| File name: | 70e3c496dae019ed1e35ea35789bdf416c9038472055f41db7d21dabea47870f.exe |
| Full analysis: | https://app.any.run/tasks/958069fb-ec46-4d46-87d8-ce10c5c0c898 |
| Verdict: | Malicious activity |
| Analysis date: | February 14, 2026, 08:03:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | 9120734E78C21CEB52520C17F0EA01D0 |
| SHA1: | 04C93309521BD7ED3DC460BABFEF96FCECA168C3 |
| SHA256: | 70E3C496DAE019ED1E35EA35789BDF416C9038472055F41DB7D21DABEA47870F |
| SSDEEP: | 98304:5B465c9t84spPMWbuhxokY+M132uqEMC7Y5Mij08GqWz3SQTazvqoZrX99urC+H1:J4aTzb3alGwRkVkz4y7M |
MALICIOUS
Executing a file with an untrusted certificate
- 70e3c496dae019ed1e35ea35789bdf416c9038472055f41db7d21dabea47870f.exe (PID: 2572)
SUSPICIOUS
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2292)
INFO
Reads the computer name
- 70e3c496dae019ed1e35ea35789bdf416c9038472055f41db7d21dabea47870f.exe (PID: 2572)
Checks proxy server information
- slui.exe (PID: 5468)
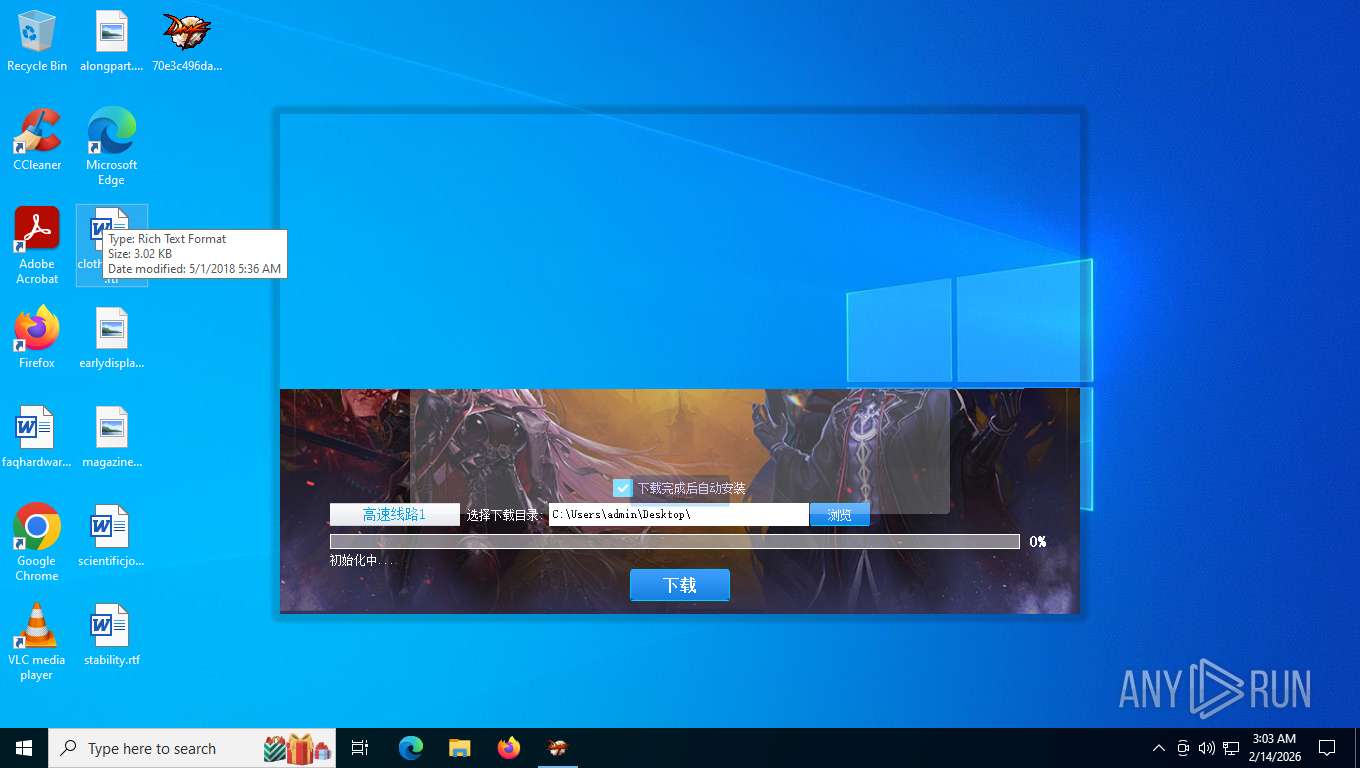
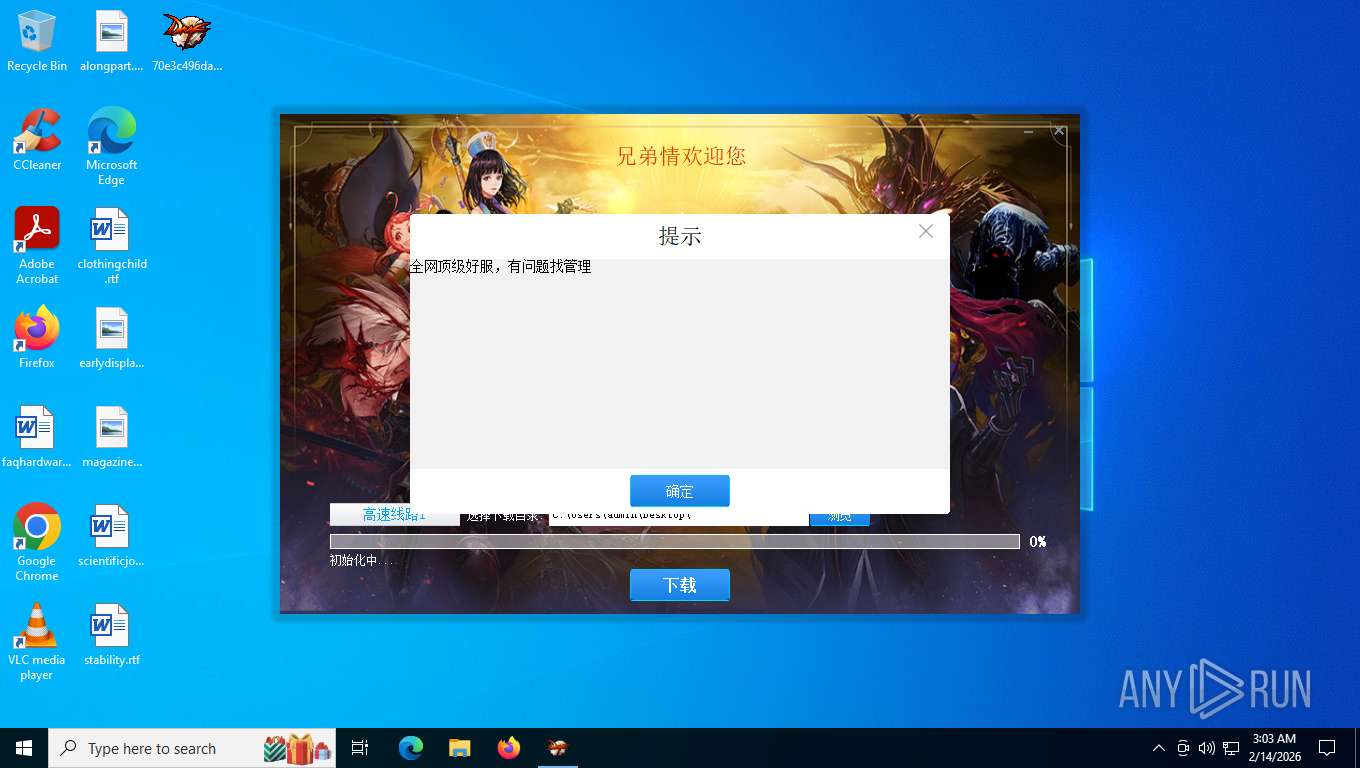
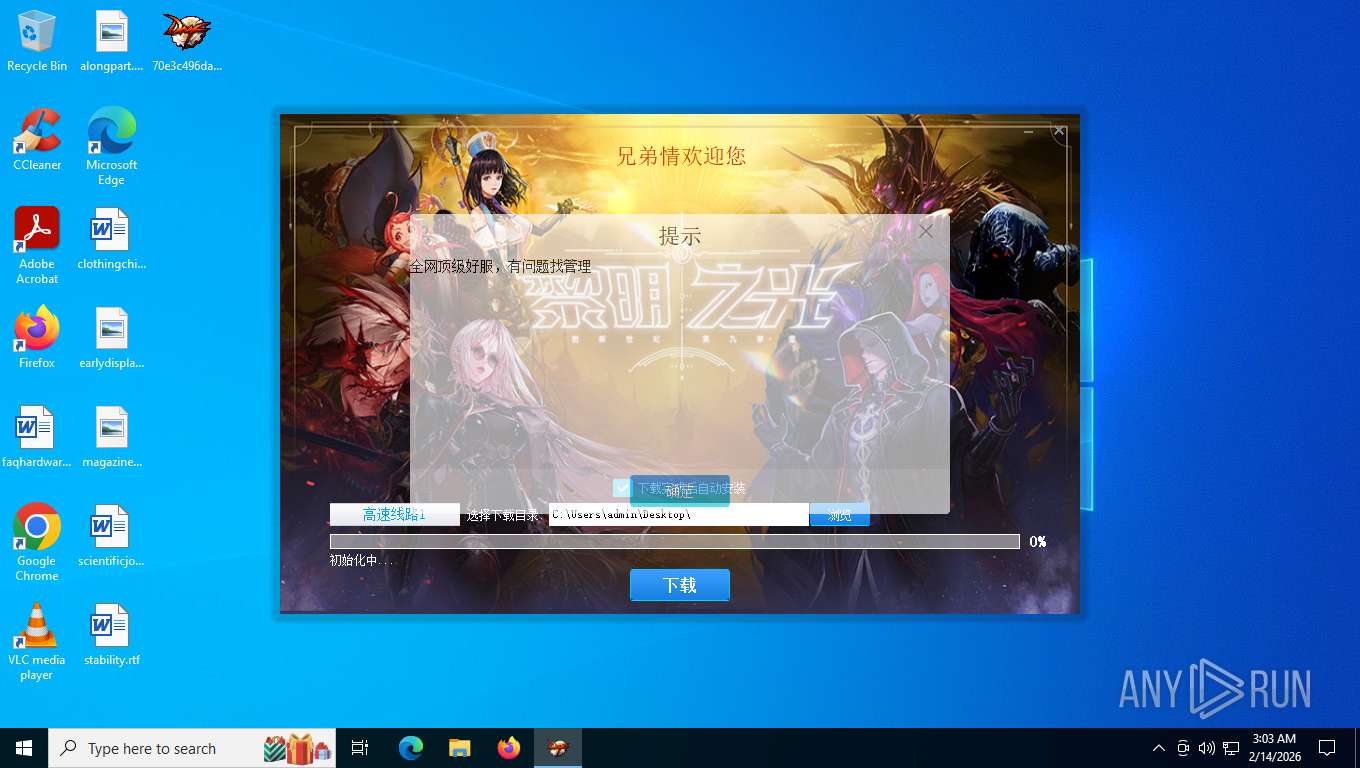
The sample compiled with chinese language support
- 70e3c496dae019ed1e35ea35789bdf416c9038472055f41db7d21dabea47870f.exe (PID: 2572)
Checks supported languages
- 70e3c496dae019ed1e35ea35789bdf416c9038472055f41db7d21dabea47870f.exe (PID: 2572)
UPX packer has been detected
- 70e3c496dae019ed1e35ea35789bdf416c9038472055f41db7d21dabea47870f.exe (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:10:17 13:54:38+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 9093120 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | 1794048 |
| EntryPoint: | 0xa61f60 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| CompanyName: | ToDayPor |
| FileDescription: | 专业版Ver0.1.9 (699416) |
| FileVersion: | 1.0.0.1 |
| InternalName: | C_ToDown.exe |
| LegalCopyright: | Copyright (C) 2025 |
| OriginalFileName: | C_ToDown.exe |
| ProductName: | ToDayPor |
| ProductVersion: | 1.0.0.1 |
Total processes
148
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1188 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 1948 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=134.0.6985.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x2a0,0x2a4,0x2a8,0x27c,0x2ac,0x139c460,0x139c46c,0x139c478 | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2572 | "C:\Users\admin\Desktop\70e3c496dae019ed1e35ea35789bdf416c9038472055f41db7d21dabea47870f.exe" | C:\Users\admin\Desktop\70e3c496dae019ed1e35ea35789bdf416c9038472055f41db7d21dabea47870f.exe | explorer.exe | ||||||||||||
User: admin Company: ToDayPor Integrity Level: MEDIUM Description: 专业版Ver0.1.9 (699416) Version: 1.0.0.1 Modules
| |||||||||||||||
| 5468 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 432
Read events
4 432
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1948 | updater.exe | C:\Program Files (x86)\Google\GoogleUpdater\updater.log | text | |
MD5:364FED3981C72595D7A45E11547D7249 | SHA256:E9BC4F2933F07DC9F9DC21A6F377AE001D4D70A80A0BC84D1938DA0249373B9D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
49
DNS requests
21
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8124 | RUXIMICS.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
8756 | svchost.exe | GET | 200 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaasMedic?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&appVer=10.0.19041.3758&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4 | US | — | 3.41 Kb | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6432 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
— | — | POST | 200 | 40.126.32.133:443 | https://login.live.com/RST2.srf | US | binary | 11.1 Kb | unknown |
8756 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
2572 | 70e3c496dae019ed1e35ea35789bdf416c9038472055f41db7d21dabea47870f.exe | POST | 200 | 211.93.211.158:80 | http://aria2c.vip/vc/SelectListOne.php | CN | text | 3.39 Kb | malicious |
356 | svchost.exe | POST | 200 | 40.126.32.133:443 | https://login.live.com/RST2.srf | US | — | 11.1 Kb | whitelisted |
— | — | POST | 200 | 20.190.160.131:443 | https://login.live.com/RST2.srf | US | binary | 10.3 Kb | unknown |
— | — | POST | 200 | 20.190.160.3:443 | https://login.live.com/RST2.srf | US | binary | 10.3 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
8756 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8124 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8124 | RUXIMICS.exe | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
8756 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
2572 | 70e3c496dae019ed1e35ea35789bdf416c9038472055f41db7d21dabea47870f.exe | 211.93.211.158:80 | aria2c.vip | CHINA169-BACKBONE CHINA UNICOM China169 Backbone | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
aria2c.vip |
| unknown |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | svchost.exe | Domain Observed Used for C2 Detected | MALWARE [ANY.RUN] Win32/Nymaim related domain (aria2c .vip) |
8756 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2572 | 70e3c496dae019ed1e35ea35789bdf416c9038472055f41db7d21dabea47870f.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Nymaim activity observed |