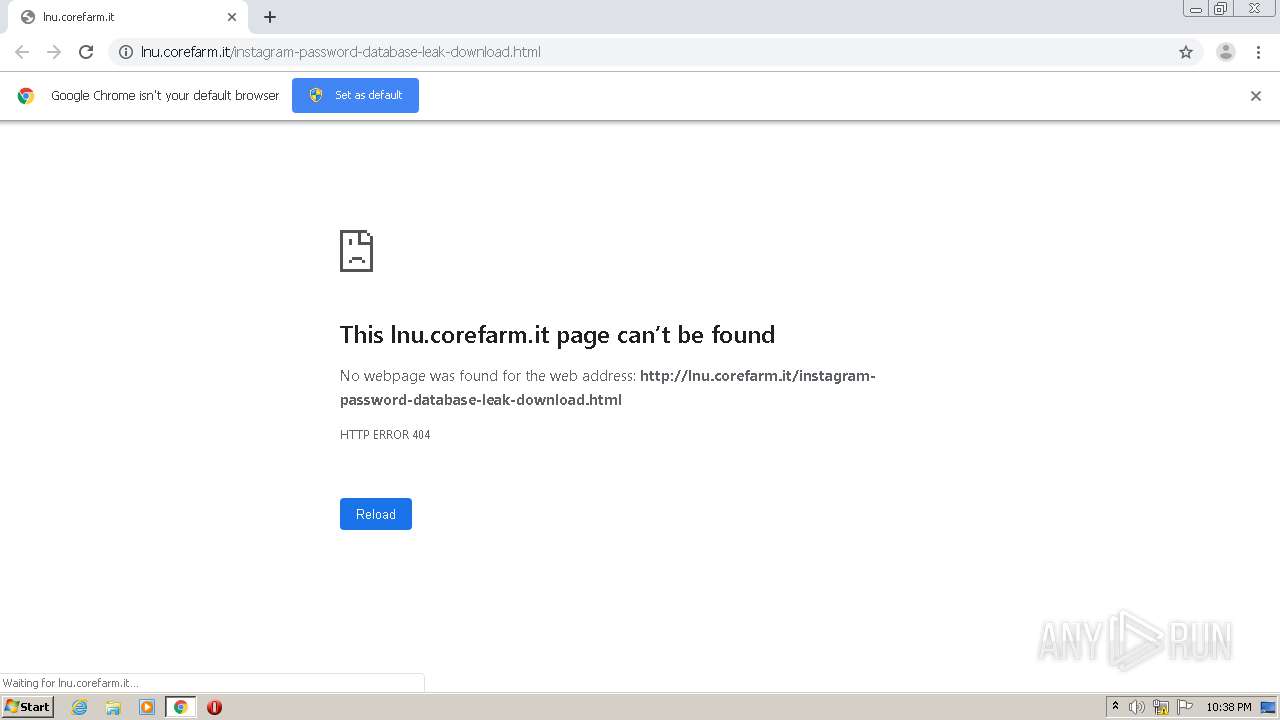
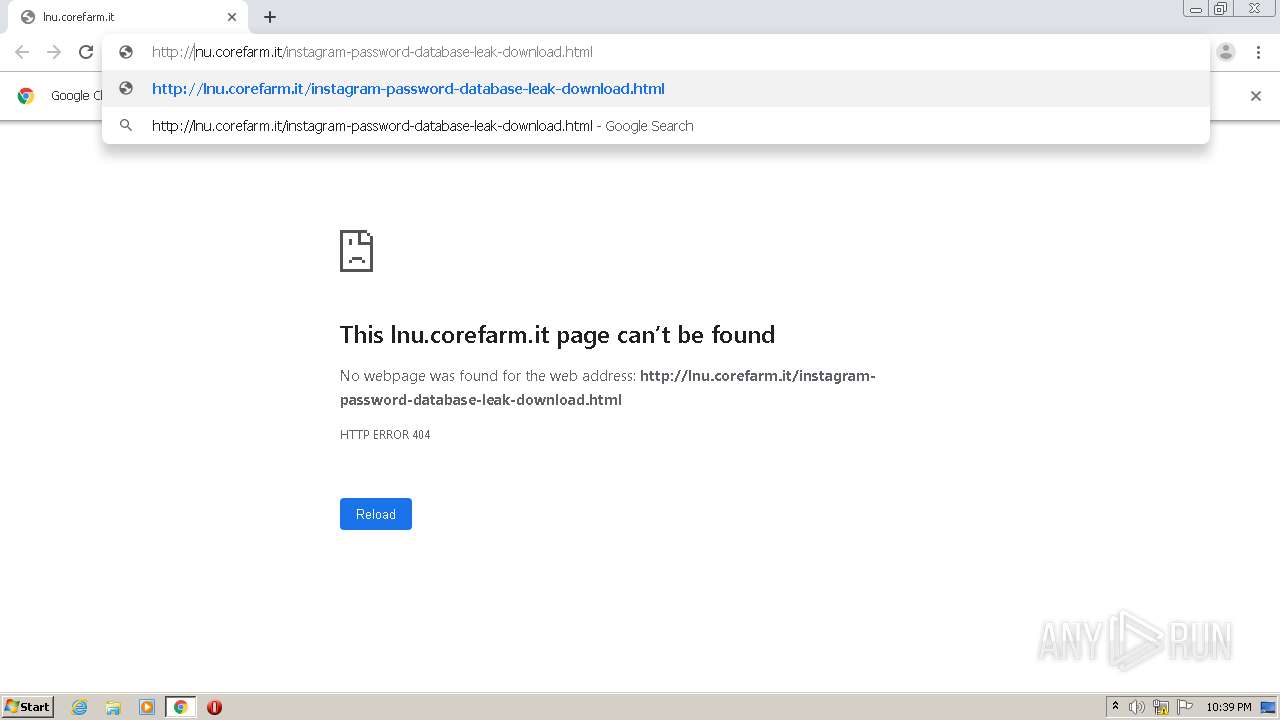
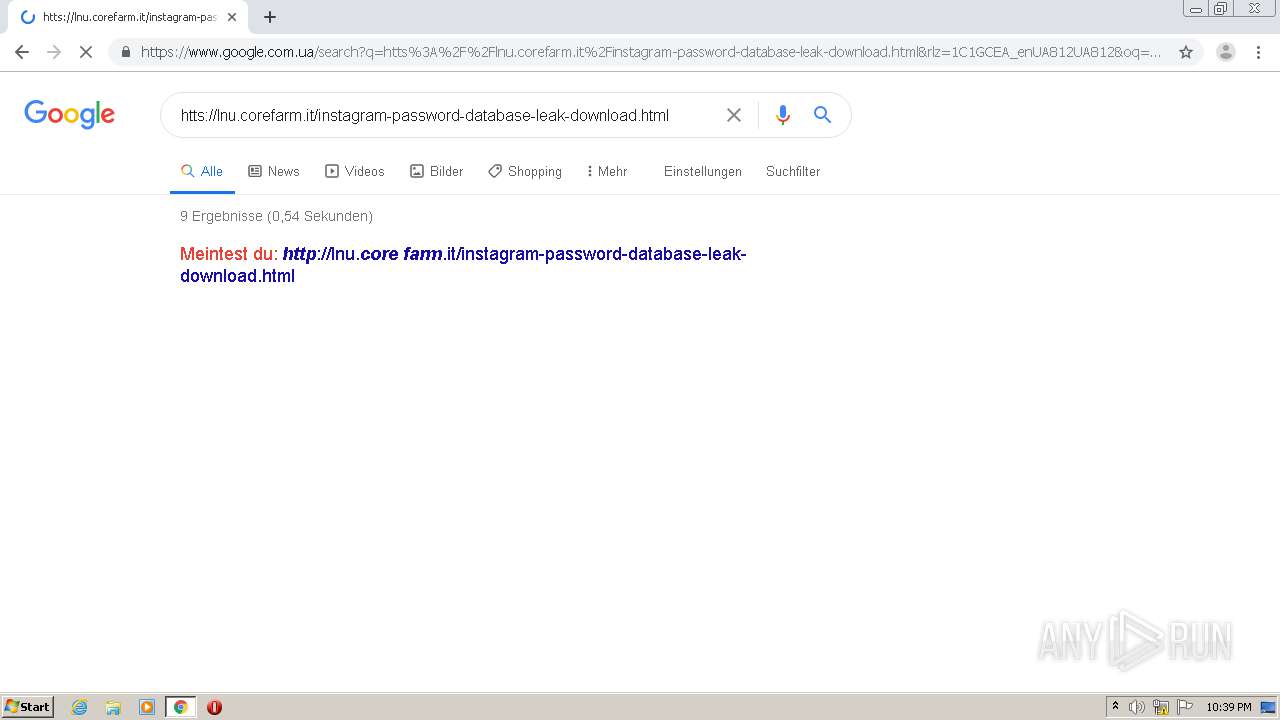
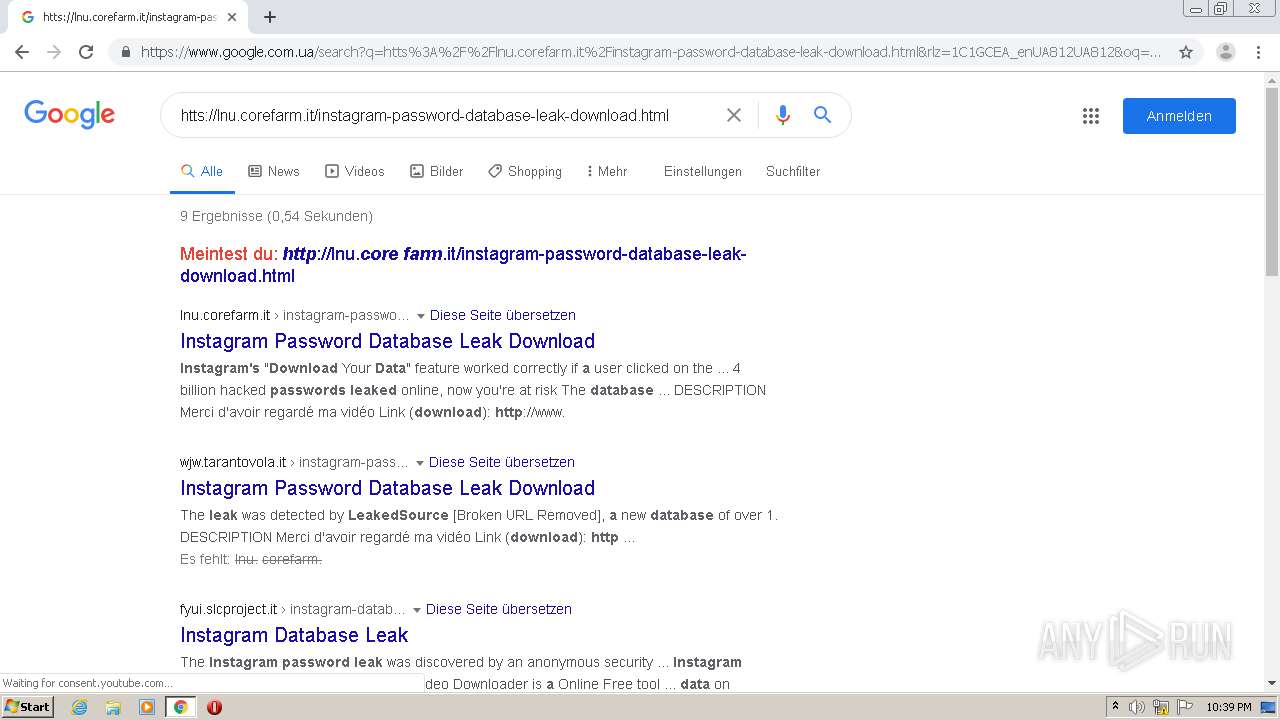
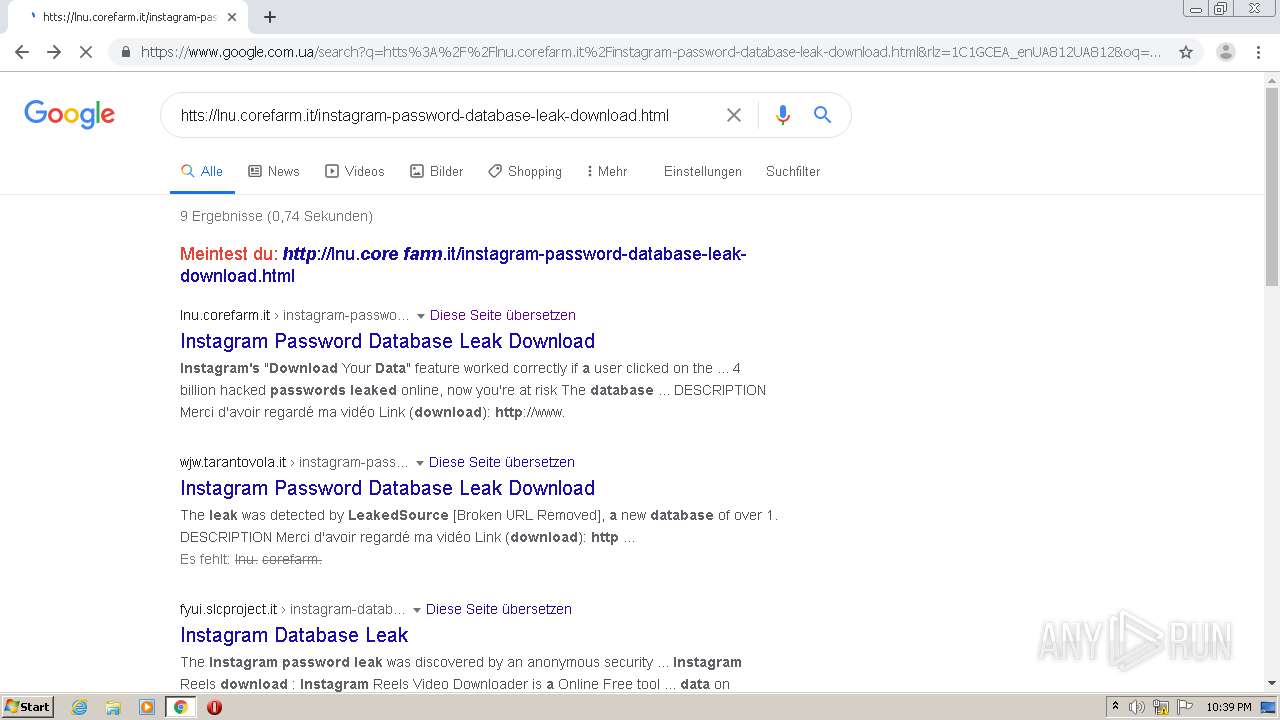
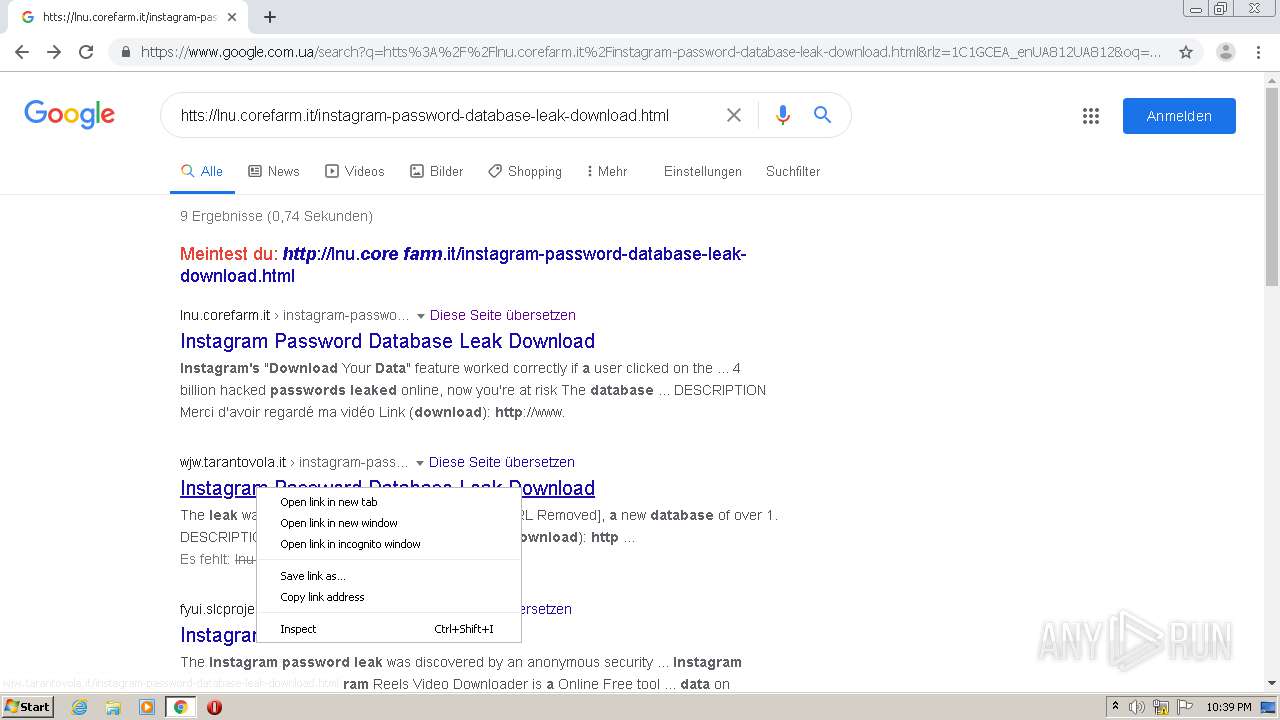
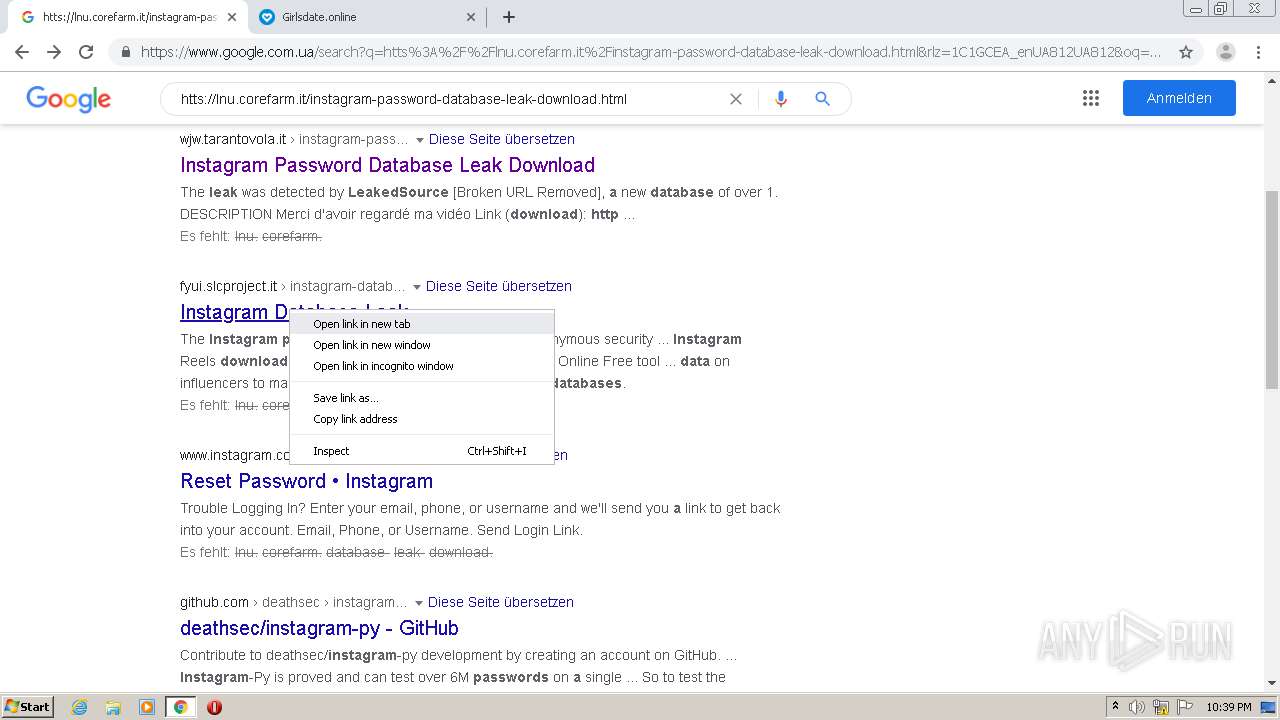
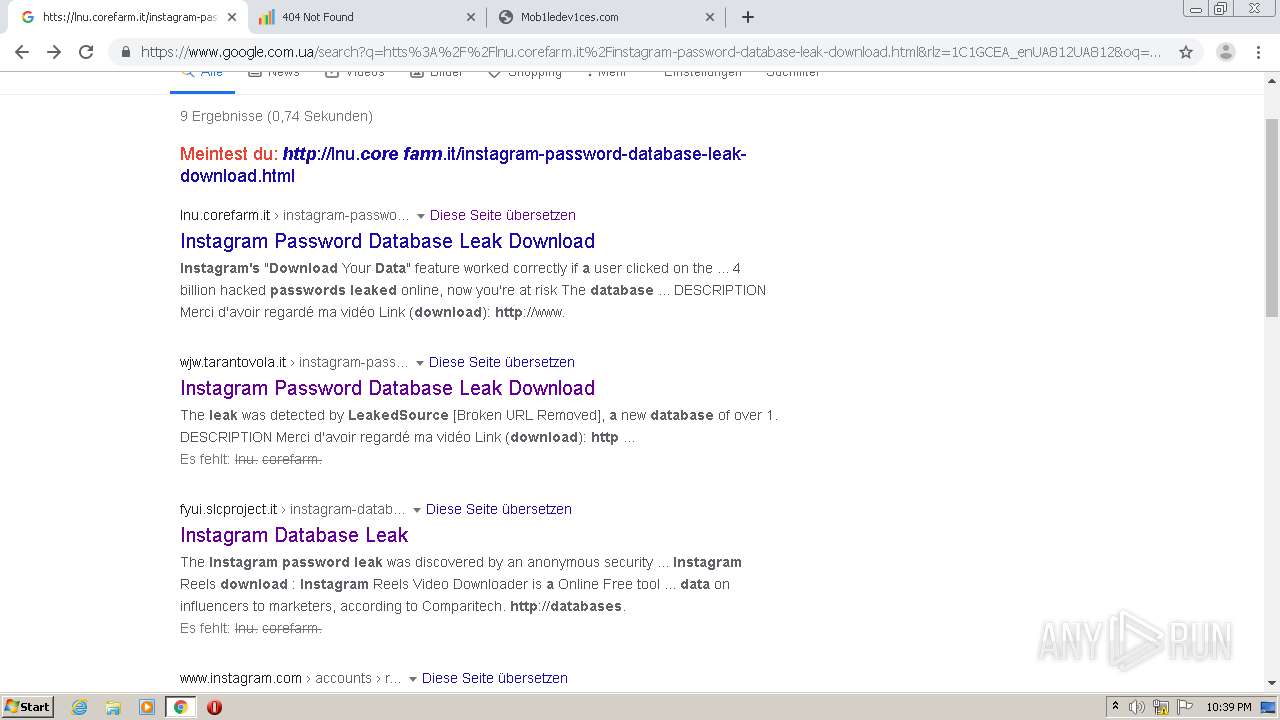
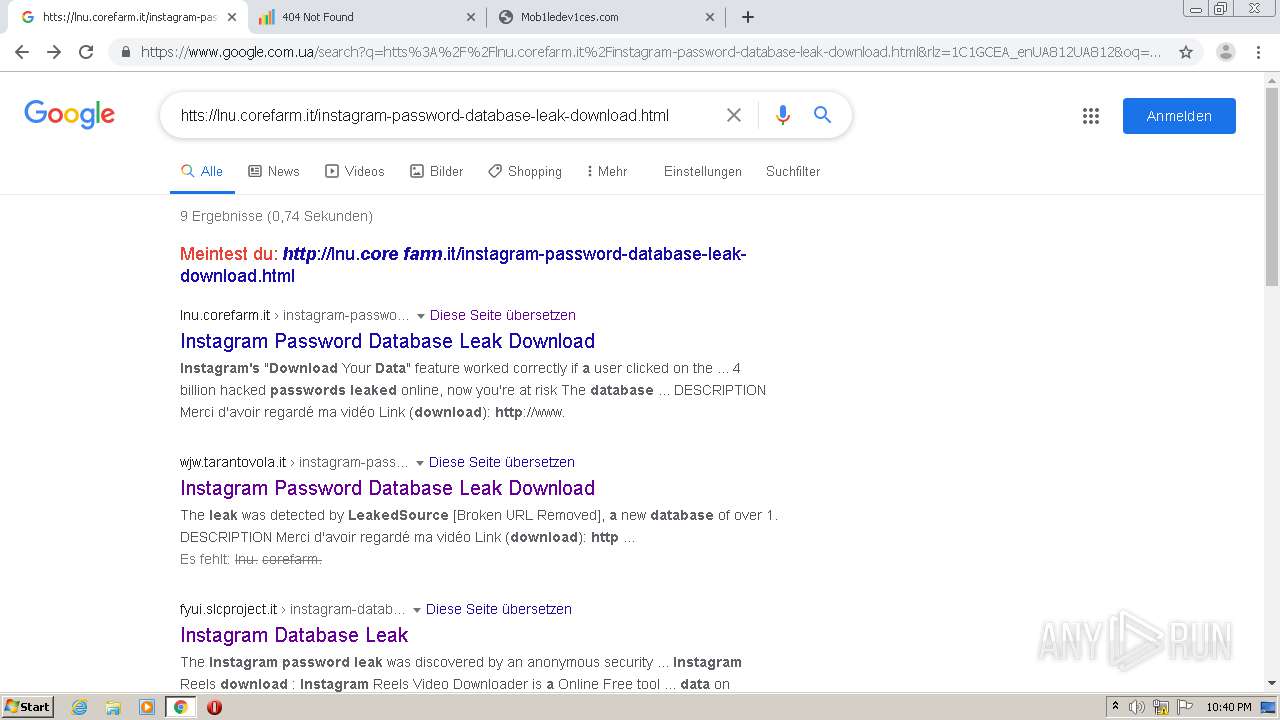
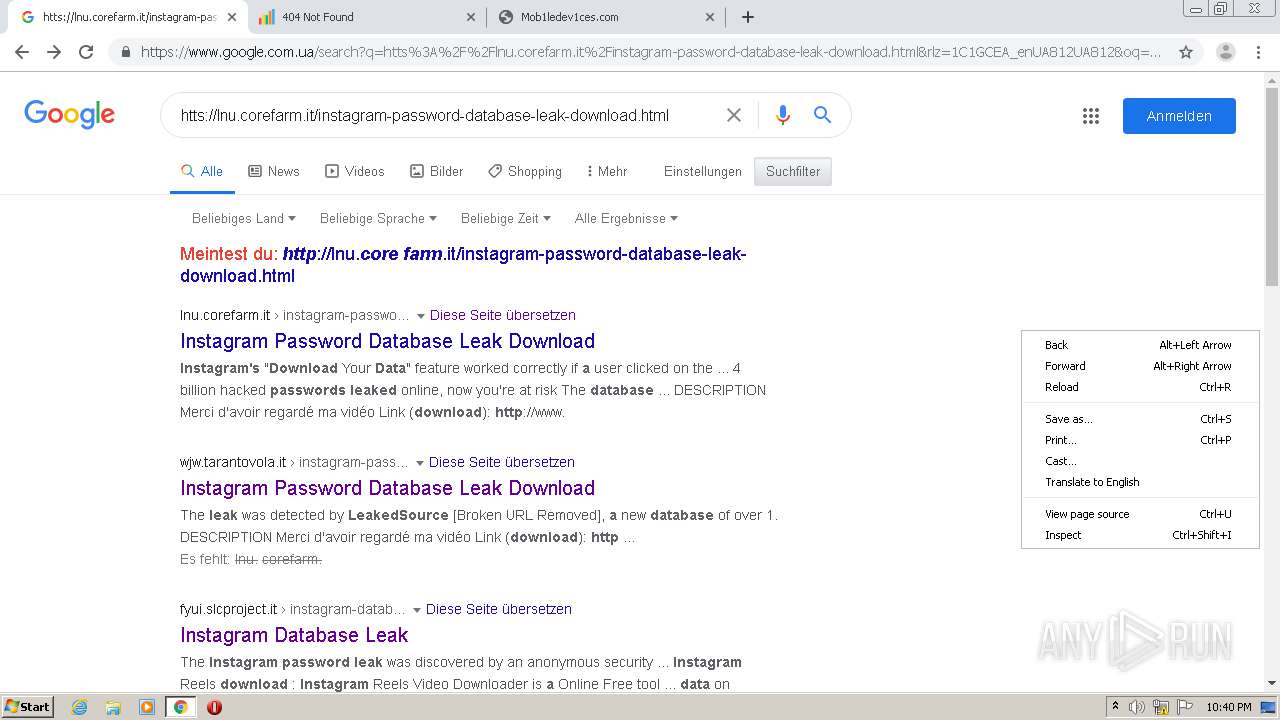
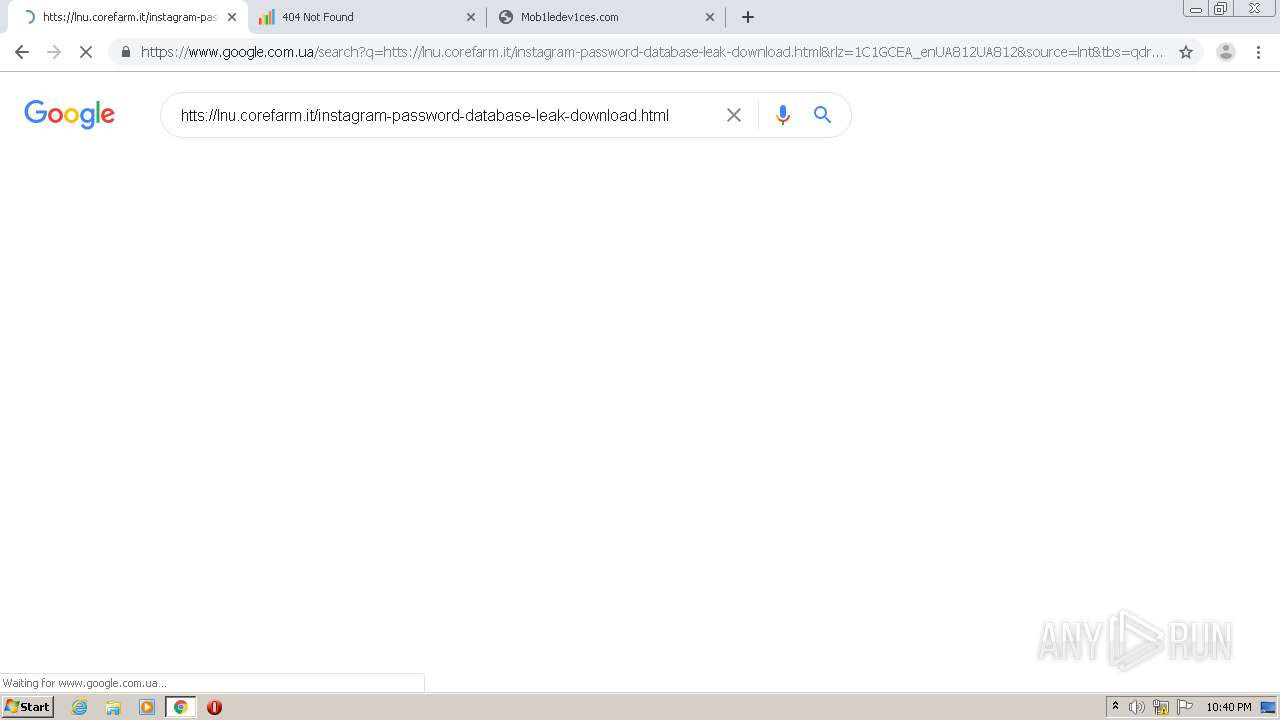
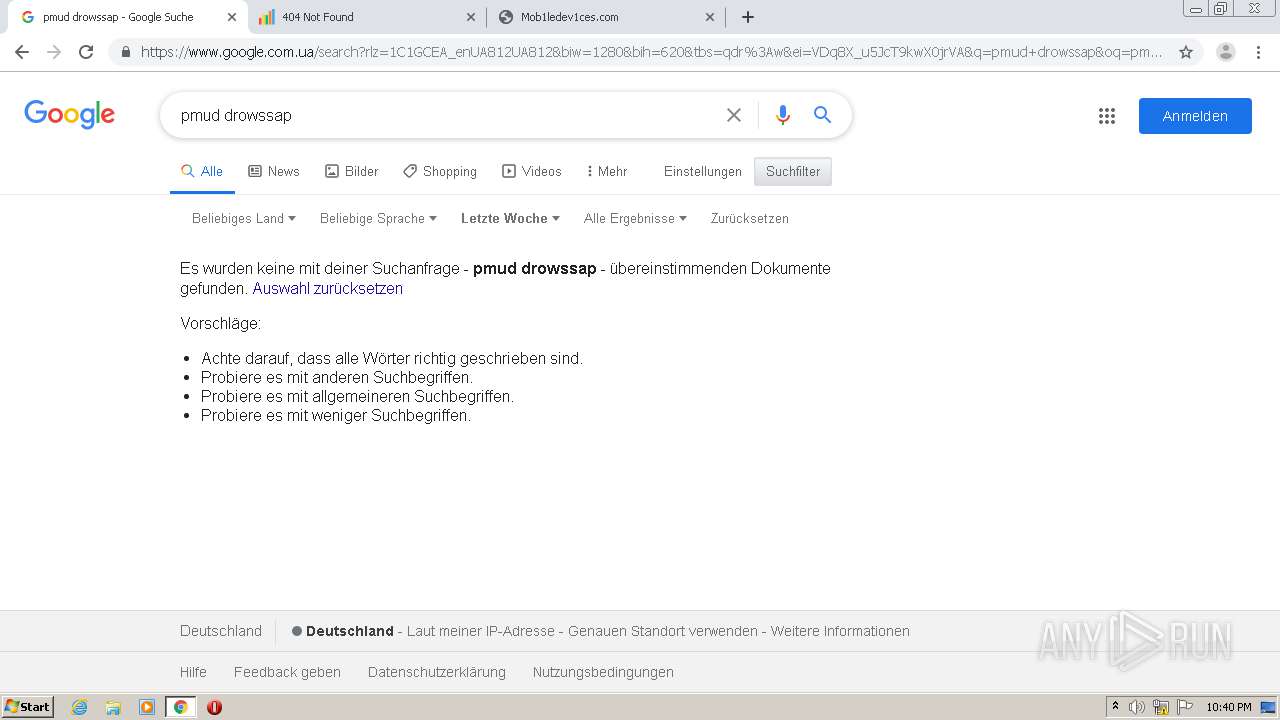
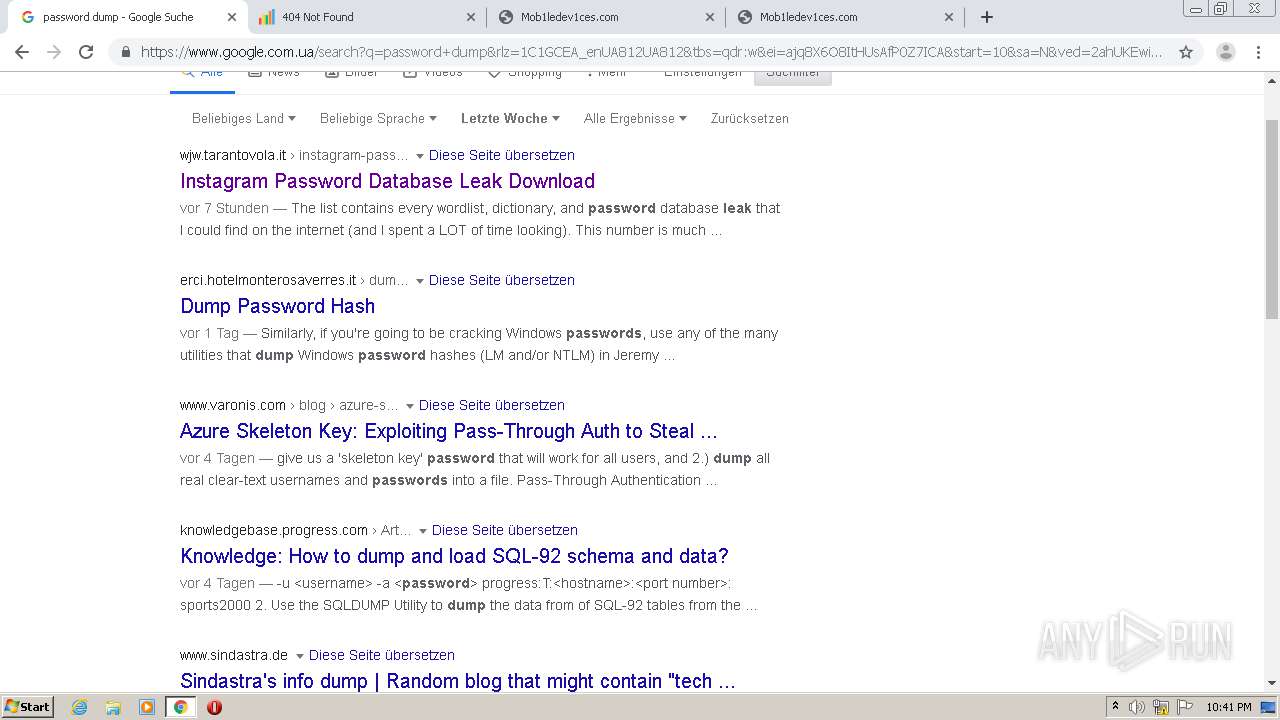
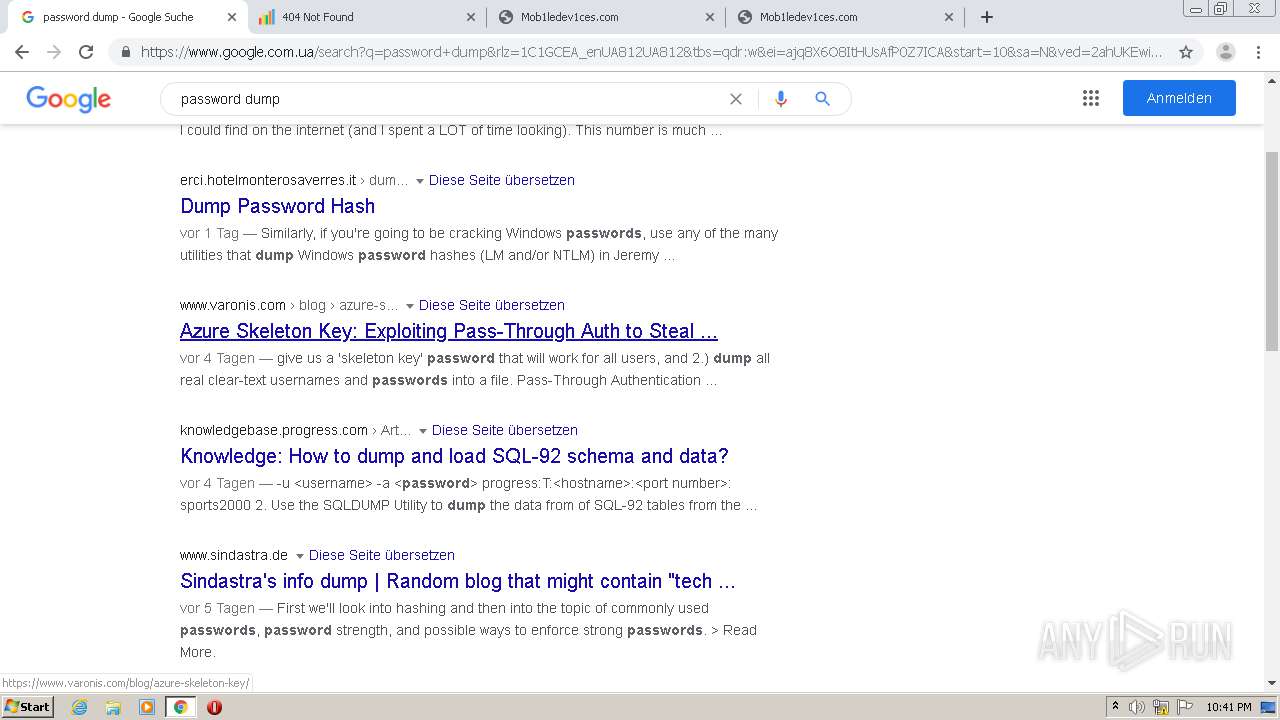
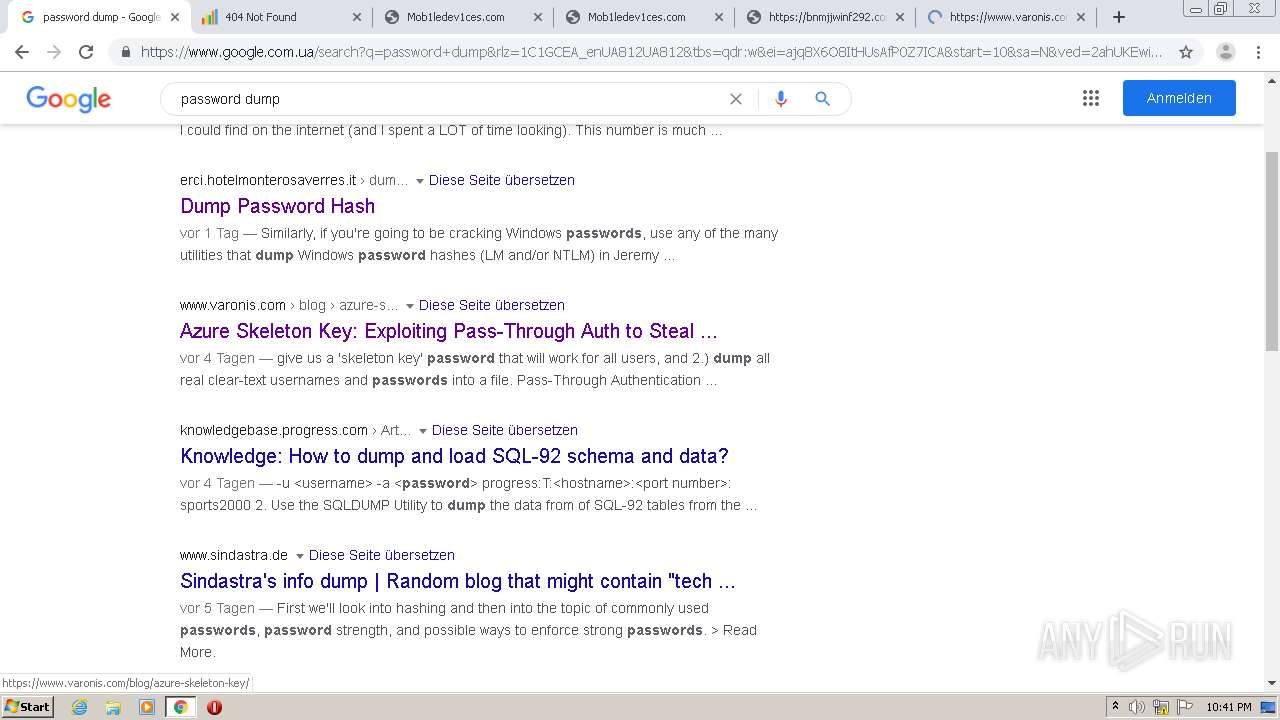
| URL: | http://lnu.corefarm.it/instagram-password-database-leak-download.html |
| Full analysis: | https://app.any.run/tasks/a639e95d-a388-4cf1-9e68-bd7efc6802cd |
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2020, 22:38:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6DC8F8F83D37238077CF36E30BE1CD60 |
| SHA1: | C2AD7475383773705C50FE9F1BDC61B0B9C48ECC |
| SHA256: | 70AB2B5391DE856B418607BF24D8EFA4EE81959795525DBDD19F832B78A4B844 |
| SSDEEP: | 3:N1KSLeGMz7sKeR1BVR0abKQ:CSLuXsKW1zbKQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2408)
- chrome.exe (PID: 4056)
Application launched itself
- chrome.exe (PID: 2408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8074286567202131604,9961485276069672845,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10453410293949024878 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8074286567202131604,9961485276069672845,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8184850157443631616 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8074286567202131604,9961485276069672845,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5859448751594185396 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8074286567202131604,9961485276069672845,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8177560862691262816 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2480 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8074286567202131604,9961485276069672845,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16527883189381292570 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3708 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,8074286567202131604,9961485276069672845,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3172929787490054156 --mojo-platform-channel-handle=3468 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2412 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8074286567202131604,9961485276069672845,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13424426275557810792 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2832 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8074286567202131604,9961485276069672845,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15239184568129816697 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8074286567202131604,9961485276069672845,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12901463357864568919 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
603
Read events
530
Write events
70
Delete events
3
Modification events
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2408-13250644726588250 |
Value: 259 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
131
Text files
138
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FBC39F7-968.pma | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\11544015-840b-492b-a8c8-c13d3f126beb.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF143f49.TMP | text | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF144209.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
140
DNS requests
94
Threats
4
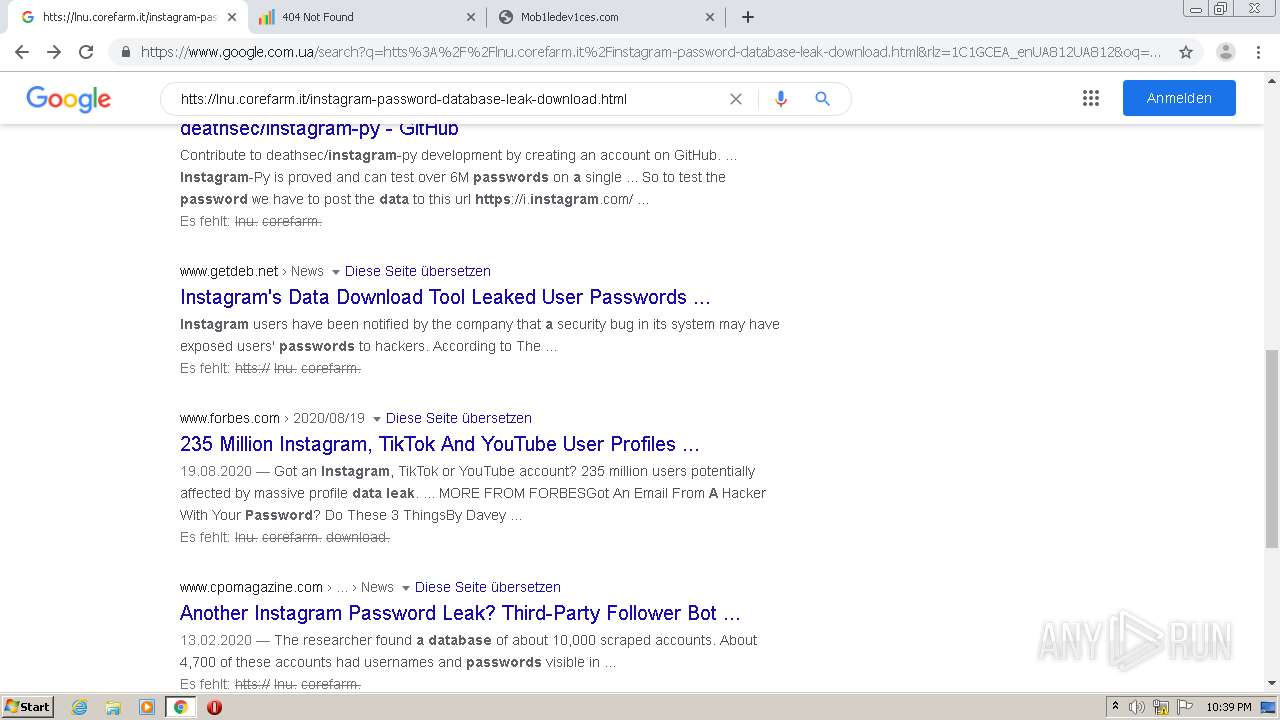
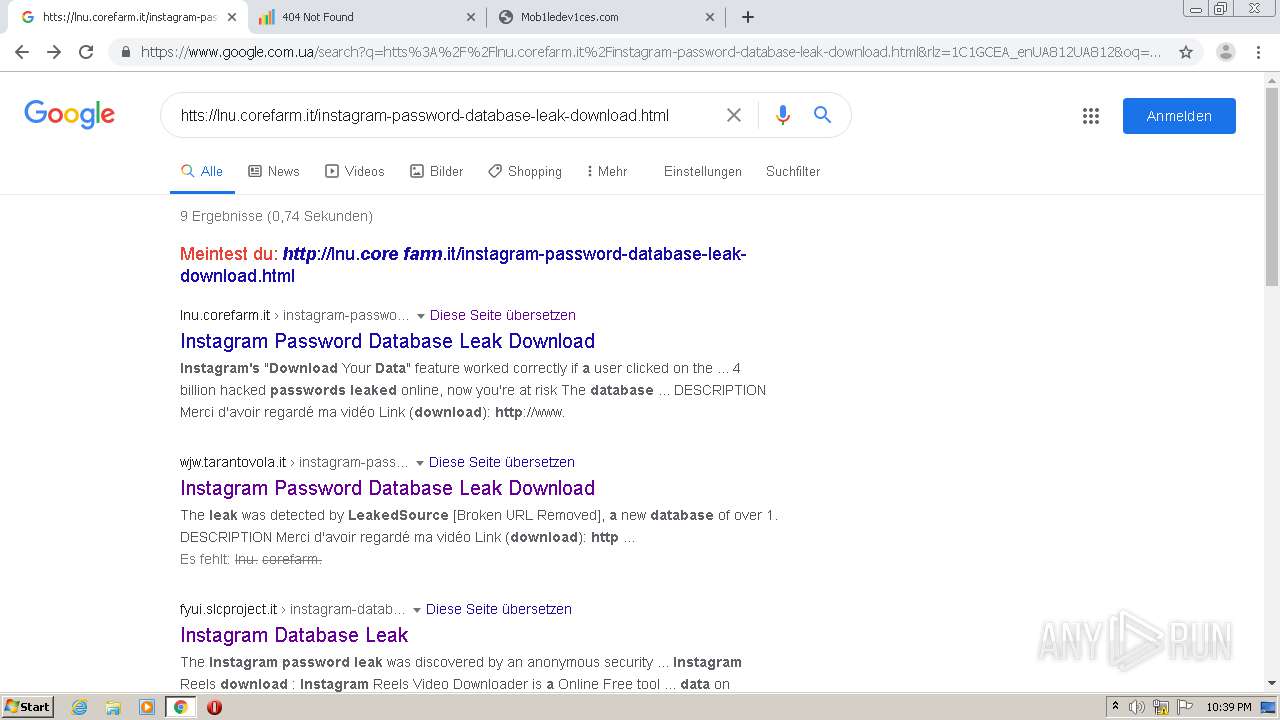
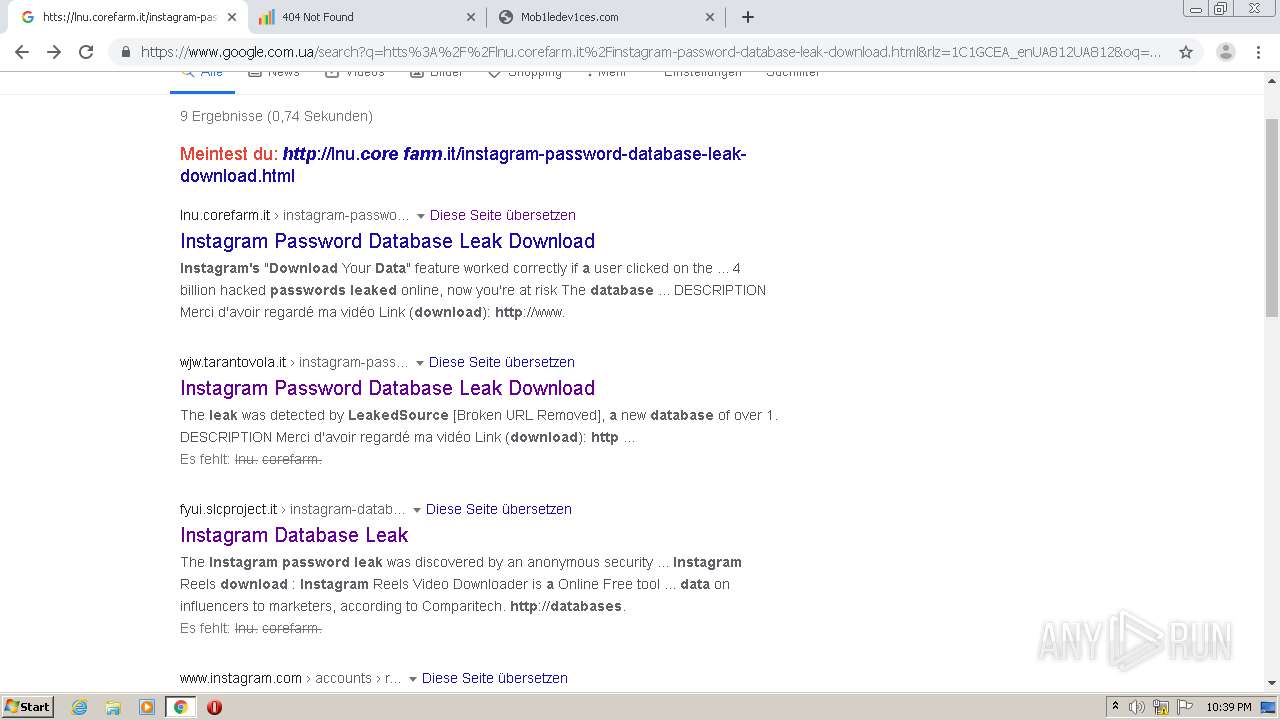
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
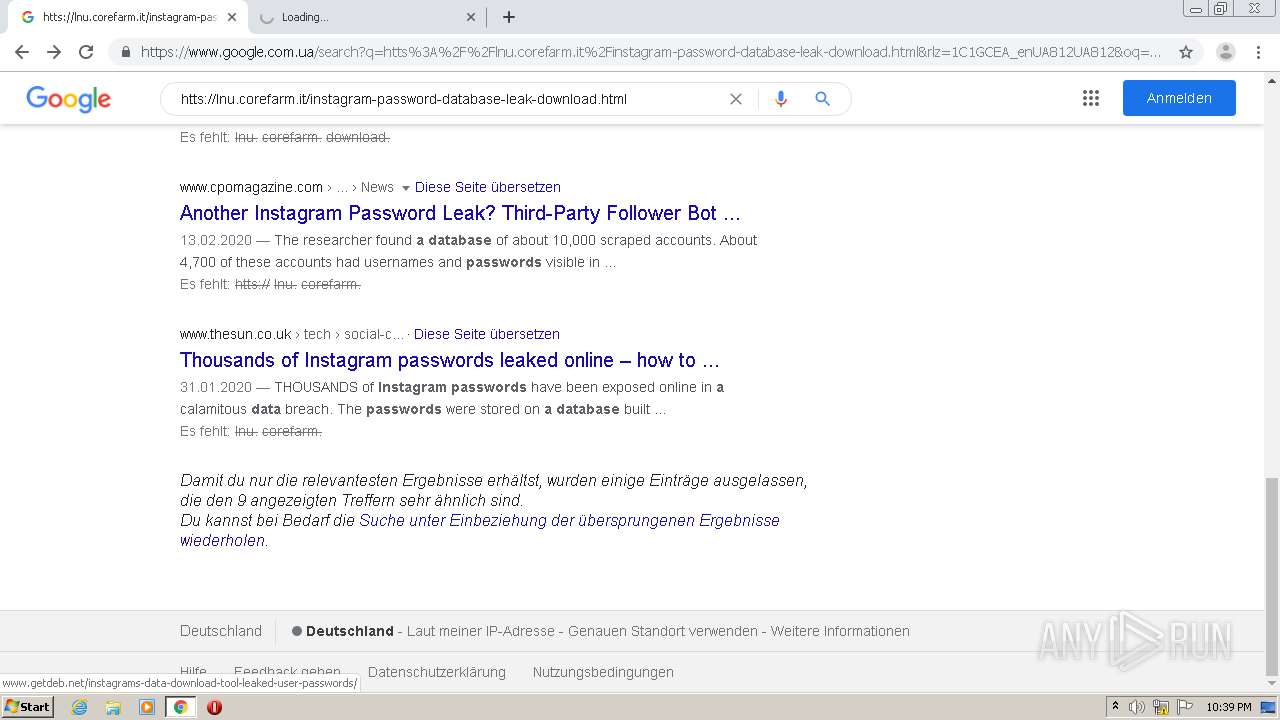
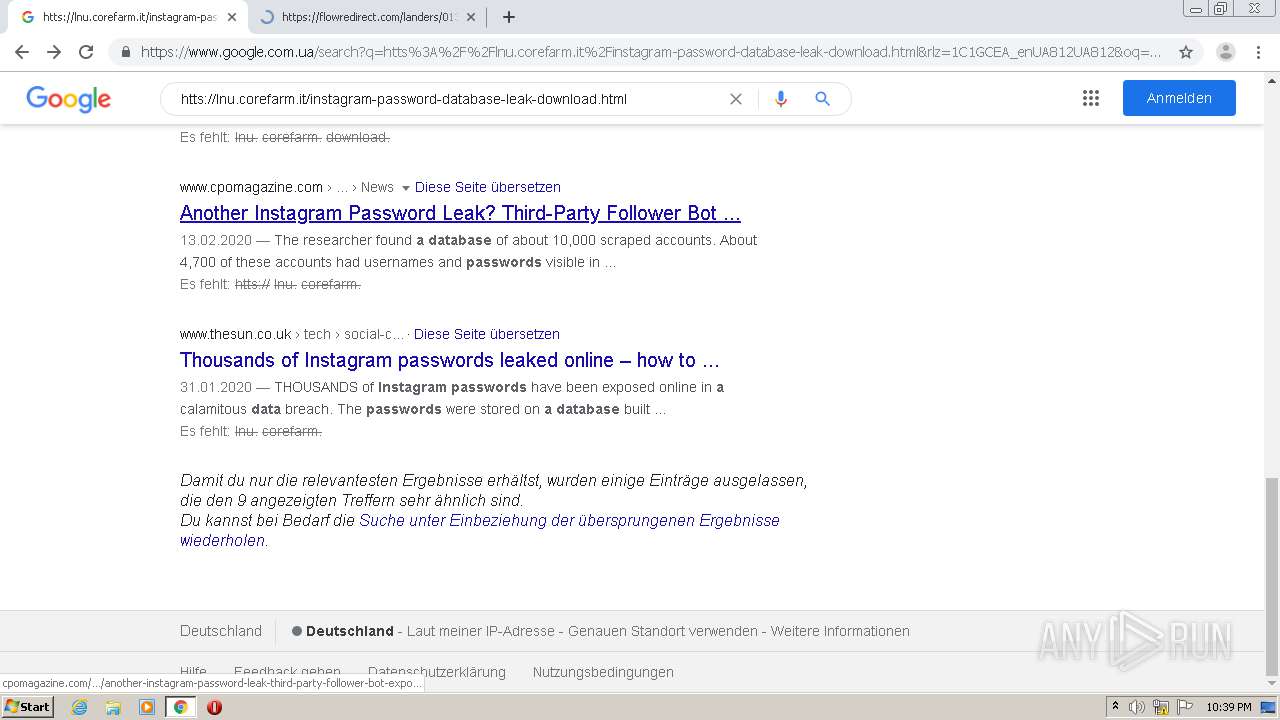
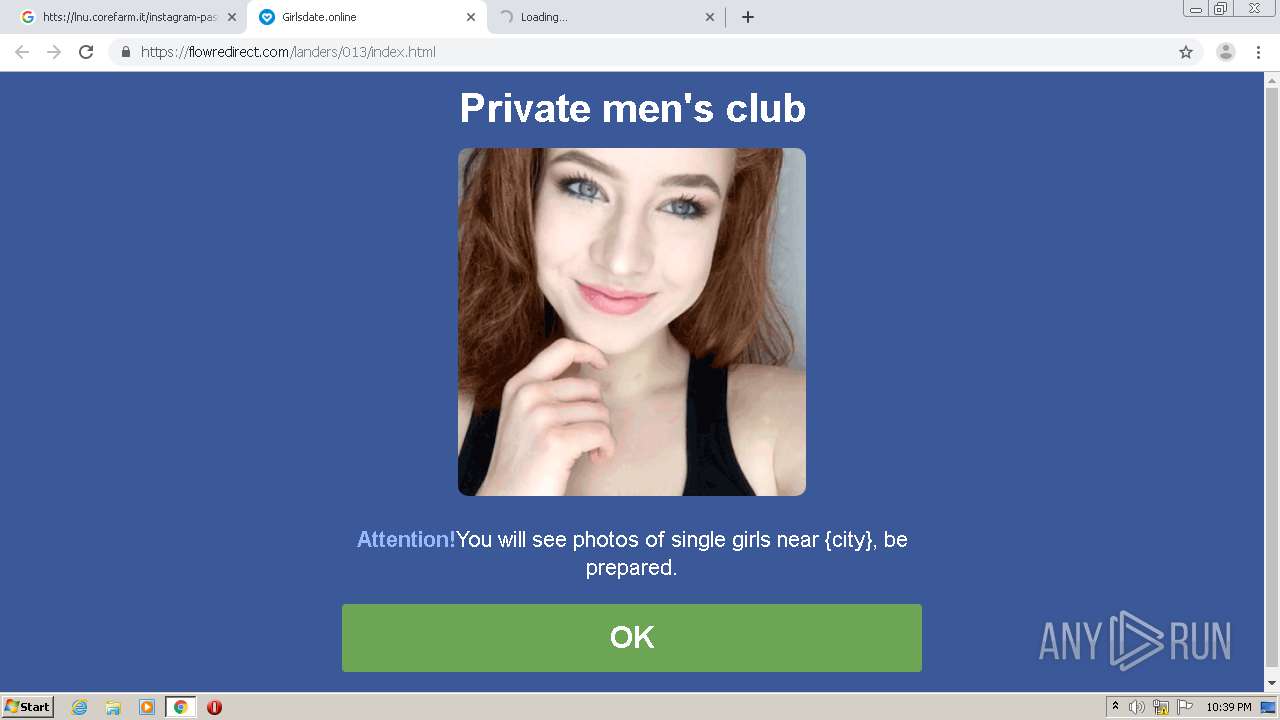
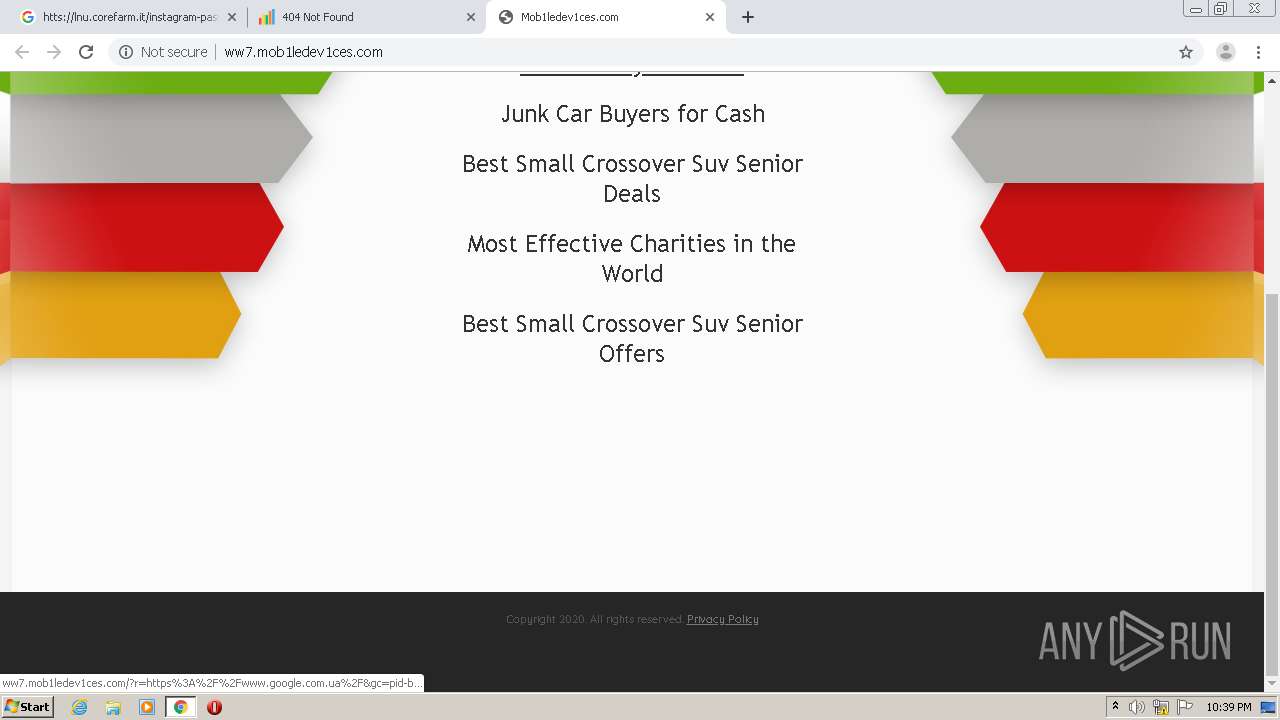
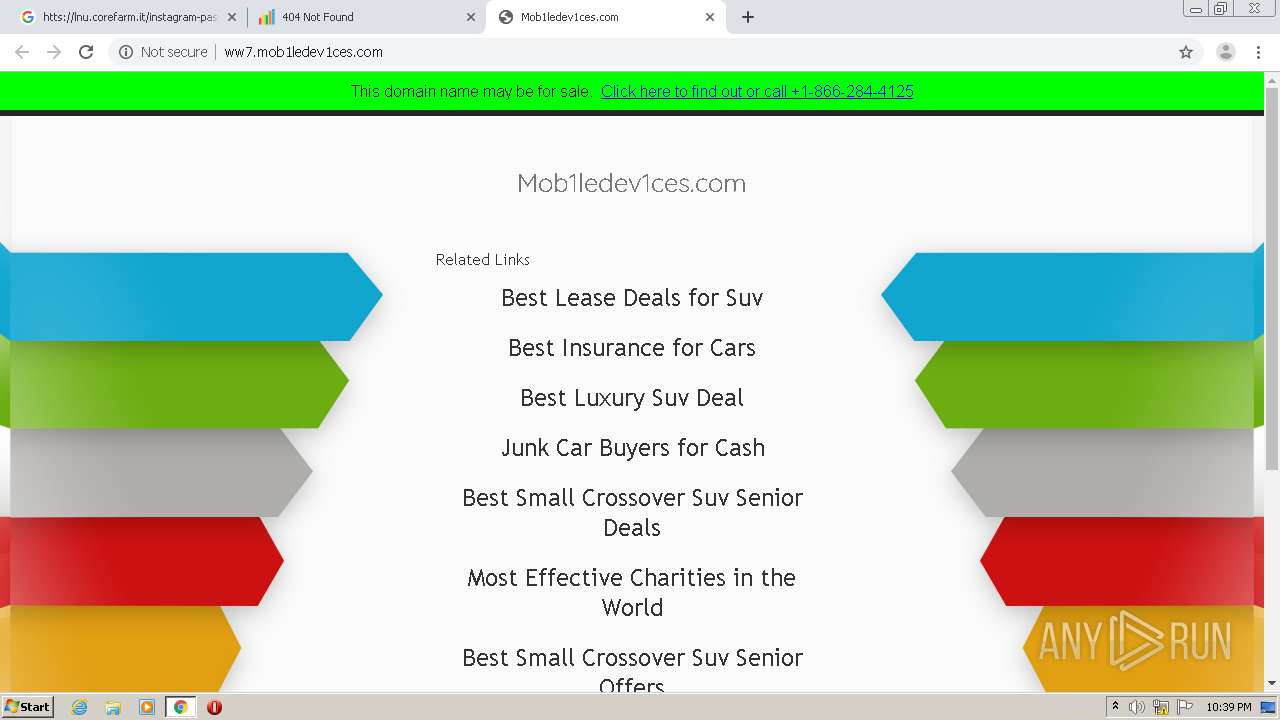
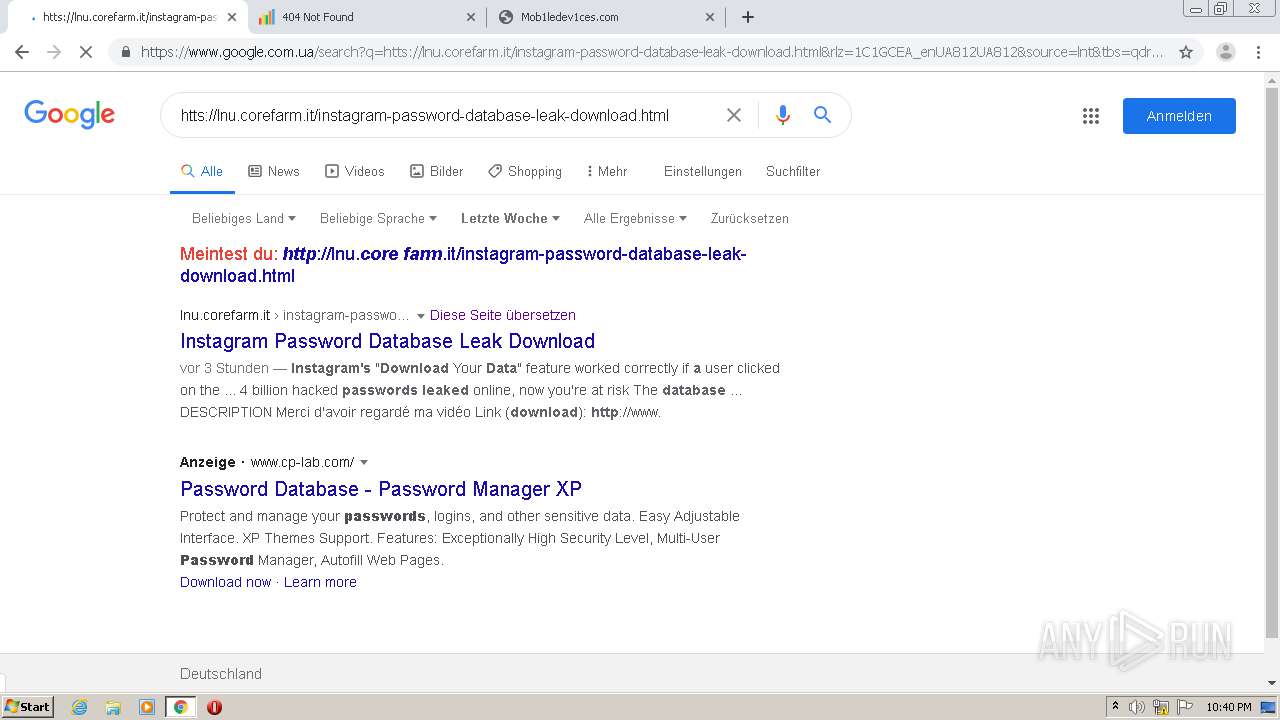
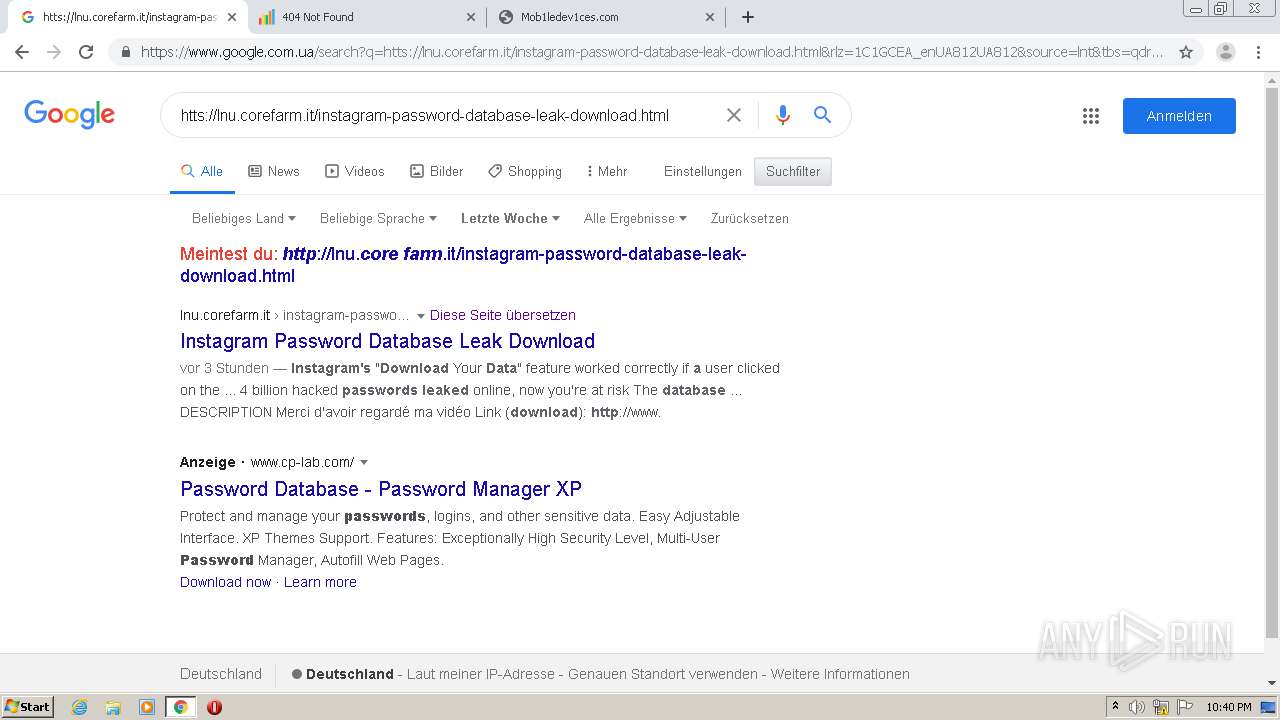
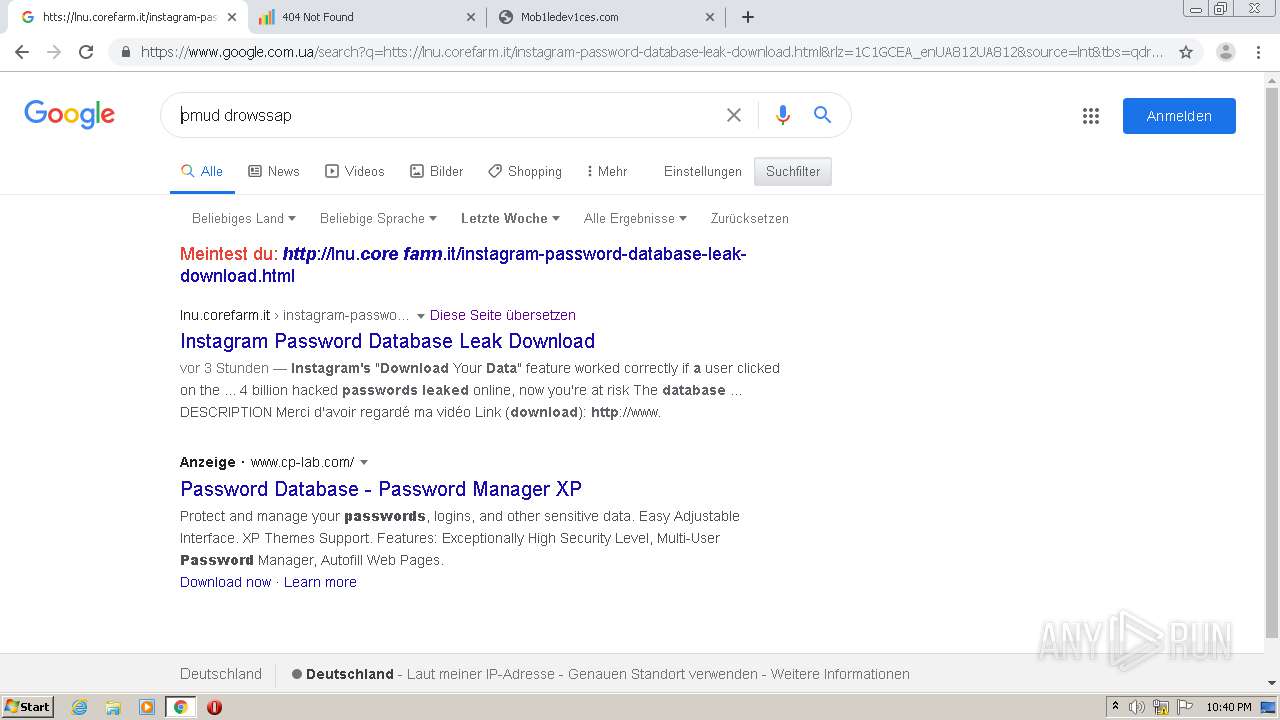
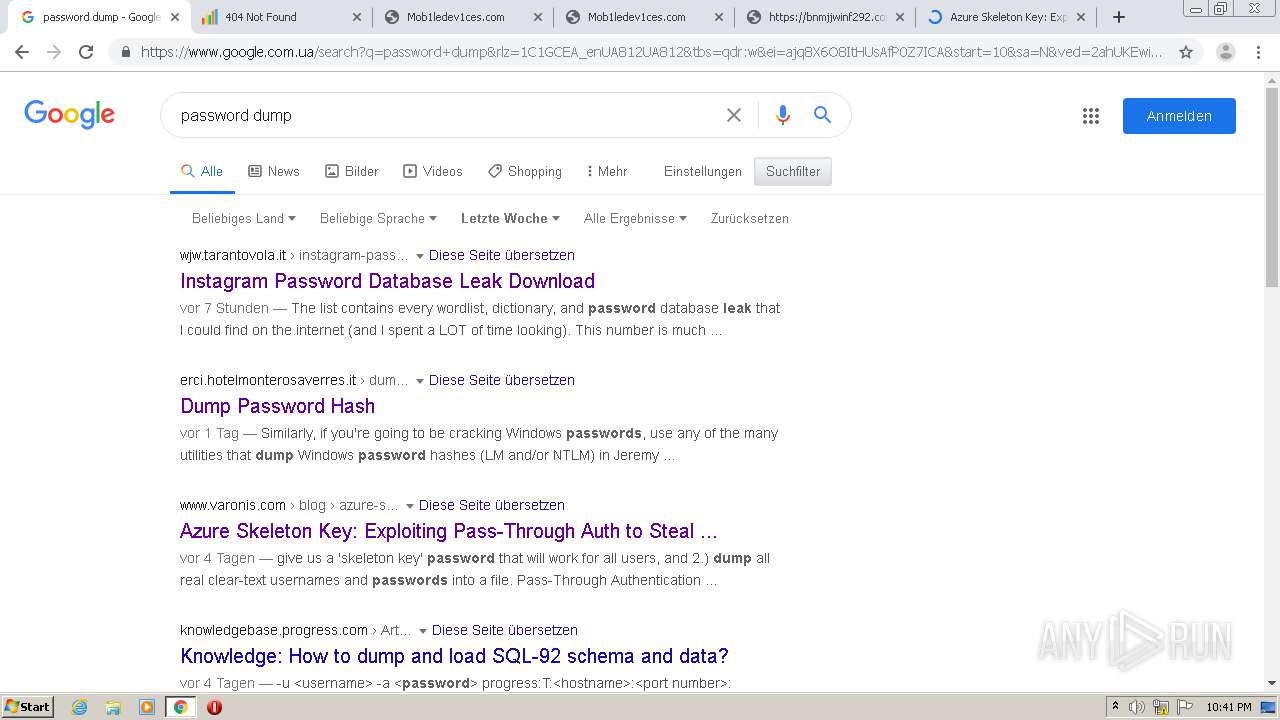
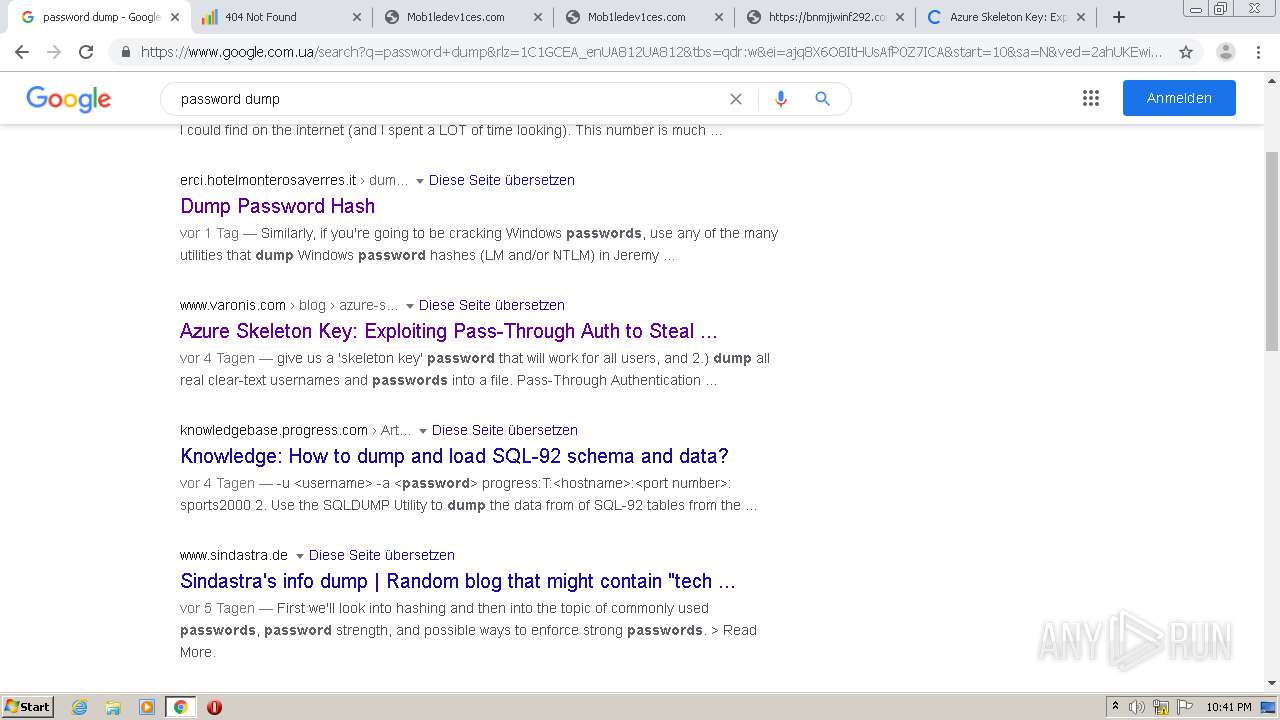
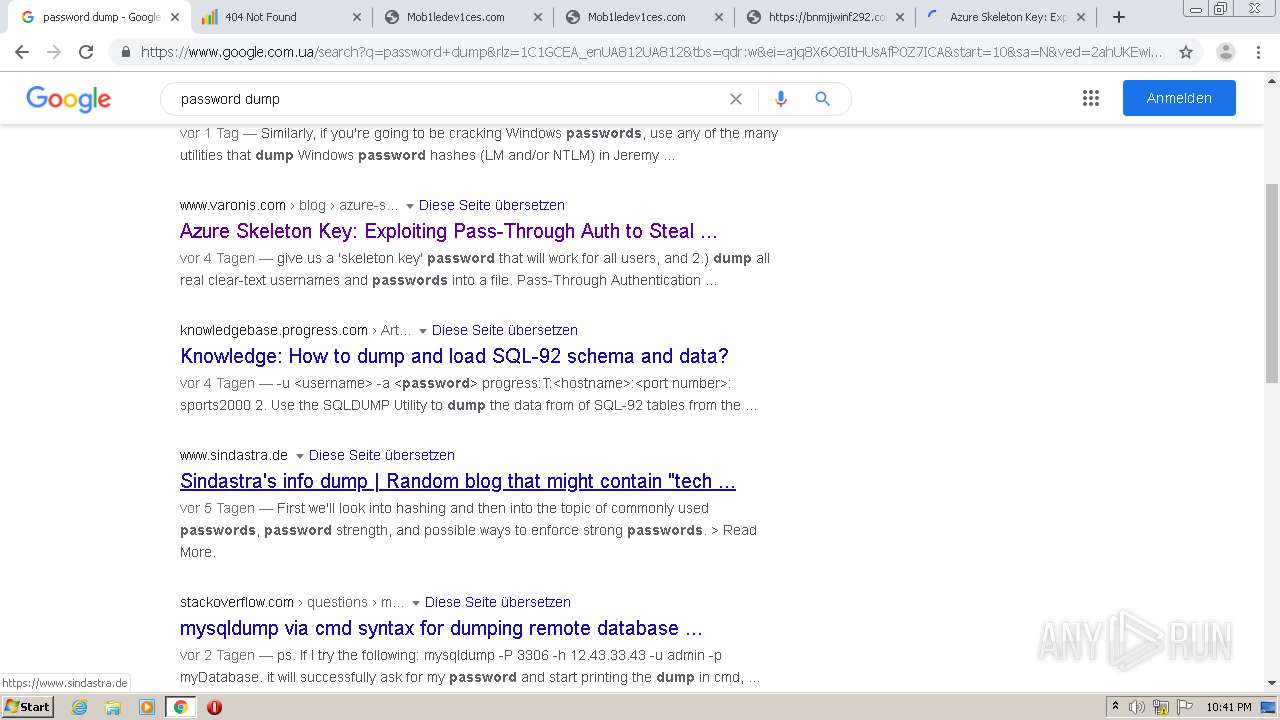
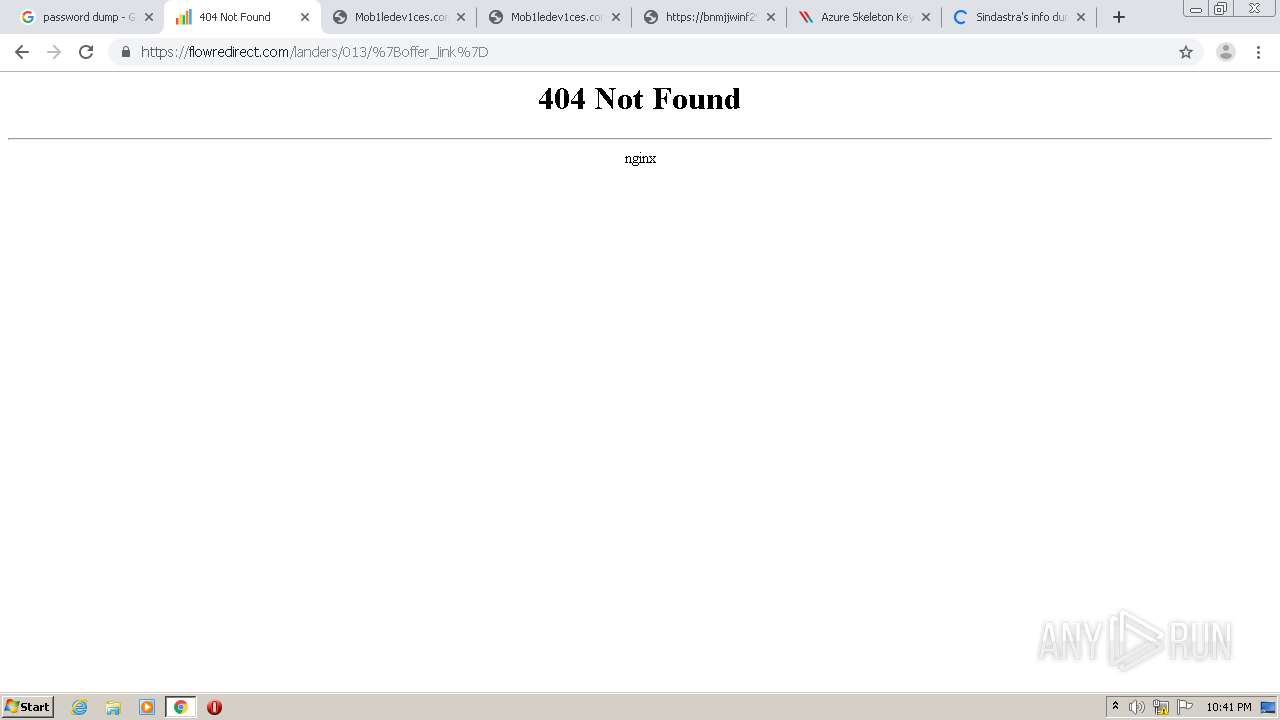
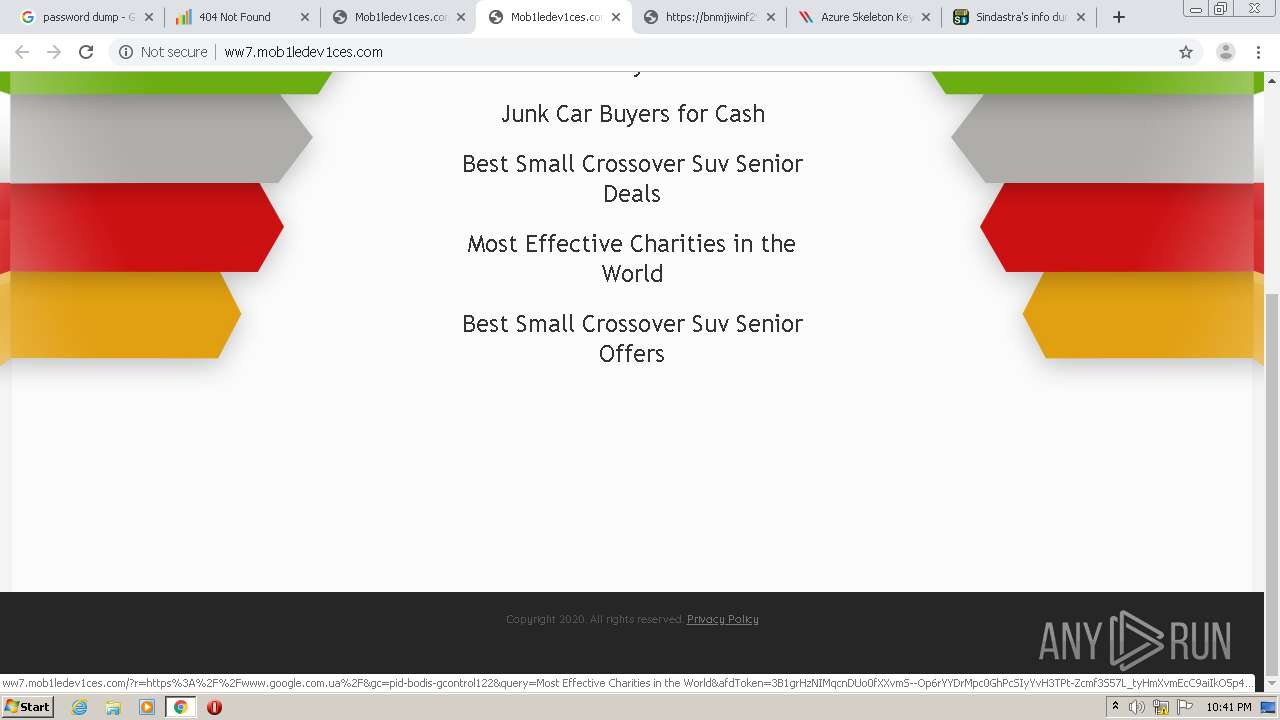
4056 | chrome.exe | GET | 302 | 149.202.65.142:80 | http://149.202.65.142/6SQ1p72g | FR | — | — | unknown |
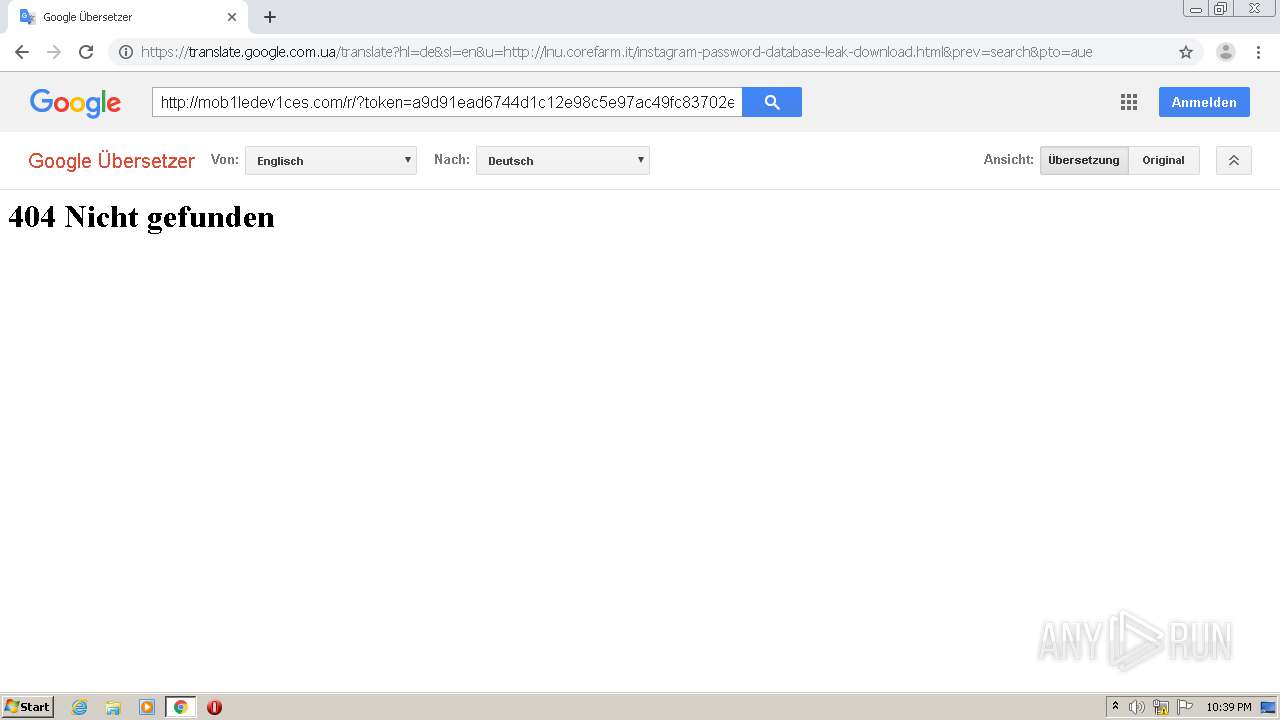
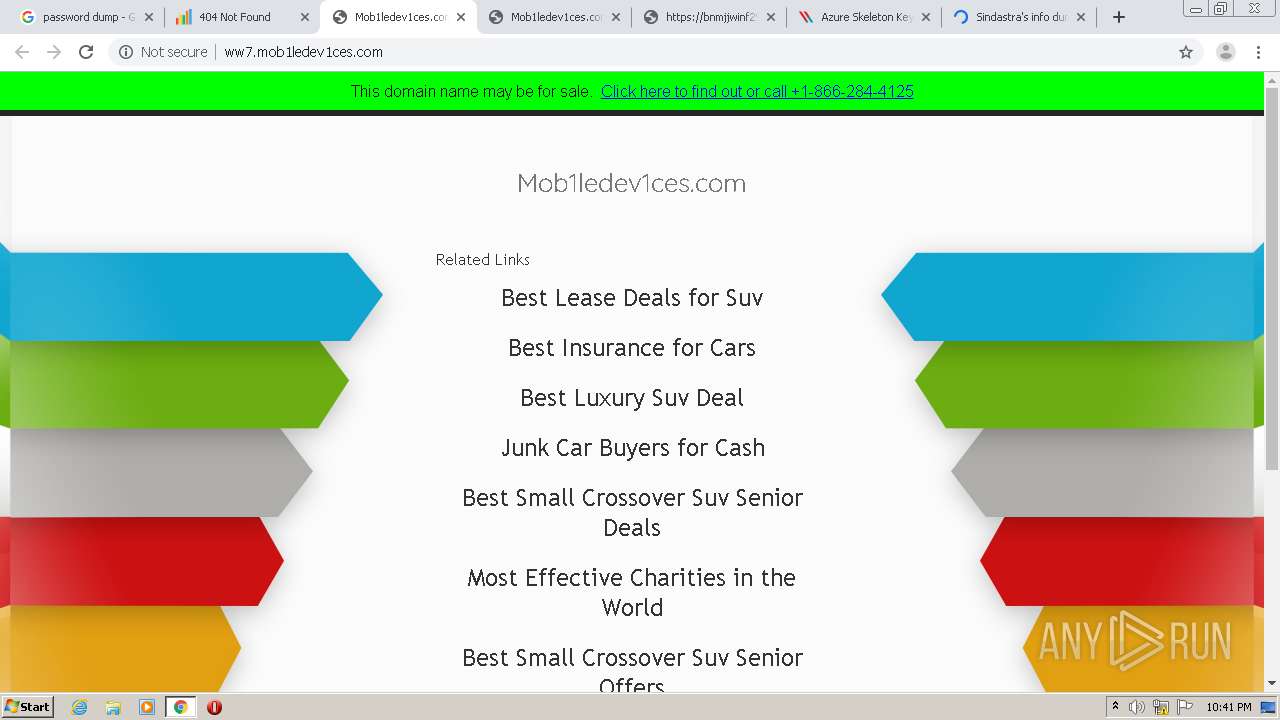
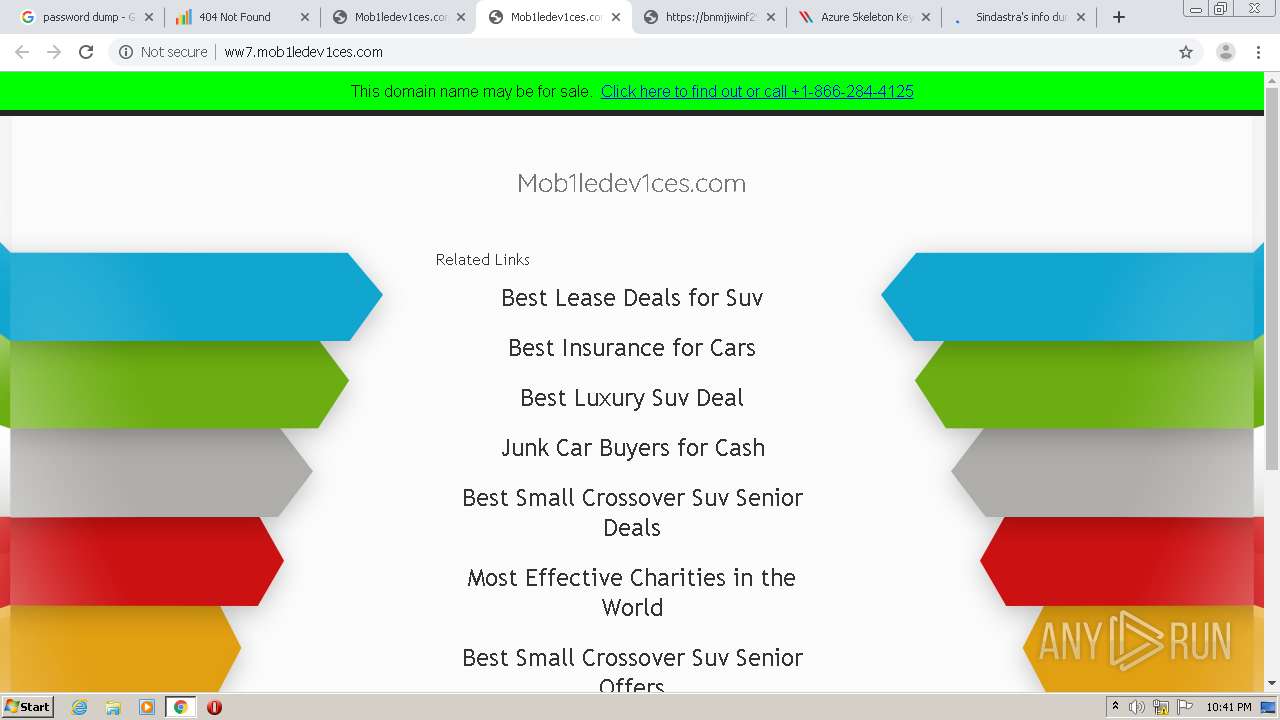
4056 | chrome.exe | GET | 302 | 72.52.178.23:80 | http://mob1ledev1ces.com/r/?token=a9d91ead6744d1c12e98c5e97ac49fc83702ec77&q=&keyword= | US | — | — | malicious |
4056 | chrome.exe | GET | 302 | 198.134.116.30:80 | http://click.expmediadirect.com/click?i=21WgtNO67Rs_0 | US | — | — | whitelisted |
4056 | chrome.exe | GET | 302 | 195.201.58.241:80 | http://195.201.58.241/Lj4RvC?sub_id_1=MixEU_All_k2_tb | RU | — | — | unknown |
4056 | chrome.exe | GET | 302 | 72.52.178.23:80 | http://mob1ledev1ces.com/r/?token=a9d91ead6744d1c12e98c5e97ac49fc83702ec77&q=&keyword= | US | — | — | malicious |
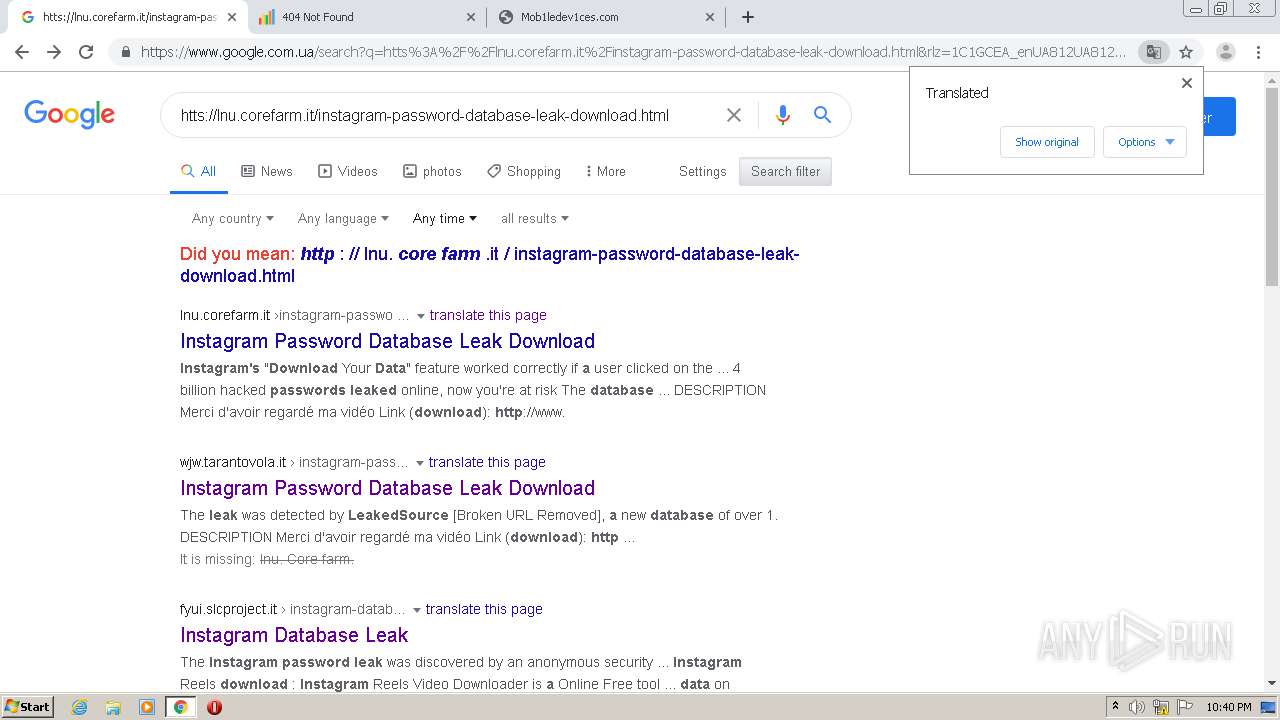
4056 | chrome.exe | GET | 204 | 172.217.7.206:80 | http://translate.google.com/gen204?nca=te_li&client=wt_lib&logld=vTE_20200506_00 | US | — | — | whitelisted |
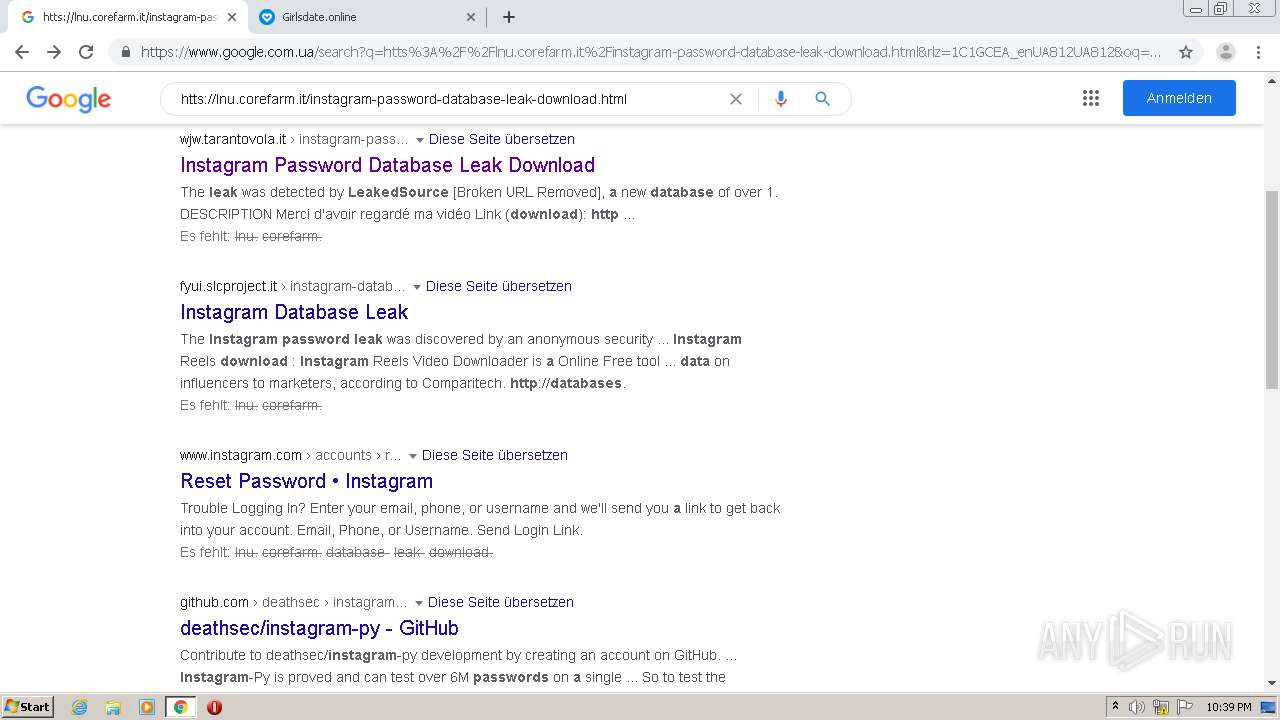
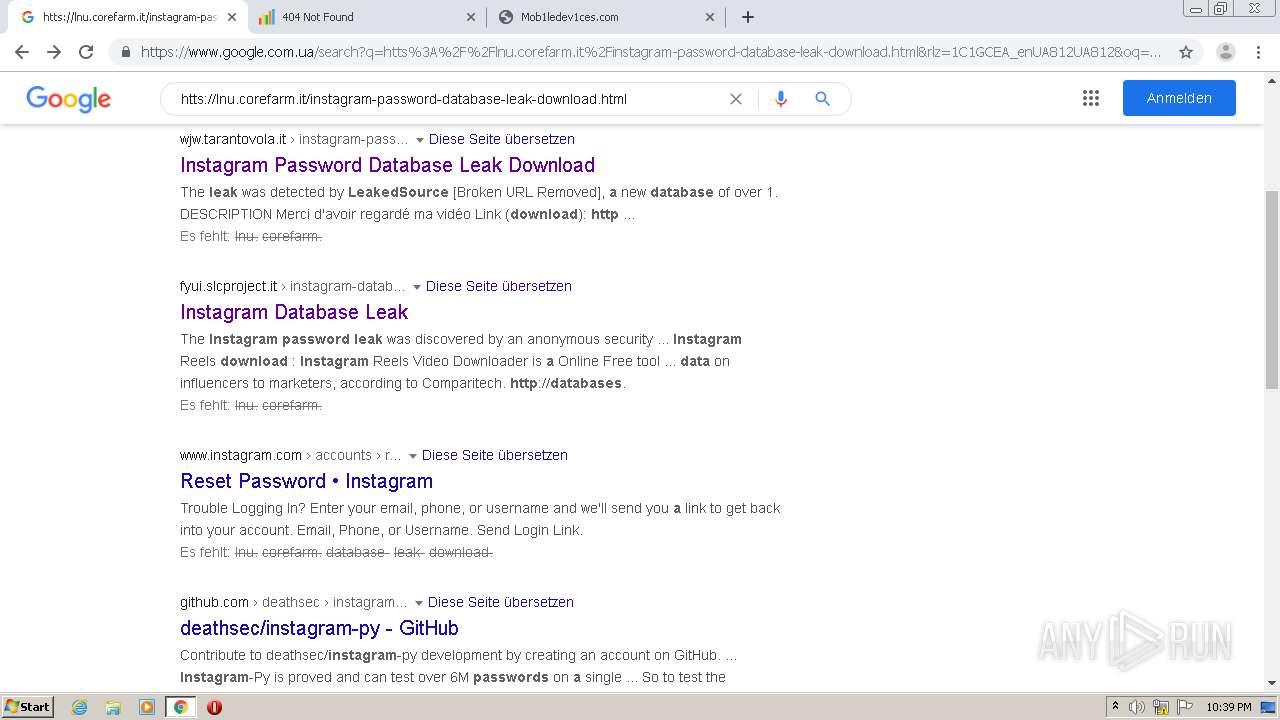
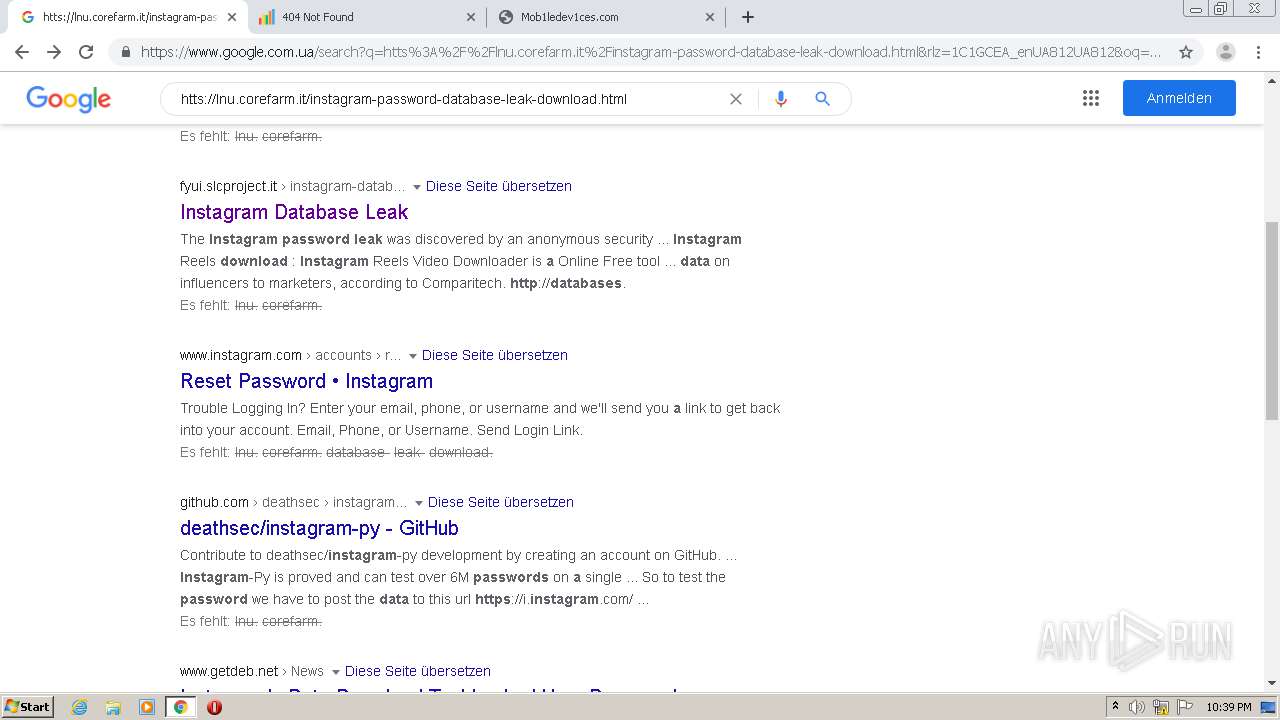
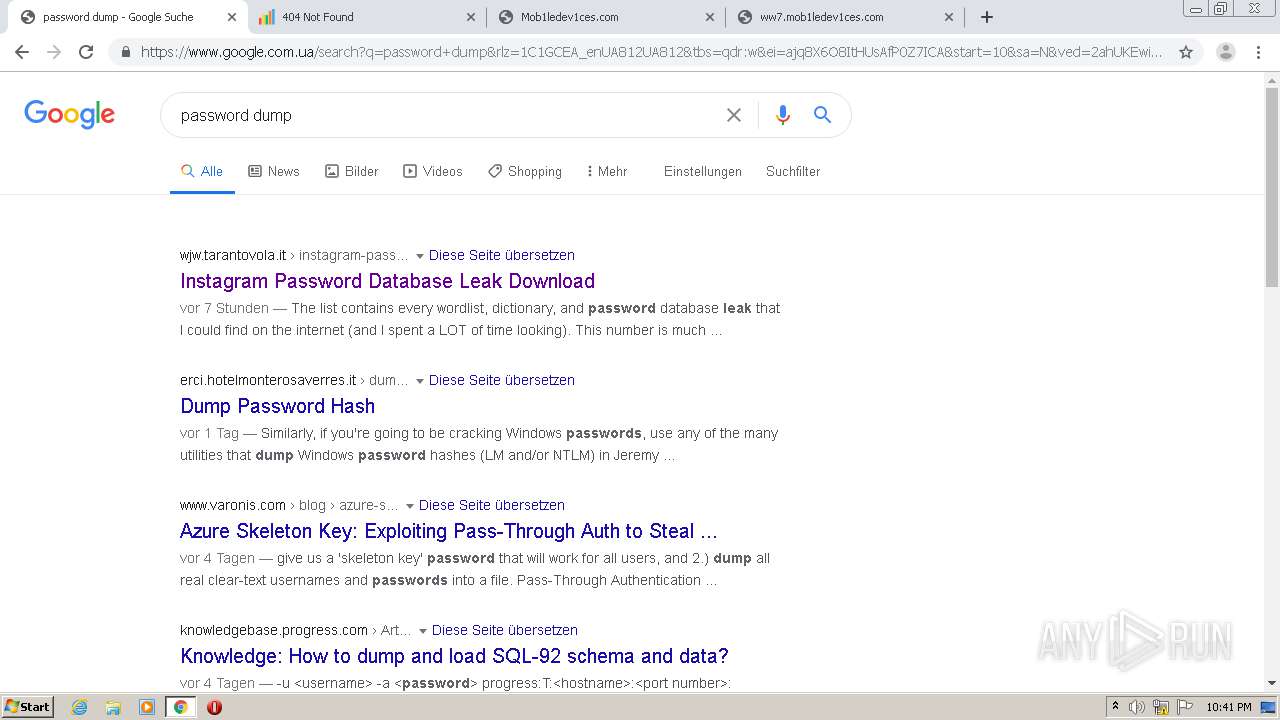
4056 | chrome.exe | GET | 302 | 104.28.28.247:80 | http://fyui.slcproject.it/instagram-database-leak.html | US | — | — | suspicious |
4056 | chrome.exe | GET | 302 | 176.114.9.149:80 | http://adservd.com/offer?sid=MixEU_All_k2&keys=instagram+database+leak&lan=en&redir=http%3A%2F%2F195.201.58.241%2FLj4RvC%3Fsub_id_1%3DMixEU_All_k2_tb | UA | — | — | suspicious |
4056 | chrome.exe | GET | 302 | 149.202.65.142:80 | http://149.202.65.142/6SQ1p72g | FR | — | — | unknown |
4056 | chrome.exe | GET | 302 | 54.225.132.253:80 | http://mnason-hec.com/zcvisitor/c1bfa739-2ddc-11eb-bb71-0af8ef2da367/6cc2f0b0-49b3-11ea-8c7f-0a71705c5345?campaignid=292dc1e0-2af9-11eb-8e59-126456bfc3df | US | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.67.136.221:80 | lnu.corefarm.it | — | US | unknown |
4056 | chrome.exe | 172.67.136.221:80 | lnu.corefarm.it | — | US | unknown |
4056 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
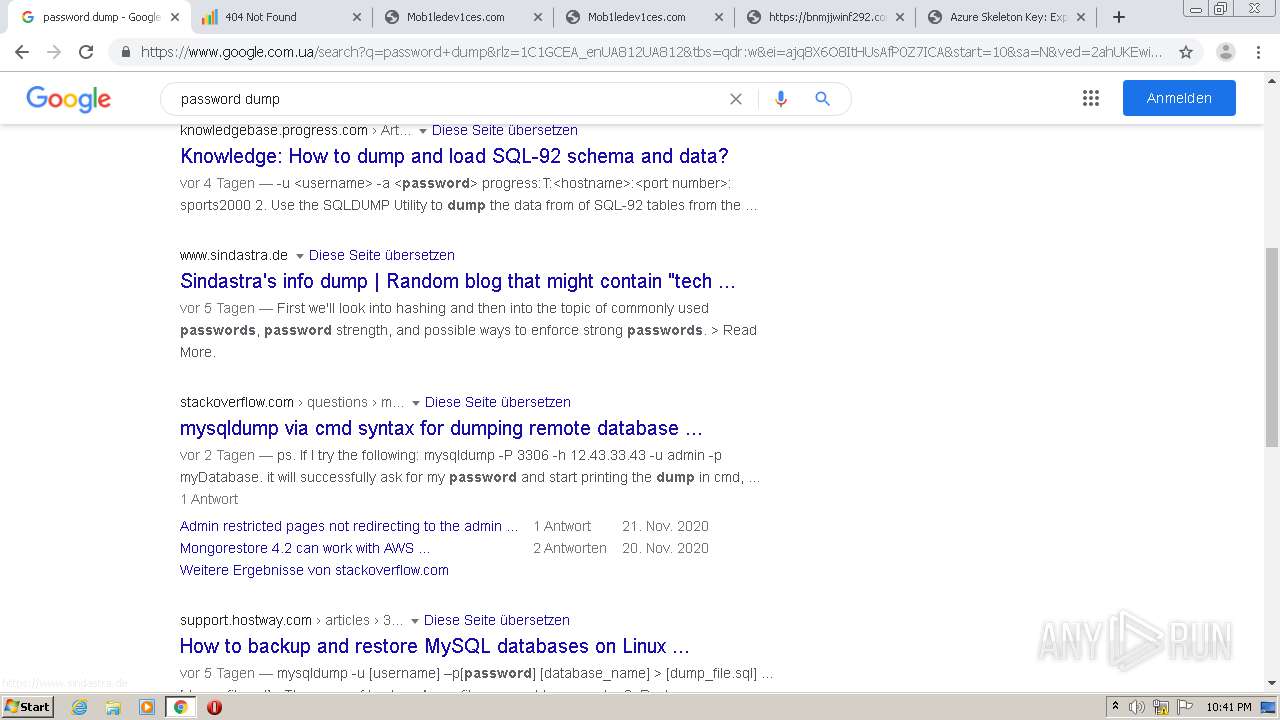
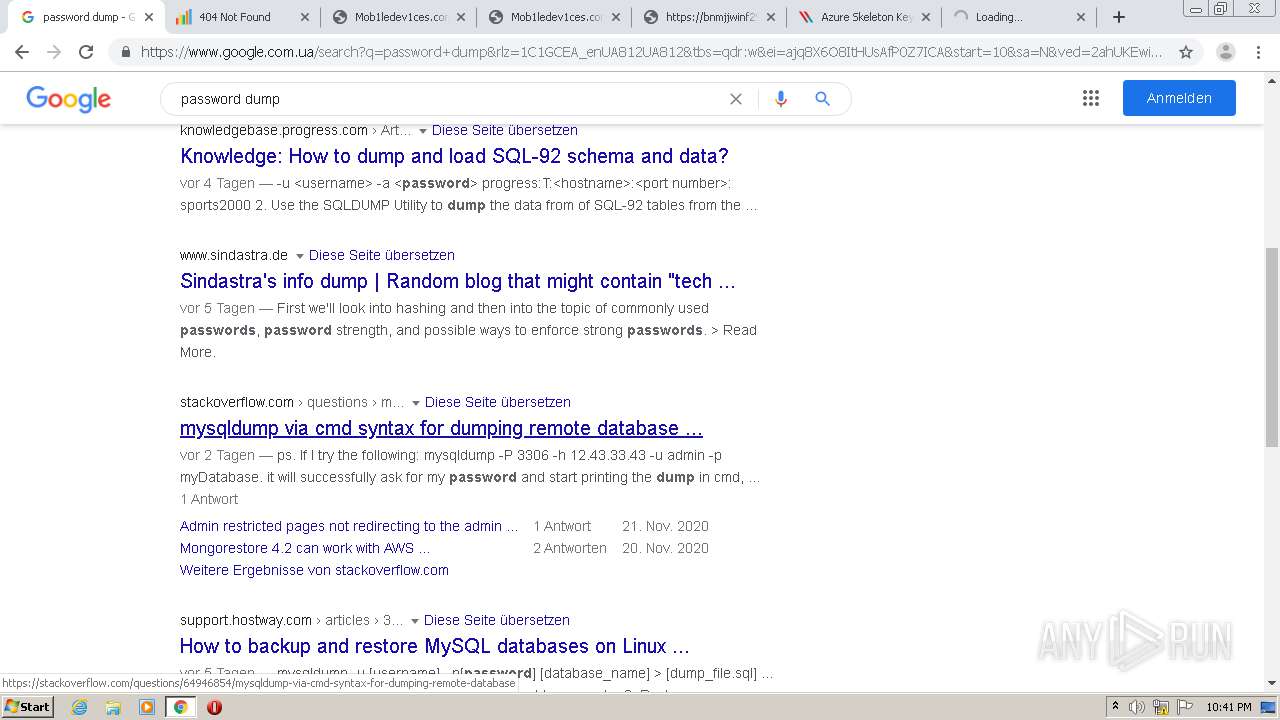
4056 | chrome.exe | 216.58.205.227:443 | www.google.com.ua | Google Inc. | US | whitelisted |
4056 | chrome.exe | 172.217.22.14:443 | consent.google.com | Google Inc. | US | whitelisted |
4056 | chrome.exe | 104.27.175.12:80 | lnu.corefarm.it | Cloudflare Inc | US | unknown |
4056 | chrome.exe | 216.58.212.174:443 | consent.google.com.ua | Google Inc. | US | whitelisted |
4056 | chrome.exe | 216.58.207.66:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
— | — | 172.217.21.195:443 | translate.google.com.ua | Google Inc. | US | whitelisted |
4056 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lnu.corefarm.it |
| unknown |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
consent.google.com |
| shared |
consent.google.com.ua |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
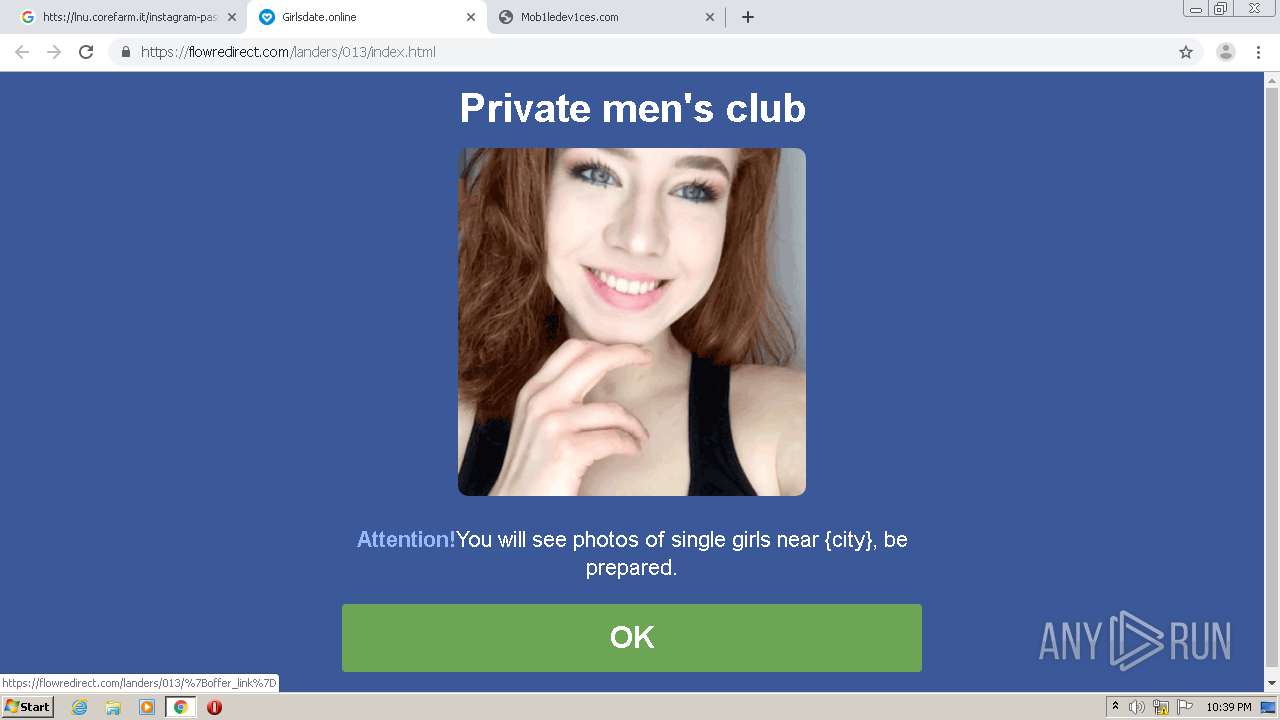
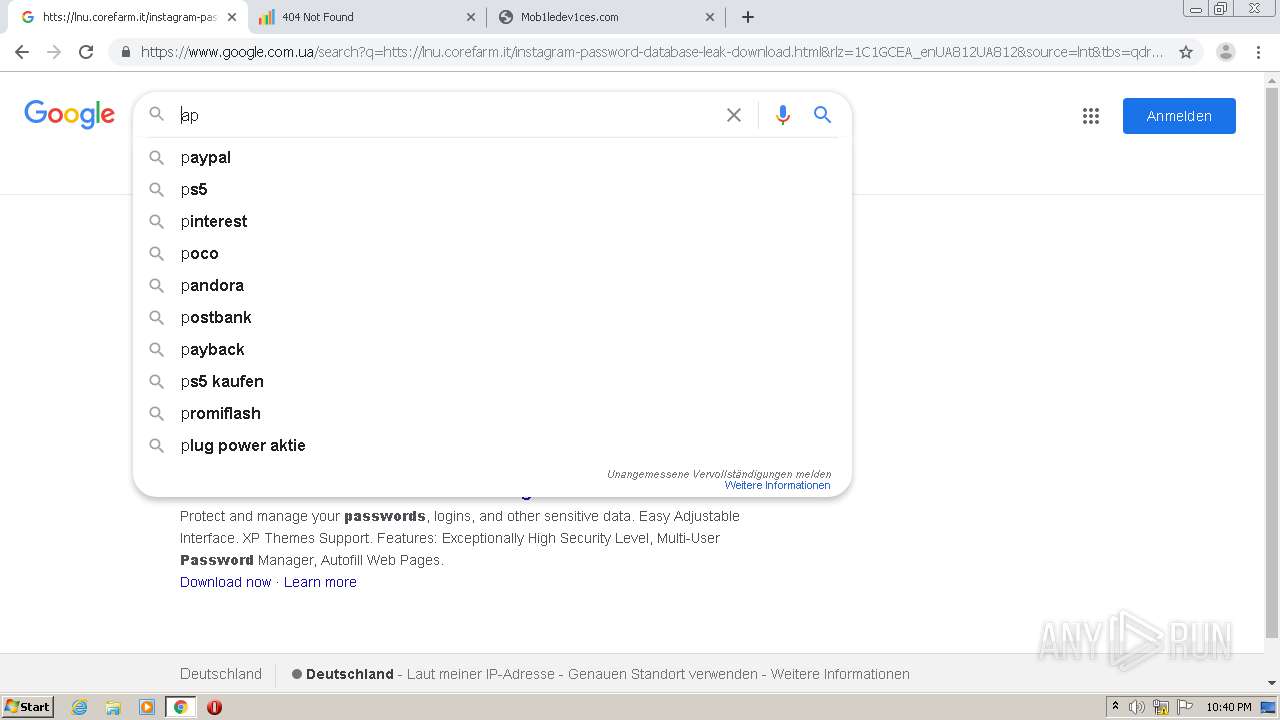
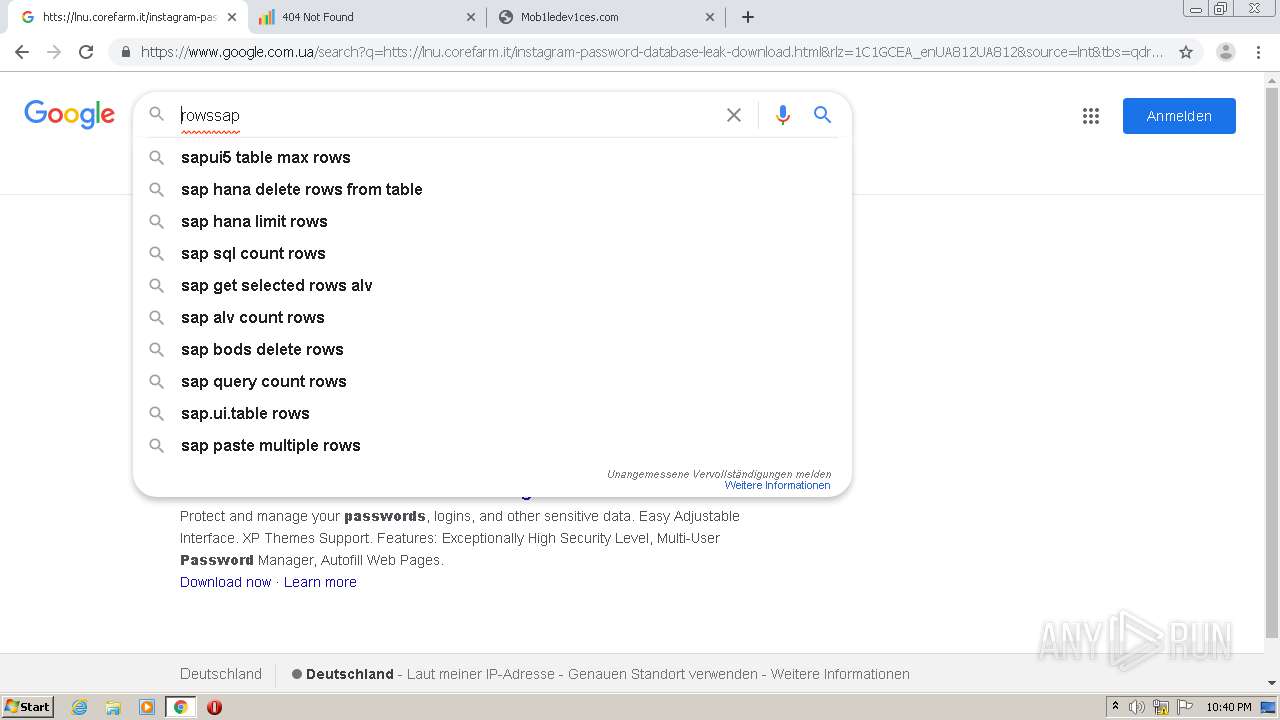
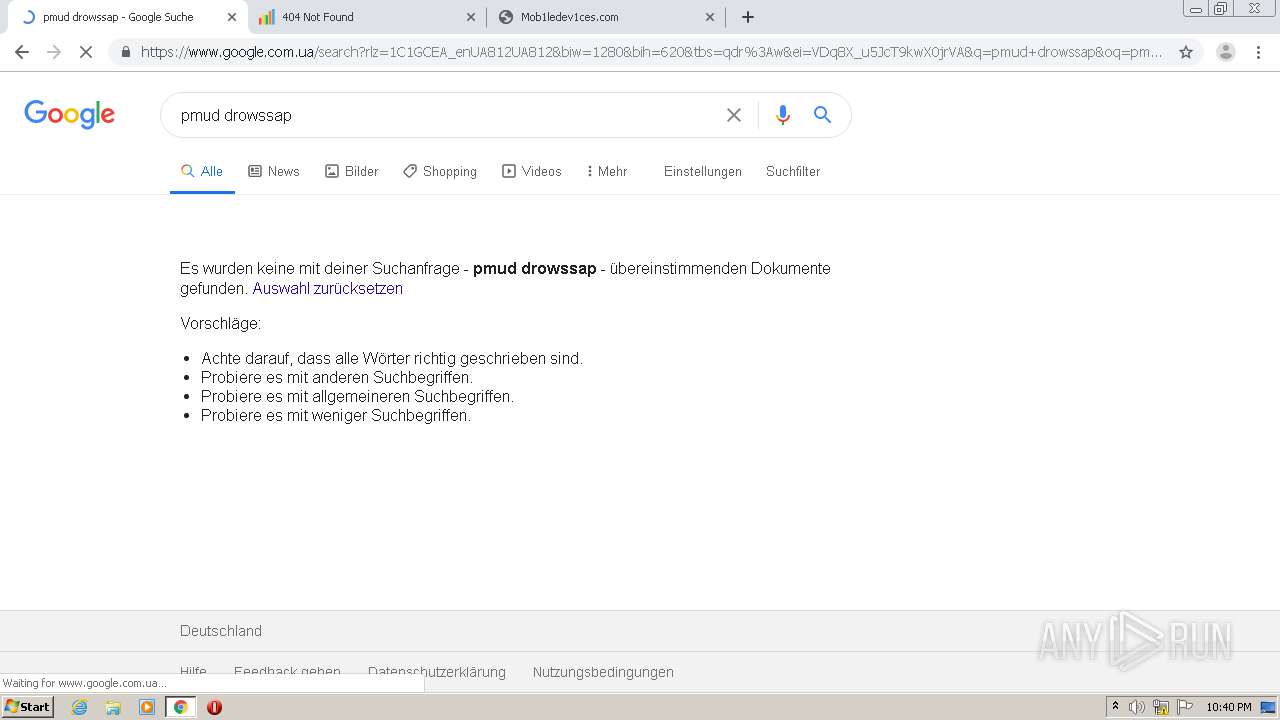
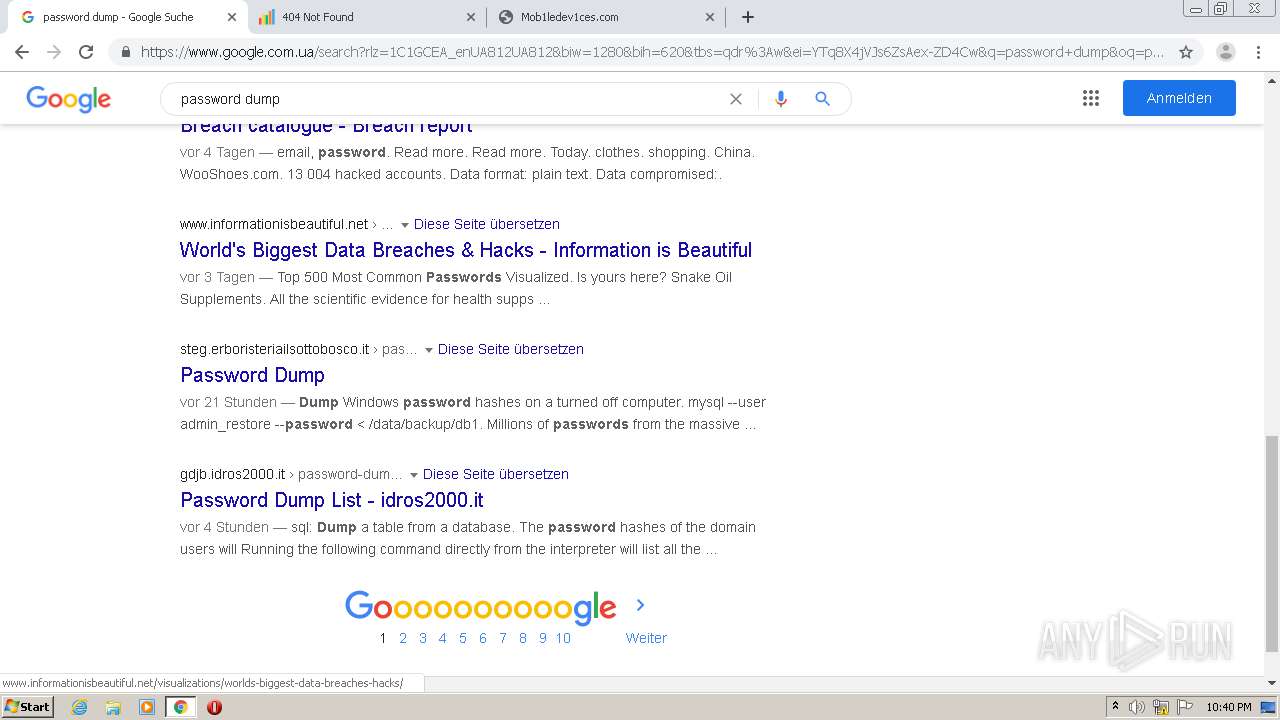
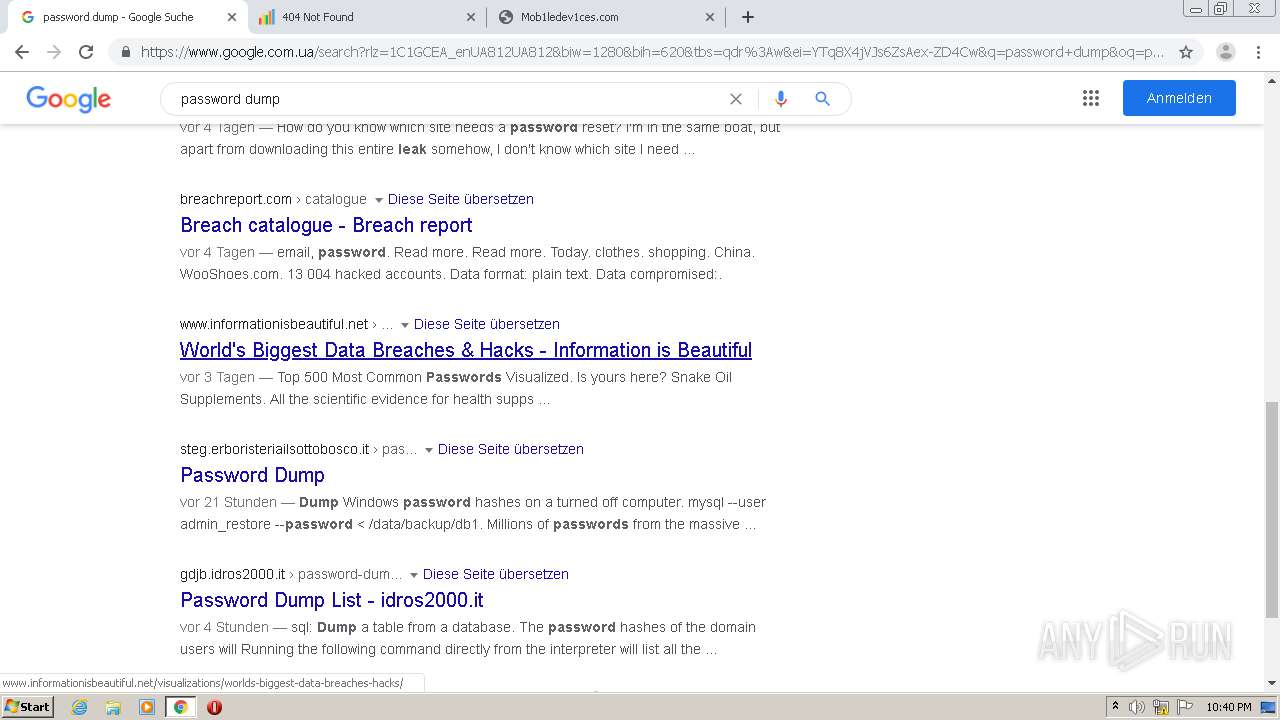
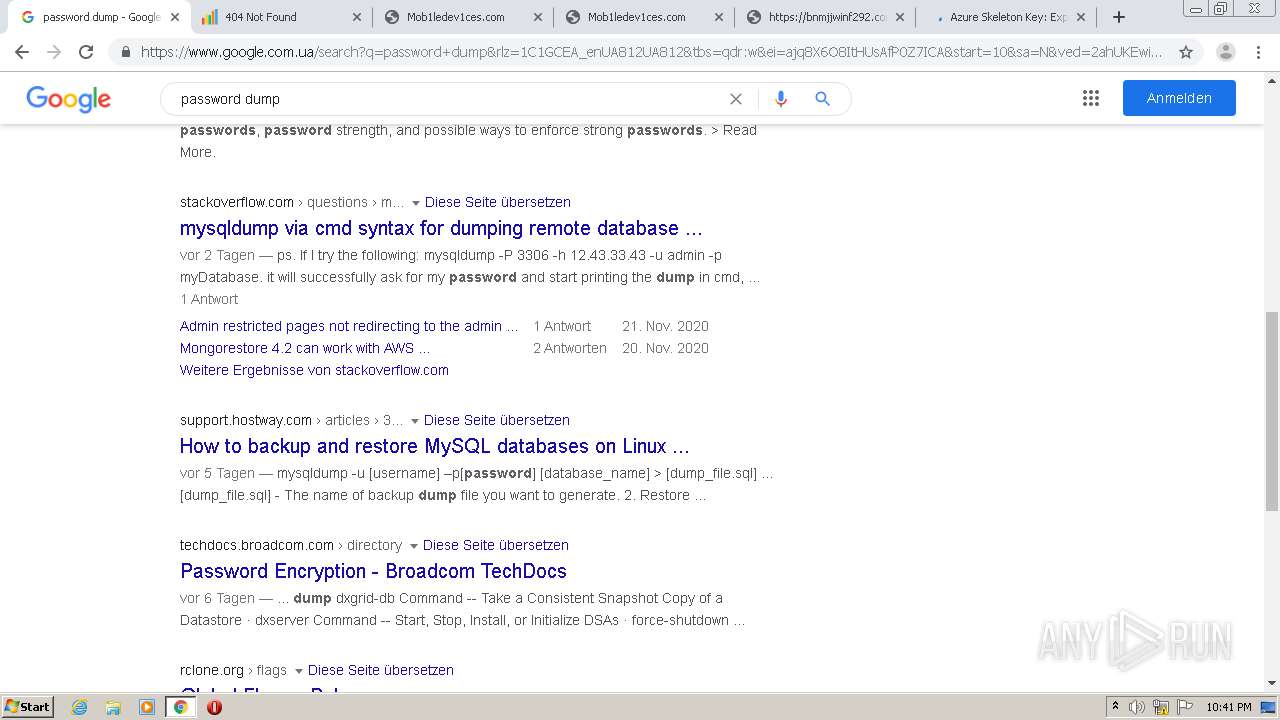
4056 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
4056 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
4056 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |