| File name: | 71357f80f90af2690d2d554f2f8ae57616556de5e0df3bc3f4e63c3bf4eca237 |
| Full analysis: | https://app.any.run/tasks/e5bd9c8d-1e38-4636-b8c3-882e9e0c0113 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 09:44:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
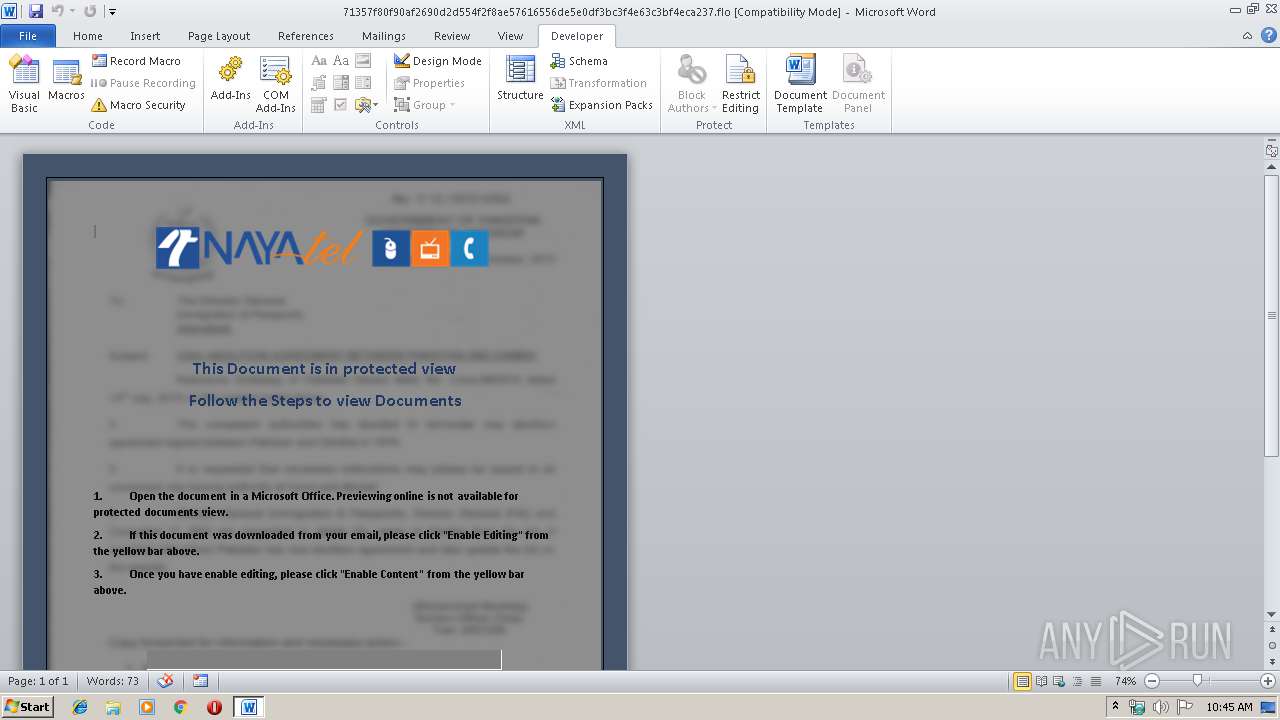
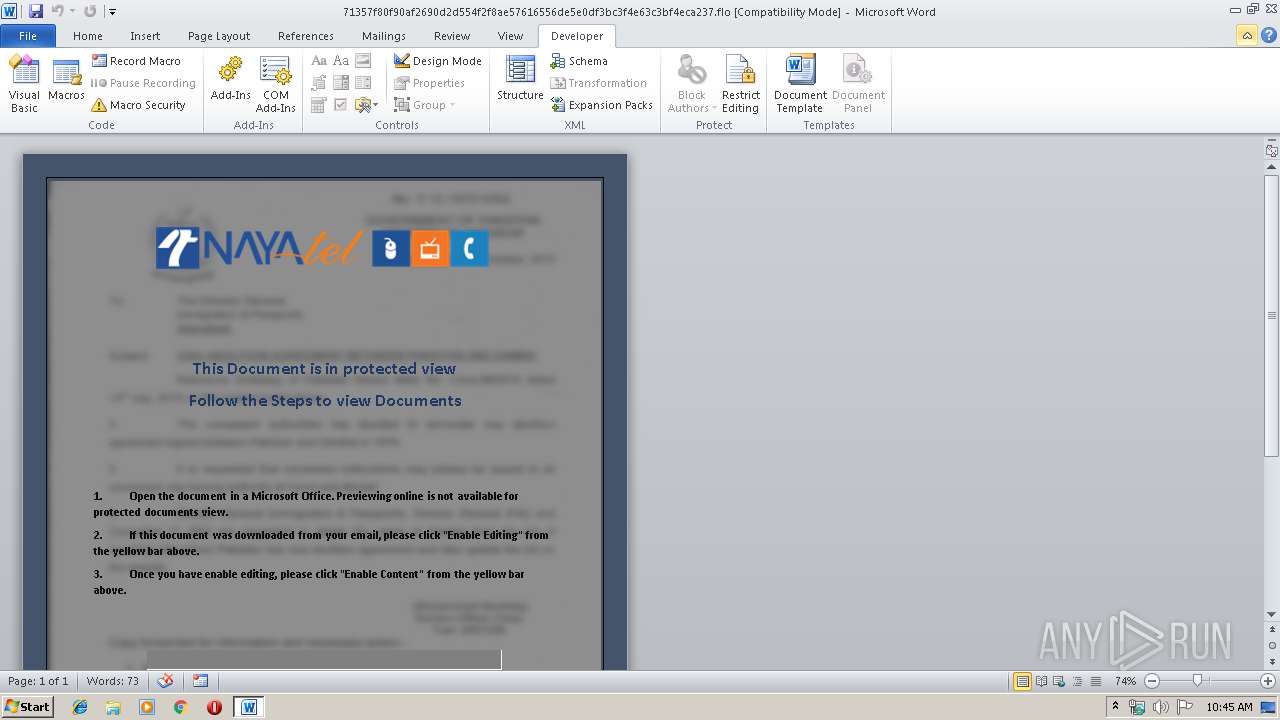
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Dec 19 07:18:00 2017, Last Saved Time/Date: Tue Dec 19 07:18:00 2017, Number of Pages: 1, Number of Words: 88, Number of Characters: 503, Security: 0 |
| MD5: | 98B3FD6949DF214BB6C4CE6B9A86D0CD |
| SHA1: | 5B308F98C9F77A7A59ADF5F050BAC5A92138637A |
| SHA256: | 71357F80F90AF2690D2D554F2F8AE57616556DE5E0DF3BC3F4E63C3BF4ECA237 |
| SSDEEP: | 24576:4COstnLozvG/vwJO2BZX6aDiRgI5eis+FpOkYRM:4CvtnLCKwJ9Bp6ye5XAw |
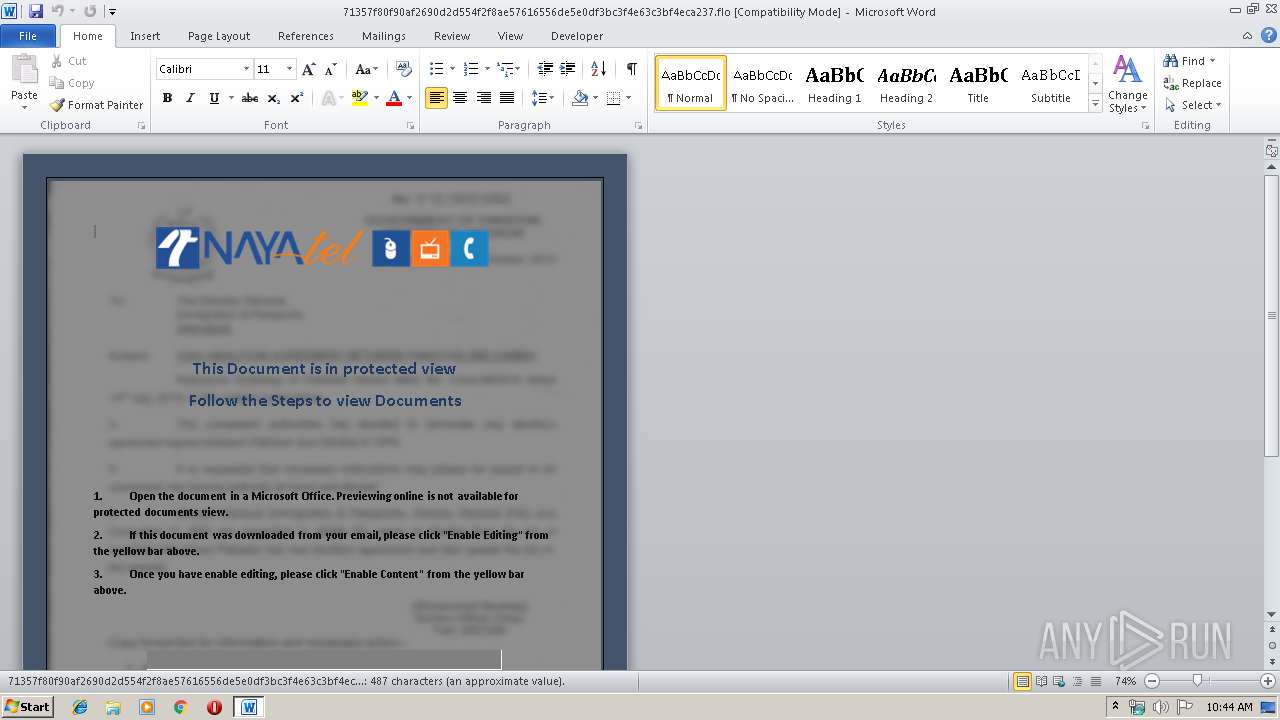
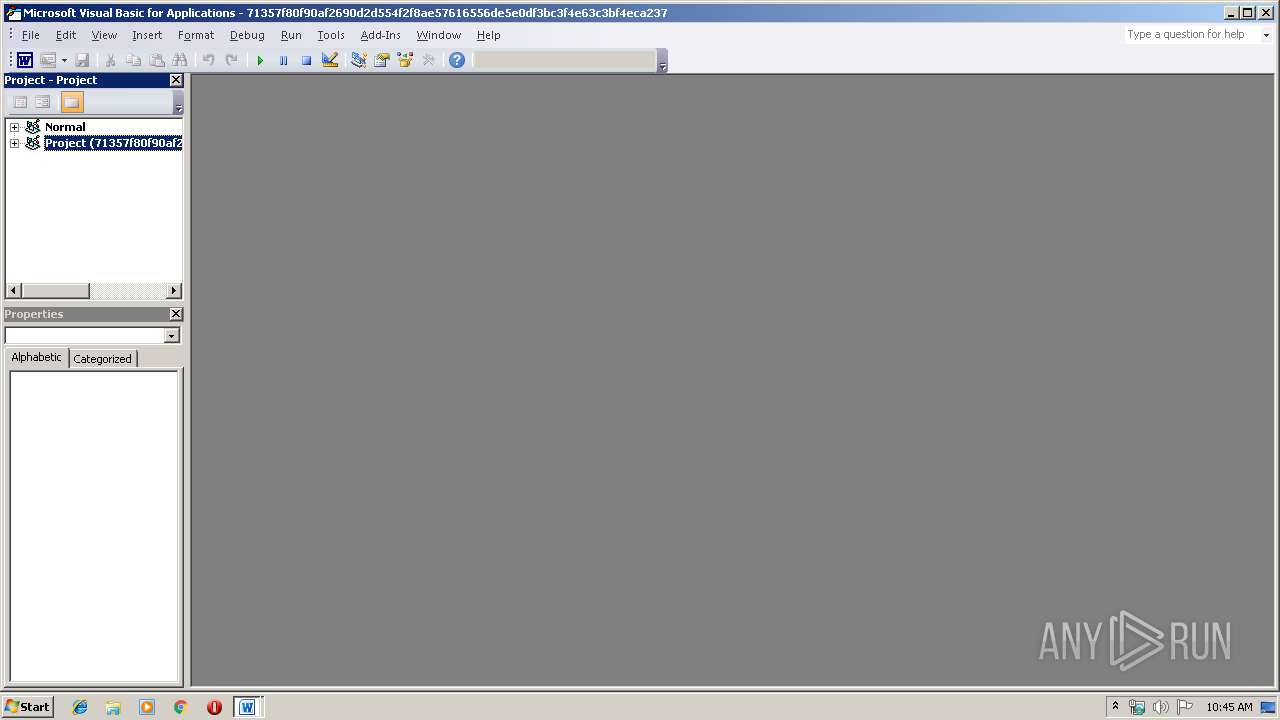
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3356)
Executes scripts
- WINWORD.EXE (PID: 3356)
Changes the autorun value in the registry
- powershell.exe (PID: 3836)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2480)
Uses Task Scheduler to run other applications
- powershell.exe (PID: 3836)
SUSPICIOUS
Starts Microsoft Office Application
- rundll32.exe (PID: 3016)
Executes PowerShell scripts
- WScript.exe (PID: 4004)
Creates files in the user directory
- powershell.exe (PID: 3836)
Uses ATTRIB.EXE to modify file attributes
- powershell.exe (PID: 3836)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3356)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .flo | | | iGrafx FlowCharter document (36.2) |
|---|---|---|
| .doc | | | Microsoft Word document (34.5) |
| .doc | | | Microsoft Word document (old ver.) (20.5) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2017:12:19 07:18:00 |
| ModifyDate: | 2017:12:19 07:18:00 |
| Pages: | 1 |
| Words: | 88 |
| Characters: | 503 |
| Security: | None |
| Company: | - |
| Lines: | 4 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 590 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Windows Latin 1 (Western European) |
| Hyperlinks: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
7
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 908 | "C:\Windows\system32\attrib.exe" +s +h C:\Users\Public\system.ps1 | C:\Windows\system32\attrib.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2480 | "C:\Windows\system32\schtasks.exe" /Create /RU system /SC ONLOGON /TN Microsoft\WindowsOptimizationsService /TR "wscript C:\Users\Public\system.vbs" /F | C:\Windows\system32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
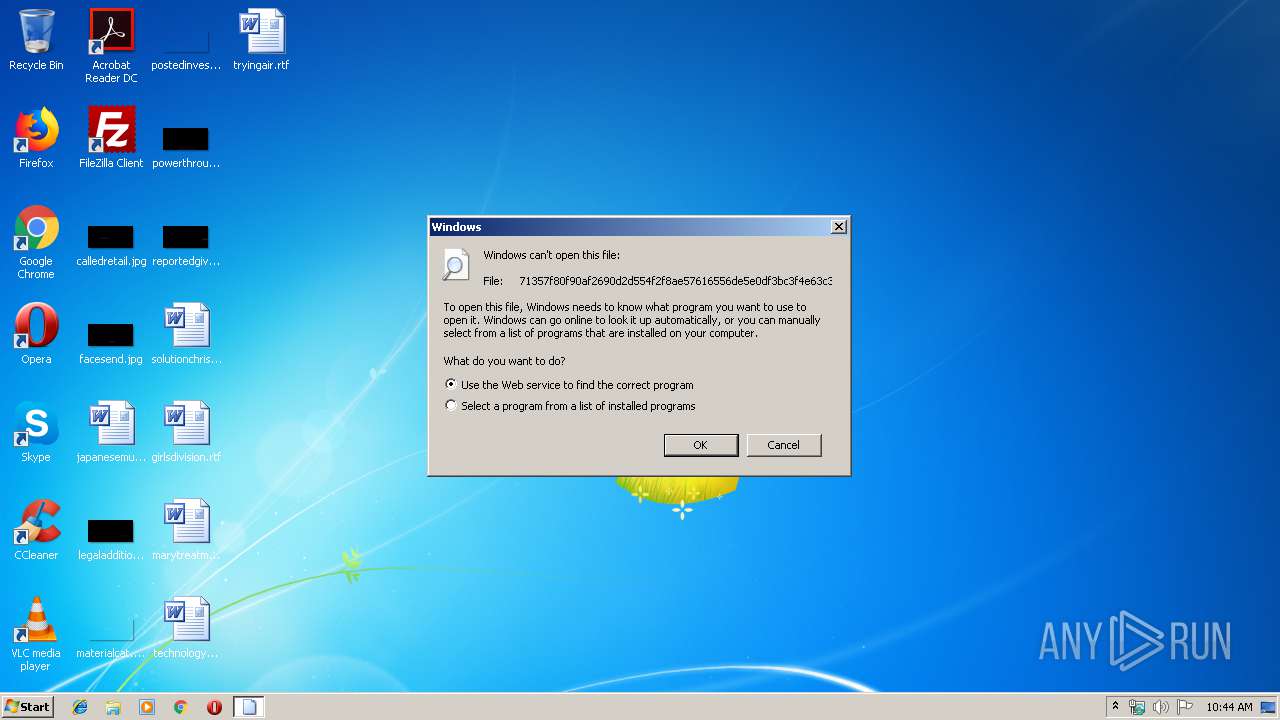
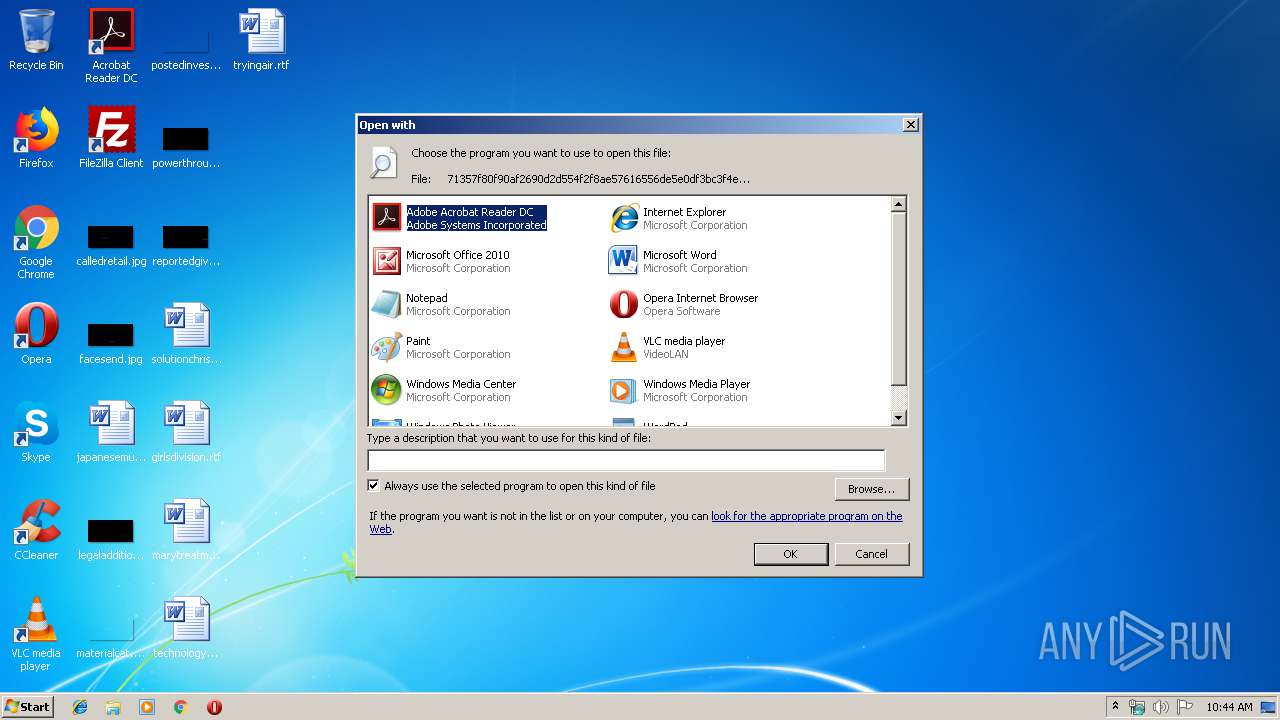
| 3016 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\71357f80f90af2690d2d554f2f8ae57616556de5e0df3bc3f4e63c3bf4eca237.flo | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3356 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\71357f80f90af2690d2d554f2f8ae57616556de5e0df3bc3f4e63c3bf4eca237.flo" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3780 | "C:\Windows\system32\attrib.exe" +s +h C:\Users\Public\system.vbs | C:\Windows\system32\attrib.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3836 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle hidden -ExecutionPolicy Bypass -nologo -noprofile -file C:\Users\Public\system.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4004 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\system.vbs" | C:\Windows\System32\WScript.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
2 143
Read events
1 577
Write events
556
Delete events
10
Modification events
| (PID) Process: | (3016) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (3016) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (3016) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (3016) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (3016) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (3016) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (3016) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (3016) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (3016) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (3016) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
Executable files
0
Suspicious files
2
Text files
3
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3356 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2723.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3836 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QB011BLTMZQ3OEPUCV9Y.temp | — | |
MD5:— | SHA256:— | |||
| 3356 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF69BAFF8005E4B44.TMP | — | |
MD5:— | SHA256:— | |||
| 3356 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{DE6916ED-FD3C-4526-9553-7E90C7ABA4C1}.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{D4B040A6-00C3-434C-8966-3465AB869D80}.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{3DB281D6-6800-408F-BBD6-862D46D8205D}.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$357f80f90af2690d2d554f2f8ae57616556de5e0df3bc3f4e63c3bf4eca237.flo | pgc | |
MD5:— | SHA256:— | |||
| 3356 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3356 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\16AC97B4.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3356 | WINWORD.EXE | C:\users\public\system.ps1 | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report