| File name: | RemoteMouse.exe |
| Full analysis: | https://app.any.run/tasks/76c785c0-285c-4bfd-800b-97cb51ce4480 |
| Verdict: | Malicious activity |
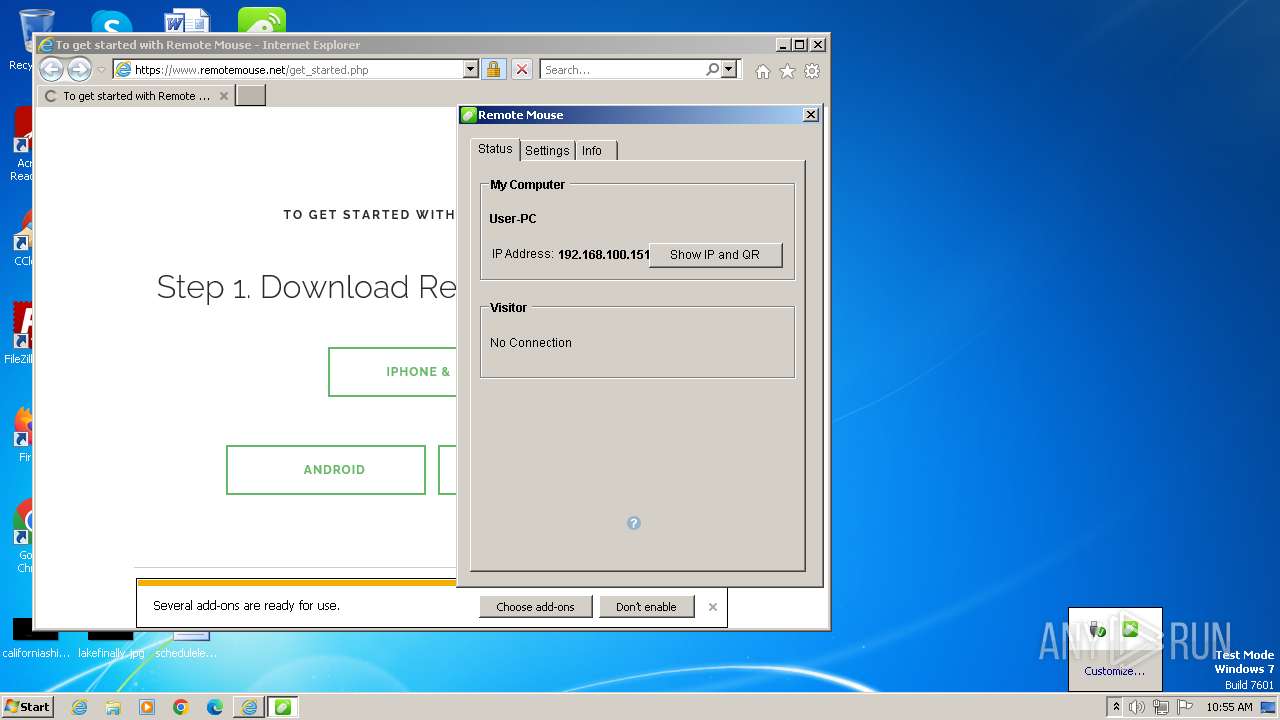
| Analysis date: | November 25, 2023, 10:54:17 |
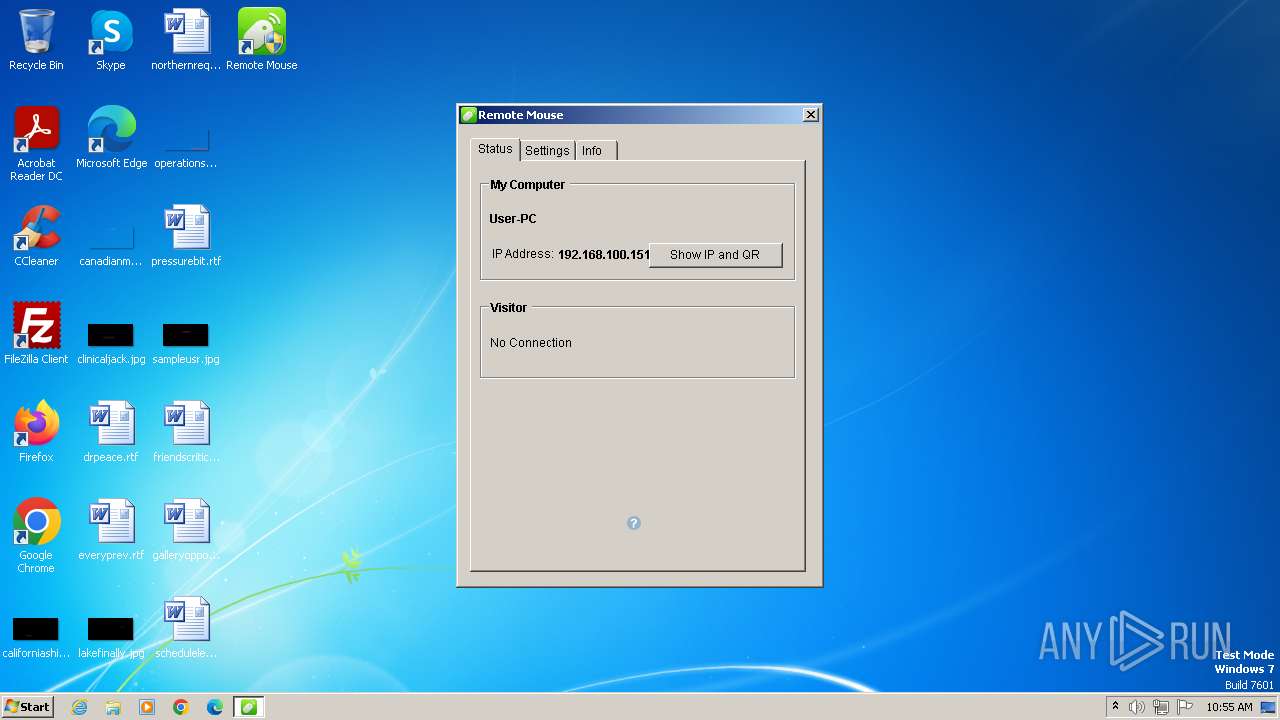
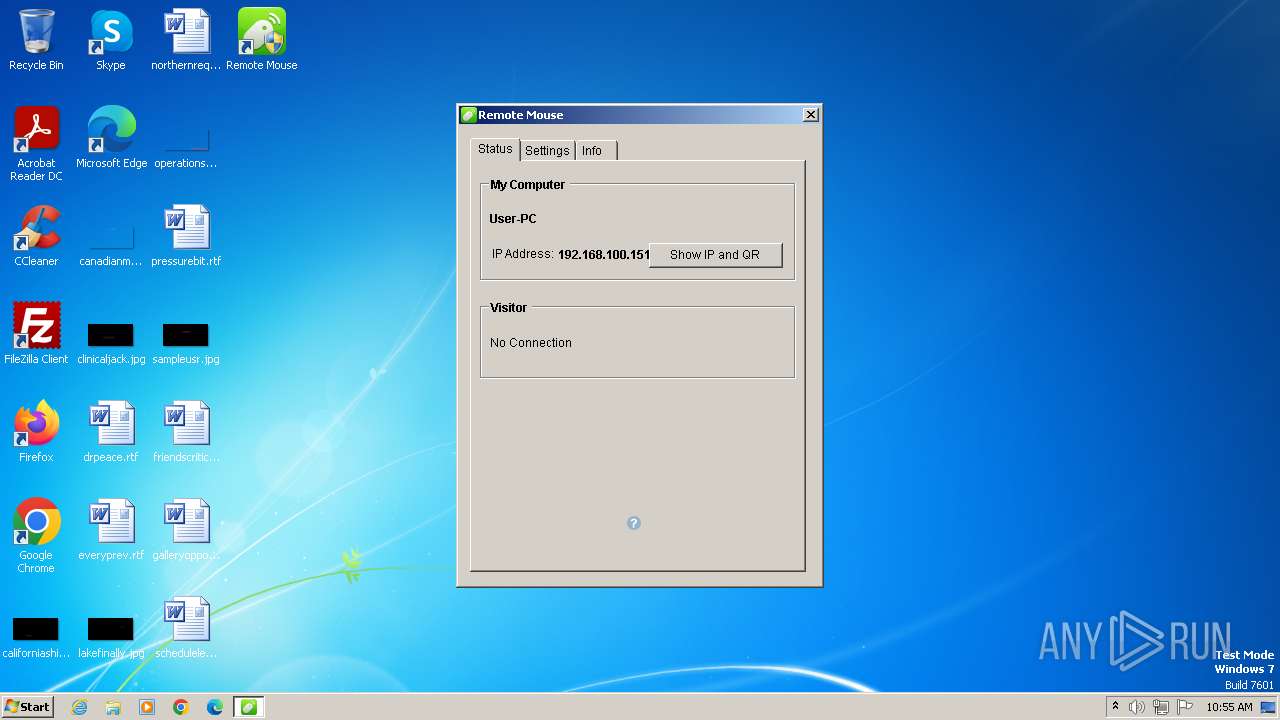
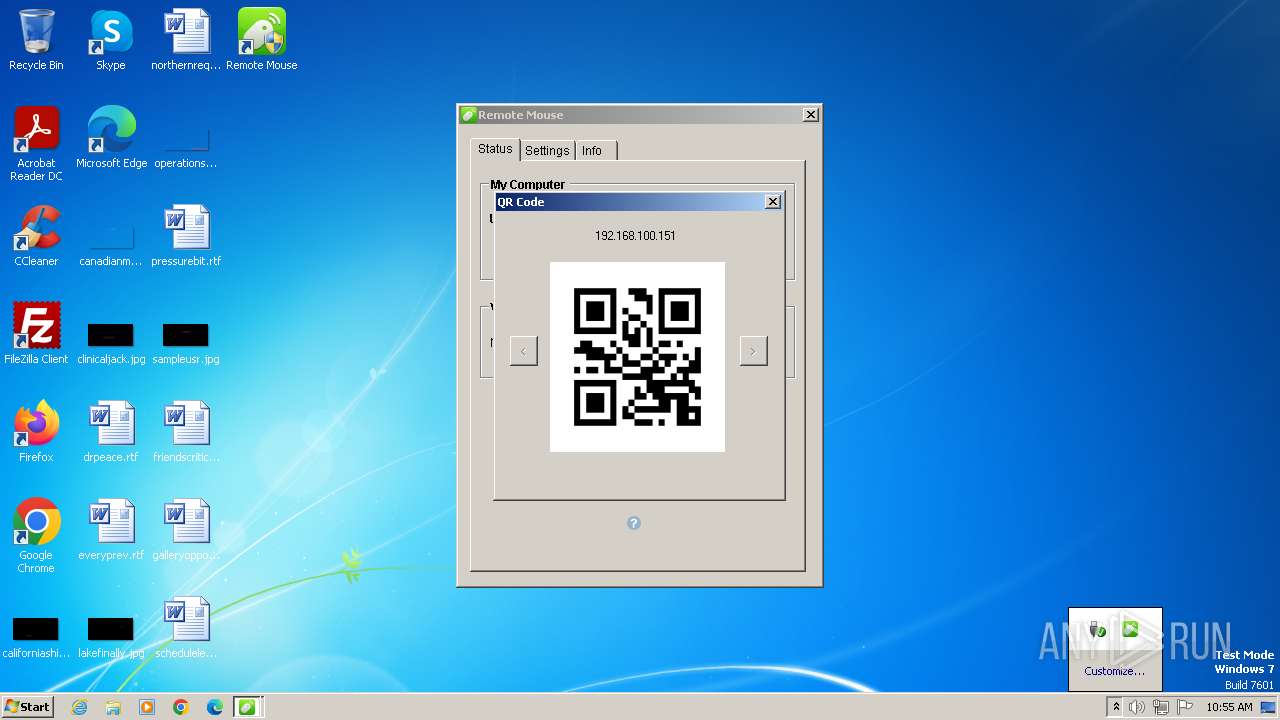
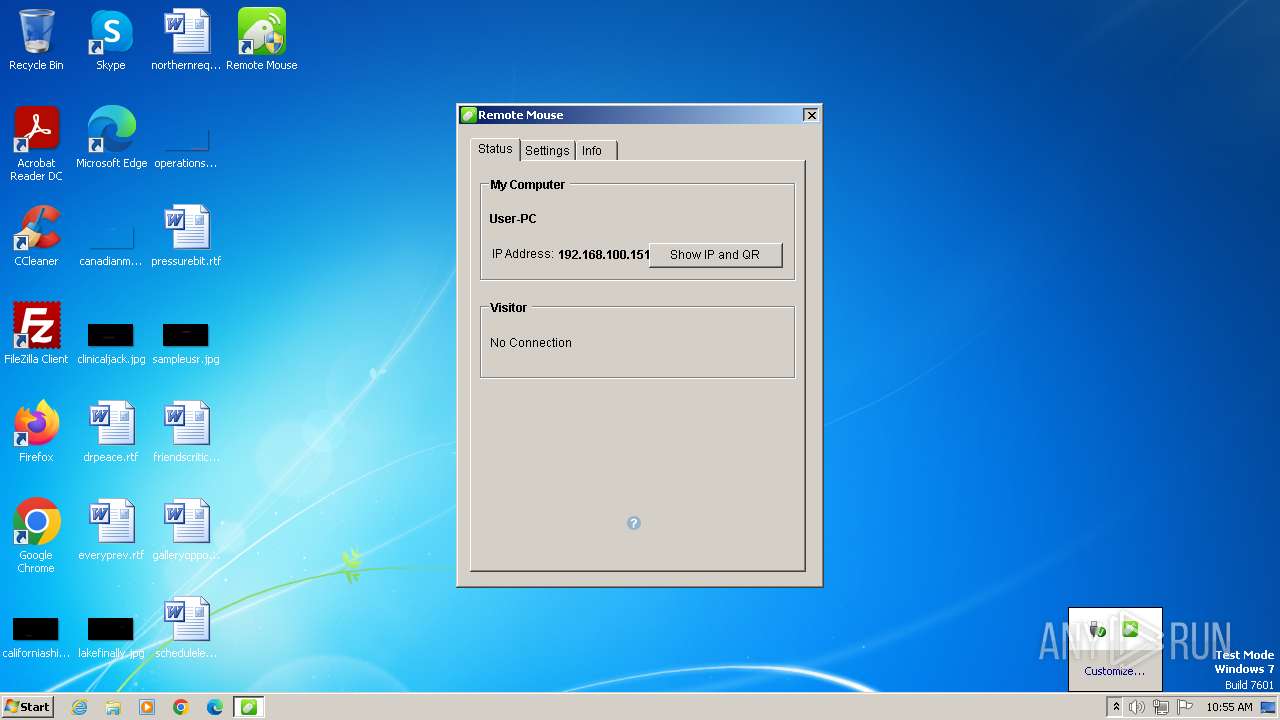
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 82BDBD98358B28B05A65F8BE37979FF2 |
| SHA1: | 8C9E1B71C3A72CF6EB006C41E90F8990E920CE09 |
| SHA256: | 705536708E71583D67BA1EB75011FB8DCA771900CDB8036A1BE24D023C70AC9B |
| SSDEEP: | 49152:Nqe3f6e5qU/798Jnkw+DidXvh6dS/04OOR5QvuE:cSie5T/7E+DidXvh6d204OOR5quE |
MALICIOUS
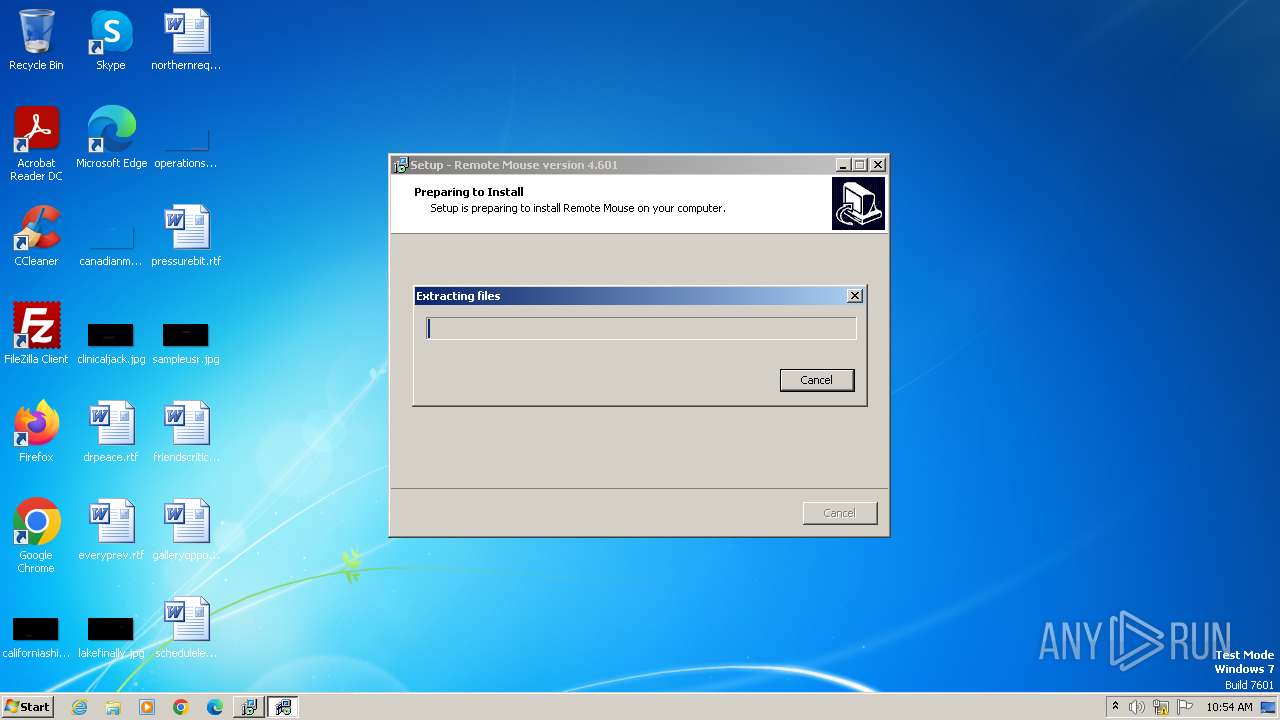
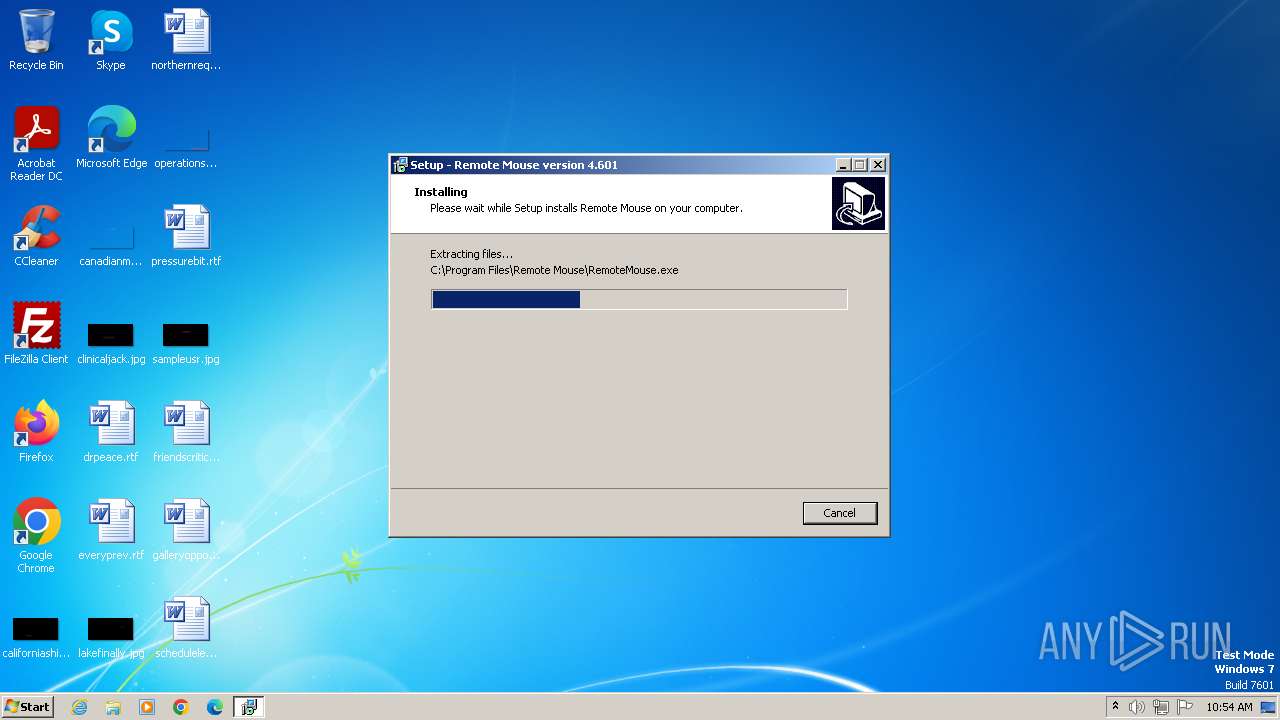
Drops the executable file immediately after the start
- RemoteMouse.exe (PID: 948)
- RemoteMouse.exe (PID: 3008)
- RemoteMouse.tmp (PID: 1988)
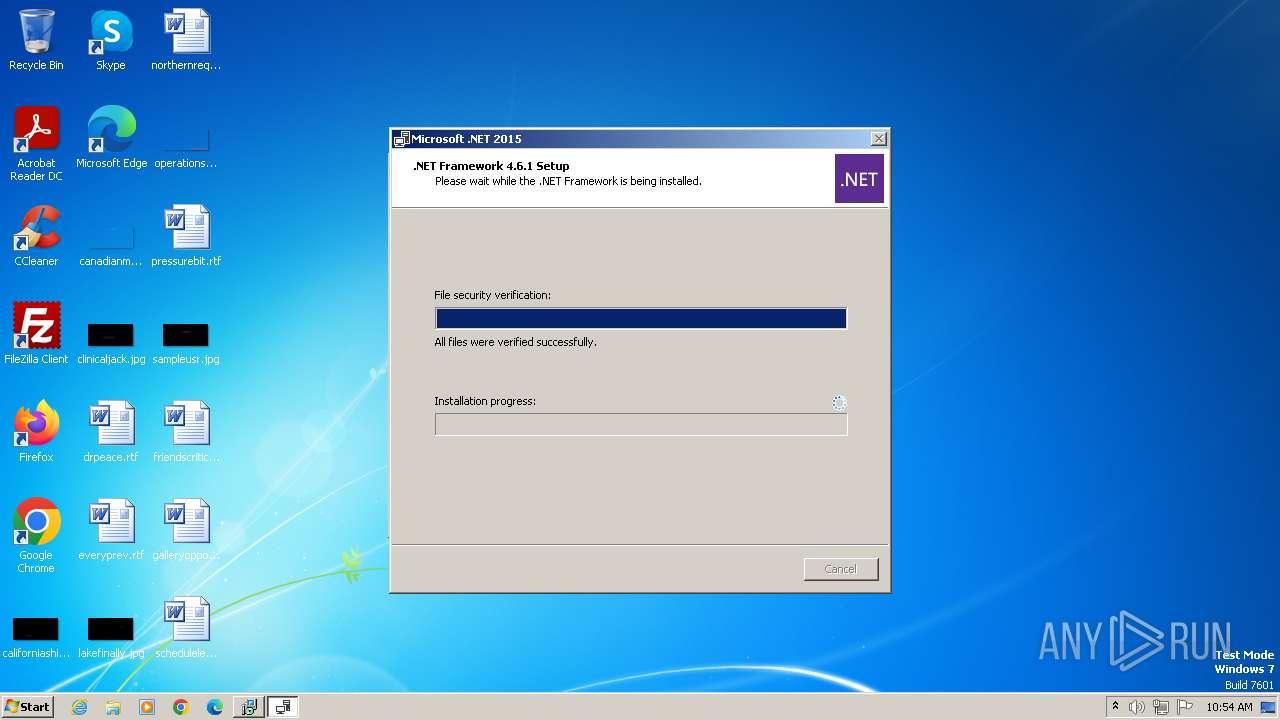
- NetFrameworkInstaller.exe (PID: 3836)
Creates a writable file in the system directory
- RemoteMouseCore.exe (PID: 3656)
- ie4uinit.exe (PID: 3220)
- msedge.exe (PID: 296)
- iexplore.exe (PID: 3268)
- iexplore.exe (PID: 1820)
- iexplore.exe (PID: 2848)
- iexplore.exe (PID: 1212)
- iexplore.exe (PID: 664)
- rundll32.exe (PID: 3932)
- rundll32.exe (PID: 1992)
- rundll32.exe (PID: 3624)
SUSPICIOUS
Reads the Windows owner or organization settings
- RemoteMouse.tmp (PID: 1988)
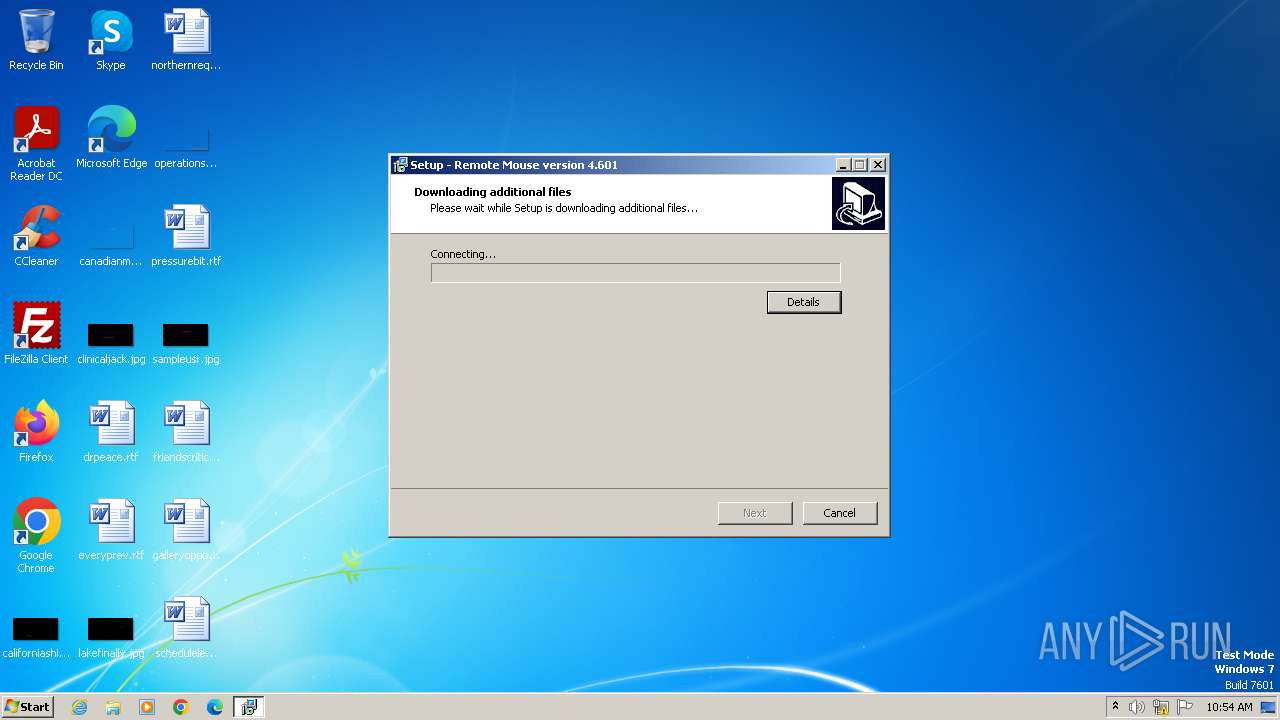
Reads the Internet Settings
- RemoteMouse.tmp (PID: 1988)
- Setup.exe (PID: 2868)
Checks Windows Trust Settings
- RemoteMouse.tmp (PID: 1988)
- Setup.exe (PID: 2868)
Process drops legitimate windows executable
- RemoteMouse.tmp (PID: 1988)
- NetFrameworkInstaller.exe (PID: 3836)
Starts SC.EXE for service management
- RemoteMouse.tmp (PID: 1988)
Reads security settings of Internet Explorer
- RemoteMouse.tmp (PID: 1988)
- Setup.exe (PID: 2868)
Reads settings of System Certificates
- RemoteMouse.tmp (PID: 1988)
- Setup.exe (PID: 2868)
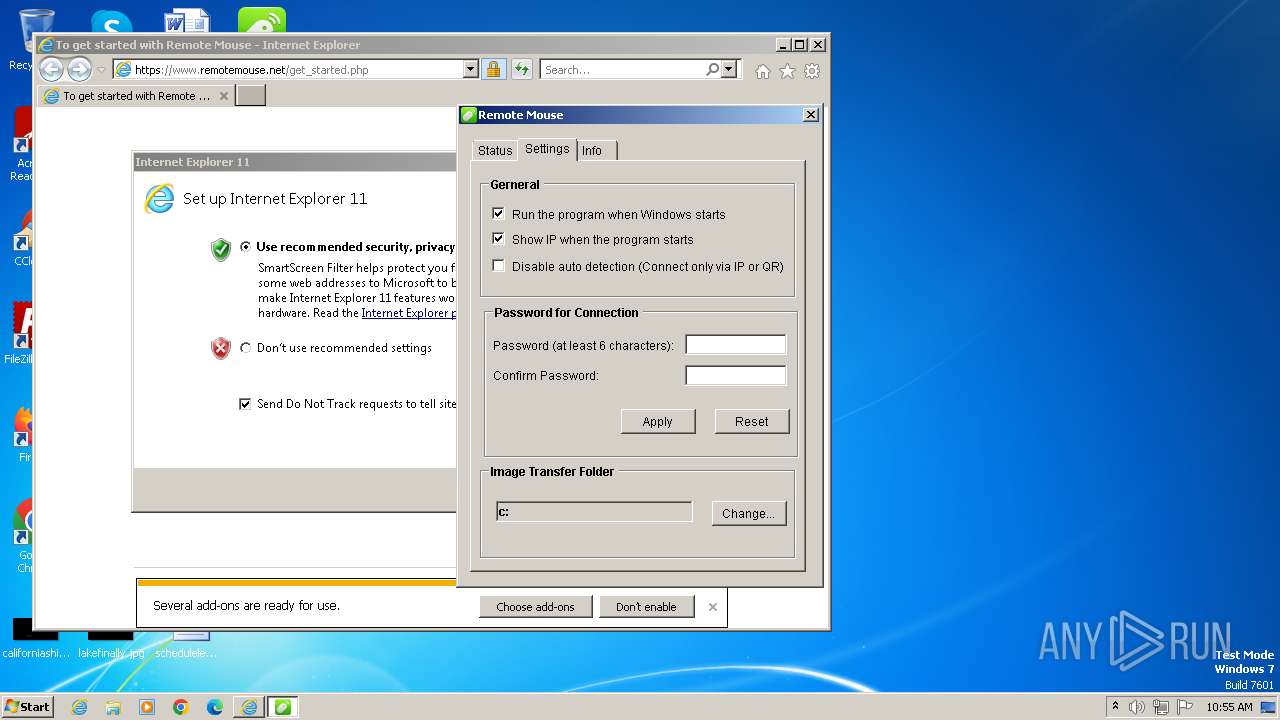
Uses NETSH.EXE to add a firewall rule or allowed programs
- RemoteMouse.tmp (PID: 1988)
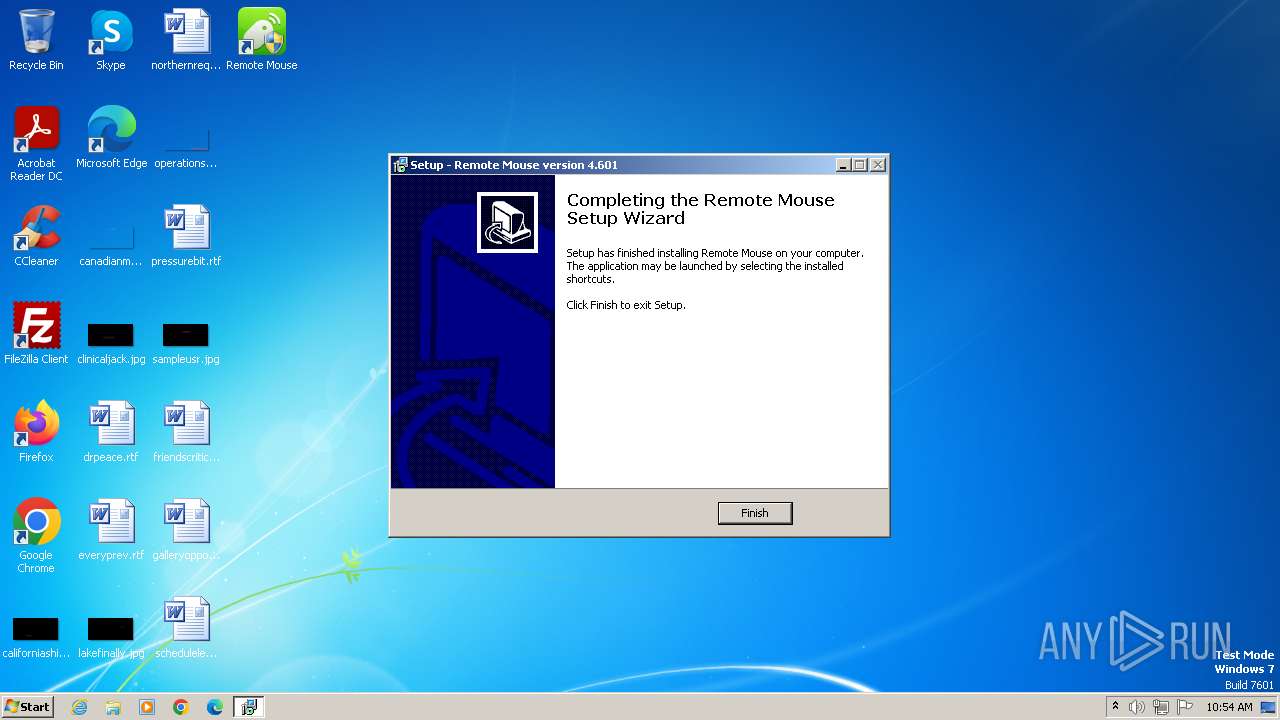
Executes as Windows Service
- RemoteMouseService.exe (PID: 4008)
Write to the desktop.ini file (may be used to cloak folders)
- ie4uinit.exe (PID: 3220)
Reads Microsoft Outlook installation path
- rundll32.exe (PID: 3932)
- rundll32.exe (PID: 1992)
- rundll32.exe (PID: 3640)
- rundll32.exe (PID: 2432)
- rundll32.exe (PID: 2308)
- rundll32.exe (PID: 3624)
Uses RUNDLL32.EXE to load library
- iexplore.exe (PID: 3268)
- iexplore.exe (PID: 664)
INFO
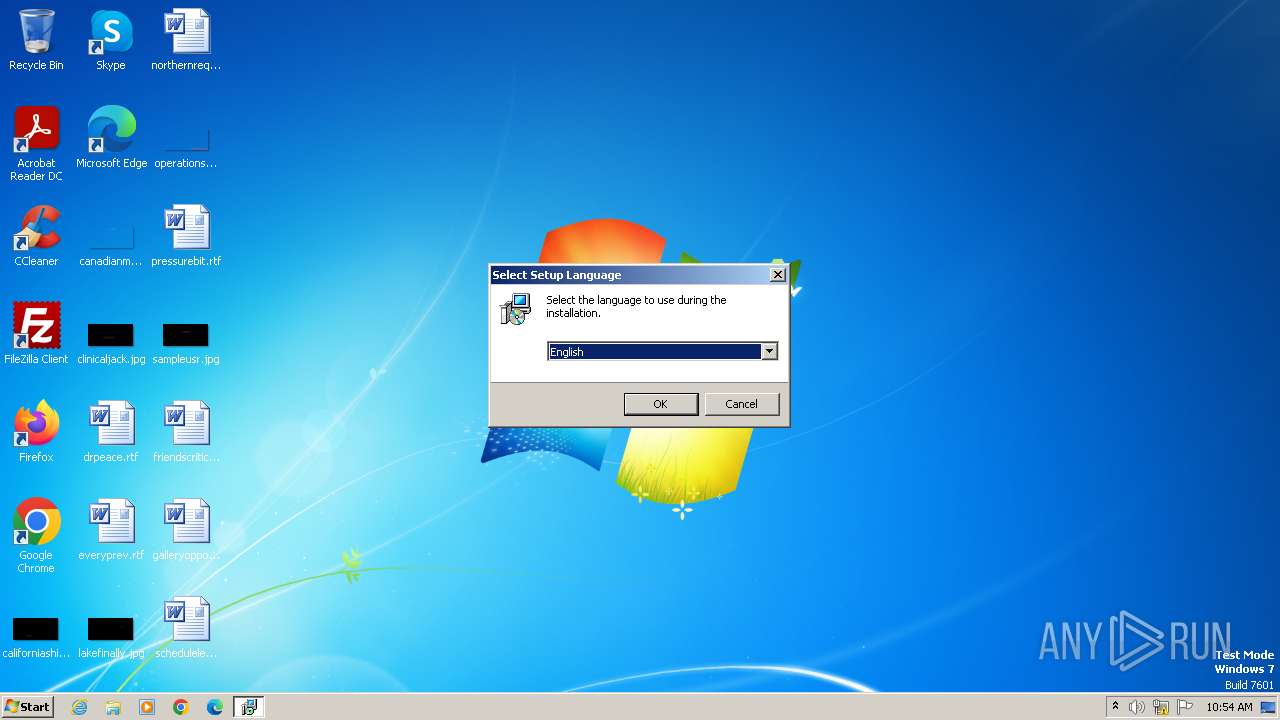
Checks supported languages
- RemoteMouse.exe (PID: 948)
- RemoteMouse.tmp (PID: 2980)
- RemoteMouse.exe (PID: 3008)
- RemoteMouse.tmp (PID: 1988)
- NetFrameworkInstaller.exe (PID: 3836)
- Setup.exe (PID: 2868)
- wmpnscfg.exe (PID: 3144)
- SetupUtility.exe (PID: 2444)
- SetupUtility.exe (PID: 3084)
- SetupUtility.exe (PID: 2072)
- GetUserProfilePath.exe (PID: 3092)
- RemoteMouseService.exe (PID: 4008)
- RemoteMouse.exe (PID: 3752)
- RemoteMouseCore.exe (PID: 3656)
Reads the computer name
- RemoteMouse.tmp (PID: 2980)
- RemoteMouse.tmp (PID: 1988)
- NetFrameworkInstaller.exe (PID: 3836)
- wmpnscfg.exe (PID: 3144)
- Setup.exe (PID: 2868)
- SetupUtility.exe (PID: 2072)
- SetupUtility.exe (PID: 3084)
- GetUserProfilePath.exe (PID: 3092)
- RemoteMouseService.exe (PID: 4008)
- RemoteMouseCore.exe (PID: 3656)
- SetupUtility.exe (PID: 2444)
- RemoteMouse.exe (PID: 3752)
Create files in a temporary directory
- RemoteMouse.exe (PID: 948)
- RemoteMouse.exe (PID: 3008)
- RemoteMouse.tmp (PID: 1988)
- NetFrameworkInstaller.exe (PID: 3836)
- Setup.exe (PID: 2868)
- SetupUtility.exe (PID: 2444)
Checks proxy server information
- RemoteMouse.tmp (PID: 1988)
Reads the machine GUID from the registry
- RemoteMouse.tmp (PID: 1988)
- NetFrameworkInstaller.exe (PID: 3836)
- wmpnscfg.exe (PID: 3144)
- Setup.exe (PID: 2868)
- SetupUtility.exe (PID: 2444)
- SetupUtility.exe (PID: 3084)
- GetUserProfilePath.exe (PID: 3092)
- RemoteMouseCore.exe (PID: 3656)
- RemoteMouse.exe (PID: 3752)
Creates files or folders in the user directory
- RemoteMouse.tmp (PID: 1988)
Manual execution by a user
- wmpnscfg.exe (PID: 3144)
Reads CPU info
- Setup.exe (PID: 2868)
Reads Environment values
- Setup.exe (PID: 2868)
- RemoteMouse.exe (PID: 3752)
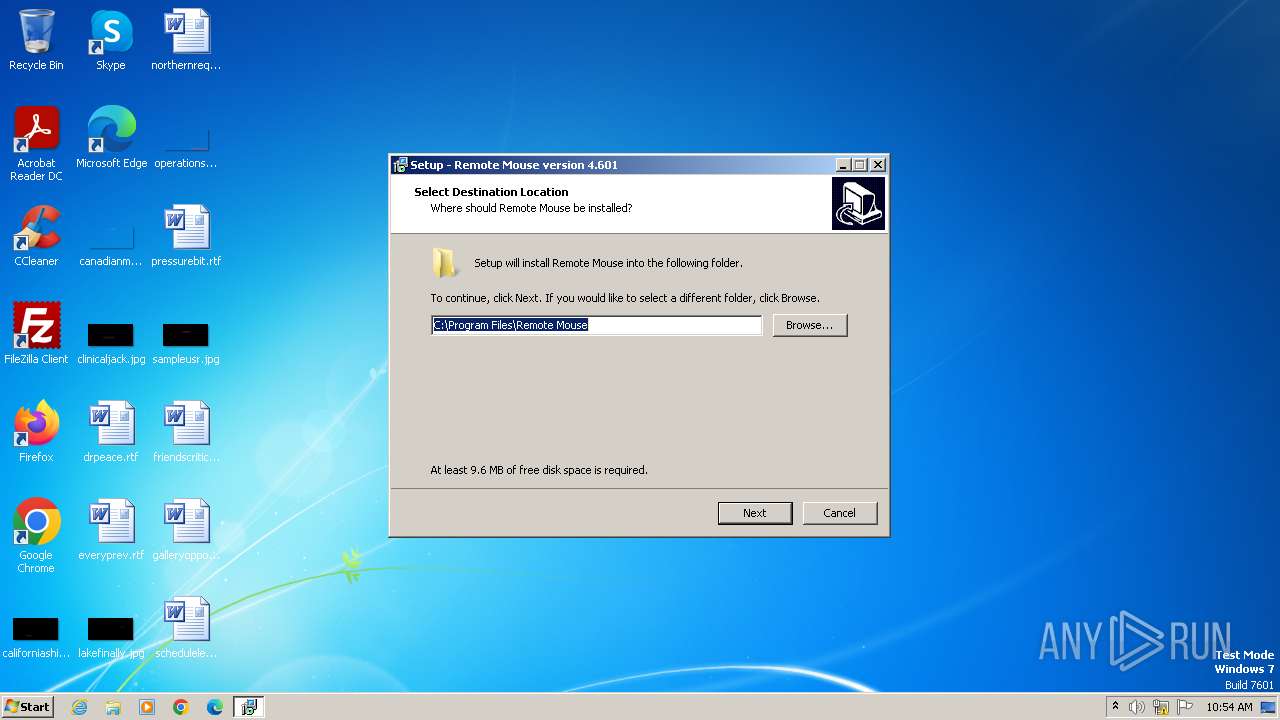
Creates files in the program directory
- RemoteMouse.tmp (PID: 1988)
- GetUserProfilePath.exe (PID: 3092)
Reads product name
- RemoteMouse.exe (PID: 3752)
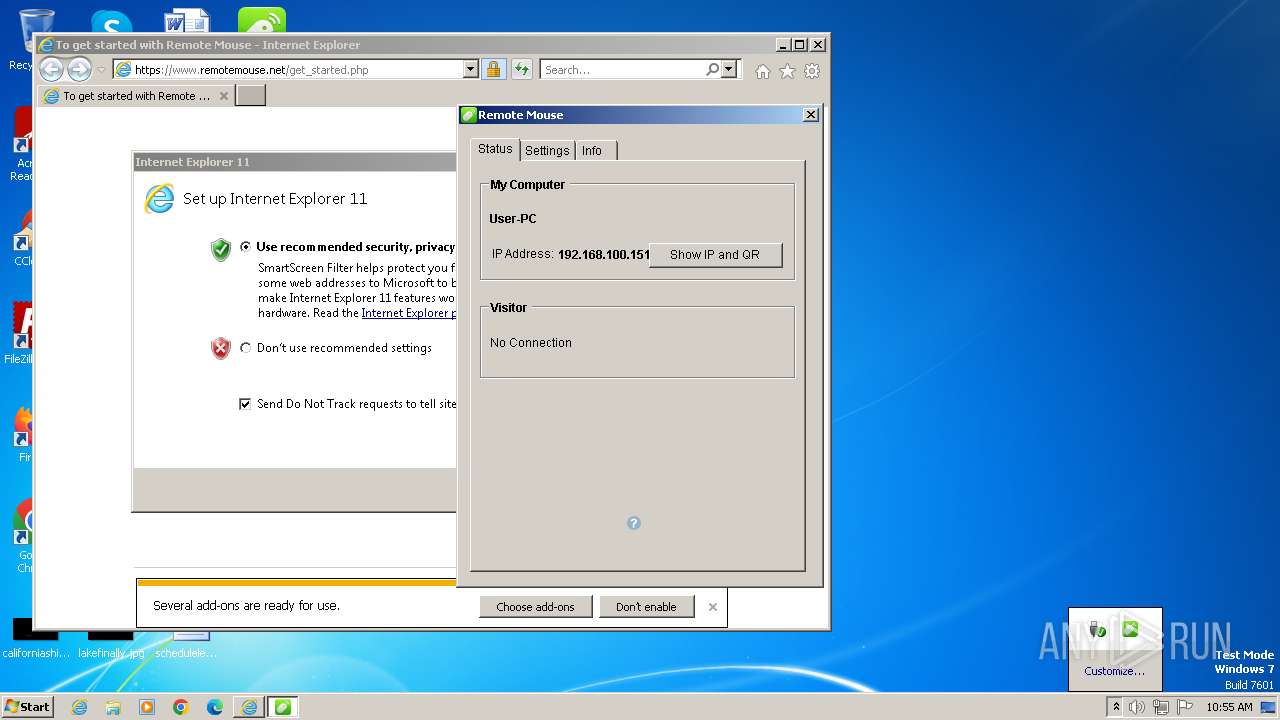
Application launched itself
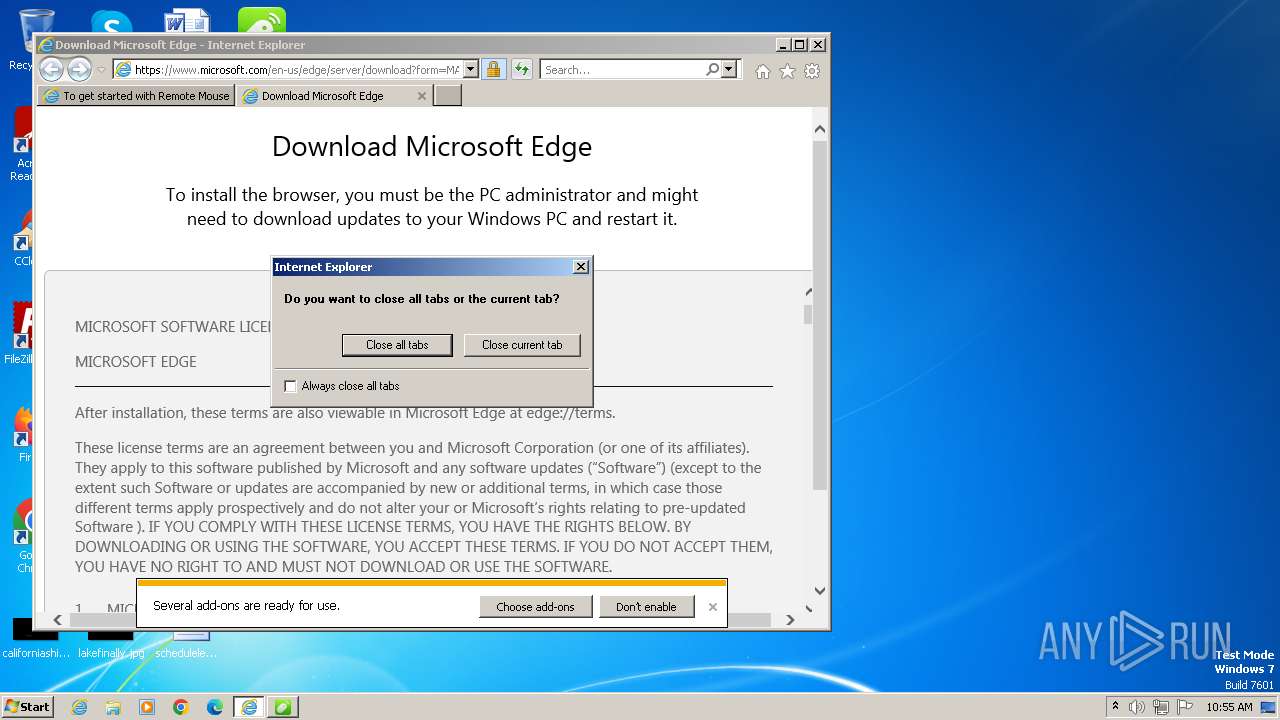
- iexplore.exe (PID: 3268)
- msedge.exe (PID: 296)
- iexplore.exe (PID: 664)
- msedge.exe (PID: 2716)
Write to the desktop.ini file (may be used to cloak folders)
- iexplore.exe (PID: 3268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (51.8) |
|---|---|---|
| .exe | | | InstallShield setup (20.3) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:15 10:48:30+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741376 |
| InitializedDataSize: | 38400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
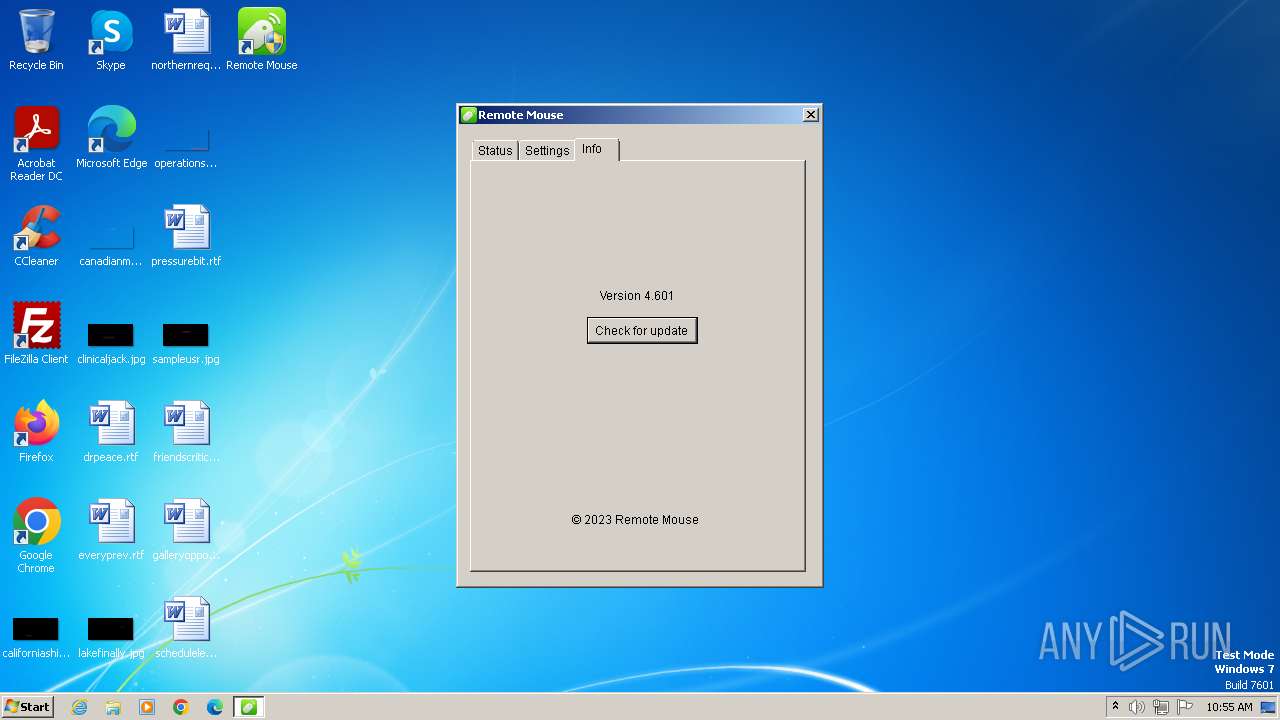
| CompanyName: | Remote Mouse |
| FileDescription: | Remote Mouse Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | Remote Mouse |
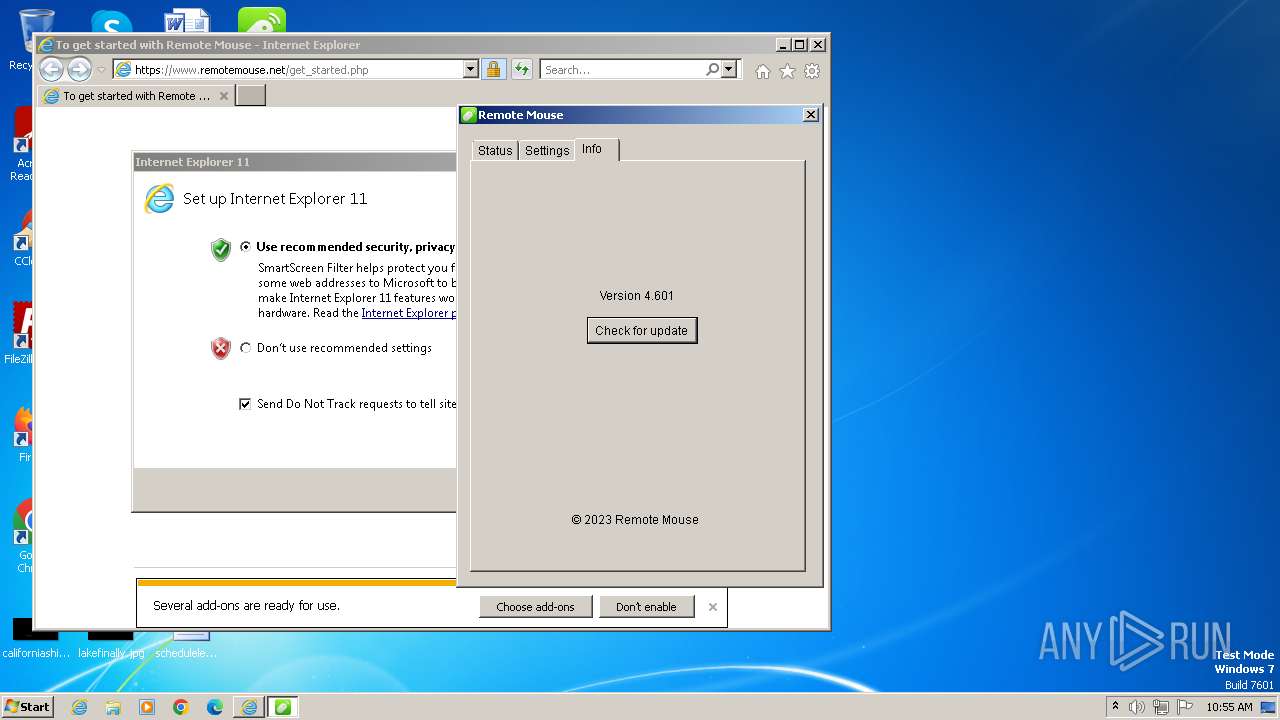
| ProductVersion: | 4.601 |
Total processes
87
Monitored processes
38
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Windows\System32\sc.exe" stop RemoteMouseService | C:\Windows\System32\sc.exe | — | RemoteMouse.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
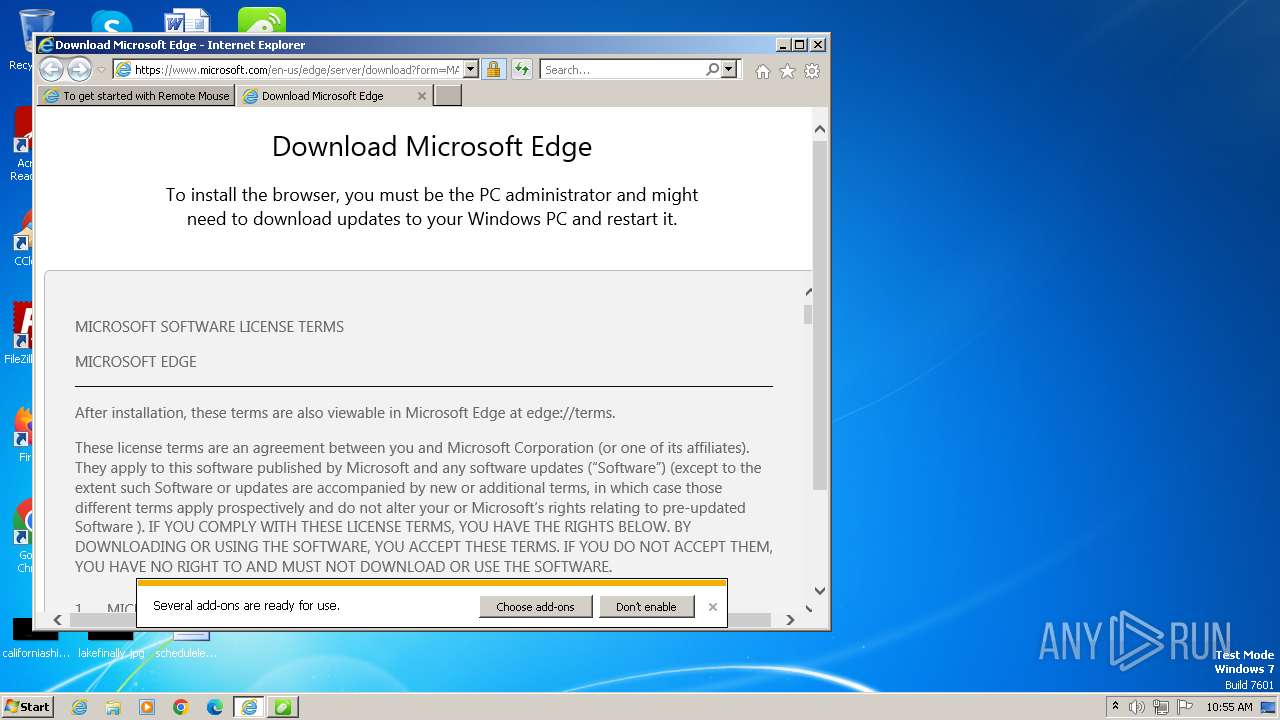
| 296 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --from-ie-to-edge=3 --ie-frame-hwnd=801be | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | ie_to_edge_stub.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Edge Exit code: 1002 Version: 109.0.1518.115 Modules
| |||||||||||||||
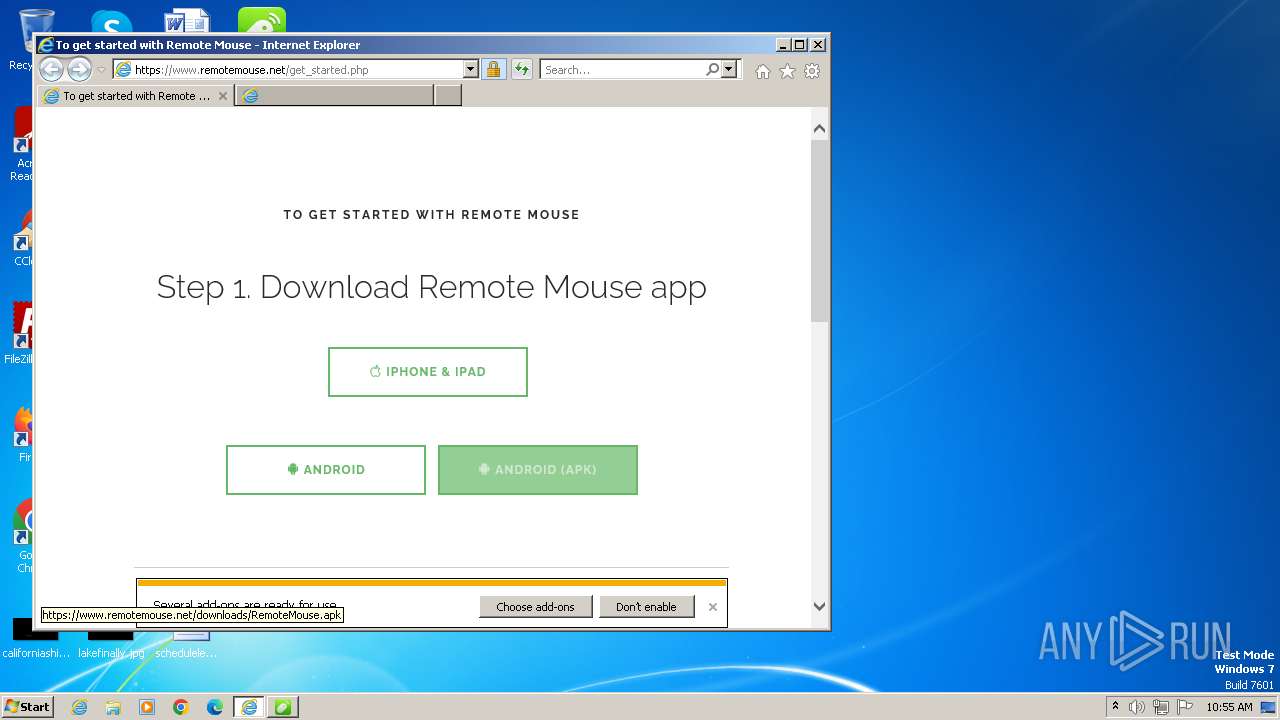
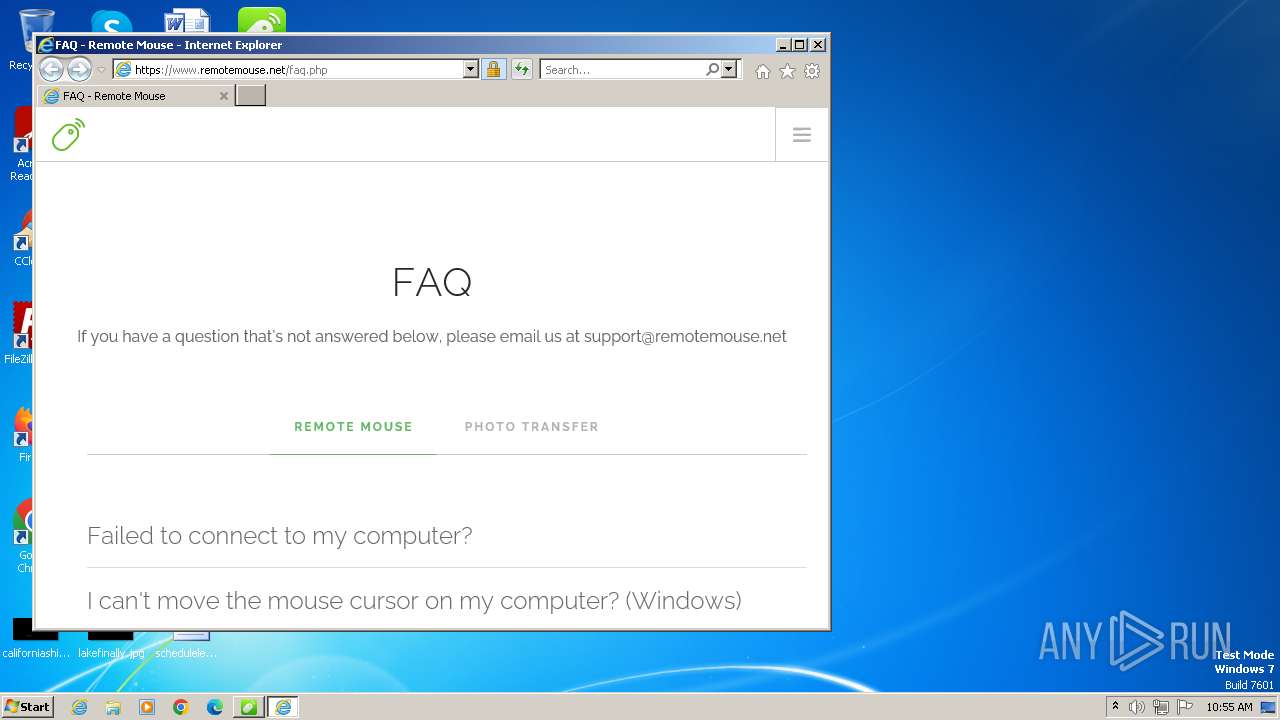
| 664 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.remotemouse.net/faq.php | C:\Program Files\Internet Explorer\iexplore.exe | RemoteMouse.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 880 | "C:\Windows\system32\netsh.exe" firewall add allowedprogram "C:\Program Files\Remote Mouse\RemoteMouse.exe" "Remote Mouse" ENABLE ALL | C:\Windows\System32\netsh.exe | — | RemoteMouse.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 900 | "C:\Windows\system32\sc.exe" create RemoteMouseService binPath= "C:\Program Files\Remote Mouse\RemoteMouseService.exe" start= auto | C:\Windows\System32\sc.exe | — | RemoteMouse.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | "C:\Users\admin\AppData\Local\Temp\RemoteMouse.exe" | C:\Users\admin\AppData\Local\Temp\RemoteMouse.exe | — | explorer.exe | |||||||||||
User: admin Company: Remote Mouse Integrity Level: MEDIUM Description: Remote Mouse Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:664 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3268 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1988 | "C:\Users\admin\AppData\Local\Temp\is-IS8C7.tmp\RemoteMouse.tmp" /SL5="$90158,1425428,780800,C:\Users\admin\AppData\Local\Temp\RemoteMouse.exe" /SPAWNWND=$D0182 /NOTIFYWND=$7019C | C:\Users\admin\AppData\Local\Temp\is-IS8C7.tmp\RemoteMouse.tmp | RemoteMouse.exe | ||||||||||||
User: admin Company: Remote Mouse Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1992 | C:\Windows\system32\rundll32.exe C:\Windows\system32\inetcpl.cpl,ClearMyTracksByProcess Flags:65800 WinX:0 WinY:0 IEFrame:00000000 | C:\Windows\System32\rundll32.exe | — | iexplore.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
47 613
Read events
47 213
Write events
379
Delete events
21
Modification events
| (PID) Process: | (1988) RemoteMouse.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1988) RemoteMouse.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000059010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1988) RemoteMouse.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1988) RemoteMouse.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1988) RemoteMouse.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1988) RemoteMouse.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1988) RemoteMouse.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1988) RemoteMouse.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1988) RemoteMouse.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3144) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{1105971C-7ABE-448B-B3DE-25911D49485E}\{8CA35885-36FF-474B-9336-17482B594C96} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
66
Suspicious files
149
Text files
168
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1988 | RemoteMouse.tmp | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:FBFD131CFF2AE795C590E7E2C44487FE | SHA256:9FE221BCCE4CD67284663015DEBC7D852681175CD2D42A507F1171F5405DF377 | |||
| 3836 | NetFrameworkInstaller.exe | C:\a9cda75f5139450cfc03\watermark.bmp | image | |
MD5:B0075CEE80173D764C0237E840BA5879 | SHA256:AB18374B3AAB10E5979E080D0410579F9771DB888BA1B80A5D81BA8896E2D33A | |||
| 1988 | RemoteMouse.tmp | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:C1BE740B0604C964FA216B9FD3E3BD3B | SHA256:780D0ECB83053E2907B44B1F026CB27CC1024DE791FB440F7DC09A09B4343464 | |||
| 1988 | RemoteMouse.tmp | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:8202A1CD02E7D69597995CABBE881A12 | SHA256:58F381C3A0A0ACE6321DA22E40BD44A597BD98B9C9390AB9258426B5CF75A7A5 | |||
| 1988 | RemoteMouse.tmp | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3836 | NetFrameworkInstaller.exe | C:\a9cda75f5139450cfc03\SplashScreen.bmp | image | |
MD5:BC32088BFAA1C76BA4B56639A2DEC592 | SHA256:B05141DBC71669A7872A8E735E5E43A7F9713D4363B7A97543E1E05DCD7470A7 | |||
| 1988 | RemoteMouse.tmp | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:8BDC863AF1C1B013AFFC62F84F80230C | SHA256:041EE8A96BE4D0418E7843FB9E66F320A0E56B86CC17A67D358A0C28F01B248B | |||
| 3836 | NetFrameworkInstaller.exe | C:\a9cda75f5139450cfc03\Graphics\Rotate10.ico | image | |
MD5:0CCA04A3468575FDCEFEE9957E32F904 | SHA256:B94E68C711B3B06D9A63C80AD013C7C7BBDB5F8E82CBC866B246FF22D99B03FE | |||
| 1988 | RemoteMouse.tmp | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:4FACCFF6EF8CB075081E76648A993FDE | SHA256:F686EEDDB5733E8A64E25380EB6B79DA0F85F241F5719144B01A8F4F7E32DDCC | |||
| 1988 | RemoteMouse.tmp | C:\Users\admin\AppData\Local\Temp\is-VG6NA.tmp\NetFrameworkInstaller.exe | executable | |
MD5:4D1BB86D0EEE168E1DA91A36350C1C21 | SHA256:E10C2A36C5013EE83815FCC38963AE3E5C4AFD7FFE770E817322FE366BDEF6E1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
86
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1988 | RemoteMouse.tmp | GET | 200 | 67.27.233.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?93fae79f393bea3b | unknown | compressed | 4.66 Kb | unknown |
1820 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDmzKJl66ZMrRKtZxoAGQQd | unknown | binary | 472 b | unknown |
3268 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 67.27.233.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a7e79e1b6451585f | unknown | compressed | 61.6 Kb | unknown |
2848 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | binary | 471 b | unknown |
1820 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCVN9Jf3G%2B1pAqd7QzTt1vx | unknown | binary | 472 b | unknown |
1212 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | binary | 471 b | unknown |
1988 | RemoteMouse.tmp | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
1988 | RemoteMouse.tmp | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
1080 | svchost.exe | GET | 304 | 67.27.233.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?60b2f43ad8cf70d9 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1988 | RemoteMouse.tmp | 188.114.97.3:443 | www.remotemouse.net | CLOUDFLARENET | NL | unknown |
1988 | RemoteMouse.tmp | 67.27.233.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
1988 | RemoteMouse.tmp | 142.250.185.99:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
1080 | svchost.exe | 67.27.233.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
2868 | Setup.exe | 2.22.242.121:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
3752 | RemoteMouse.exe | 192.168.100.255:2008 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.remotemouse.net |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
crl.microsoft.com |
| whitelisted |
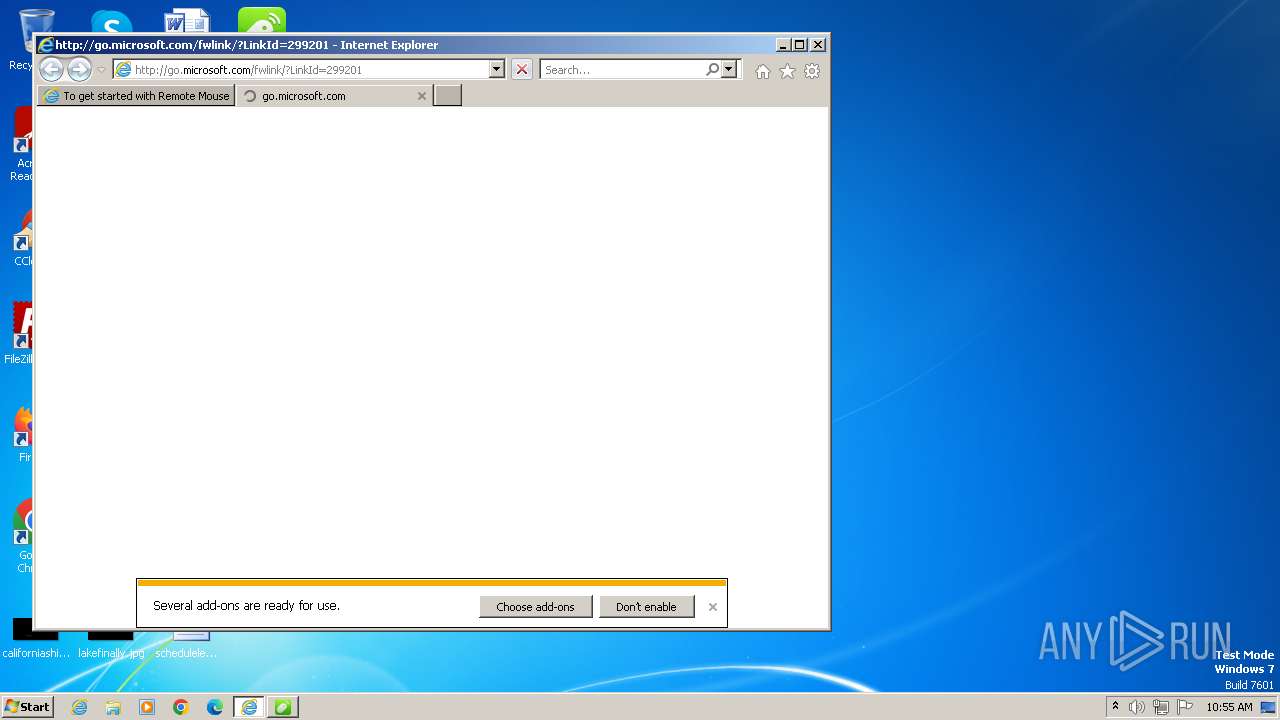
go.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
query.prod.cms.rt.microsoft.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Setup.exe | The operation completed successfully.
|