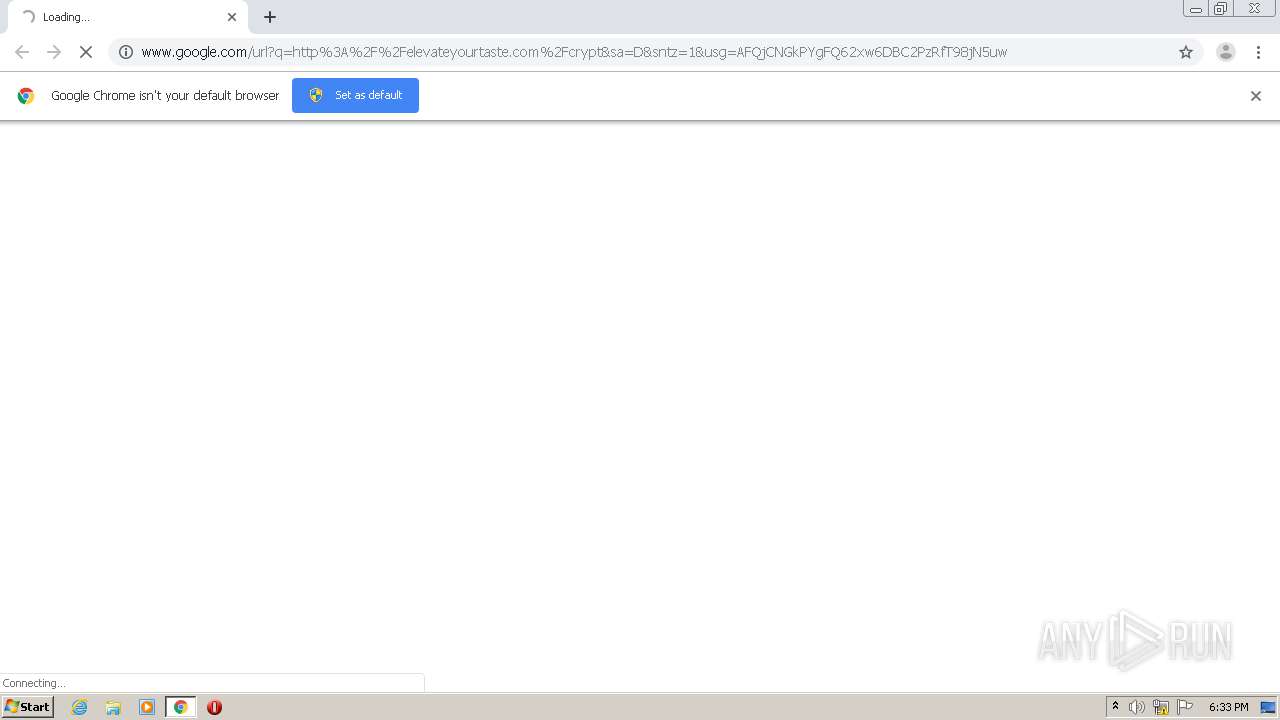
| URL: | http://www.google.com/url?q=http%3A%2F%2Felevateyourtaste.com%2Fcrypt&sa=D&sntz=1&usg=AFQjCNGkPYgFQ62xw6DBC2PzRfT98jN5uw |
| Full analysis: | https://app.any.run/tasks/4109be13-913a-40af-9279-df2e69a51be6 |
| Verdict: | Malicious activity |
| Analysis date: | December 11, 2020, 18:33:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 135A3C429CB5475309C5CAE98759613F |
| SHA1: | 70F522869AD7F0C9317550F261A2A021F8FD7379 |
| SHA256: | 704F2D21CE61EFA17523B10FB3FEF68866ED92354AF27A56FF004E492641A63D |
| SSDEEP: | 3:N1KJS4I2GdJsXj+rLyWAZoMVRKKLfDCG0cgsDX1f38M:Cc4I2Isz+KKpKzDCG0c9DF7 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2212)
Reads the hosts file
- chrome.exe (PID: 2488)
- chrome.exe (PID: 2212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
14
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2192 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,347557868726719846,5255905121992443803,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3831750360532851334 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,347557868726719846,5255905121992443803,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8657344744897052547 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,347557868726719846,5255905121992443803,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18027158524224998120 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2156 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://www.google.com/url?q=http%3A%2F%2Felevateyourtaste.com%2Fcrypt&sa=D&sntz=1&usg=AFQjCNGkPYgFQ62xw6DBC2PzRfT98jN5uw" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,347557868726719846,5255905121992443803,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12275699091916755951 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,347557868726719846,5255905121992443803,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6395300600181014512 --mojo-platform-channel-handle=1552 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,347557868726719846,5255905121992443803,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16708565476570152754 --mojo-platform-channel-handle=3504 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,347557868726719846,5255905121992443803,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16682980653869563773 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,347557868726719846,5255905121992443803,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17646331798136238800 --mojo-platform-channel-handle=3680 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
572
Read events
519
Write events
50
Delete events
3
Modification events
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2212-13252185216109750 |
Value: 259 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
30
Text files
52
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FD3BB80-8A4.pma | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7ee29acd-3f21-4747-8b93-f8a2163fd06d.tmp | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF15aaff.TMP | text | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15acd4.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
77
TCP/UDP connections
27
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
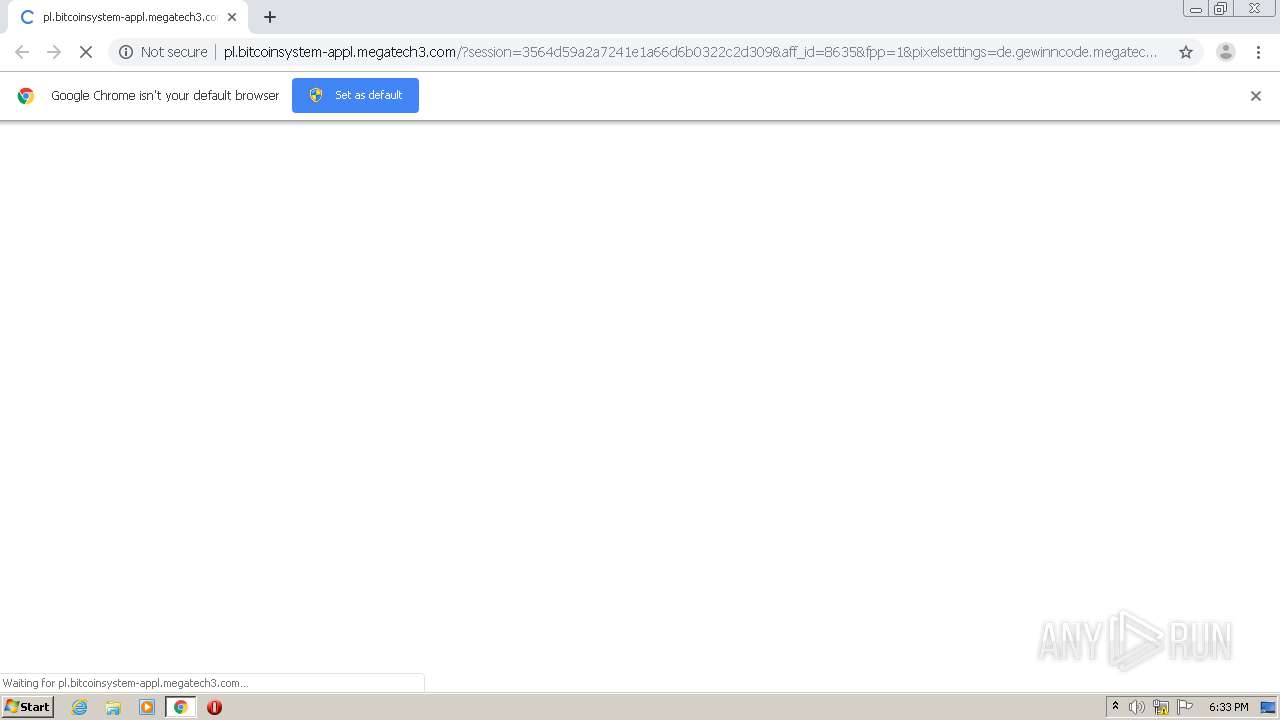
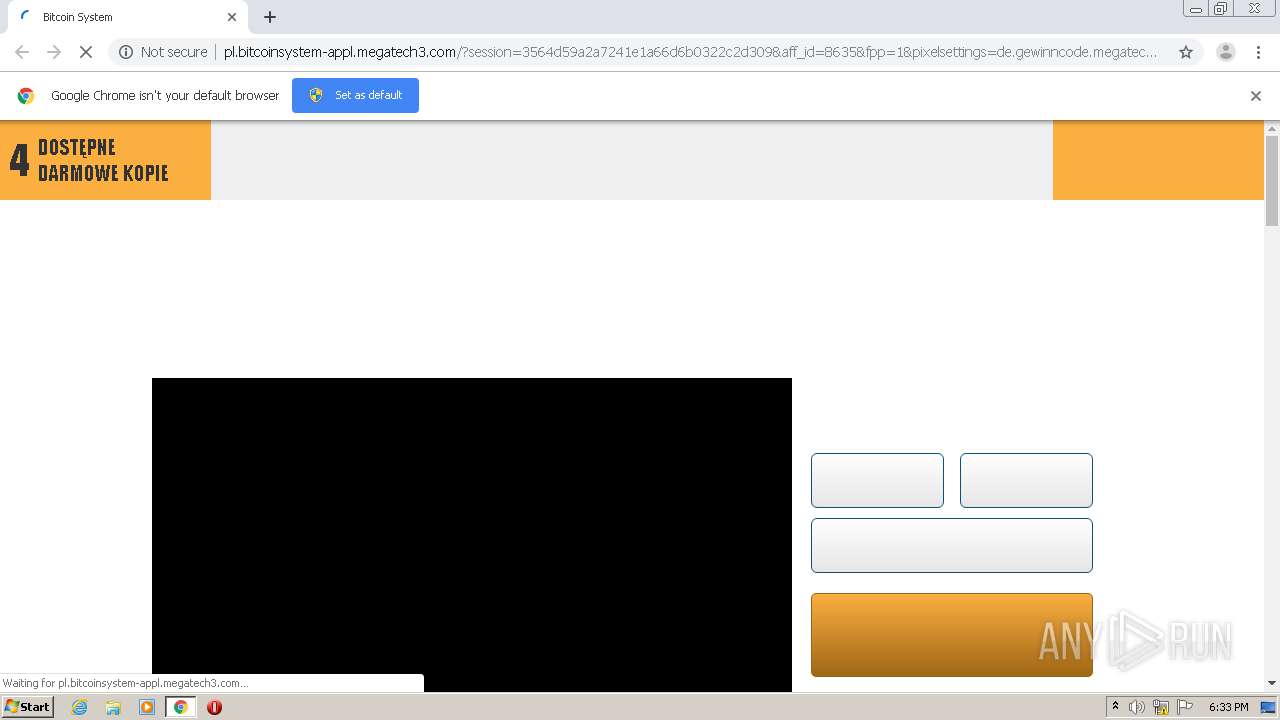
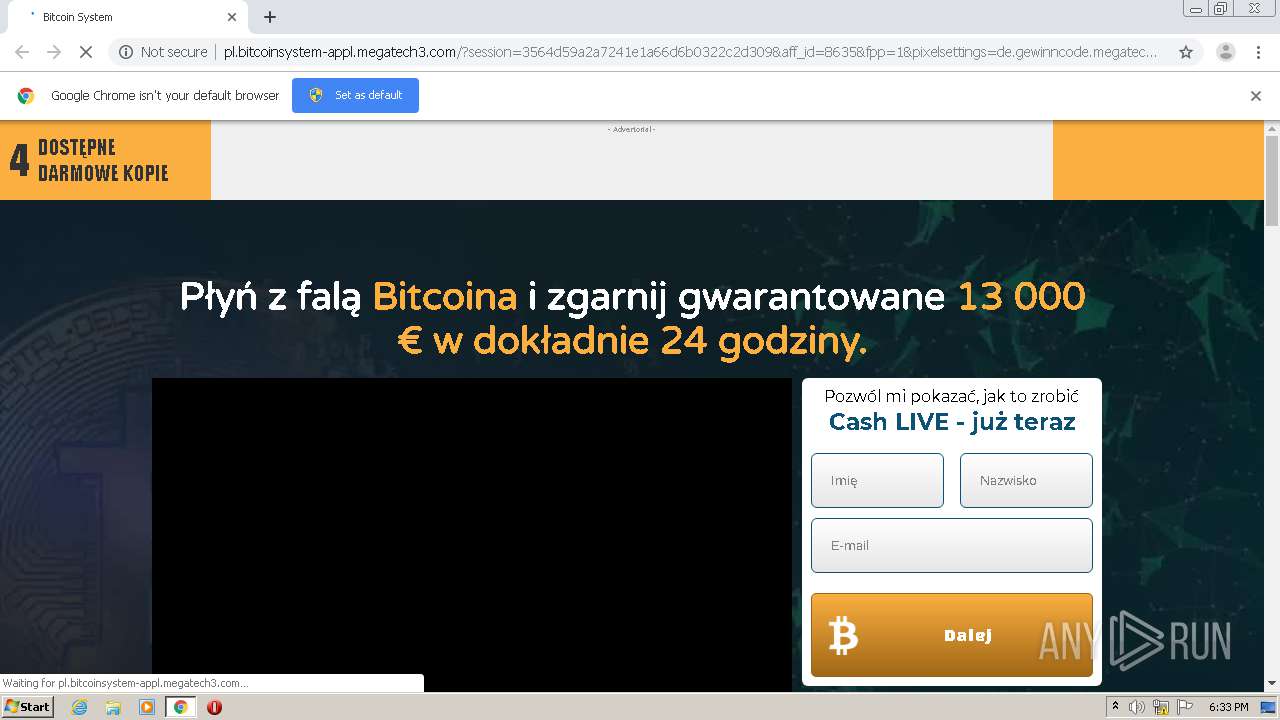
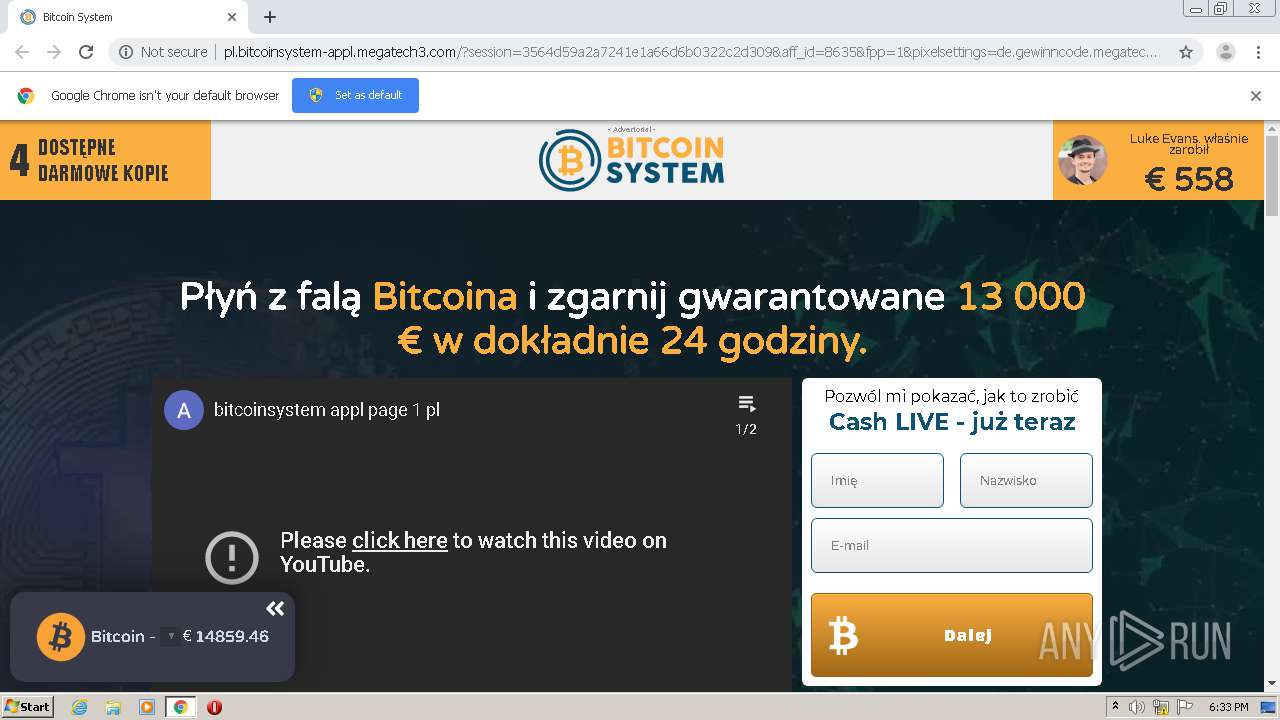
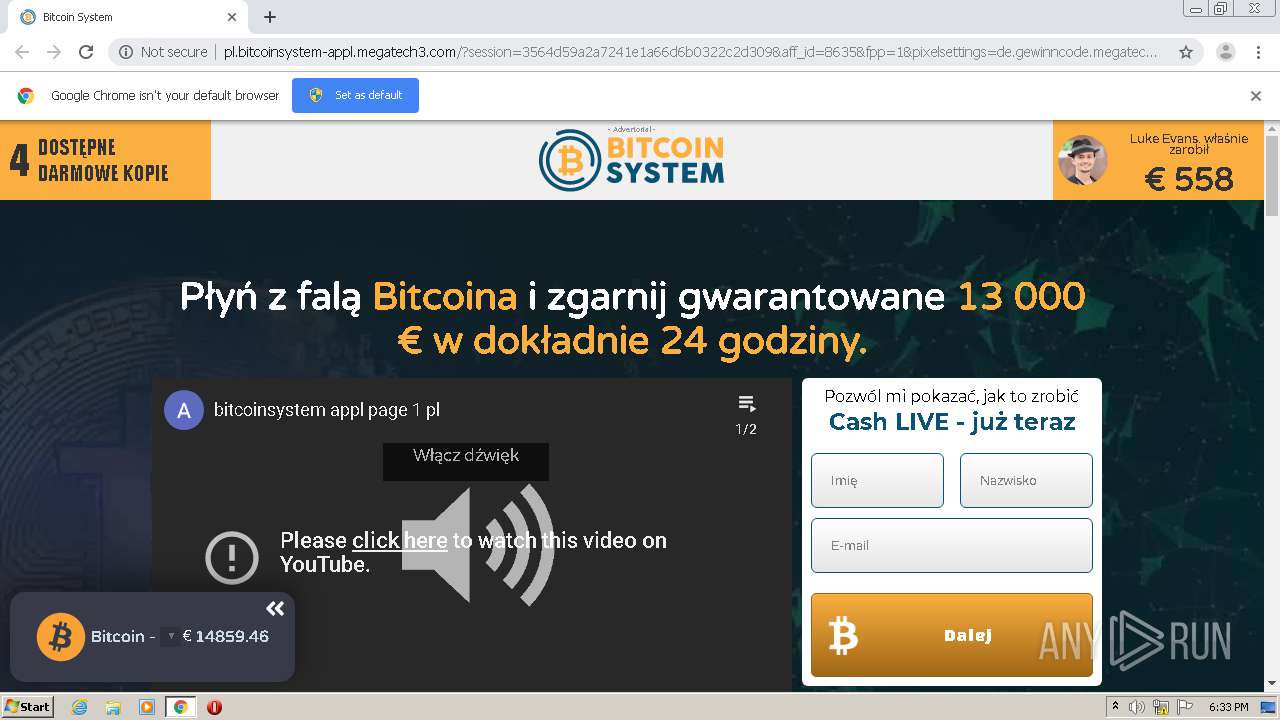
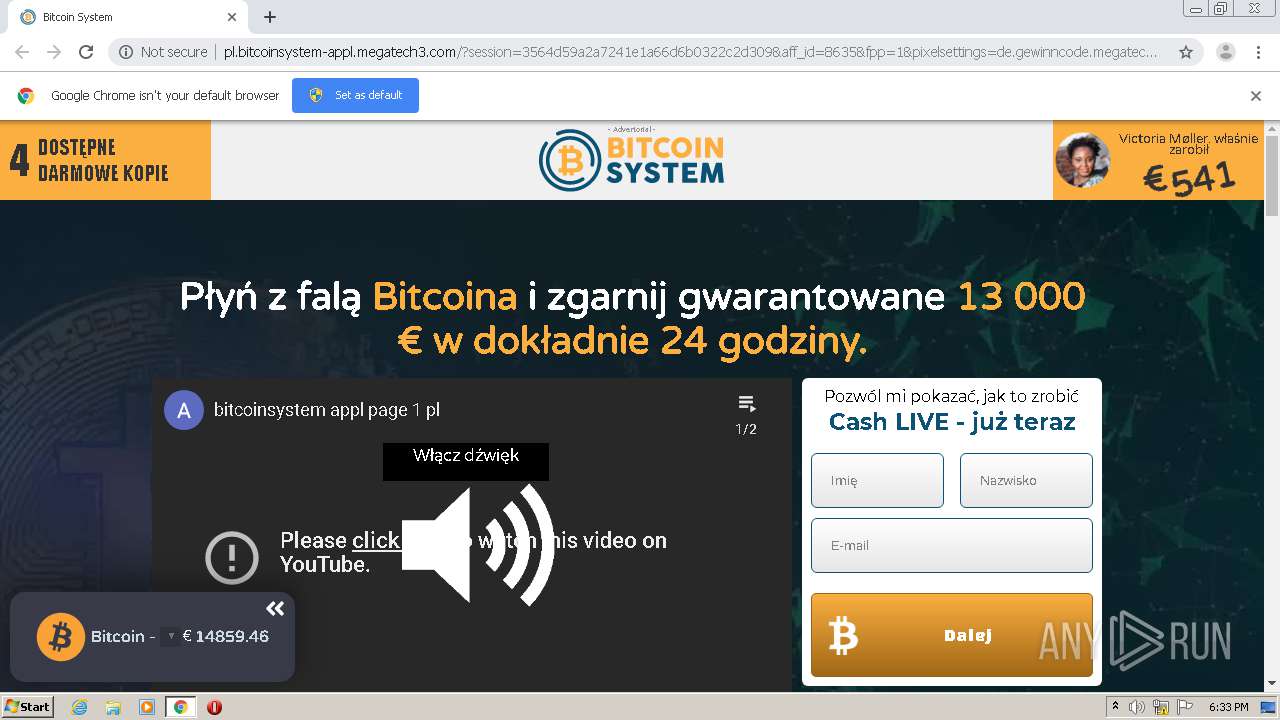
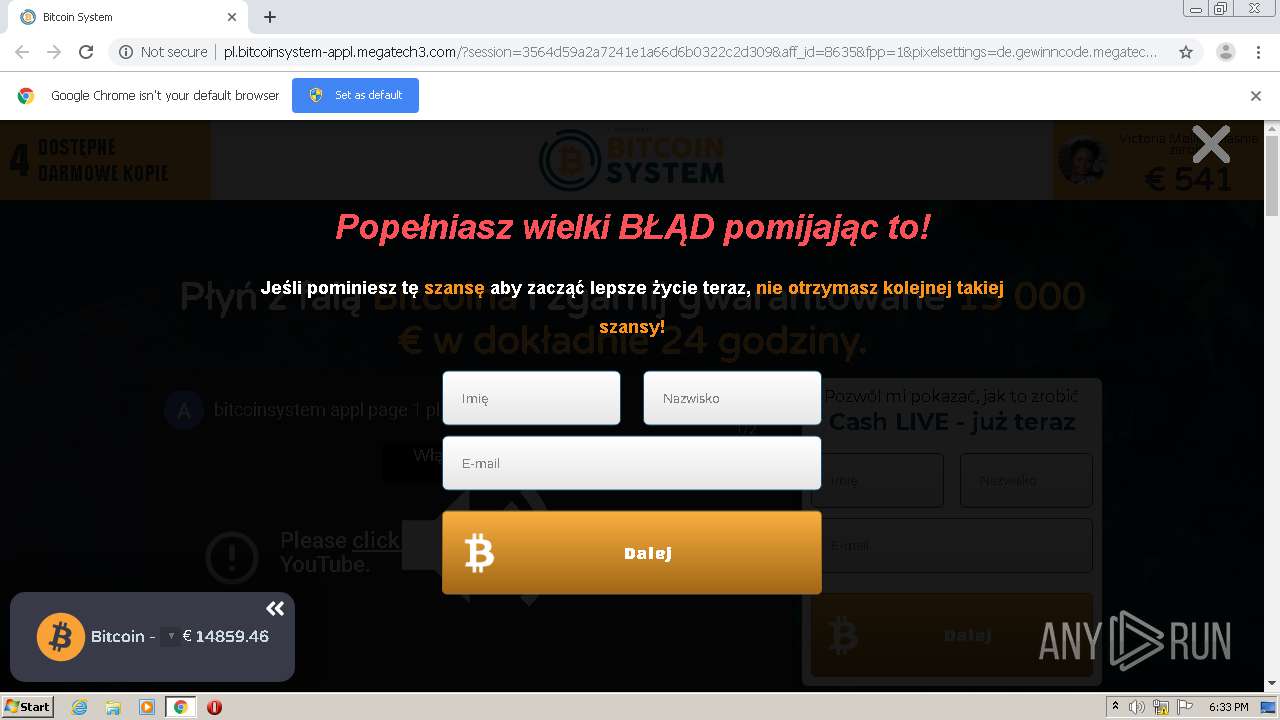
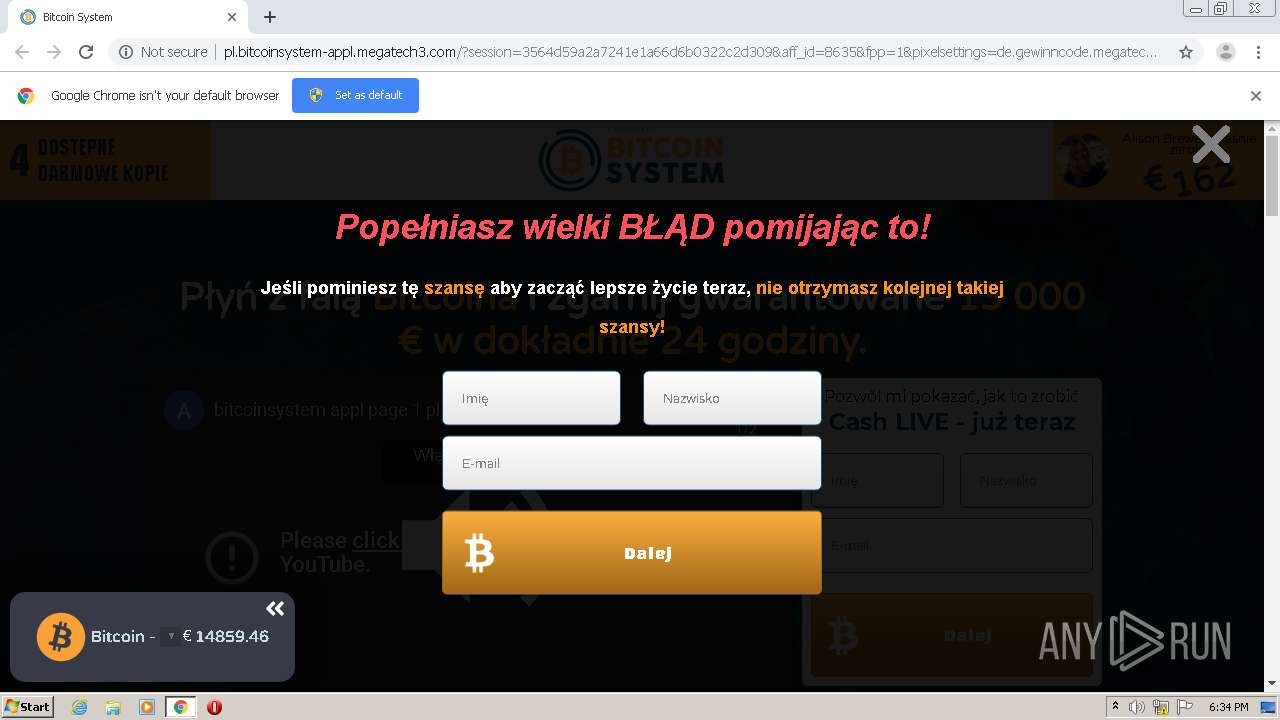
2488 | chrome.exe | GET | 302 | 104.27.130.185:80 | http://de.gewinncode.megatech3.com/09r3 | US | — | — | suspicious |
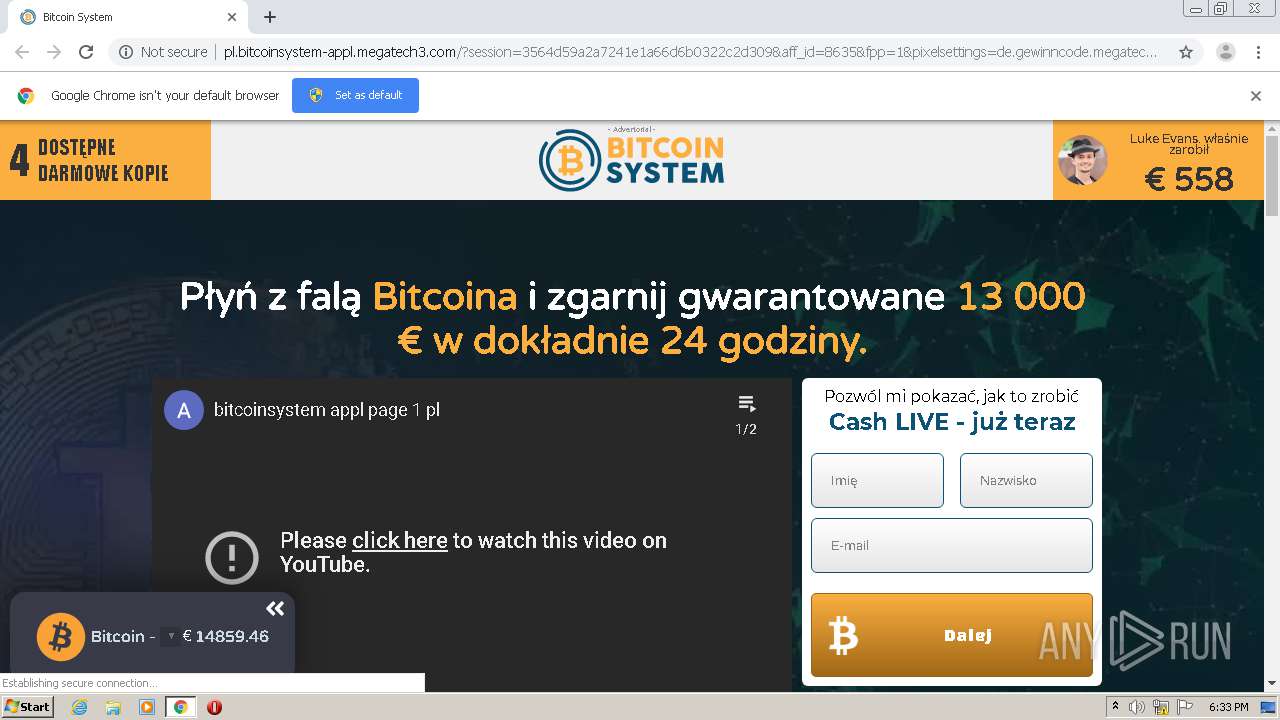
2488 | chrome.exe | GET | 200 | 172.67.150.214:80 | http://pl.bitcoinsystem-appl.megatech3.com/?session=3564d59a2a7241e1a66d6b0322c2d309&aff_id=8635&fpp=1&pixelsettings=de.gewinncode.megatech3.com%2Ffbp%3Fev%3D%7Bev%7D%26pixel%3D%7Bpixel%7D | US | html | 11.7 Kb | suspicious |
2488 | chrome.exe | GET | 302 | 85.239.35.175:80 | http://elevateyourtaste.com/crypt/ | RU | html | 242 b | suspicious |
2488 | chrome.exe | GET | 200 | 172.67.150.214:80 | http://pl.bitcoinsystem-appl.megatech3.com/css/systembitcoin.css?v=3 | US | text | 3.56 Kb | suspicious |
2488 | chrome.exe | GET | 200 | 172.67.150.214:80 | http://pl.bitcoinsystem-appl.megatech3.com/css/custom.css?v=3 | US | text | 352 b | suspicious |
2488 | chrome.exe | GET | 200 | 172.67.150.214:80 | http://pl.bitcoinsystem-appl.megatech3.com/css/custom-alt.css?v=3 | US | text | 939 b | suspicious |
2488 | chrome.exe | GET | 200 | 172.67.150.214:80 | http://pl.bitcoinsystem-appl.megatech3.com/css/components.css?v=3 | US | text | 8.99 Kb | suspicious |
2488 | chrome.exe | GET | 200 | 172.67.150.214:80 | http://pl.bitcoinsystem-appl.megatech3.com/css/main.min.css?v=3 | US | text | 3.91 Kb | suspicious |
2488 | chrome.exe | GET | 200 | 172.67.150.214:80 | http://pl.bitcoinsystem-appl.megatech3.com/css/popup.css?v=3 | US | text | 737 b | suspicious |
2488 | chrome.exe | GET | 200 | 172.67.150.214:80 | http://pl.bitcoinsystem-appl.megatech3.com/css/form.css?v=3 | US | text | 2.86 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2488 | chrome.exe | 104.28.10.45:443 | randomuser.me | Cloudflare Inc | US | shared |
2488 | chrome.exe | 216.58.206.2:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2488 | chrome.exe | 172.217.21.230:443 | static.doubleclick.net | Google Inc. | US | whitelisted |
2488 | chrome.exe | 216.58.210.14:443 | s.ytimg.com | Google Inc. | US | whitelisted |
2488 | chrome.exe | 216.58.212.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
2488 | chrome.exe | 172.67.150.214:80 | de.gewinncode.megatech3.com | — | US | suspicious |
2488 | chrome.exe | 216.58.207.78:443 | www.youtube.com | Google Inc. | US | whitelisted |
2488 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2488 | chrome.exe | 64.233.178.132:443 | yt3.ggpht.com | Google Inc. | — | unknown |
2488 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
accounts.google.com |
| shared |
elevateyourtaste.com |
| suspicious |
de.gewinncode.megatech3.com |
| suspicious |
pl.bitcoinsystem-appl.megatech3.com |
| suspicious |
s.ytimg.com |
| whitelisted |
clients1.google.com |
| whitelisted |
randomuser.me |
| malicious |
www.youtube.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |