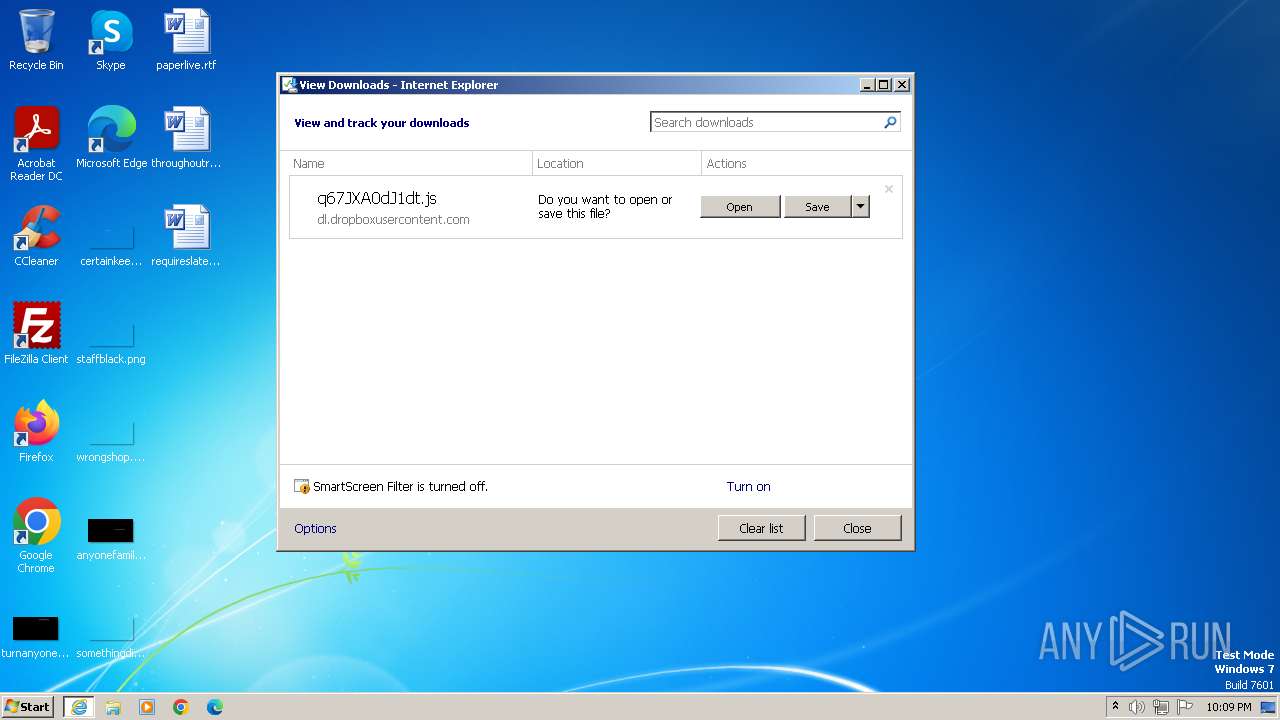
| URL: | dl.dropboxusercontent.com/s/pxxqg90g7zxtt8n/q67jxa0dj1dt.js?ver=1694533035 |
| Full analysis: | https://app.any.run/tasks/211fc2e7-ea25-4677-87c4-dcddf9c24e6b |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2023, 21:09:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 96EACF77EFF6E94E08045AF10163352B604664D9 |
| SHA256: | 7077AE7ED762C28805A5066AD938AB8019B79DA0676774C7A877D338C39B6DB4 |
| SSDEEP: | 3:dXNcvALtGTIbcjGlEbYtPdTyORKB:DFGAxEba5b8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process executes JS scripts
- iexplore.exe (PID: 556)
INFO
The process uses the downloaded file
- iexplore.exe (PID: 556)
Application launched itself
- iexplore.exe (PID: 556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Program Files\Internet Explorer\iexplore.exe" "dl.dropboxusercontent.com/s/pxxqg90g7zxtt8n/q67jxa0dj1dt.js?ver=1694533035" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1804 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:556 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
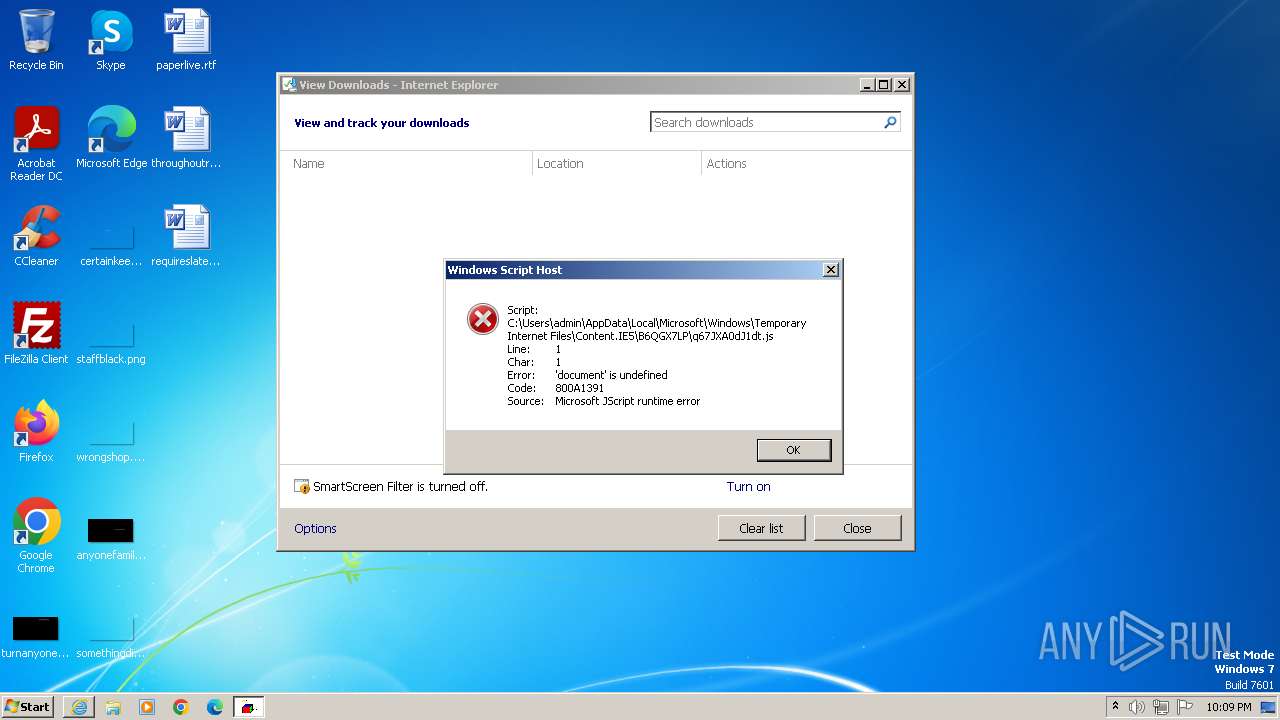
| 2816 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\q67JXA0dJ1dt.js" | C:\Windows\System32\wscript.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
11 839
Read events
11 785
Write events
54
Delete events
0
Modification events
| (PID) Process: | (556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
11
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1804 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E573CDF4C6D731D56A665145182FD759_43DD603AEAEEB8700A510492908E711D | binary | |
MD5:5CD46E3169F6F21122BE467AB1B46E15 | SHA256:4A9F0200002B90FBBEB9390297FAD74DB20A862DB04B9145D71808E55F0AE7E4 | |||
| 1804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\q67JXA0dJ1dt[1].js | text | |
MD5:7C473F21C4682D9970C71F4FB5355C83 | SHA256:33C9136445EC8660003870768940E5EC57DFC7FC91A22B9FF095BF7DBDE7BBEF | |||
| 1804 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 1804 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E573CDF4C6D731D56A665145182FD759_43DD603AEAEEB8700A510492908E711D | binary | |
MD5:6E6D2B049B76D3720C952D1836928F82 | SHA256:0B0346DE6423B1CC6BDA64D733AEB7C3DF2626C5E060E3D2D9C8039253528448 | |||
| 1804 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:BCA02A0B2C0D048B56553E74B2D3C28F | SHA256:9E0EE6830C4765FD770BD80682E3C7DF6661EF9A7D31FD630F20468D24A604BA | |||
| 1804 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:A085CD0B187115A19A0D49609C095806 | SHA256:6CC9BAB6262E923353D3D56AFF5974494F9F149F52B9E0A72BC331C3A5A5E34B | |||
| 556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\q67JXA0dJ1dt.js.q7s1hzr.partial:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{FE9A3971-6F8C-11EE-B150-12A9866C77DE}.dat | binary | |
MD5:B941947FC82A26679C16245E6D5163A2 | SHA256:6CF4586E88EB1ED71F7413DDDDEF5C3F38EF8FEFE806DCA1AB4A823535E88CDA | |||
| 1804 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:787E7DF9799B9BA828A23102D8A2B3D6 | SHA256:F2FFE01C9764E82F333FAEFA776D98ED36773D0B3C19E13DABFFF5CD26A3ADA3 | |||
| 556 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF640BA02537D82294.TMP | binary | |
MD5:FE8E78D8F61A33D8E10CBCFAE4248D8C | SHA256:2EDF6F2AA2F2A30C52F8CE79ECD37FD6D70094039D63C4673547366BE96A131C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
12
DNS requests
9
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1804 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAv4pCY7dOqroY%2Fobakg4w8%3D | US | binary | 471 b | unknown |
1804 | iexplore.exe | GET | 301 | 162.125.66.15:80 | http://dl.dropboxusercontent.com/s/pxxqg90g7zxtt8n/q67jxa0dj1dt.js?ver=1694533035 | DE | — | — | unknown |
1804 | iexplore.exe | GET | 200 | 184.24.77.202:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8957bee211228715 | DE | compressed | 4.66 Kb | unknown |
1804 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | binary | 471 b | unknown |
556 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1804 | iexplore.exe | 162.125.66.15:80 | dl.dropboxusercontent.com | DROPBOX | DE | malicious |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1804 | iexplore.exe | 162.125.66.15:443 | dl.dropboxusercontent.com | DROPBOX | DE | malicious |
1804 | iexplore.exe | 184.24.77.202:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1804 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
556 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
556 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.dropboxusercontent.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1804 | iexplore.exe | Misc activity | ET INFO DropBox User Content Domain (dl .dropboxusercontent .com in TLS SNI) |
1804 | iexplore.exe | Misc activity | ET INFO DropBox User Content Download Access over SSL M2 |