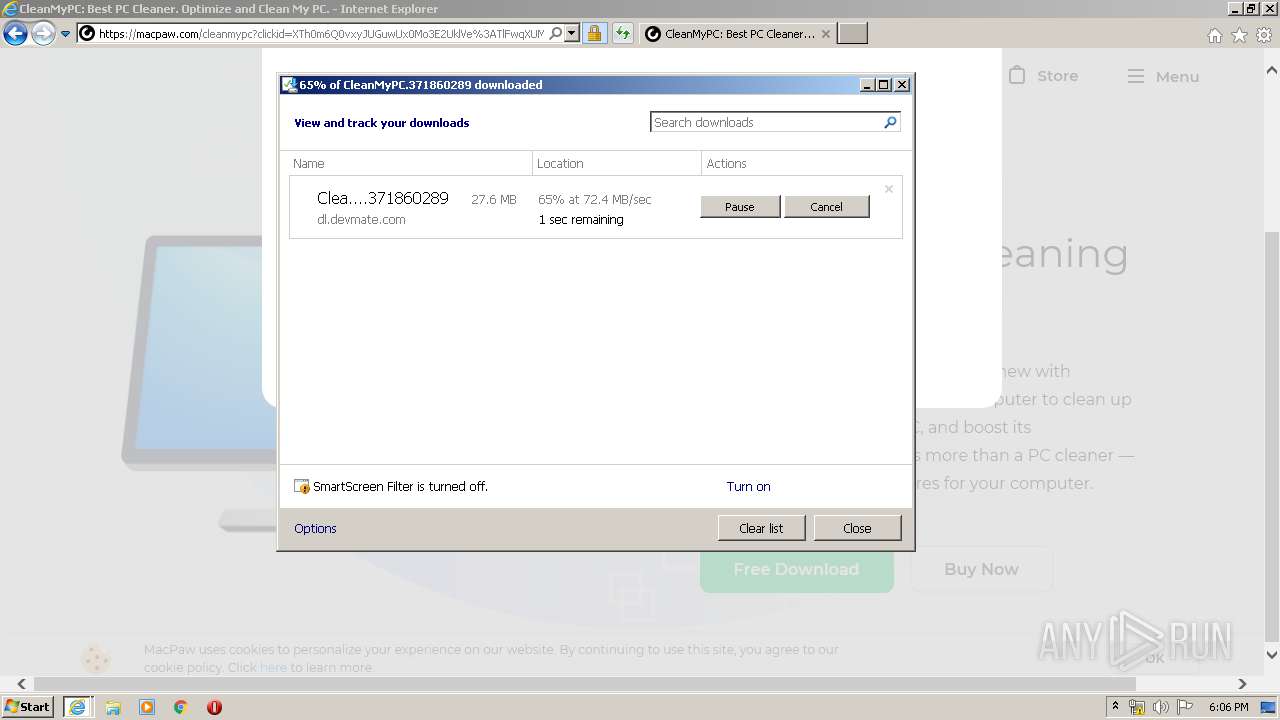
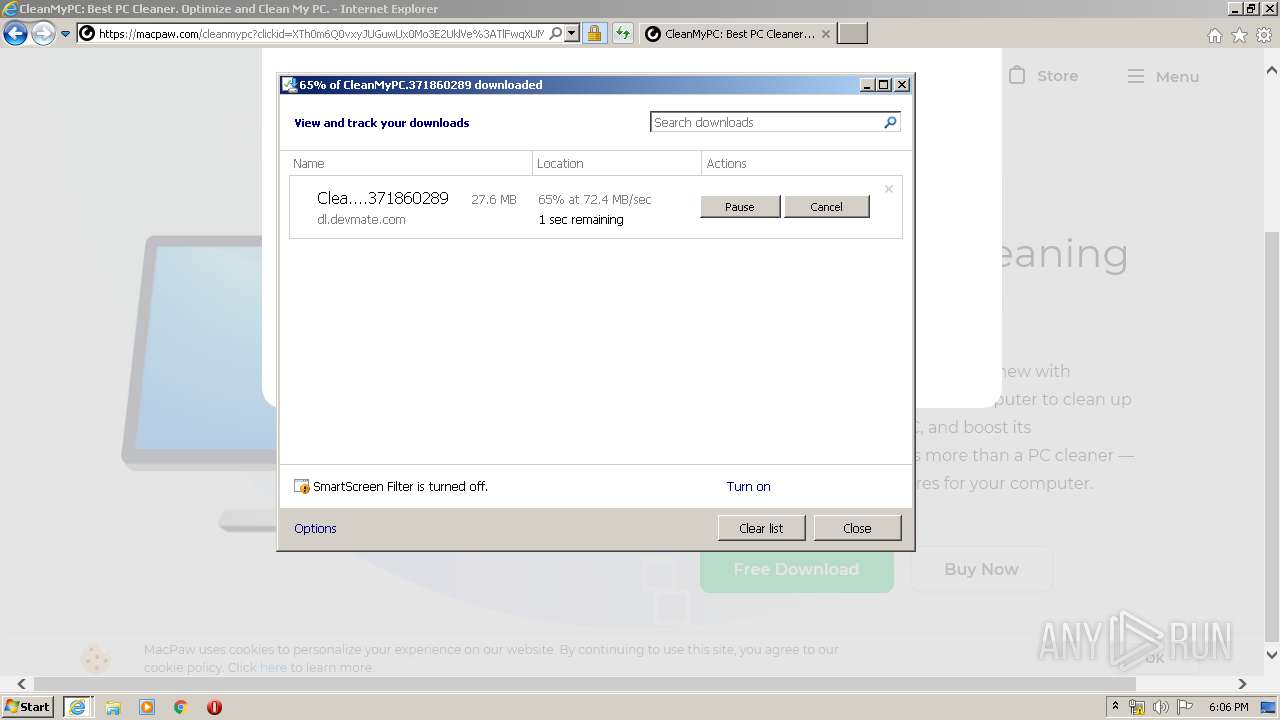
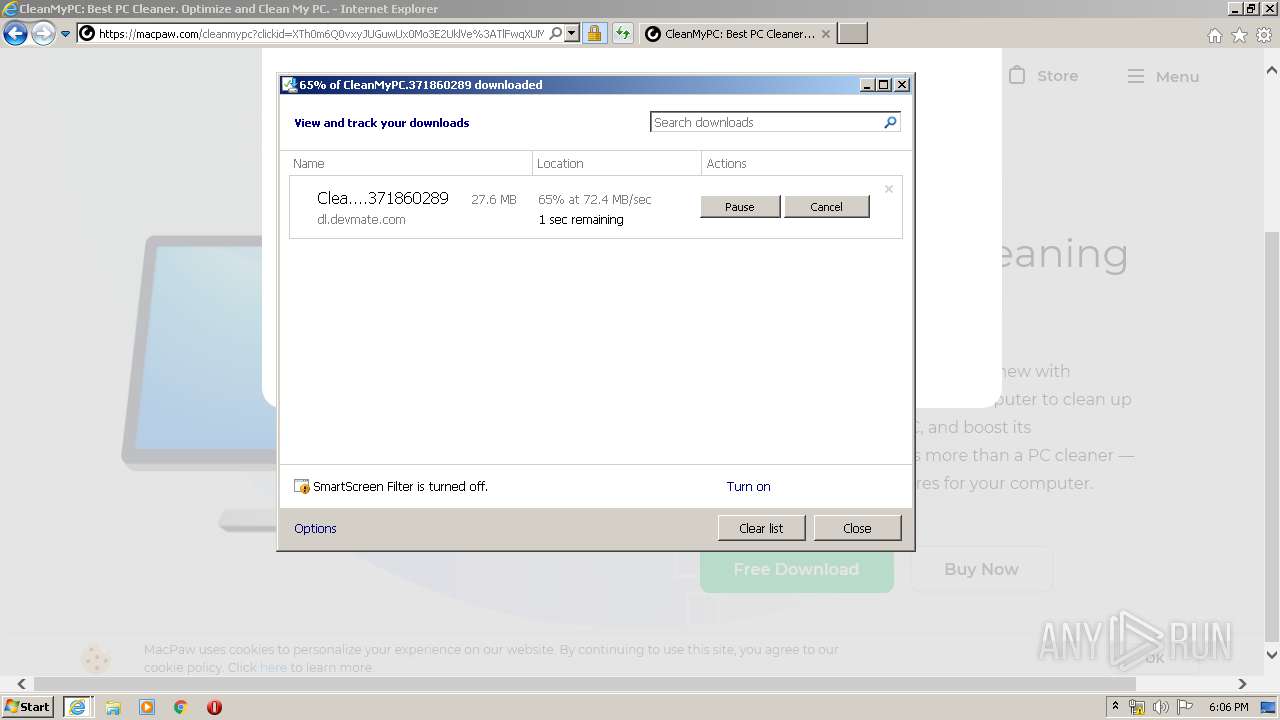
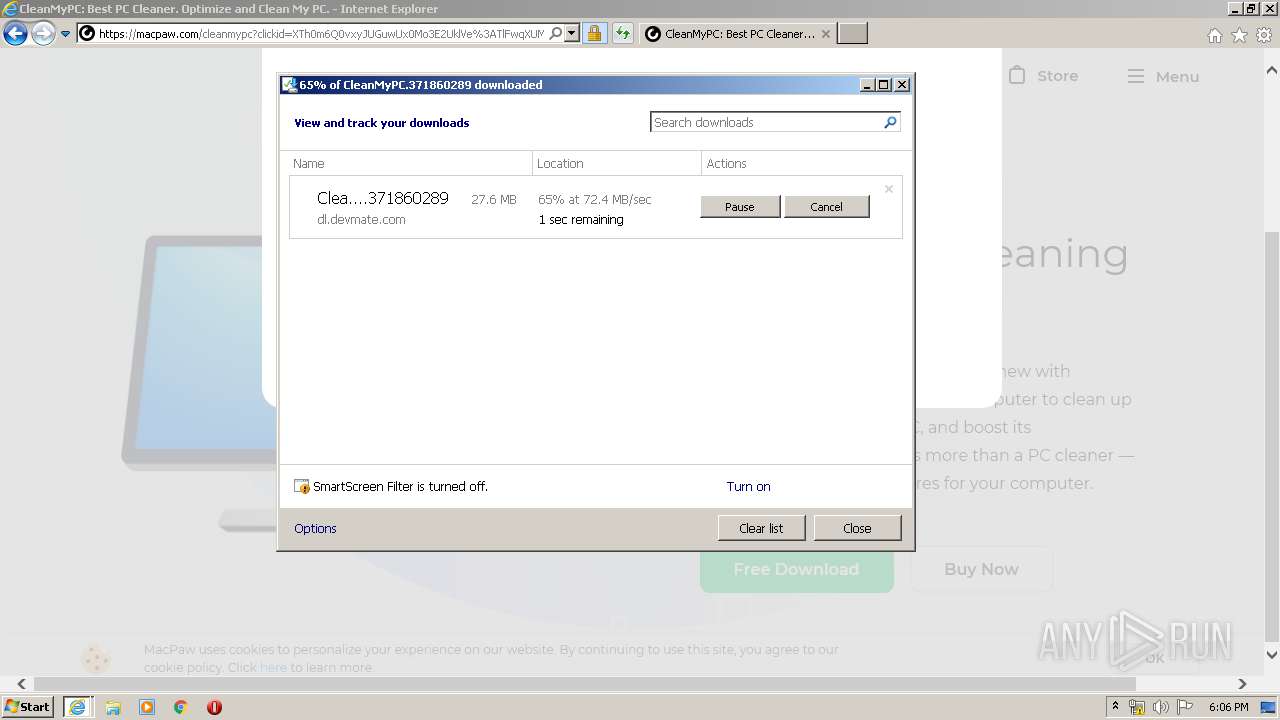
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2F453E7AF5DDCC4E354C478C50B72D3E |
| SHA1: | DE7D9C40DD3A9B40BFCC28D520662AA4832AD3A8 |
| SHA256: | 7147B75F112E86282237EAA65032AD9FD320A5ADC2C92EB211814078D80621E4 |
| SSDEEP: | 3:N1KJS4MbyIFGJT2:Cc4Mbys |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 1748)
Reads Internet Cache Settings
- iexplore.exe (PID: 1748)
- iexplore.exe (PID: 3252)
Application launched itself
- iexplore.exe (PID: 1748)
Reads settings of System Certificates
- iexplore.exe (PID: 3252)
- iexplore.exe (PID: 1748)
Reads internet explorer settings
- iexplore.exe (PID: 3252)
Creates files in the user directory
- iexplore.exe (PID: 1748)
- iexplore.exe (PID: 3252)
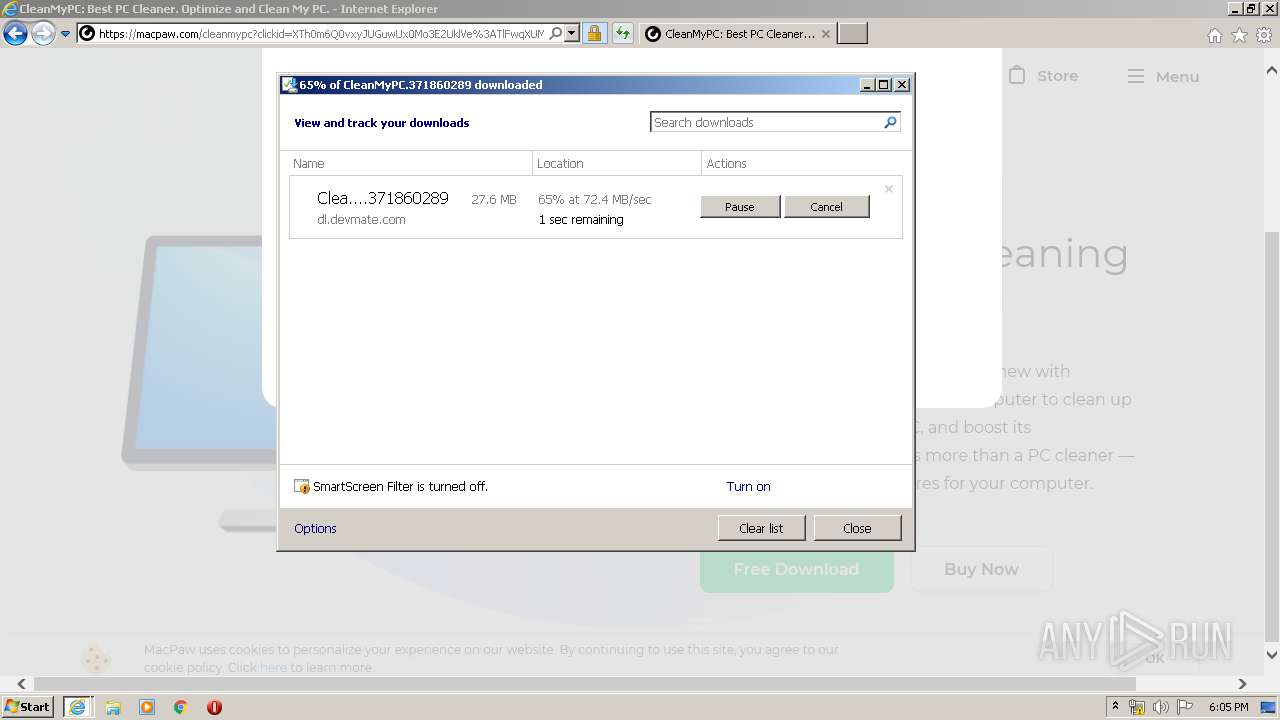
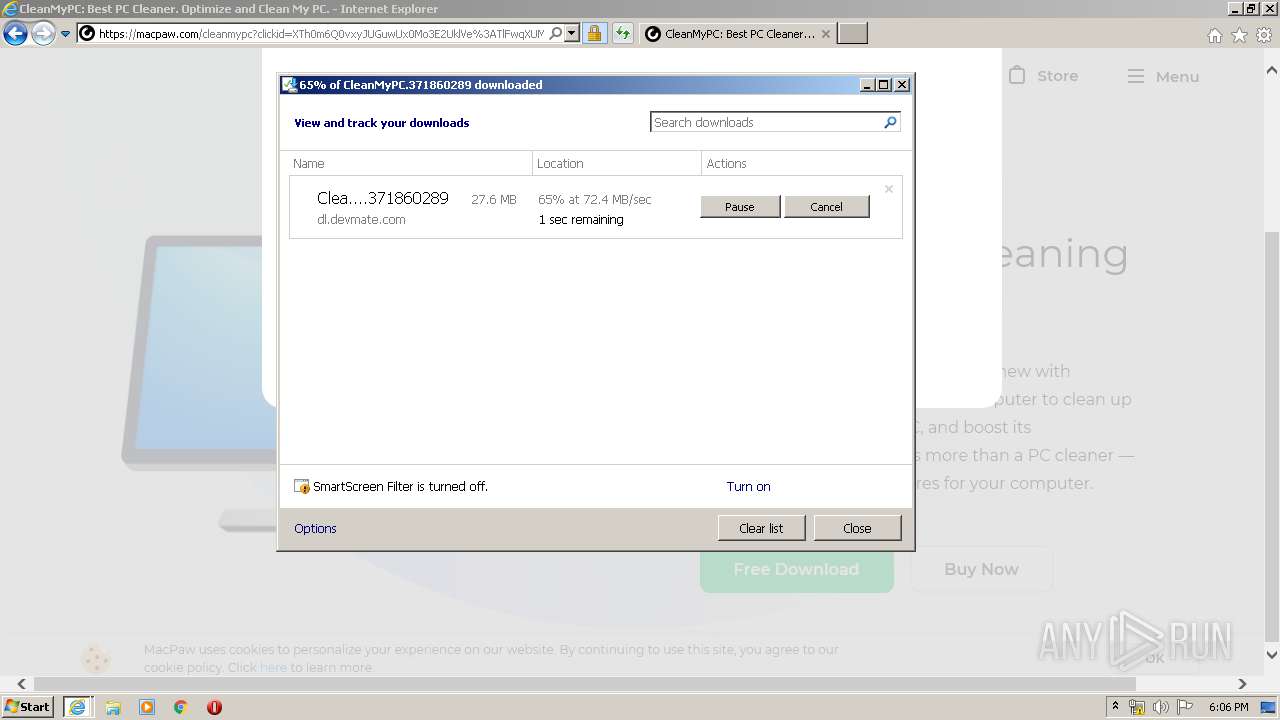
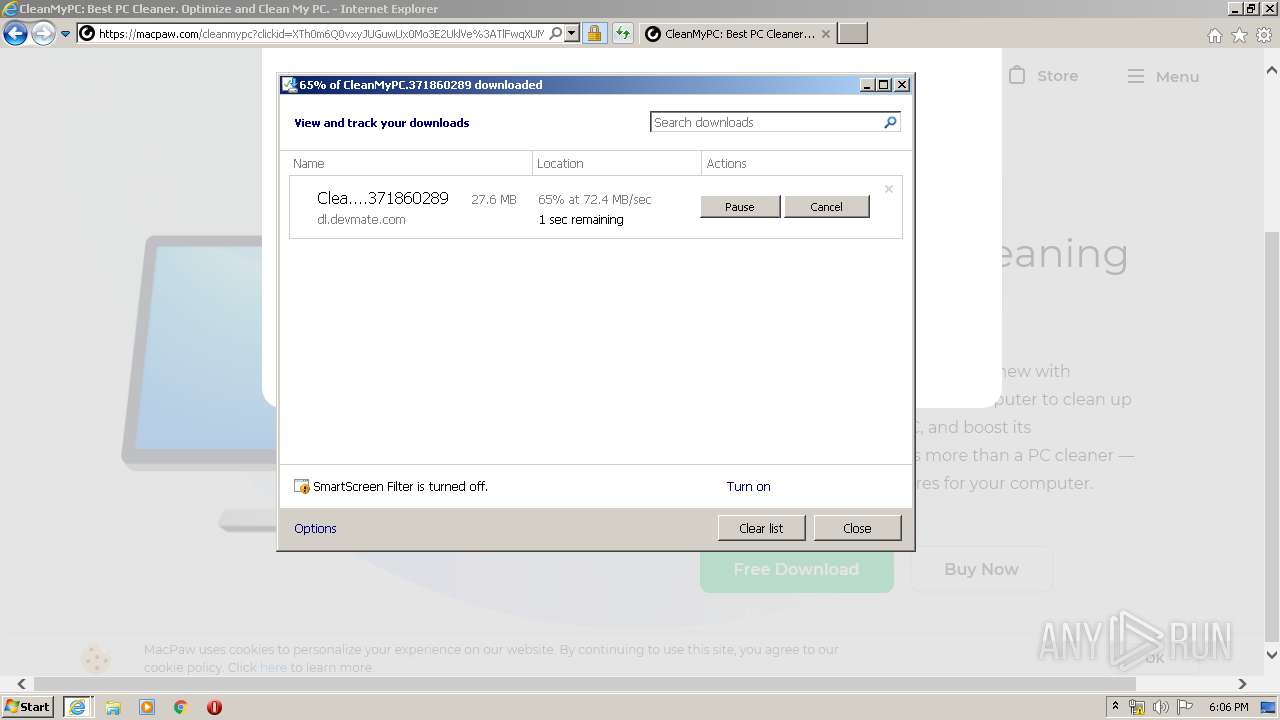
Modifies the phishing filter of IE
- iexplore.exe (PID: 1748)
Changes settings of System certificates
- iexplore.exe (PID: 1748)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1748 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.furnituremediclv.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3252 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1748 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 871
Read events
1 074
Write events
3 903
Delete events
1 894
Modification events
| (PID) Process: | (3252) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3252) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3252) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 778251704 | |||
| (PID) Process: | (1748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30796001 | |||
| (PID) Process: | (1748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
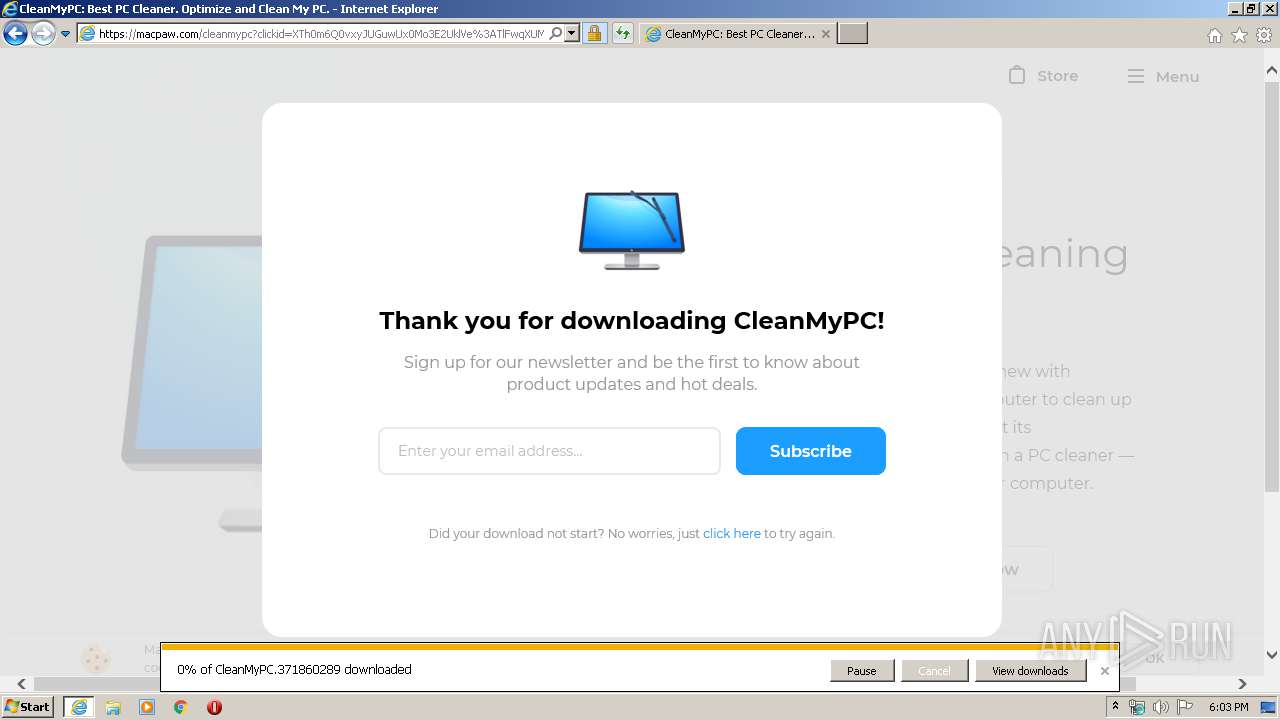
Executable files
0
Suspicious files
165
Text files
103
Unknown types
77
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8C89.tmp | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8C8A.tmp | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\KKW686VR.txt | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\RZF6ZES4.txt | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\EBLOKCBZ.txt | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\U9NR0FD2.txt | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PGXAICWX.txt | text | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\8QU1CQCK.txt | text | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\1UAOJV3W.htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
80
TCP/UDP connections
137
DNS requests
64
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
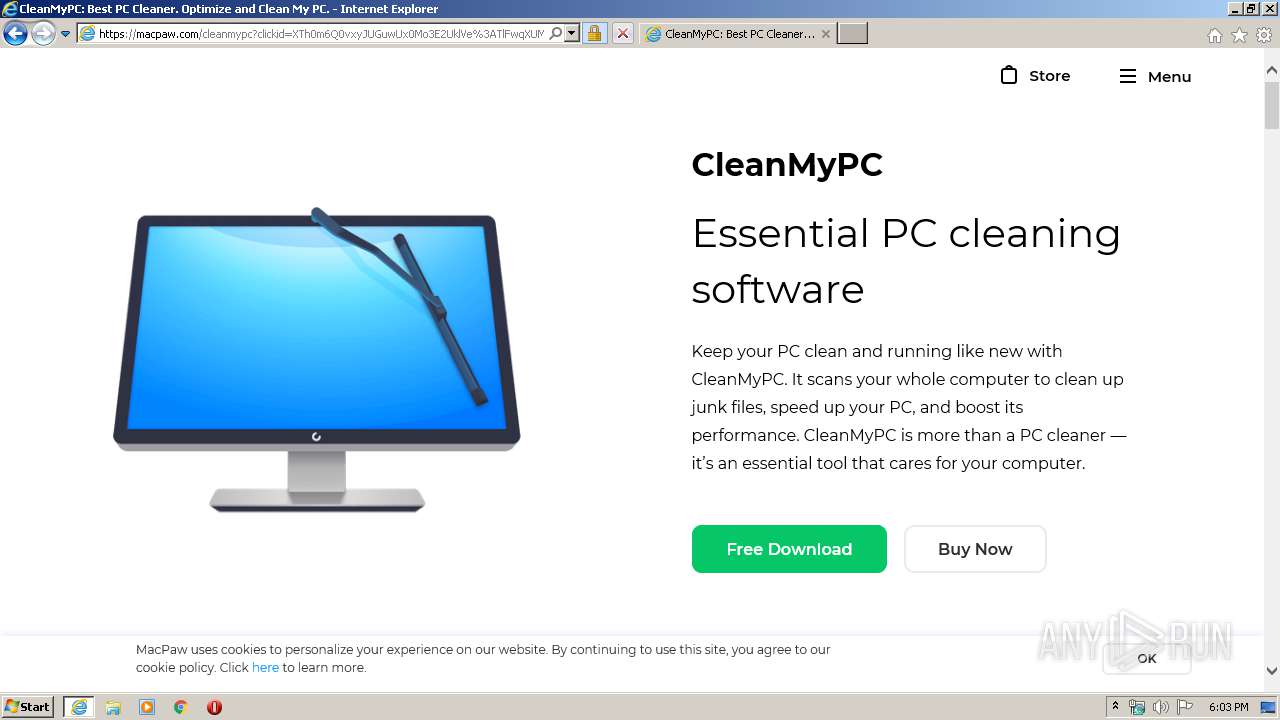
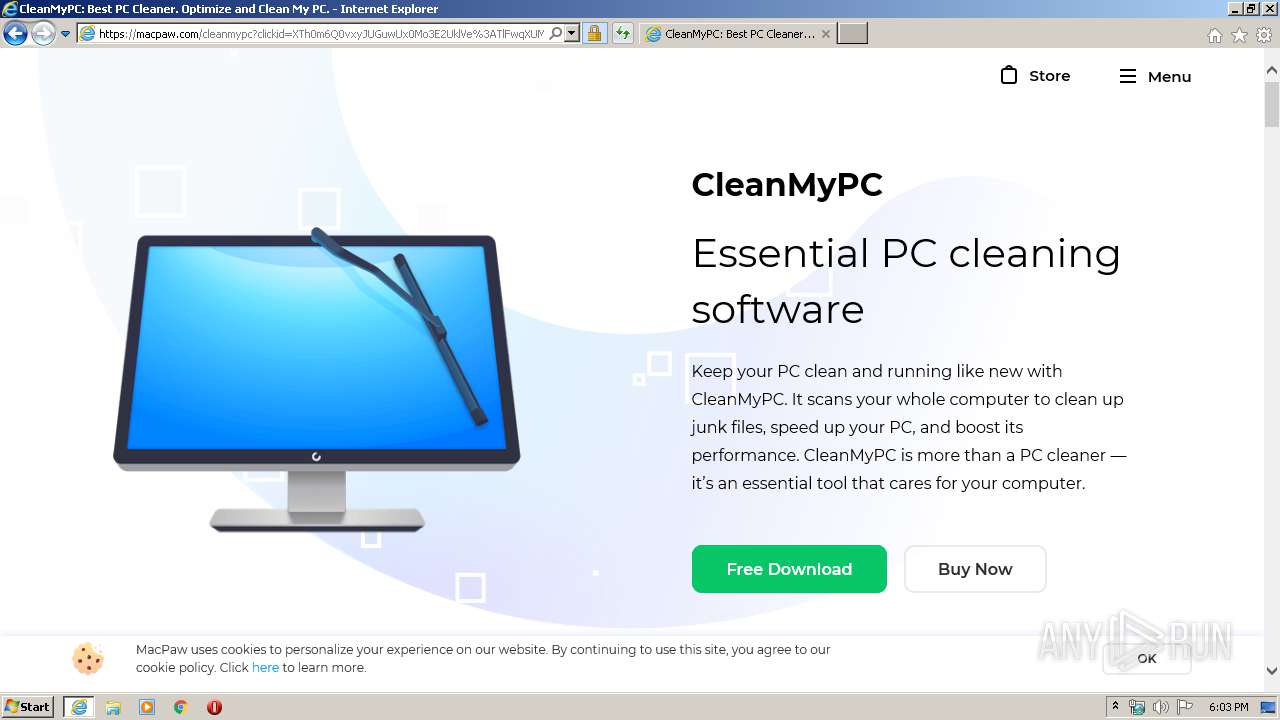
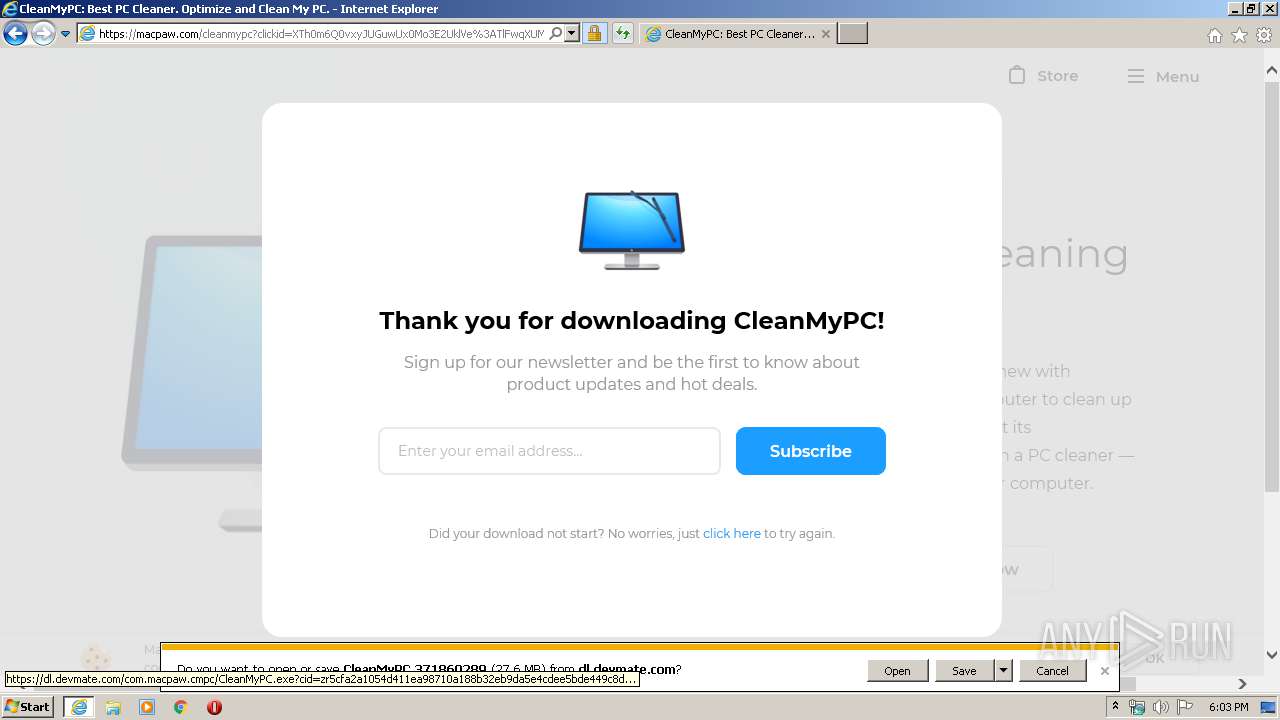
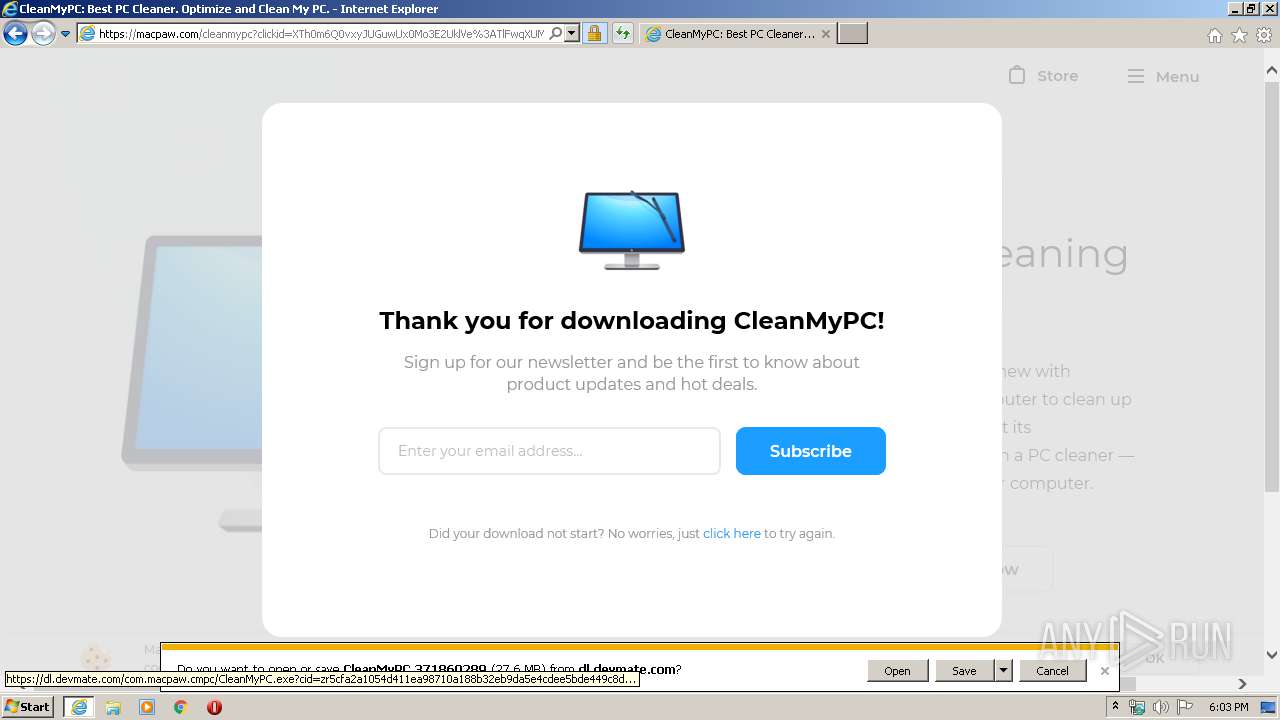
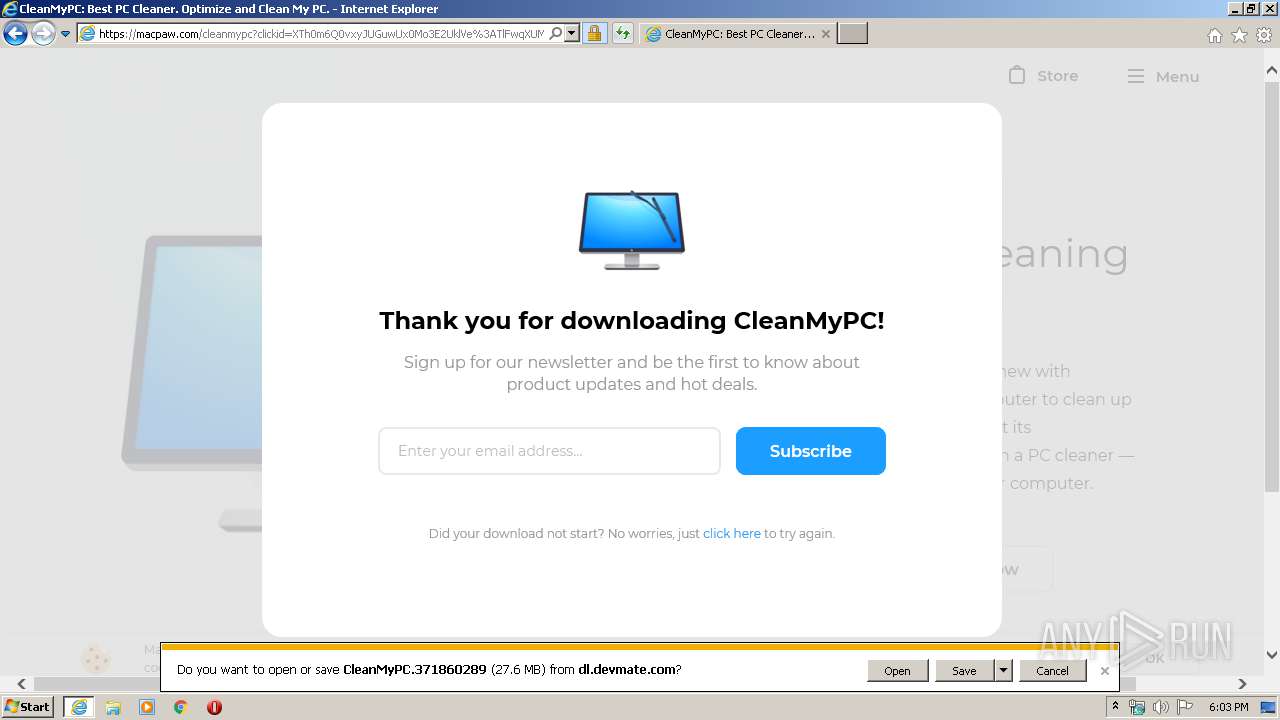
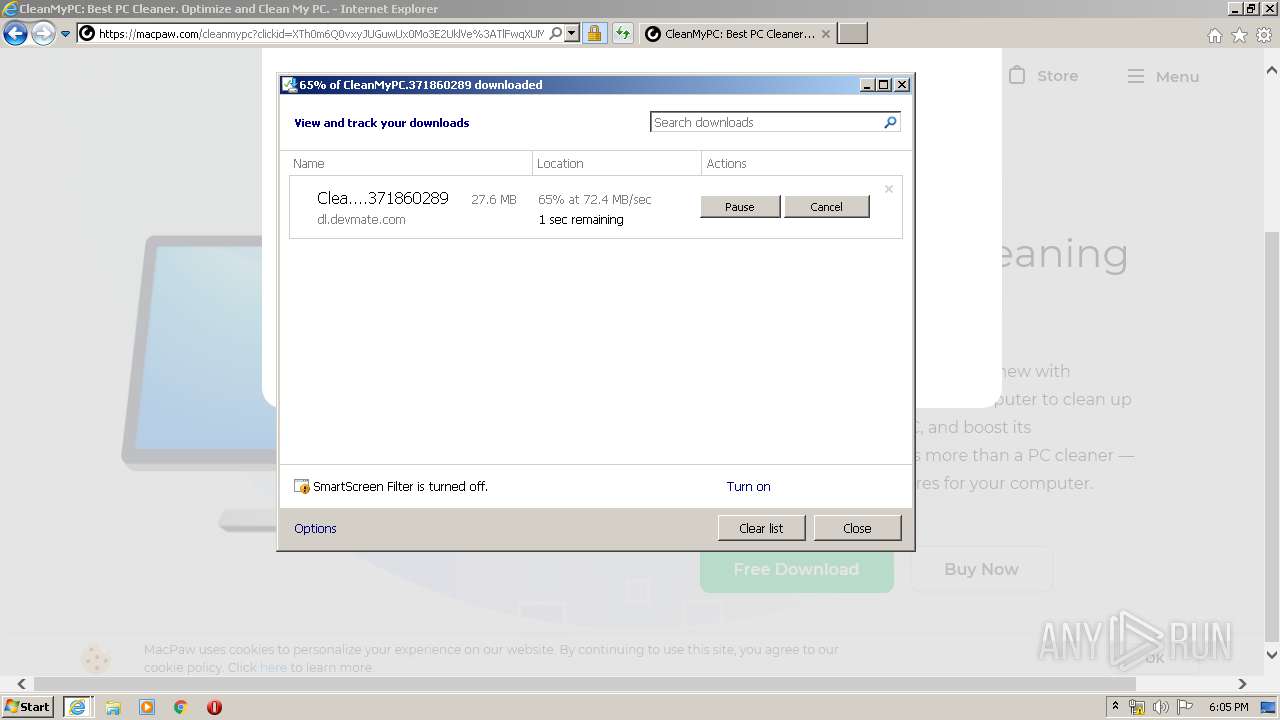
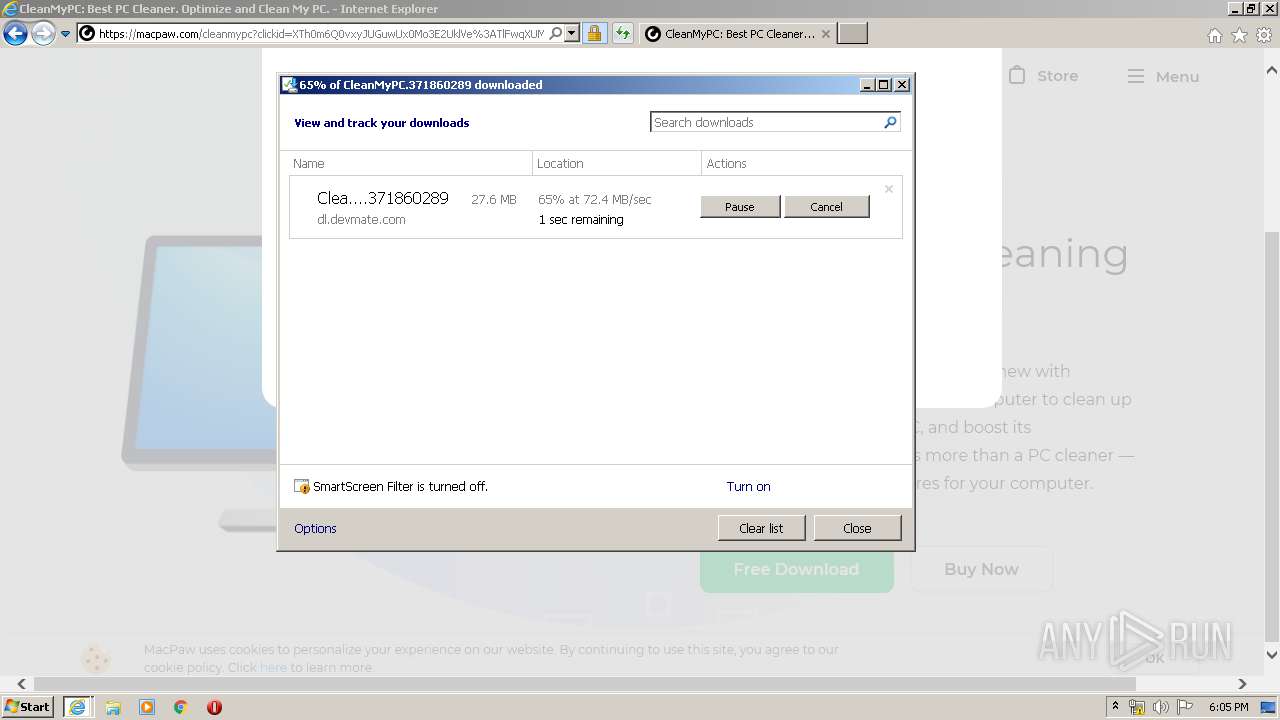
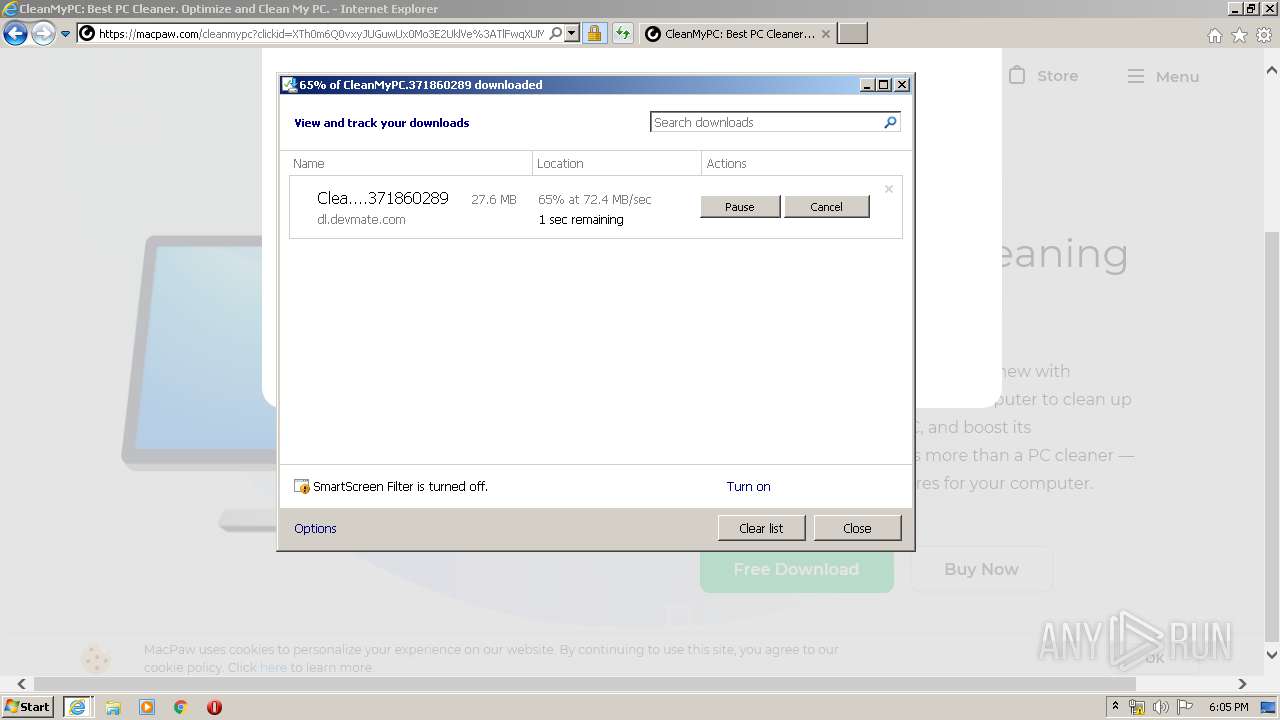
3252 | iexplore.exe | GET | 200 | 81.17.18.196:80 | http://www.furnituremediclv.com/ | CH | html | 480 b | malicious |
3252 | iexplore.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
3252 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3252 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDhKaVxWCYaNQgAAAAALC5%2B | US | der | 472 b | whitelisted |
3252 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3252 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDu3mVgzTXArwIAAAAAWXG3 | US | der | 472 b | whitelisted |
3252 | iexplore.exe | GET | 200 | 13.35.254.57:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
1748 | iexplore.exe | GET | 404 | 35.168.147.213:80 | http://usa.iulianus-mon.com/favicon.ico | US | html | 940 b | shared |
3252 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3252 | iexplore.exe | GET | 200 | 143.204.208.127:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3252 | iexplore.exe | 81.17.18.196:80 | — | Private Layer INC | CH | malicious |
3252 | iexplore.exe | 35.168.147.213:80 | usa.iulianus-mon.com | Amazon.com, Inc. | US | malicious |
1748 | iexplore.exe | 35.168.147.213:80 | usa.iulianus-mon.com | Amazon.com, Inc. | US | malicious |
3252 | iexplore.exe | 172.217.23.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1748 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3252 | iexplore.exe | 178.128.33.47:443 | qualmode.website | Forthnet | GR | suspicious |
3252 | iexplore.exe | 2.21.242.187:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
3252 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
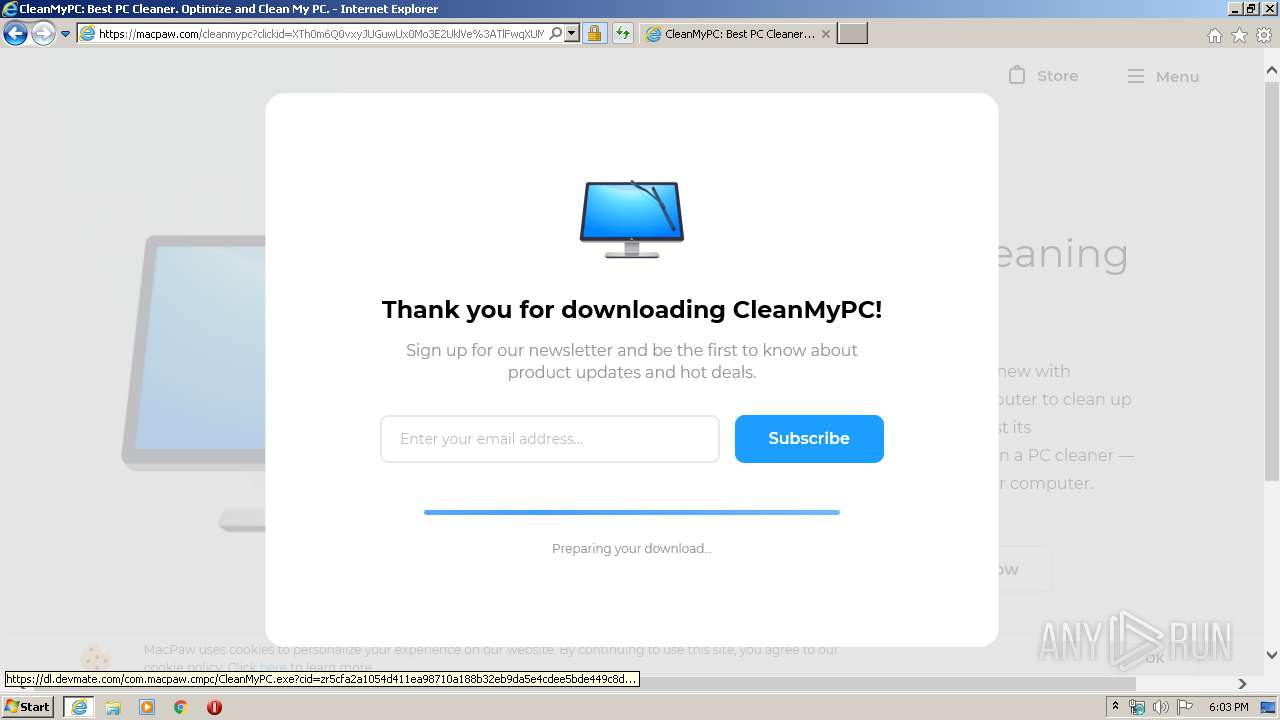
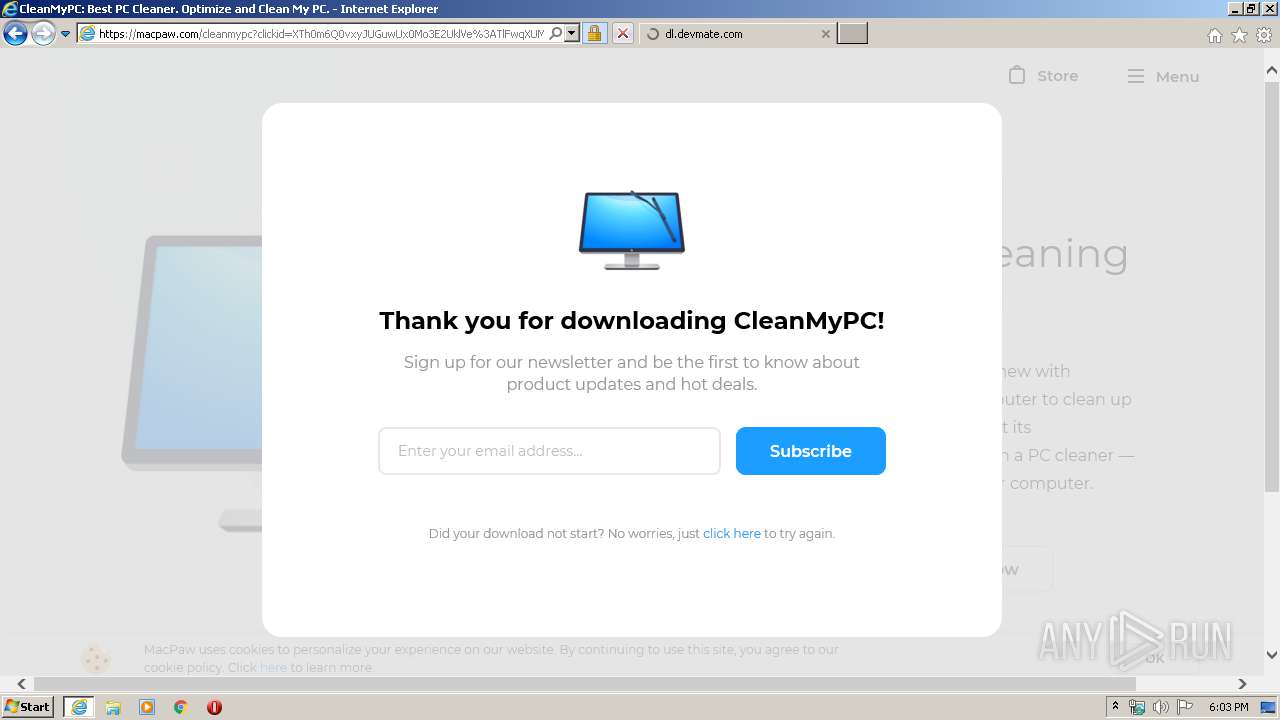
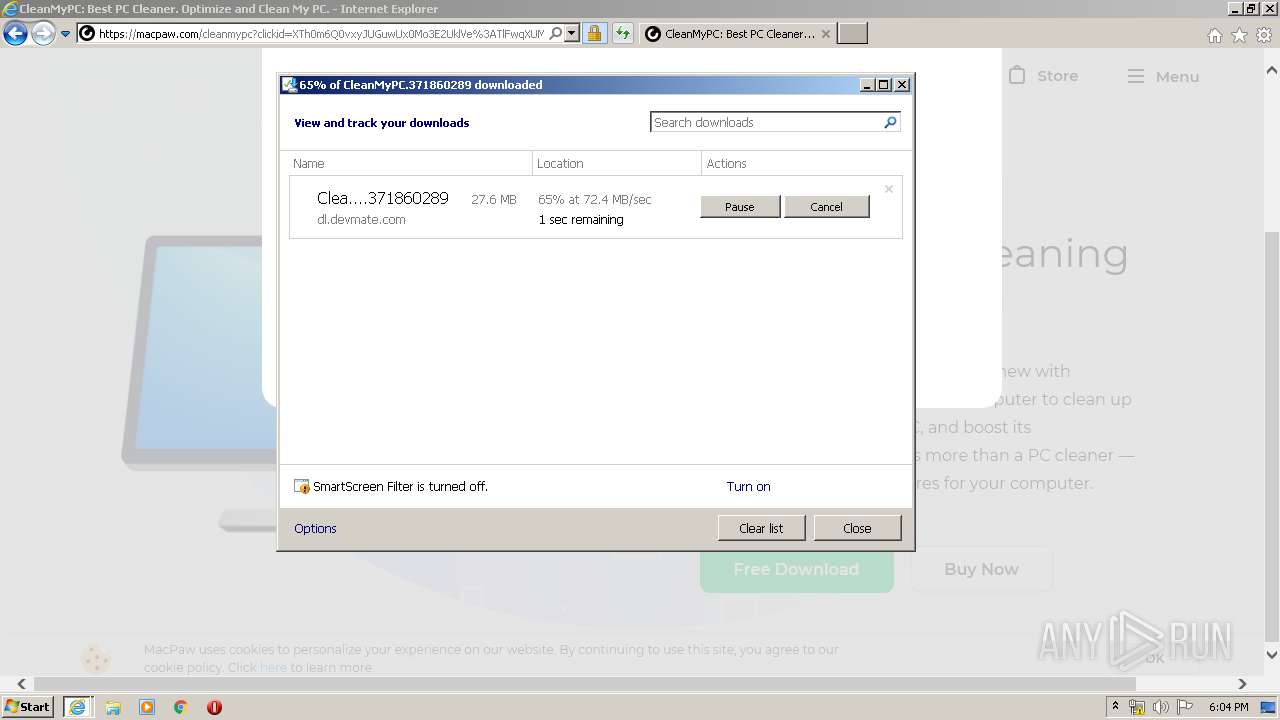
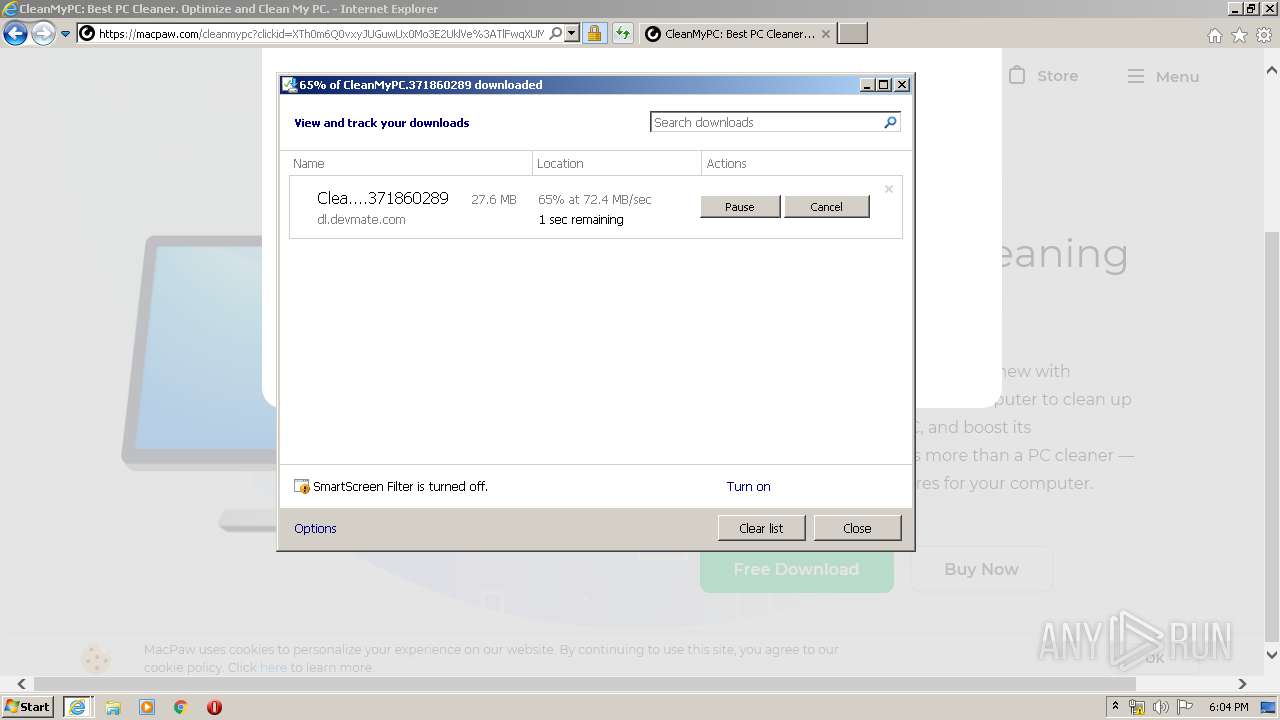
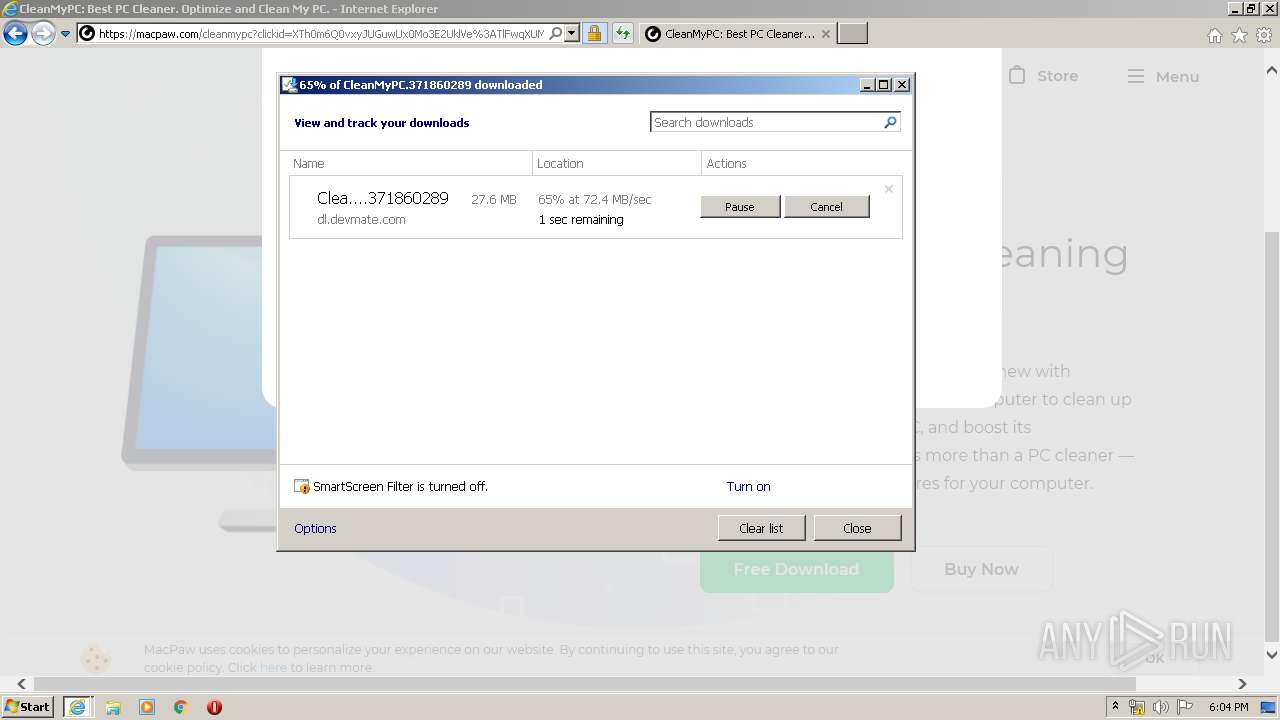
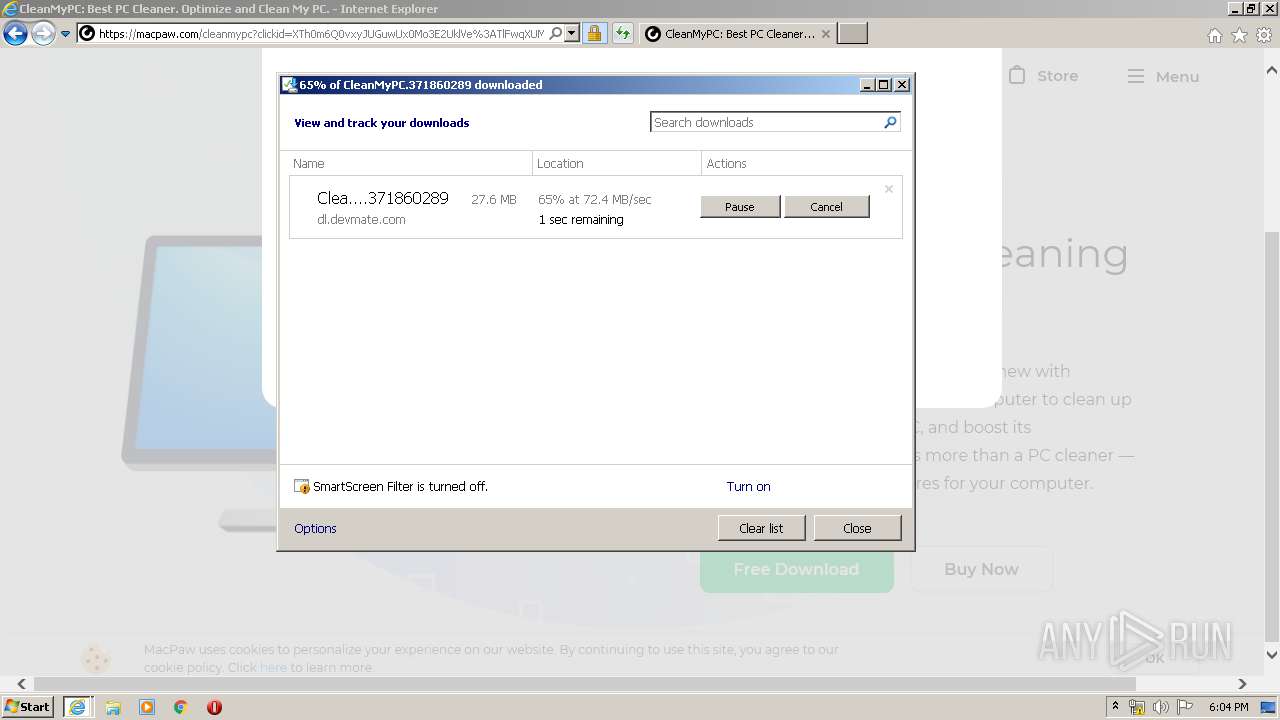
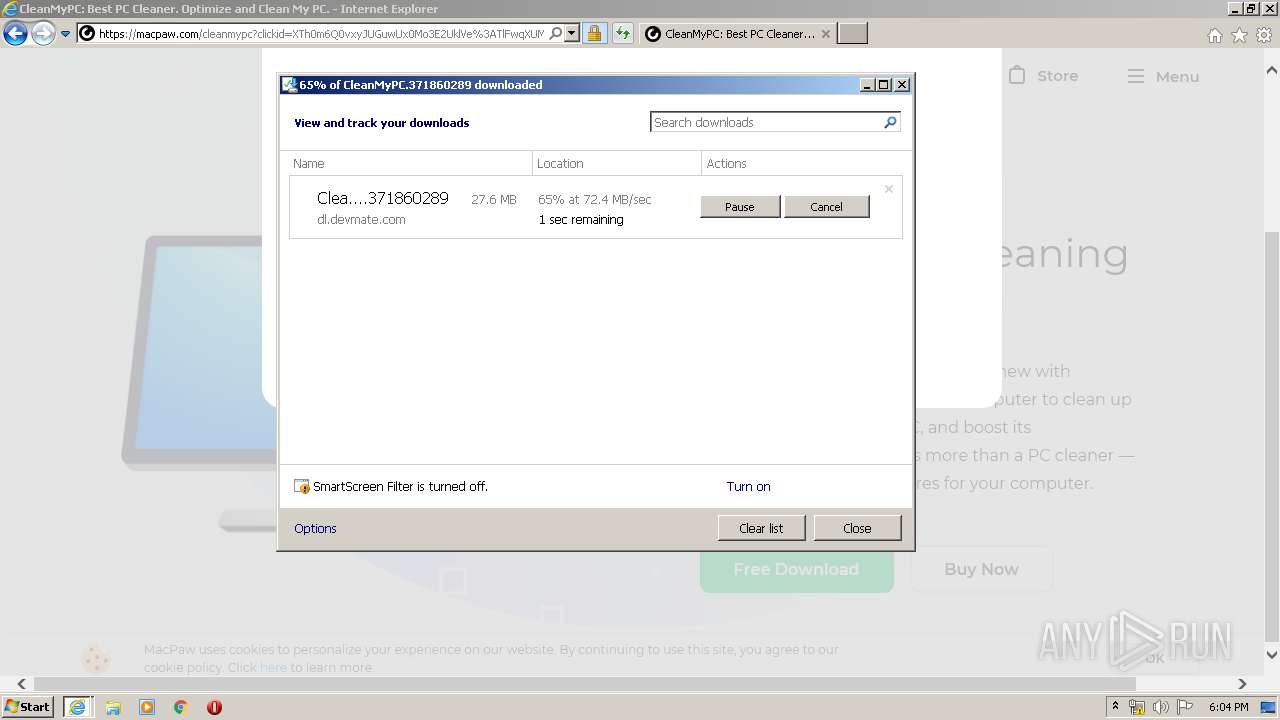
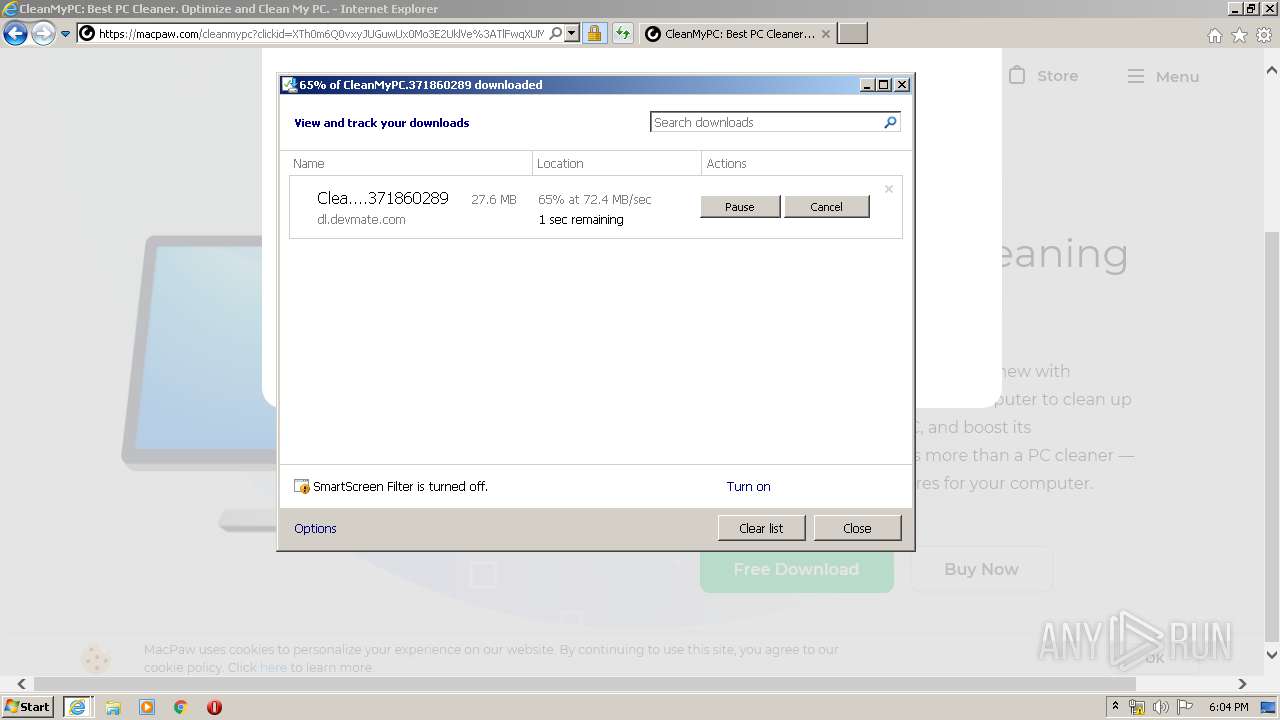
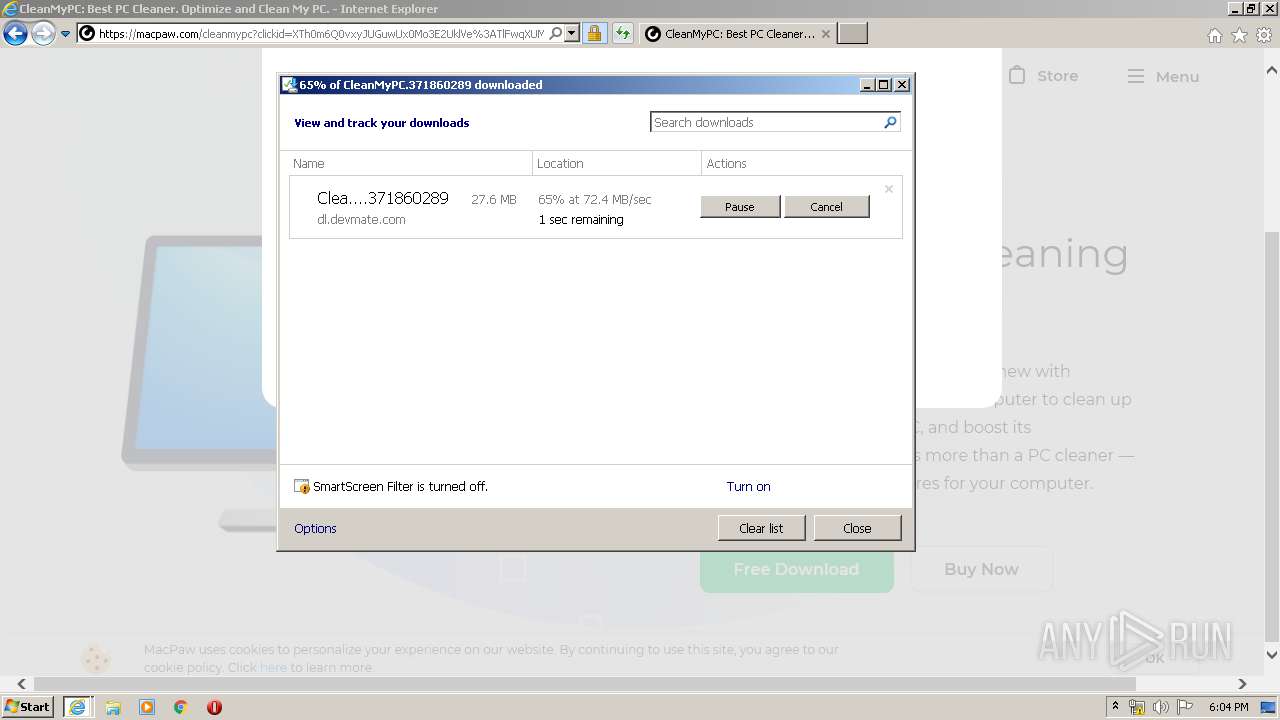
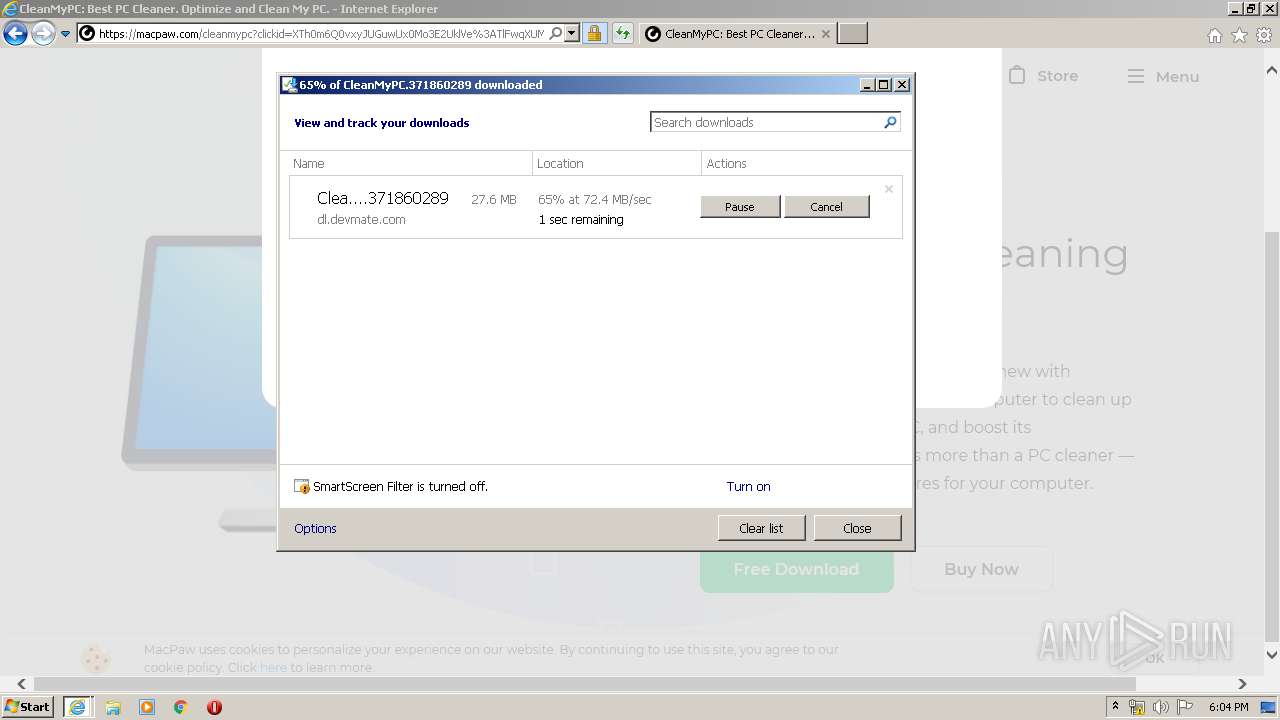
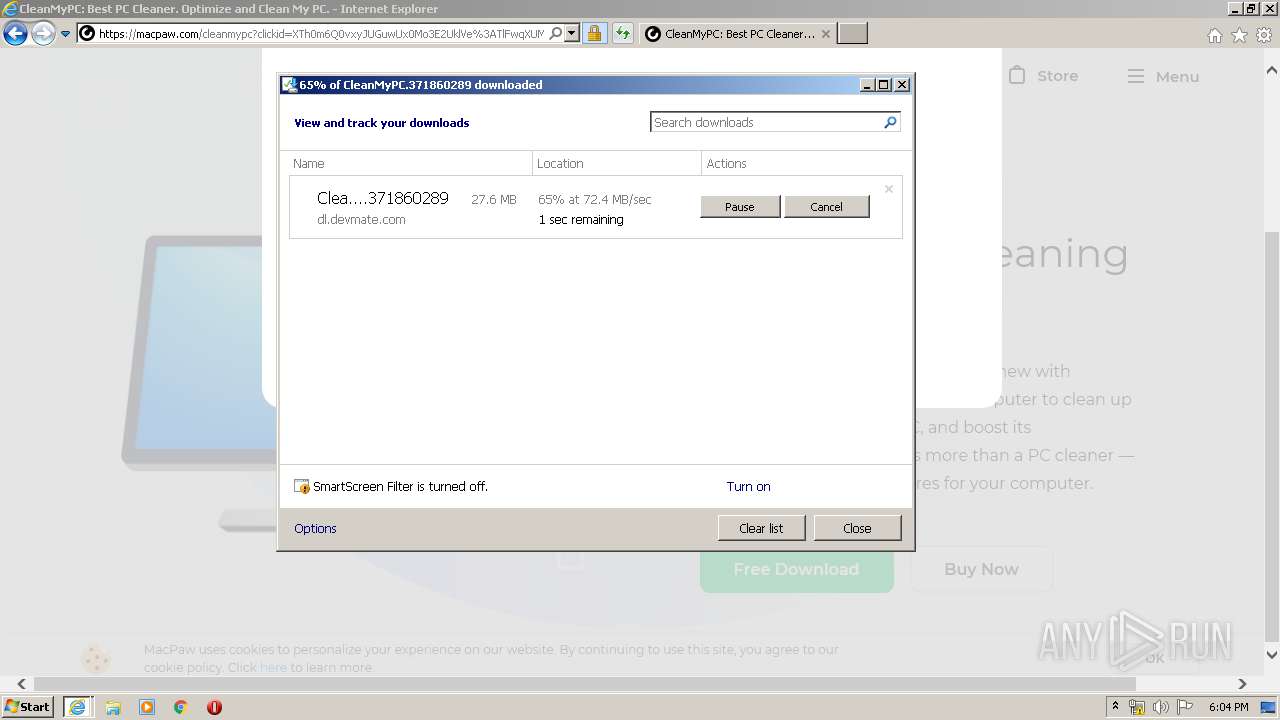
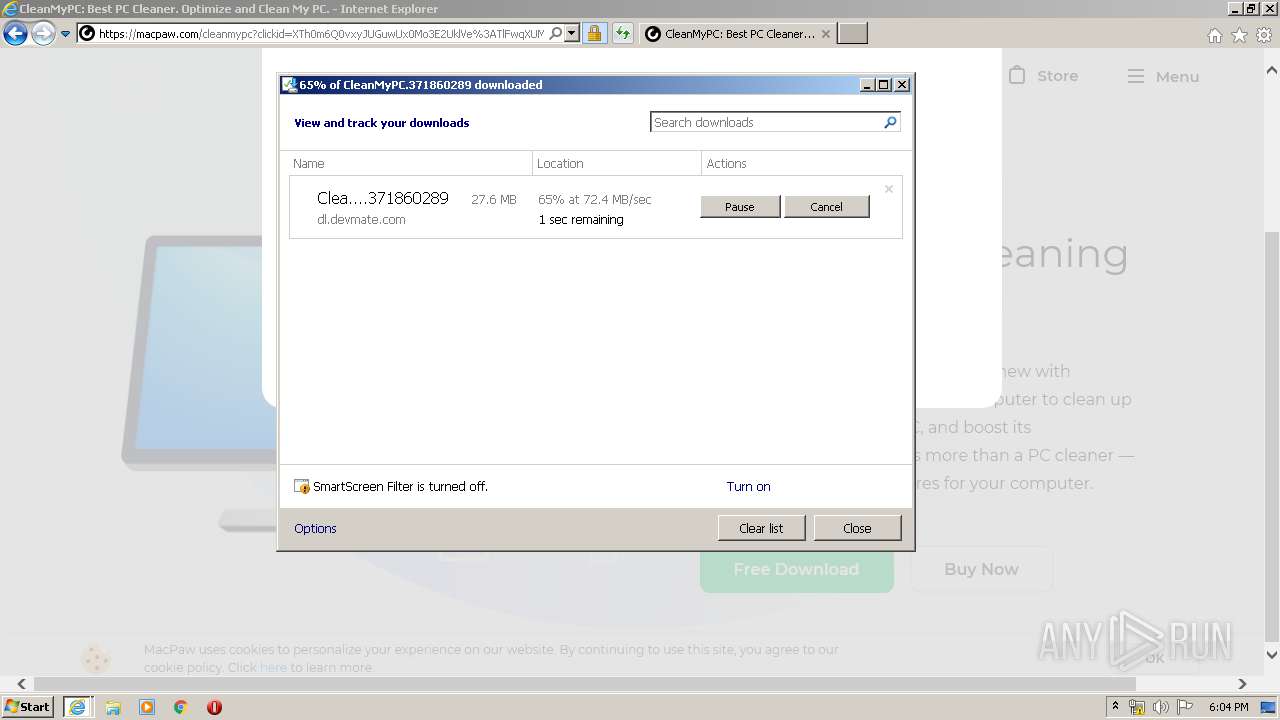
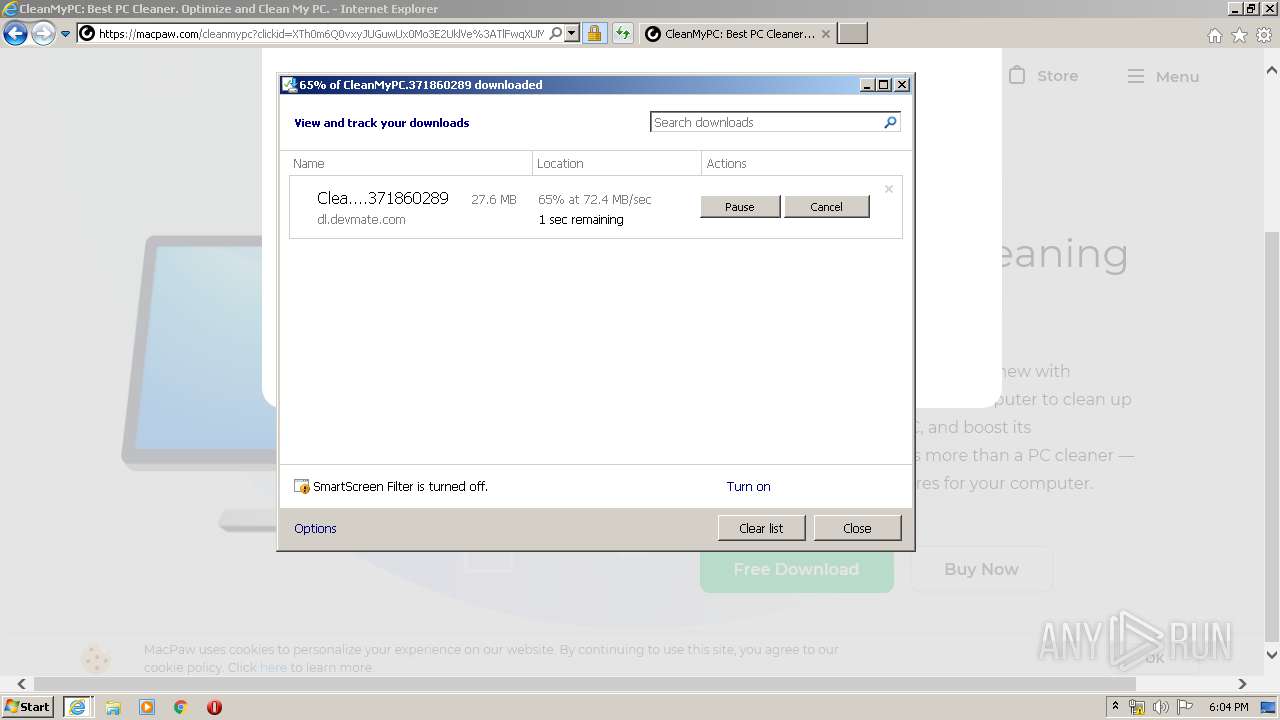
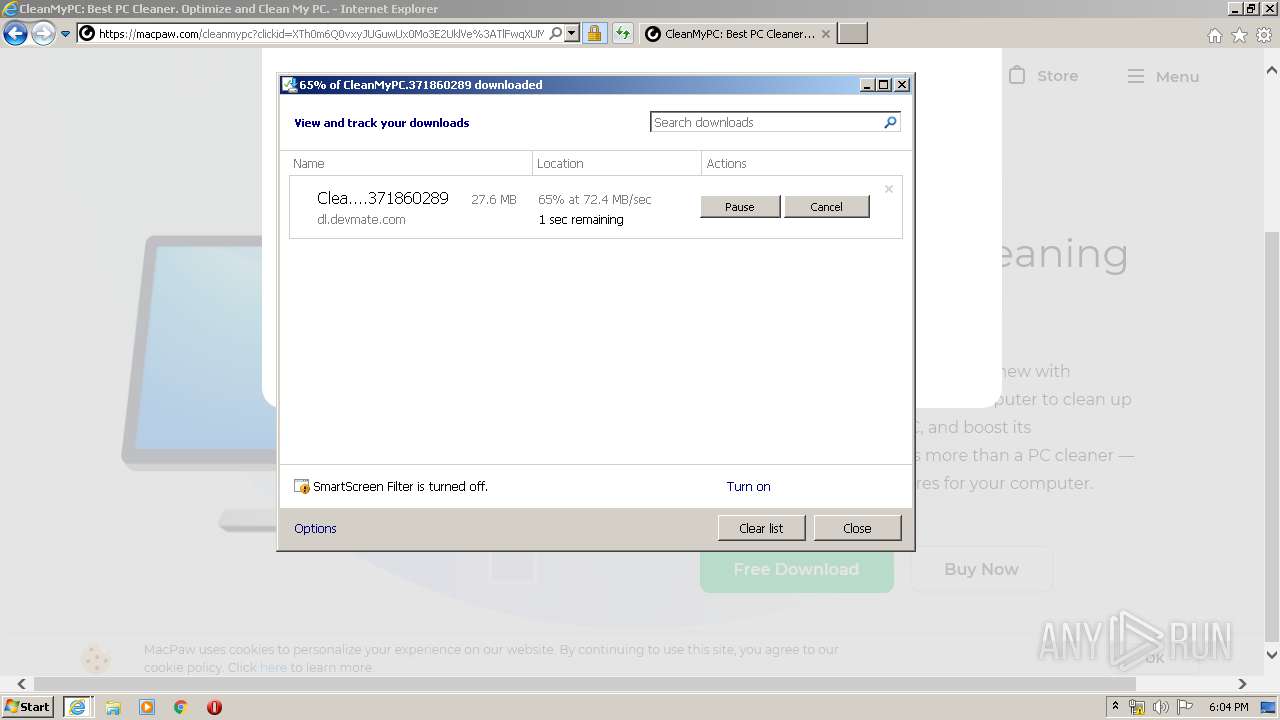
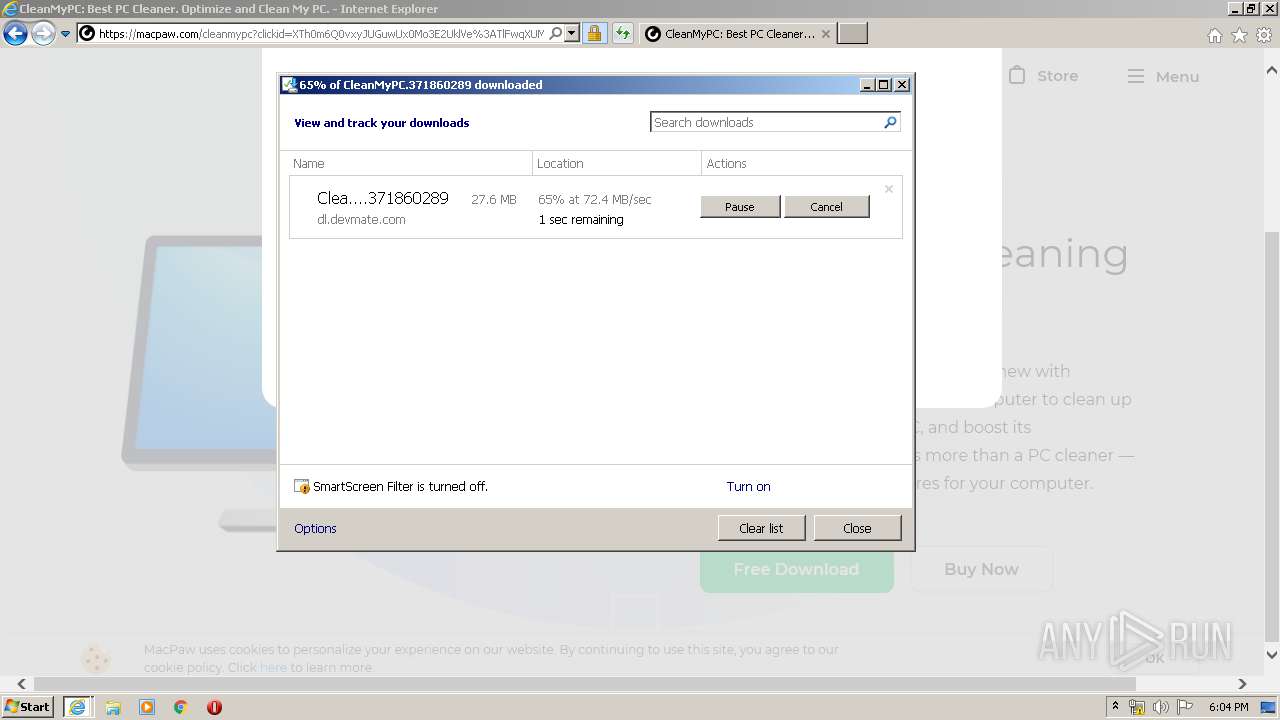
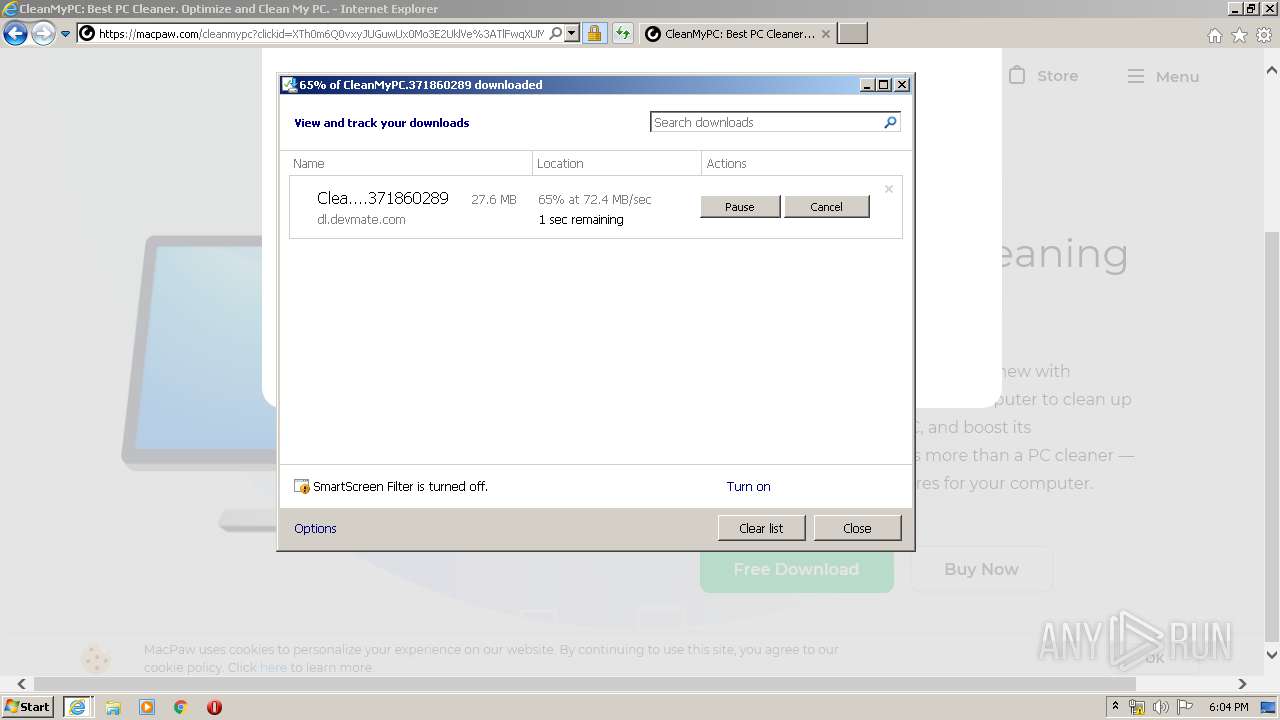
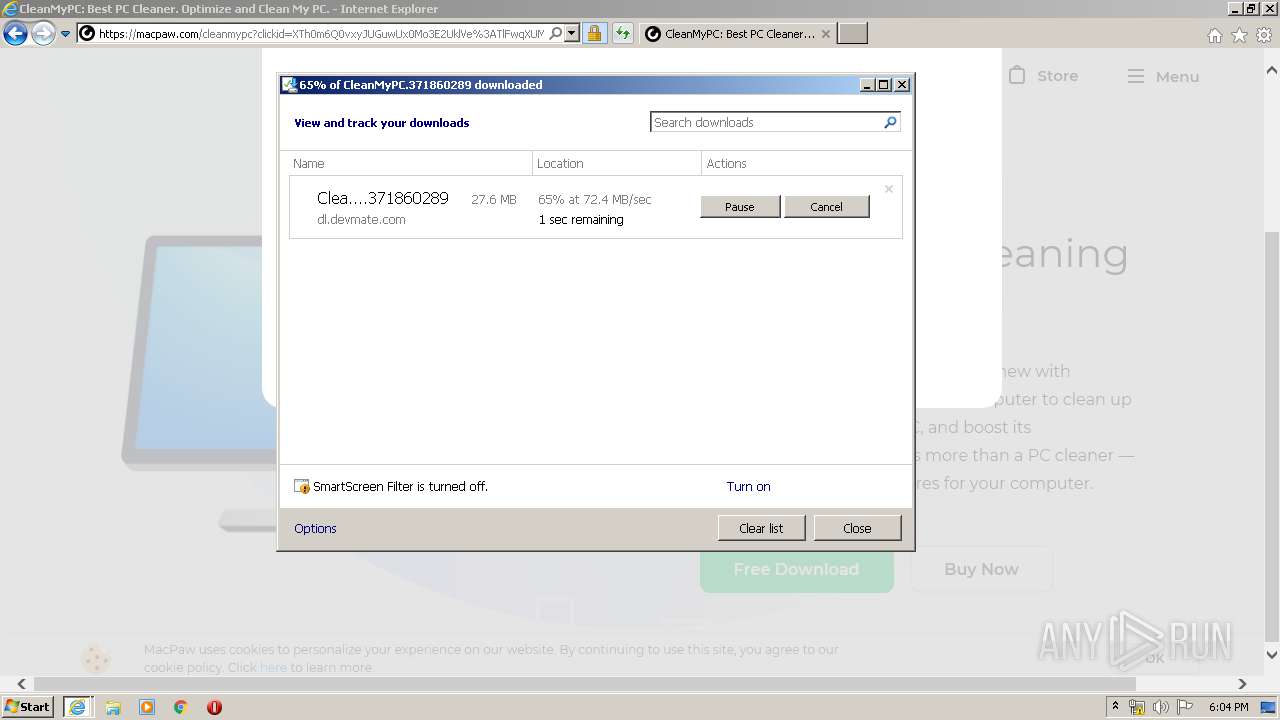
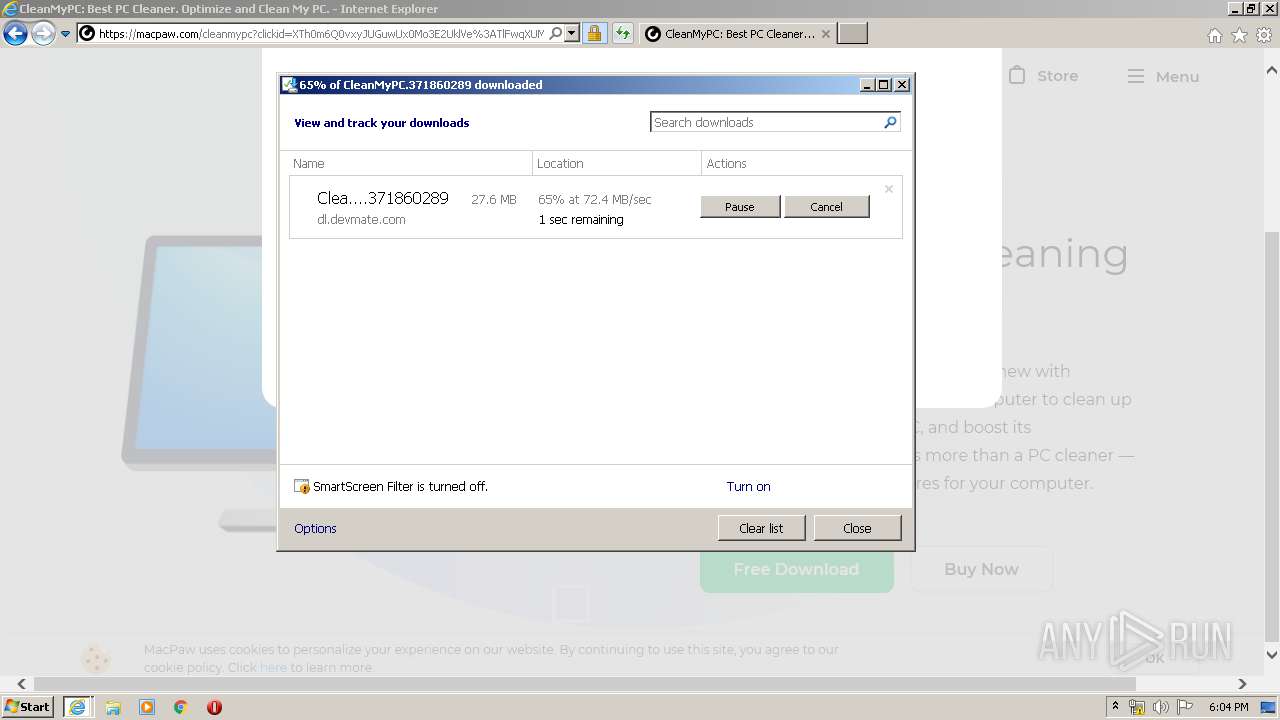
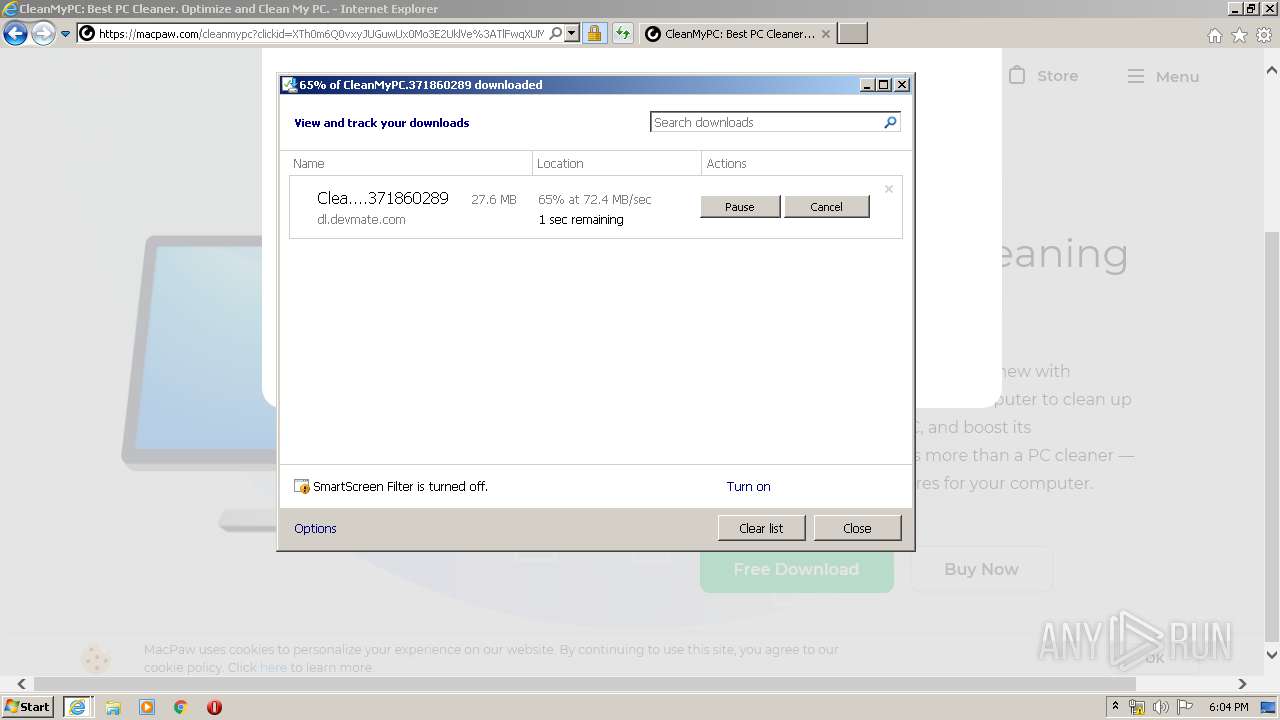
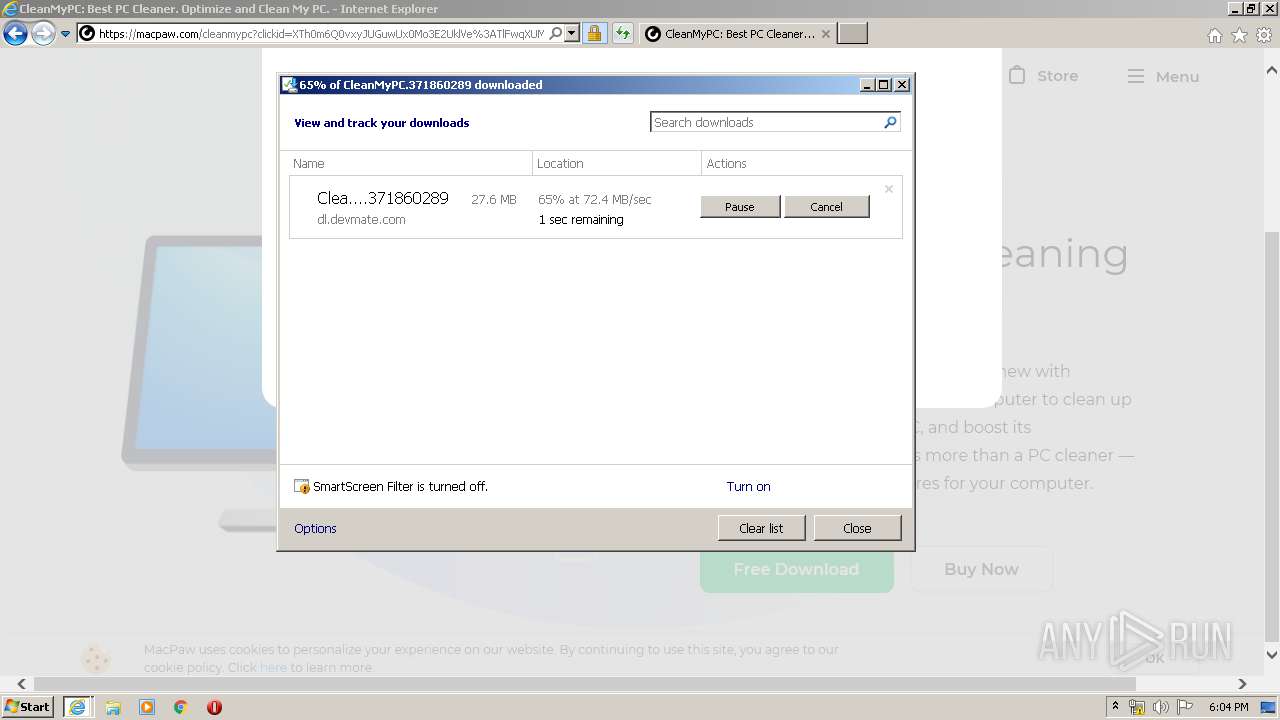
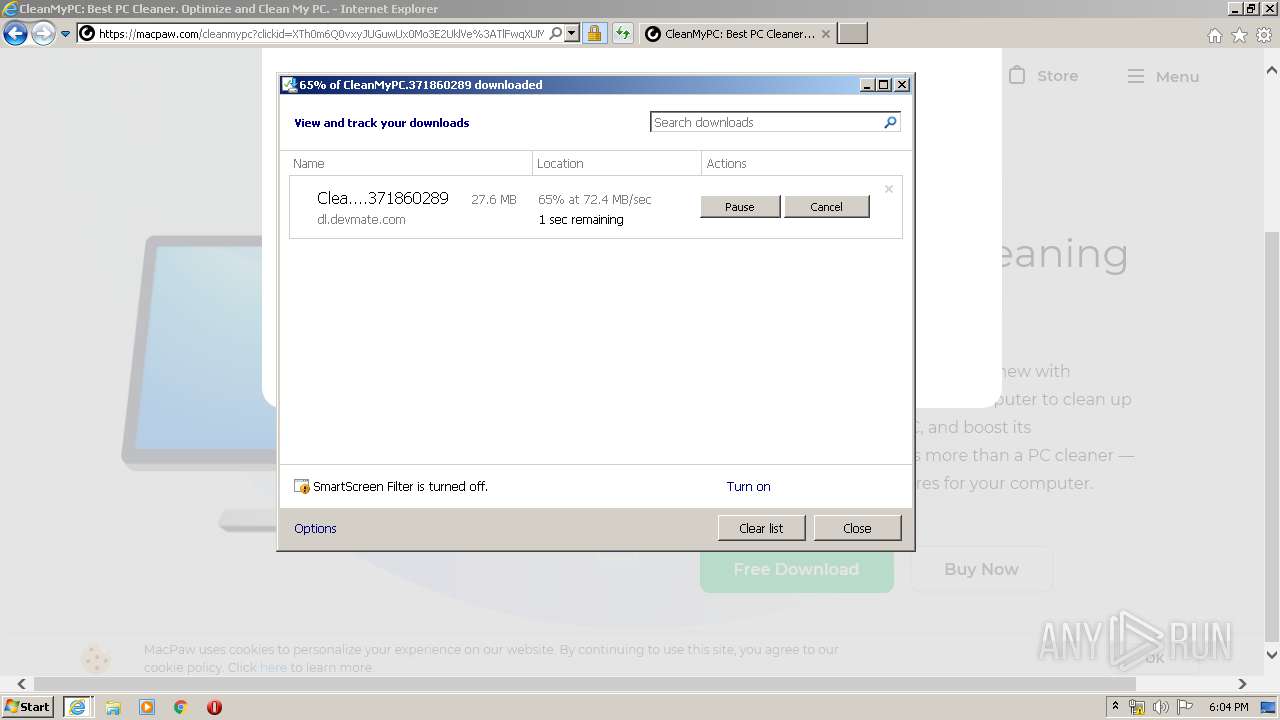
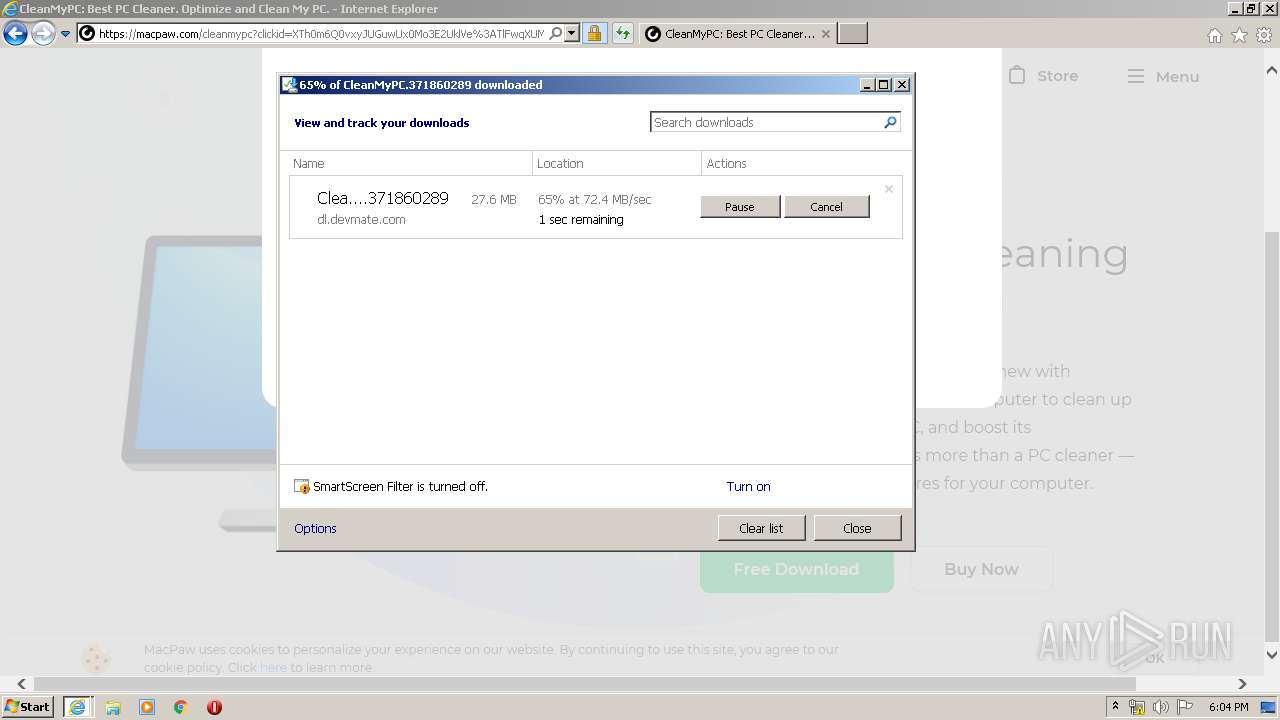
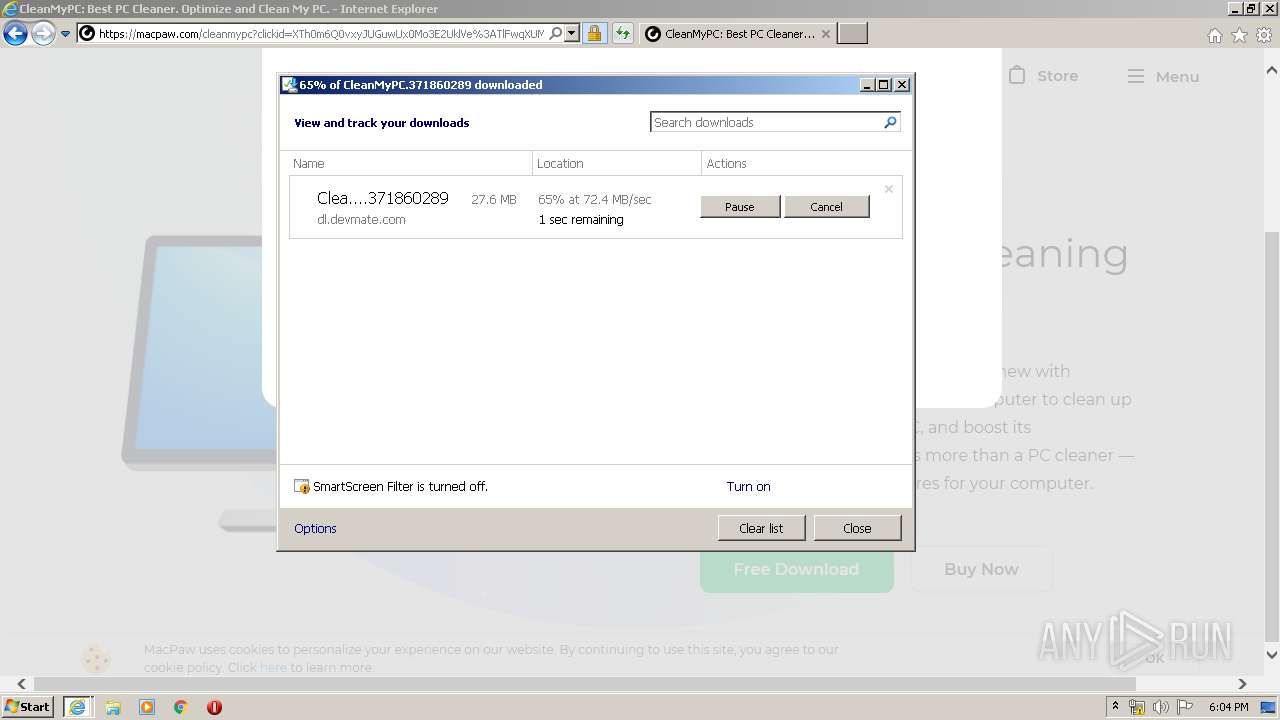
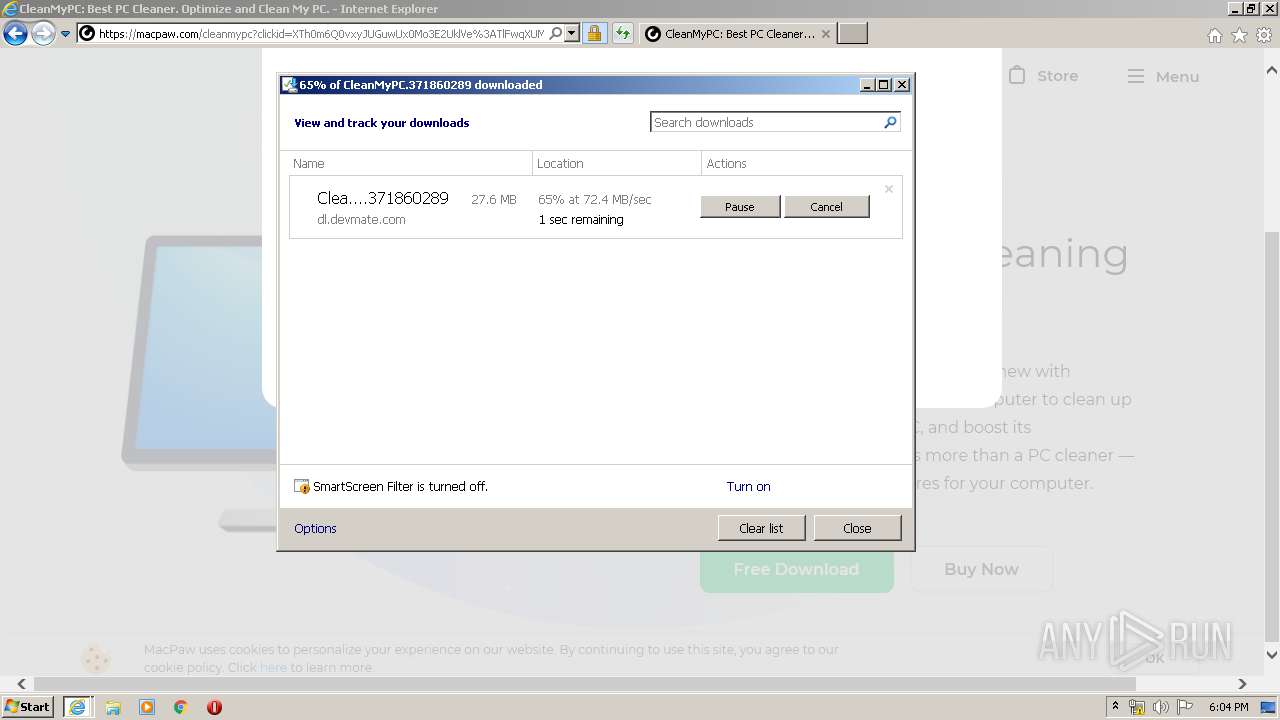
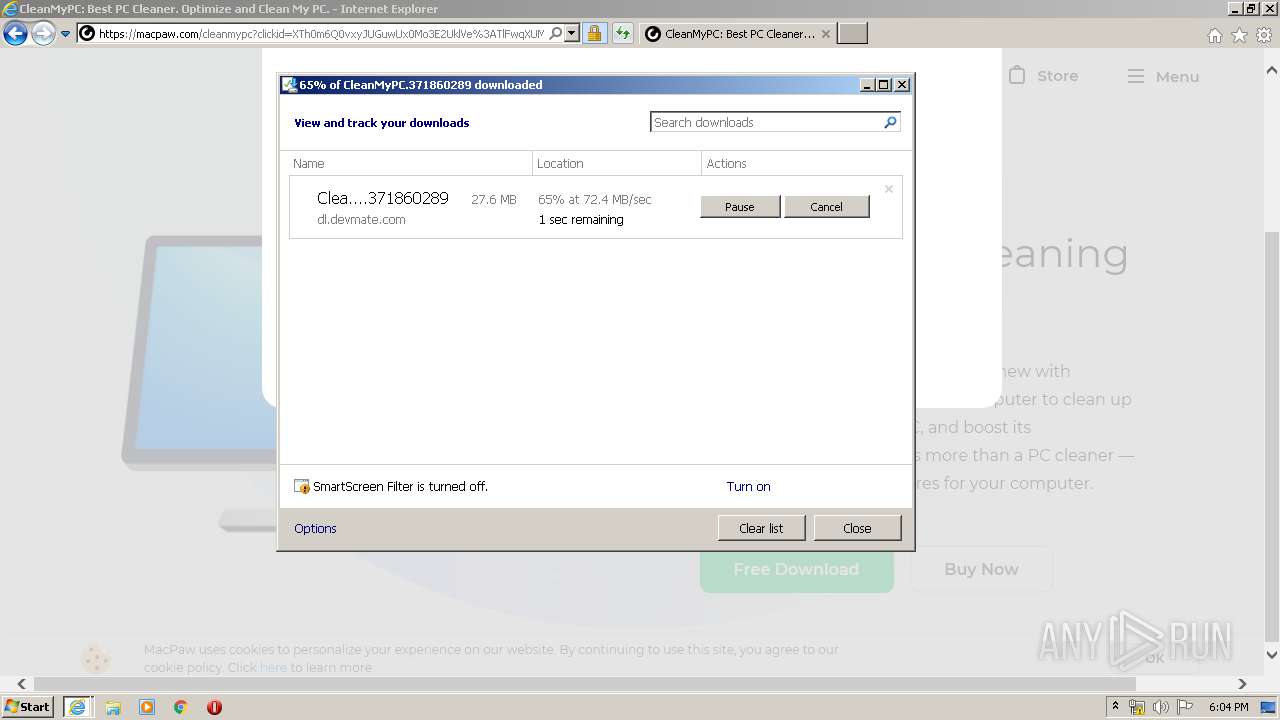
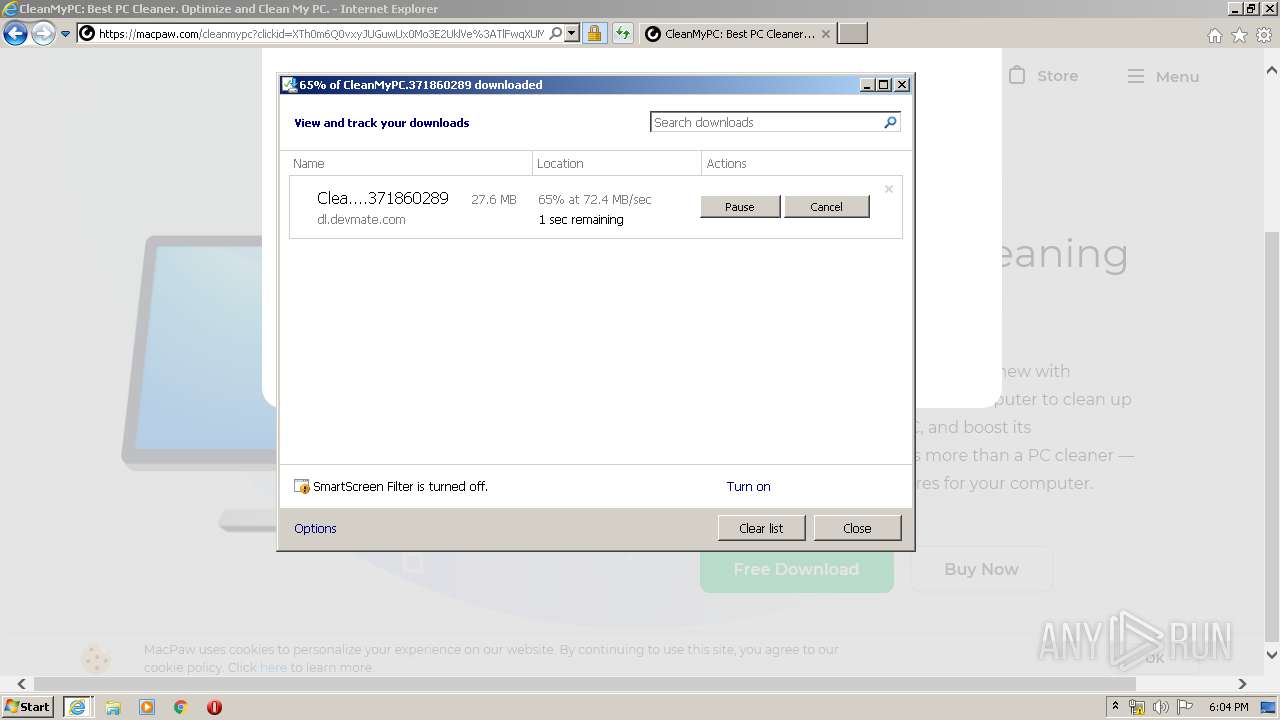
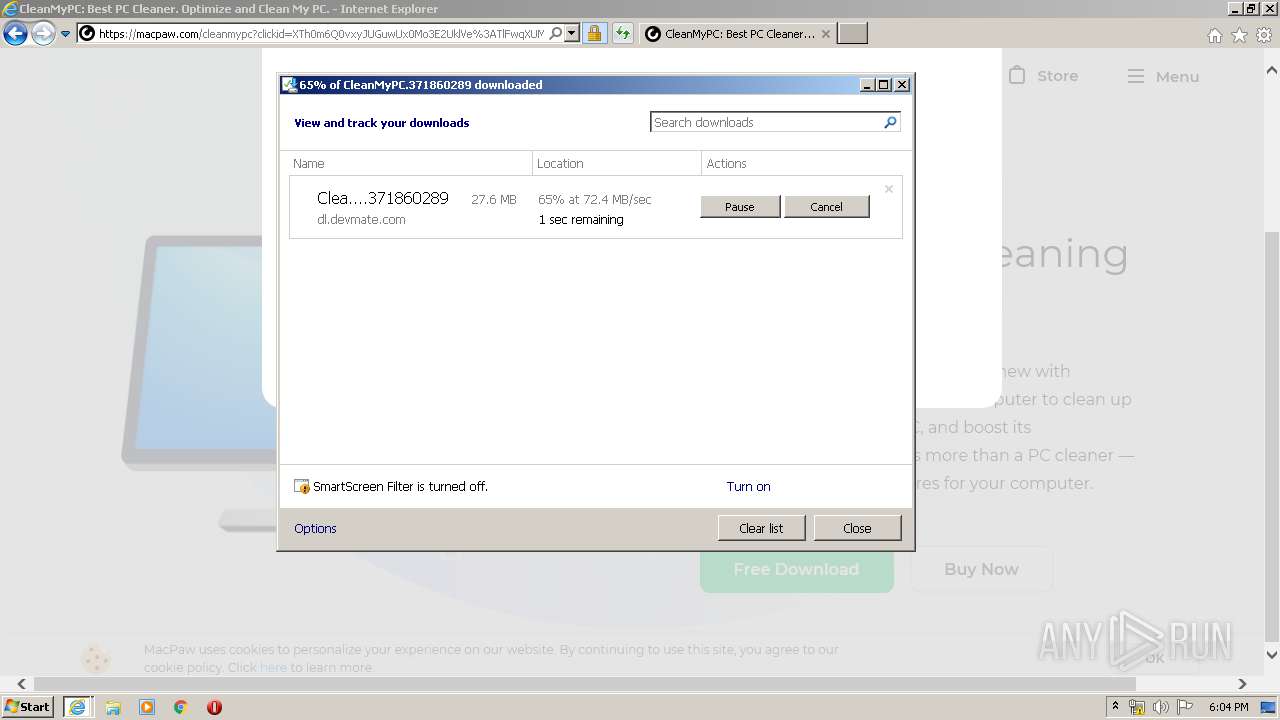
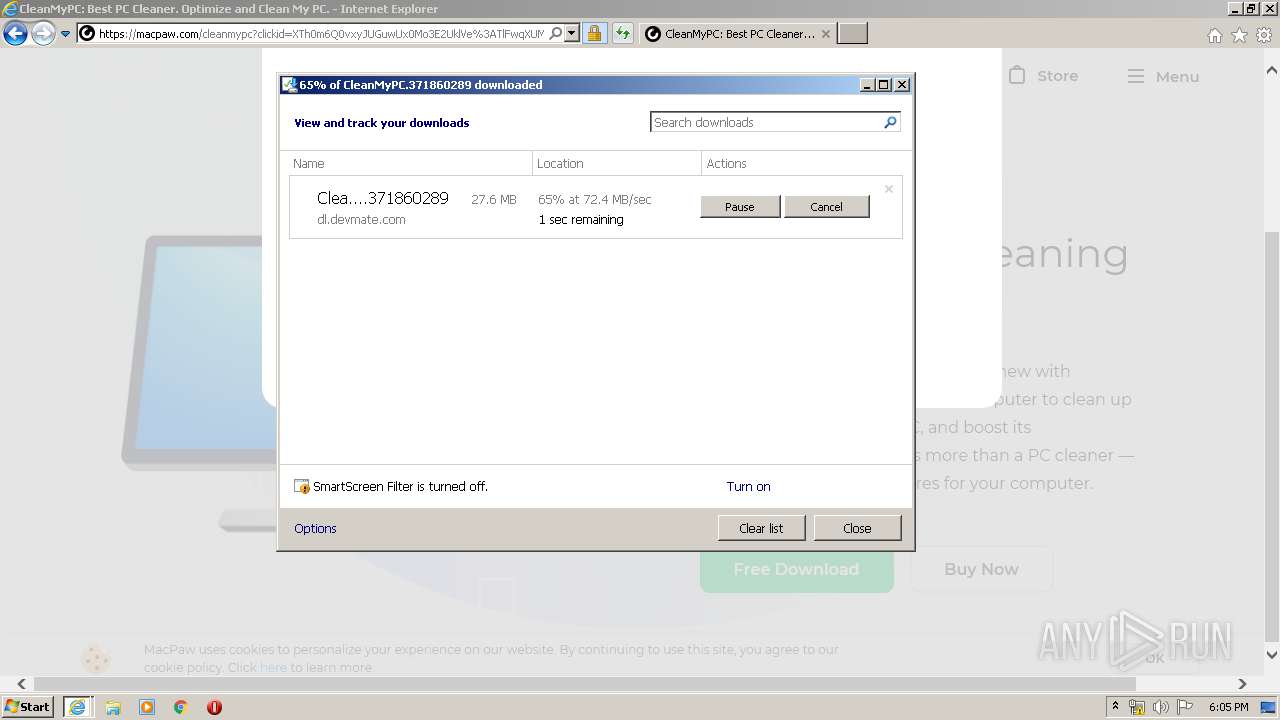
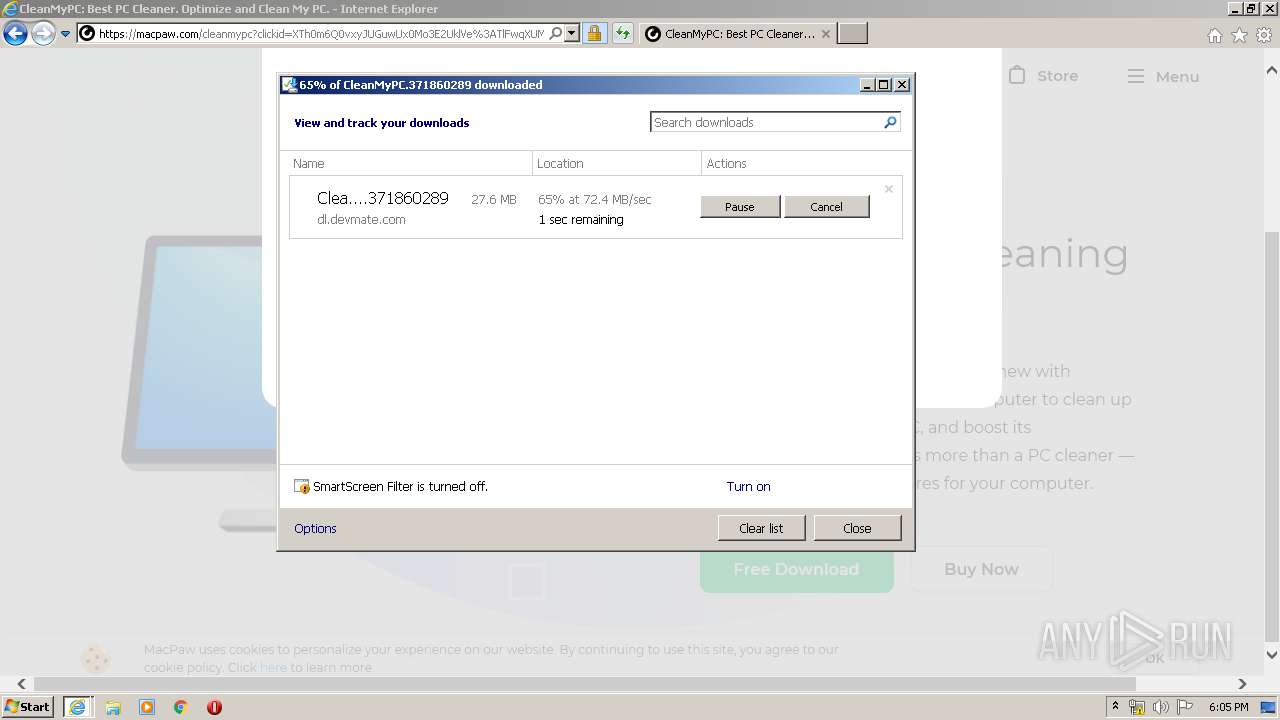
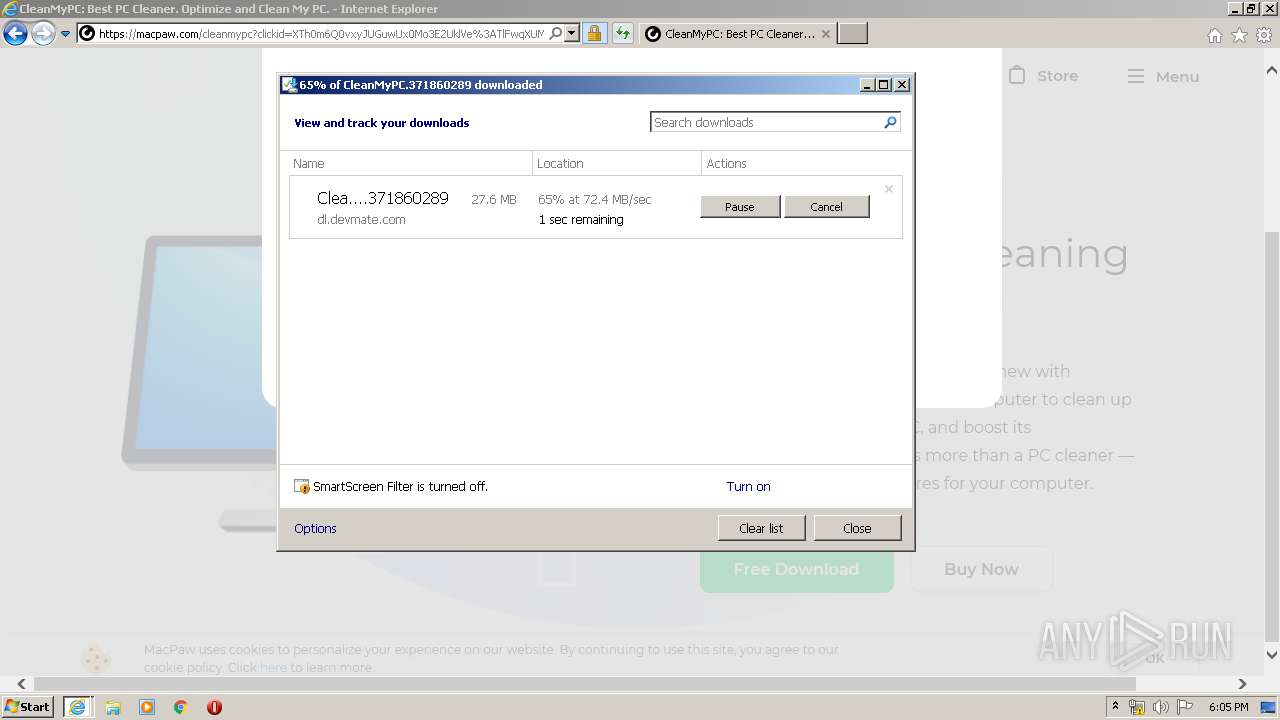
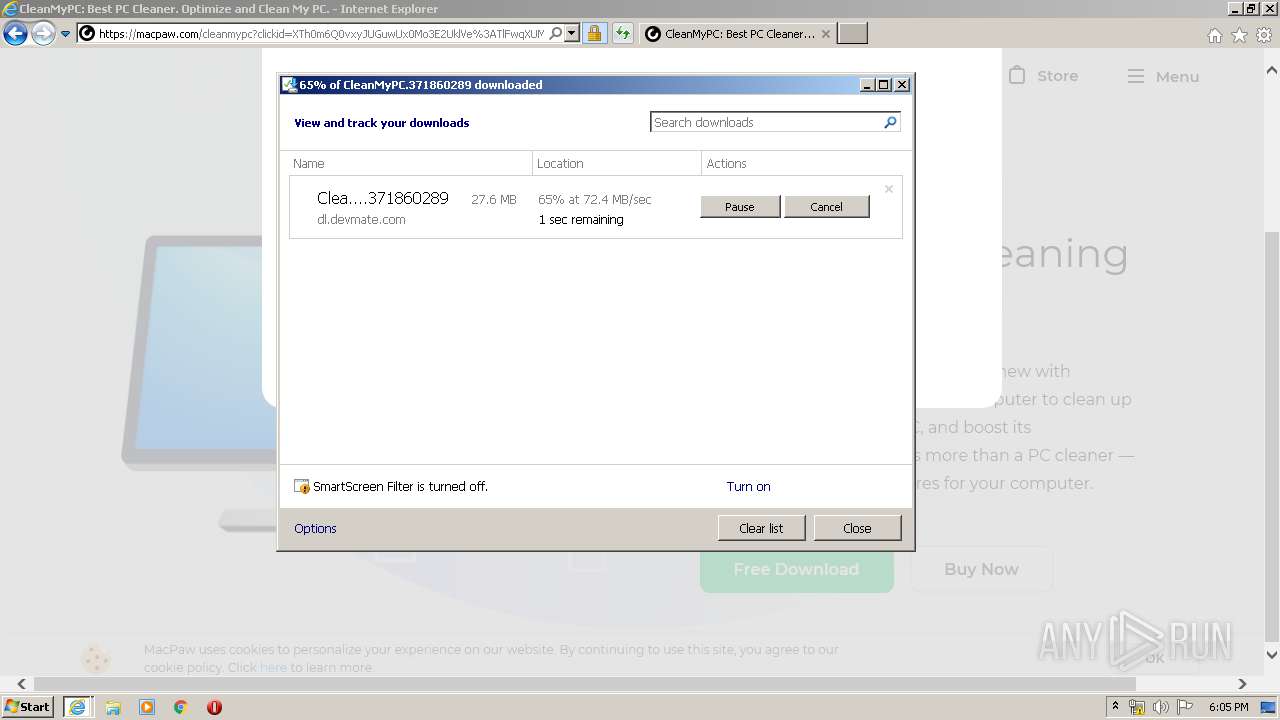
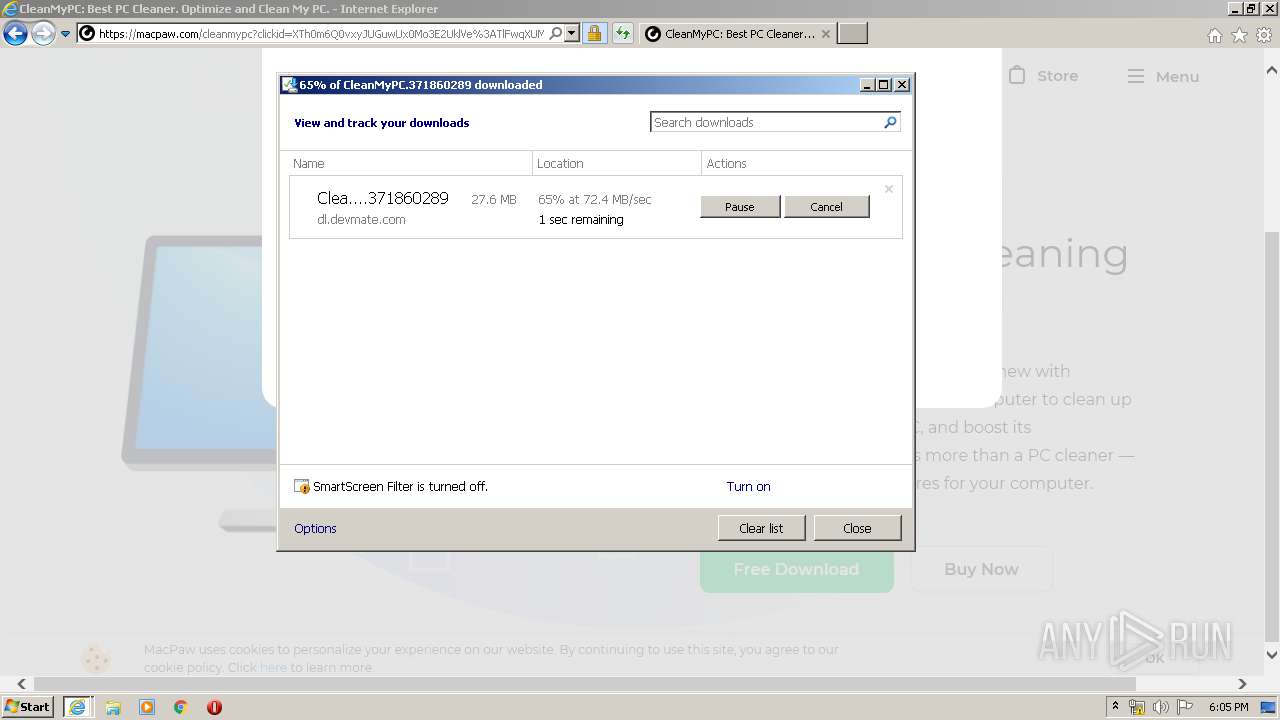
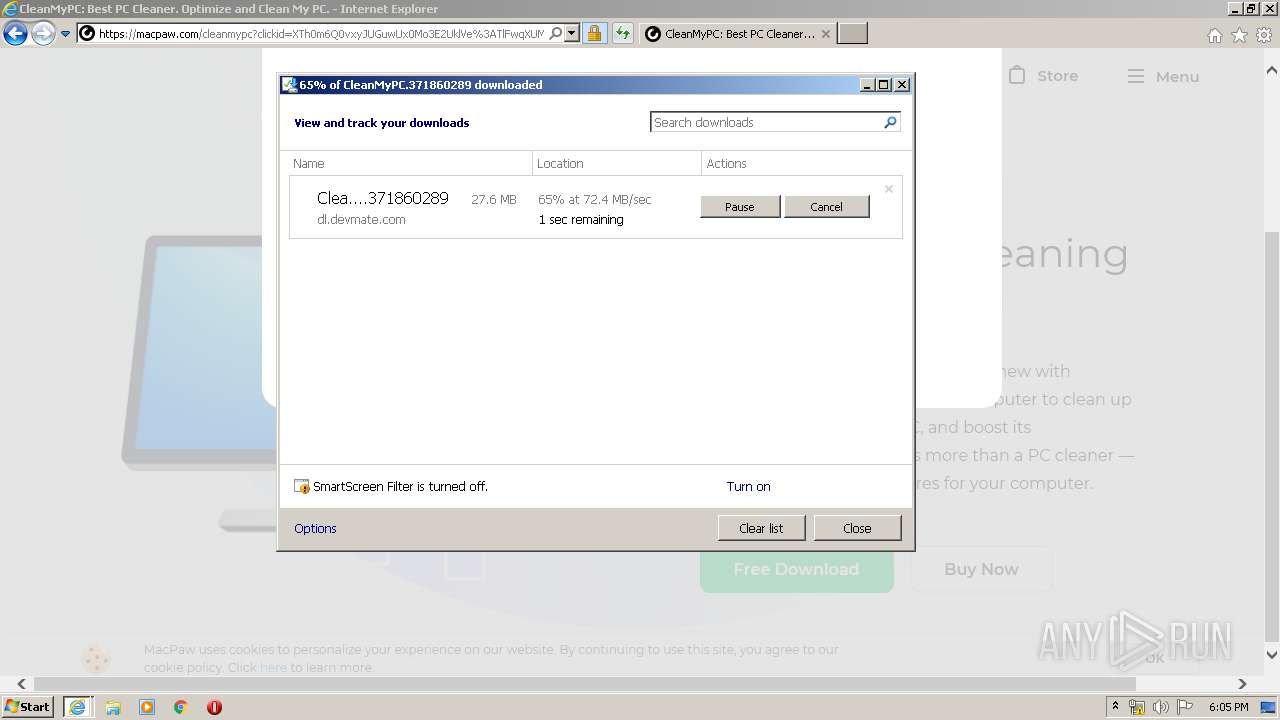
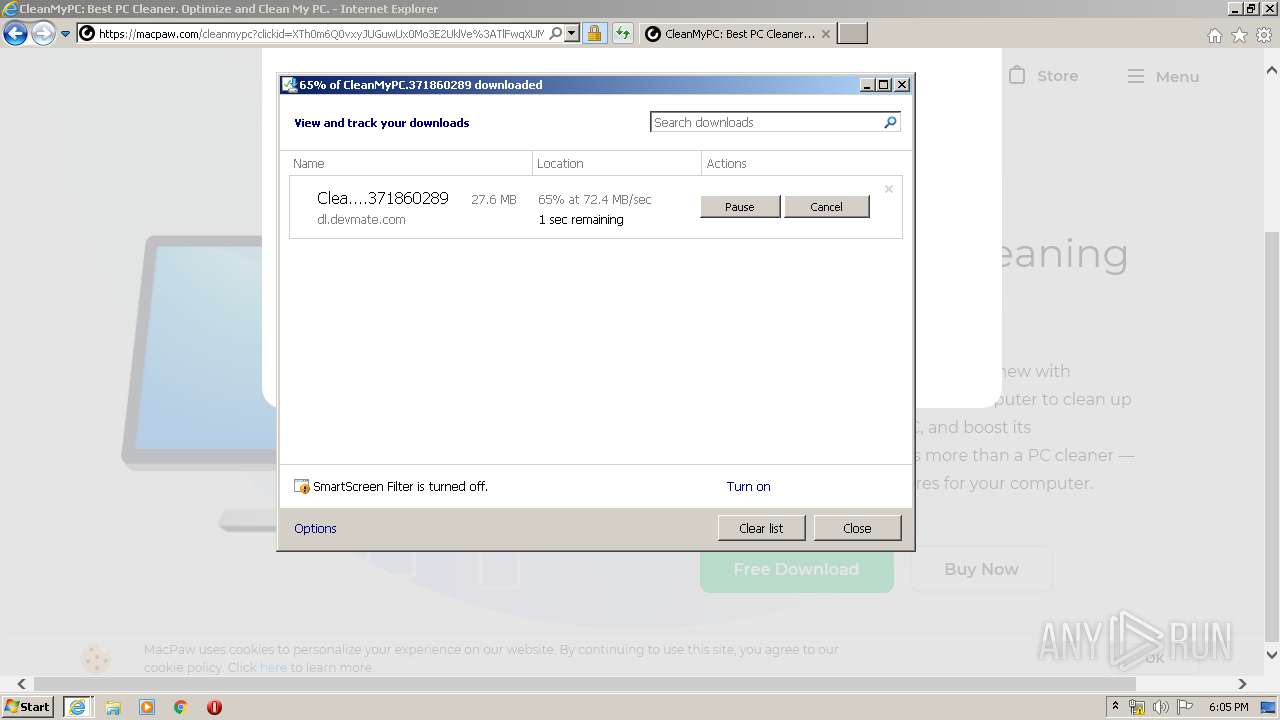
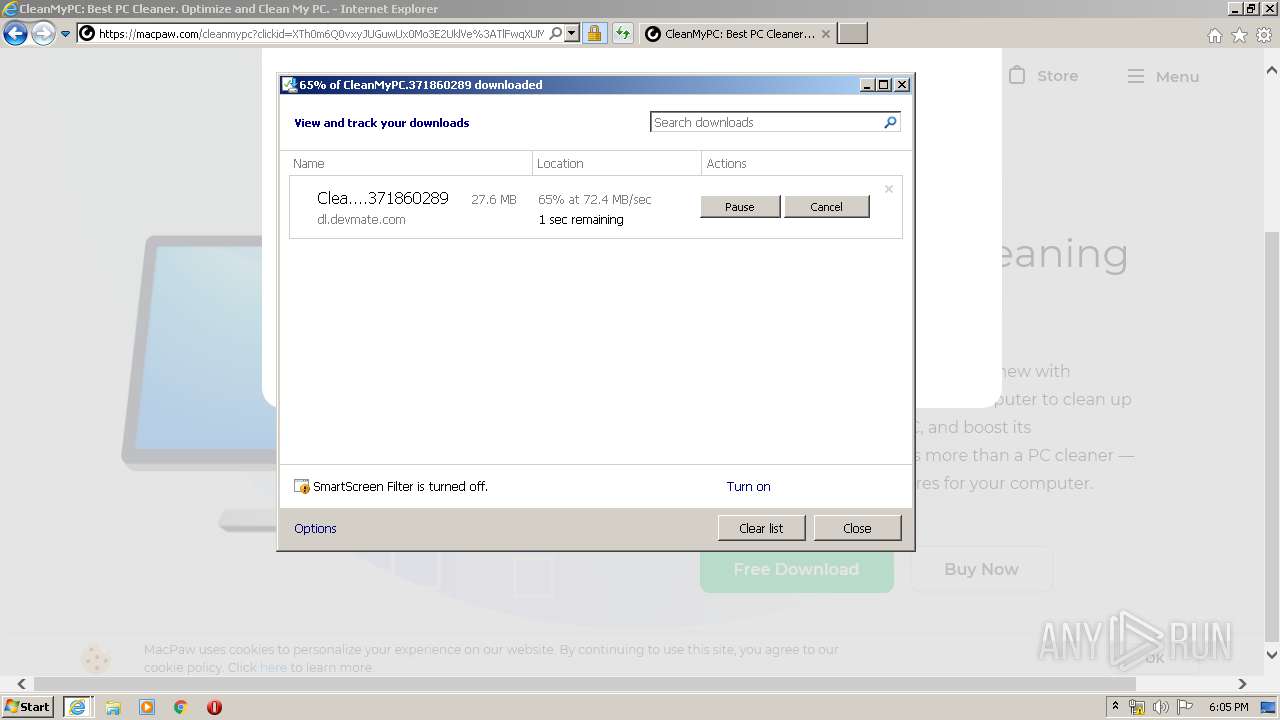
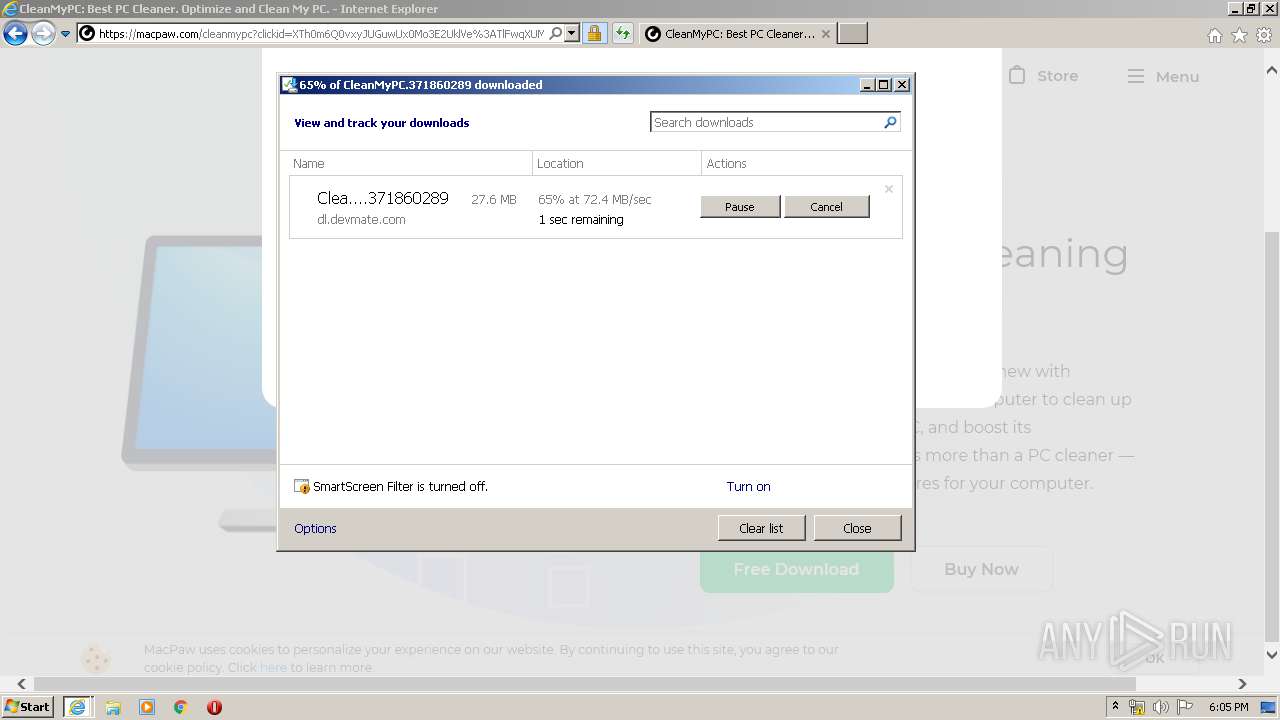
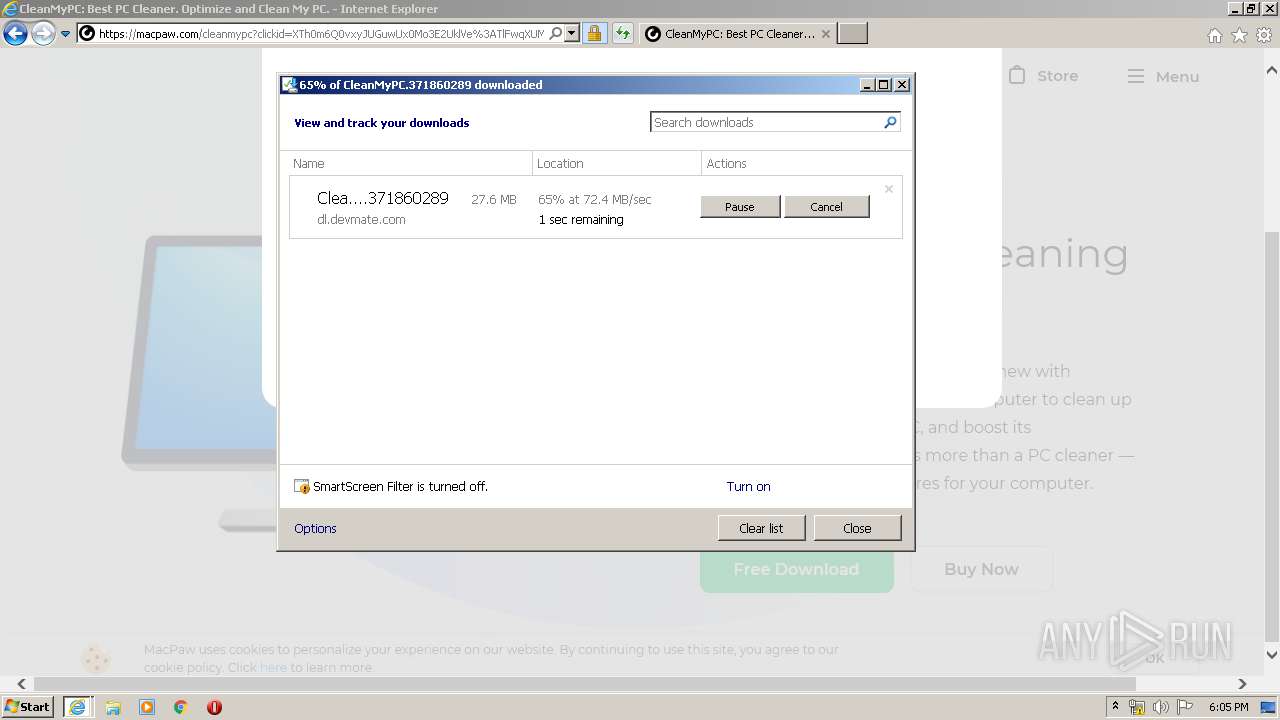
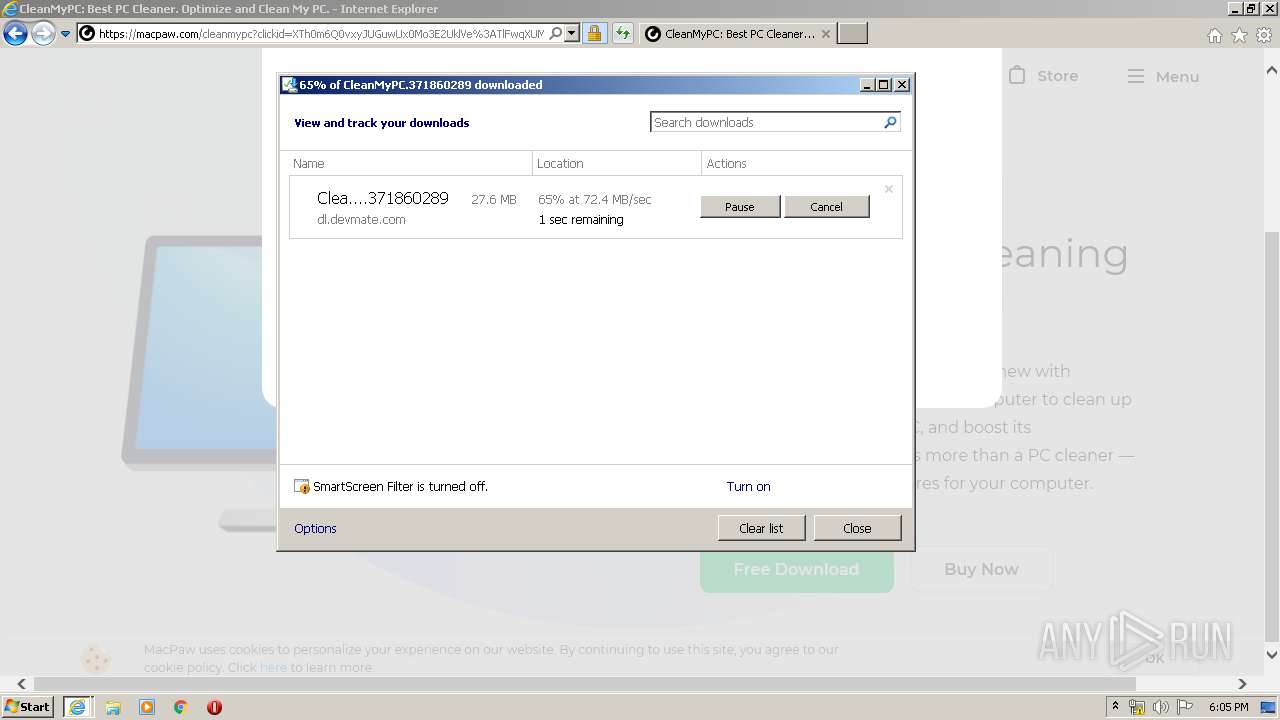
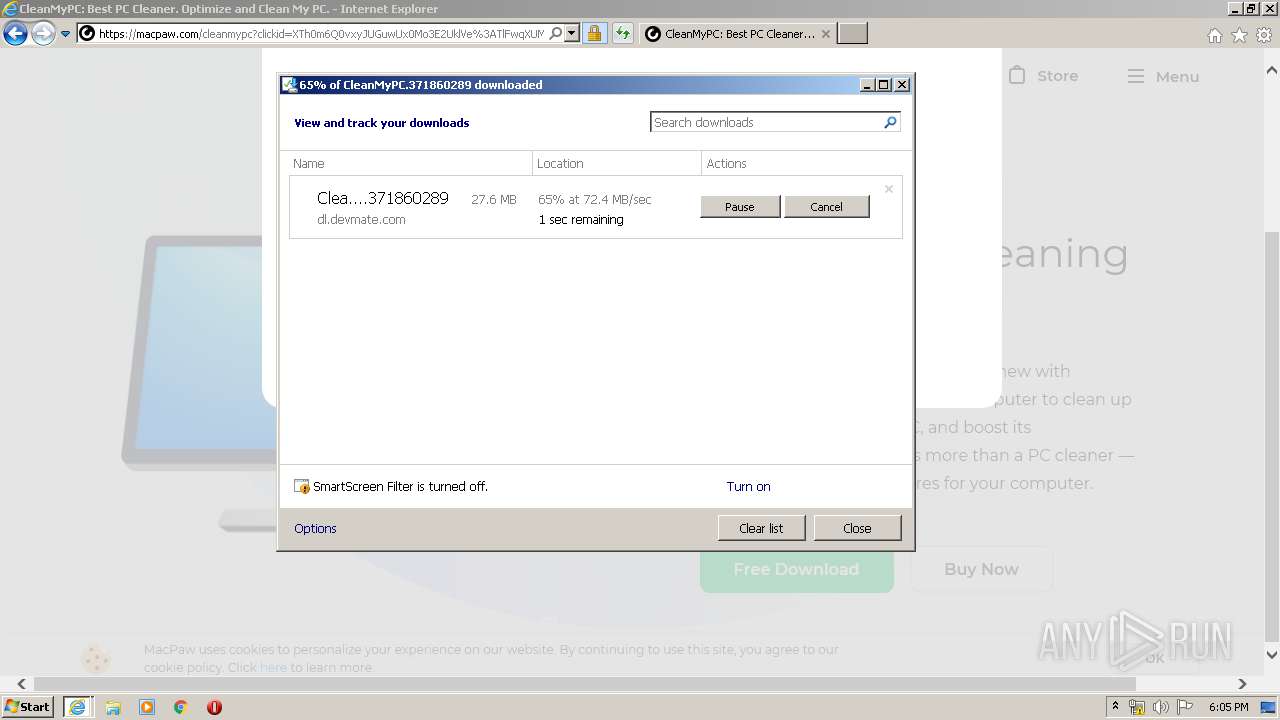
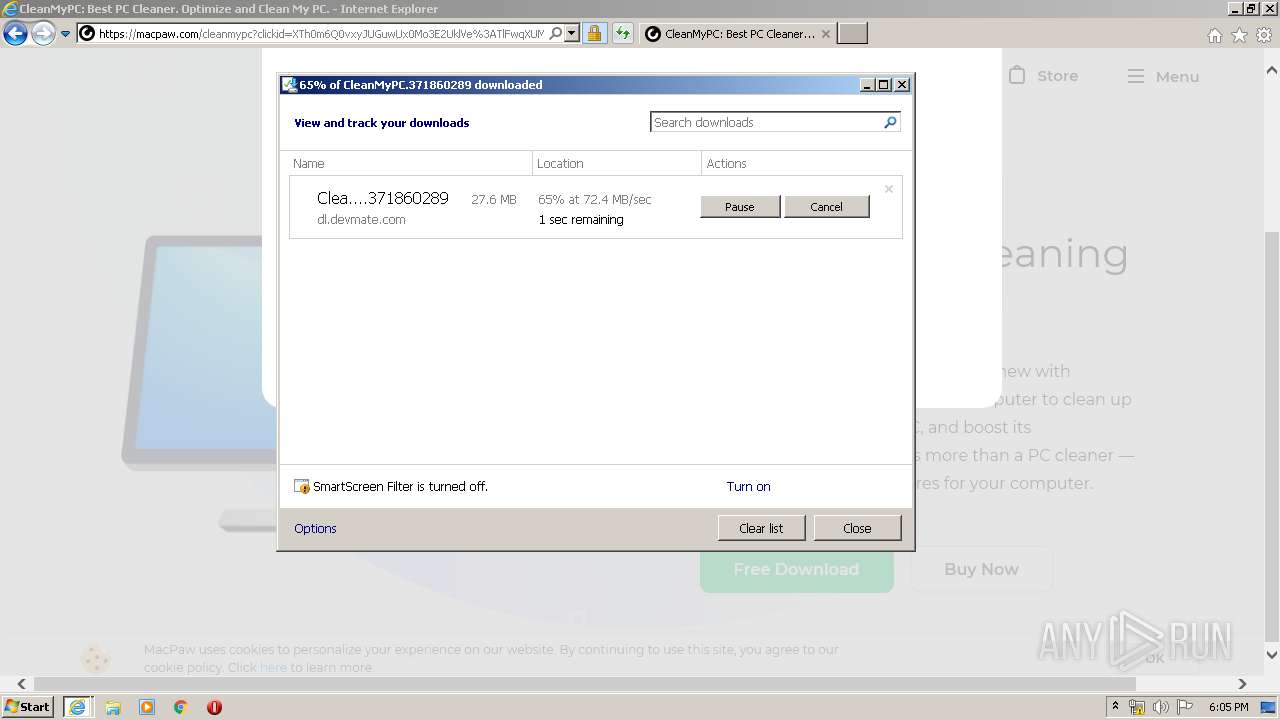
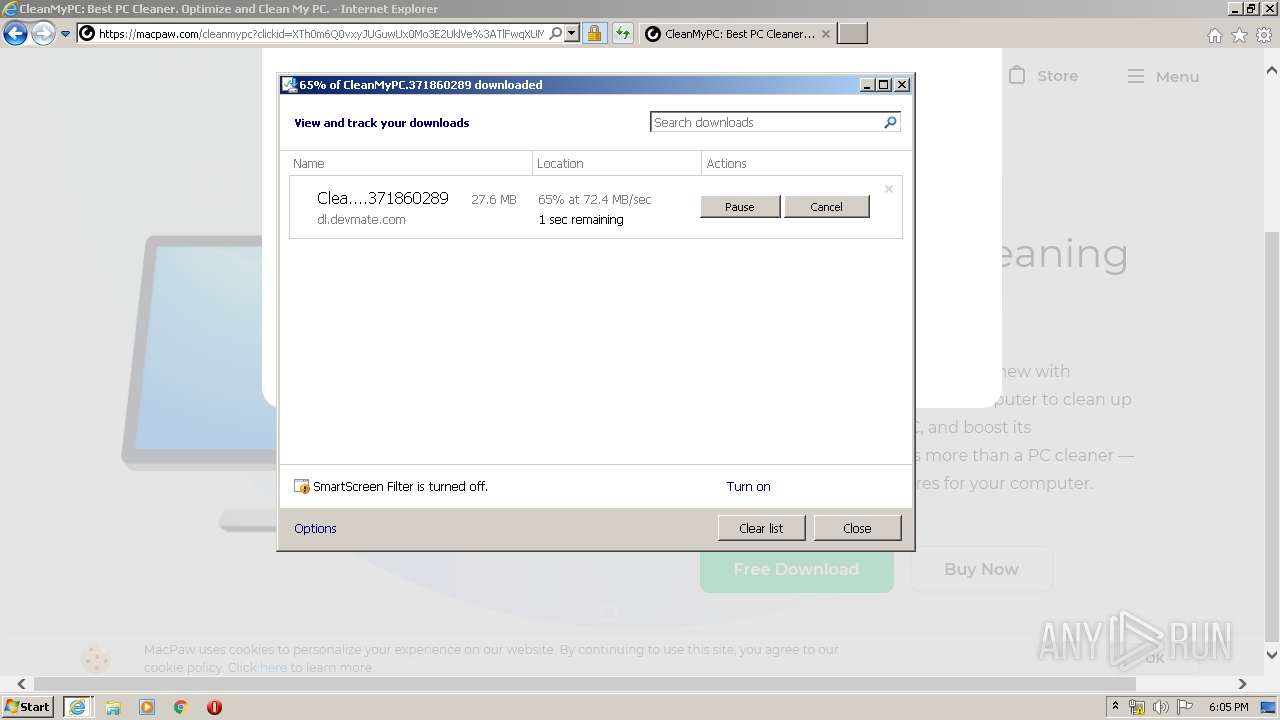
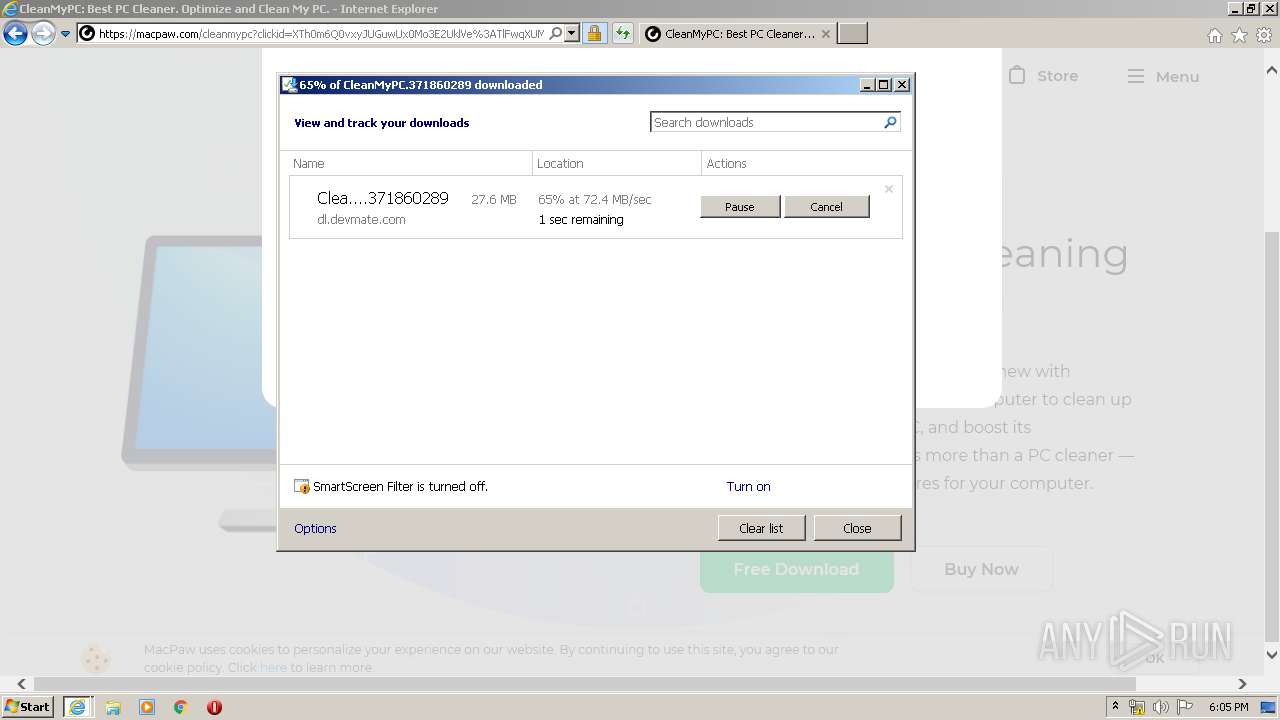
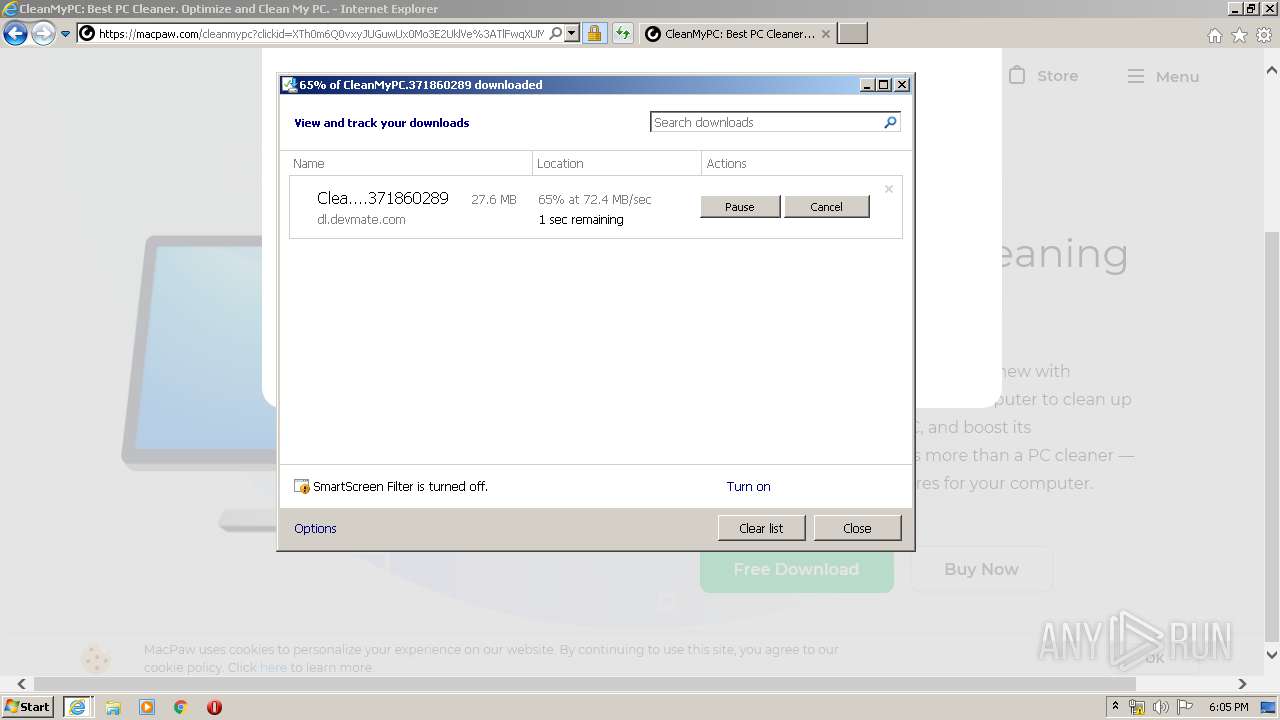
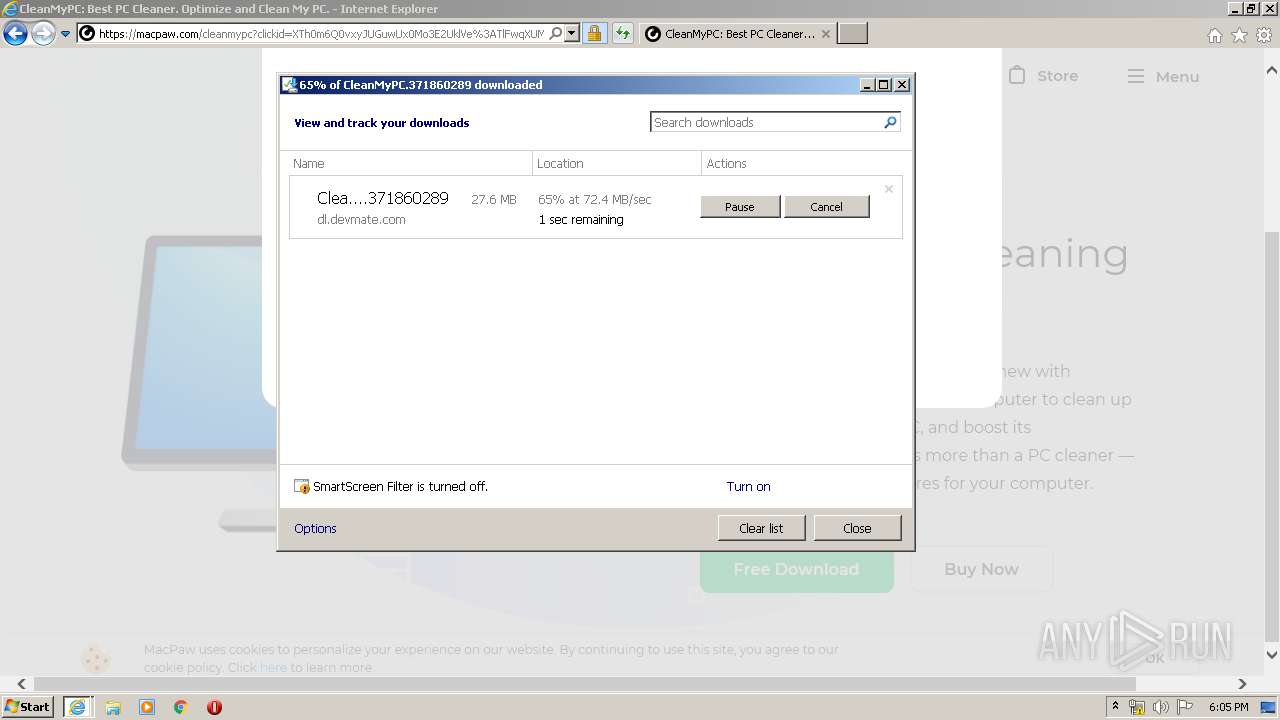
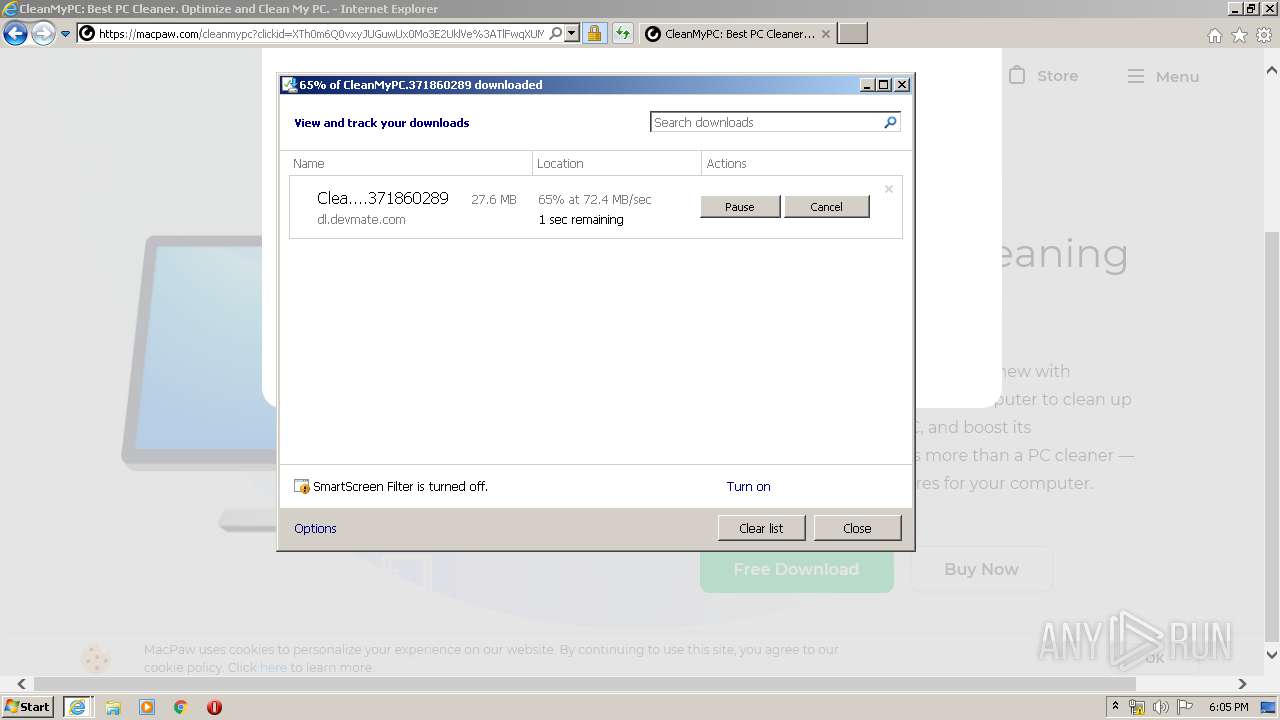
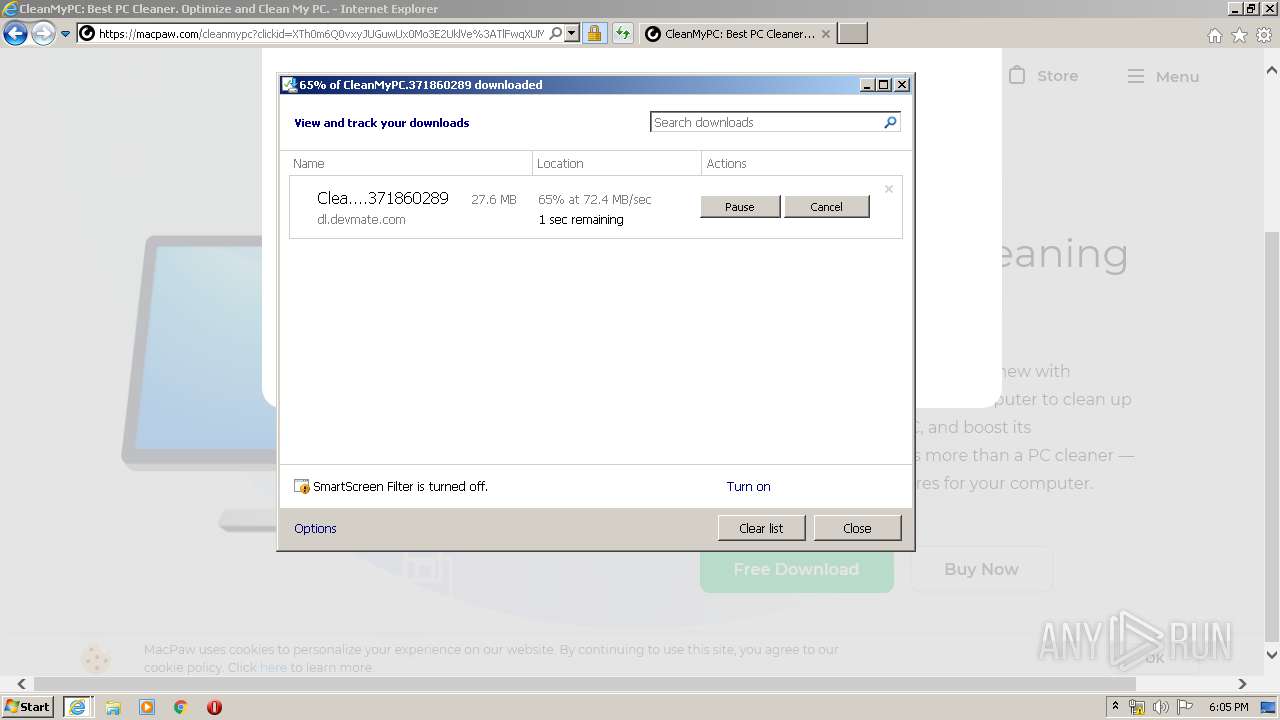
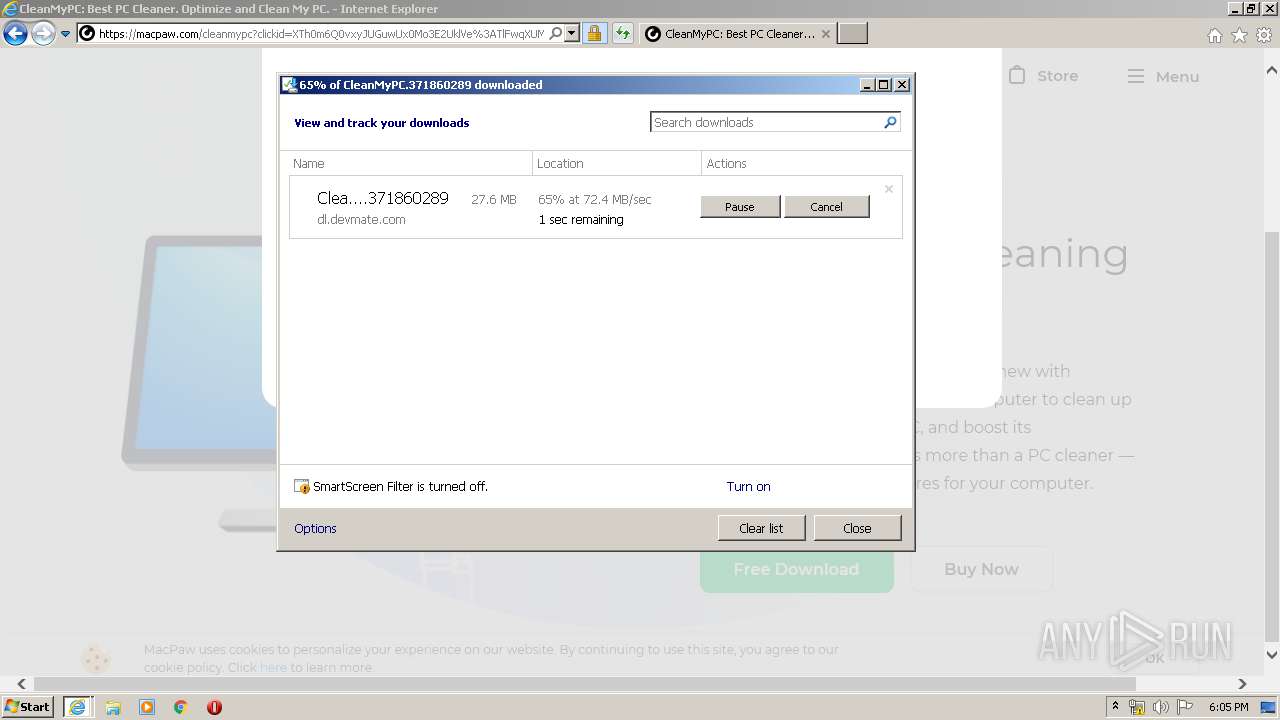
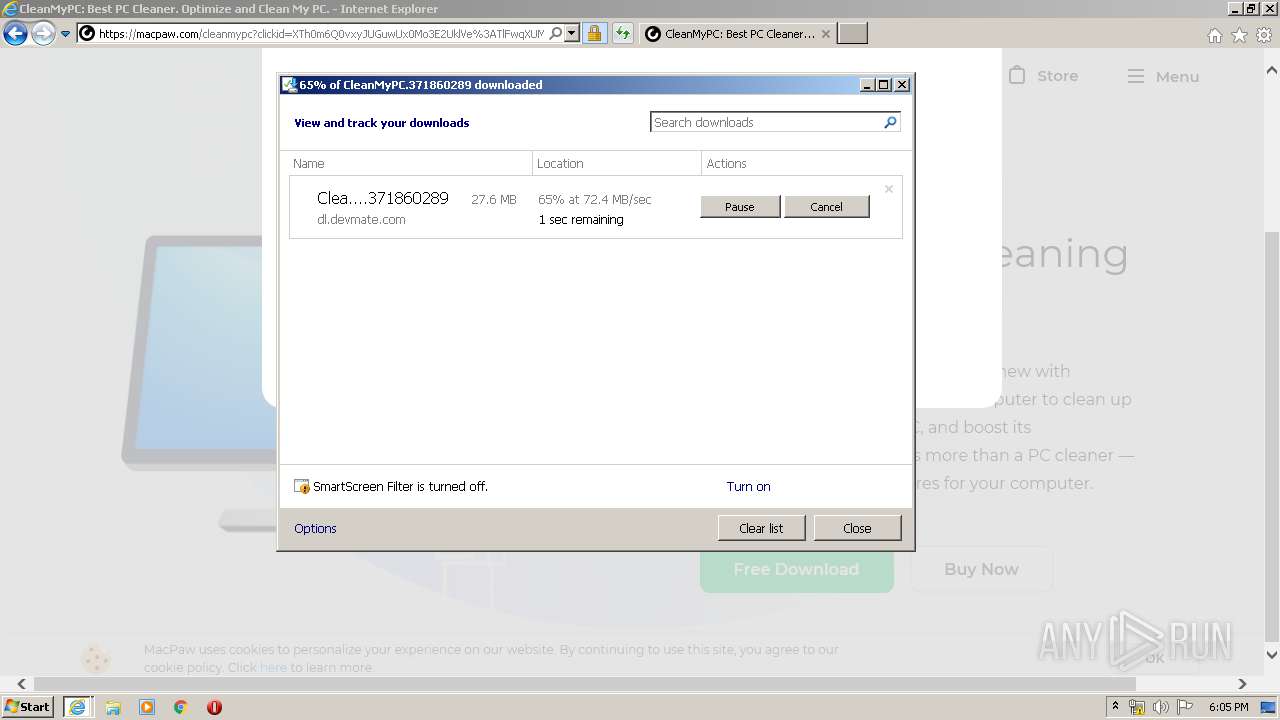
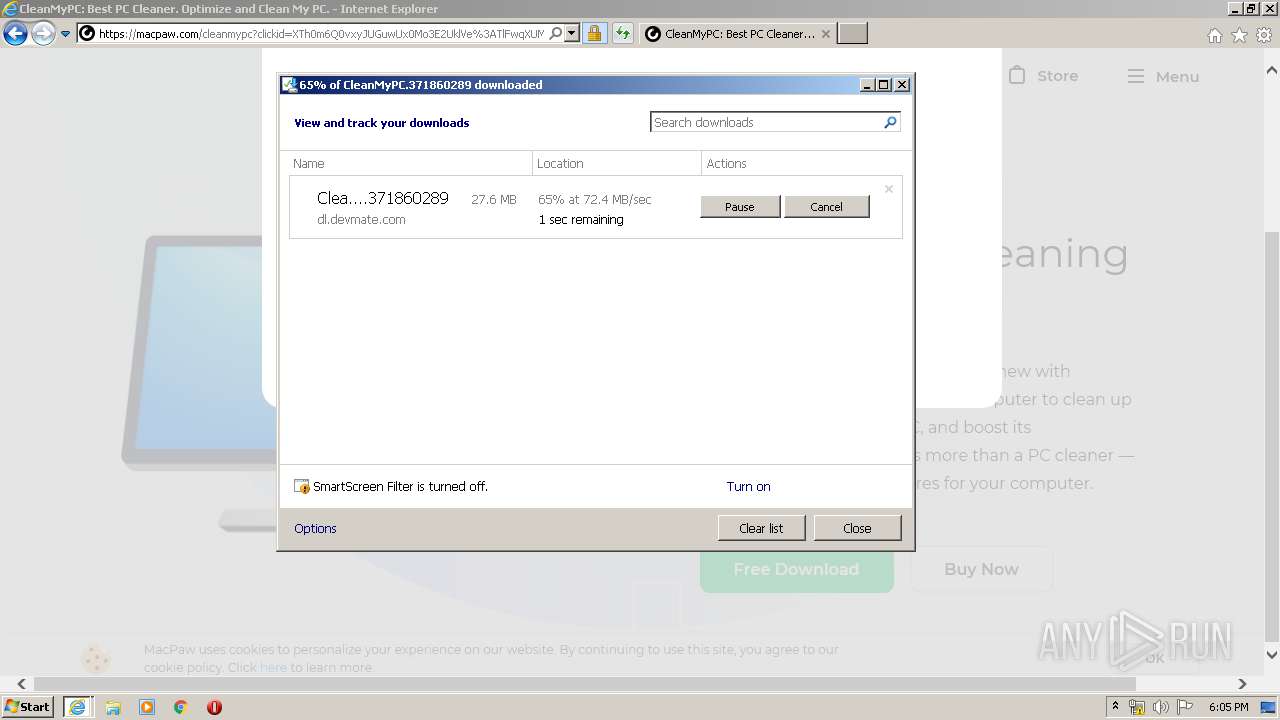
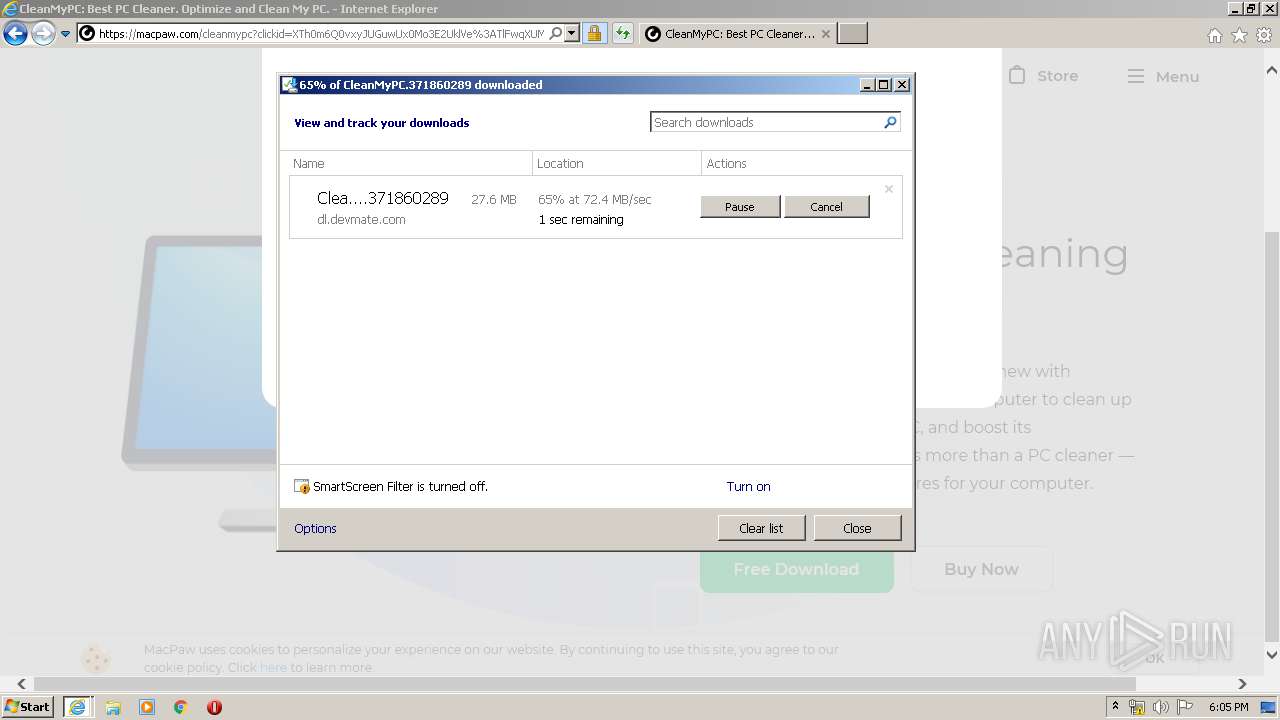
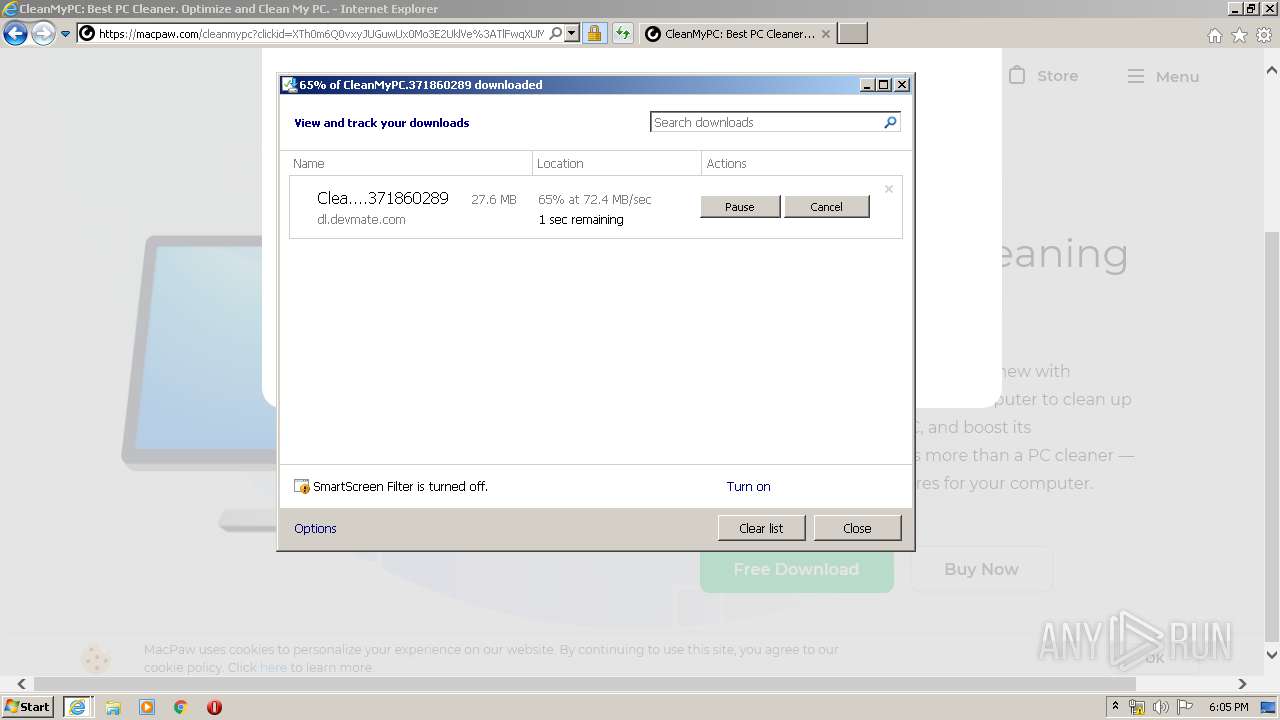
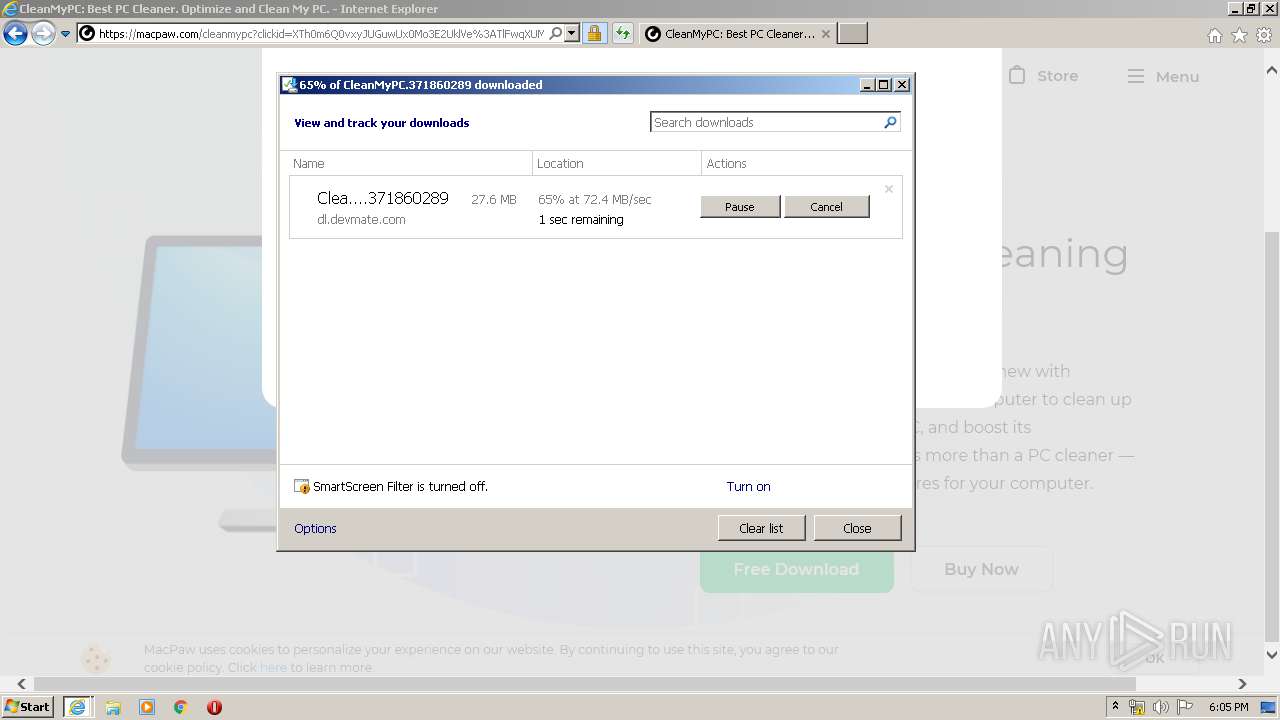
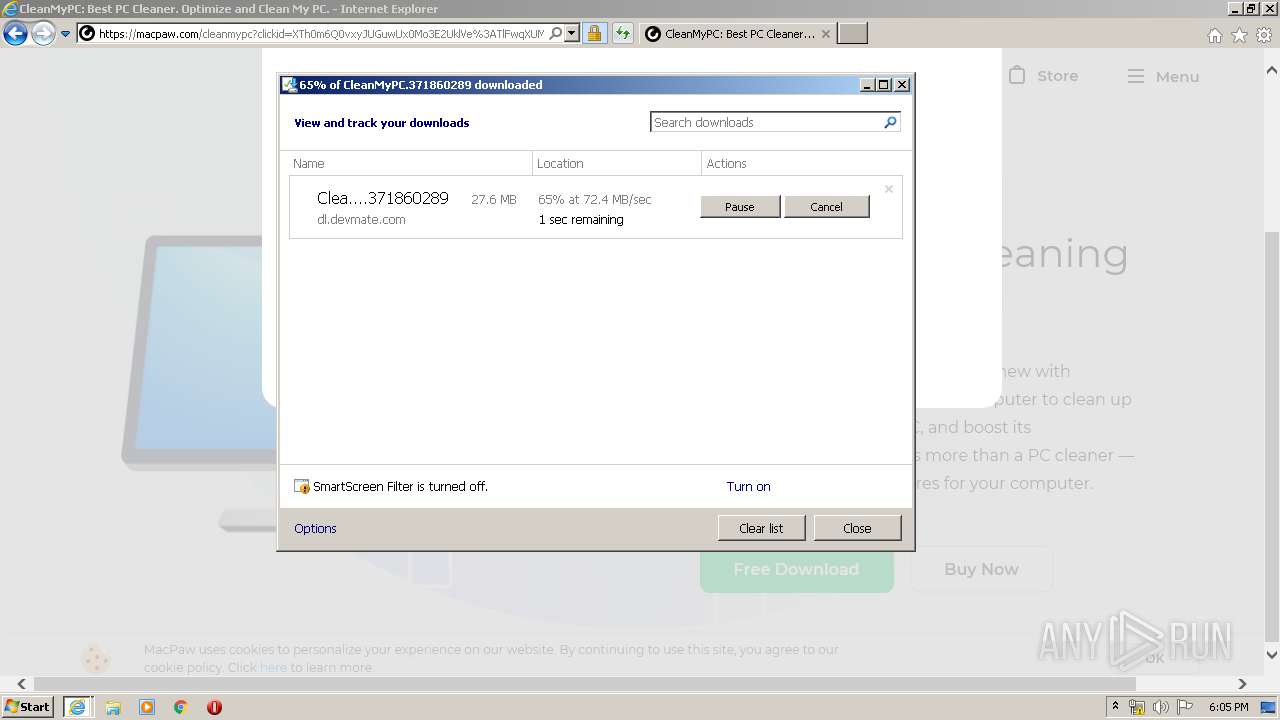
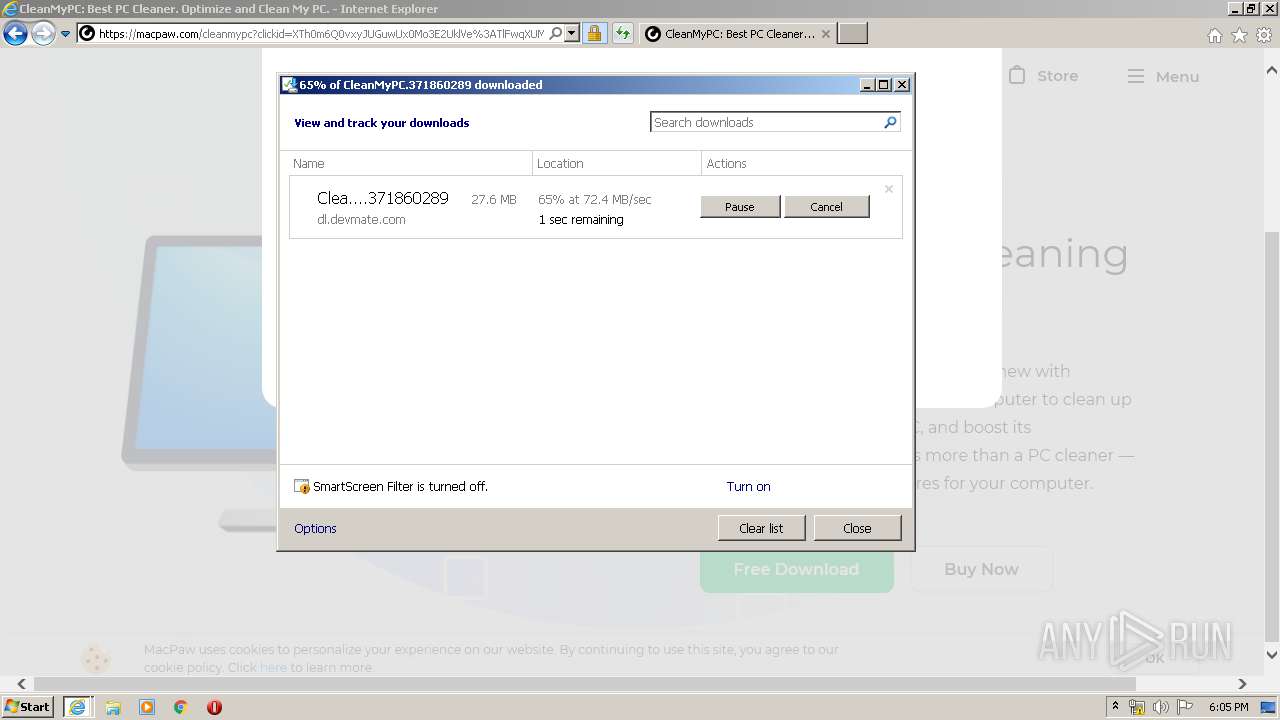
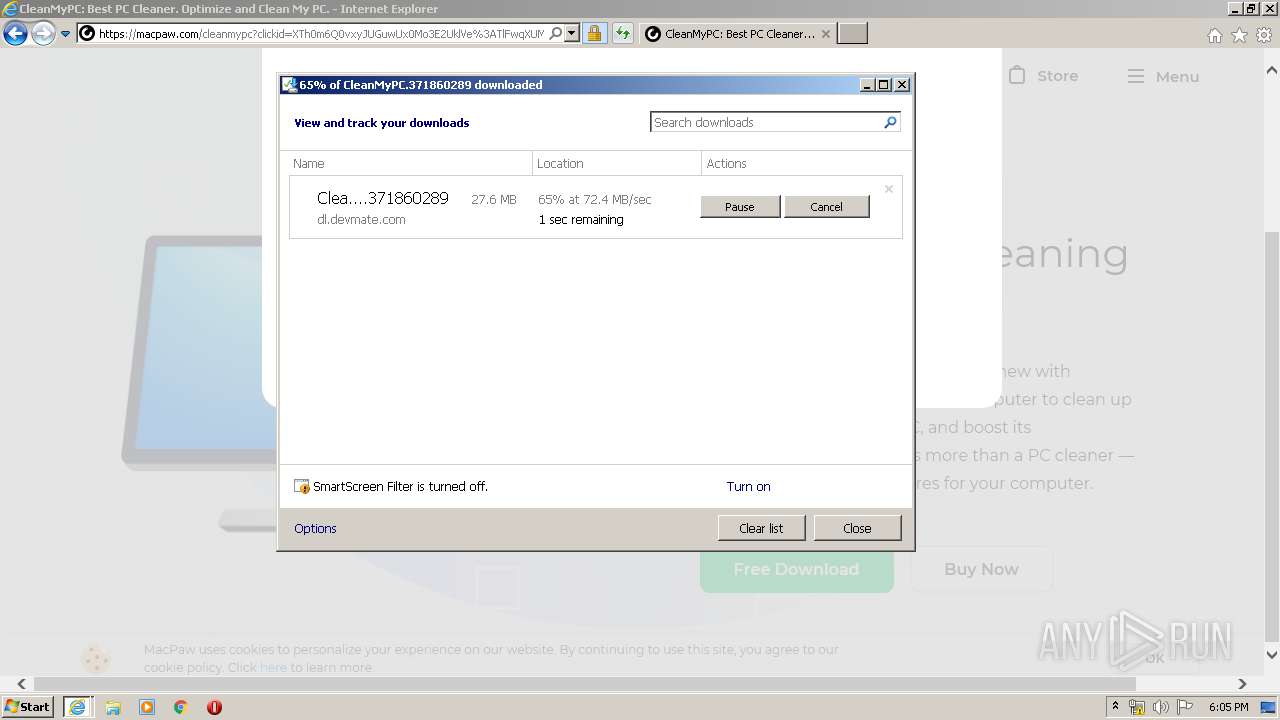
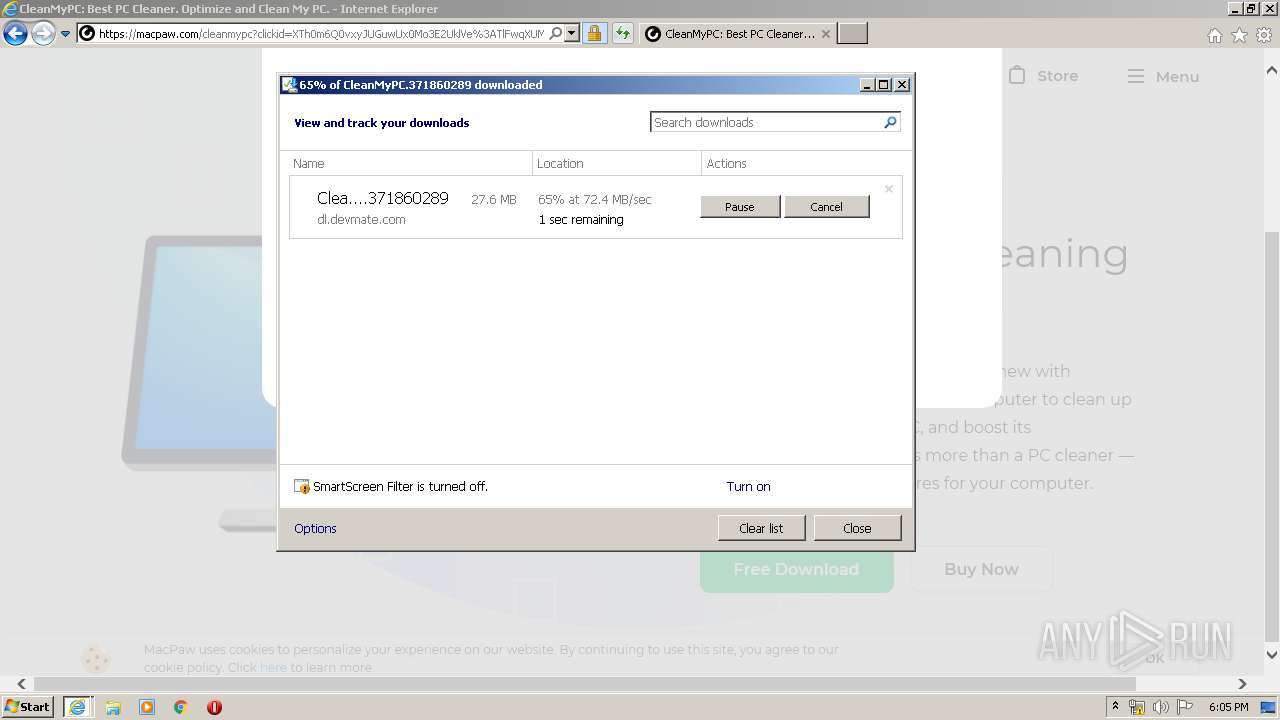
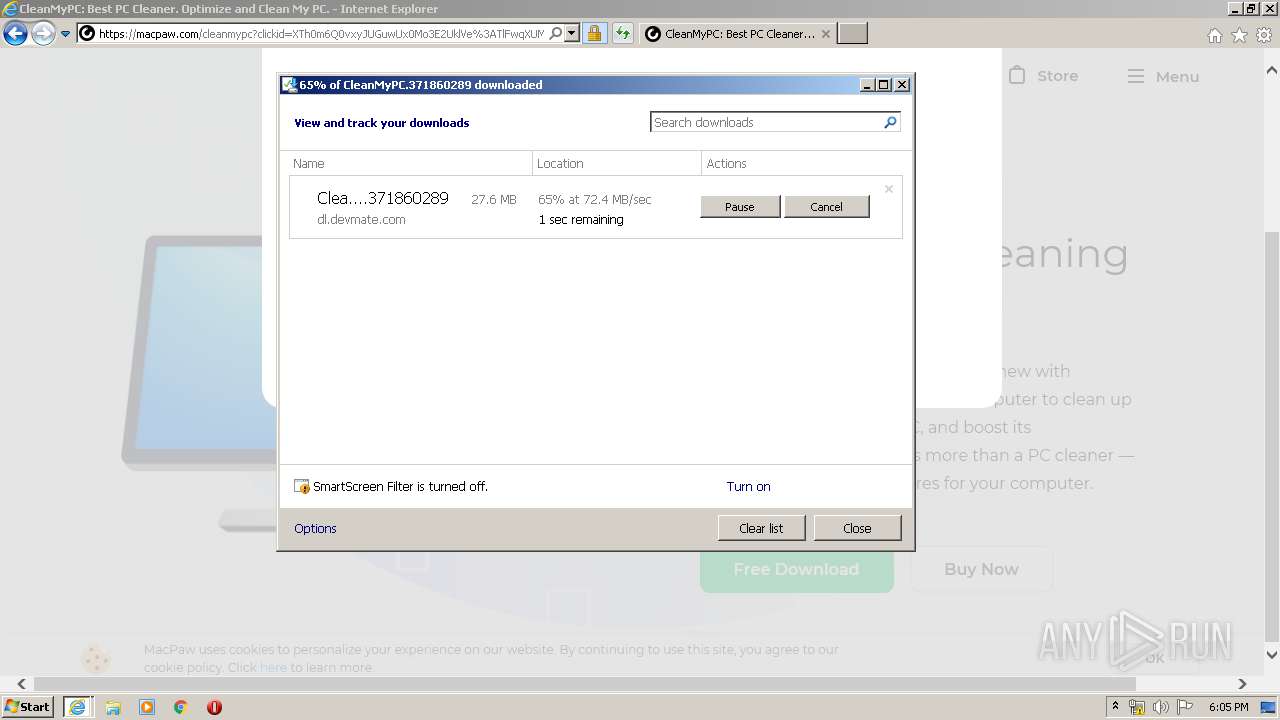
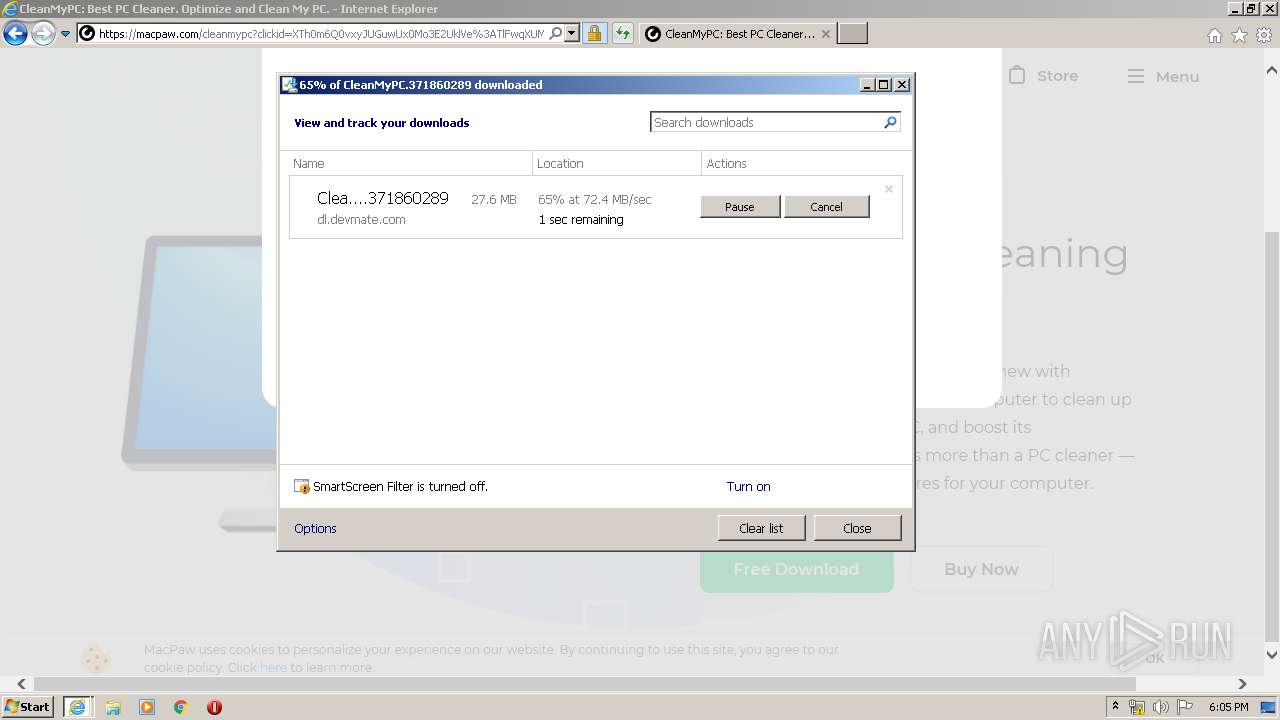
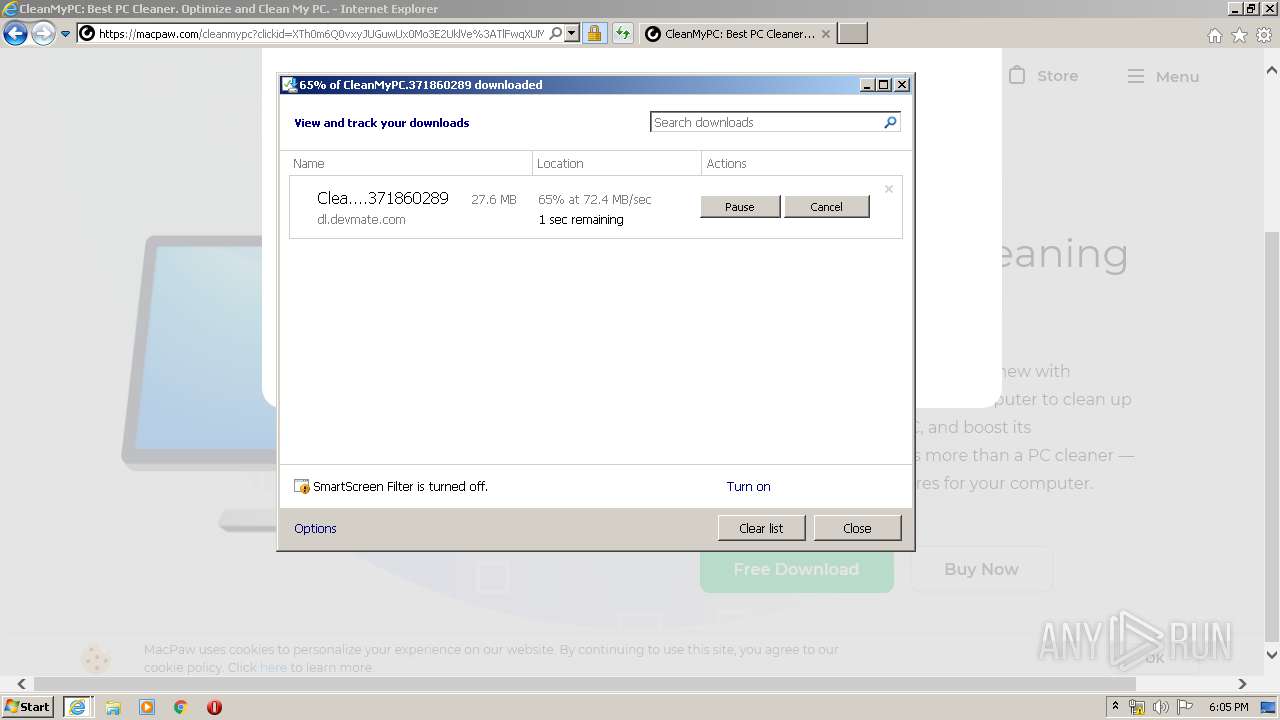
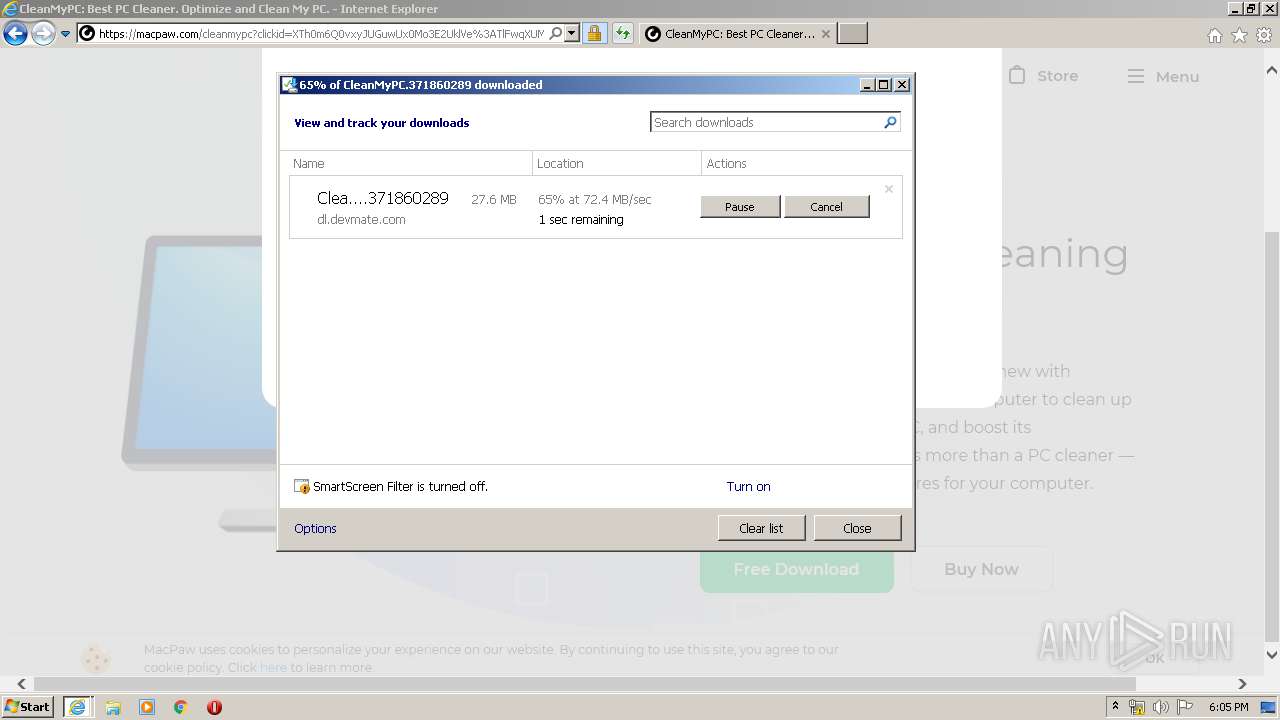
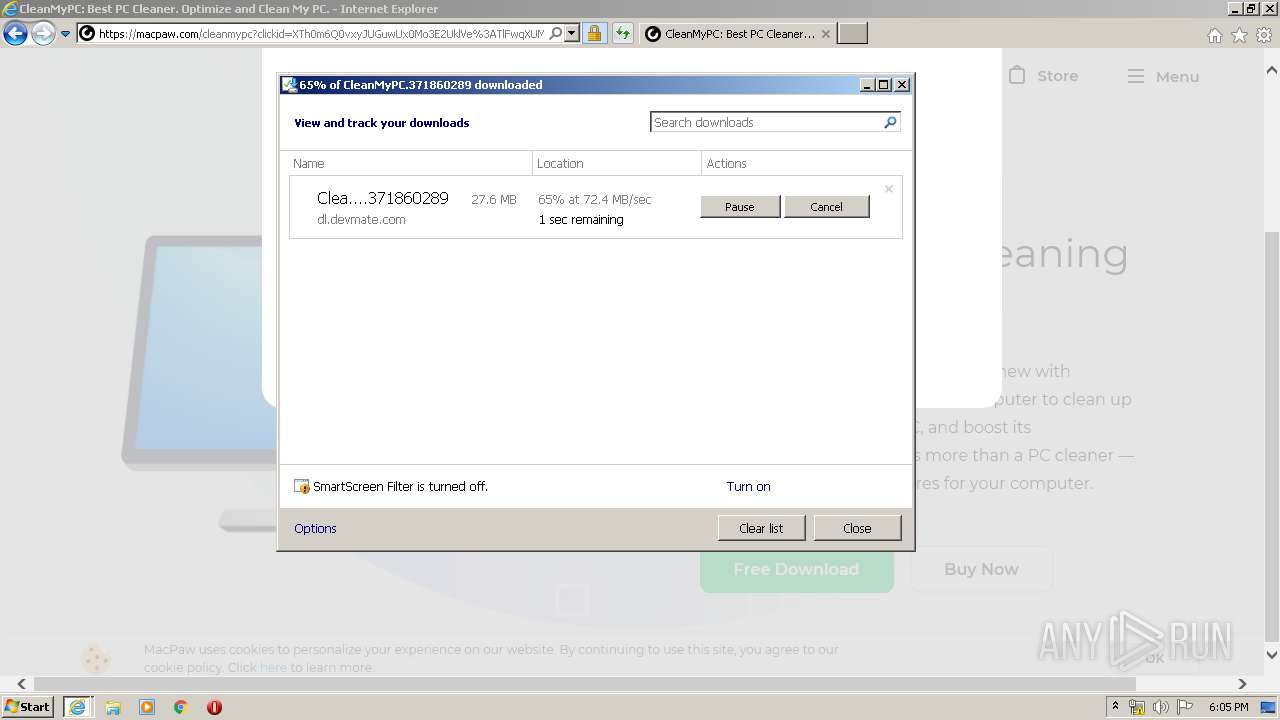
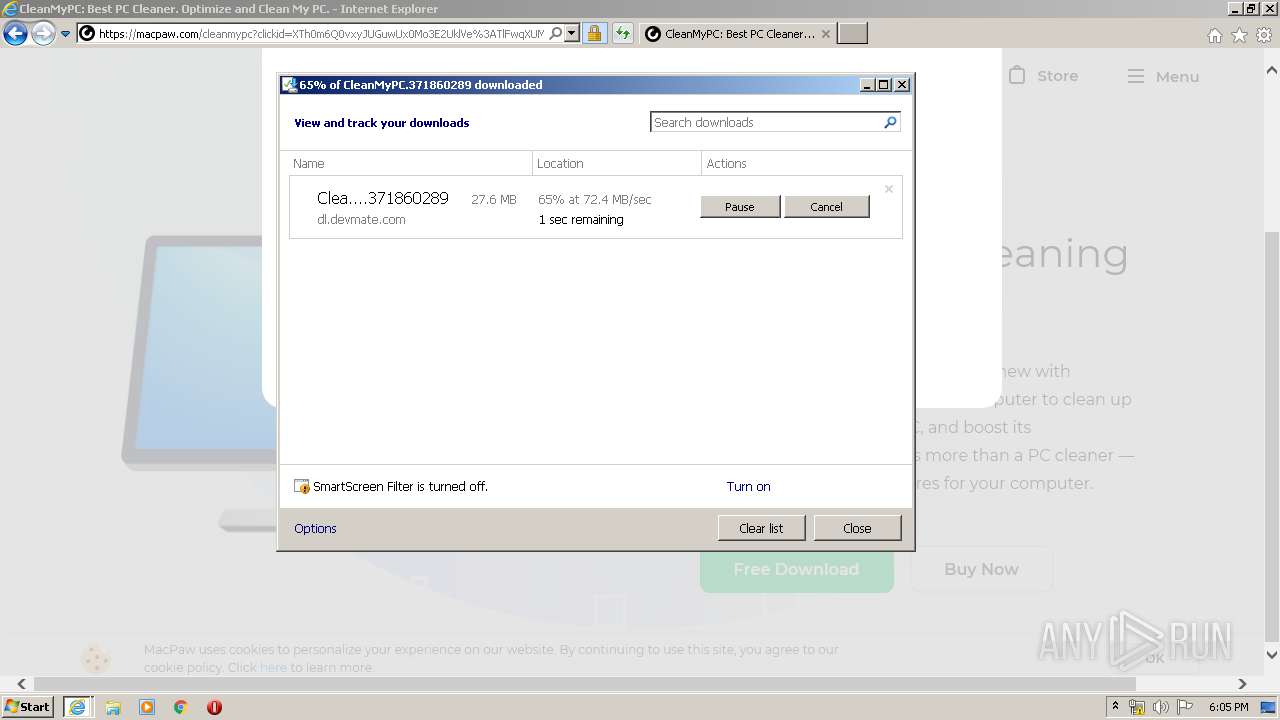
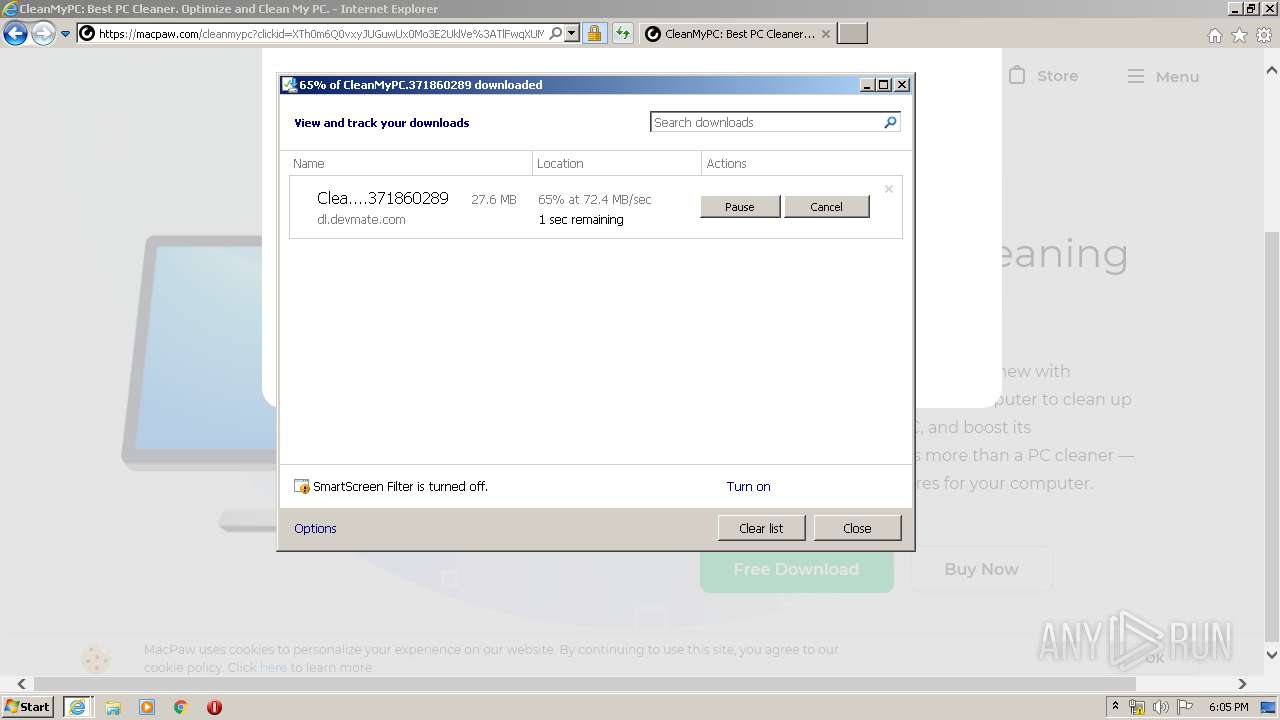
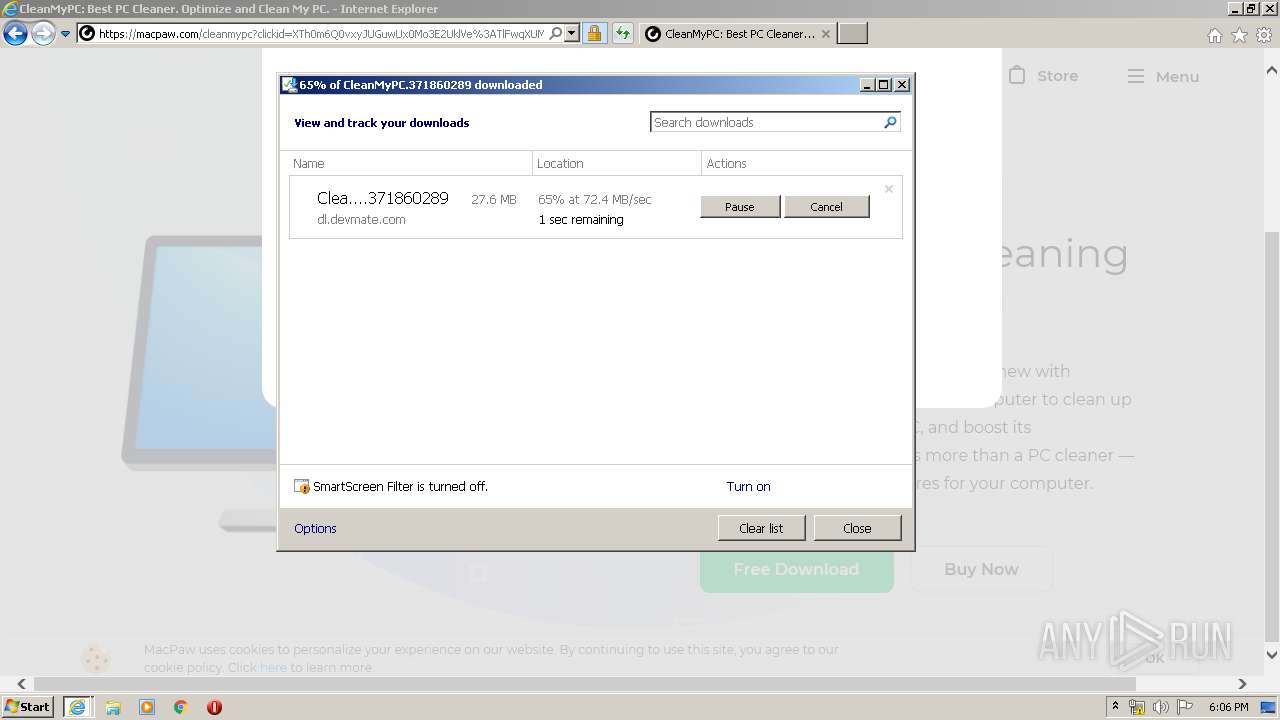
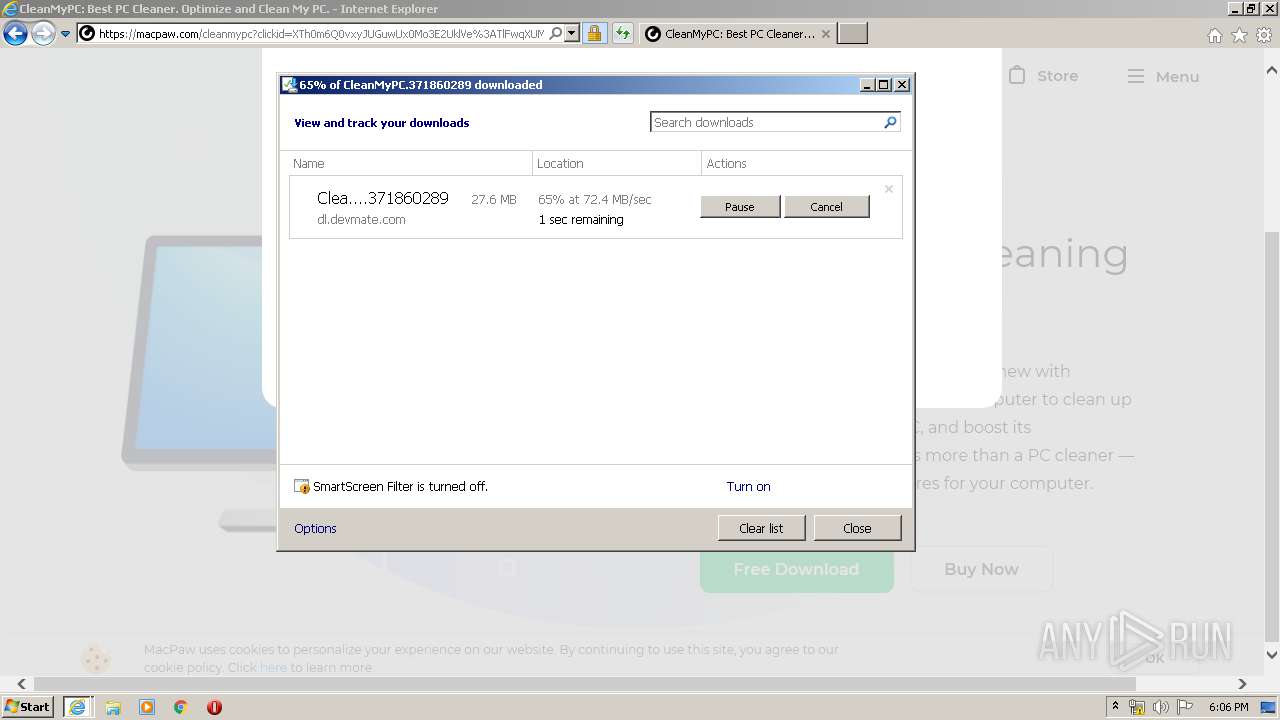
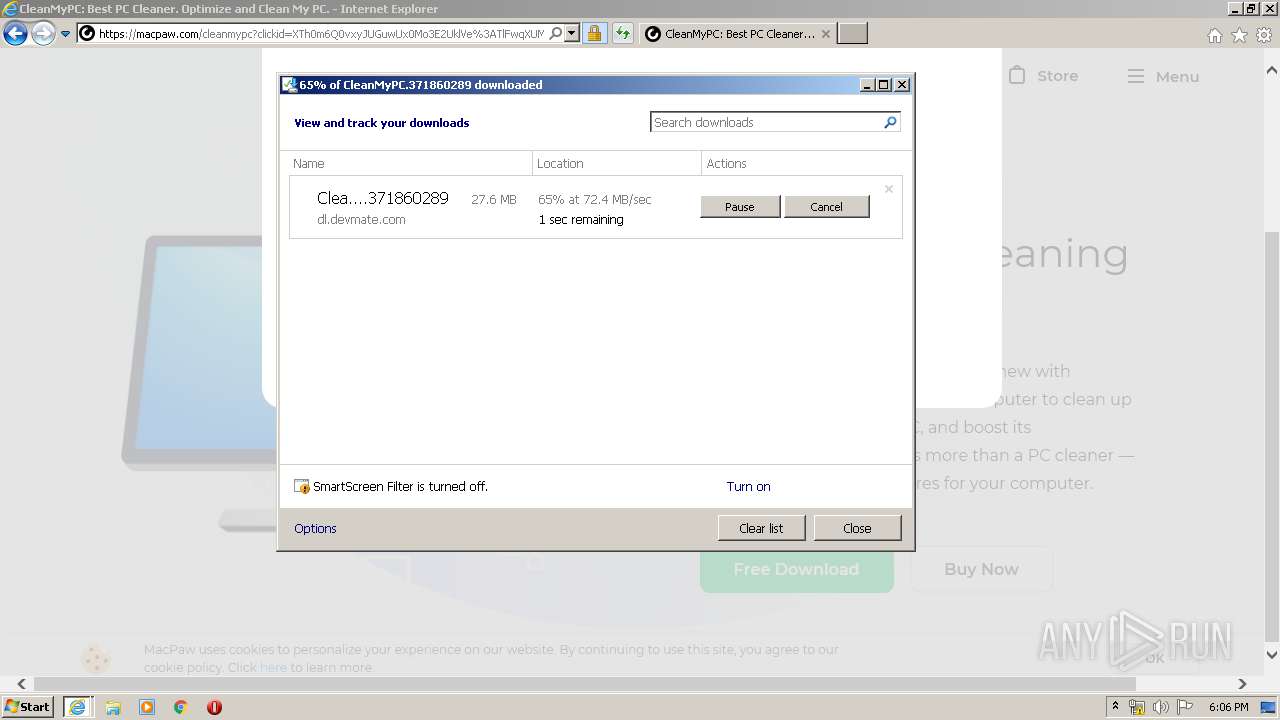
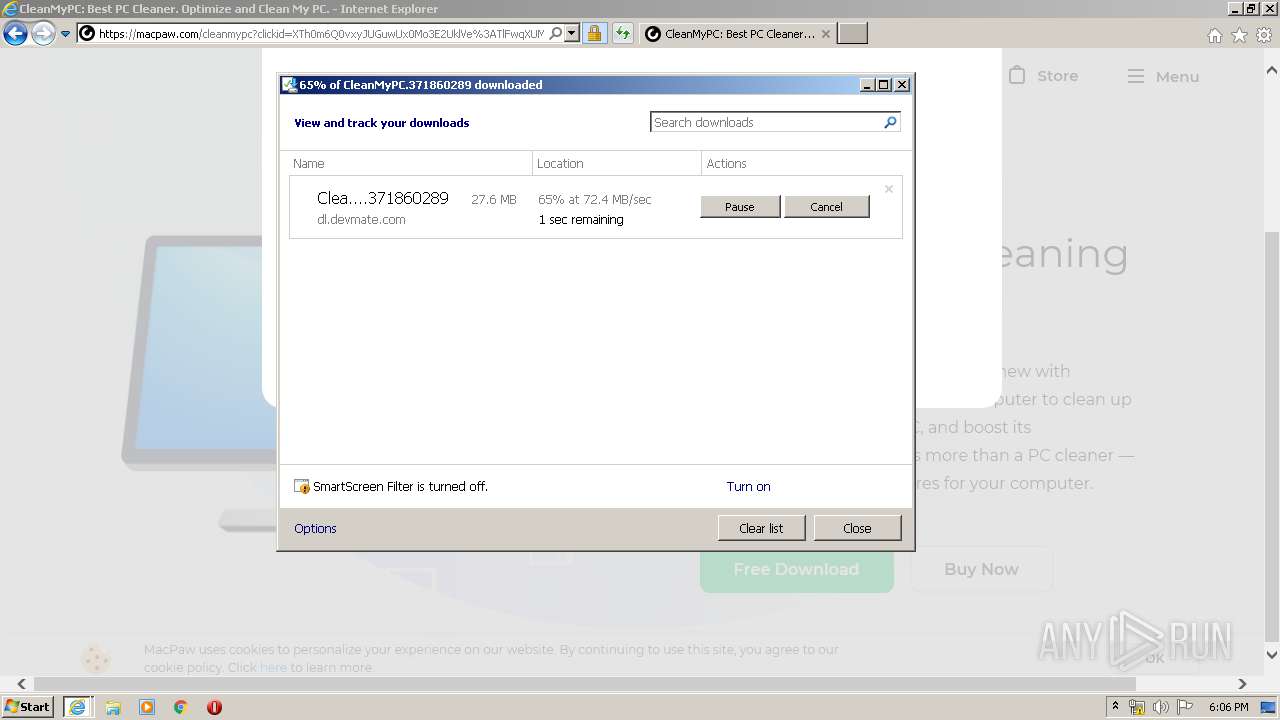
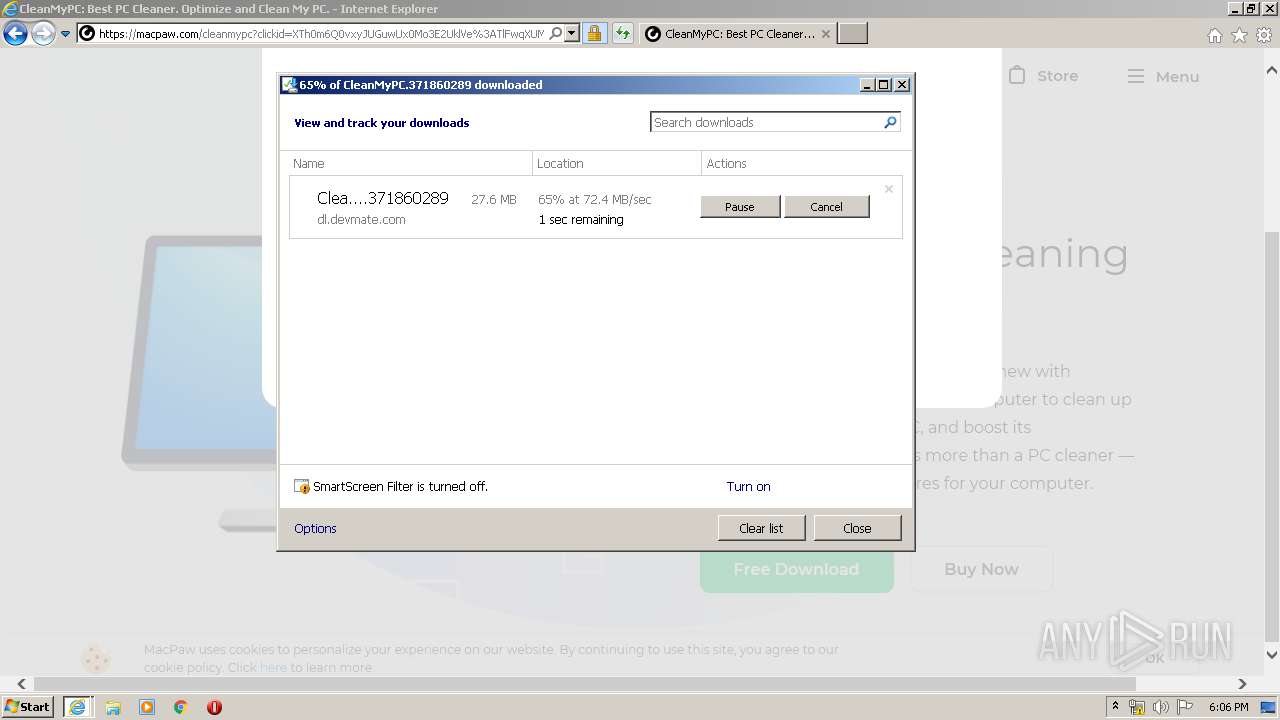
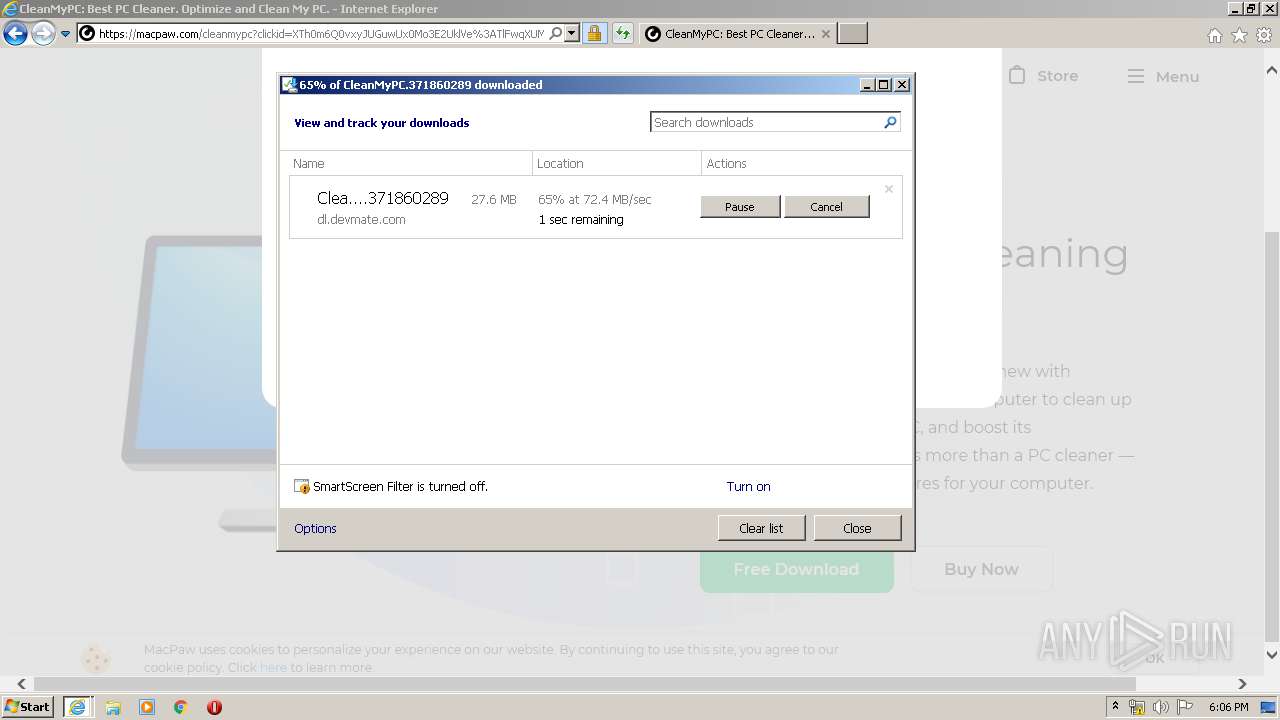
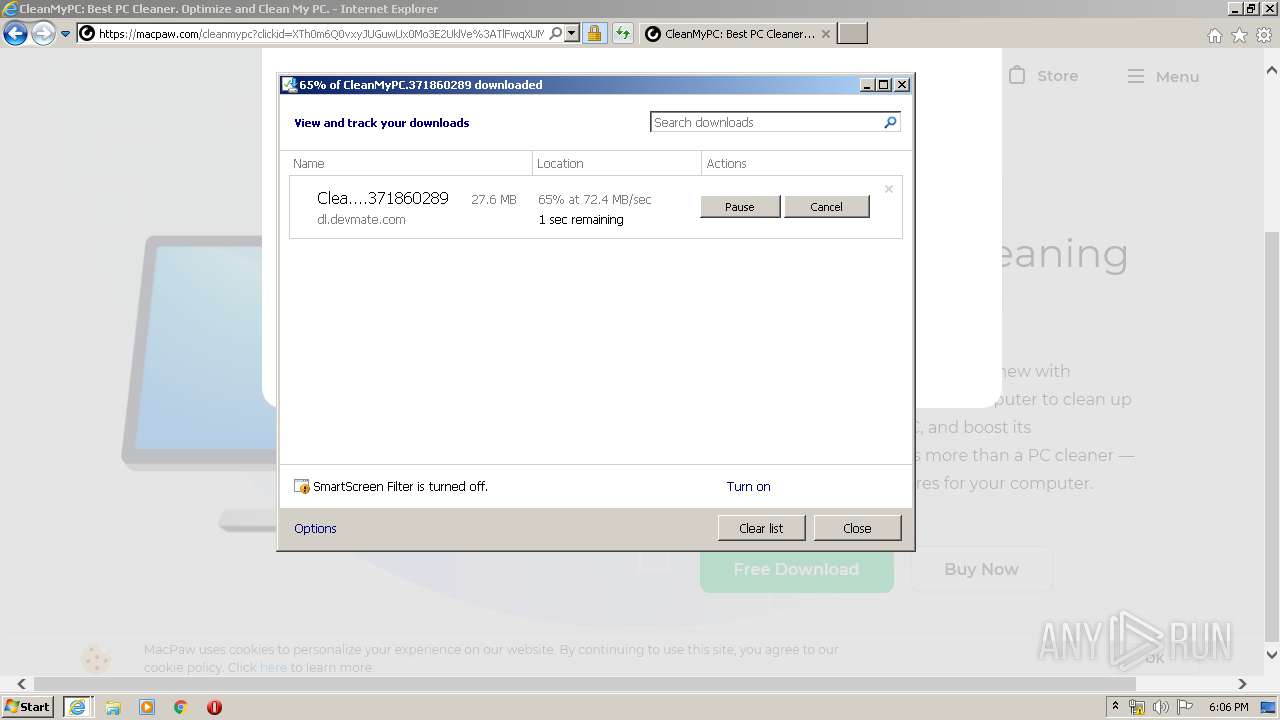
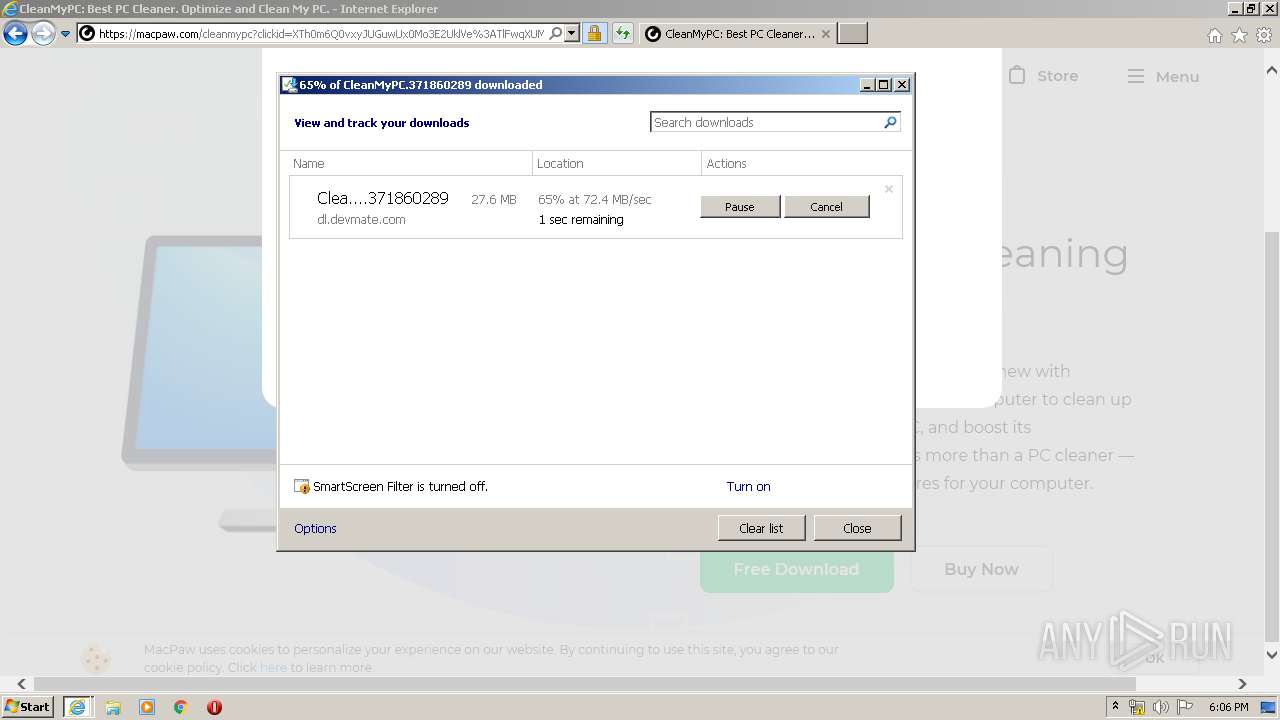
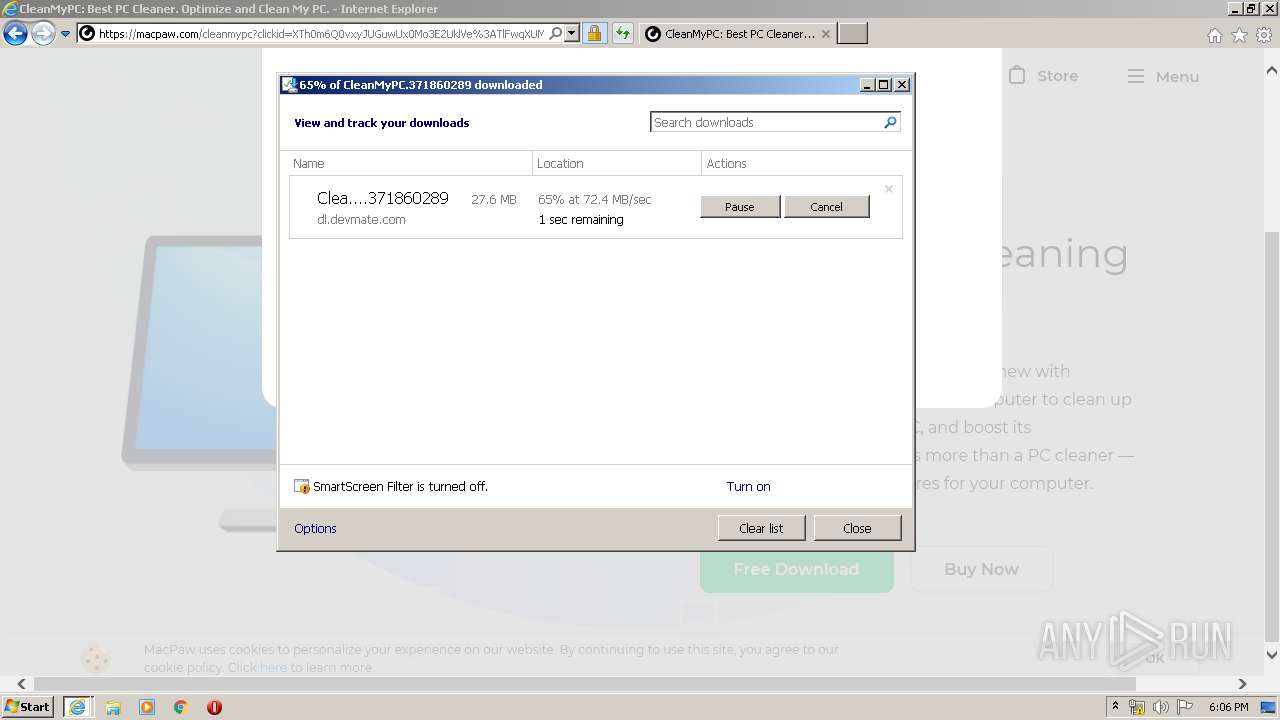
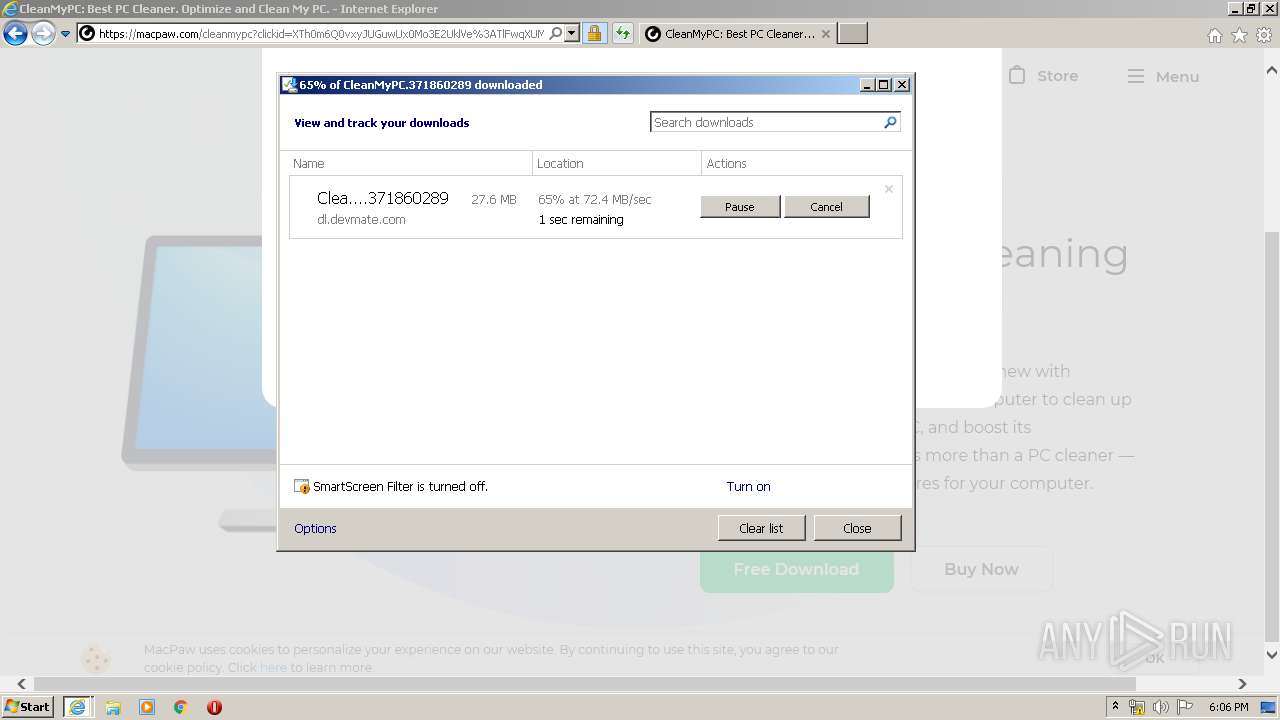
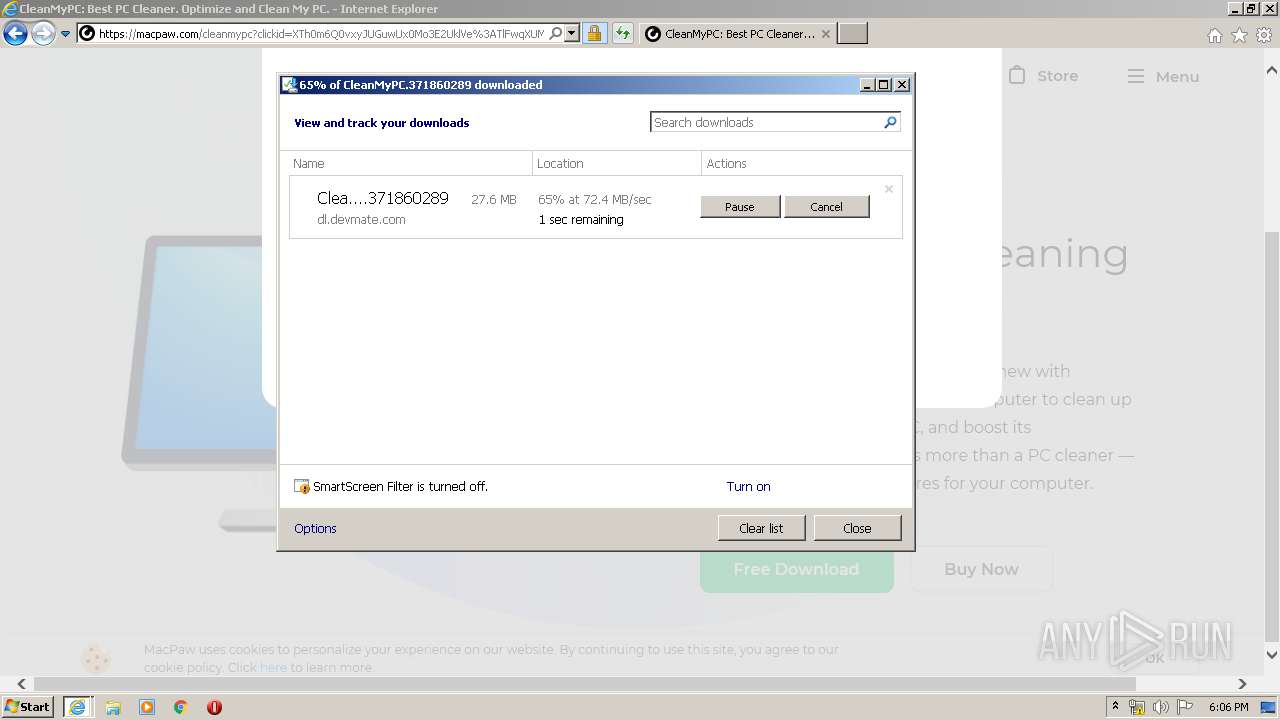
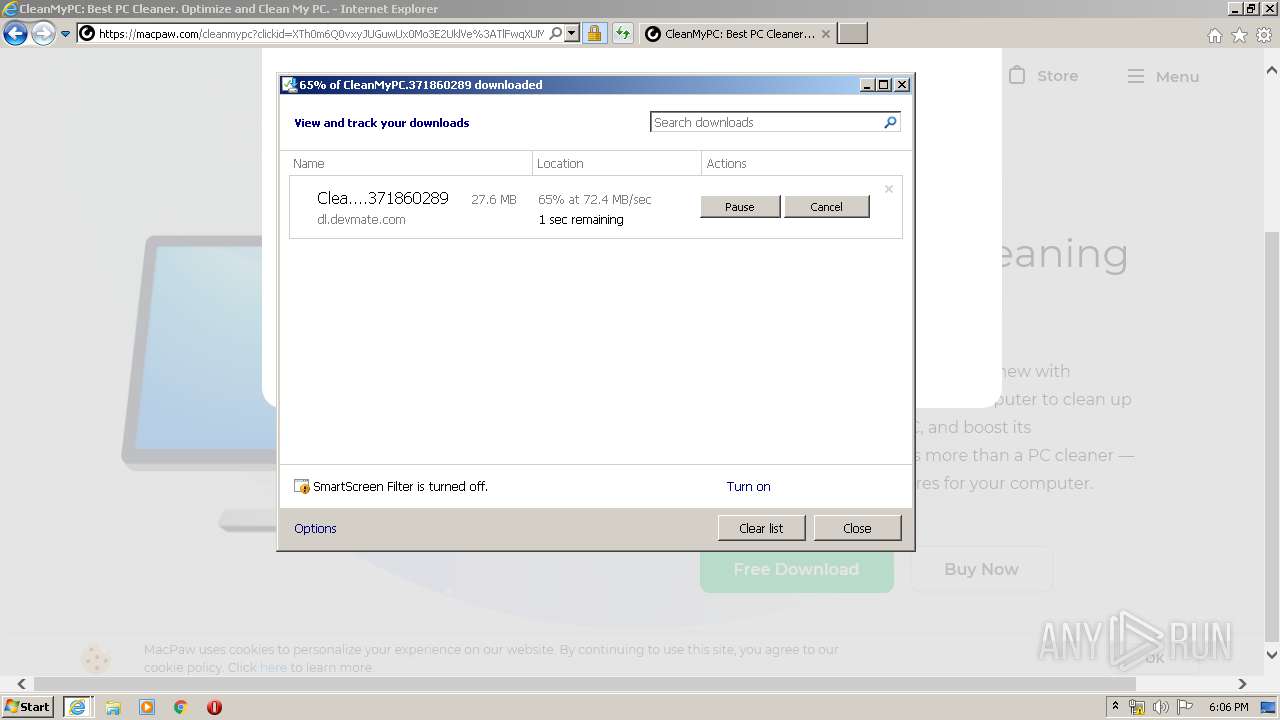
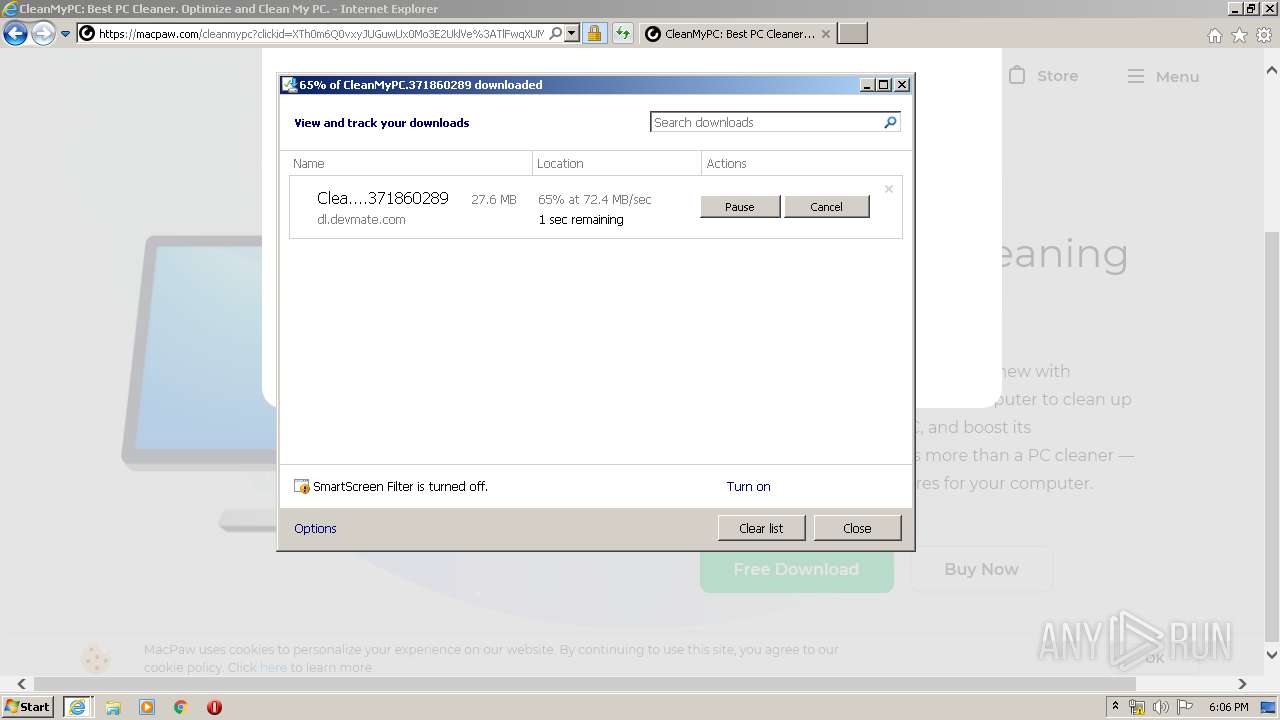
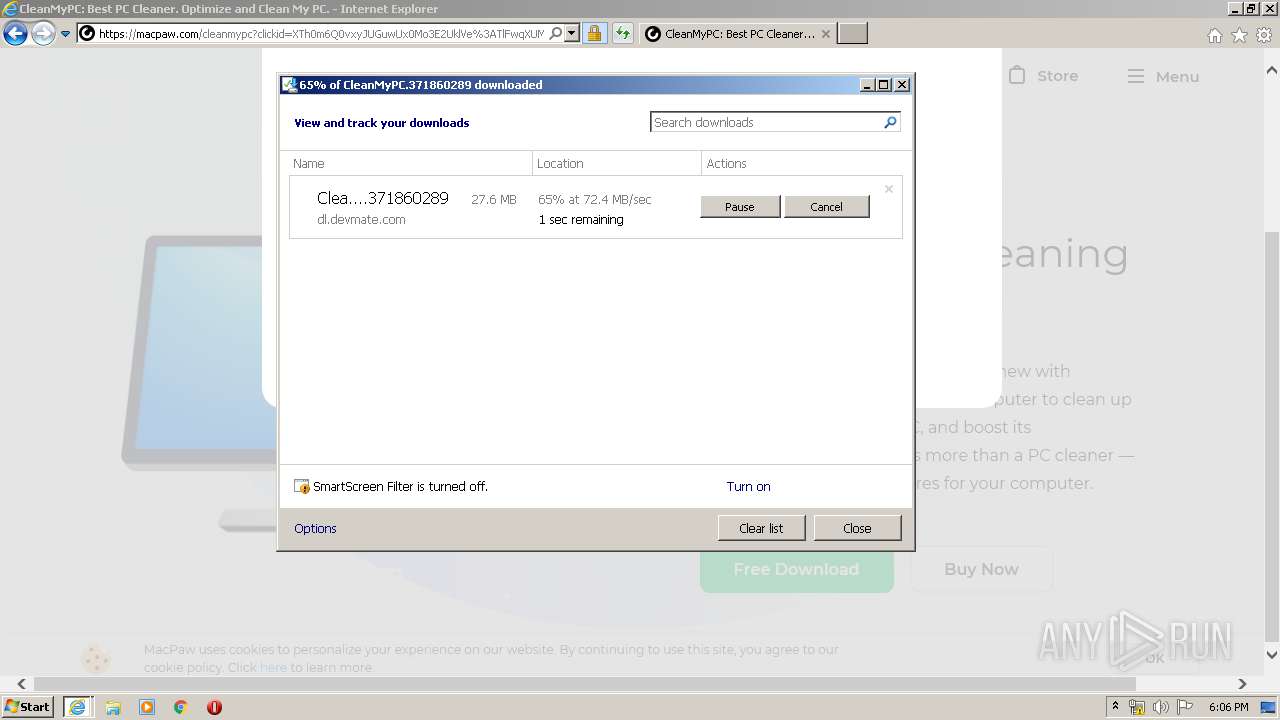
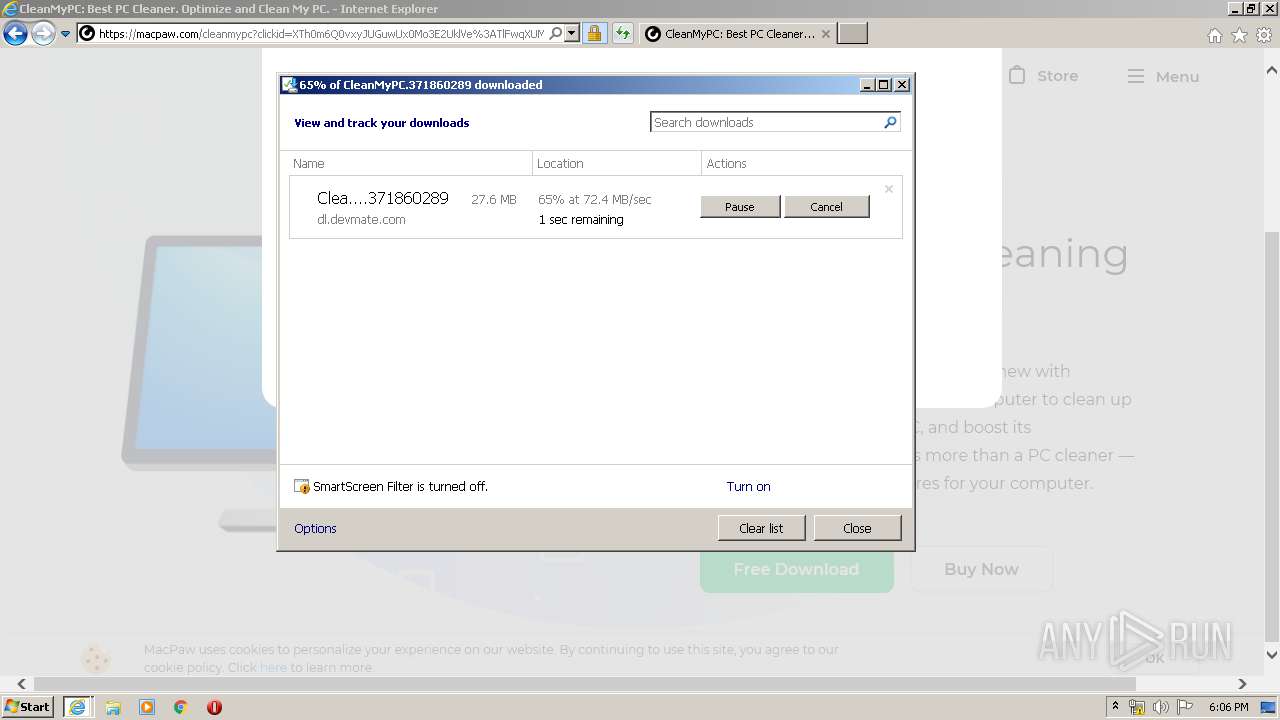
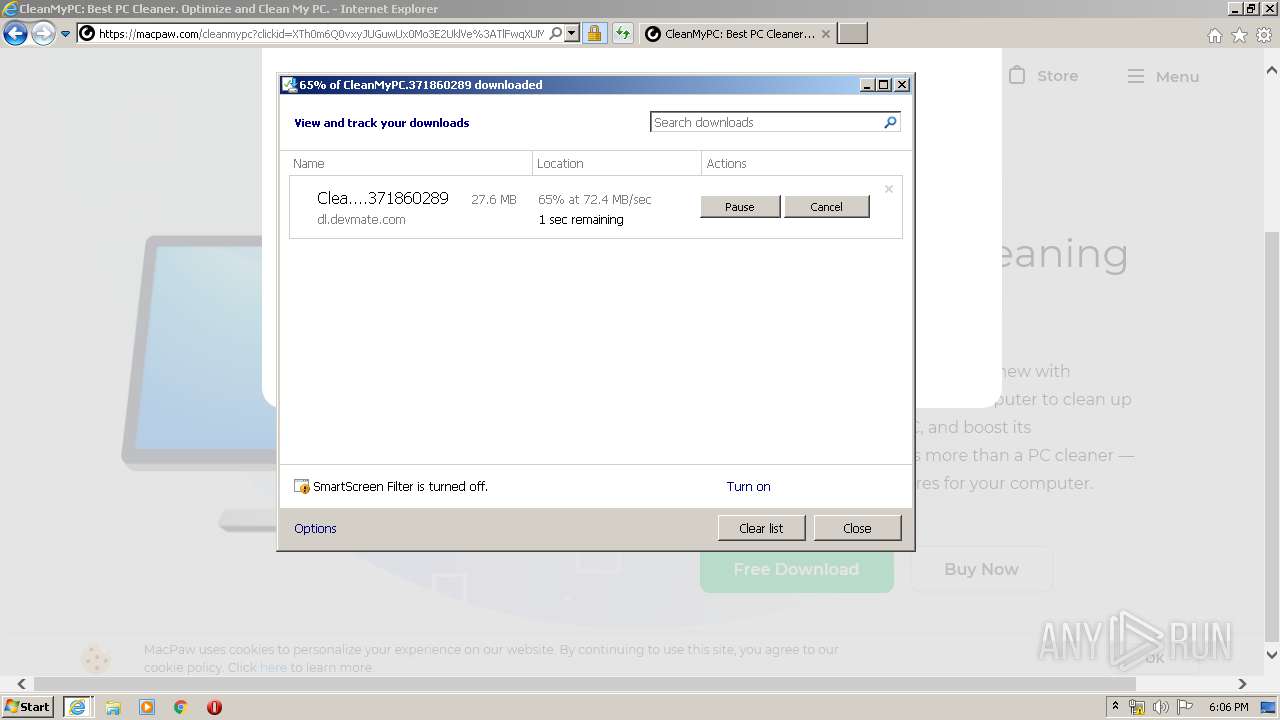
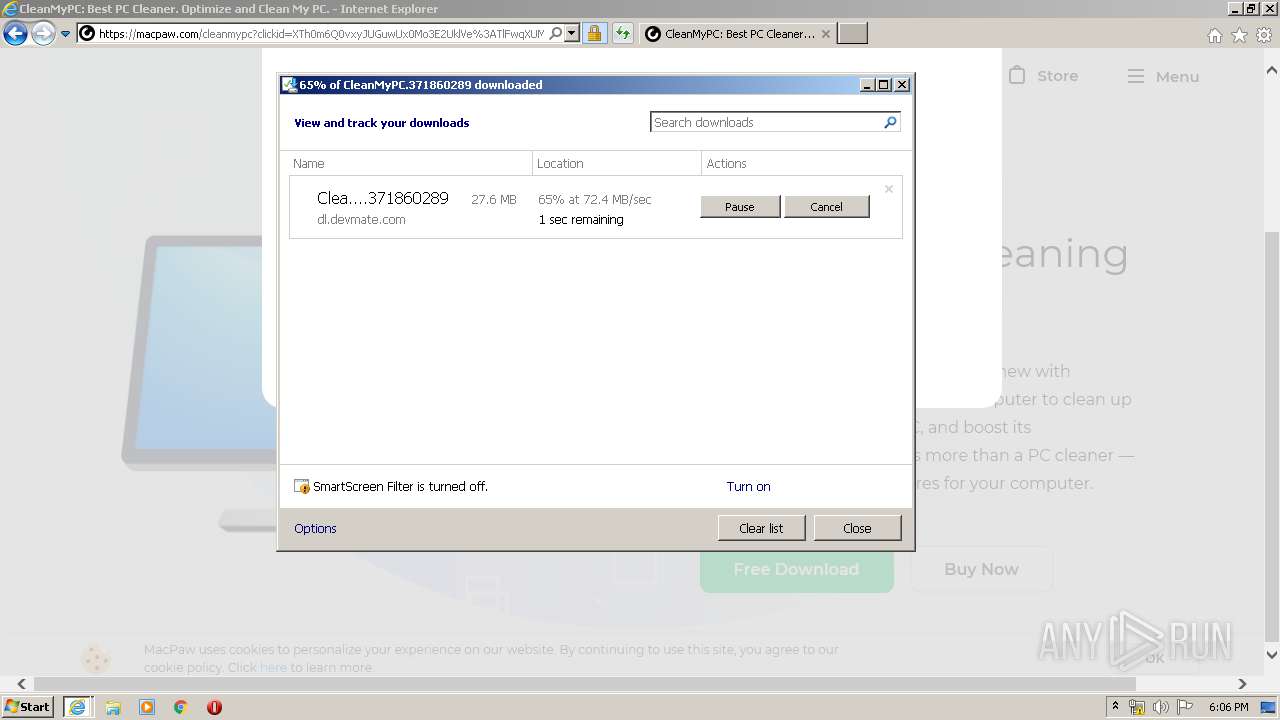
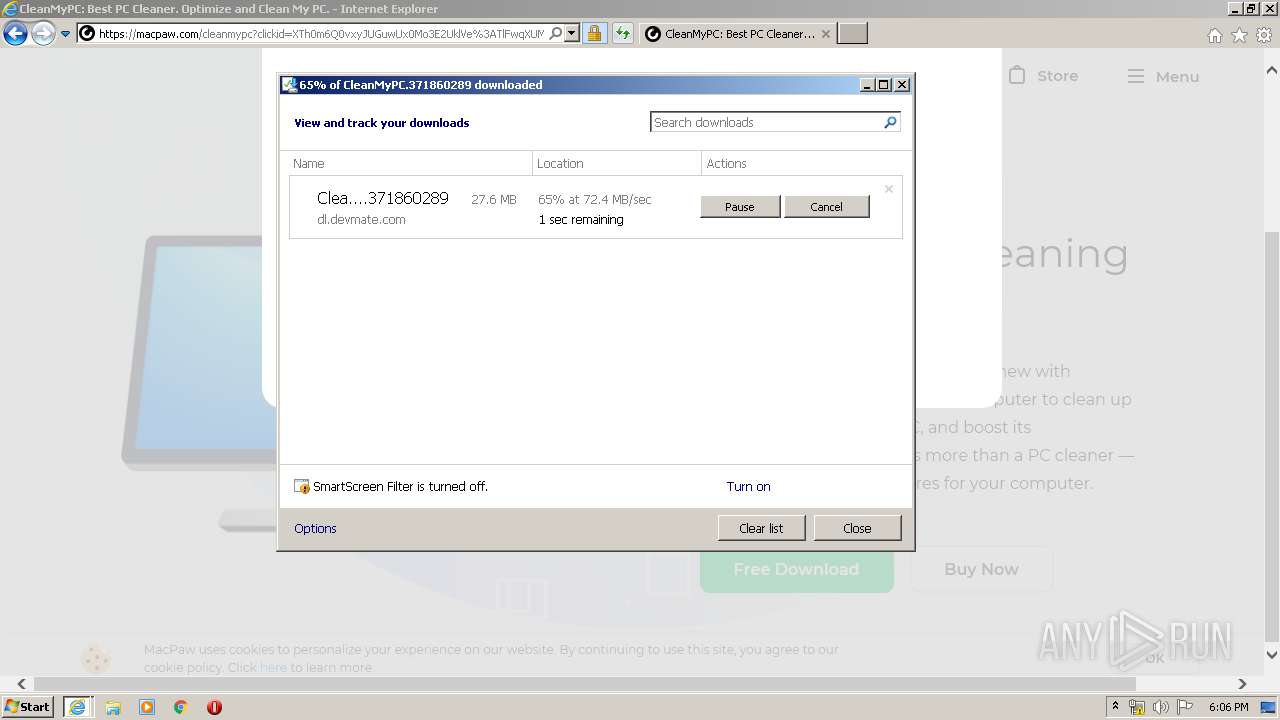
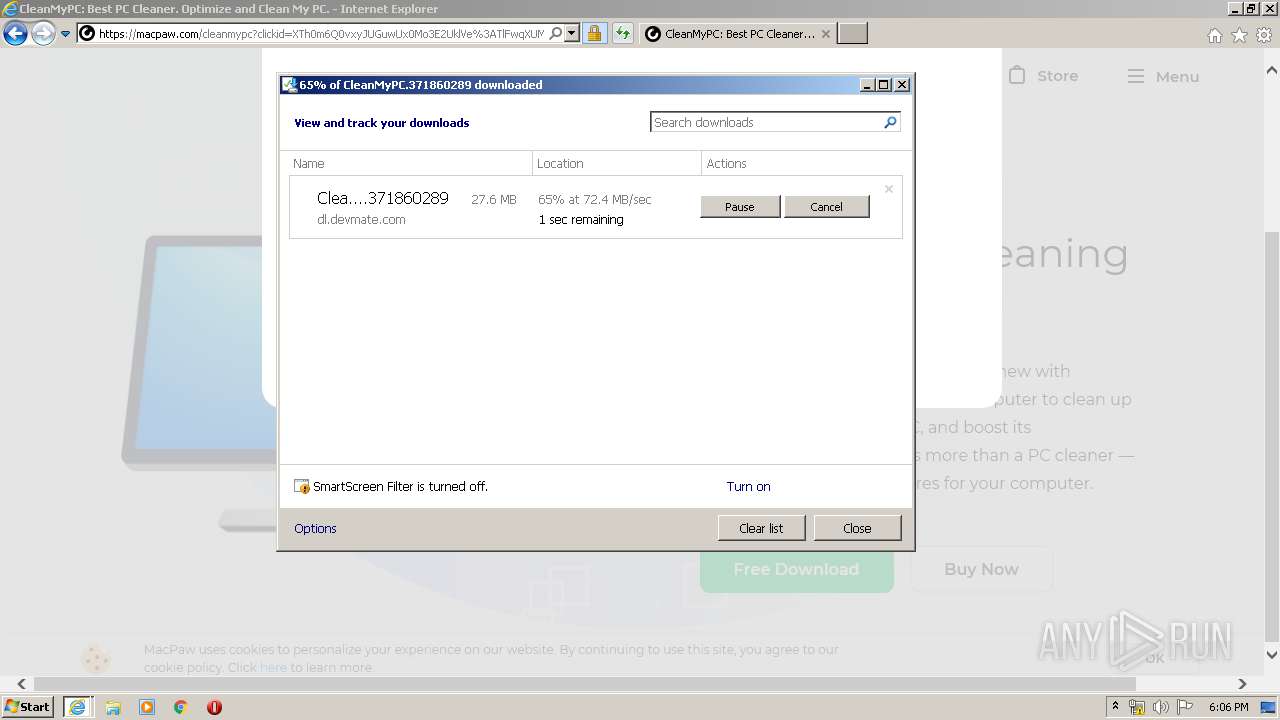
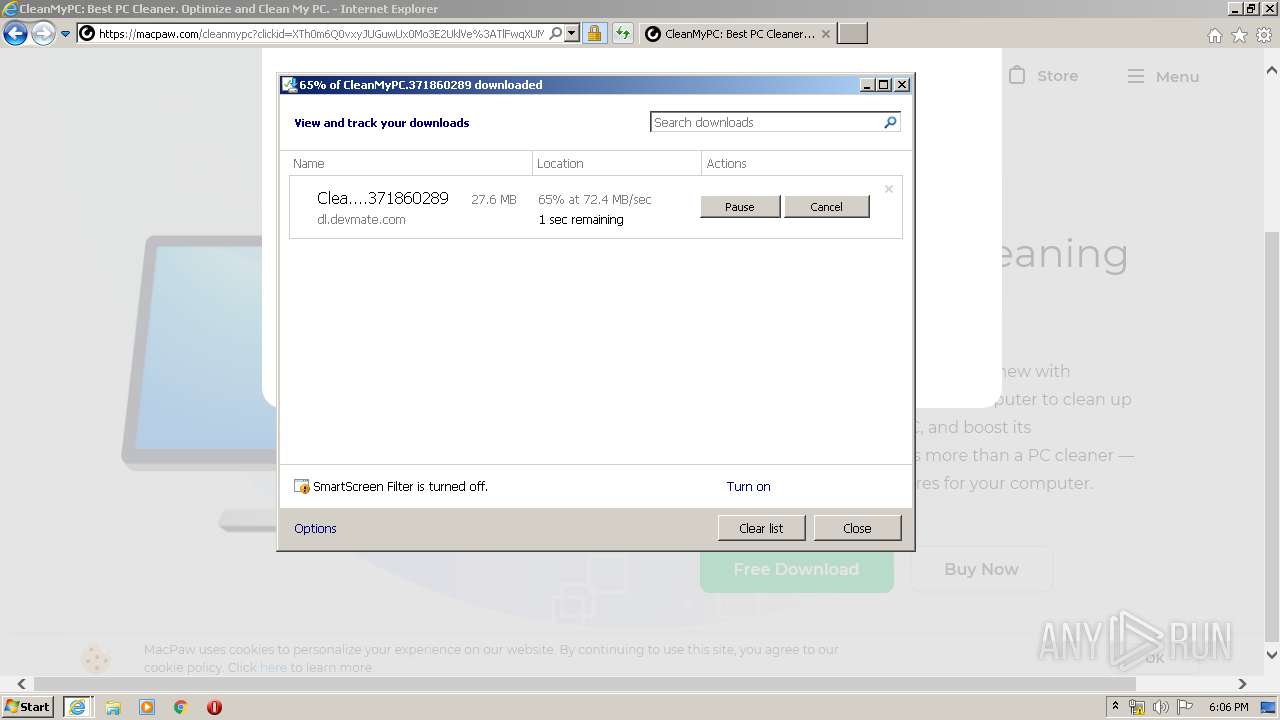
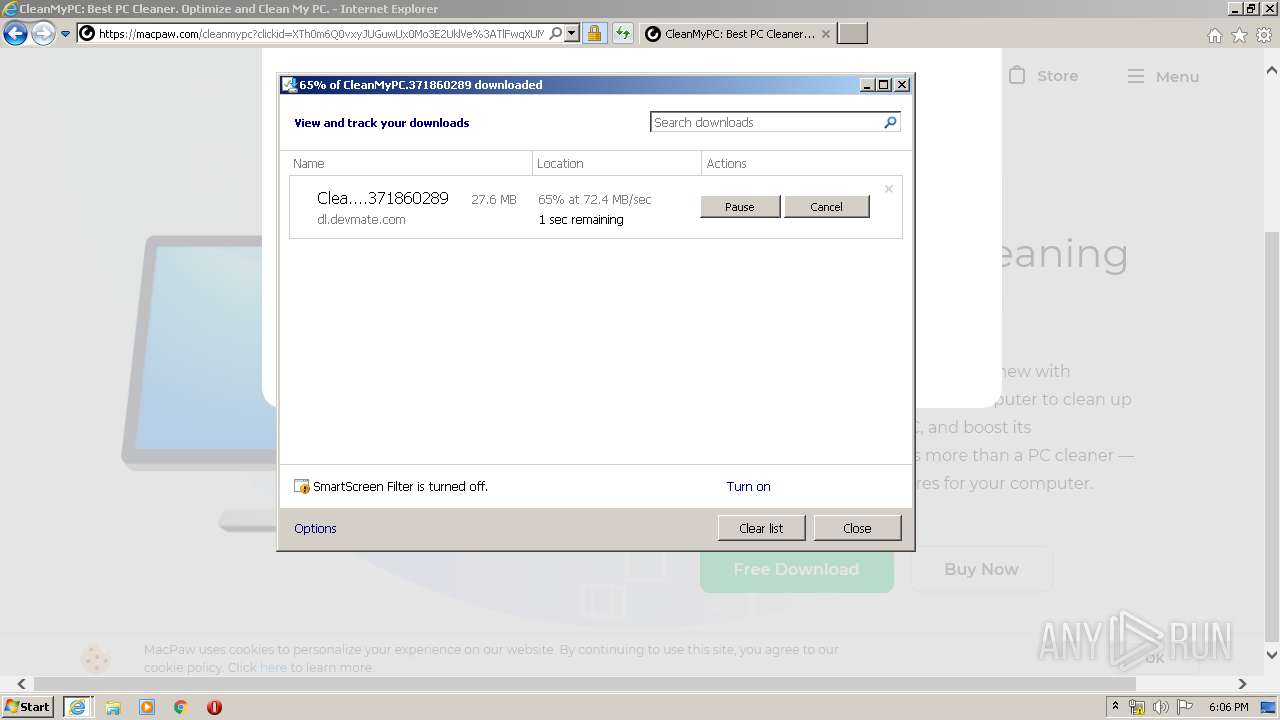
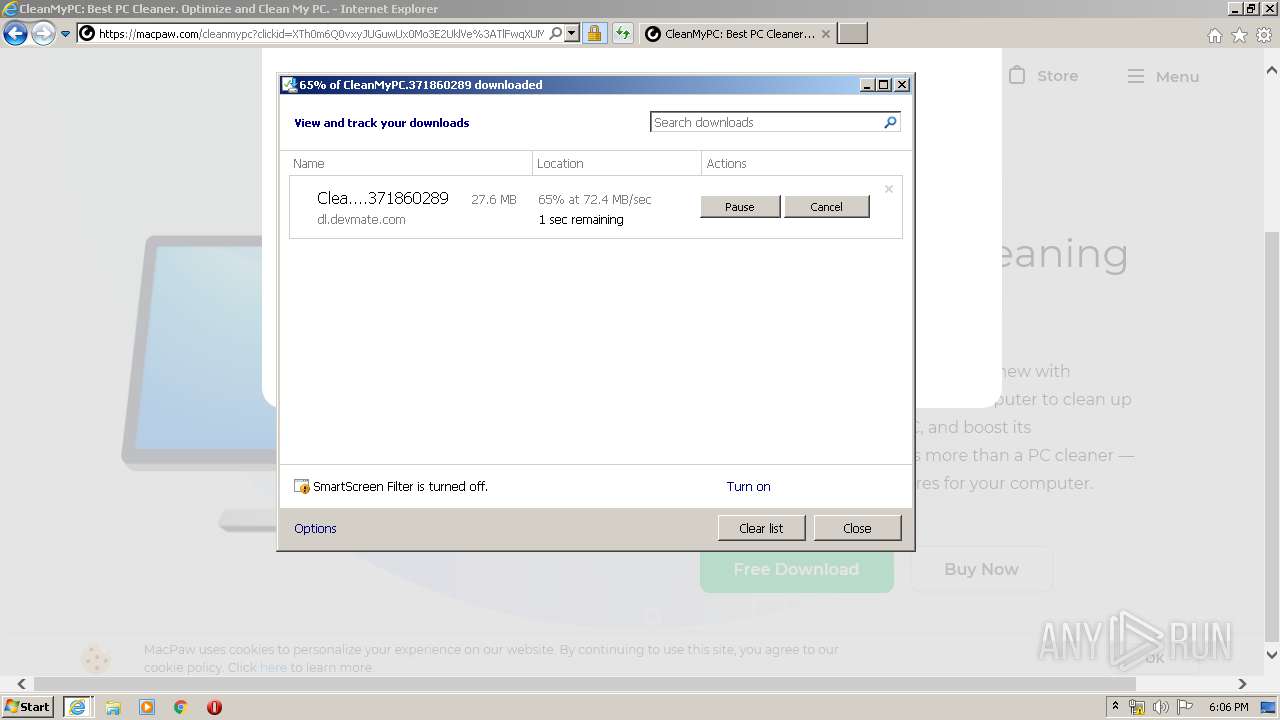
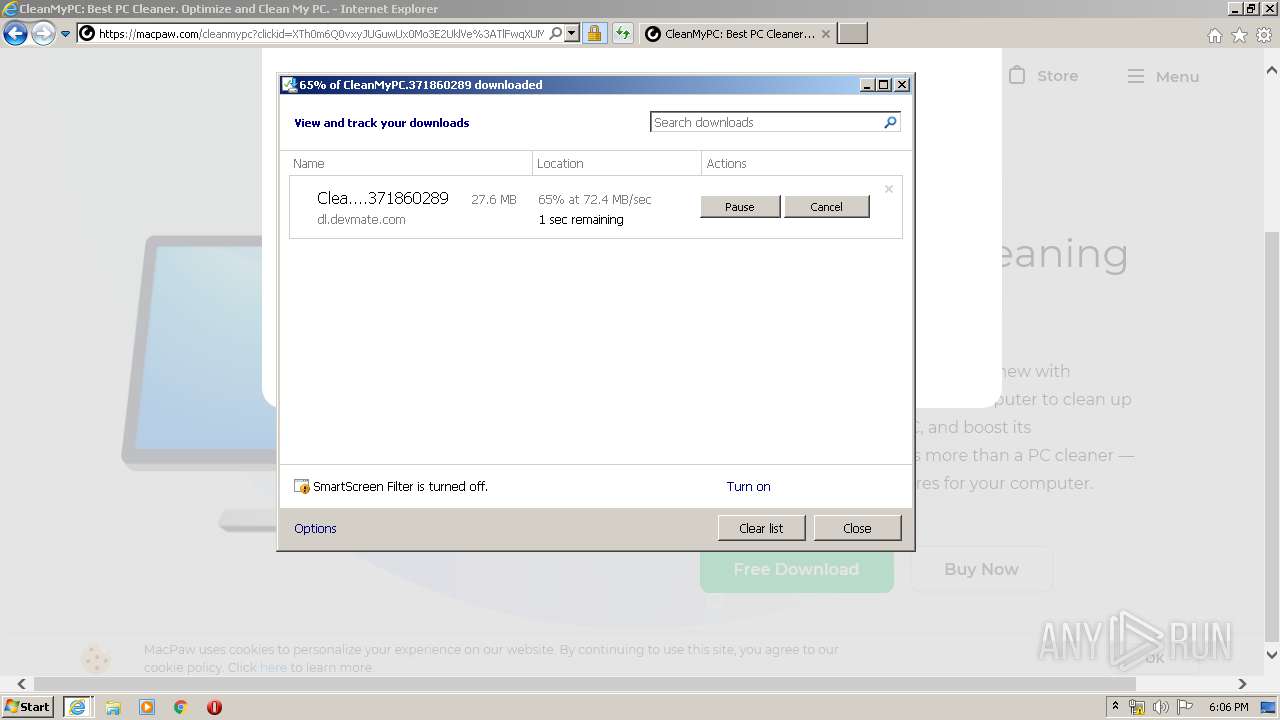
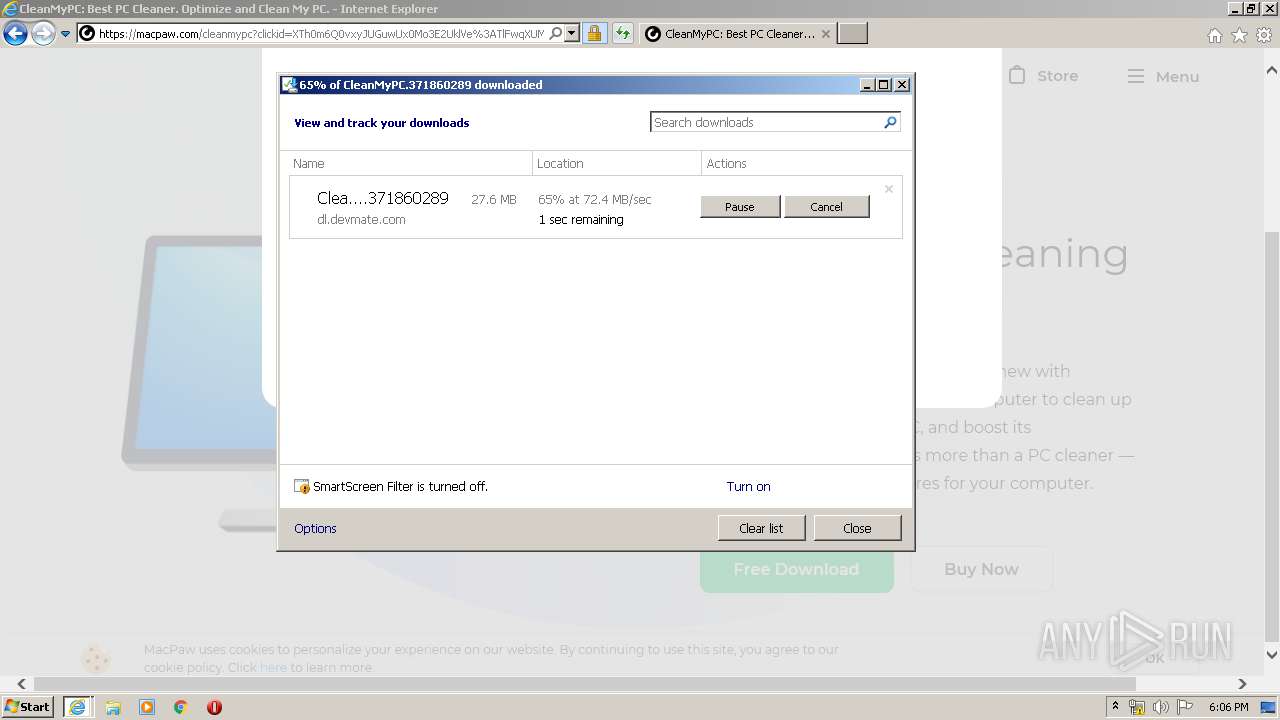
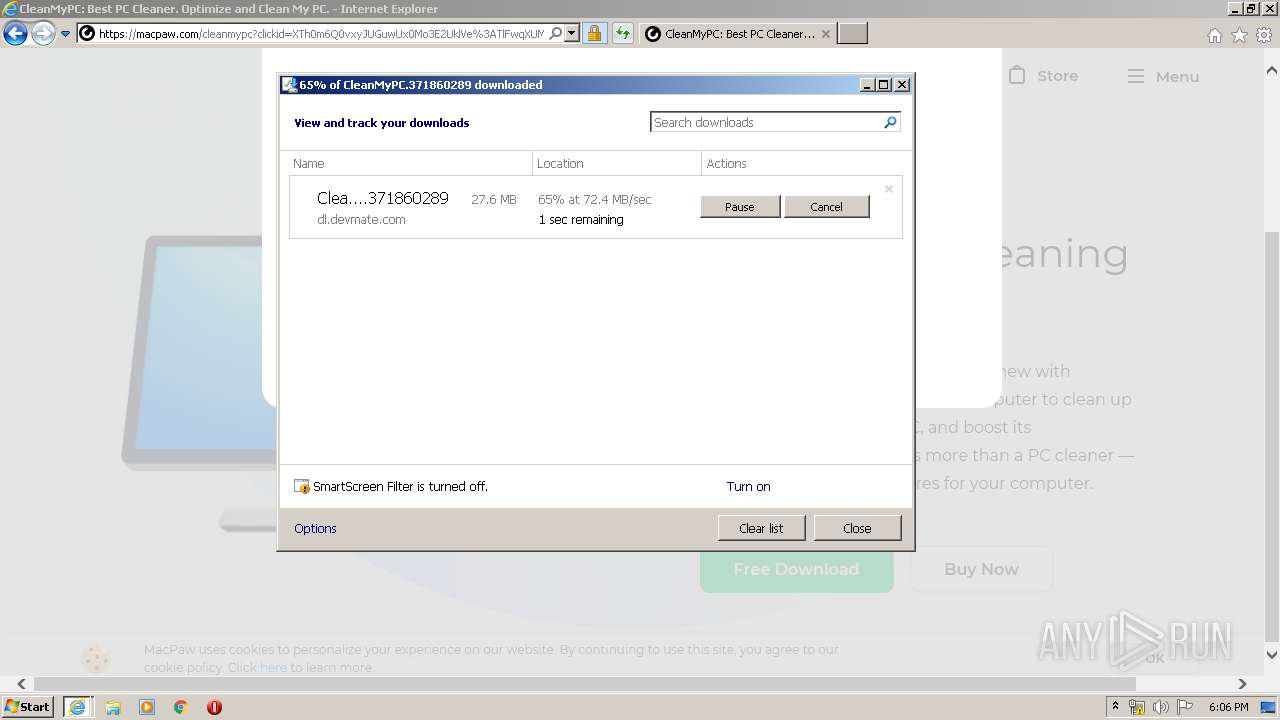
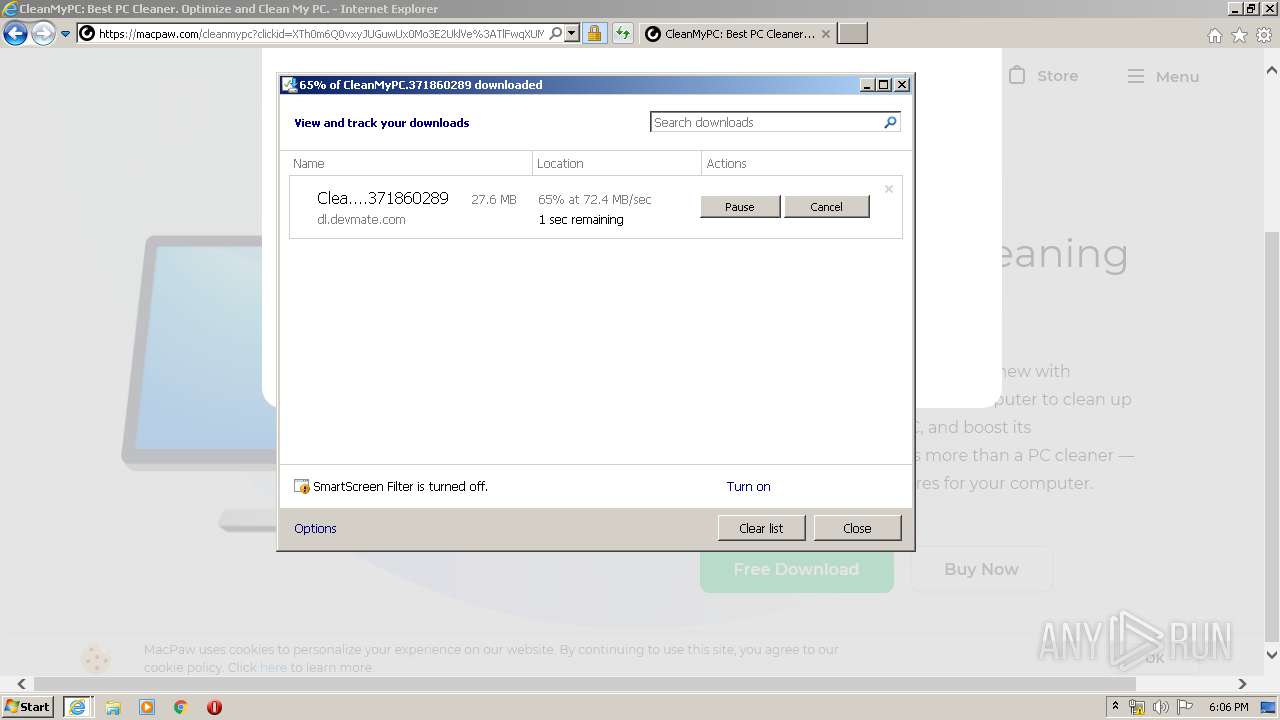
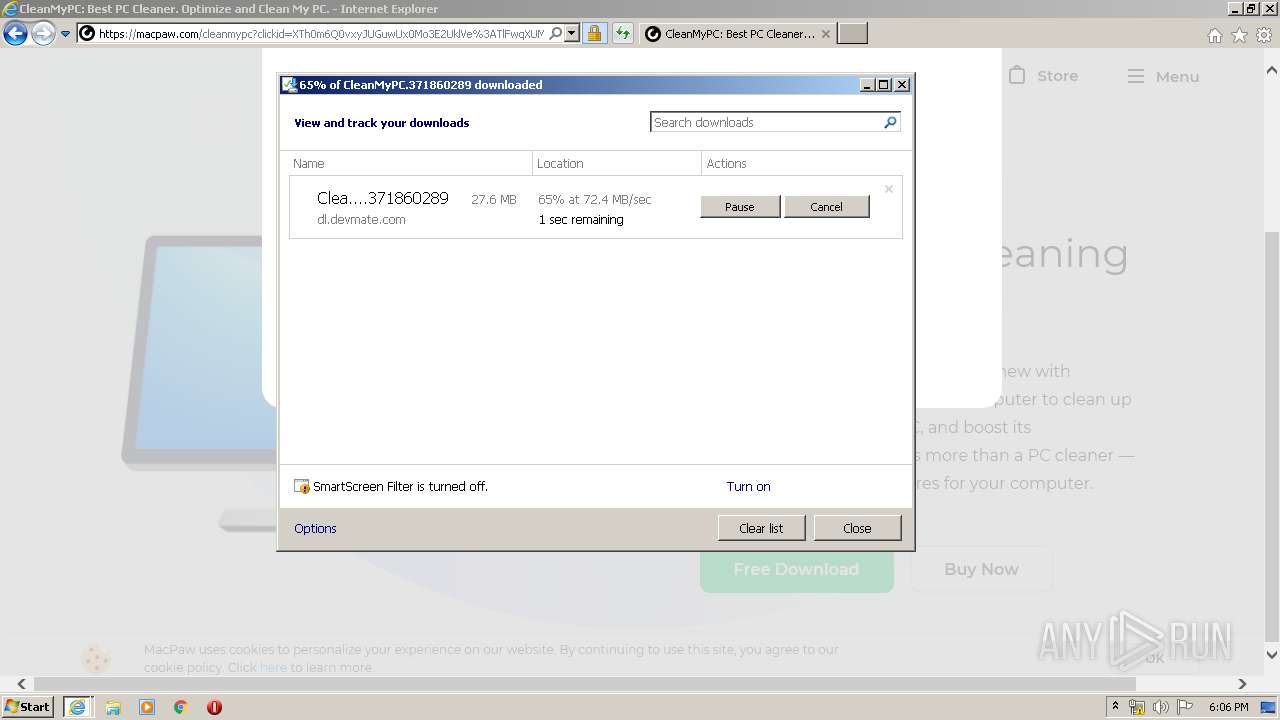
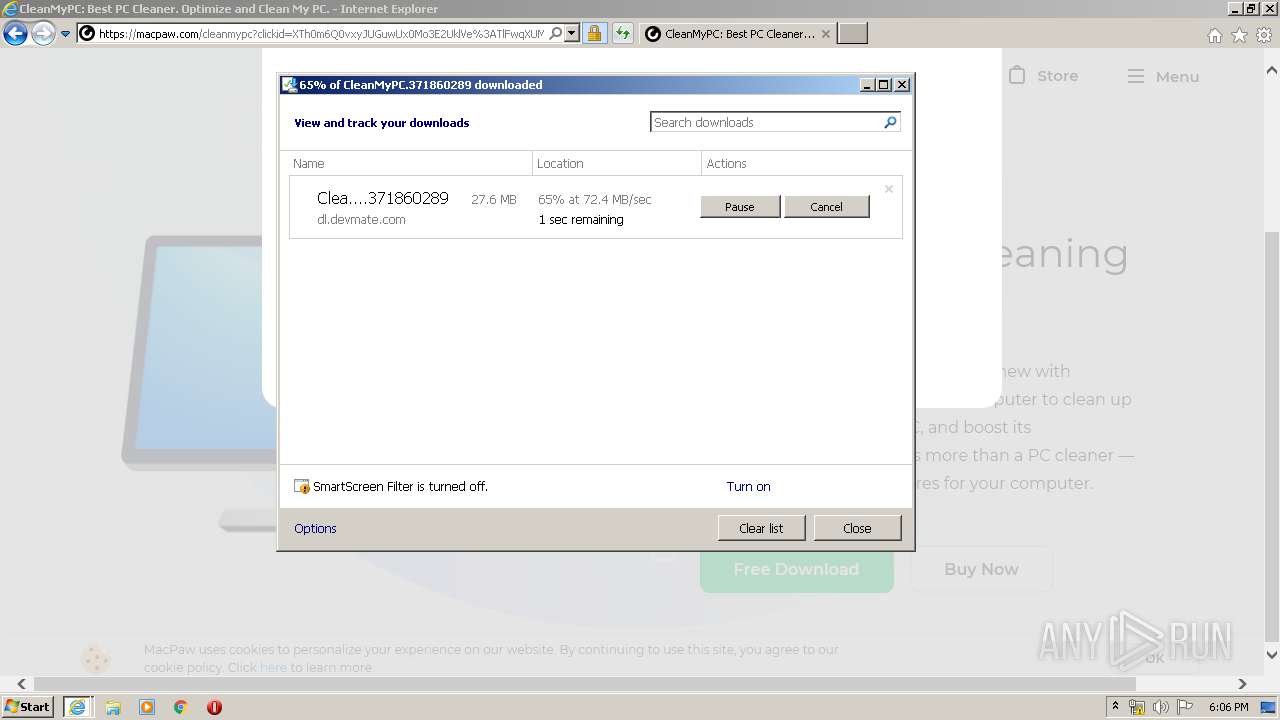
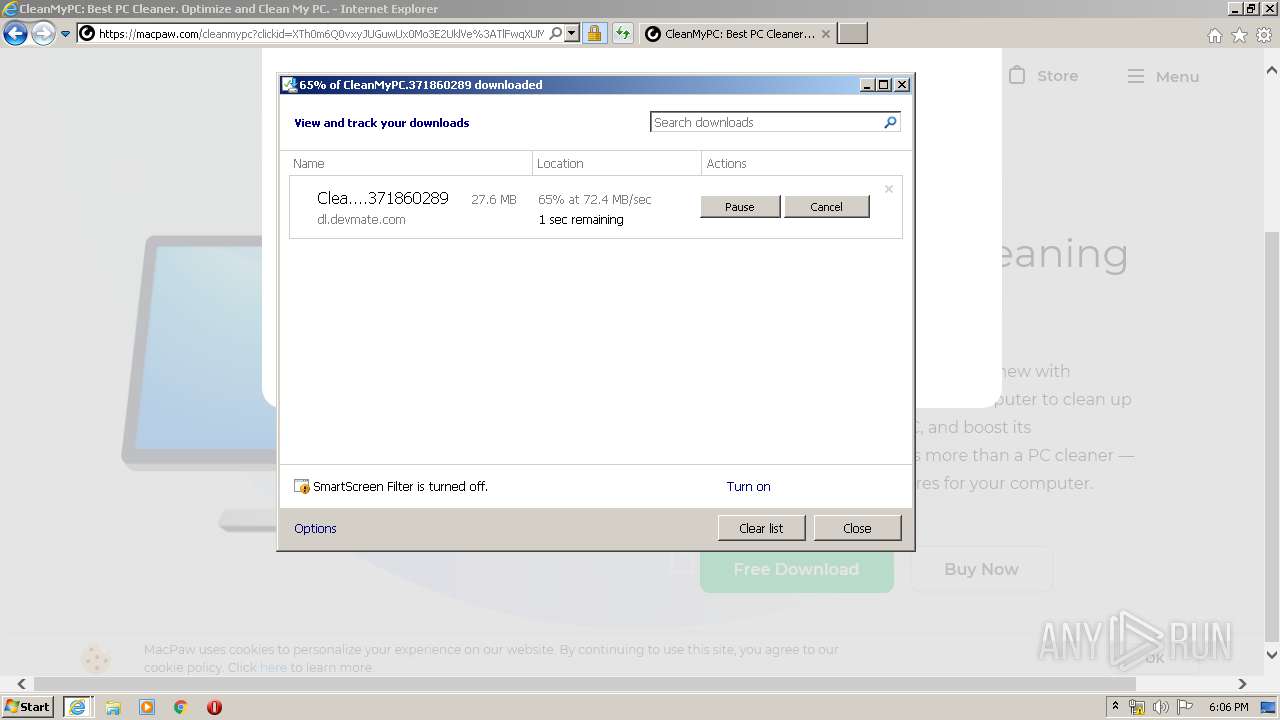
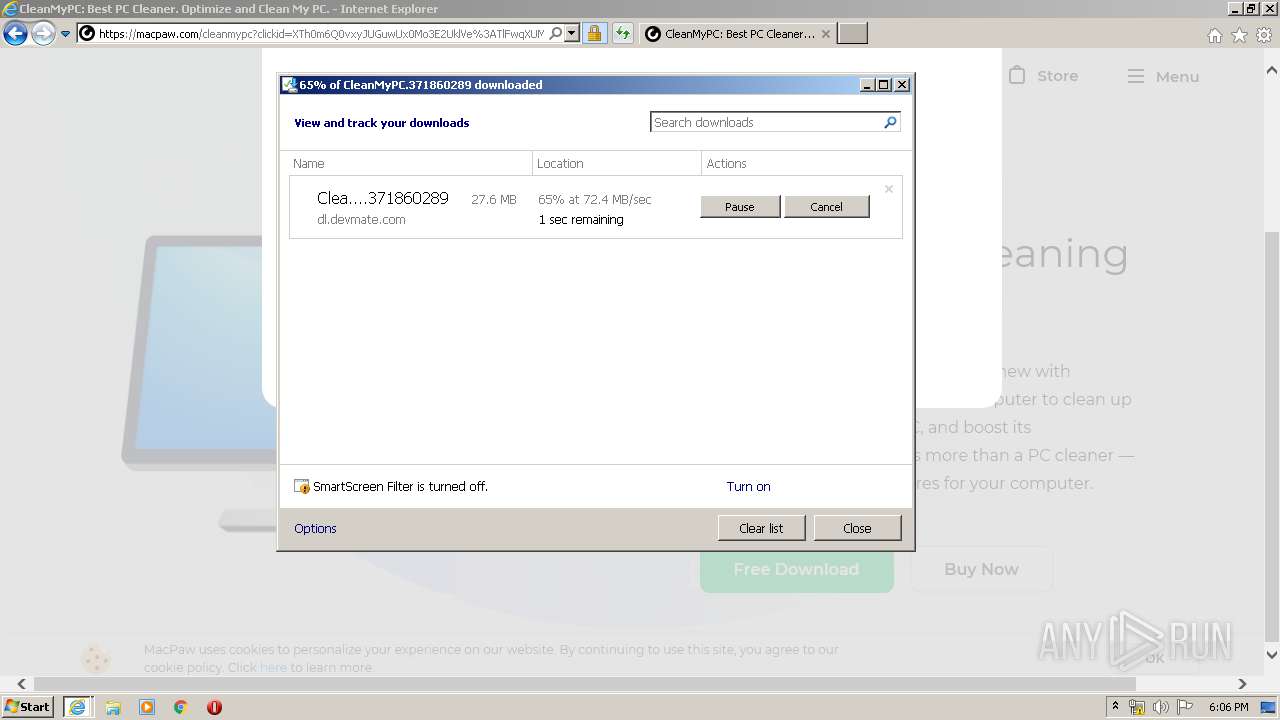
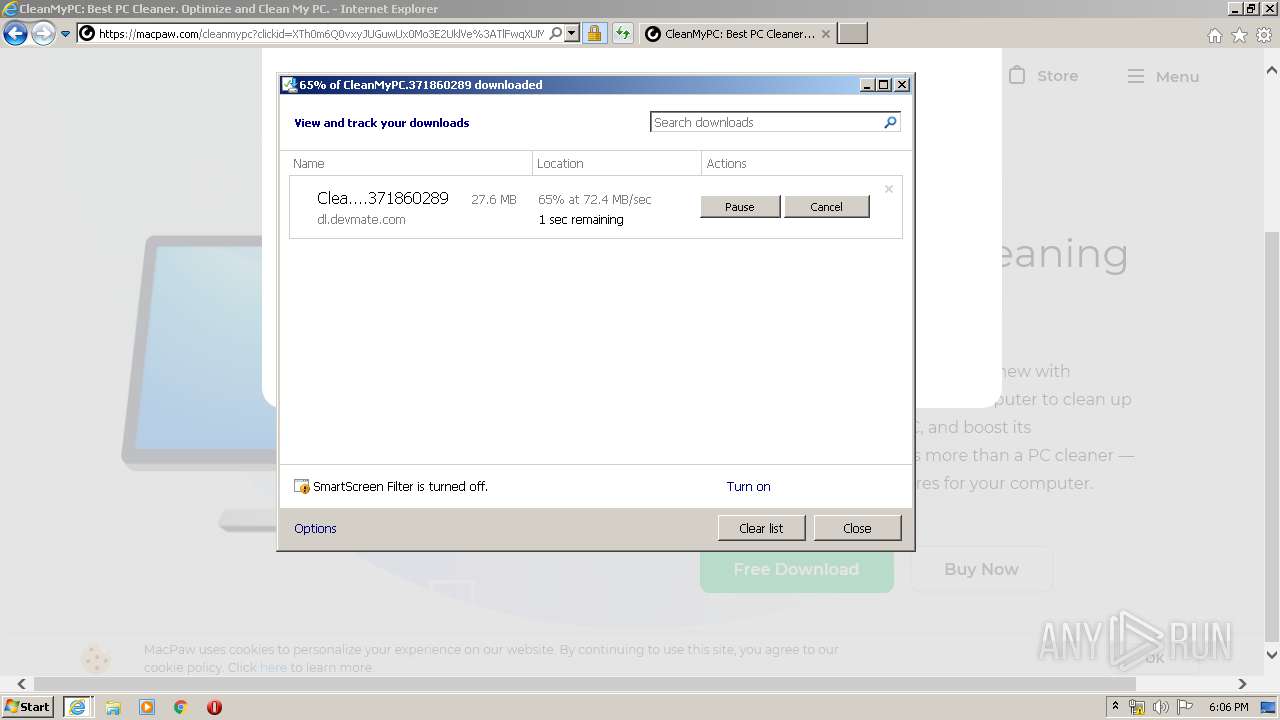
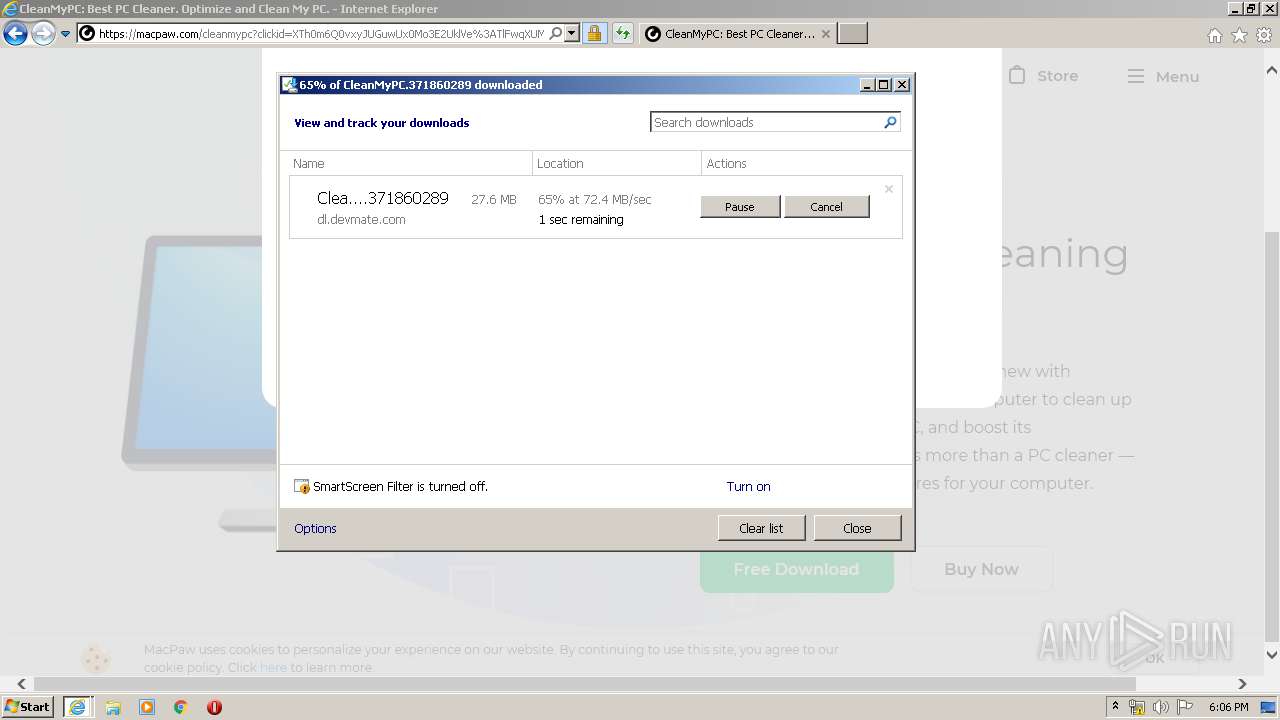
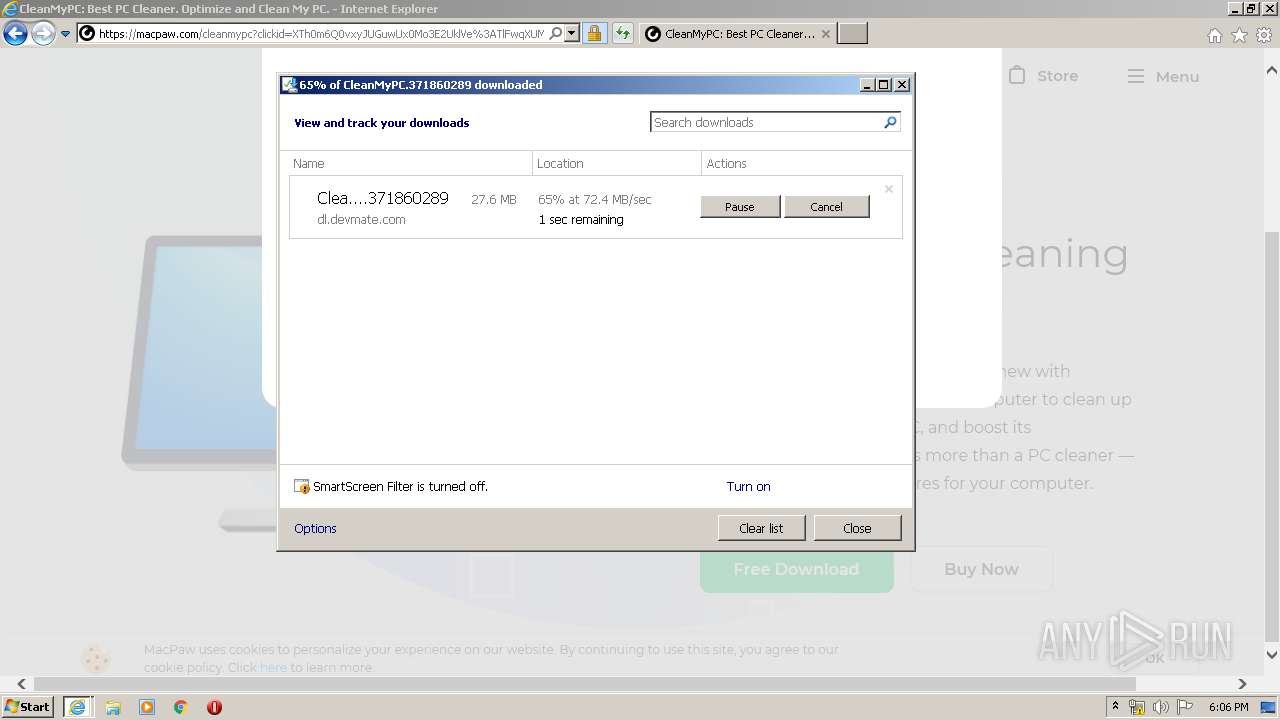
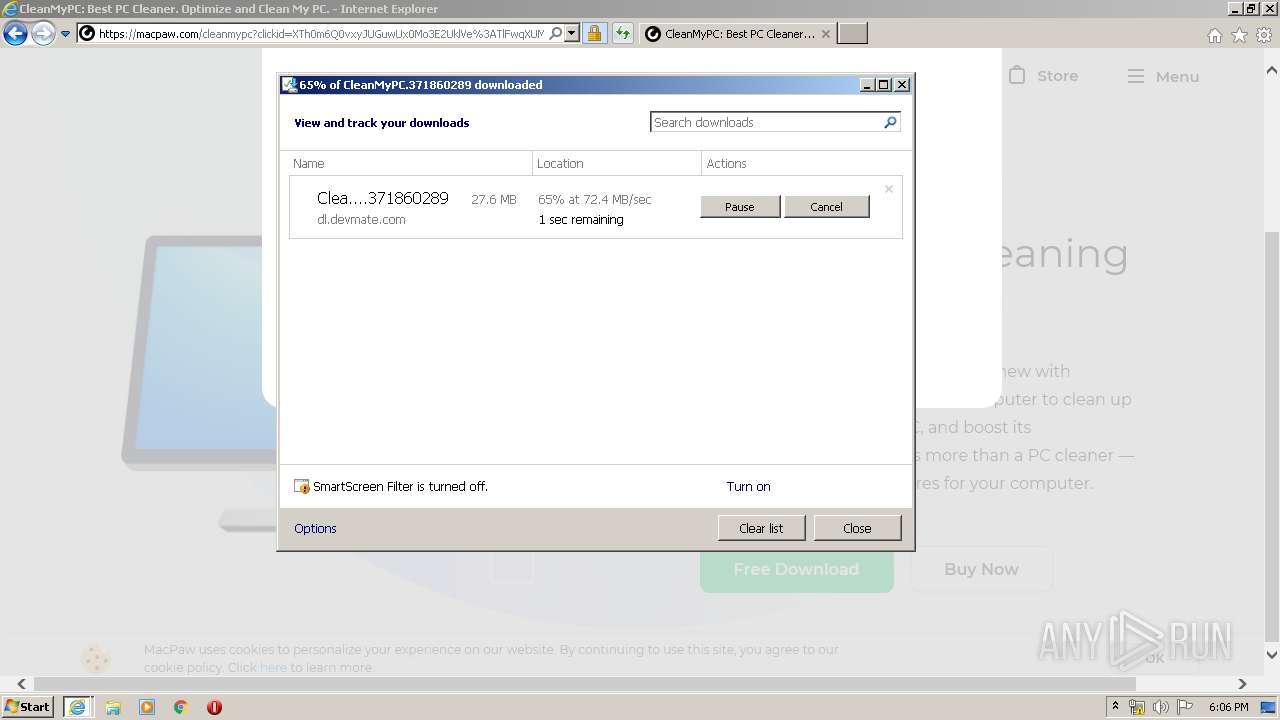
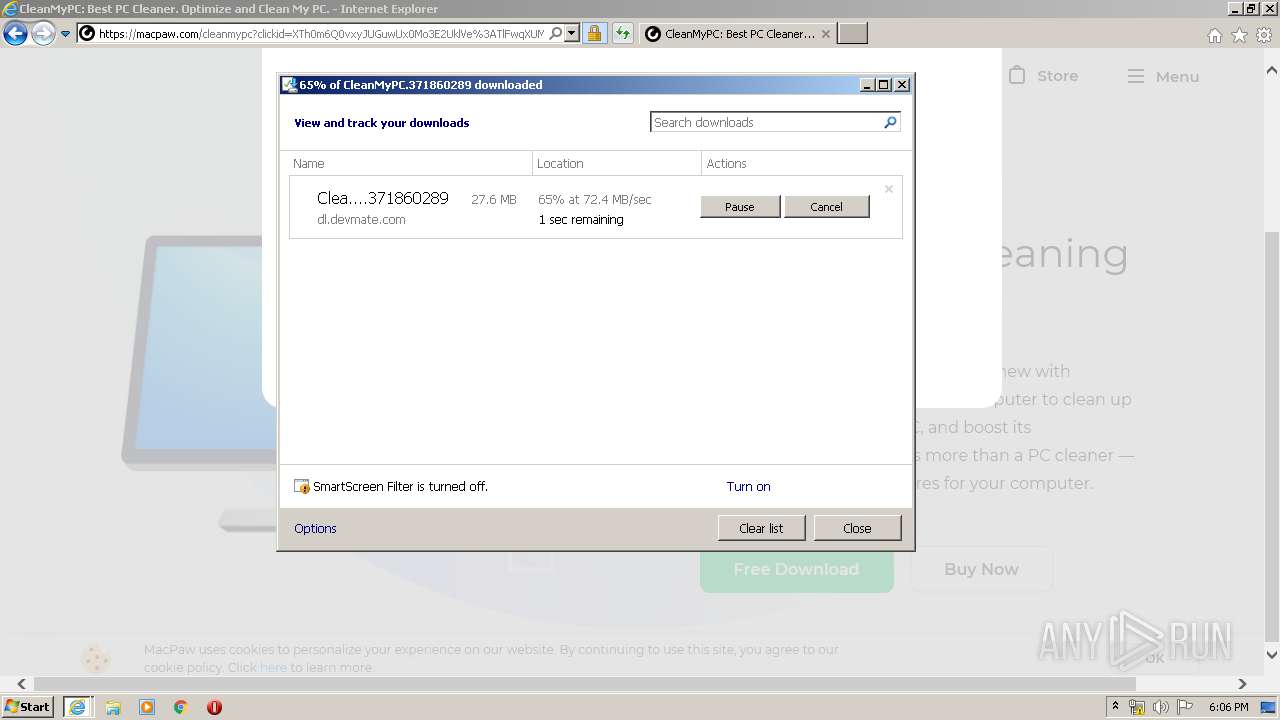
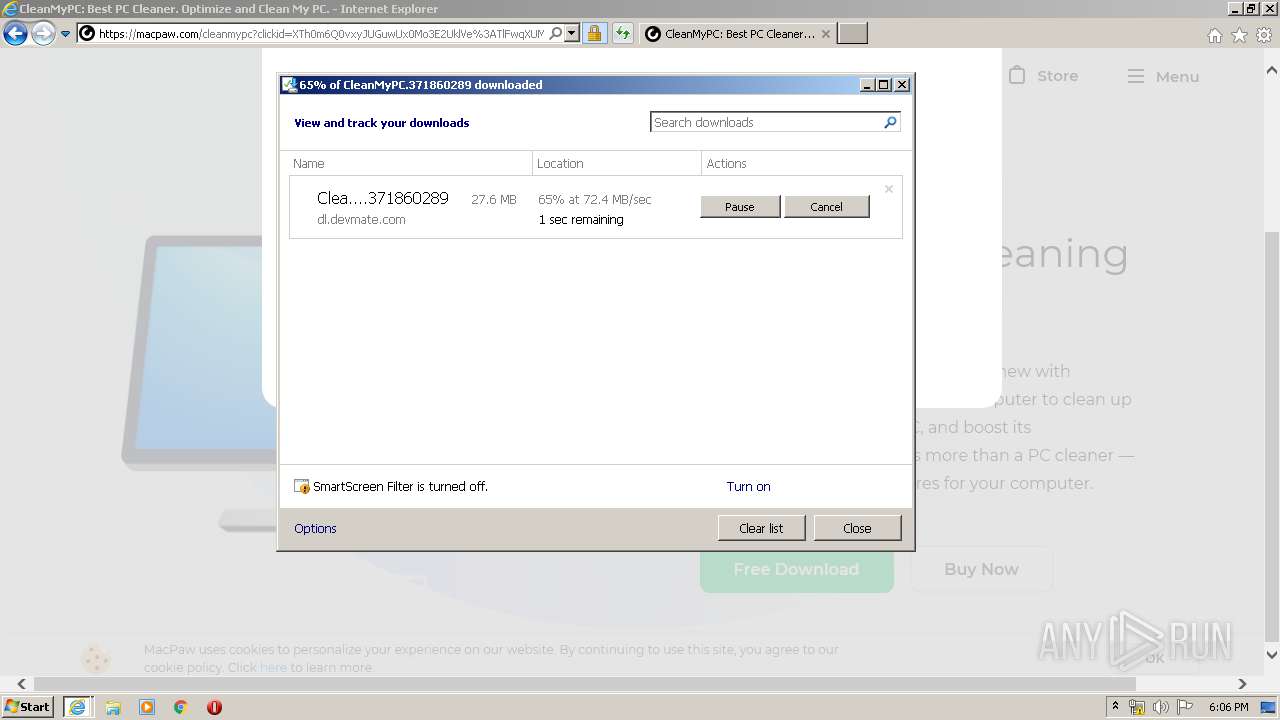
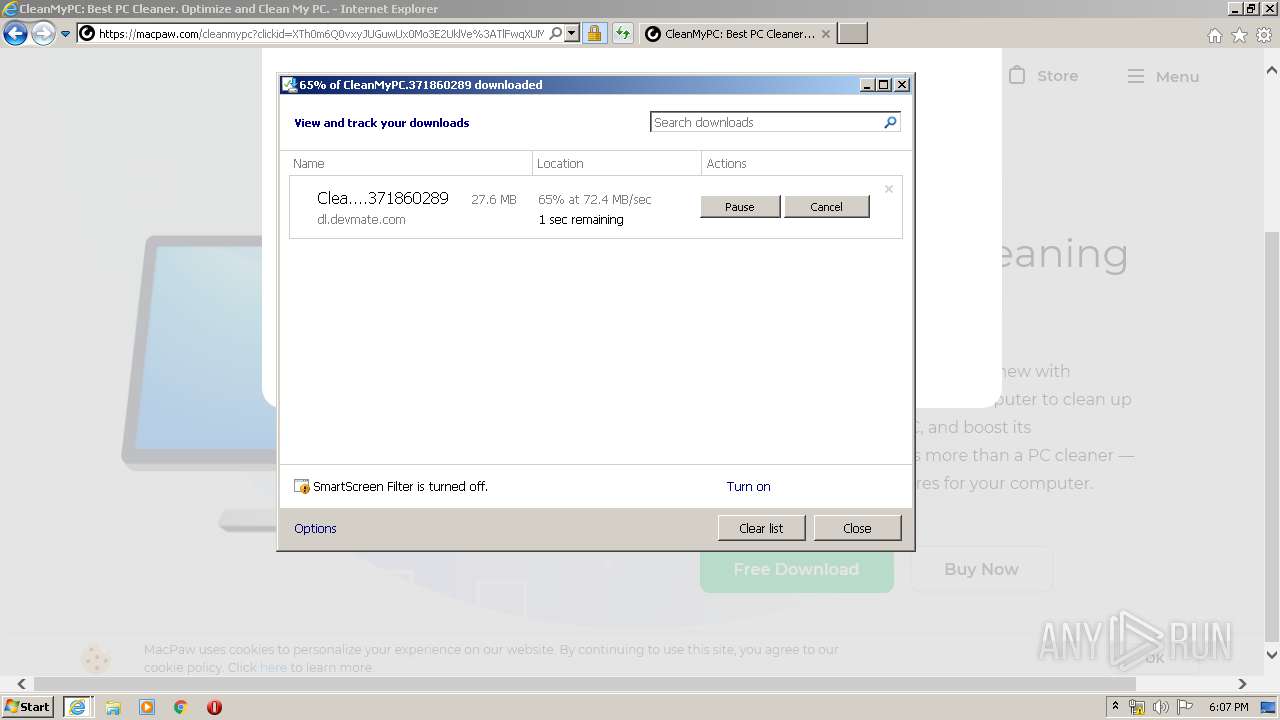
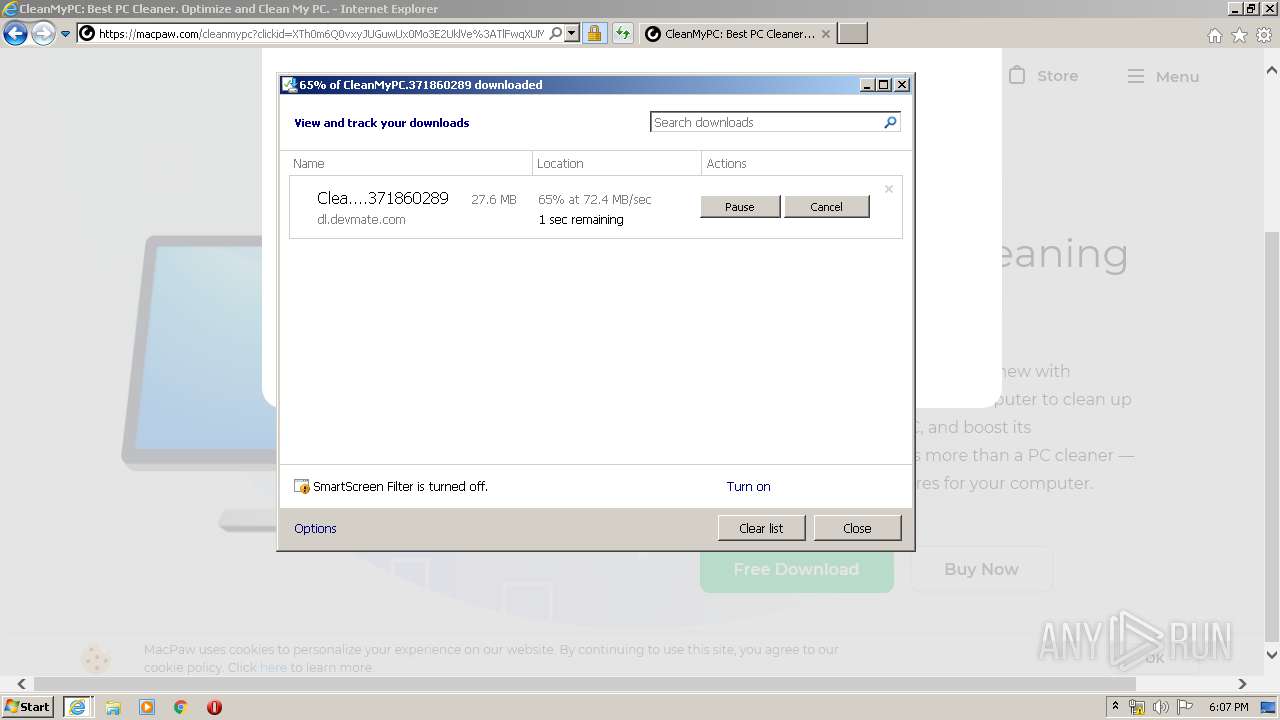
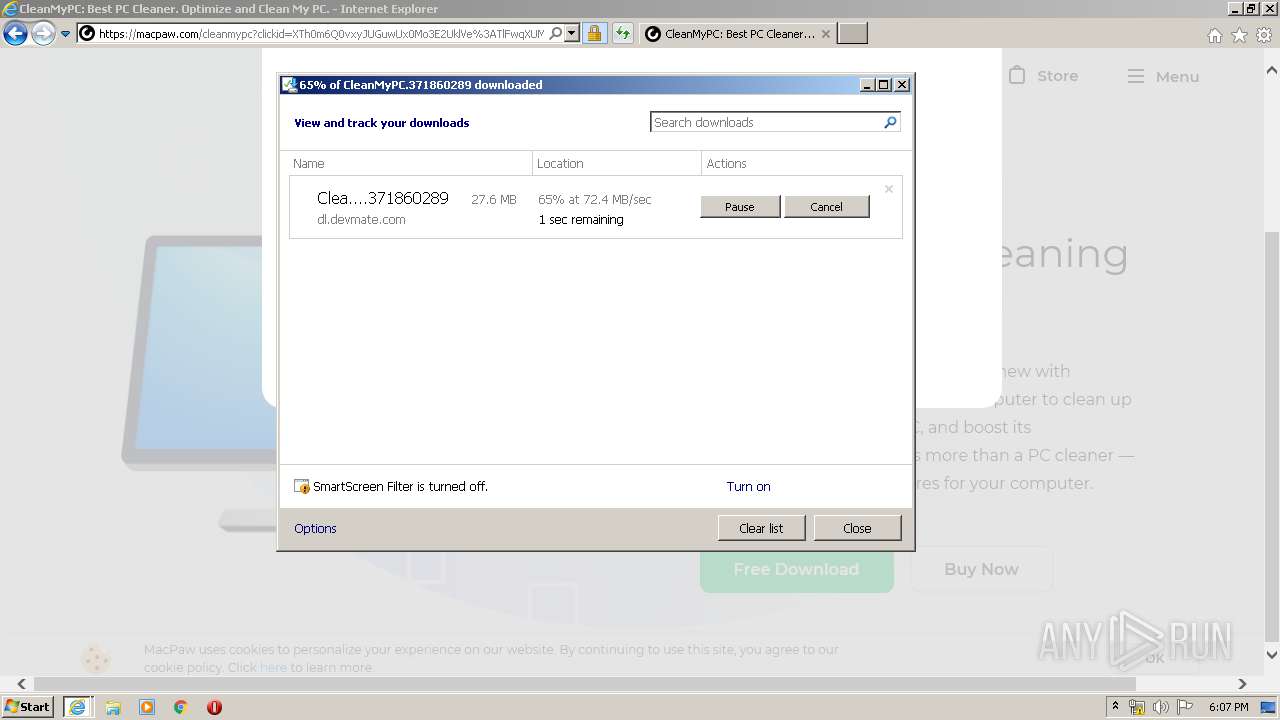
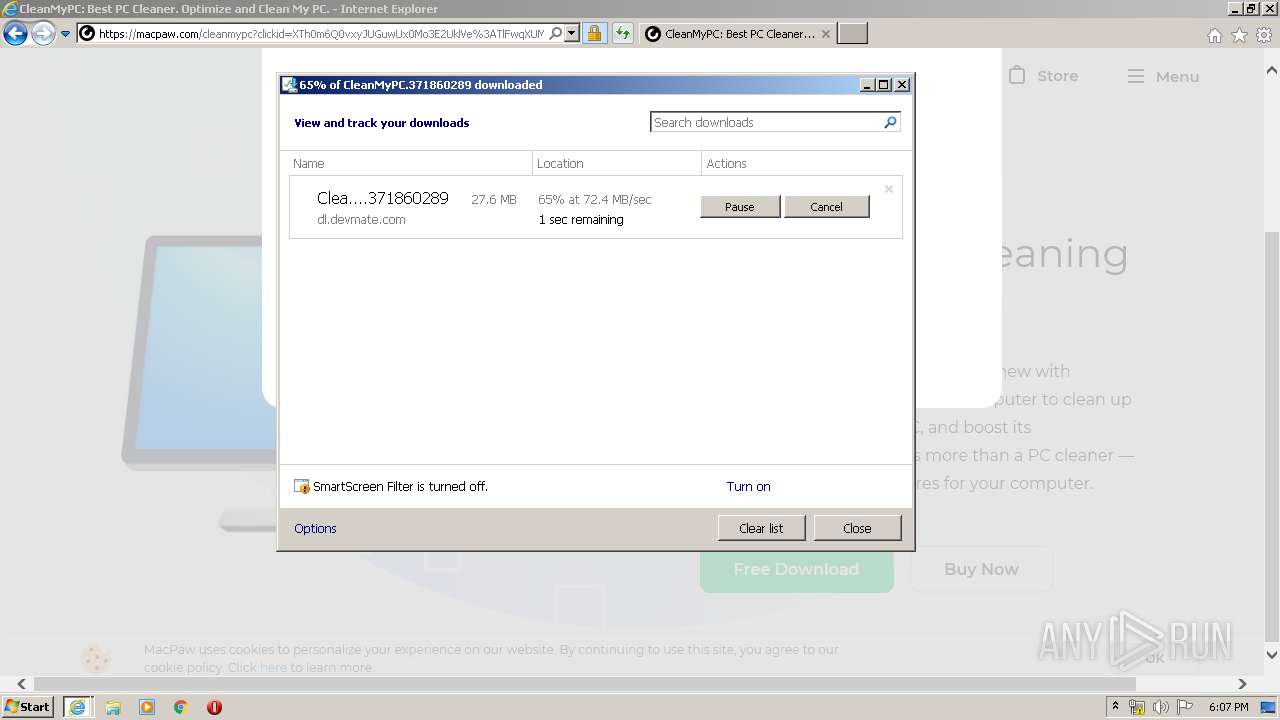
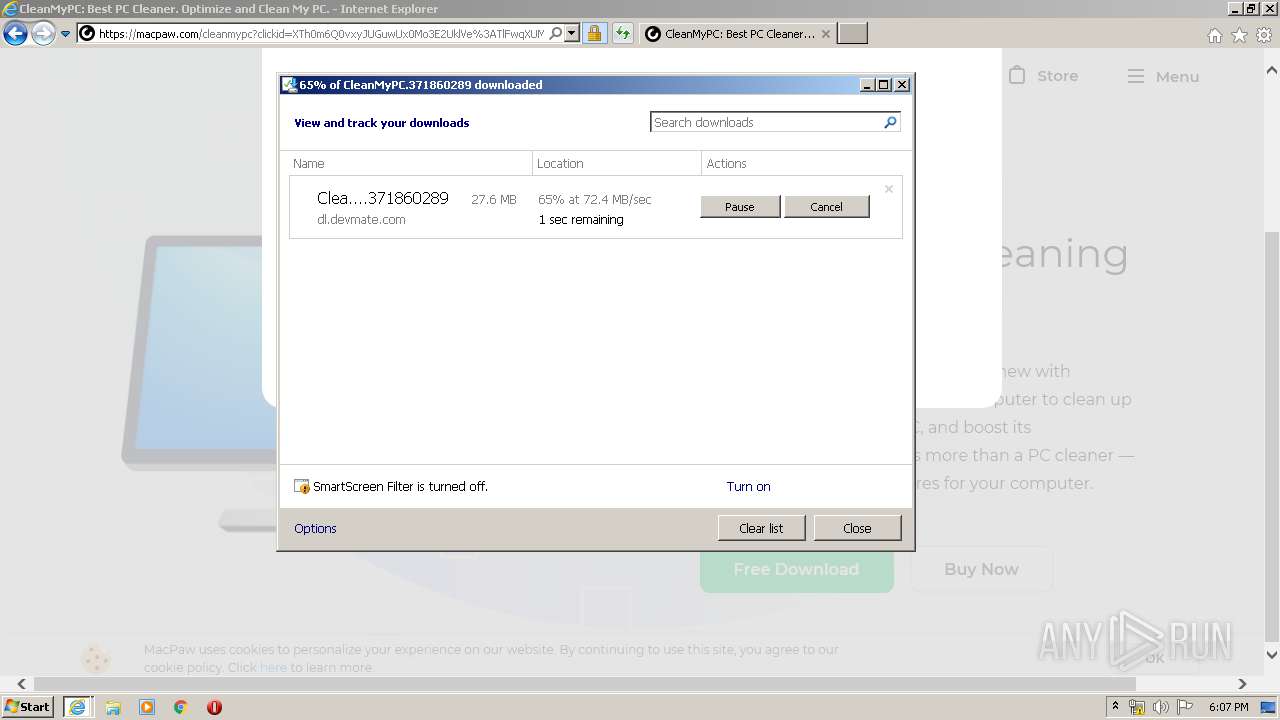
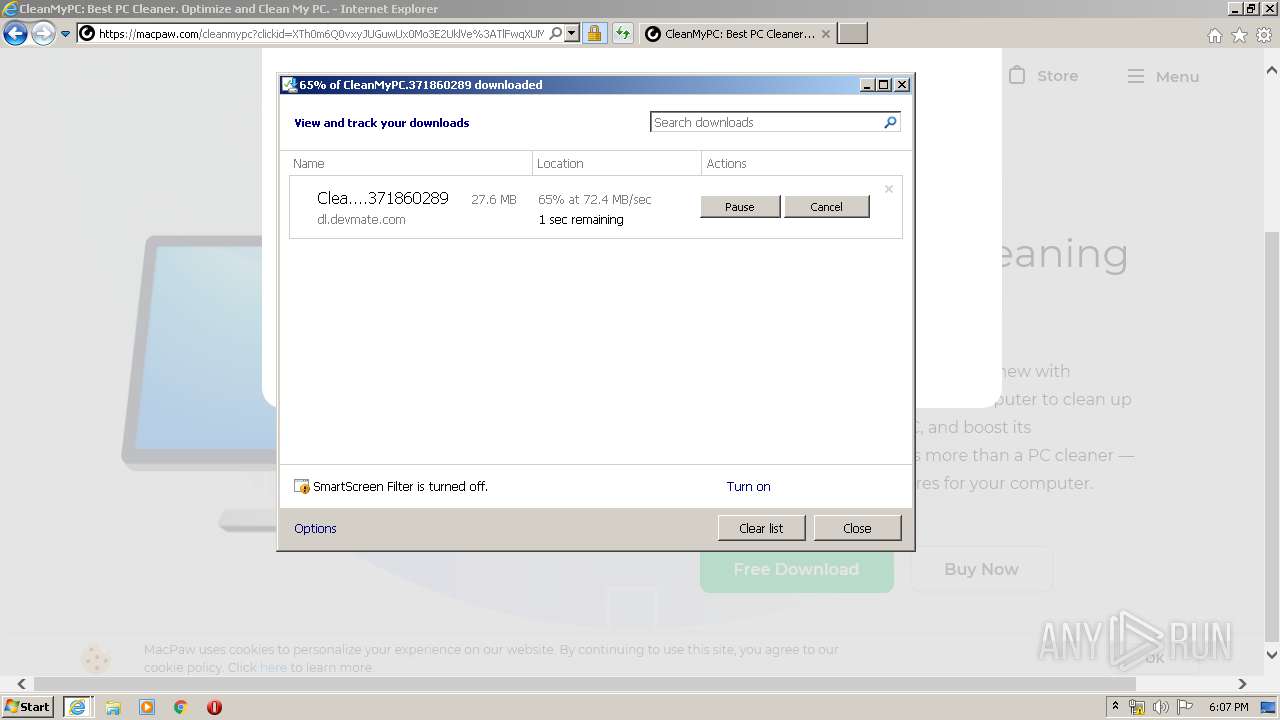
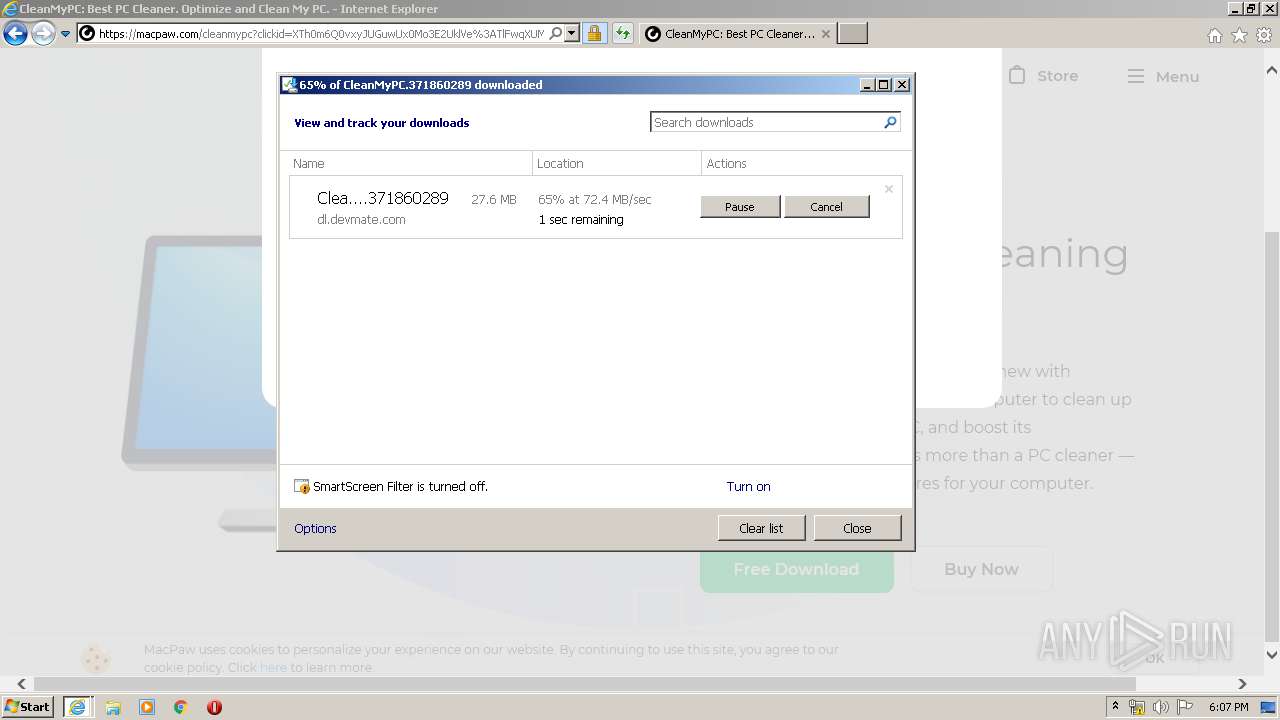
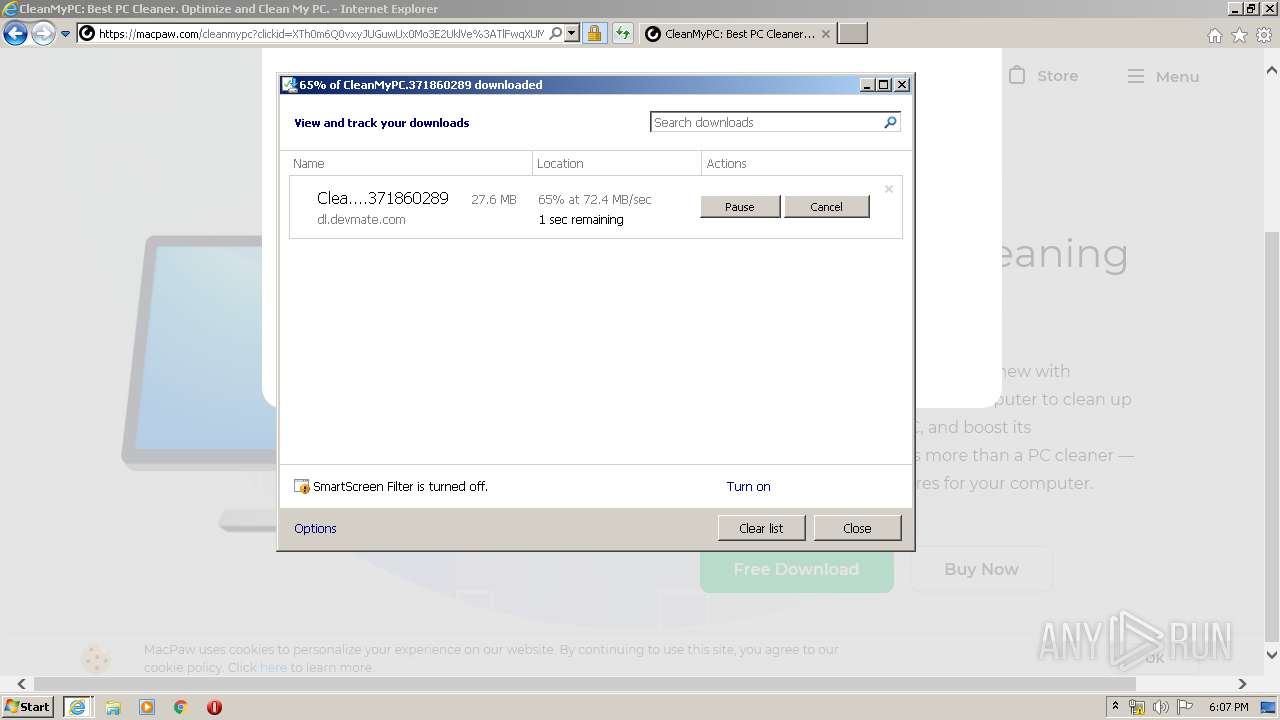
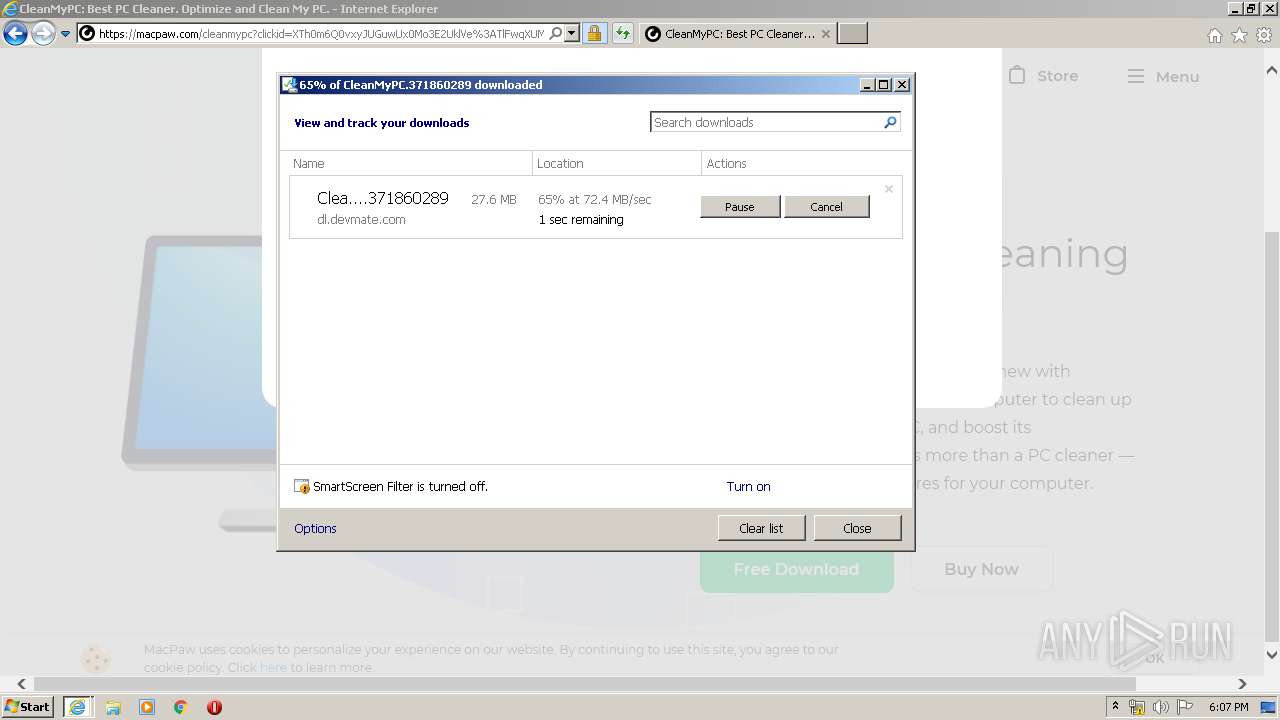
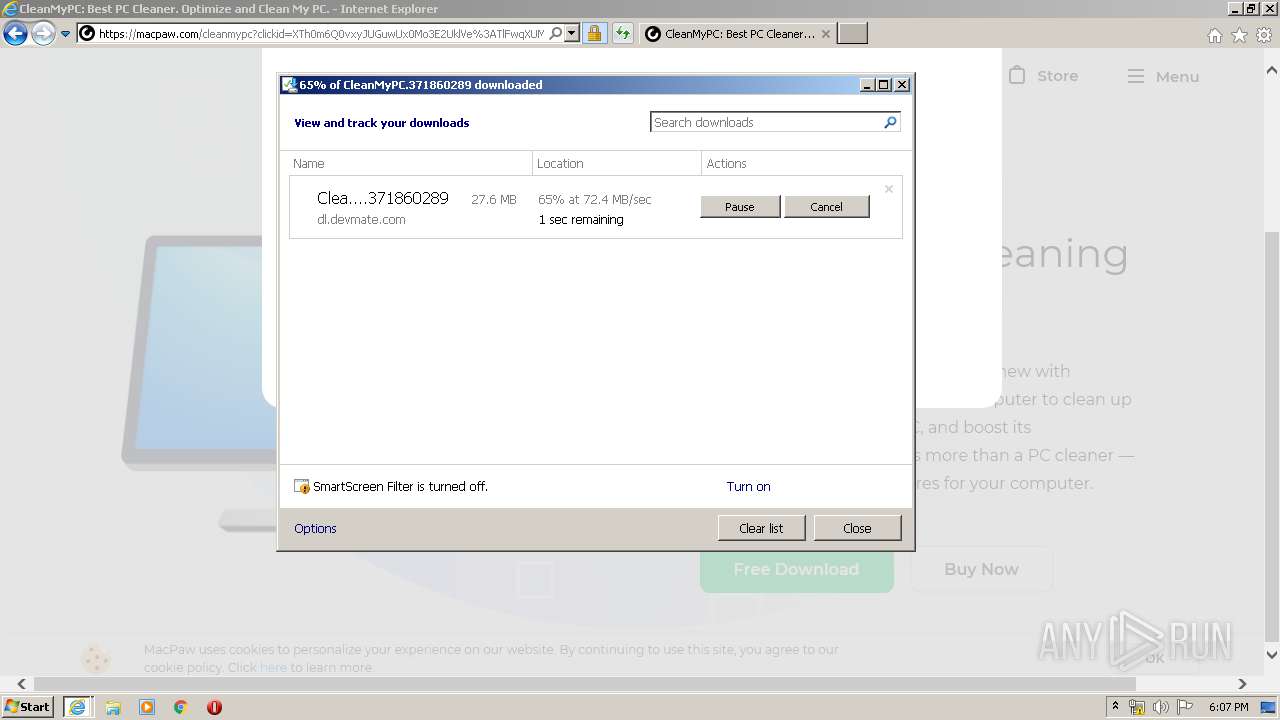
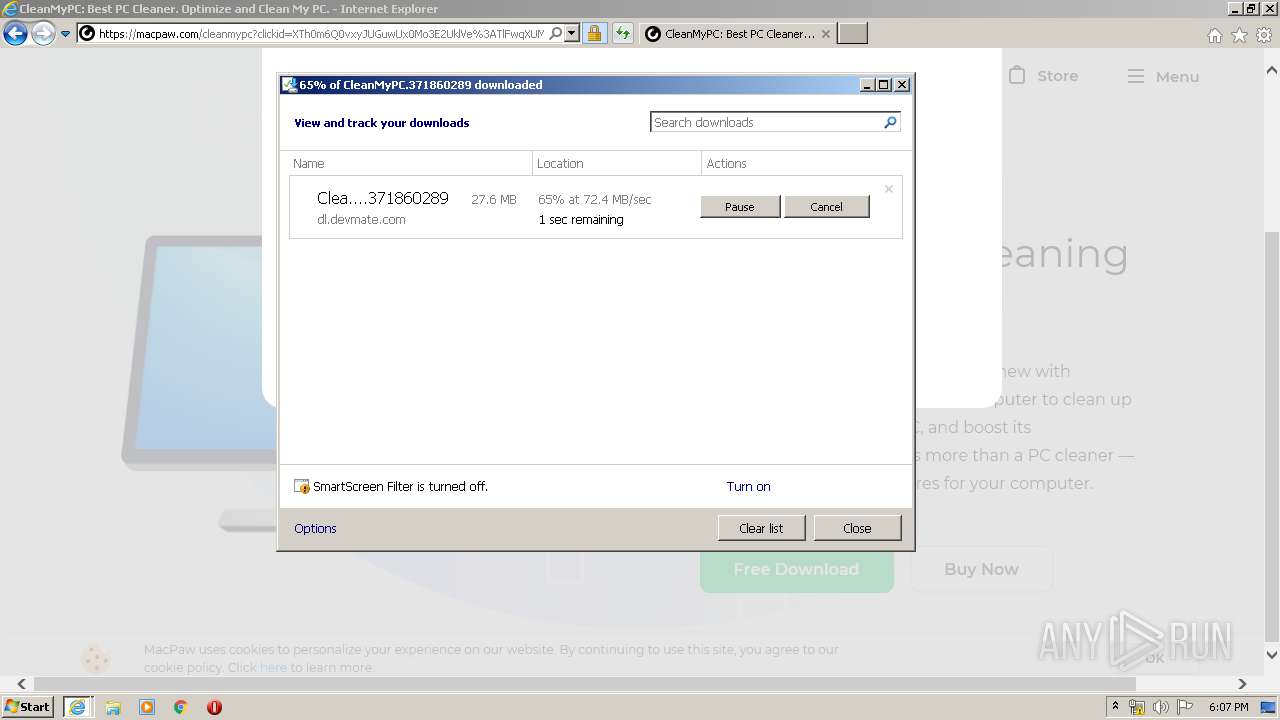
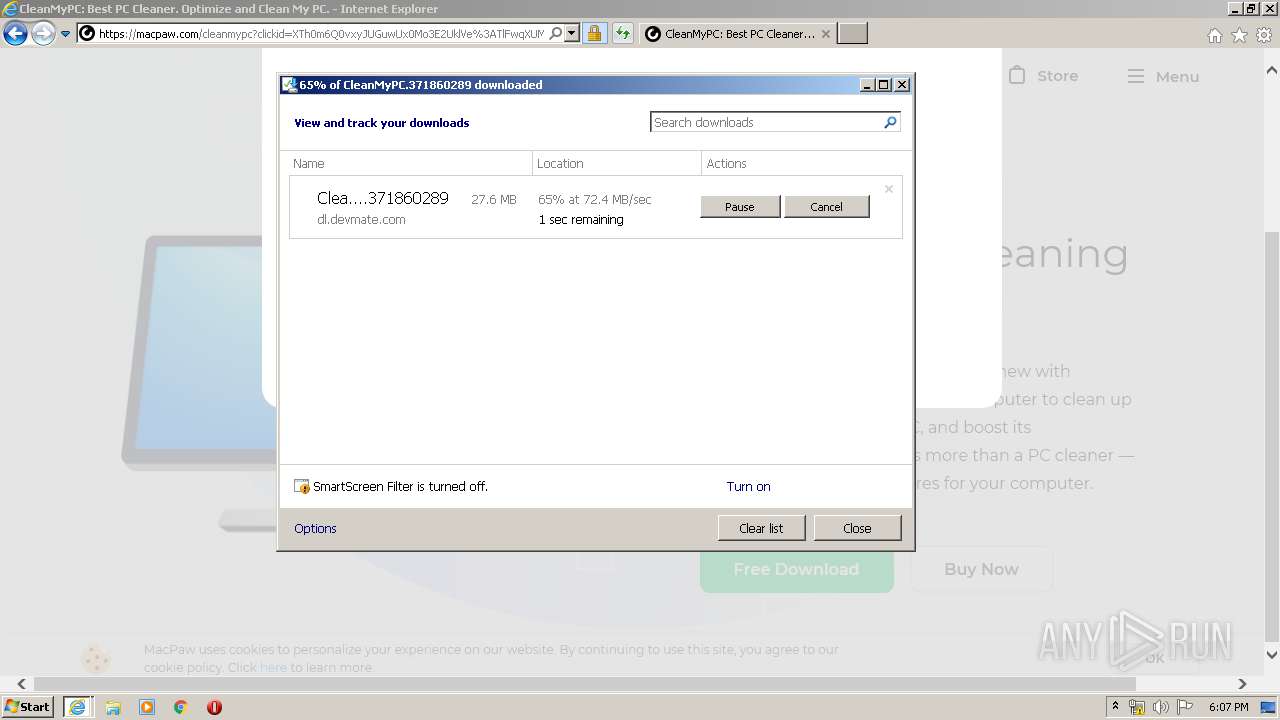
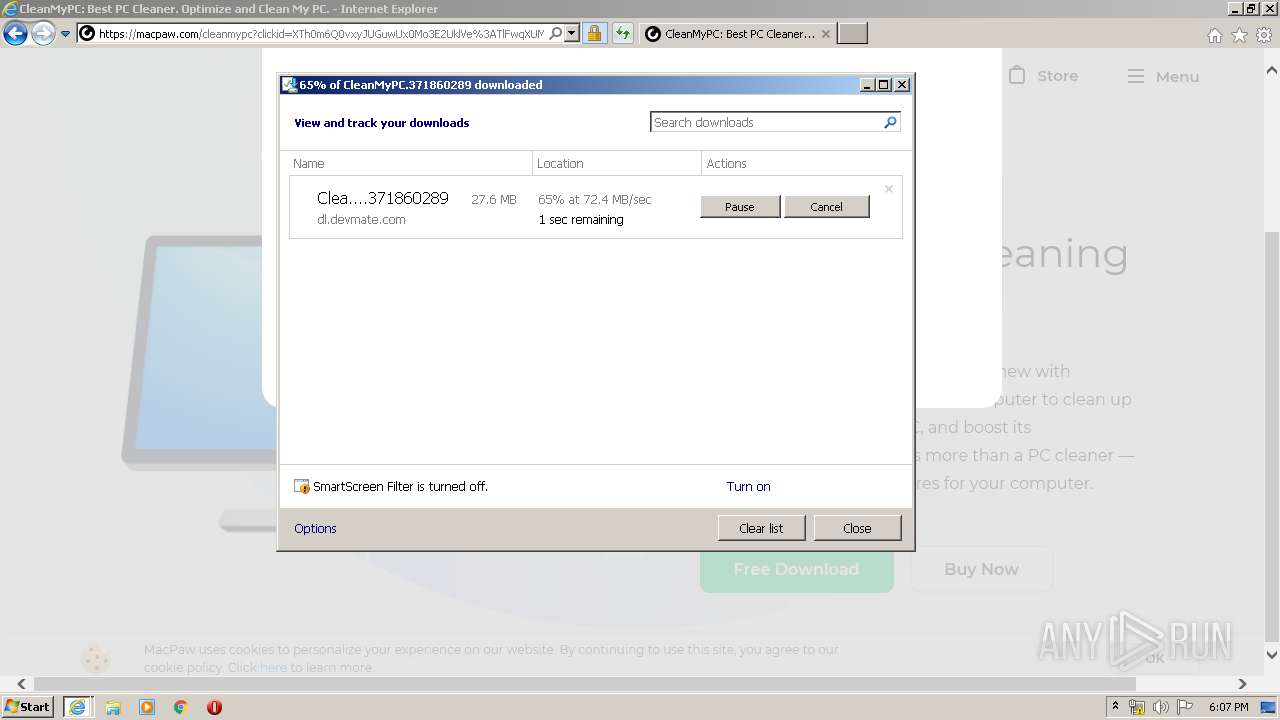
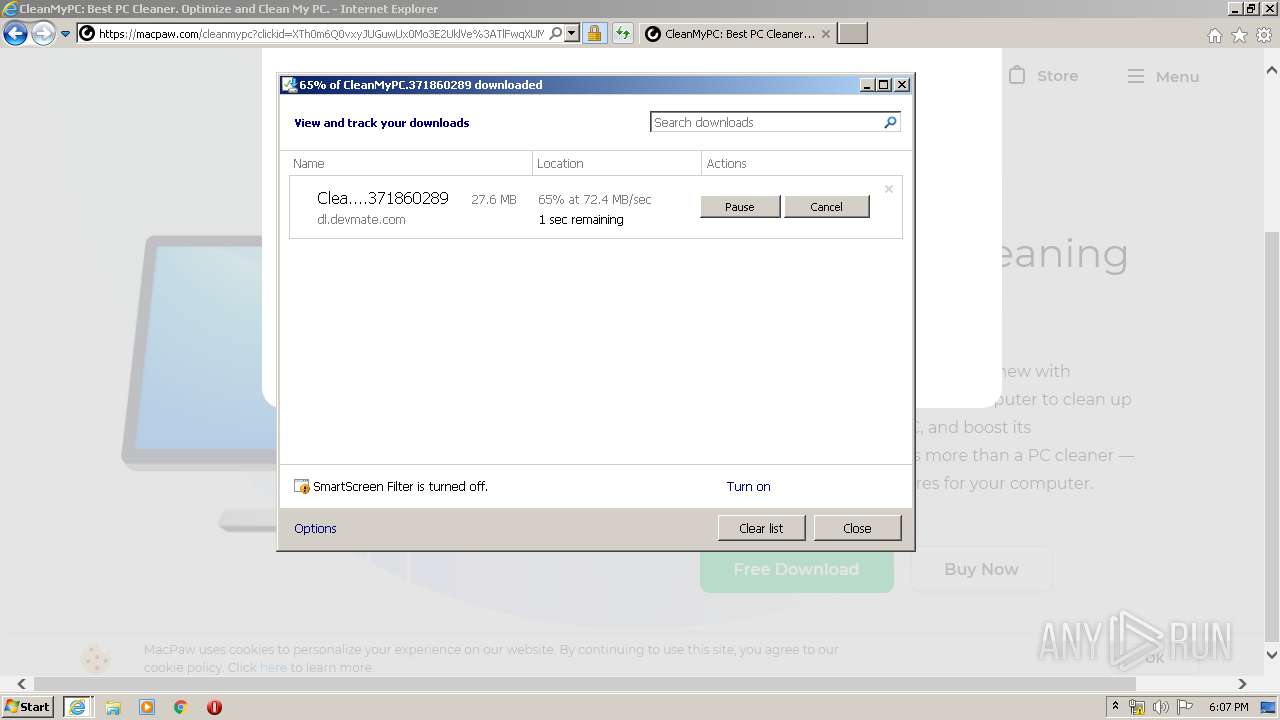
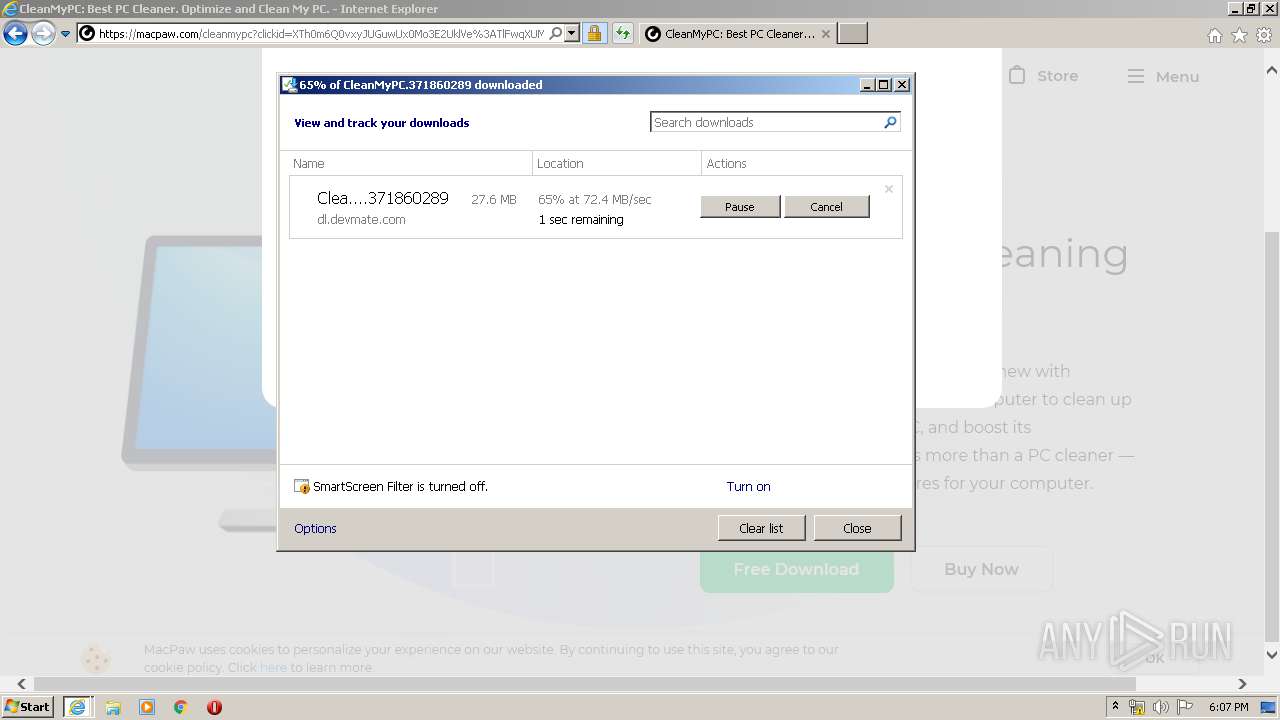
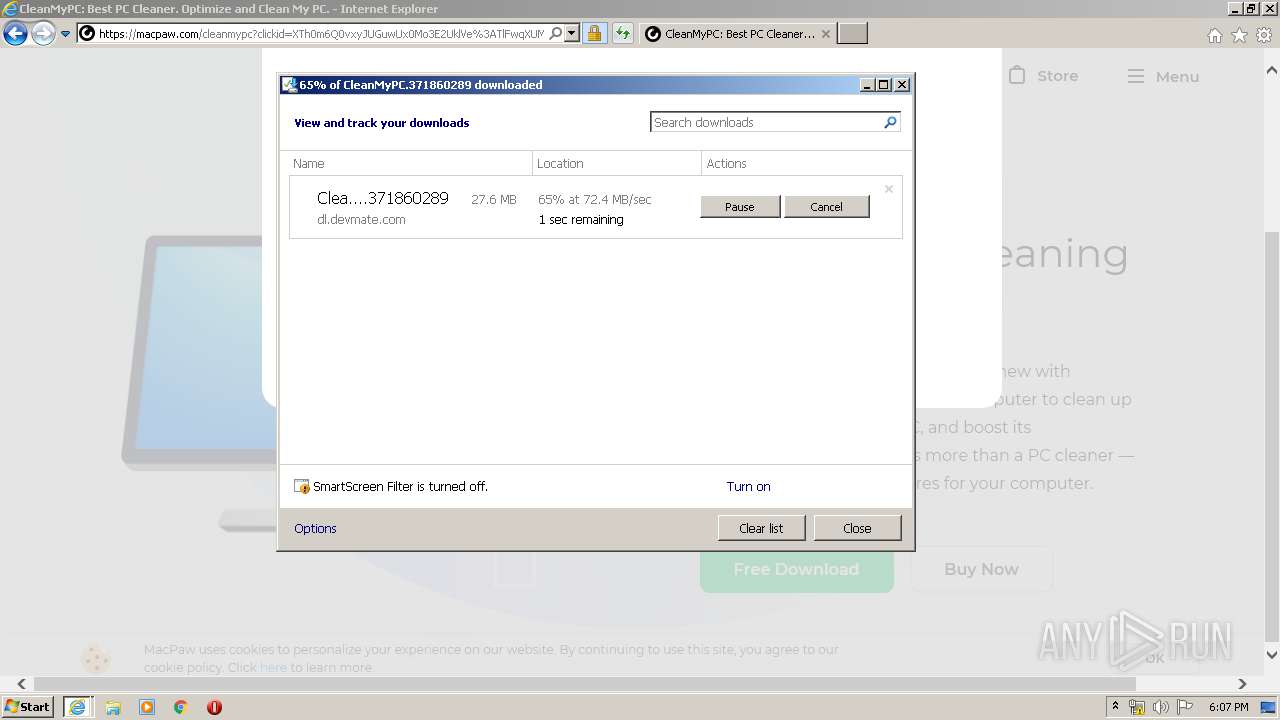
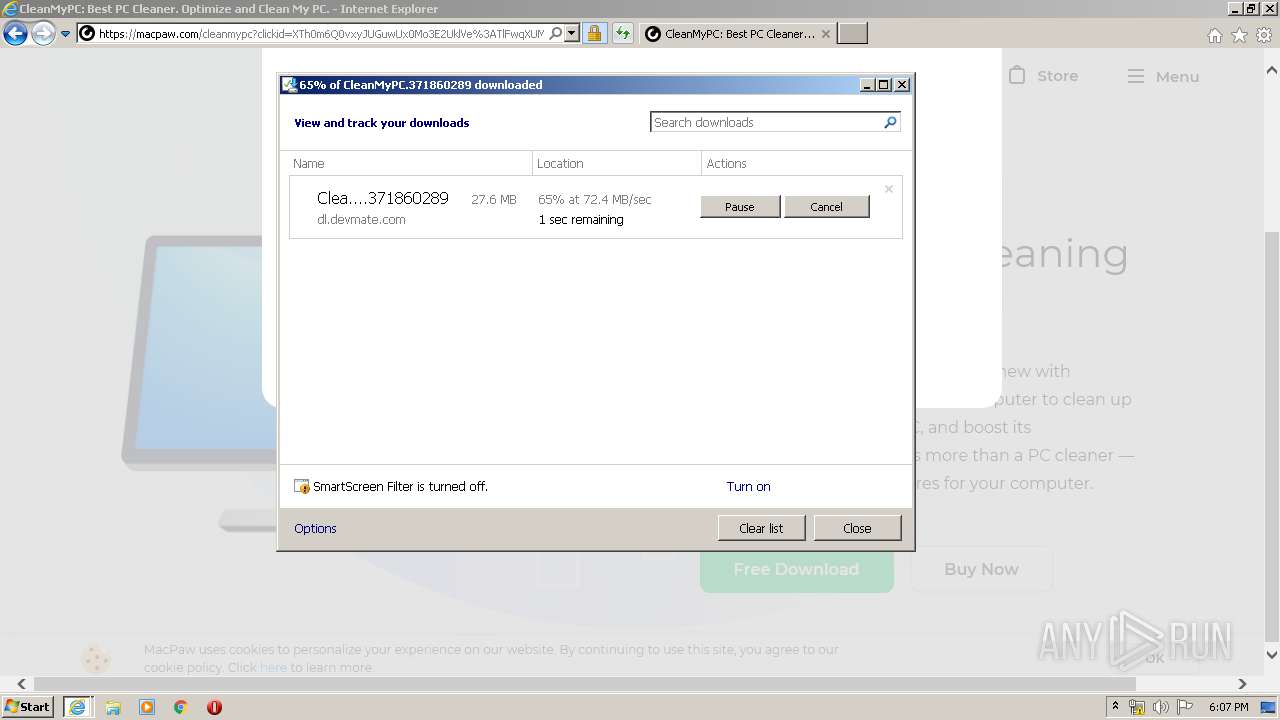
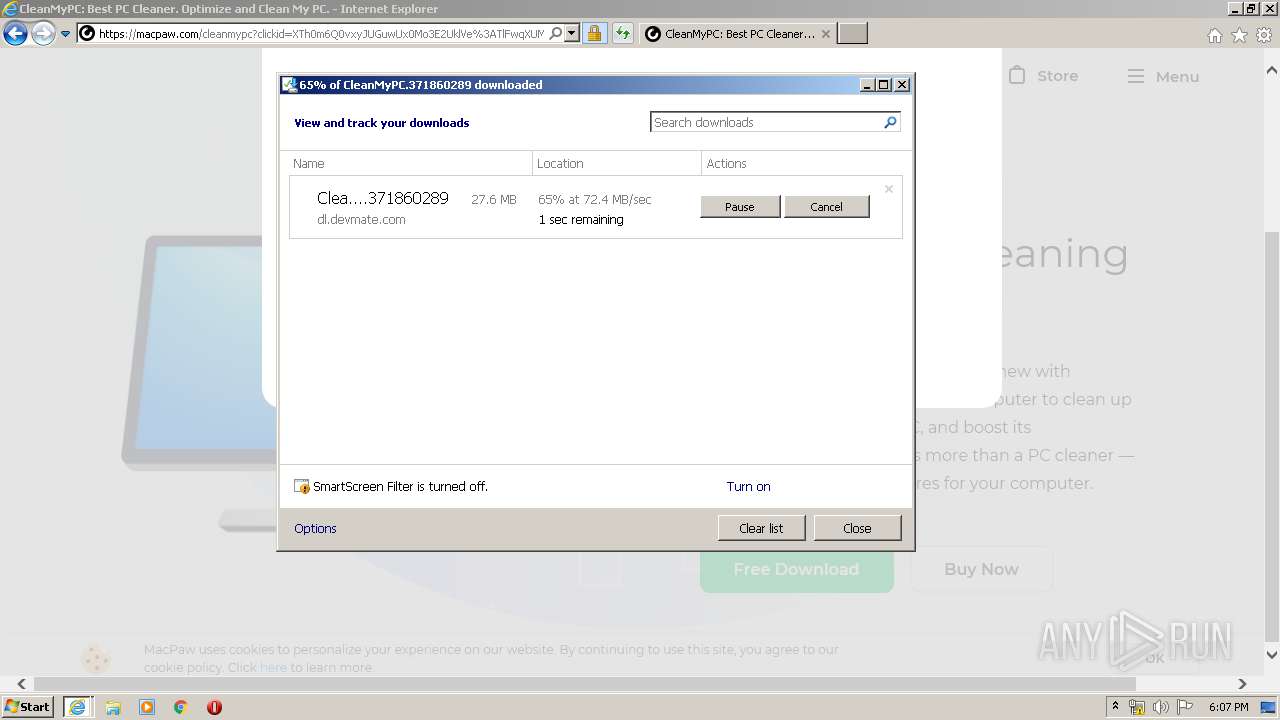
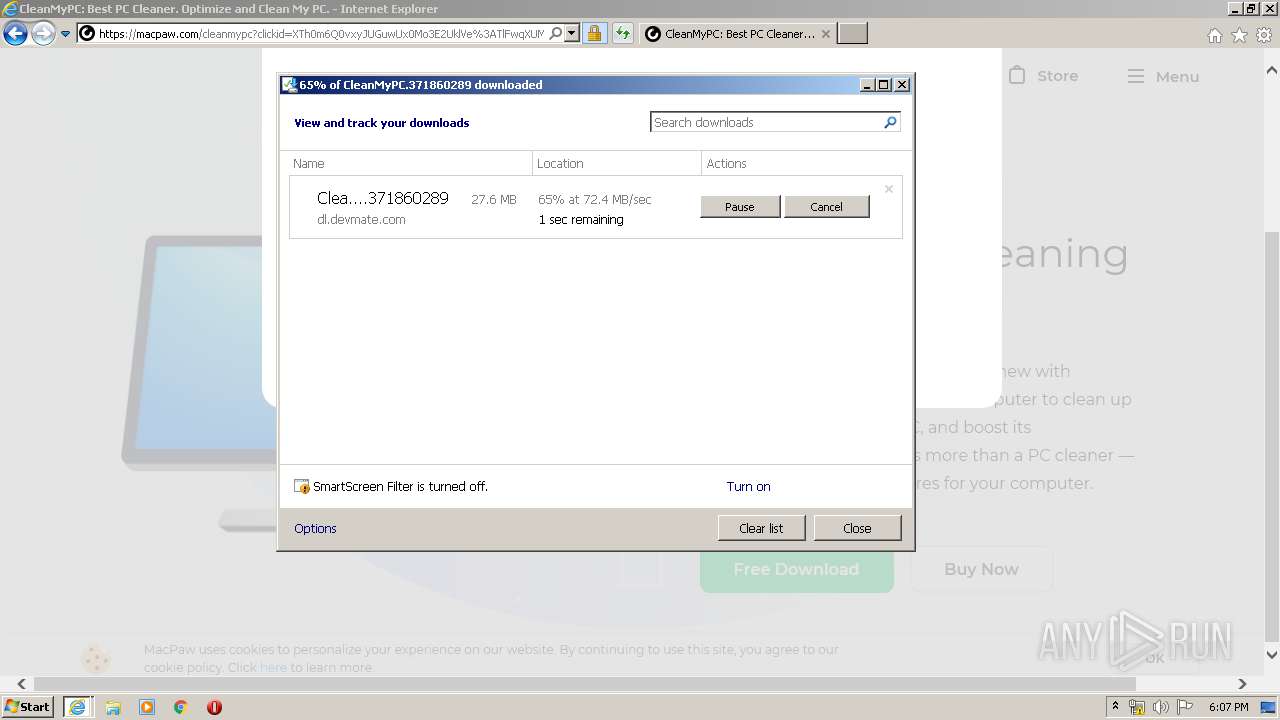
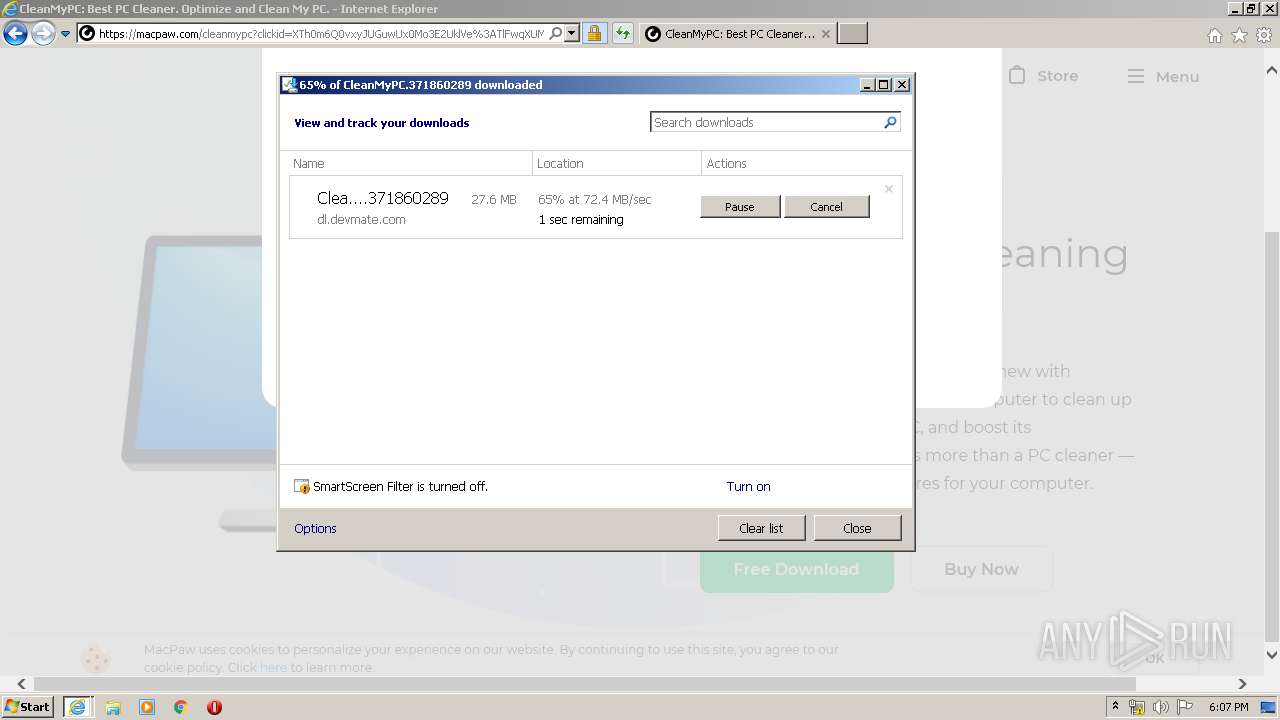
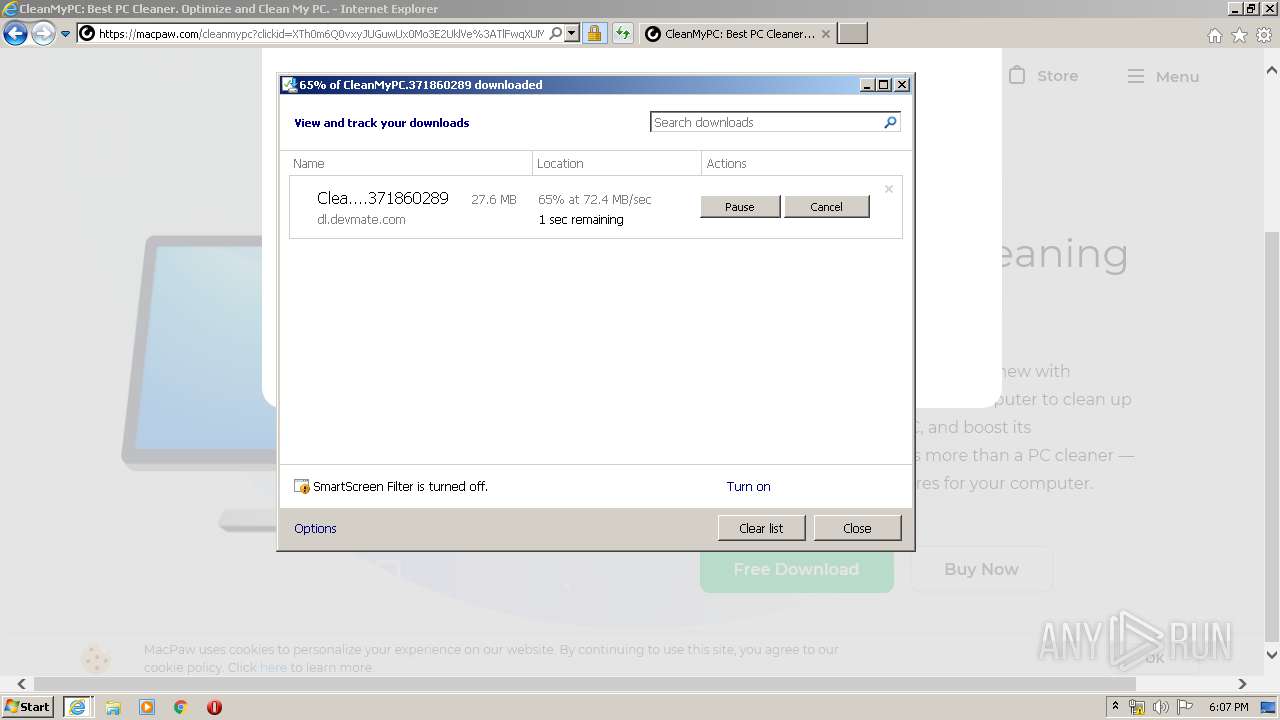
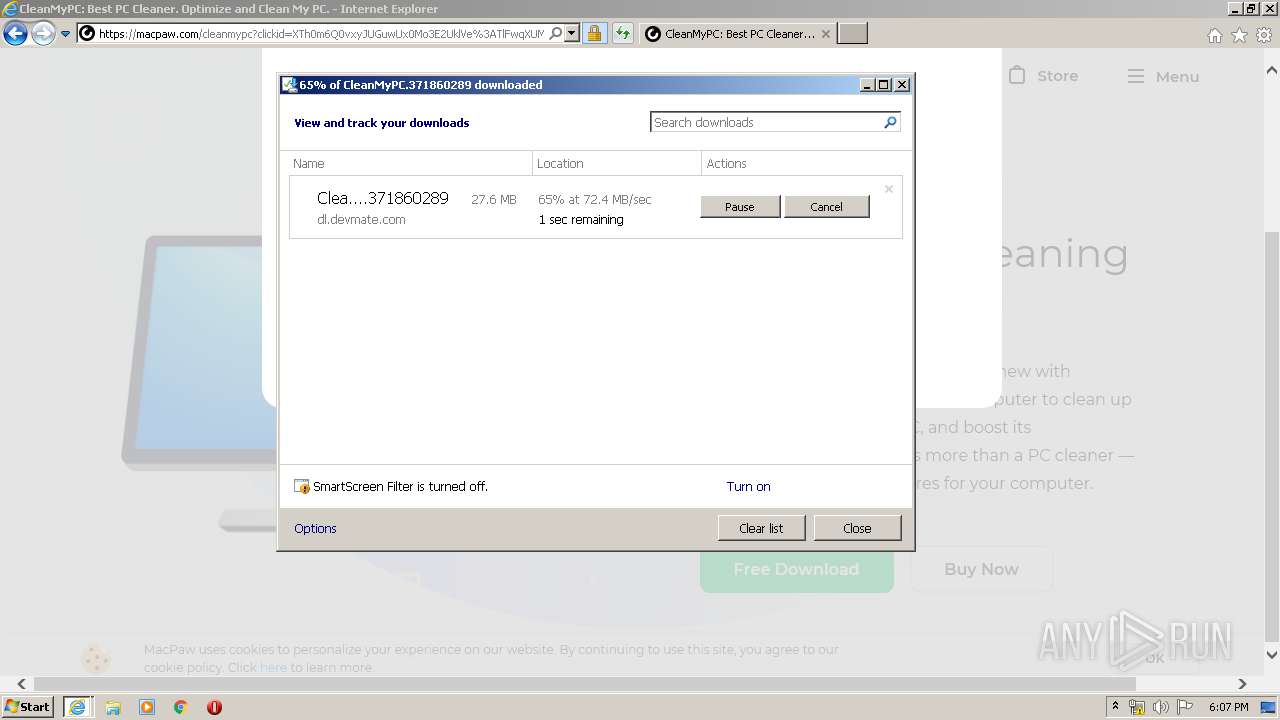
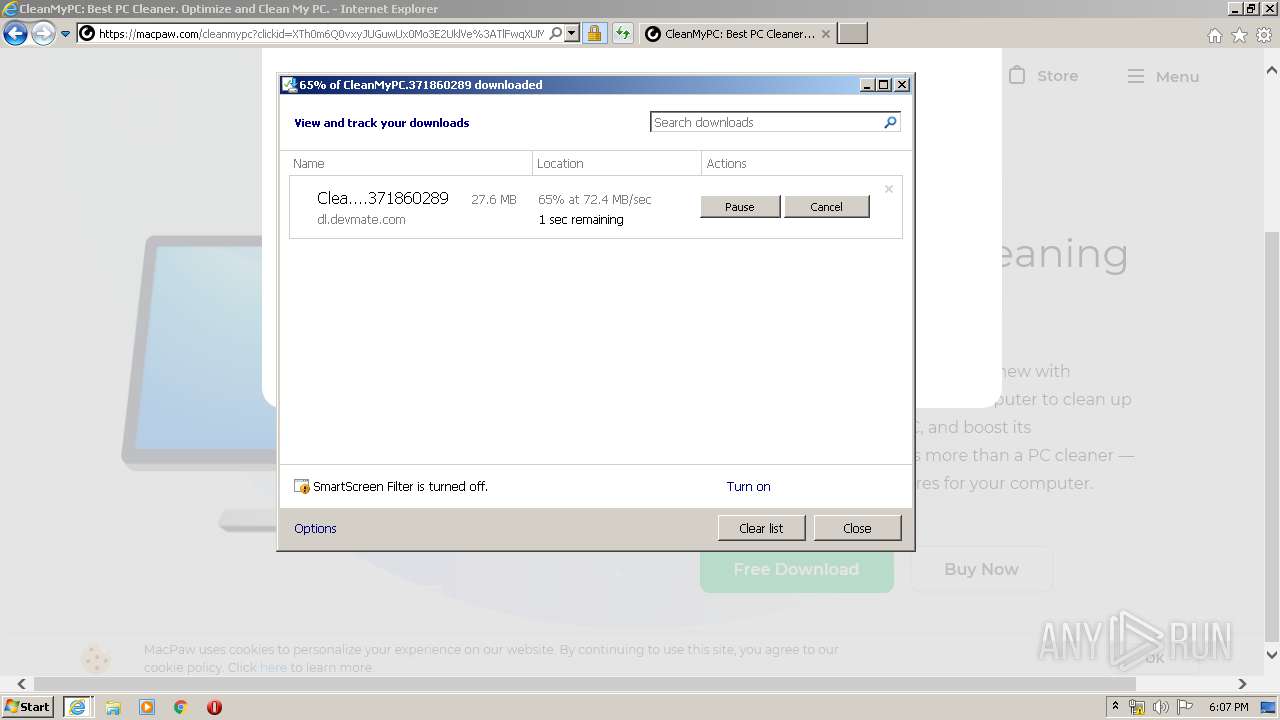
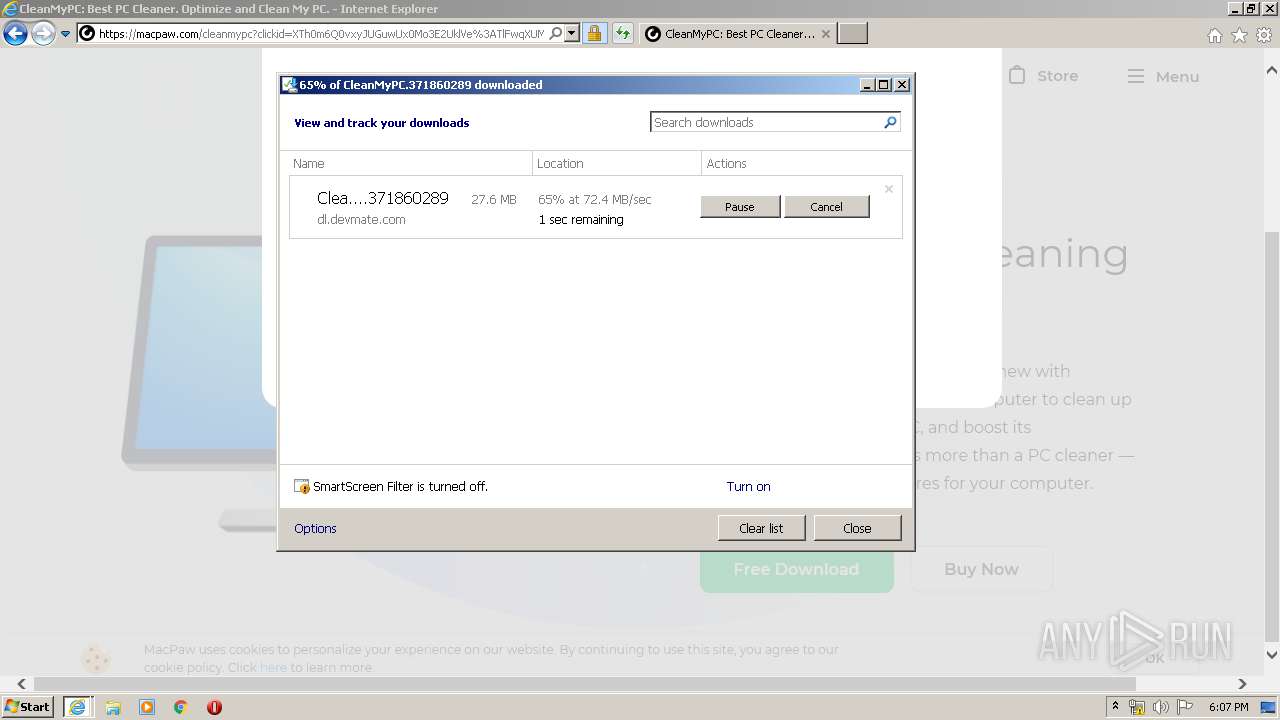
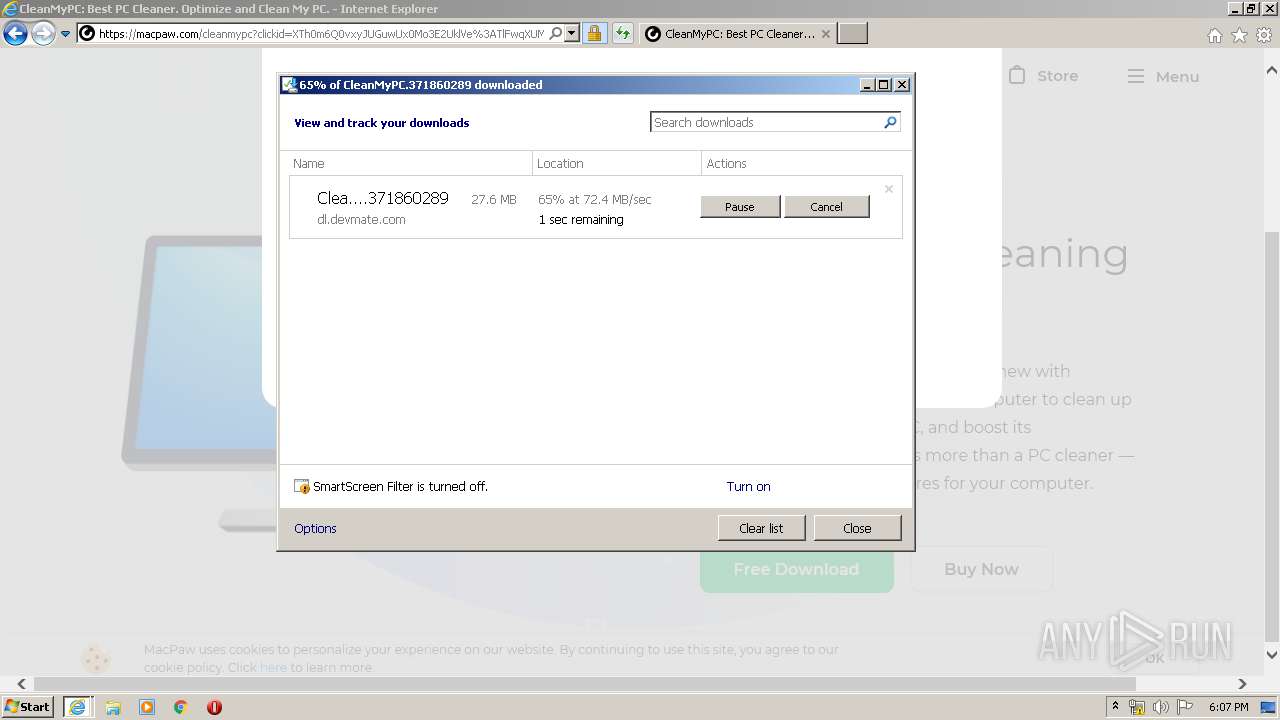
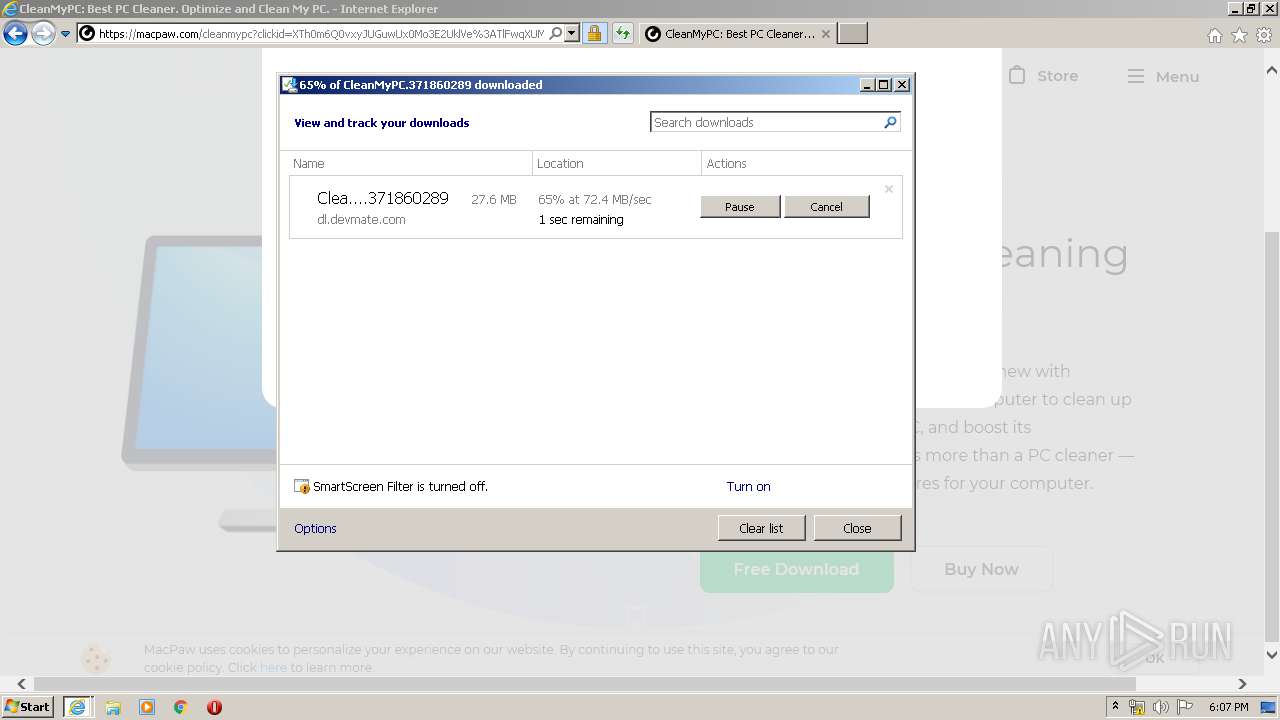
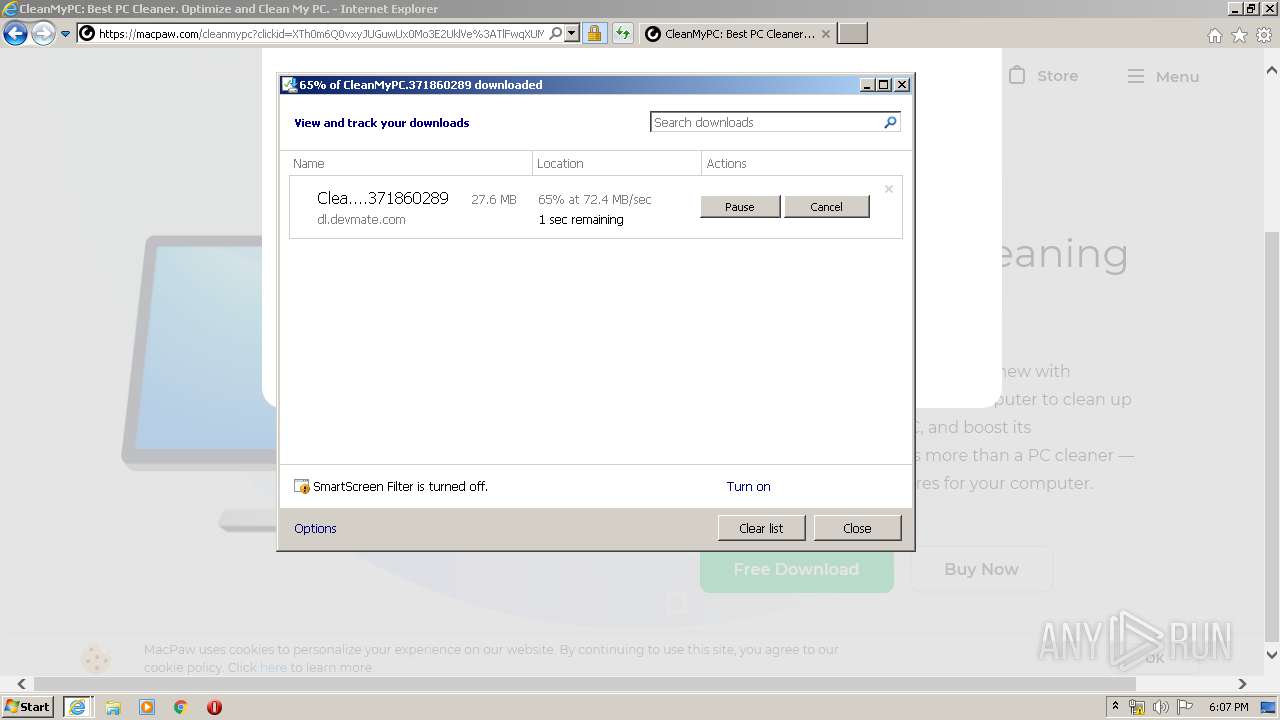
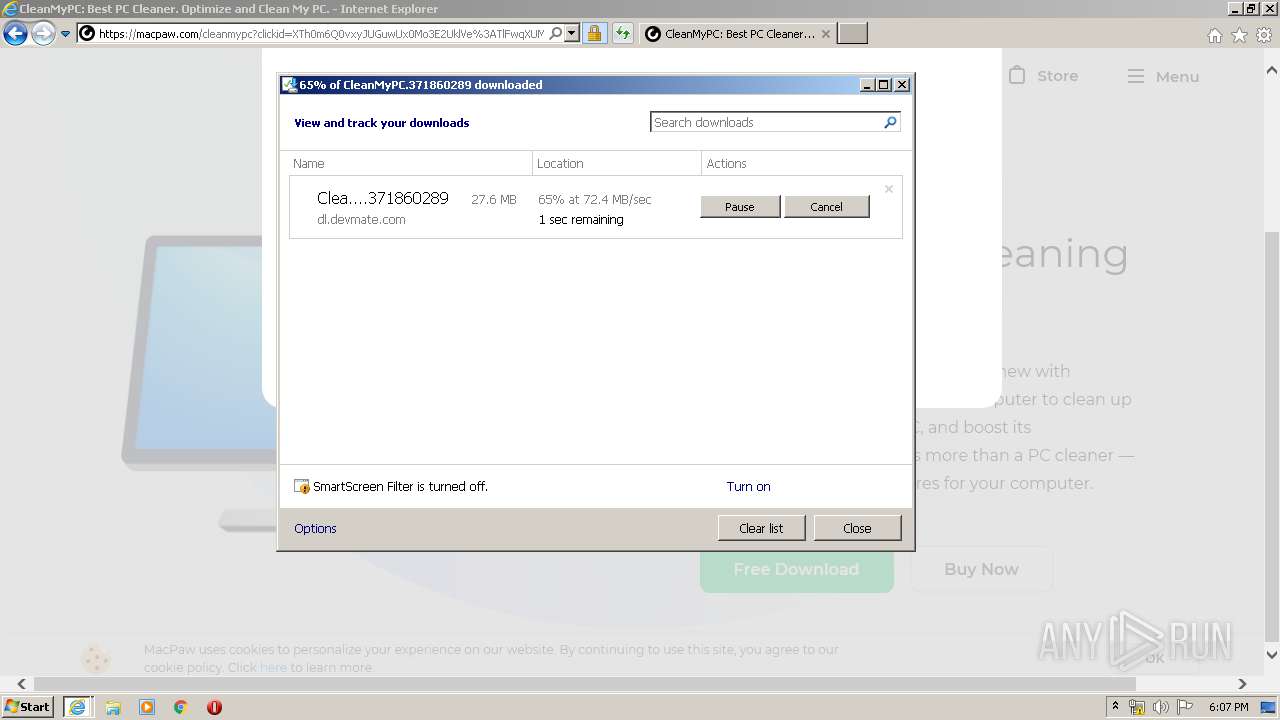
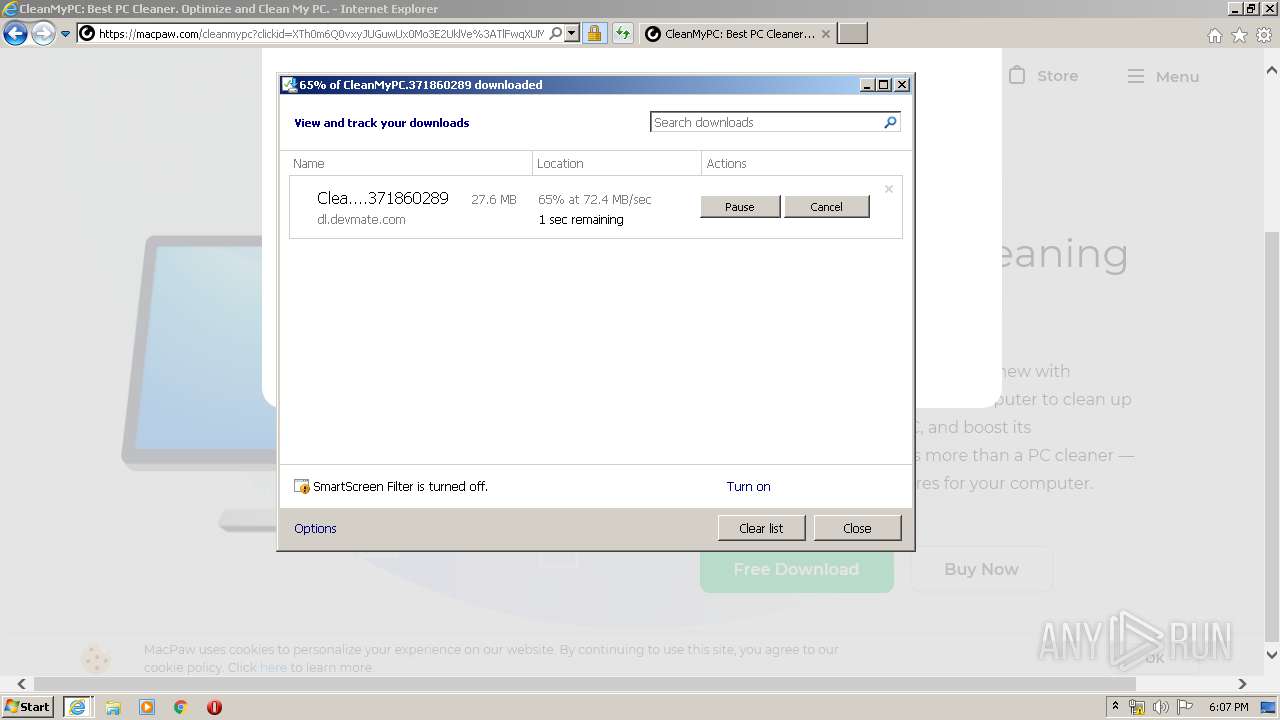
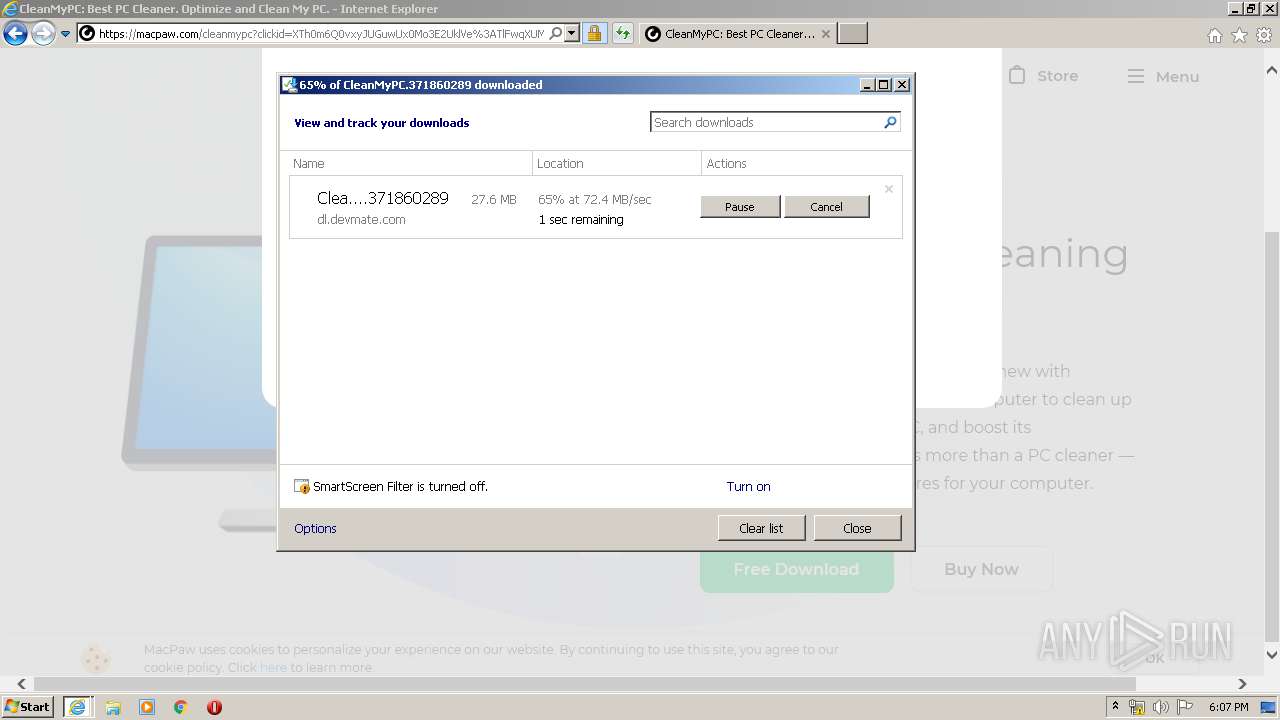
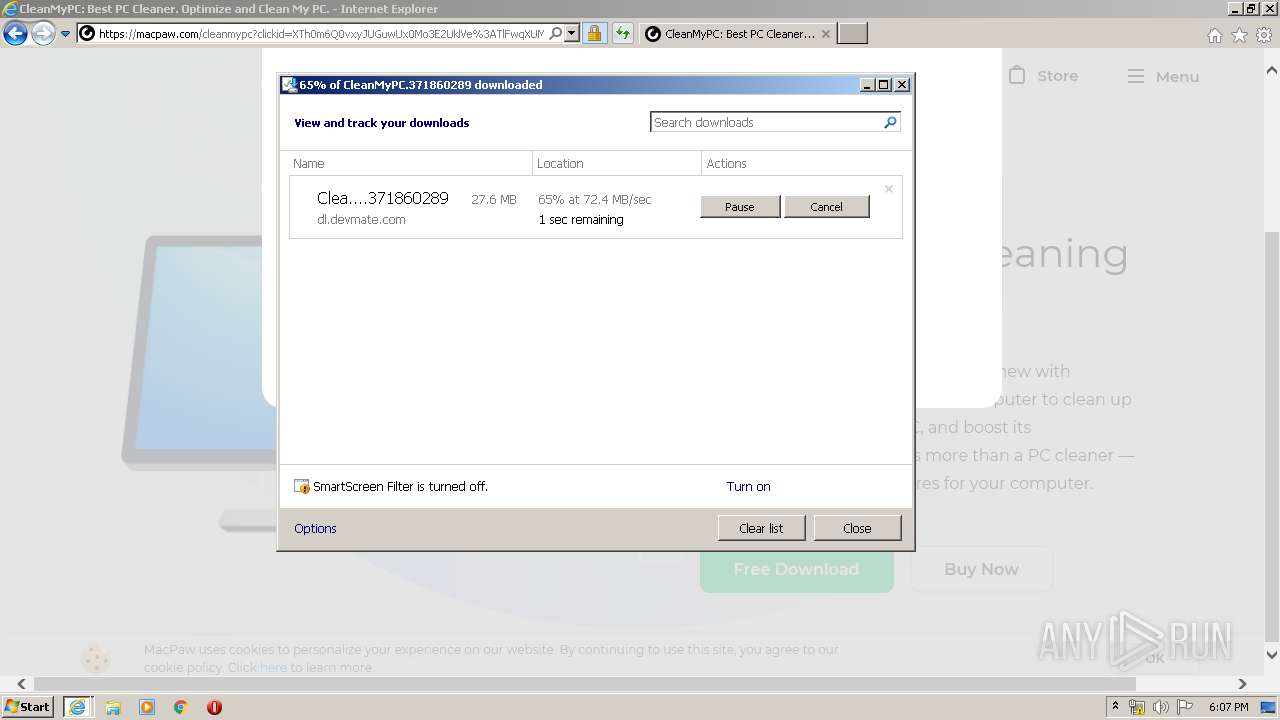
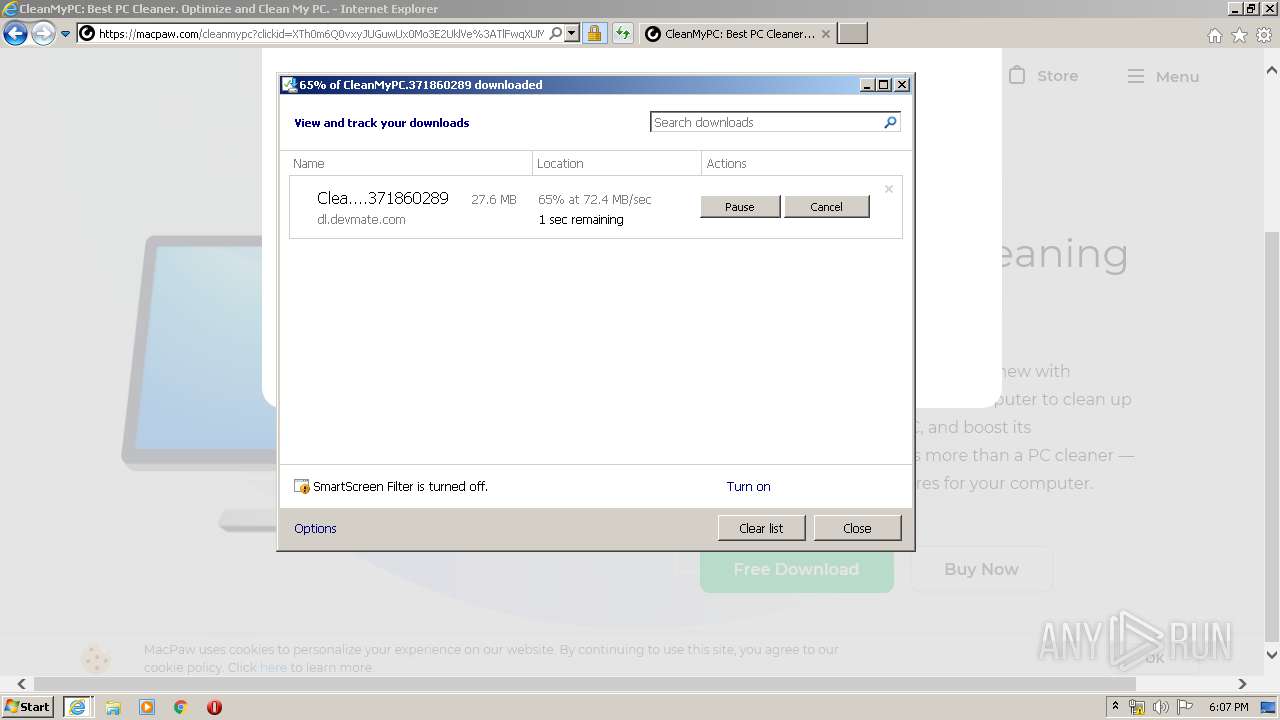
3252 | iexplore.exe | 143.204.202.118:443 | cdn2.macpaw.com | — | US | suspicious |
3252 | iexplore.exe | 143.204.208.127:80 | o.ss2.us | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
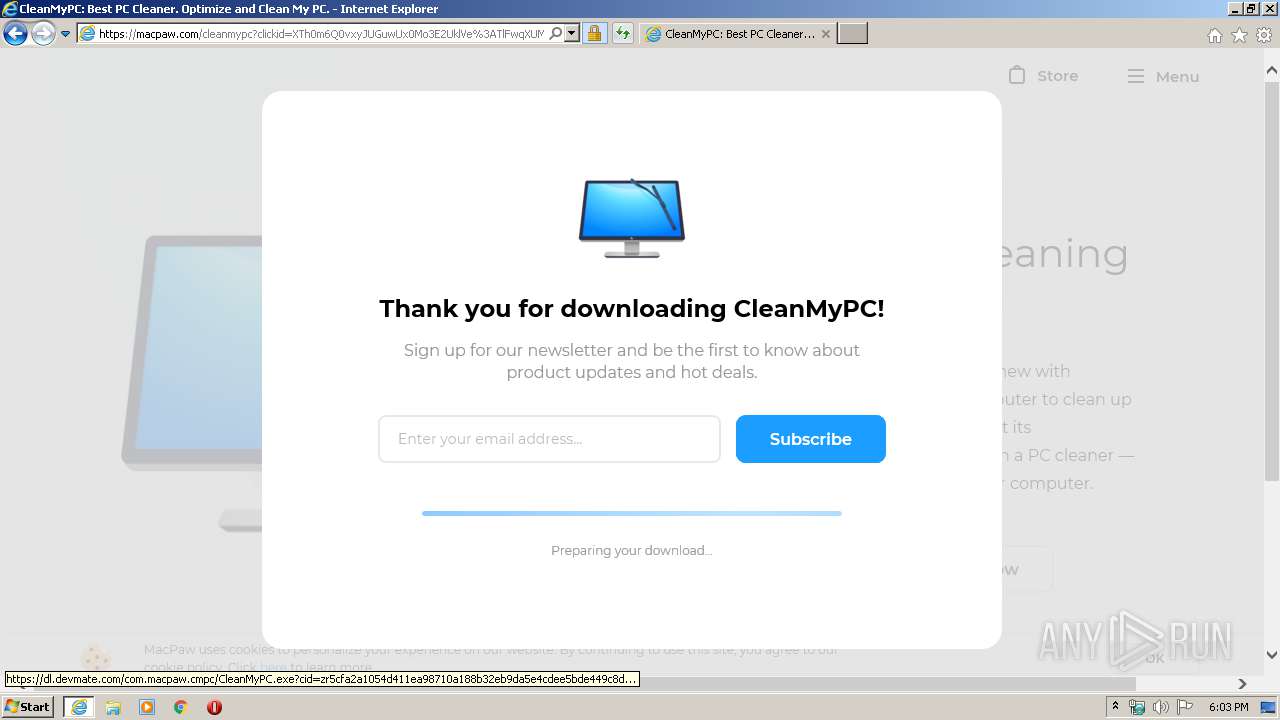
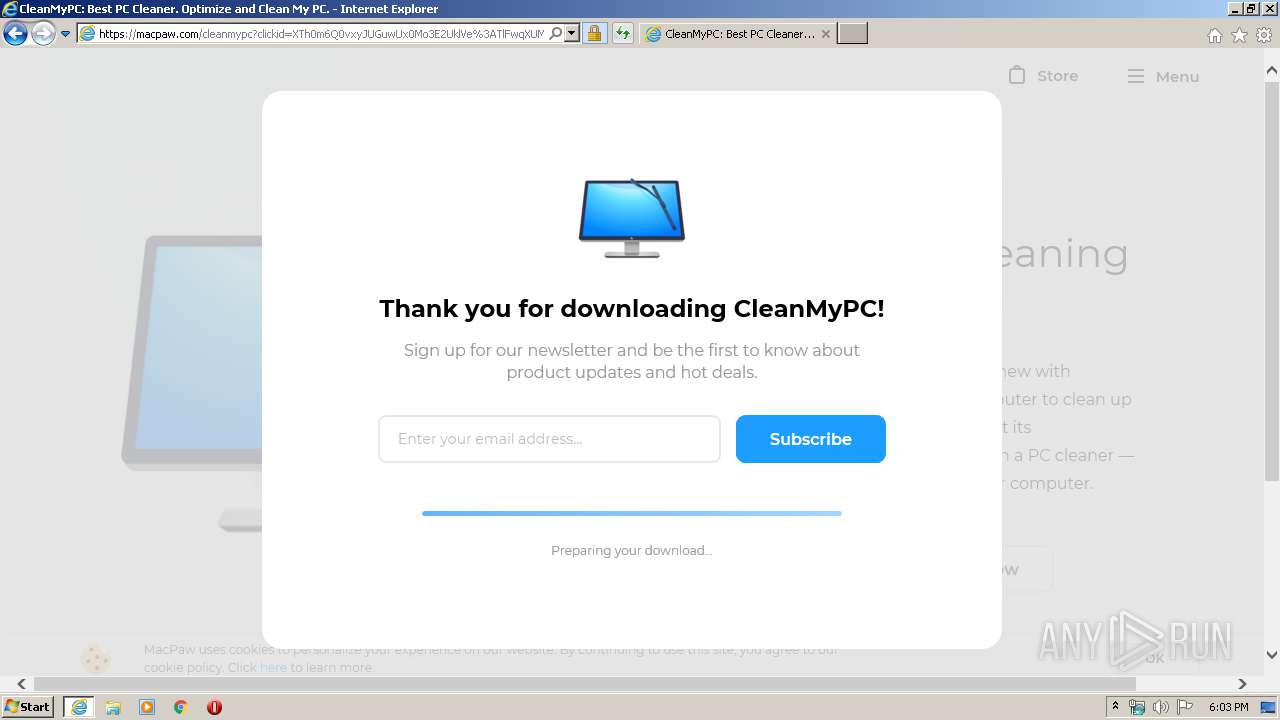
www.furnituremediclv.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
usa.iulianus-mon.com |
| shared |
qualmode.website |
| suspicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
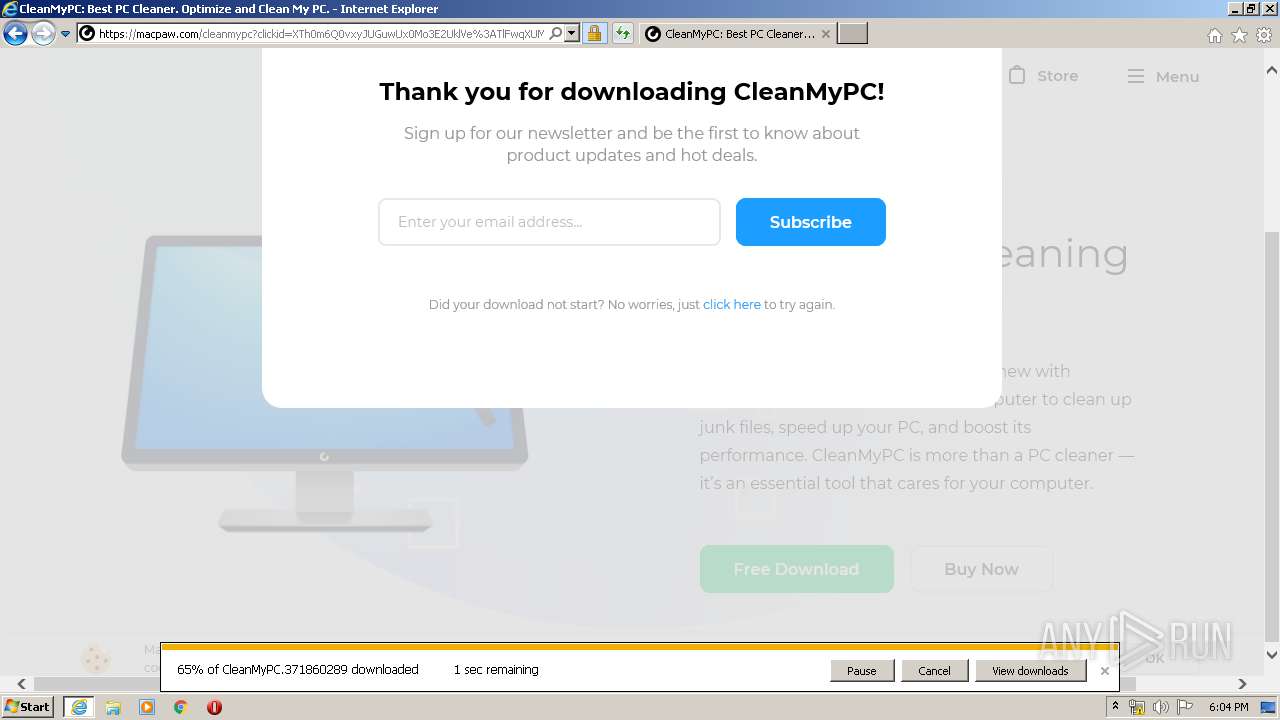
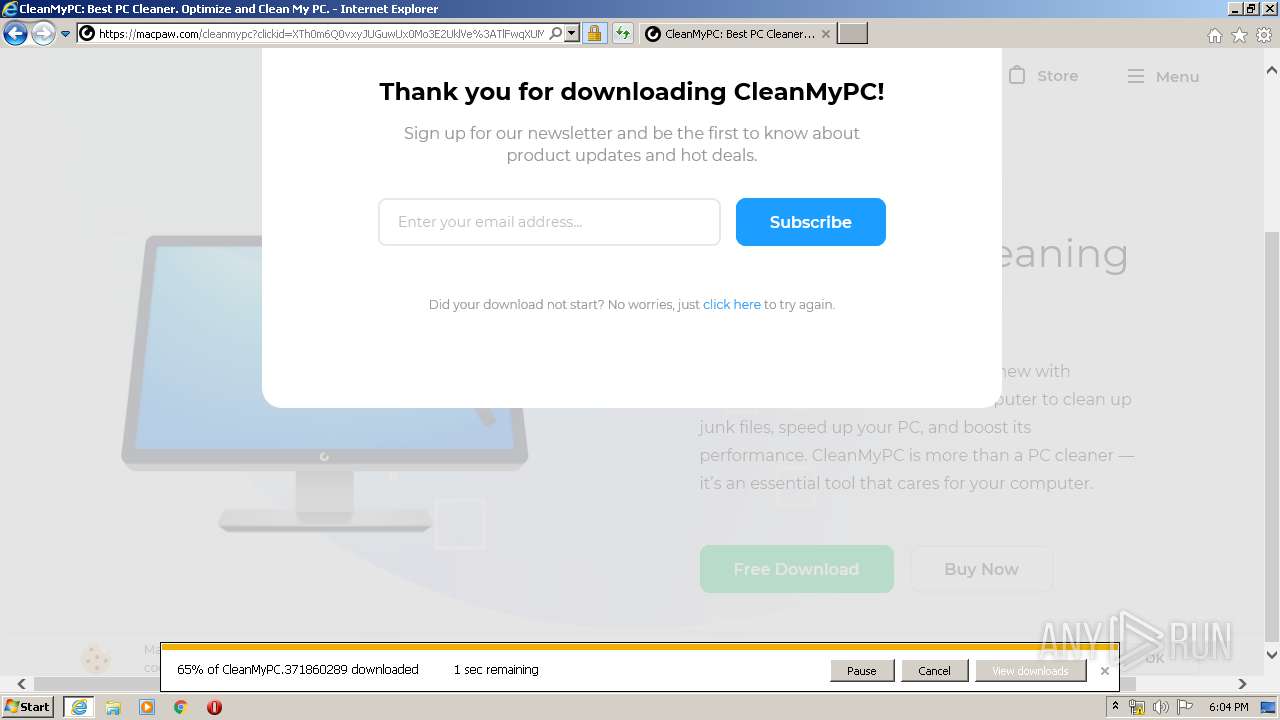
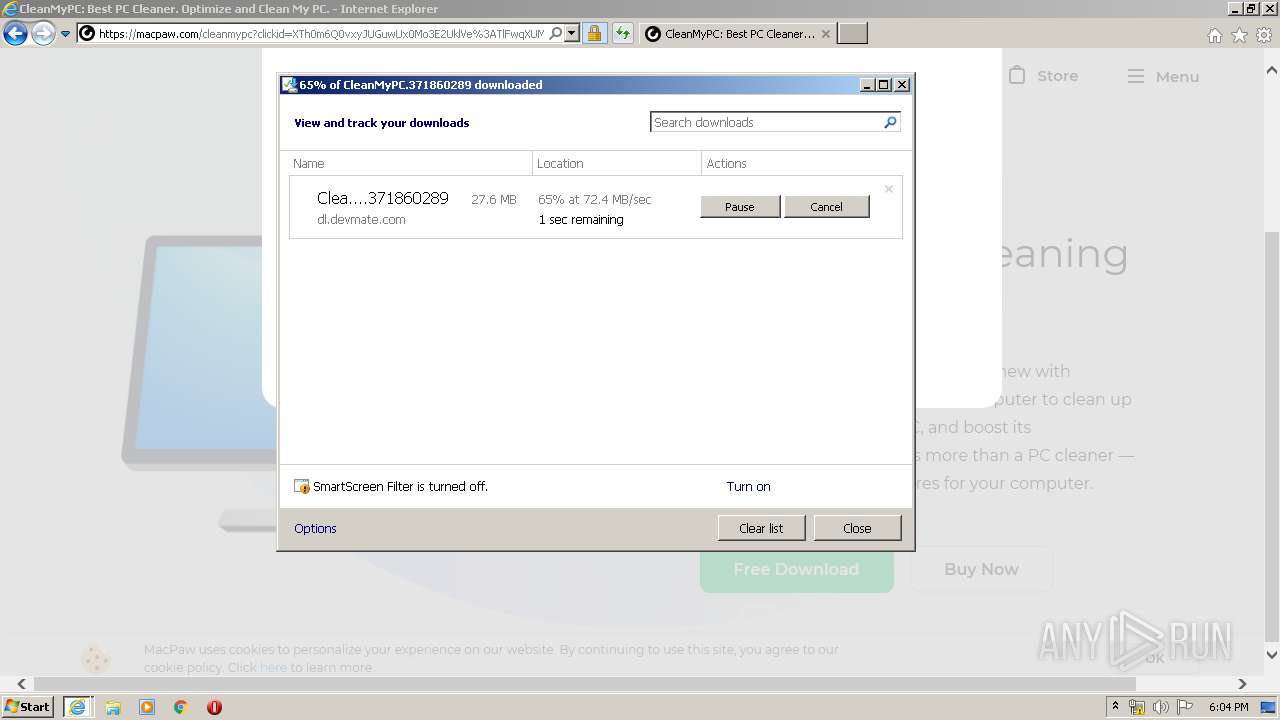
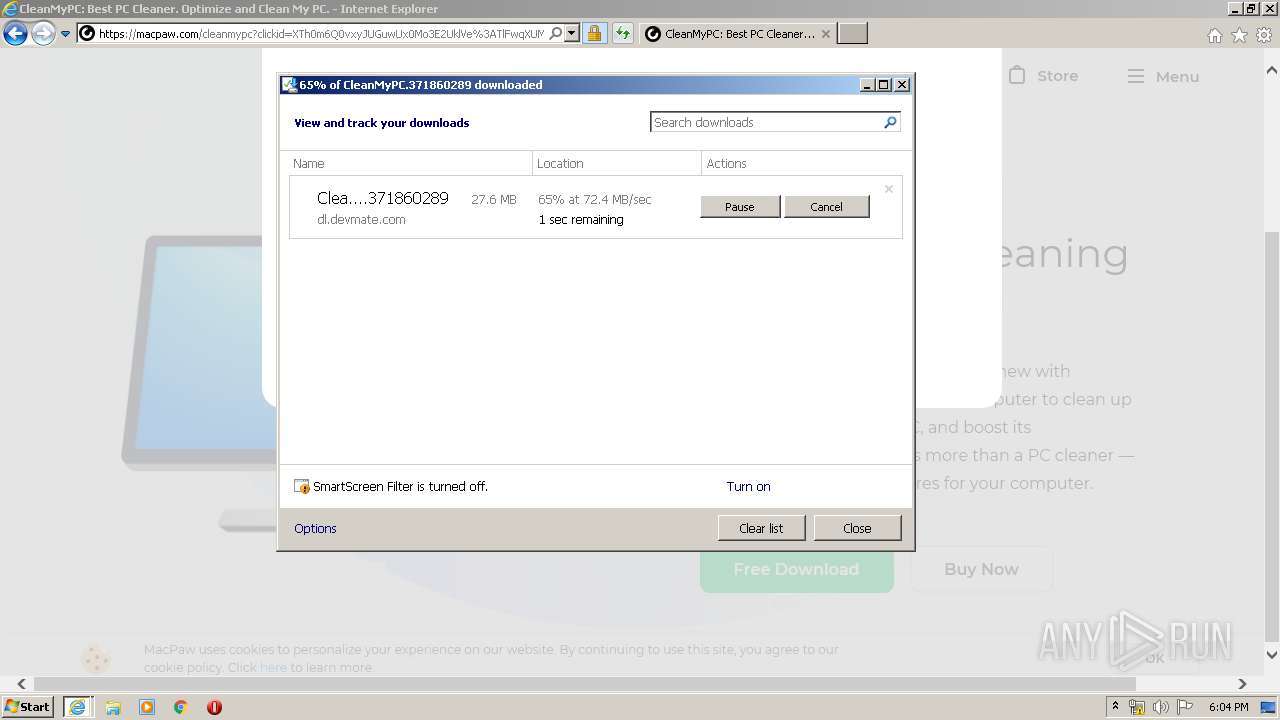
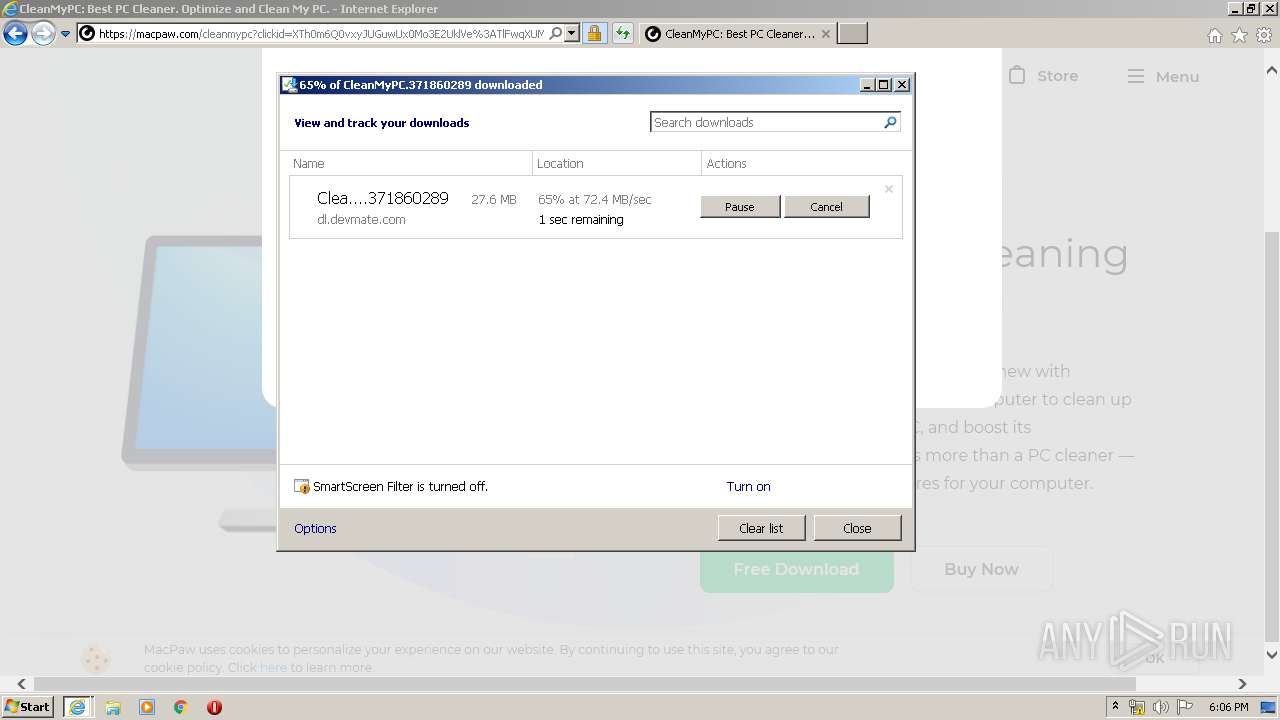
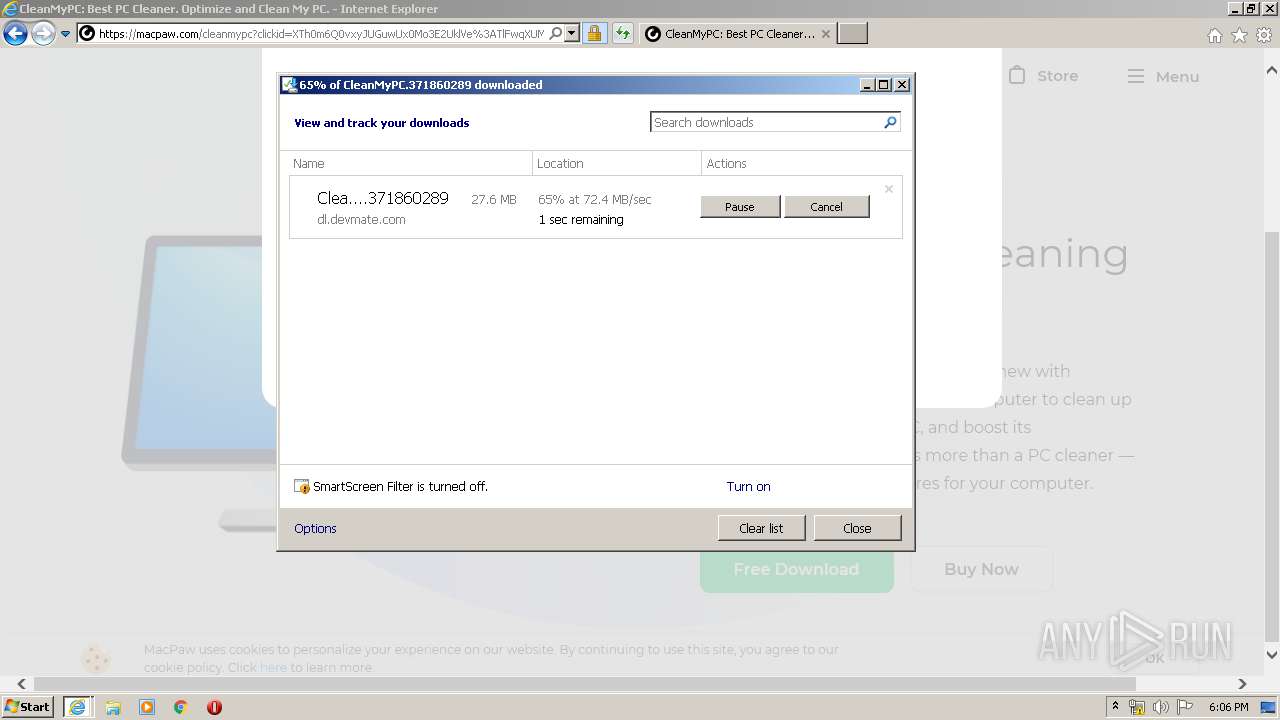
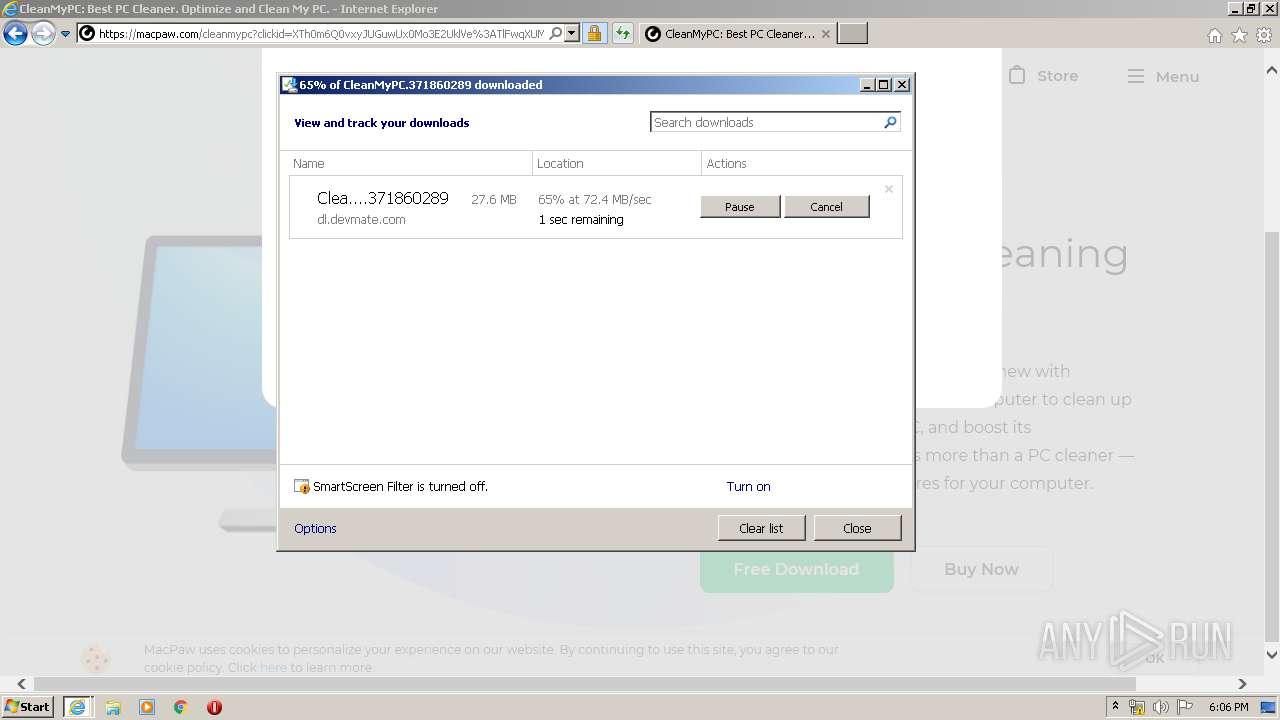
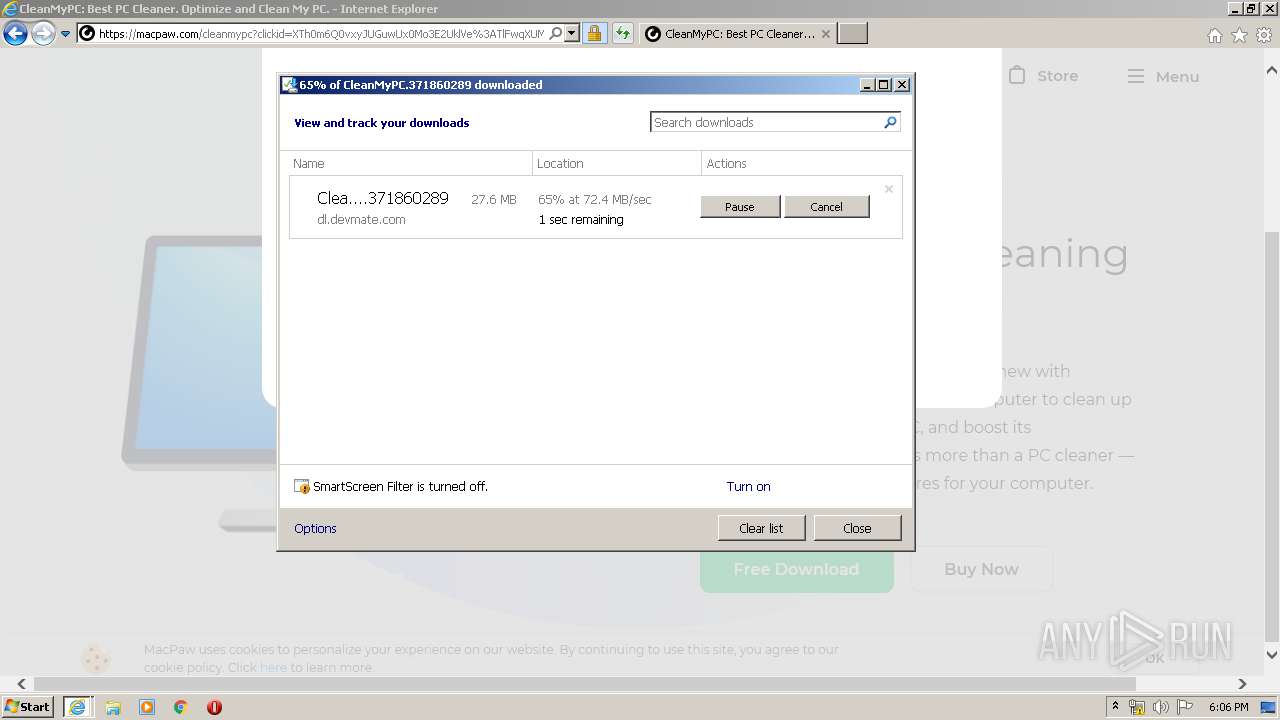
macpaw.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |