| File name: | 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe |
| Full analysis: | https://app.any.run/tasks/fe89ec7e-2df7-4420-8d4e-4242fc43da16 |
| Verdict: | Malicious activity |
| Analysis date: | April 04, 2024, 15:51:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 4551BD1A7BF821809FB9B358438EC935 |
| SHA1: | 85C44D9607BEEE8A35E140AF652925A552FA6B80 |
| SHA256: | 707BEF517183638BDB4FA8914BEF5E59970EDF9FE89B9BDADDAD010D413818FA |
| SSDEEP: | 98304:K9Iiynq0a5/nT/Q6KaDCgi2pX7rPwgagD6DTe3q5spvZa4BAplk/42pw4QP/GEqx:ZofxMG |
MALICIOUS
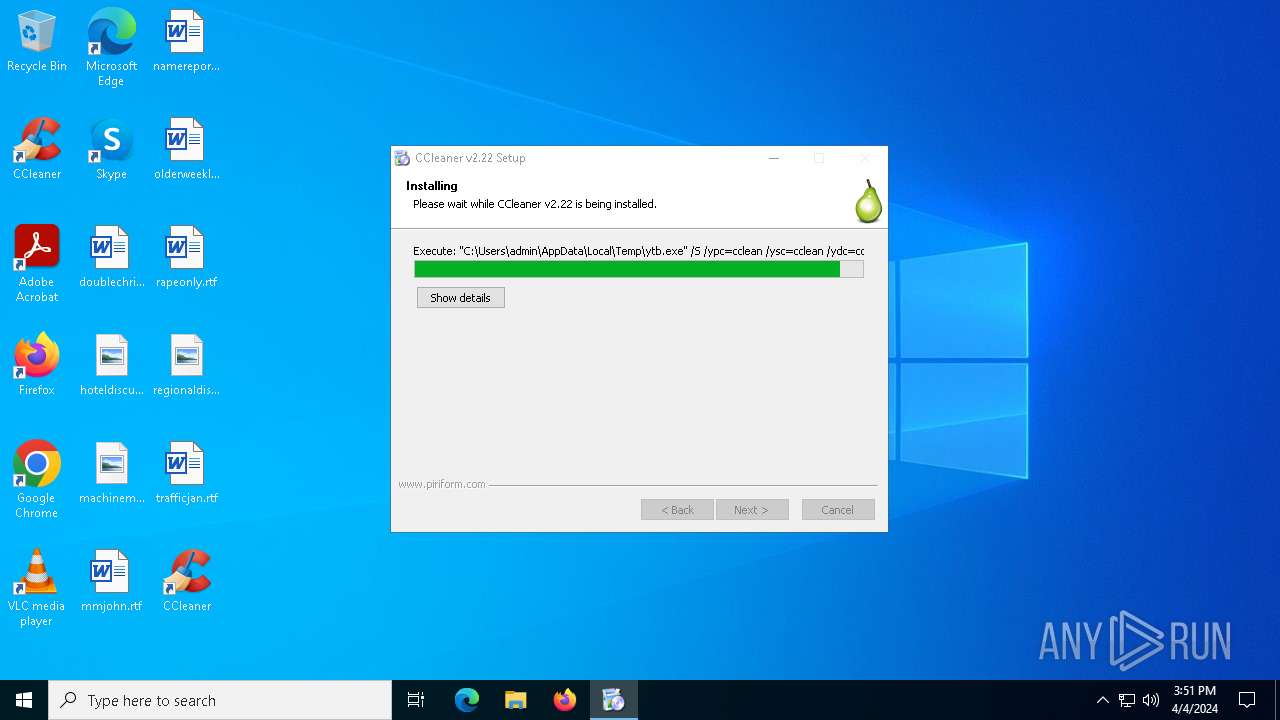
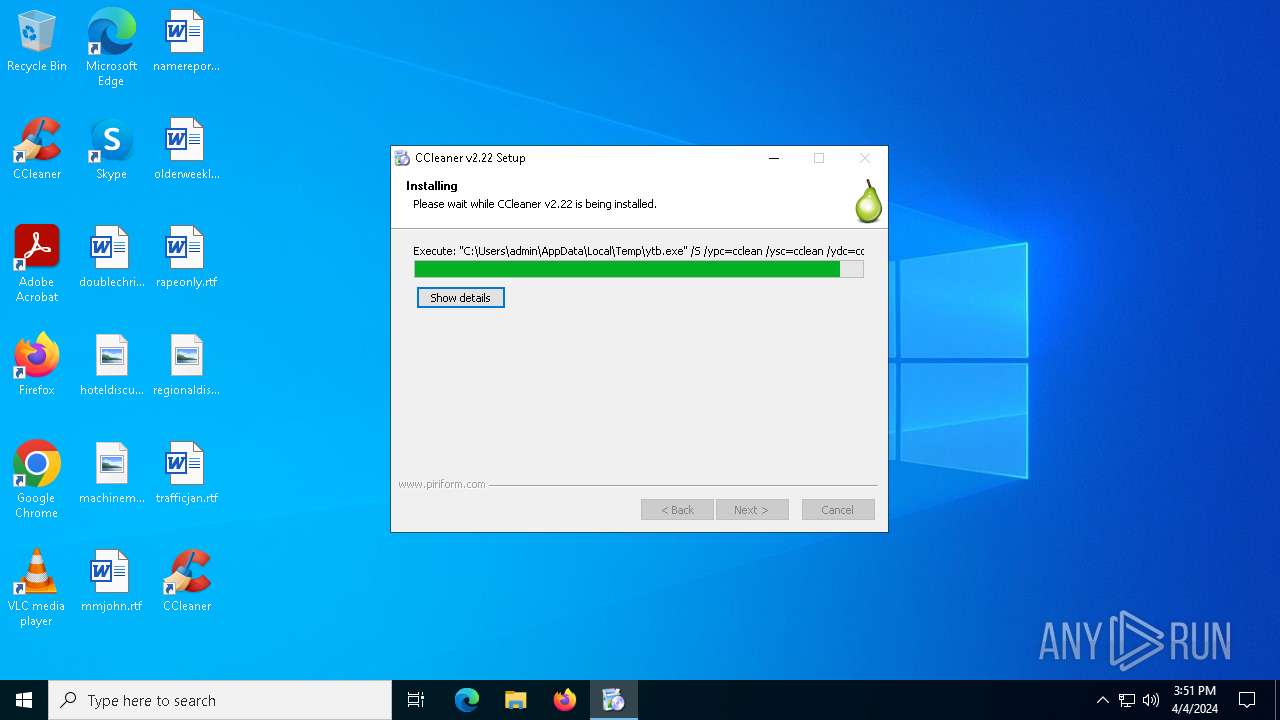
Drops the executable file immediately after the start
- ytb.exe (PID: 4968)
- 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe (PID: 6332)
- ytb_setup.exe (PID: 5136)
Steals credentials from Web Browsers
- ytb.exe (PID: 4968)
- ytb_setup.exe (PID: 5136)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe (PID: 6332)
- ytb.exe (PID: 4968)
- ytb_setup.exe (PID: 5136)
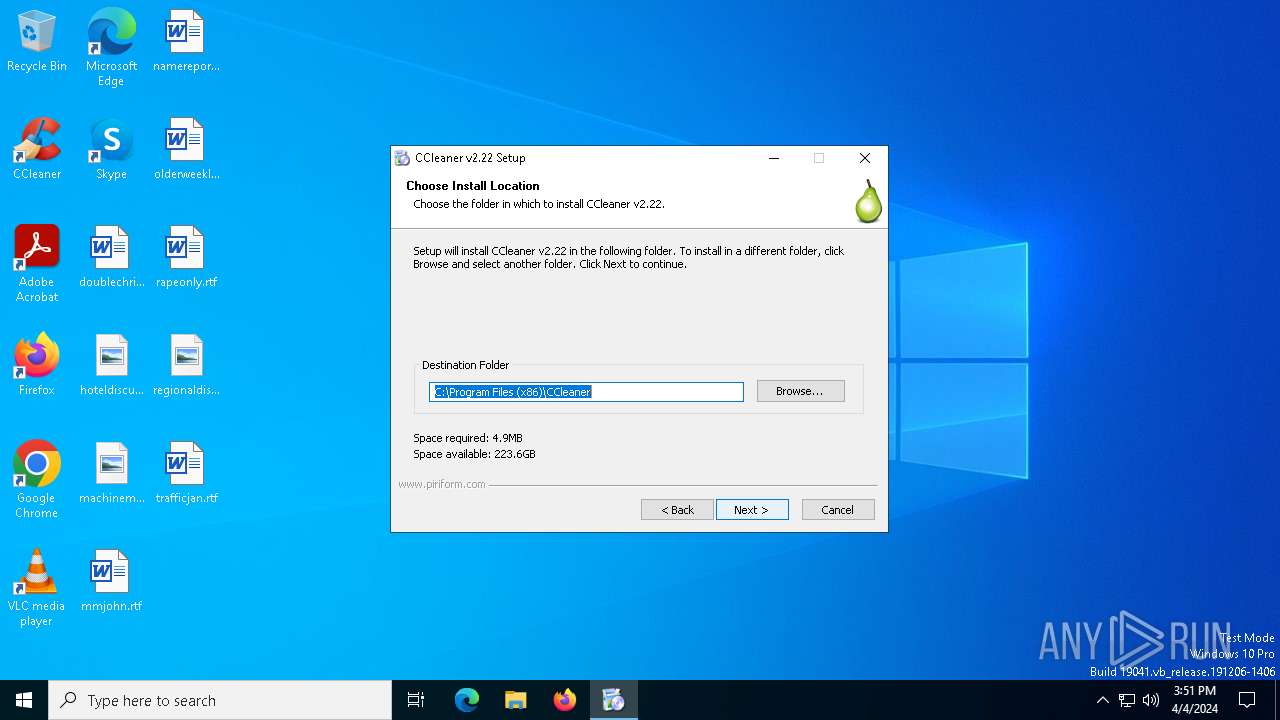
Creates a software uninstall entry
- 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe (PID: 6332)
- ytb_setup.exe (PID: 5136)
The process creates files with name similar to system file names
- 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe (PID: 6332)
- ytb.exe (PID: 4968)
- ytb_setup.exe (PID: 5136)
Creates/Modifies COM task schedule object
- ytb_setup.exe (PID: 5136)
Reads security settings of Internet Explorer
- ytb.exe (PID: 4968)
- ytb_setup.exe (PID: 5136)
- ytbb.exe (PID: 6472)
Reads the date of Windows installation
- ytb.exe (PID: 4968)
INFO
Reads Environment values
- 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe (PID: 6332)
- ytb_setup.exe (PID: 5136)
Checks supported languages
- 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe (PID: 6332)
- ytb.exe (PID: 4968)
- ytb_setup.exe (PID: 5136)
- ytbb.exe (PID: 6472)
Reads the computer name
- 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe (PID: 6332)
- ytb_setup.exe (PID: 5136)
- ytb.exe (PID: 4968)
- ytbb.exe (PID: 6472)
Creates files in the program directory
- 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe (PID: 6332)
- ytb_setup.exe (PID: 5136)
- ytbb.exe (PID: 6472)
Create files in a temporary directory
- 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe (PID: 6332)
- ytb_setup.exe (PID: 5136)
- ytb.exe (PID: 4968)
Creates files or folders in the user directory
- 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe (PID: 6332)
Process checks computer location settings
- ytb.exe (PID: 4968)
- ytb_setup.exe (PID: 5136)
Checks proxy server information
- slui.exe (PID: 2388)
- ytb_setup.exe (PID: 5136)
Reads the software policy settings
- slui.exe (PID: 2388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:06:06 21:41:54+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Piriform Ltd |
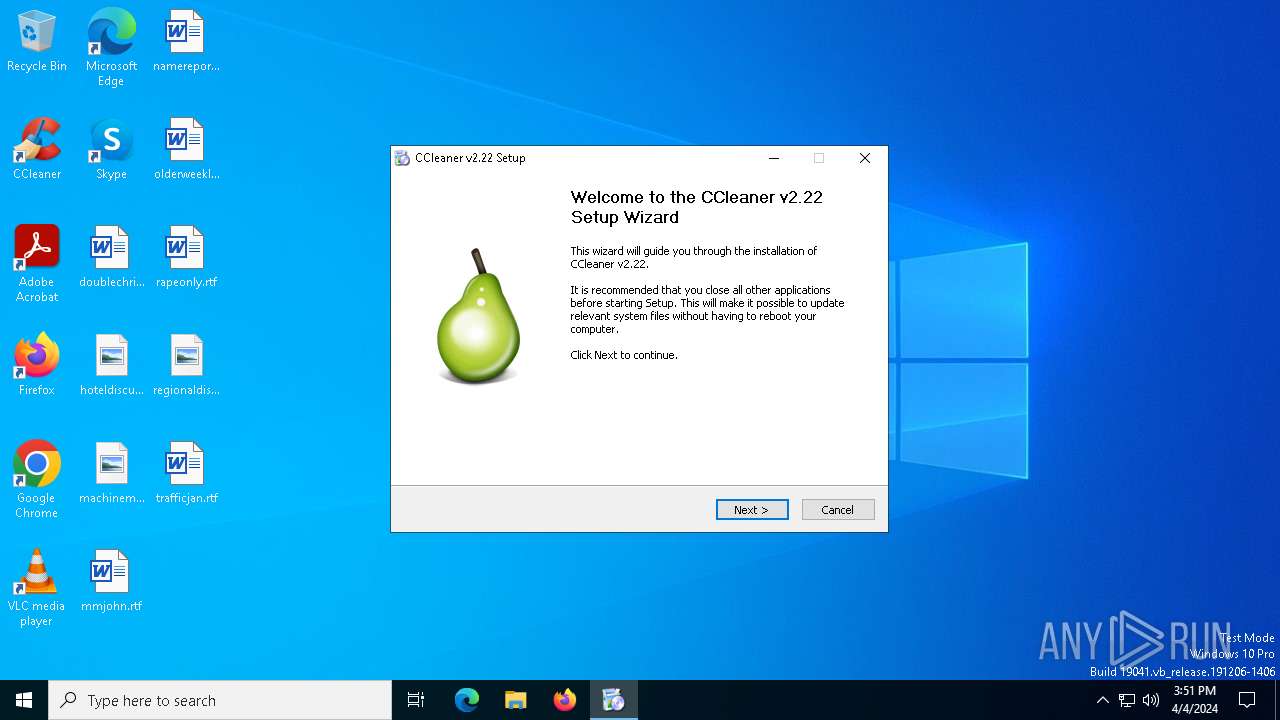
| FileDescription: | CCleaner Installer |
| FileVersion: | 2.0.0.0 |
| LegalCopyright: | ©2005-2009 Piriform Ltd |
| ProductName: | CCleaner |
Total processes
131
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2388 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2428 | "C:\Users\admin\AppData\Local\Temp\707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe" | C:\Users\admin\AppData\Local\Temp\707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Ltd Integrity Level: MEDIUM Description: CCleaner Installer Exit code: 3221226540 Version: 2.0.0.0 Modules
| |||||||||||||||
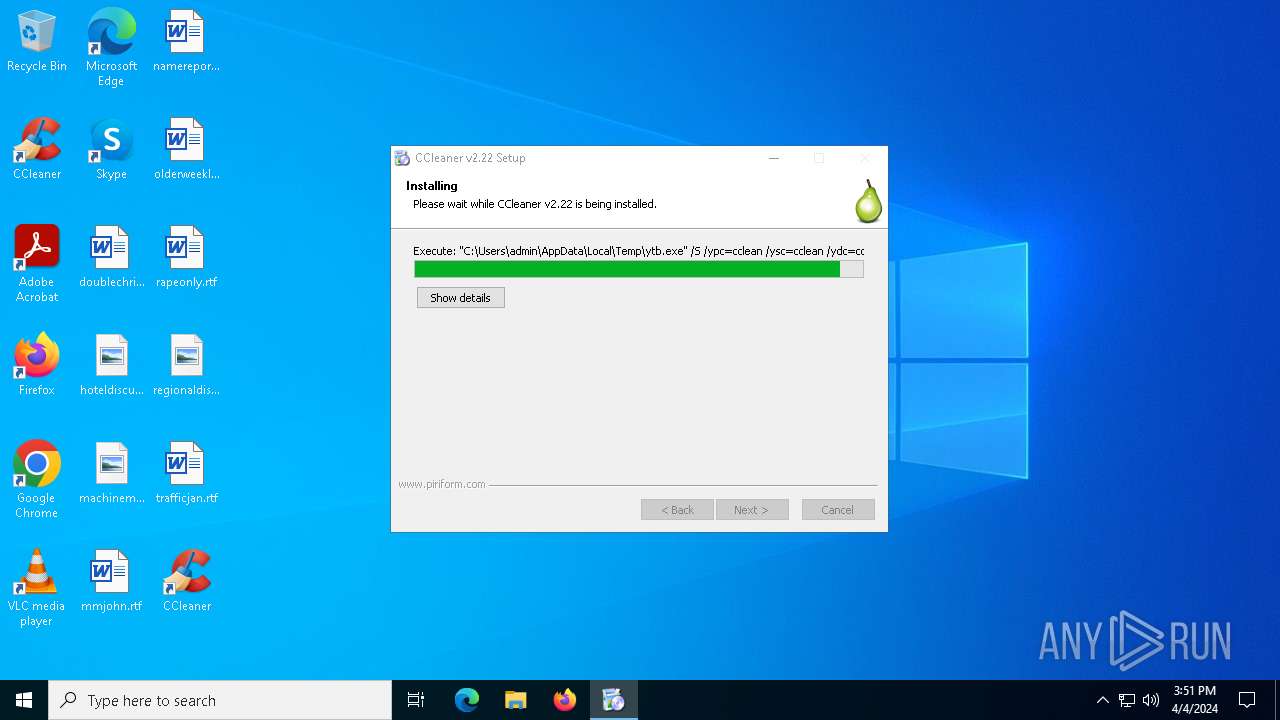
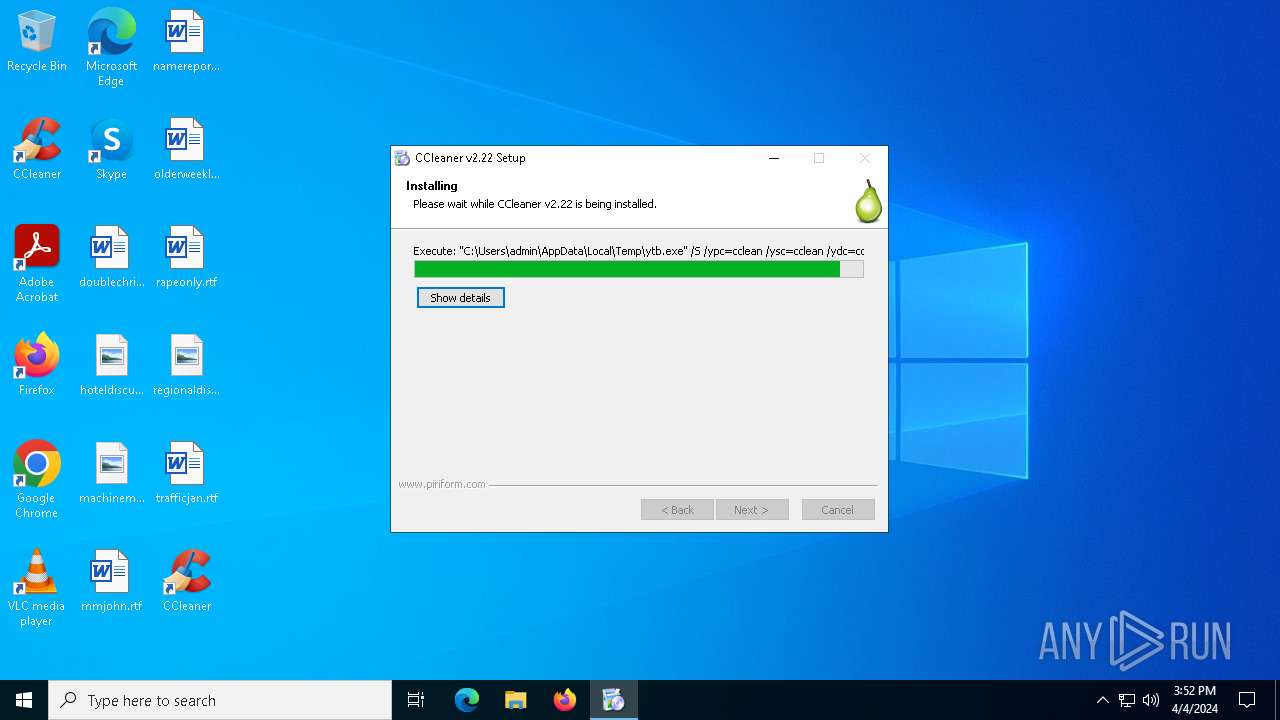
| 4968 | "C:\Users\admin\AppData\Local\Temp\ytb.exe" /S /ypc=cclean /ysc=cclean /ydc=cclean /yinstytff /ydontask | C:\Users\admin\AppData\Local\Temp\ytb.exe | 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | ||||||||||||
User: admin Company: Yahoo! Inc. Integrity Level: HIGH Description: Yahoo! Toolbar Bootstrapper Setup Exit code: 0 Version: 2008.11.25.01 Modules
| |||||||||||||||
| 5136 | "C:\Users\admin\AppData\Local\Temp\nss74CF.tmp\ytb_setup.exe" /S /ypc=cclean /ysc=cclean /ydc=cclean /yinstytff /ydontask /ybsini=C:\Users\admin\AppData\Local\Temp\nss74CF.tmp\BOOTST~1.INI | C:\Users\admin\AppData\Local\Temp\nss74CF.tmp\ytb_setup.exe | ytb.exe | ||||||||||||
User: admin Company: Yahoo! Inc. Integrity Level: HIGH Description: Yahoo! Toolbar Setup Exit code: 0 Version: 2008.11.25.01 Modules
| |||||||||||||||
| 6332 | "C:\Users\admin\AppData\Local\Temp\707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe" | C:\Users\admin\AppData\Local\Temp\707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | explorer.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Installer Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 6472 | "C:\Program Files (x86)\Yahoo!\Companion\Installs\cpn\ytbb.exe" /RegServer | C:\Program Files (x86)\Yahoo!\Companion\Installs\cpn\ytbb.exe | — | ytb_setup.exe | |||||||||||
User: admin Company: Yahoo! Inc. Integrity Level: HIGH Description: Yahoo! Toolbar Assistant Exit code: 0 Version: 2008, 7, 28, 01 Modules
| |||||||||||||||
Total events
11 448
Read events
11 247
Write events
194
Delete events
7
Modification events
| (PID) Process: | (6332) 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{645FF040-5081-101B-9F08-00AA002F954E}\shell\Open CCleaner...\command |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6332) 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{645FF040-5081-101B-9F08-00AA002F954E}\shell\Open CCleaner... |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6332) 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{645FF040-5081-101B-9F08-00AA002F954E}\shell\Run CCleaner\command |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6332) 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{645FF040-5081-101B-9F08-00AA002F954E}\shell\Run CCleaner |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6332) 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\CCleaner |
| Operation: | write | Name: | UpdateCheck |
Value: 1 | |||
| (PID) Process: | (6332) 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\cclaunch |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (6332) 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\ccleaner.exe |
| Operation: | write | Name: | Path |
Value: C:\Program Files (x86)\CCleaner | |||
| (PID) Process: | (6332) 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CCleaner |
| Operation: | write | Name: | DisplayName |
Value: CCleaner (remove only) | |||
| (PID) Process: | (6332) 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CCleaner |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files (x86)\CCleaner\uninst.exe" | |||
| (PID) Process: | (6332) 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CCleaner |
| Operation: | write | Name: | Publisher |
Value: Piriform | |||
Executable files
67
Suspicious files
3
Text files
49
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6332 | 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | C:\Users\admin\AppData\Local\Temp\nsd53D.tmp\LangDLL.dll | executable | |
MD5:— | SHA256:— | |||
| 6332 | 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | C:\Users\admin\AppData\Local\Temp\nsd53D.tmp\ioFileY.ini | text | |
MD5:— | SHA256:— | |||
| 6332 | 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | C:\Users\admin\AppData\Local\Temp\nsd53D.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 6332 | 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | C:\Users\admin\AppData\Local\Temp\nsd53D.tmp\modern-wizard.bmp | image | |
MD5:— | SHA256:— | |||
| 6332 | 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | C:\Users\admin\AppData\Local\Temp\nsd53D.tmp\modern-header.bmp | image | |
MD5:— | SHA256:— | |||
| 6332 | 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | C:\Users\admin\AppData\Local\Temp\nsd53D.tmp\InstallOptions.dll | executable | |
MD5:— | SHA256:— | |||
| 6332 | 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | C:\Program Files (x86)\CCleaner\CCleaner.exe | executable | |
MD5:— | SHA256:— | |||
| 6332 | 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | C:\Program Files (x86)\CCleaner\Lang\lang-1031.dll | executable | |
MD5:— | SHA256:— | |||
| 6332 | 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | C:\Program Files (x86)\CCleaner\Lang\lang-1041.dll | executable | |
MD5:— | SHA256:— | |||
| 6332 | 707bef517183638bdb4fa8914bef5e59970edf9fe89b9bdaddad010d413818fa.exe | C:\Program Files (x86)\CCleaner\Lang\lang-1049.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
26
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3996 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4828 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
6120 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3996 | svchost.exe | 40.126.32.134:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1280 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3996 | svchost.exe | 40.126.32.138:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | SIHClient.exe | 13.85.23.86:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4852 | backgroundTaskHost.exe | 20.199.58.43:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
5136 | ytb_setup.exe | 188.125.72.139:80 | pclick.internal.yahoo.com | Yahoo! UK Services Limited | IE | unknown |
5272 | SearchApp.exe | 23.15.178.147:443 | www.bing.com | Akamai International B.V. | DE | unknown |
3996 | svchost.exe | 40.126.32.140:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
slscr.update.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
pclick.internal.yahoo.com |
| unknown |
www.bing.com |
| whitelisted |
installerstats.yahoo.com |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |