| File name: | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader |
| Full analysis: | https://app.any.run/tasks/6e12e656-ec82-4609-8b3e-3cb3fde3d550 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 20:40:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | E57FB92B7E274F8A99FF52BFEC4E3C04 |
| SHA1: | E8D15385CC2D1C2D92F0594BD352D46DD3B594D6 |
| SHA256: | 70849971F503186F6BE3CD5EDEC609A71BD7C72F11E36D1F1C5A4E59589851E0 |
| SSDEEP: | 24576:4Kyj0zgtbr6YGsrFY7xNINUQfF7OOMFg5jRp:tyj0zgtbr6YGsrFWNINUQfF7OOMFg5jL |
MALICIOUS
Executing a file with an untrusted certificate
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 6036)
- FileCoAuth.exe (PID: 4844)
NESHTA mutex has been found
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
- FileCoAuth.exe (PID: 6372)
Connects to the CnC server
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 6036)
- FileCoAuth.exe (PID: 6372)
Process drops legitimate windows executable
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 6036)
- FileCoAuth.exe (PID: 6372)
Starts a Microsoft application from unusual location
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 6036)
- FileCoAuth.exe (PID: 4844)
Mutex name with non-standard characters
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
- FileCoAuth.exe (PID: 6372)
Searches for installed software
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 6036)
Reads security settings of Internet Explorer
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
- FileCoAuth.exe (PID: 6372)
There is functionality for taking screenshot (YARA)
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
Contacting a server suspected of hosting an CnC
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
INFO
The sample compiled with english language support
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 6036)
- FileCoAuth.exe (PID: 6372)
Process checks computer location settings
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
- FileCoAuth.exe (PID: 6372)
Create files in a temporary directory
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 6036)
- FileCoAuth.exe (PID: 4844)
Reads the computer name
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 6036)
- FileCoAuth.exe (PID: 4844)
Failed to create an executable file in Windows directory
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
Checks supported languages
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 6036)
- FileCoAuth.exe (PID: 4844)
Checks proxy server information
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
UPX packer has been detected
- 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe (PID: 7012)
Reads the machine GUID from the registry
- FileCoAuth.exe (PID: 4844)
Creates files or folders in the user directory
- FileCoAuth.exe (PID: 4844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 6 (85.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (4.6) |
| .scr | | | Windows screen saver (4.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (2.1) |
| .exe | | | Win32 Executable (generic) (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 29696 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x80e4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
128
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4844 | "C:\Users\admin\AppData\Local\Temp\3582-490\FileCoAuth.exe" -Embedding | C:\Users\admin\AppData\Local\Temp\3582-490\FileCoAuth.exe | — | FileCoAuth.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneDriveFile Co-Authoring Executable Exit code: 0 Version: 19.043.0304.0013 Modules
| |||||||||||||||
| 5984 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
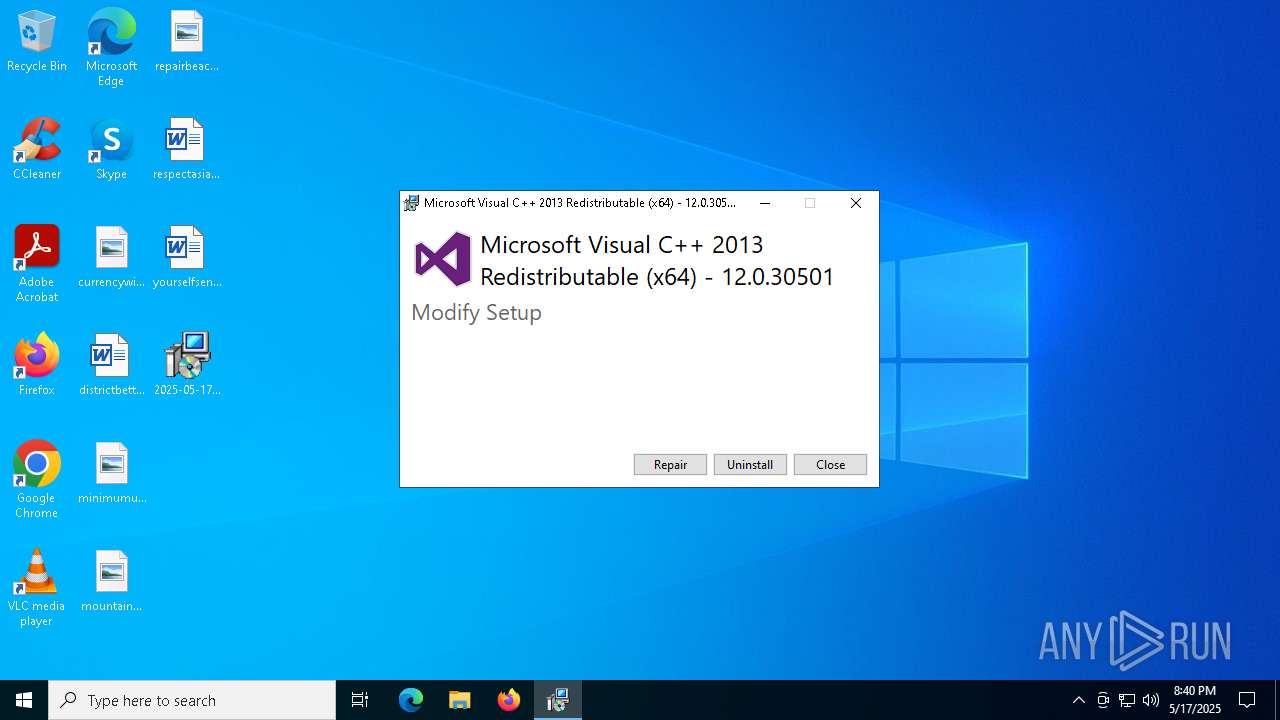
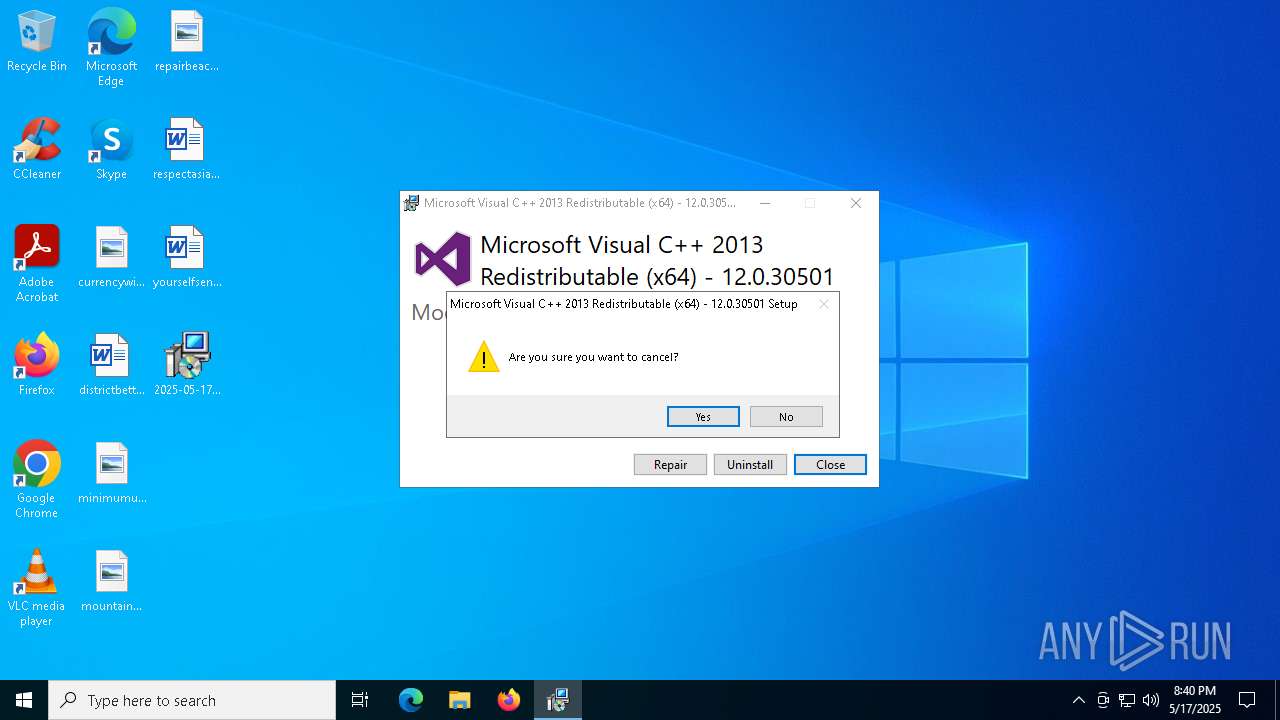
| 6036 | "C:\Users\admin\AppData\Local\Temp\3582-490\2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2013 Redistributable (x64) - 12.0.30501 Exit code: 1602 Version: 12.0.30501.0 Modules
| |||||||||||||||
| 6372 | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe -Embedding | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7012 | "C:\Users\admin\Desktop\2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe" | C:\Users\admin\Desktop\2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 442
Read events
4 439
Write events
3
Delete events
0
Modification events
| (PID) Process: | (7012) 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7012) 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7012) 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
12
Suspicious files
2
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6036 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | C:\Users\admin\AppData\Local\Temp\{050d4fc8-5d48-4b8f-8972-47c82c46020f}\.ba1\BootstrapperApplicationData.xml | xml | |
MD5:0BD4FA44198EB101D1F070BB99A12C0B | SHA256:54BF9F4BC4ADCBBA99AEF3C048522C23822D3DDAB51891DCBA3B6F59192A2B28 | |||
| 6036 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | C:\Users\admin\AppData\Local\Temp\{050d4fc8-5d48-4b8f-8972-47c82c46020f}\.ba1\license.rtf | text | |
MD5:1E47EE7B71B22488068343DF4CE30534 | SHA256:8518F0420972C1DBE8A323FFC6F57863AF0B80C6A3B27FD0C6FC9BDABB7E2D13 | |||
| 7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\OneDriveUpdaterService.exe | executable | |
MD5:E73AC057B2CFEF016B8199389F0DF590 | SHA256:20ABA9D6001E5CDC287CD5BD452D0F2D05980D83F851D2B309BF49E9D9A8AC4C | |||
| 7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | executable | |
MD5:13C2D5BF03C4A2B28E930F990CCC32DB | SHA256:12D24D0BC0E7CDC902E3540A3C6F7B755094F011A8EAD49A47A00563710B8F80 | |||
| 7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | C:\ProgramData\Adobe\ARM\S\388\AdobeARMHelper.exe | executable | |
MD5:85A67D34298E33D2D5A9EC789B6AB594 | SHA256:1DEE143B4F88F2375B85C6271A58E2E78FED081BEAE4090678CB2DD7A37FB2D4 | |||
| 7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | C:\Users\admin\AppData\Local\Temp\conres.dll.000 | text | |
MD5:1130C911BF5DB4B8F7CF9B6F4B457623 | SHA256:EBA08CC8182F379392A97F542B350EA0DBBE5E4009472F35AF20E3D857EAFDF1 | |||
| 7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | C:\Users\admin\AppData\Local\Temp\3582-490\2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | executable | |
MD5:E16E6D68CE1949C9721656390F47CE07 | SHA256:18E6D3D96FCD39BA069C0E6EBC108881EC5BB07E29A24B0177688CE391DAC526 | |||
| 7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileSyncHelper.exe | executable | |
MD5:1C0BE16E6ED8F5B6F0910650A25F4FA7 | SHA256:3028F6A6A7A10DC5D63F256FEEB8275F3818BF3371EAF8B20A2D0BF2FCD5F4A9 | |||
| 6372 | FileCoAuth.exe | C:\Users\admin\AppData\Local\Temp\3582-490\FileCoAuth.exe | executable | |
MD5:394DEEEF3E5FFE6C77A9CDA1832361BB | SHA256:37DCEC7509B0803F2BBA453845ED67FDBAA15771F8A60FC11F9082FD2A64BD23 | |||
| 7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | C:\Users\admin\AppData\Local\Temp\conres.dll | executable | |
MD5:7574CF2C64F35161AB1292E2F532AABF | SHA256:DE055A89DE246E629A8694BDE18AF2B1605E4B9B493C7E4AEF669DD67ACF5085 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
51
DNS requests
21
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6476 | RUXIMICS.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | GET | 403 | 45.56.79.23:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | GET | 403 | 45.56.79.23:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
6476 | RUXIMICS.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | GET | 403 | 45.56.79.23:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | GET | 403 | 45.56.79.23:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | GET | 403 | 45.56.79.23:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
5776 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
5776 | SIHClient.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5776 | SIHClient.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6476 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6476 | RUXIMICS.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
6476 | RUXIMICS.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | 45.56.79.23:80 | www.aieov.com | Linode, LLC | US | malicious |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5776 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
5isohu.com |
| whitelisted |
www.aieov.com |
| malicious |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
7012 | 2025-05-17_e57fb92b7e274f8a99ff52bfec4e3c04_amadey_coinminer_elex_floxif_gcleaner_neshta_smoke-loader.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |