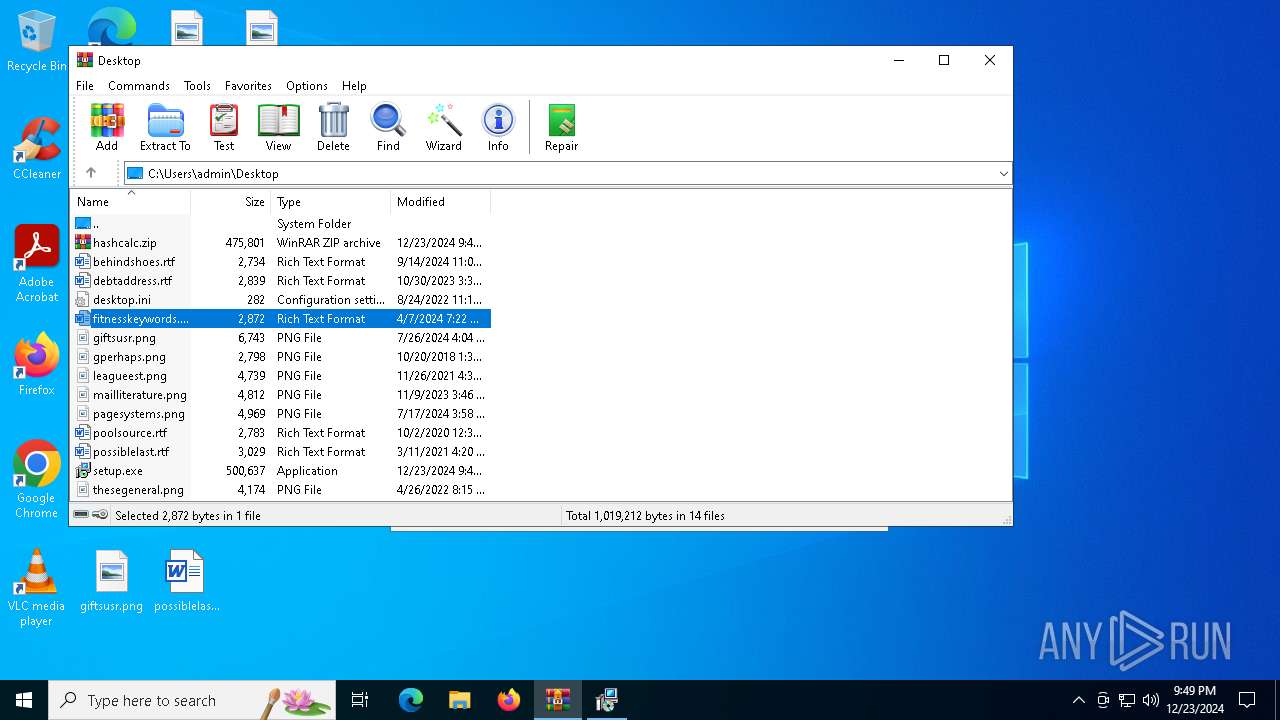
| File name: | hashcalc.zip |
| Full analysis: | https://app.any.run/tasks/7127714c-f9d1-4899-ad90-dd97ef6d9c98 |
| Verdict: | Malicious activity |
| Analysis date: | December 23, 2024, 21:46:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
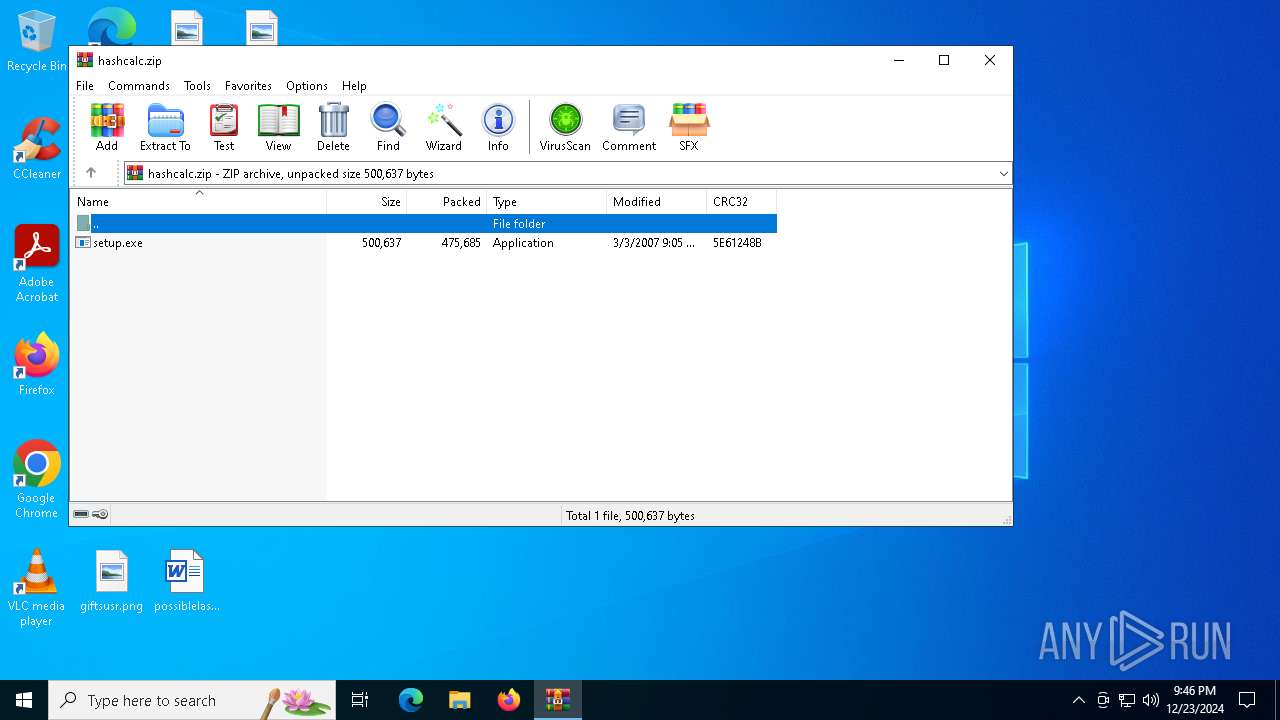
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 3763CE0490295B4BCBE4E4CDBC85BE48 |
| SHA1: | F262B8A580FE26C317105E30BC03857CDD6F7ECF |
| SHA256: | 70D2197BE429A63E737747F356D0658764B35D194CDBAD9EE1BDEB30C8641D90 |
| SSDEEP: | 12288:HSak4X99u16iaPNW6meV8lliOUHqgC6I:HSa999u16foMIXgCT |
MALICIOUS
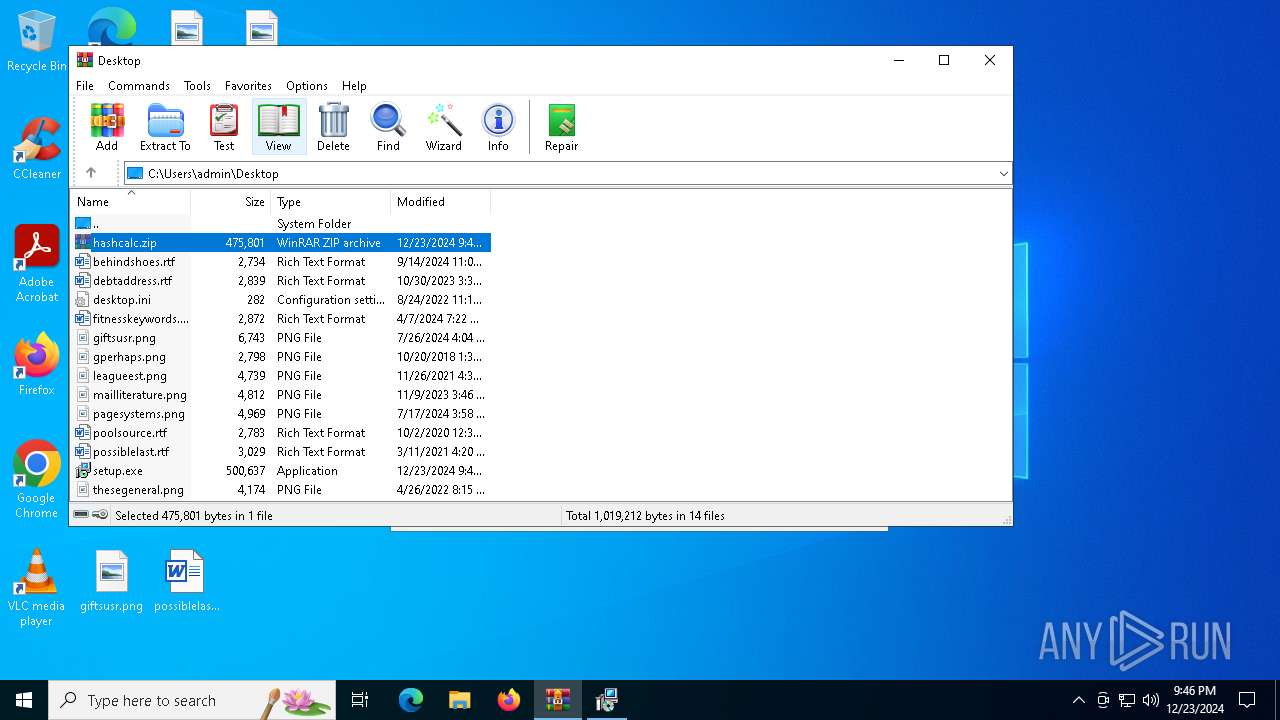
Generic archive extractor
- WinRAR.exe (PID: 5740)
SUSPICIOUS
Executable content was dropped or overwritten
- setup.exe (PID: 5548)
- is-J0JV3.tmp (PID: 5748)
Reads the Windows owner or organization settings
- is-J0JV3.tmp (PID: 5748)
Process drops legitimate windows executable
- is-J0JV3.tmp (PID: 5748)
INFO
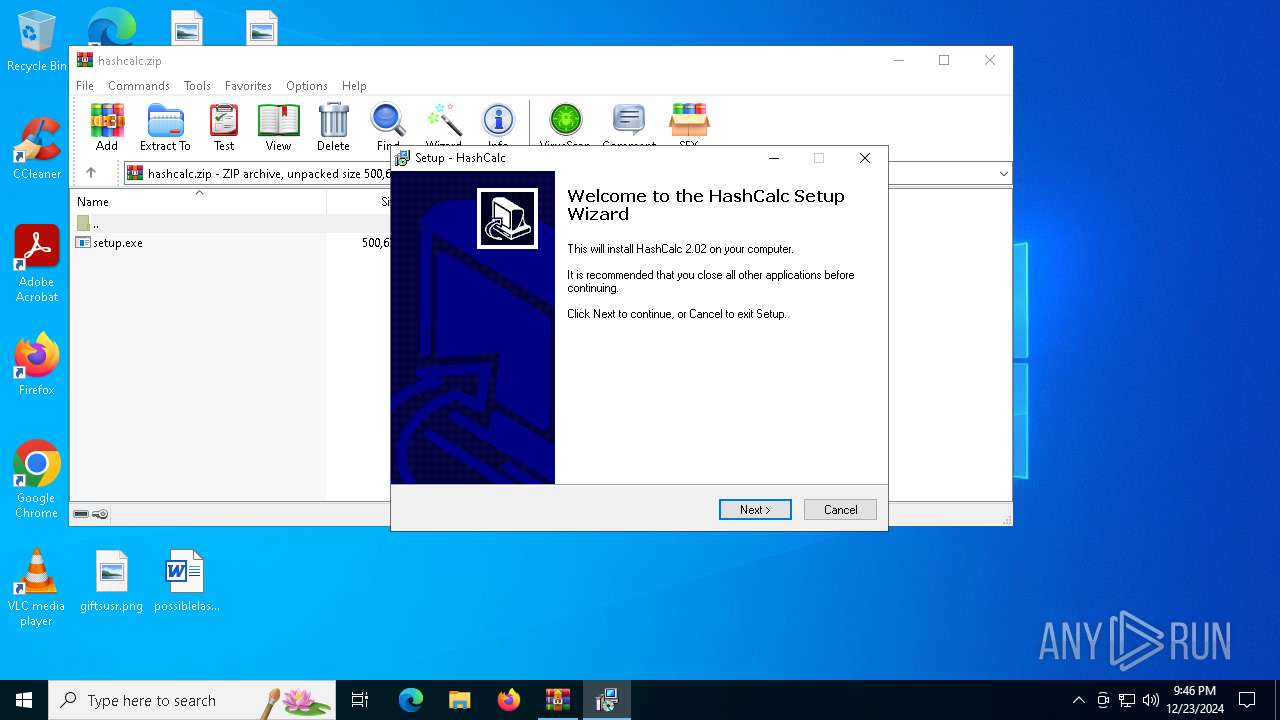
Manual execution by a user
- setup.exe (PID: 836)
- setup.exe (PID: 5548)
Create files in a temporary directory
- setup.exe (PID: 5548)
- is-J0JV3.tmp (PID: 5748)
Reads the computer name
- is-J0JV3.tmp (PID: 5748)
Checks supported languages
- setup.exe (PID: 5548)
- is-J0JV3.tmp (PID: 5748)
The sample compiled with english language support
- is-J0JV3.tmp (PID: 5748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2007:03:03 21:05:00 |
| ZipCRC: | 0x5e61248b |
| ZipCompressedSize: | 475685 |
| ZipUncompressedSize: | 500637 |
| ZipFileName: | setup.exe |
Total processes
122
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 836 | "C:\Users\admin\Desktop\setup.exe" | C:\Users\admin\Desktop\setup.exe | — | explorer.exe | |||||||||||
User: admin Company: SlavaSoft Inc. Integrity Level: MEDIUM Description: HashCalc Setup Exit code: 3221226540 Version: 2.0.2.0 Modules
| |||||||||||||||
| 5548 | "C:\Users\admin\Desktop\setup.exe" | C:\Users\admin\Desktop\setup.exe | explorer.exe | ||||||||||||
User: admin Company: SlavaSoft Inc. Integrity Level: HIGH Description: HashCalc Setup Version: 2.0.2.0 Modules
| |||||||||||||||
| 5740 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\hashcalc.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5748 | "C:\Users\admin\AppData\Local\Temp\is-LEP4J.tmp\is-J0JV3.tmp" /SL4 $80350 "C:\Users\admin\Desktop\setup.exe" 256685 52224 | C:\Users\admin\AppData\Local\Temp\is-LEP4J.tmp\is-J0JV3.tmp | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Version: 51.44.0.0 Modules
| |||||||||||||||
Total events
1 753
Read events
1 732
Write events
21
Delete events
0
Modification events
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\hashcalc.zip | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 32 | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
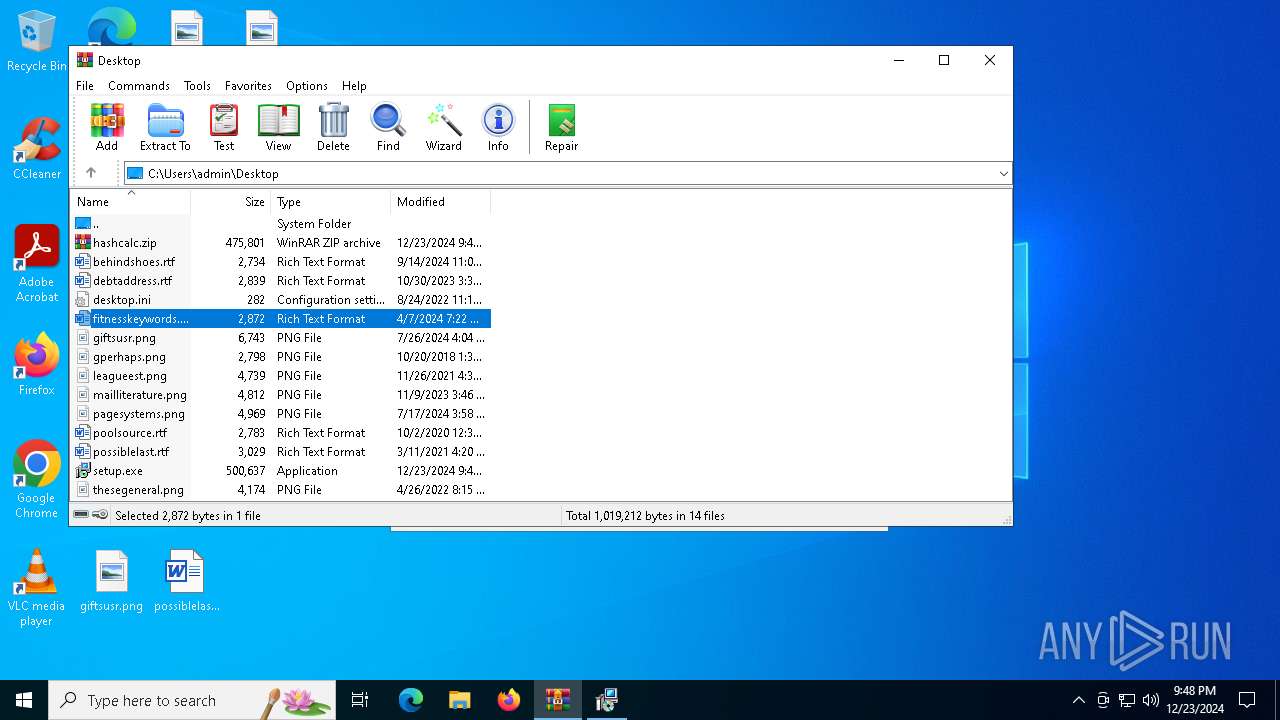
Executable files
5
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5748 | is-J0JV3.tmp | C:\Users\admin\AppData\Local\Temp\is-25LFP.tmp\_isetup\_setup64.tmp | executable | |
MD5:AA879BAA50DCCA58AD6CD14A92814695 | SHA256:7C4BCD92059137479EC4863A202D8E6EEA878EF1E45AC6C9E503498EA4977B8A | |||
| 5748 | is-J0JV3.tmp | C:\Users\admin\AppData\Local\Temp\is-25LFP.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:C594B792B9C556EA62A30DE541D2FB03 | SHA256:5DCC1E0A197922907BCA2C4369F778BD07EE4B1BBBDF633E987A028A314D548E | |||
| 5748 | is-J0JV3.tmp | C:\Users\admin\AppData\Local\Temp\is-25LFP.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 5748 | is-J0JV3.tmp | C:\Users\admin\AppData\Local\Temp\is-25LFP.tmp\_isetup\_isdecmp.dll | executable | |
MD5:A813D18268AFFD4763DDE940246DC7E5 | SHA256:E19781AABE466DD8779CB9C8FA41BBB73375447066BB34E876CF388A6ED63C64 | |||
| 5548 | setup.exe | C:\Users\admin\AppData\Local\Temp\is-LEP4J.tmp\is-J0JV3.tmp | executable | |
MD5:4FA180886FF7C0FD86A65F760EDE6318 | SHA256:1D9026C60374B056720CDFCFA598A641CC8FBC9932590D69B4CFBC32CD09871C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
20
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1488 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1488 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1488 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 104.126.37.136:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1488 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1488 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |