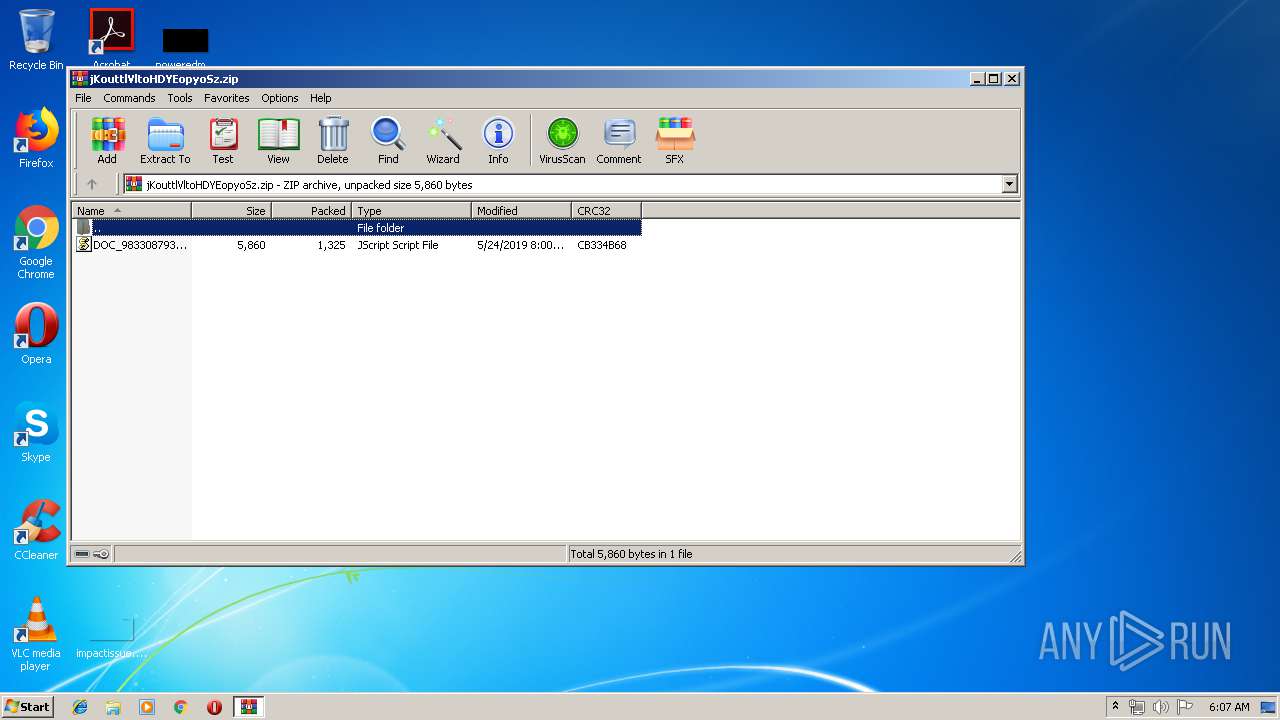
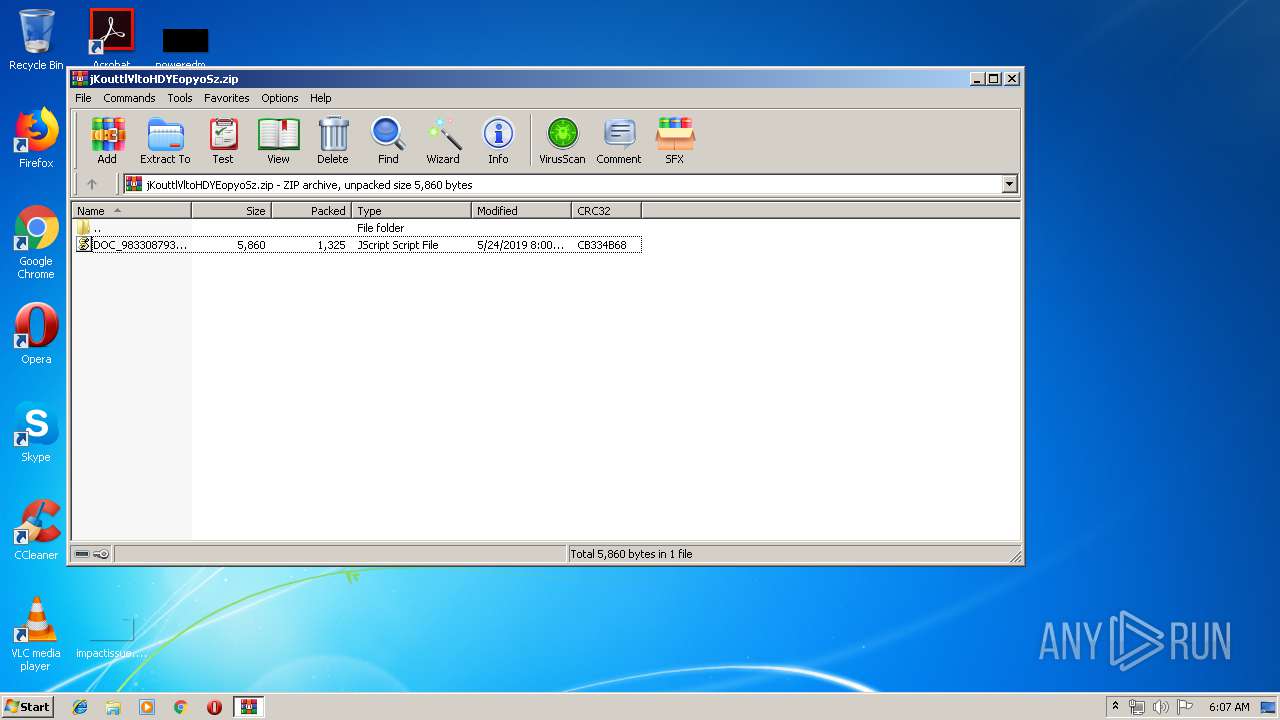
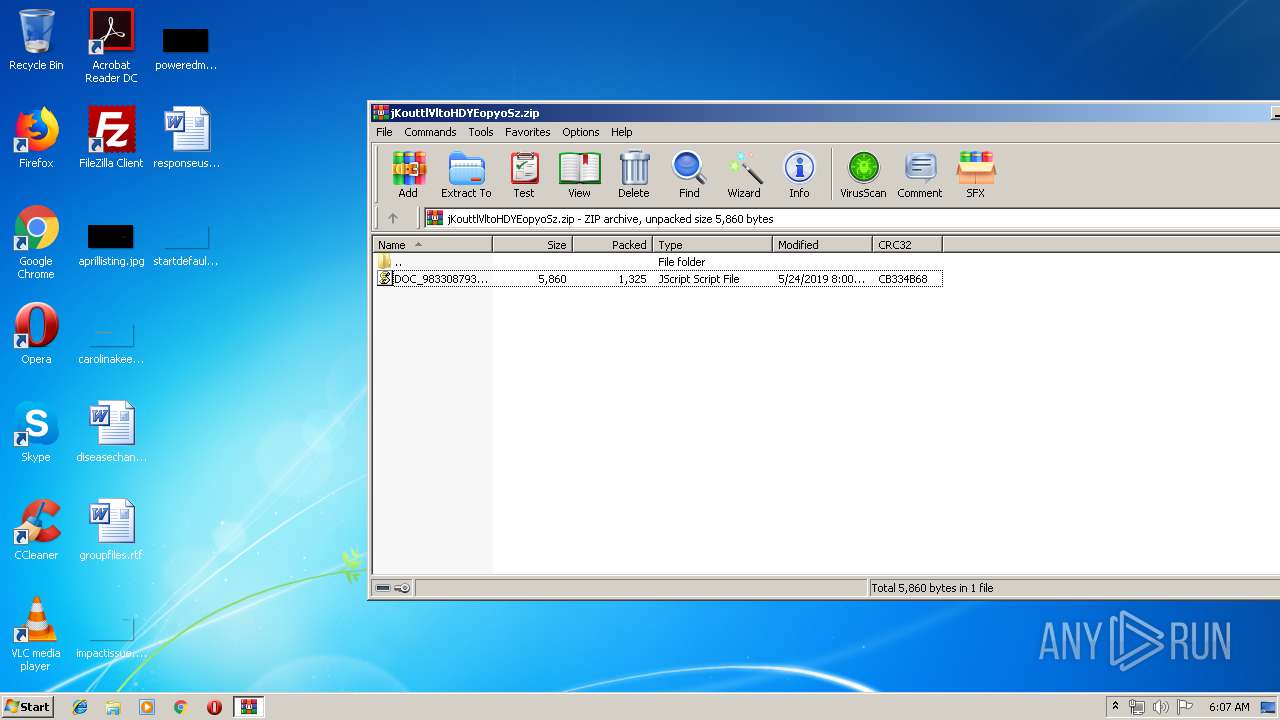
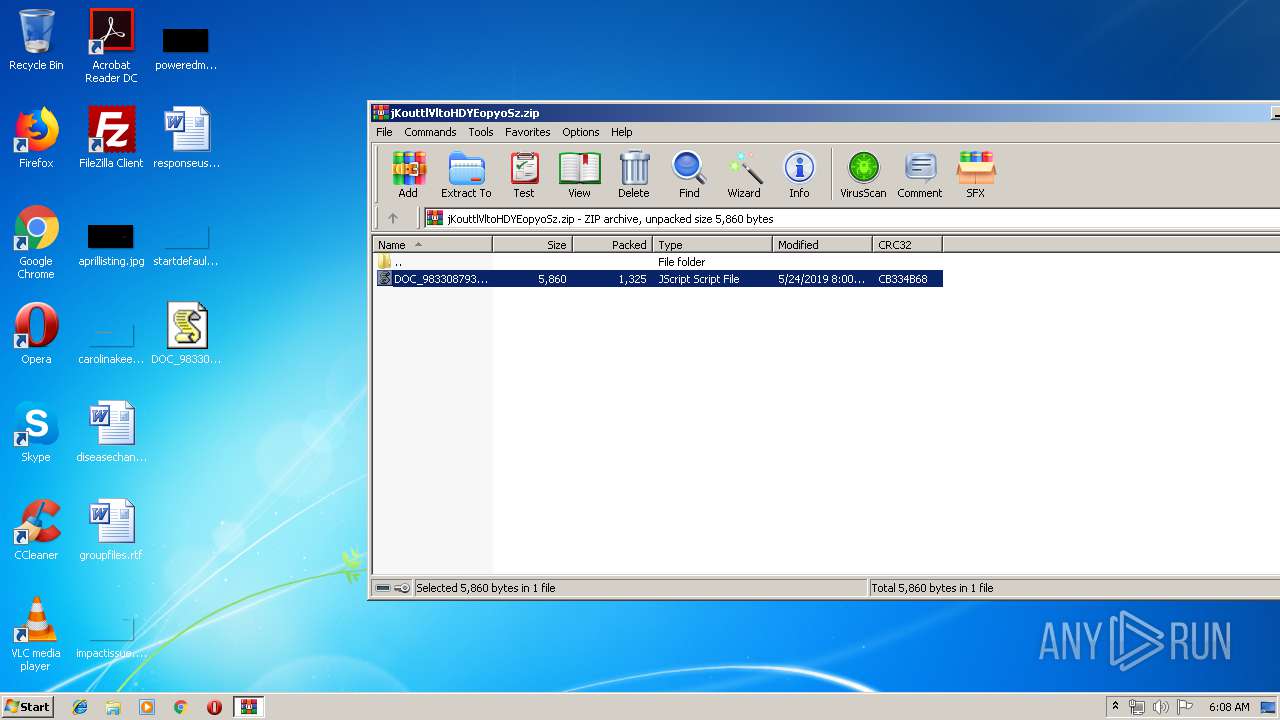
| download: | jKouttlVltoHDYEopyoSz |
| Full analysis: | https://app.any.run/tasks/068c0201-324e-43a5-b387-e42cdd2ba7cc |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 24, 2019, 05:07:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | AA1F1E0563281F5B8BECF2D200B8FCD7 |
| SHA1: | 4ABA46BBEAB1288C937D924D2A0610116CFDAACE |
| SHA256: | 7130568ED0C32B4A08429E9B83E6CC83A4EDE4B16038AC0C68C5EB4388F89582 |
| SSDEEP: | 24:9IUHUTFdS9P5IItOApueMqRaiA2mh8myTetjAF0Zr3ve/Cq1lc65HD:9yTFcR5/tOBeMKaiZhbOZUCp2 |
MALICIOUS
Changes settings of System certificates
- WScript.exe (PID: 3316)
Application was dropped or rewritten from another process
- 31zbg8lng.exe (PID: 1276)
- 31zbg8lng.exe (PID: 296)
- soundser.exe (PID: 1780)
- soundser.exe (PID: 2120)
Emotet process was detected
- soundser.exe (PID: 1780)
Changes the autorun value in the registry
- soundser.exe (PID: 2120)
EMOTET was detected
- soundser.exe (PID: 2120)
Connects to CnC server
- soundser.exe (PID: 2120)
SUSPICIOUS
Adds / modifies Windows certificates
- WScript.exe (PID: 3316)
Creates files in the user directory
- WScript.exe (PID: 3316)
Executable content was dropped or overwritten
- WScript.exe (PID: 3316)
- 31zbg8lng.exe (PID: 1276)
Starts itself from another location
- 31zbg8lng.exe (PID: 1276)
INFO
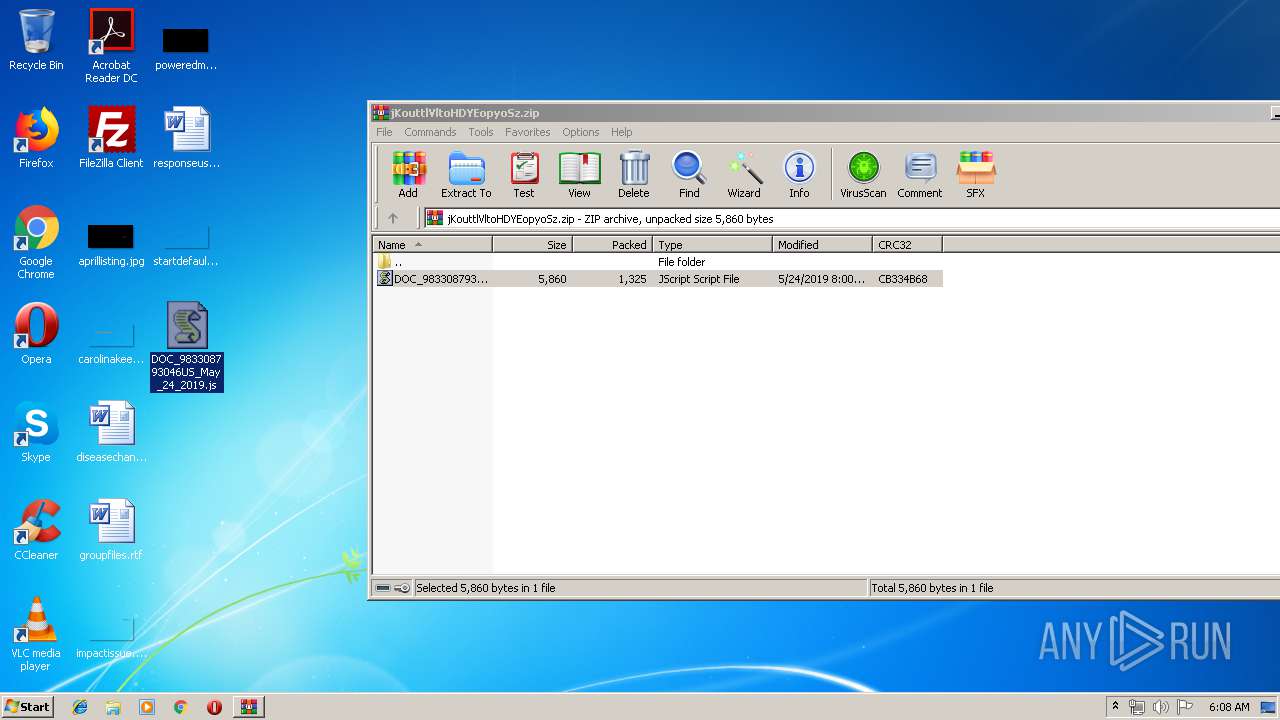
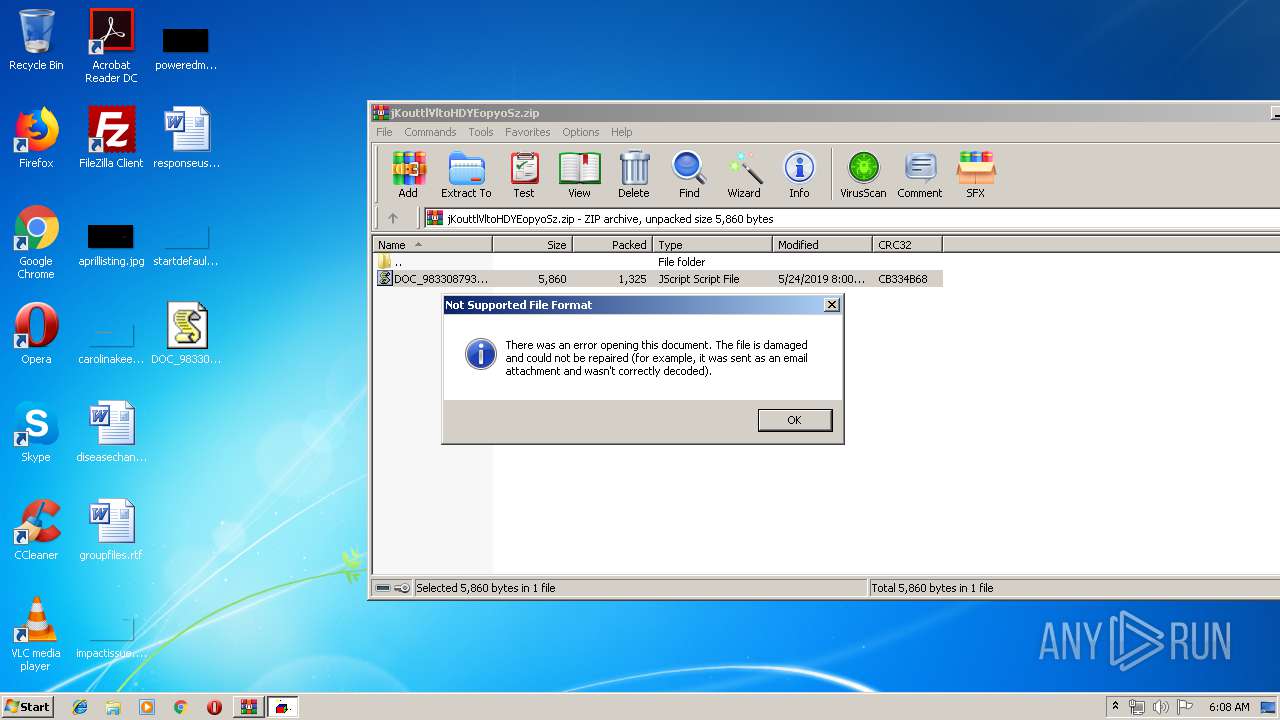
Manual execution by user
- WScript.exe (PID: 3316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:24 08:00:00 |
| ZipCRC: | 0xcb334b68 |
| ZipCompressedSize: | 1325 |
| ZipUncompressedSize: | 5860 |
| ZipFileName: | DOC_983308793046US_May_24_2019.js |
Total processes
38
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Users\admin\AppData\Local\Temp\31zbg8lng.exe" | C:\Users\admin\AppData\Local\Temp\31zbg8lng.exe | — | WScript.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1276 | --65a89952 | C:\Users\admin\AppData\Local\Temp\31zbg8lng.exe | 31zbg8lng.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1780 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 31zbg8lng.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2120 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2912 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\jKouttlVltoHDYEopyoSz.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3316 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\DOC_983308793046US_May_24_2019.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
948
Read events
886
Write events
59
Delete events
3
Modification events
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\jKouttlVltoHDYEopyoSz.zip | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2912) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4804 |
Value: JScript Script File | |||
| (PID) Process: | (3316) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2912.48501\DOC_983308793046US_May_24_2019.js | — | |
MD5:— | SHA256:— | |||
| 3316 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@dnmartin[1].txt | text | |
MD5:— | SHA256:— | |||
| 1276 | 31zbg8lng.exe | C:\Users\admin\AppData\Local\soundser\soundser.exe | executable | |
MD5:— | SHA256:— | |||
| 3316 | WScript.exe | C:\Users\admin\AppData\Local\Temp\31zbg8lng.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | soundser.exe | POST | 200 | 104.131.11.150:8080 | http://104.131.11.150:8080/img/badge/ | US | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3316 | WScript.exe | 51.38.185.91:443 | dnmartin.net | — | GB | unknown |
2120 | soundser.exe | 104.131.11.150:8080 | — | Digital Ocean, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dnmartin.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2120 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2 ETPRO signatures available at the full report