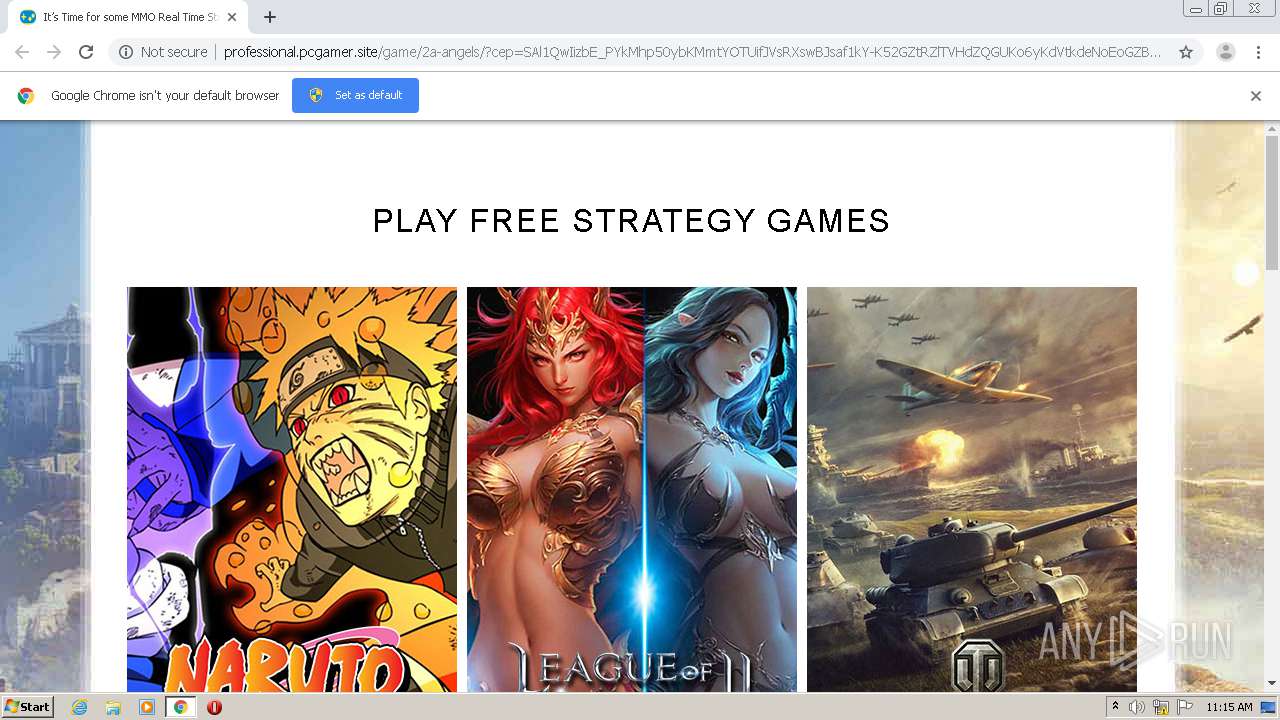
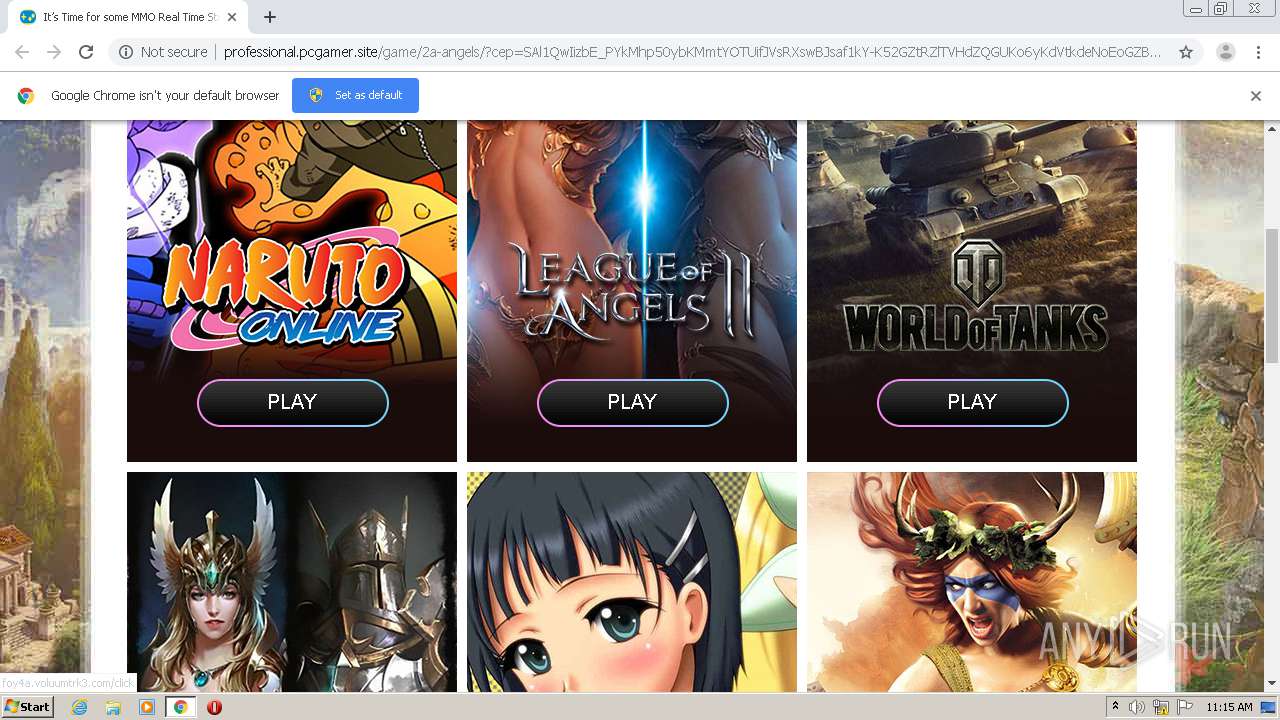
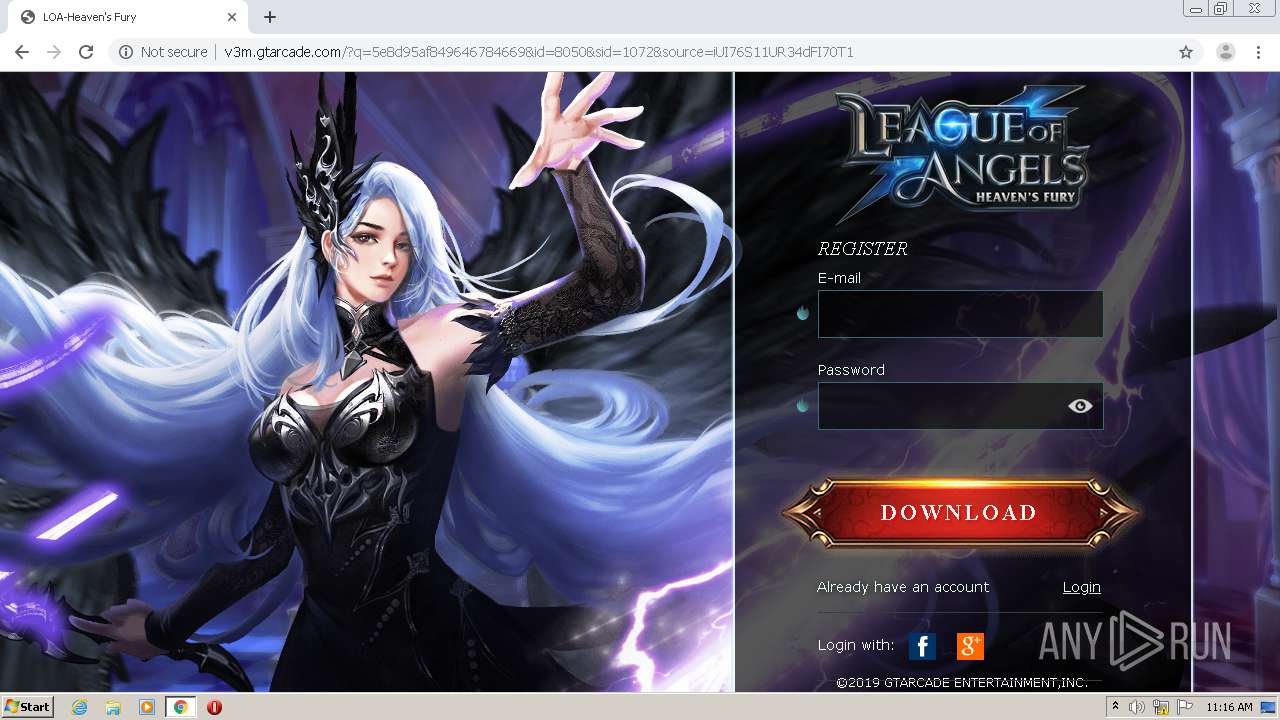
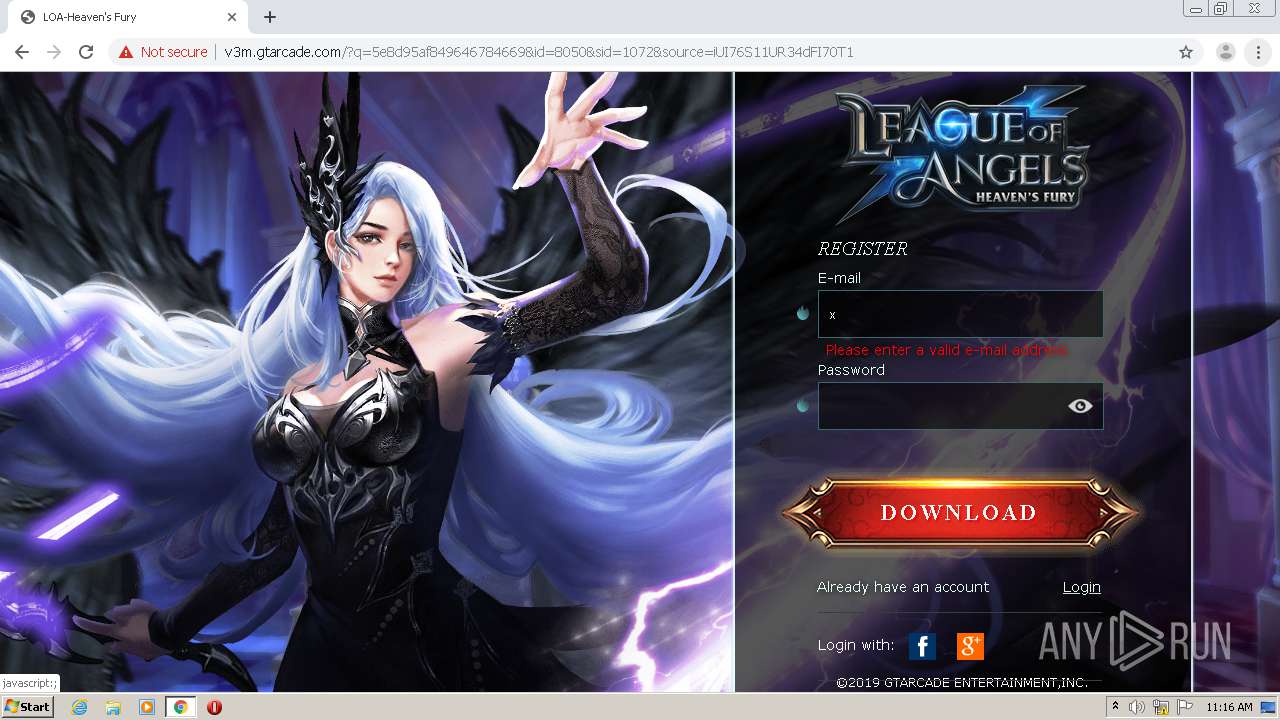
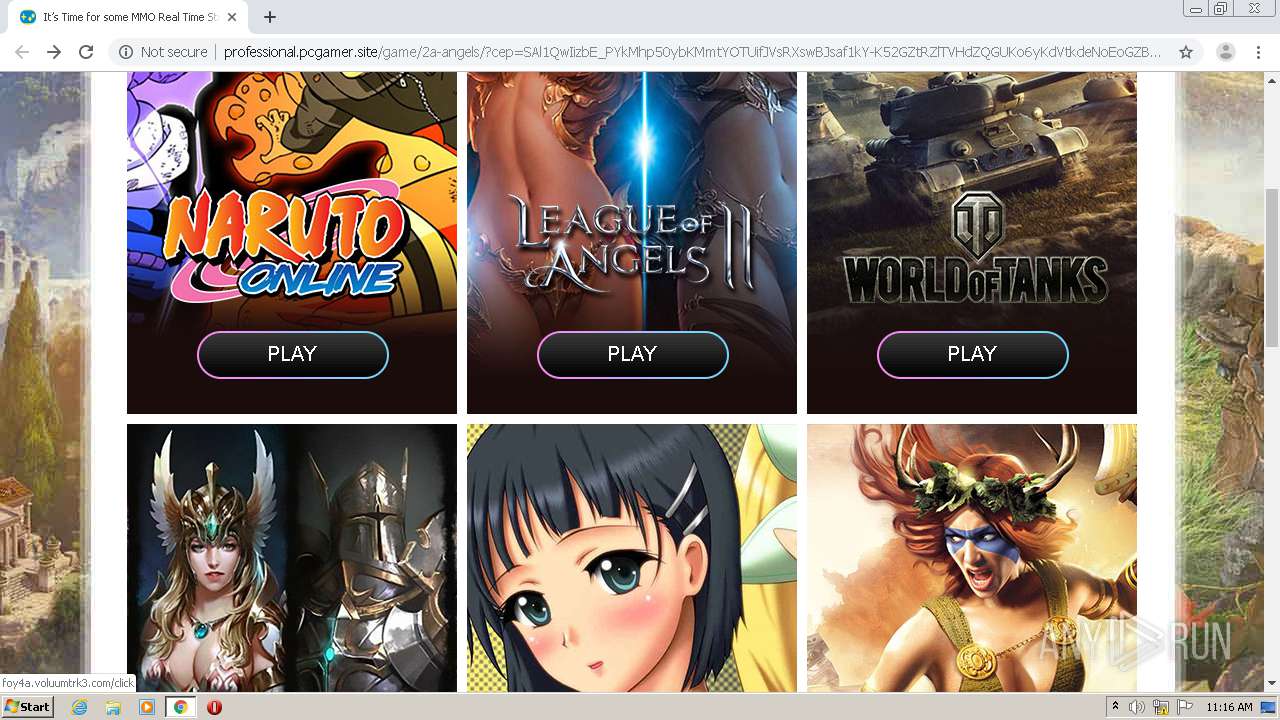
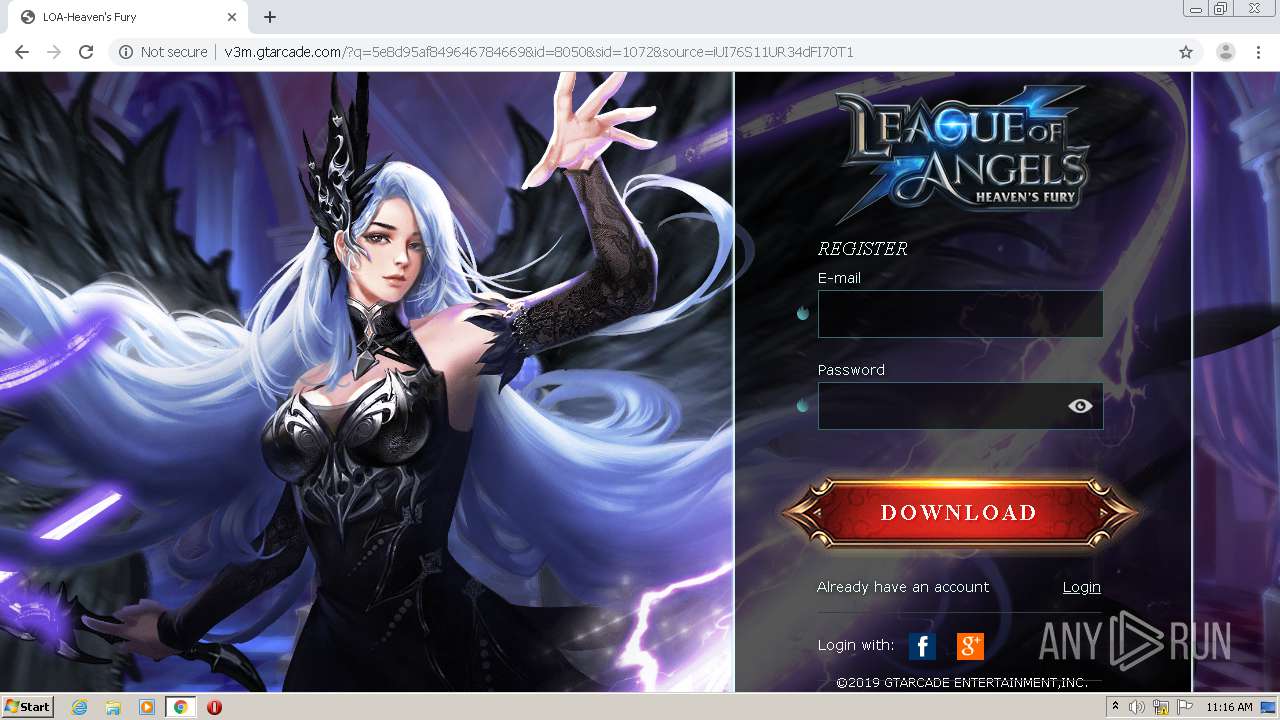
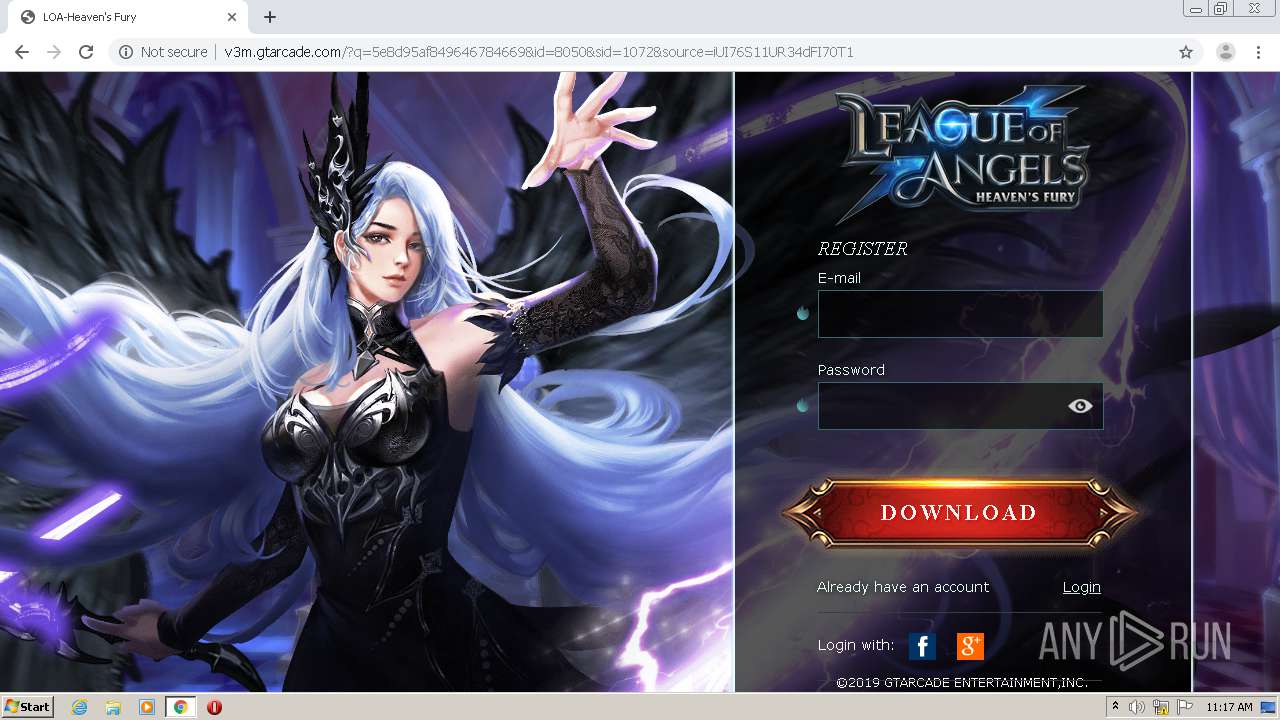
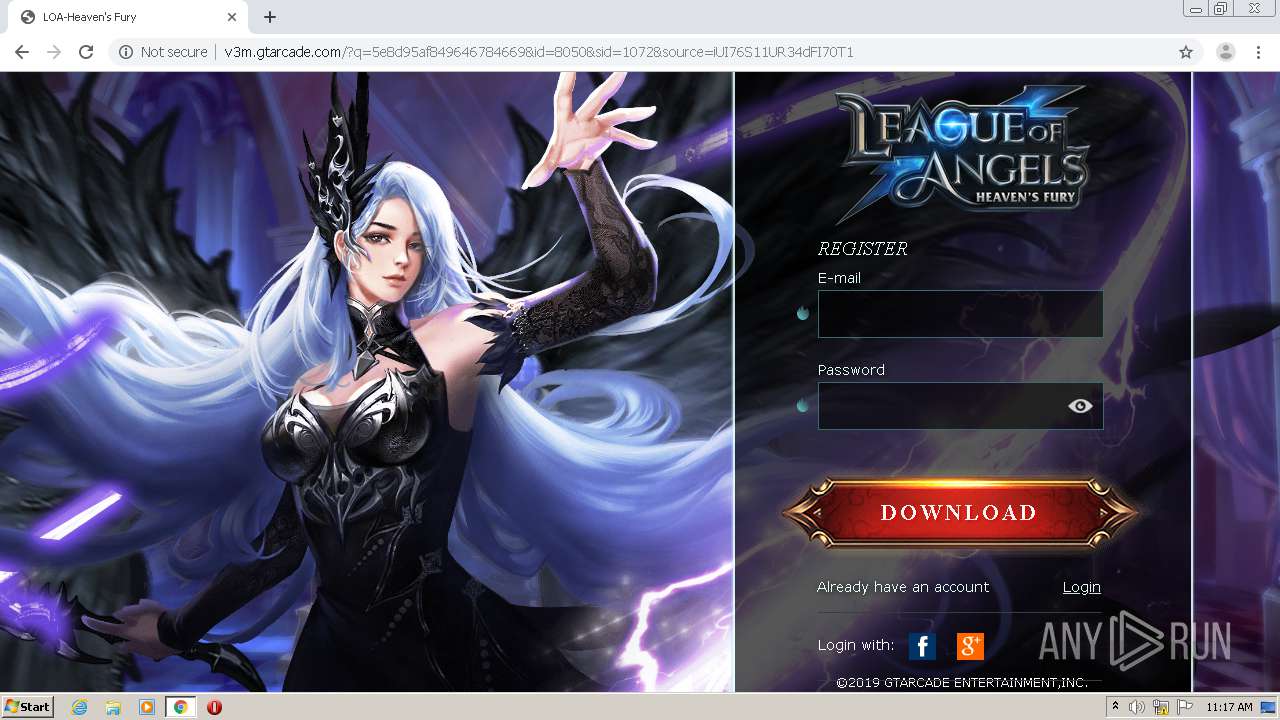
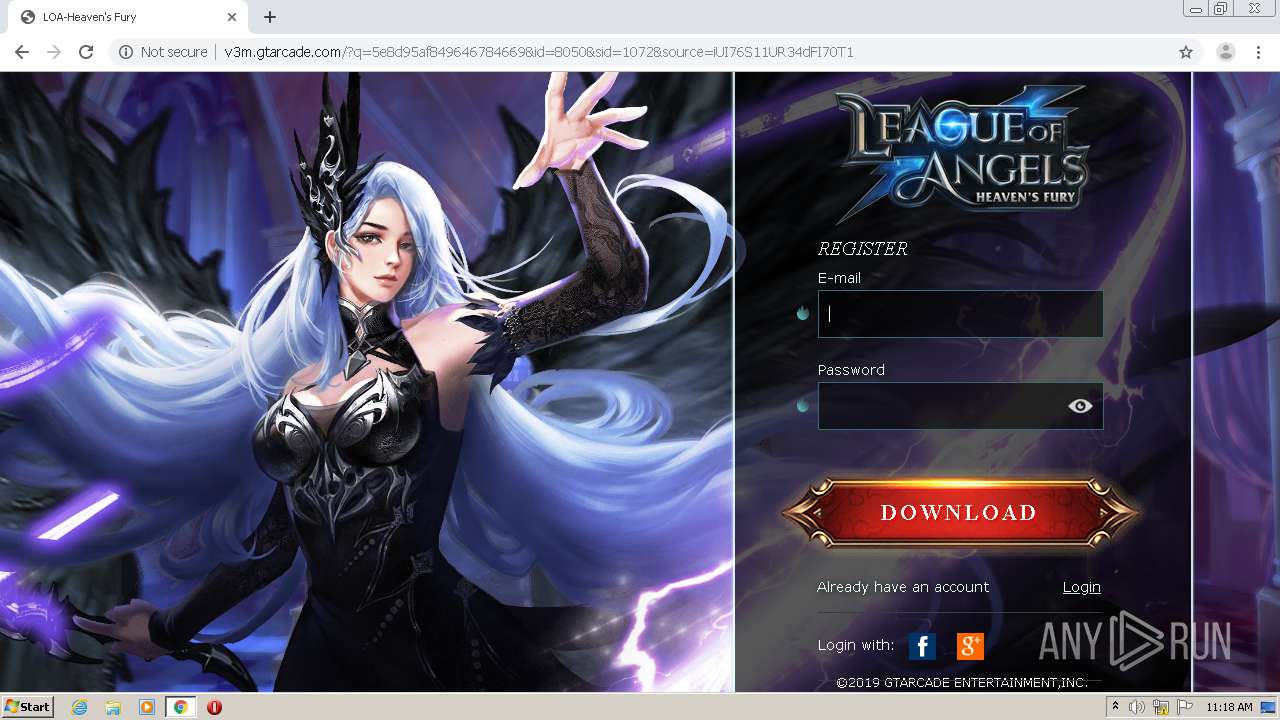
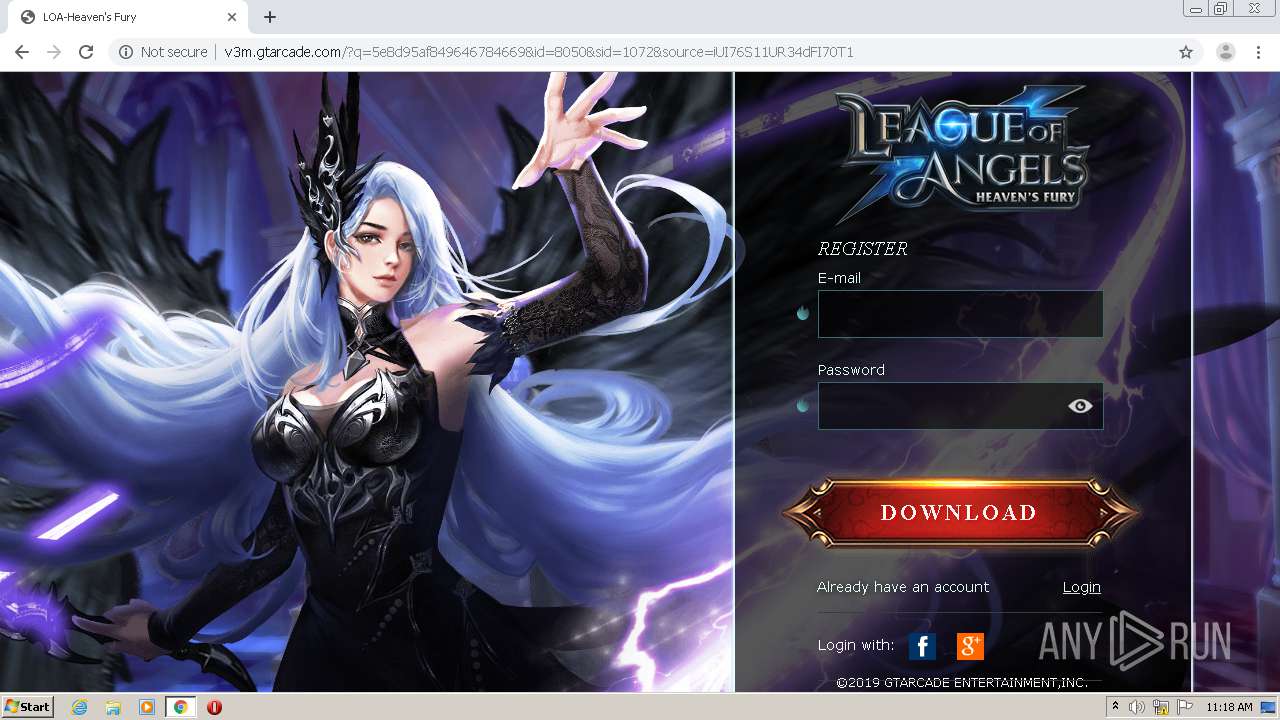
| URL: | http://professional.pcgamer.site/game/2a-angels/?cep=SAl1QwIizbE_PYkMhp50ybKMmtYOTUifJVsRXswBJsaf1kY-K52GZtRZlTVHdZQGUKo6yKdVtkdeNoEoGZBdKMku0-tmawnnnvCdAbRKyNWu6i6PpUZr4_RbCdQU21lqTfM4QHjhCkoSaIWeow2Kvpa98GUWvilWaukJlRSFfx8EbTbMCGalREruFpoXdQBv7poefKDDYgprasVgyr5GuBiQHlr5irKkobNDB5mE1GNwA5YdLSsLhuetEyScdndupw7ZPfeArZ3Ufnp1aH61X_Slm-ULGYR0SdPVHwbGF82Npuq-3L-_JrNfCAfsrsEUbrvUQZ4LKZnPSE_pYs_ZEtROqvedMCu9ph6Qq-7wGcvgGSFn_l4hw5KX5oMcSiTOFb21KYralwFJMan0Ab9X1_i5qz20uaU5tcRbeyJyaC82I1OSVybRfWTKg7SVDfxLyCoxGUtoi4LjQAgfGBnBceWXyOpibQ63MVLdsjWdwEWlsg0jKJa3xLjkA4W4HI9W4lcSYFPHI8ICdACZAil0MQW1flBs4USEO8fU9EThDbU&lptoken=161606465655319203d2&token=ckdFYzQyUjFCR2o2VHFqdFZiRlZSUT09&placement=3744083&country=UK&clickid=16065612972806007818214687232696289&src=anhUczZ1MmNxYTIveUV5a2R6SDM3Zz09 |
| Full analysis: | https://app.any.run/tasks/c6398f6f-bf7f-4722-b39a-70332b15fa51 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 11:15:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 68618F52095E96AADADCBED869215313 |
| SHA1: | 9B3CFADC417AE6D668224DE7F249DEDB43E76BAC |
| SHA256: | 704EE24A53AE309A54E91556C708AA32E4E82DDCC7C8DE572476F12D4A7511FA |
| SSDEEP: | 12:zXto7H+lNyowYxsr2a2Euvc59a/Y5jjuaKhtNjpROPd5wARgu6V+WgVv/RcXur+:zdo7elN7z2r2EUy9a/YcFfNcd5C/gFK |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2208)
- chrome.exe (PID: 1628)
Application launched itself
- chrome.exe (PID: 2208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
17
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5034547673093815112,6526221746928765621,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=105851513366729636 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3136 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,5034547673093815112,6526221746928765621,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17092691886724548335 --mojo-platform-channel-handle=1520 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5034547673093815112,6526221746928765621,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15519468131104716097 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3512 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5034547673093815112,6526221746928765621,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15216920363777870443 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5034547673093815112,6526221746928765621,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11226798098698566754 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2420 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,5034547673093815112,6526221746928765621,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10828918031122853411 --mojo-platform-channel-handle=1964 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://professional.pcgamer.site/game/2a-angels/?cep=SAl1QwIizbE_PYkMhp50ybKMmtYOTUifJVsRXswBJsaf1kY-K52GZtRZlTVHdZQGUKo6yKdVtkdeNoEoGZBdKMku0-tmawnnnvCdAbRKyNWu6i6PpUZr4_RbCdQU21lqTfM4QHjhCkoSaIWeow2Kvpa98GUWvilWaukJlRSFfx8EbTbMCGalREruFpoXdQBv7poefKDDYgprasVgyr5GuBiQHlr5irKkobNDB5mE1GNwA5YdLSsLhuetEyScdndupw7ZPfeArZ3Ufnp1aH61X_Slm-ULGYR0SdPVHwbGF82Npuq-3L-_JrNfCAfsrsEUbrvUQZ4LKZnPSE_pYs_ZEtROqvedMCu9ph6Qq-7wGcvgGSFn_l4hw5KX5oMcSiTOFb21KYralwFJMan0Ab9X1_i5qz20uaU5tcRbeyJyaC82I1OSVybRfWTKg7SVDfxLyCoxGUtoi4LjQAgfGBnBceWXyOpibQ63MVLdsjWdwEWlsg0jKJa3xLjkA4W4HI9W4lcSYFPHI8ICdACZAil0MQW1flBs4USEO8fU9EThDbU&lptoken=161606465655319203d2&token=ckdFYzQyUjFCR2o2VHFqdFZiRlZSUT09&placement=3744083&country=UK&clickid=16065612972806007818214687232696289&src=anhUczZ1MmNxYTIveUV5a2R6SDM3Zz09" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2184 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5034547673093815112,6526221746928765621,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4602337498072070907 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,5034547673093815112,6526221746928765621,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18064883878227728327 --mojo-platform-channel-handle=3664 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
594
Read events
534
Write events
57
Delete events
3
Modification events
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2276) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2208-13251122142679000 |
Value: 259 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
19
Text files
65
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC382DF-8A0.pma | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9d28941d-3ef4-4cf5-a452-b411b61dde3e.tmp | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1431bd.TMP | text | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF14319d.TMP | text | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF14346c.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
93
TCP/UDP connections
50
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
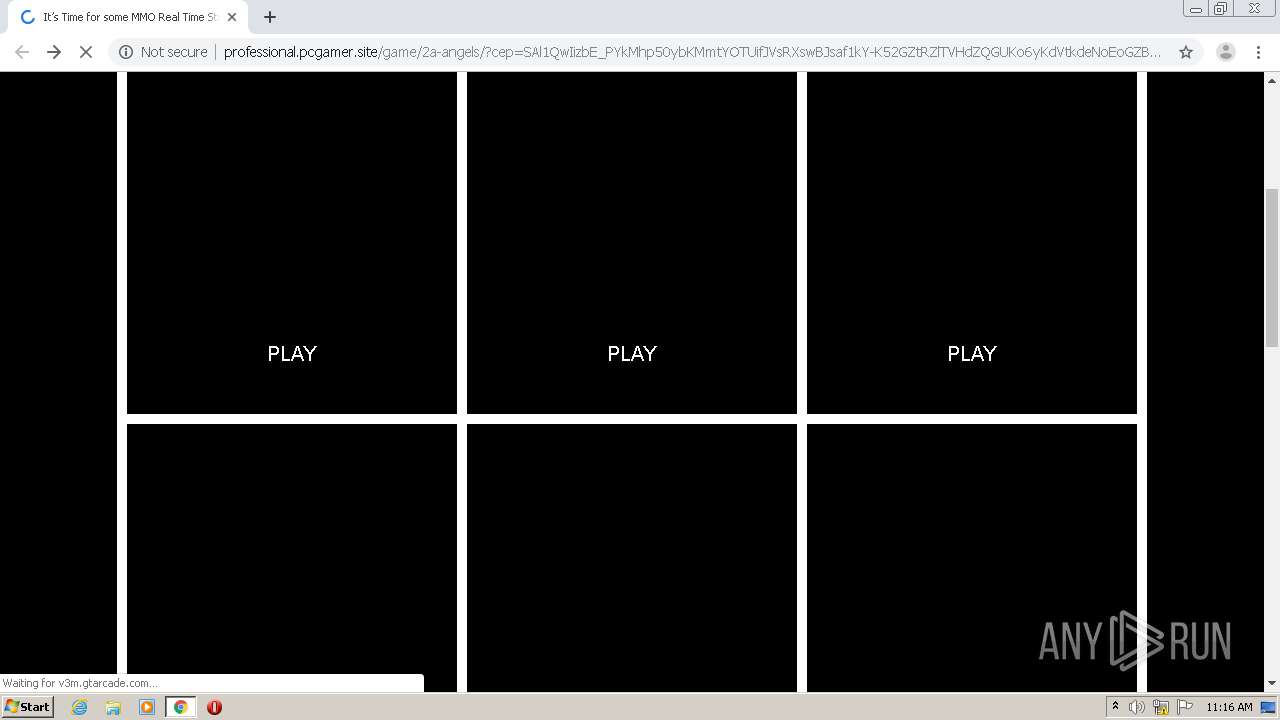
1628 | chrome.exe | GET | — | 139.162.190.215:80 | http://professional.pcgamer.site/game/2a-angels/canvas.ashx | DE | — | — | suspicious |
1628 | chrome.exe | GET | 200 | 139.162.190.215:80 | http://professional.pcgamer.site/game/2a-angels/?cep=SAl1QwIizbE_PYkMhp50ybKMmtYOTUifJVsRXswBJsaf1kY-K52GZtRZlTVHdZQGUKo6yKdVtkdeNoEoGZBdKMku0-tmawnnnvCdAbRKyNWu6i6PpUZr4_RbCdQU21lqTfM4QHjhCkoSaIWeow2Kvpa98GUWvilWaukJlRSFfx8EbTbMCGalREruFpoXdQBv7poefKDDYgprasVgyr5GuBiQHlr5irKkobNDB5mE1GNwA5YdLSsLhuetEyScdndupw7ZPfeArZ3Ufnp1aH61X_Slm-ULGYR0SdPVHwbGF82Npuq-3L-_JrNfCAfsrsEUbrvUQZ4LKZnPSE_pYs_ZEtROqvedMCu9ph6Qq-7wGcvgGSFn_l4hw5KX5oMcSiTOFb21KYralwFJMan0Ab9X1_i5qz20uaU5tcRbeyJyaC82I1OSVybRfWTKg7SVDfxLyCoxGUtoi4LjQAgfGBnBceWXyOpibQ63MVLdsjWdwEWlsg0jKJa3xLjkA4W4HI9W4lcSYFPHI8ICdACZAil0MQW1flBs4USEO8fU9EThDbU&lptoken=161606465655319203d2&token=ckdFYzQyUjFCR2o2VHFqdFZiRlZSUT09&placement=3744083&country=UK&clickid=16065612972806007818214687232696289&src=anhUczZ1MmNxYTIveUV5a2R6SDM3Zz09 | DE | html | 4.65 Kb | suspicious |
1628 | chrome.exe | GET | 200 | 139.162.190.215:80 | http://professional.pcgamer.site/game/2a-angels/clean-lp/main.css | DE | text | 640 Kb | suspicious |
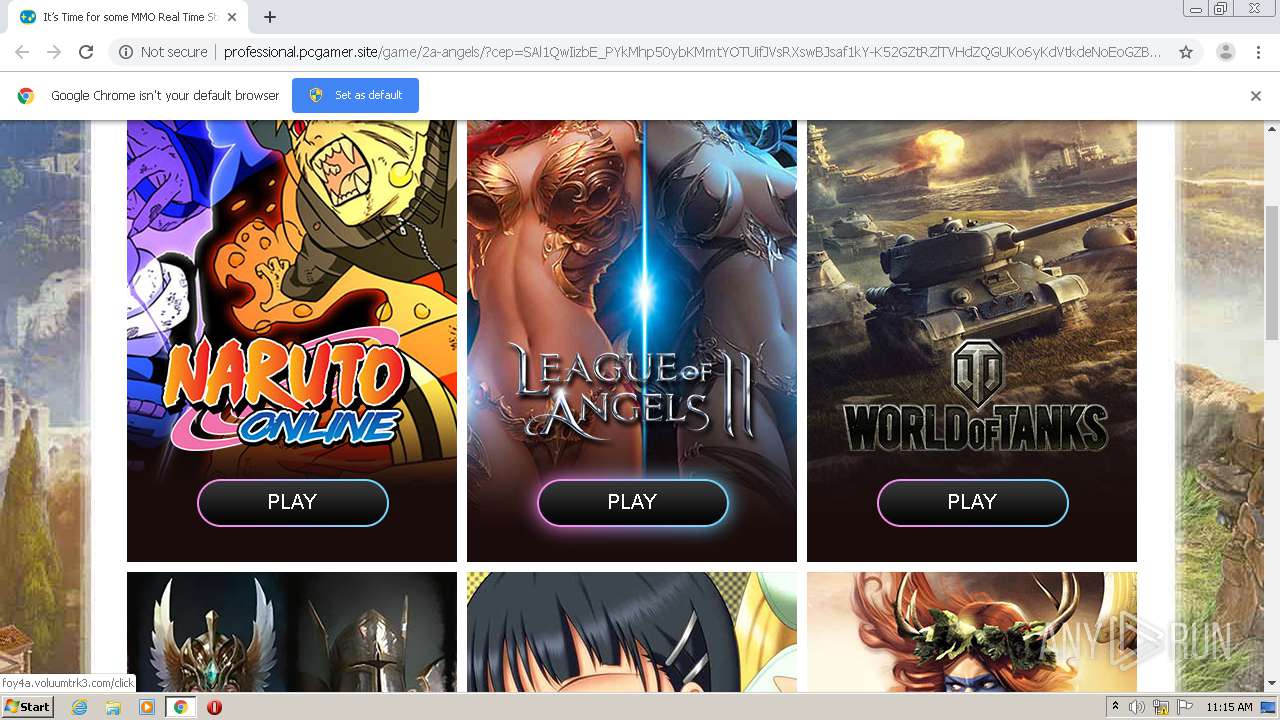
1628 | chrome.exe | GET | 200 | 139.162.190.215:80 | http://professional.pcgamer.site/game/2a-angels/clean-lp/unit_pi.jpg | DE | image | 47.5 Kb | suspicious |
1628 | chrome.exe | GET | 200 | 139.162.190.215:80 | http://professional.pcgamer.site/game/2a-angels/clean-lp/bg.jpg | DE | image | 265 Kb | suspicious |
1628 | chrome.exe | GET | 200 | 139.162.190.215:80 | http://professional.pcgamer.site/game/2a-angels/clean-lp/unit_sf.jpg | DE | image | 58.9 Kb | suspicious |
1628 | chrome.exe | GET | 200 | 139.162.190.215:80 | http://professional.pcgamer.site/game/2a-angels/clean-lp/unit_td.jpg | DE | image | 57.4 Kb | suspicious |
1628 | chrome.exe | GET | 200 | 139.162.190.215:80 | http://professional.pcgamer.site/game/2a-angels/clean-lp/unit_sl.jpg | DE | image | 50.1 Kb | suspicious |
1628 | chrome.exe | GET | 200 | 139.162.190.215:80 | http://professional.pcgamer.site/game/2a-angels/clean-lp/btn_01.png | DE | image | 3.93 Kb | suspicious |
1628 | chrome.exe | GET | 200 | 139.162.190.215:80 | http://professional.pcgamer.site/game/2a-angels/clean-lp/unit_nd.jpg | DE | image | 53.7 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1628 | chrome.exe | 139.162.190.215:80 | professional.pcgamer.site | Linode, LLC | DE | suspicious |
1628 | chrome.exe | 52.57.174.187:80 | foy4a.voluumtrk3.com | Amazon.com, Inc. | DE | unknown |
1628 | chrome.exe | 34.227.236.18:443 | go.playmmogames.com | Amazon.com, Inc. | US | unknown |
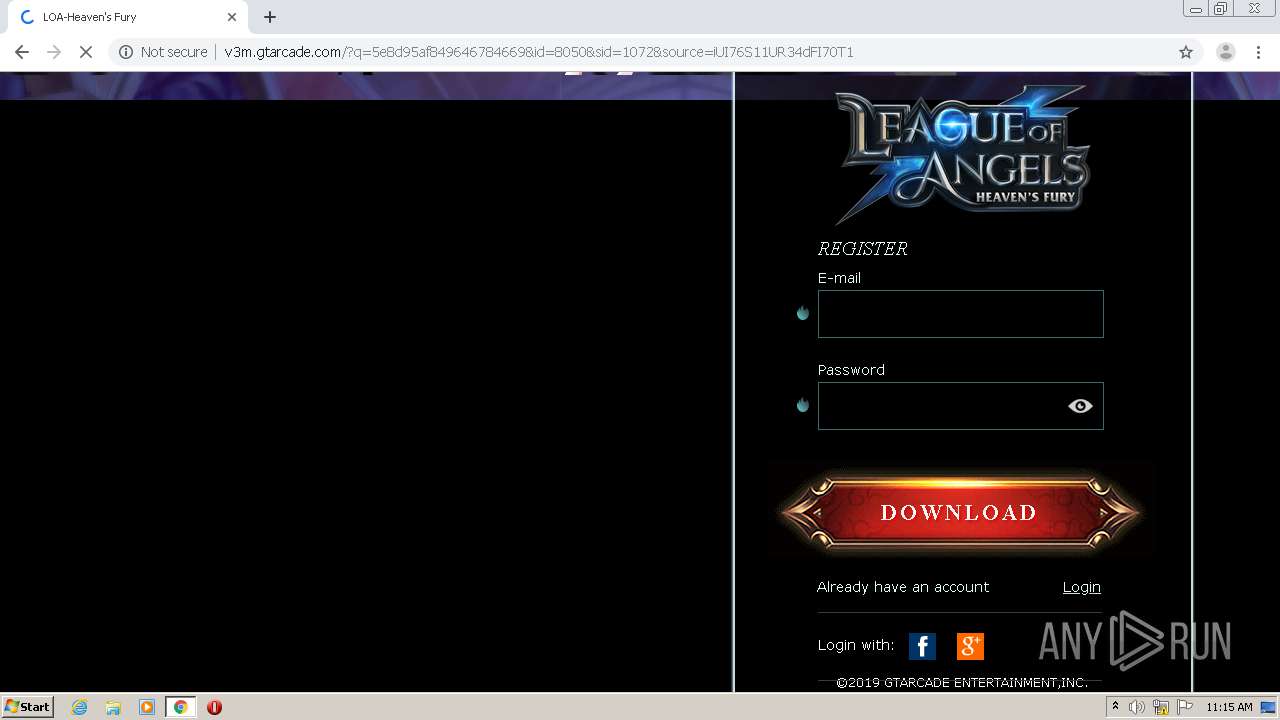
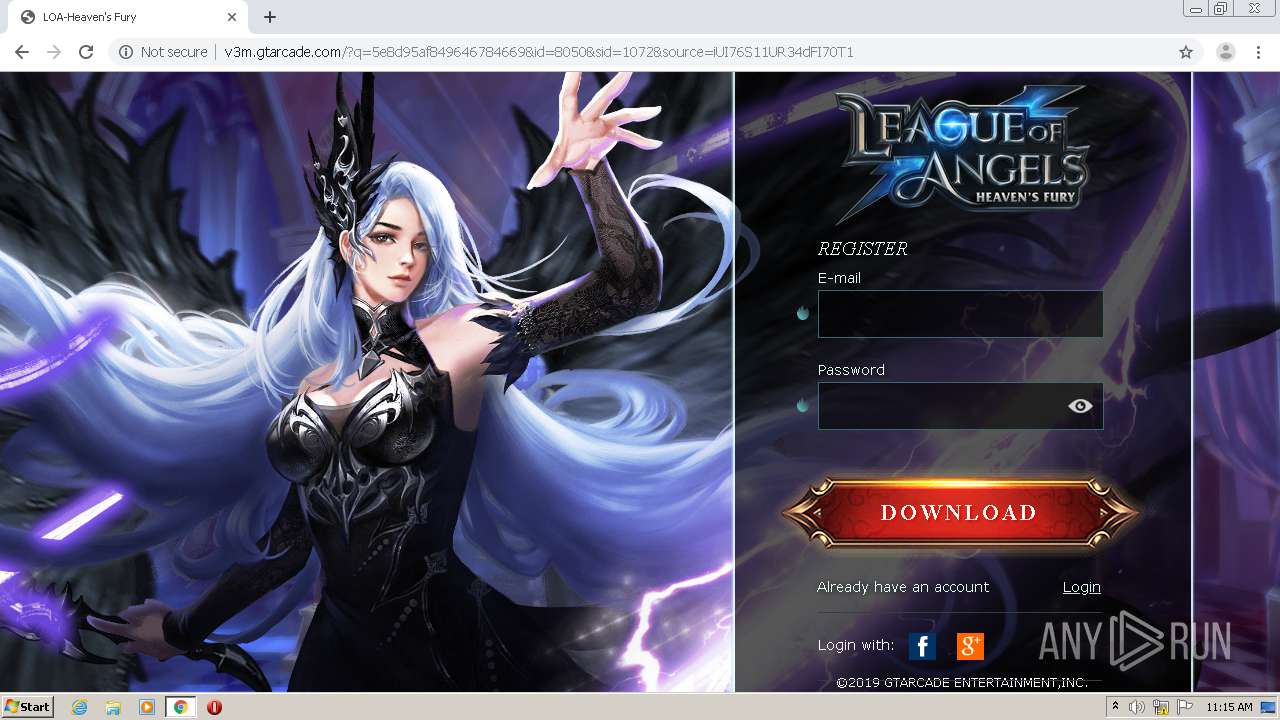
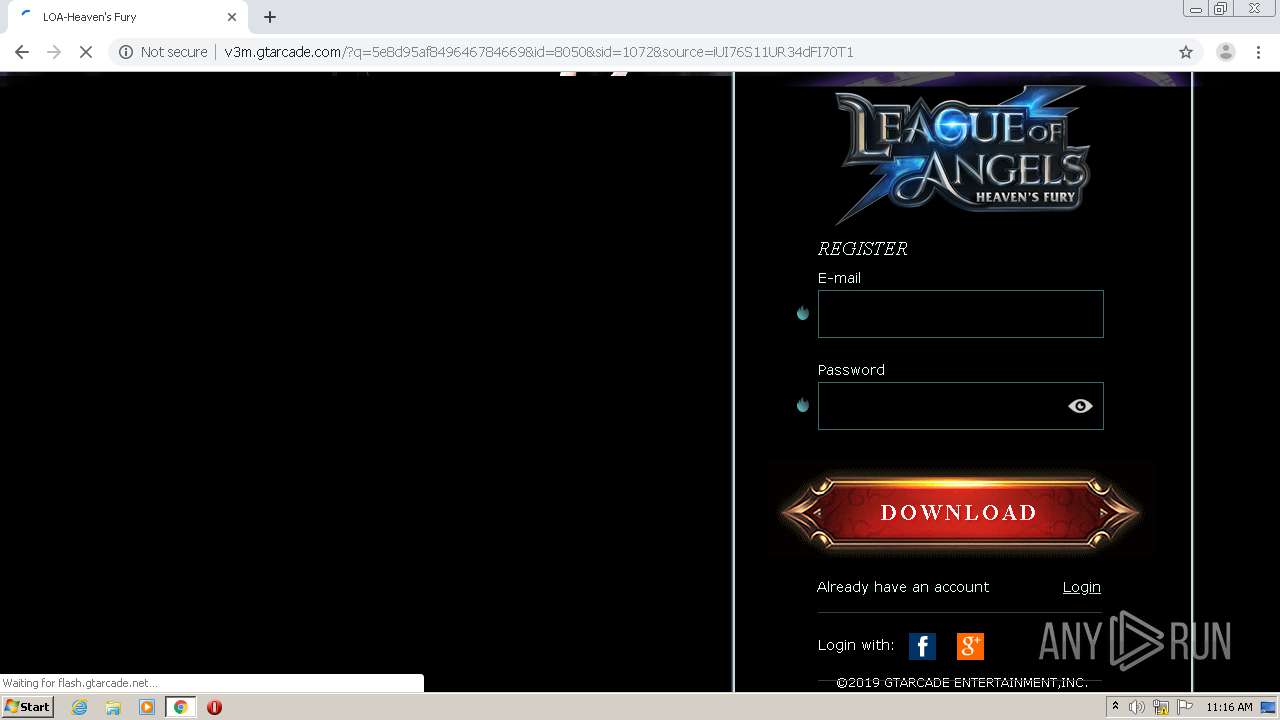
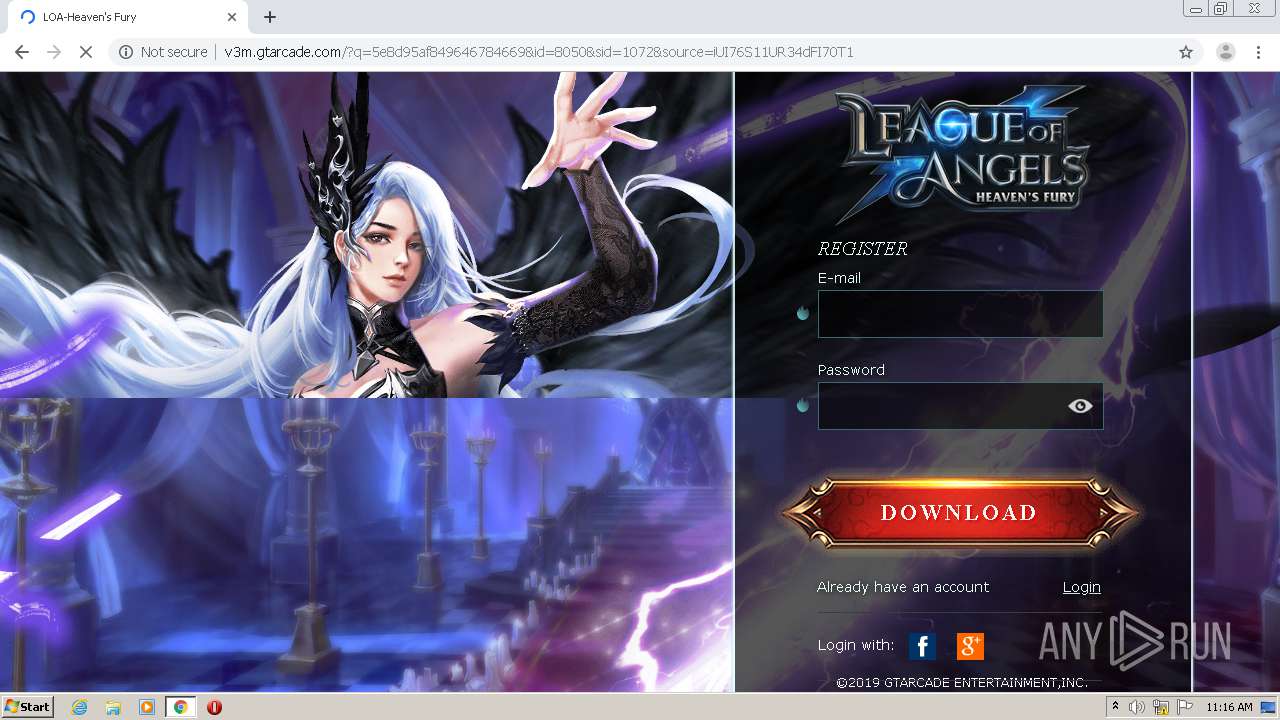
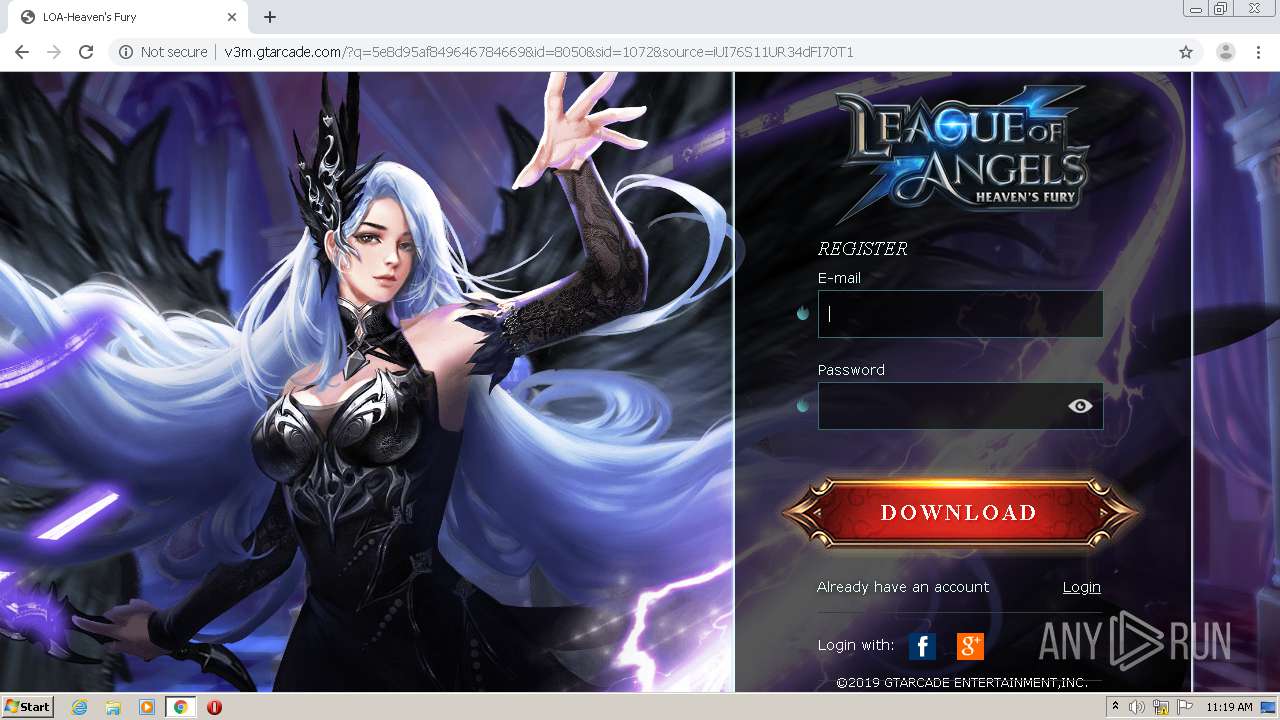
1628 | chrome.exe | 104.75.89.116:80 | v3m.gtarcade.com | Akamai Technologies, Inc. | NL | unknown |
1628 | chrome.exe | 104.75.89.116:443 | v3m.gtarcade.com | Akamai Technologies, Inc. | NL | unknown |
1628 | chrome.exe | 142.250.80.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
1628 | chrome.exe | 142.250.64.77:443 | accounts.google.com | Google Inc. | US | unknown |
1628 | chrome.exe | 184.30.223.111:80 | flash.gtarcade.net | Akamai International B.V. | NL | unknown |
1628 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
professional.pcgamer.site |
| suspicious |
accounts.google.com |
| shared |
foy4a.voluumtrk3.com |
| suspicious |
go.playmmogames.com |
| unknown |
ssl.gstatic.com |
| whitelisted |
v3m.gtarcade.com |
| unknown |
flash.gtarcade.net |
| unknown |
static.gtarcade.com |
| unknown |
apipool.gtarcade.com |
| unknown |
collect.gtarcade.com |
| unknown |