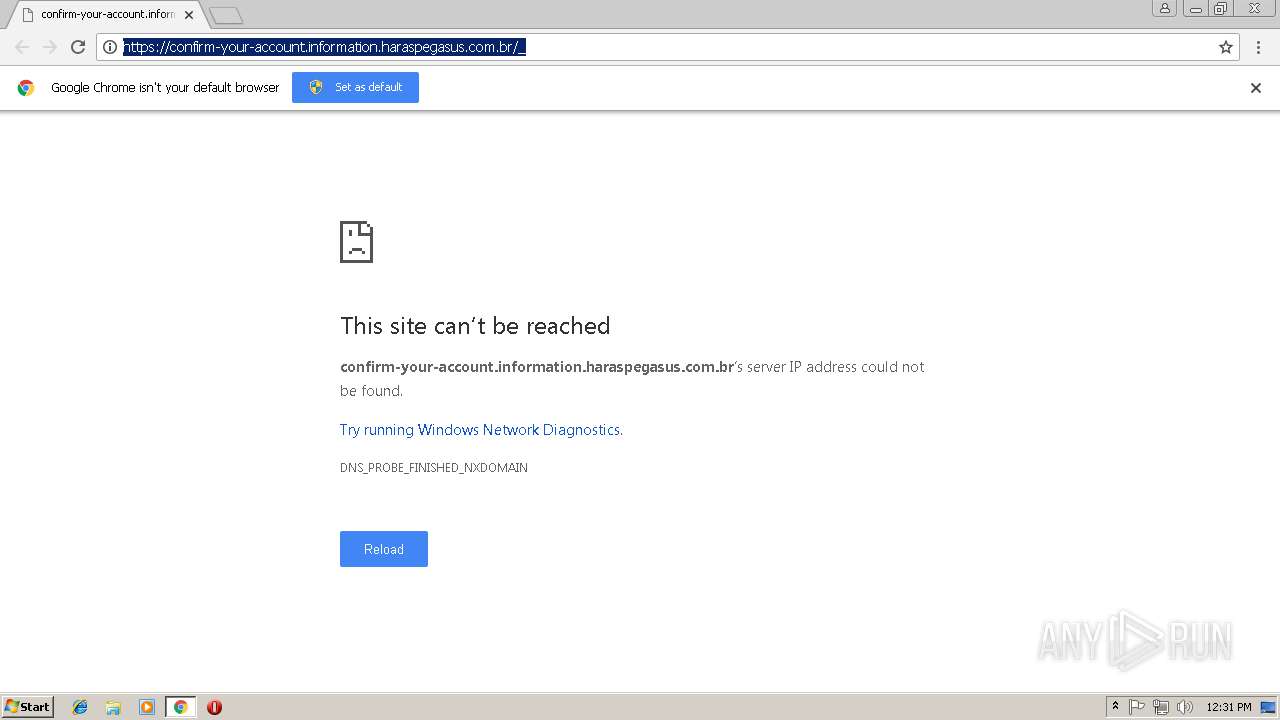
| URL: | https://confirm-your-account.information.haraspegasus.com.br/_ |
| Full analysis: | https://app.any.run/tasks/e3bf0af0-cdc5-4b7e-aef1-500d5f9c2ff8 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 12:31:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D5F23EEB5E858E5EEA35D22DBBF50968 |
| SHA1: | 75AAC95E355C932BC5167ED86AFD5E54C6E8CA40 |
| SHA256: | 70B0E229686B8A71CD477D45881ECED80B28156BCCE6530CD2CB304D75F0CB54 |
| SSDEEP: | 3:N8X8XNCY4h/MKLLWPqHh:2MkY4VMKoqHh |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2748)
Reads settings of System Certificates
- chrome.exe (PID: 2748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
11
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=944,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=27FA7F2C489BAE057CB7508B5C678935 --mojo-platform-channel-handle=924 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --service-pipe-token=B444575A4A9132E3AC74899C0BFD7EA9 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B444575A4A9132E3AC74899C0BFD7EA9 --renderer-client-id=4 --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://confirm-your-account.information.haraspegasus.com.br/_ | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1D4F6DD7C7BBBF0433BBE3CC97DB31D6 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1D4F6DD7C7BBBF0433BBE3CC97DB31D6 --renderer-client-id=7 --mojo-platform-channel-handle=3536 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2752 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=944,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=58D1BFC55129EB479FB64936029BAE10 --mojo-platform-channel-handle=3492 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=F07C830BB372BDCD18A988957AB7D086 --mojo-platform-channel-handle=2916 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=C5DCBE88DE1B5AA0E0A51742931FA24D --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C5DCBE88DE1B5AA0E0A51742931FA24D --renderer-client-id=6 --mojo-platform-channel-handle=2152 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8A9B04C0E5404C7D17270B09321FBF6A --mojo-platform-channel-handle=2592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,15711921451958387943,14411485918852507715,131072 --enable-features=PasswordImport --service-pipe-token=51FCC4DE1B02732CF48AF41457A4022A --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=51FCC4DE1B02732CF48AF41457A4022A --renderer-client-id=3 --mojo-platform-channel-handle=2156 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
504
Read events
454
Write events
47
Delete events
3
Modification events
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2748-13192633880075375 |
Value: 259 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2748-13192633880075375 |
Value: 259 | |||
Executable files
0
Suspicious files
27
Text files
79
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b03920e5-56e9-456a-8bdf-f5c7bd450edf.tmp | — | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fe877fb3-9414-47f5-b4e3-ee79a26896bc.tmp | — | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2459d8.TMP | text | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF2459f8.TMP | text | |
MD5:— | SHA256:— | |||
| 2748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2459f8.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
36
DNS requests
21
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
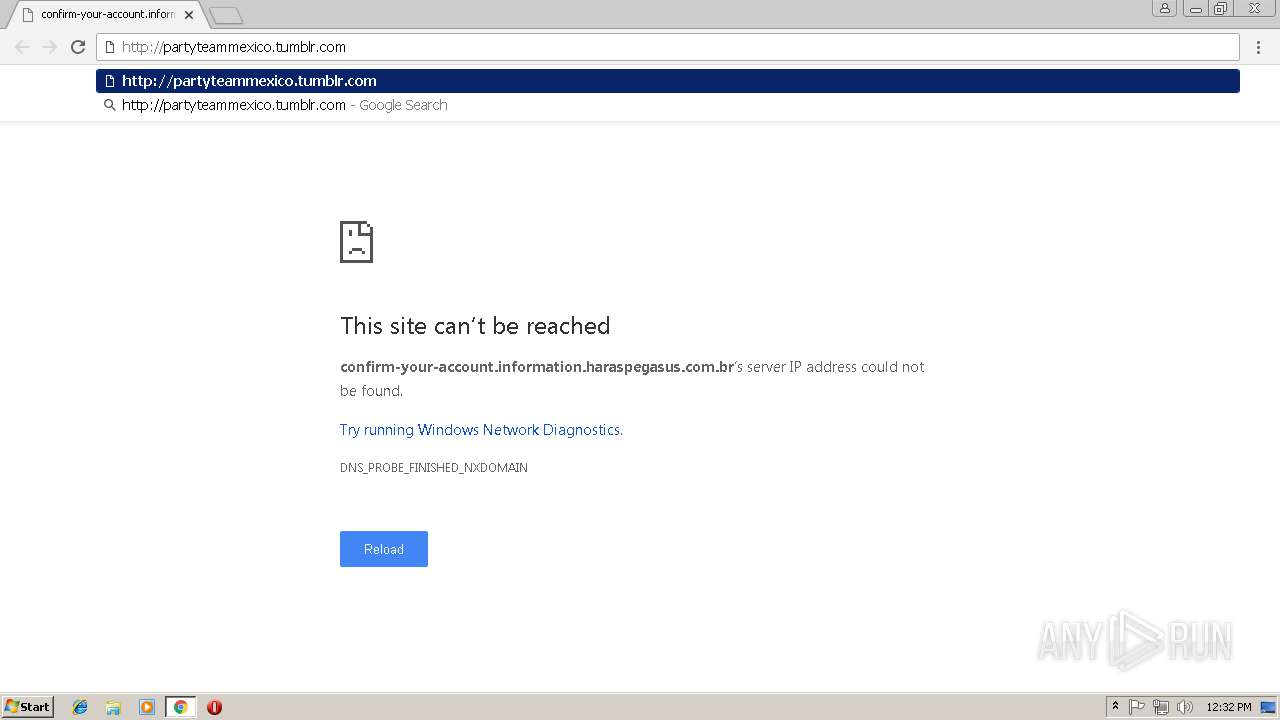
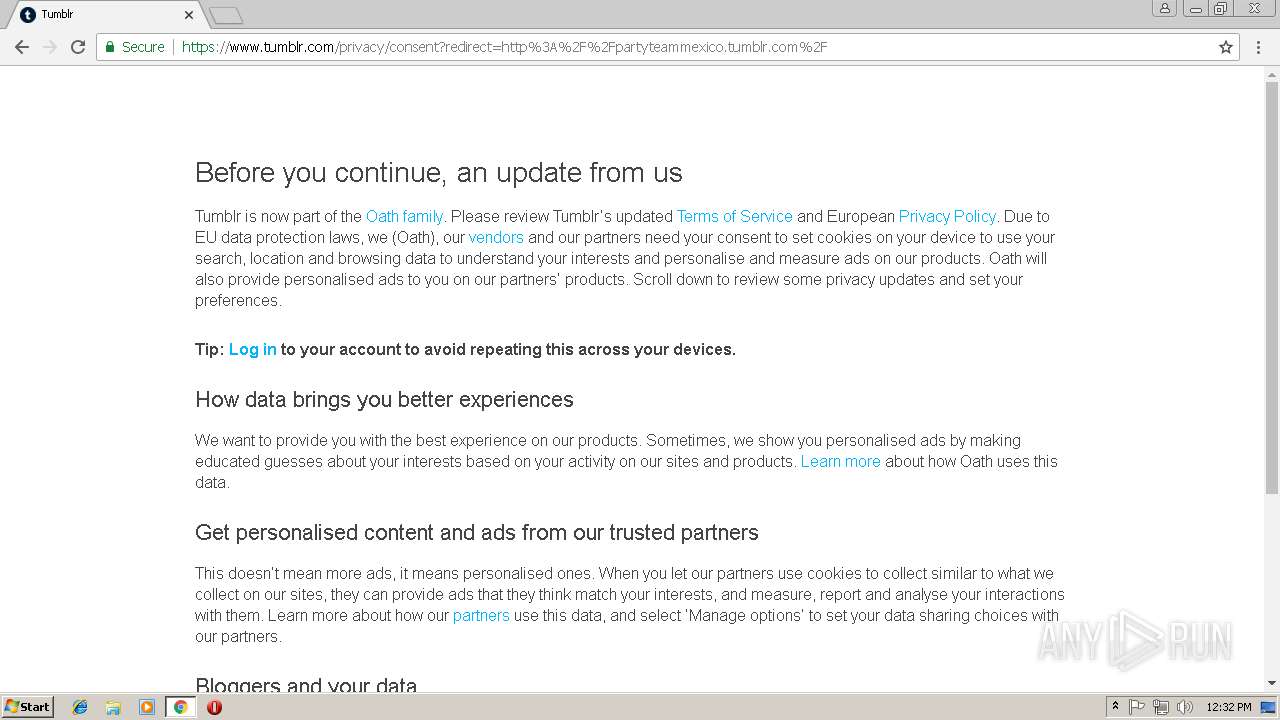
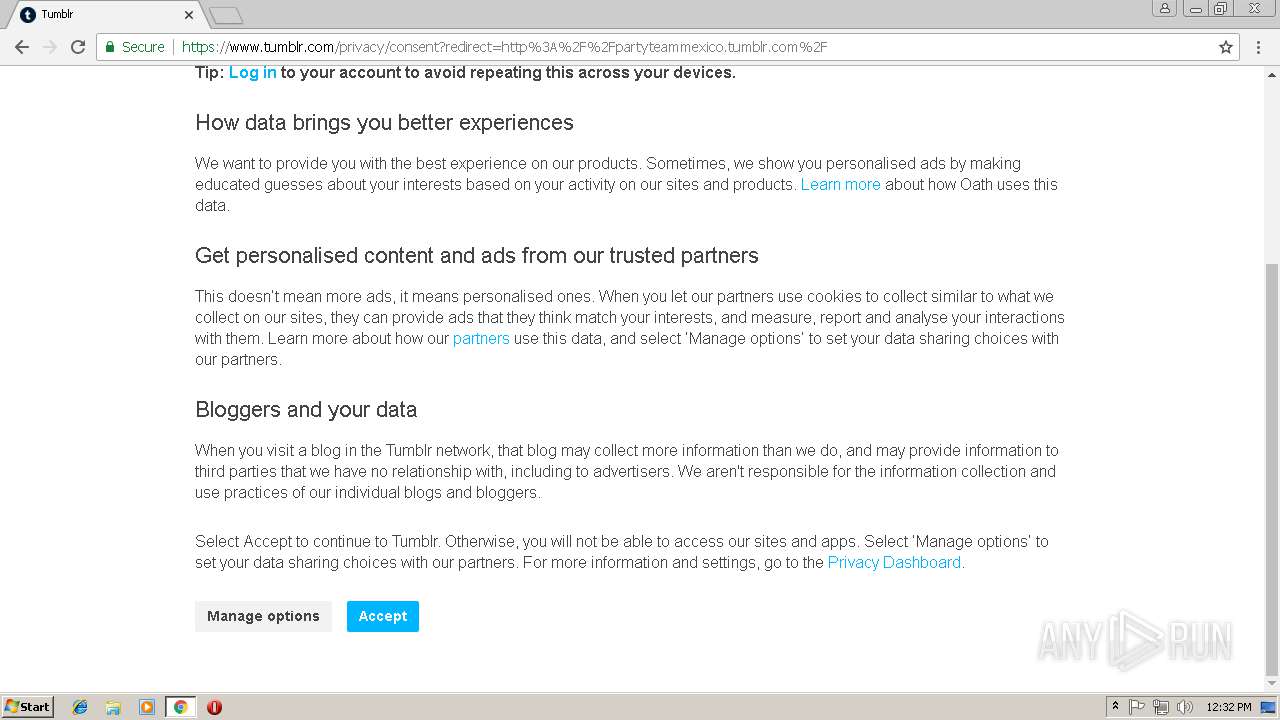
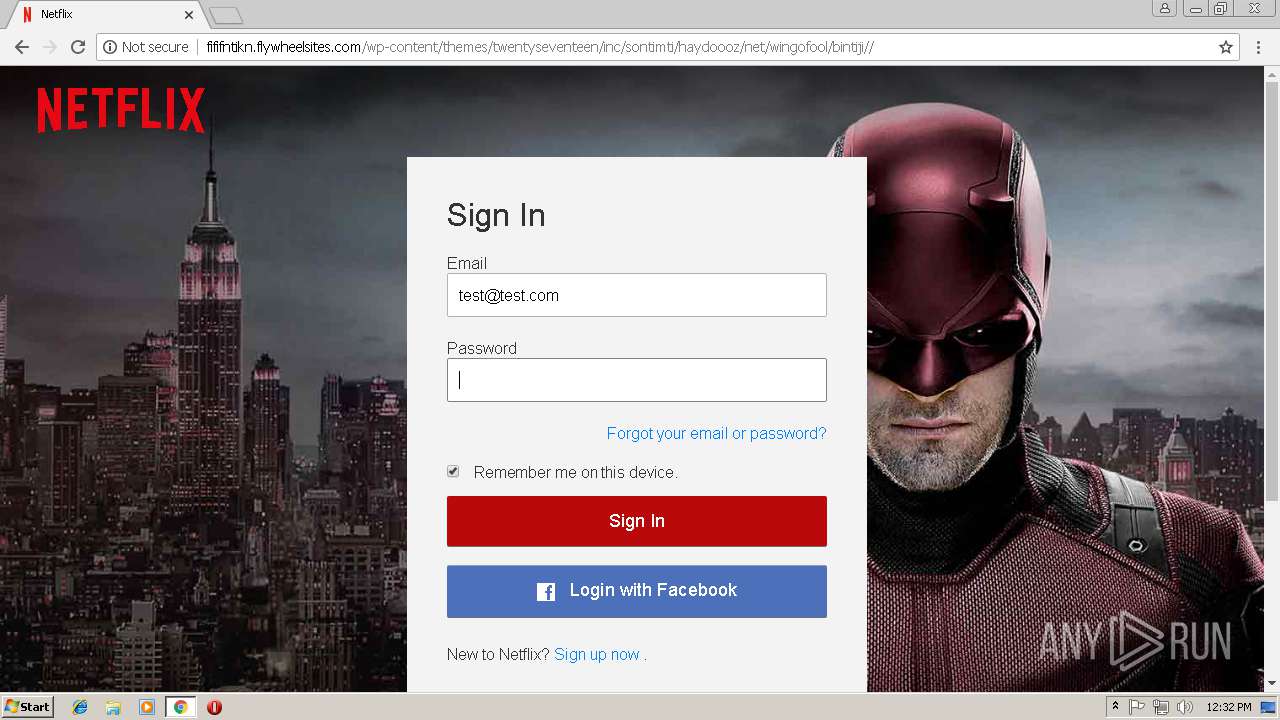
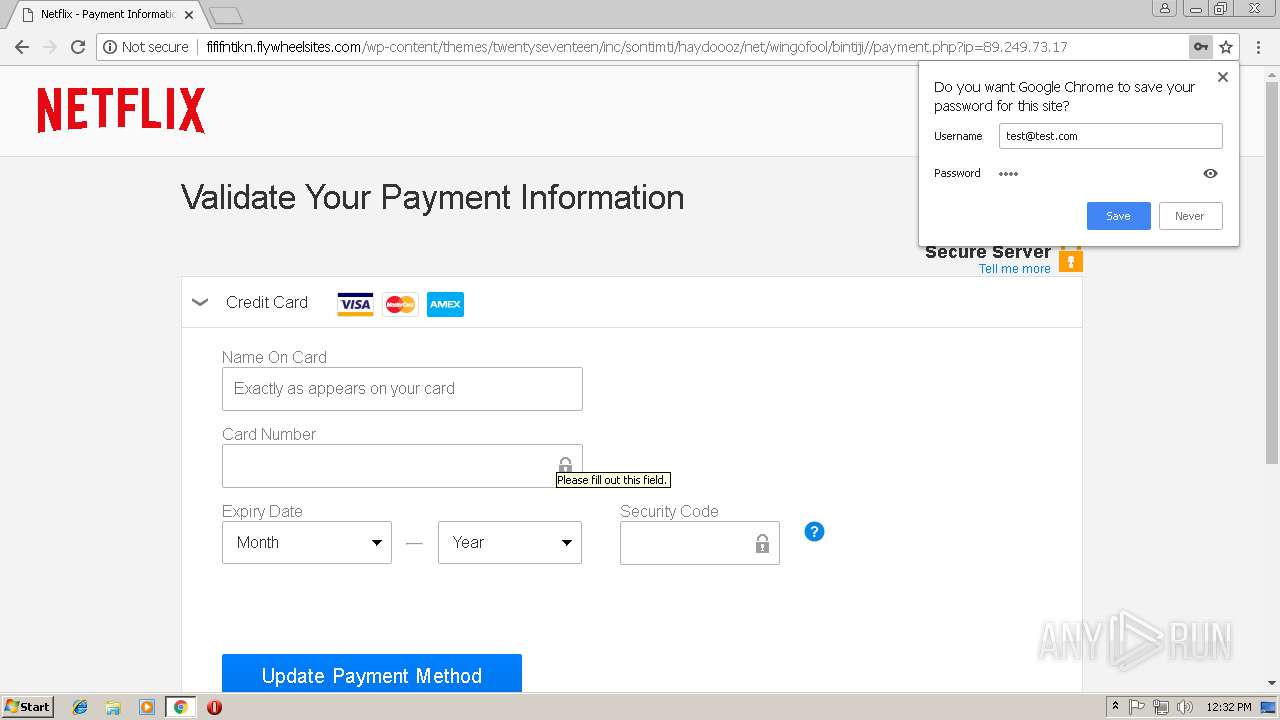
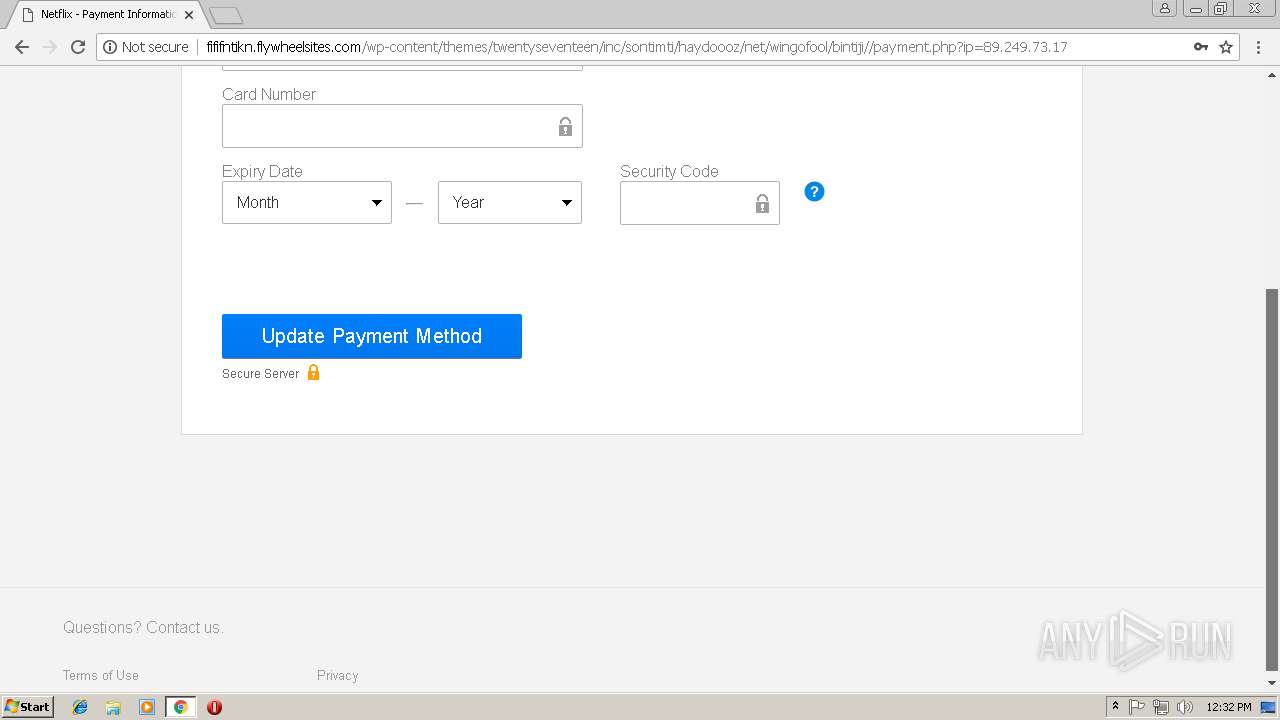
2748 | chrome.exe | GET | 302 | 66.6.32.21:80 | http://partyteammexico.tumblr.com/ | US | — | — | suspicious |
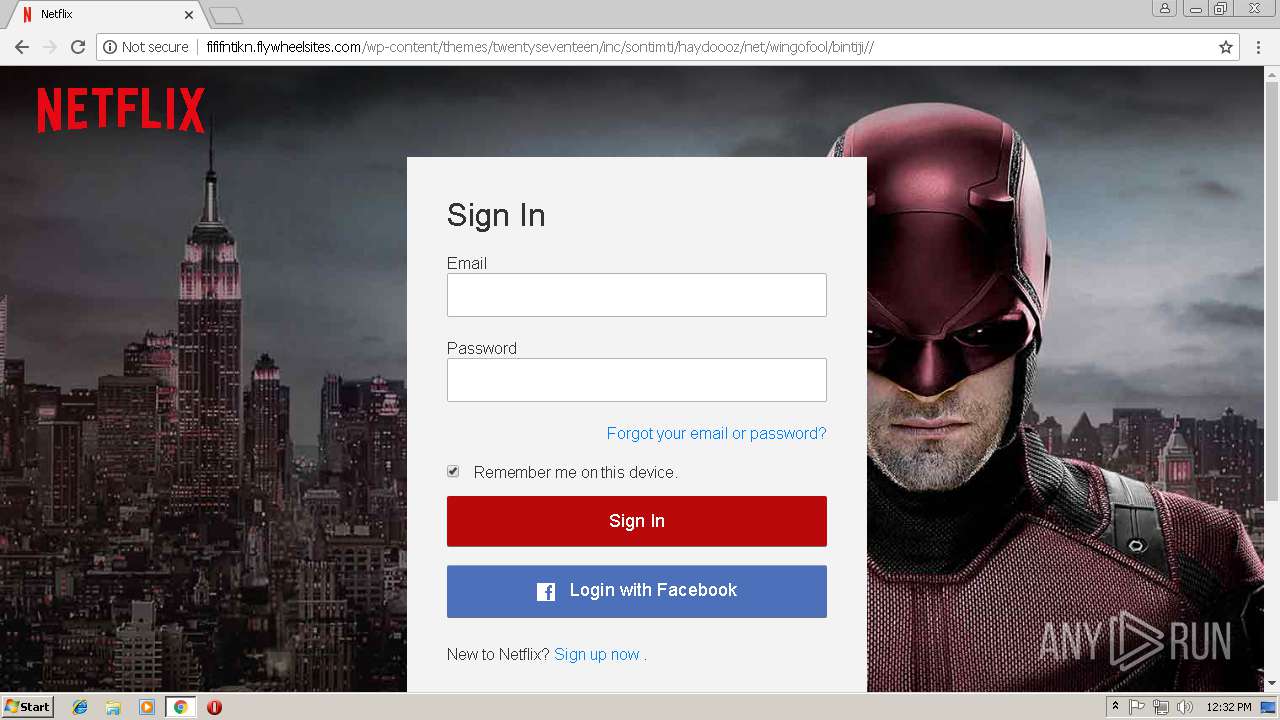
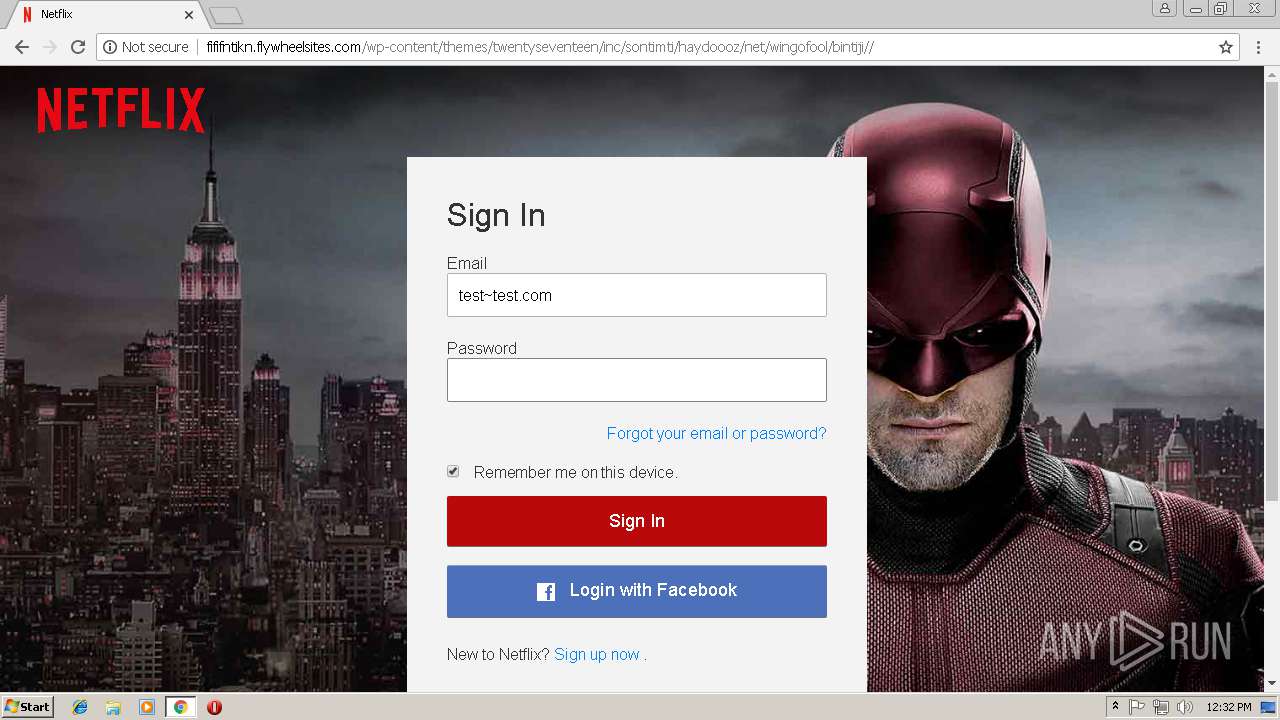
2748 | chrome.exe | GET | 200 | 206.189.59.99:80 | http://fififntikn.flywheelsites.com/wp-content/themes/twentyseventeen/inc/sontimti/haydoooz/net/wingofool/bintiji//img/nficon2015.ico | US | image | 7.61 Kb | suspicious |
2748 | chrome.exe | GET | 200 | 206.189.59.99:80 | http://fififntikn.flywheelsites.com/wp-content/themes/twentyseventeen/inc/sontimti/haydoooz/net/wingofool/bintiji//css/c.css | US | text | 7.94 Kb | suspicious |
2748 | chrome.exe | POST | 302 | 206.189.59.99:80 | http://fififntikn.flywheelsites.com/wp-content/themes/twentyseventeen/inc/sontimti/haydoooz/net/wingofool/bintiji//r1.php | US | — | — | suspicious |
2748 | chrome.exe | GET | 200 | 206.189.59.99:80 | http://fififntikn.flywheelsites.com/wp-content/themes/twentyseventeen/inc/sontimti/haydoooz/net/wingofool/bintiji//css/b.css | US | text | 8.48 Kb | suspicious |
2748 | chrome.exe | GET | 404 | 206.189.59.99:80 | http://fififntikn.flywheelsites.com/wp-content/themes/twentyseventeen/inc/sontimti/haydoooz/net/wingofool/bintiji/imag/nficon2015.ico | US | html | 2.82 Kb | suspicious |
2748 | chrome.exe | GET | 301 | 206.189.59.99:80 | http://fififntikn.flywheelsites.com/wp-content/themes/twentyseventeen/inc/sontimti/haydoooz/net/wingofool/bintiji//imag/nficon2015.ico | US | compressed | 7.94 Kb | suspicious |
2748 | chrome.exe | GET | 200 | 206.189.59.99:80 | http://fififntikn.flywheelsites.com/wp-content/themes/twentyseventeen/inc/sontimti/haydoooz/net/wingofool/bintiji// | US | html | 3.71 Kb | suspicious |
2748 | chrome.exe | GET | 200 | 206.189.59.99:80 | http://fififntikn.flywheelsites.com/wp-content/themes/twentyseventeen/inc/sontimti/haydoooz/net/wingofool/bintiji//hok.js | US | text | 5.95 Kb | suspicious |
2748 | chrome.exe | GET | 200 | 206.189.59.99:80 | http://fififntikn.flywheelsites.com/wp-content/themes/twentyseventeen/inc/sontimti/haydoooz/net/wingofool/bintiji//css/a.css | US | text | 8.07 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2748 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2748 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2748 | chrome.exe | 216.58.211.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
2748 | chrome.exe | 8.8.8.8:53 | — | Google Inc. | US | malicious |
2748 | chrome.exe | 172.217.23.142:443 | google.com | Google Inc. | US | whitelisted |
2748 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
2748 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2748 | chrome.exe | 66.6.32.21:80 | partyteammexico.tumblr.com | Yahoo! | US | unknown |
2748 | chrome.exe | 216.58.207.35:443 | www.google.de | Google Inc. | US | whitelisted |
2748 | chrome.exe | 87.248.114.13:443 | www.tumblr.com | Yahoo! UK Services Limited | GB | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
confirm-your-account.information.haraspegasus.com.br |
| unknown |
accounts.google.com |
| shared |
google.com |
| malicious |
clients4.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
partyteammexico.tumblr.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2748 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS AES Crypto Observed in Javascript - Possible Phishing Landing |
2748 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS AES Crypto Observed in Javascript - Possible Phishing Landing M1 Dec 28 2015 |
2748 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Generic AES Phishing Landing 2018-08-30 |
2748 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] AES Crypto Observed in Javascript - Possible Phishing |
2748 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Successful Generic AES Phish M1 Oct 24 2017 |
2748 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Successful Generic AES Phish M2 Oct 24 2017 |
2748 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS AES Crypto Observed in Javascript - Possible Phishing Landing |
2748 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS AES Crypto Observed in Javascript - Possible Phishing Landing M1 Dec 28 2015 |
2748 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Generic AES Phishing Landing 2018-08-30 |
2748 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] AES Crypto Observed in Javascript - Possible Phishing |
3 ETPRO signatures available at the full report