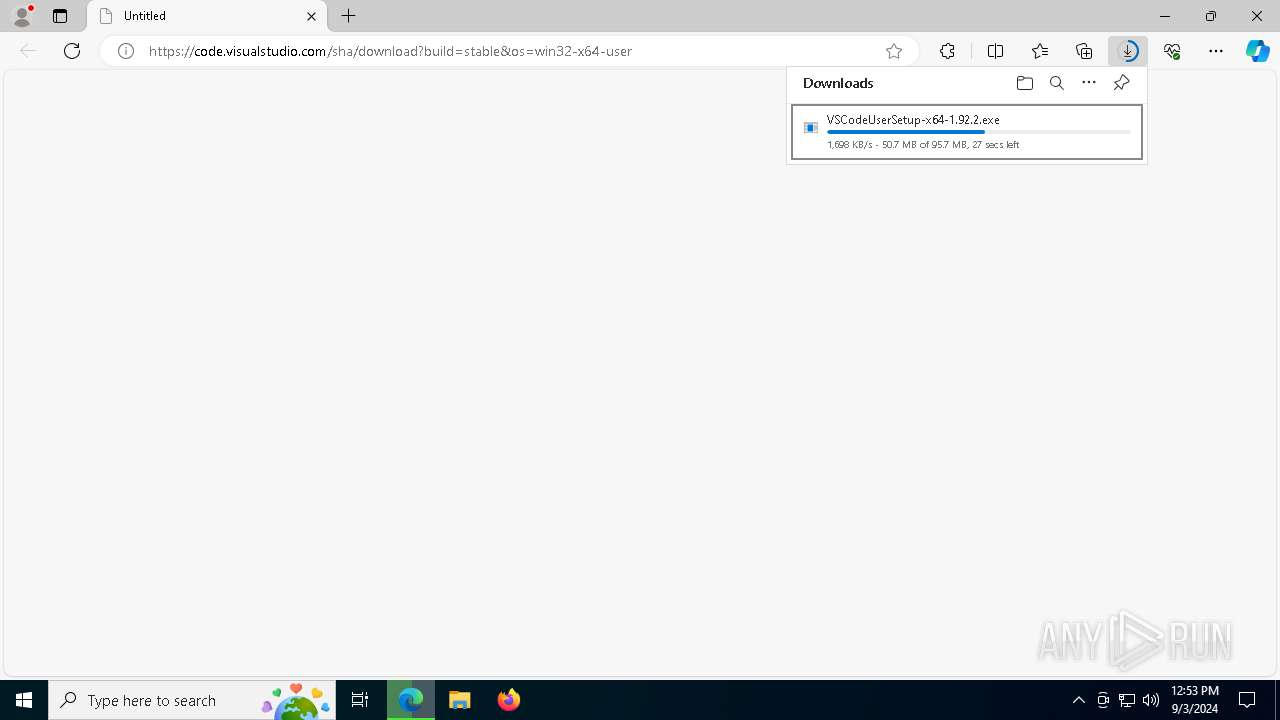
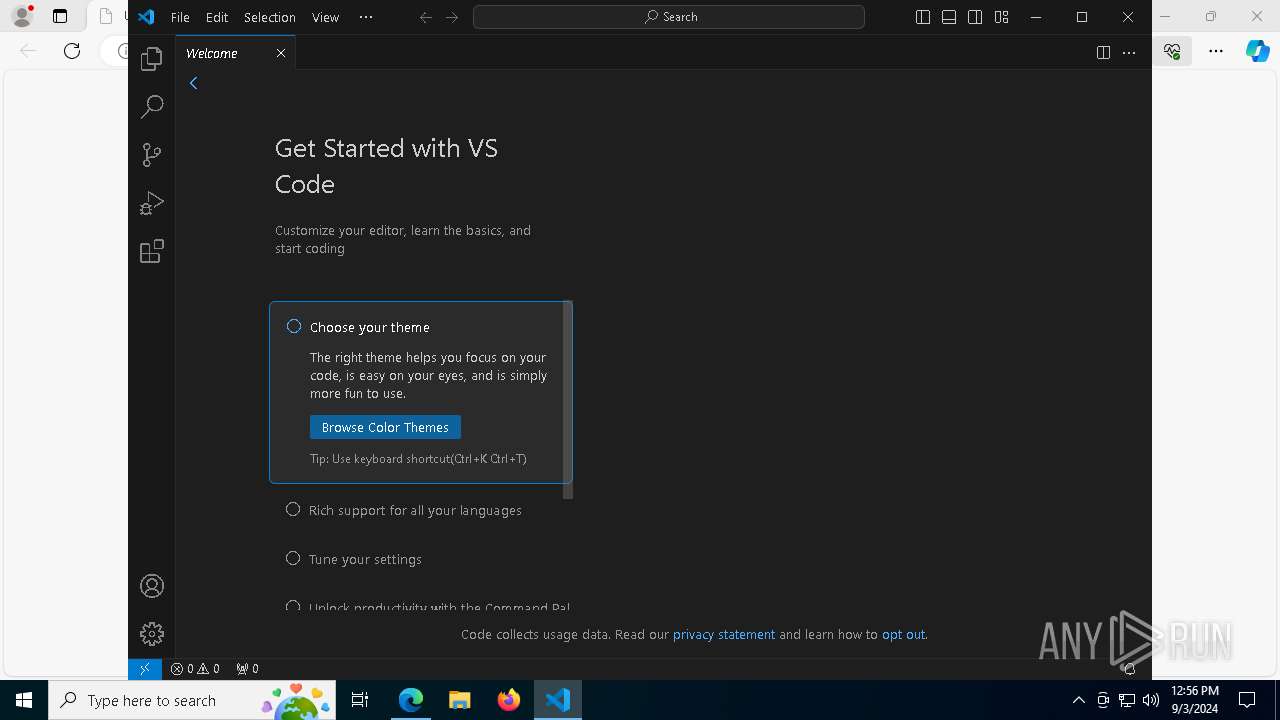
| URL: | https://code.visualstudio.com/sha/download?build=stable&os=win32-x64-user |
| Full analysis: | https://app.any.run/tasks/68ec2c52-be3c-4b19-8d4c-11168fc48571 |
| Verdict: | Malicious activity |
| Analysis date: | September 03, 2024, 12:53:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | F63E3E3C3B1D50C103BD81BF488CA47B |
| SHA1: | 36E5920D4E79F5CB58F2B86CA49B71BD4E9A52E2 |
| SHA256: | 70892A7911641F8E15CDA7961D1297D728F8069557E850A228F3802A43CD7632 |
| SSDEEP: | 3:N8X2XvWRQBLL49ow8YWiuDNdWtHX:2m+RU/4ClDNdoHX |
MALICIOUS
The DLL Hijacking
- Code.exe (PID: 3864)
SUSPICIOUS
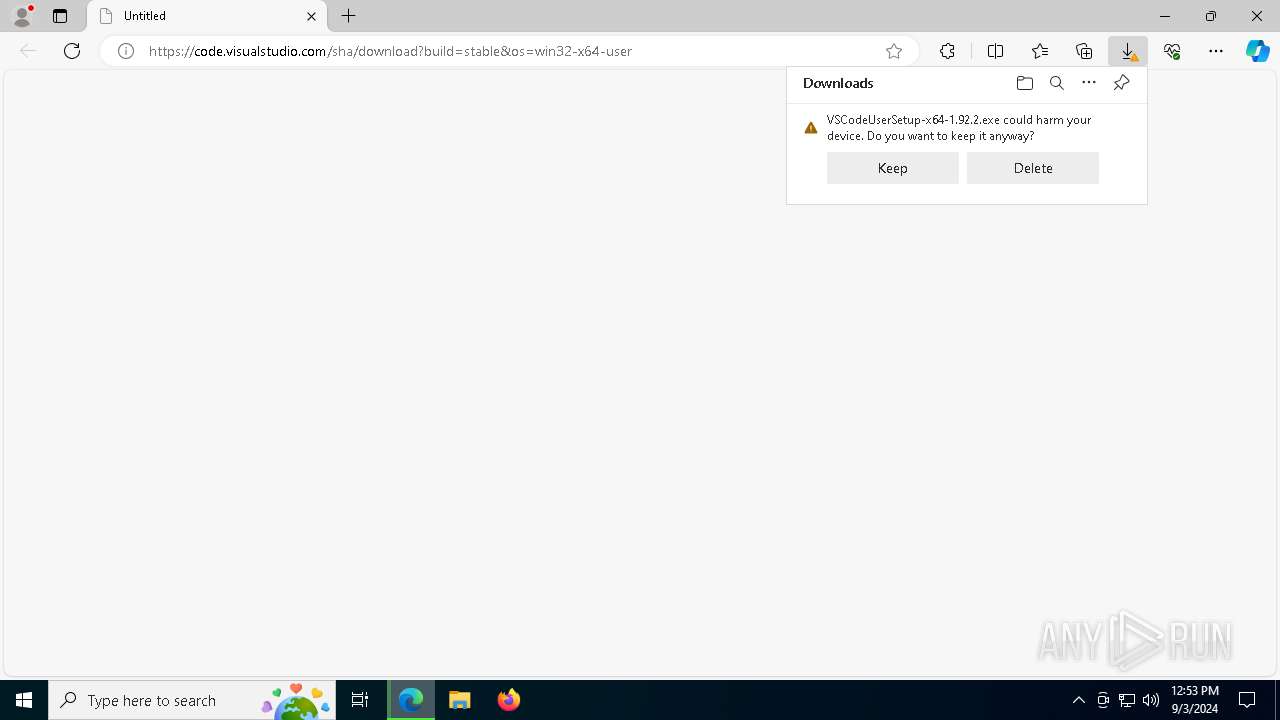
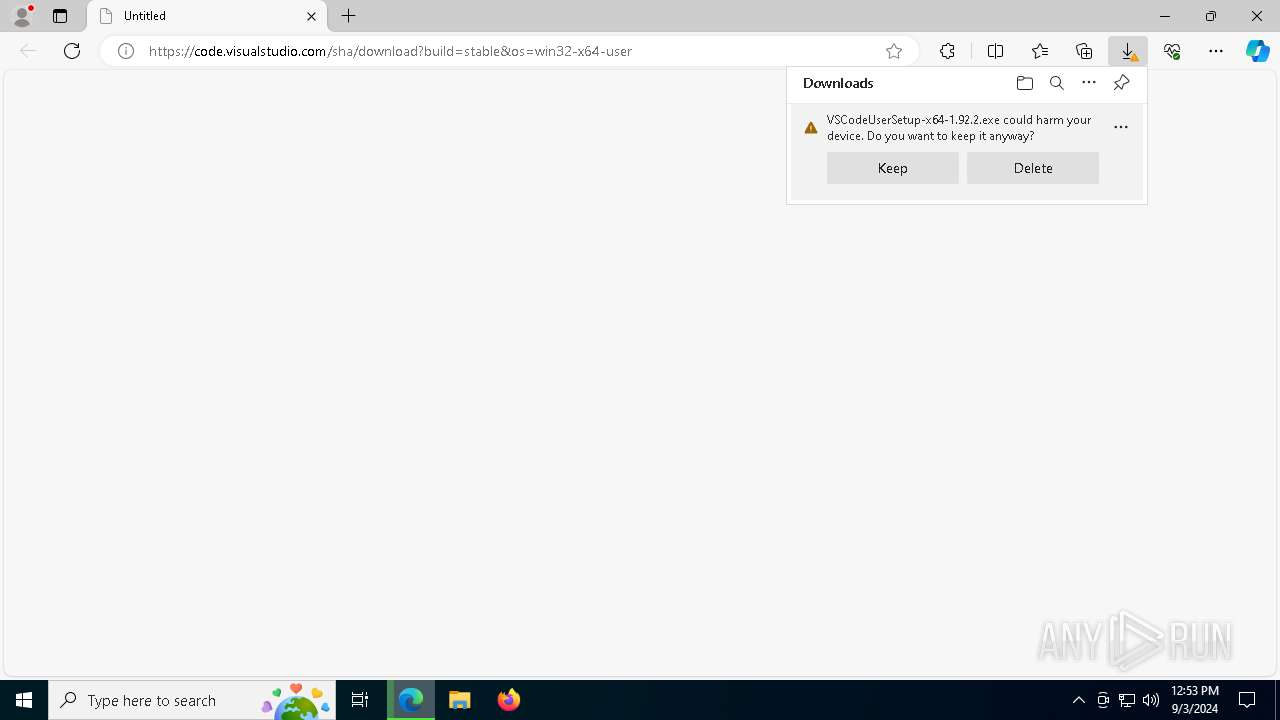
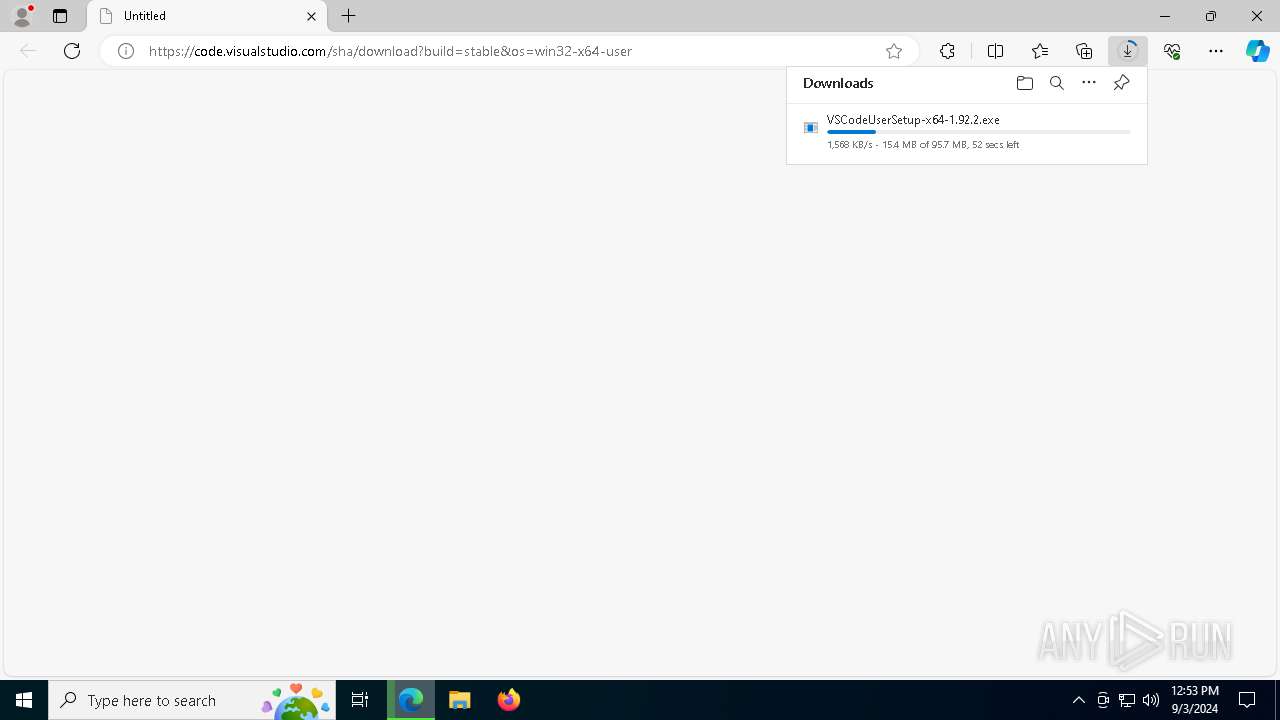
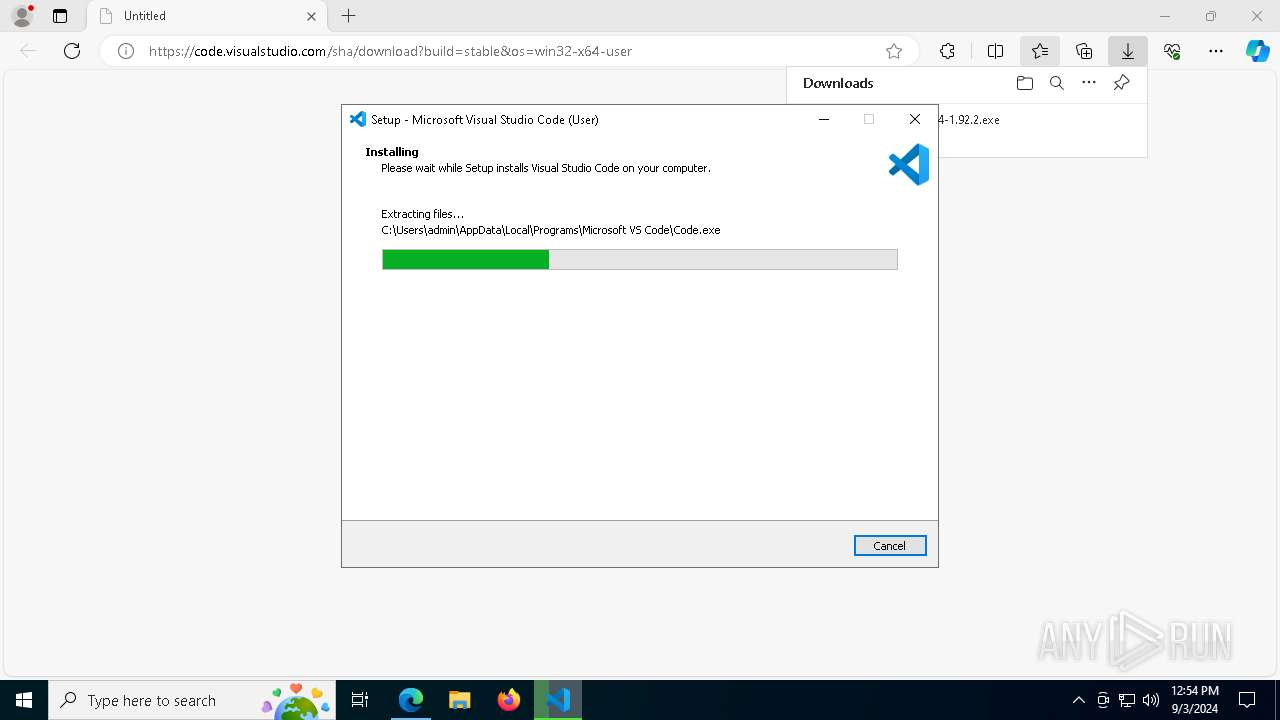
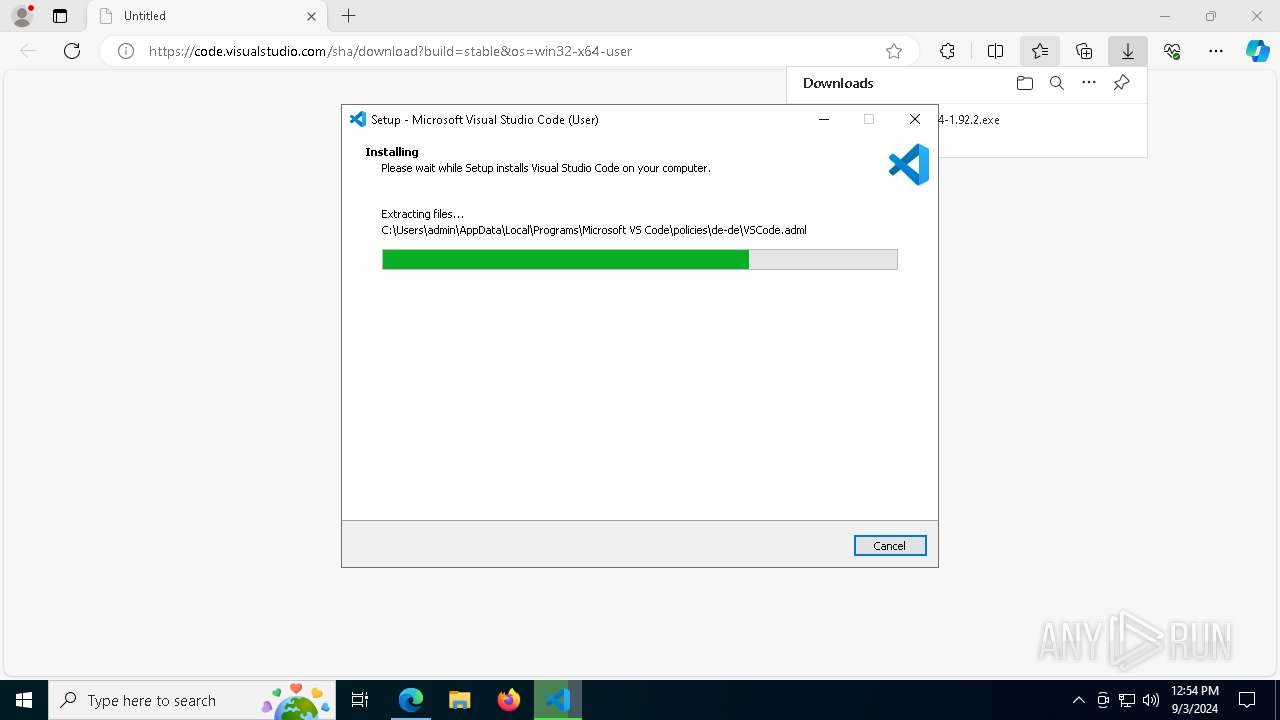
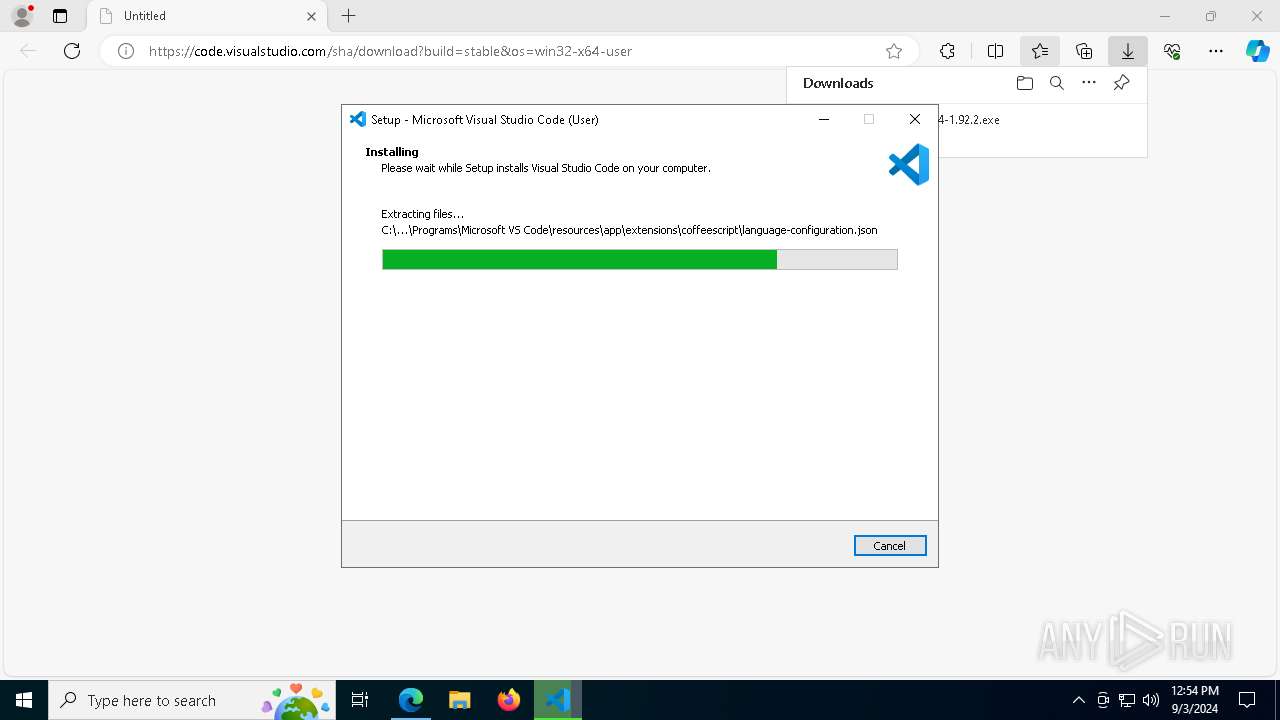
Executable content was dropped or overwritten
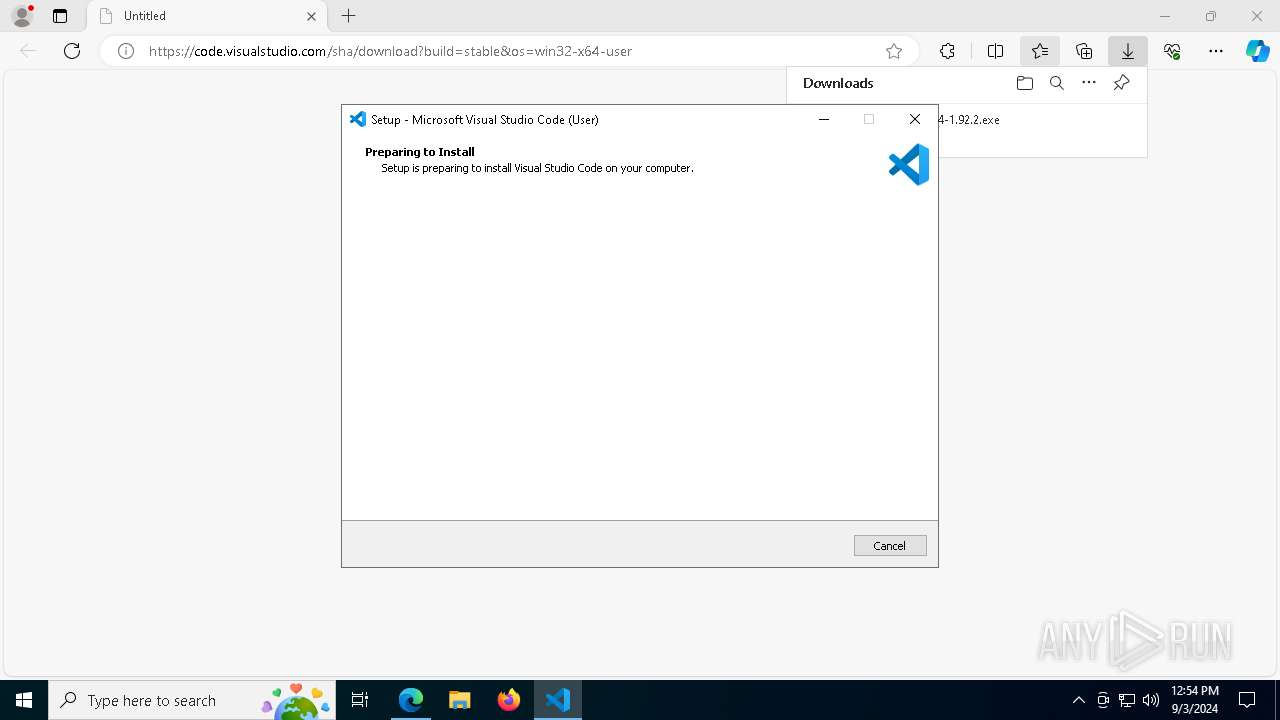
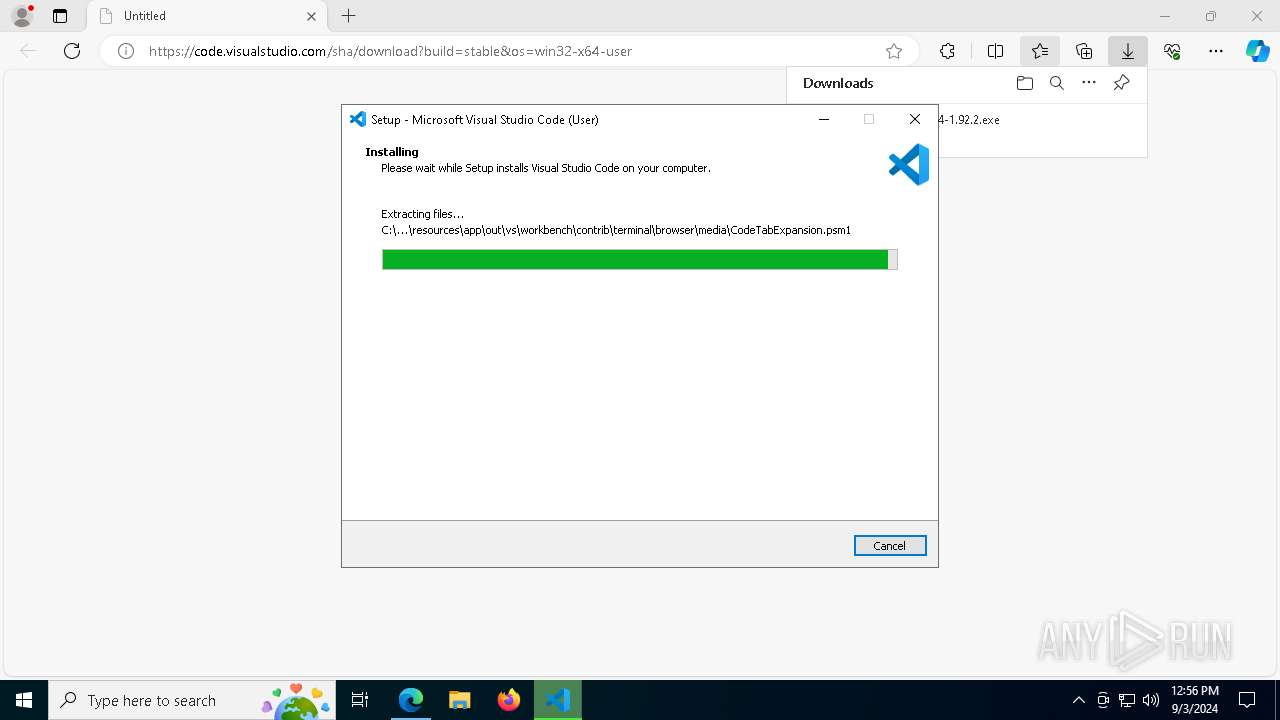
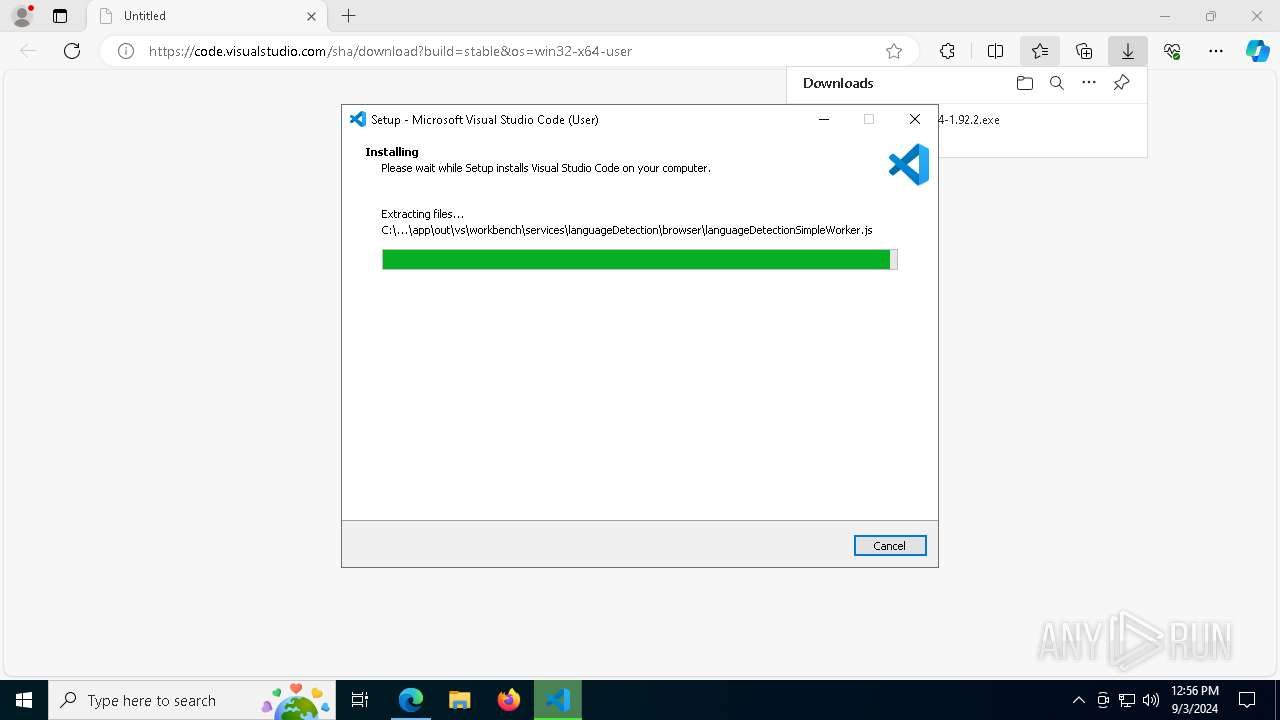
- VSCodeUserSetup-x64-1.92.2.exe (PID: 7024)
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
Reads the Windows owner or organization settings
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
Reads security settings of Internet Explorer
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
Reads the date of Windows installation
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
Process drops legitimate windows executable
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
Starts POWERSHELL.EXE for commands execution
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
Kill processes via PowerShell
- powershell.exe (PID: 1124)
Get information on the list of running processes
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
The process drops C-runtime libraries
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
Uses ICACLS.EXE to modify access control lists
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
Application launched itself
- Code.exe (PID: 6040)
Starts CMD.EXE for commands execution
- Code.exe (PID: 6040)
Found regular expressions for crypto-addresses (YARA)
- Code.exe (PID: 6040)
INFO
Application launched itself
- msedge.exe (PID: 6172)
Checks supported languages
- identity_helper.exe (PID: 3036)
- VSCodeUserSetup-x64-1.92.2.exe (PID: 7024)
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
- Code.exe (PID: 4072)
- Code.exe (PID: 6040)
- Code.exe (PID: 3864)
- Code.exe (PID: 7040)
- Code.exe (PID: 3980)
- Code.exe (PID: 6864)
- Code.exe (PID: 6240)
- Code.exe (PID: 5768)
- code-tunnel.exe (PID: 6632)
- Code.exe (PID: 4168)
Executable content was dropped or overwritten
- msedge.exe (PID: 6172)
Reads Environment values
- identity_helper.exe (PID: 3036)
- Code.exe (PID: 6040)
- Code.exe (PID: 7040)
- Code.exe (PID: 6240)
- Code.exe (PID: 6864)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6172)
Reads the computer name
- identity_helper.exe (PID: 3036)
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
- Code.exe (PID: 4072)
- Code.exe (PID: 3864)
- Code.exe (PID: 6040)
- Code.exe (PID: 7040)
- Code.exe (PID: 6864)
- code-tunnel.exe (PID: 6632)
The process uses the downloaded file
- msedge.exe (PID: 6172)
- msedge.exe (PID: 4344)
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
Create files in a temporary directory
- VSCodeUserSetup-x64-1.92.2.exe (PID: 7024)
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
- Code.exe (PID: 6040)
Process checks computer location settings
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
- Code.exe (PID: 6040)
- Code.exe (PID: 3980)
- Code.exe (PID: 5768)
- Code.exe (PID: 7040)
- Code.exe (PID: 6864)
- Code.exe (PID: 4168)
Creates a software uninstall entry
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
Creates files or folders in the user directory
- VSCodeUserSetup-x64-1.92.2.tmp (PID: 5376)
- Code.exe (PID: 6040)
- Code.exe (PID: 4072)
- Code.exe (PID: 6864)
- Code.exe (PID: 6240)
- Code.exe (PID: 7040)
Reads product name
- Code.exe (PID: 6040)
- Code.exe (PID: 6240)
- Code.exe (PID: 6864)
- Code.exe (PID: 7040)
Reads the machine GUID from the registry
- Code.exe (PID: 6040)
Checks proxy server information
- Code.exe (PID: 6040)
- code-tunnel.exe (PID: 6632)
Reads CPU info
- Code.exe (PID: 6040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
193
Monitored processes
64
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1060 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4104 --field-trial-handle=2408,i,6516066681149166348,6391619074383134198,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1124 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Command "Get-WmiObject Win32_Process | Where-Object { $_.ExecutablePath -eq 'C:\Users\admin\AppData\Local\Programs\Microsoft VS Code\bin\code-tunnel.exe' } | Select @{Name='Id'; Expression={$_.ProcessId}} | Stop-Process -Force" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | VSCodeUserSetup-x64-1.92.2.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1744 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7484 --field-trial-handle=2408,i,6516066681149166348,6391619074383134198,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1748 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6768 --field-trial-handle=2408,i,6516066681149166348,6391619074383134198,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1748 | "C:\WINDOWS\system32\icacls.exe" "C:\Users\admin\AppData\Local\Programs\Microsoft VS Code" /inheritancelevel:r /grant:r "*S-1-5-18:(OI)(CI)F" /grant:r "*S-1-5-32-544:(OI)(CI)F" /grant:r "*S-1-5-11:(OI)(CI)RX" /grant:r "*S-1-5-32-545:(OI)(CI)RX" /grant:r "*S-1-3-0:(OI)(CI)F" /grant:r "admin:(OI)(CI)F" | C:\Windows\System32\icacls.exe | — | VSCodeUserSetup-x64-1.92.2.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1992 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4380 --field-trial-handle=2408,i,6516066681149166348,6391619074383134198,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1992 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6592 --field-trial-handle=2408,i,6516066681149166348,6391619074383134198,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2008 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2080 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6424 --field-trial-handle=2408,i,6516066681149166348,6391619074383134198,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
31 349
Read events
30 742
Write events
575
Delete events
32
Modification events
| (PID) Process: | (6172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6172) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6172) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
76
Suspicious files
1 450
Text files
1 156
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF129f84.TMP | — | |
MD5:— | SHA256:— | |||
| 6172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF129fb3.TMP | — | |
MD5:— | SHA256:— | |||
| 6172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF129fb3.TMP | — | |
MD5:— | SHA256:— | |||
| 6172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF129fb3.TMP | — | |
MD5:— | SHA256:— | |||
| 6172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF129fe2.TMP | — | |
MD5:— | SHA256:— | |||
| 6172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
68
DNS requests
66
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2092 | svchost.exe | HEAD | 200 | 23.32.238.128:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7b9cac0d-9ca2-42ef-9c46-ce975d51335a?P1=1725569099&P2=404&P3=2&P4=OVfneXxbP5JFXehxUvEcCgpiFs32d3kBRwfRaGgnxDK3GfnAXJmY530vwNVtJds%2fjxVYZXPECXk1qkAxUjc5iA%3d%3d | unknown | — | — | whitelisted |
6952 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1440 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6952 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6172 | msedge.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
2092 | svchost.exe | GET | 206 | 23.32.238.128:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7b9cac0d-9ca2-42ef-9c46-ce975d51335a?P1=1725569099&P2=404&P3=2&P4=OVfneXxbP5JFXehxUvEcCgpiFs32d3kBRwfRaGgnxDK3GfnAXJmY530vwNVtJds%2fjxVYZXPECXk1qkAxUjc5iA%3d%3d | unknown | — | — | whitelisted |
2092 | svchost.exe | GET | 206 | 23.32.238.128:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7b9cac0d-9ca2-42ef-9c46-ce975d51335a?P1=1725569099&P2=404&P3=2&P4=OVfneXxbP5JFXehxUvEcCgpiFs32d3kBRwfRaGgnxDK3GfnAXJmY530vwNVtJds%2fjxVYZXPECXk1qkAxUjc5iA%3d%3d | unknown | — | — | whitelisted |
2092 | svchost.exe | GET | 206 | 23.32.238.128:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7b9cac0d-9ca2-42ef-9c46-ce975d51335a?P1=1725569099&P2=404&P3=2&P4=OVfneXxbP5JFXehxUvEcCgpiFs32d3kBRwfRaGgnxDK3GfnAXJmY530vwNVtJds%2fjxVYZXPECXk1qkAxUjc5iA%3d%3d | unknown | — | — | whitelisted |
2092 | svchost.exe | GET | 206 | 23.32.238.128:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7b9cac0d-9ca2-42ef-9c46-ce975d51335a?P1=1725569099&P2=404&P3=2&P4=OVfneXxbP5JFXehxUvEcCgpiFs32d3kBRwfRaGgnxDK3GfnAXJmY530vwNVtJds%2fjxVYZXPECXk1qkAxUjc5iA%3d%3d | unknown | — | — | whitelisted |
2092 | svchost.exe | GET | 206 | 23.32.238.128:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7b9cac0d-9ca2-42ef-9c46-ce975d51335a?P1=1725569099&P2=404&P3=2&P4=OVfneXxbP5JFXehxUvEcCgpiFs32d3kBRwfRaGgnxDK3GfnAXJmY530vwNVtJds%2fjxVYZXPECXk1qkAxUjc5iA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7056 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3852 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6172 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3852 | msedge.exe | 13.107.246.57:443 | code.visualstudio.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | suspicious |
3852 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3852 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3852 | msedge.exe | 94.245.104.56:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
code.visualstudio.com |
| unknown |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
vscode.download.prss.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |