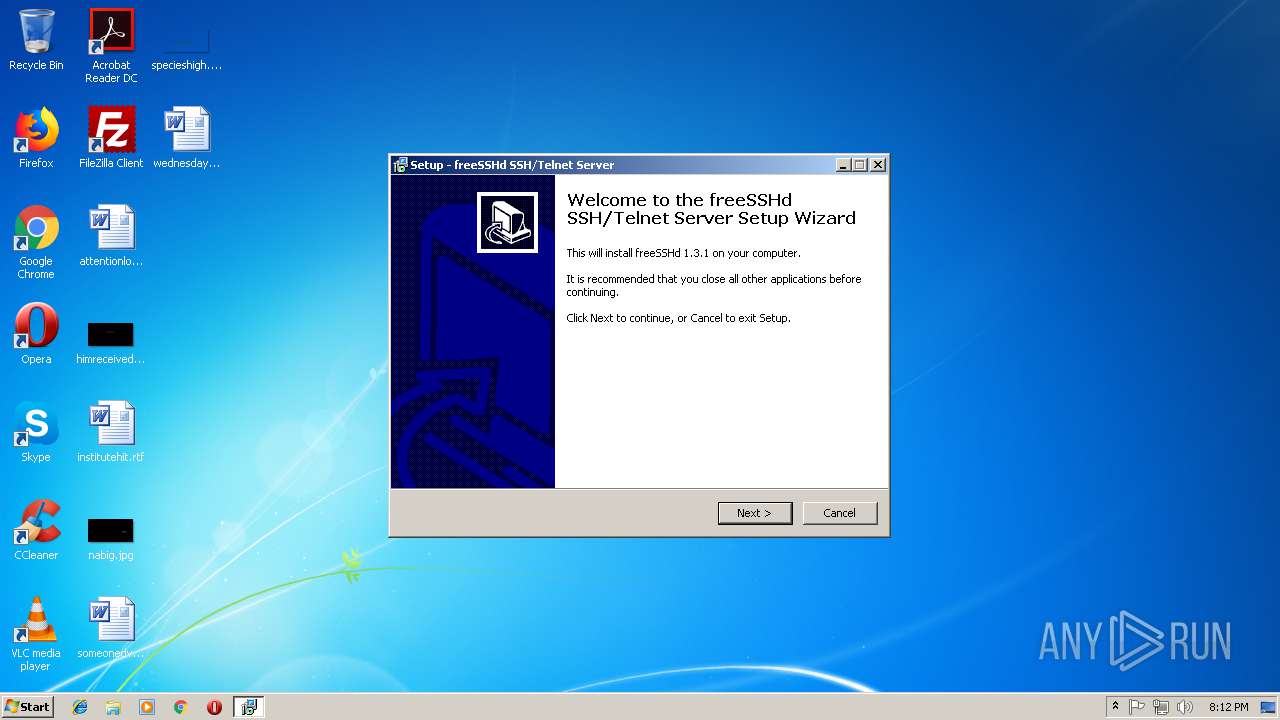
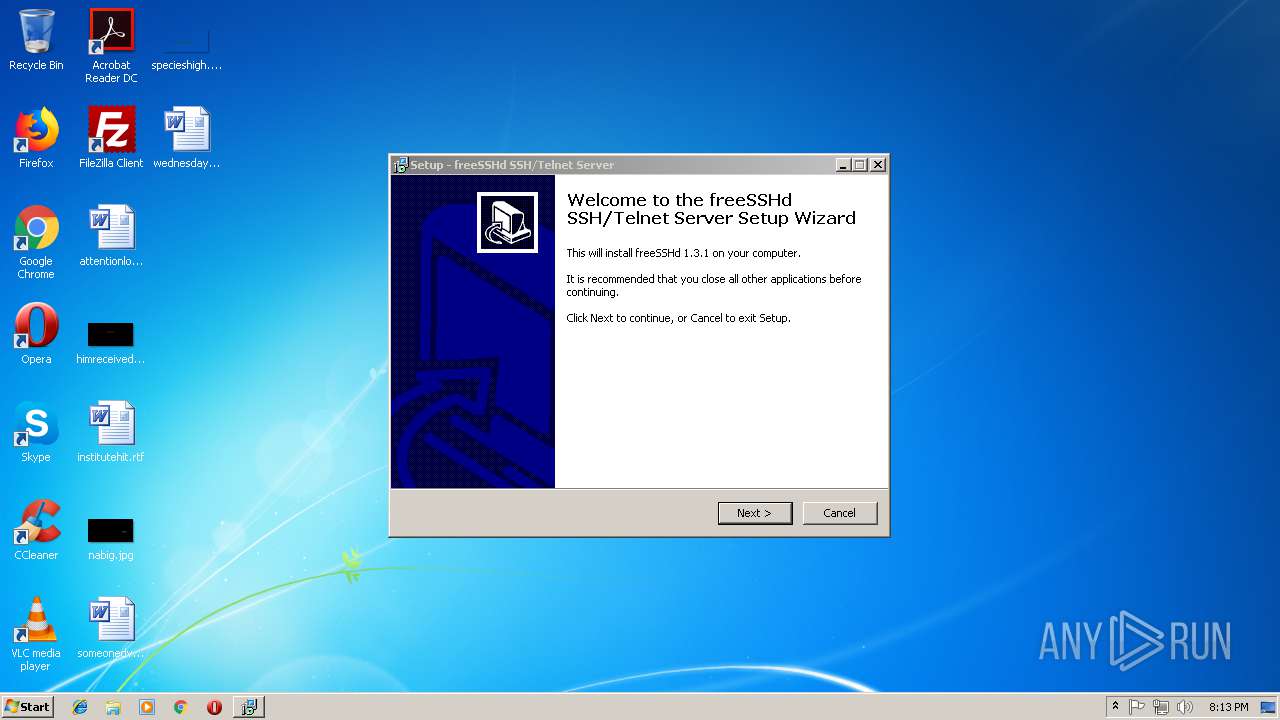
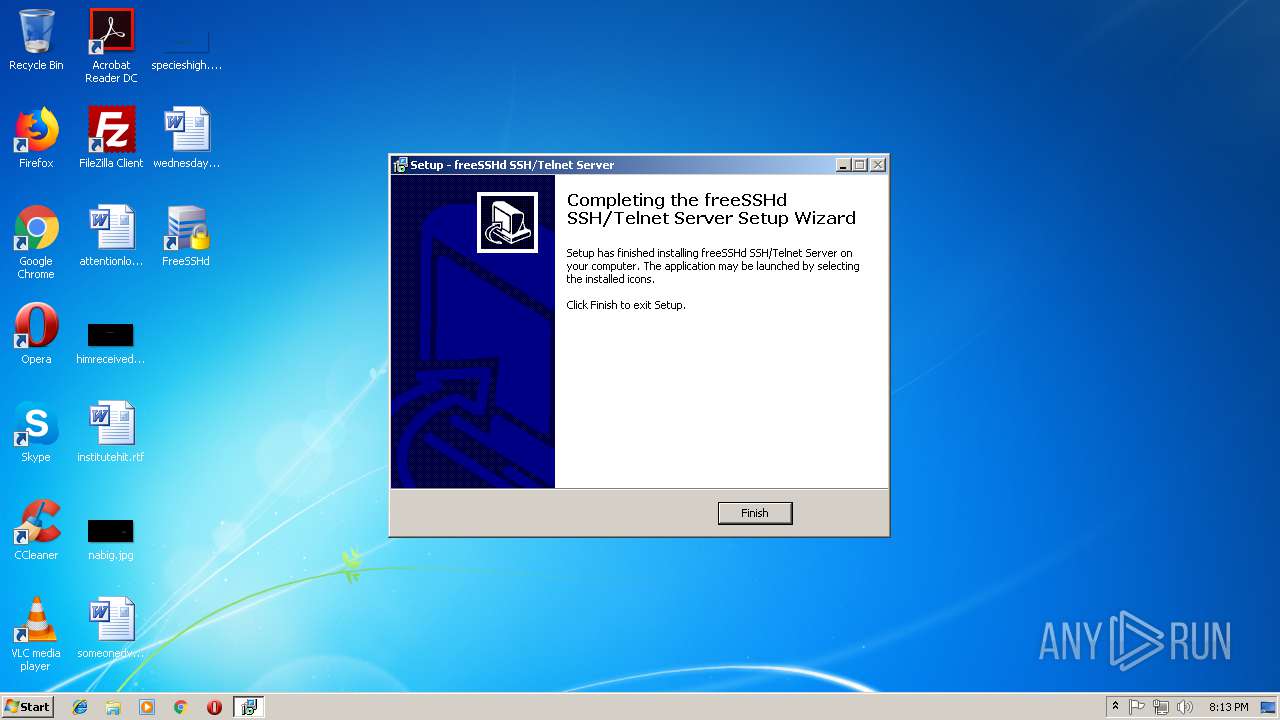
| File name: | freeSSHd.exe |
| Full analysis: | https://app.any.run/tasks/ae58e47a-bea9-4637-8bde-ceae84be4f9a |
| Verdict: | Suspicious activity |
| Analysis date: | October 10, 2018, 19:12:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B68996385F10DB76CFDD37A5E8C96424 |
| SHA1: | 6345B241B4C284916C3993F2C291B367CDABD0A9 |
| SHA256: | 7135B6F6C58E6A3FA6E3FD25322E35A6904EAC59C3E0A7E5E510EA12D23D37CA |
| SSDEEP: | 24576:j20y+3P5EPpRAB+9h910VmkfCkMpLoPG+l3tZGAj2wT:j2GBwAQ9v10UlBpLo3l3Pz1T |
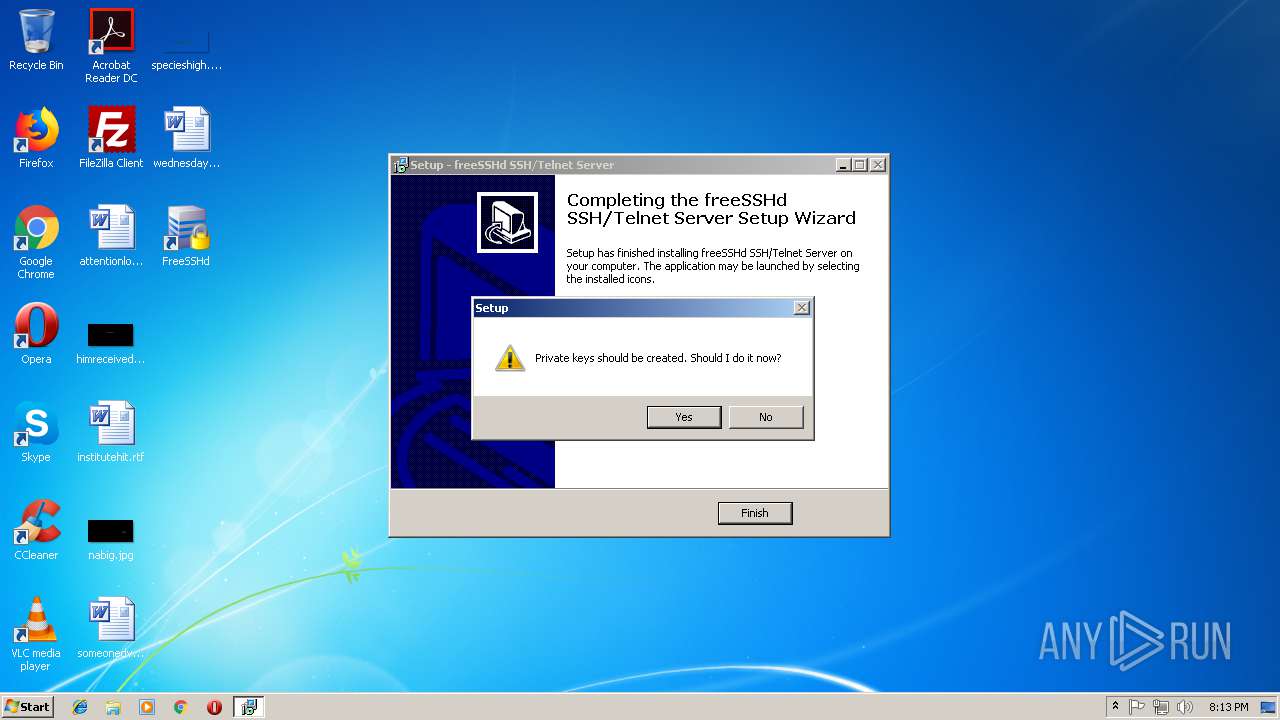
MALICIOUS
Application was dropped or rewritten from another process
- FreeSSHDService.exe (PID: 3208)
- FreeSSHDService.exe (PID: 940)
- FreeSSHDService.exe (PID: 1708)
- FreeSSHDService.exe (PID: 3788)
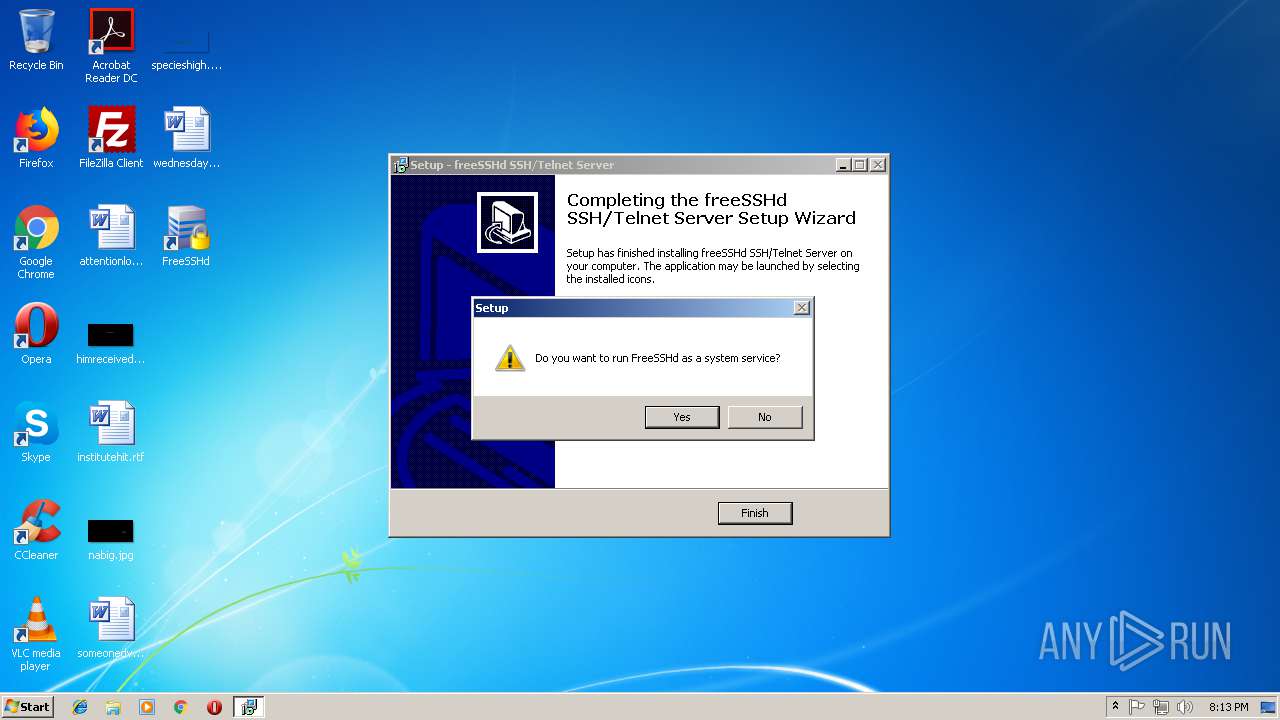
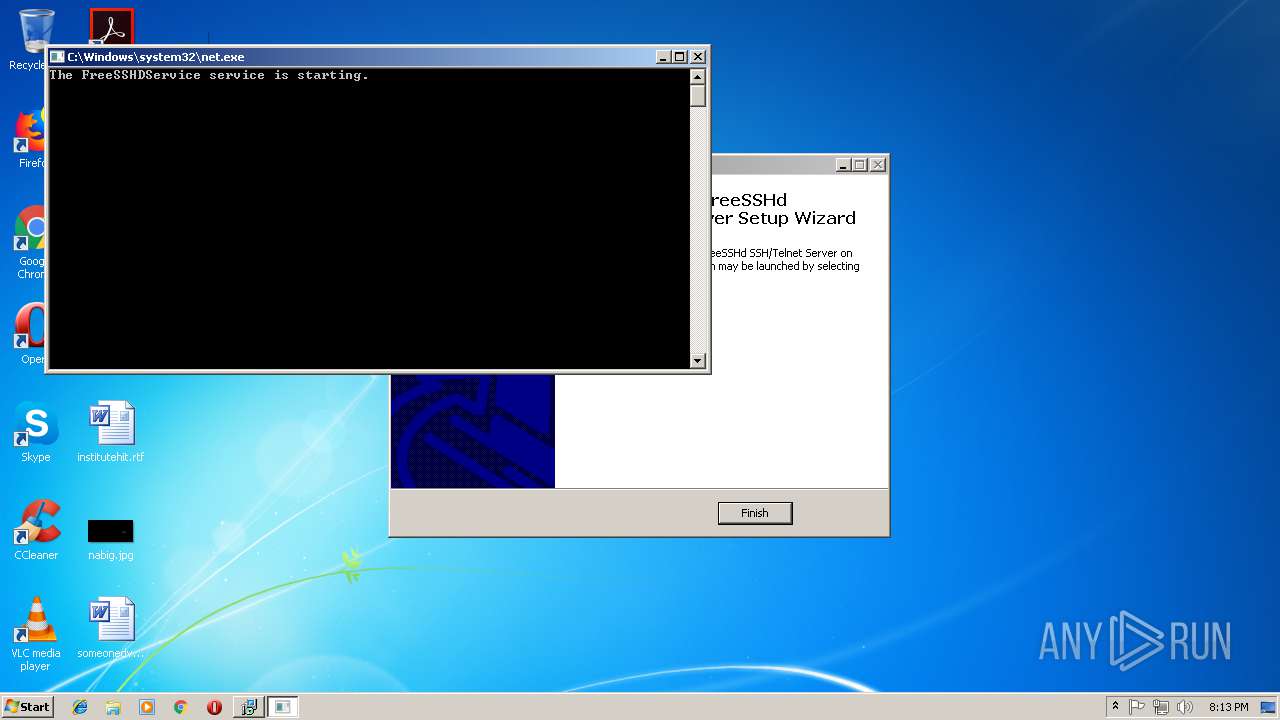
Starts NET.EXE for service management
- freeSSHd.tmp (PID: 3976)
SUSPICIOUS
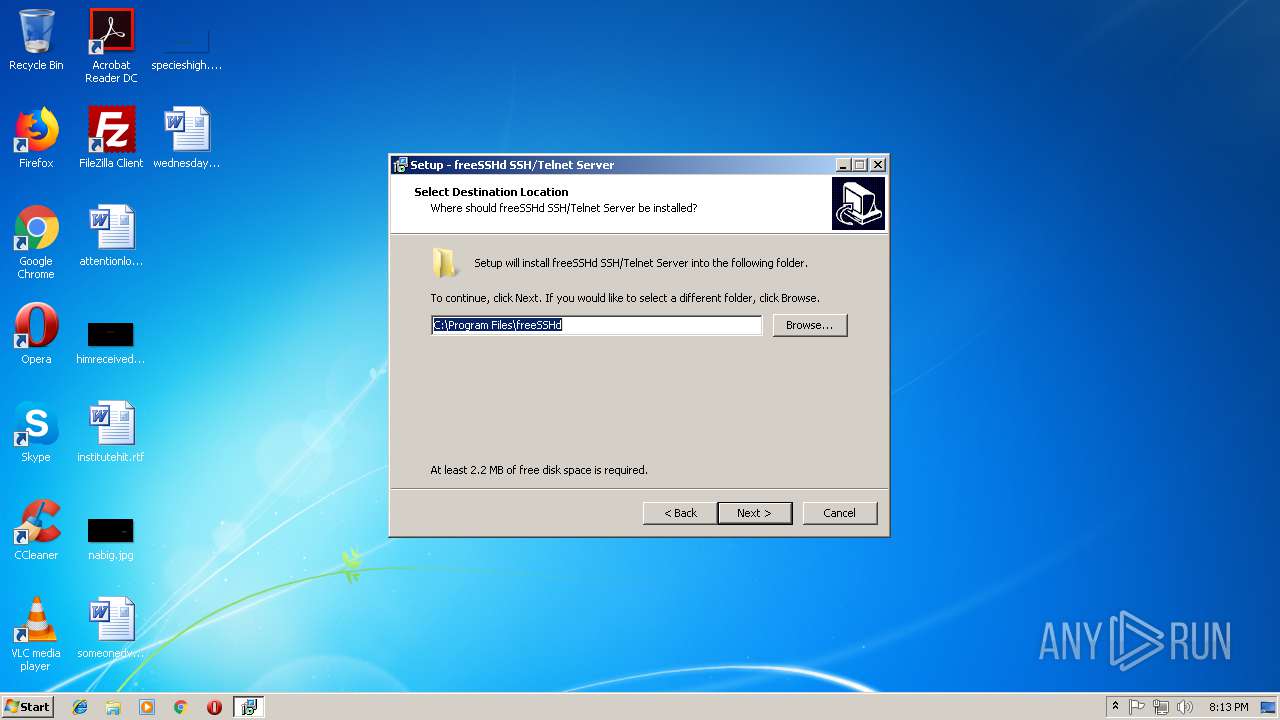
Creates or modifies windows services
- freeSSHd.tmp (PID: 3976)
Creates files in the program directory
- FreeSSHDService.exe (PID: 3208)
Creates files in the Windows directory
- FreeSSHDService.exe (PID: 3788)
Executable content was dropped or overwritten
- FreeSSHDService.exe (PID: 3788)
- freeSSHd.exe (PID: 3552)
- freeSSHd.exe (PID: 3232)
- freeSSHd.tmp (PID: 3976)
INFO
Application was dropped or rewritten from another process
- freeSSHd.tmp (PID: 584)
- wodOther.exe (PID: 2364)
- freeSSHd.tmp (PID: 3976)
Creates files in the program directory
- freeSSHd.tmp (PID: 3976)
Creates files in the user directory
- opera.exe (PID: 3868)
Application launched itself
- chrome.exe (PID: 1996)
Creates a software uninstall entry
- freeSSHd.tmp (PID: 3976)
Loads dropped or rewritten executable
- freeSSHd.tmp (PID: 3976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9b60 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Kresimir Petric |
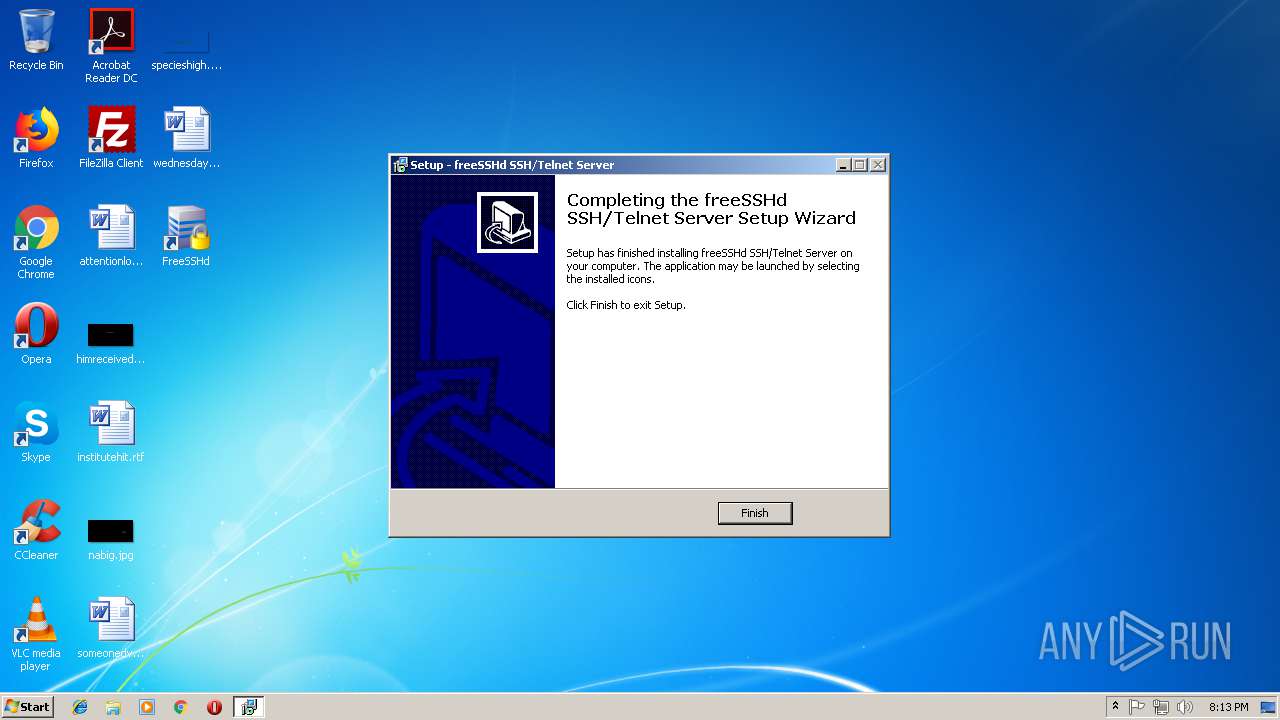
| FileDescription: | freeSSHd SSH/Telnet Server Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | freeSSHd SSH/Telnet Server |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Kresimir Petric |
| FileDescription: | freeSSHd SSH/Telnet Server Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | freeSSHd SSH/Telnet Server |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009280 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53783 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.73544 |
BSS | 0x0000C000 | 0x00000E54 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B0 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00002C00 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.47076 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05007 | 1376 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
56
Monitored processes
20
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Users\admin\AppData\Local\Temp\is-CCE77.tmp\freeSSHd.tmp" /SL5="$C05C2,624808,54272,C:\Users\admin\AppData\Local\Temp\freeSSHd.exe" | C:\Users\admin\AppData\Local\Temp\is-CCE77.tmp\freeSSHd.tmp | — | freeSSHd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,14124863652119053414,5567300597640113184,131072 --enable-features=PasswordImport --service-pipe-token=C3A985CFCB82CAA3C45A073678EA14FE --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C3A985CFCB82CAA3C45A073678EA14FE --renderer-client-id=5 --mojo-platform-channel-handle=1936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 928 | C:\Windows\system32\UI0Detect.exe | C:\Windows\system32\UI0Detect.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Interactive services detection Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 940 | "C:\Program Files\freeSSHd\FreeSSHDService.exe" /RegServer | C:\Program Files\freeSSHd\FreeSSHDService.exe | — | freeSSHd.tmp | |||||||||||
User: admin Integrity Level: HIGH Description: FreeSSHDService Module Exit code: 0 Version: 1, 3, 1, 26 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\freeSSHd\FreeSSHDService.exe" /Service | C:\Program Files\freeSSHd\FreeSSHDService.exe | — | freeSSHd.tmp | |||||||||||
User: admin Integrity Level: HIGH Description: FreeSSHDService Module Exit code: 0 Version: 1, 3, 1, 26 Modules
| |||||||||||||||
| 1996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
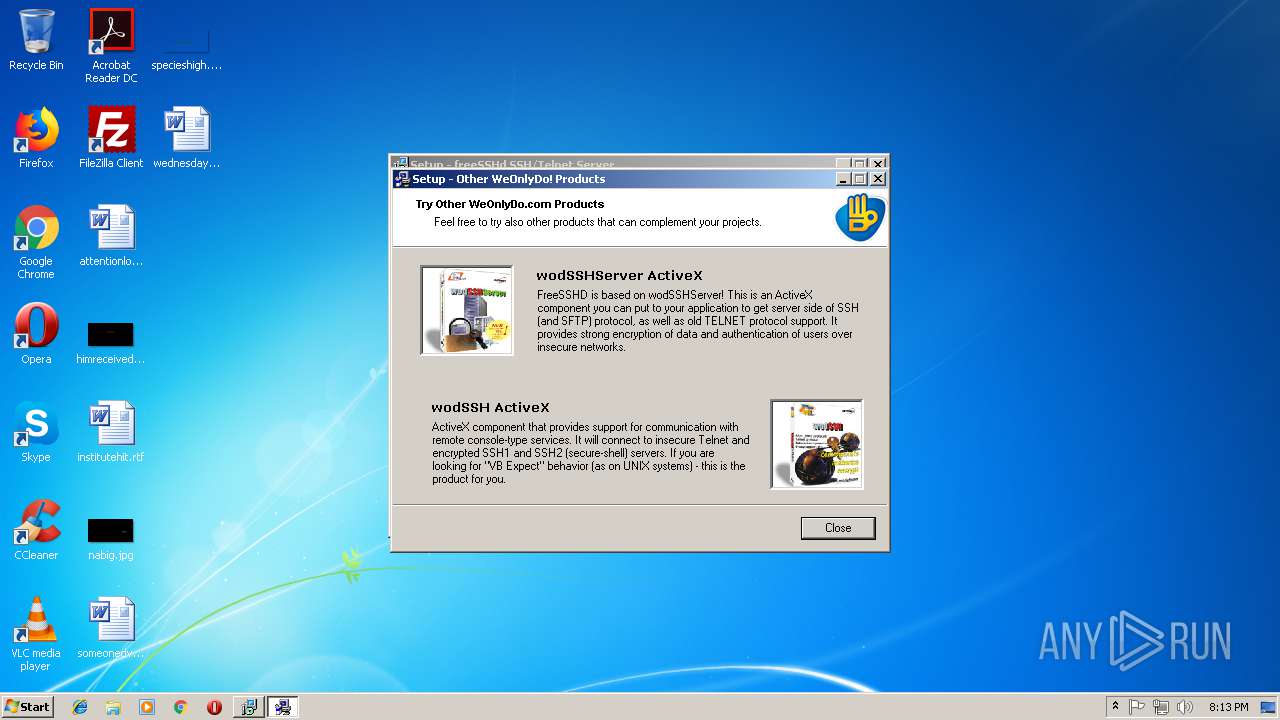
| 2364 | "C:\Users\admin\AppData\Local\Temp\is-CMFNE.tmp\wodOther.exe" | C:\Users\admin\AppData\Local\Temp\is-CMFNE.tmp\wodOther.exe | — | freeSSHd.tmp | |||||||||||
User: admin Company: WeOnlyDo! Software Integrity Level: HIGH Description: Setup addon Exit code: 0 Version: 1,0,0,1 Modules
| |||||||||||||||
| 3052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3612 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3208 | "C:\Program Files\freeSSHd\FreeSSHDService.exe" /KeyGen | C:\Program Files\freeSSHd\FreeSSHDService.exe | — | freeSSHd.tmp | |||||||||||
User: admin Integrity Level: HIGH Description: FreeSSHDService Module Exit code: 0 Version: 1, 3, 1, 26 Modules
| |||||||||||||||
| 3232 | "C:\Users\admin\AppData\Local\Temp\freeSSHd.exe" /SPAWNWND=$1C0206 /NOTIFYWND=$C05C2 | C:\Users\admin\AppData\Local\Temp\freeSSHd.exe | freeSSHd.tmp | ||||||||||||
User: admin Company: Kresimir Petric Integrity Level: HIGH Description: freeSSHd SSH/Telnet Server Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
914
Read events
711
Write events
200
Delete events
3
Modification events
| (PID) Process: | (3868) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (3868) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3052) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1996-13183672379880281 |
Value: 259 | |||
| (PID) Process: | (1996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (1996) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
8
Suspicious files
49
Text files
137
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3868 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr3C5D.tmp | — | |
MD5:— | SHA256:— | |||
| 3868 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr3C7D.tmp | — | |
MD5:— | SHA256:— | |||
| 1996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c0e0d6fe-8204-40f9-9ce4-e3613a1174b8.tmp | — | |
MD5:— | SHA256:— | |||
| 1996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 1996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF5c4258.TMP | text | |
MD5:— | SHA256:— | |||
| 3868 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 1996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b4f6ec81-220e-4e0a-a9f7-e156bb31122a.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
12
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3788 | FreeSSHDService.exe | GET | 200 | 91.134.235.212:80 | http://www.freesshd.com/update.php | FR | text | 287 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3868 | opera.exe | 82.145.215.40:443 | certs.opera.com | Opera Software AS | — | whitelisted |
1996 | chrome.exe | 172.217.17.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1996 | chrome.exe | 216.58.211.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1996 | chrome.exe | 216.58.211.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
1996 | chrome.exe | 172.217.20.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1996 | chrome.exe | 172.217.17.35:443 | www.google.de | Google Inc. | US | whitelisted |
1996 | chrome.exe | 216.58.212.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3788 | FreeSSHDService.exe | 91.134.235.212:80 | www.freesshd.com | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.freesshd.com |
| malicious |