| URL: | http://r20.rs6.net/tn.jsp?f=001ROQa8mruWtx3hC-XjRum-ix0iEmF2vOYTeDNNl-asCq10-nbVK1vPv0uqfVxK1MYrcWknUXEP_vkvyATOiSpsB-fbmfrX7fH2QXaGrSSjLJw7CGcifzQ198-PwYBKprVXg0AQaXBEZZ3Q5M-FoLvG8vZSTl2Npm8_ihI27b_4X7ZQtCZTCxonqYjwN1GnVDUILz-YmTEIjvyH4f3IcsRejOJLeVv7qky&c=FxO5xUKOxl9Vxwc3xbOeptObQFS4lkD9S3Wqgg1vGTaJAoXC_xvjHA==&ch=DuTGDmRxcpKDUzbYIz_vEREfWQfE0tD6WBuZphMqGsfCS8OcgQ3JJQ== |
| Full analysis: | https://app.any.run/tasks/5c26fb25-08de-443a-be37-7a9442a20bfc |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 03:28:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B12384A3AF8FE15B70CD966826B1F336 |
| SHA1: | D8F56B5117FA5F3DB1D029E9933C5C25E20DE1AE |
| SHA256: | 70CE31BA692CB00A2D53D92E28663EA1B16DC9DED6CAE87A12796ABAAEEE6CF5 |
| SSDEEP: | 6:CMXVBTmcq29OpNVkIr8c4qMyRGmh6G9ef3yaIkd7Ikmeoxm8Ahosw22hIsPlHari:ZFBqcq2eDrWqMyRGmh6UeCaDoeoxm8Xj |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 1032)
Reads the hosts file
- chrome.exe (PID: 1032)
- chrome.exe (PID: 4072)
Reads settings of System Certificates
- chrome.exe (PID: 4072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
37
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9858265473704001369,17928192741480053024,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15585193072661954244 --mojo-platform-channel-handle=4156 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9858265473704001369,17928192741480053024,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2665251009787677309 --mojo-platform-channel-handle=4432 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9858265473704001369,17928192741480053024,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1724936885835676433 --mojo-platform-channel-handle=5008 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9858265473704001369,17928192741480053024,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=386277052098201327 --mojo-platform-channel-handle=4344 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9858265473704001369,17928192741480053024,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12527547022592139859 --mojo-platform-channel-handle=3788 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://r20.rs6.net/tn.jsp?f=001ROQa8mruWtx3hC-XjRum-ix0iEmF2vOYTeDNNl-asCq10-nbVK1vPv0uqfVxK1MYrcWknUXEP_vkvyATOiSpsB-fbmfrX7fH2QXaGrSSjLJw7CGcifzQ198-PwYBKprVXg0AQaXBEZZ3Q5M-FoLvG8vZSTl2Npm8_ihI27b_4X7ZQtCZTCxonqYjwN1GnVDUILz-YmTEIjvyH4f3IcsRejOJLeVv7qky&c=FxO5xUKOxl9Vxwc3xbOeptObQFS4lkD9S3Wqgg1vGTaJAoXC_xvjHA==&ch=DuTGDmRxcpKDUzbYIz_vEREfWQfE0tD6WBuZphMqGsfCS8OcgQ3JJQ==" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,9858265473704001369,17928192741480053024,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12049227430553737910 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9858265473704001369,17928192741480053024,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1919654515270756024 --mojo-platform-channel-handle=4308 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=984 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9858265473704001369,17928192741480053024,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13451769899973738716 --mojo-platform-channel-handle=3940 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
373
Read events
305
Write events
64
Delete events
4
Modification events
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1032-13239084523840000 |
Value: 259 | |||
Executable files
0
Suspicious files
99
Text files
200
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0BD4EC-408.pma | — | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5cd8b904-b7cb-4e04-aae7-c1ffdef1598a.tmp | — | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF15cacb.TMP | text | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF15caeb.TMP | text | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15cccf.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
66
DNS requests
36
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4072 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
4072 | chrome.exe | GET | 302 | 208.75.122.11:80 | http://r20.rs6.net/tn.jsp?f=001ROQa8mruWtx3hC-XjRum-ix0iEmF2vOYTeDNNl-asCq10-nbVK1vPv0uqfVxK1MYrcWknUXEP_vkvyATOiSpsB-fbmfrX7fH2QXaGrSSjLJw7CGcifzQ198-PwYBKprVXg0AQaXBEZZ3Q5M-FoLvG8vZSTl2Npm8_ihI27b_4X7ZQtCZTCxonqYjwN1GnVDUILz-YmTEIjvyH4f3IcsRejOJLeVv7qky&c=FxO5xUKOxl9Vxwc3xbOeptObQFS4lkD9S3Wqgg1vGTaJAoXC_xvjHA==&ch=DuTGDmRxcpKDUzbYIz_vEREfWQfE0tD6WBuZphMqGsfCS8OcgQ3JJQ== | US | — | — | whitelisted |
4072 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
4072 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
4072 | chrome.exe | GET | 200 | 74.125.110.170:80 | http://r5---sn-5go7yner.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=196.244.192.14&mm=28&mn=sn-5go7yner&ms=nvh&mt=1594610571&mv=u&mvi=5&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
4072 | chrome.exe | GET | 200 | 173.194.163.105:80 | http://r3---sn-5go7yne6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=196.244.192.14&mm=28&mn=sn-5go7yne6&ms=nvh&mt=1594610571&mv=u&mvi=3&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4072 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 208.75.122.11:80 | r20.rs6.net | Constant Contact, Inc | US | suspicious |
4072 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
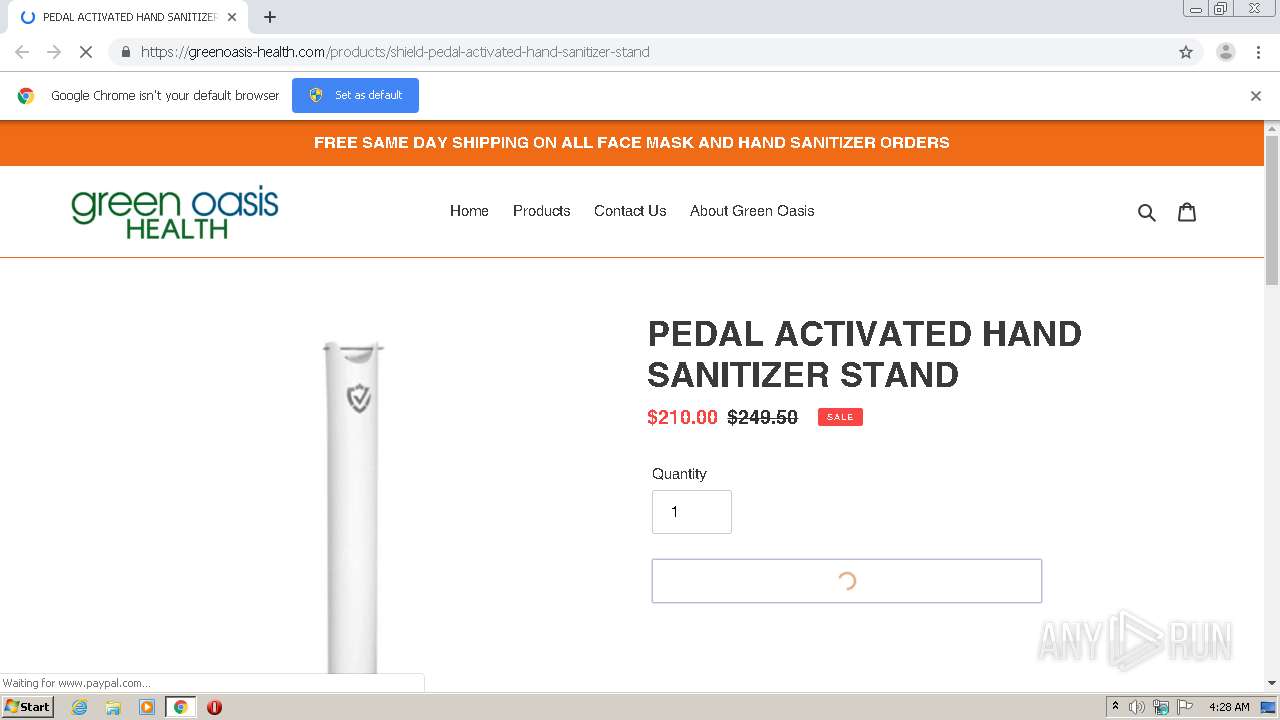
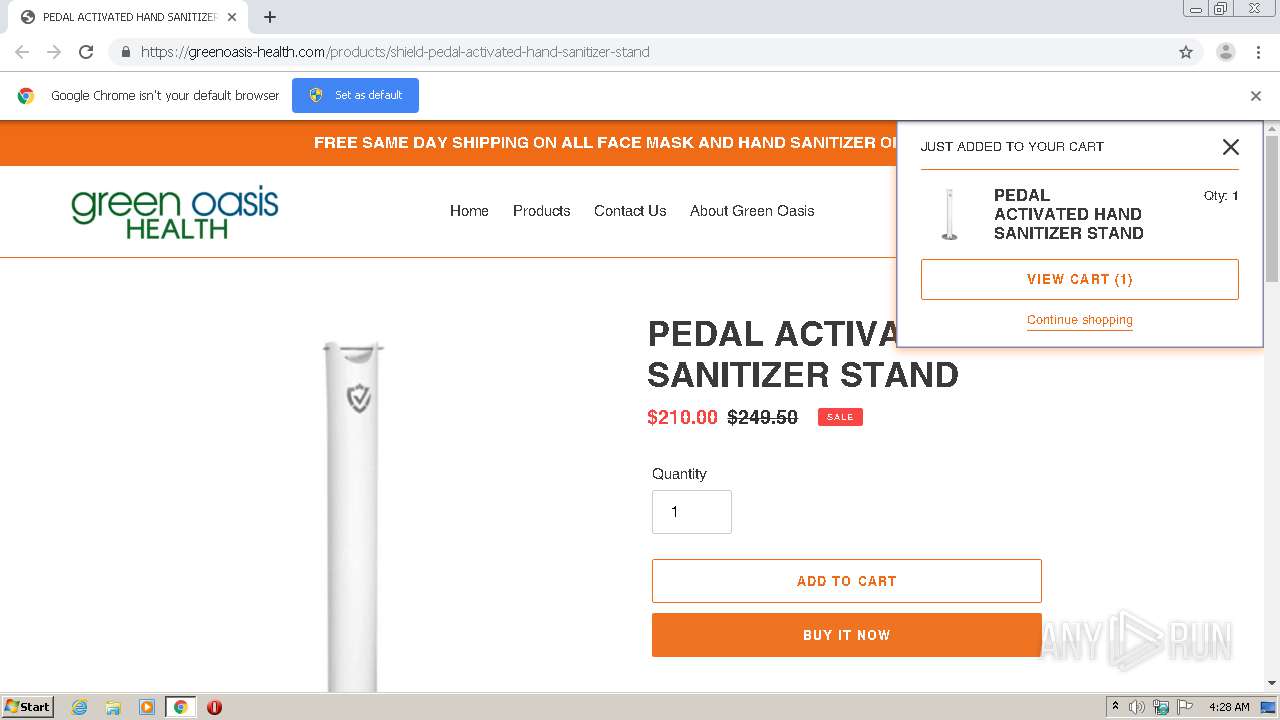
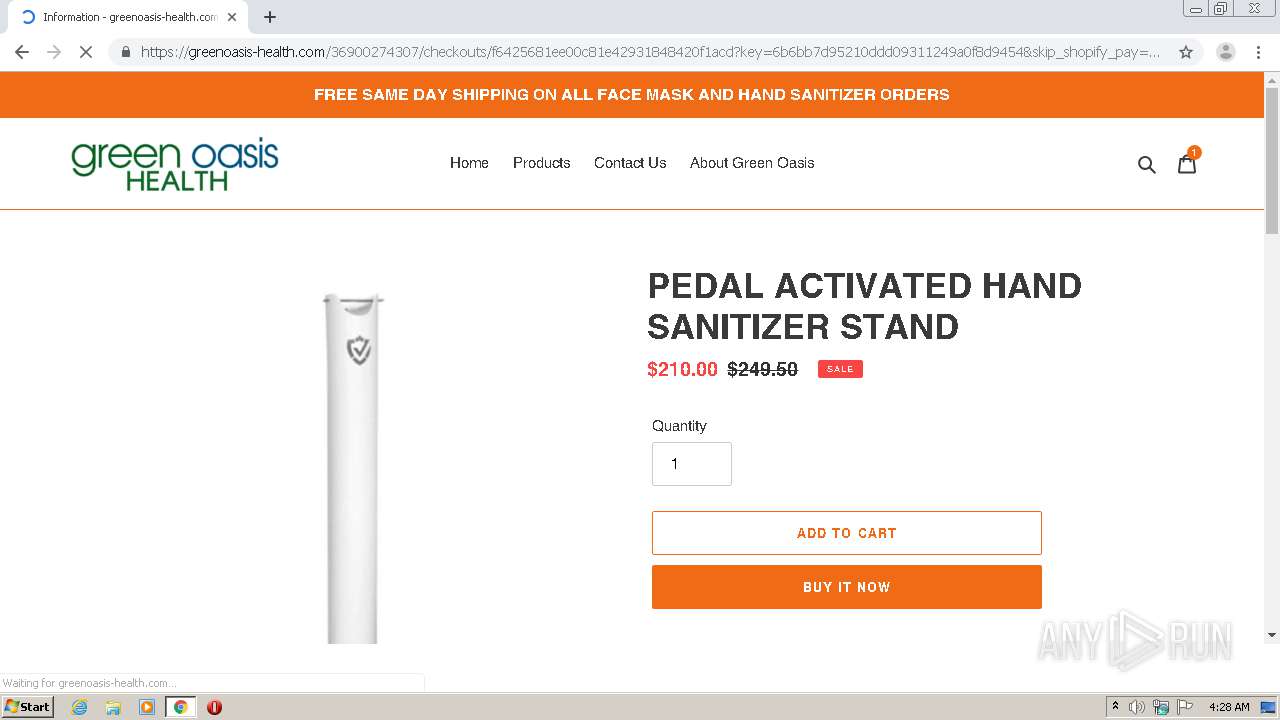
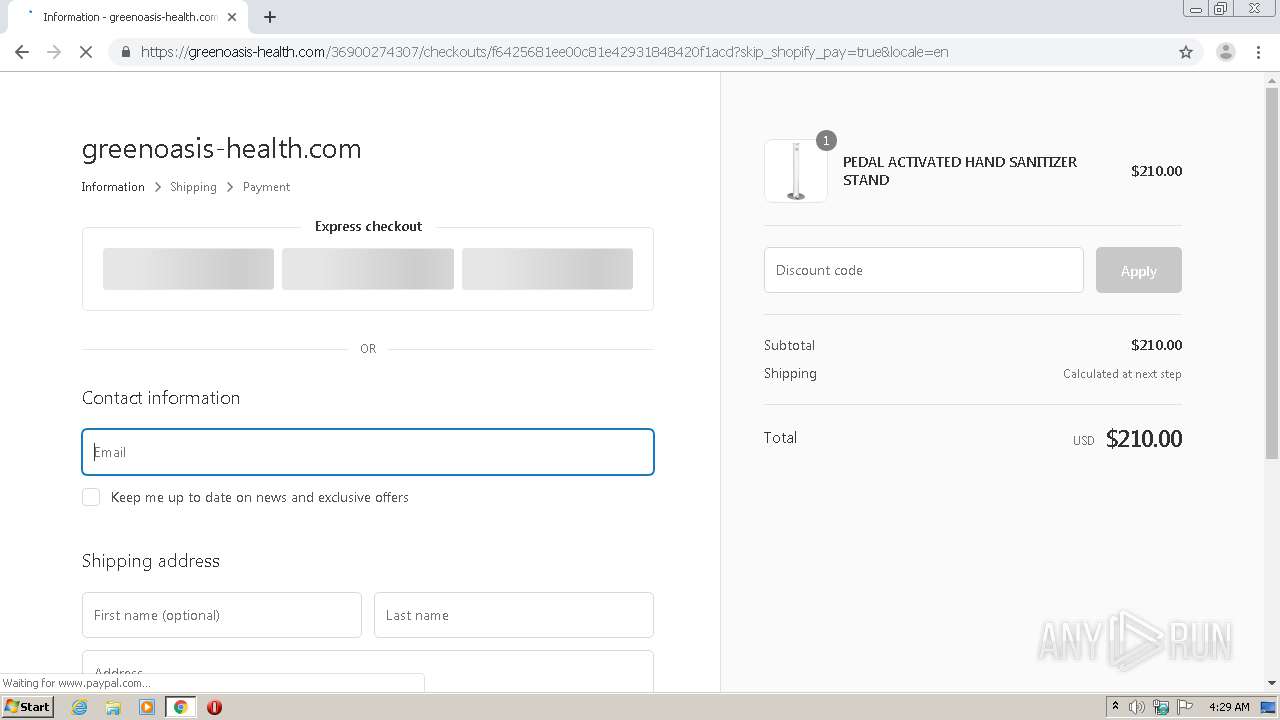
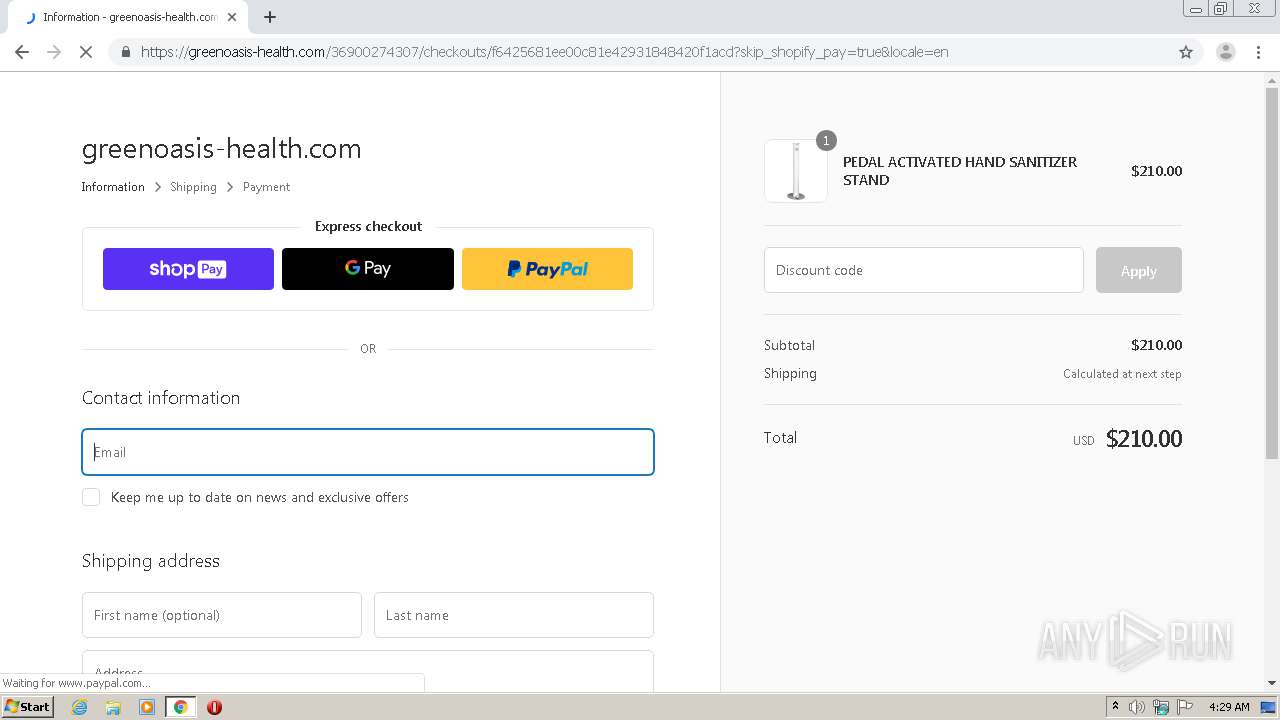
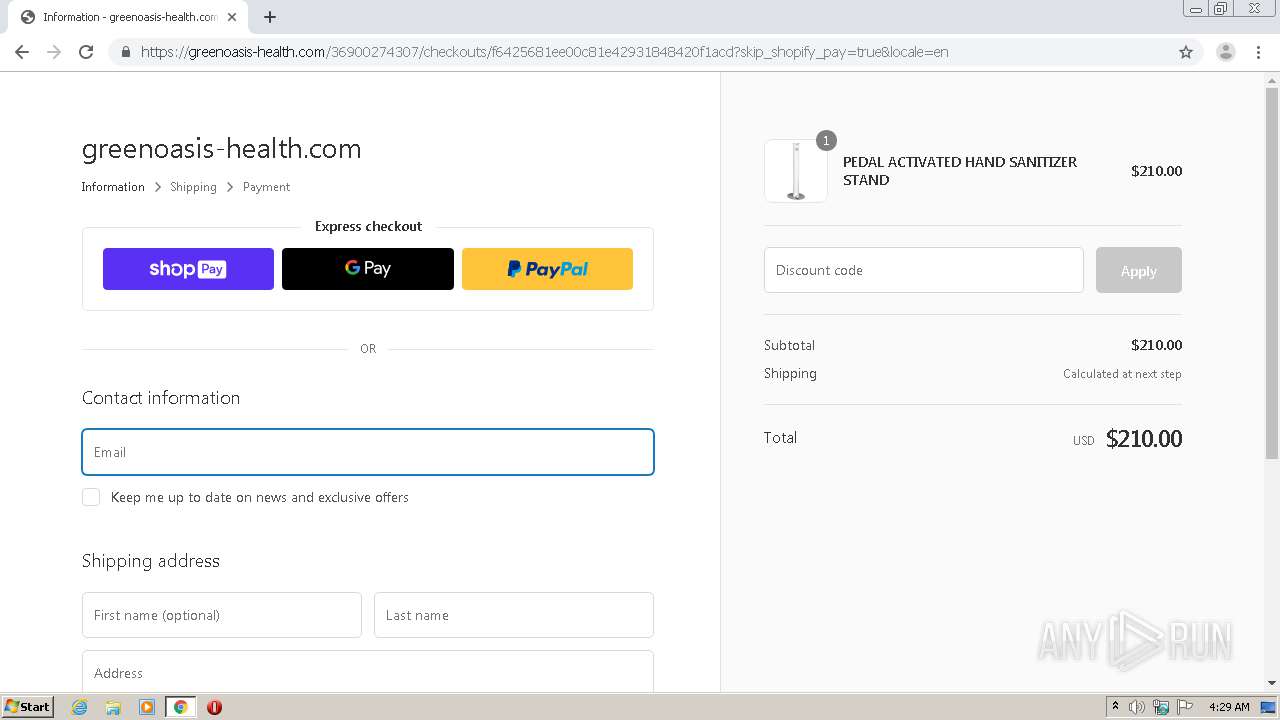
4072 | chrome.exe | 23.227.38.32:443 | greenoasis-health.com | Shopify, Inc. | CA | malicious |
4072 | chrome.exe | 143.204.208.2:443 | doxfy73wugunk.cloudfront.net | — | US | malicious |
4072 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 172.217.16.130:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 108.177.15.92:443 | pay.google.com | Google Inc. | US | unknown |
4072 | chrome.exe | 151.101.65.21:443 | www.paypal.com | Fastly | US | suspicious |
4072 | chrome.exe | 172.217.22.66:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
r20.rs6.net |
| whitelisted |
accounts.google.com |
| shared |
greenoasis-health.com |
| malicious |
doxfy73wugunk.cloudfront.net |
| whitelisted |
cdn.shopify.com |
| whitelisted |
www.google.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
fonts.shopifycdn.com |
| whitelisted |
monorail-edge.shopifysvc.com |
| whitelisted |