| URL: | https://jump.offerclk.net/aff_c?offer_id=69540&aff_id=410081&aff_sub=AffiliateApi&aff_sub2=6oq69&aff_sub3=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzUxMiJ9.eyJpc3MiOiJvZ2FkcyIsImF1ZCI6InBvc3RiYWNrIiwiaWF0IjoxNzY3NjIwNzExLCJuYmYiOjE3Njc2MjA3MTEsImRhdGEiOnsiaXAiOiIyYTAyOjZlYTA6Y2MwMjo1NTE2OjoxMiIsInVhIjoiTW96aWxsYS81LjAgKFgxMTsgQ3JPUyB4ODZfNjQgMTQ1NDEuMC4wKSBBcHBsZVdlYktpdC81MzcuMzYgKEtIVE1MLCBsaWtlIEdlY2tvKSBDaHJvbWUvMTQyLjAuMC4wIFNhZmFyaS81MzcuMzYiLCJyZWYiOm51bGx9fQ.Q4VzuQDgtqAjm_QUgUWxajTMT43eWv_pTQiJu4-KoEbiInDniPqEc9NKyHF9-AcQkC-hOpz-uPzS8WWiqaK2gw&aff_sub4=a0f0a076&aff_sub5=42b6aaa8-6f90-48b8-bf11-1a63836eab7c_69682283&aff_sub4=a0f0a076&aff_sub5=42b6aaa8-6f90-48b8-bf11-1a63836eab7c_69682283 |
| Full analysis: | https://app.any.run/tasks/a4055517-c5aa-4acc-92d9-2bbd65a187e1 |
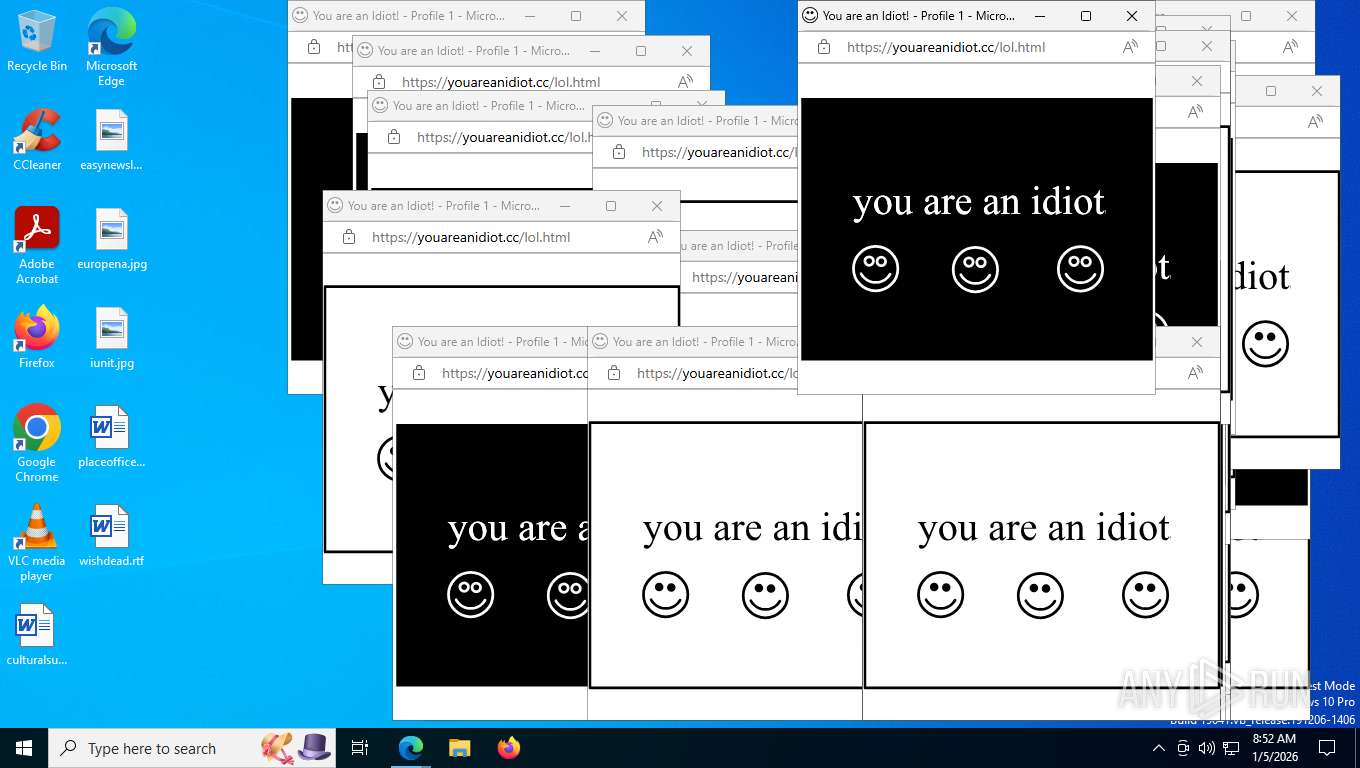
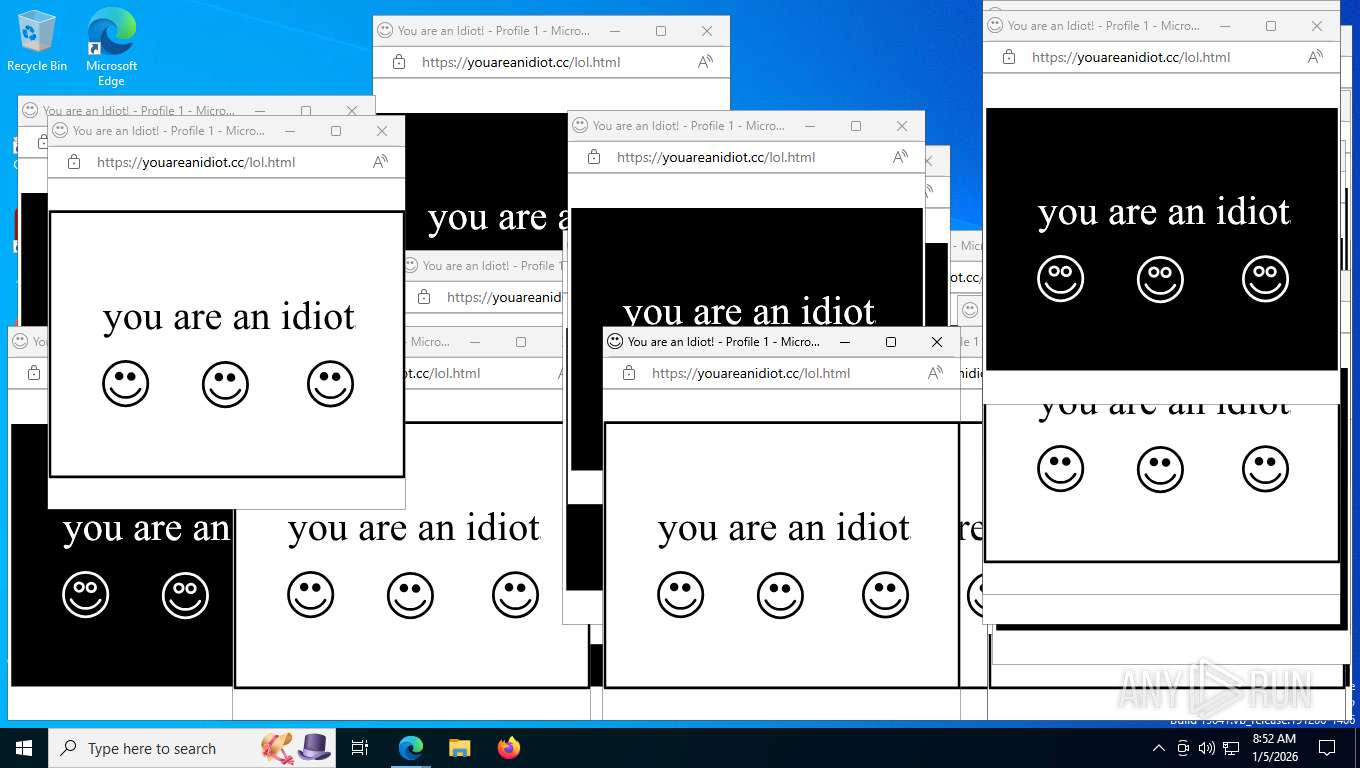
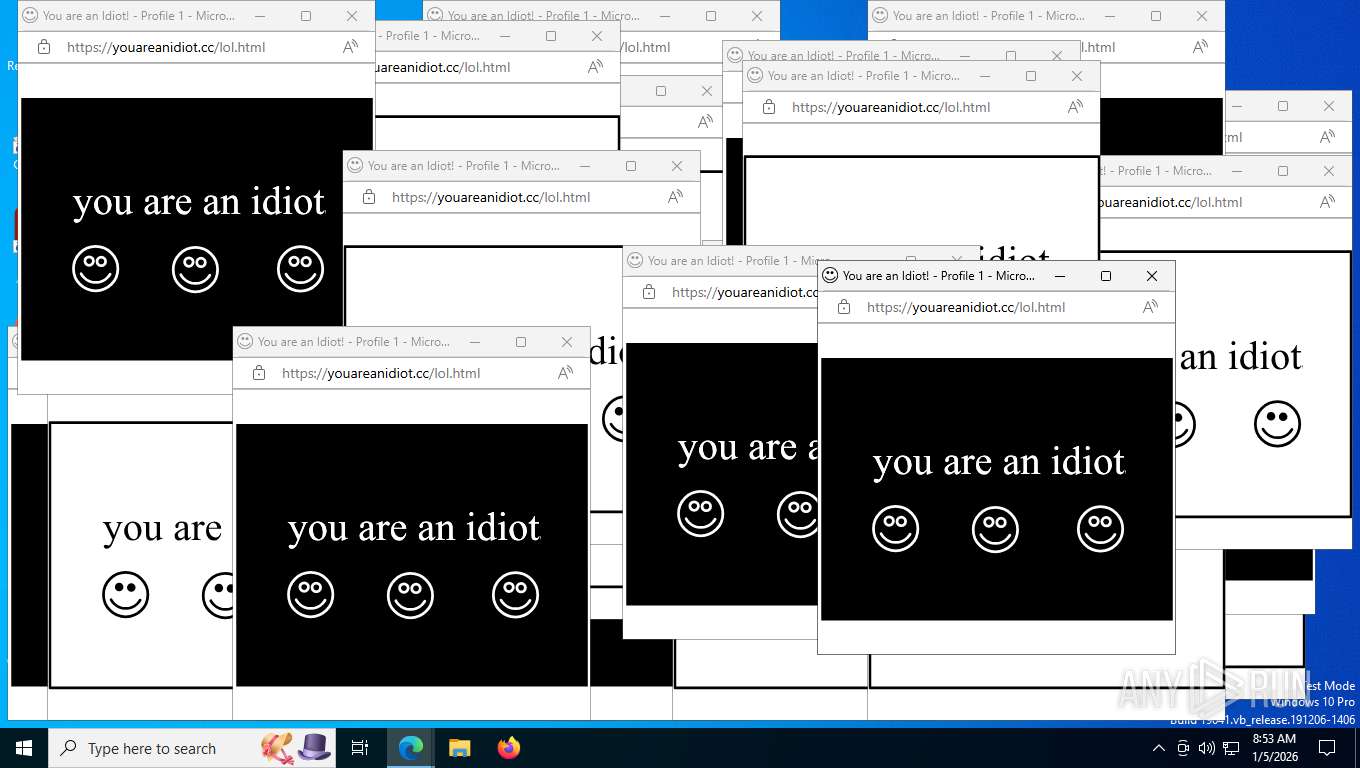
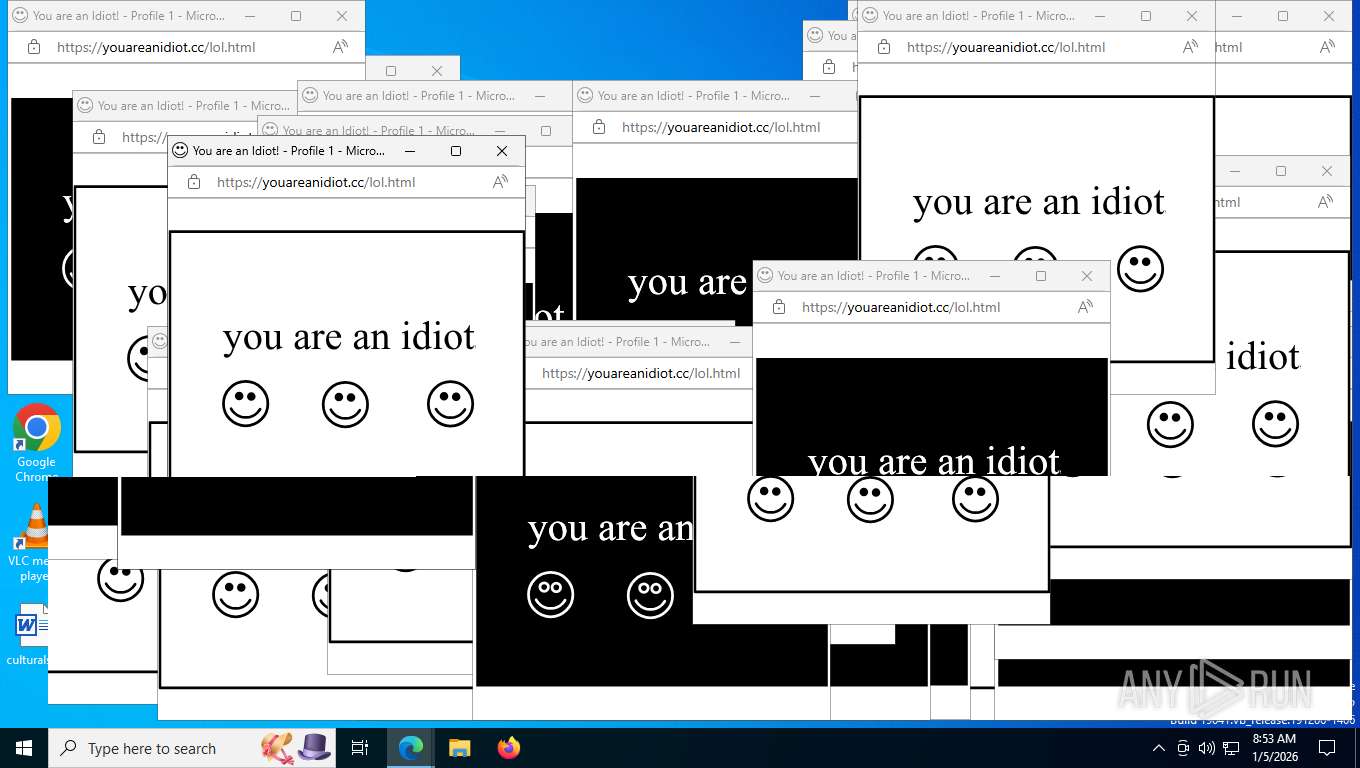
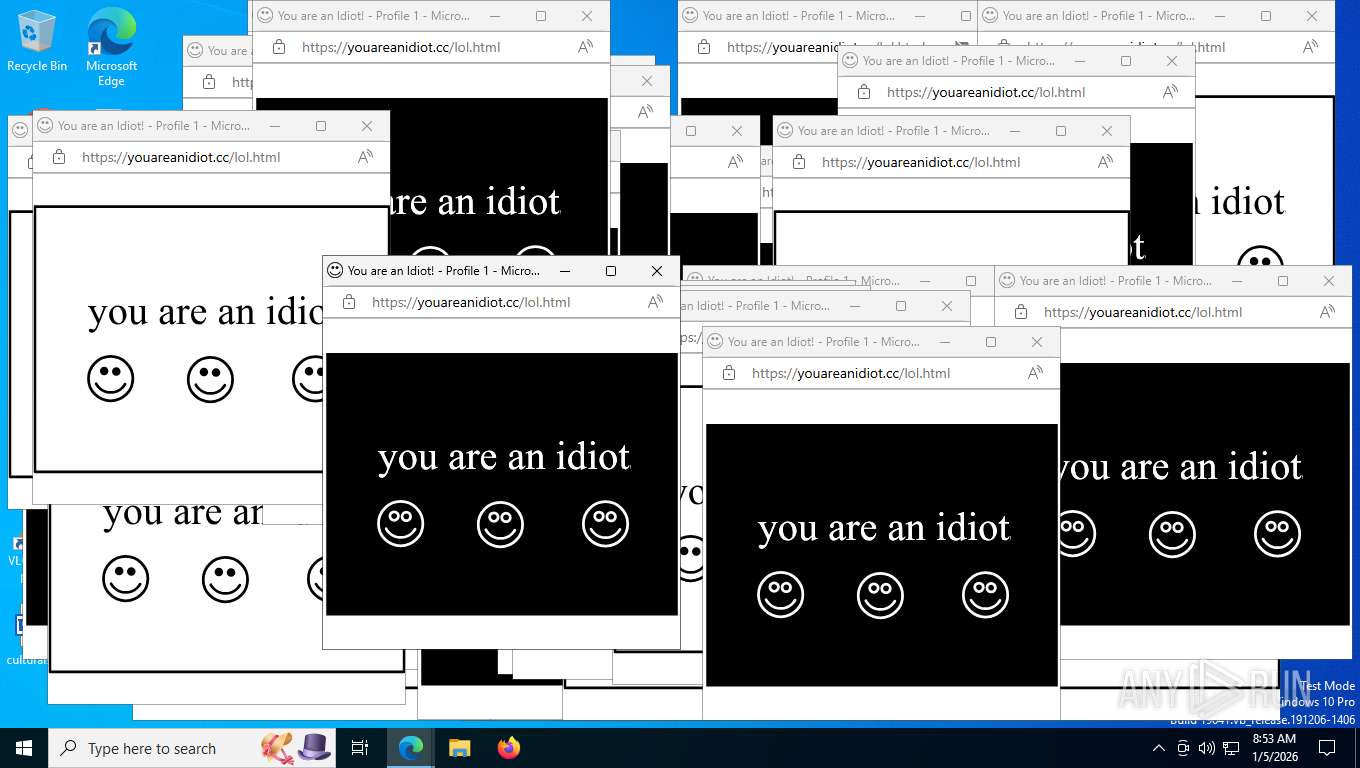
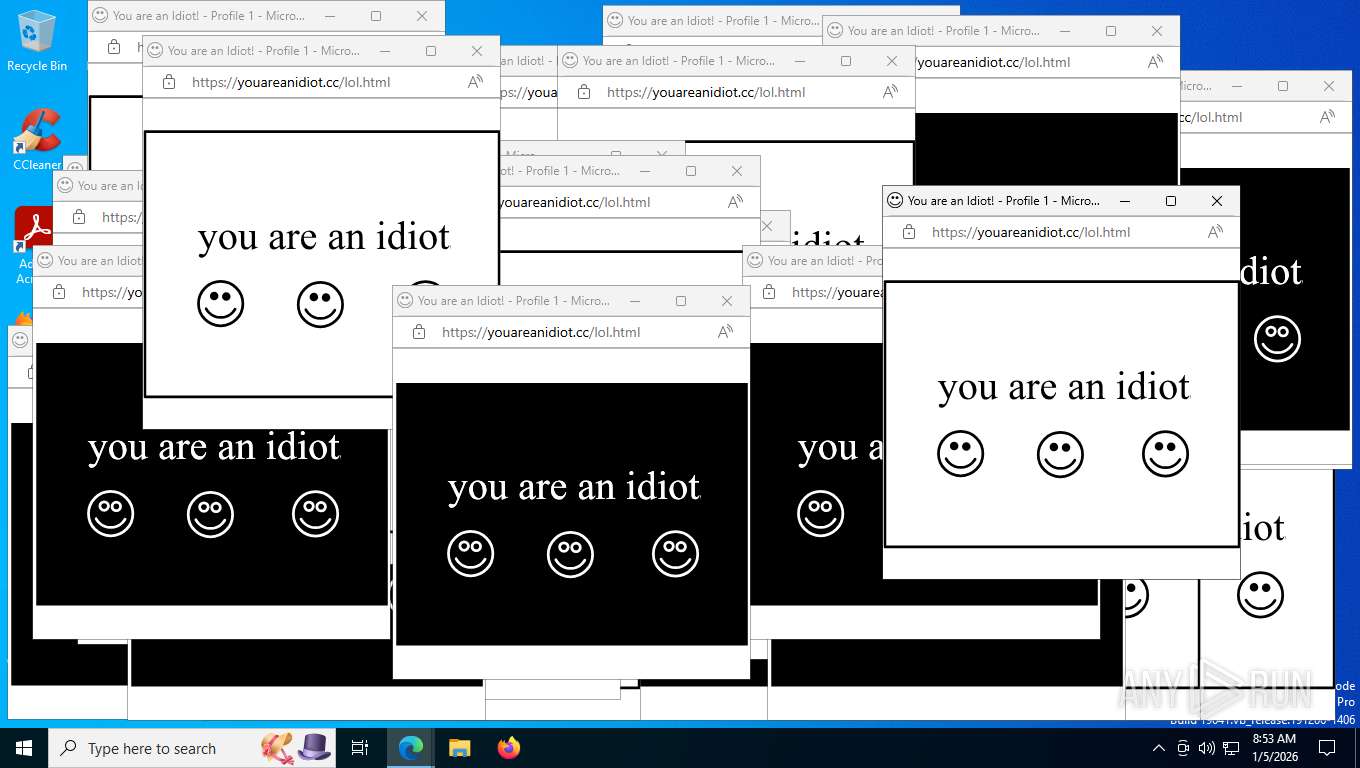
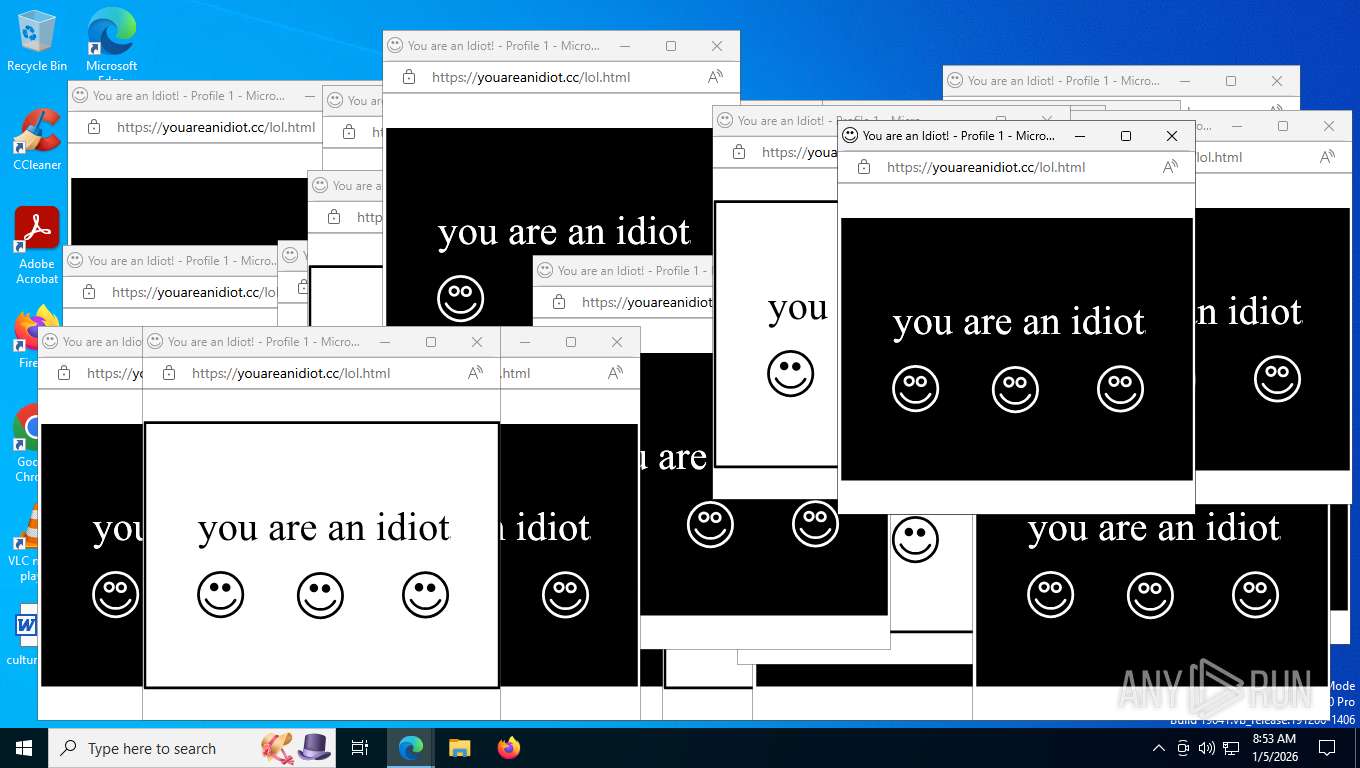
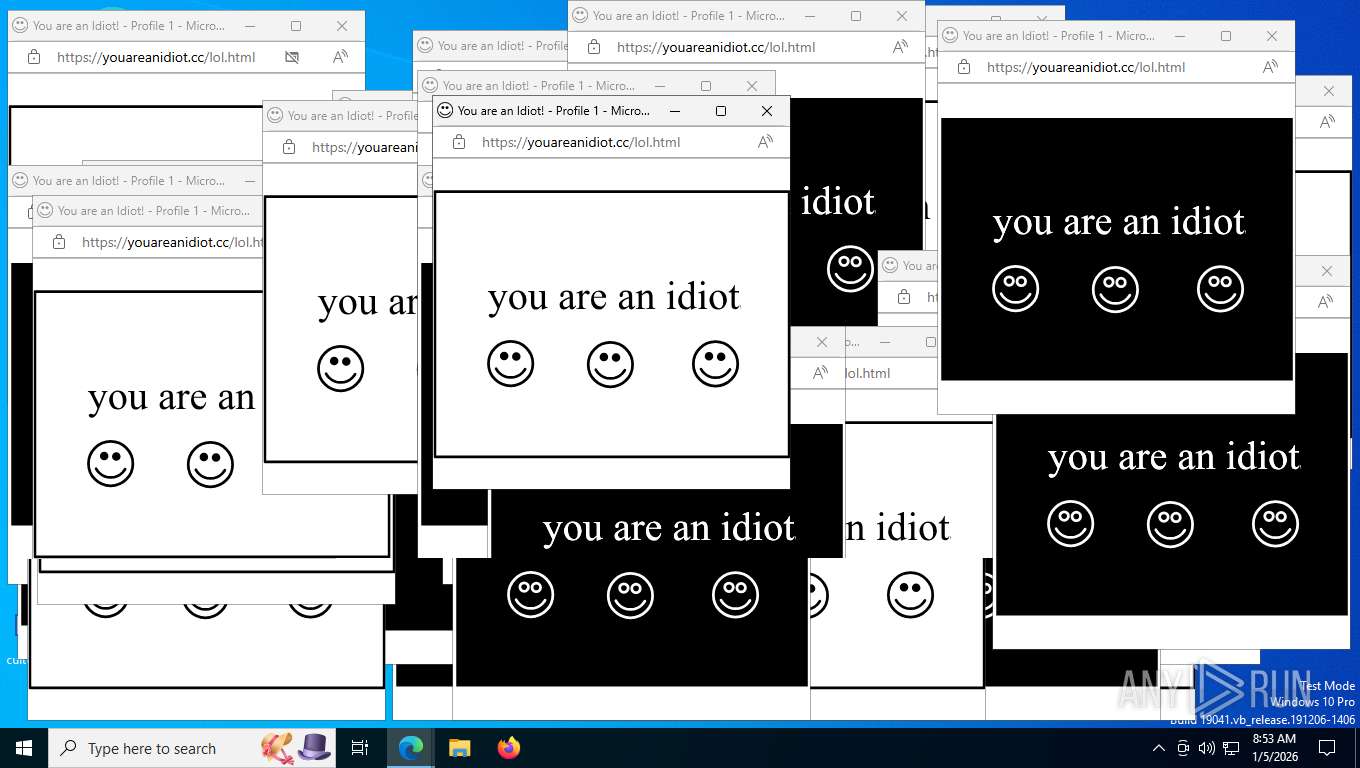
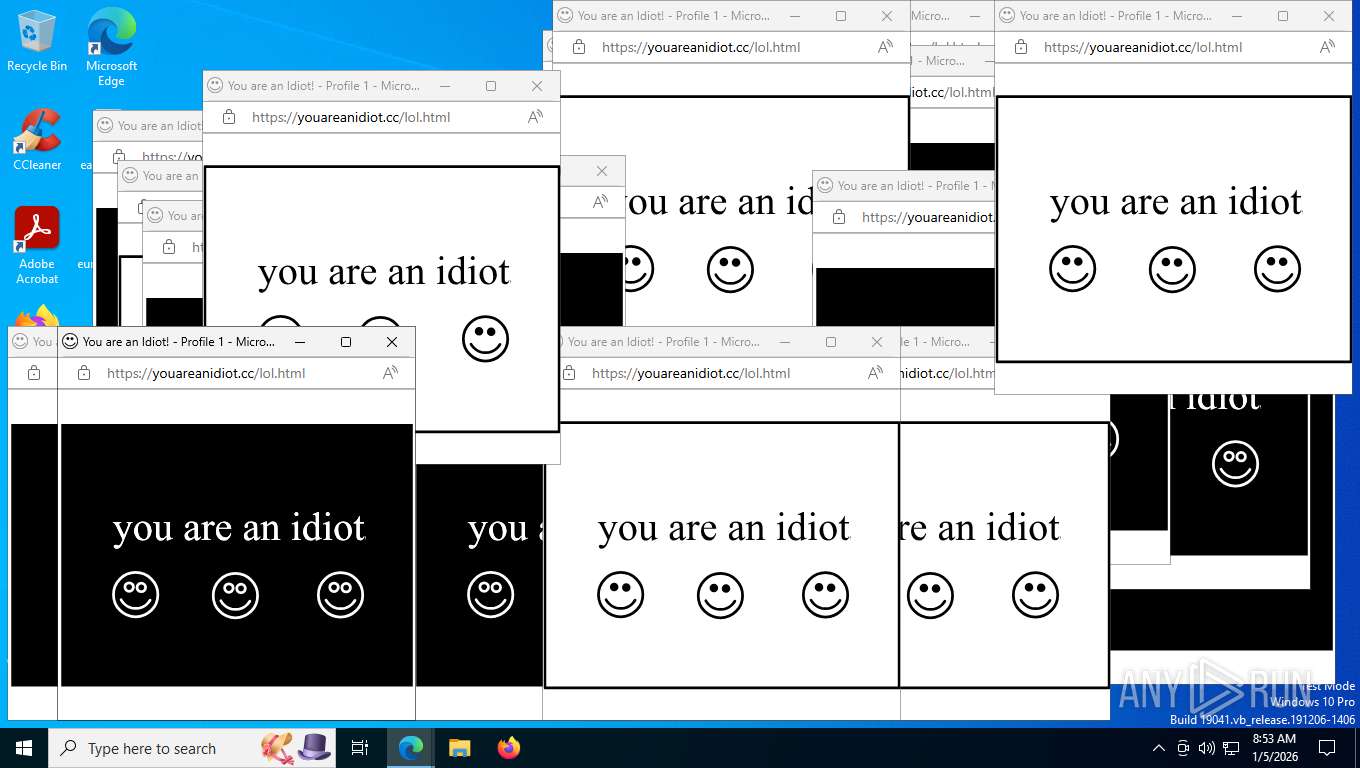
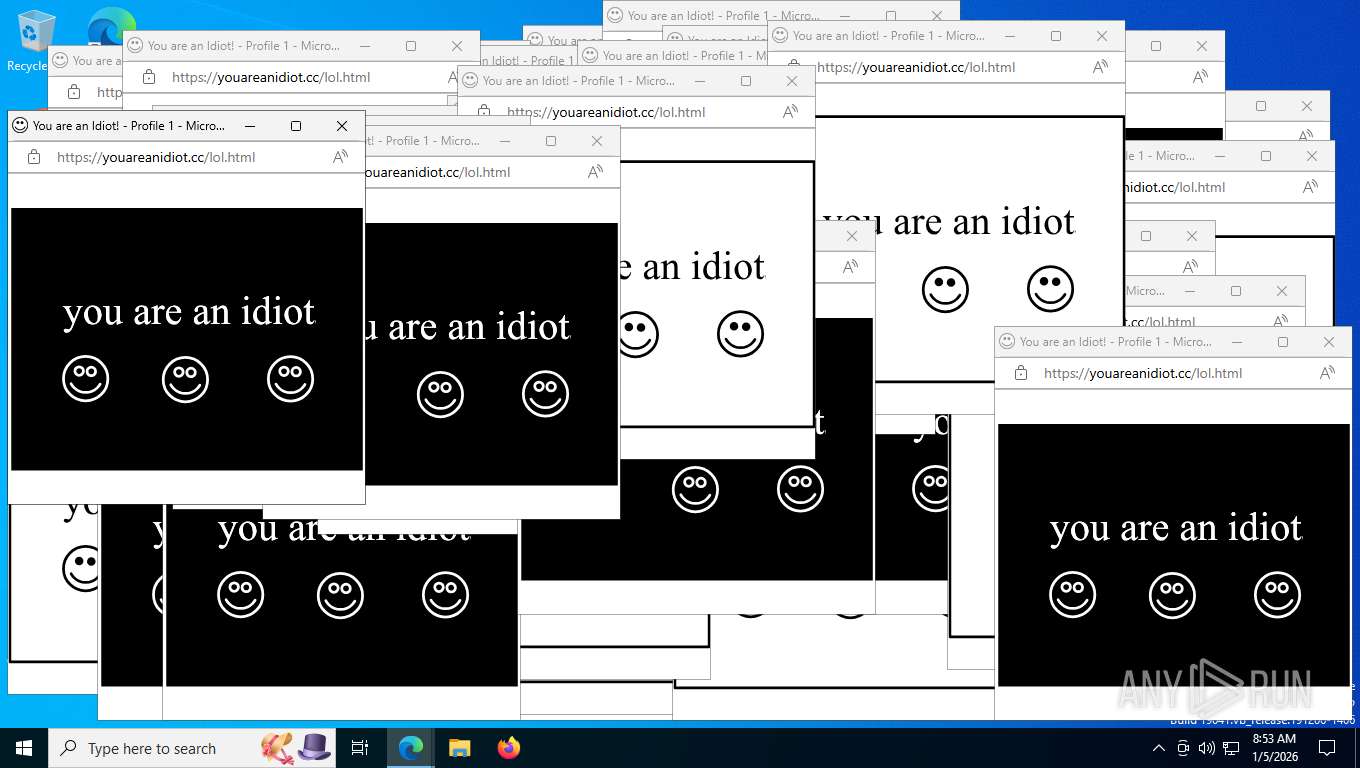
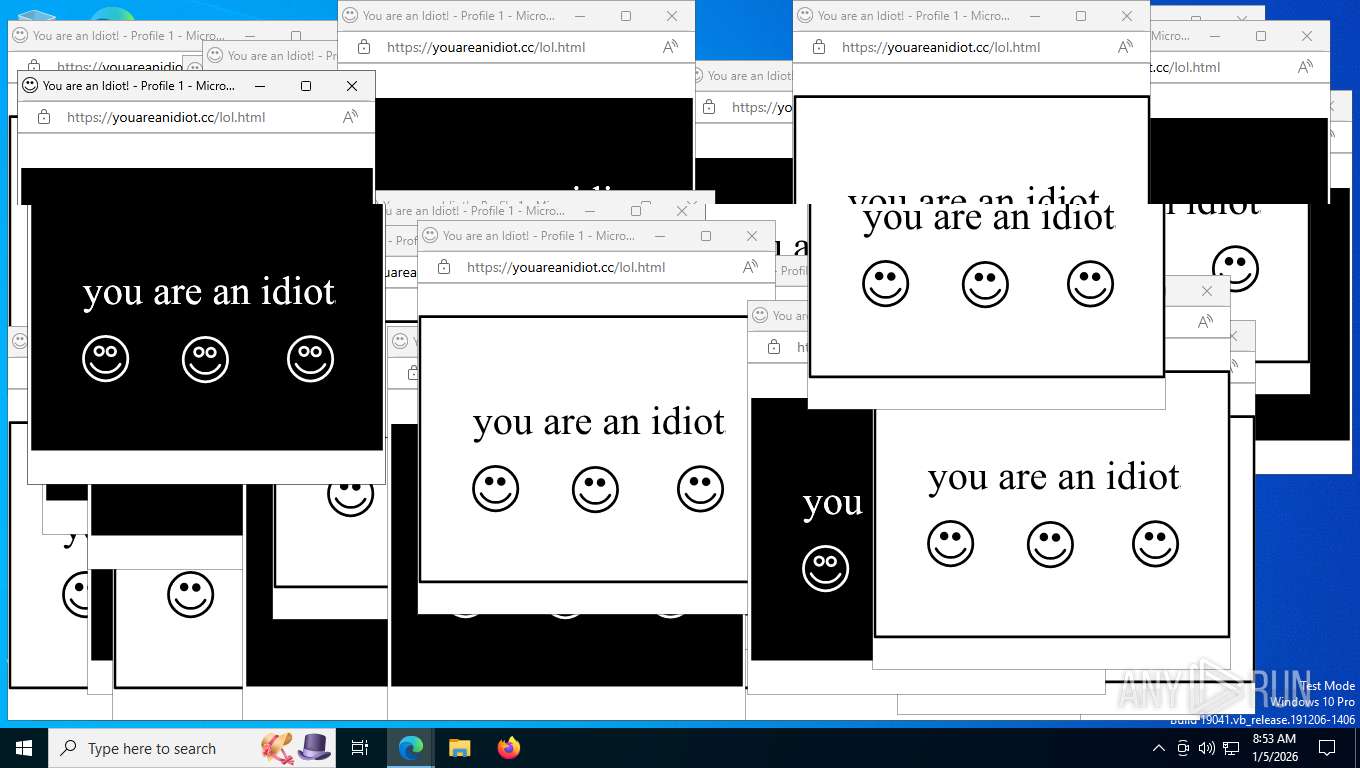
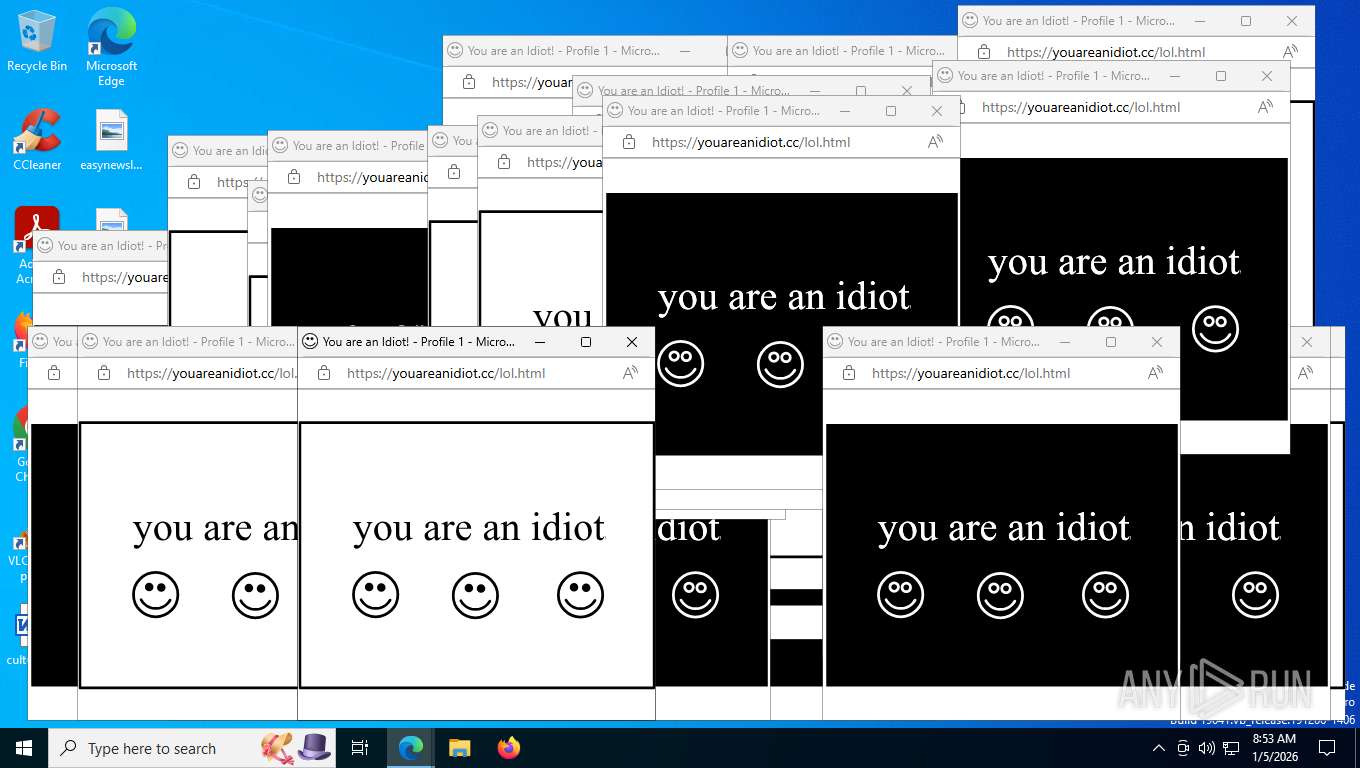
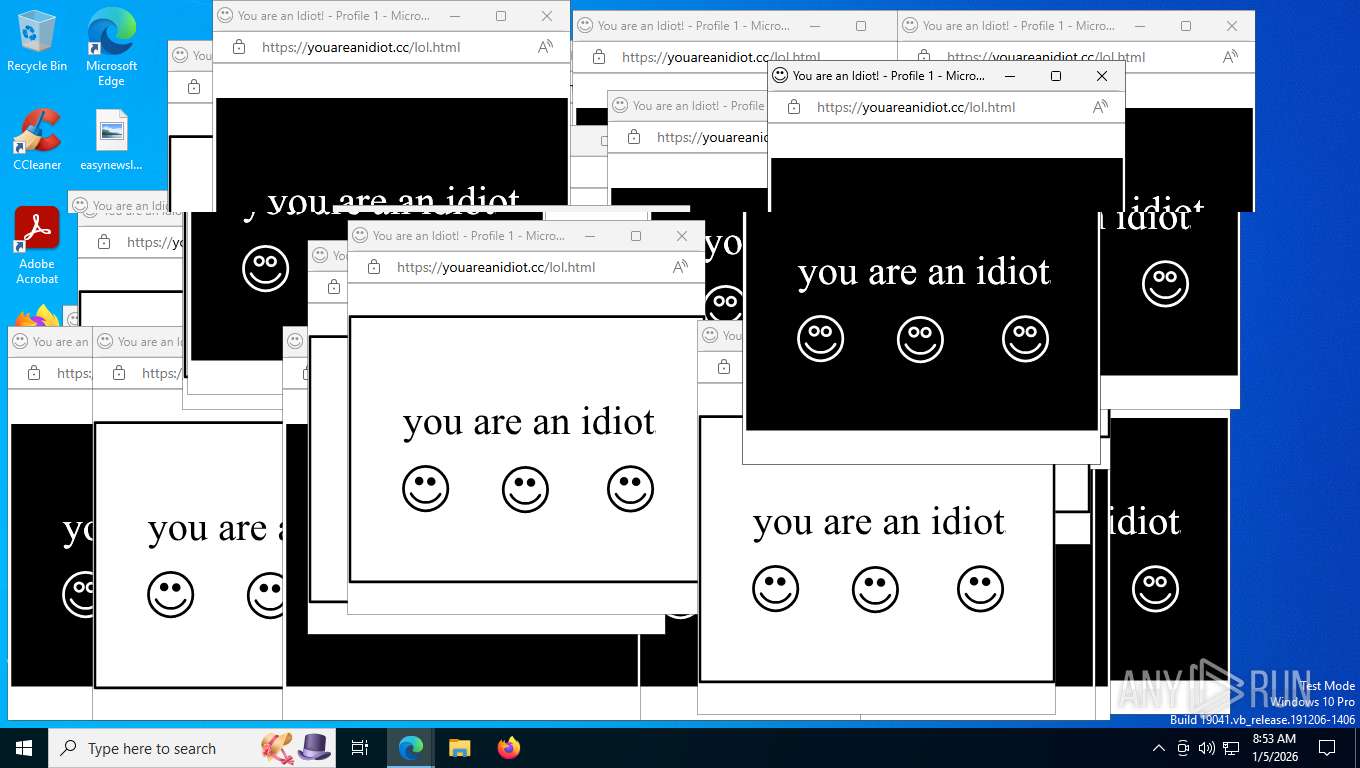
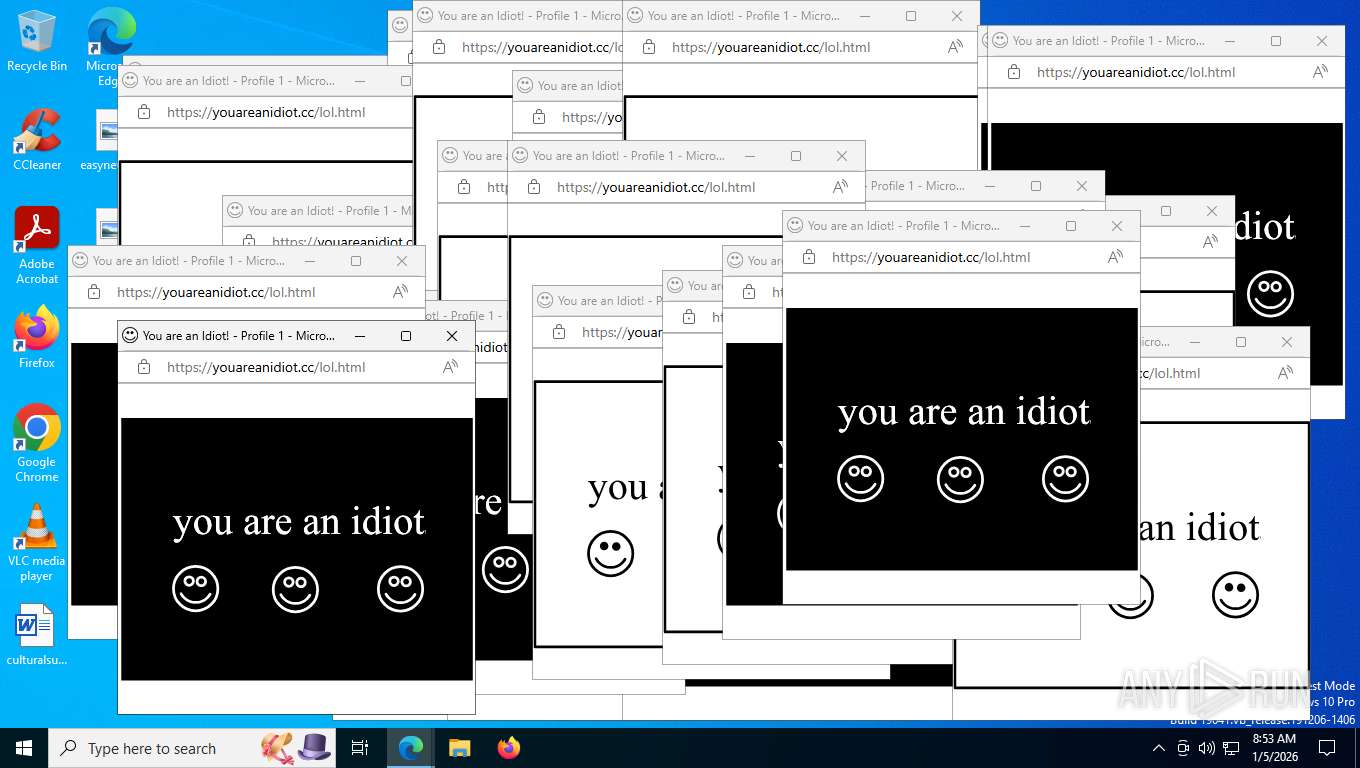
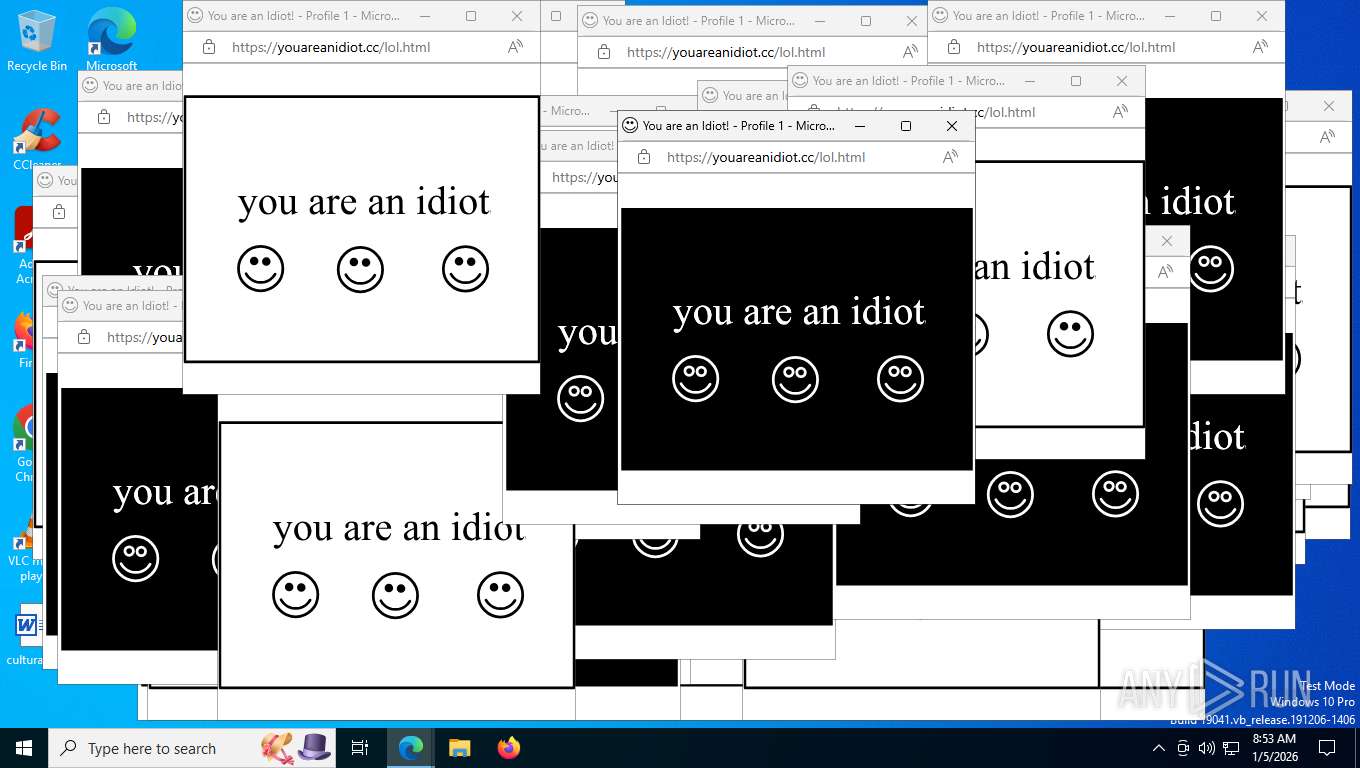
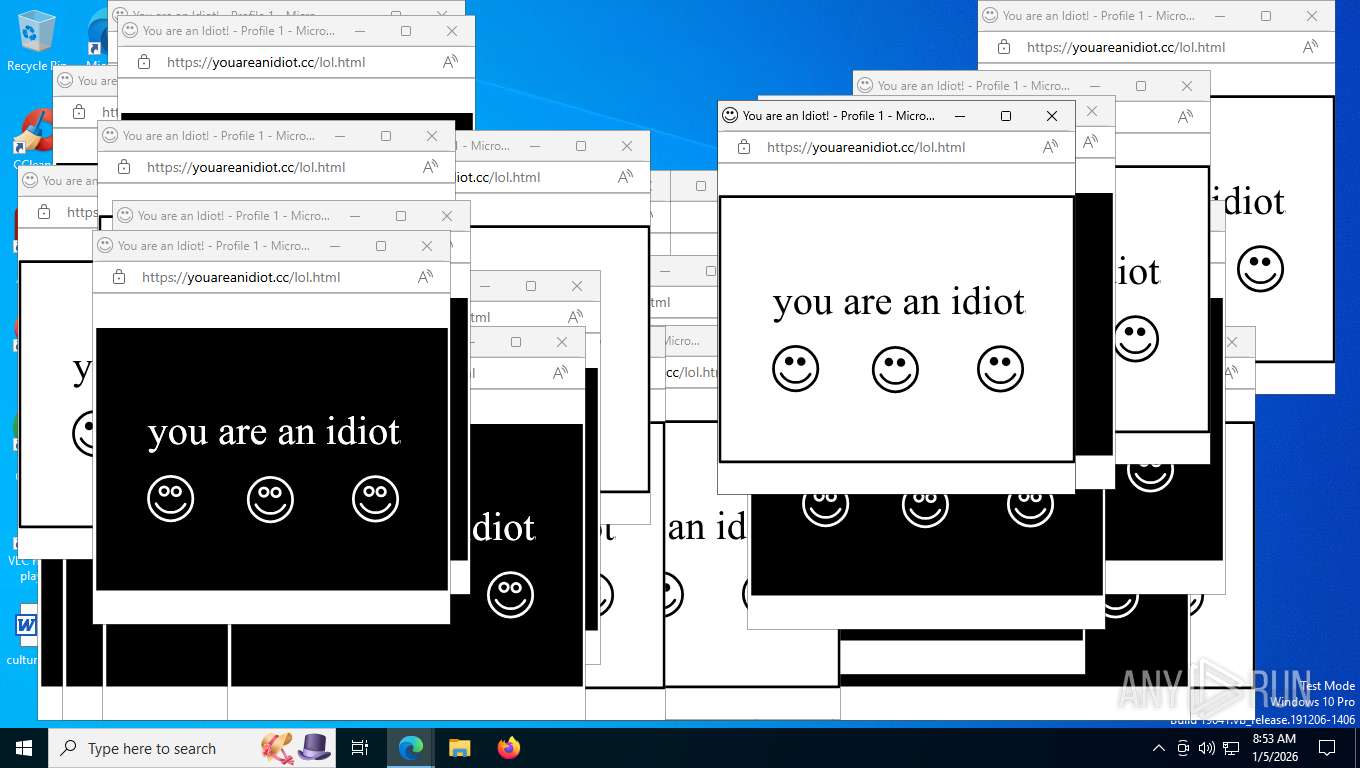
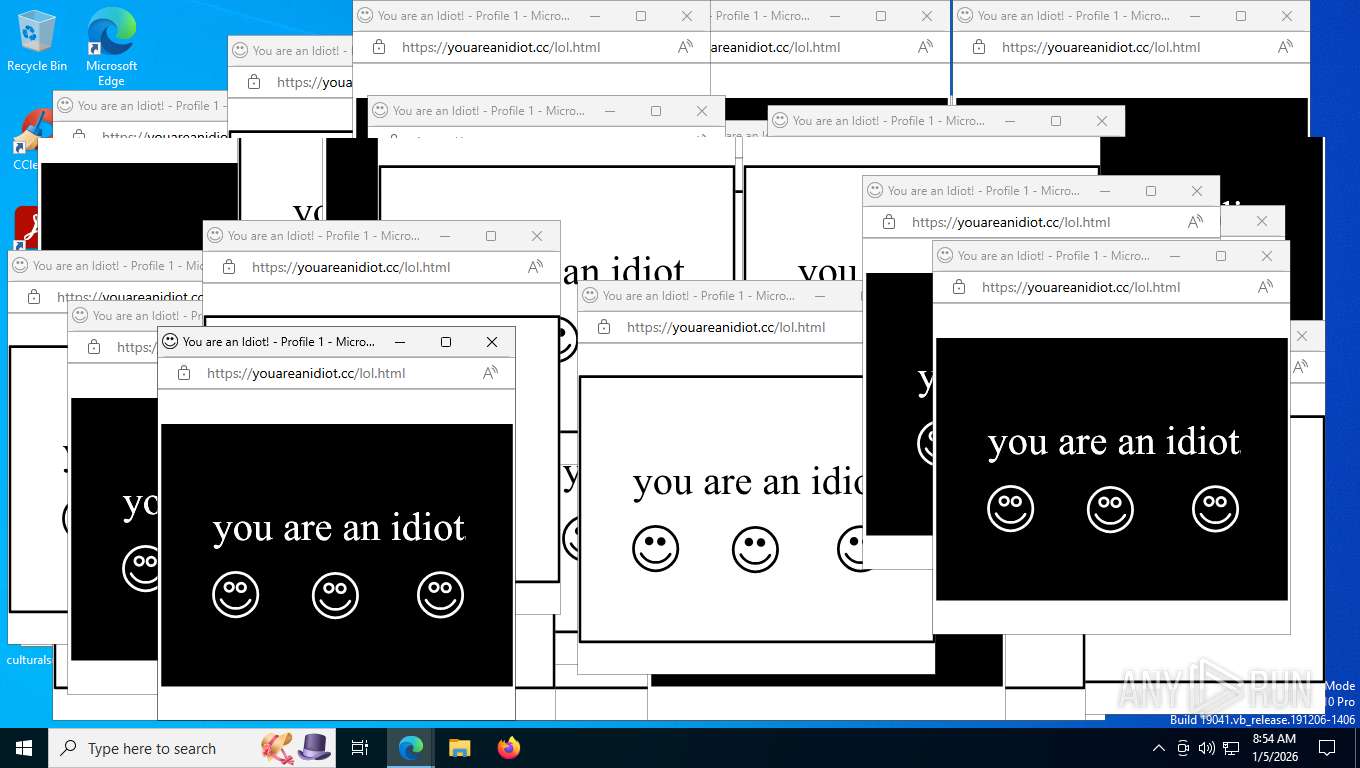
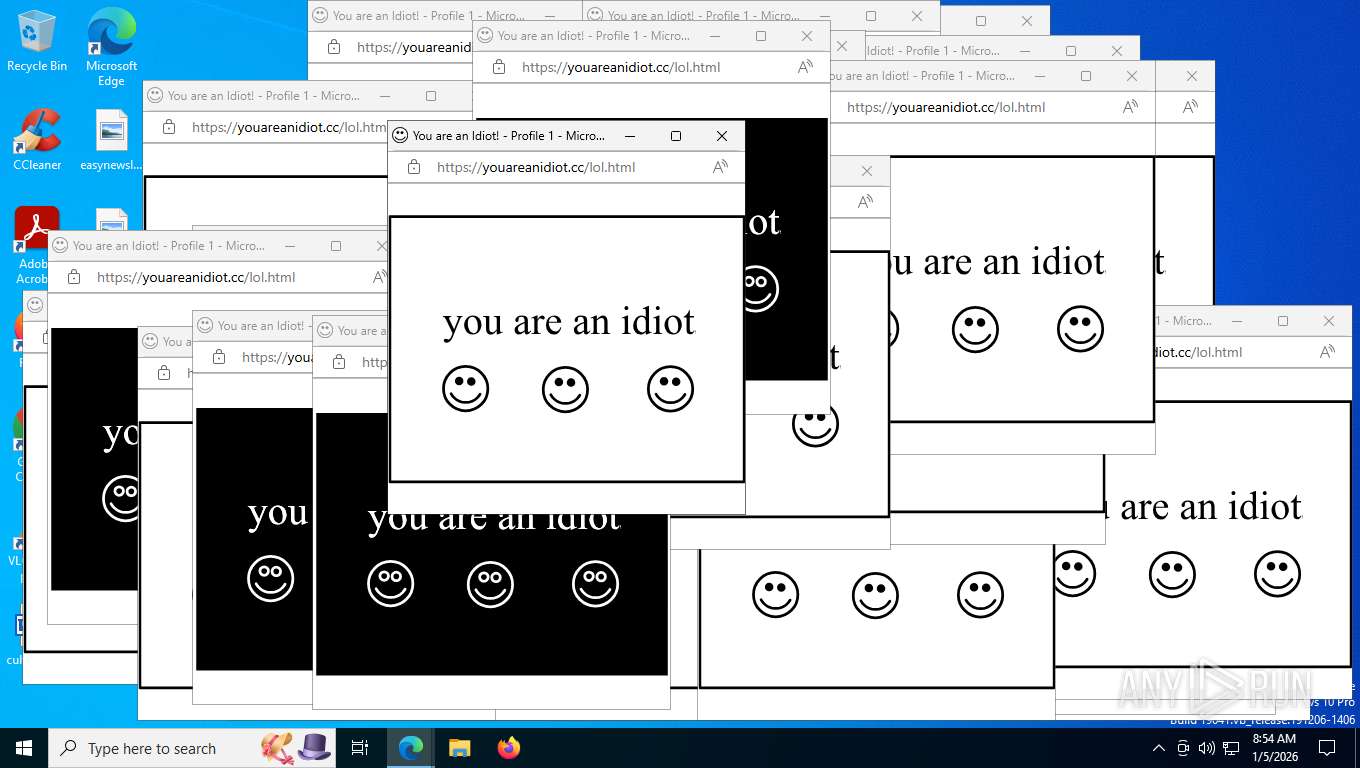
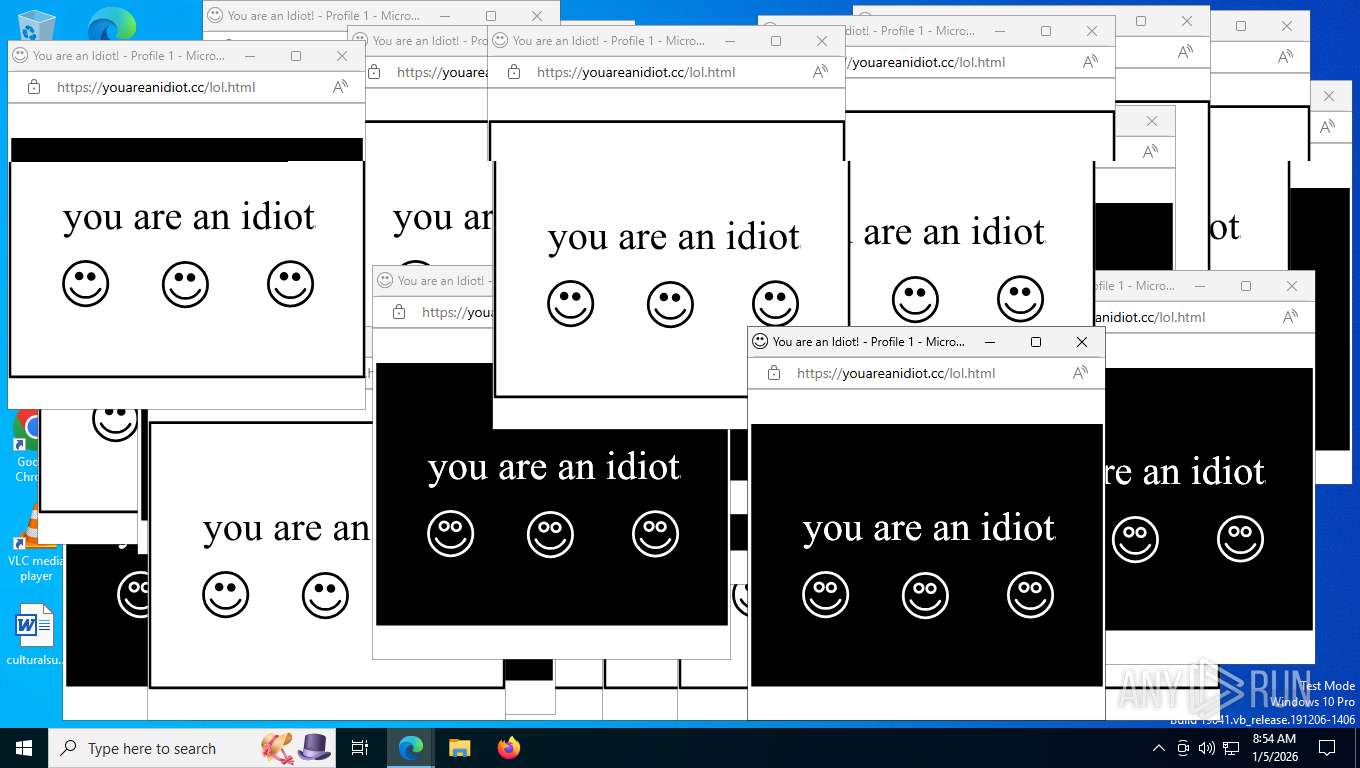
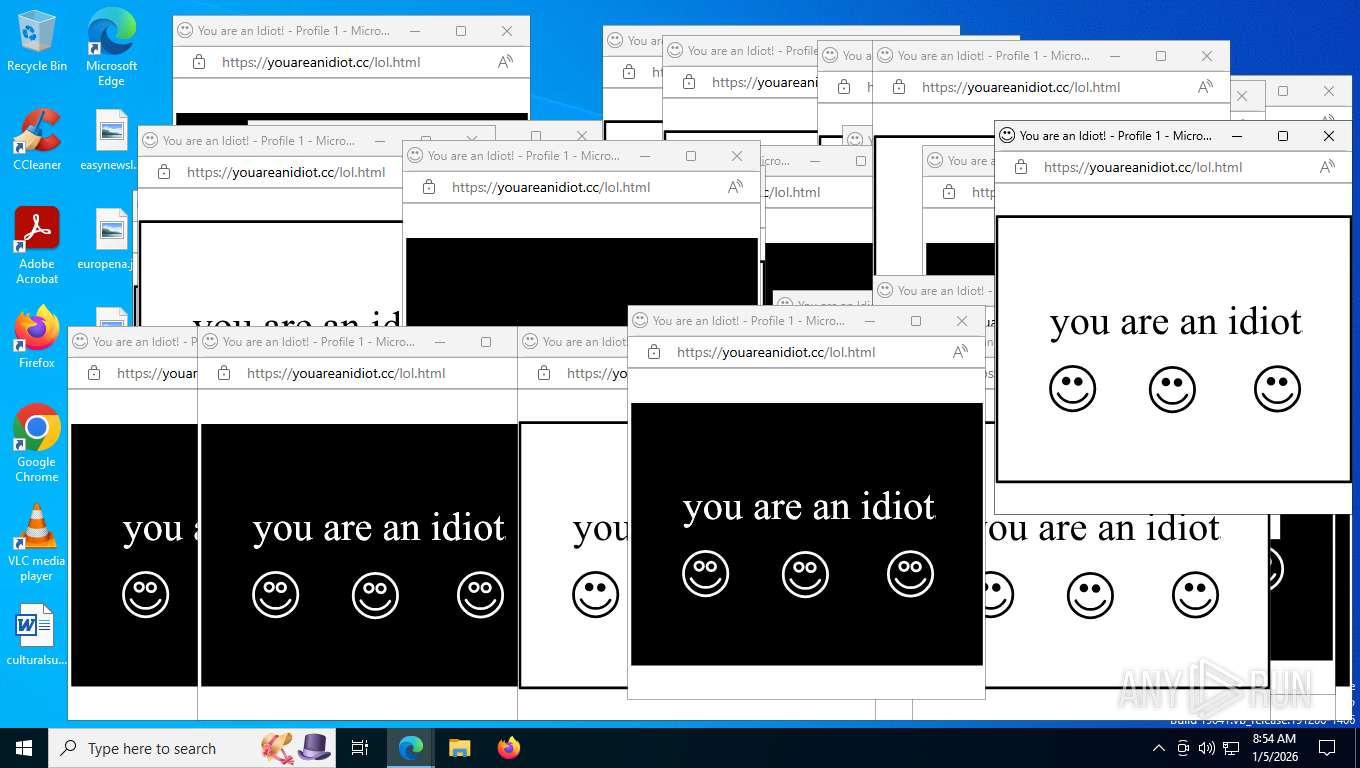
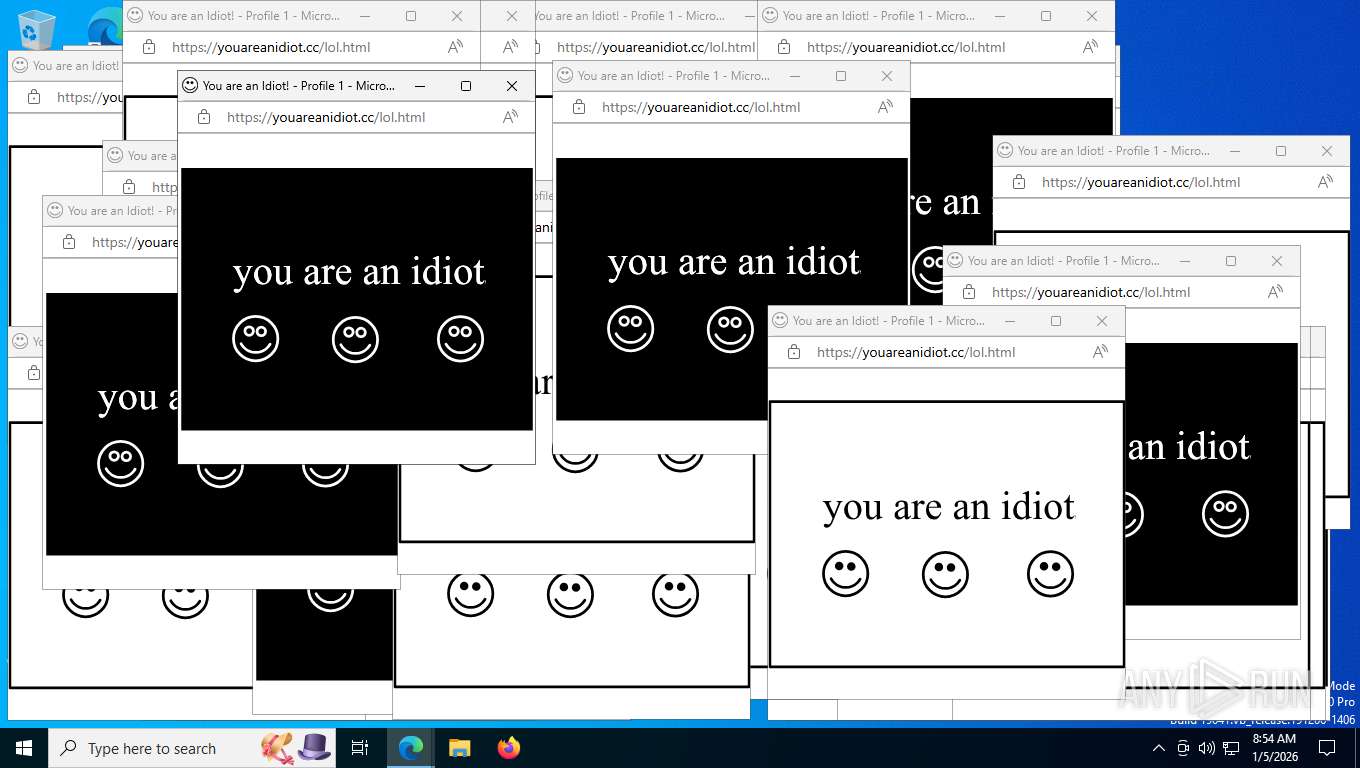
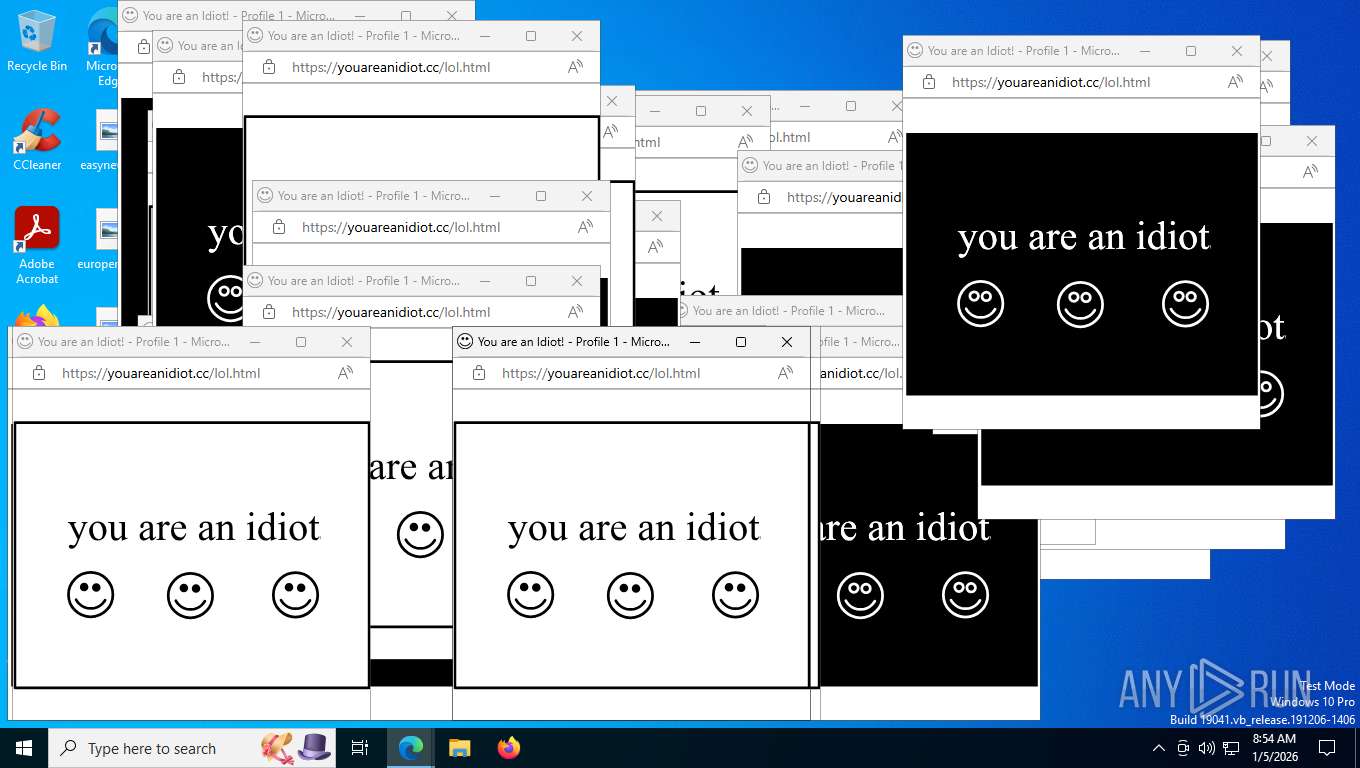
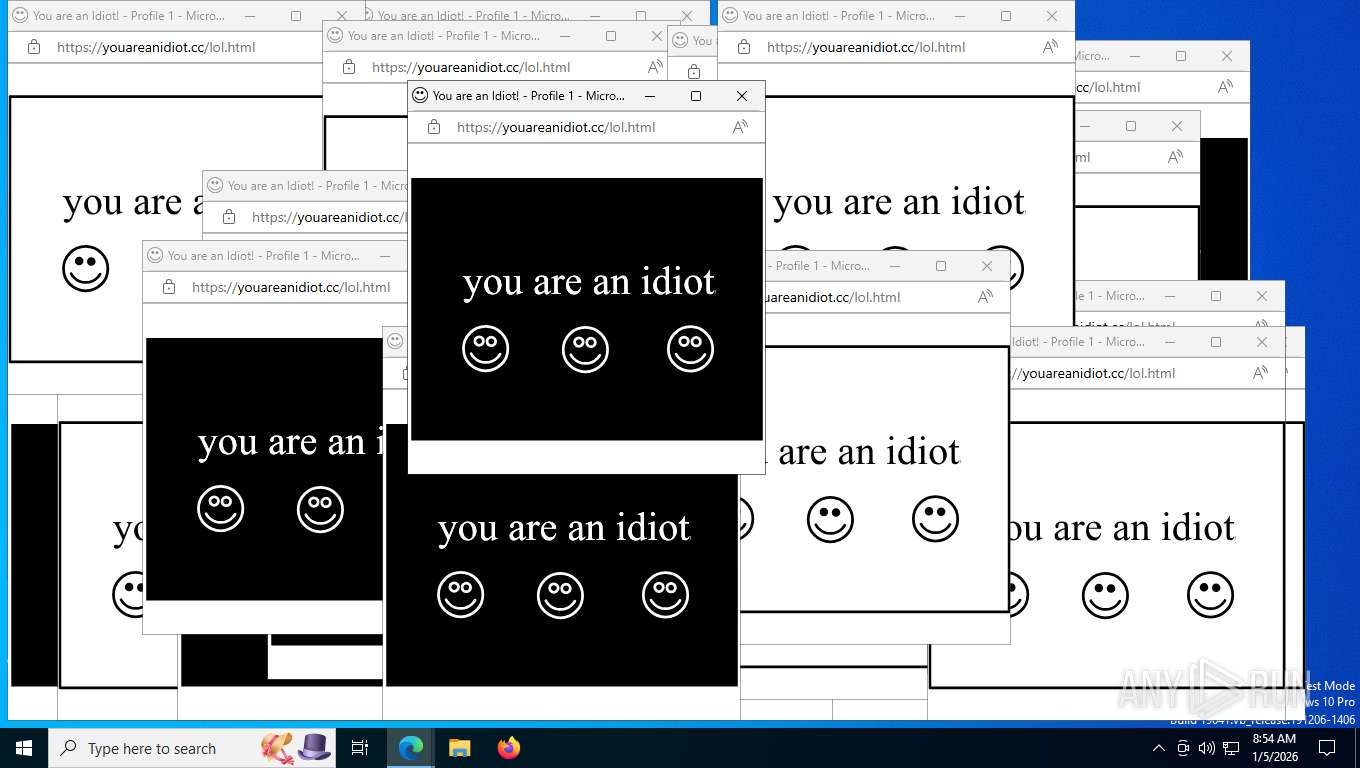
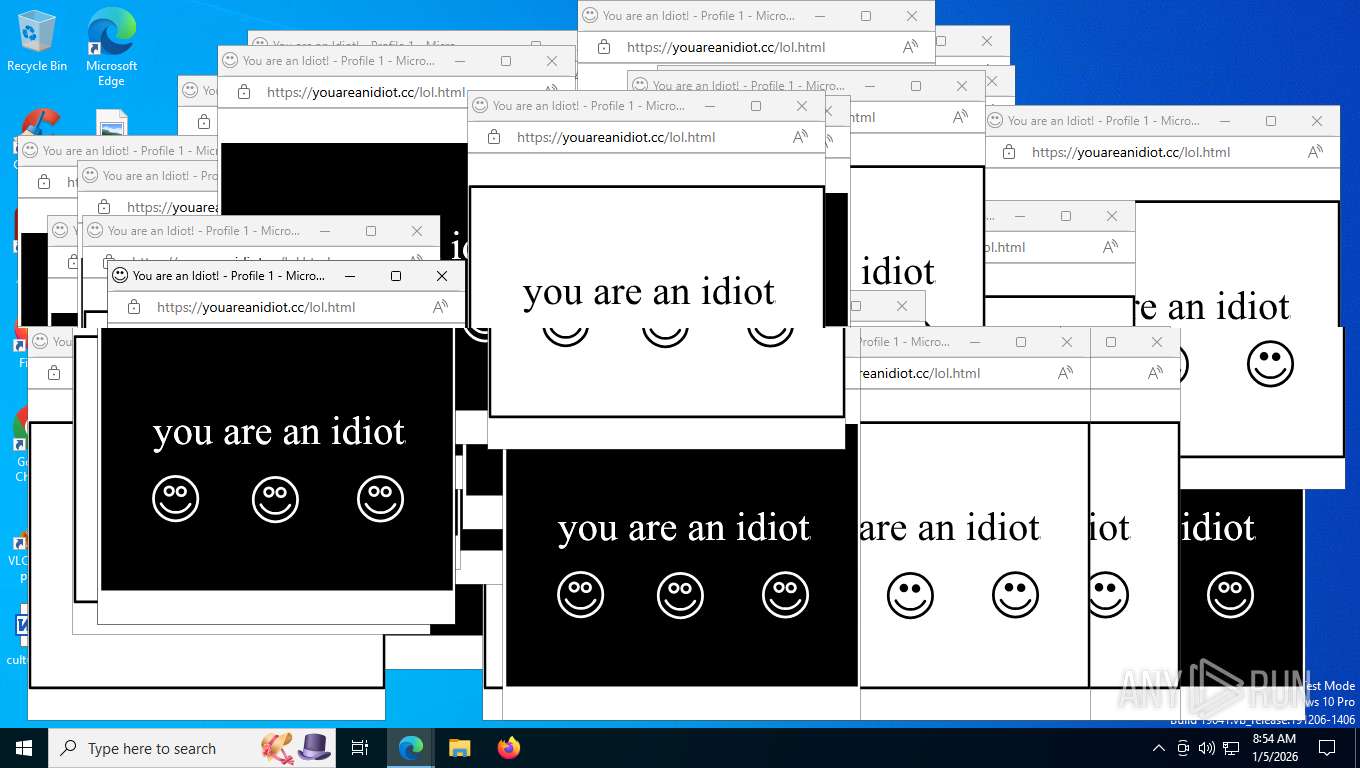
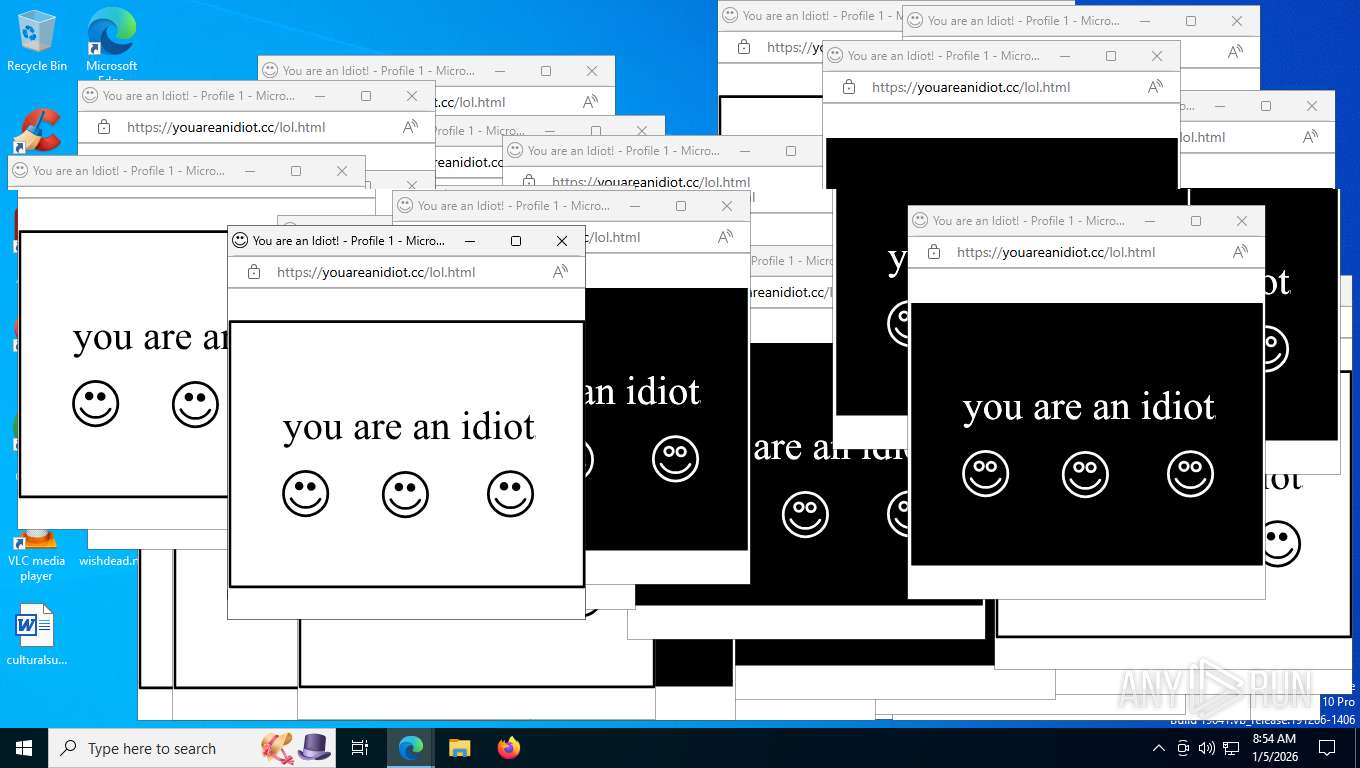
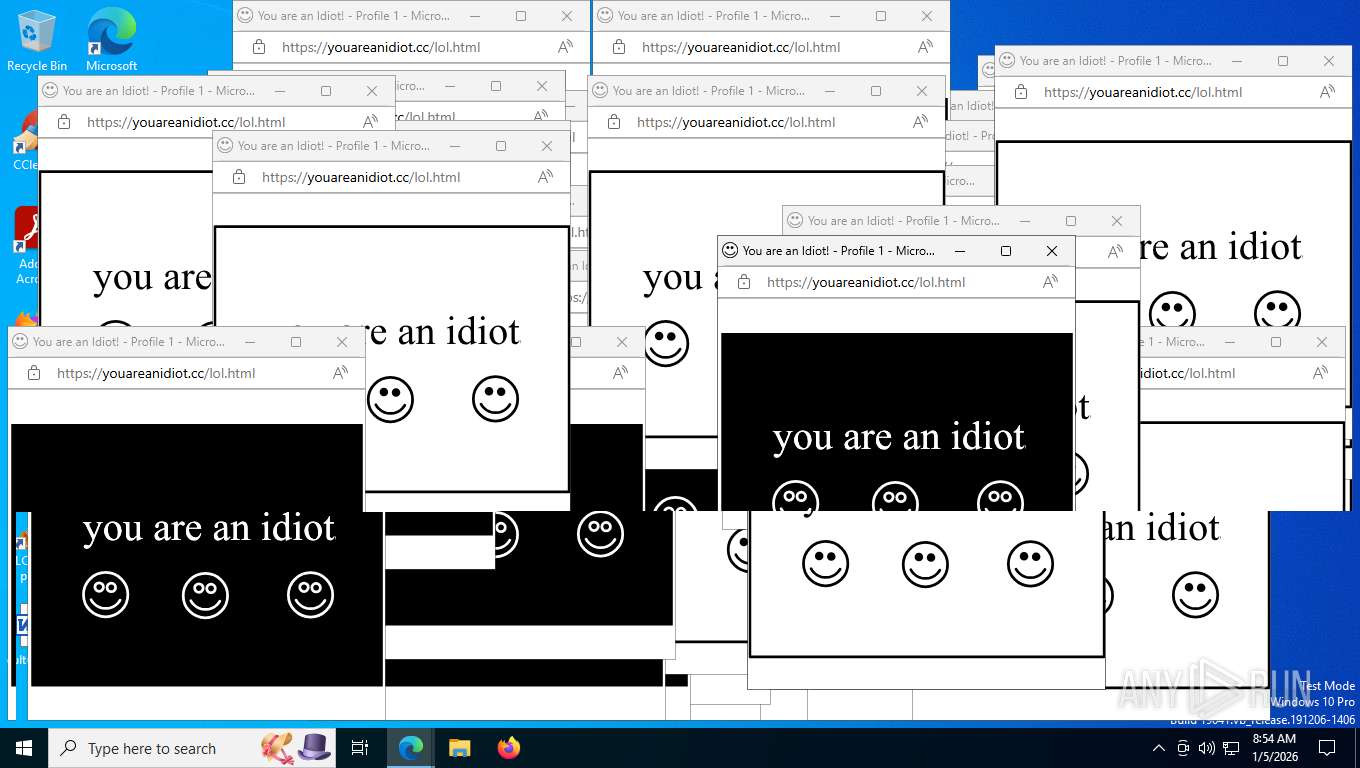
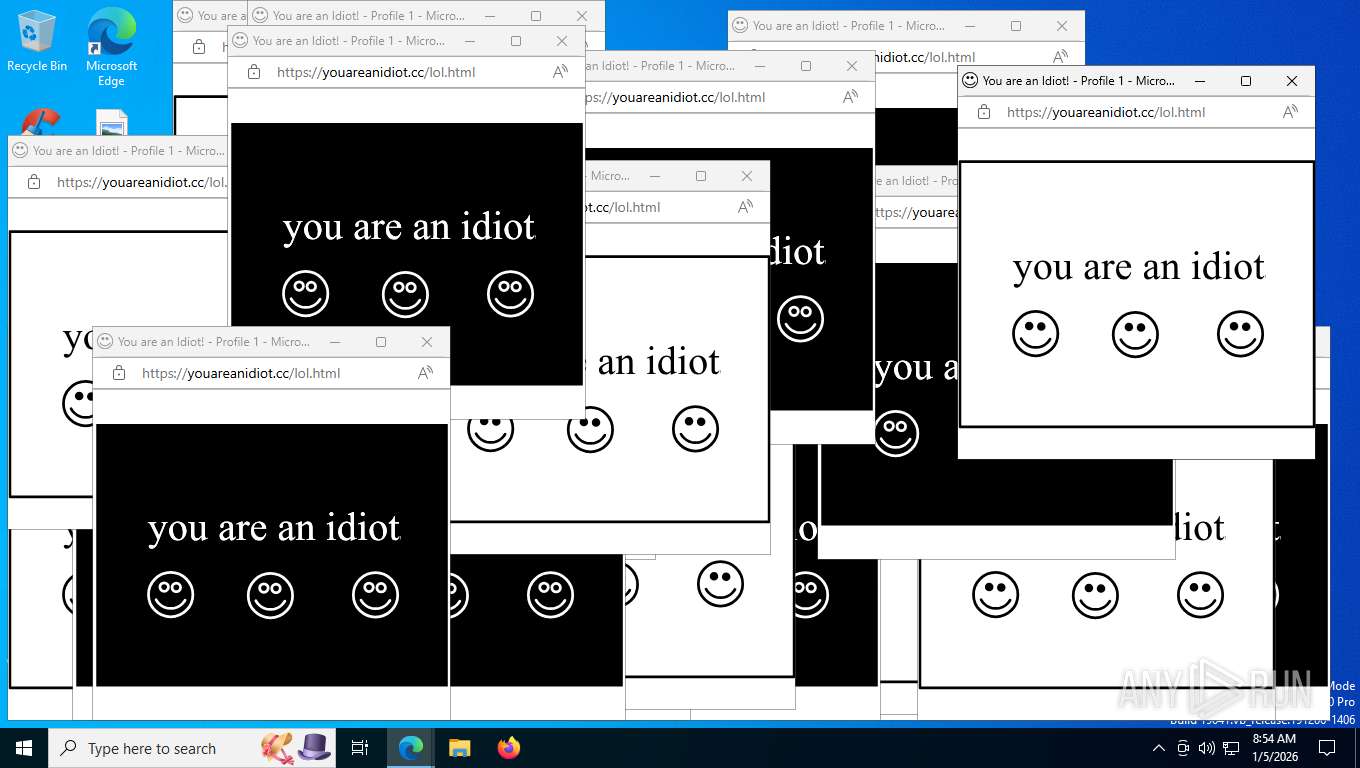
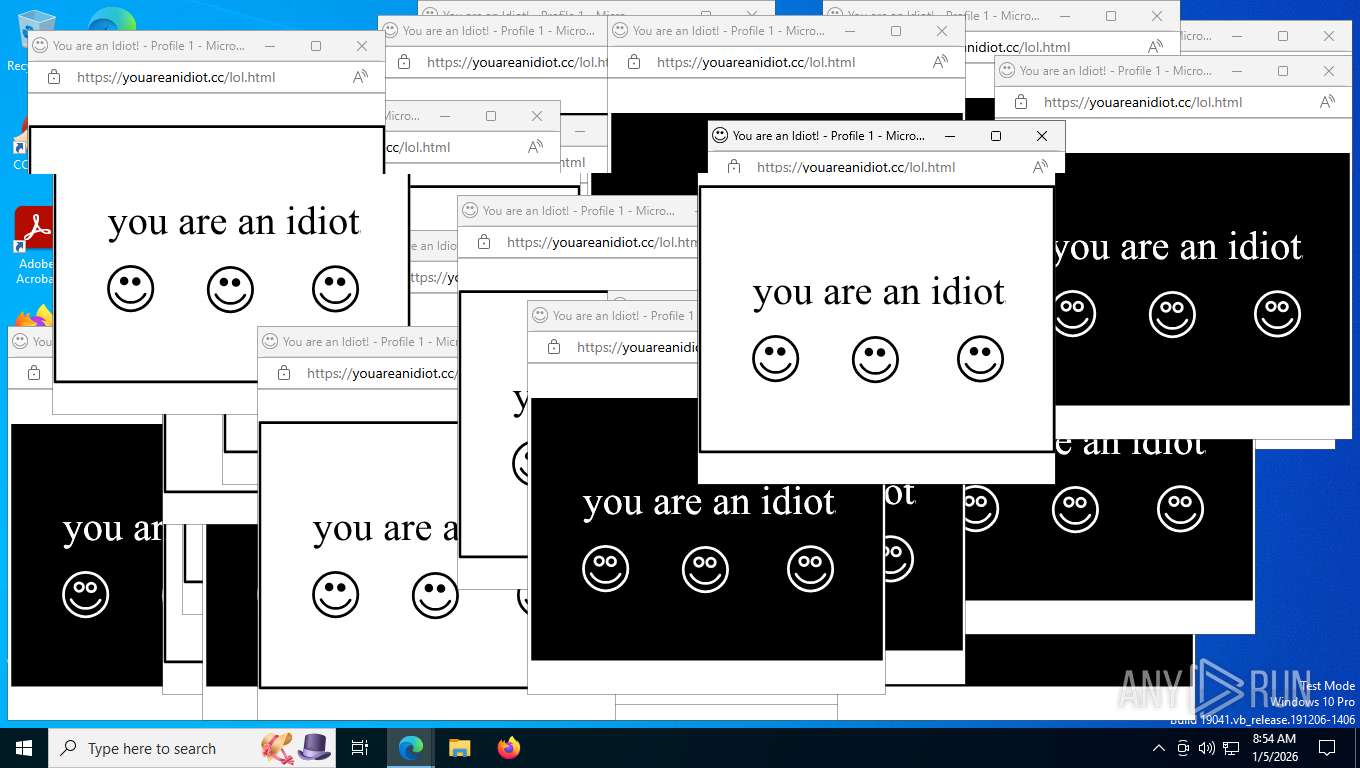
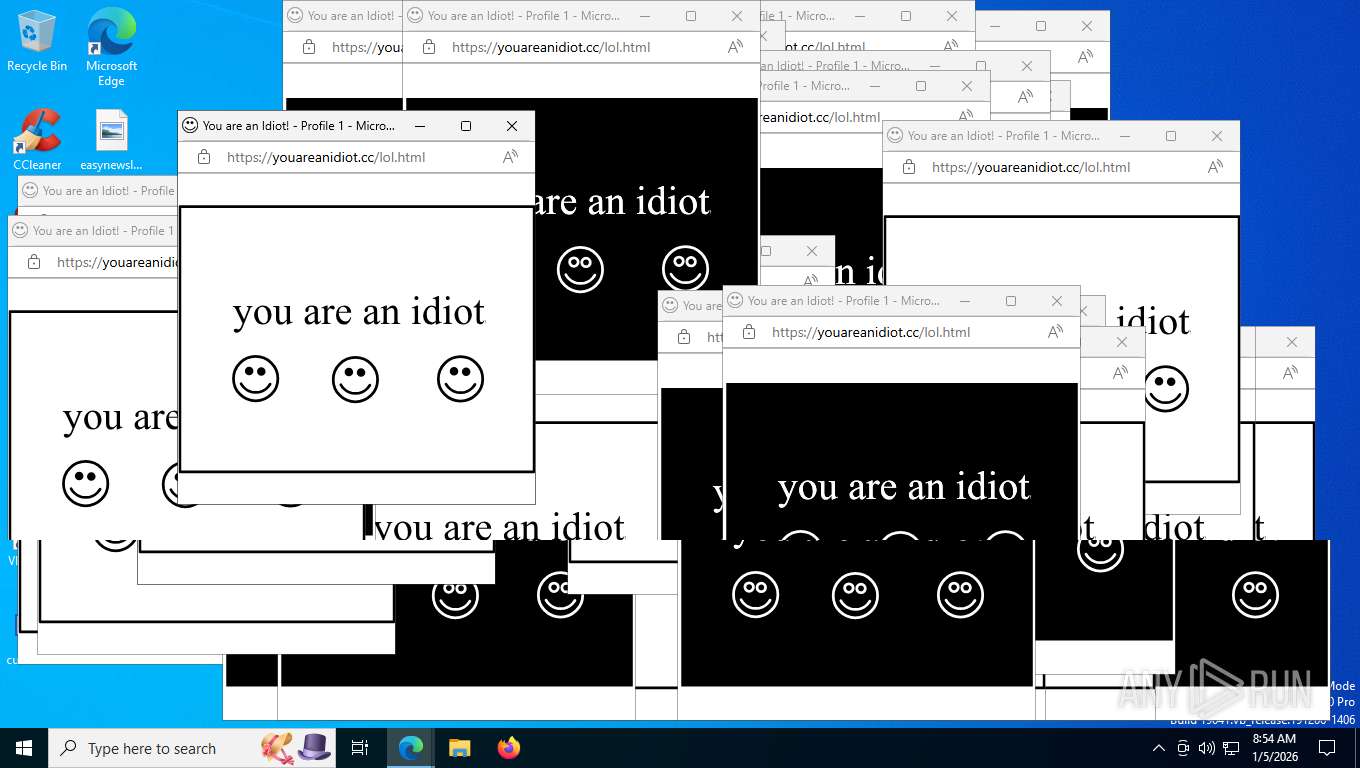
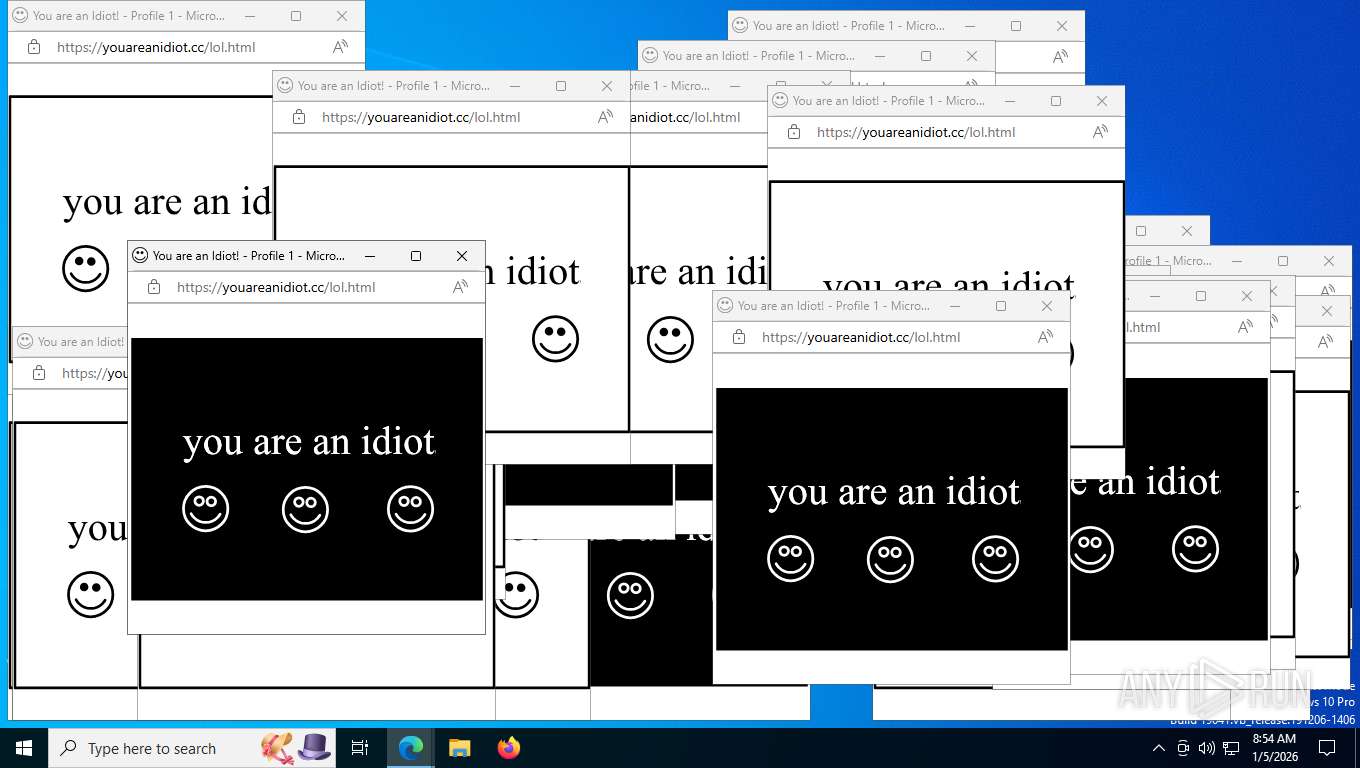
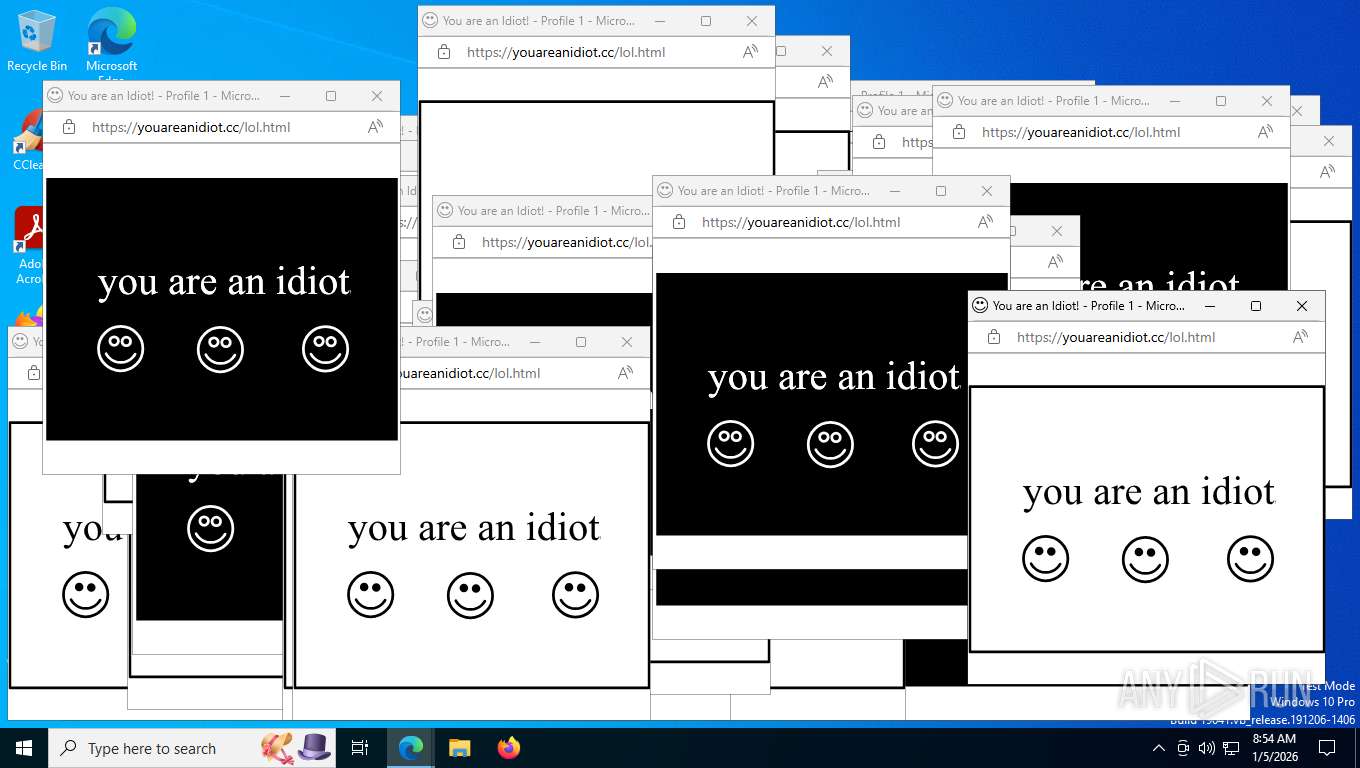
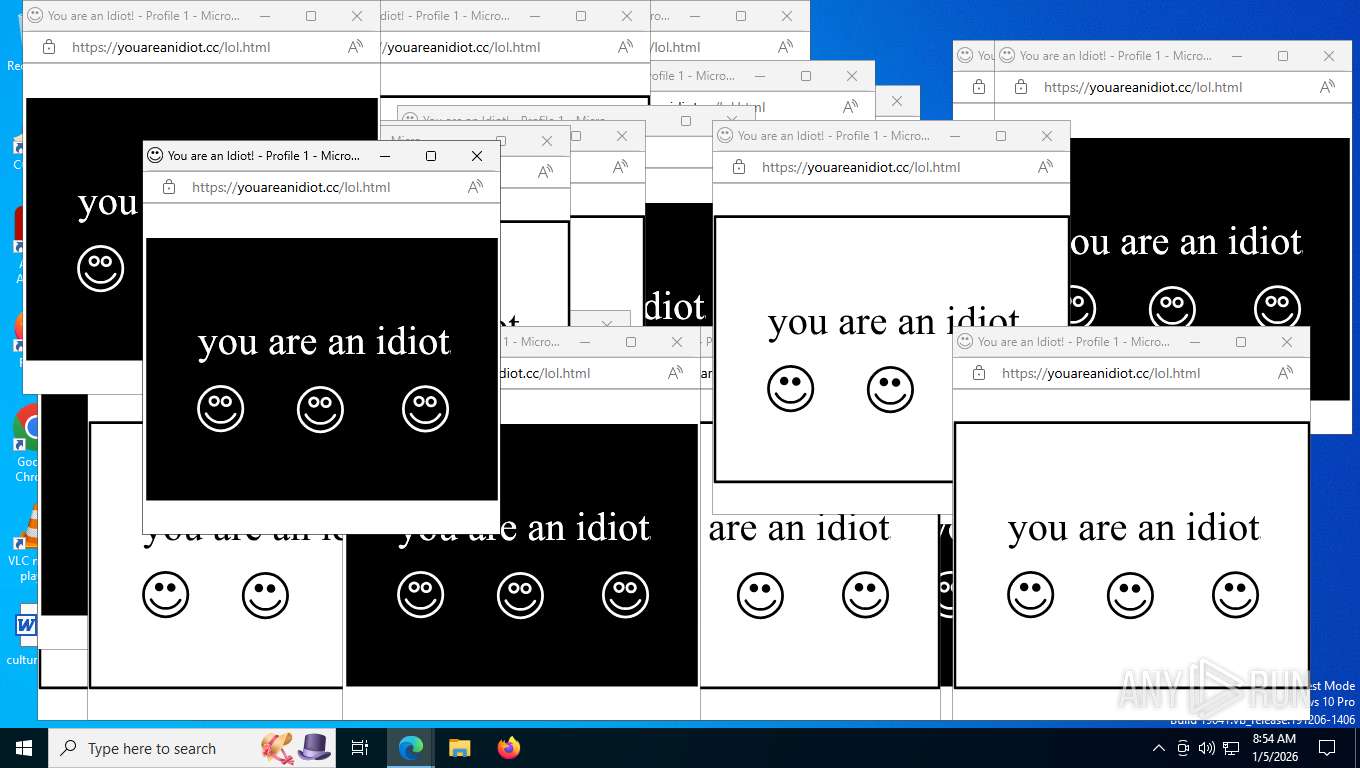
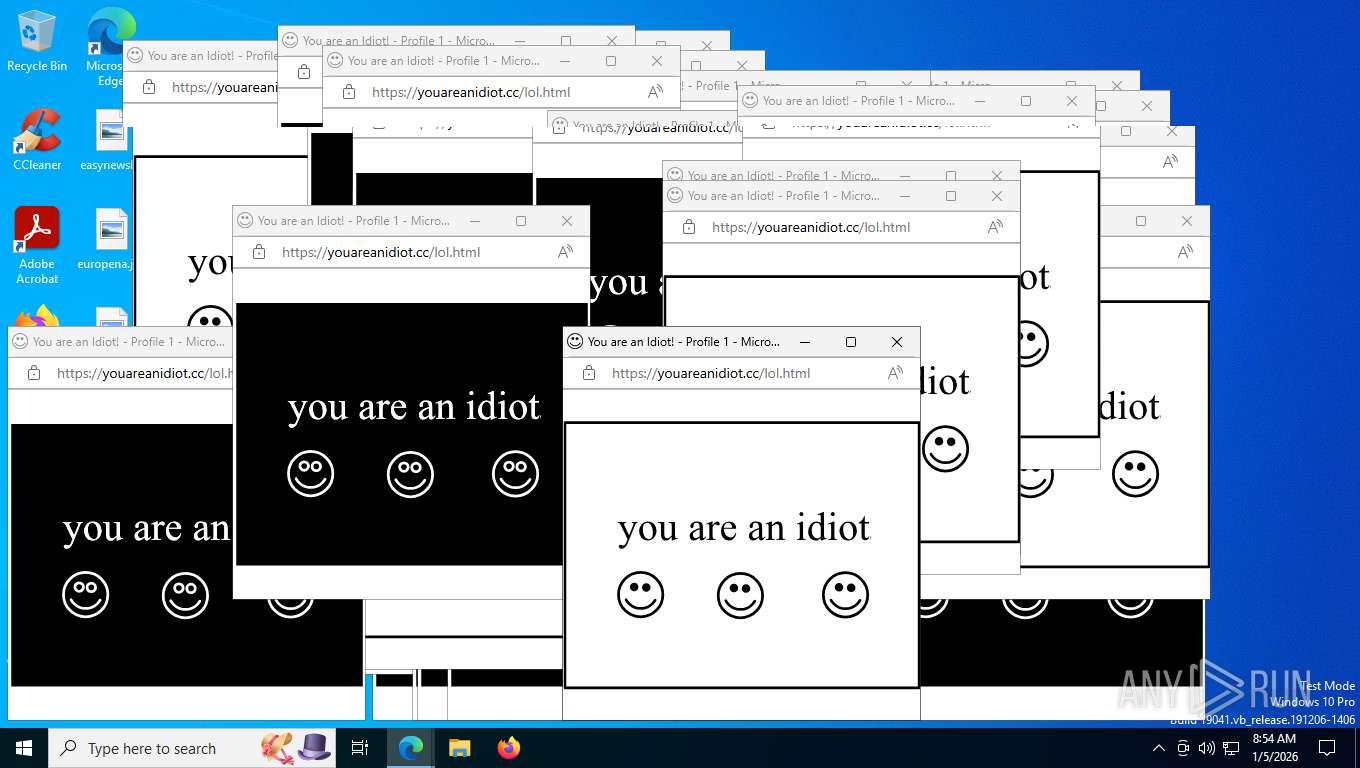
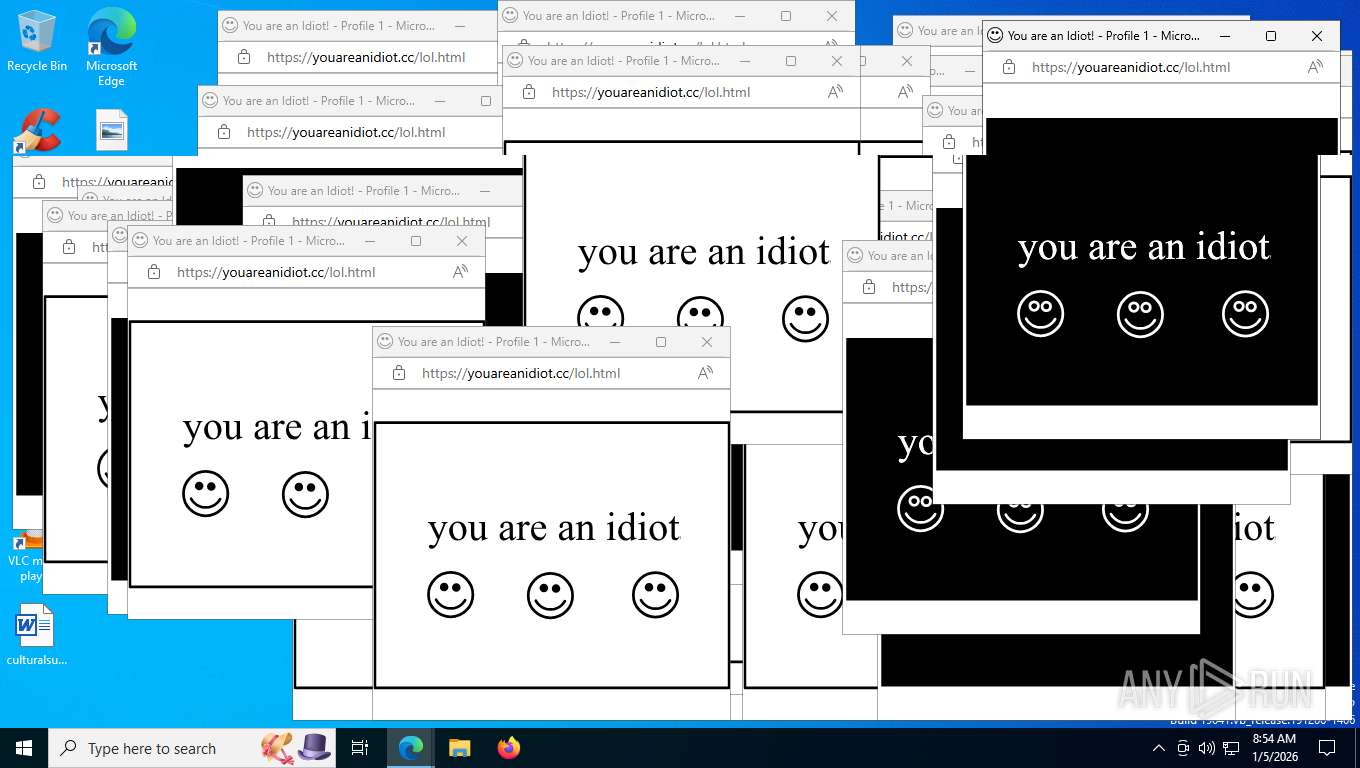
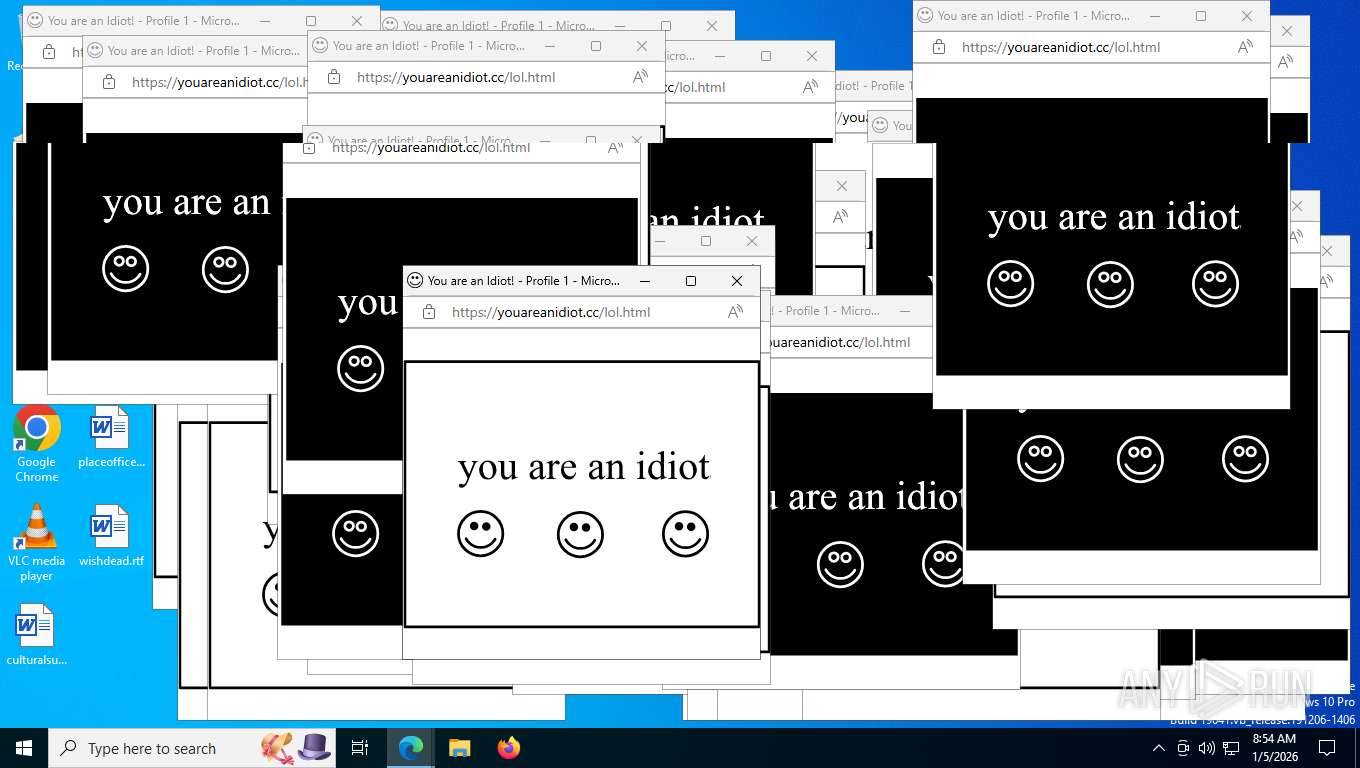
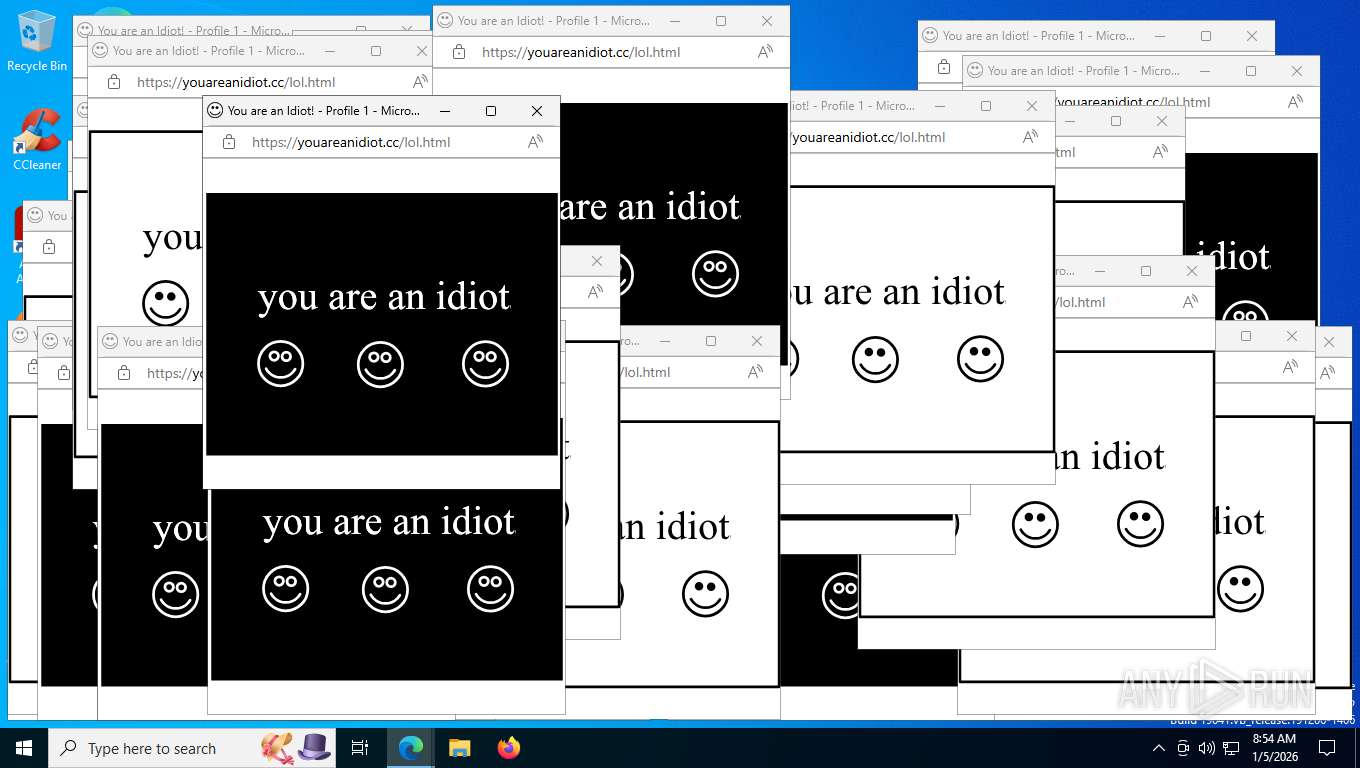
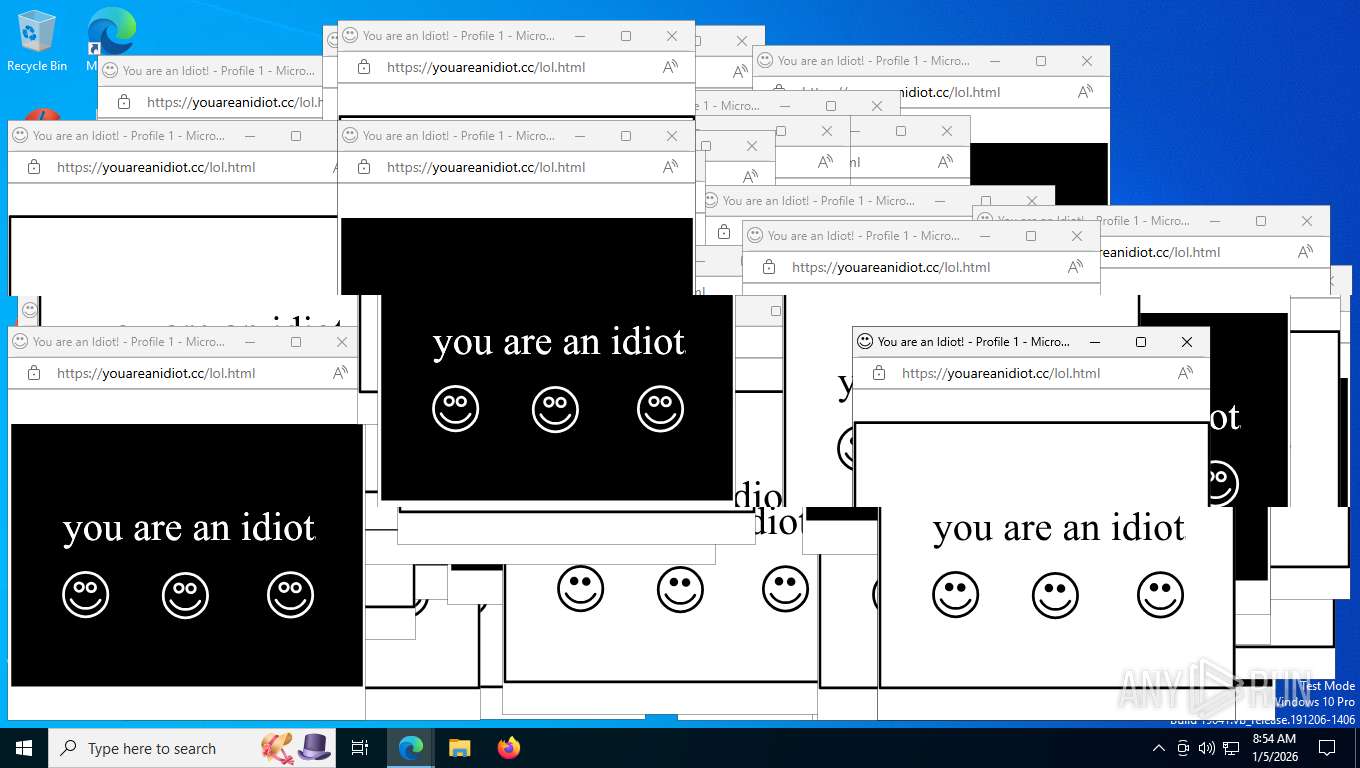
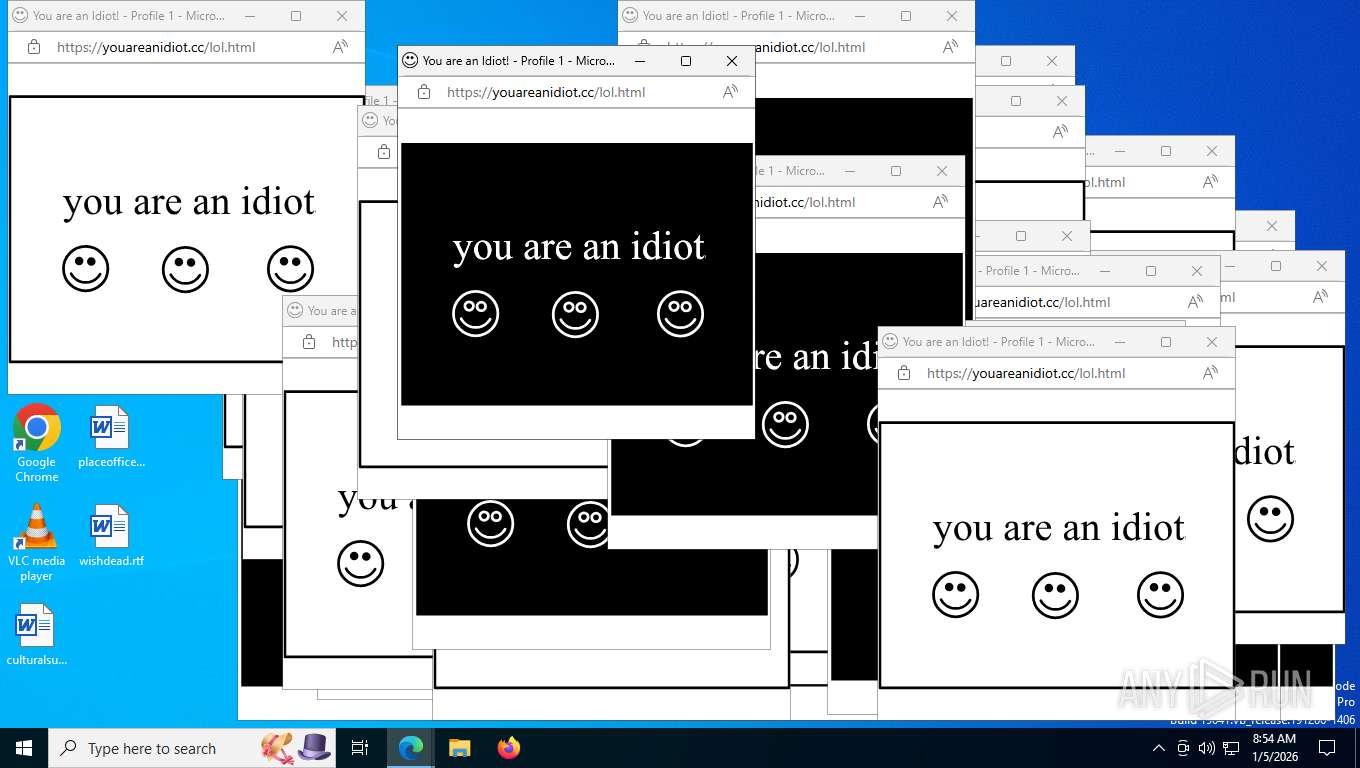
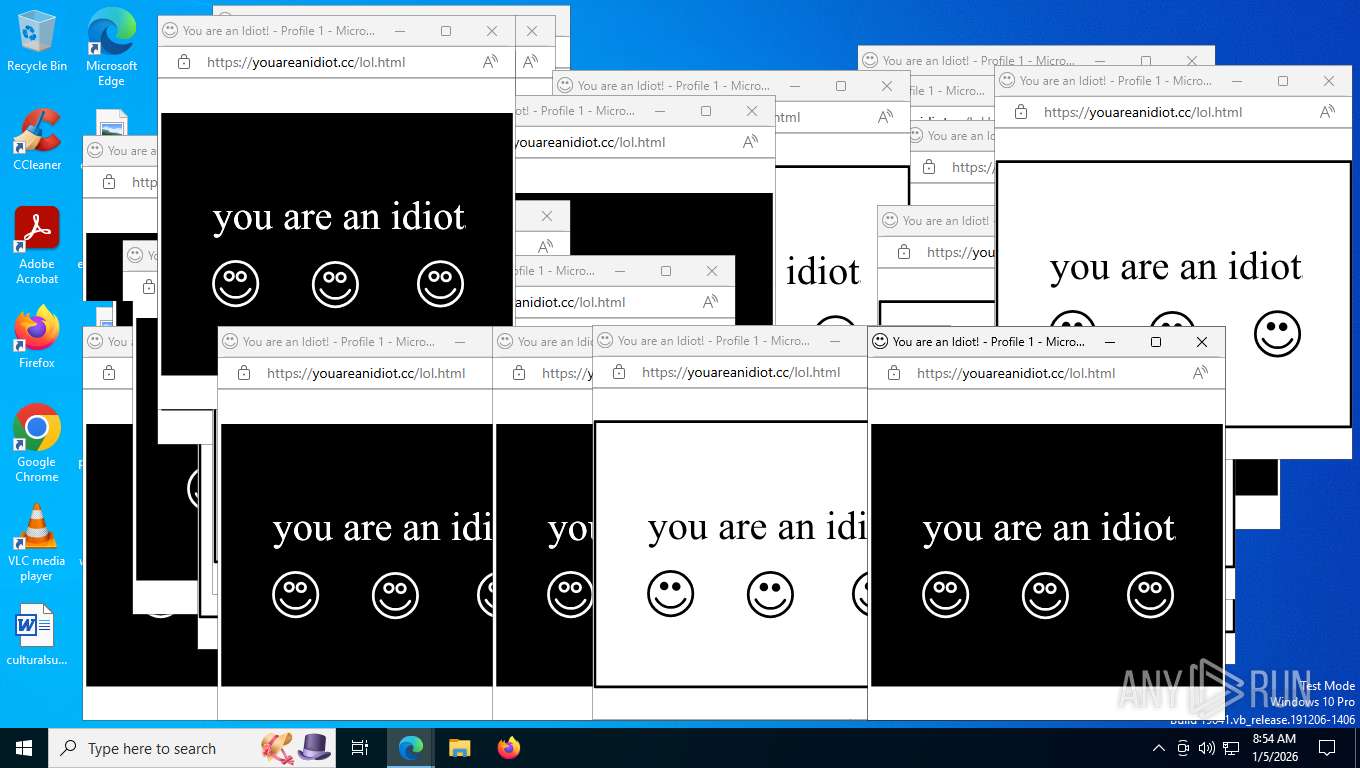
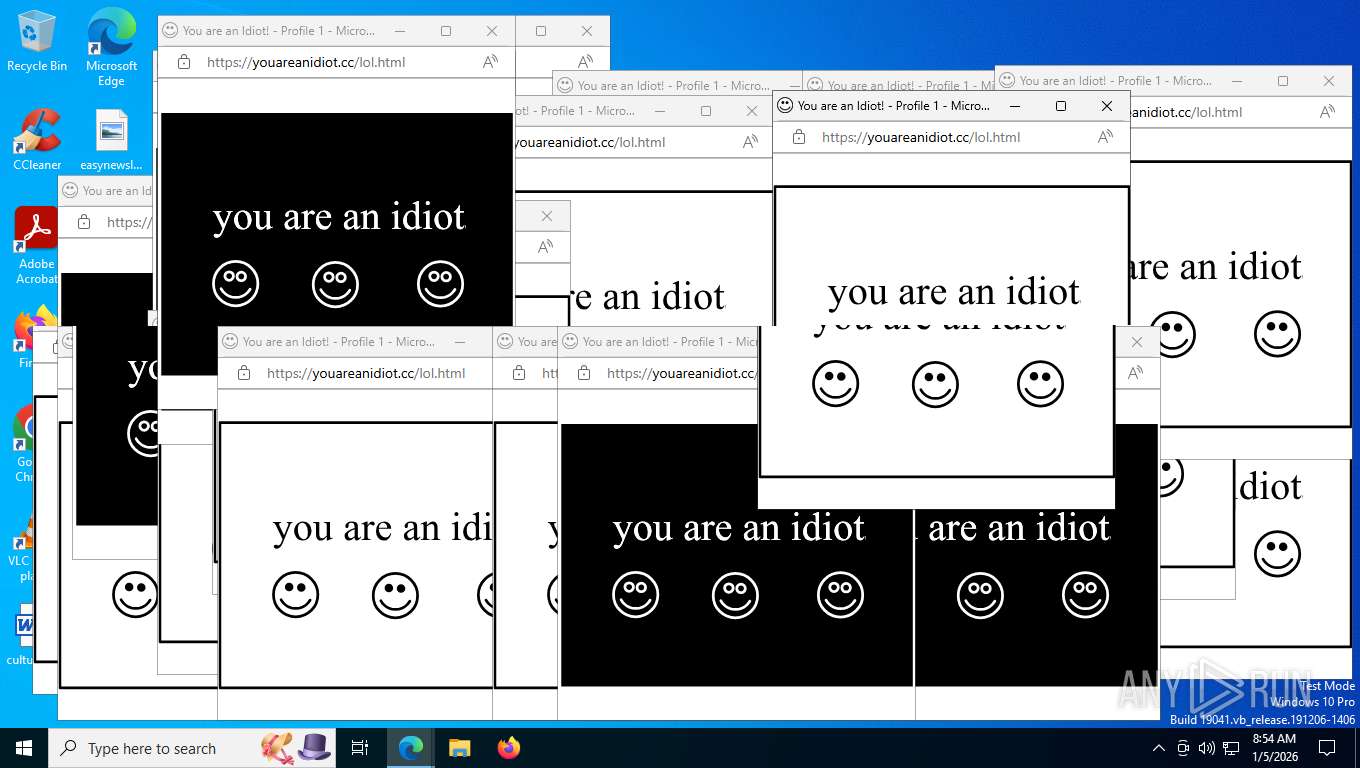
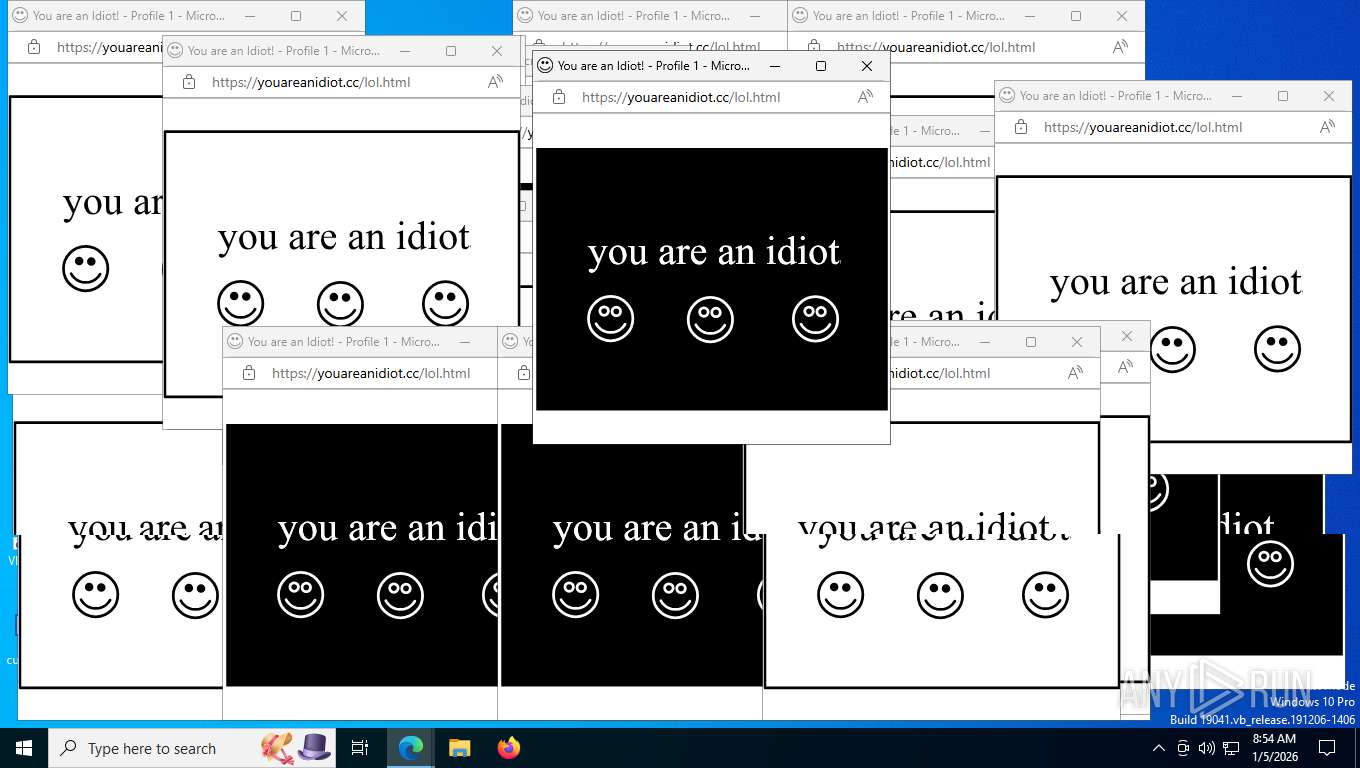
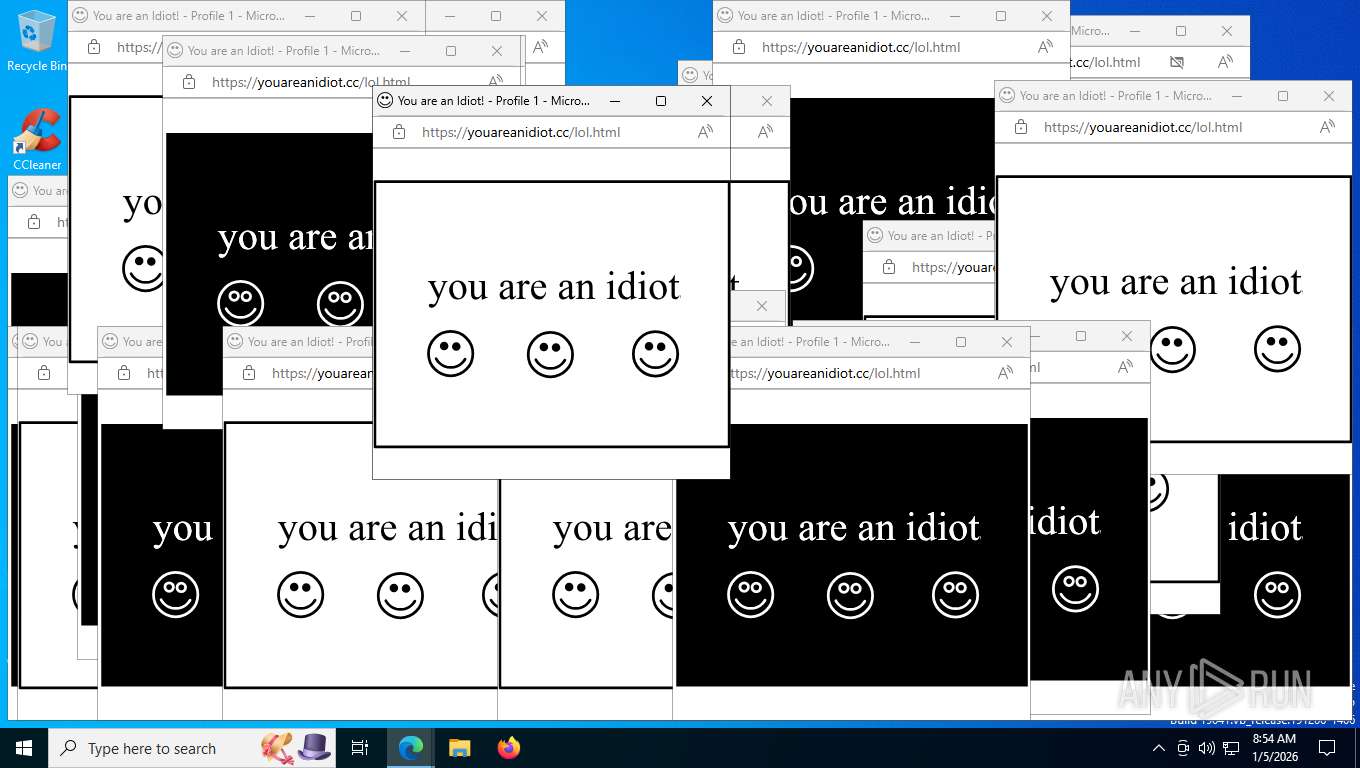
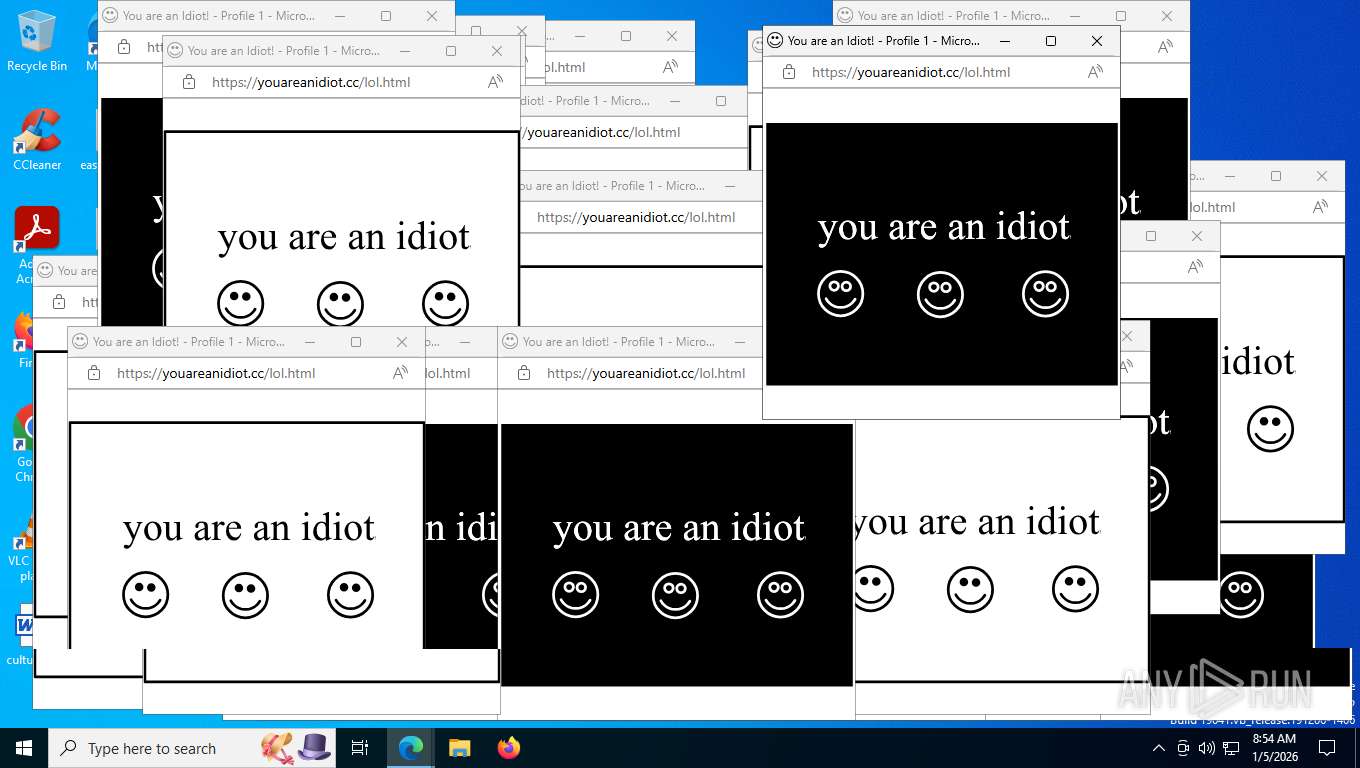
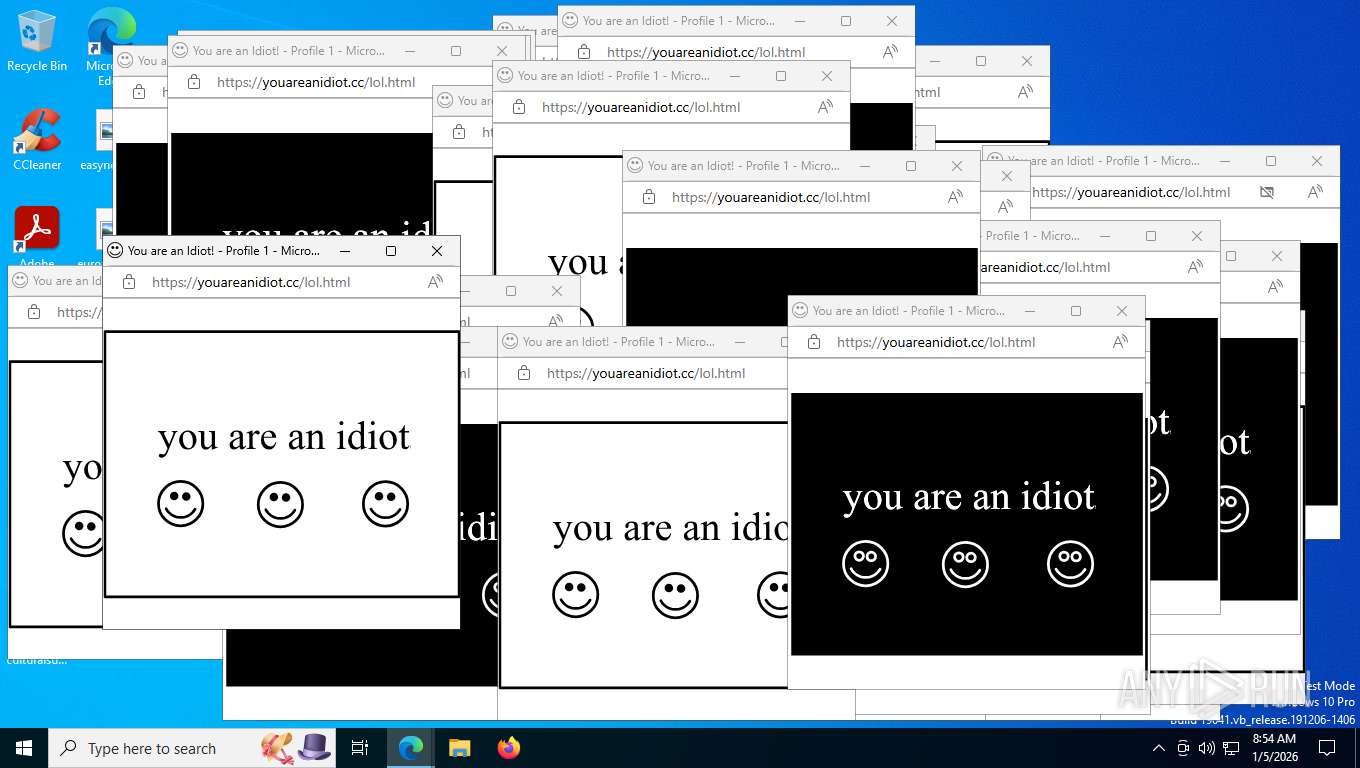
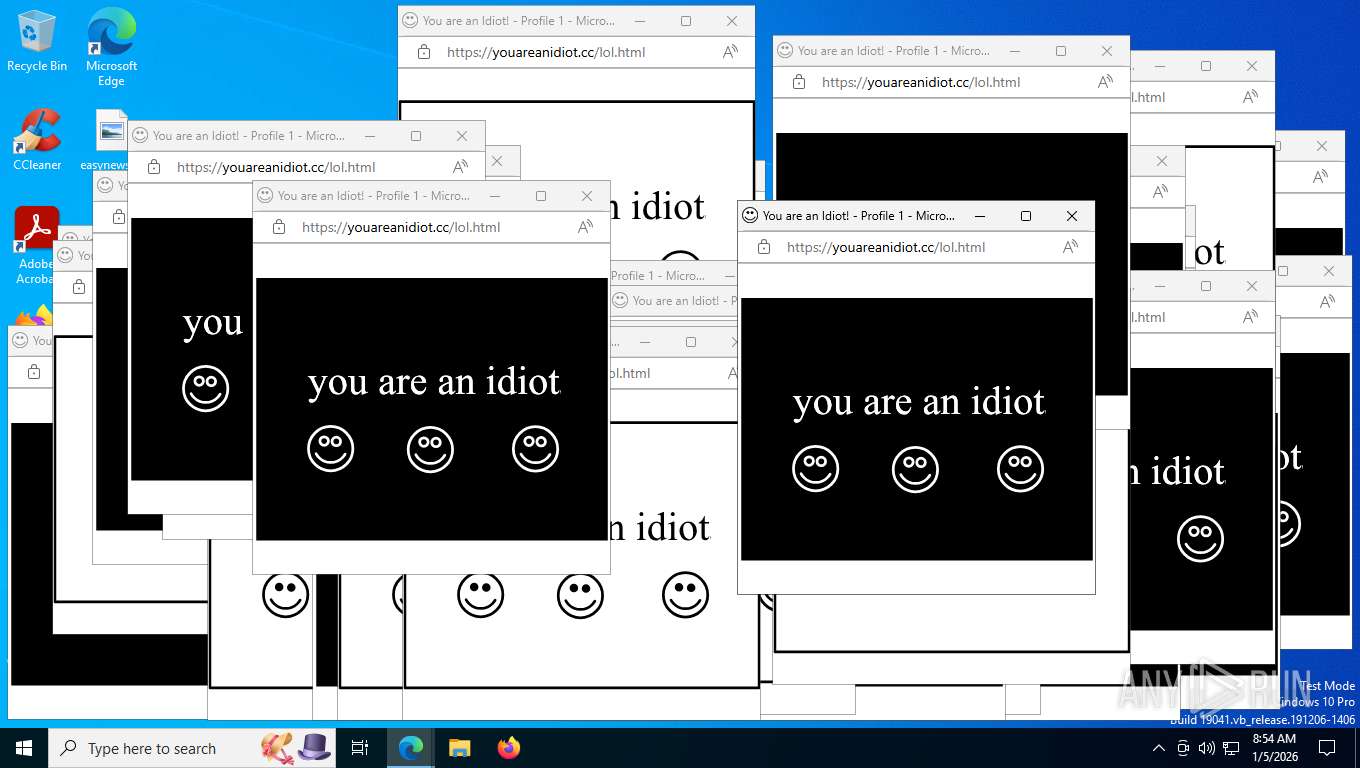
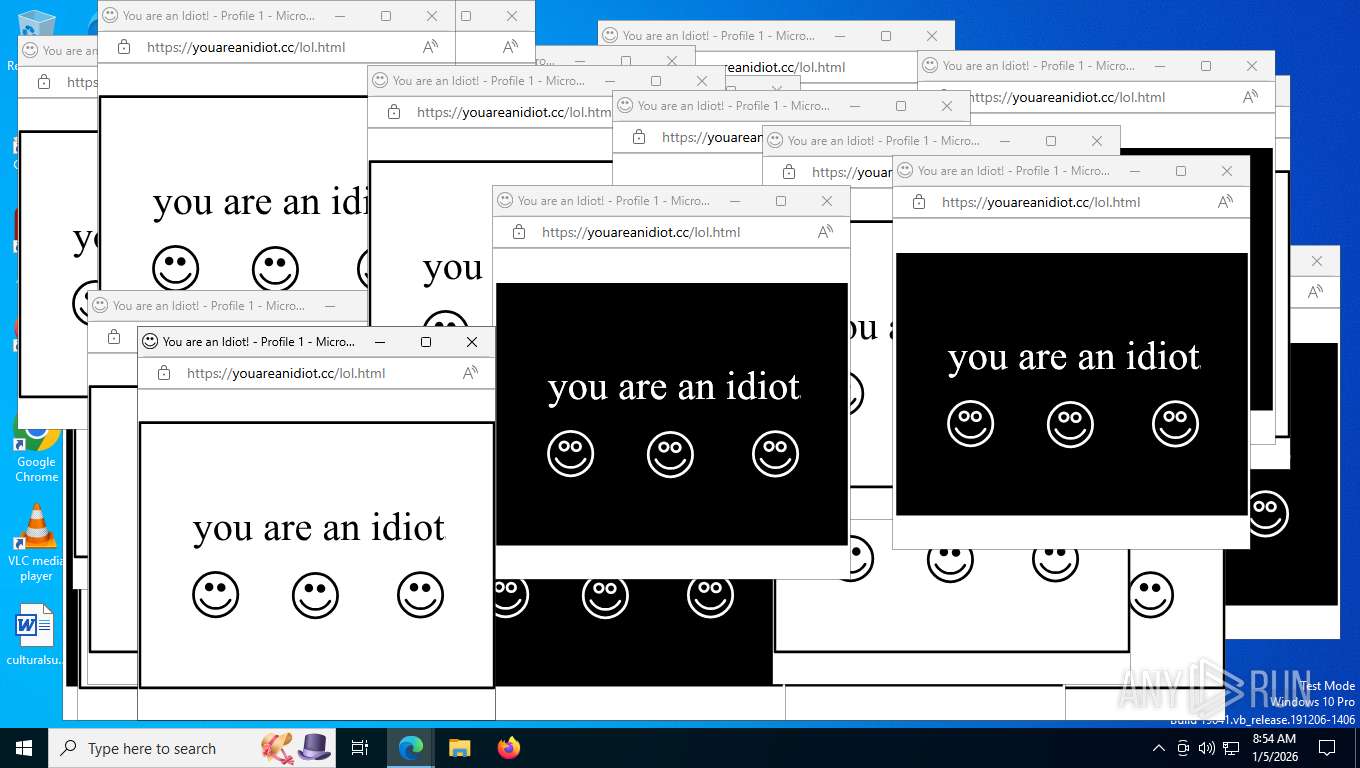
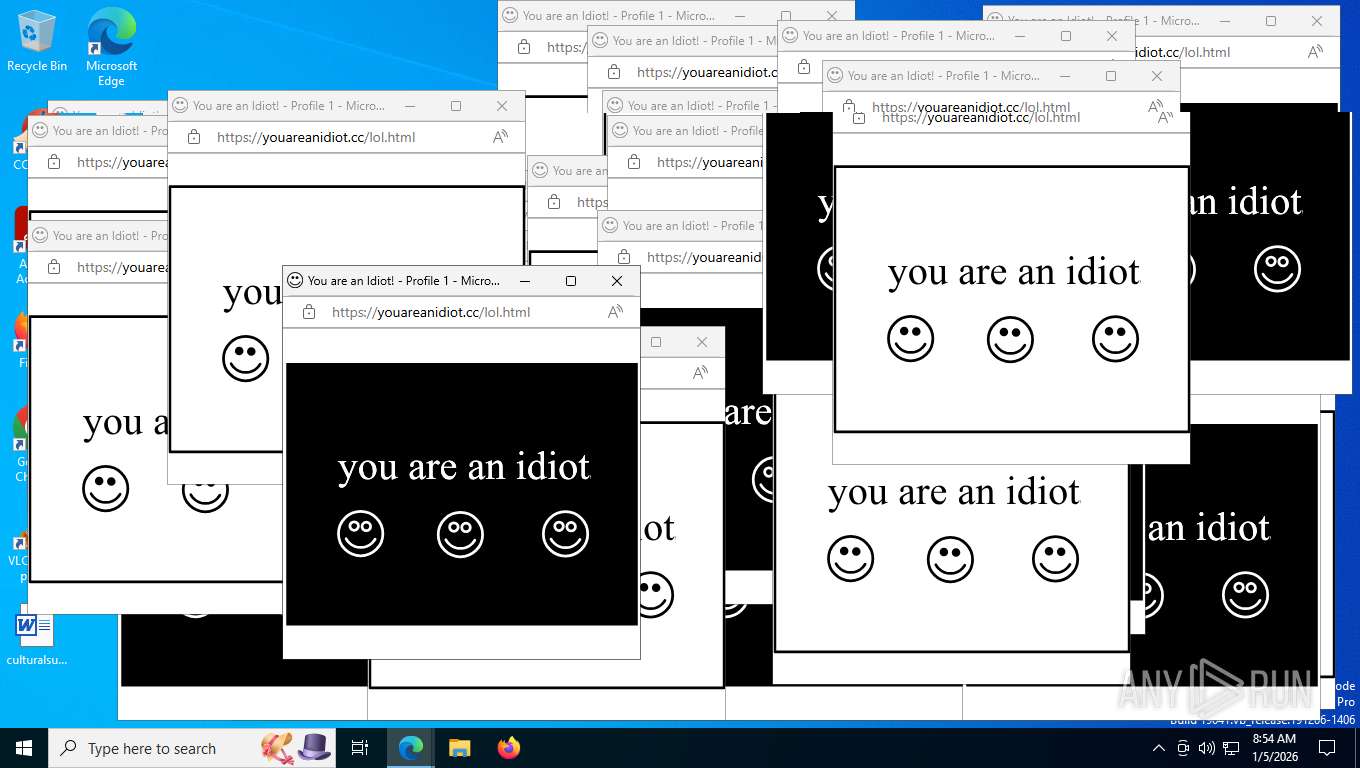
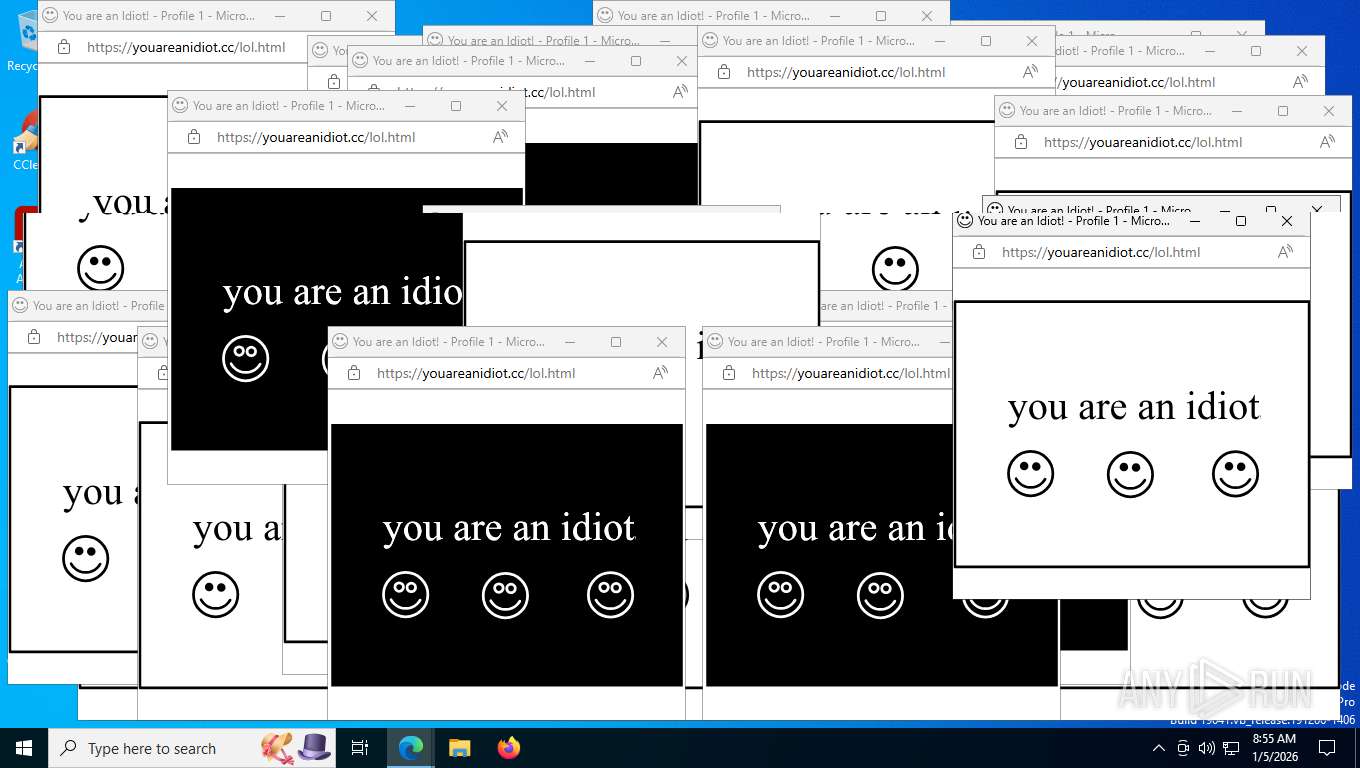
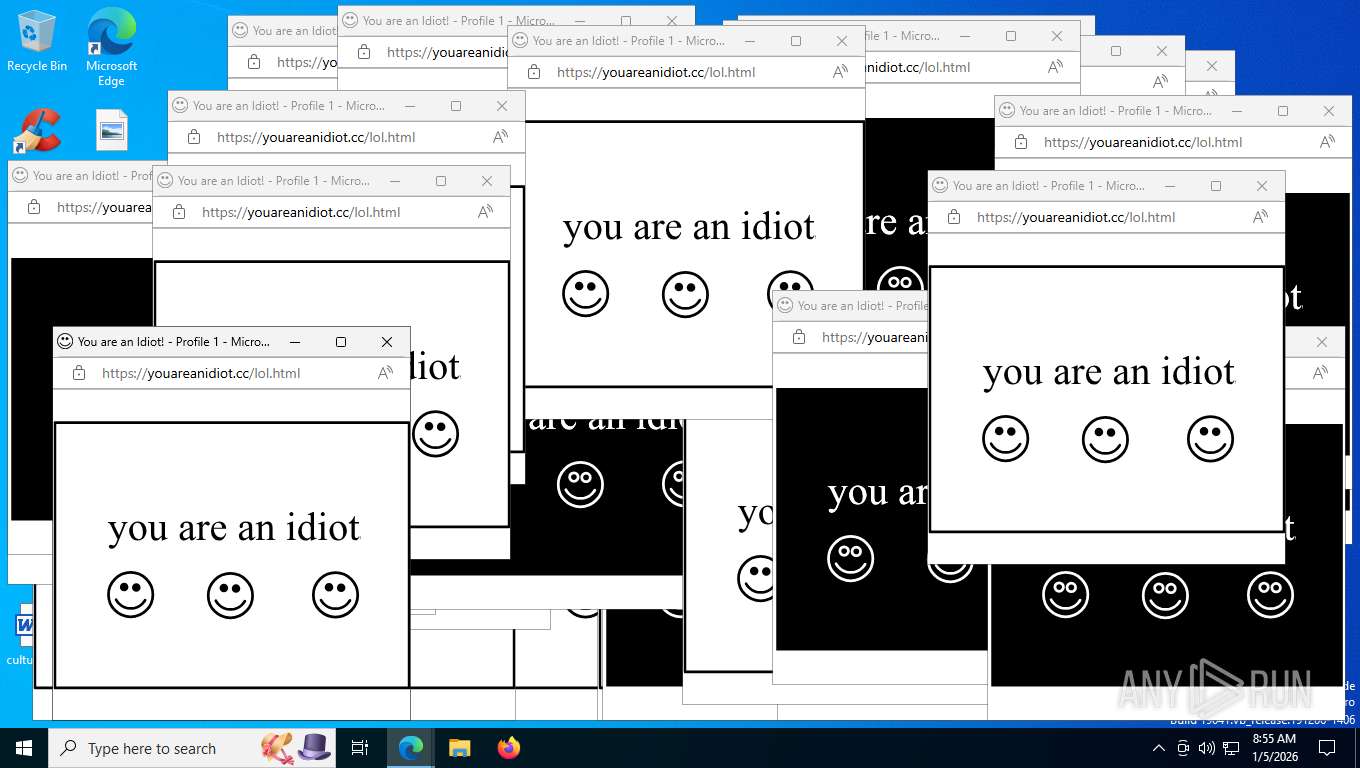
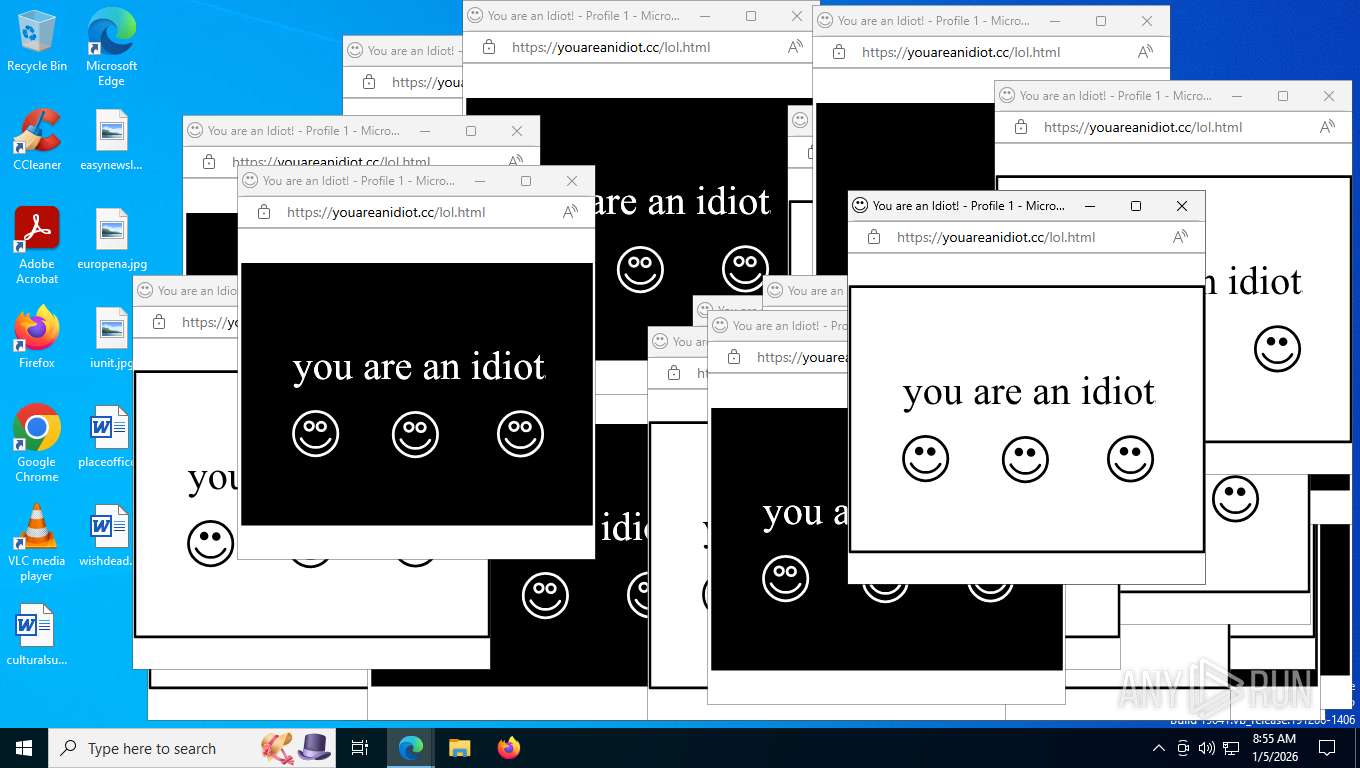
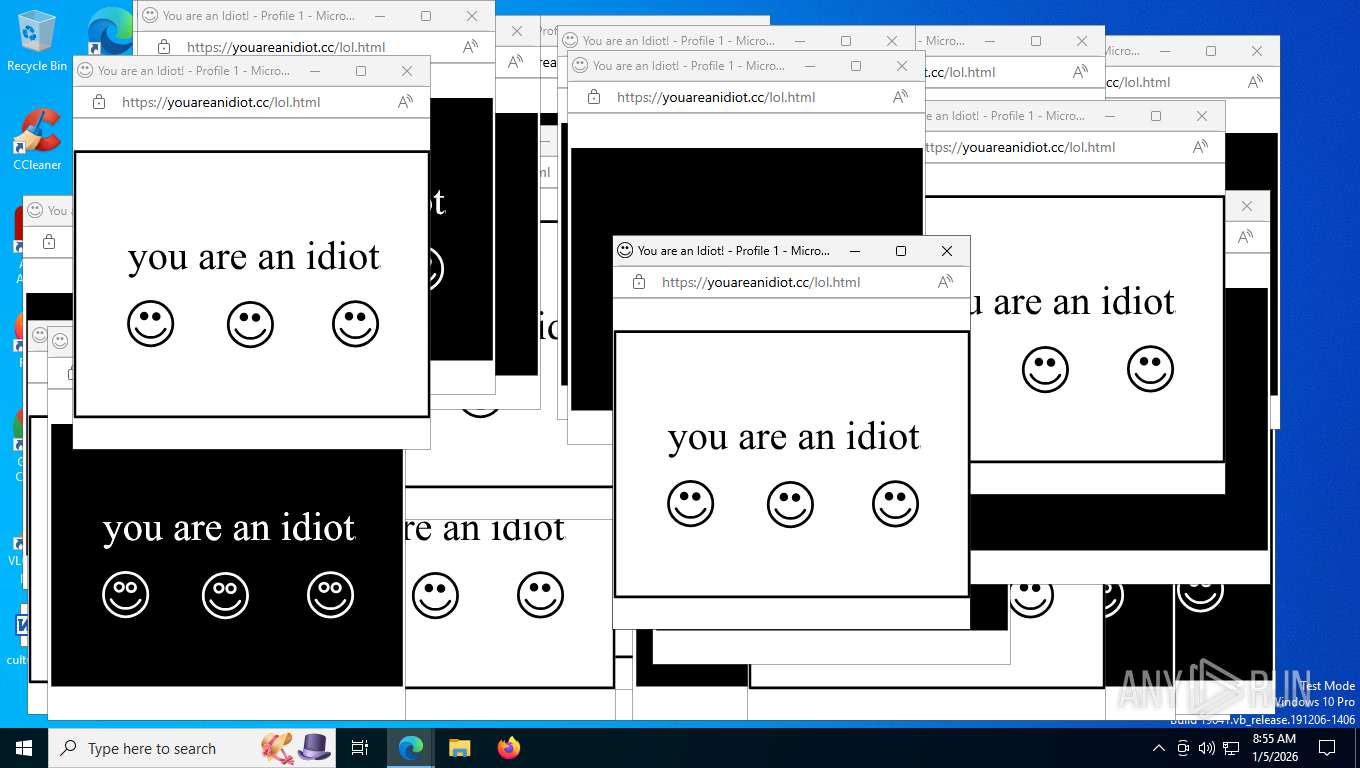
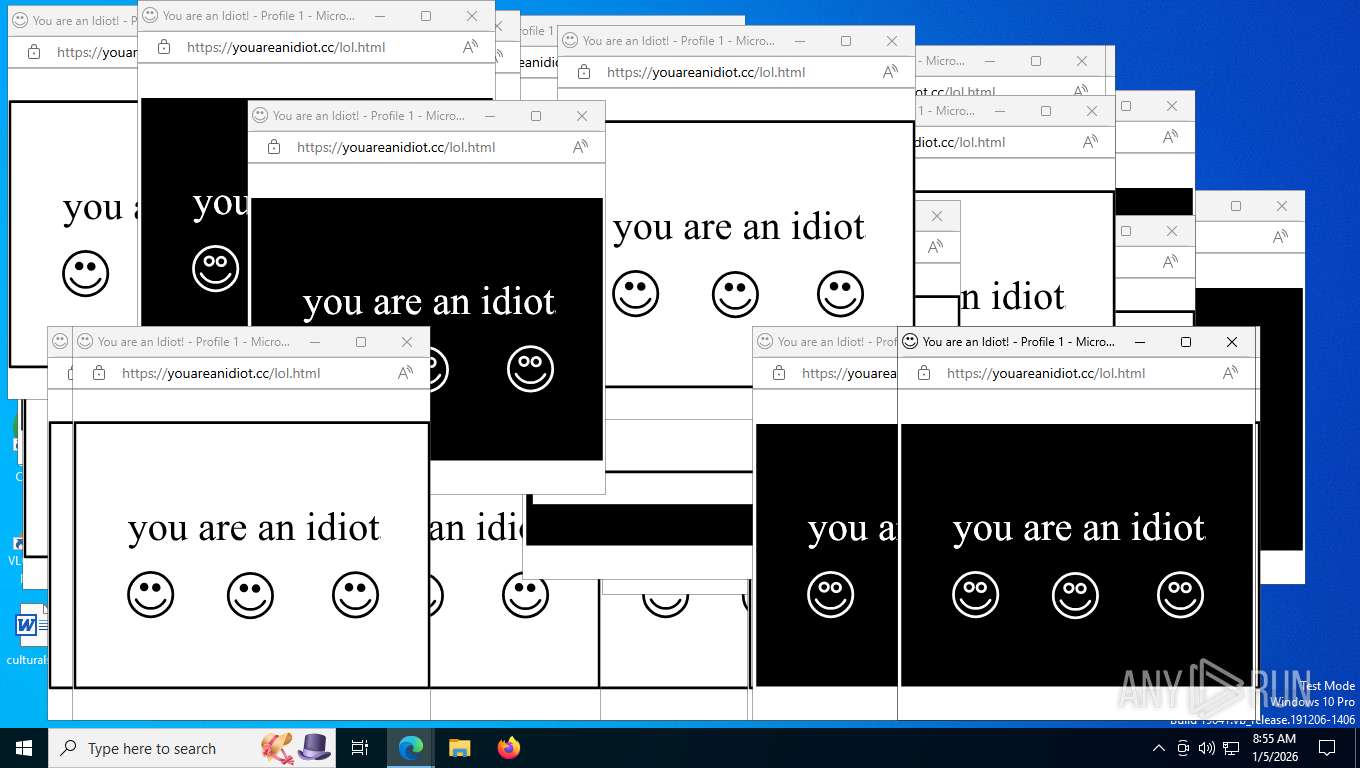
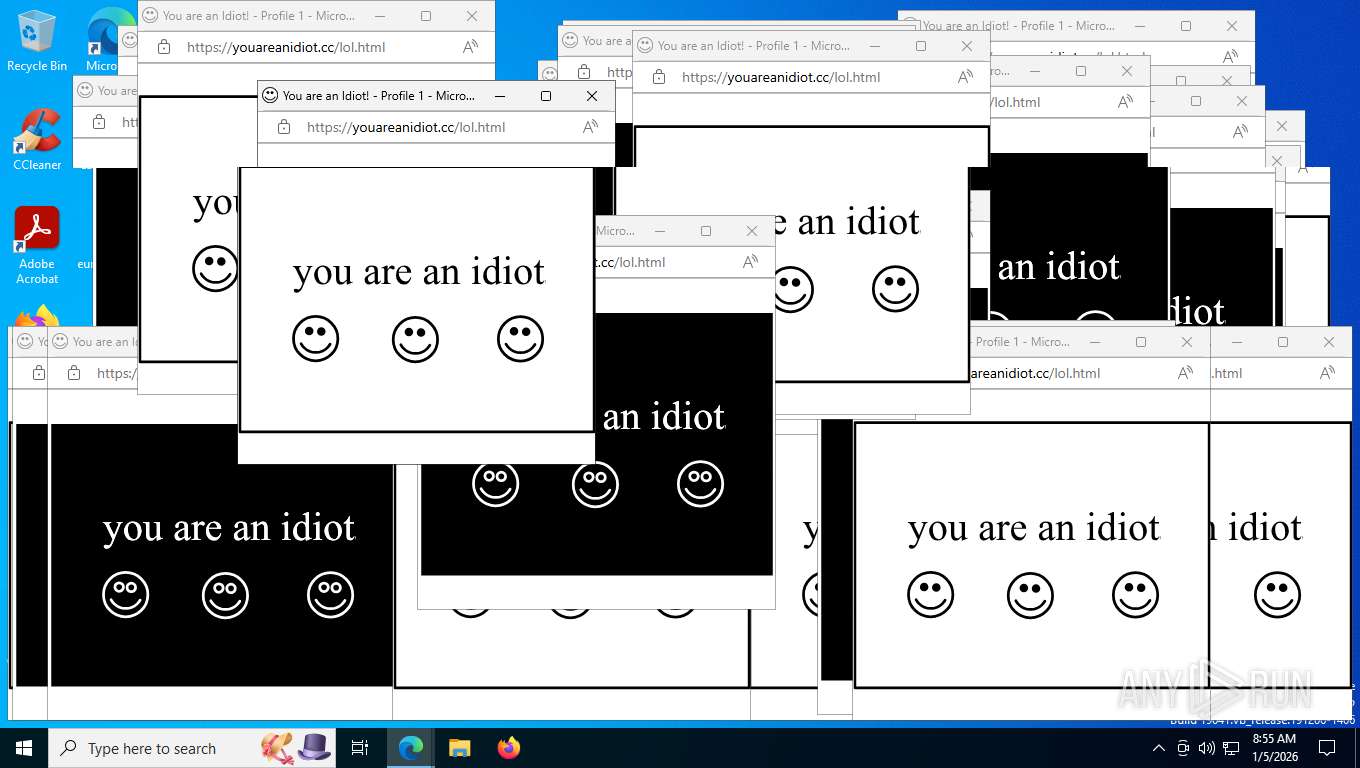
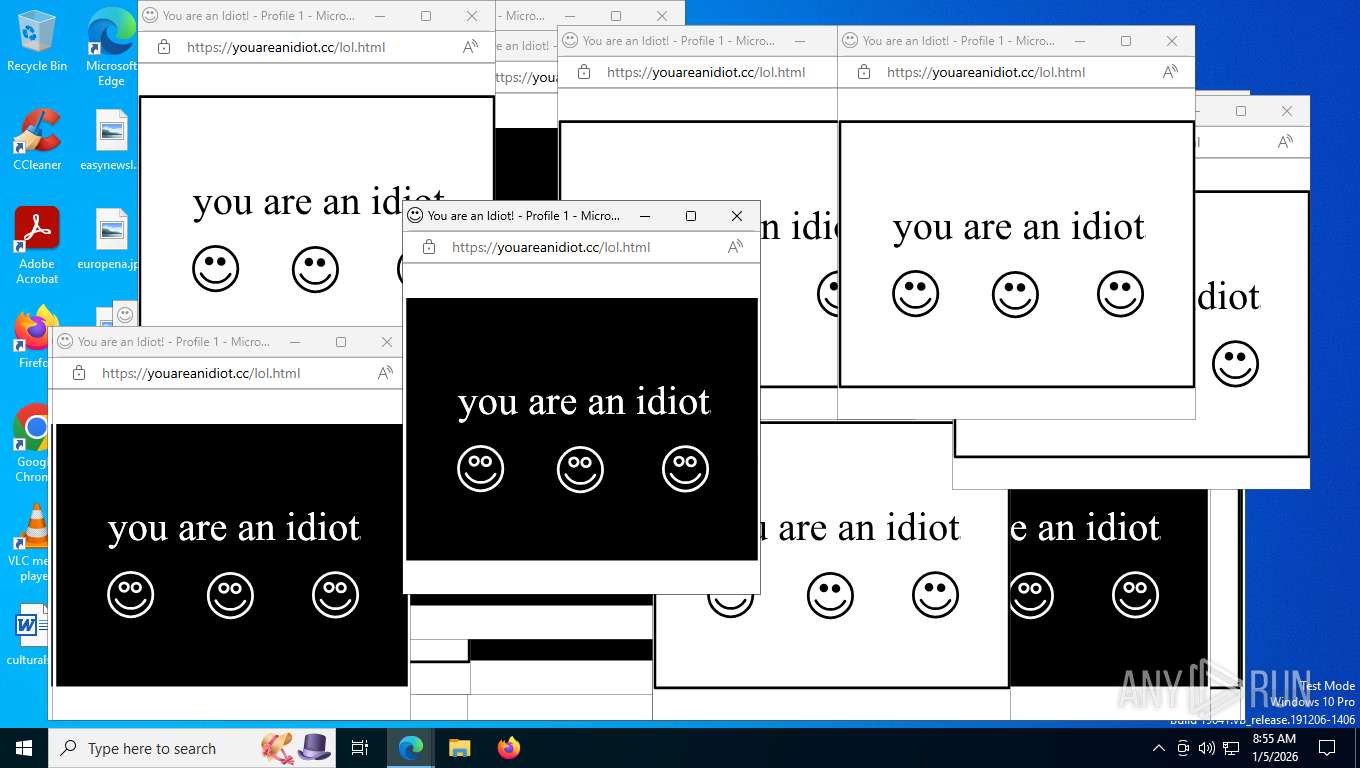
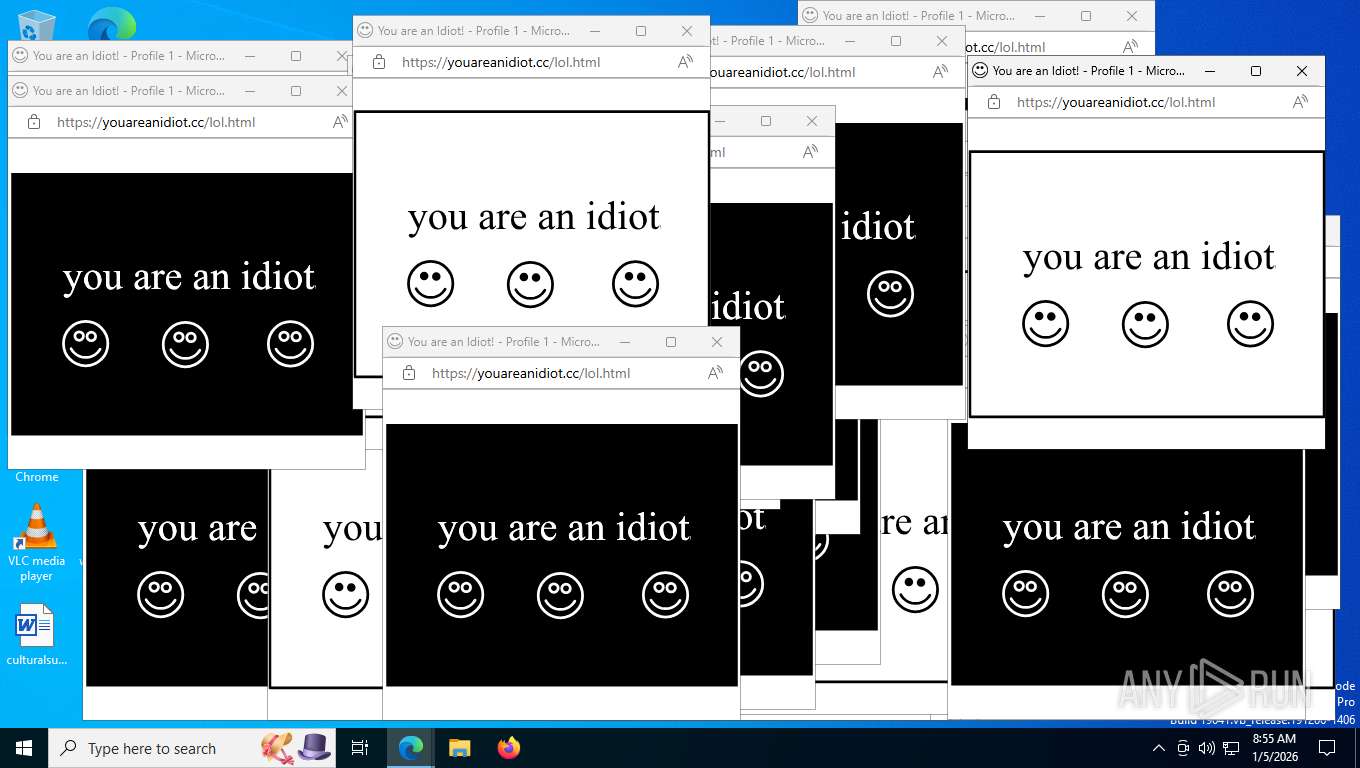
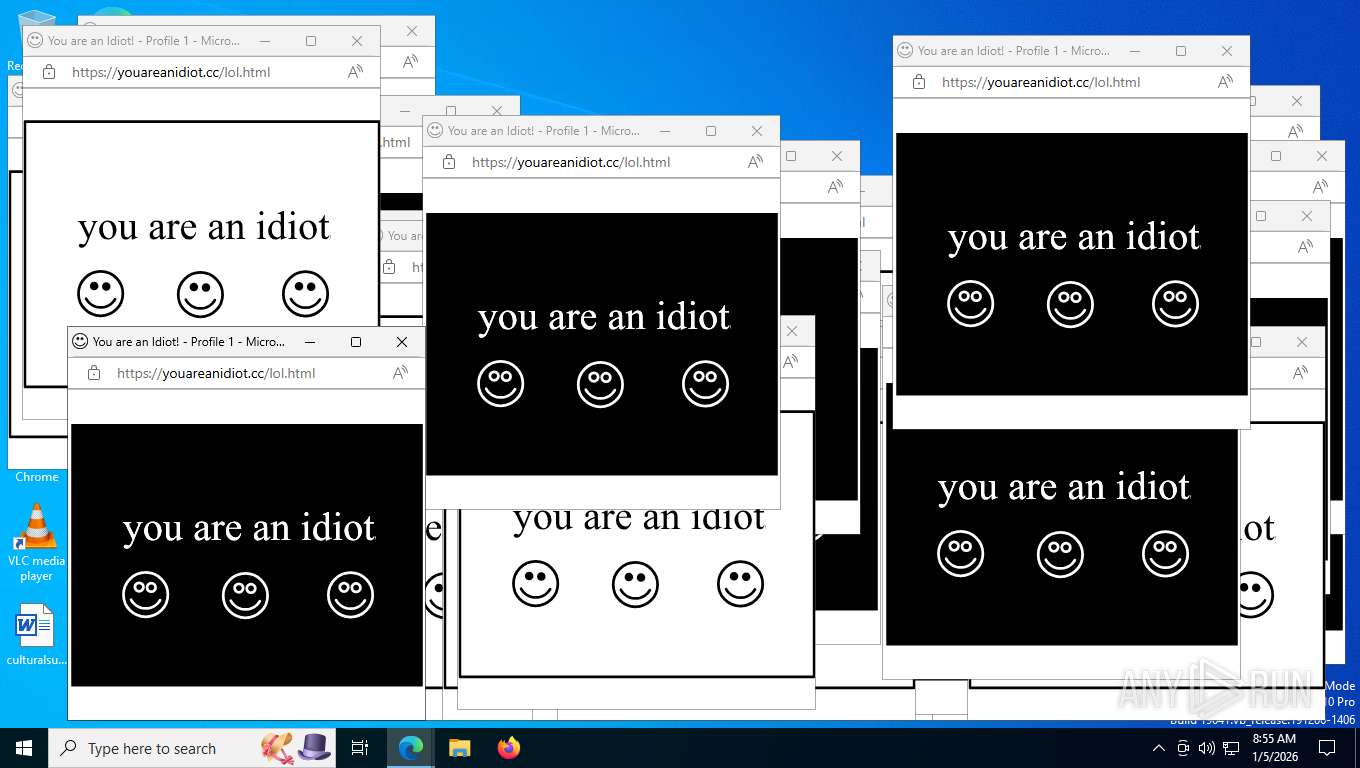
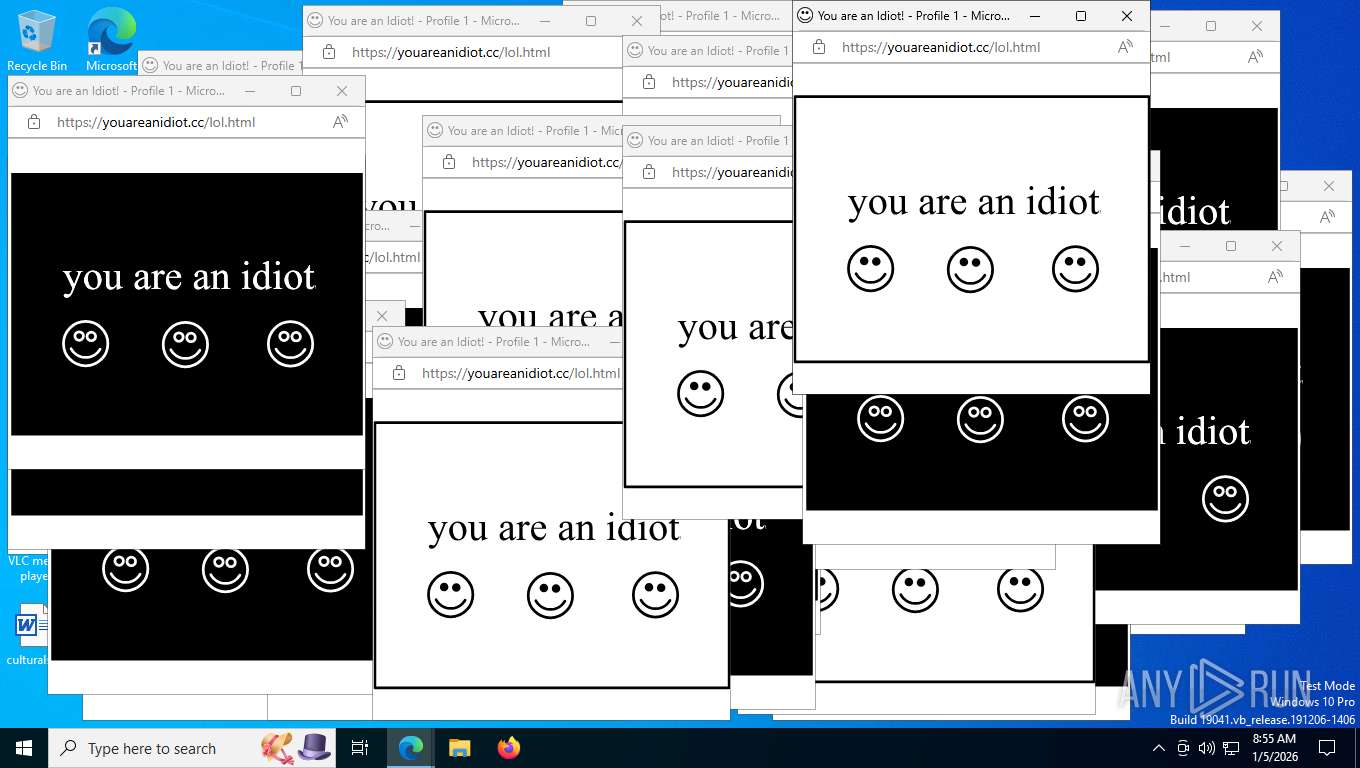
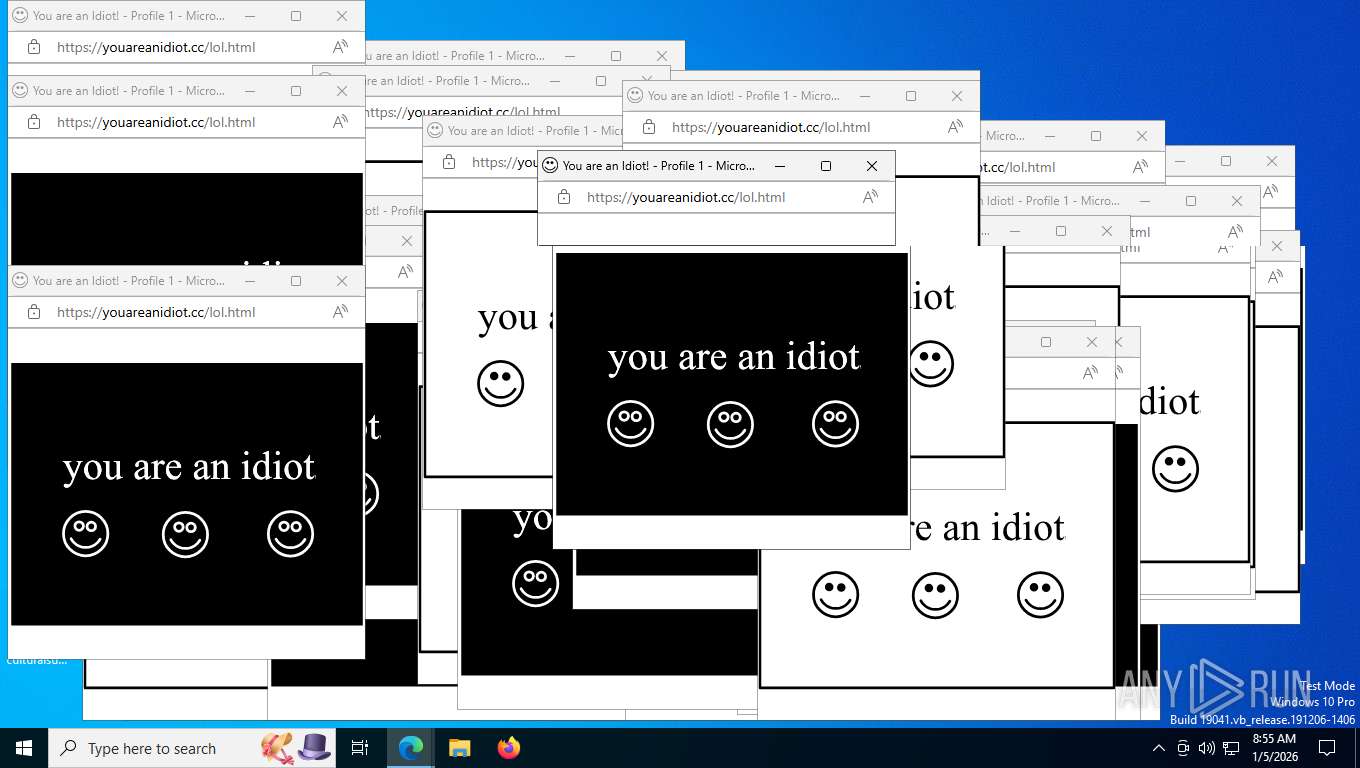
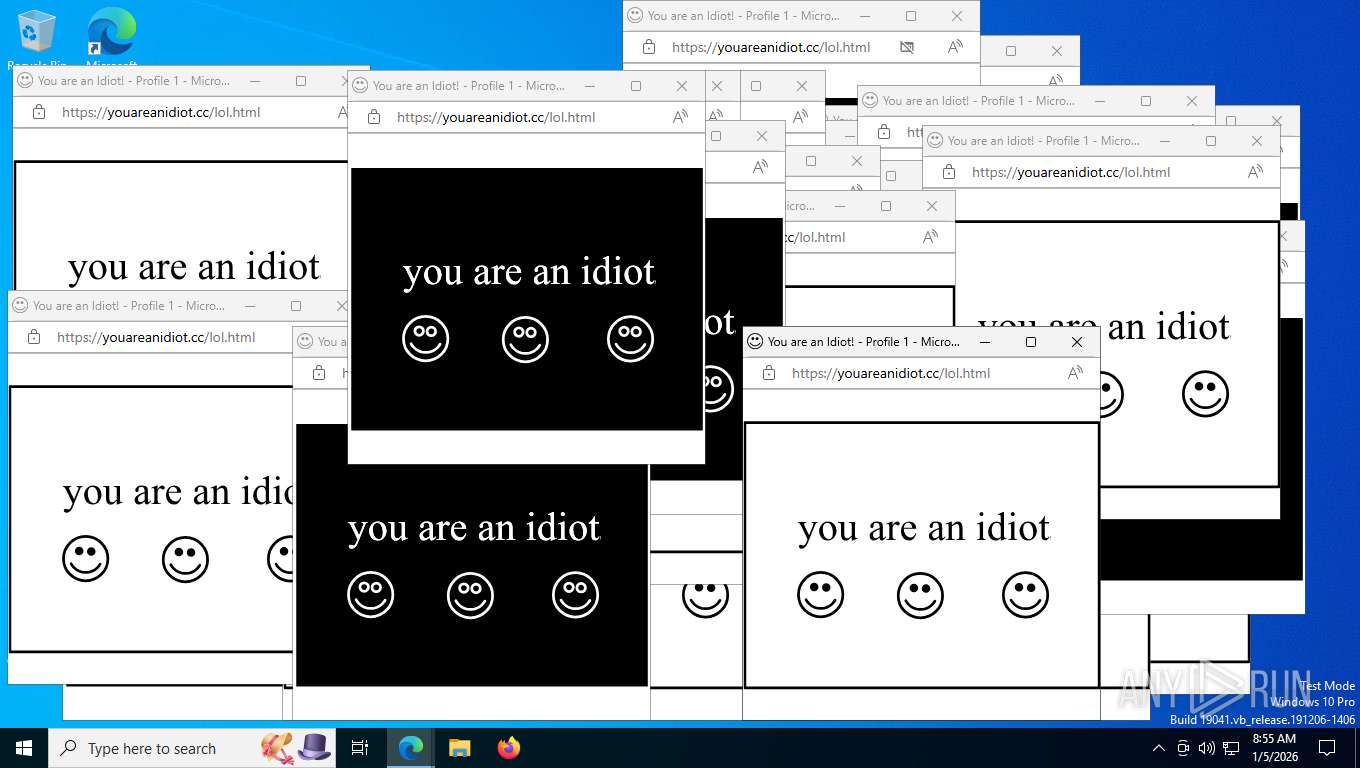
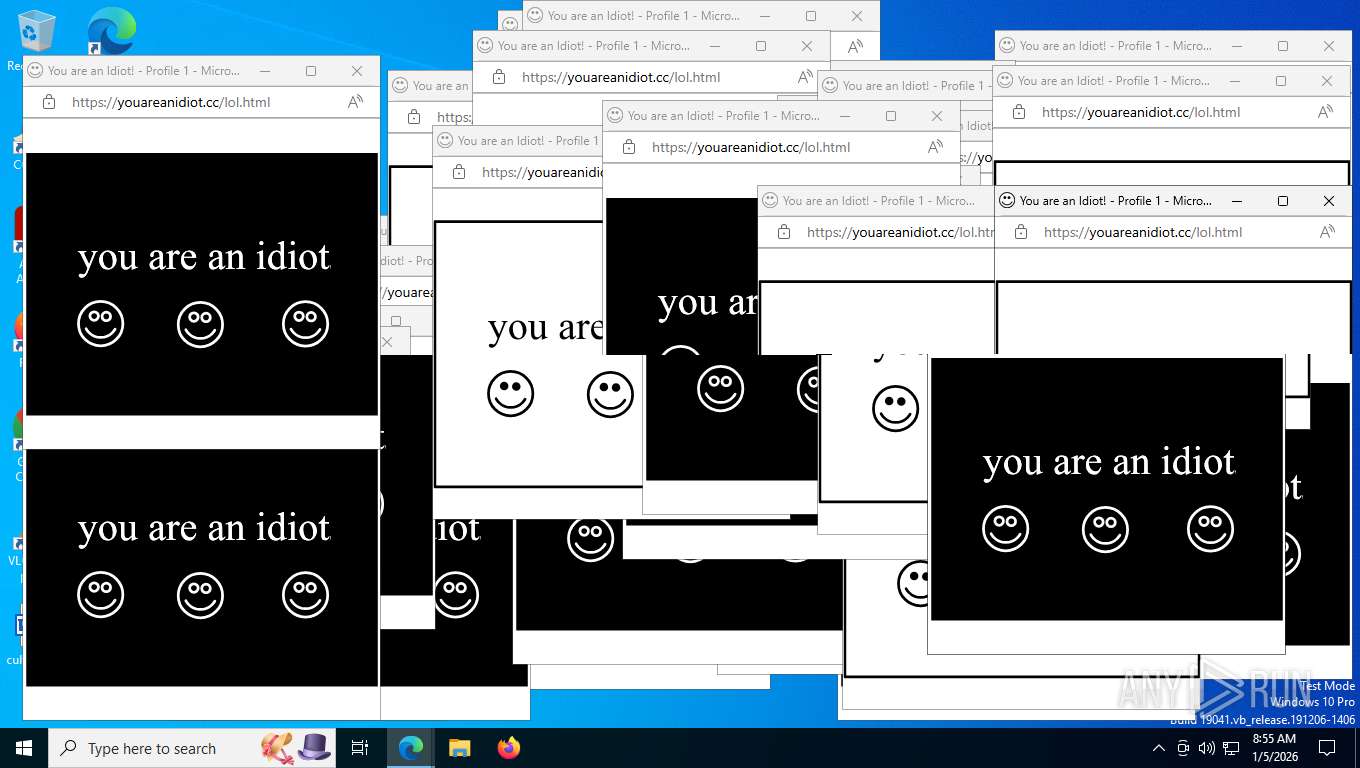
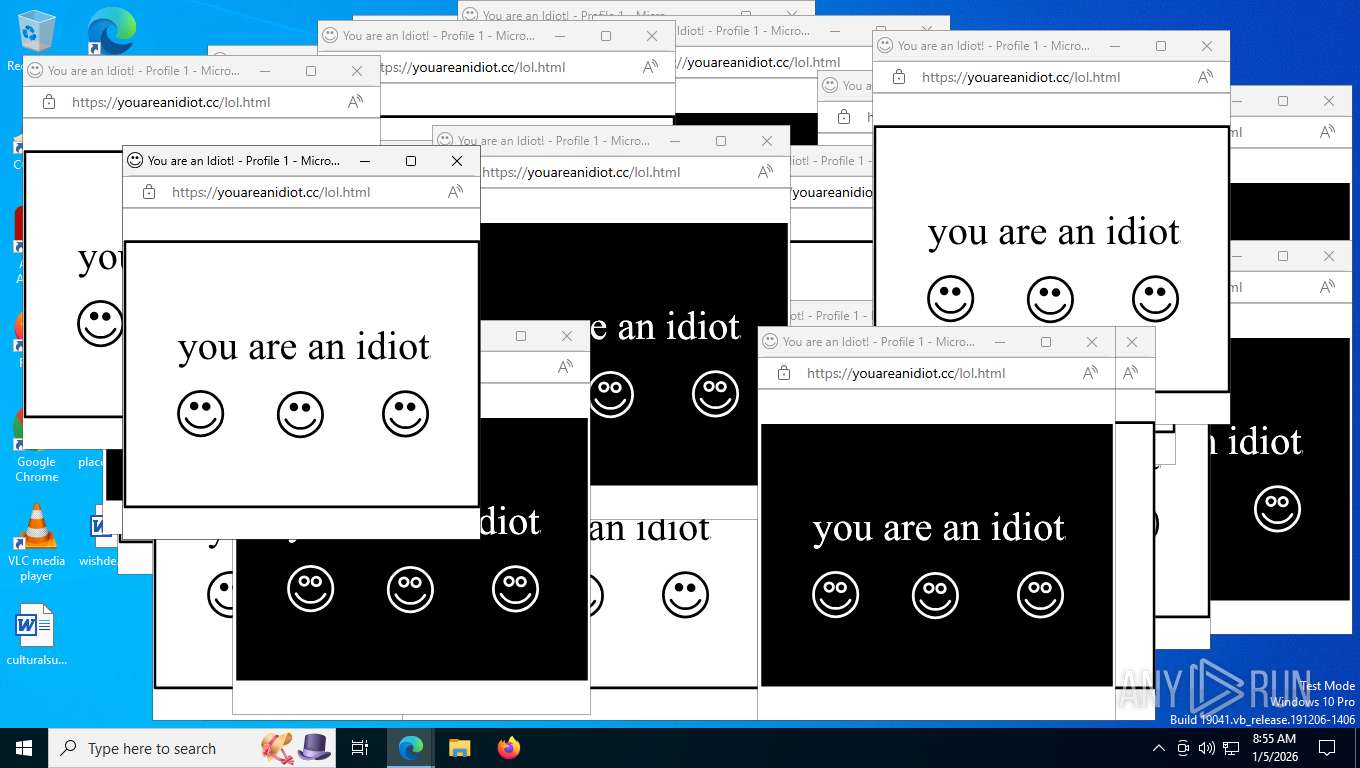
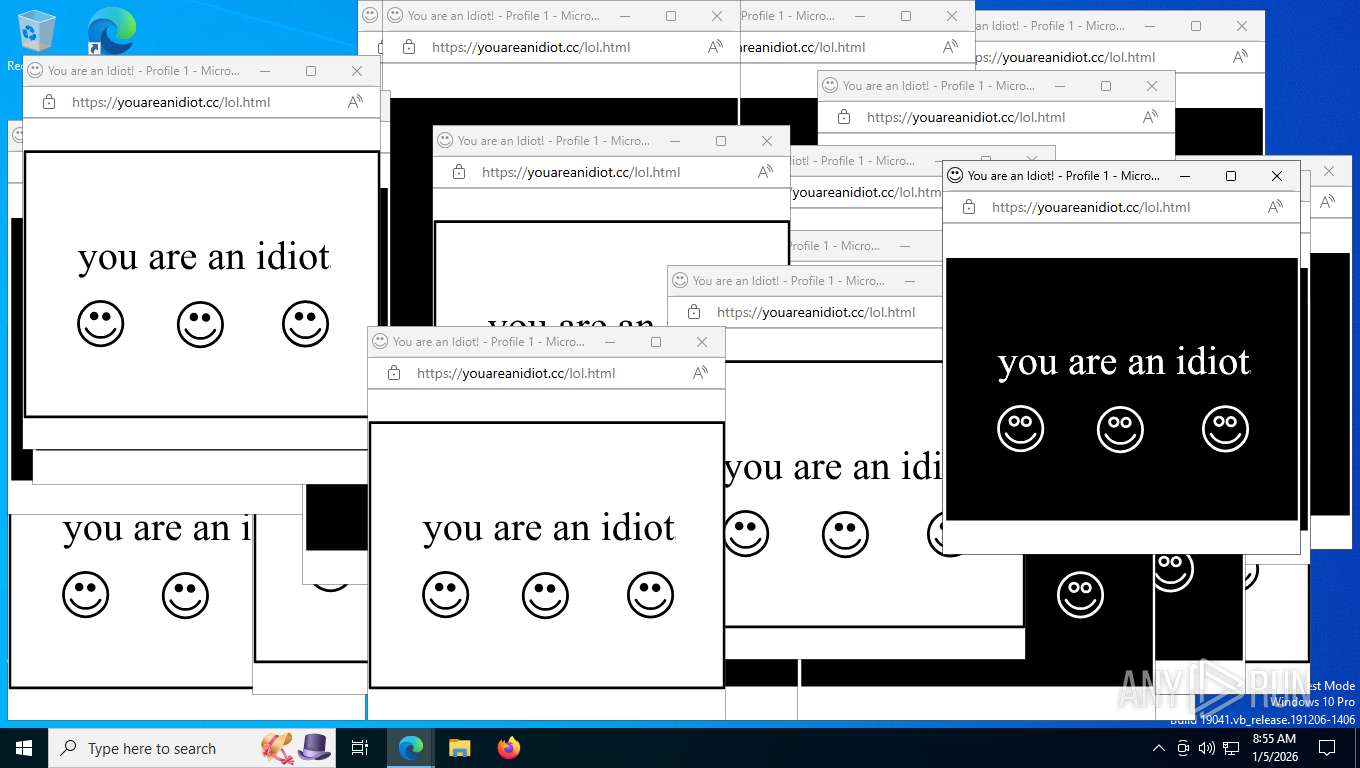
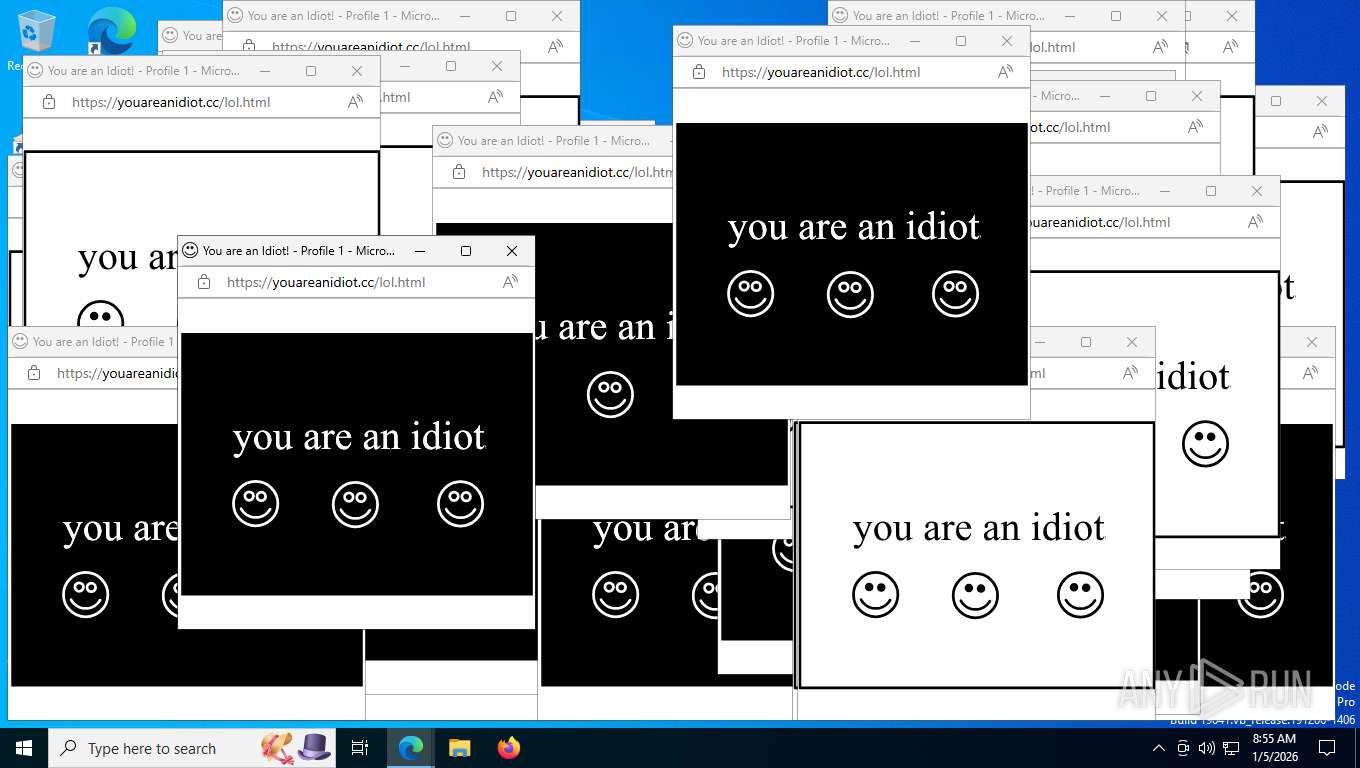
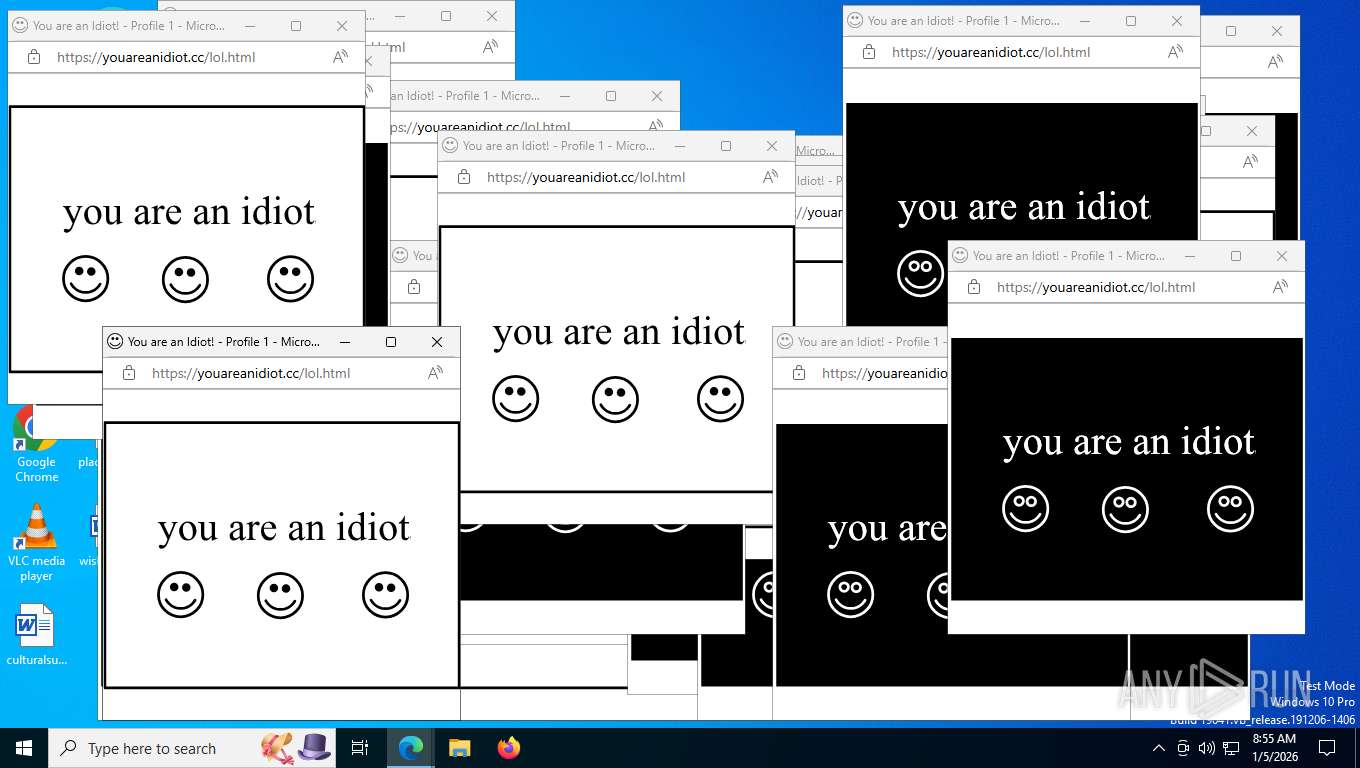
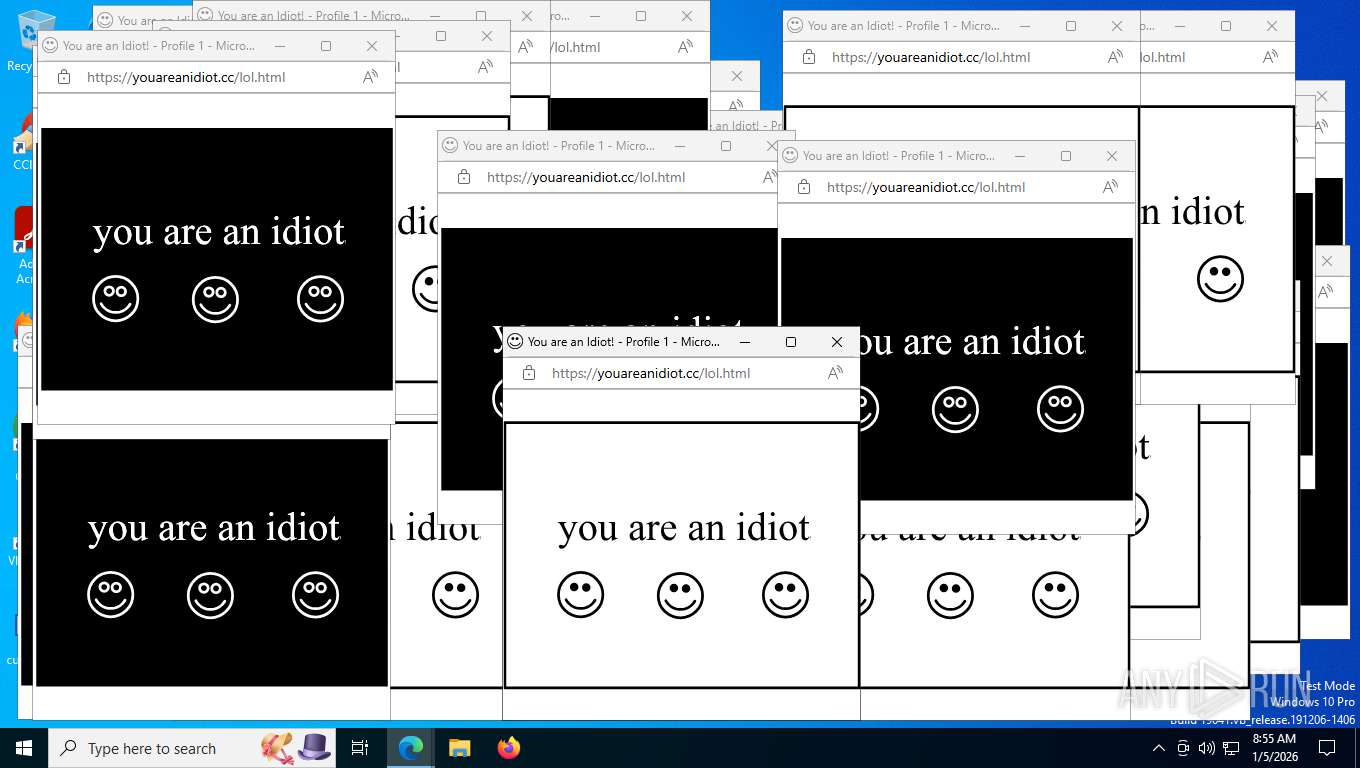
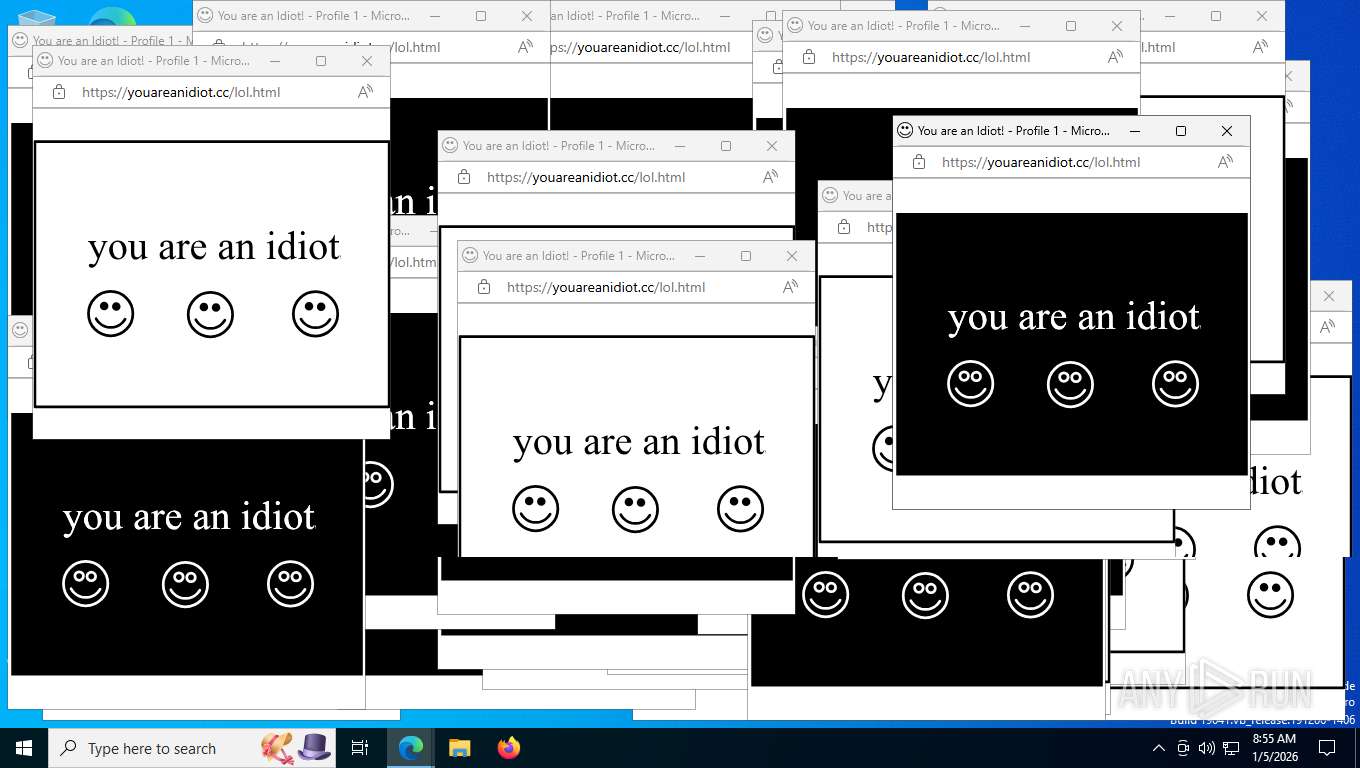
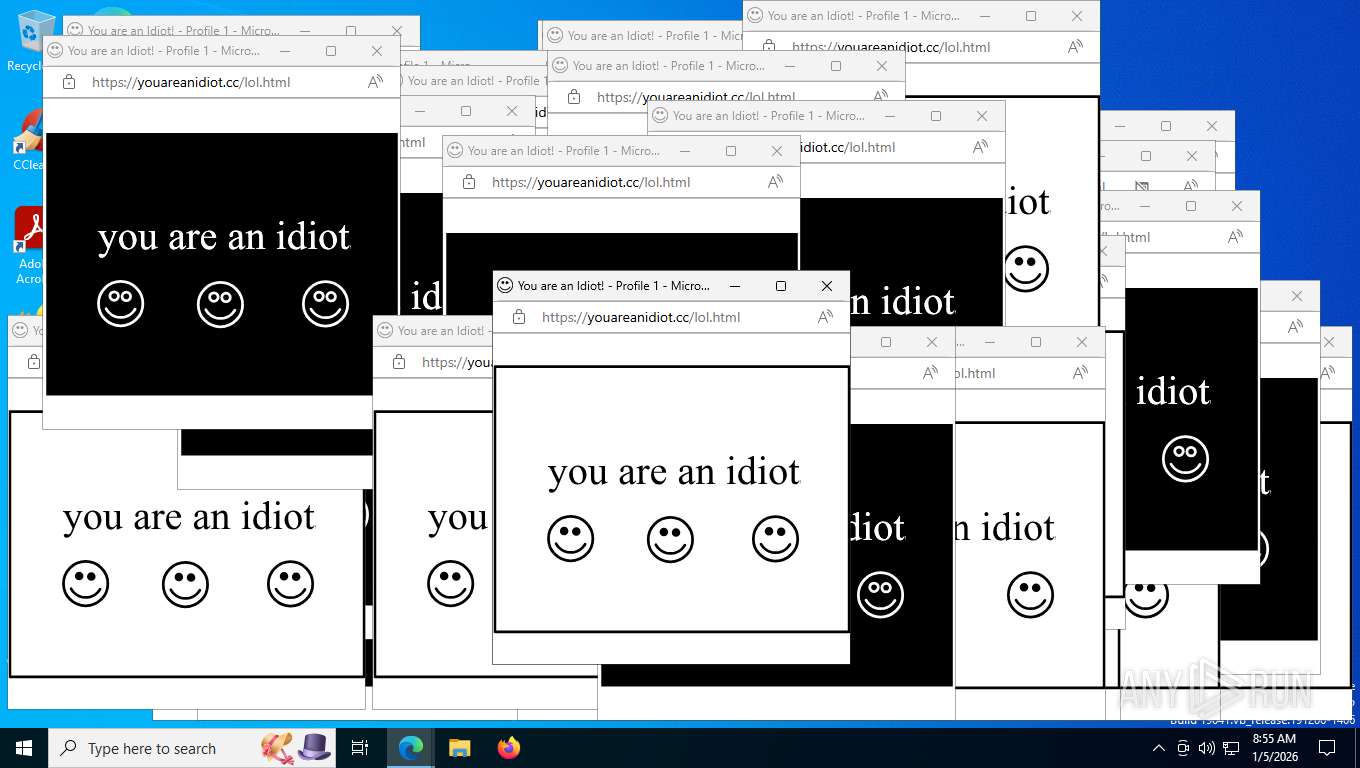
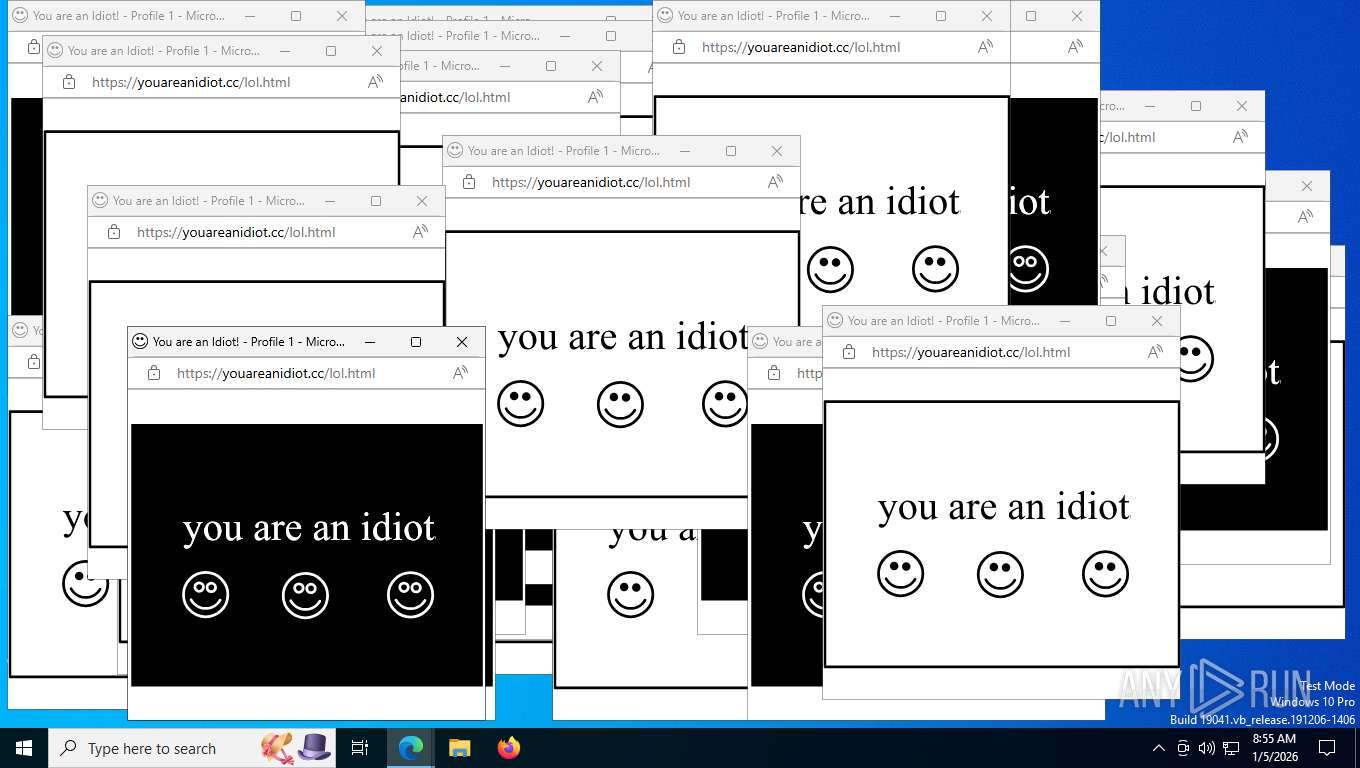
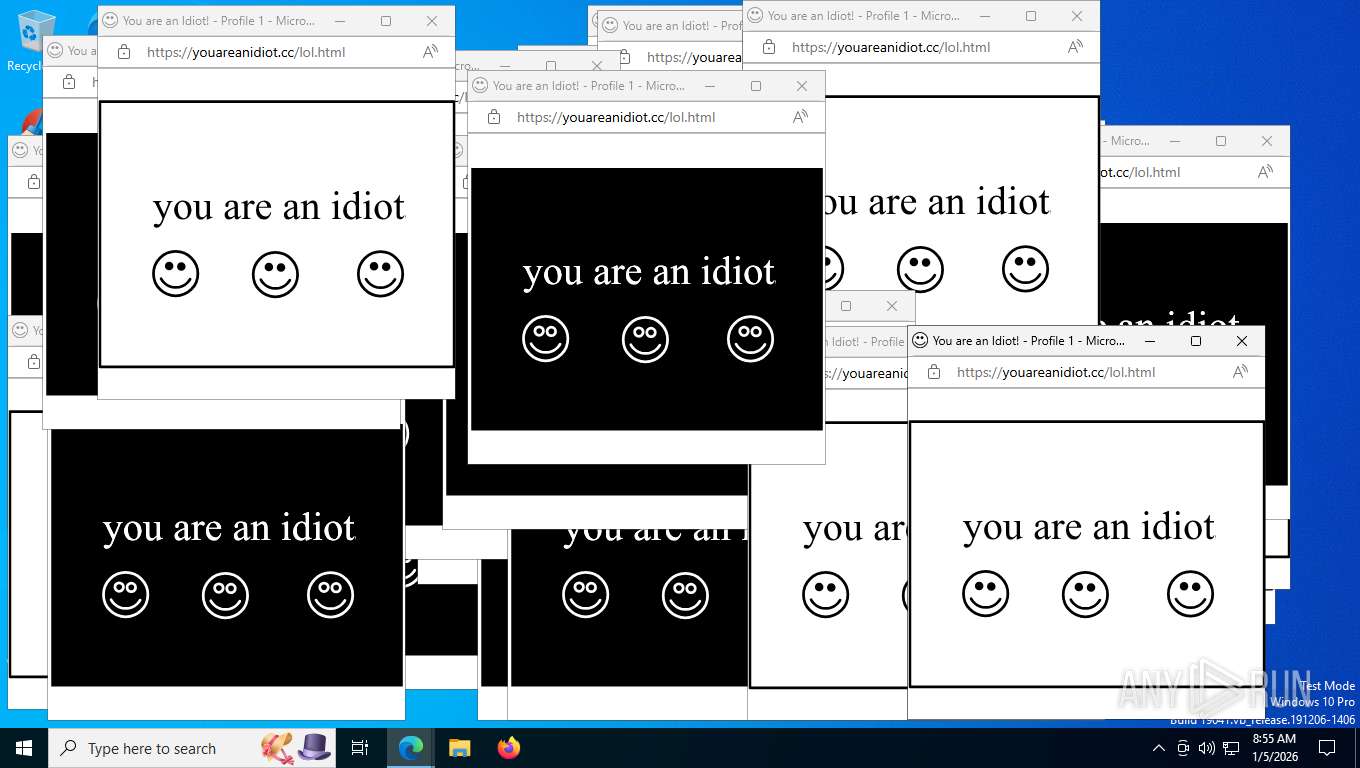
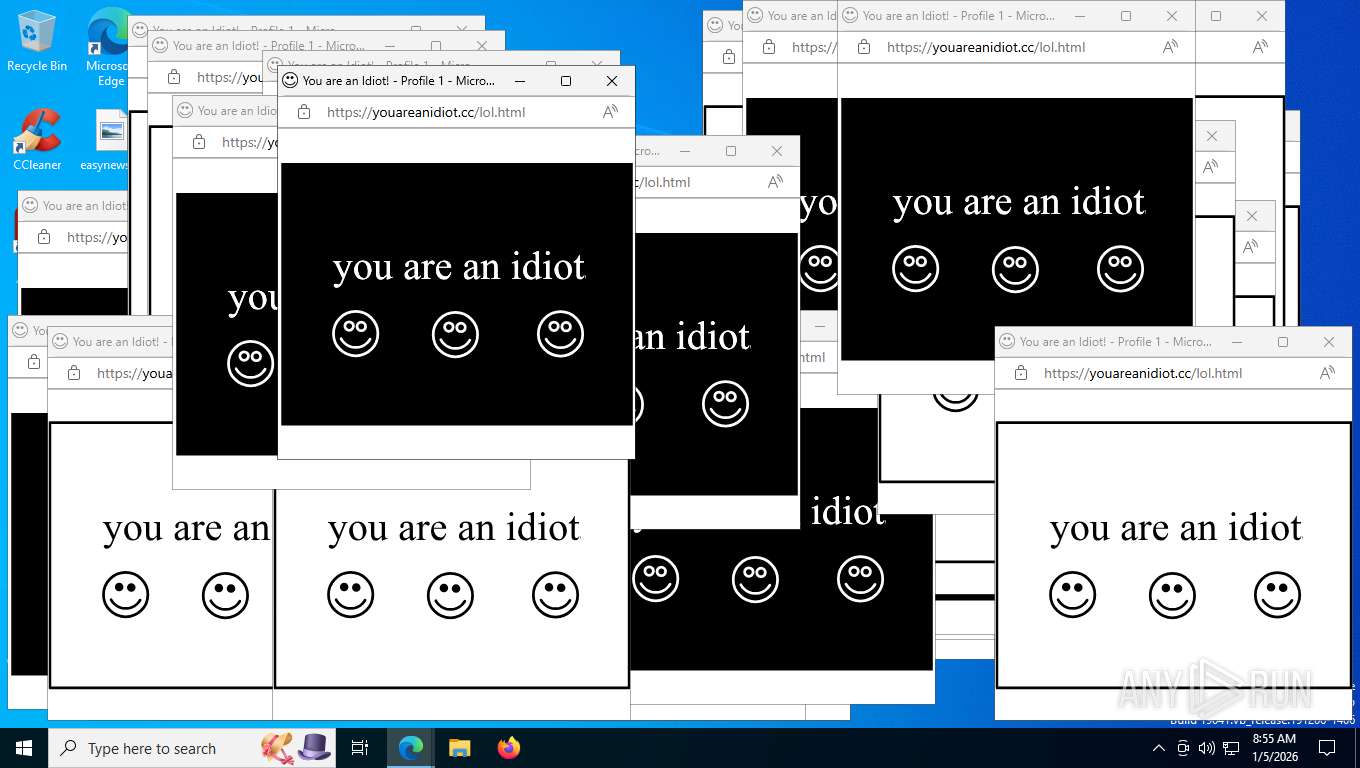
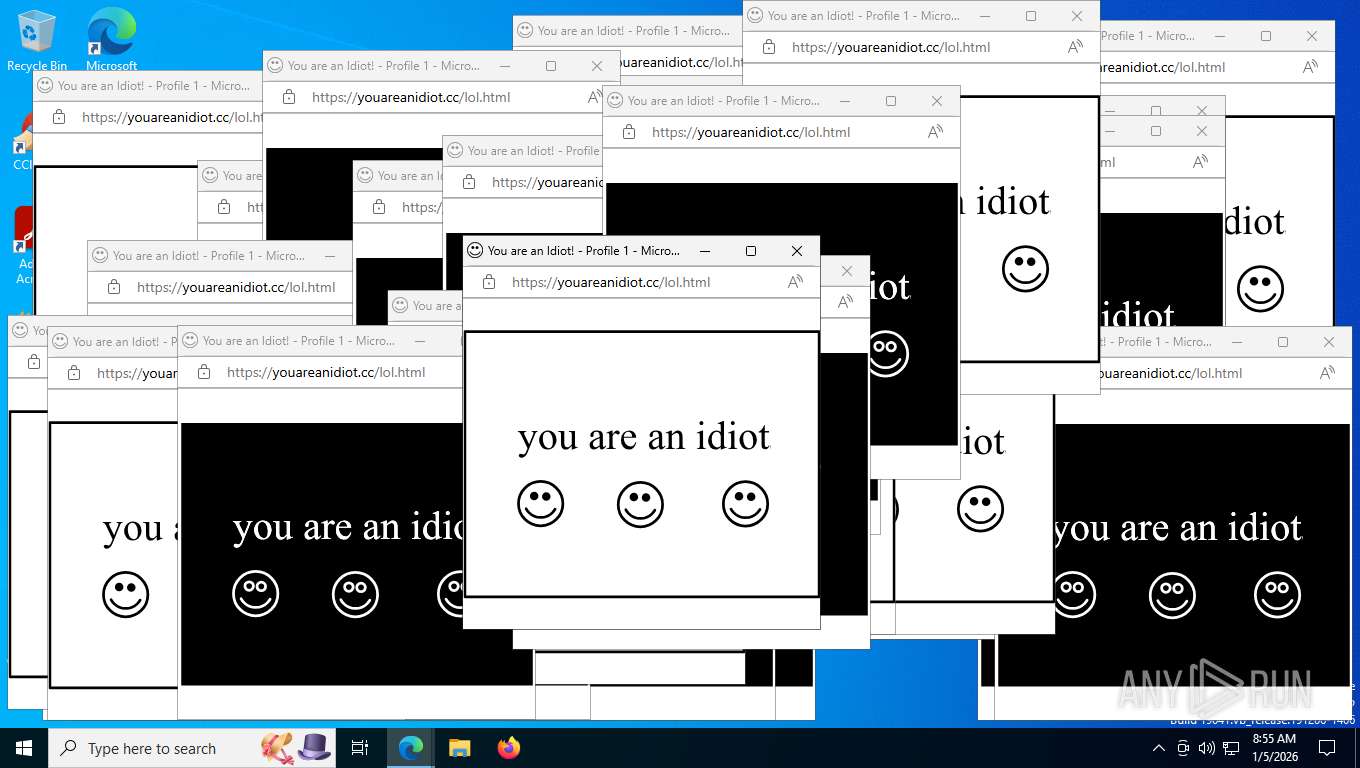
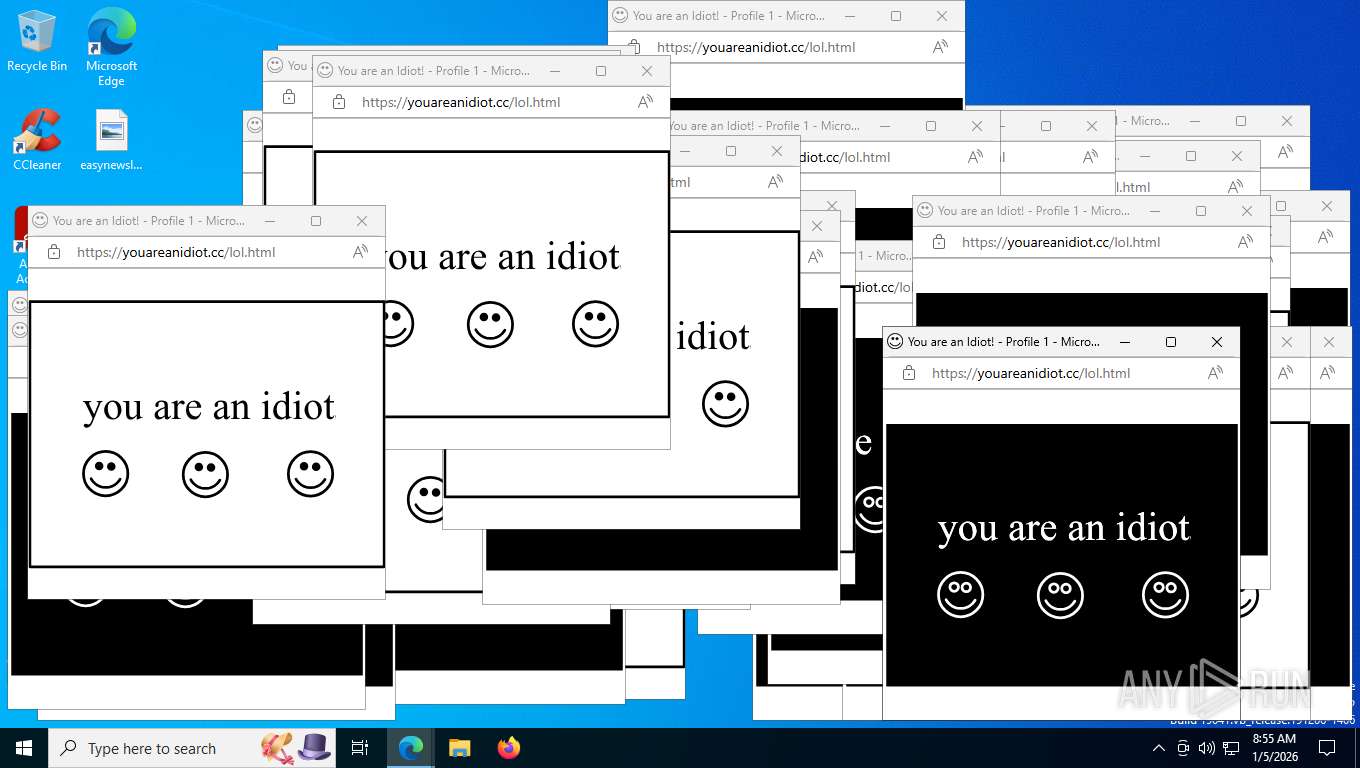
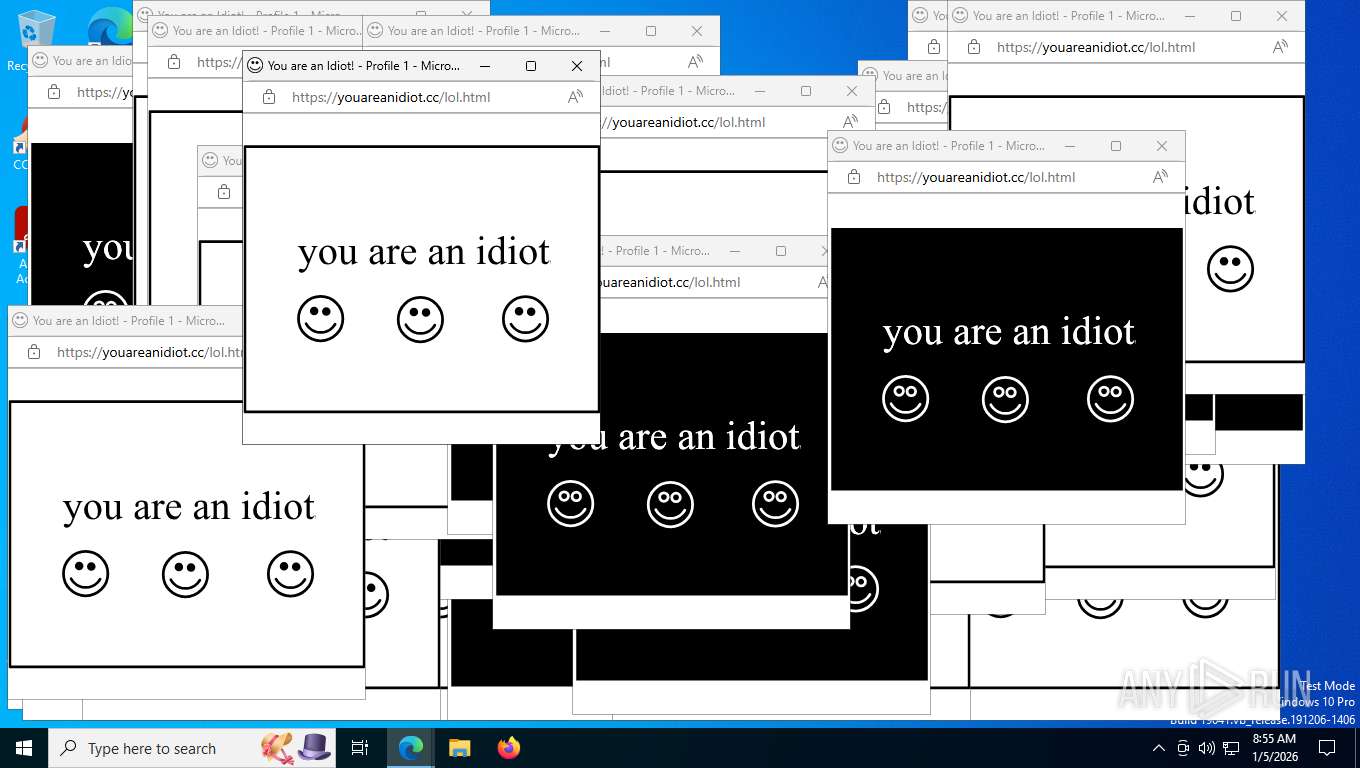
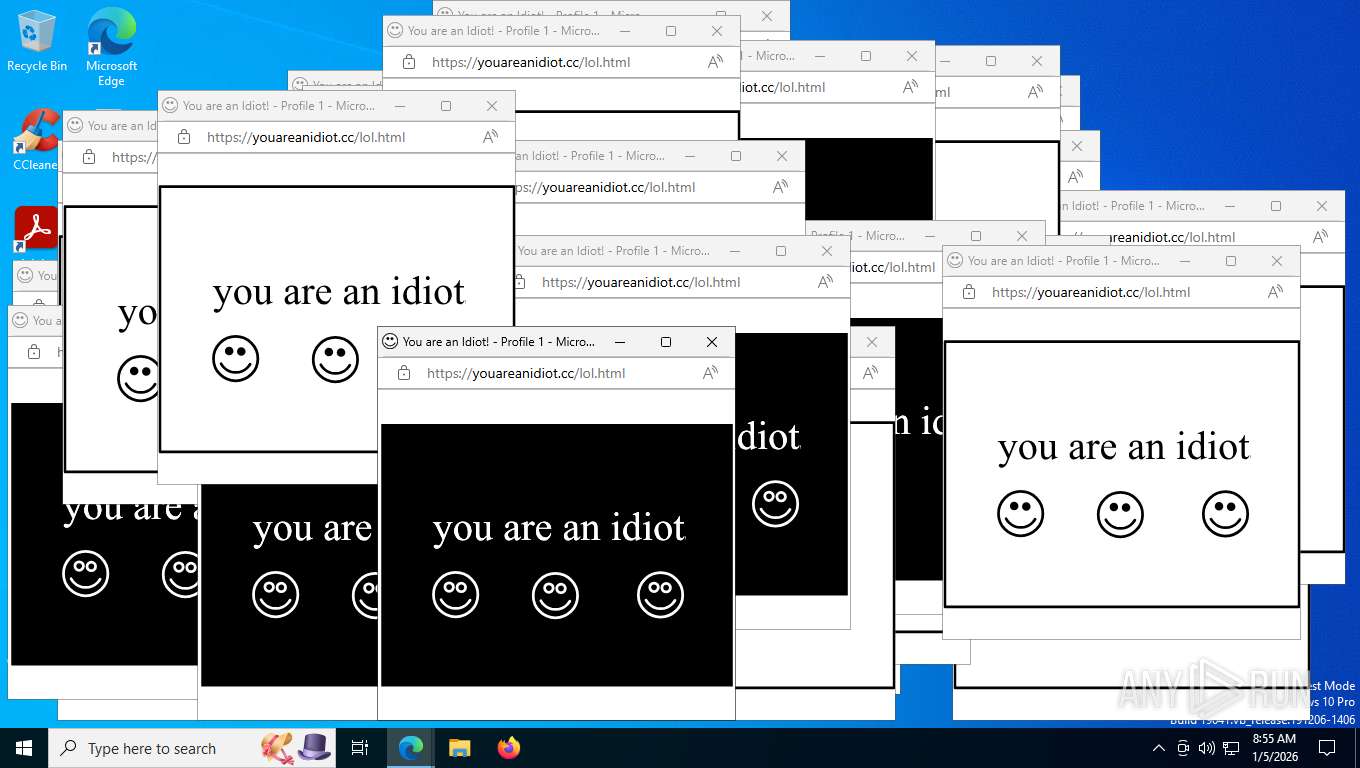
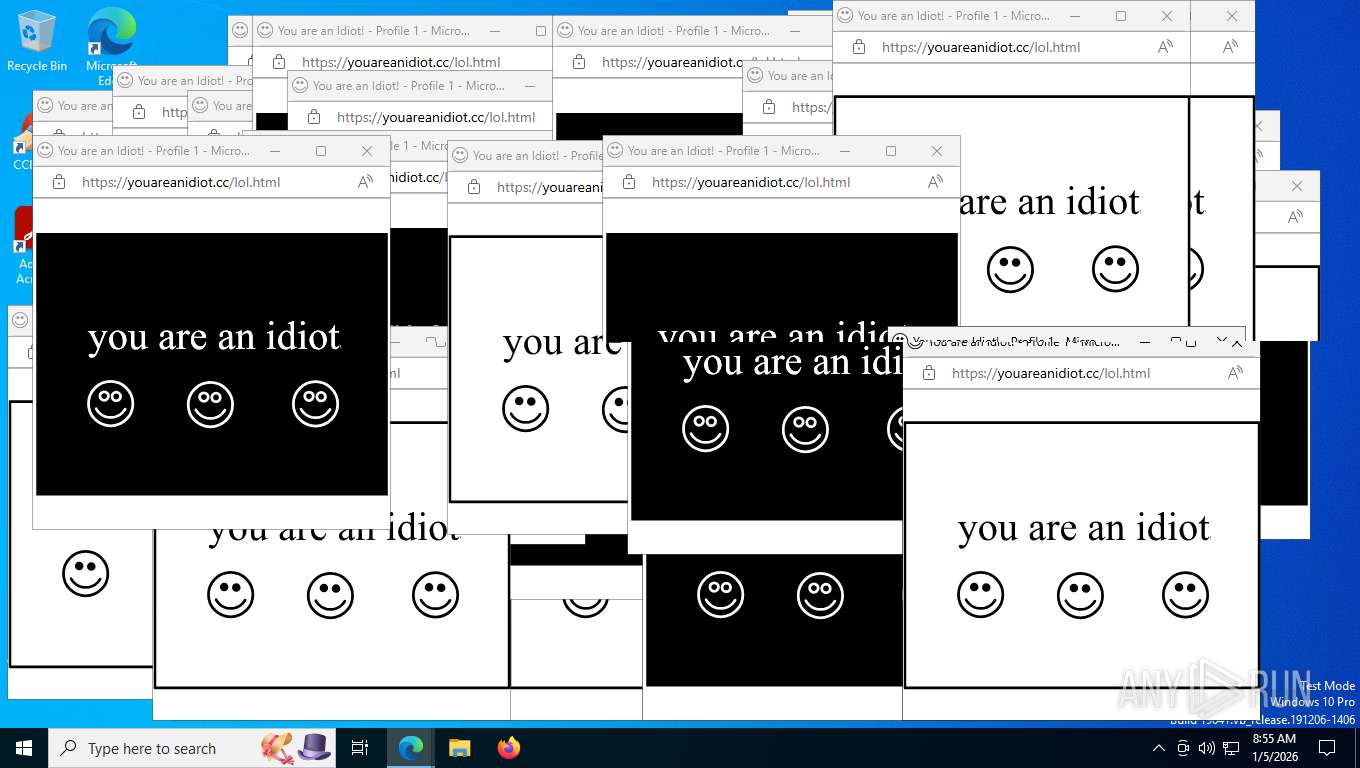
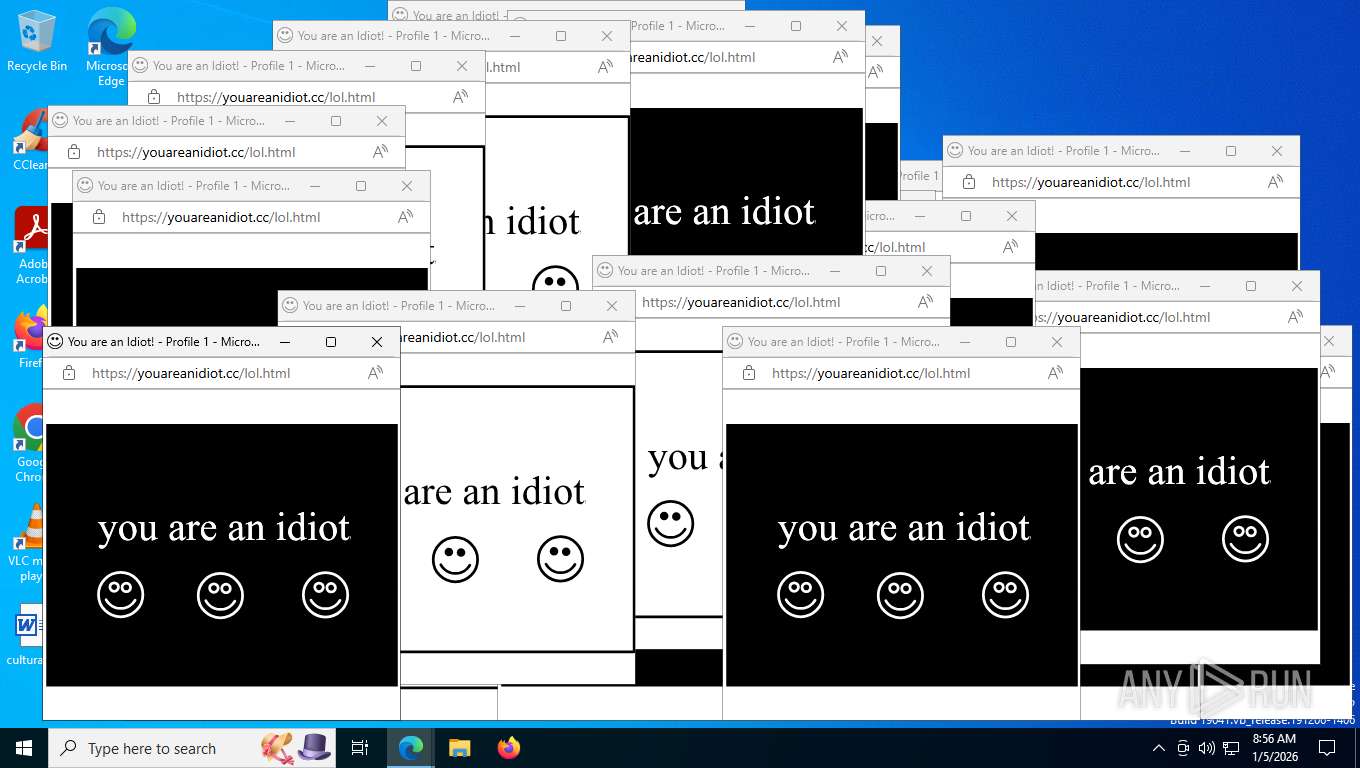
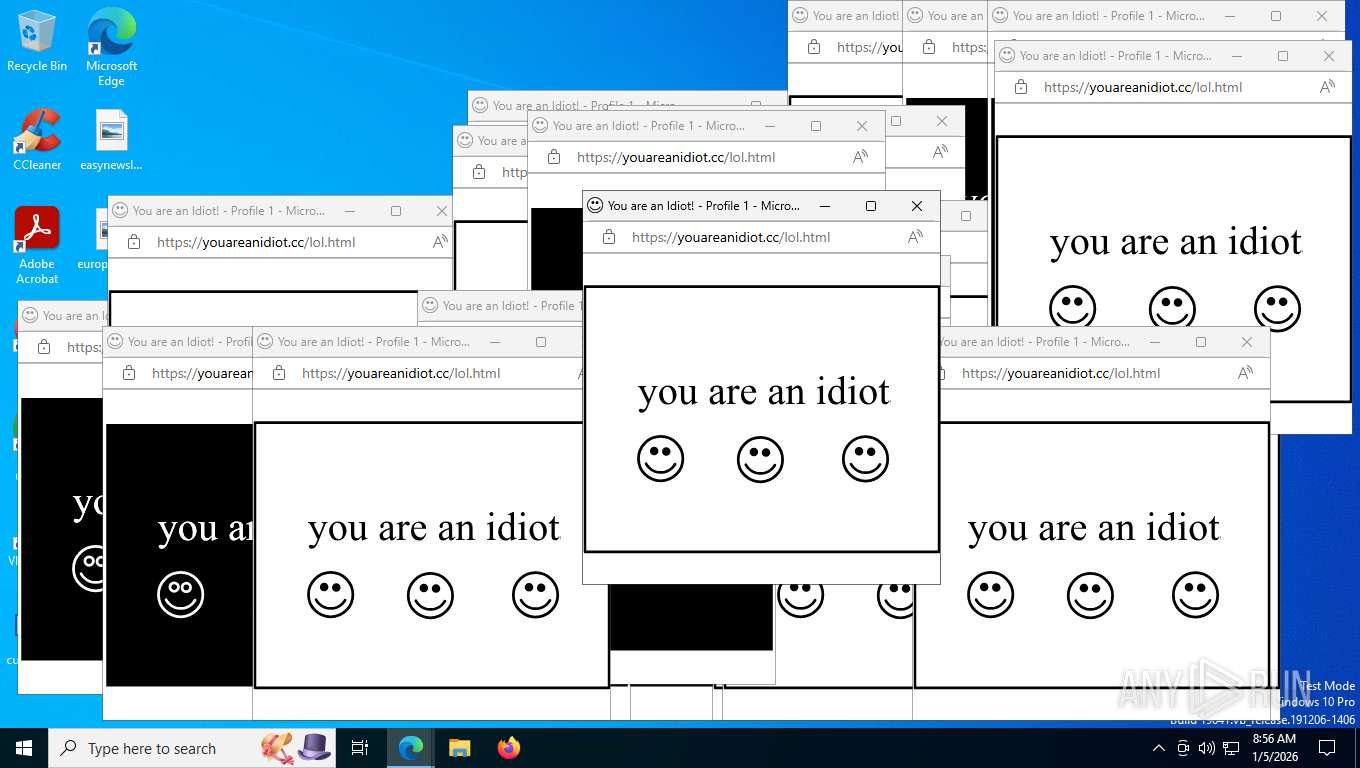
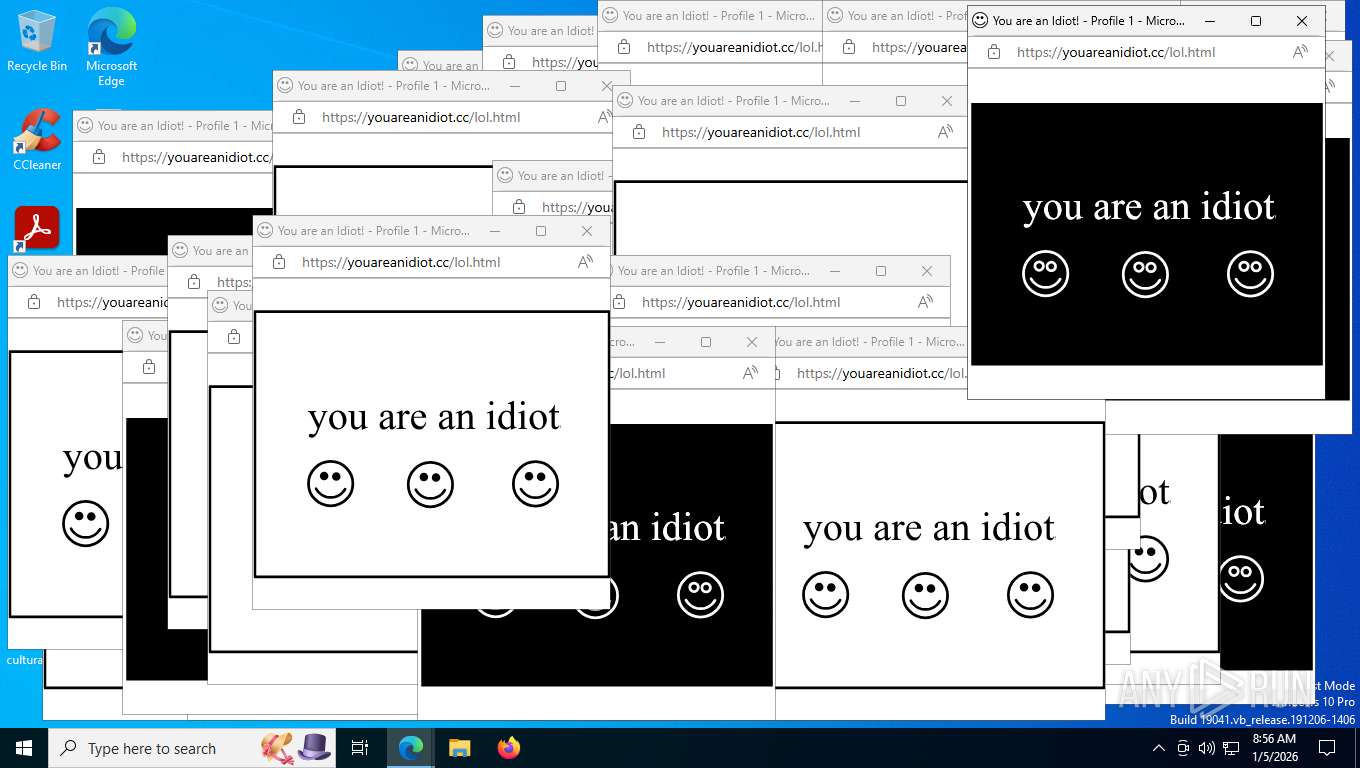
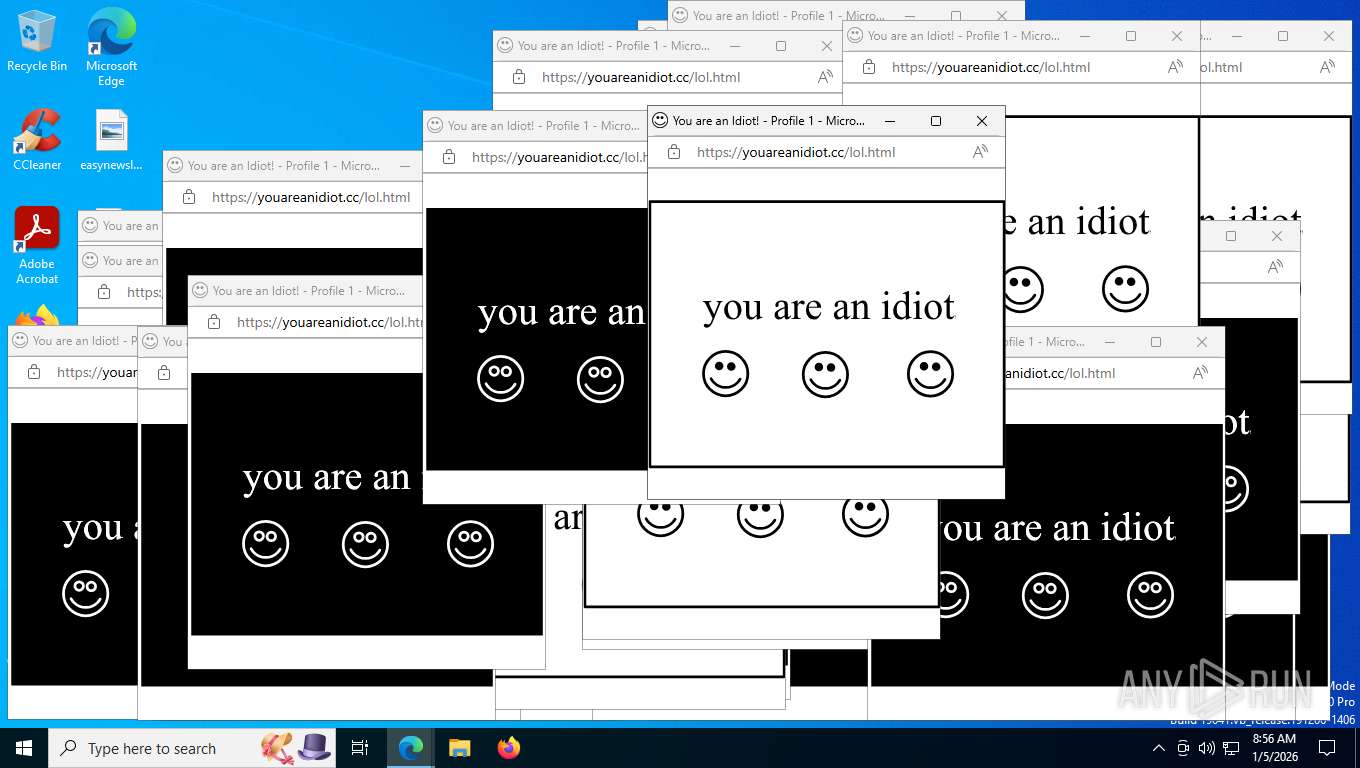
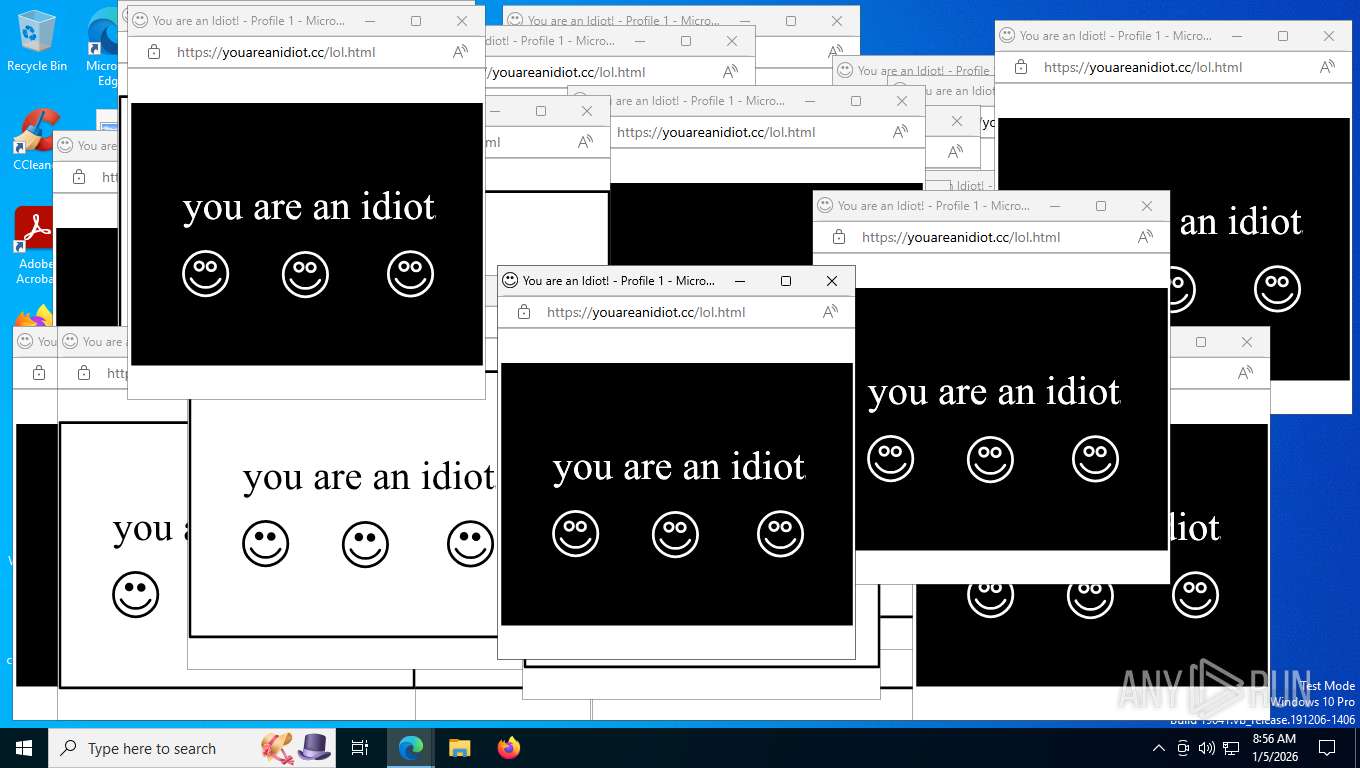
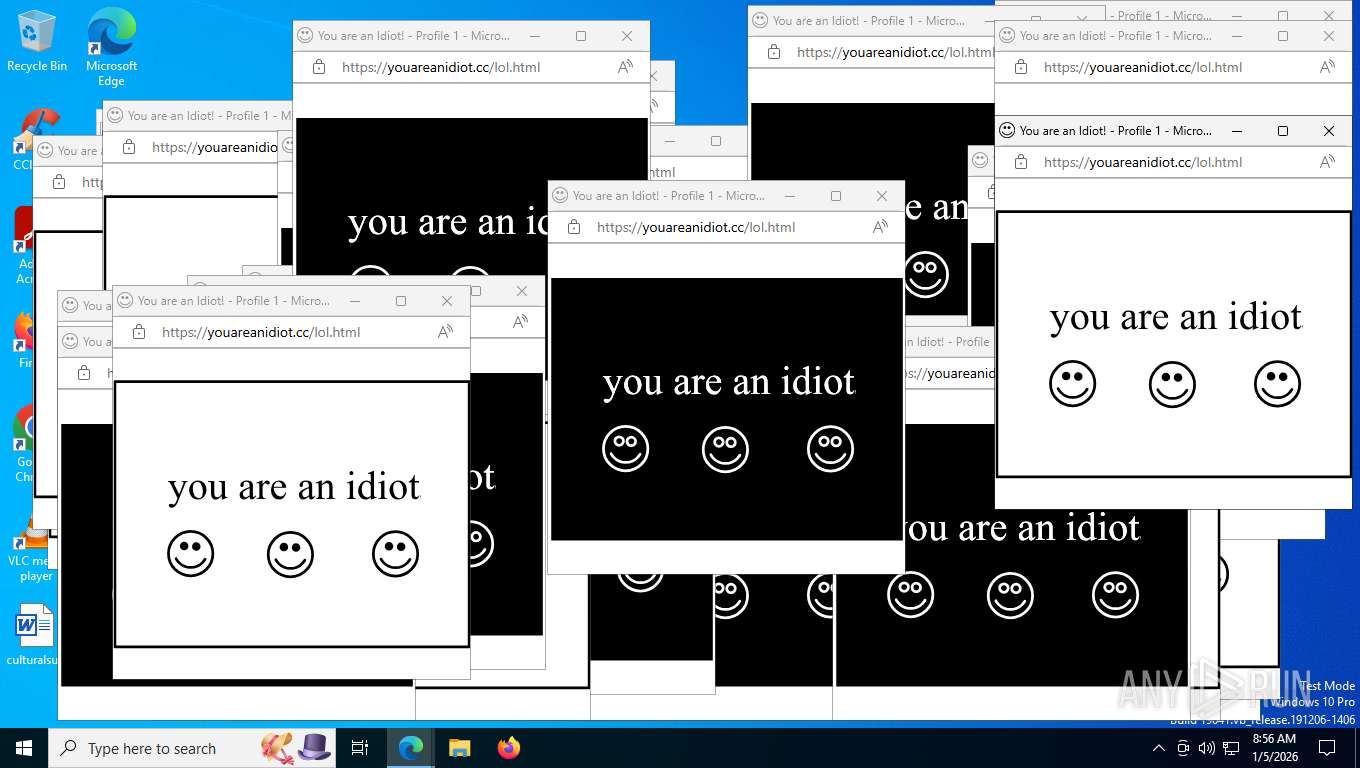
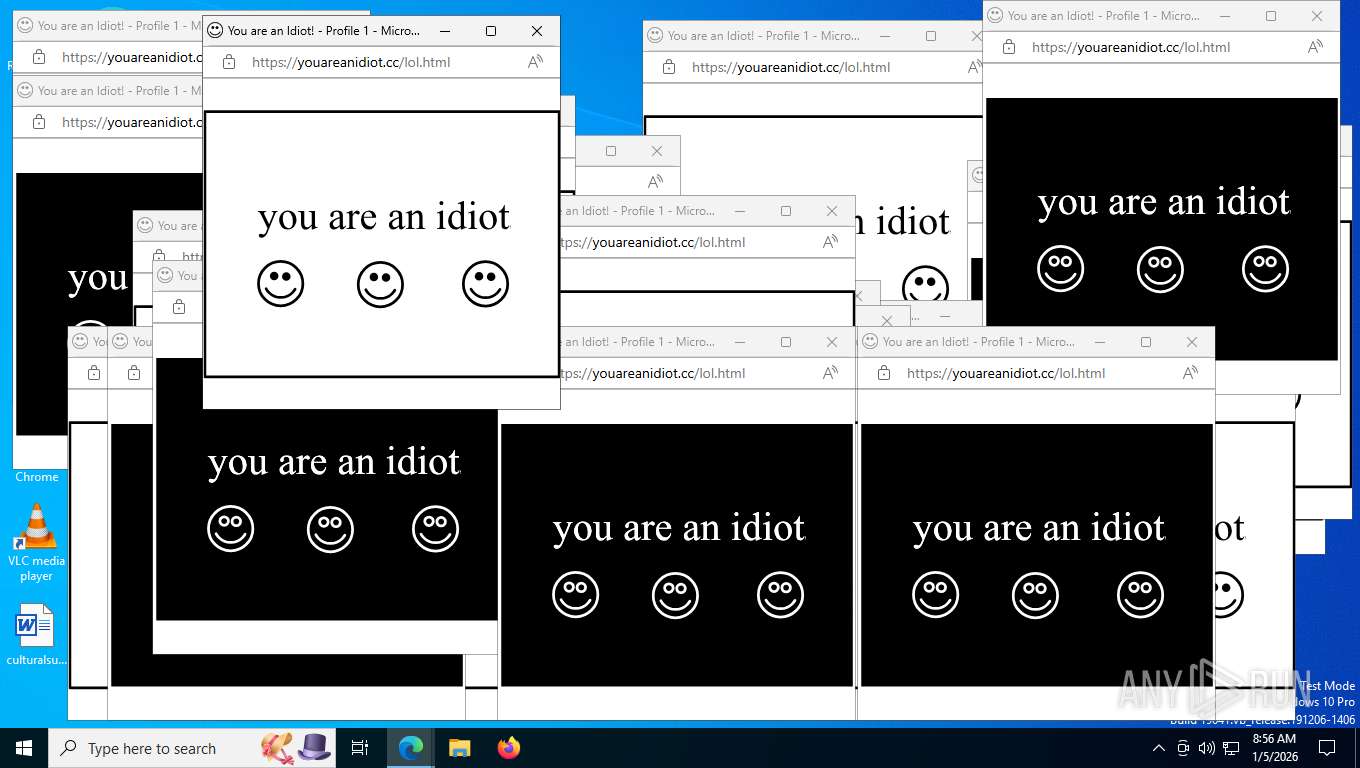
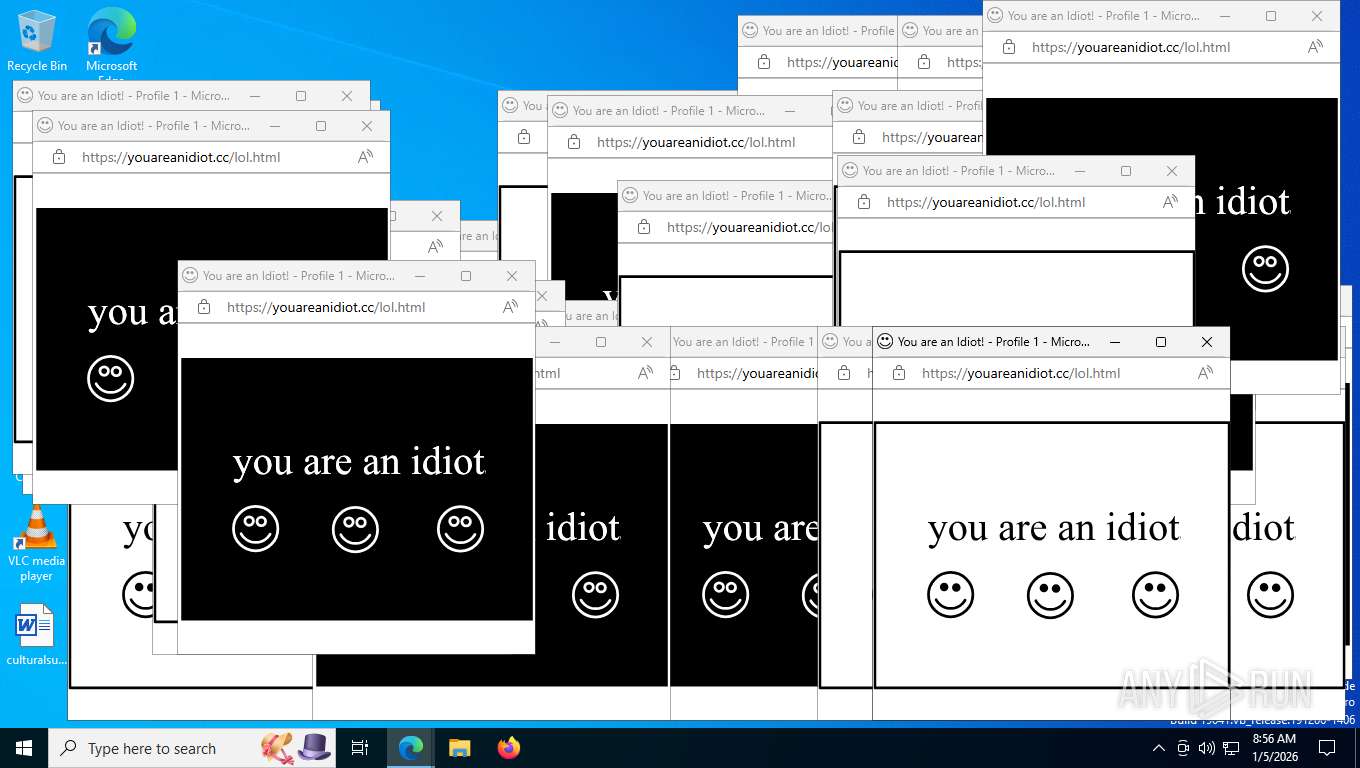
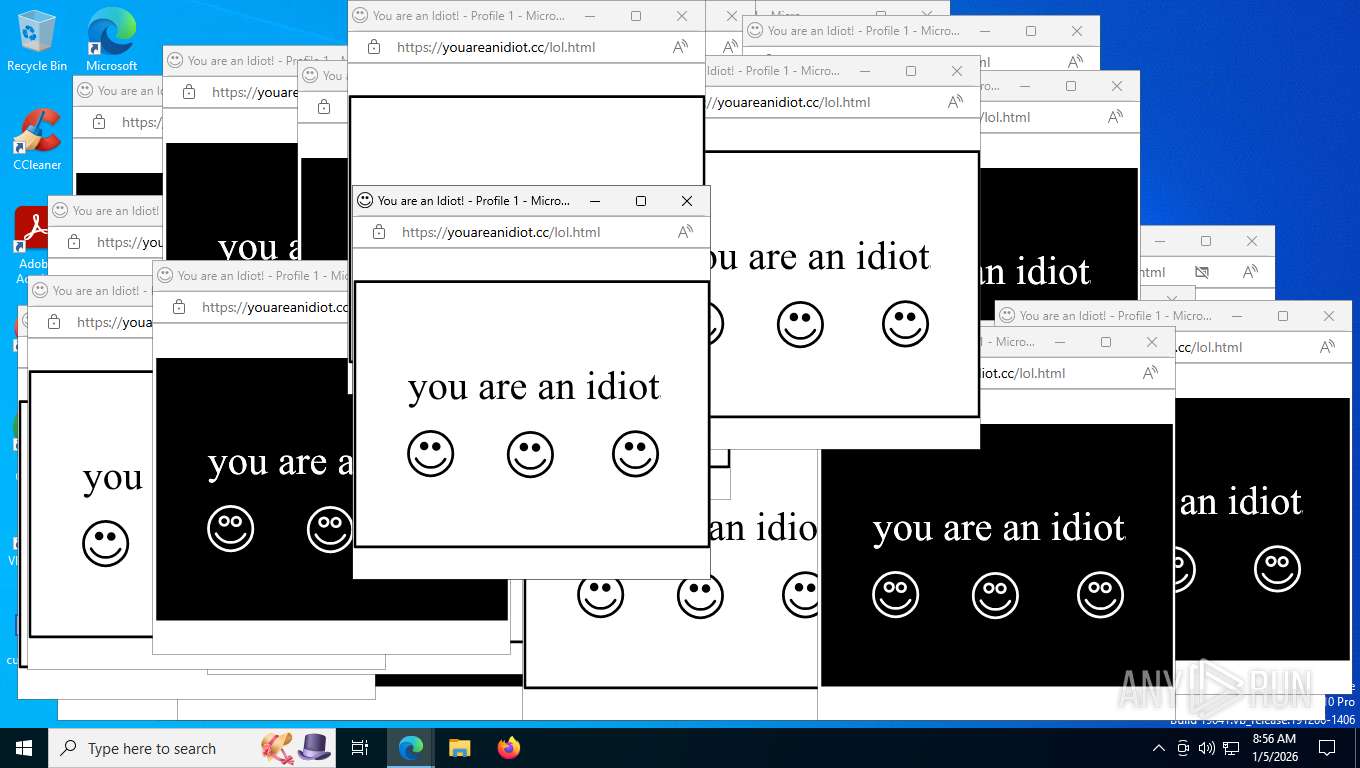
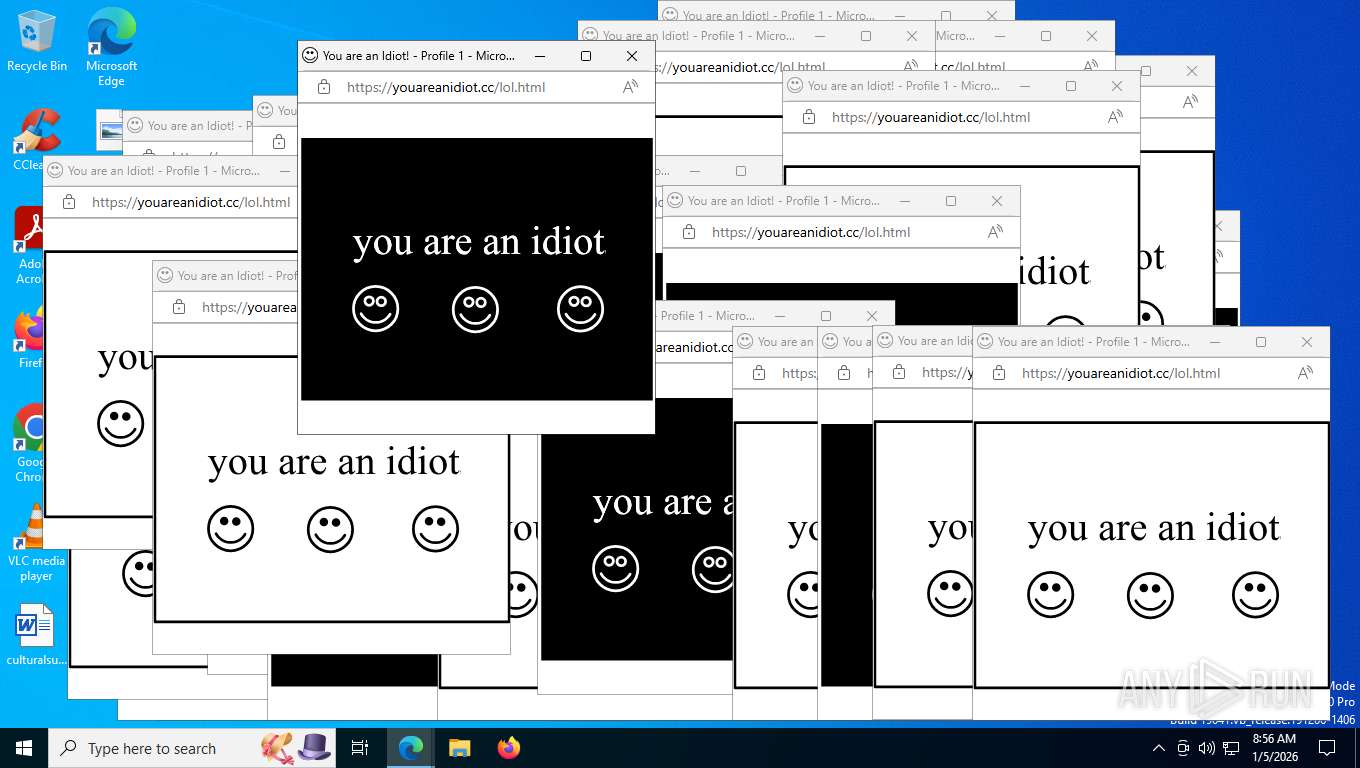
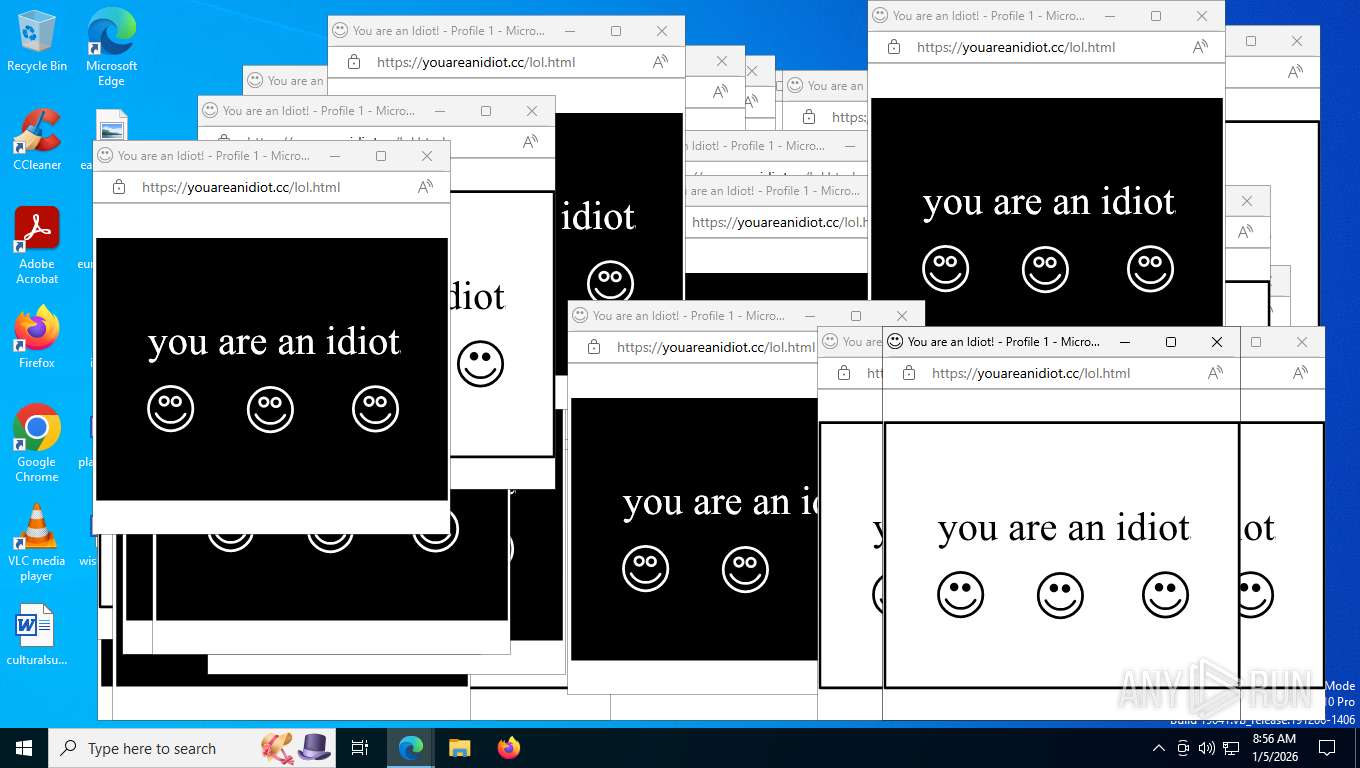
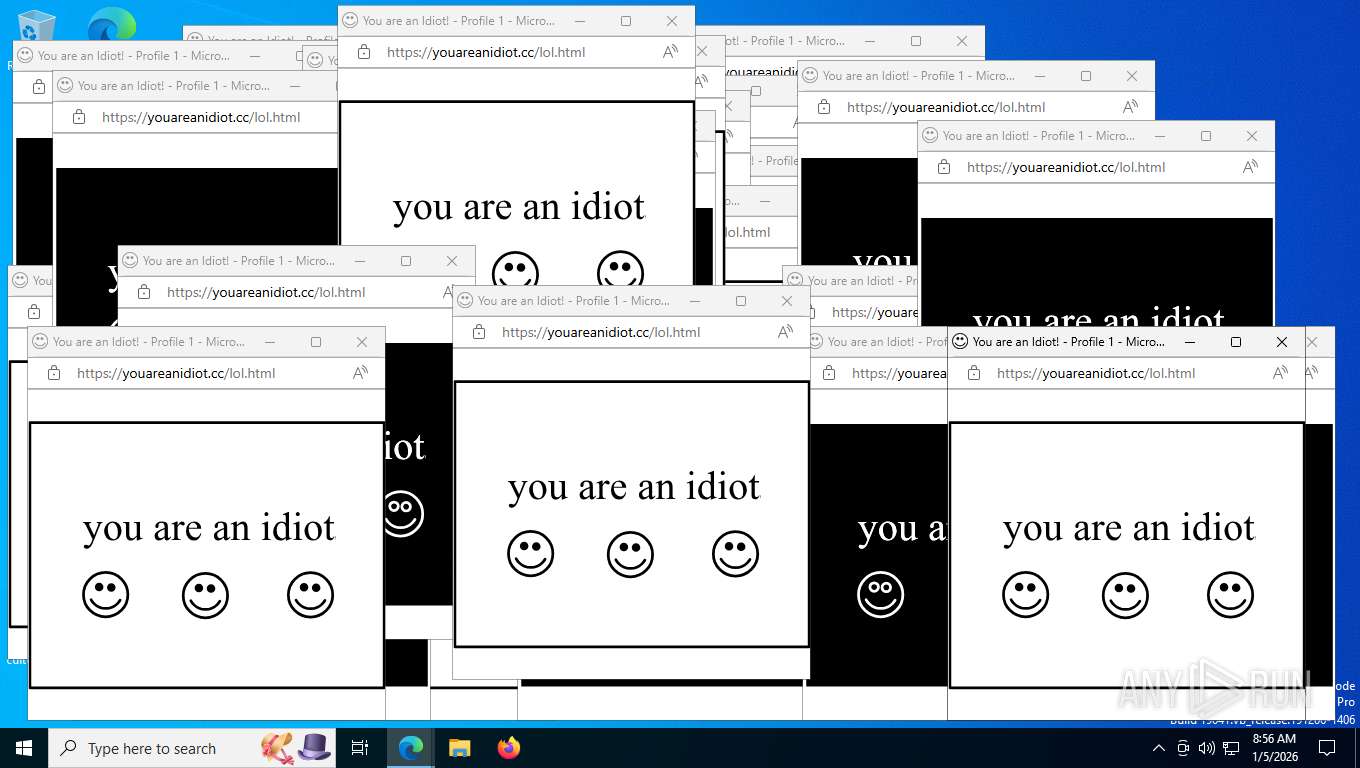
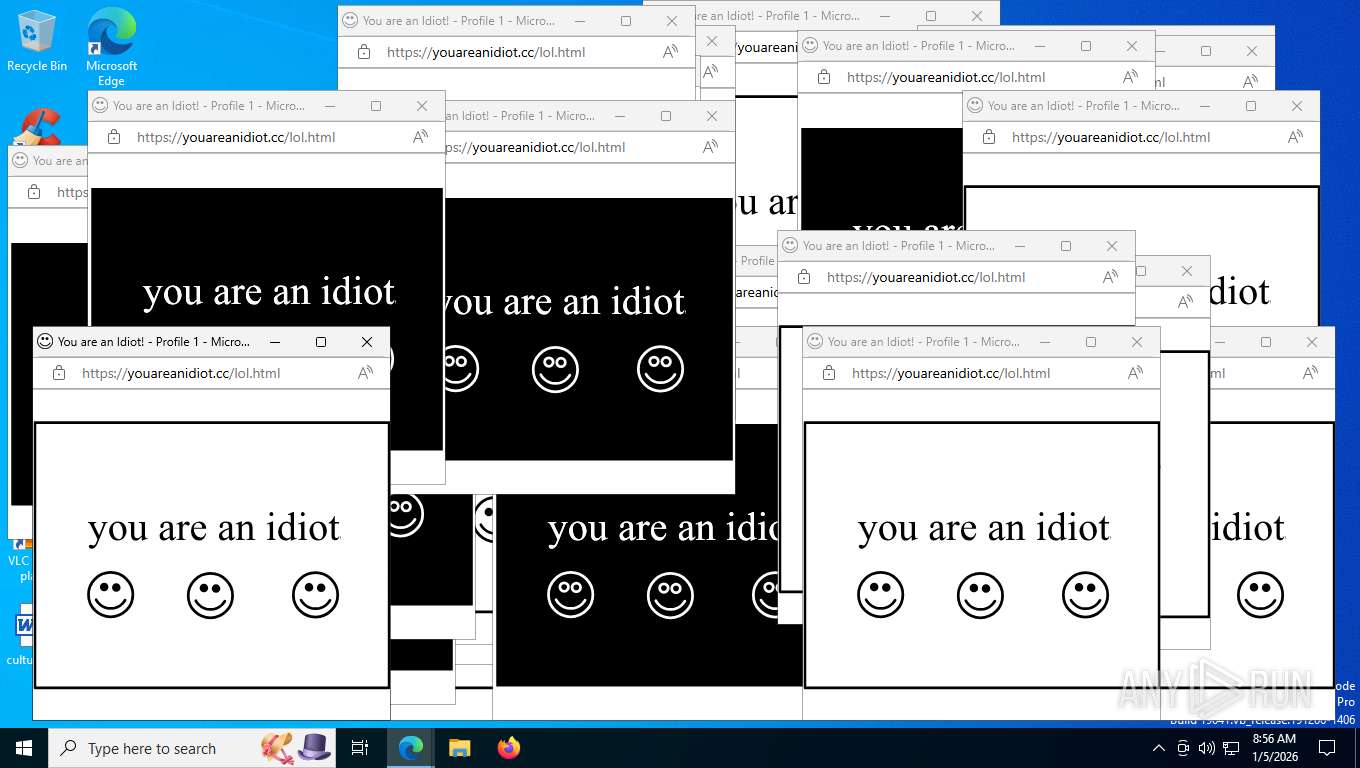
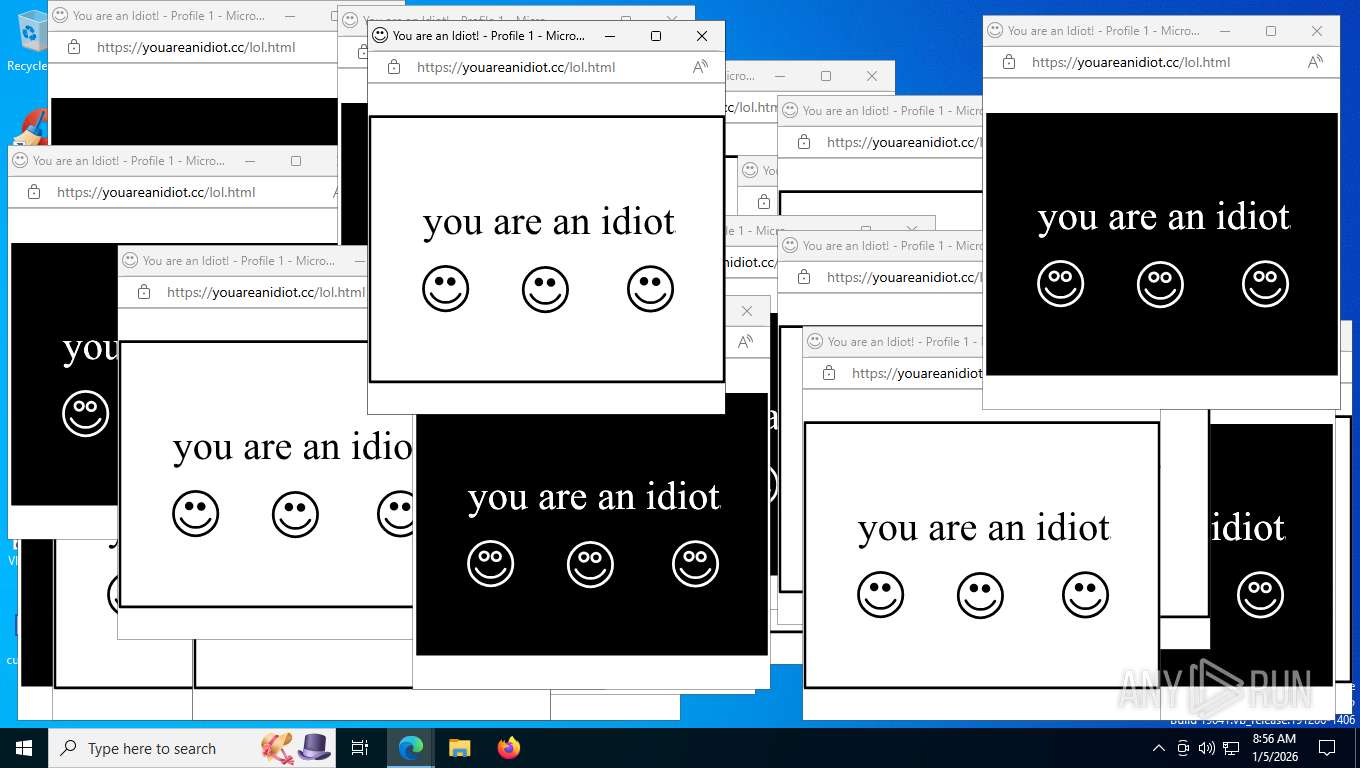
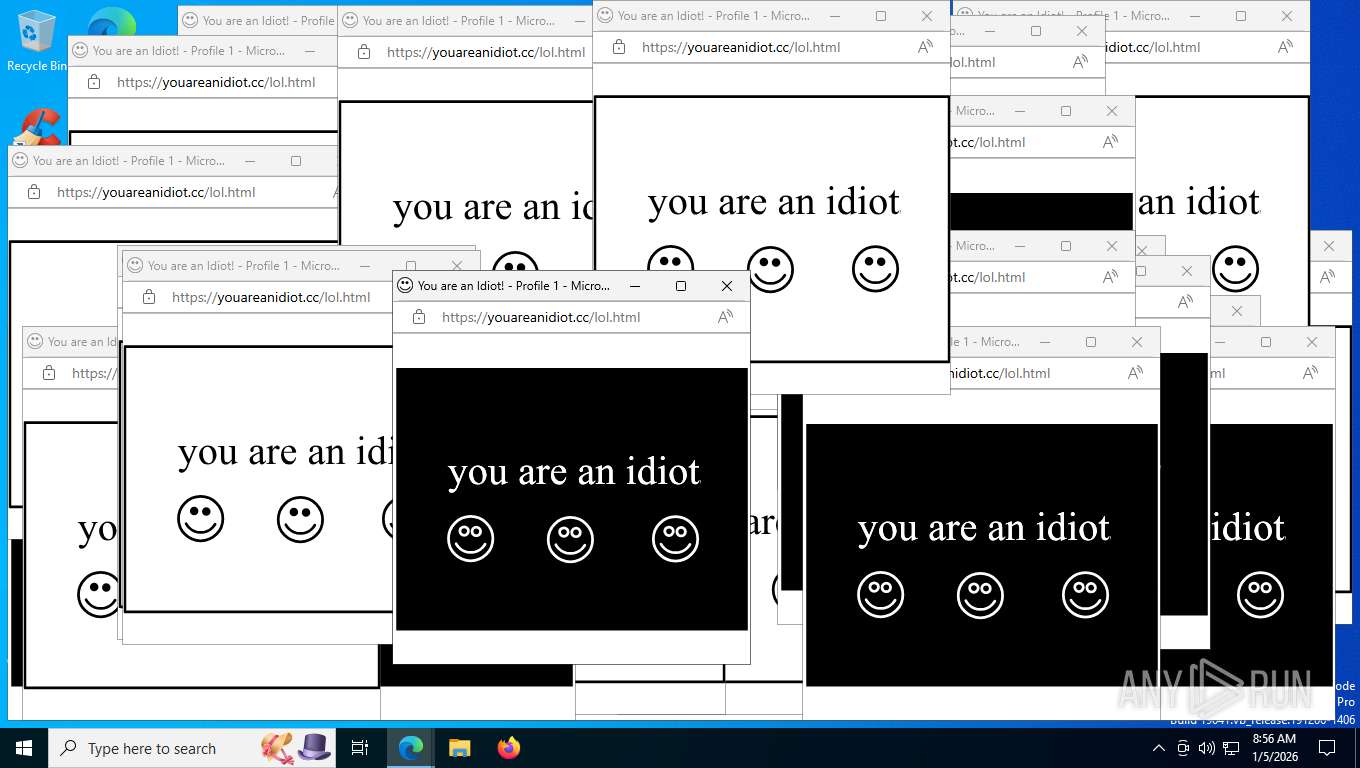
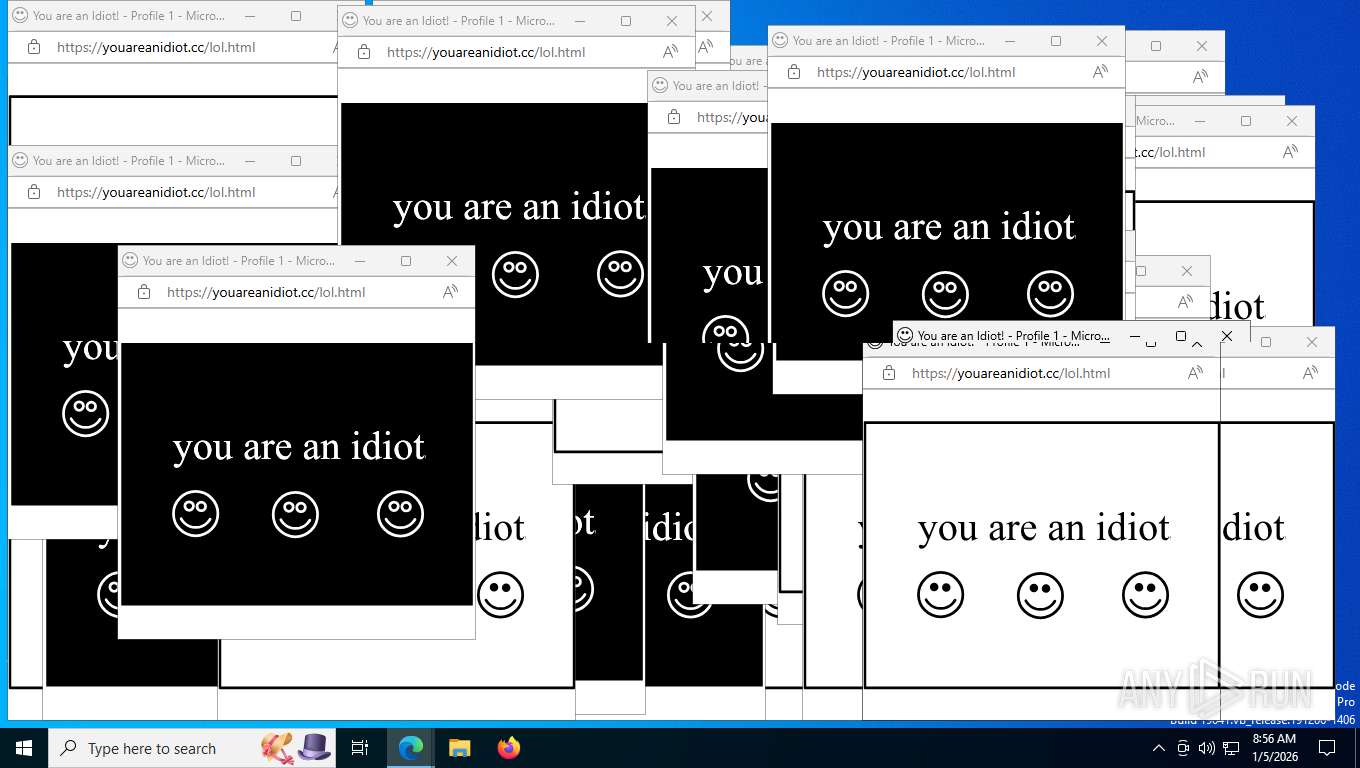
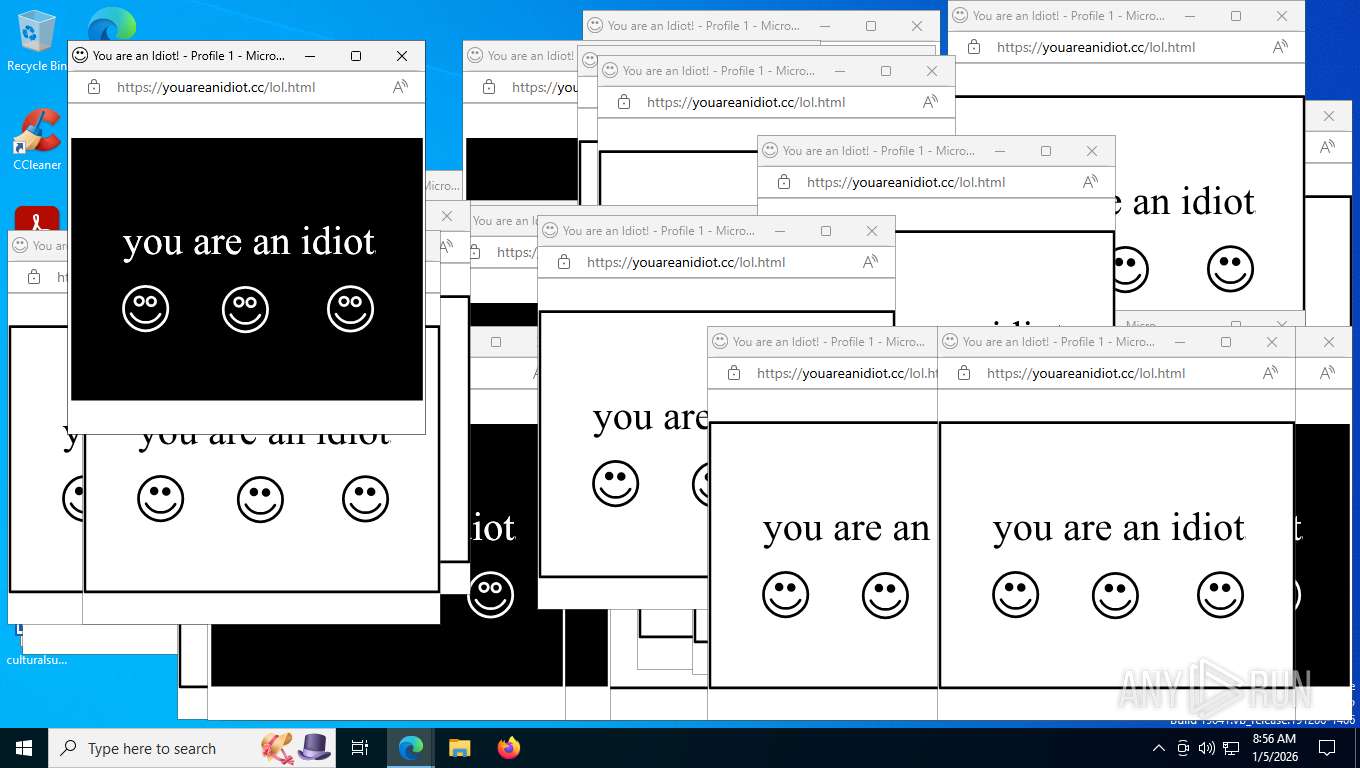
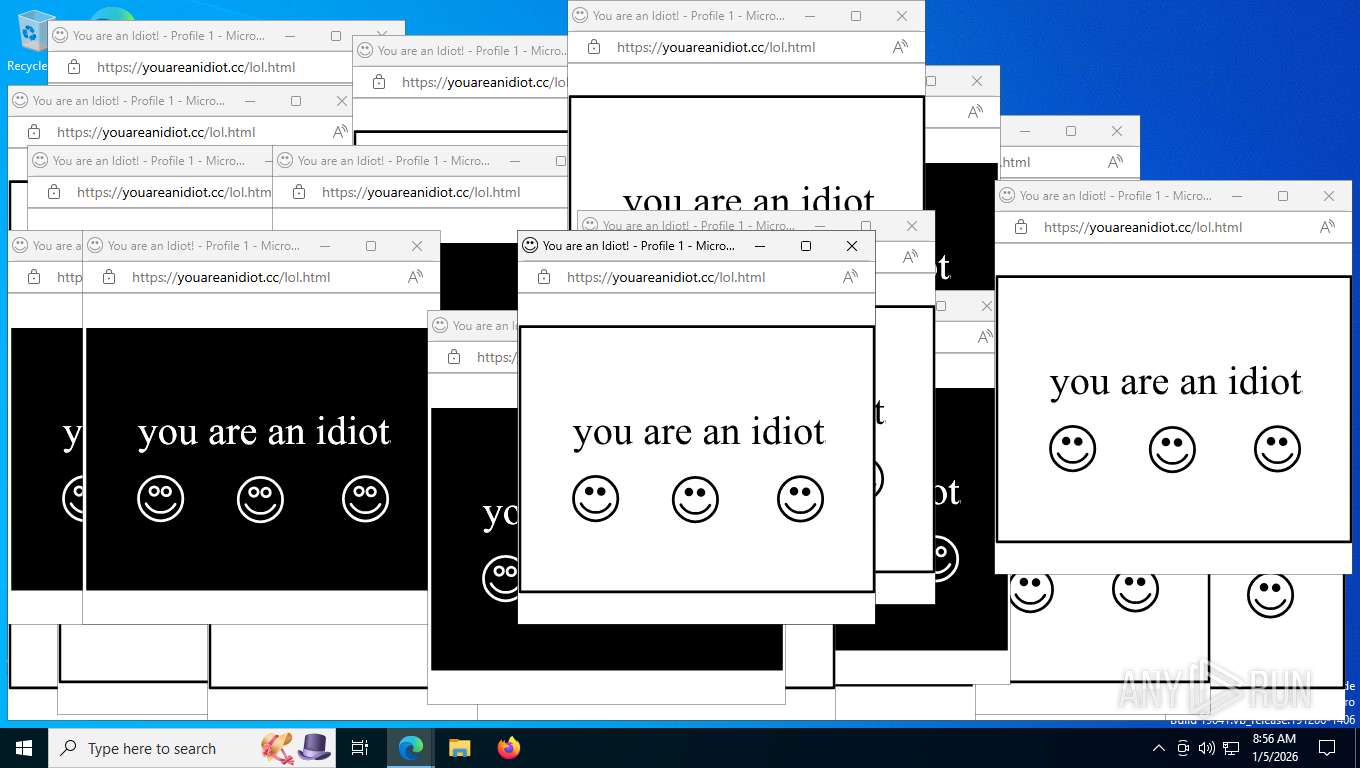
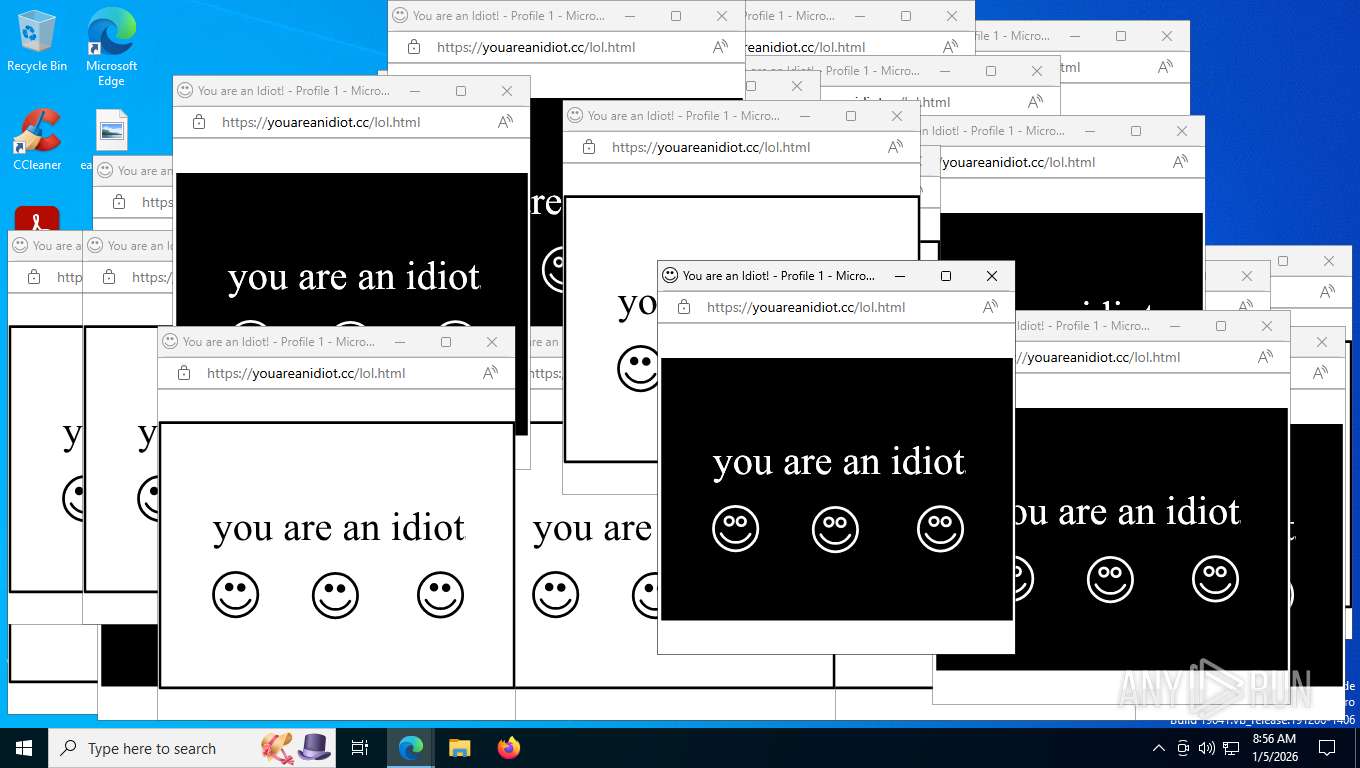
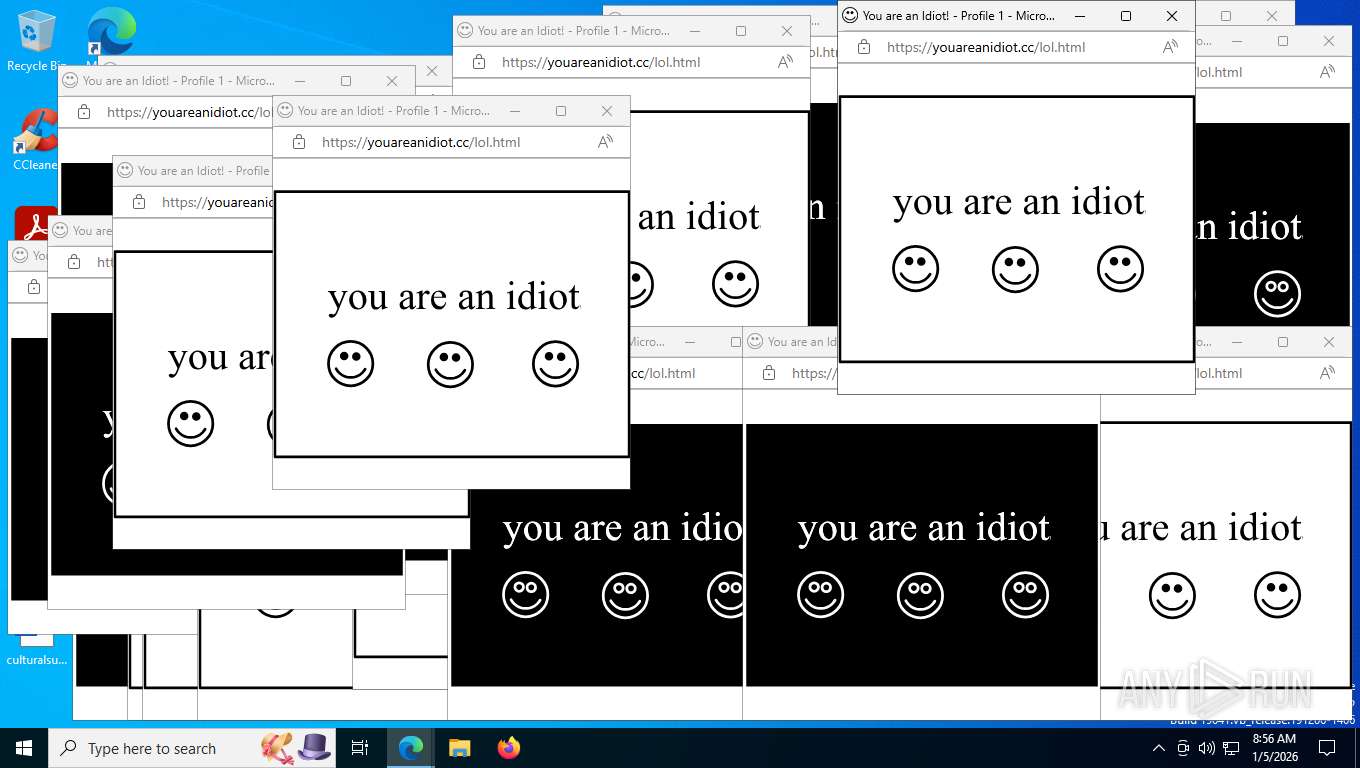
| Verdict: | Malicious activity |
| Analysis date: | January 05, 2026, 13:51:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B7EB6382A3FC193711670059D75EA3FE |
| SHA1: | CB4CA86F30D452B767DC355C27BD41D76386E589 |
| SHA256: | 7142588219C7B42BE4E76AC0769819A24487D1424970D4DB6947ED614DFADACF |
| SSDEEP: | 12:2fc1cAQEXon1zYgtRLDwWitISnnZ7fxCsfy3U+4SARIkbmrE/UyQmrE/Uyd:2fehQEXg1E2tDwWit7nnCHUNJRPMyyMM |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
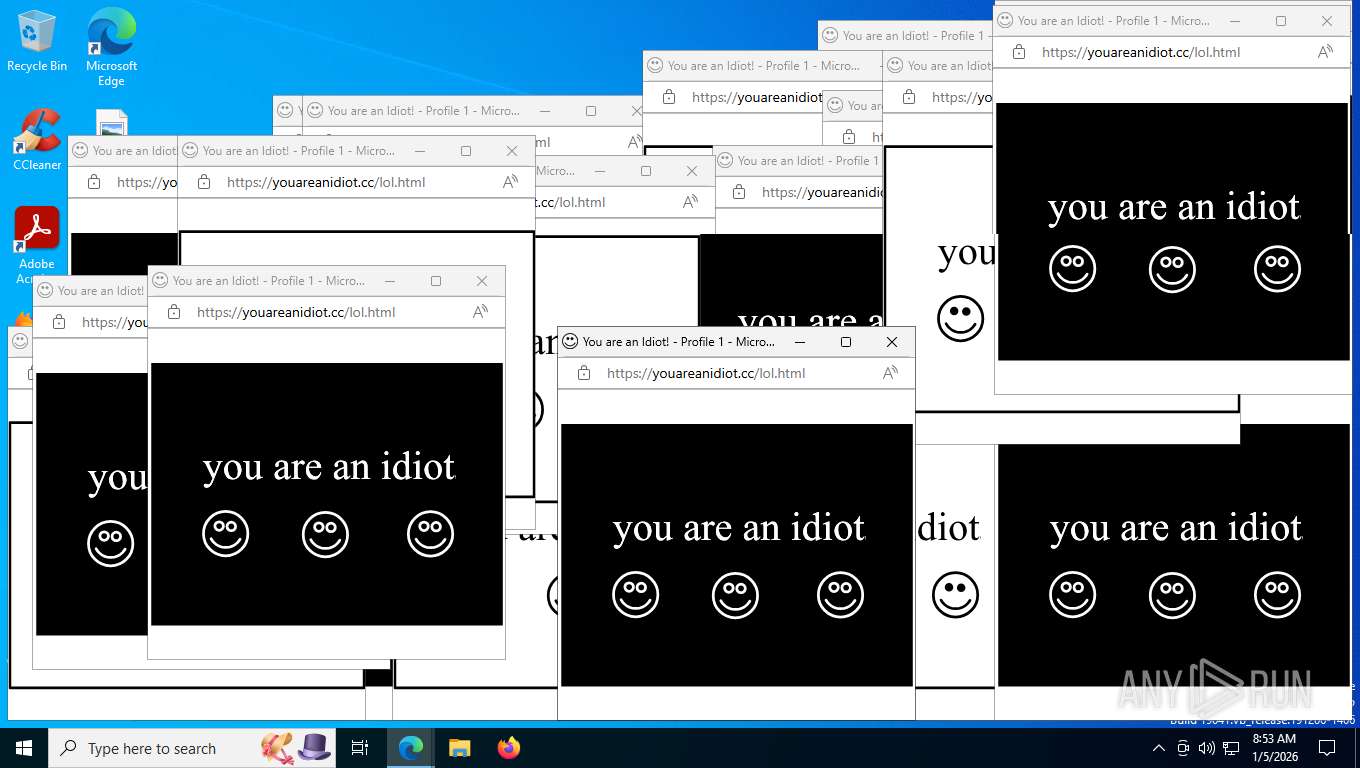
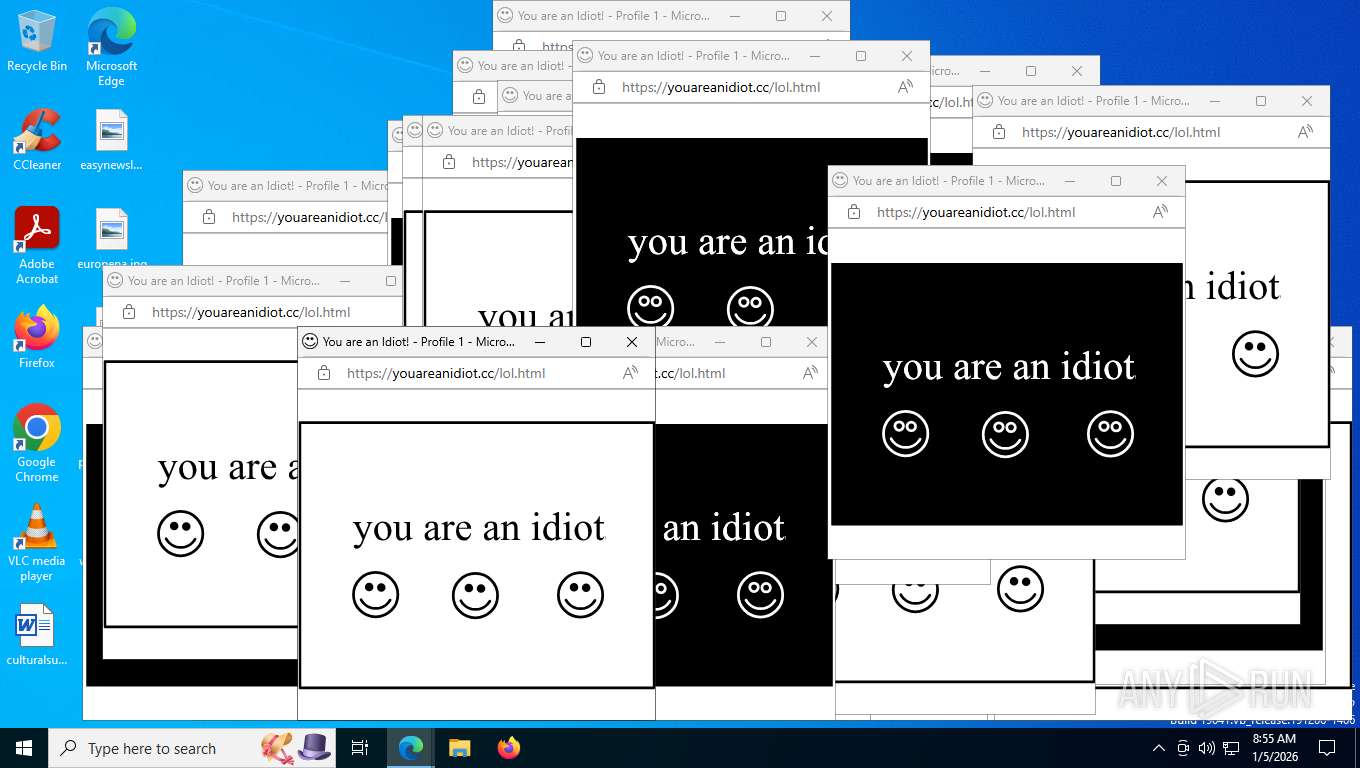
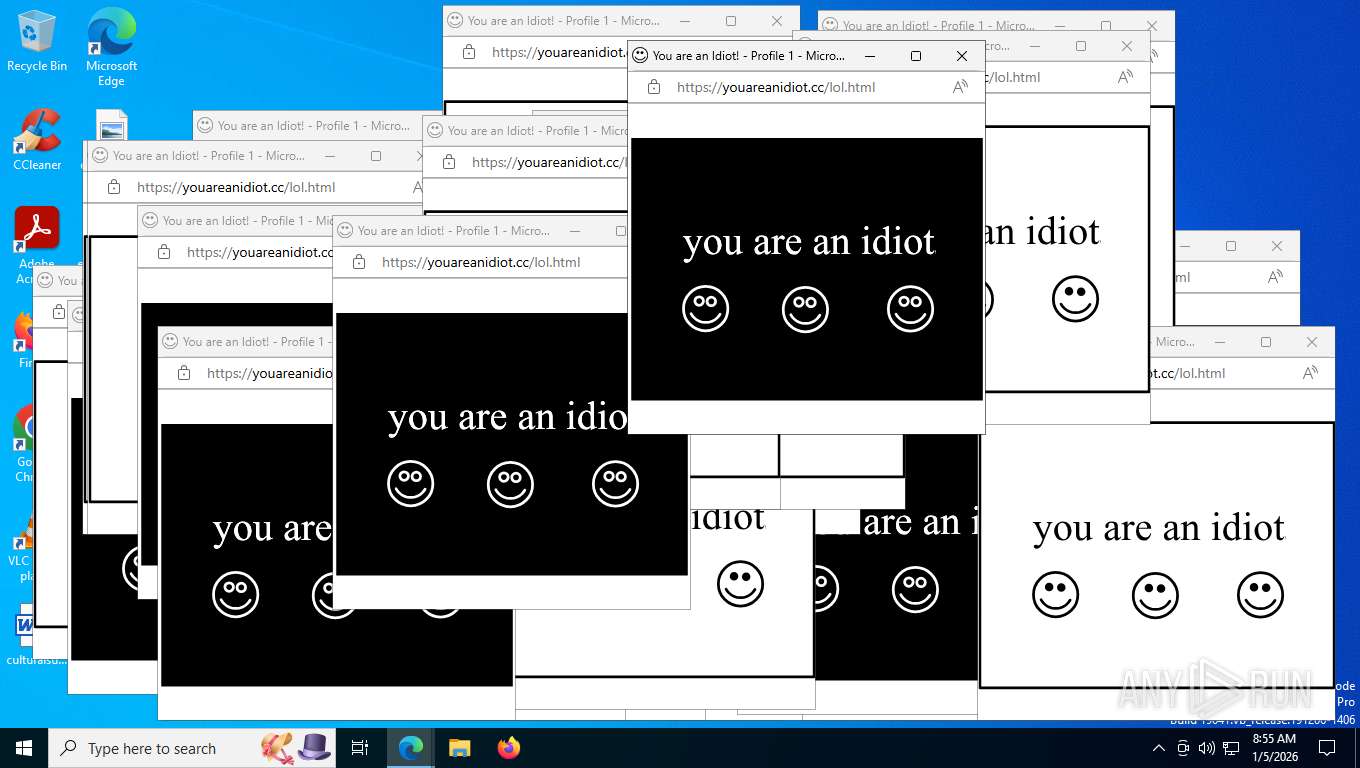
Application launched itself
- msedge.exe (PID: 7484)
Reads the computer name
- identity_helper.exe (PID: 6916)
- TextInputHost.exe (PID: 5304)
Checks supported languages
- identity_helper.exe (PID: 6916)
- TextInputHost.exe (PID: 5304)
Reads Environment values
- identity_helper.exe (PID: 6916)
Checks proxy server information
- slui.exe (PID: 5336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
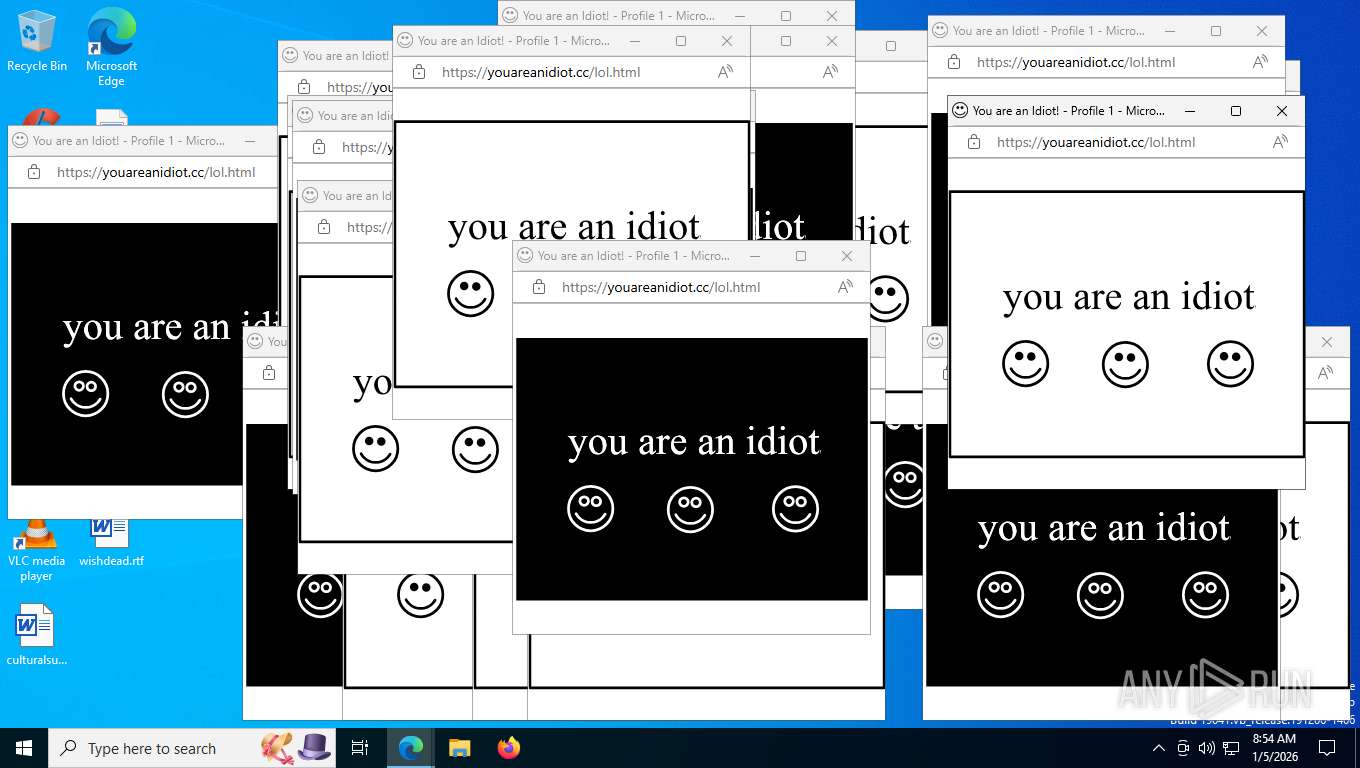
Total processes
183
Monitored processes
32
Malicious processes
0
Suspicious processes
0
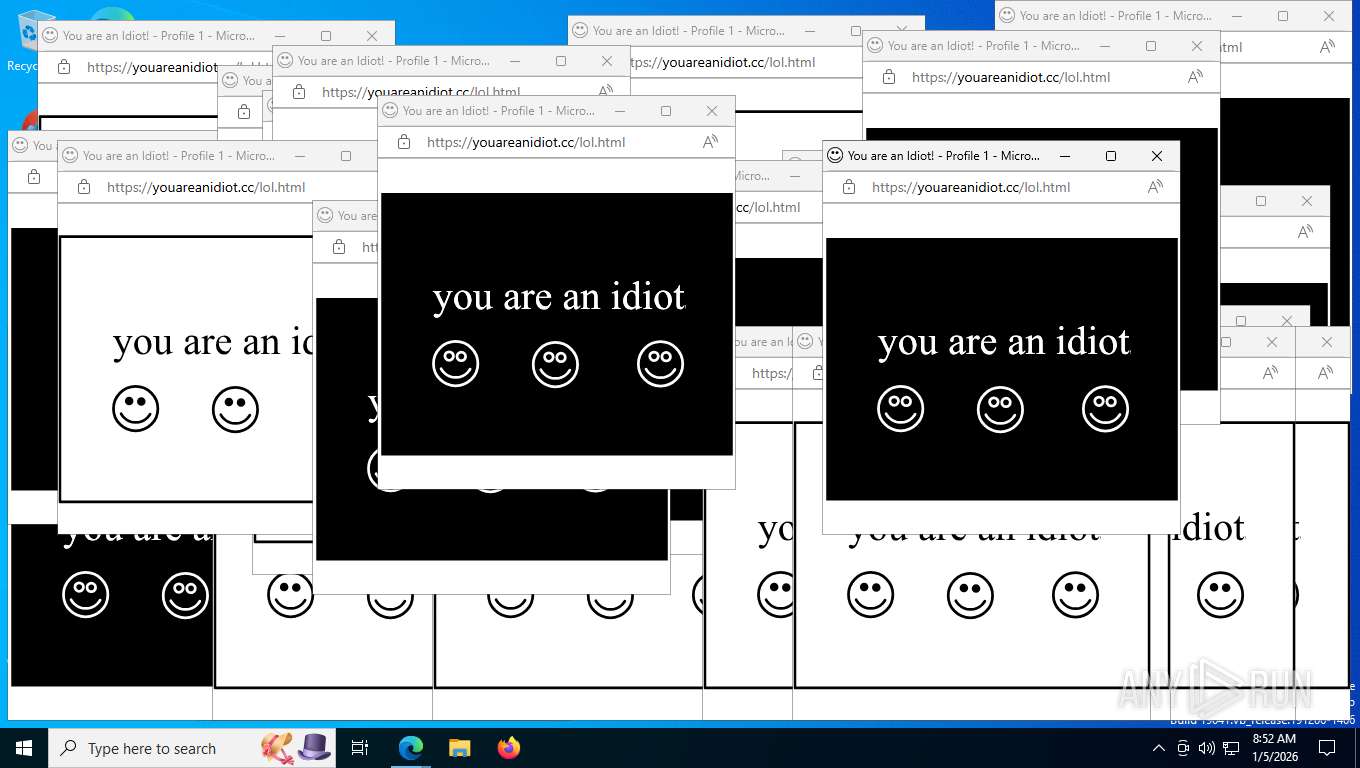
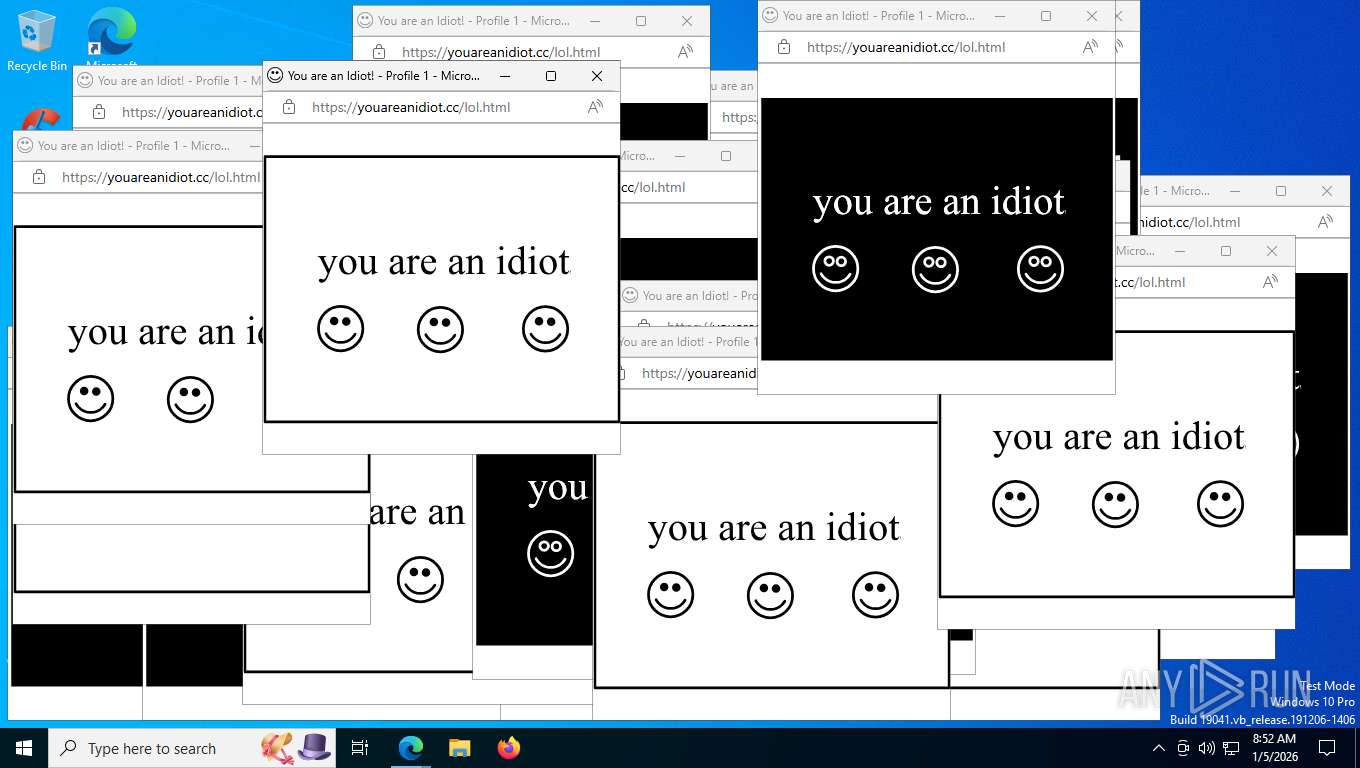
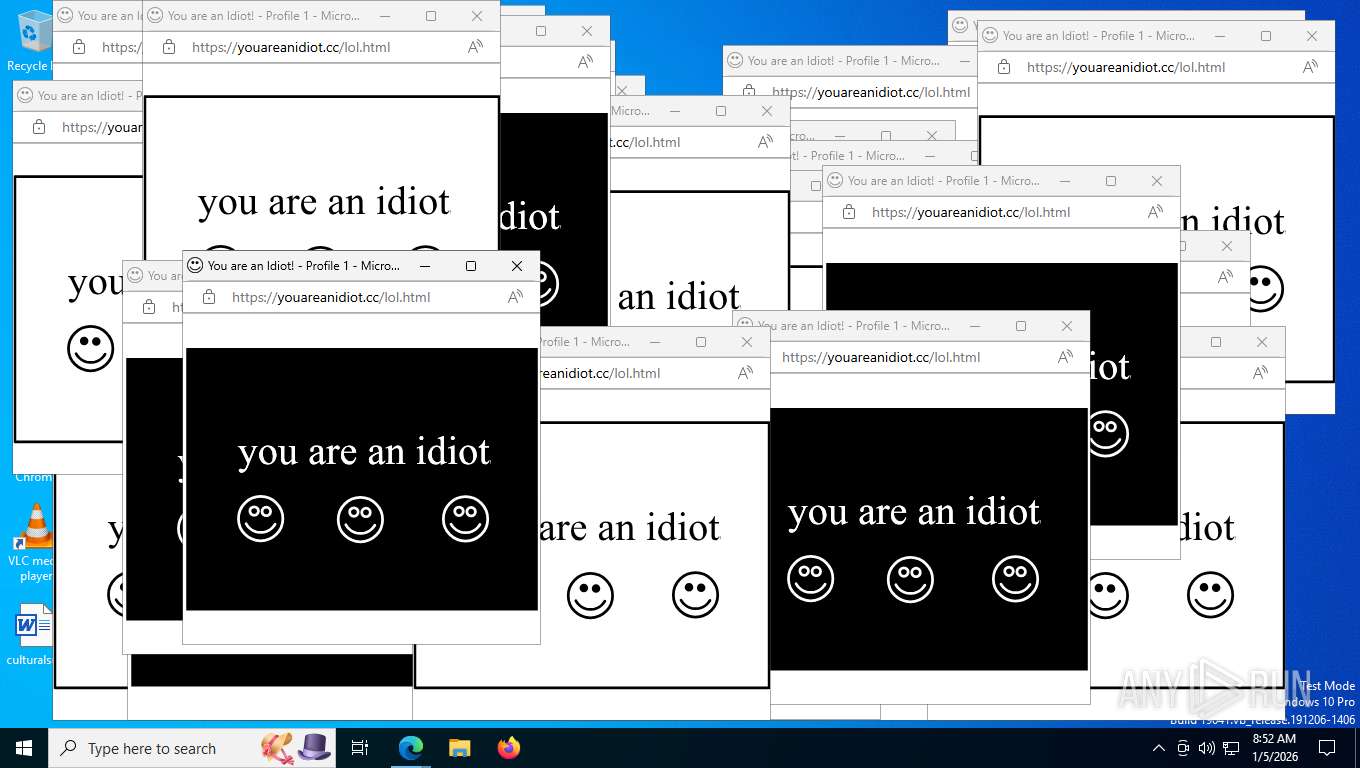
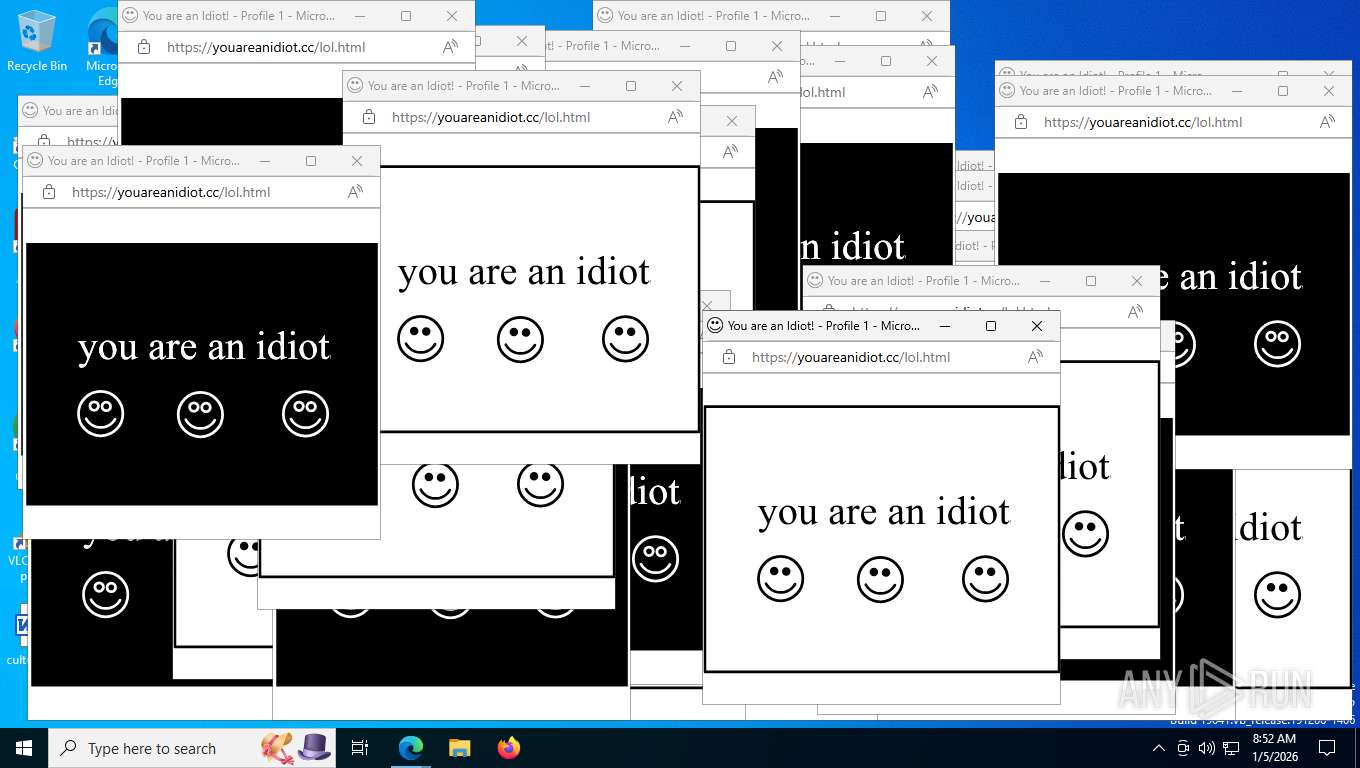
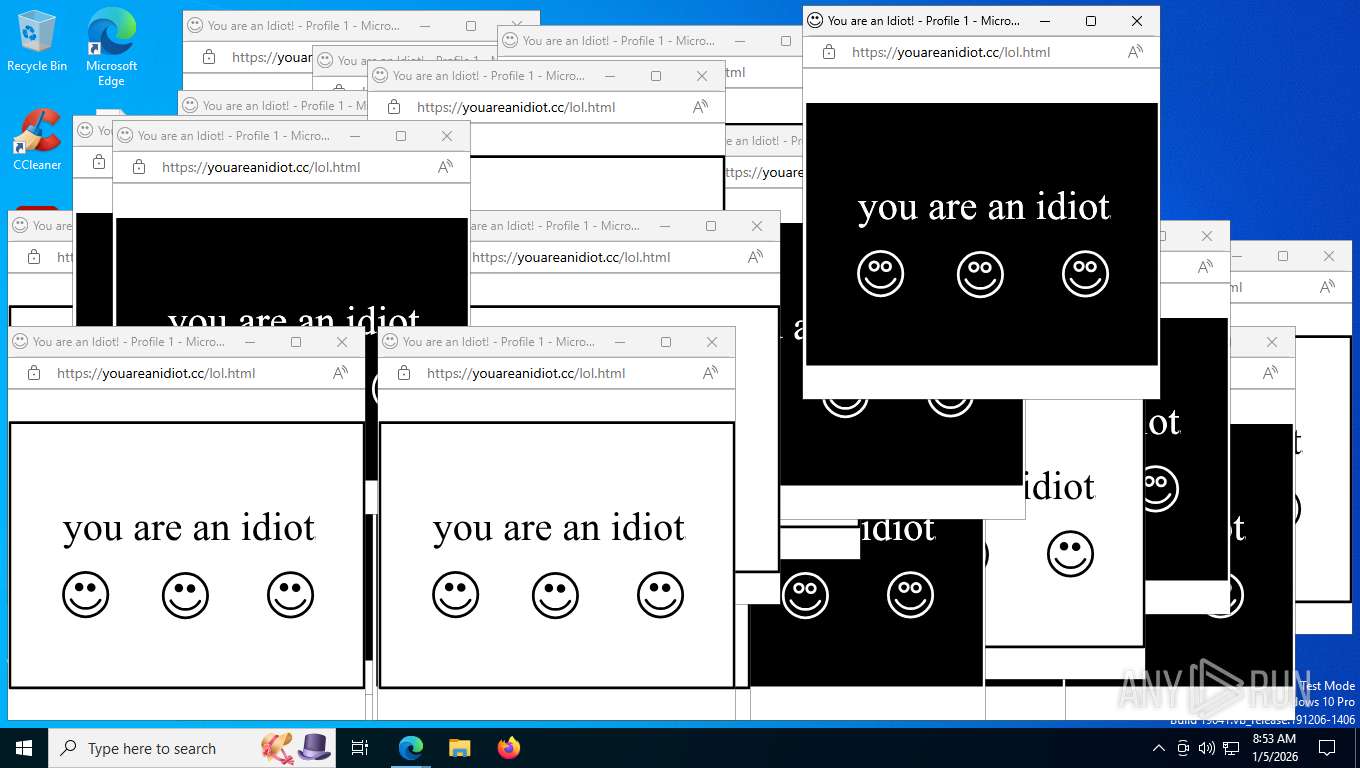
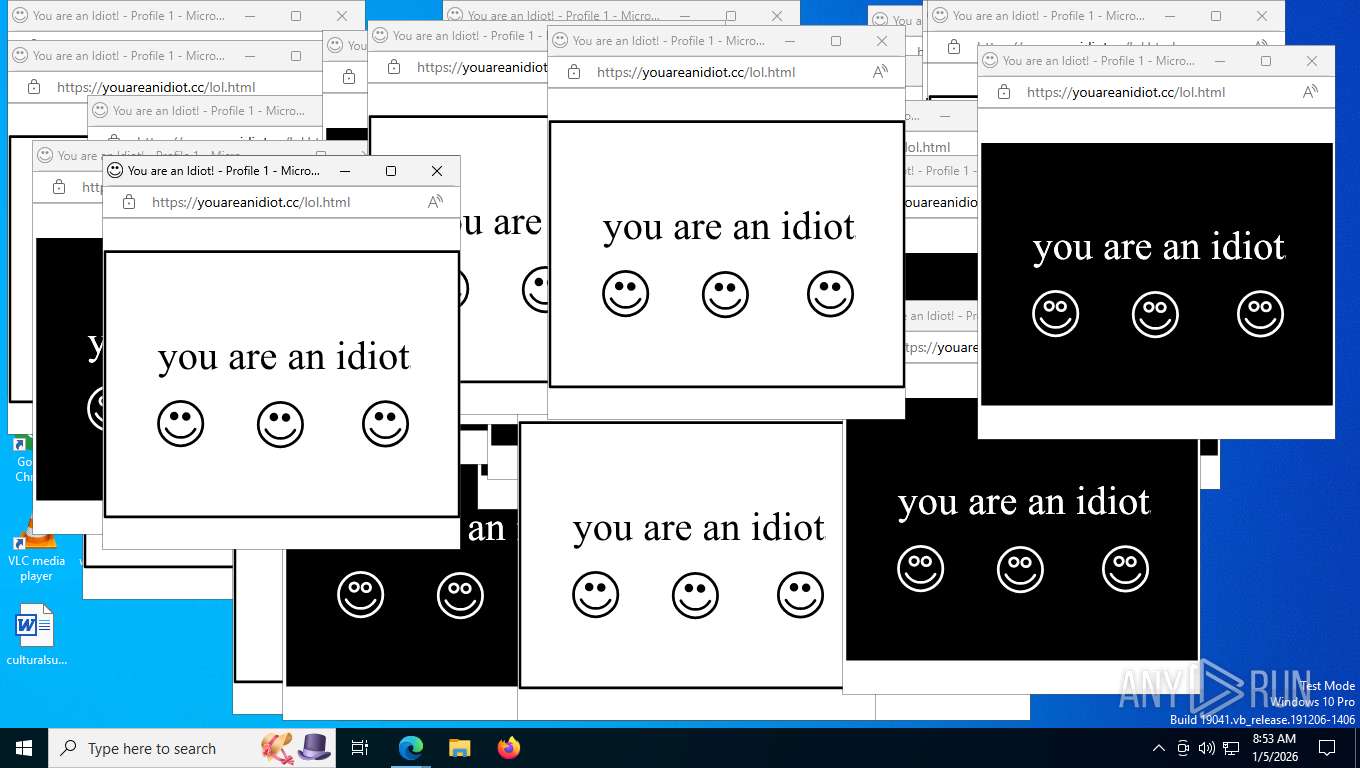
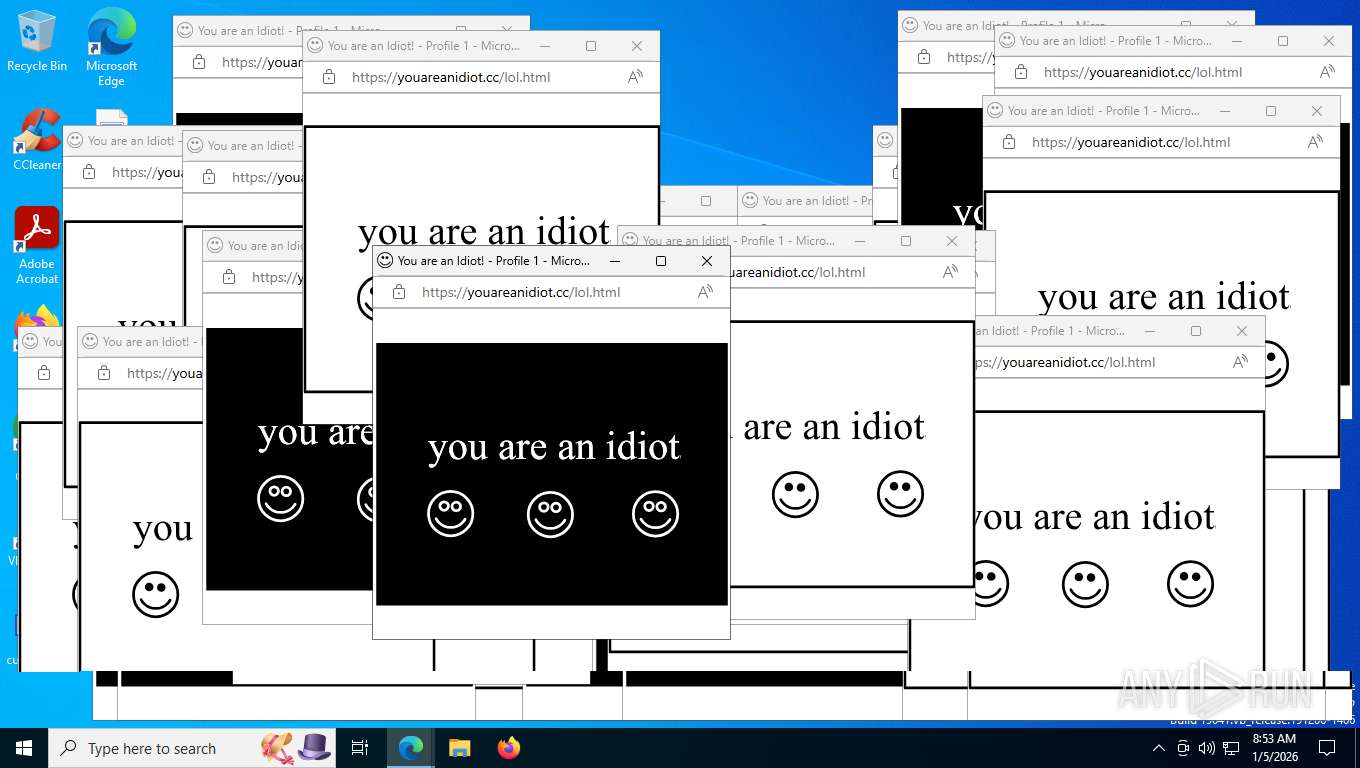
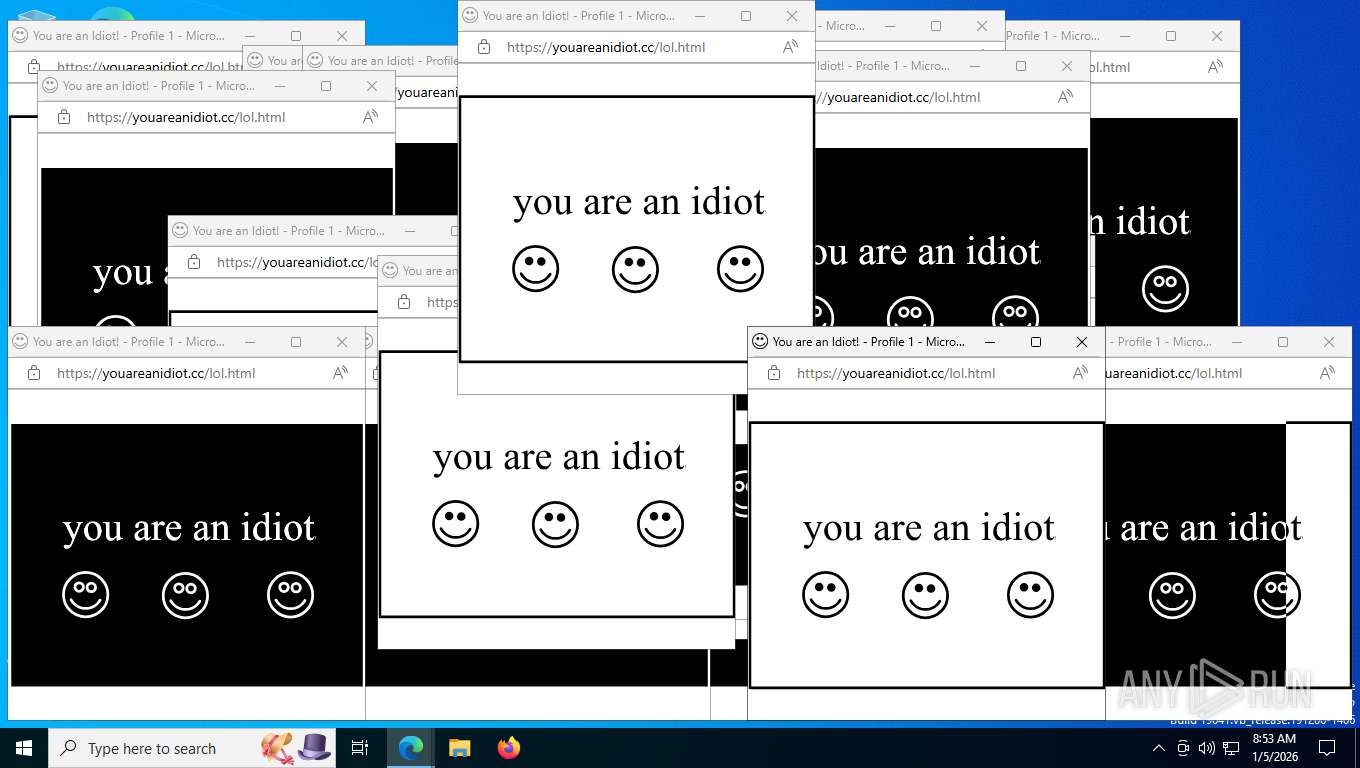
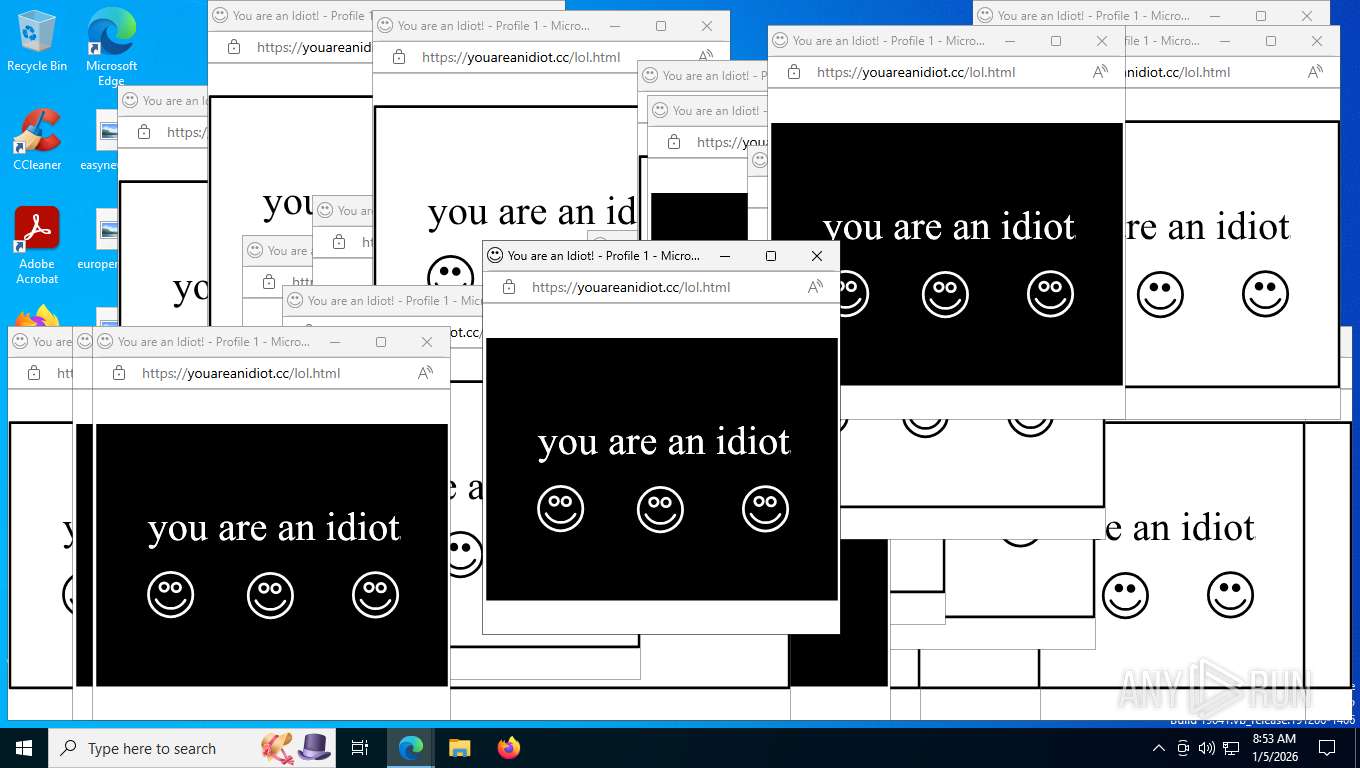
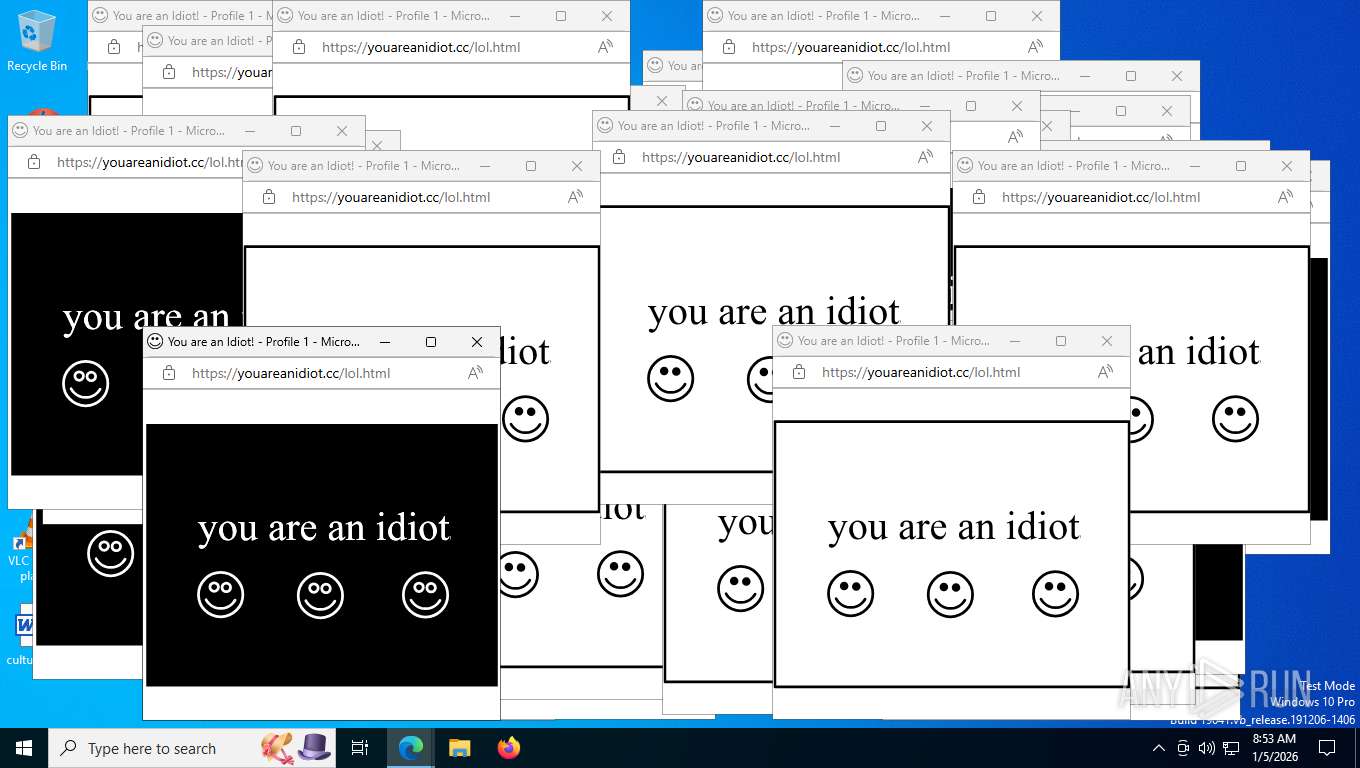
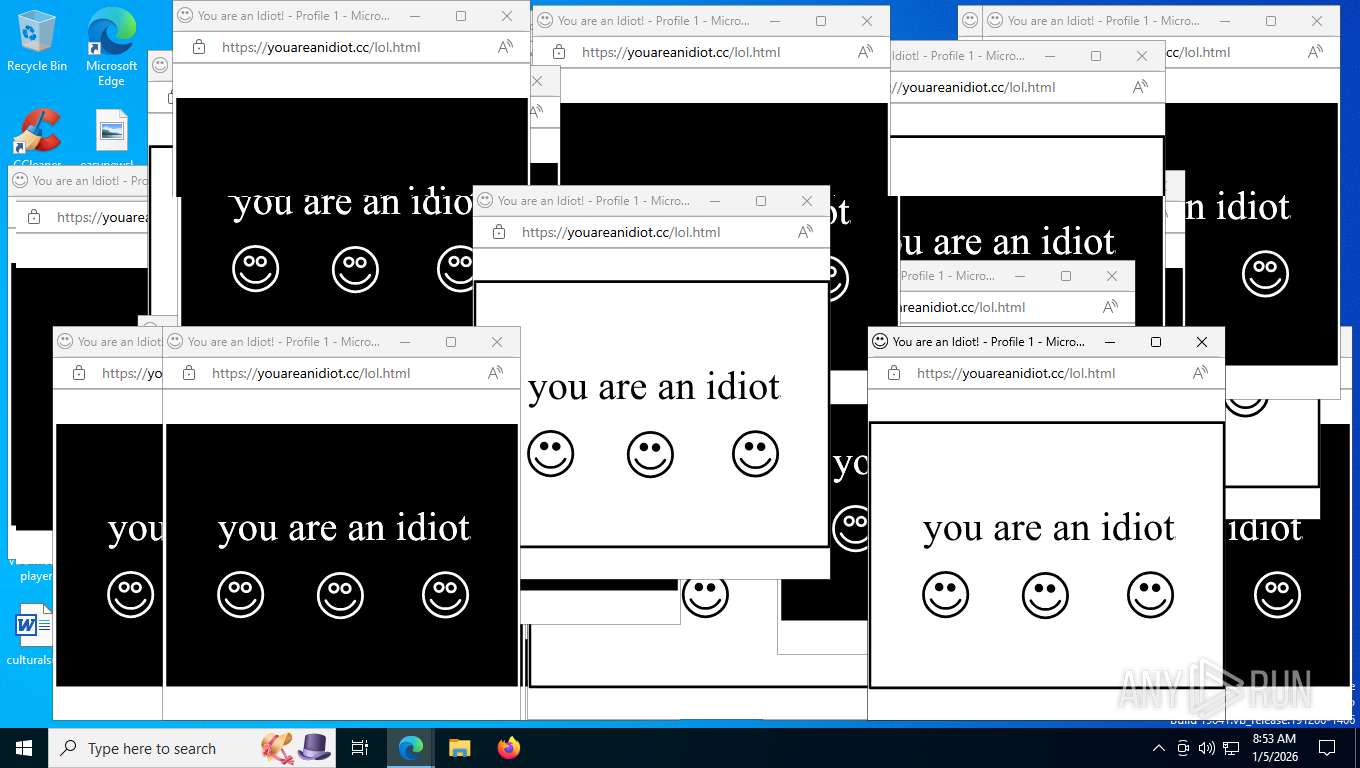
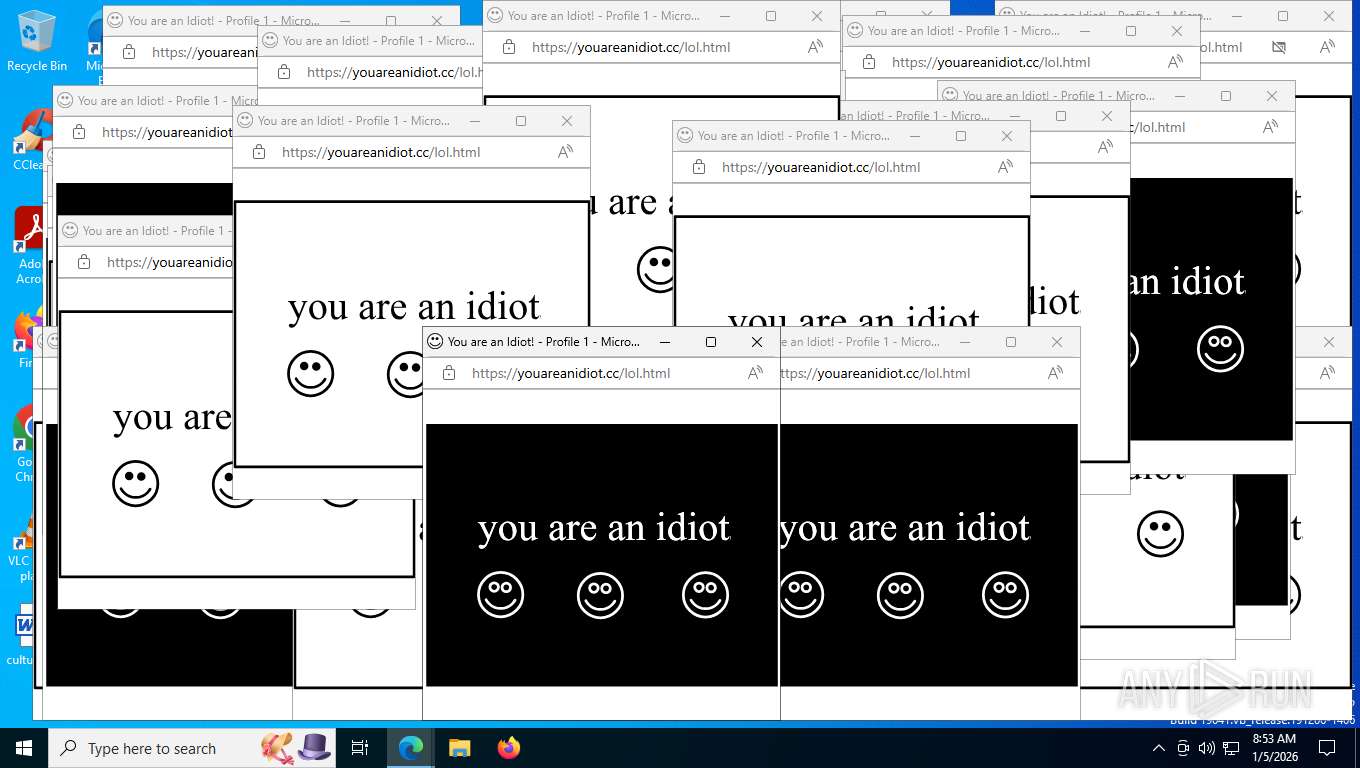
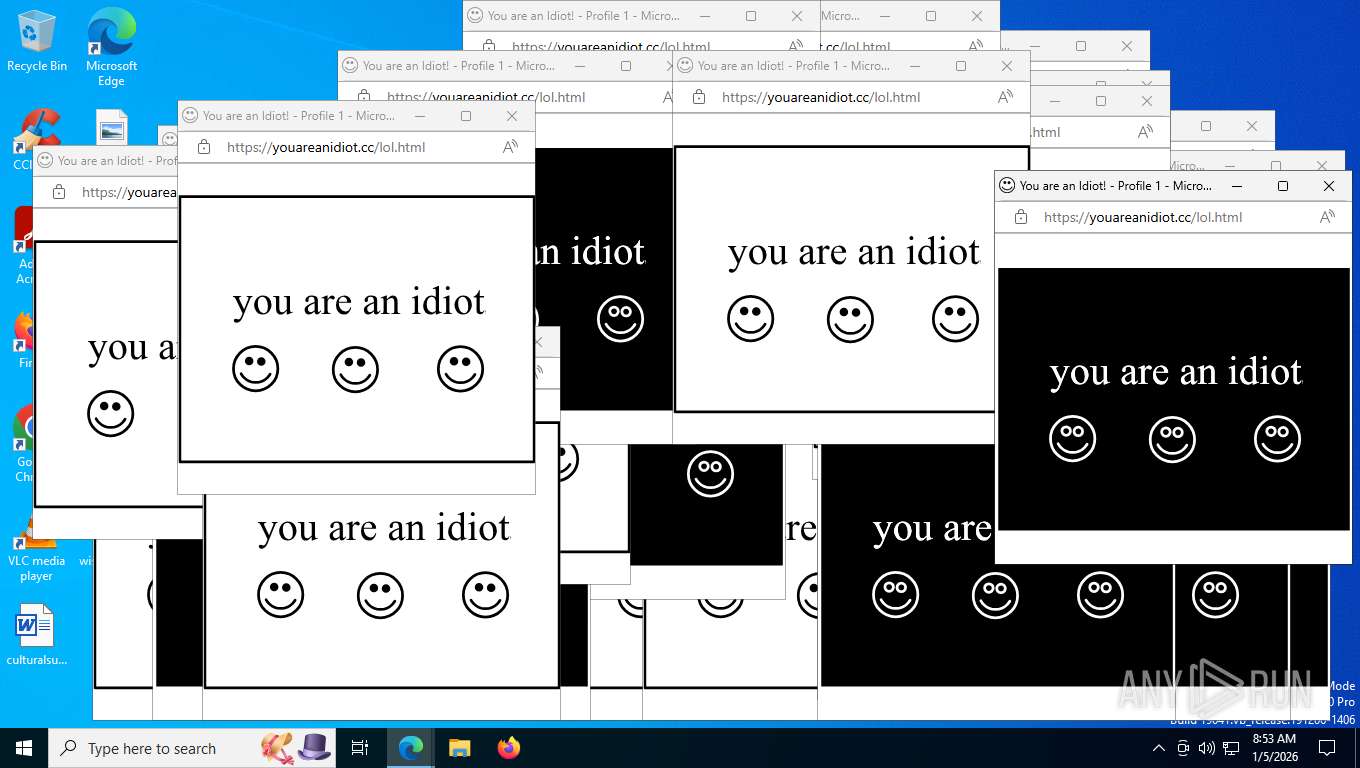
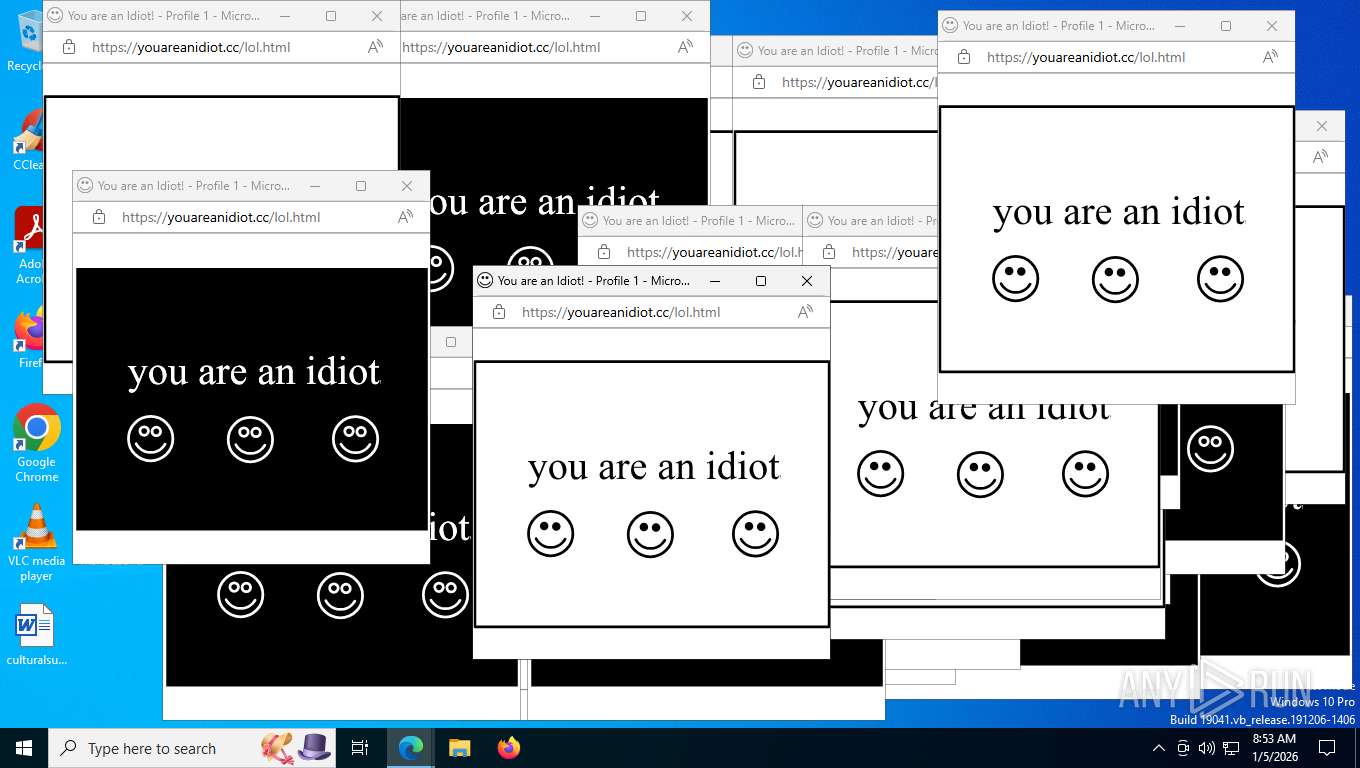
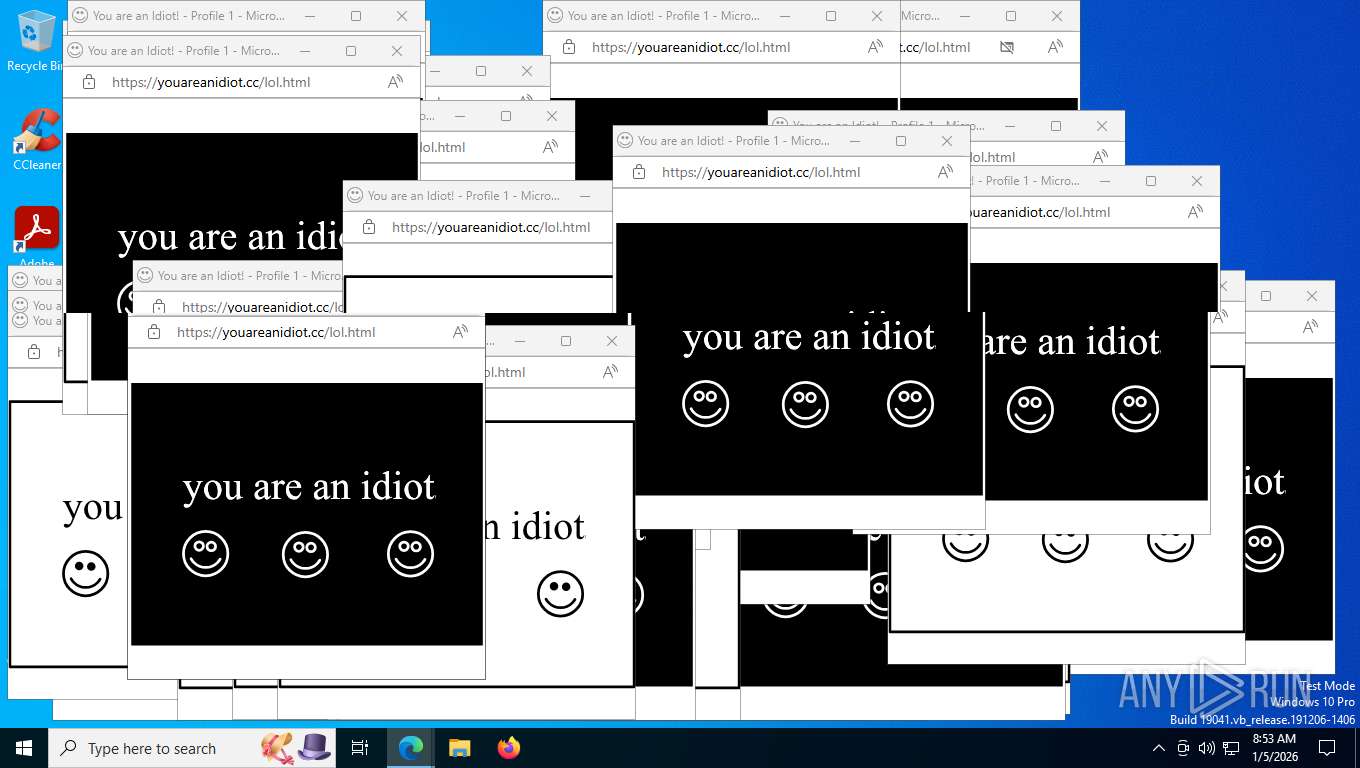
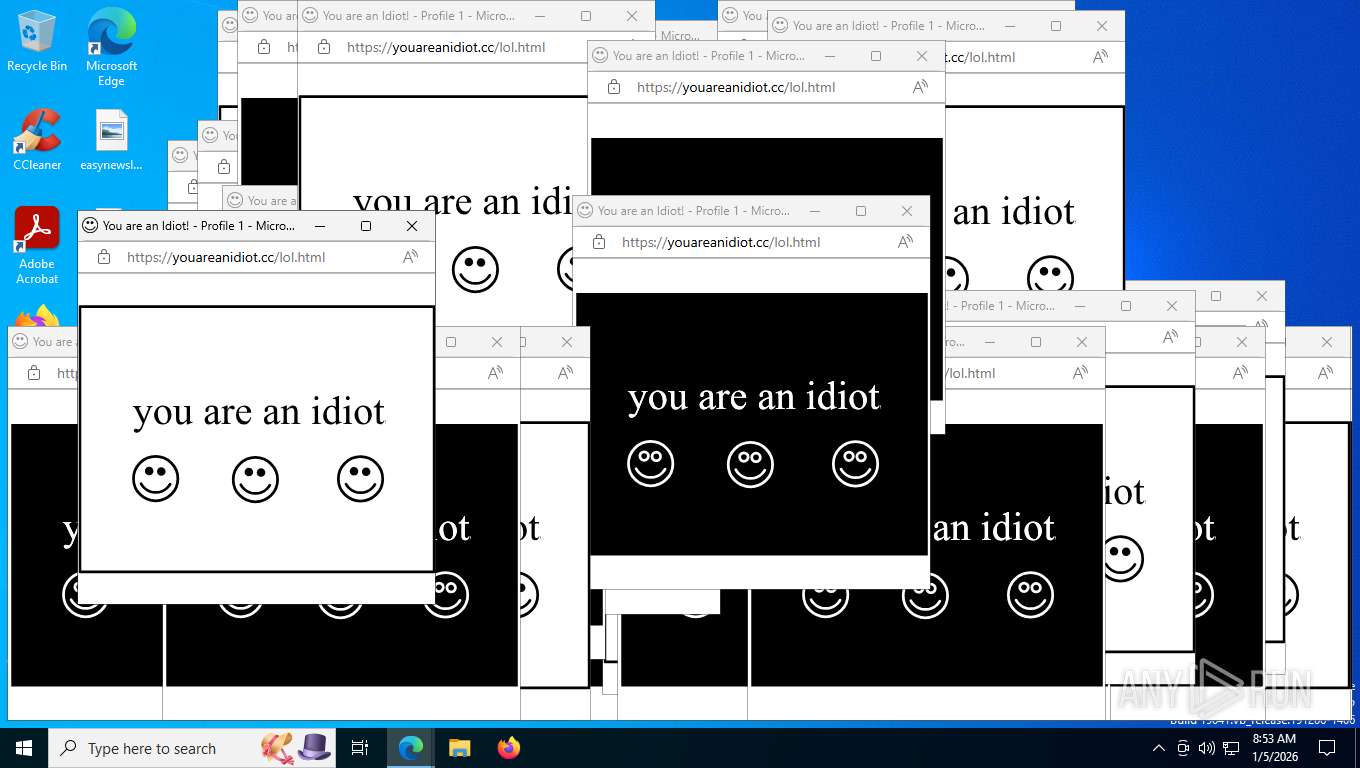
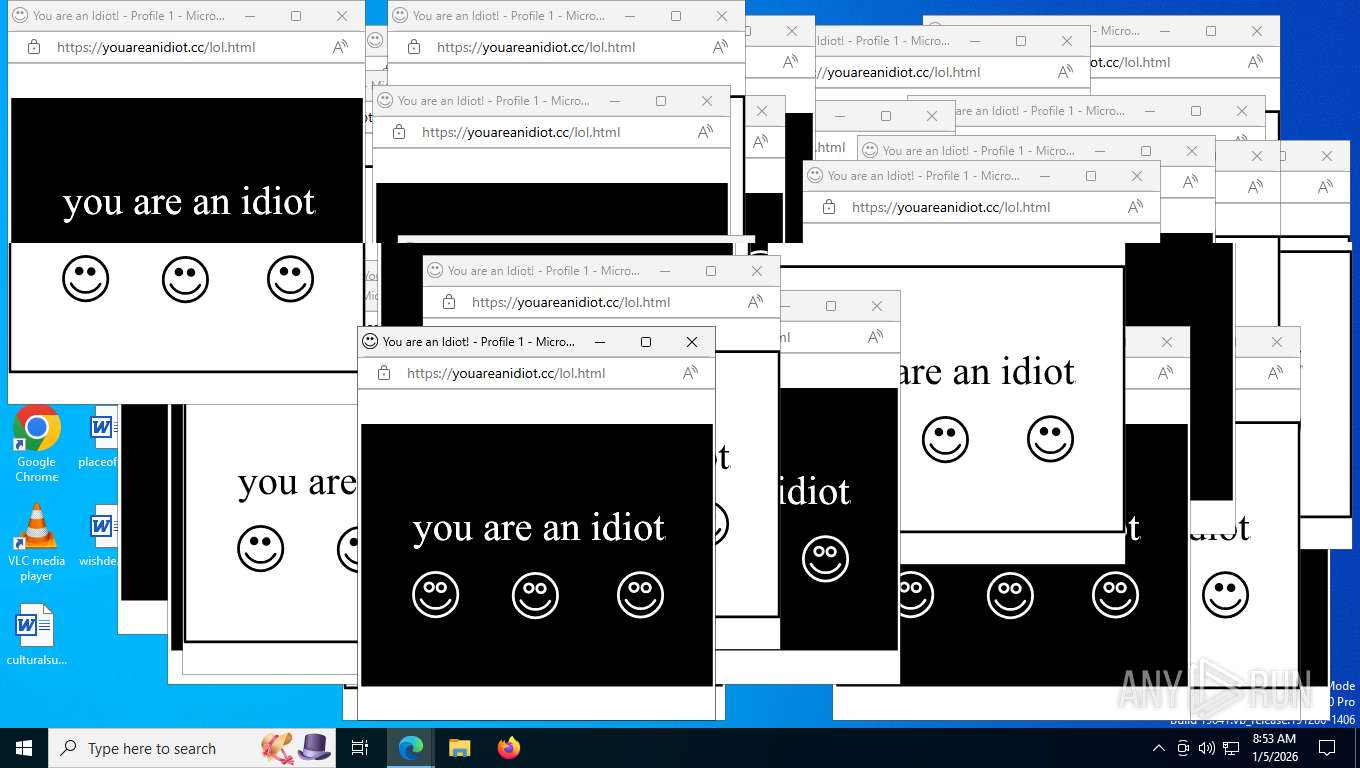
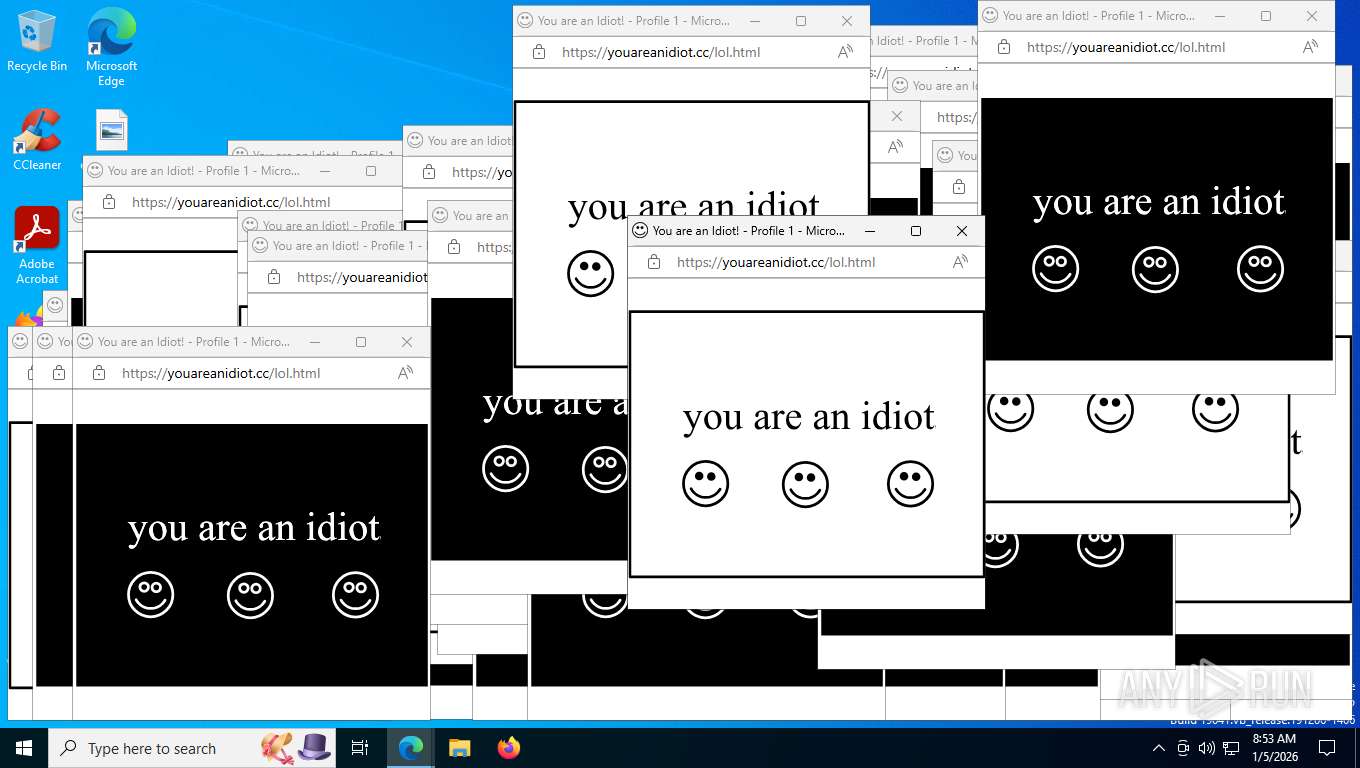
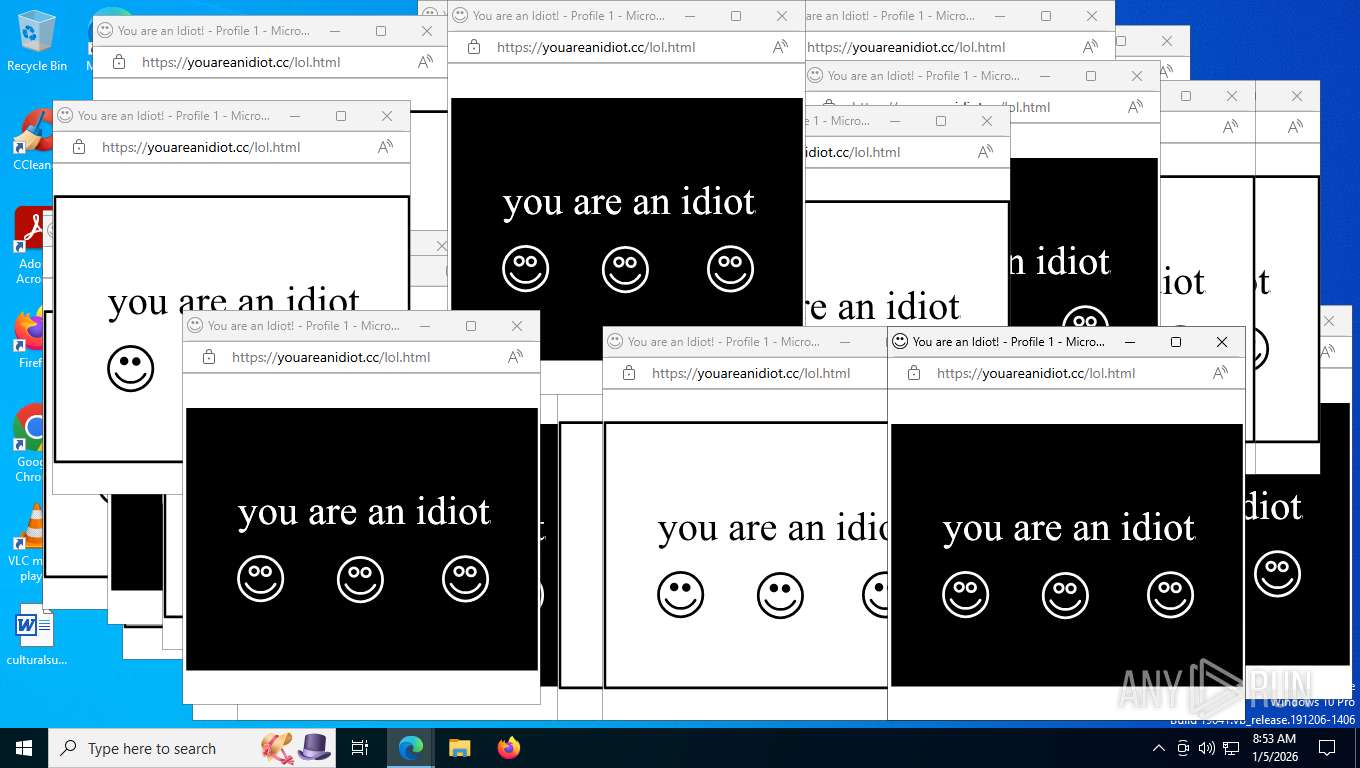
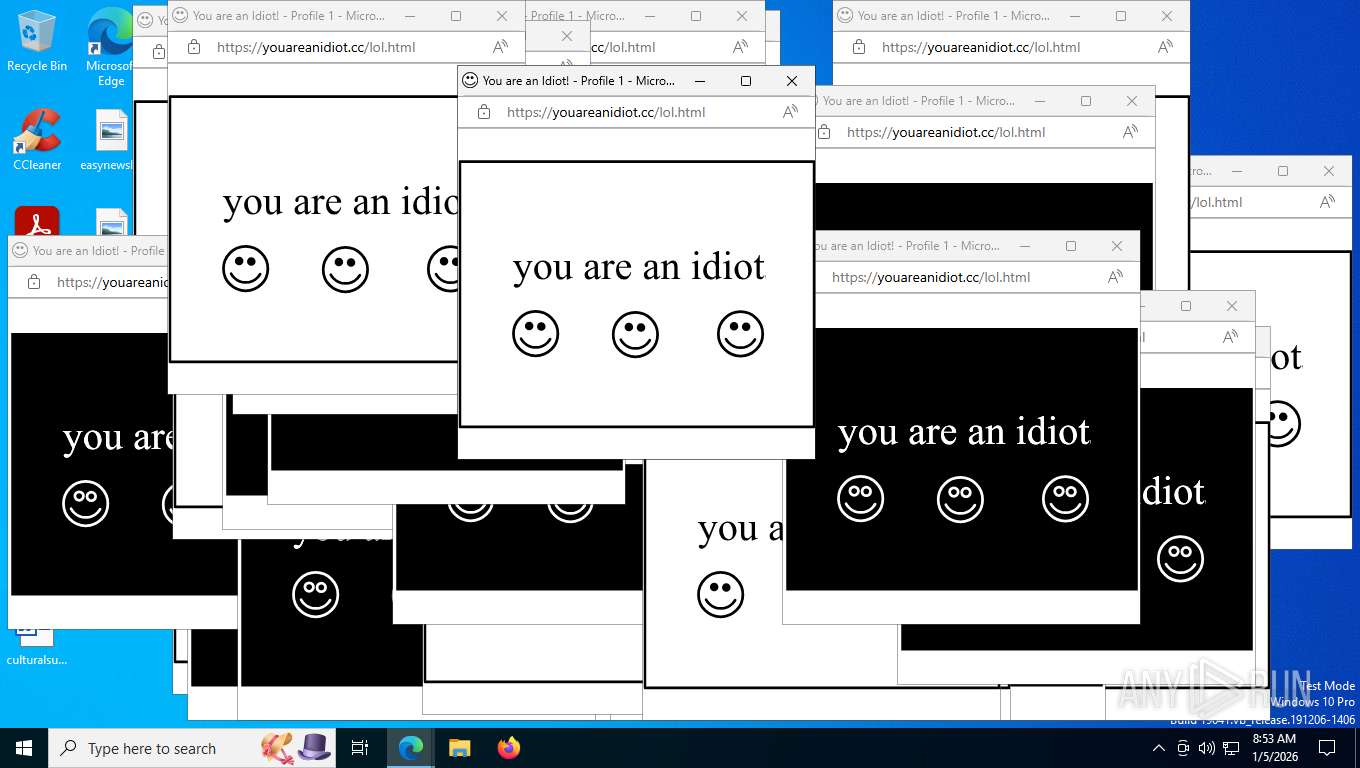
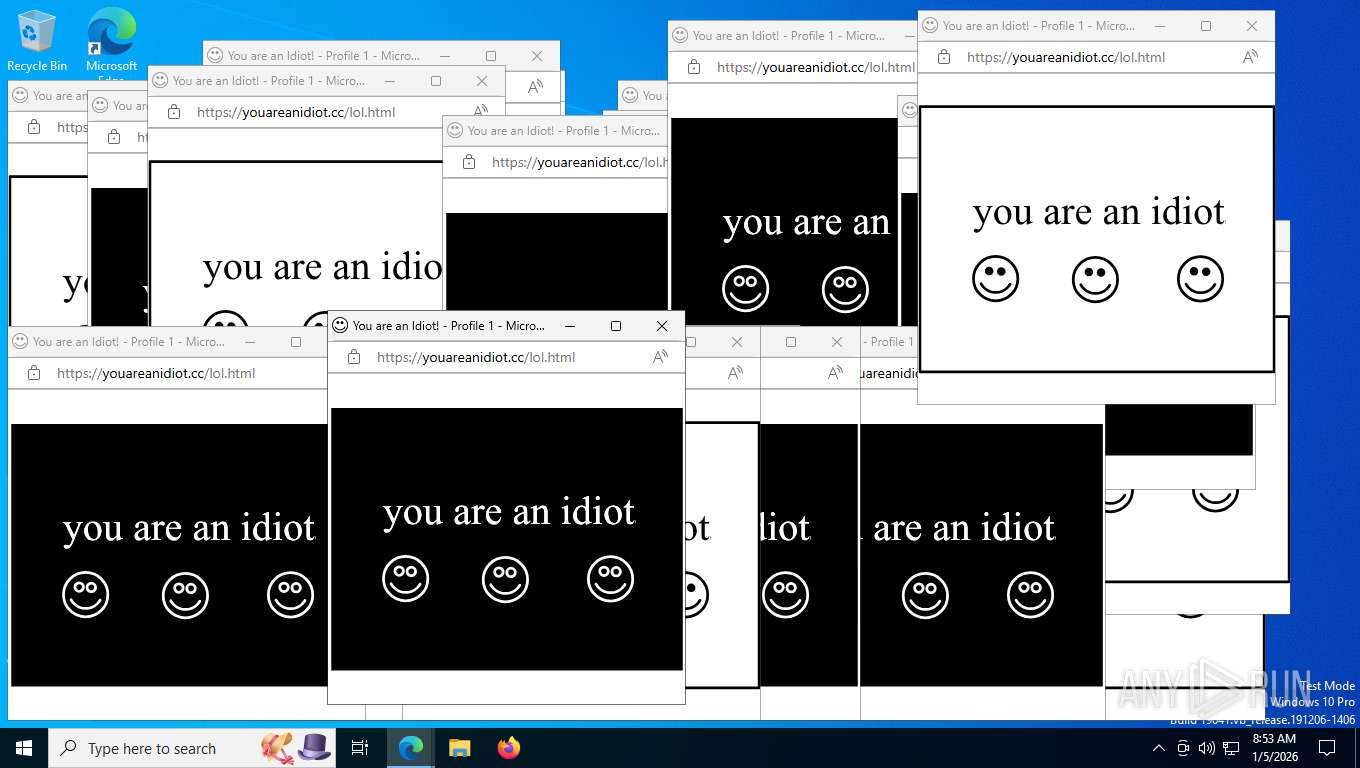
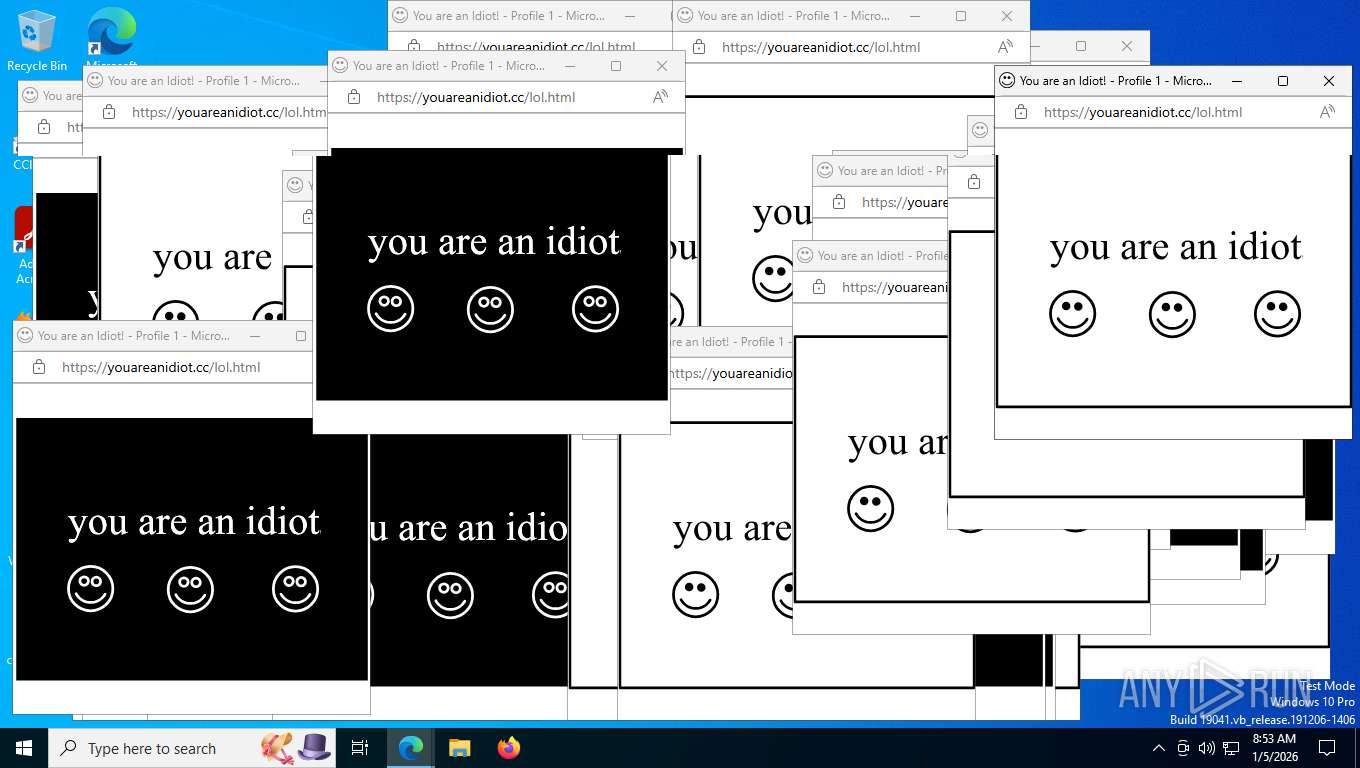
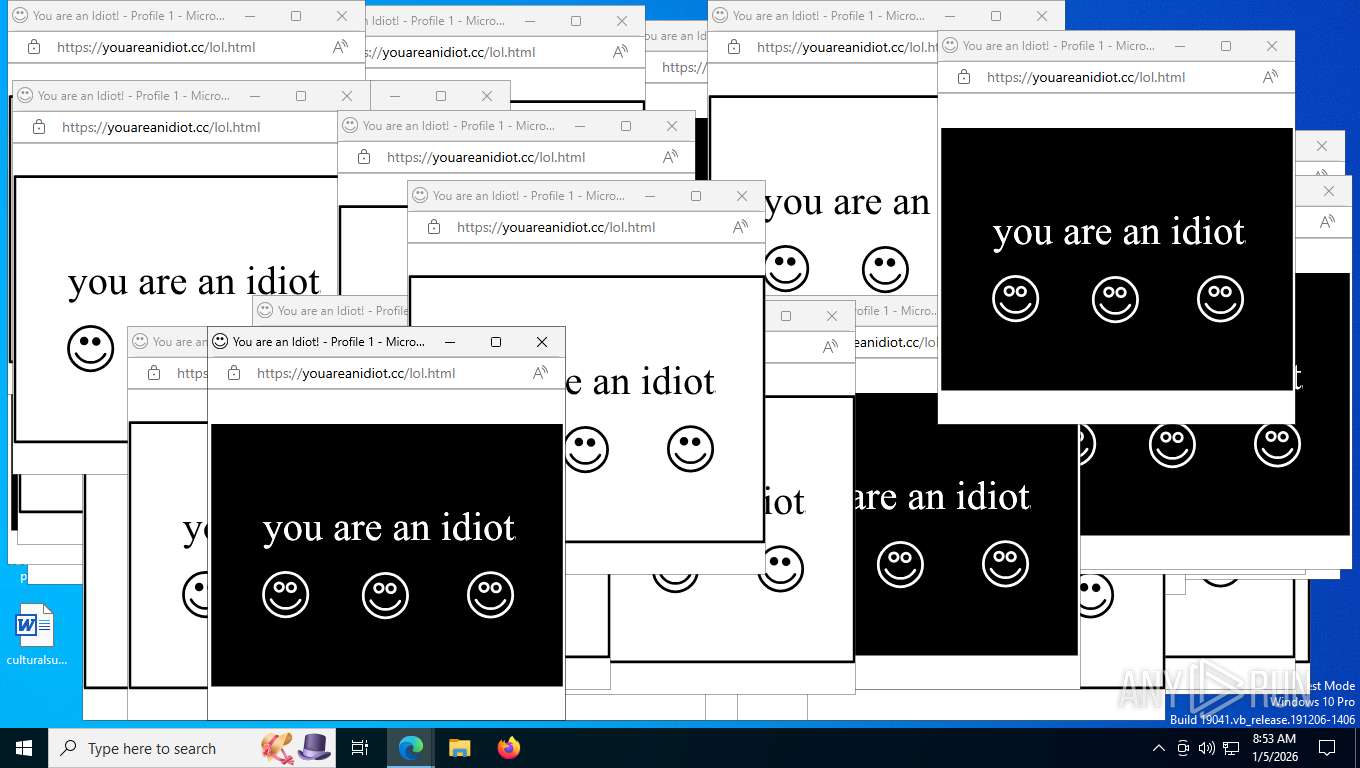
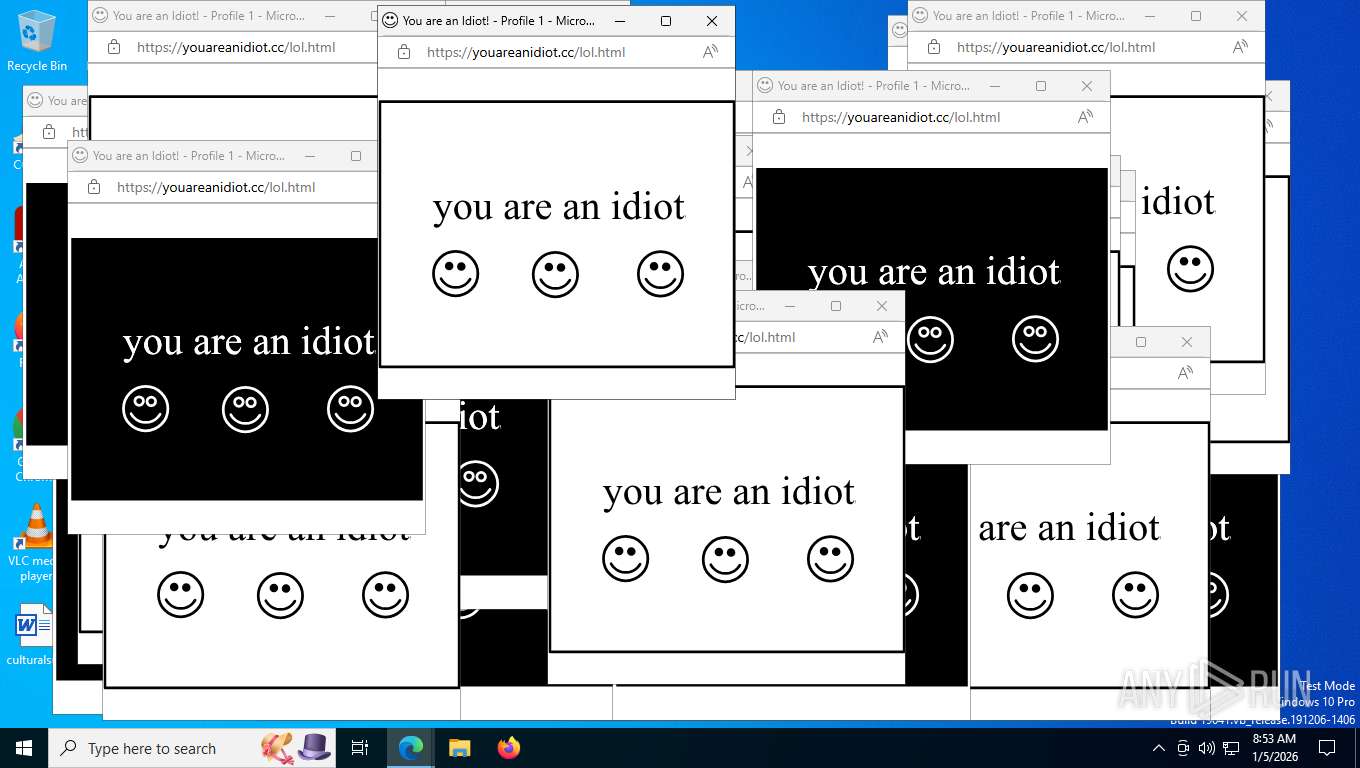
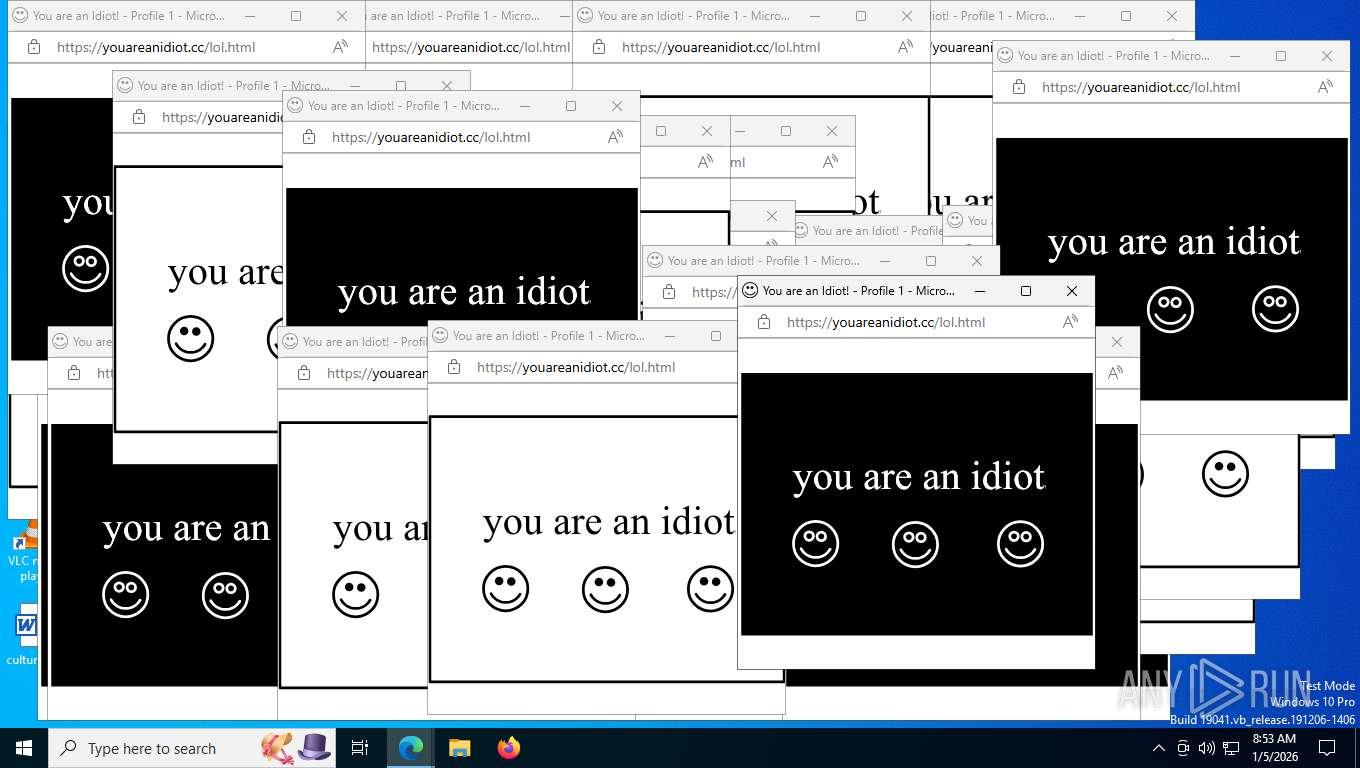
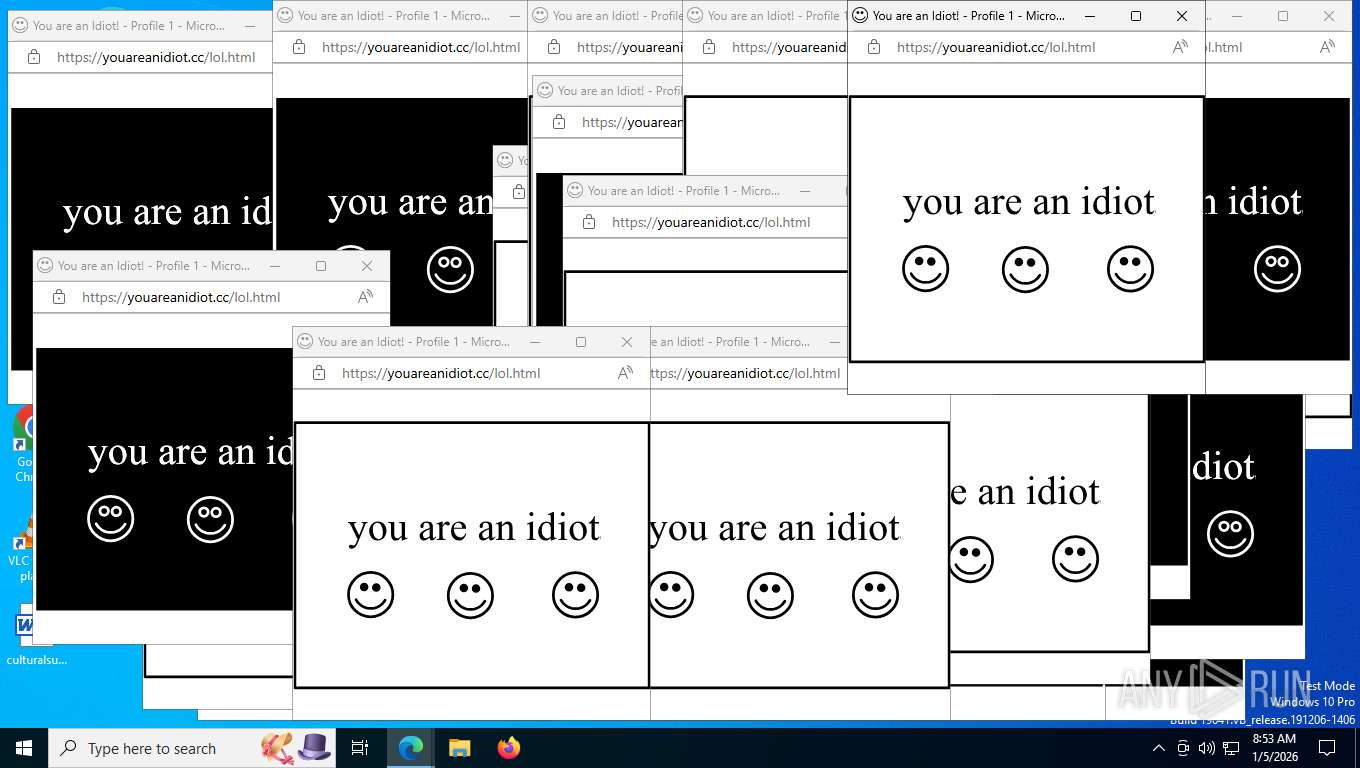
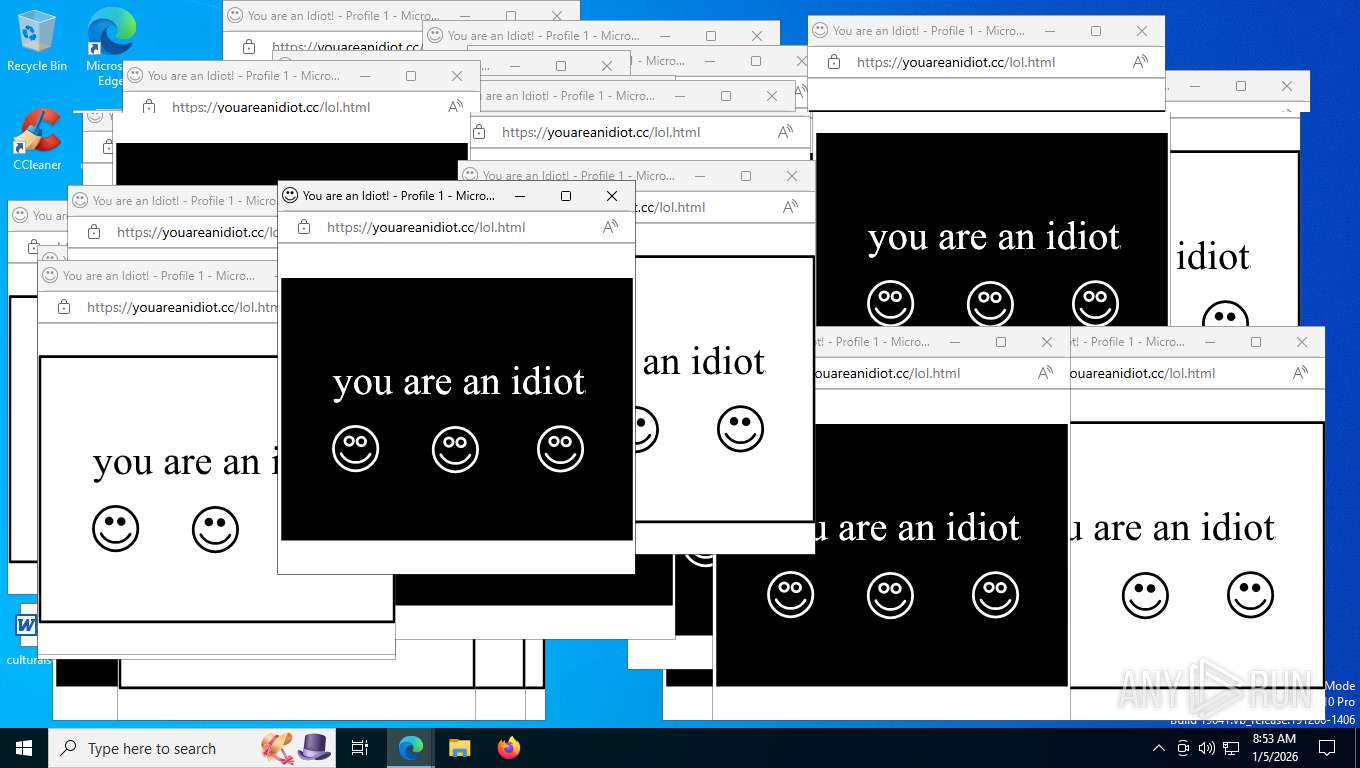
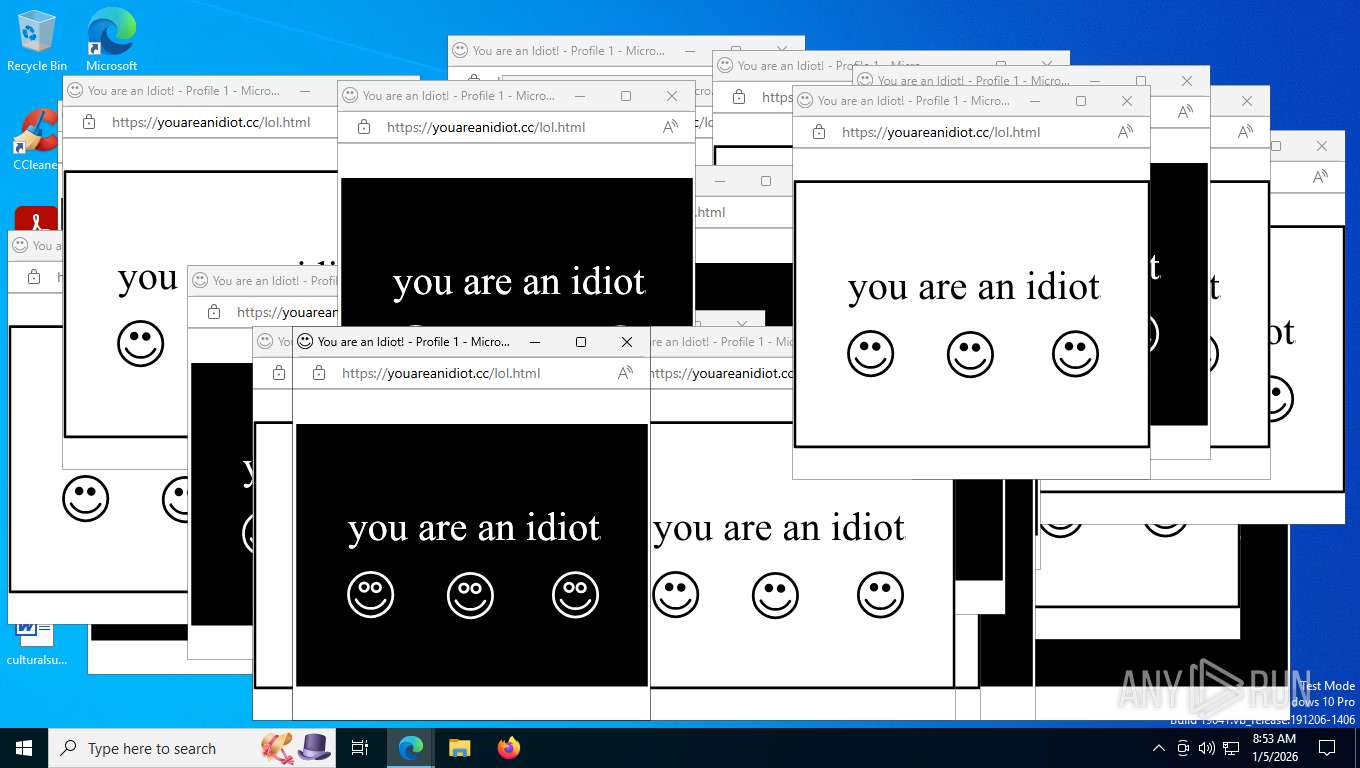
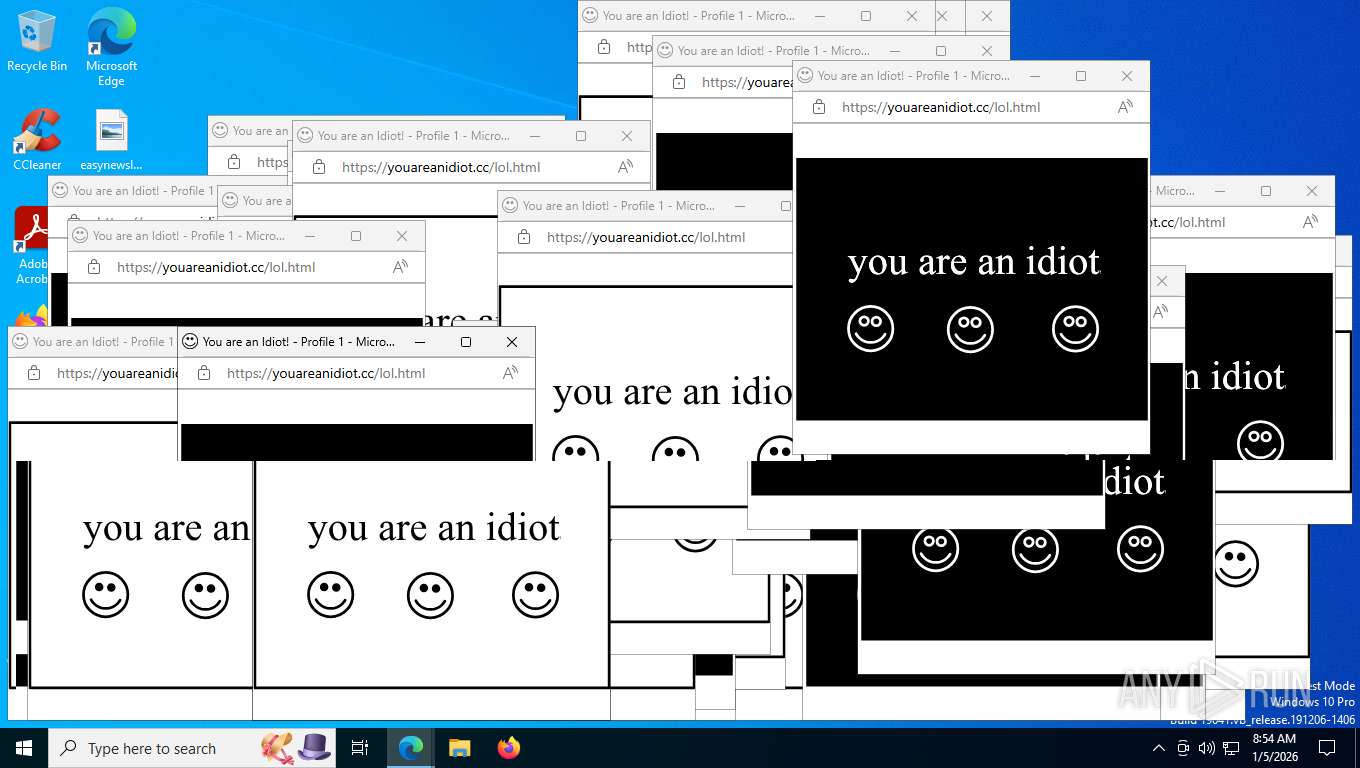
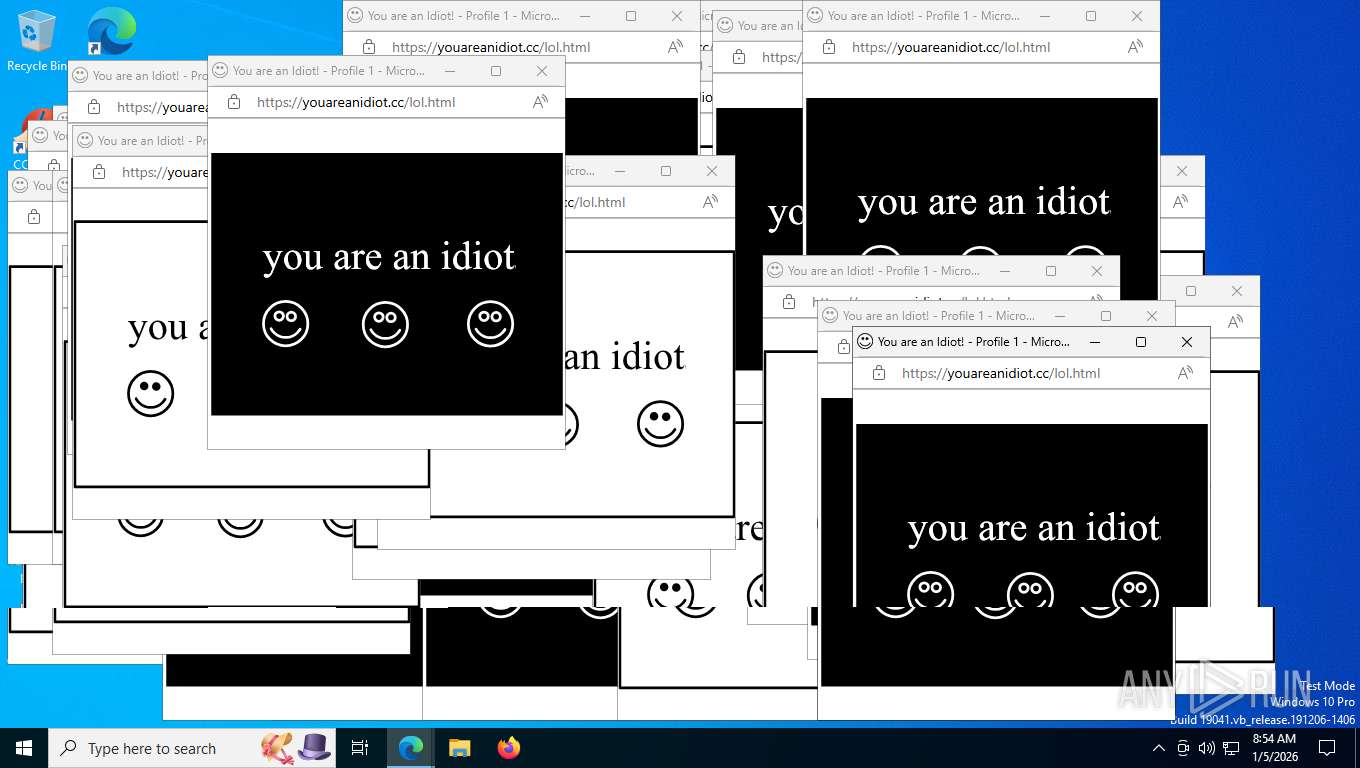
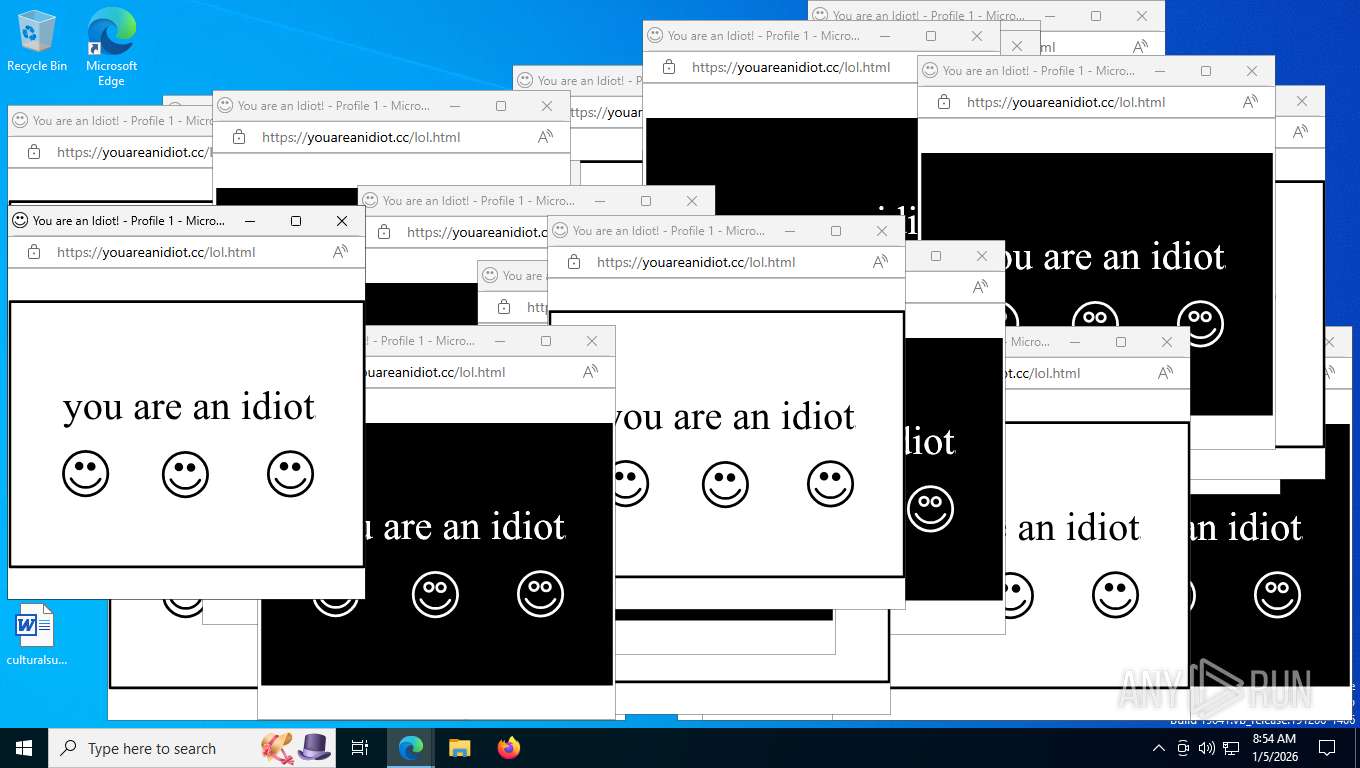
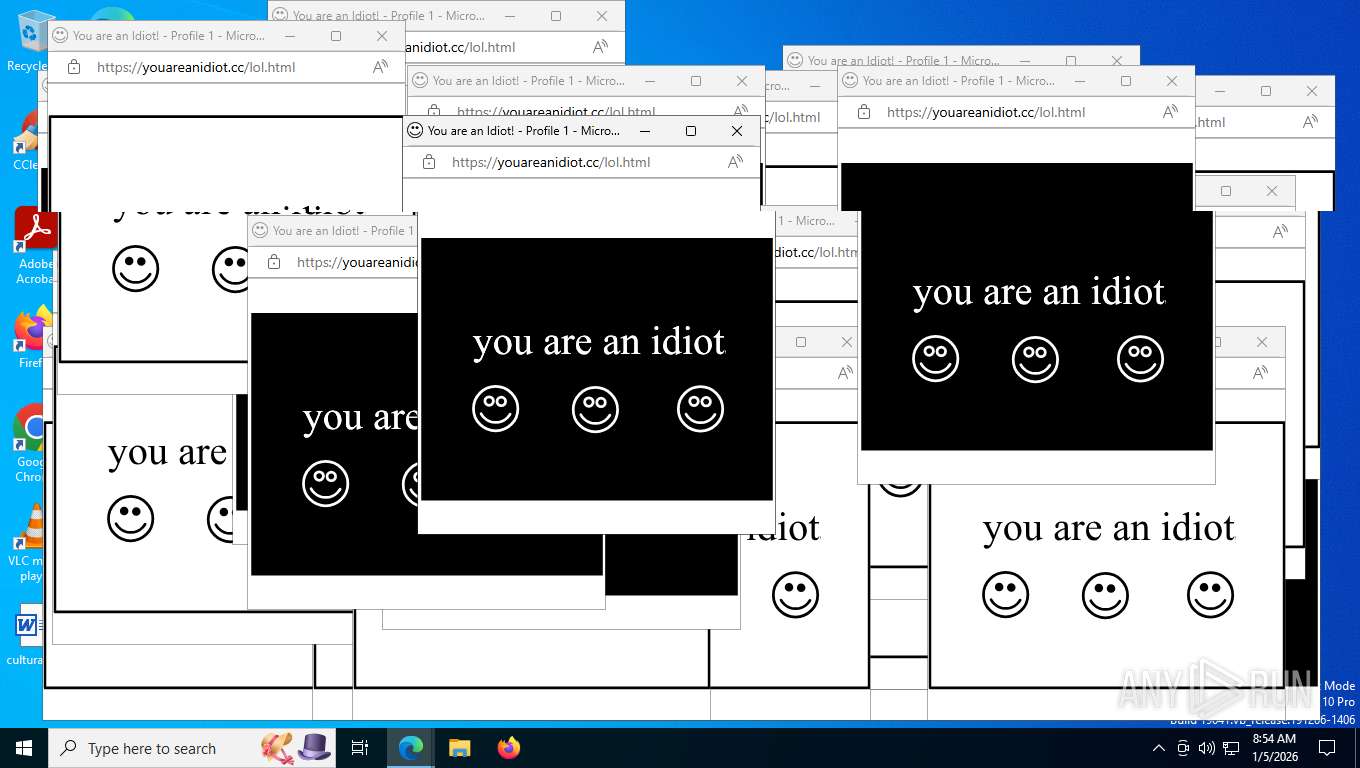
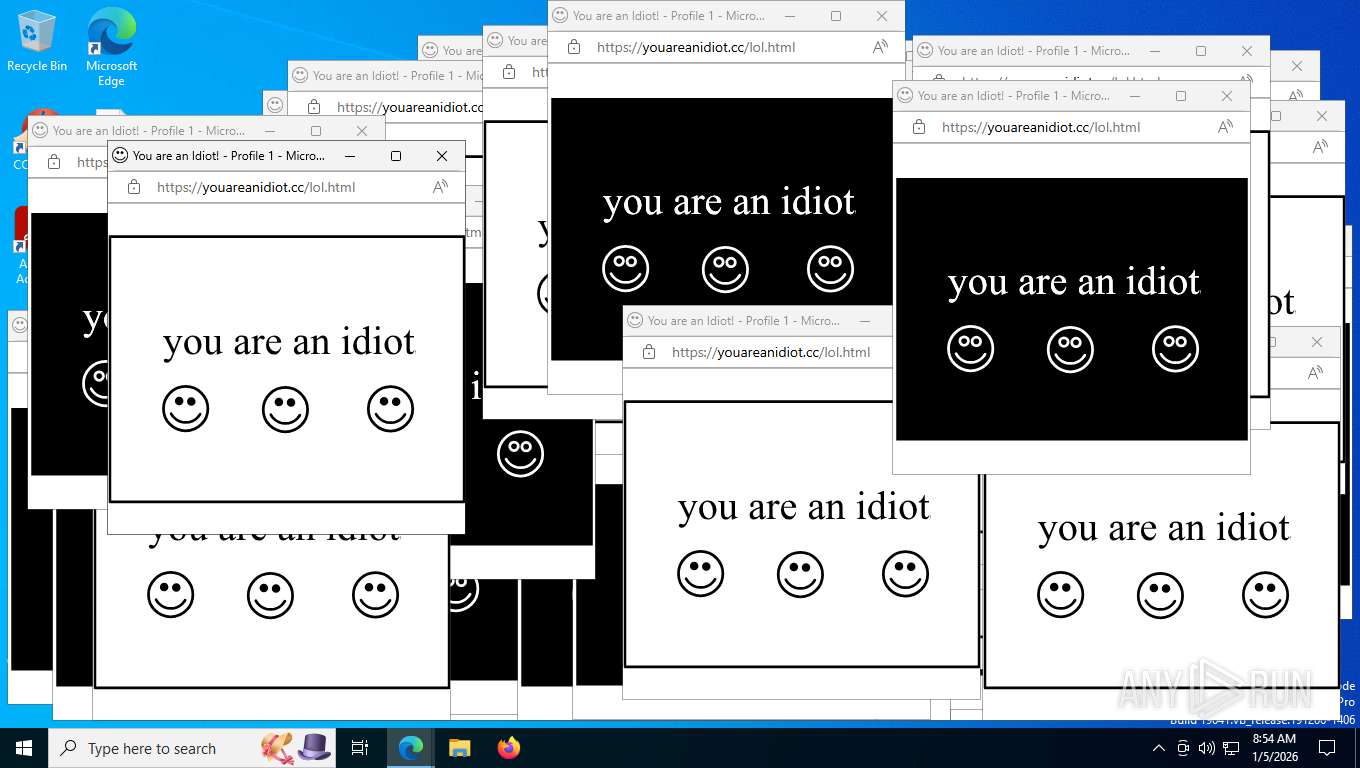
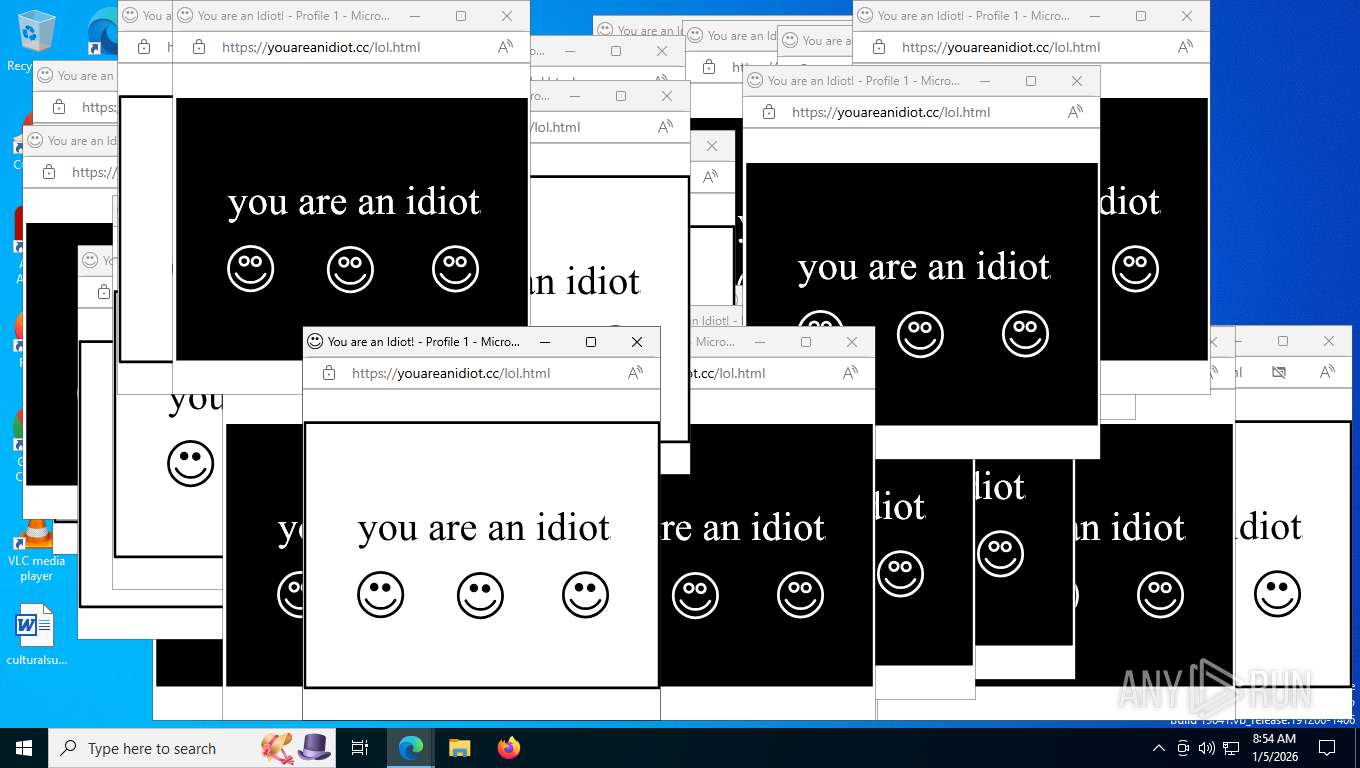
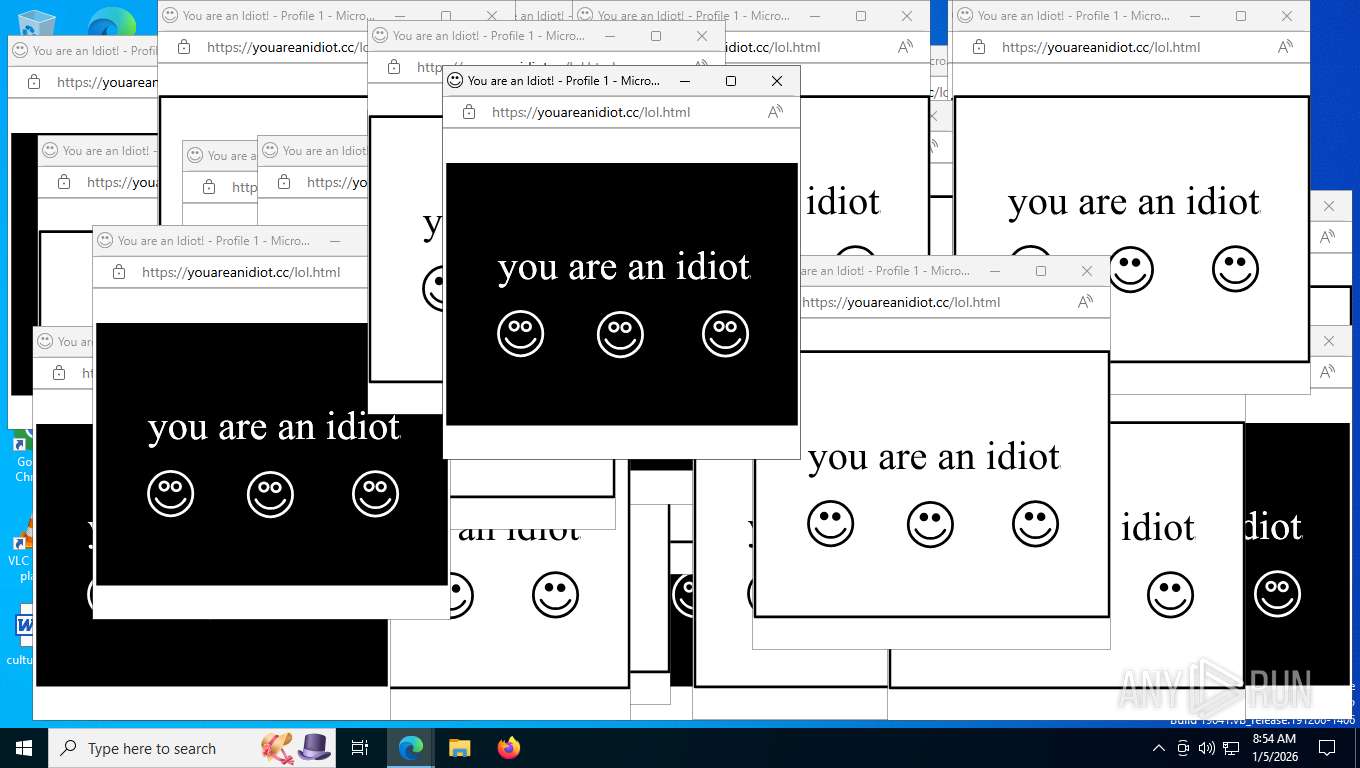
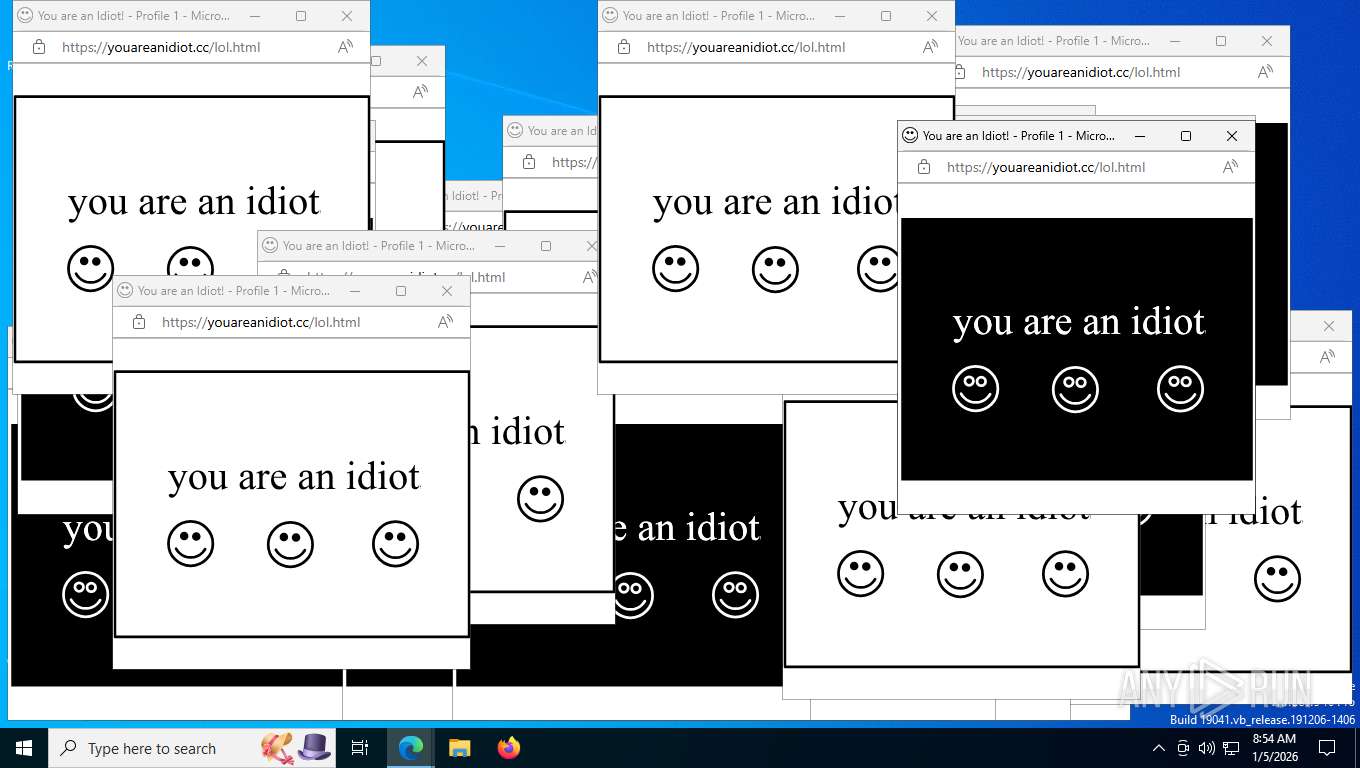
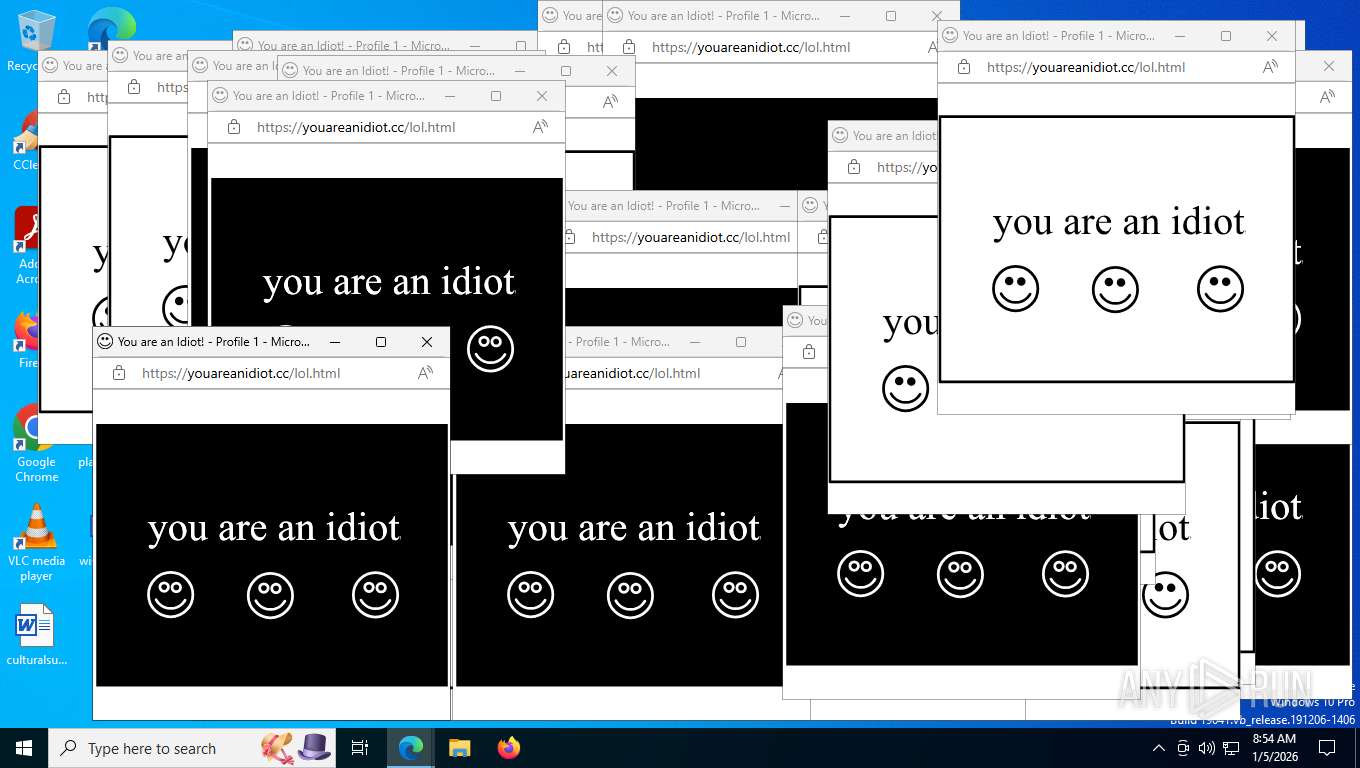
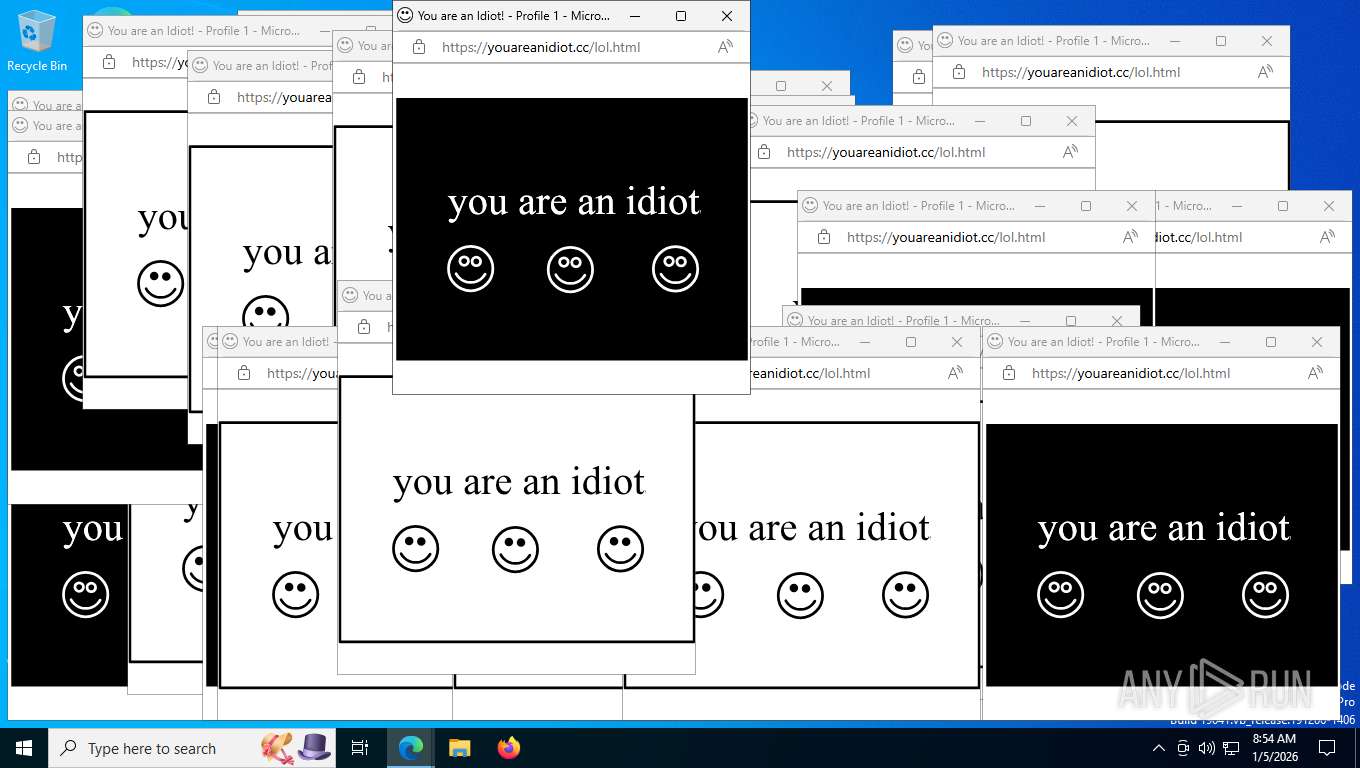
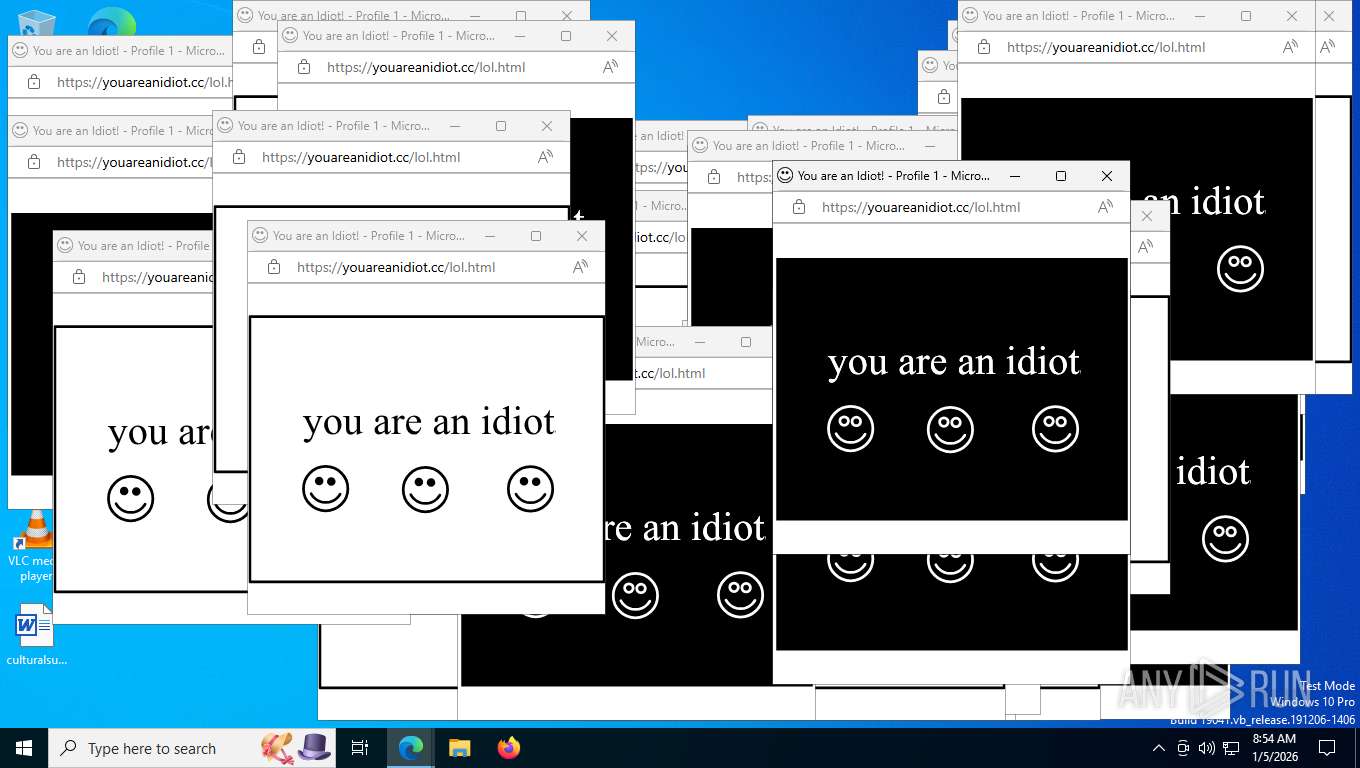
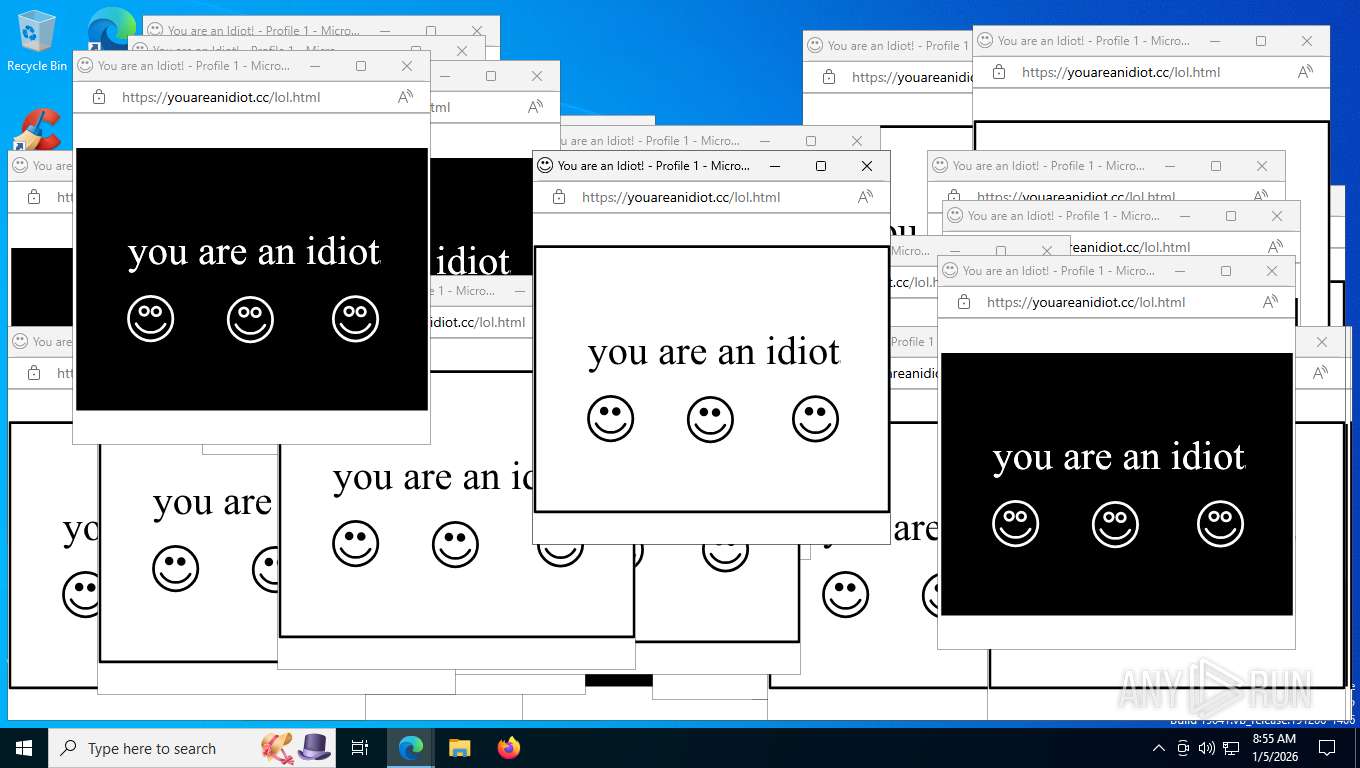
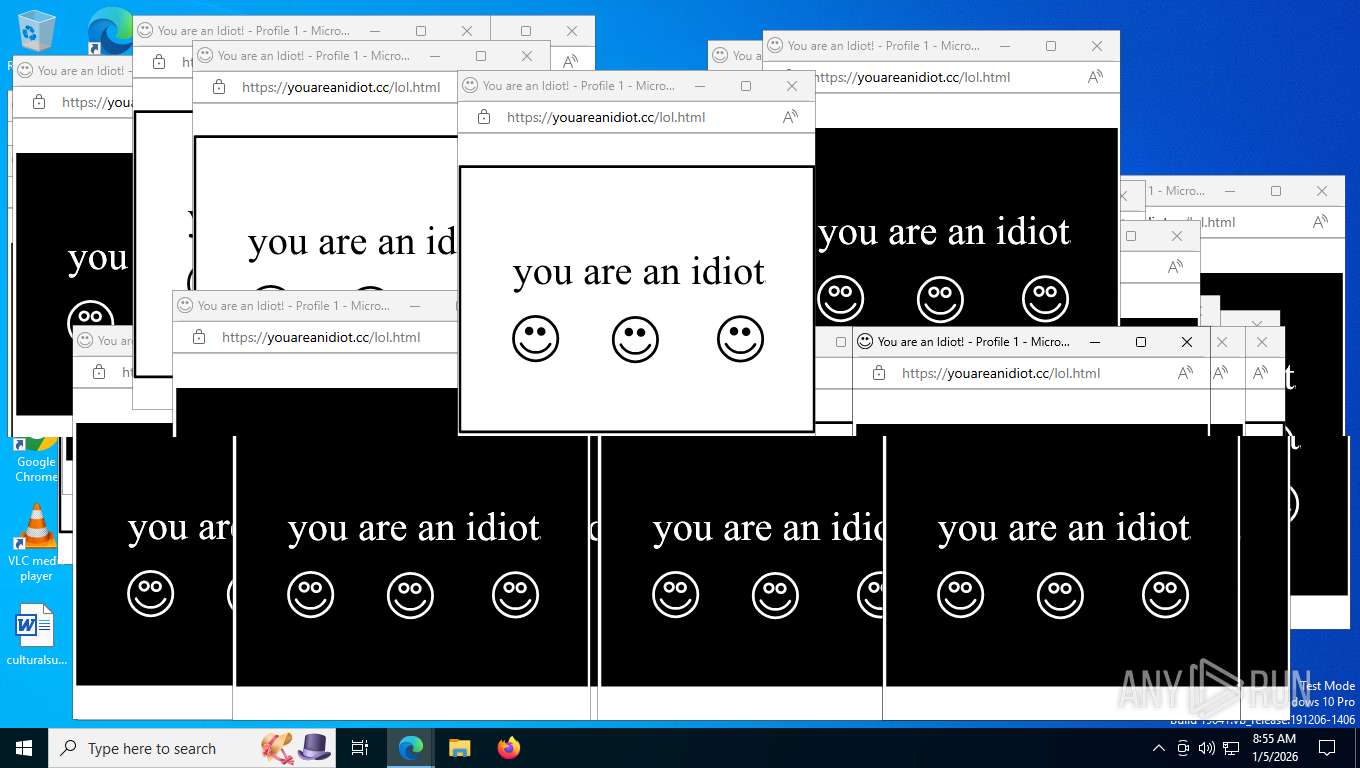
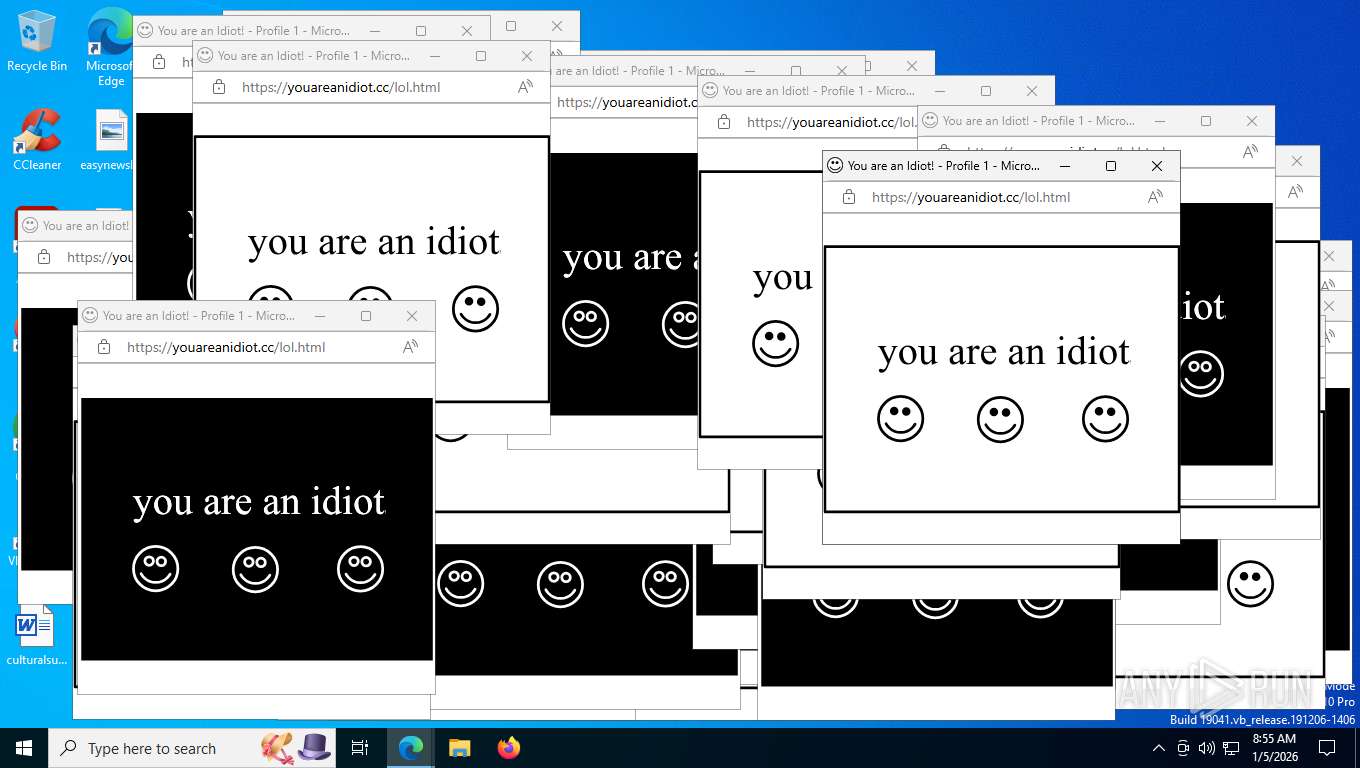
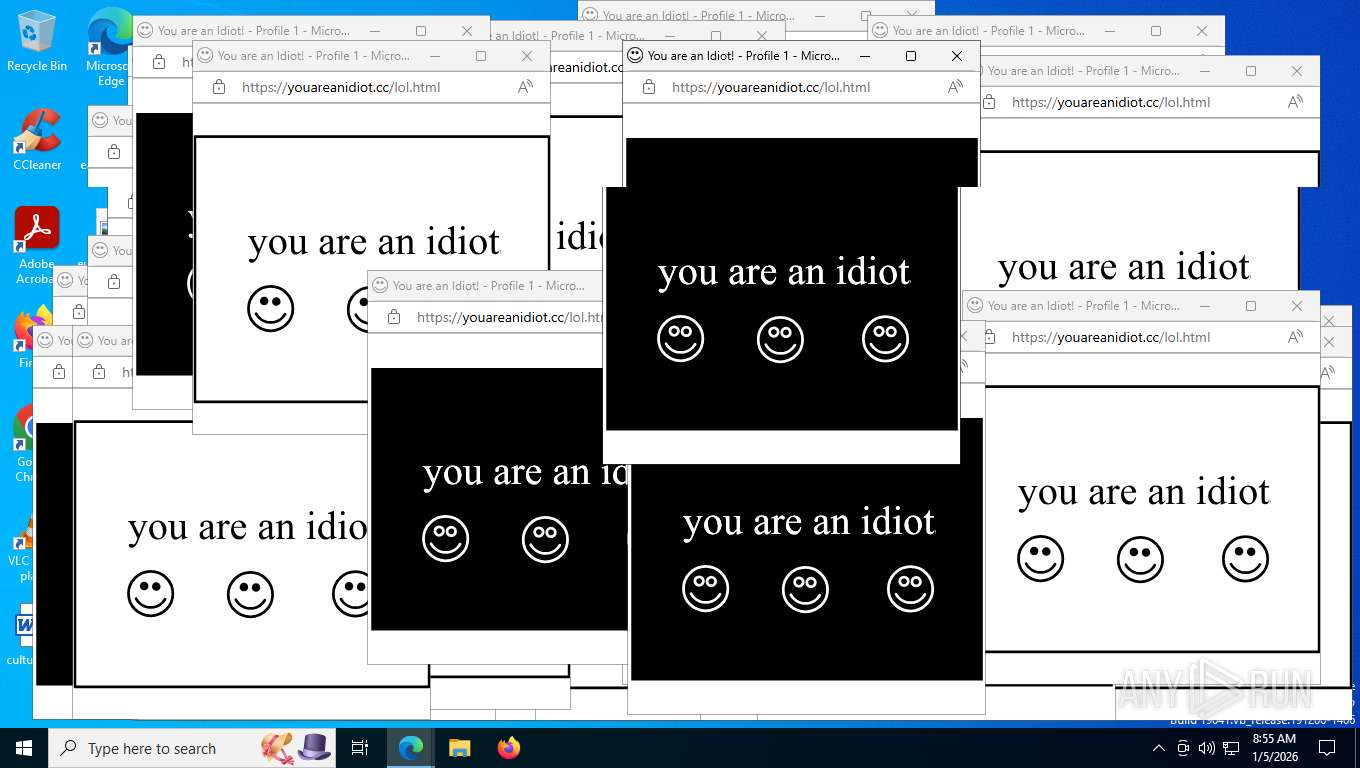
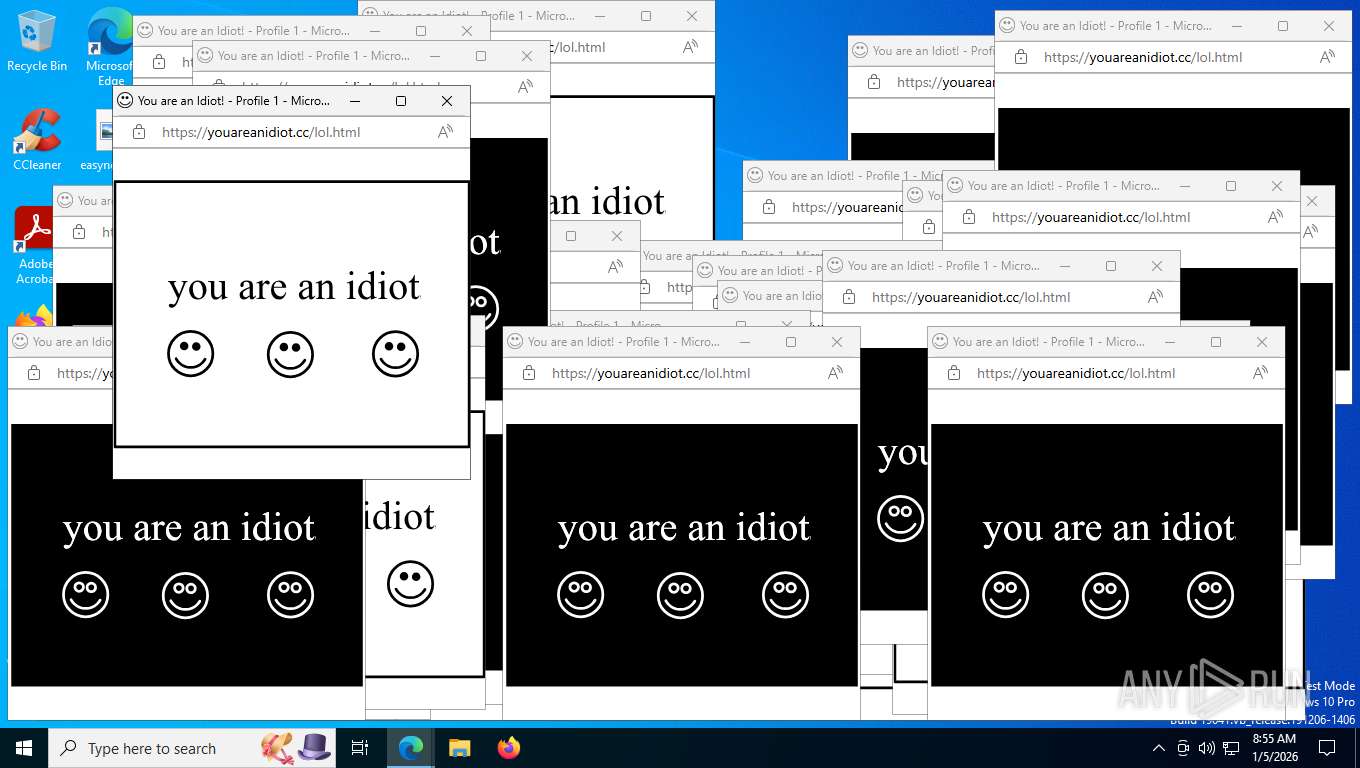
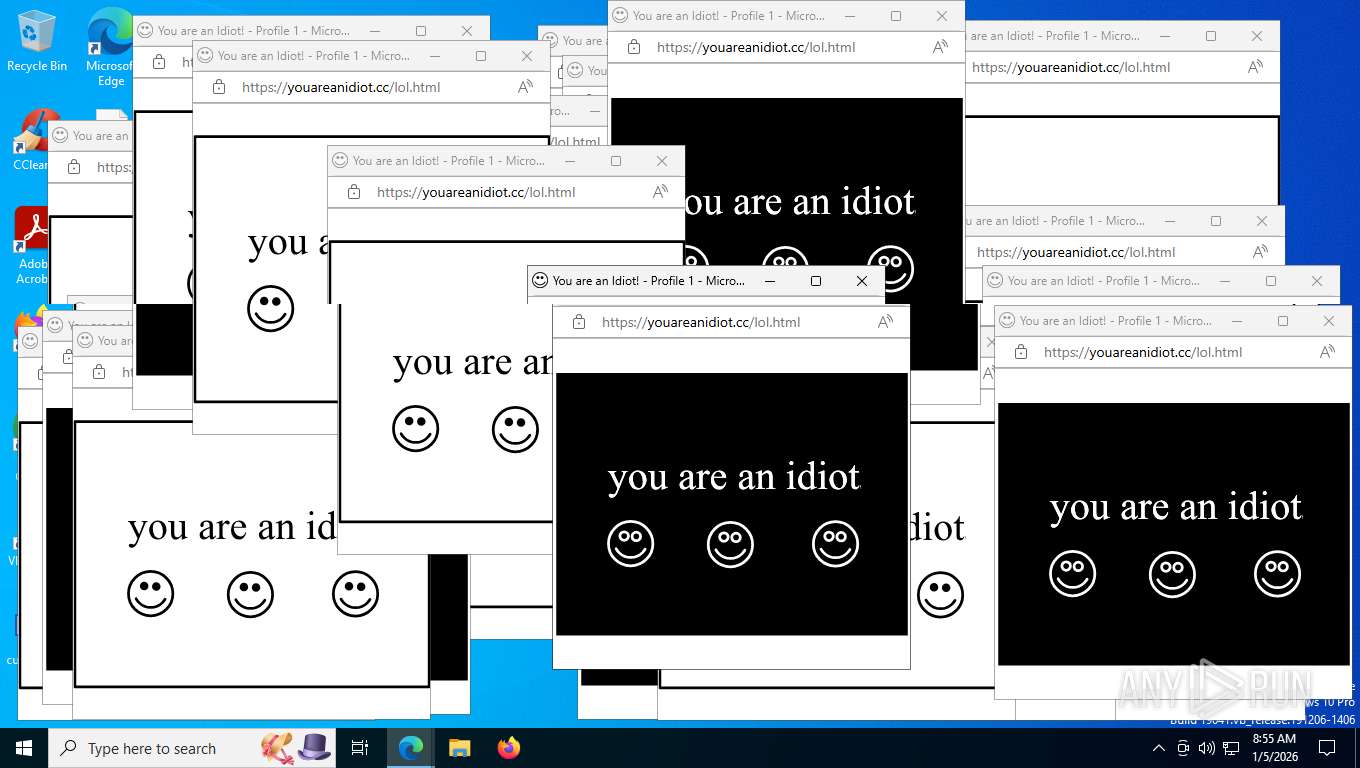
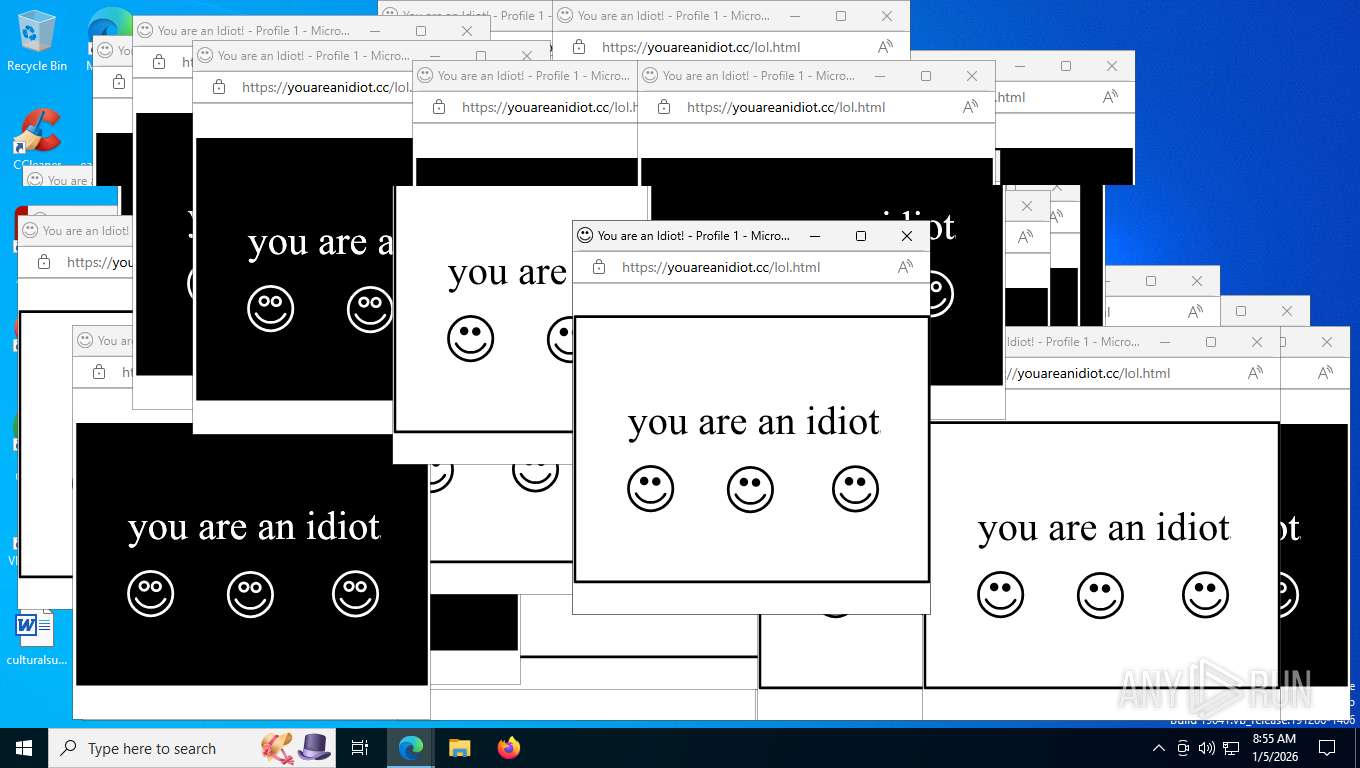
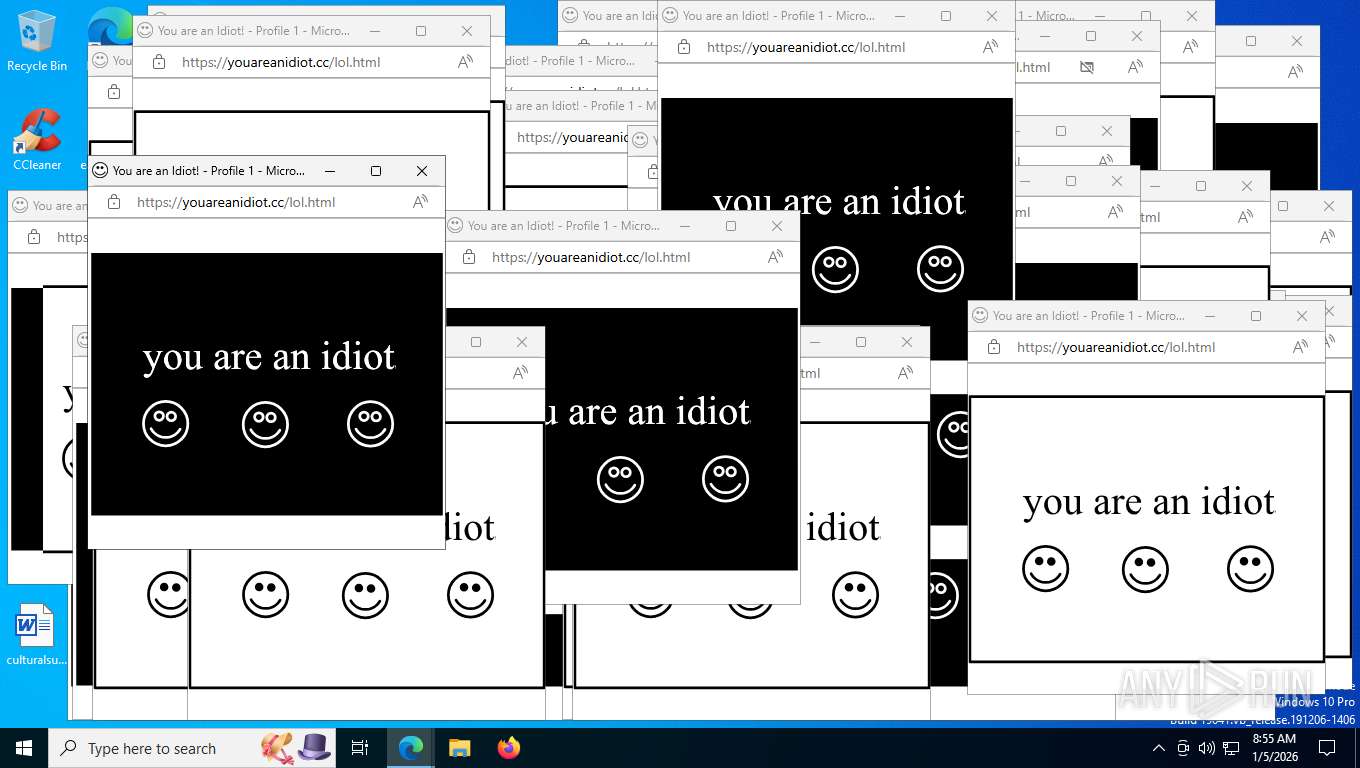
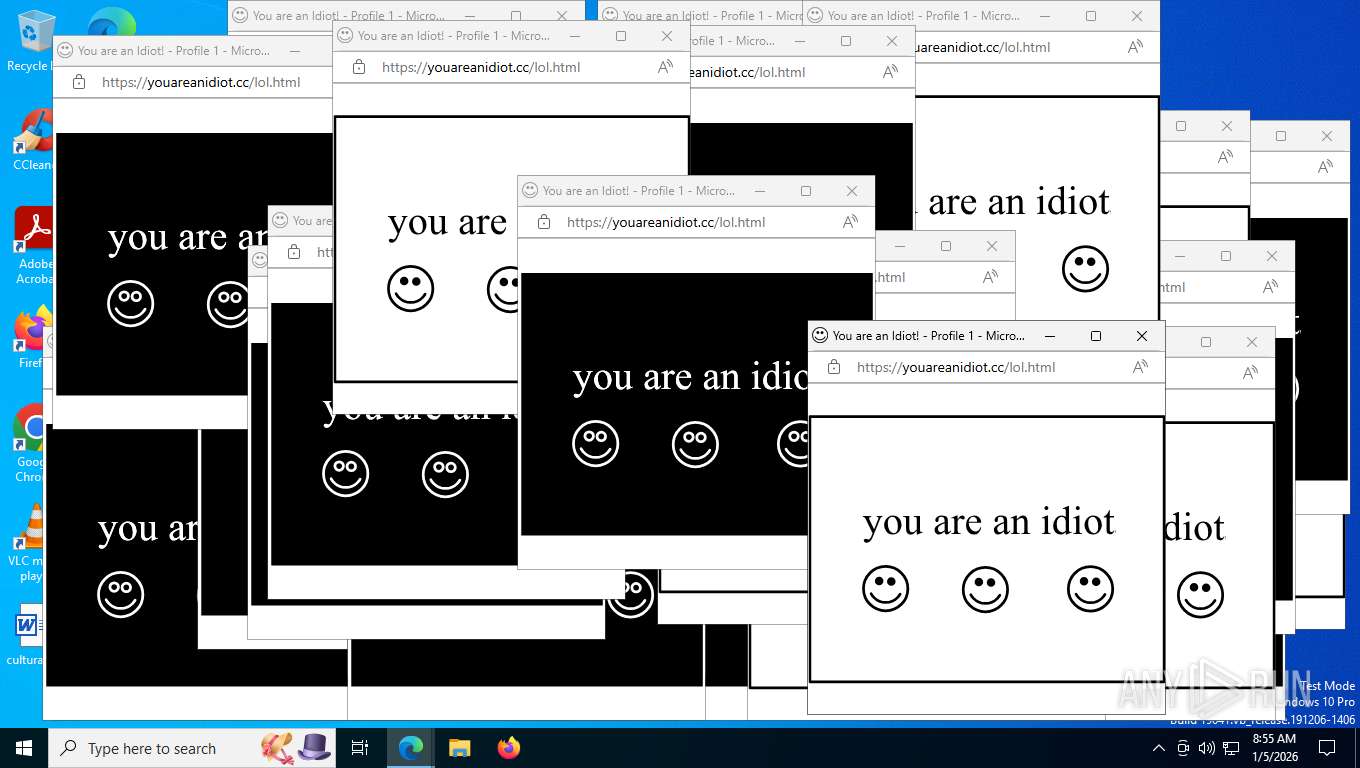
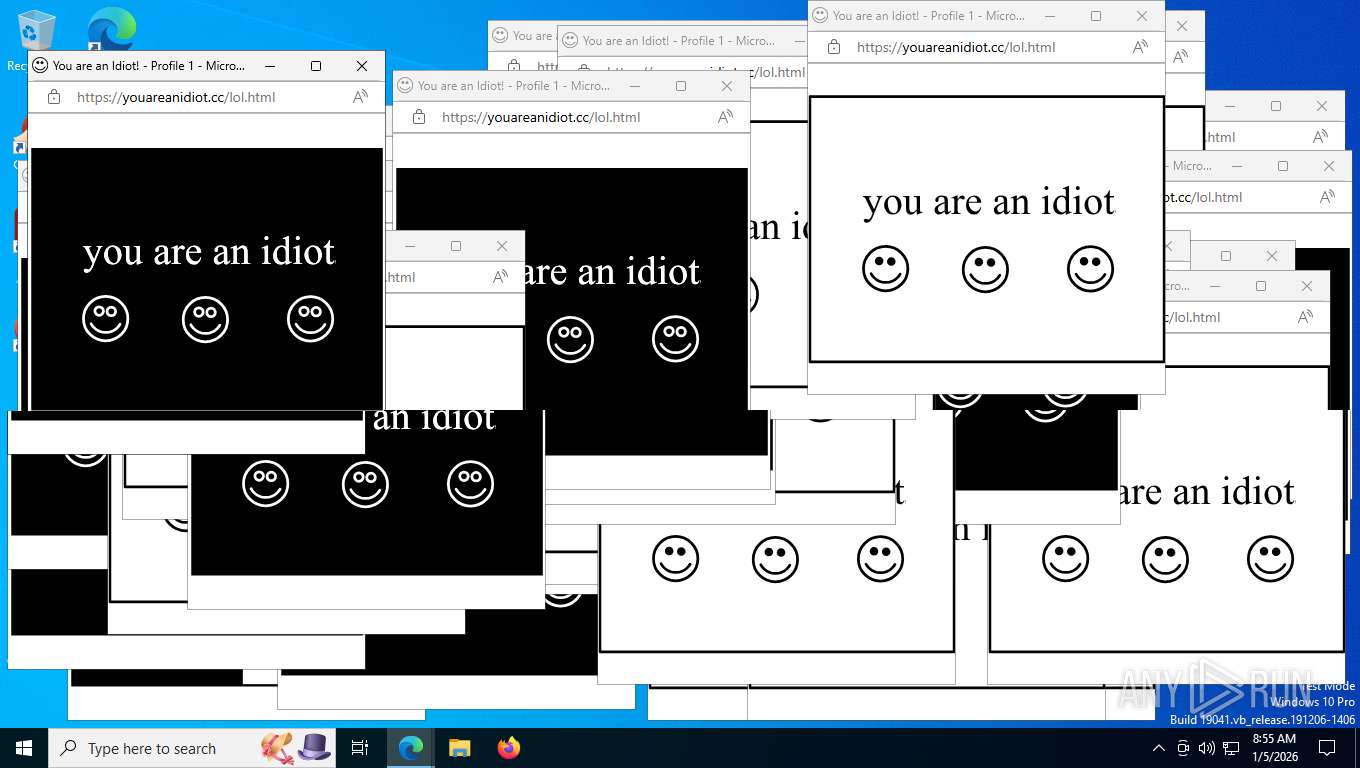
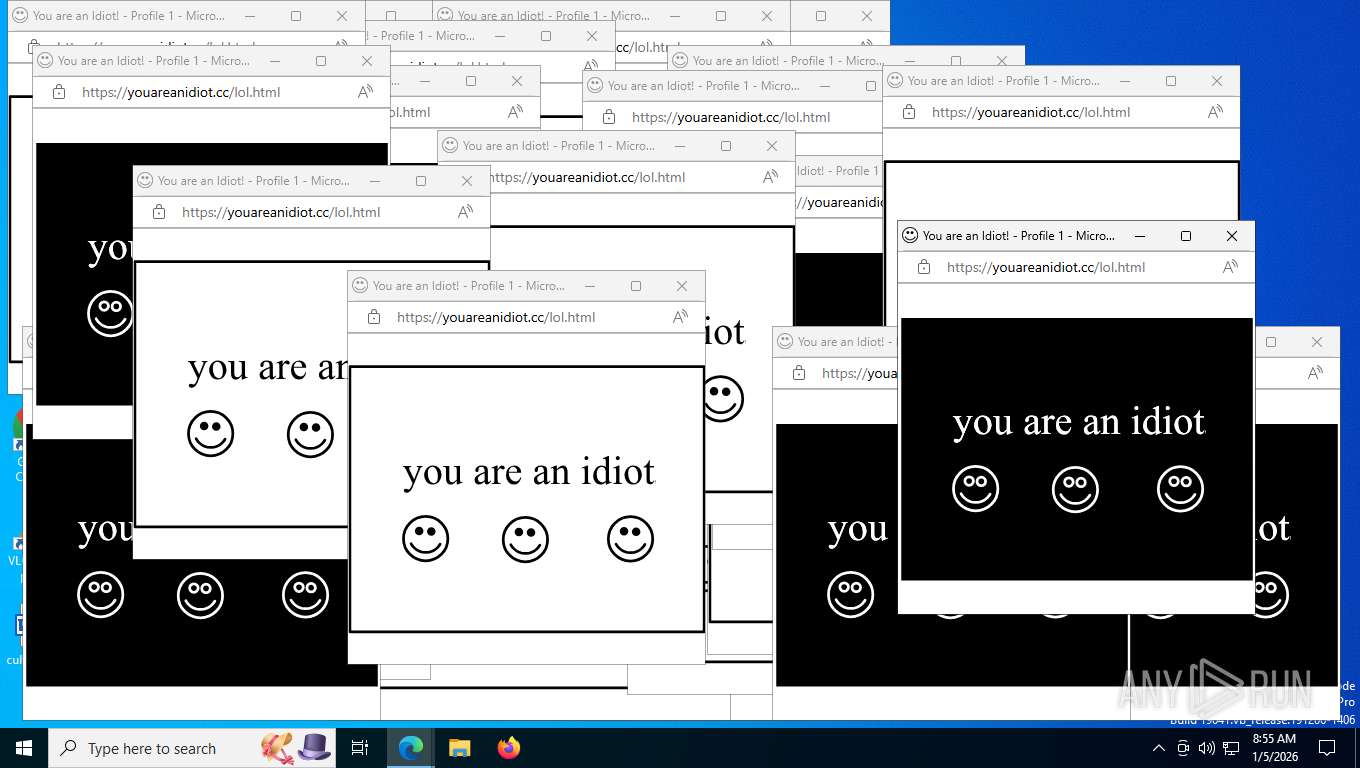
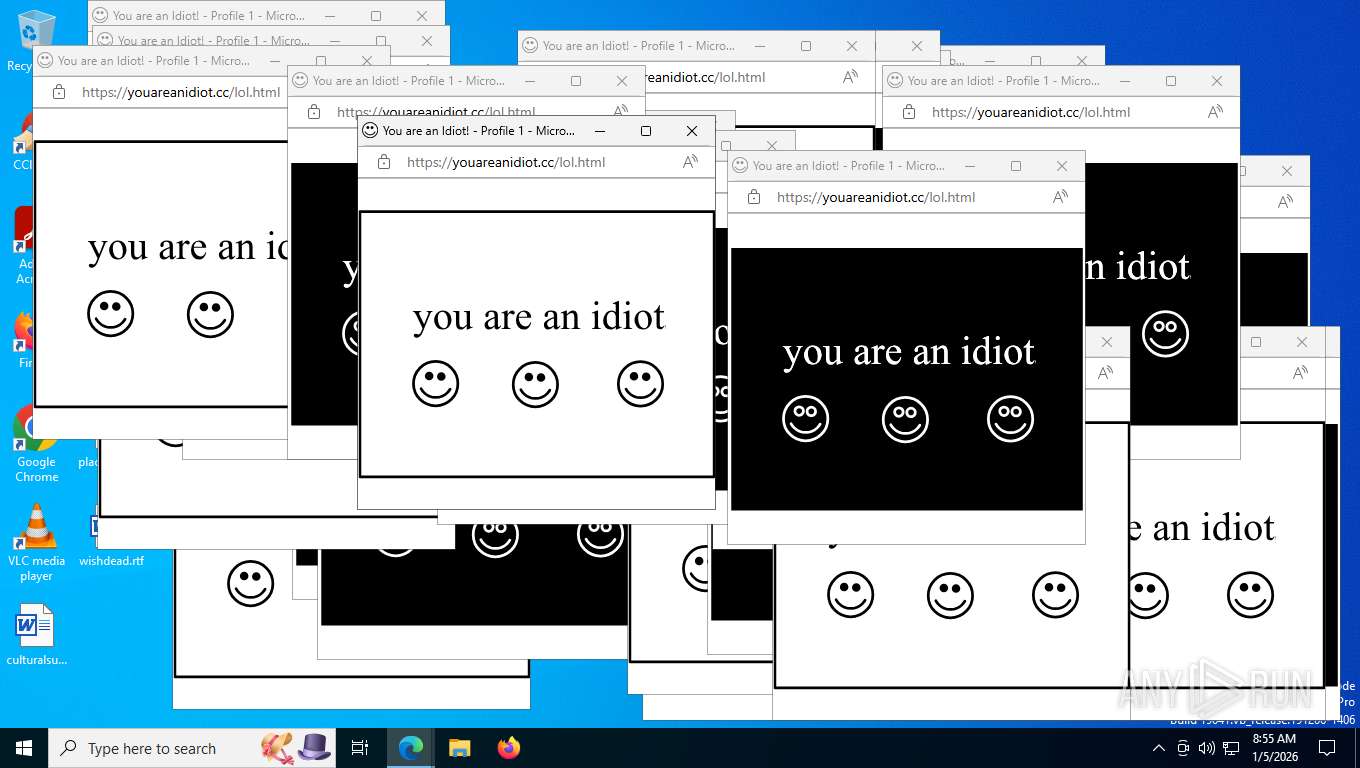
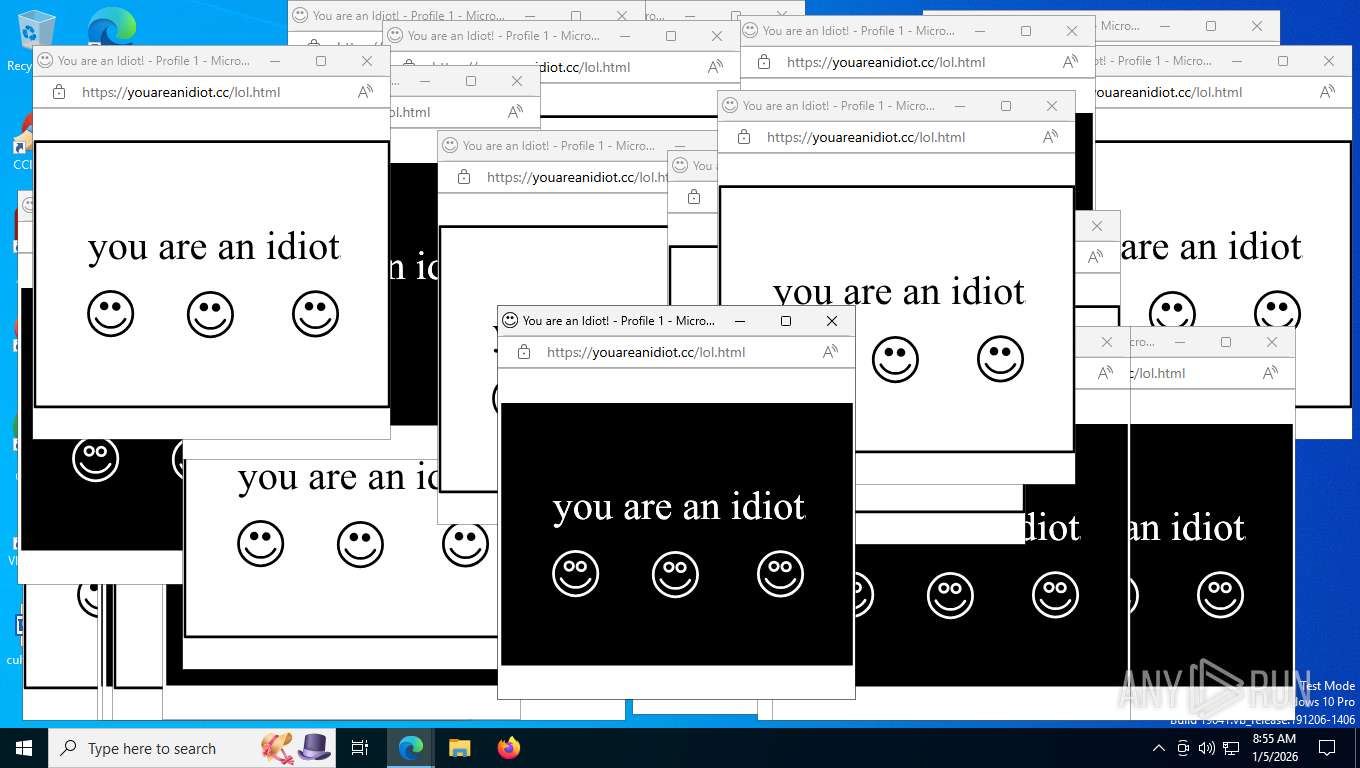
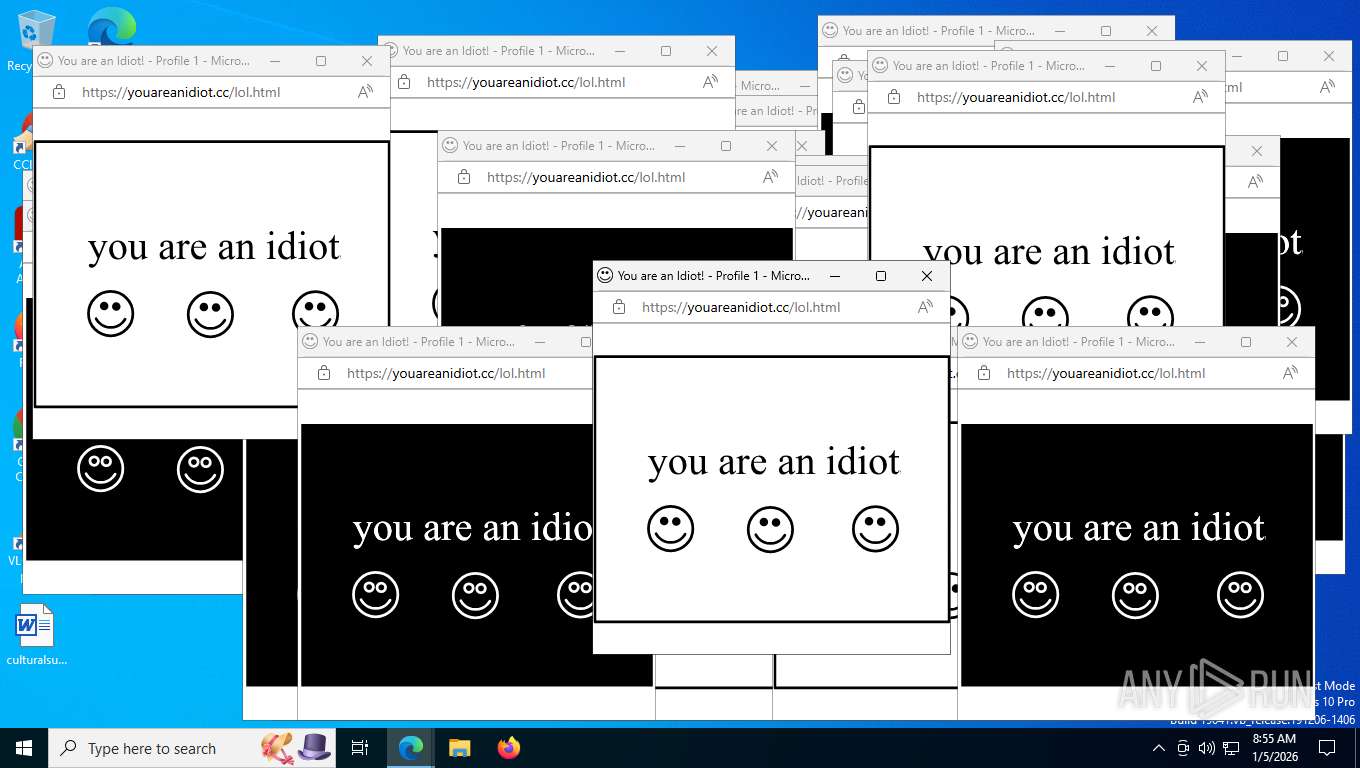
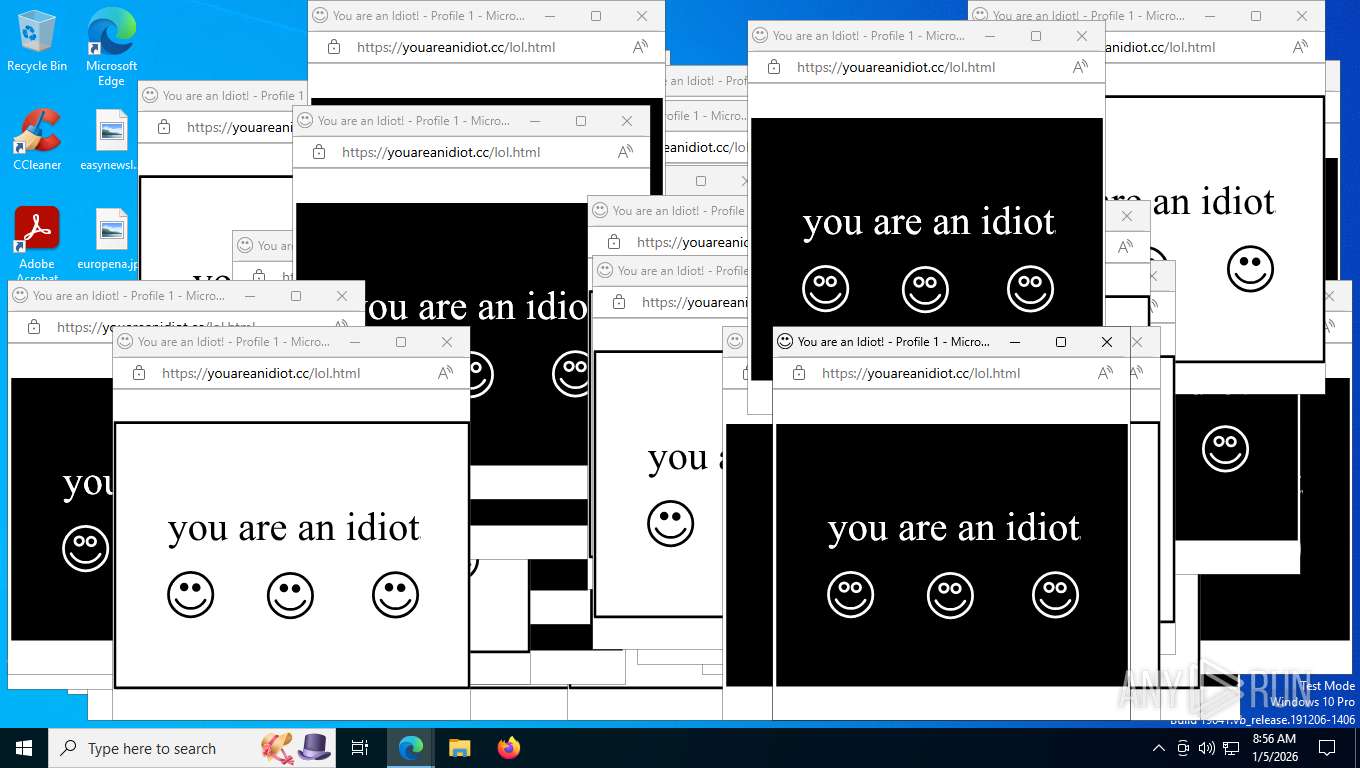
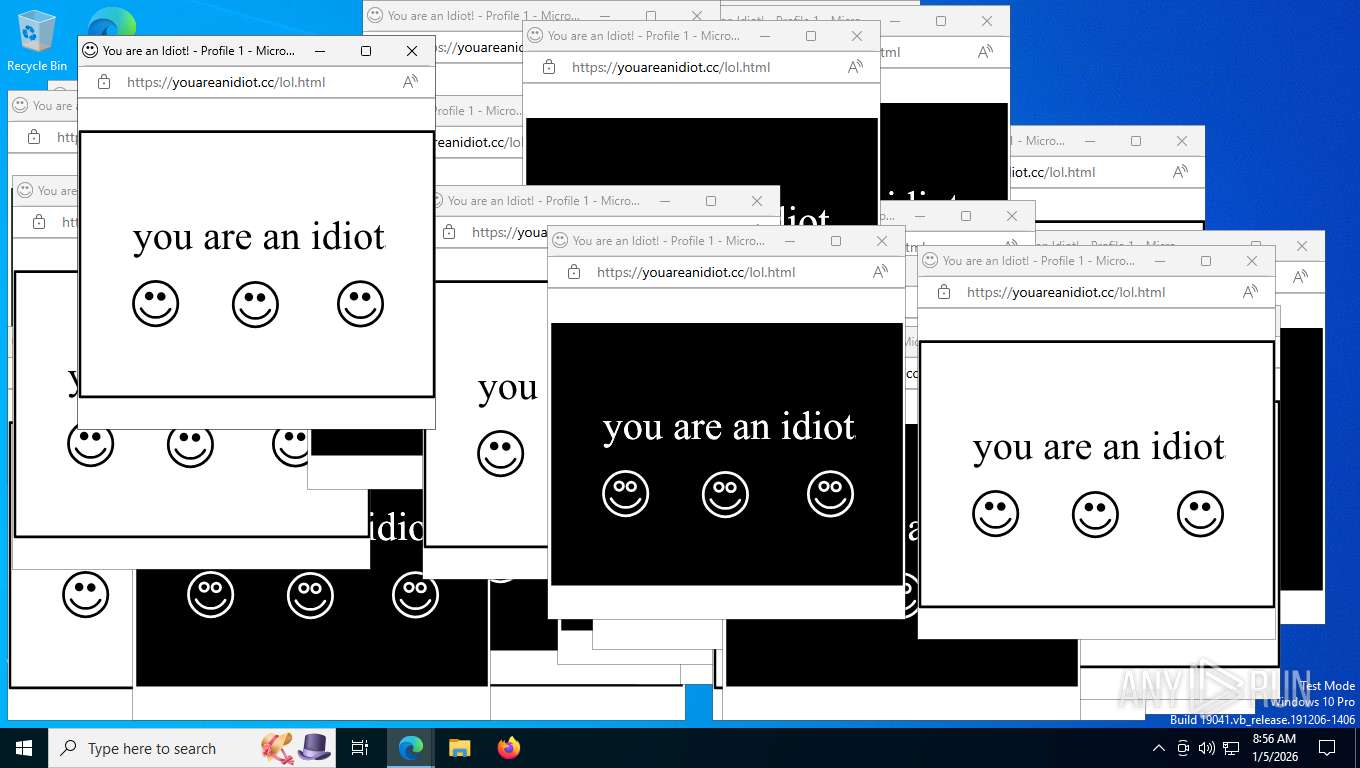
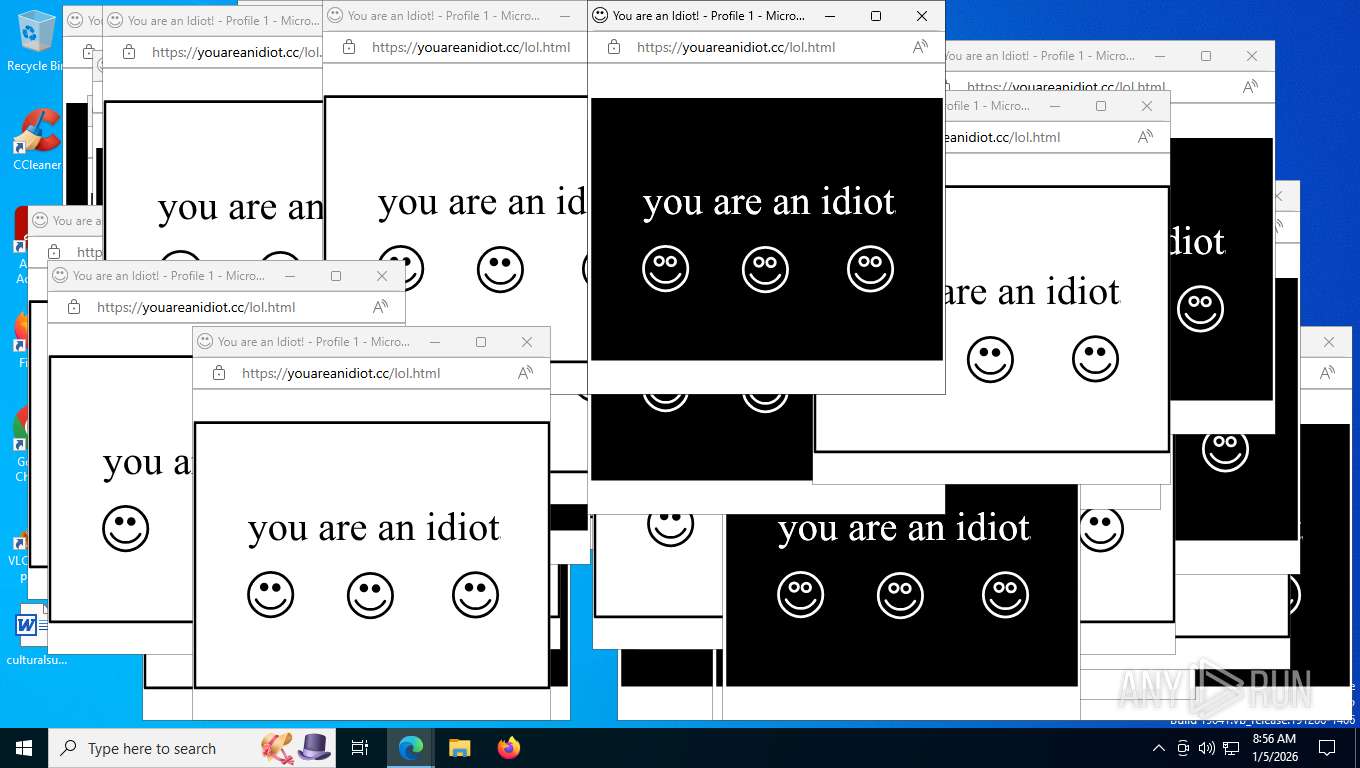
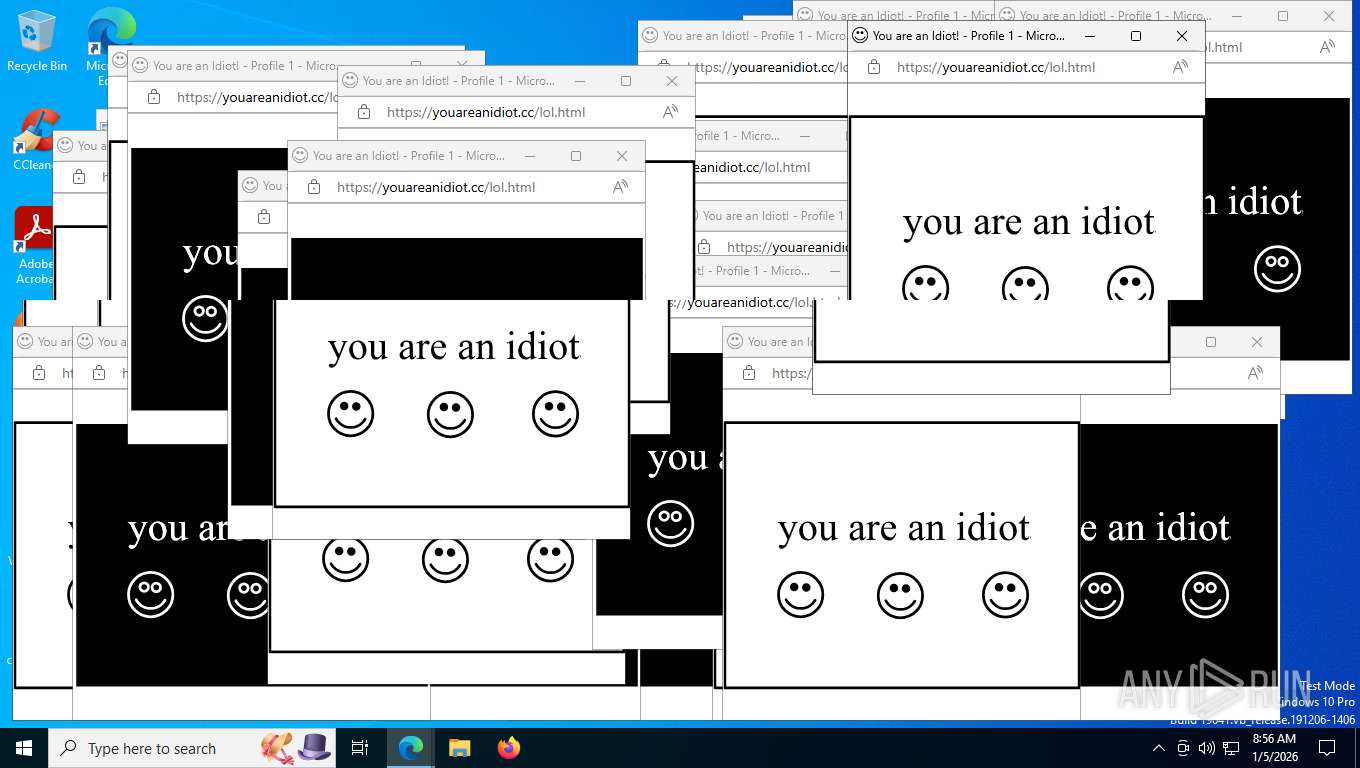
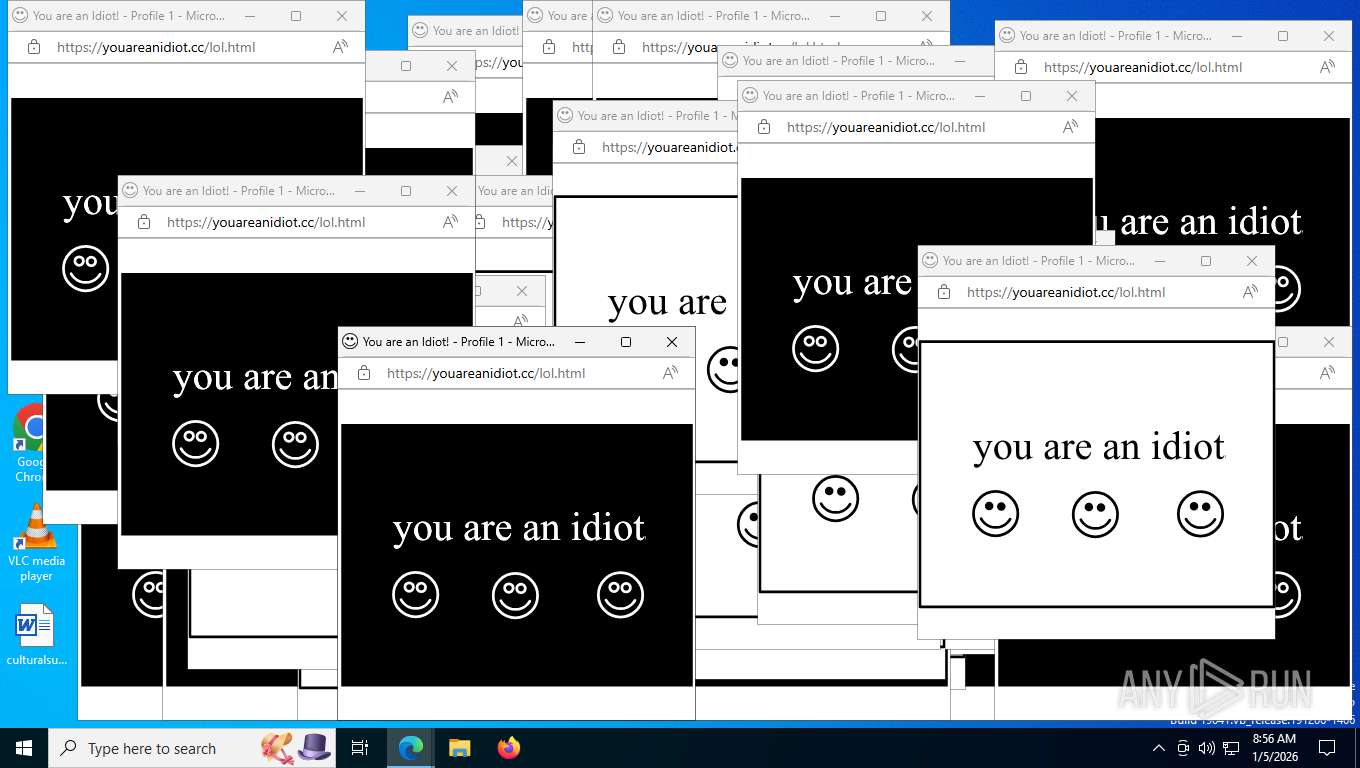
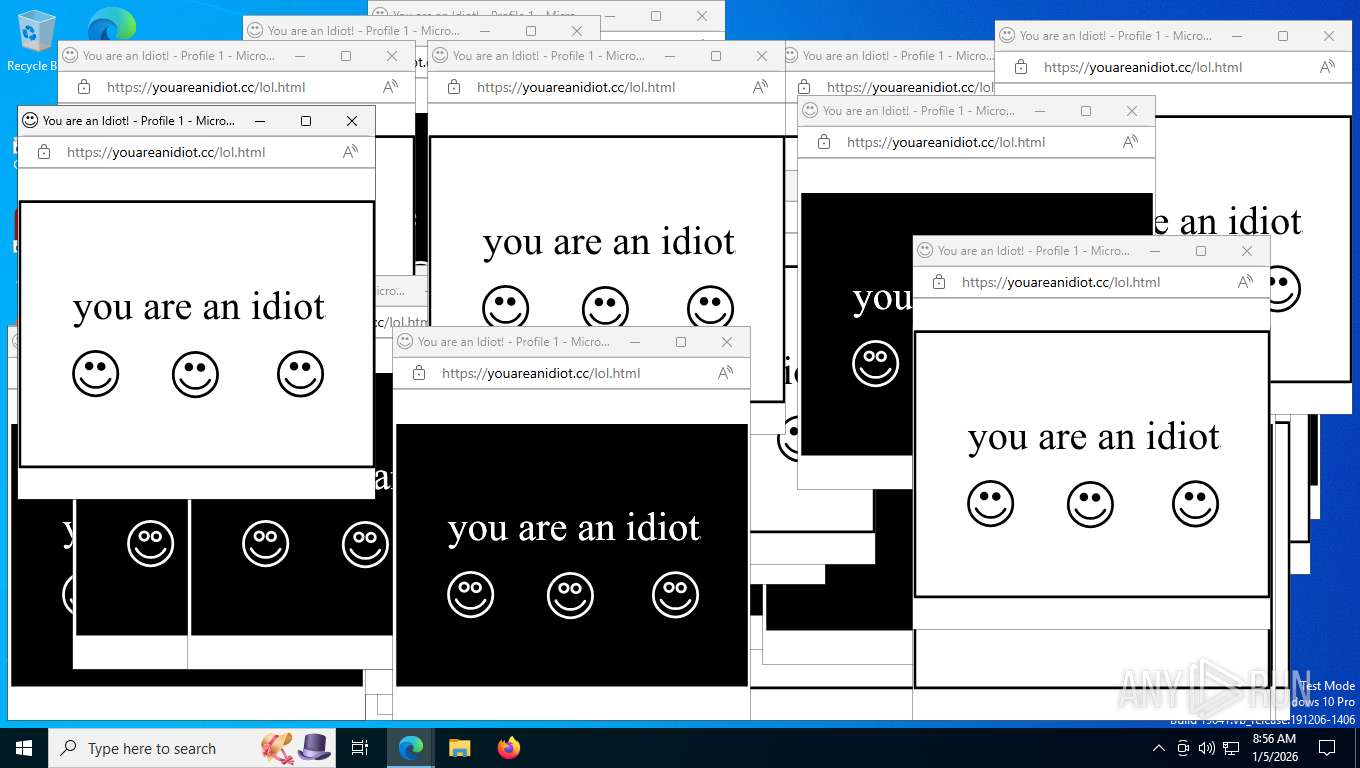
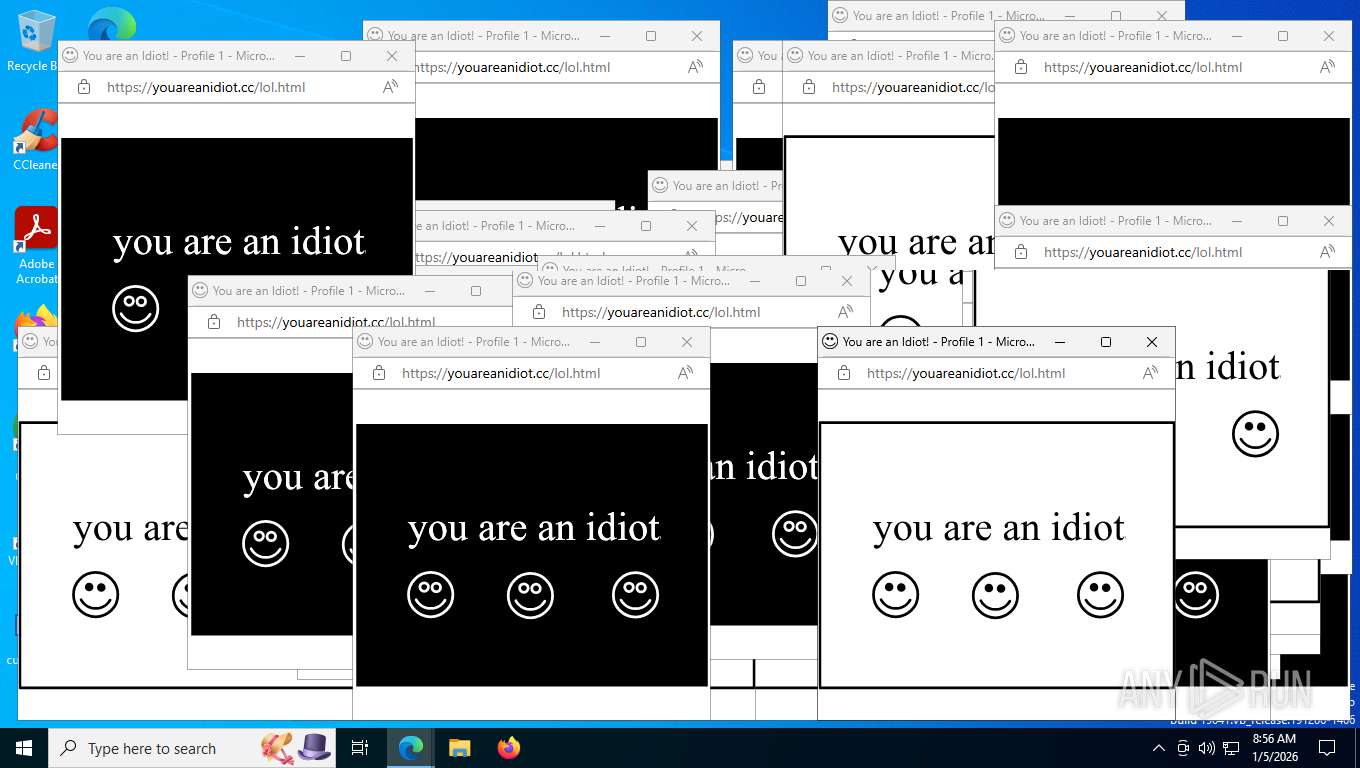
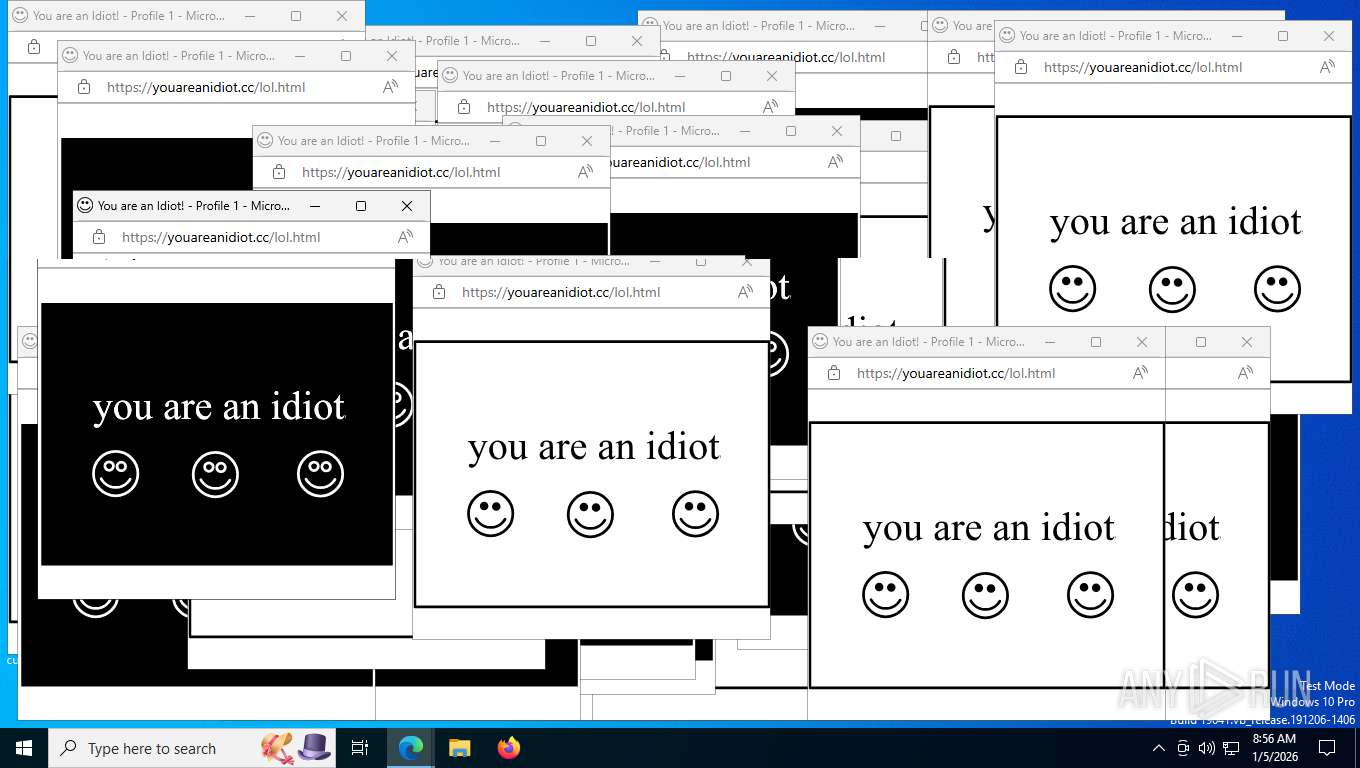
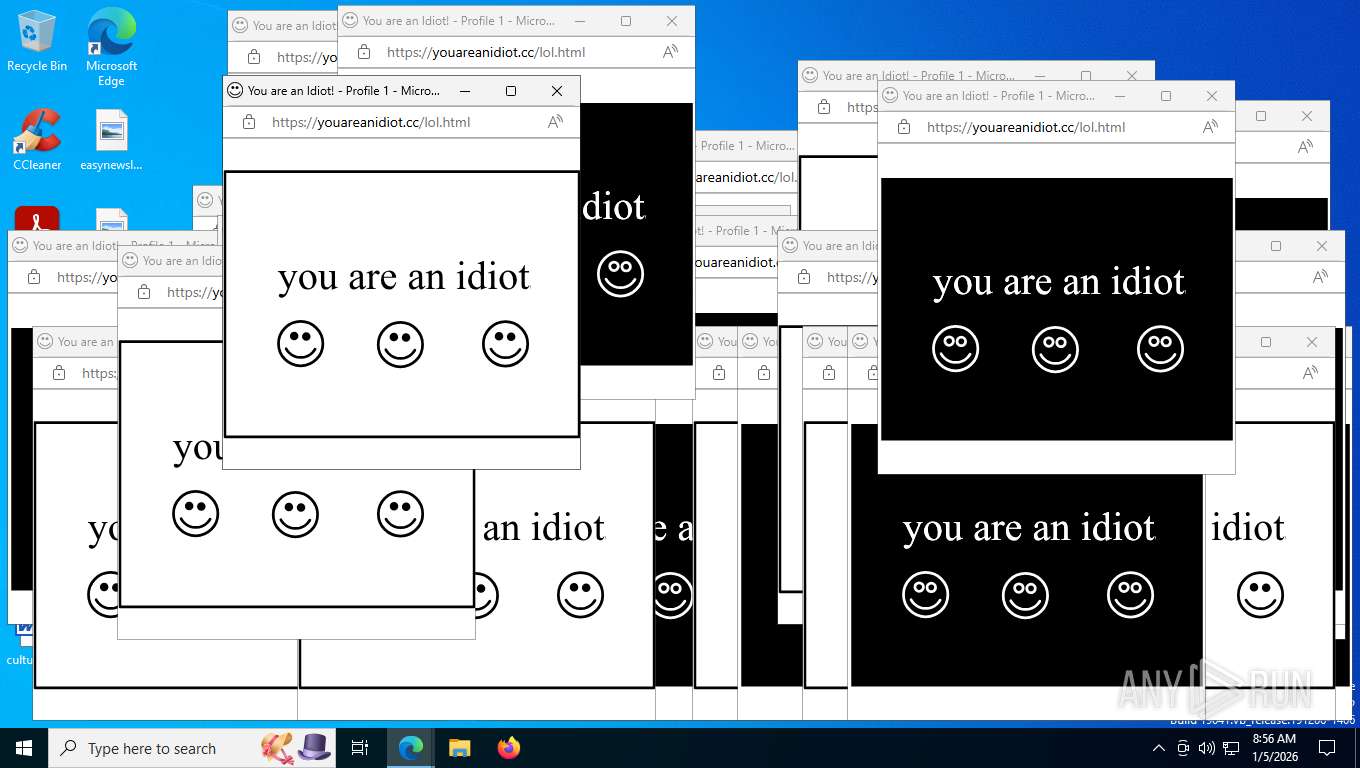
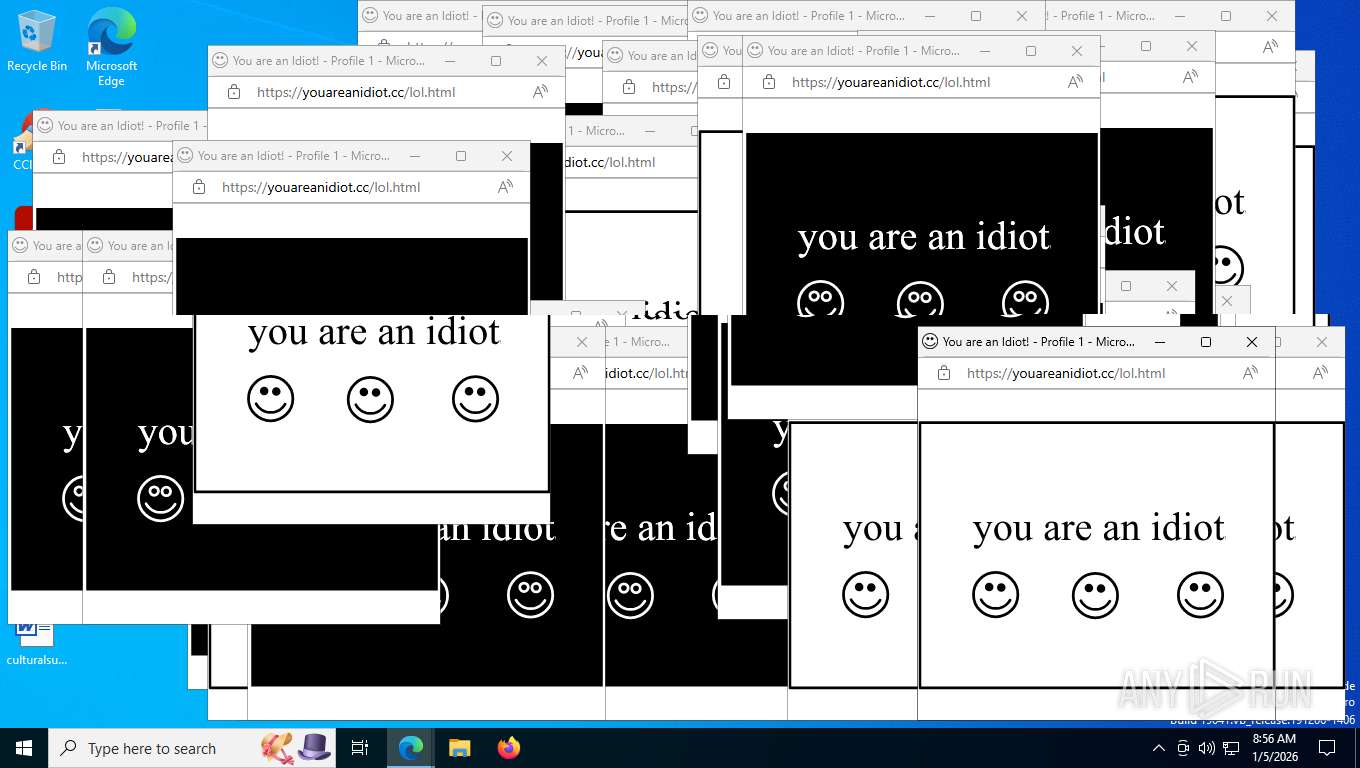
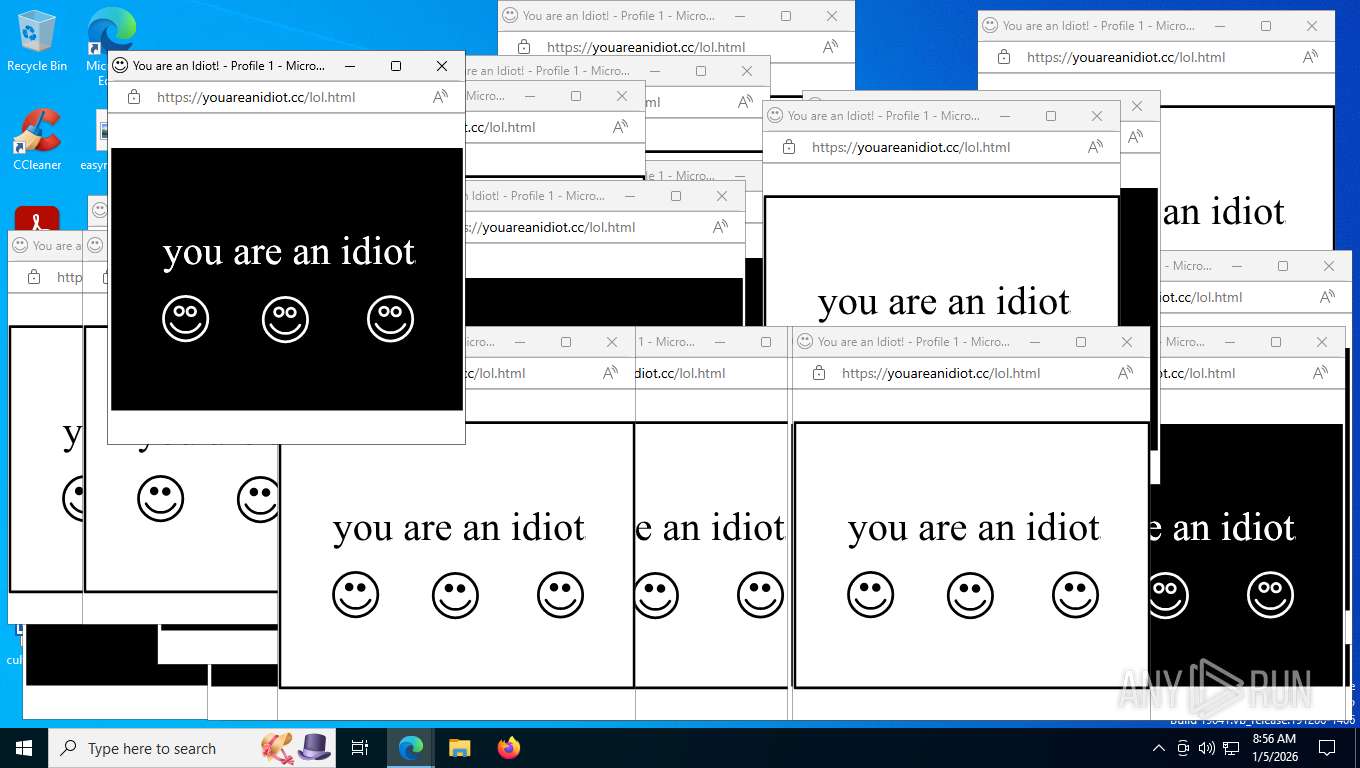
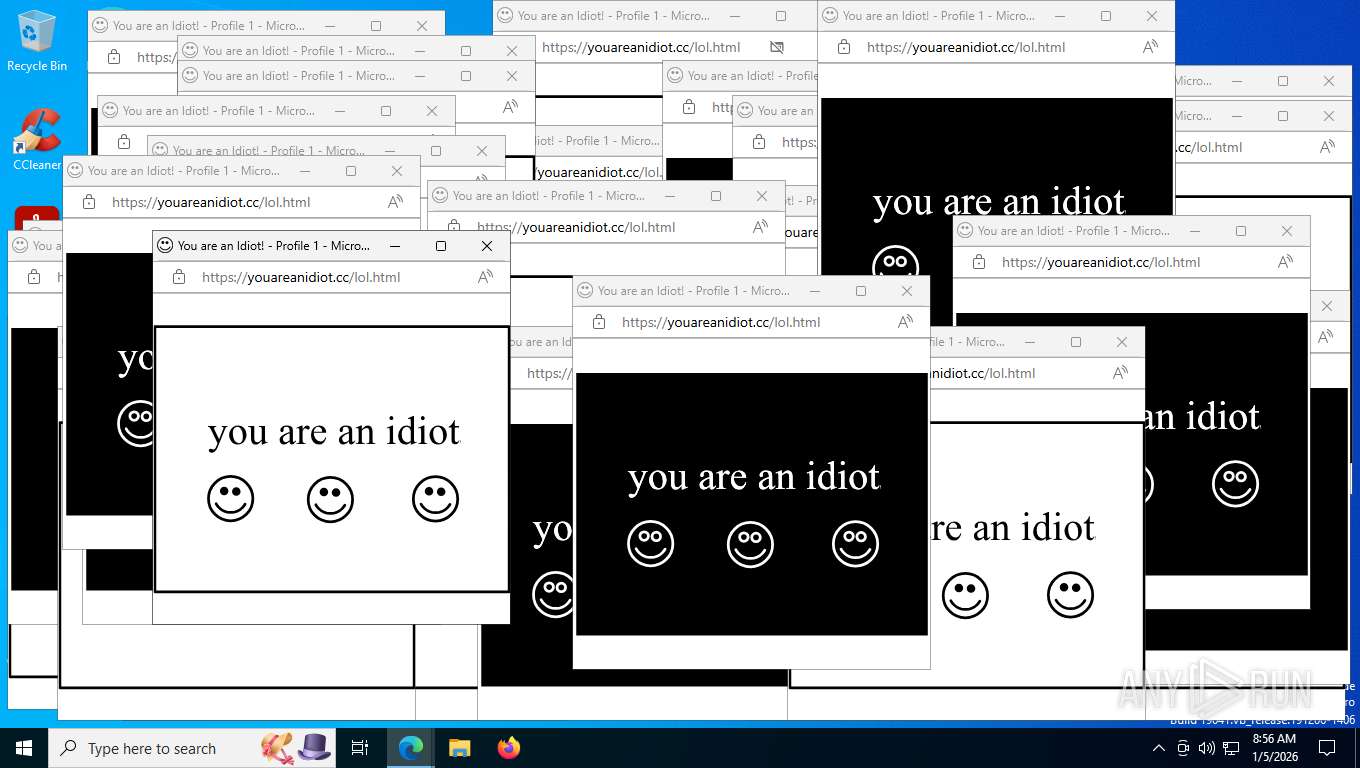
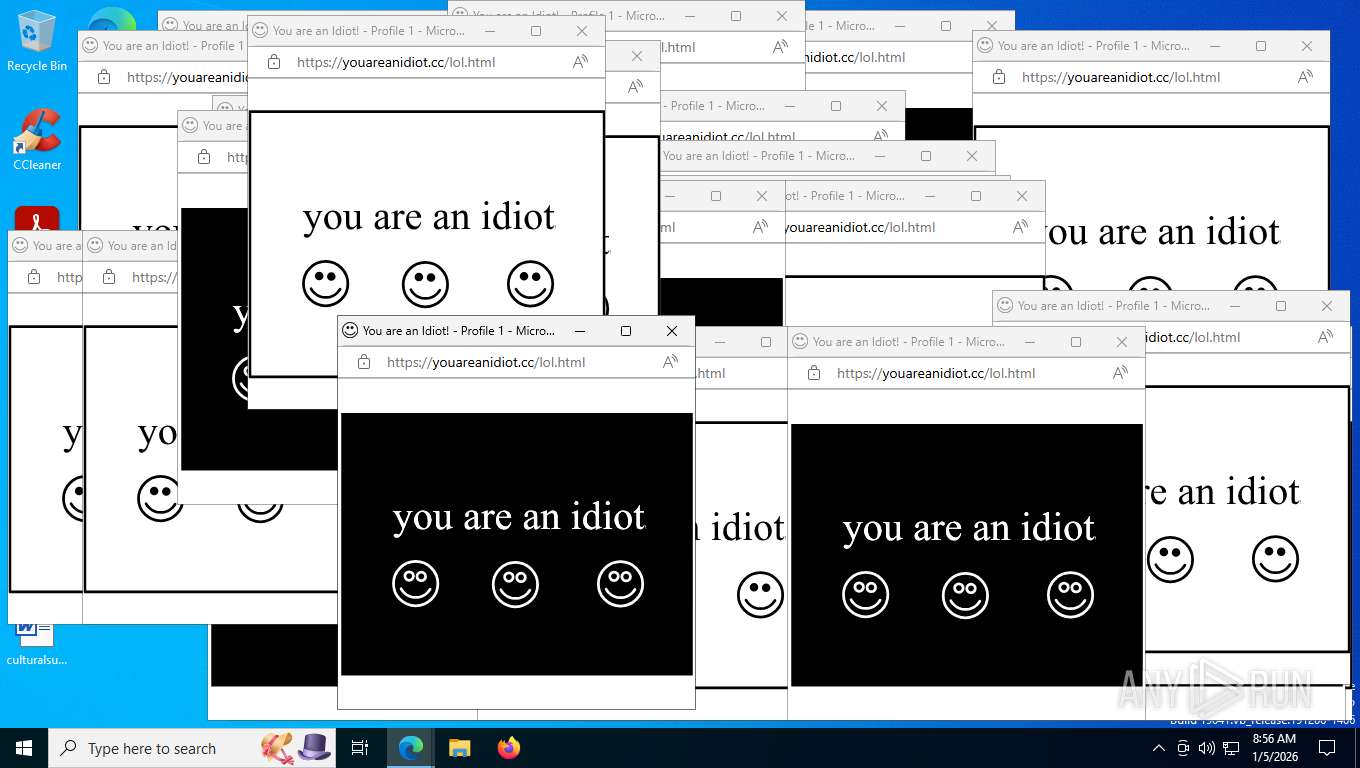
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=26 --always-read-main-dll --field-trial-handle=7928,i,7962077999772660873,4736964718991699309,262144 --variations-seed-version --mojo-platform-channel-handle=1460 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4092,i,7962077999772660873,4736964718991699309,262144 --variations-seed-version --mojo-platform-channel-handle=3884 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3152 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6044,i,7962077999772660873,4736964718991699309,262144 --variations-seed-version --mojo-platform-channel-handle=6072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6552,i,7962077999772660873,4736964718991699309,262144 --variations-seed-version --mojo-platform-channel-handle=6776 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5304 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 5336 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5868 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --instant-process --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=16 --always-read-main-dll --field-trial-handle=6236,i,7962077999772660873,4736964718991699309,262144 --variations-seed-version --mojo-platform-channel-handle=6736 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=8228,i,7962077999772660873,4736964718991699309,262144 --variations-seed-version --mojo-platform-channel-handle=8240 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6916 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6044,i,7962077999772660873,4736964718991699309,262144 --variations-seed-version --mojo-platform-channel-handle=6072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6940 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4672,i,7962077999772660873,4736964718991699309,262144 --variations-seed-version --mojo-platform-channel-handle=6136 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
4 246
Read events
4 246
Write events
0
Delete events
0
Modification events
Executable files
26
Suspicious files
425
Text files
318
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfe11f.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfe11f.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfe12f.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfe12f.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfe12f.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
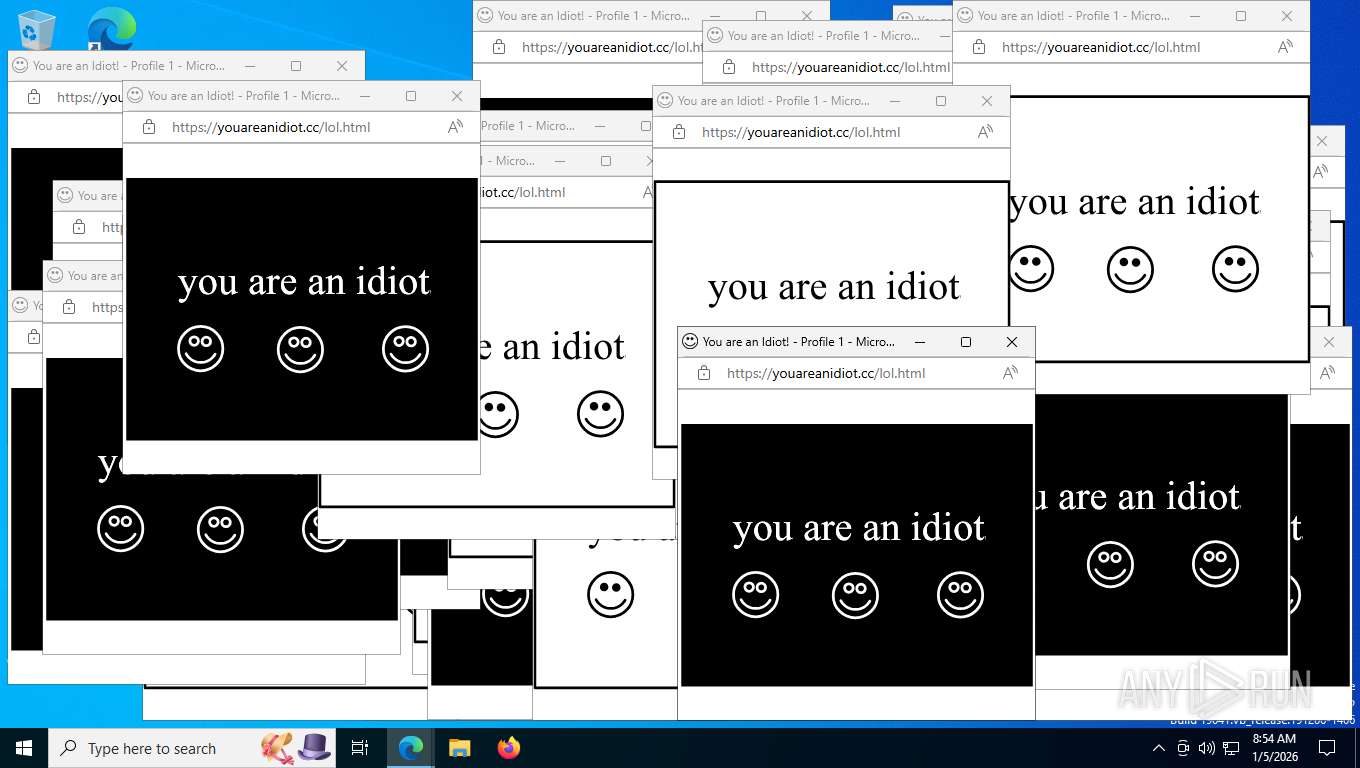
HTTP(S) requests
611
TCP/UDP connections
98
DNS requests
111
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7824 | msedge.exe | GET | 302 | 52.213.100.209:443 | https://jump.offerclk.net/aff_c?offer_id=69540&aff_id=410081&aff_sub=AffiliateApi&aff_sub2=6oq69&aff_sub3=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzUxMiJ9.eyJpc3MiOiJvZ2FkcyIsImF1ZCI6InBvc3RiYWNrIiwiaWF0IjoxNzY3NjIwNzExLCJuYmYiOjE3Njc2MjA3MTEsImRhdGEiOnsiaXAiOiIyYTAyOjZlYTA6Y2MwMjo1NTE2OjoxMiIsInVhIjoiTW96aWxsYS81LjAgKFgxMTsgQ3JPUyB4ODZfNjQgMTQ1NDEuMC4wKSBBcHBsZVdlYktpdC81MzcuMzYgKEtIVE1MLCBsaWtlIEdlY2tvKSBDaHJvbWUvMTQyLjAuMC4wIFNhZmFyaS81MzcuMzYiLCJyZWYiOm51bGx9fQ.Q4VzuQDgtqAjm_QUgUWxajTMT43eWv_pTQiJu4-KoEbiInDniPqEc9NKyHF9-AcQkC-hOpz-uPzS8WWiqaK2gw&aff_sub4=a0f0a076&aff_sub5=42b6aaa8-6f90-48b8-bf11-1a63836eab7c_69682283&aff_sub4=a0f0a076&aff_sub5=42b6aaa8-6f90-48b8-bf11-1a63836eab7c_69682283 | US | — | — | unknown |
7824 | msedge.exe | GET | 200 | 23.22.126.183:443 | https://mobileoasis.net/favicon.ico | US | — | — | unknown |
7824 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
7824 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:WIveDiGoA-8Xi7raDPEjZzAE2i_ow_zxXVhBGq2kvgA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
7824 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | US | text | 768 b | whitelisted |
7824 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 446 b | whitelisted |
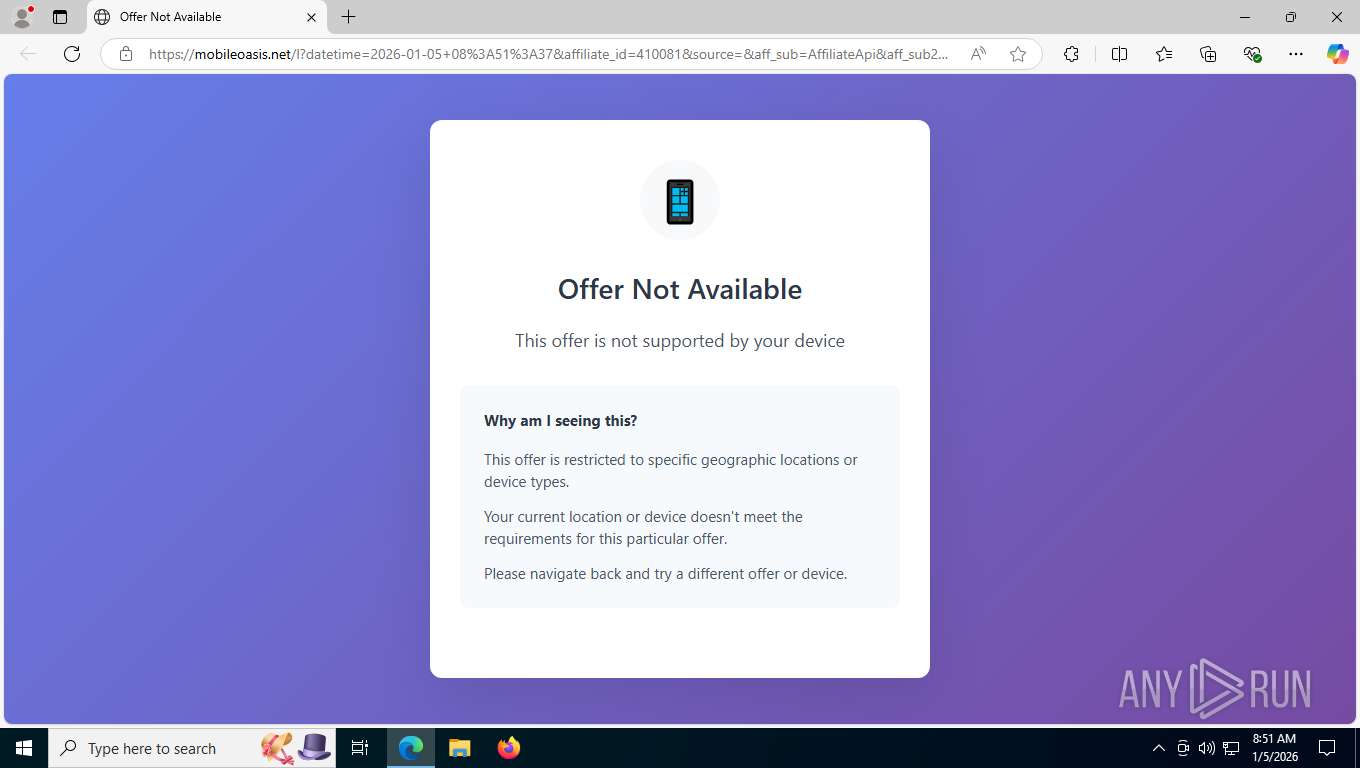
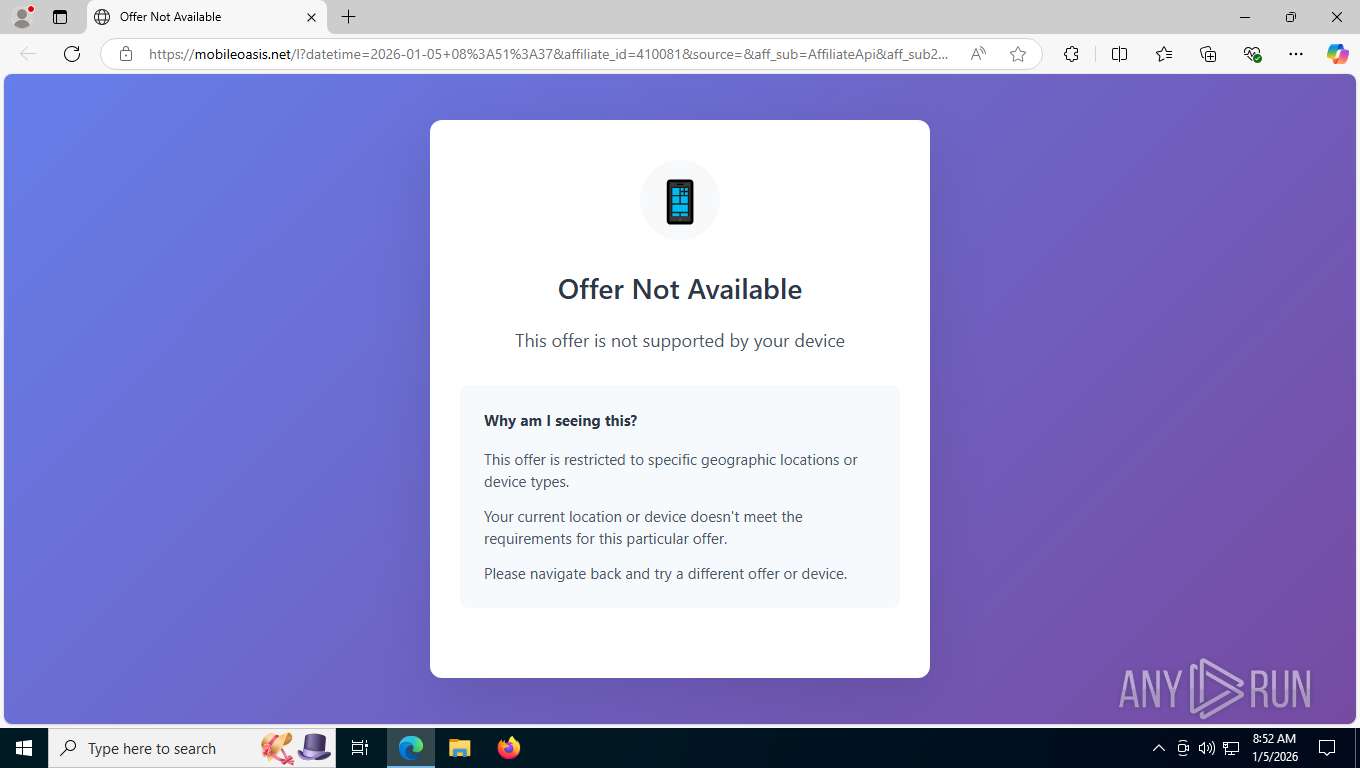
7824 | msedge.exe | GET | 200 | 23.22.126.183:443 | https://mobileoasis.net/l?datetime=2026-01-05+08%3A51%3A37&affiliate_id=410081&source=&aff_sub=AffiliateApi&aff_sub2=6oq69&offer_id=69540&advertiser_id=718&country_code=FR&ip=45.91.22.76&device_os=Desktop&device_os_version= | US | html | 3.70 Kb | unknown |
7824 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
7824 | msedge.exe | GET | 302 | 52.213.100.209:443 | https://jump.offerclk.net/aff_c?offer_id=69540&aff_id=410081&aff_sub=AffiliateApi&aff_sub2=6oq69&aff_sub3=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzUxMiJ9.eyJpc3MiOiJvZ2FkcyIsImF1ZCI6InBvc3RiYWNrIiwiaWF0IjoxNzY3NjIwNzExLCJuYmYiOjE3Njc2MjA3MTEsImRhdGEiOnsiaXAiOiIyYTAyOjZlYTA6Y2MwMjo1NTE2OjoxMiIsInVhIjoiTW96aWxsYS81LjAgKFgxMTsgQ3JPUyB4ODZfNjQgMTQ1NDEuMC4wKSBBcHBsZVdlYktpdC81MzcuMzYgKEtIVE1MLCBsaWtlIEdlY2tvKSBDaHJvbWUvMTQyLjAuMC4wIFNhZmFyaS81MzcuMzYiLCJyZWYiOm51bGx9fQ.Q4VzuQDgtqAjm_QUgUWxajTMT43eWv_pTQiJu4-KoEbiInDniPqEc9NKyHF9-AcQkC-hOpz-uPzS8WWiqaK2gw&aff_sub4=a0f0a076&aff_sub5=42b6aaa8-6f90-48b8-bf11-1a63836eab7c_69682283&aff_sub4=a0f0a076&aff_sub5=42b6aaa8-6f90-48b8-bf11-1a63836eab7c_69682283&ch-redirect=1 | US | html | 447 b | unknown |
7824 | msedge.exe | GET | 200 | 2.16.204.152:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | NL | text | 128 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4020 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3520 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7824 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7824 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7824 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7824 | msedge.exe | 52.213.100.209:443 | jump.offerclk.net | AMAZON-02 | US | whitelisted |
7824 | msedge.exe | 104.18.23.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
jump.offerclk.net |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
mobileoasis.net |
| unknown |
www.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
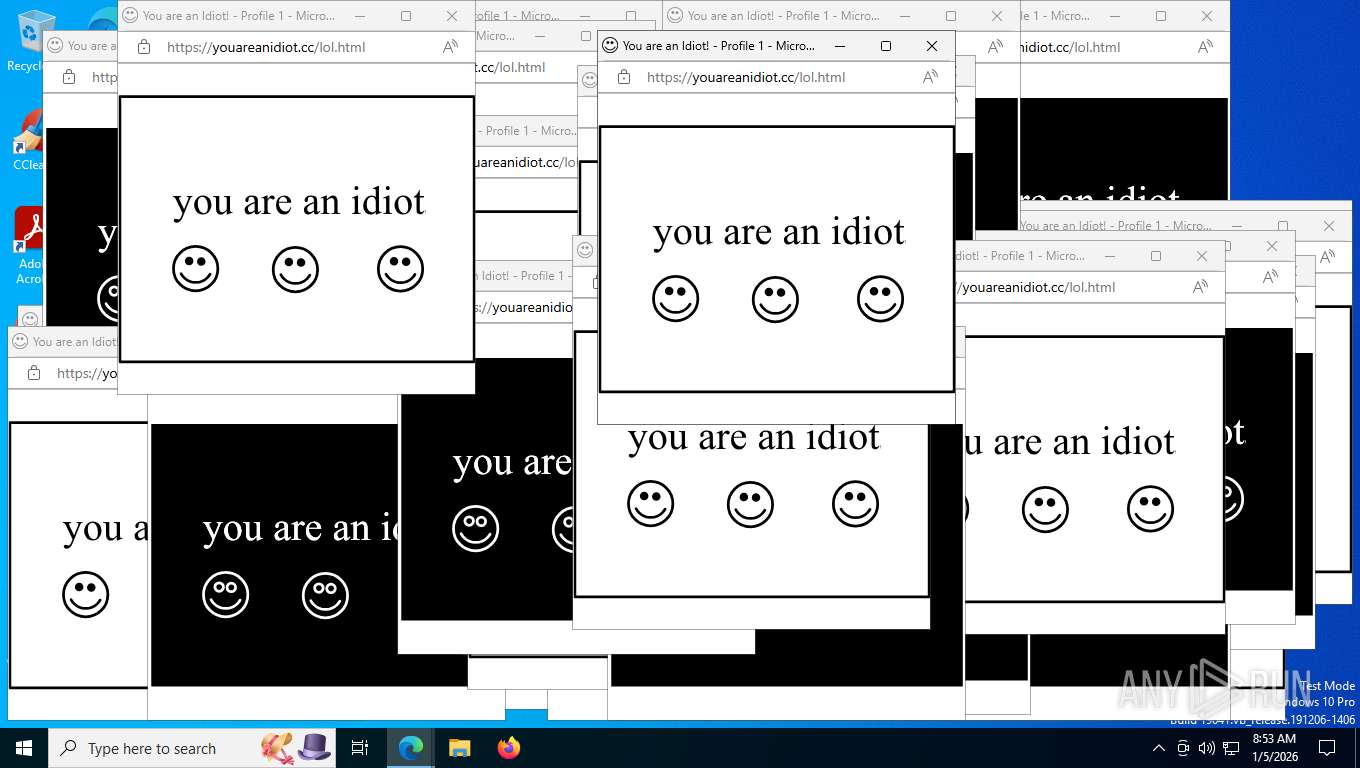
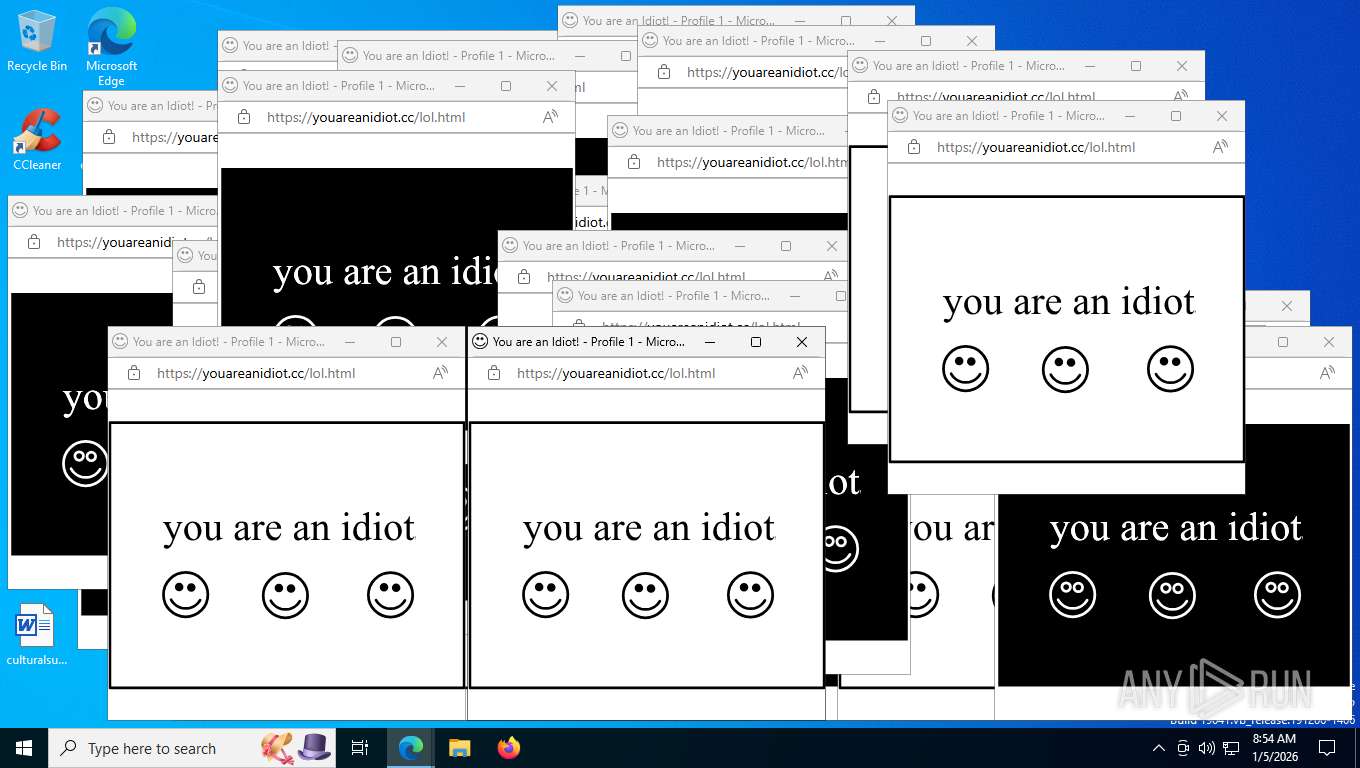
Threats
PID | Process | Class | Message |
|---|---|---|---|
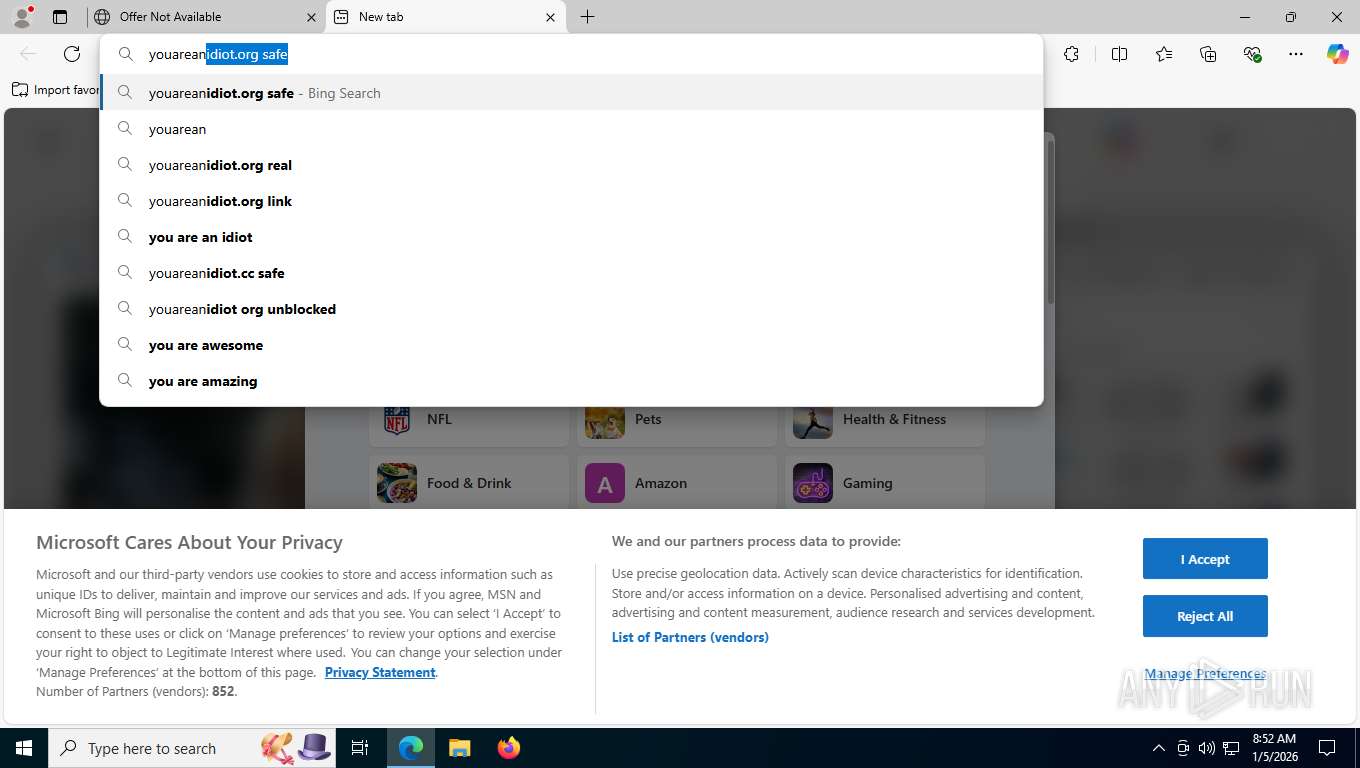
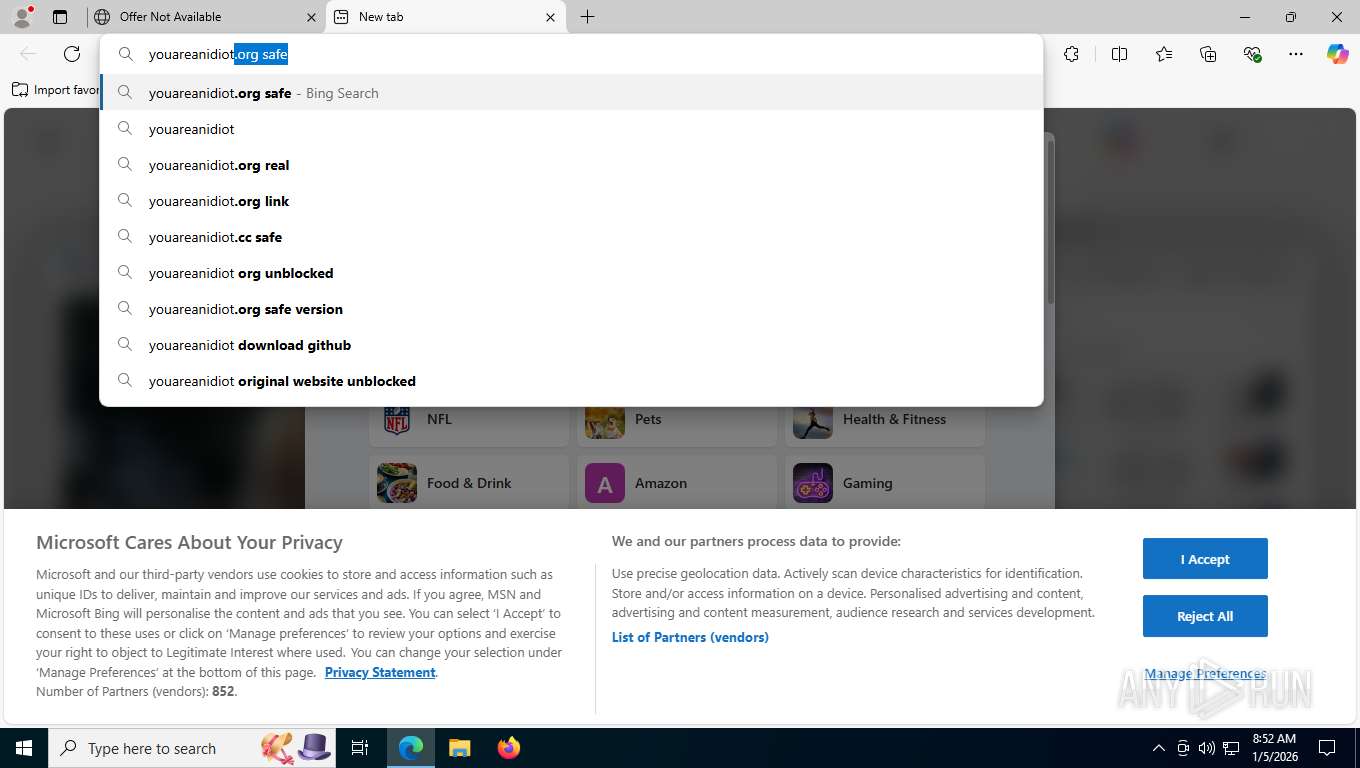
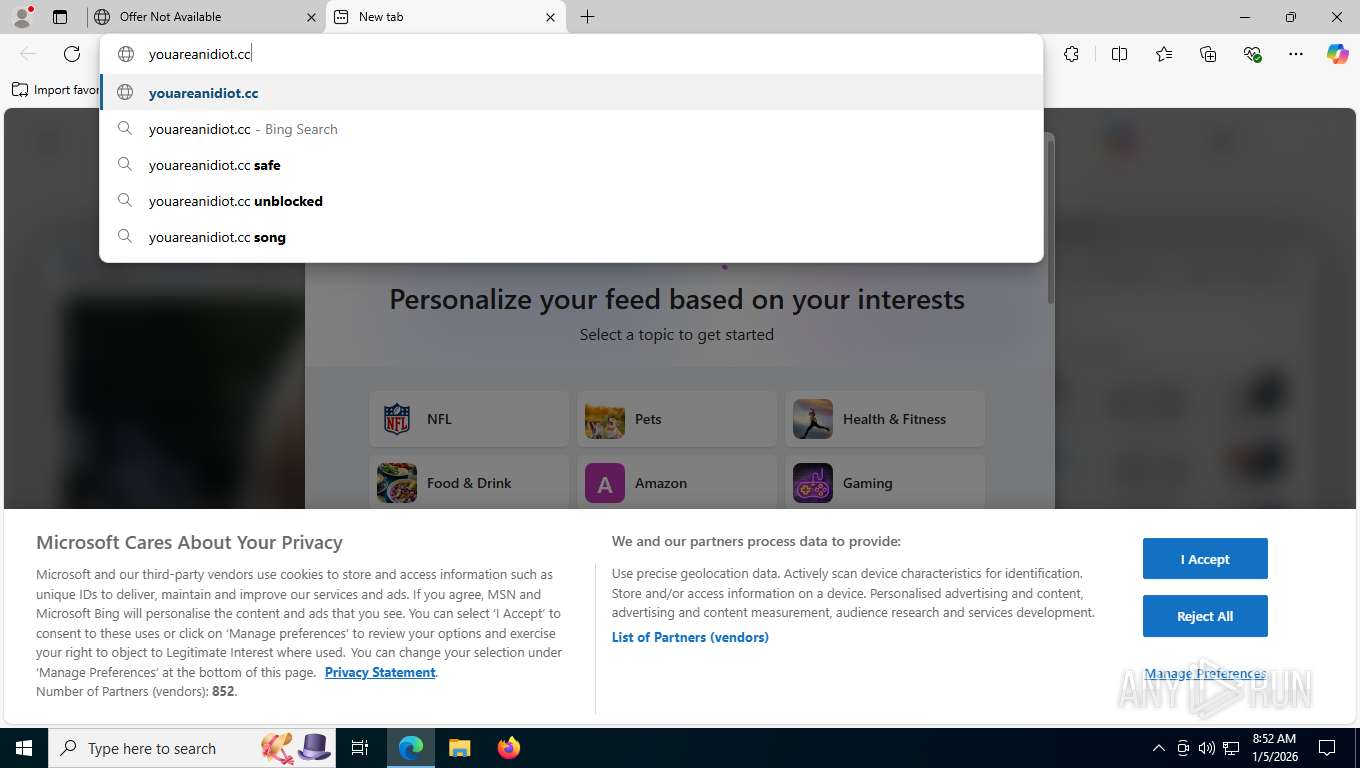
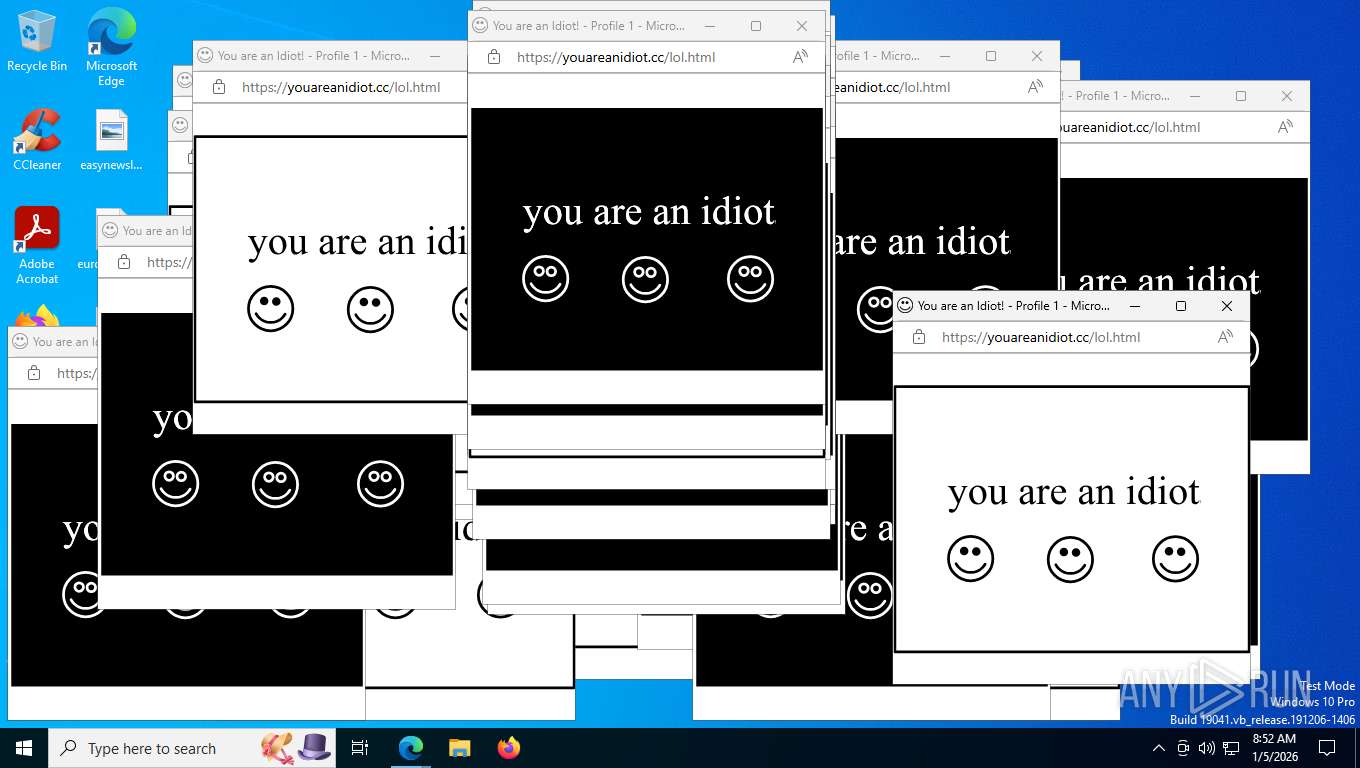
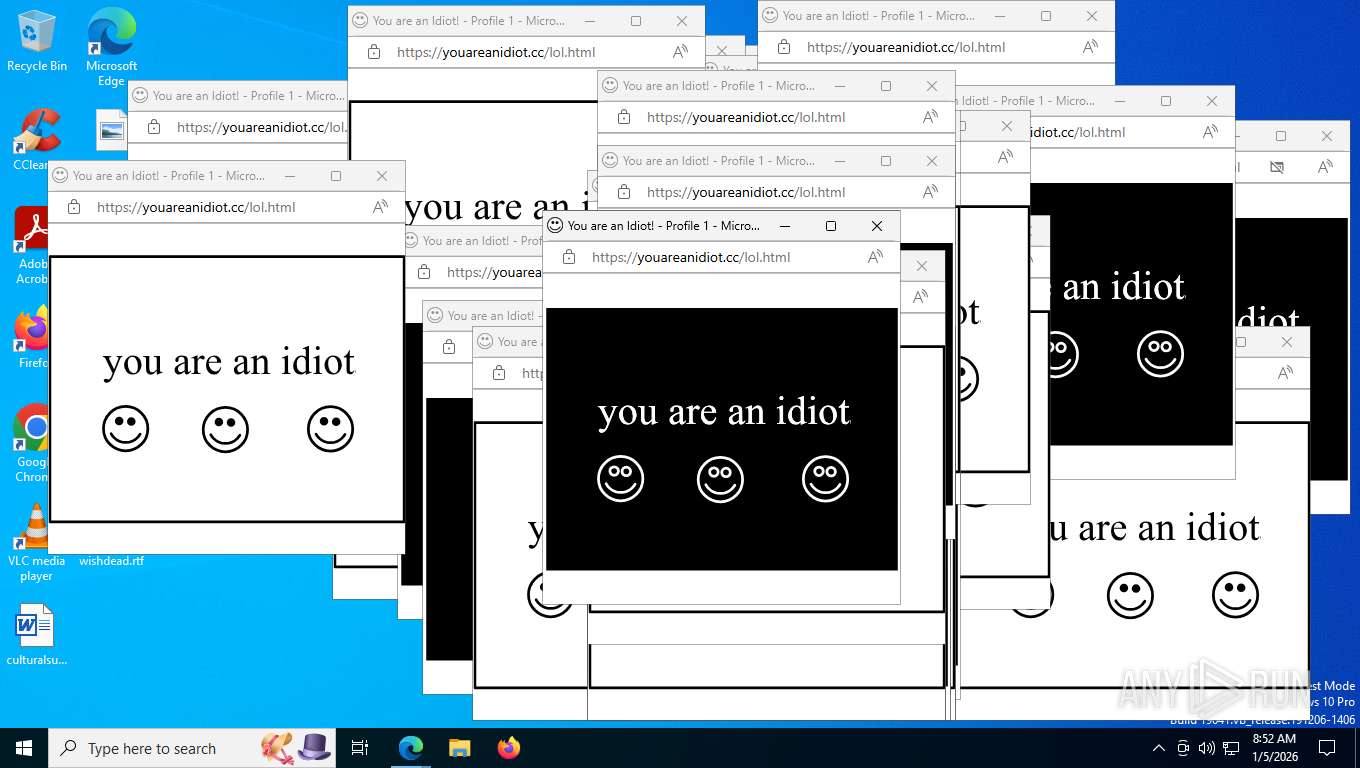
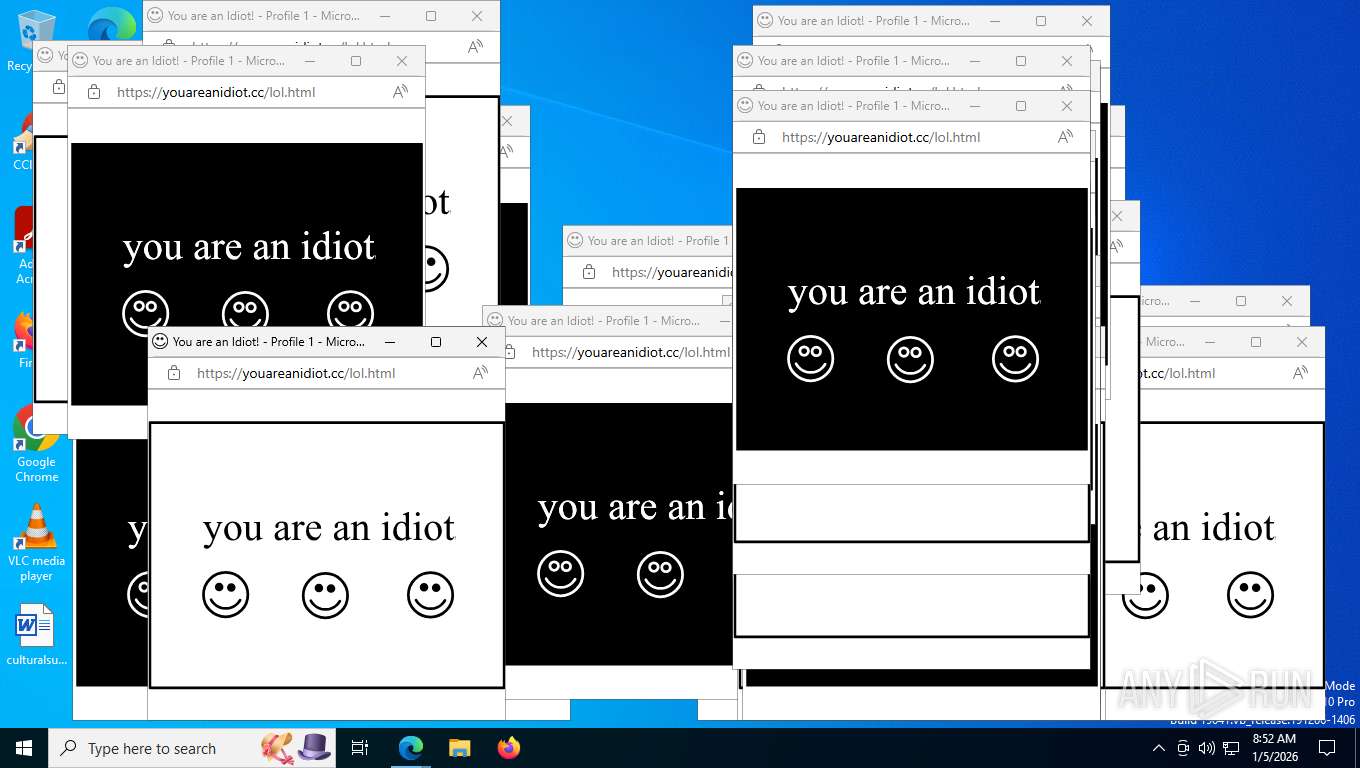
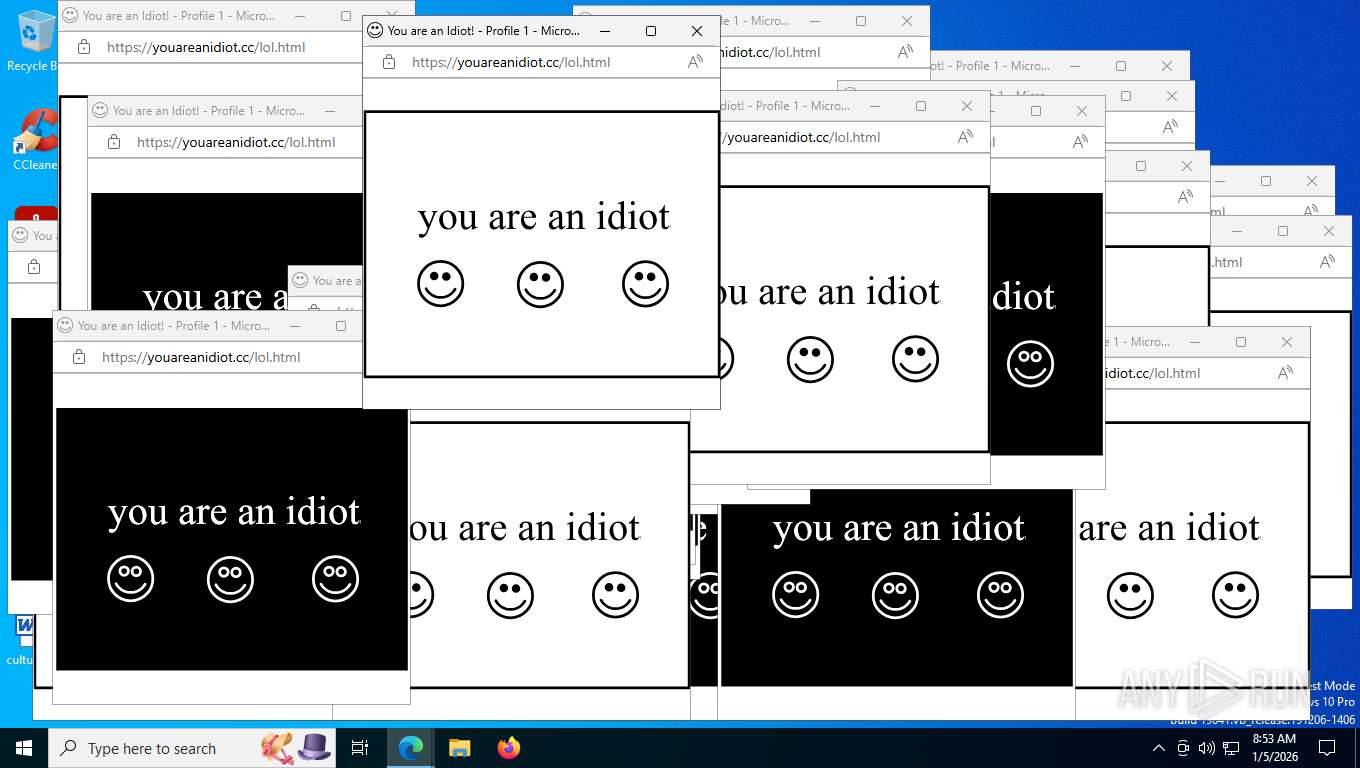
7824 | msedge.exe | Misc activity | INFO [ANY.RUN] .cc TLD domain request |
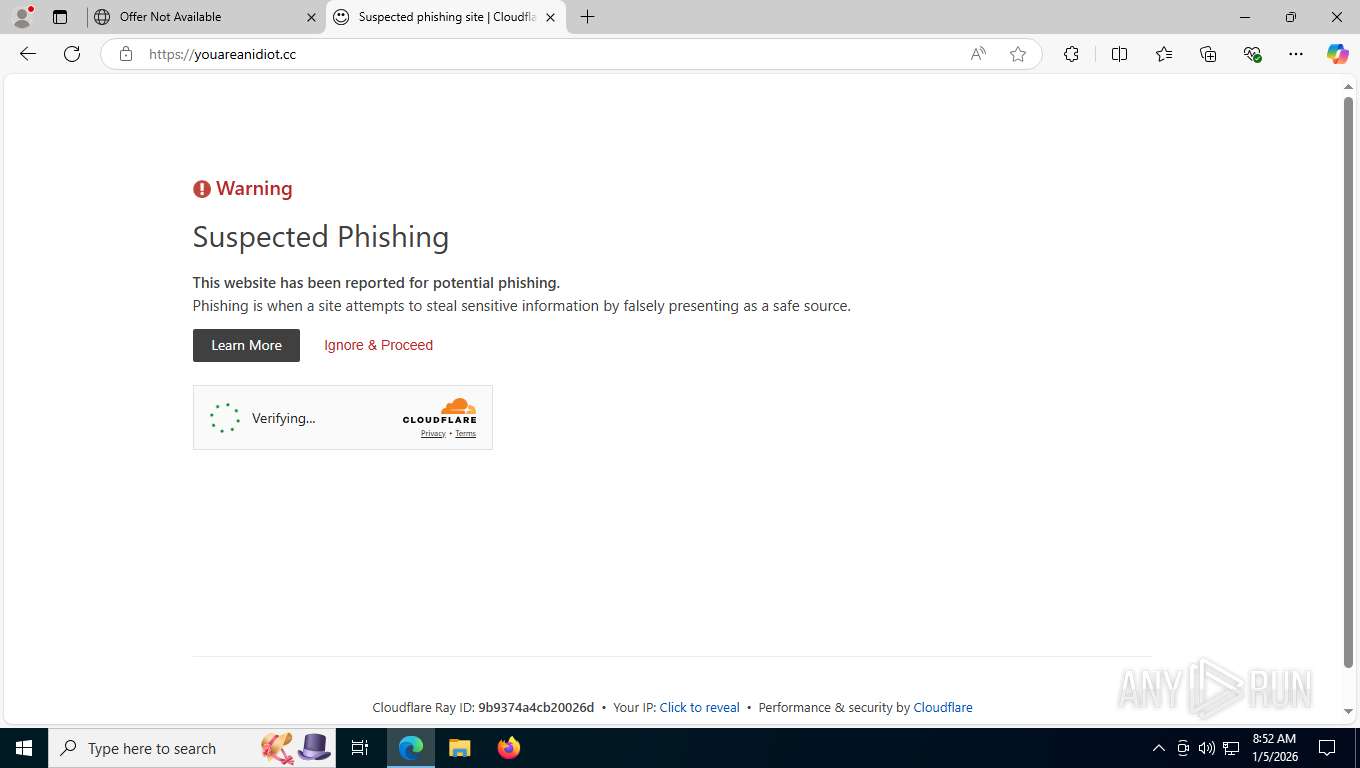
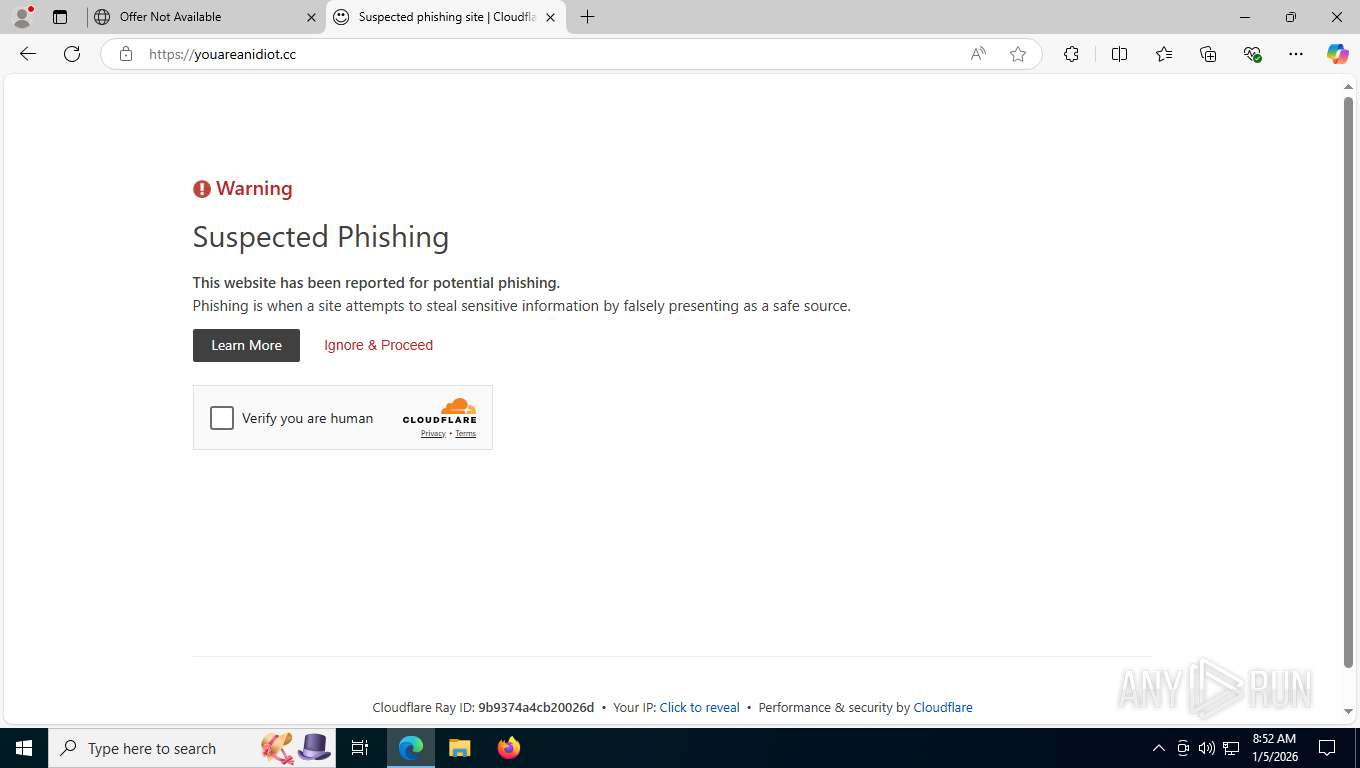
7824 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7824 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7824 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
— | — | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain by Cloudflare Turnstile warning |
7824 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7824 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |