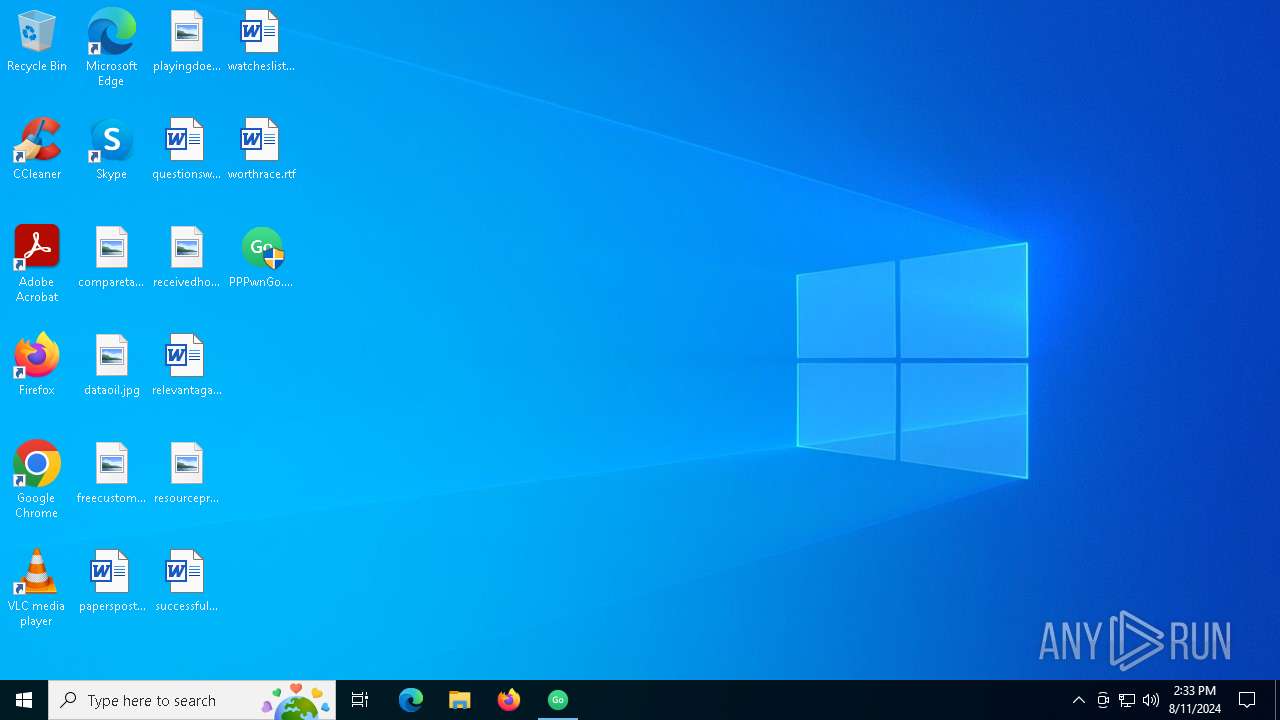
| File name: | PPPwnGo.exe |
| Full analysis: | https://app.any.run/tasks/c7d35bbc-91db-473a-806f-249819290592 |
| Verdict: | Malicious activity |
| Analysis date: | August 11, 2024, 14:32:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 1F2E533441F0511252C4505C10143463 |
| SHA1: | 3A2258599939CC746BDA3DC88A23EE7186CFB828 |
| SHA256: | 70759C183188AEAE174CEEC9F0F7E3FF317A96C305AACC41E2AD851A1DF8E366 |
| SSDEEP: | 3072:f2IbKDzvyeAFIkoYFZigGVmvQCXeWFeqFQd/gW:azvyeAFIkog3GV+QCXkqFQJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
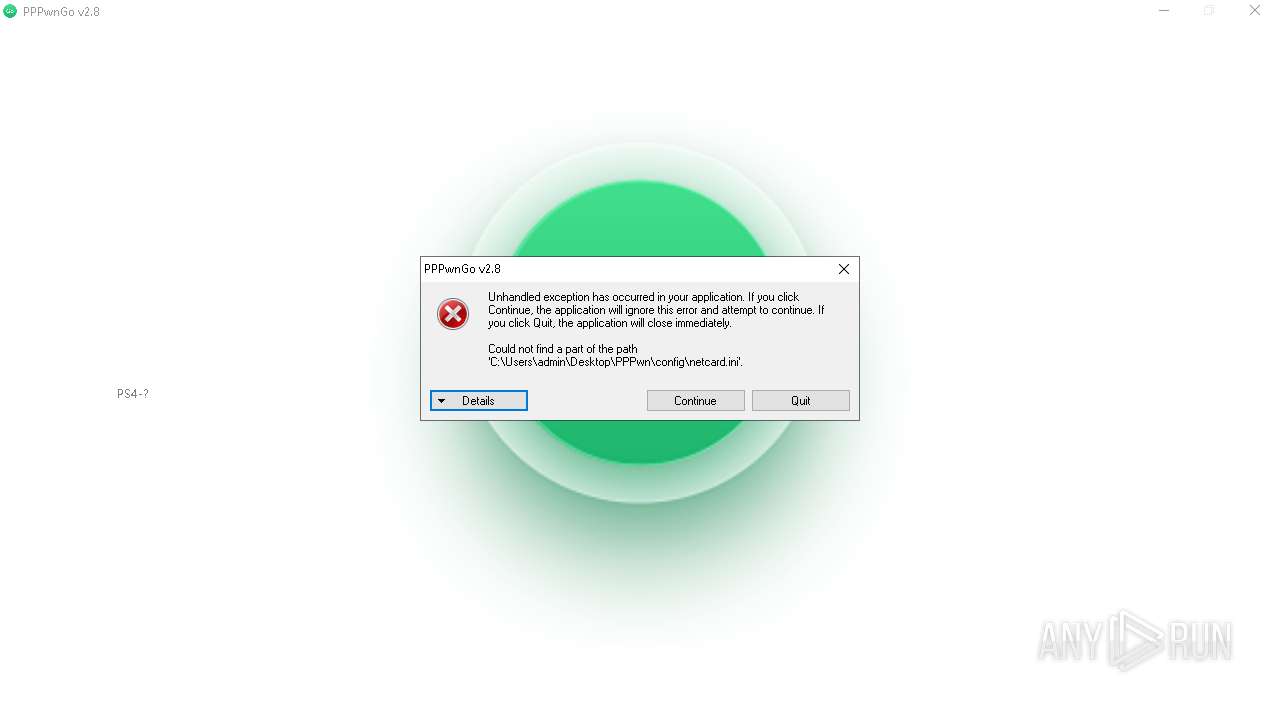
Drops the executable file immediately after the start
- PPPwnGo.exe (PID: 6452)
Starts CMD.EXE for commands execution
- PPPwnGo.exe (PID: 6452)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 7076)
- cmd.exe (PID: 6240)
- cmd.exe (PID: 304)
- cmd.exe (PID: 5796)
- cmd.exe (PID: 6396)
- cmd.exe (PID: 5052)
- cmd.exe (PID: 2636)
- cmd.exe (PID: 1132)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 6540)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 6668)
INFO
Checks supported languages
- PPPwnGo.exe (PID: 6452)
- ShellExperienceHost.exe (PID: 6668)
Reads the machine GUID from the registry
- PPPwnGo.exe (PID: 6452)
Reads Environment values
- PPPwnGo.exe (PID: 6452)
Reads the computer name
- PPPwnGo.exe (PID: 6452)
- ShellExperienceHost.exe (PID: 6668)
Disables trace logs
- netsh.exe (PID: 7128)
- netsh.exe (PID: 4064)
- netsh.exe (PID: 360)
- netsh.exe (PID: 5656)
- netsh.exe (PID: 6536)
- netsh.exe (PID: 2852)
- netsh.exe (PID: 964)
- netsh.exe (PID: 7112)
- netsh.exe (PID: 6240)
- netsh.exe (PID: 1372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2047:07:20 00:39:48+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 98304 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x19fbe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.7.0.0 |
| ProductVersionNumber: | 2.7.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
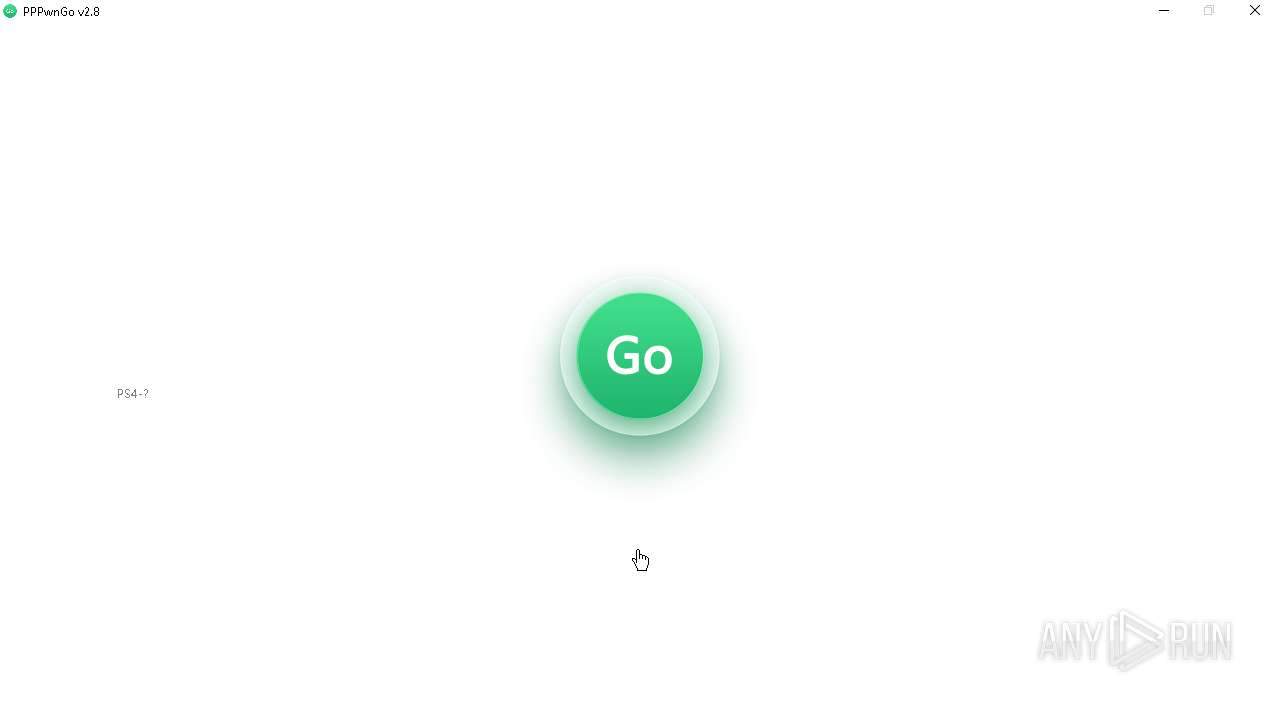
| CompanyName: | PSGO |
| FileDescription: | PPPwnGo |
| FileVersion: | 2.7.0.0 |
| InternalName: | PPPwnGo.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | PPPwnGo.exe |
| ProductName: | PPPwnGo |
| ProductVersion: | 2.7.0.0 |
| AssemblyVersion: | 2.7.0.0 |
Total processes
157
Monitored processes
33
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "cmd.exe" /c netsh interface set interface "Connection" admin=disable | C:\Windows\System32\cmd.exe | — | PPPwnGo.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 360 | netsh interface set interface "Connection" admin=disable | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 964 | netsh interface set interface "Connection" admin=disable | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "cmd.exe" /c netsh interface set interface "Connection" admin=disable | C:\Windows\System32\cmd.exe | — | PPPwnGo.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1372 | netsh interface set interface "Connection" admin=enable | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2636 | "cmd.exe" /c netsh interface set interface "Connection" admin=disable | C:\Windows\System32\cmd.exe | — | PPPwnGo.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2852 | netsh interface set interface "Connection" admin=enable | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4064 | netsh interface set interface "Connection" admin=enable | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 536
Read events
14 535
Write events
1
Delete events
0
Modification events
| (PID) Process: | (6668) ShellExperienceHost.exe | Key: | \REGISTRY\A\{9cb4366d-b6ff-5d73-8e11-726a803790d8}\LocalState |
| Operation: | write | Name: | LastNetworkingFlyoutHeight |
Value: 0000124352A2B55FFBEBDA01 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
24
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1420 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4084 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1420 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4324 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2256 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |