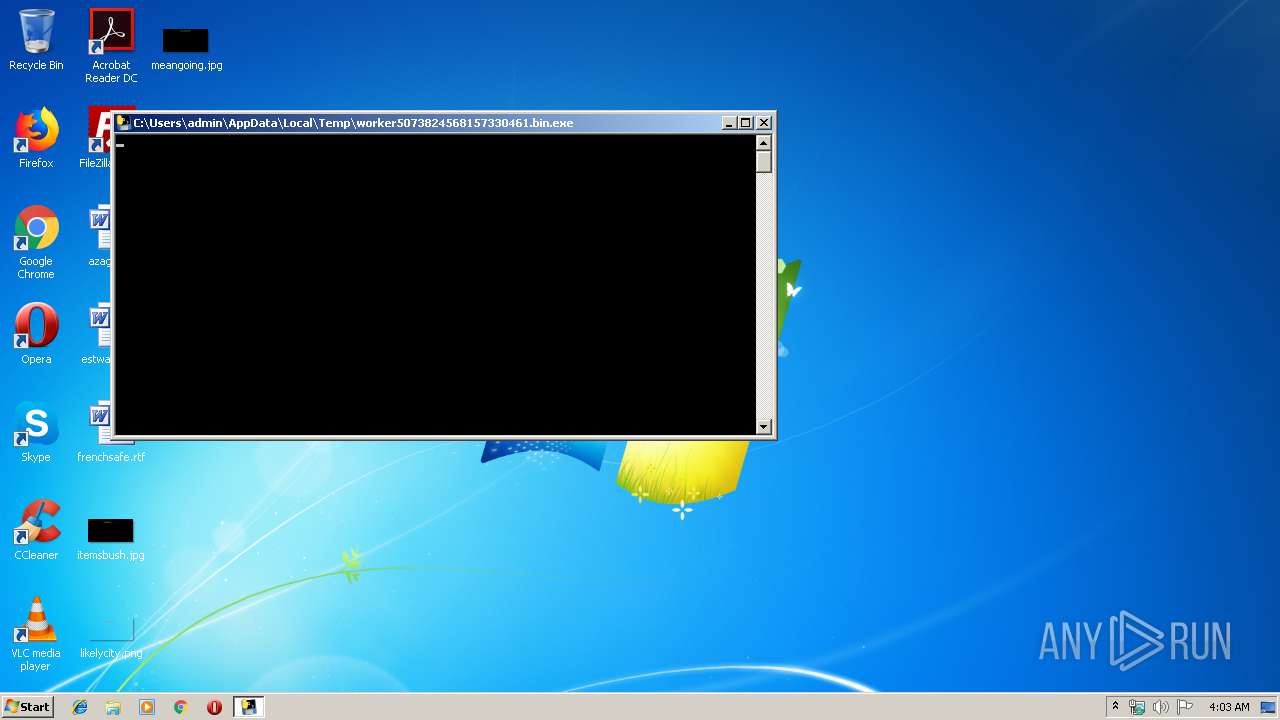
| File name: | worker5073824568157330461.bin |
| Full analysis: | https://app.any.run/tasks/1521fbb5-a767-407b-985a-d6d359268be0 |
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2019, 03:02:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | E3D01098E4B9FFF919EDBA7E2A8739E9 |
| SHA1: | 63B16DFEC23E64B7A8298D5A3B32473072B8CEB7 |
| SHA256: | 7071EA8AD454F54BC611C3ACEA5F08D5514C4214C1AB53E504B52A96093FDB19 |
| SSDEEP: | 98304:aiMRqcAckMX/y5oVeLn/oApIBVeq9EEckBQt8tBkrYmE9jYvOVglqWssiUXnXrgO:9yqlk/ySIx9eEpIQnUmExm1kWss5XrgO |
MALICIOUS
Loads dropped or rewritten executable
- worker5073824568157330461.bin.exe (PID: 2868)
Actions looks like stealing of personal data
- worker5073824568157330461.bin.exe (PID: 2868)
SUSPICIOUS
Creates files in the user directory
- worker5073824568157330461.bin.exe (PID: 2868)
- powershell.exe (PID: 3548)
Executes PowerShell scripts
- worker5073824568157330461.bin.exe (PID: 2868)
Application launched itself
- taskmgr.exe (PID: 3016)
Executable content was dropped or overwritten
- worker5073824568157330461.bin.exe (PID: 3912)
Loads Python modules
- worker5073824568157330461.bin.exe (PID: 2868)
Reads Internet Cache Settings
- powershell.exe (PID: 3548)
INFO
Manual execution by user
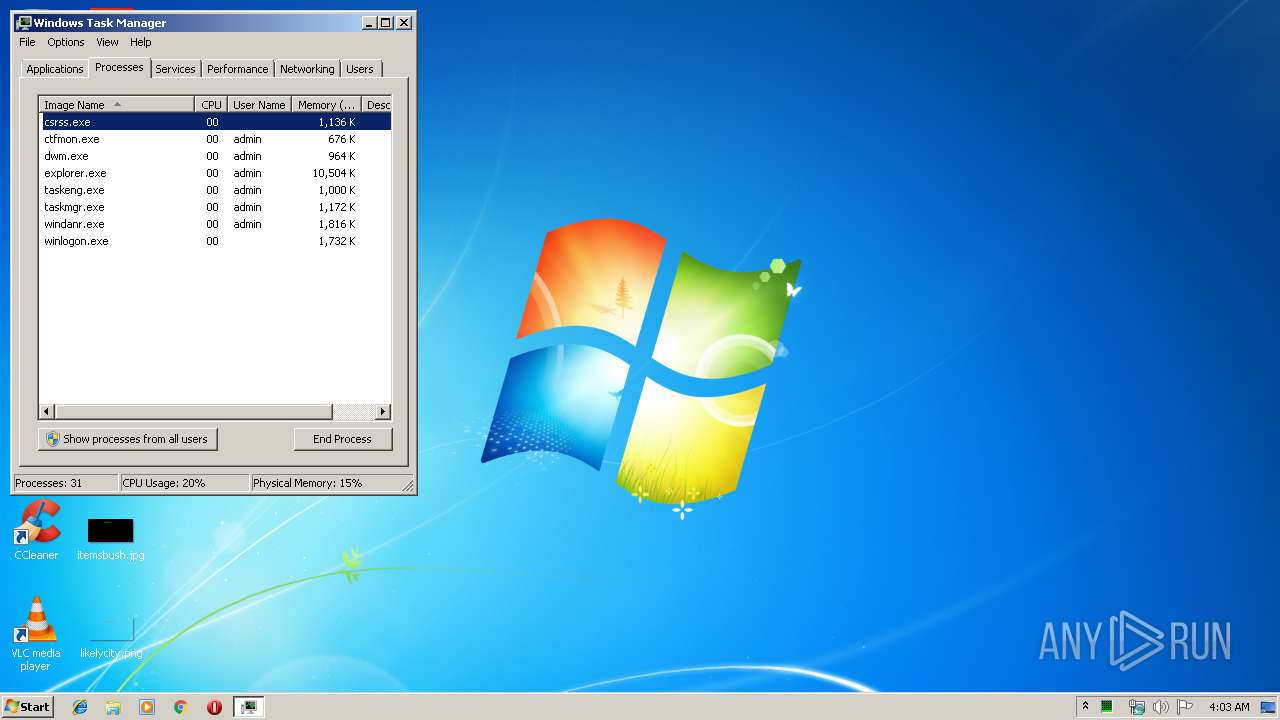
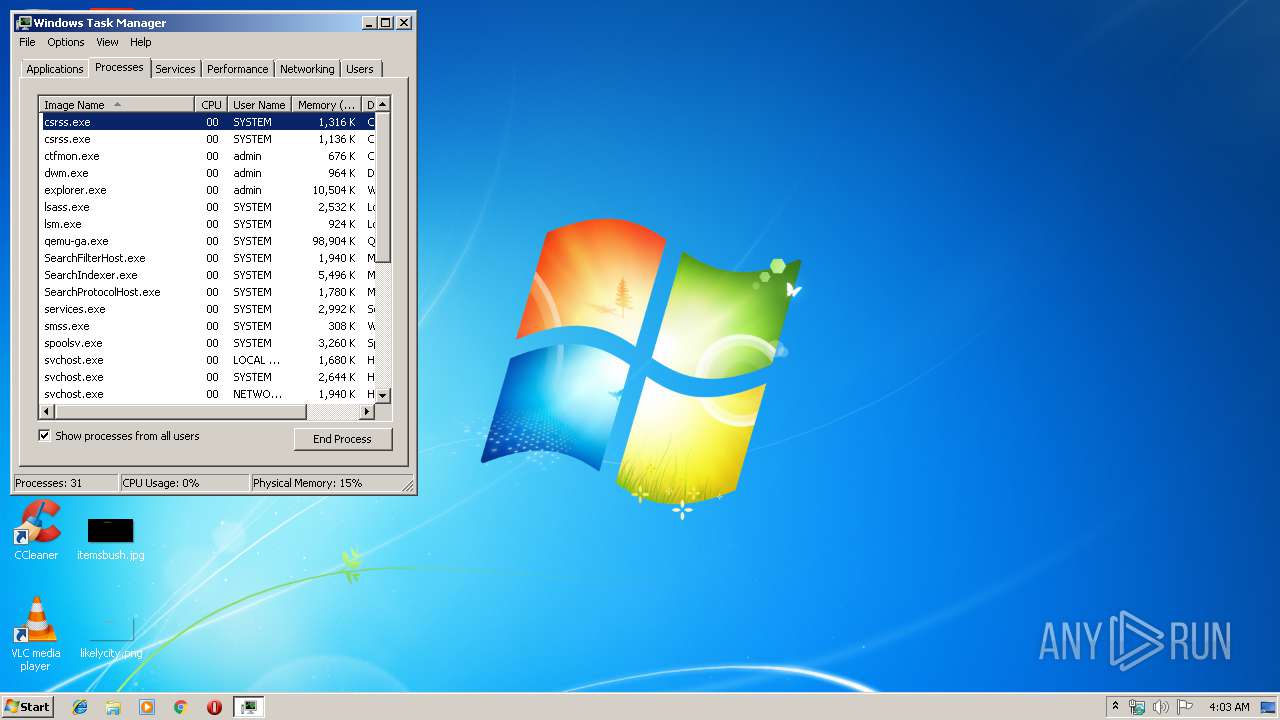
- taskmgr.exe (PID: 3016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:04 16:42:13+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128000 |
| InitializedDataSize: | 172032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x779a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 04-Sep-2018 14:42:13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 04-Sep-2018 14:42:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F224 | 0x0001F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65269 |
.rdata | 0x00021000 | 0x0000B0EC | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10091 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.94098 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.89006 |
.rsrc | 0x0003D000 | 0x0000EA38 | 0x0000EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.29706 |
.reloc | 0x0004C000 | 0x000017B8 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65088 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.58652 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 6.05629 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.5741 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.95079 | 37019 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.29119 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
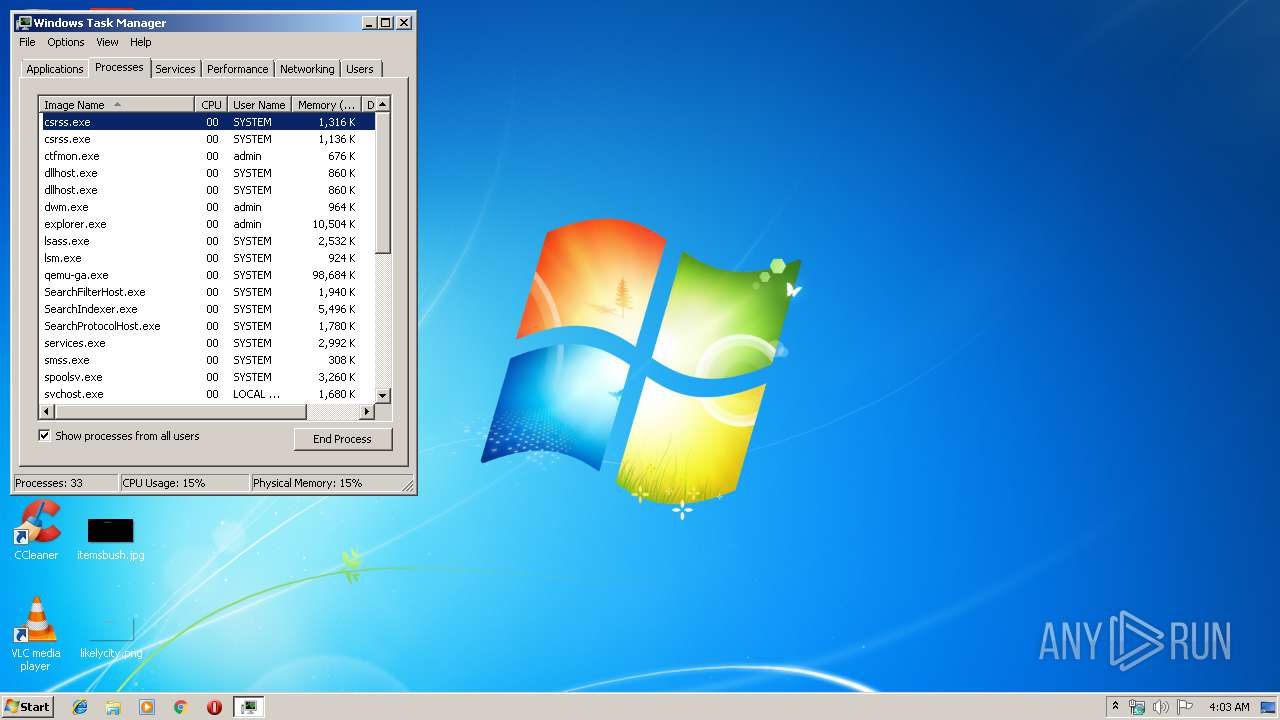
Total processes
40
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2868 | "C:\Users\admin\AppData\Local\Temp\worker5073824568157330461.bin.exe" | C:\Users\admin\AppData\Local\Temp\worker5073824568157330461.bin.exe | worker5073824568157330461.bin.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3016 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3548 | powershell.exe /c " function get-iehistory { [CmdletBinding()] param () $shell = New-Object -ComObject Shell.Application $hist = $shell.NameSpace(34) $folder = $hist.Self $hist.Items() | foreach { if ($_.IsFolder) { $siteFolder = $_.GetFolder $siteFolder.Items() | foreach { $site = $_ if ($site.IsFolder) { $pageFolder = $site.GetFolder $pageFolder.Items() | foreach { $visit = New-Object -TypeName PSObject -Property @{ URL = $($pageFolder.GetDetailsOf($_,0)) } $visit } } } } } } get-iehistory " | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | worker5073824568157330461.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3680 | "C:\Windows\system32\taskmgr.exe" /1 | C:\Windows\system32\taskmgr.exe | taskmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3912 | "C:\Users\admin\AppData\Local\Temp\worker5073824568157330461.bin.exe" | C:\Users\admin\AppData\Local\Temp\worker5073824568157330461.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
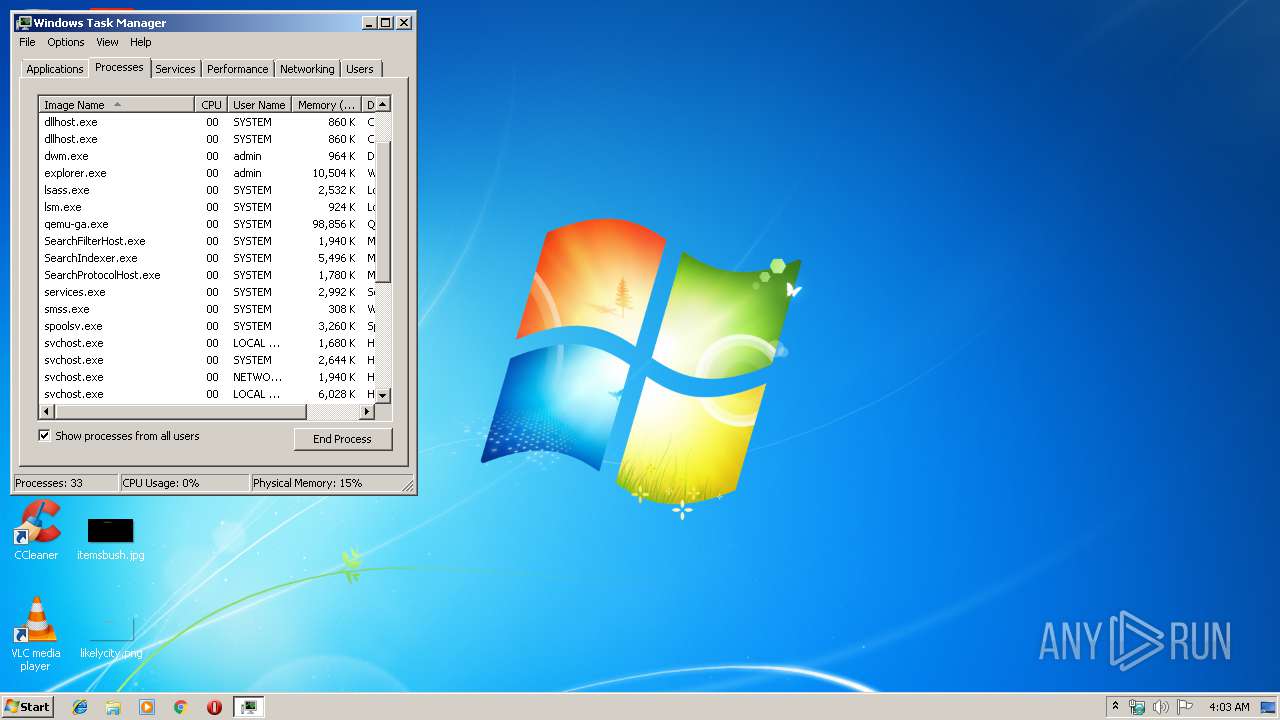
Total events
291
Read events
220
Write events
70
Delete events
1
Modification events
| (PID) Process: | (3548) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3548) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019082620190827 |
| Operation: | write | Name: | CachePath |
Value: %USERPROFILE%\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019082620190827 | |||
| (PID) Process: | (3548) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019082620190827 |
| Operation: | write | Name: | CachePrefix |
Value: :2019082620190827: | |||
| (PID) Process: | (3548) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019082620190827 |
| Operation: | write | Name: | CacheLimit |
Value: 8192 | |||
| (PID) Process: | (3548) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019082620190827 |
| Operation: | write | Name: | CacheOptions |
Value: 11 | |||
| (PID) Process: | (3548) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019082620190827 |
| Operation: | write | Name: | CacheRepair |
Value: 0 | |||
| (PID) Process: | (3548) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019032320190324 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3016) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3016) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3016) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E803000001000000010000000A0000000A000000A2010000F00100000100000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF00000000FFFFFFFF4F00000028000000500000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
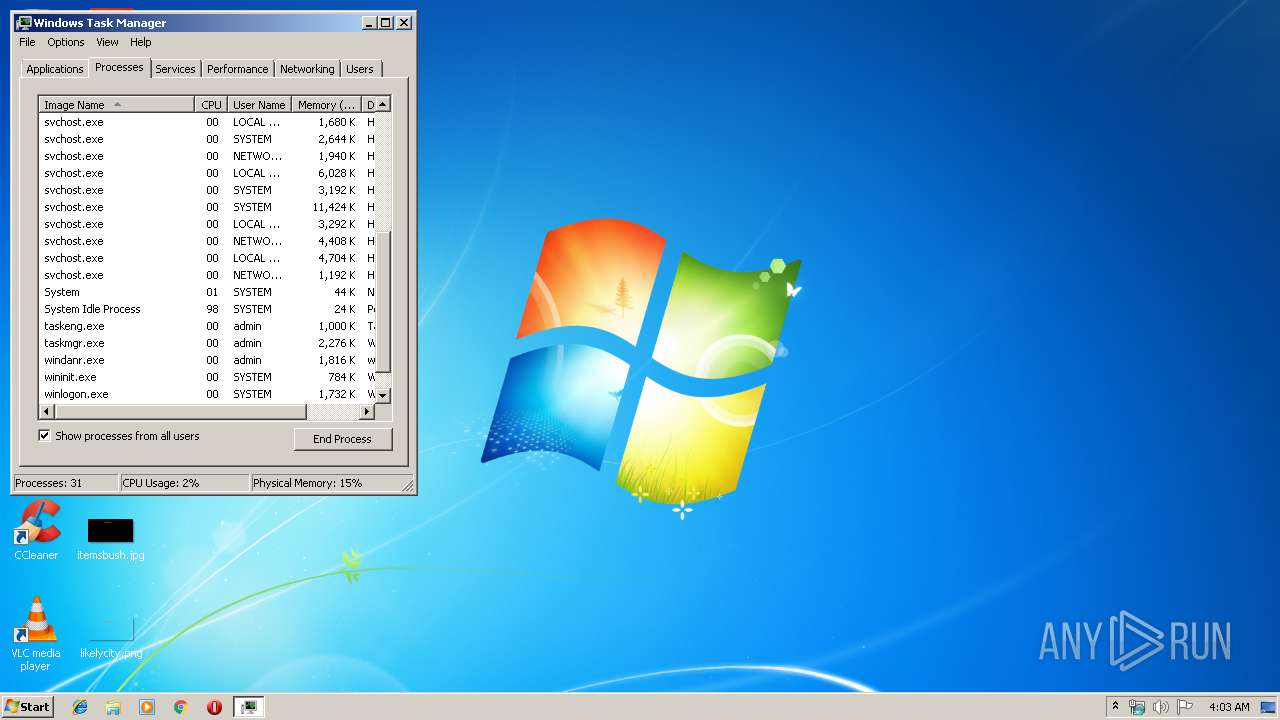
Executable files
17
Suspicious files
2
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2868 | worker5073824568157330461.bin.exe | C:\users\admin\appdata\local\temp\sj6w4v | — | |
MD5:— | SHA256:— | |||
| 2868 | worker5073824568157330461.bin.exe | C:\users\admin\appdata\local\temp\tjjbyxuwy | — | |
MD5:— | SHA256:— | |||
| 3548 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FH87IL0NUTA9J6LEE092.temp | — | |
MD5:— | SHA256:— | |||
| 3912 | worker5073824568157330461.bin.exe | C:\Users\admin\AppData\Local\Temp\_MEI39122\mein.exe.manifest | xml | |
MD5:— | SHA256:— | |||
| 3912 | worker5073824568157330461.bin.exe | C:\Users\admin\AppData\Local\Temp\_MEI39122\sqlite3.dll | executable | |
MD5:C5892E001721B82FFB7A7A03CB13E908 | SHA256:BE889EAD7A0D67F94CDFA20B9E8F21D73B1BB19B5FC7D7403911ED4307C9DBBB | |||
| 3912 | worker5073824568157330461.bin.exe | C:\Users\admin\AppData\Local\Temp\_MEI39122\Crypto.Cipher._AES.pyd | executable | |
MD5:DD3DB5480EB52E8F69D47F3B725E6BFB | SHA256:51054F4D28782B6698B1B6510317650E797E11F87FA29FCEAF8559B6BCBF4DFE | |||
| 3912 | worker5073824568157330461.bin.exe | C:\Users\admin\AppData\Local\Temp\_MEI39122\_ctypes.pyd | executable | |
MD5:7896F2B2B44A6DC7F8021C142339CE07 | SHA256:DA6F2A24EE007F2BA49B120F6253E2030563093B6ABD4514BF81F7F2326AC96A | |||
| 3912 | worker5073824568157330461.bin.exe | C:\Users\admin\AppData\Local\Temp\_MEI39122\_socket.pyd | executable | |
MD5:7B2AAEF4135DF0FD137DF1F152DE1708 | SHA256:00B31446AD5F7038F253B64A60753D07FF082923C108752D565717947F1A38BA | |||
| 3912 | worker5073824568157330461.bin.exe | C:\Users\admin\AppData\Local\Temp\_MEI39122\_multiprocessing.pyd | executable | |
MD5:D675D1F065D2A22EC122375BF8069C1B | SHA256:1B9E81143AADA184ECDA900B93CFFE4A4BBD6820CA4F6D7F32EB46A000B66099 | |||
| 3912 | worker5073824568157330461.bin.exe | C:\Users\admin\AppData\Local\Temp\_MEI39122\_hashlib.pyd | executable | |
MD5:AE0EF46BC3A52A92544B6FACAB0F32A1 | SHA256:61372337FE96D67F92BCB44E6FAEEFB7FE404A326F819EA33E27D33DB98226F5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report